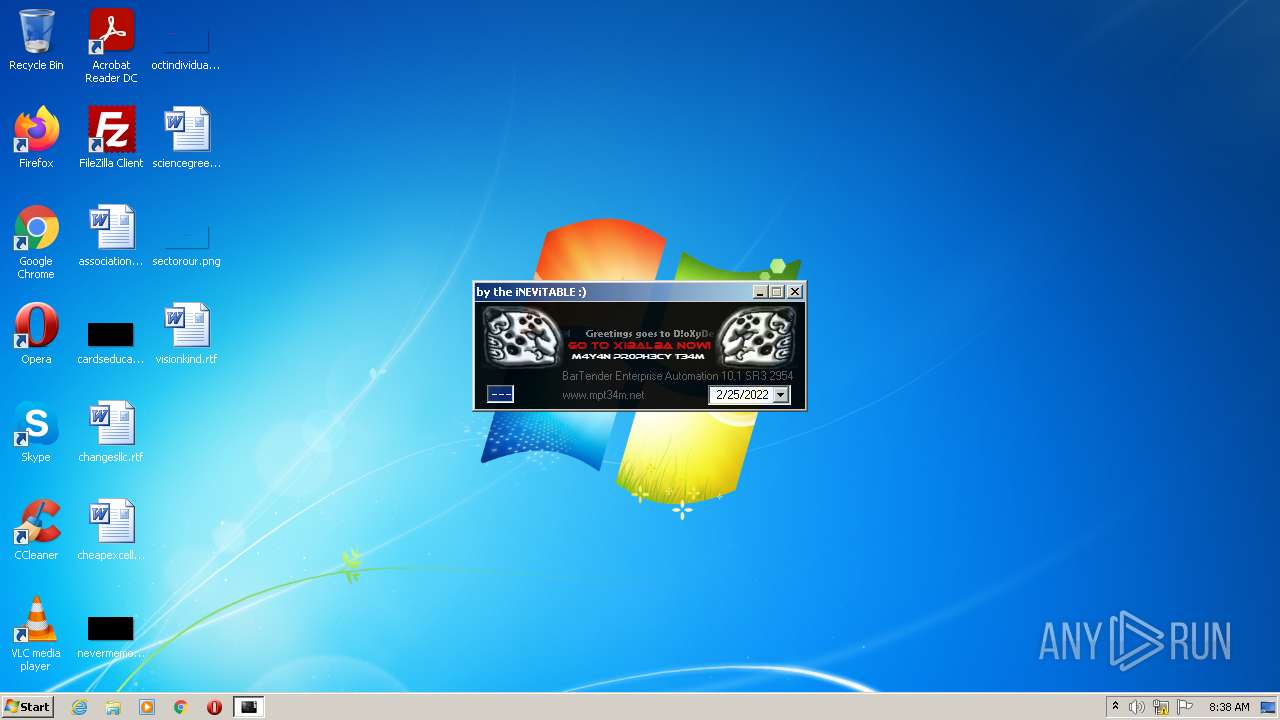
| File name: | bartender.enterprise.automation.10.1.sr3.2954-mpt.exe |
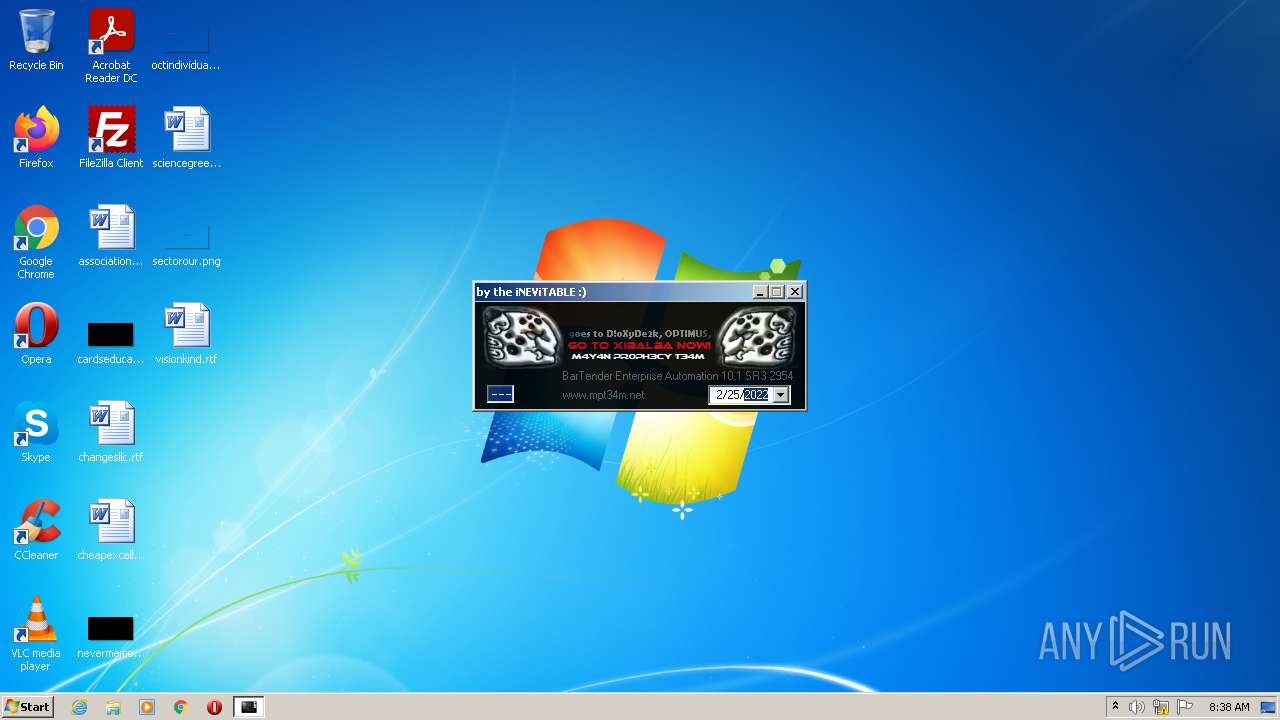
| Full analysis: | https://app.any.run/tasks/99617669-fbdf-4730-8f0c-15c57657903b |
| Verdict: | Malicious activity |
| Analysis date: | February 25, 2022, 08:37:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 1481AE6D9CBBB0D5FE5603186B1C89B7 |
| SHA1: | 95962E1EFE5C35DF063E269698D09AADDBD59BC7 |
| SHA256: | 7021A0D052A36FDD53D0E8F19E30F0C389BC4EFF445AC0CE420EC16BF2B31AFD |
| SSDEEP: | 12288:yieURneQi1mFExzoLLqd5sSQxQ3o9Kt2+aXKXh4QR46eeg6ql8Z+QqVK:yfEMPzoLLqzpQxLKt2J8im46eeg6/Z+a |
MALICIOUS
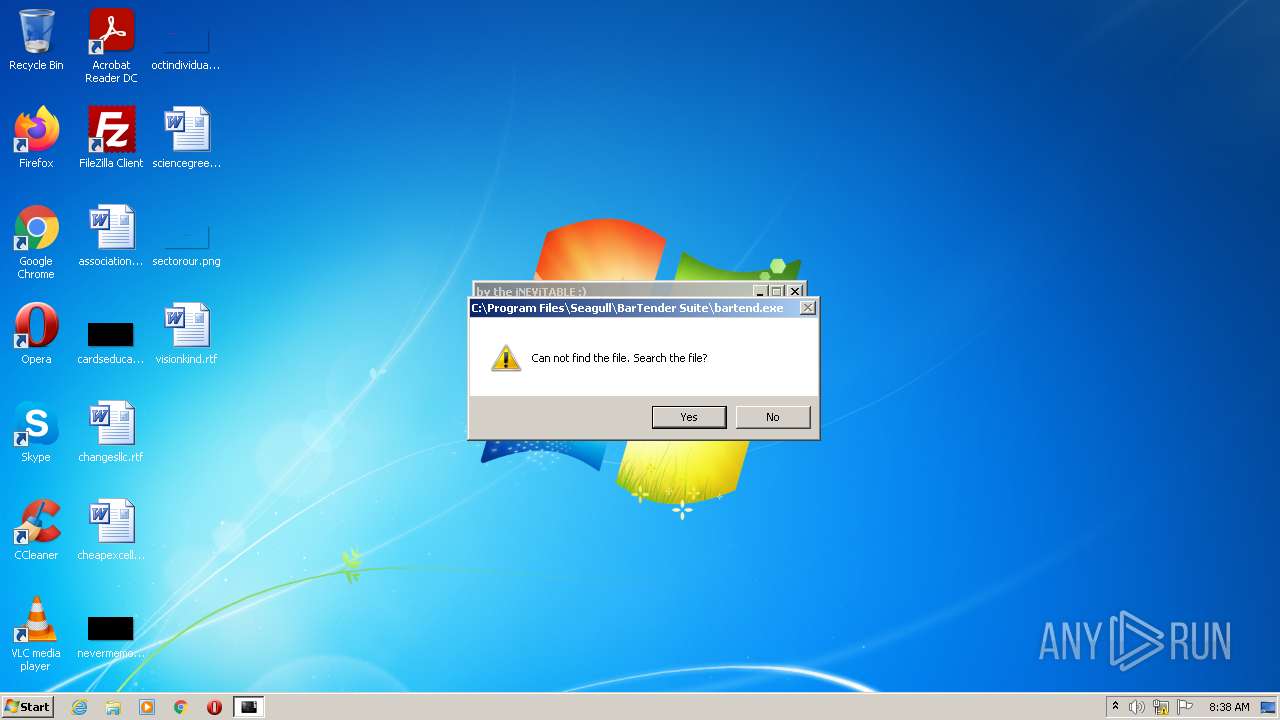
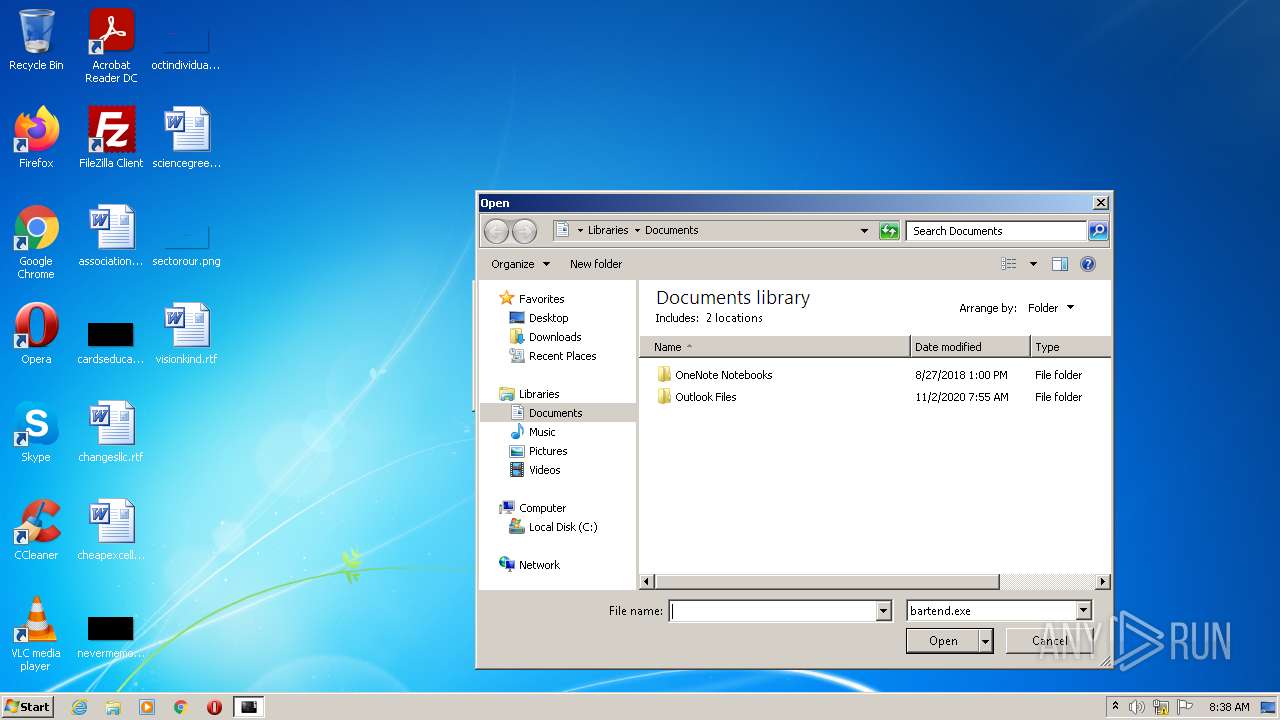
Drops executable file immediately after starts
- bartender.enterprise.automation.10.1.sr3.2954-mpt.exe (PID: 116)
Loads dropped or rewritten executable
- bartender.enterprise.automation.10.1.sr3.2954-mpt.exe (PID: 116)
SUSPICIOUS
Checks supported languages
- bartender.enterprise.automation.10.1.sr3.2954-mpt.exe (PID: 116)
Executable content was dropped or overwritten
- bartender.enterprise.automation.10.1.sr3.2954-mpt.exe (PID: 116)
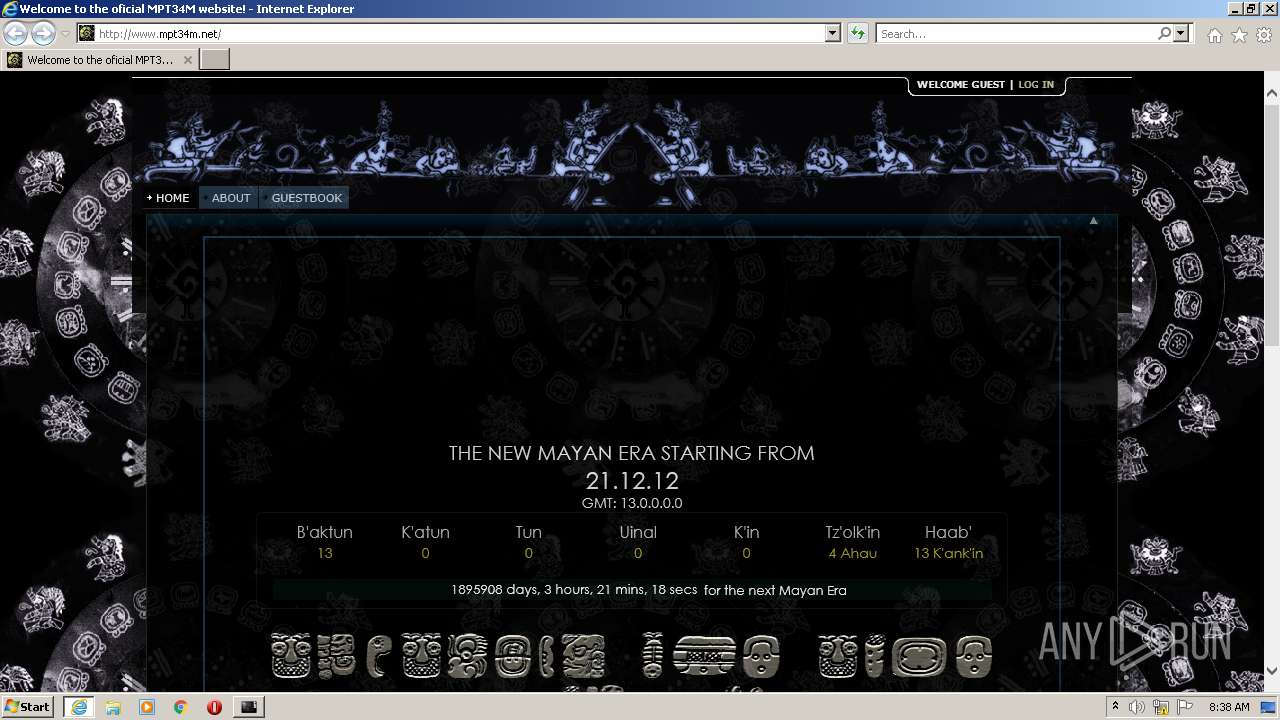
Starts Internet Explorer
- bartender.enterprise.automation.10.1.sr3.2954-mpt.exe (PID: 116)
Drops a file with too old compile date
- bartender.enterprise.automation.10.1.sr3.2954-mpt.exe (PID: 116)
Reads the computer name
- bartender.enterprise.automation.10.1.sr3.2954-mpt.exe (PID: 116)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3260)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2816)
Checks supported languages
- regedit.exe (PID: 692)
- iexplore.exe (PID: 2816)
- iexplore.exe (PID: 3260)
Reads internet explorer settings
- iexplore.exe (PID: 3260)
Checks Windows Trust Settings
- iexplore.exe (PID: 3260)
- iexplore.exe (PID: 2816)
Reads the computer name
- iexplore.exe (PID: 2816)
- iexplore.exe (PID: 3260)
Application launched itself
- iexplore.exe (PID: 2816)
Reads settings of System Certificates
- iexplore.exe (PID: 3260)
- iexplore.exe (PID: 2816)
Changes settings of System certificates
- iexplore.exe (PID: 3260)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3260)
Creates files in the user directory
- iexplore.exe (PID: 3260)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| Subsystem: | Windows GUI |
|---|---|
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x102b |
| UninitializedDataSize: | - |
| InitializedDataSize: | 744960 |
| CodeSize: | 512 |
| LinkerVersion: | 10 |
| PEType: | PE32 |
| TimeStamp: | 2012:12:21 21:59:46+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Dec-2012 20:59:46 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 21-Dec-2012 20:59:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000001F6 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.06408 |
.rdata | 0x00002000 | 0x000001D8 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.27064 |
.data | 0x00003000 | 0x00000034 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.568988 |
.rsrc | 0x00004000 | 0x000B579C | 0x000B5800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.97437 |
.reloc | 0x000BA000 | 0x00000052 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.736046 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.85663 | 898 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 3.34777 | 744 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 3.08777 | 488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 2.65367 | 296 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 5.72922 | 3752 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 6.11731 | 2216 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 6.09324 | 1736 | Latin 1 / Western European | UNKNOWN | RT_ICON |
8 | 4.62248 | 1384 | Latin 1 / Western European | UNKNOWN | RT_ICON |
9 | 4.86341 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
10 | 4.93104 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
Imports
kernel32.dll |
Total processes
43
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | "C:\Users\admin\AppData\Local\Temp\bartender.enterprise.automation.10.1.sr3.2954-mpt.exe" | C:\Users\admin\AppData\Local\Temp\bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | Explorer.EXE | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 692 | "C:\Windows\regedit.exe" /s "C:\Users\admin\AppData\Local\Temp\\regpatch.reg" | C:\Windows\regedit.exe | — | bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2816 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.mpt34m.net/ | C:\Program Files\Internet Explorer\iexplore.exe | bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3260 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2816 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3740 | "C:\Users\admin\AppData\Local\Temp\bartender.enterprise.automation.10.1.sr3.2954-mpt.exe" | C:\Users\admin\AppData\Local\Temp\bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | — | Explorer.EXE | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
18 143
Read events
17 937
Write events
205
Delete events
1
Modification events
| (PID) Process: | (116) bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (116) bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (116) bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (116) bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (692) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Seagull Scientific\BarTender\Licensing\10.0 |
| Operation: | write | Name: | Product Key Code |
Value: M4Y4NPR0PH3CYT34M | |||
| (PID) Process: | (692) regedit.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Seagull Scientific\BarTender\Licensing\10.1 |
| Operation: | write | Name: | Product Key Code |
Value: M4Y4NPR0PH3CYT34M | |||
| (PID) Process: | (116) bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (116) bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 02000000010000000D0000000C000000000000000B00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (116) bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_FolderType |
Value: {FBB3477E-C9E4-4B3B-A2BA-D3F5D3CD46F9} | |||
| (PID) Process: | (116) bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\Bags\50\ComDlg |
| Operation: | write | Name: | TV_TopViewID |
Value: {82BA0782-5B7A-4569-B5D7-EC83085F08CC} | |||
Executable files
3
Suspicious files
9
Text files
38
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\J2YUNK7K.htm | html | |
MD5:D4C9FC68B36C8BEF5A4515C44A0997F3 | SHA256:D165520D414953639C48AEF58BD9B67952AC6A80C7CA0374C6762EB4DB738137 | |||
| 116 | bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | C:\Users\admin\AppData\Local\Temp\bassmod.dll | executable | |
MD5:780D14604D49E3C634200C523DEF8351 | SHA256:844EB66A10B848D3A71A8C63C35F0A01550A46D2FF8503E2CA8947978B03B4D2 | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\zen_18_dropdown_v1_2_1[1].gif | image | |
MD5:7F7CA5B65719FB906CF83A6431F057E7 | SHA256:75E98FA40D10F4F9DF5A5183484E7FFADE4233715B048D44EF113997A2DD5BF8 | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\zen_18_dropdown_v1_2_3[1].gif | image | |
MD5:AB1D91A77AF4FBB189F52C4ACB7DC0A3 | SHA256:8BEDCDA3588F43827FCD985F9B19CC0FDF600880E3B0745C736A1B83A2AAF624 | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\jquery_utils[1].js | text | |
MD5:208E99007D8D50F9C24670EBFCD70C79 | SHA256:C8B92E64CCA1F9E138874FA267DF226A5F544B5203EA164ED1AD59EC7D7AE43E | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\zen_18_dropdown_v1_2_4[1].gif | image | |
MD5:D940469EE17B2346E8E611BE5638D01A | SHA256:663B9778AD702EDC99B4FDD75001426E52612D1C6BB7B4088074194CD331D86C | |||
| 116 | bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | C:\Users\admin\AppData\Local\Temp\Berlin Sans FB.TTF | odttf | |
MD5:FE2027C27B6A24505F548C6FD2E1076D | SHA256:0B6044C72E67AAAE9C2AE3C8B4BB06D066FDBC02779C68E3883984ACBBE24CB8 | |||
| 116 | bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | C:\Users\admin\AppData\Local\Temp\dup2patcher.dll | executable | |
MD5:D2E2AD01BEA3BDA62F490B3A1A0C008A | SHA256:4E088116F9FE471A21F2C941C77CC700F804751AB482BB821310F38EF68AD517 | |||
| 116 | bartender.enterprise.automation.10.1.sr3.2954-mpt.exe | C:\Users\admin\AppData\Local\Temp\regpatch.reg | text | |
MD5:B43DE2C38E12D2FDC16C31CDFF8DCEB2 | SHA256:633BC1BAF29F22A791D1B5304481837000B15359201A59763C9E5979BBA09ACA | |||
| 3260 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\textstyles_nf[1].css | text | |
MD5:3CB9DAB1CFF72285E3DA6A37C684FD9E | SHA256:53995401BE1D103A8C5CC04DC980D34F69C968A47B939F81F402889C938525FF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
21
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3260 | iexplore.exe | GET | 200 | 91.223.82.6:80 | http://www.mpt34m.net/documents/textstyles_nf.css | NL | compressed | 7.53 Kb | malicious |
3260 | iexplore.exe | GET | 200 | 91.223.82.6:80 | http://www.mpt34m.net/jquery_utils.js | NL | compressed | 26.9 Kb | malicious |
3260 | iexplore.exe | GET | 200 | 91.223.82.6:80 | http://www.mpt34m.net/ | NL | compressed | 4.51 Kb | malicious |
3260 | iexplore.exe | GET | 200 | 91.223.82.6:80 | http://www.mpt34m.net/extdocs/rssReader.php?action=true&url=https://www.mpt34m.net/tutos%2Ephp%3Faction%3Drss&headeron=true&h=5&style=12&ima=true&datestyle=8&titleon=true&titlelink=true&dateon=true&twidth=500&df=&loc=EN&descon=true&descstyle=80&max=0&rows=1&e_h=&align=0&rand=true&rev=false&cnt=0&etarget=&tic_h=150&tic_id=rss_9&tic_d=3000&tic_c=4&tic_du=1000&tic_dir=0&novid=1&root=1&tic_nb=1&x=1&l=1 | NL | compressed | 8.58 Kb | malicious |
3260 | iexplore.exe | GET | 200 | 91.223.82.6:80 | http://www.mpt34m.net/innovaeditor/scripts/style/innova.css | NL | compressed | 1.37 Kb | malicious |
3260 | iexplore.exe | GET | 200 | 91.223.82.6:80 | http://www.mpt34m.net/innovaeditor/bootstrap/css/bootstrap.css | NL | compressed | 6.73 Kb | malicious |
3260 | iexplore.exe | GET | 200 | 91.223.82.6:80 | http://www.mpt34m.net/2bmos.png | NL | image | 30.7 Kb | malicious |
3260 | iexplore.exe | GET | 200 | 91.223.82.6:80 | http://www.mpt34m.net/1amos_1.png | NL | image | 62.1 Kb | malicious |
3260 | iexplore.exe | GET | 200 | 91.223.82.6:80 | http://www.mpt34m.net/bitcoin_383_920568_1.png | NL | image | 24.4 Kb | malicious |
3260 | iexplore.exe | GET | 200 | 91.223.82.6:80 | http://www.mpt34m.net/13BAKOPT_midnight_mos.png | NL | image | 159 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3260 | iexplore.exe | 91.223.82.6:80 | www.mpt34m.net | Iws Networks LLC | NL | malicious |
3260 | iexplore.exe | 142.250.185.170:443 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3260 | iexplore.exe | 104.18.11.207:80 | netdna.bootstrapcdn.com | Cloudflare Inc | US | suspicious |
3260 | iexplore.exe | 8.248.119.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
3260 | iexplore.exe | 142.250.184.227:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3260 | iexplore.exe | 185.60.216.19:443 | connect.facebook.net | Facebook, Inc. | IE | whitelisted |
3260 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3260 | iexplore.exe | 185.60.216.15:443 | web.facebook.com | Facebook, Inc. | IE | whitelisted |
2816 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
2816 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mpt34m.net |
| malicious |
ajax.googleapis.com |
| whitelisted |
netdna.bootstrapcdn.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
connect.facebook.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
web.facebook.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |