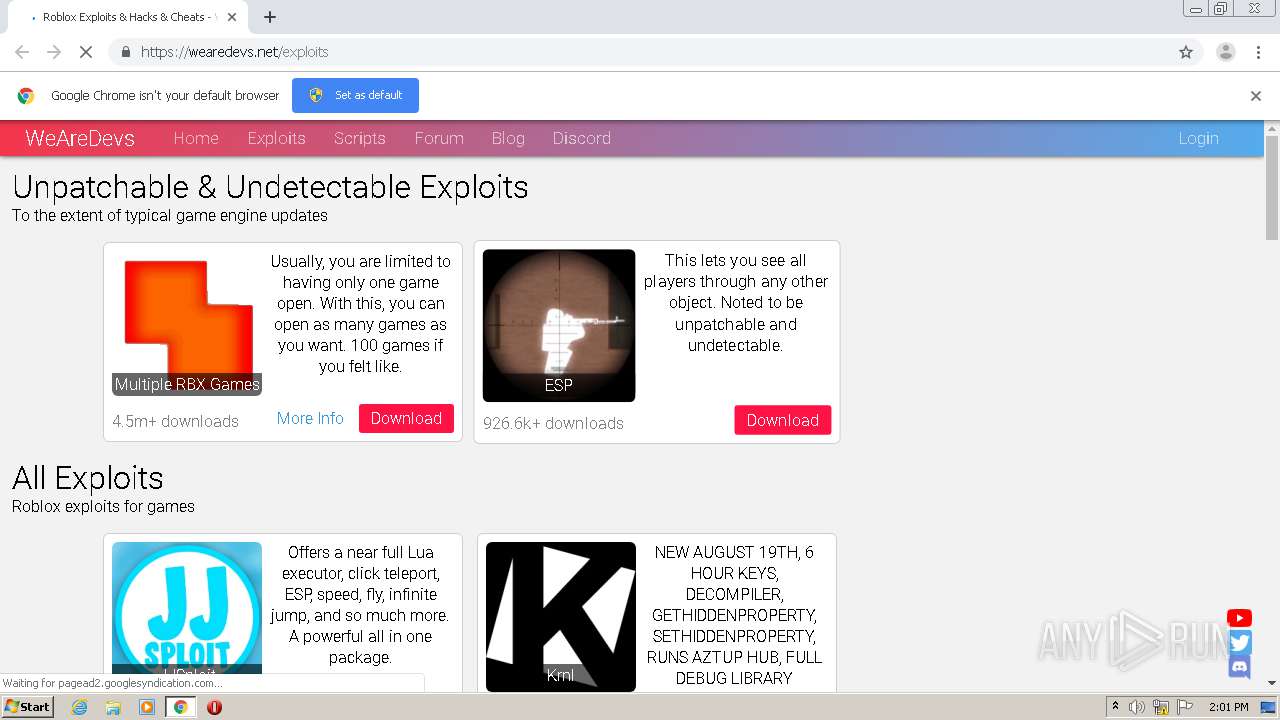
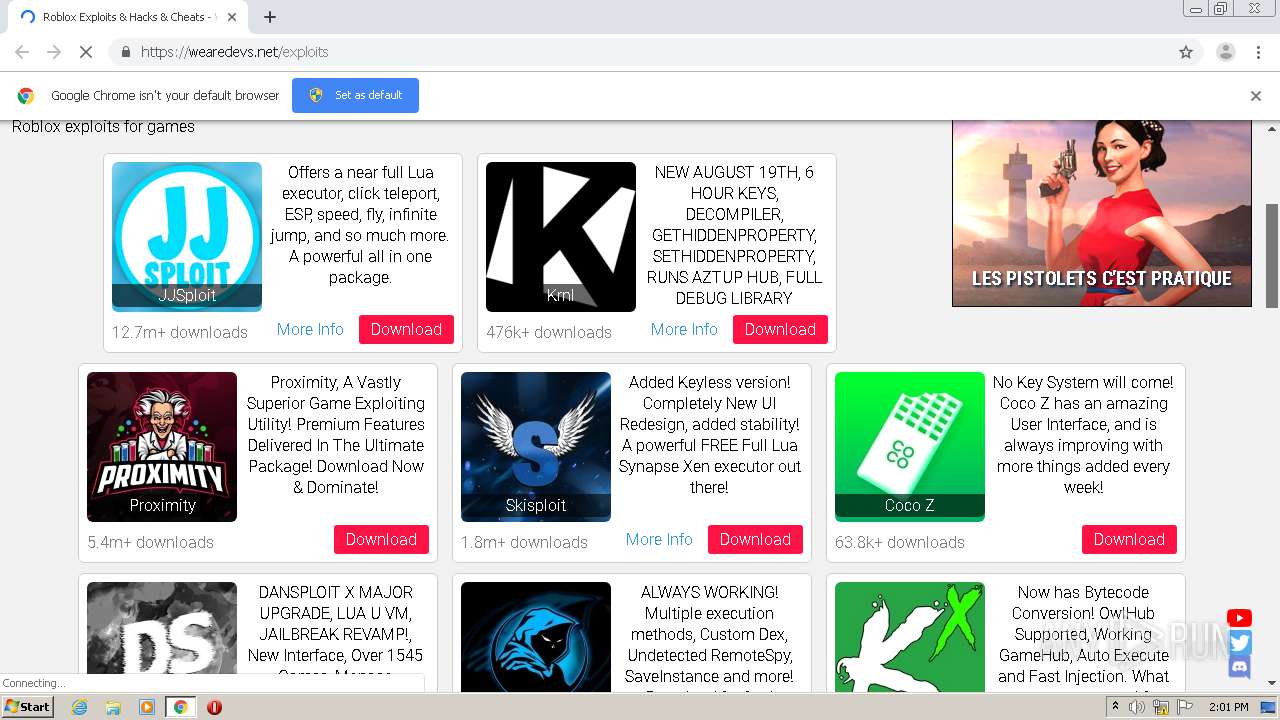
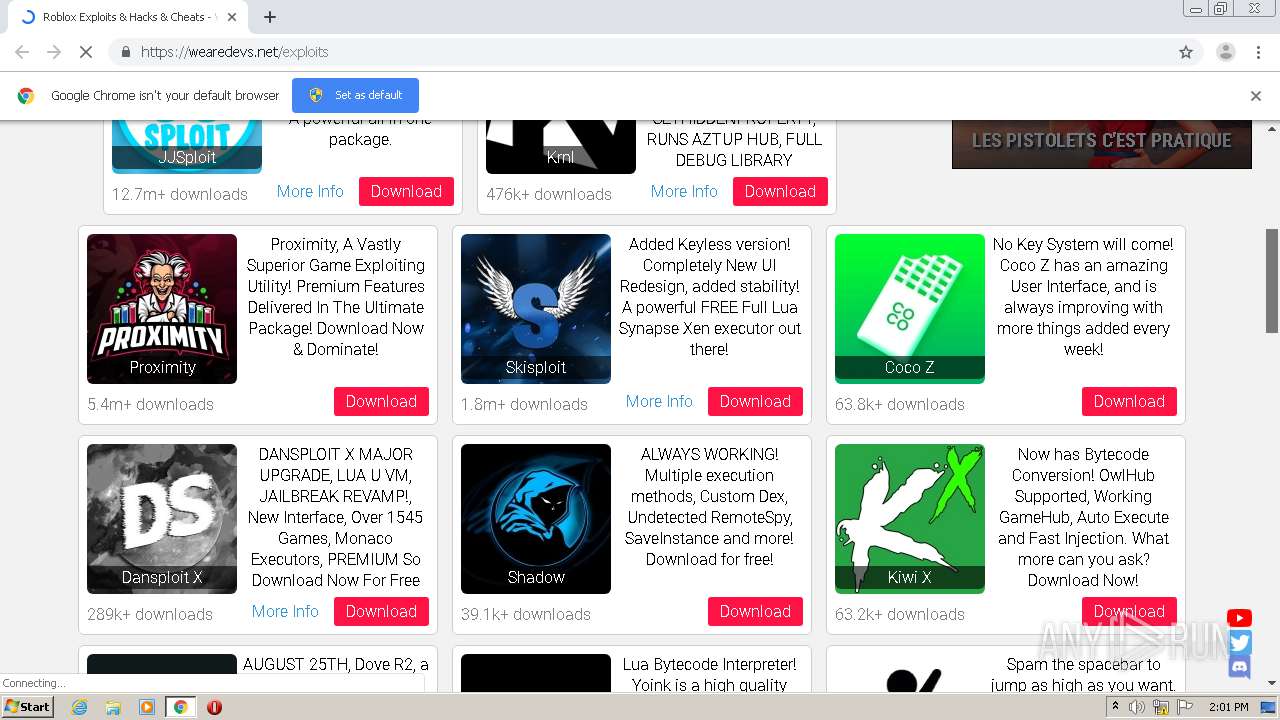
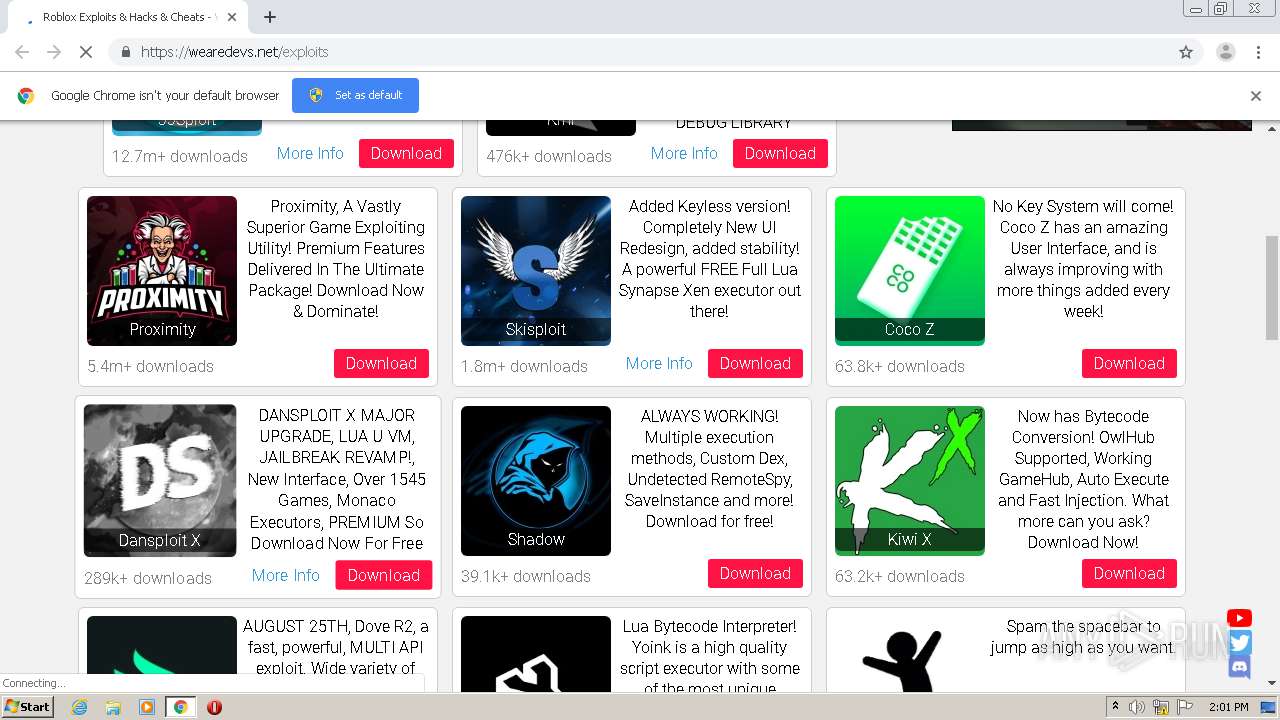
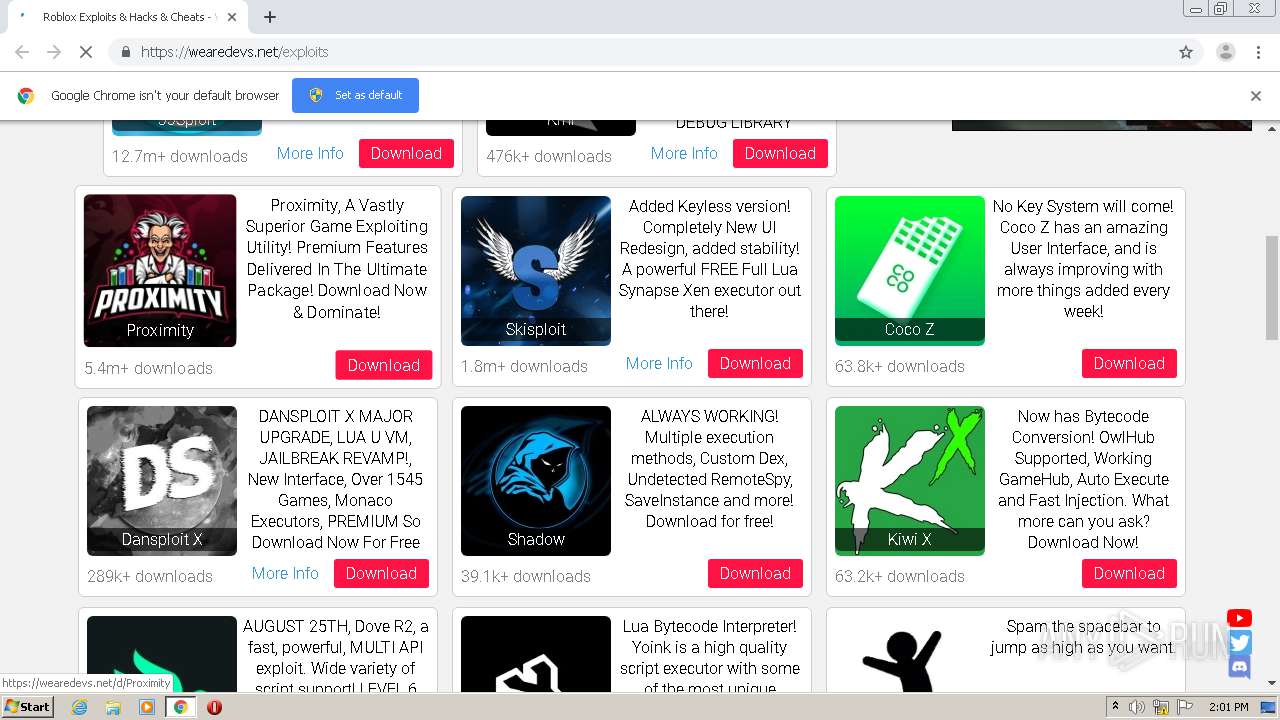
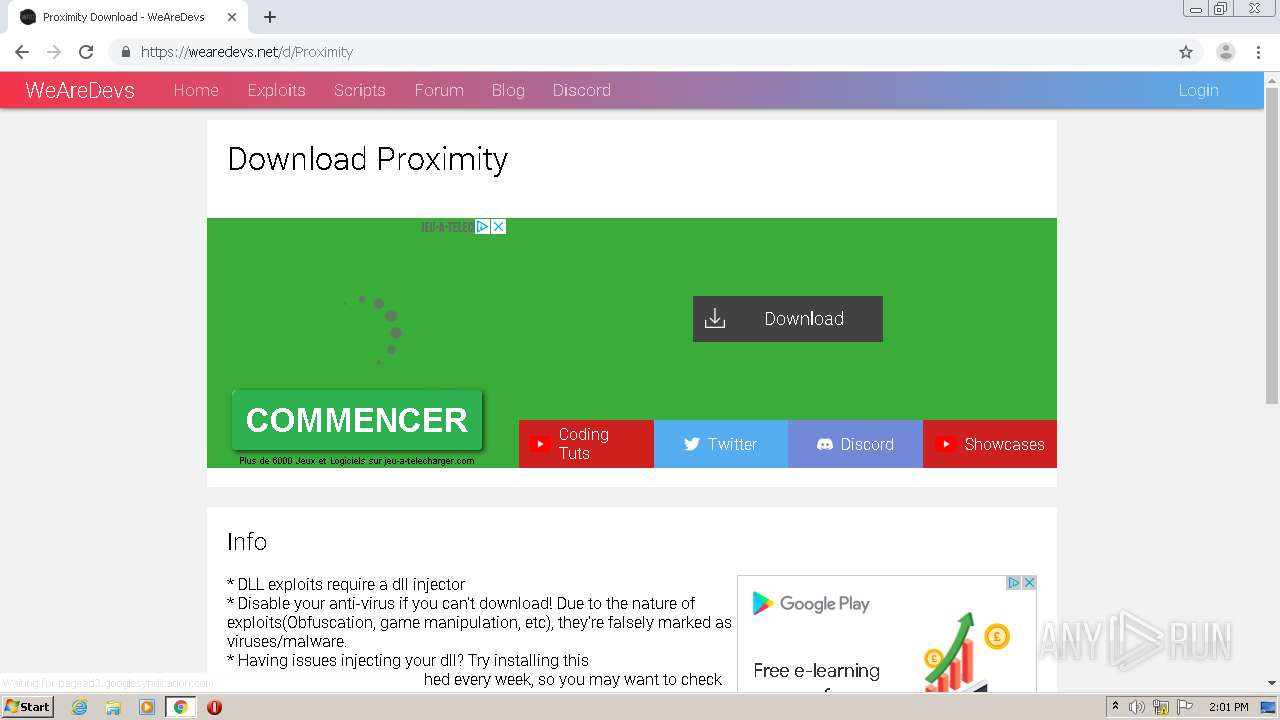
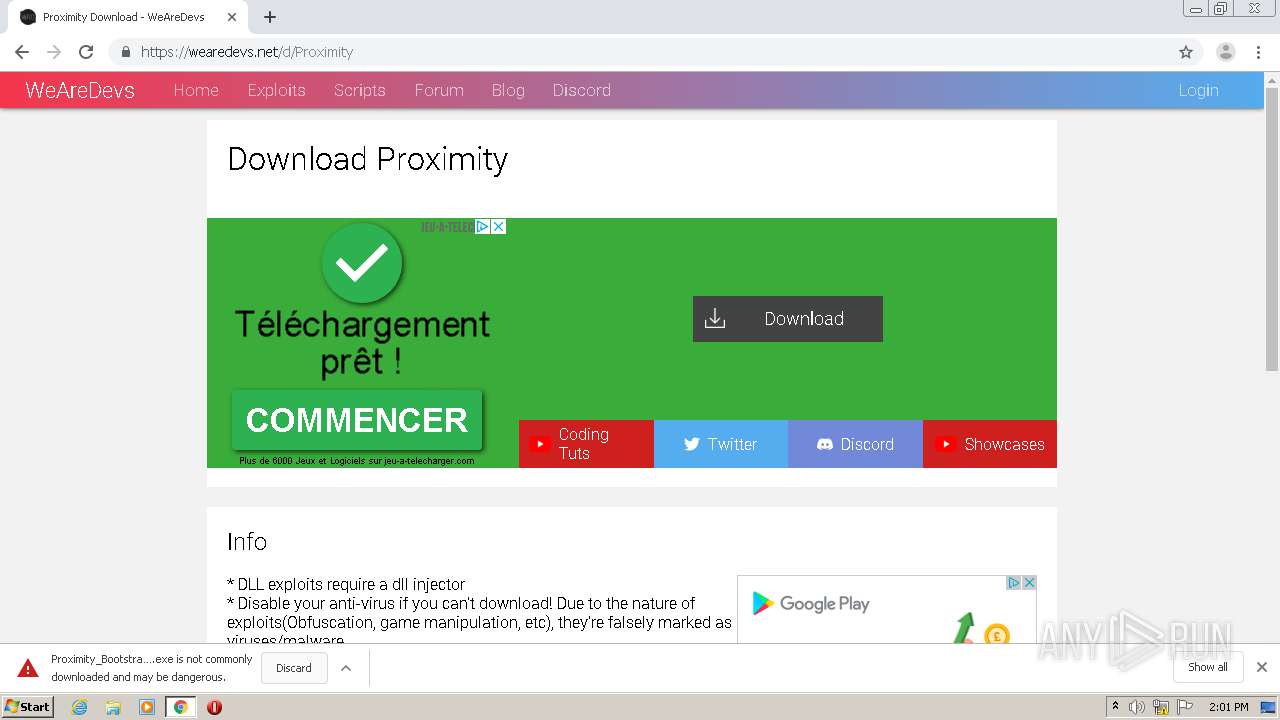
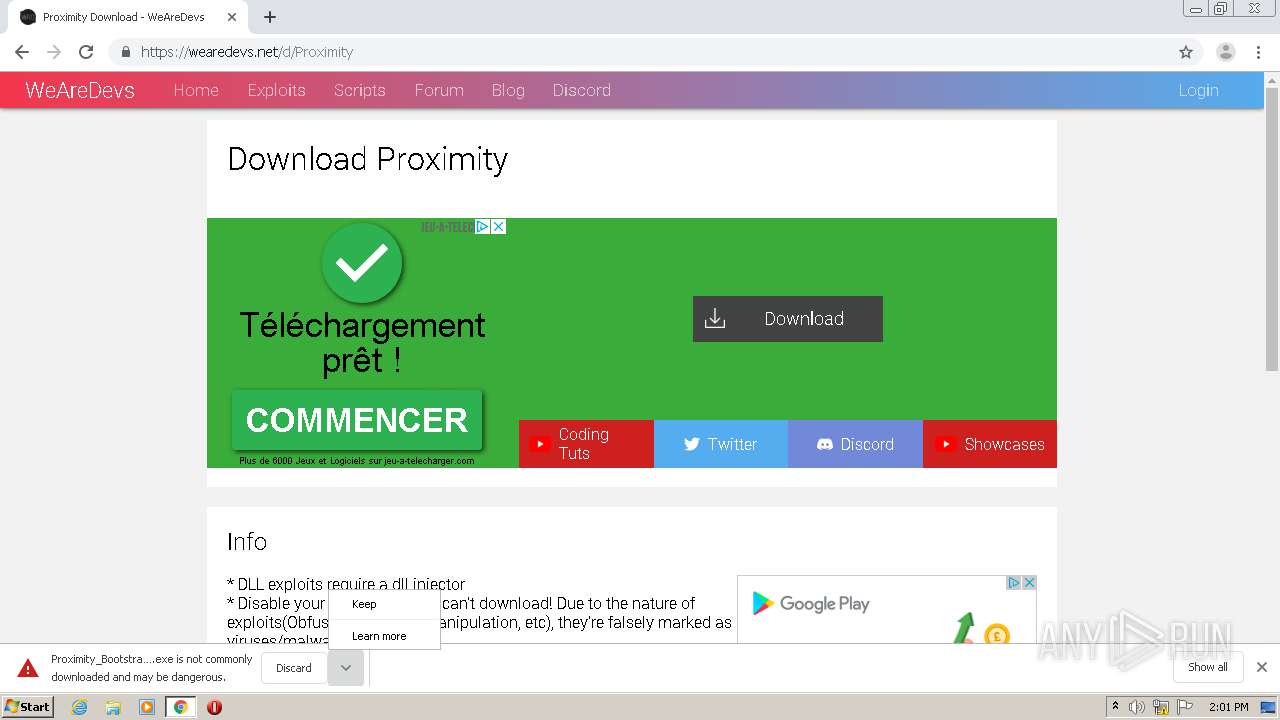
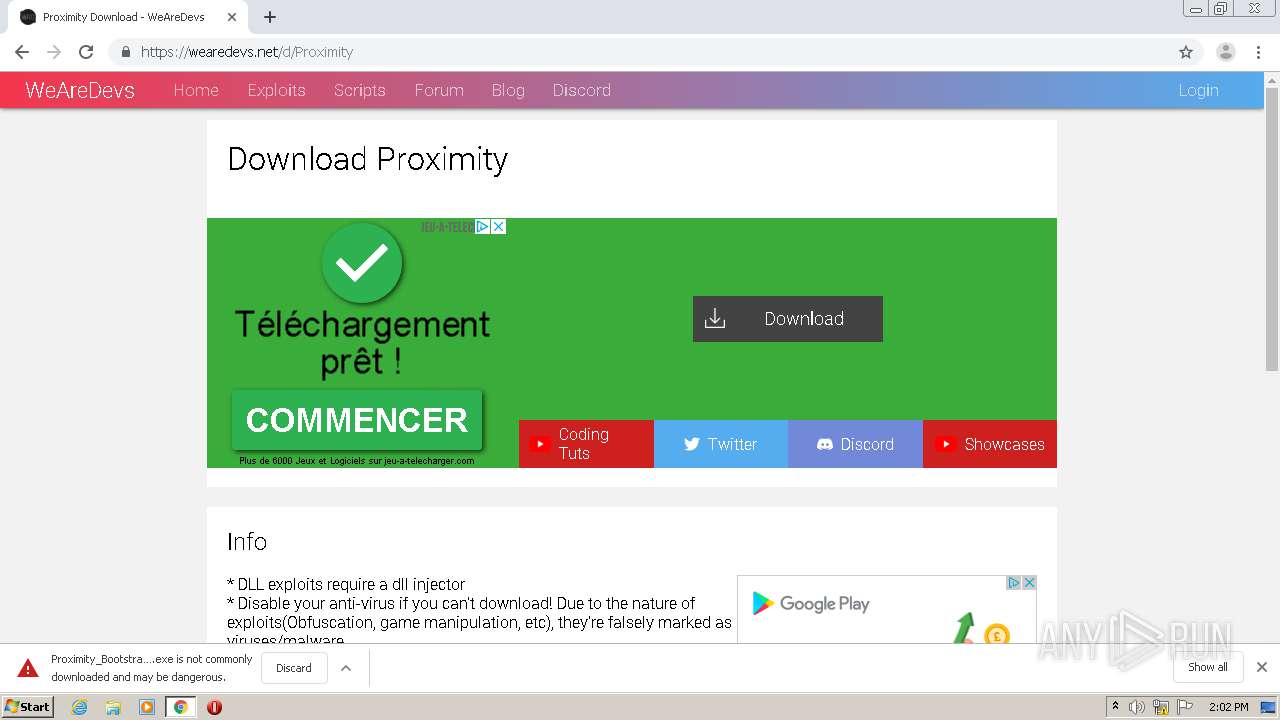
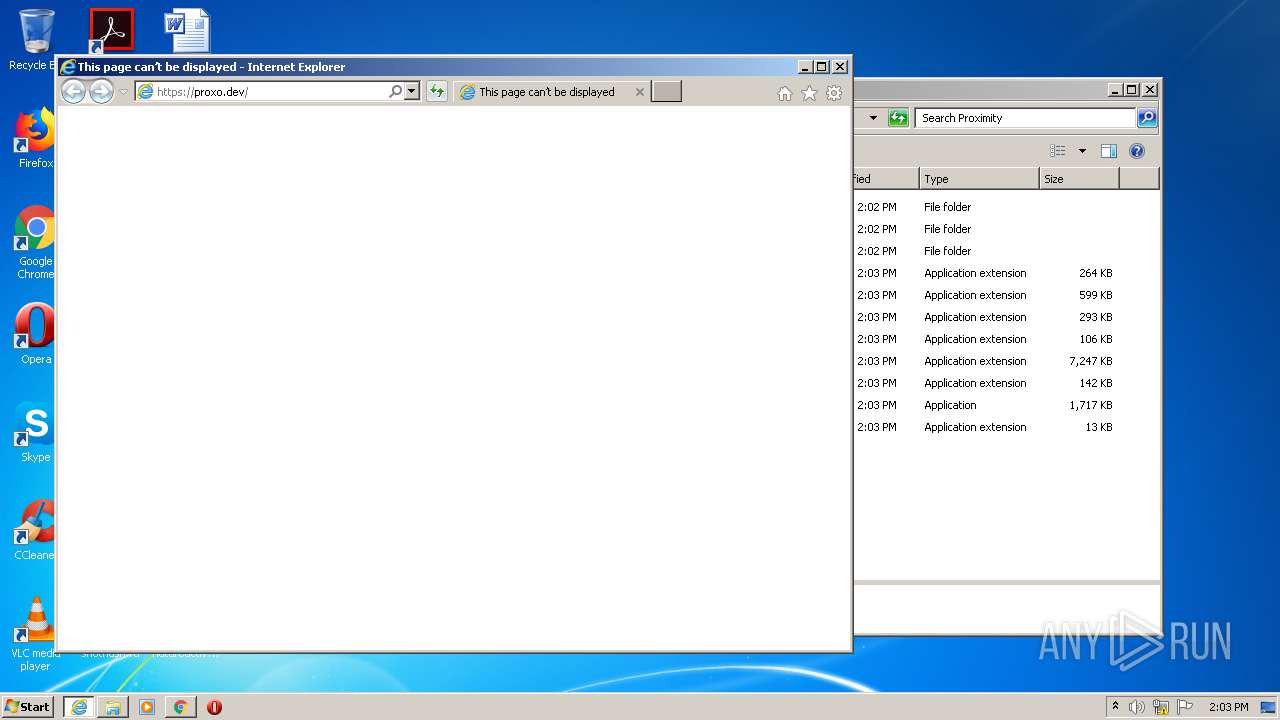
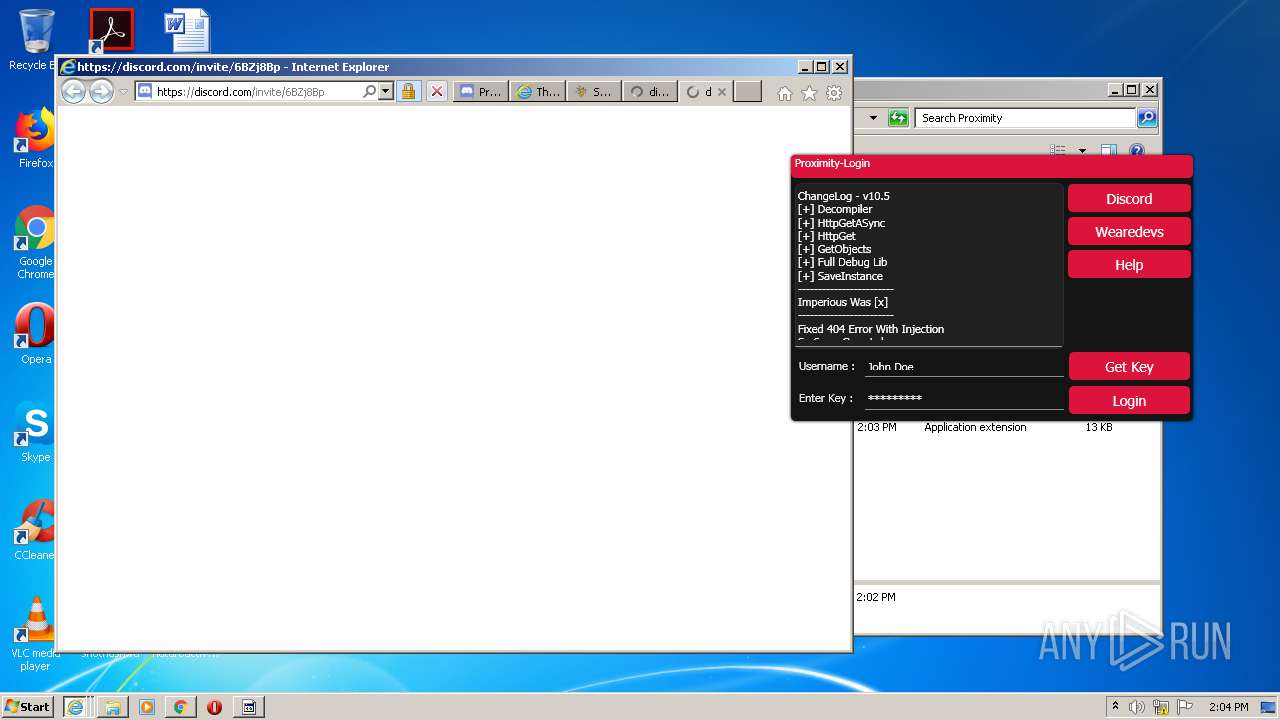
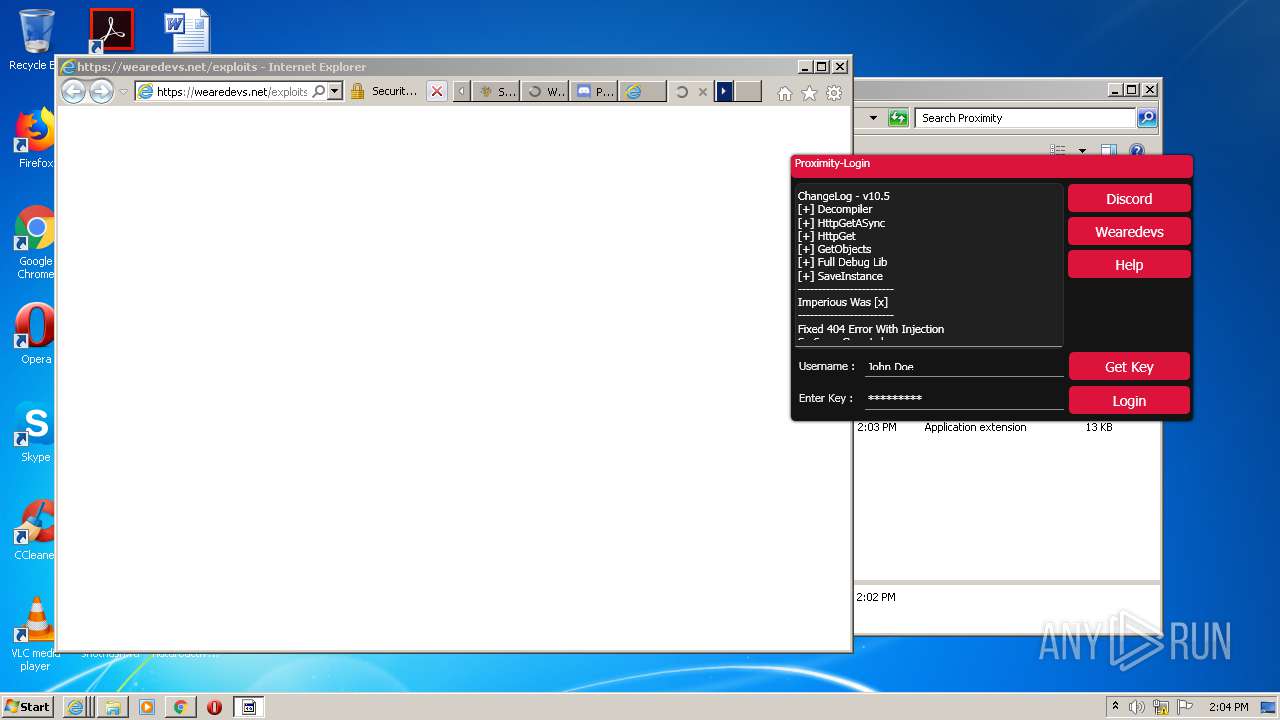
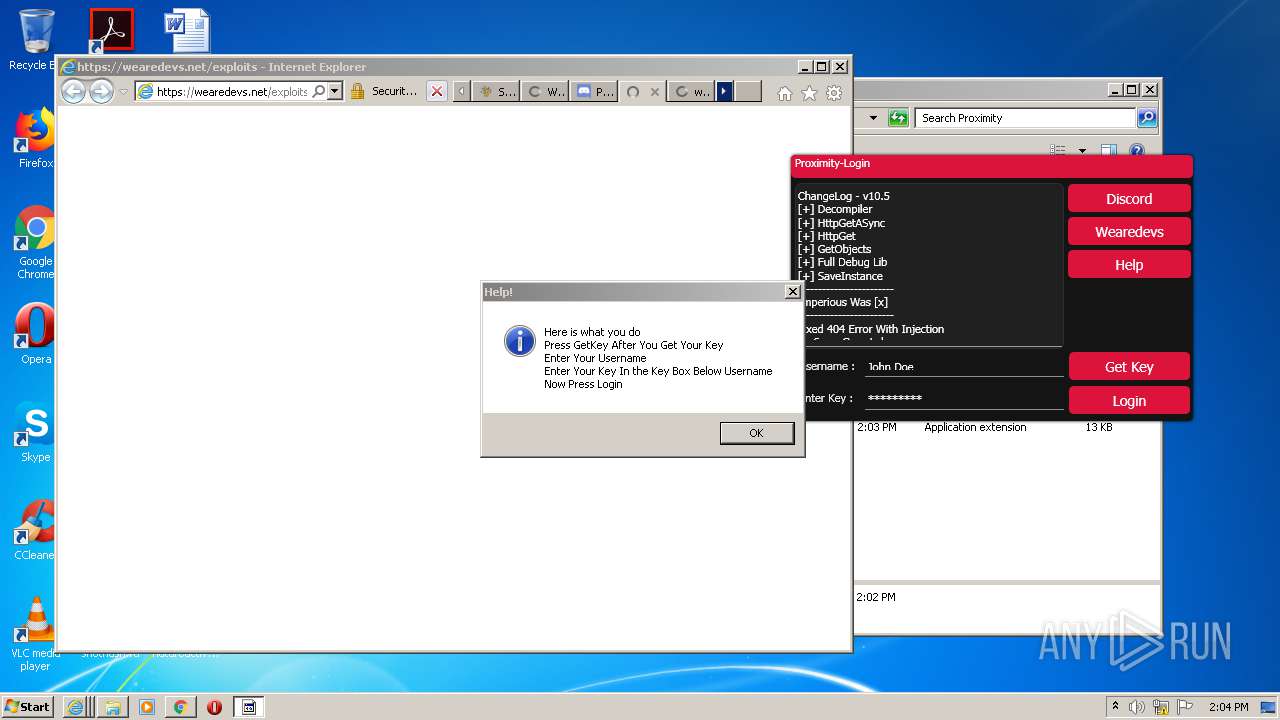
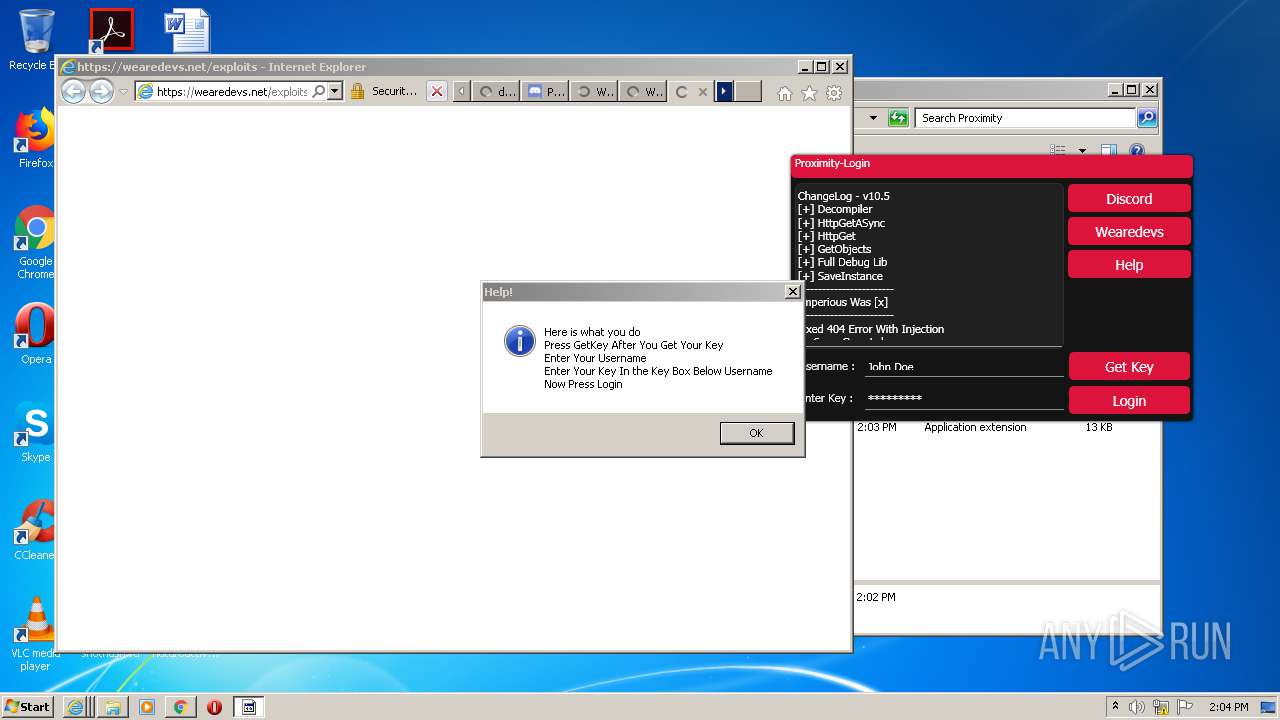
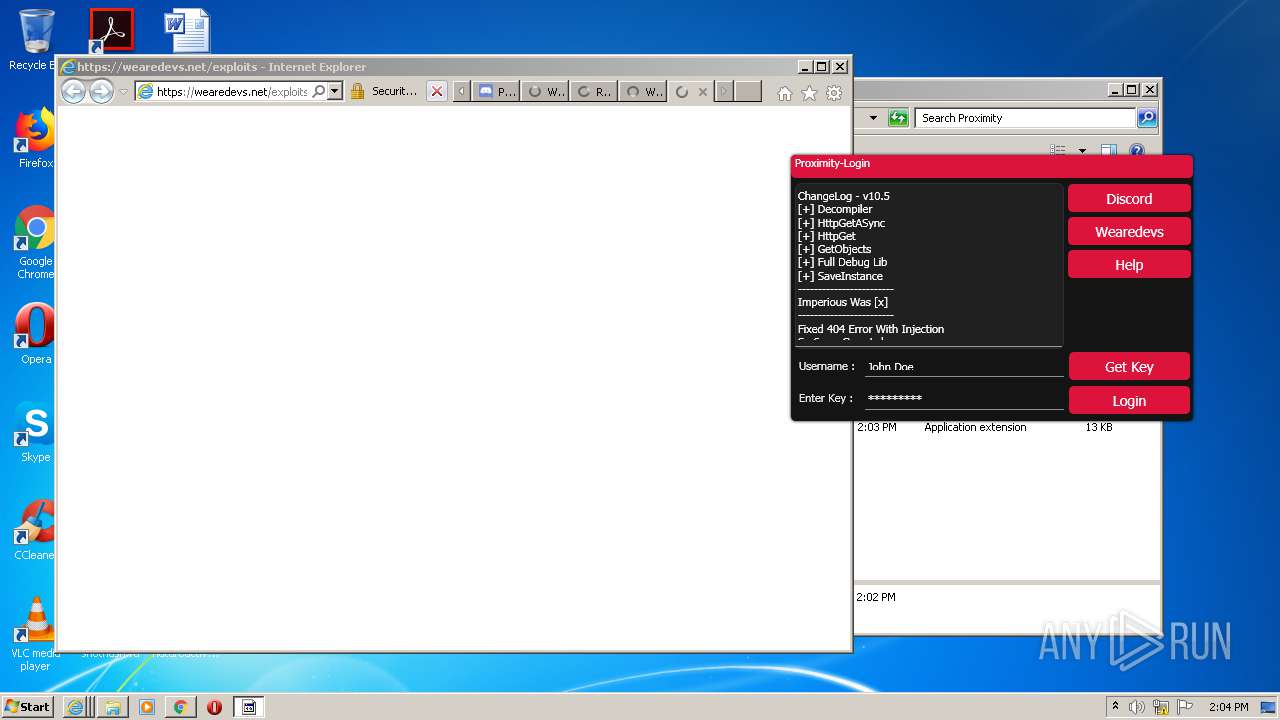
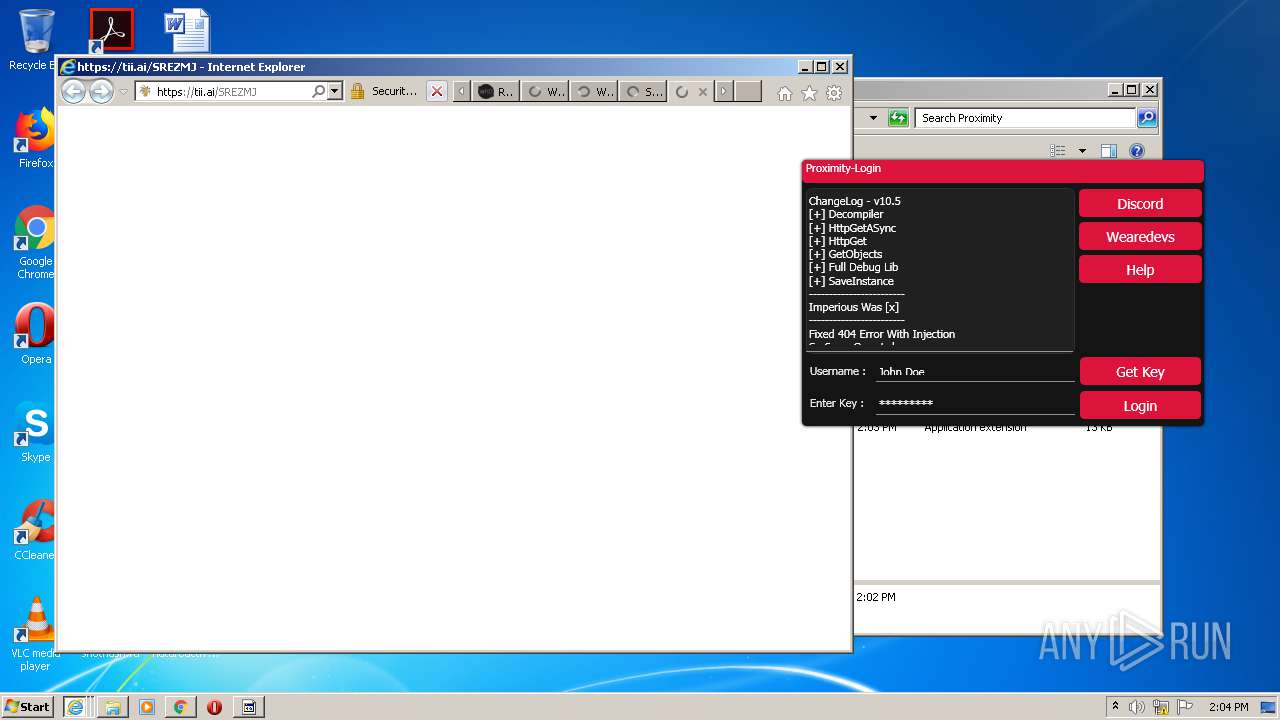
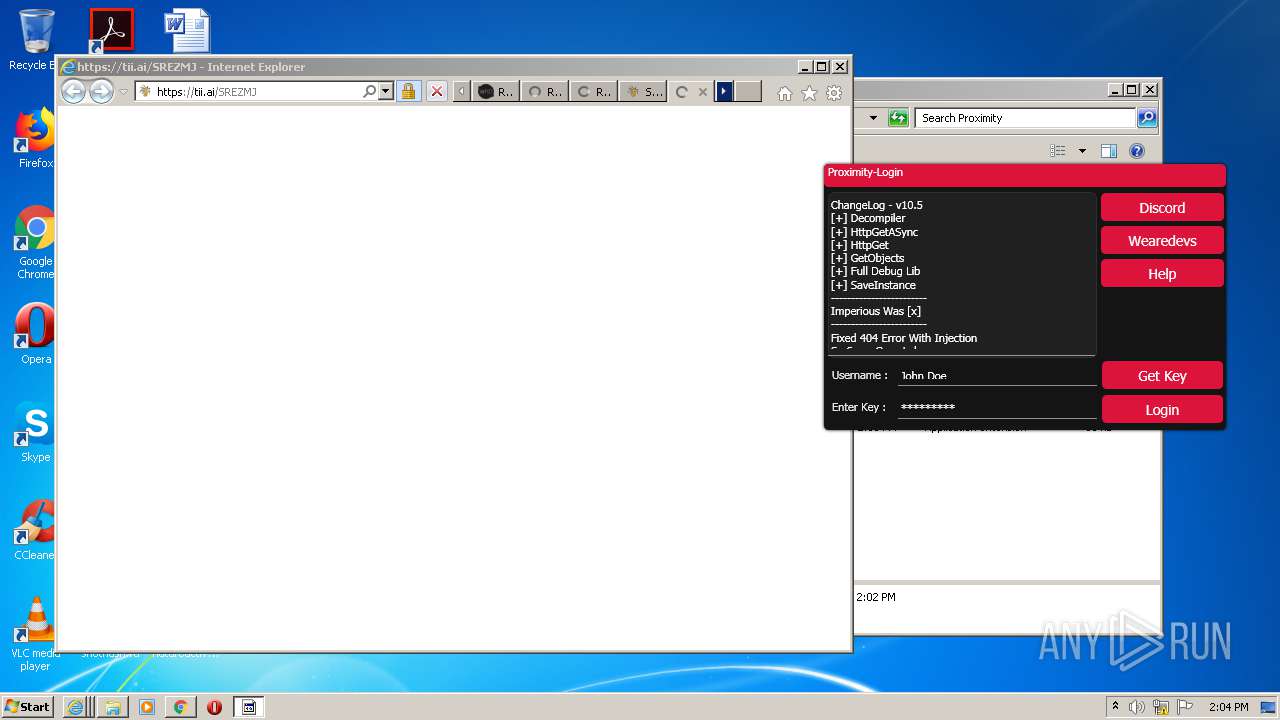
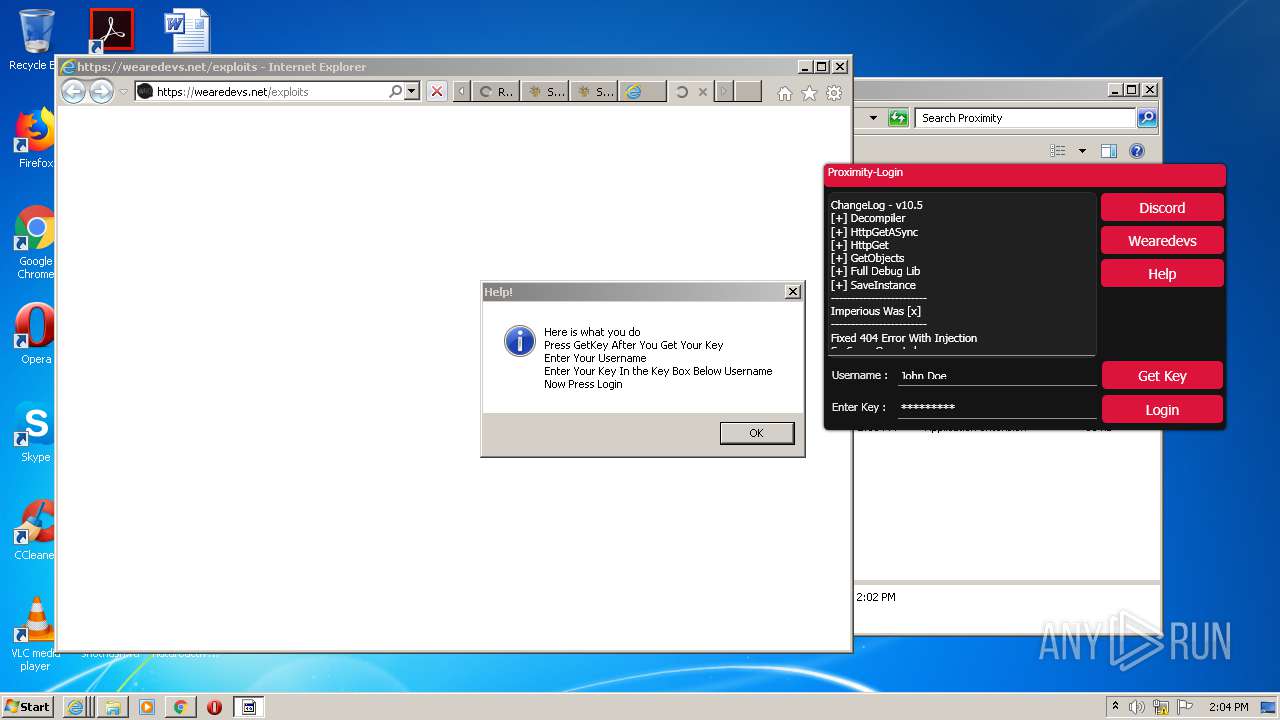
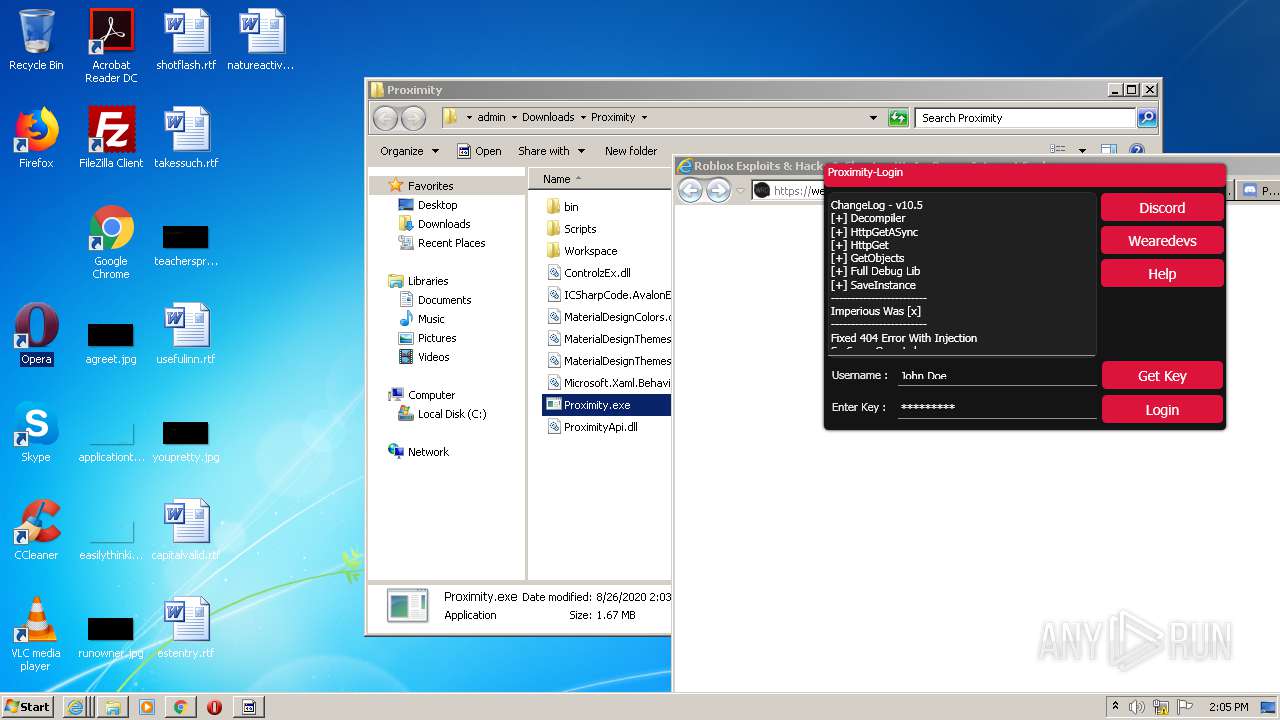
| URL: | https://wearedevs.net/exploits |
| Full analysis: | https://app.any.run/tasks/638a2965-63bf-4079-9d89-af6439e762c6 |
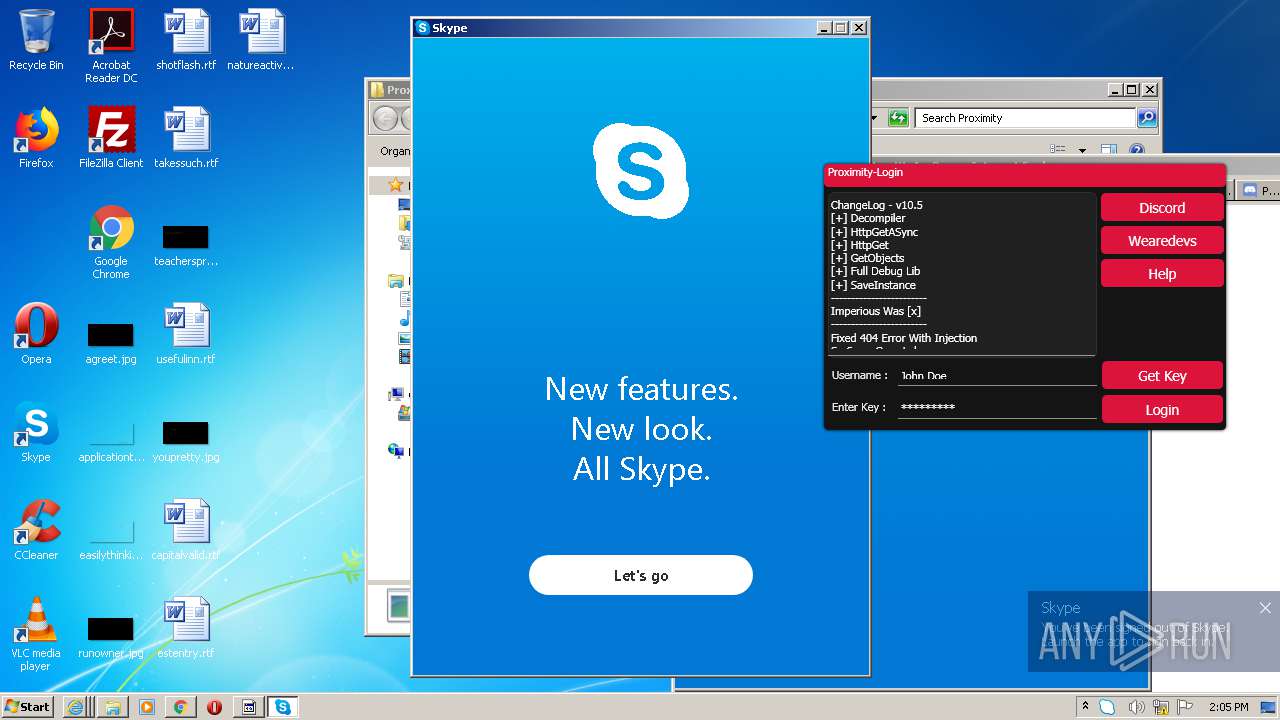
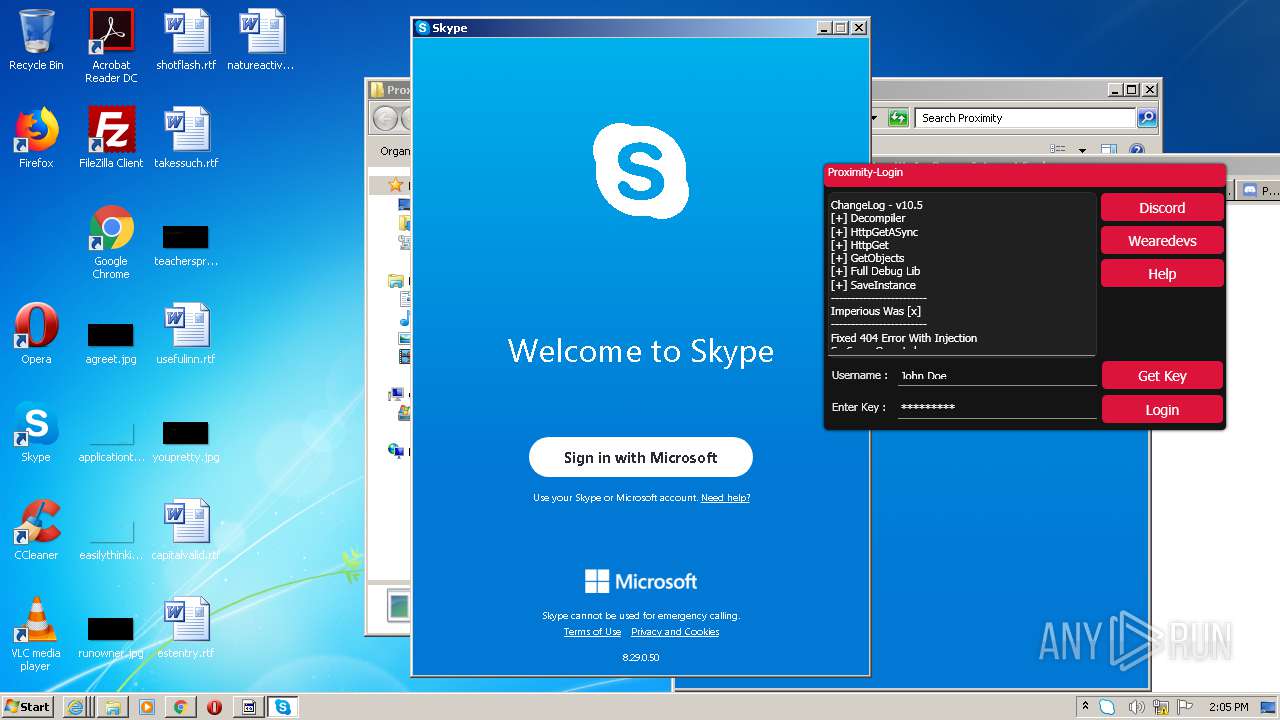
| Verdict: | Malicious activity |
| Analysis date: | August 26, 2020, 13:01:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A30BCDF6A2392436D6EB27CF9CCA01D6 |
| SHA1: | 6457EA1346387E57B5DD8097576710DF7A9FB266 |
| SHA256: | 7017467F047C32C773BD9A9CA012F5214812B39127EAA94043FB36D317C83CB3 |
| SSDEEP: | 3:N8R/BApKYEMw:25BuRw |
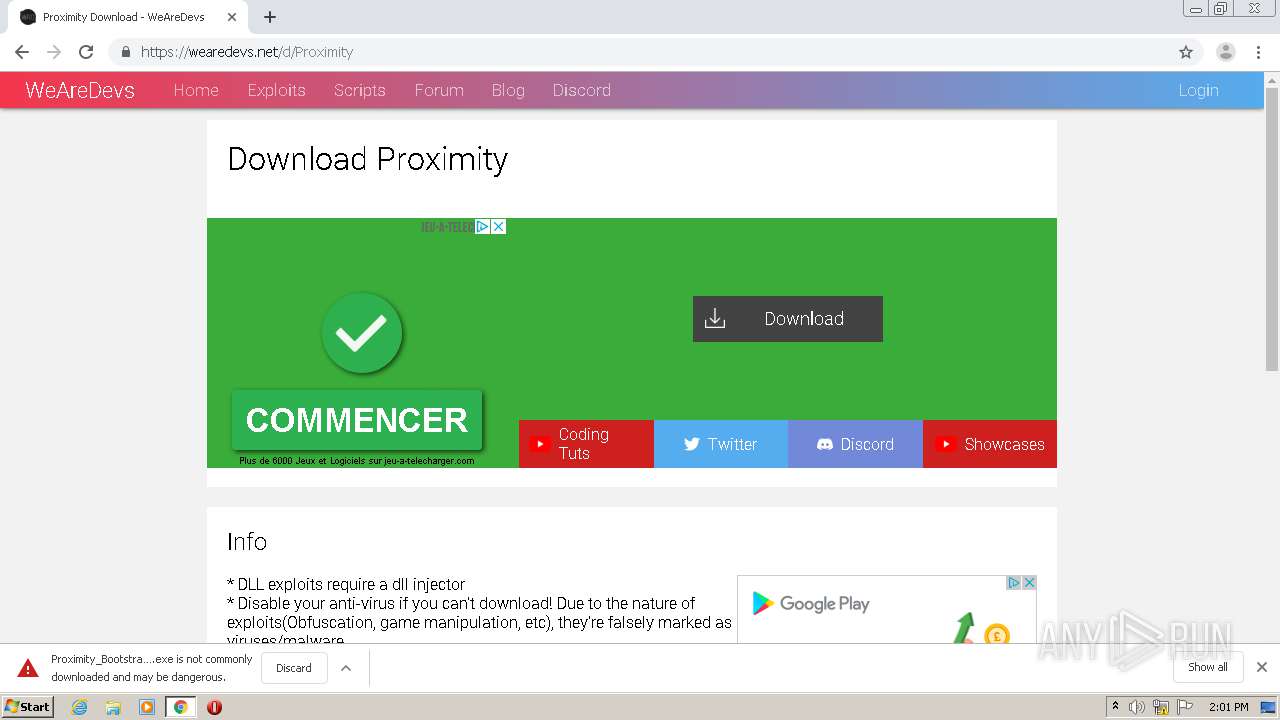
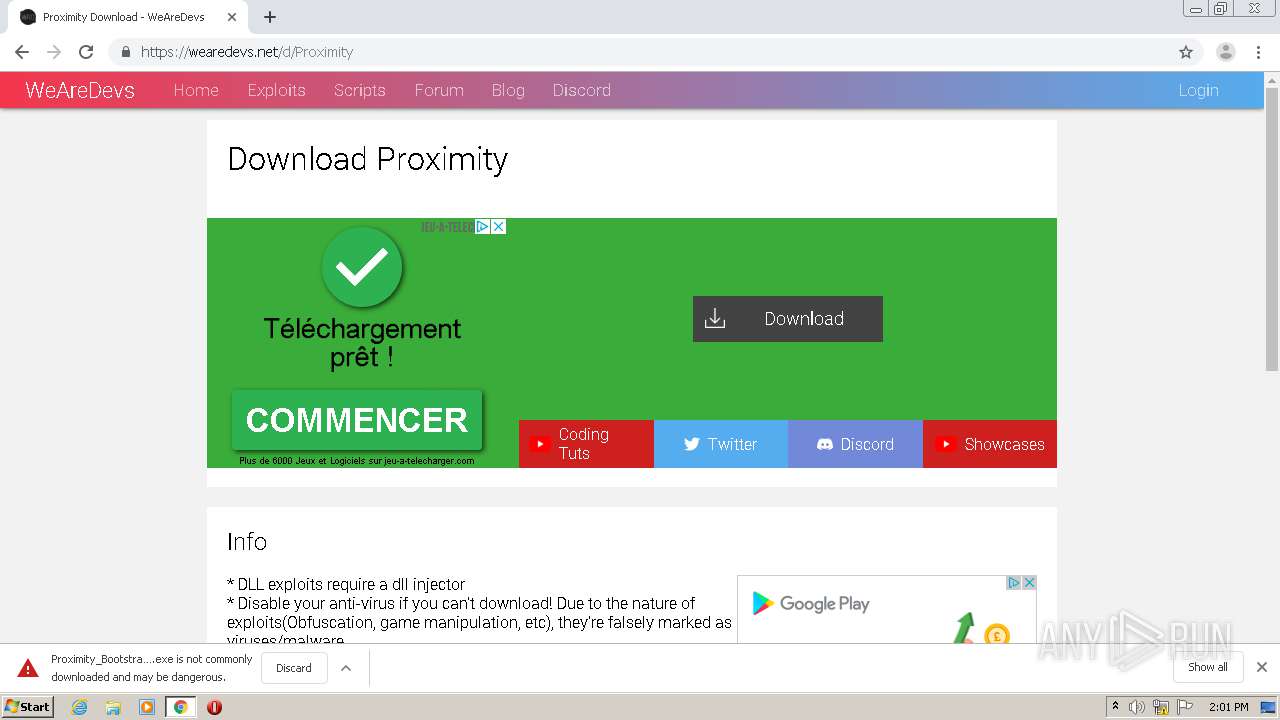
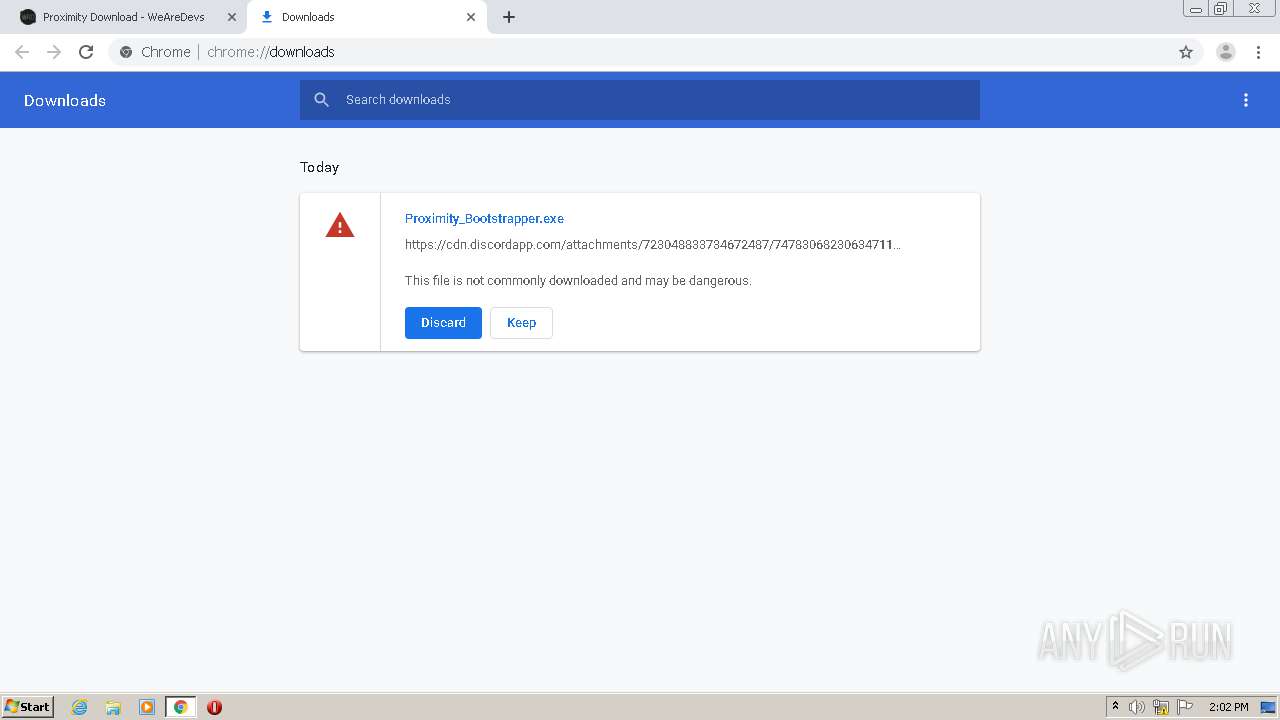
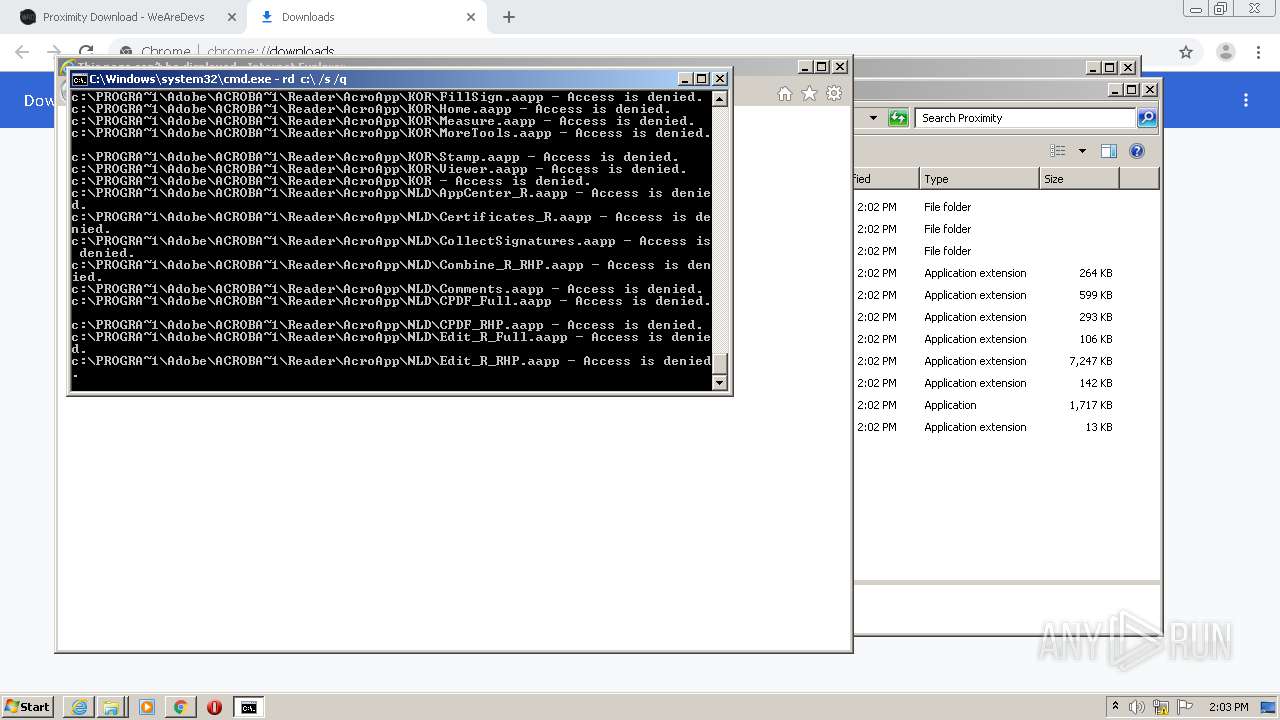
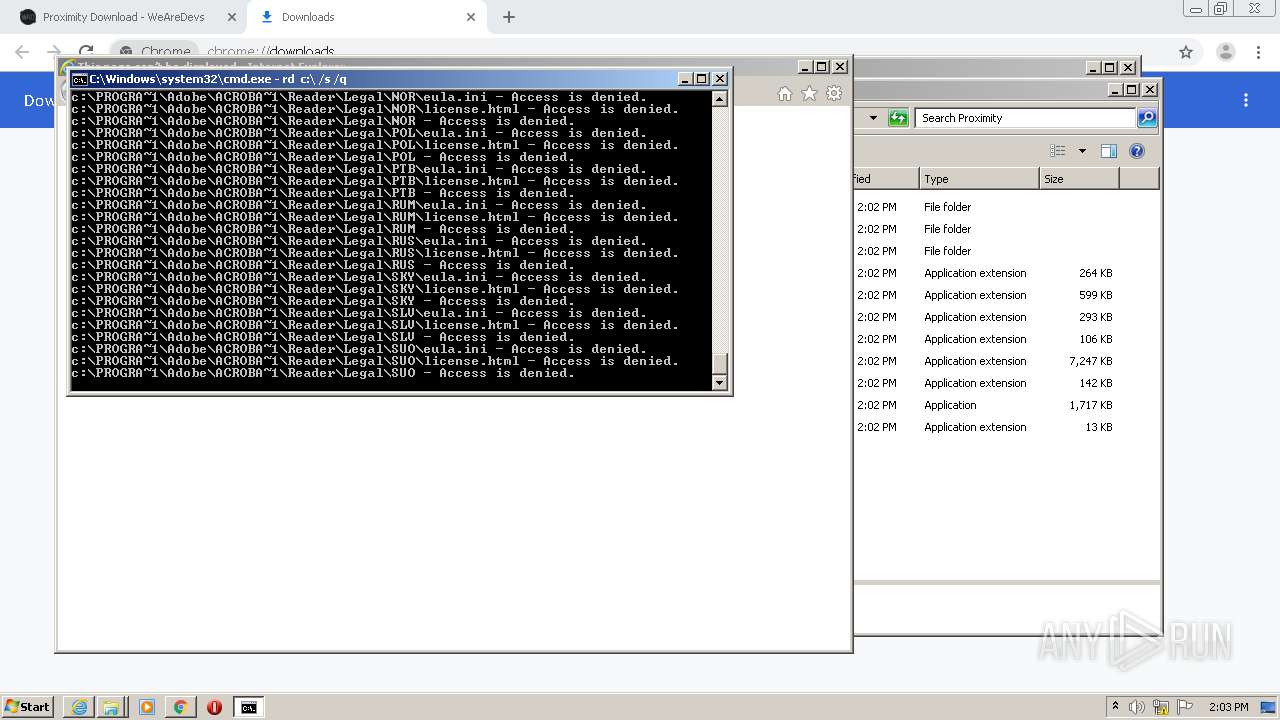
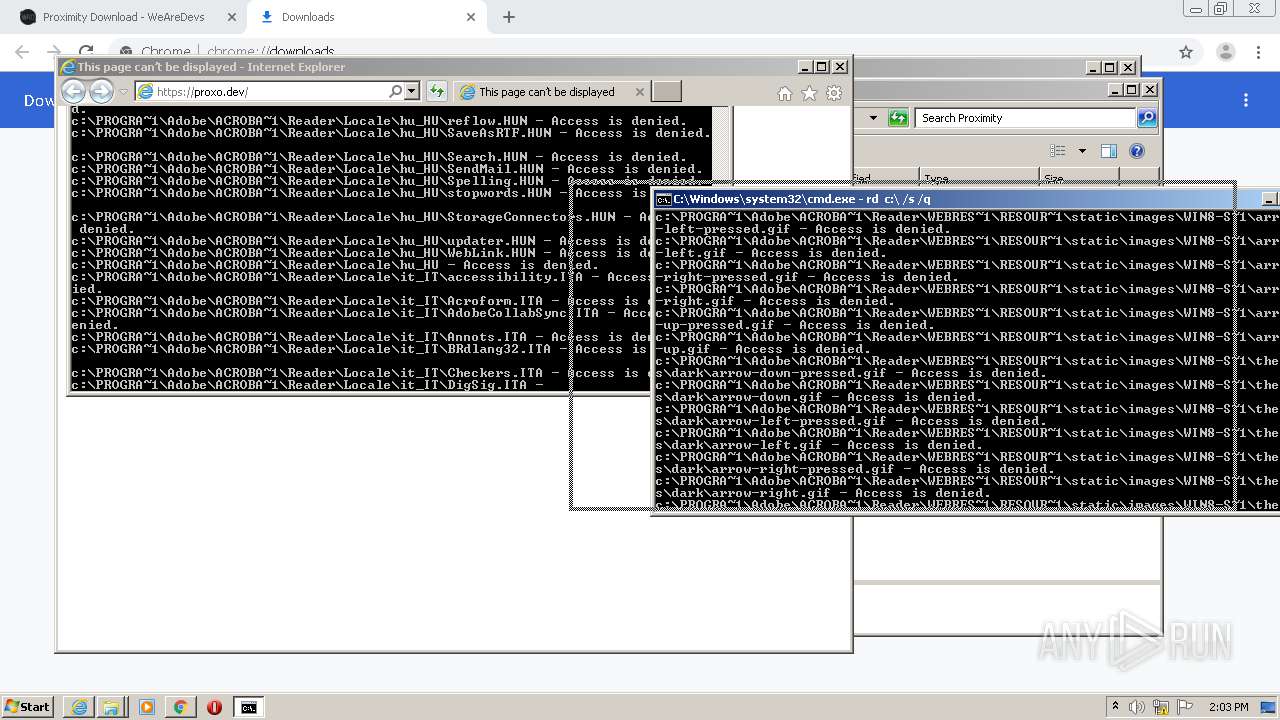
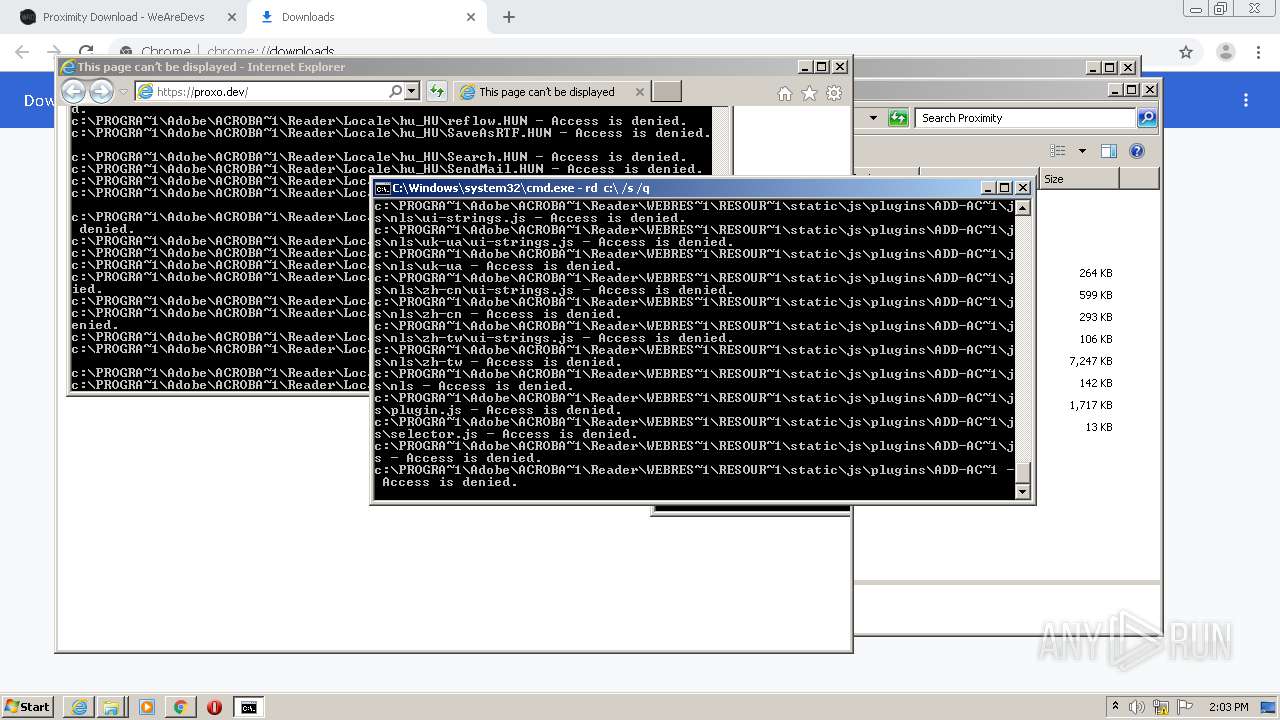
MALICIOUS
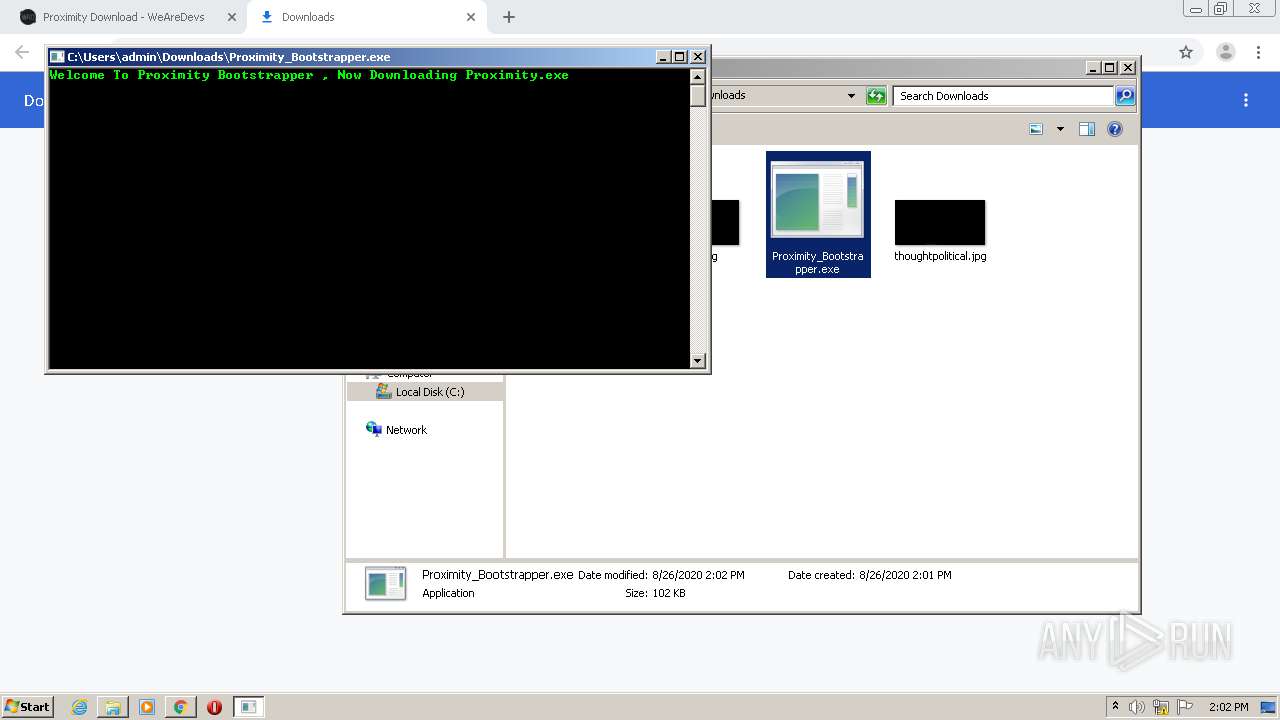
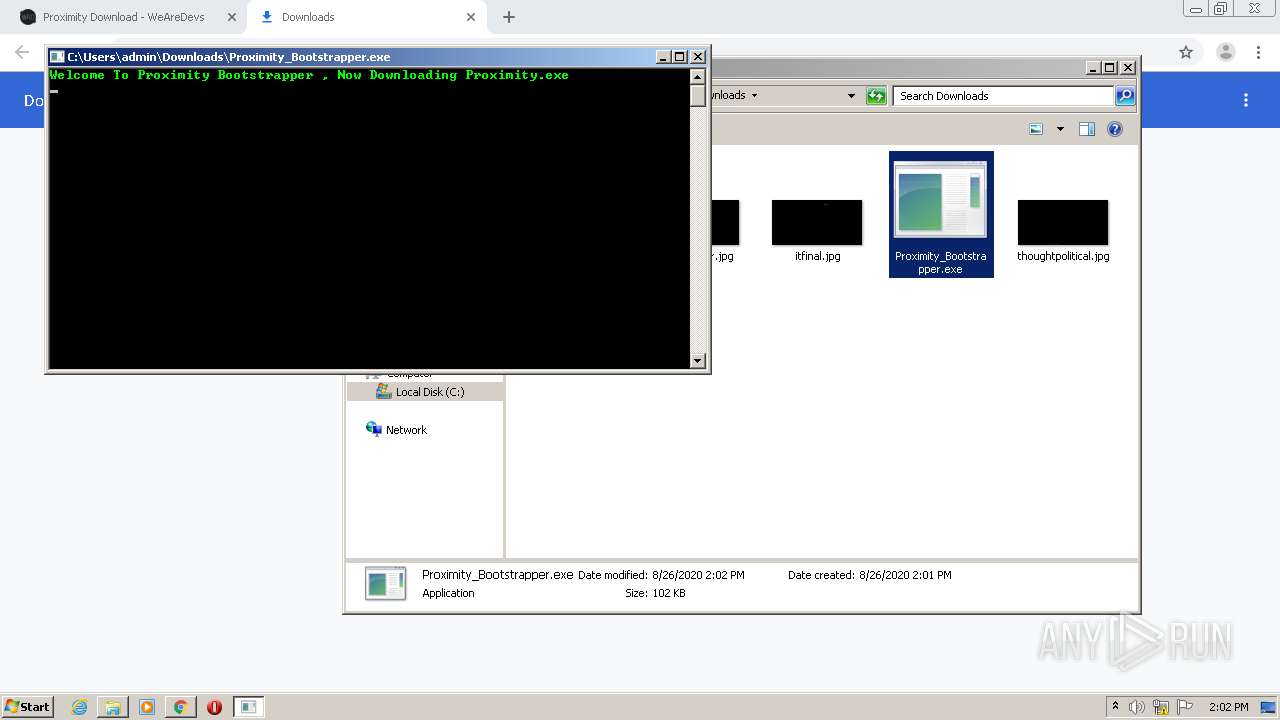
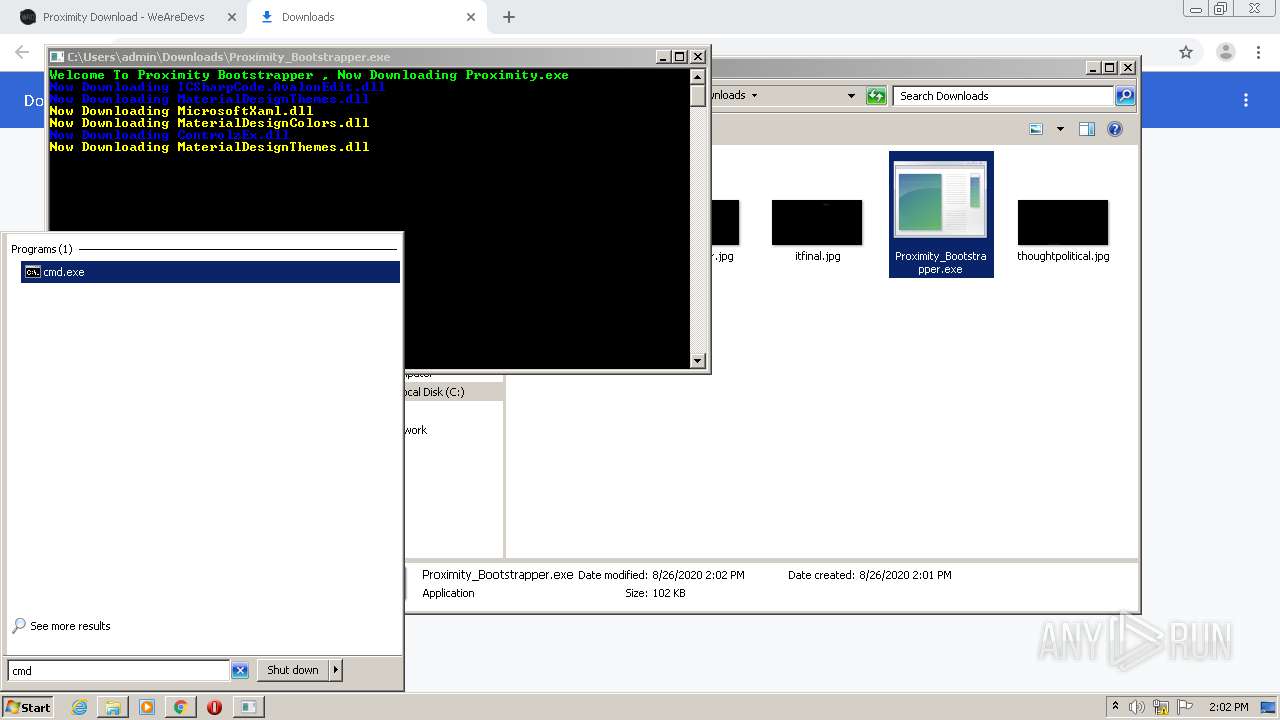
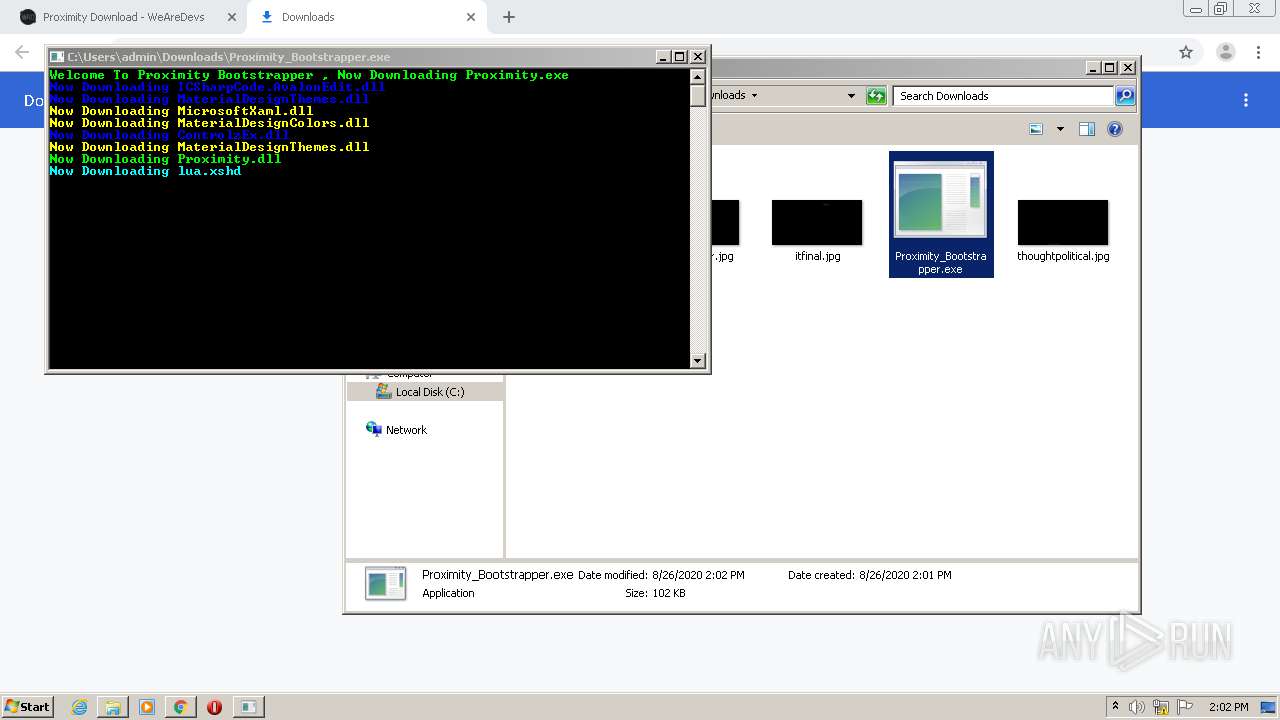
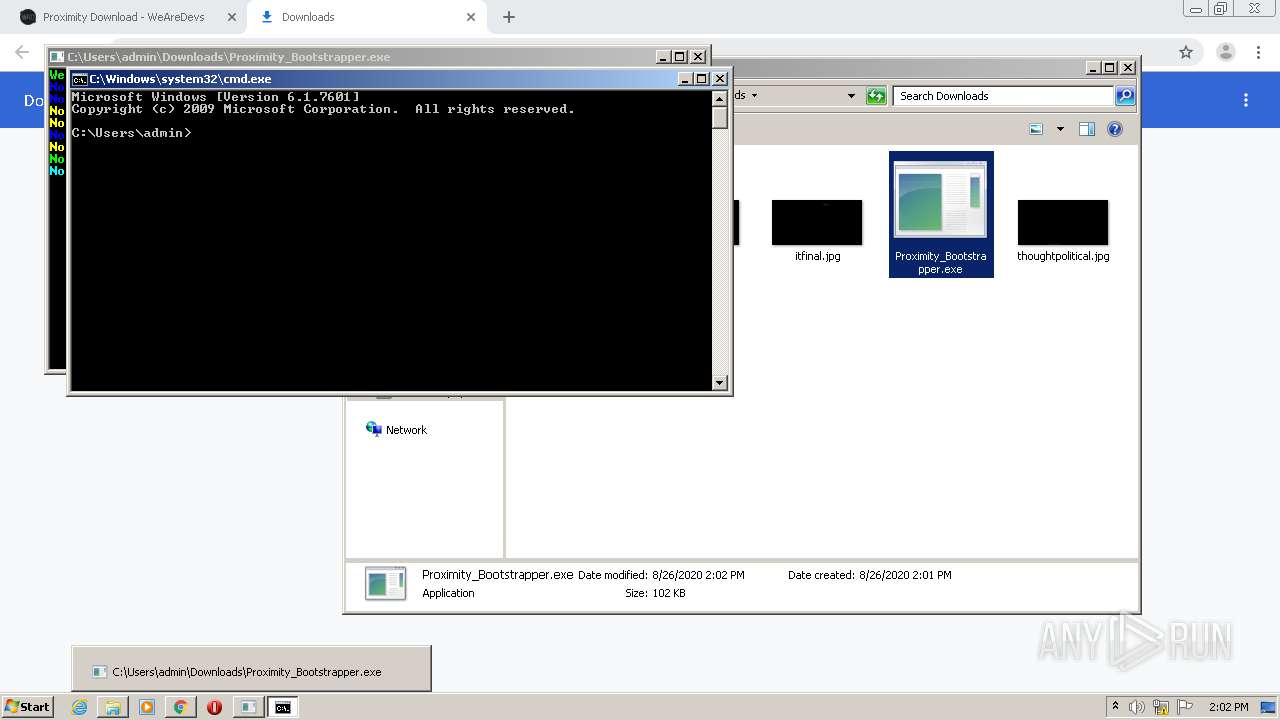
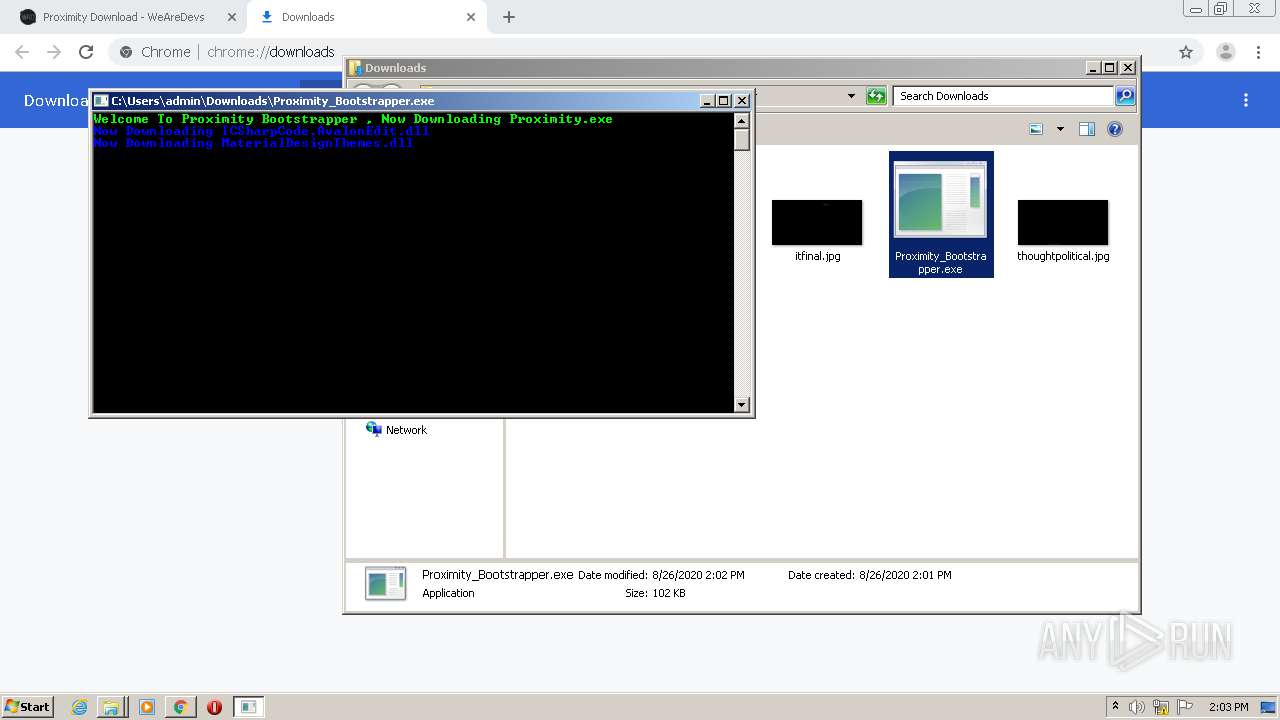
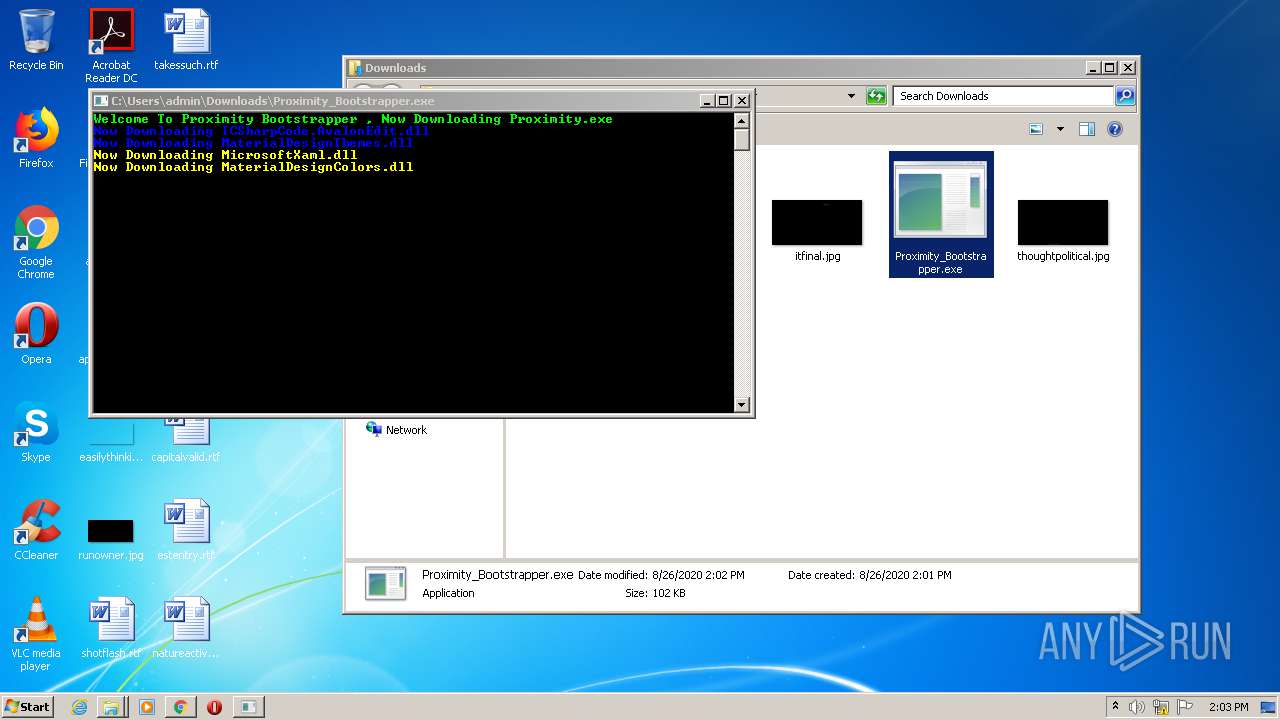
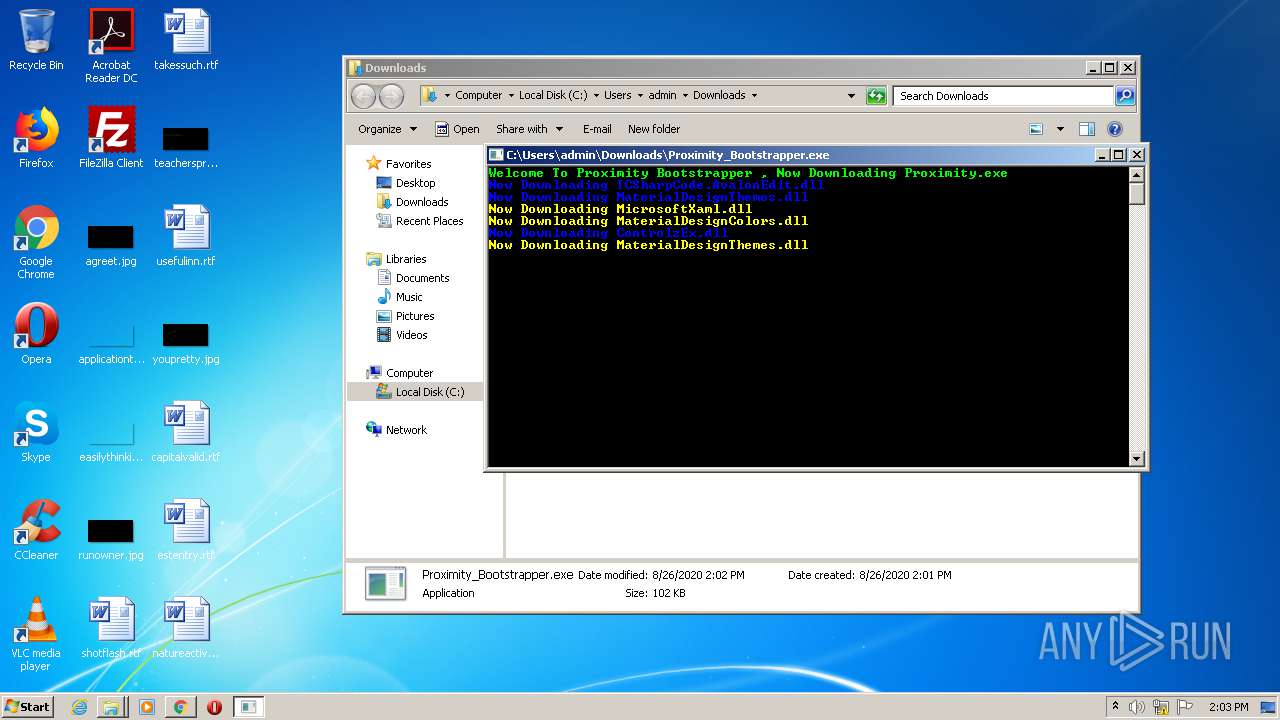
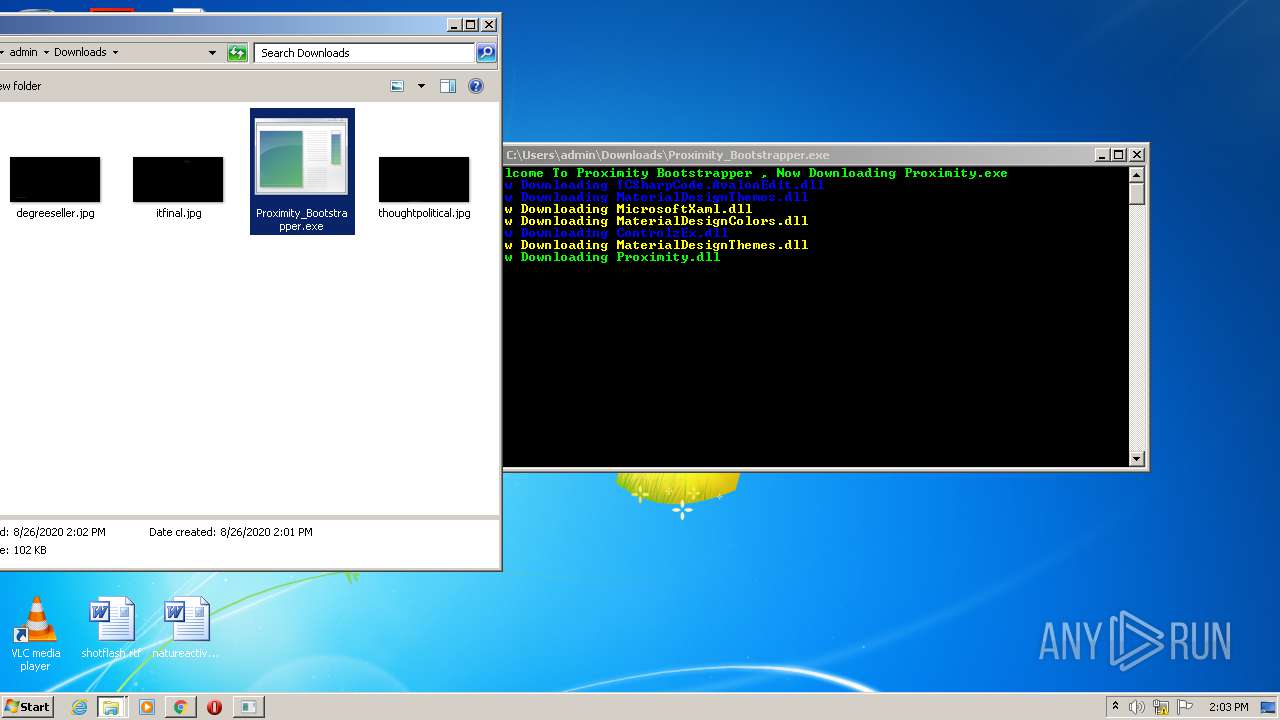
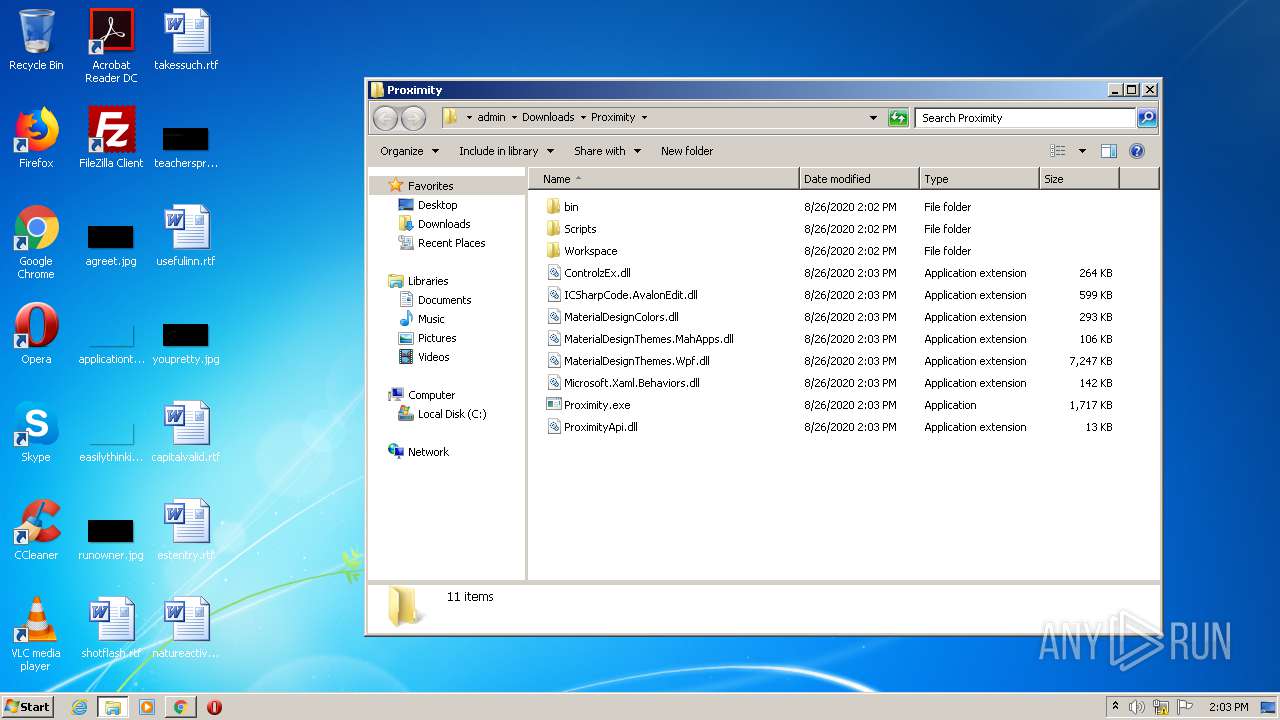
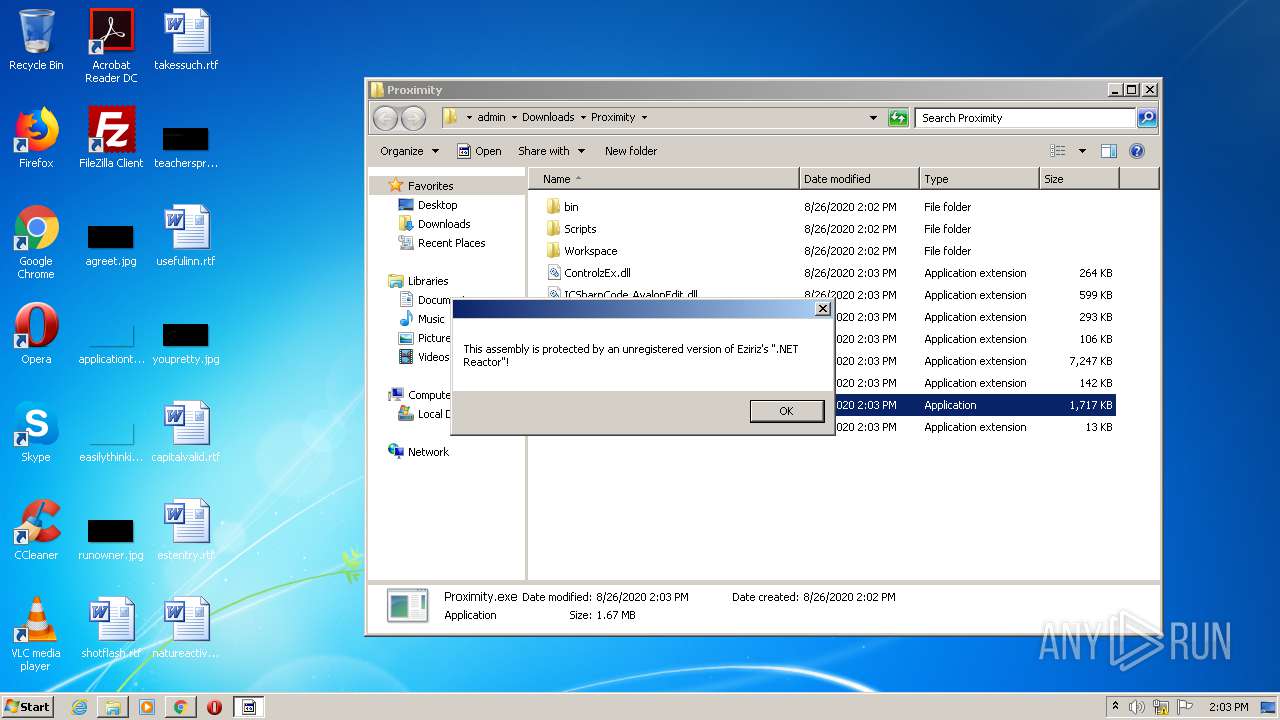
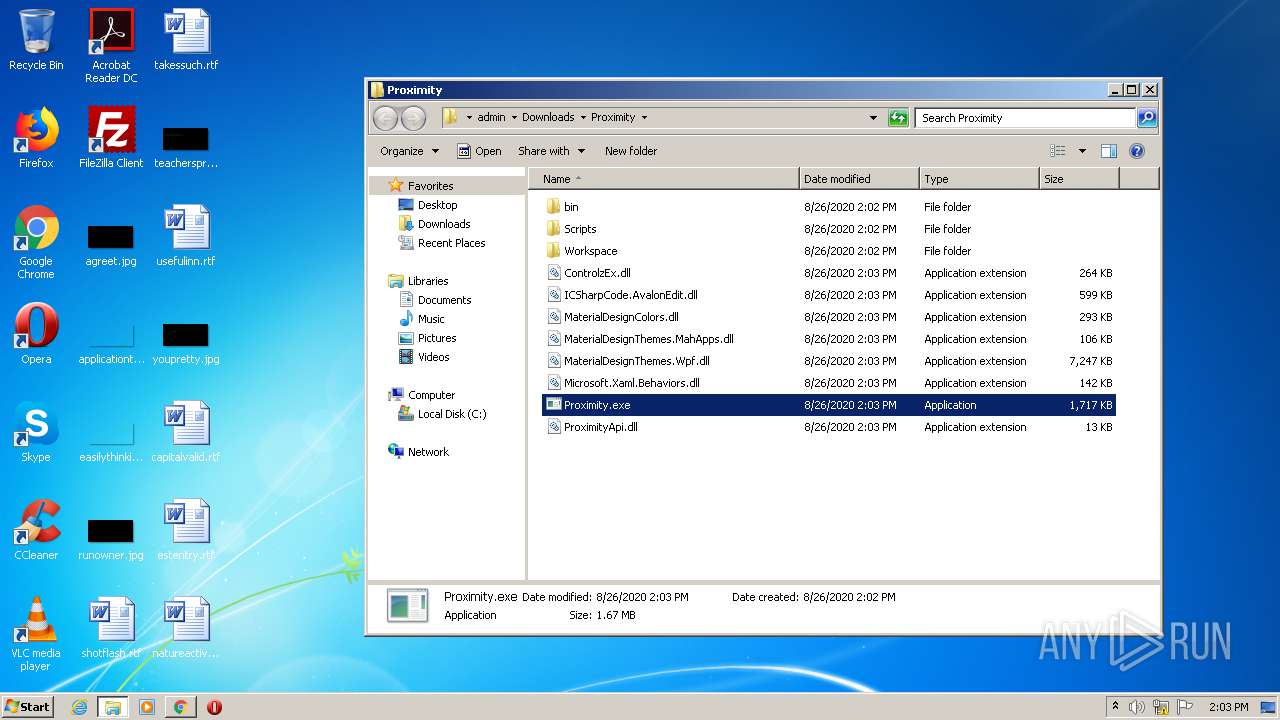
Application was dropped or rewritten from another process
- Proximity_Bootstrapper.exe (PID: 2336)
- Proximity_Bootstrapper.exe (PID: 1852)
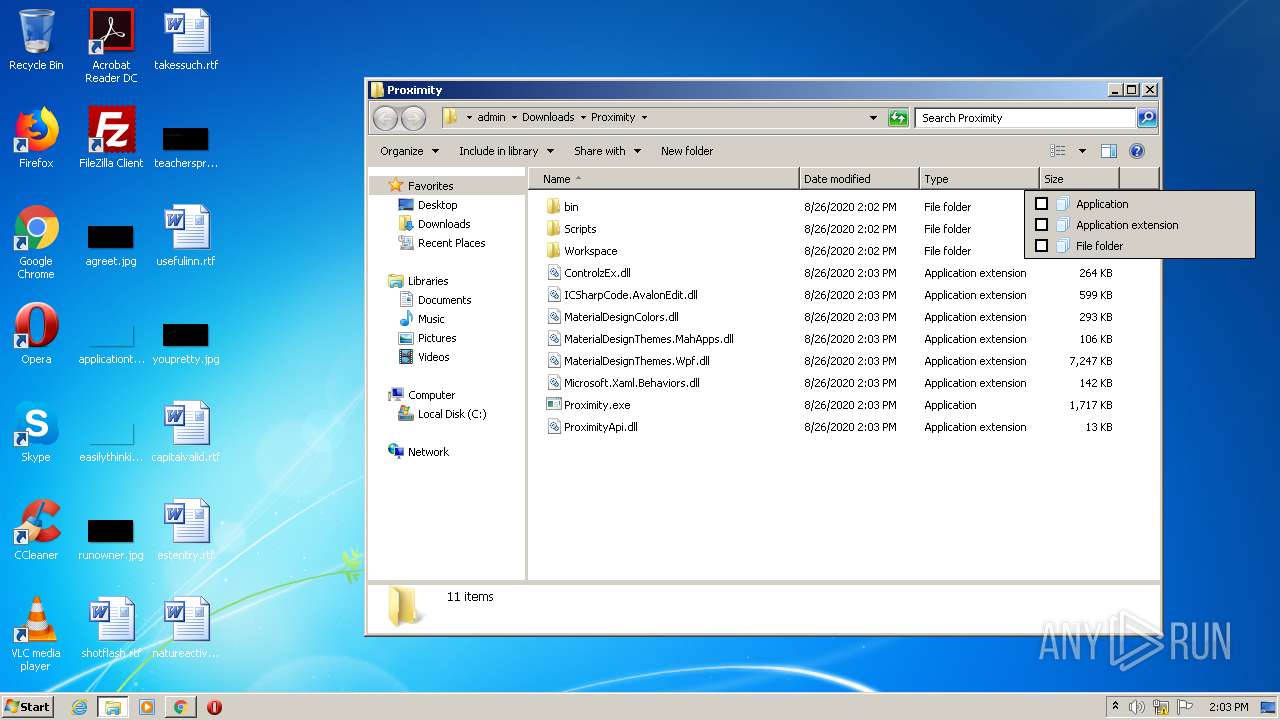
- Proximity.exe (PID: 1080)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 2568)
- Proximity.exe (PID: 1080)
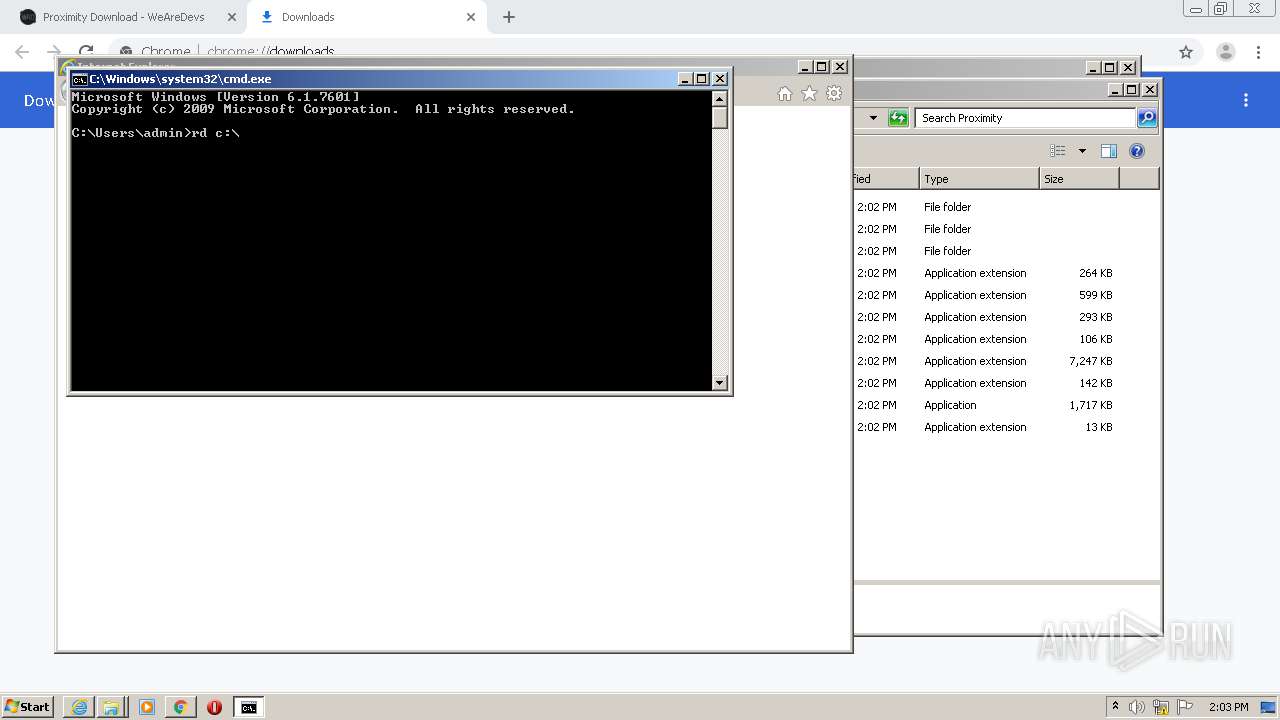
Changes the autorun value in the registry
- reg.exe (PID: 4144)
SUSPICIOUS
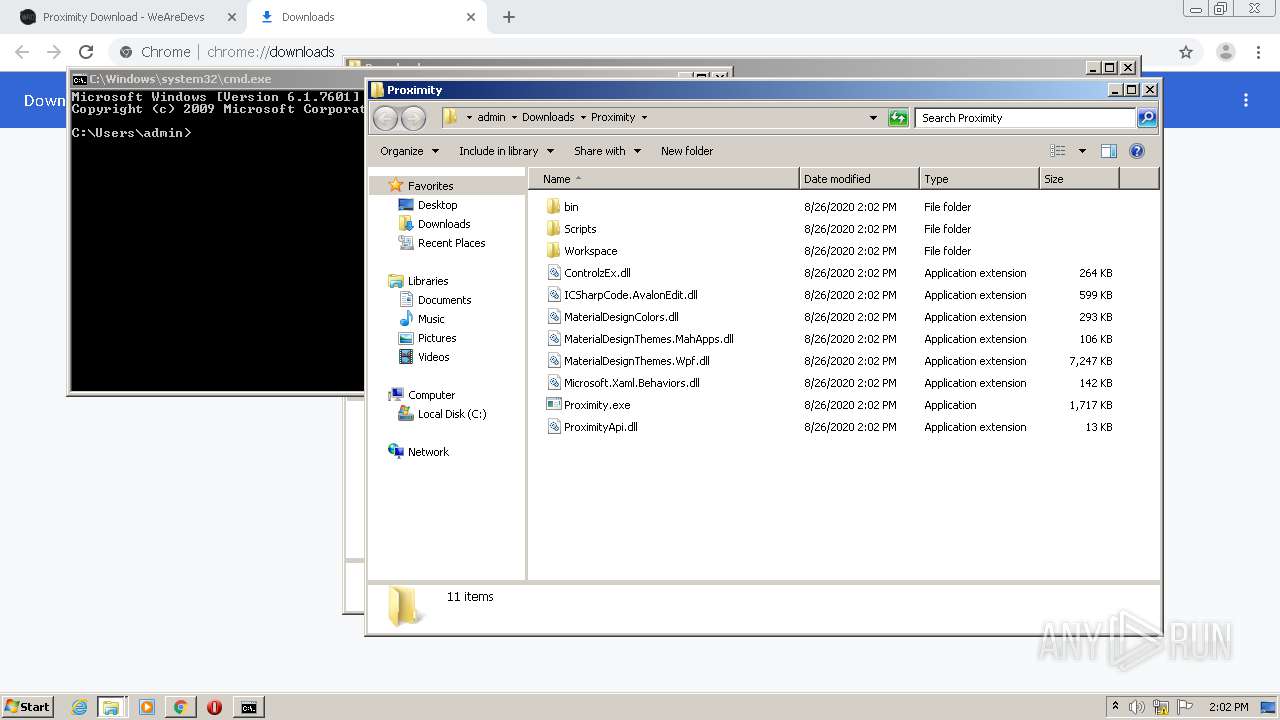
Executable content was dropped or overwritten
- chrome.exe (PID: 2980)
- chrome.exe (PID: 2076)
- Proximity_Bootstrapper.exe (PID: 2336)
- Proximity_Bootstrapper.exe (PID: 1852)
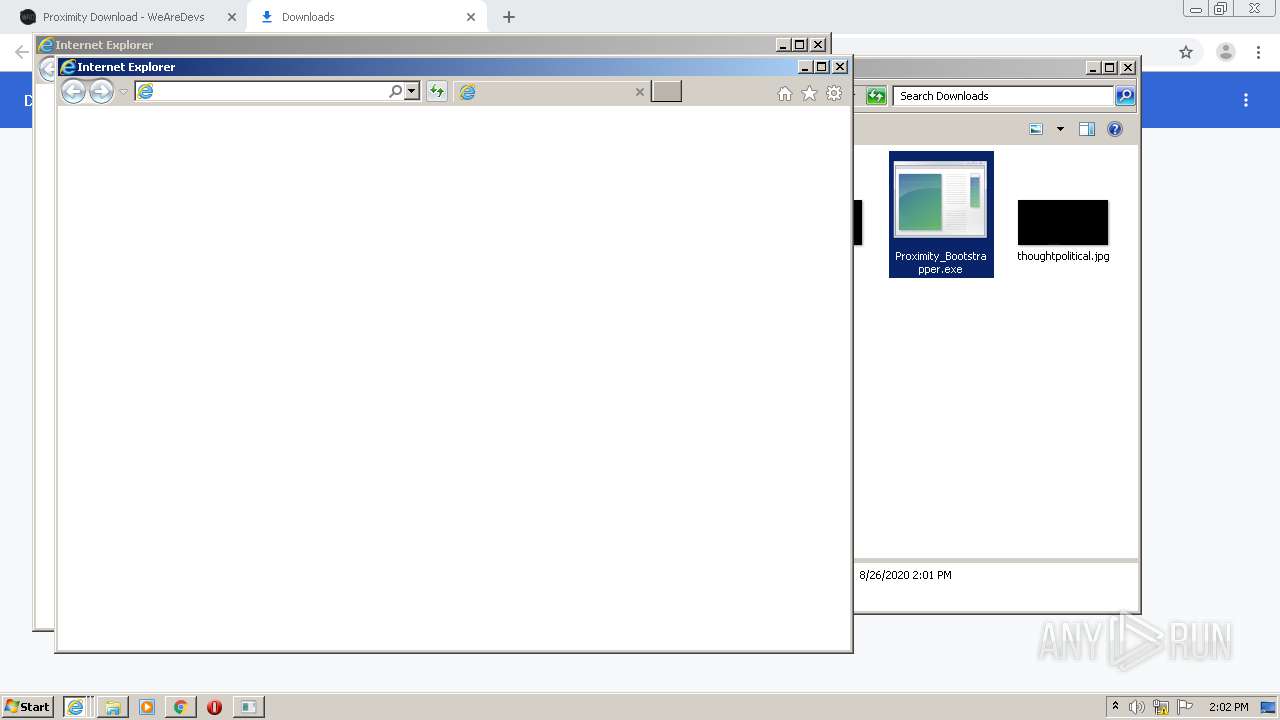
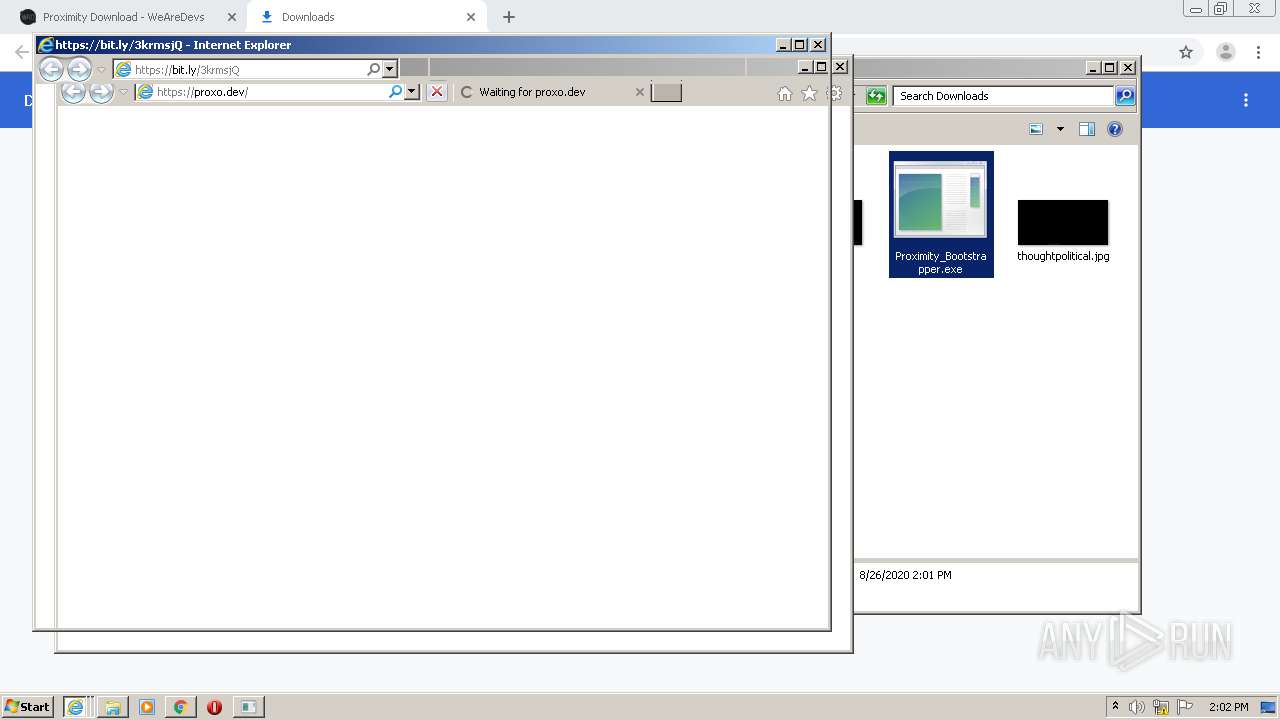
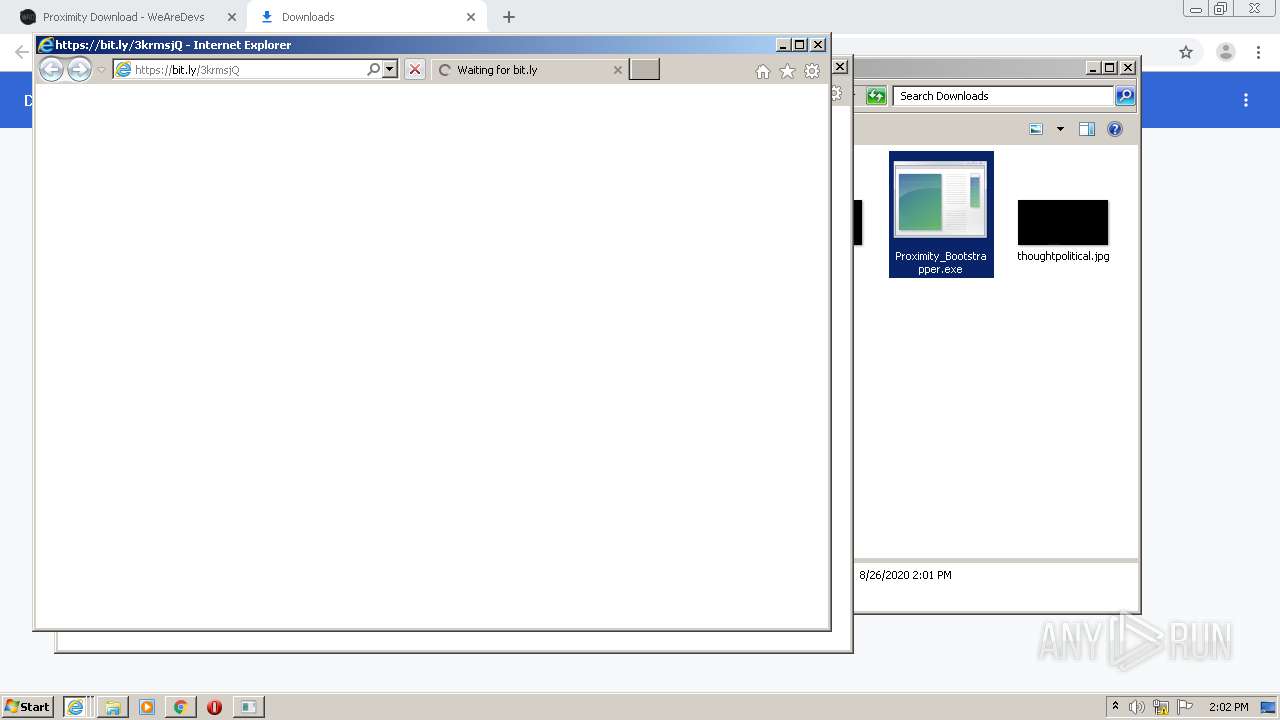
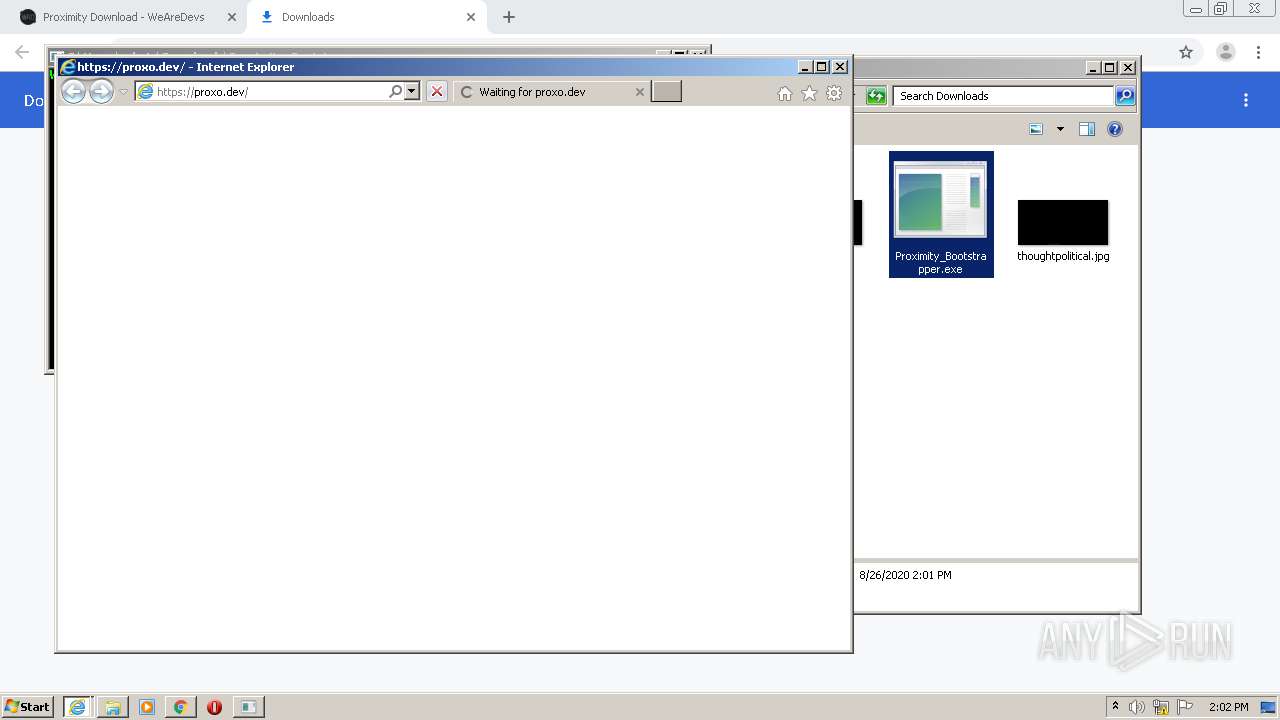
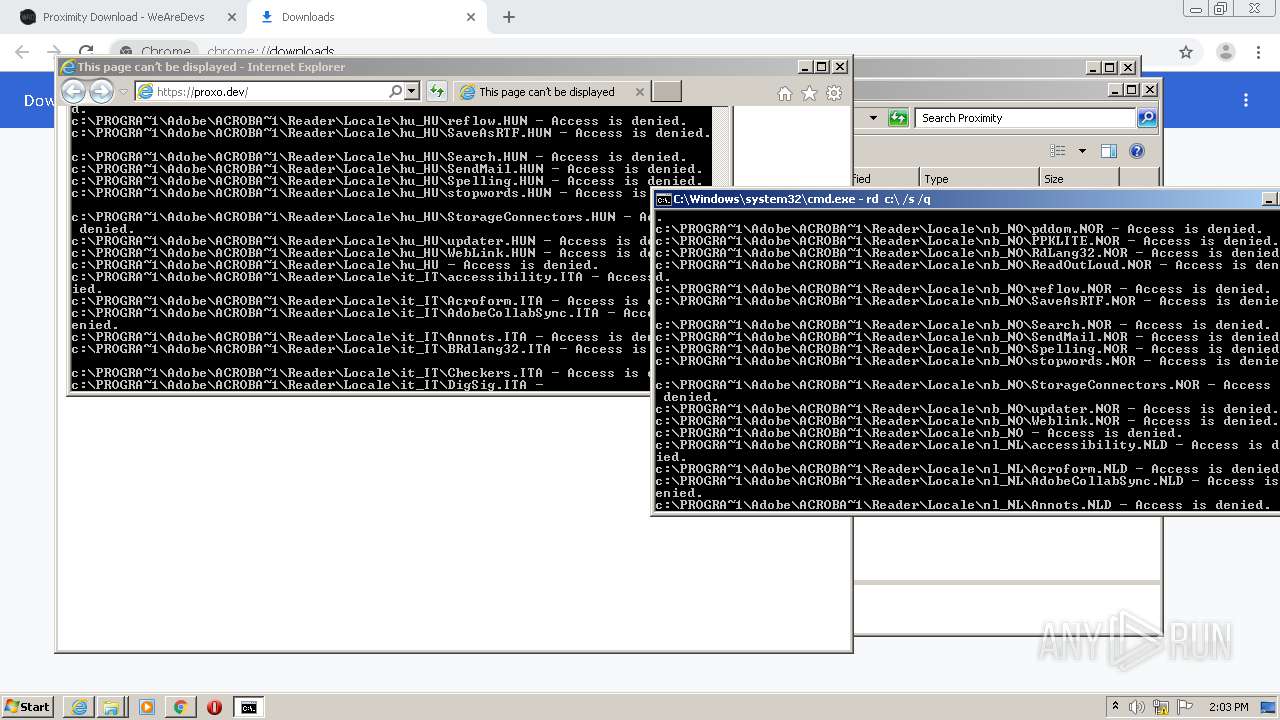
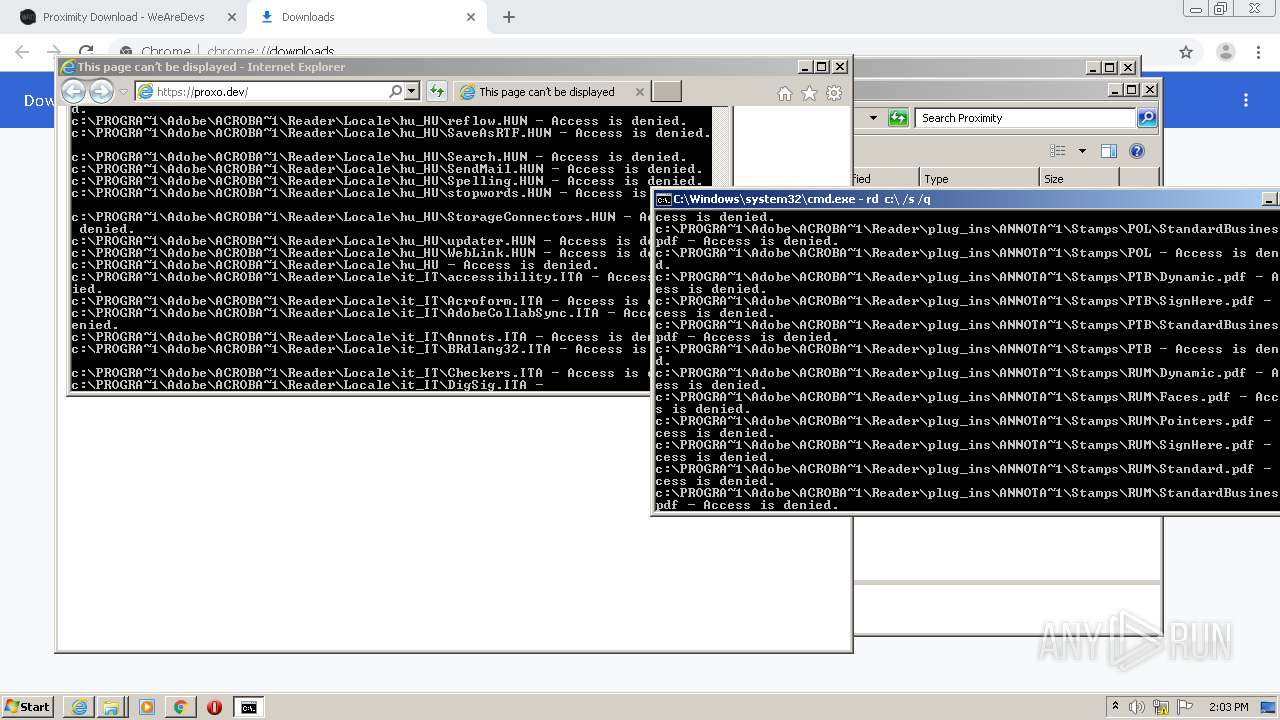
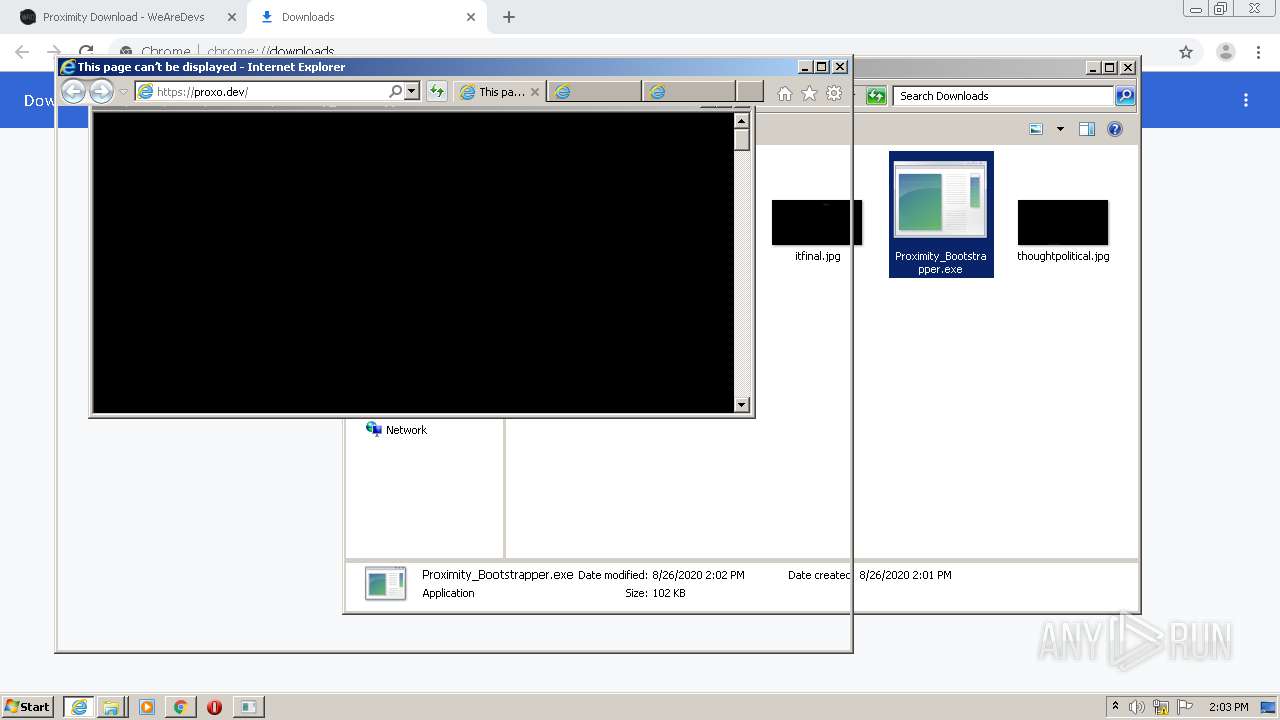
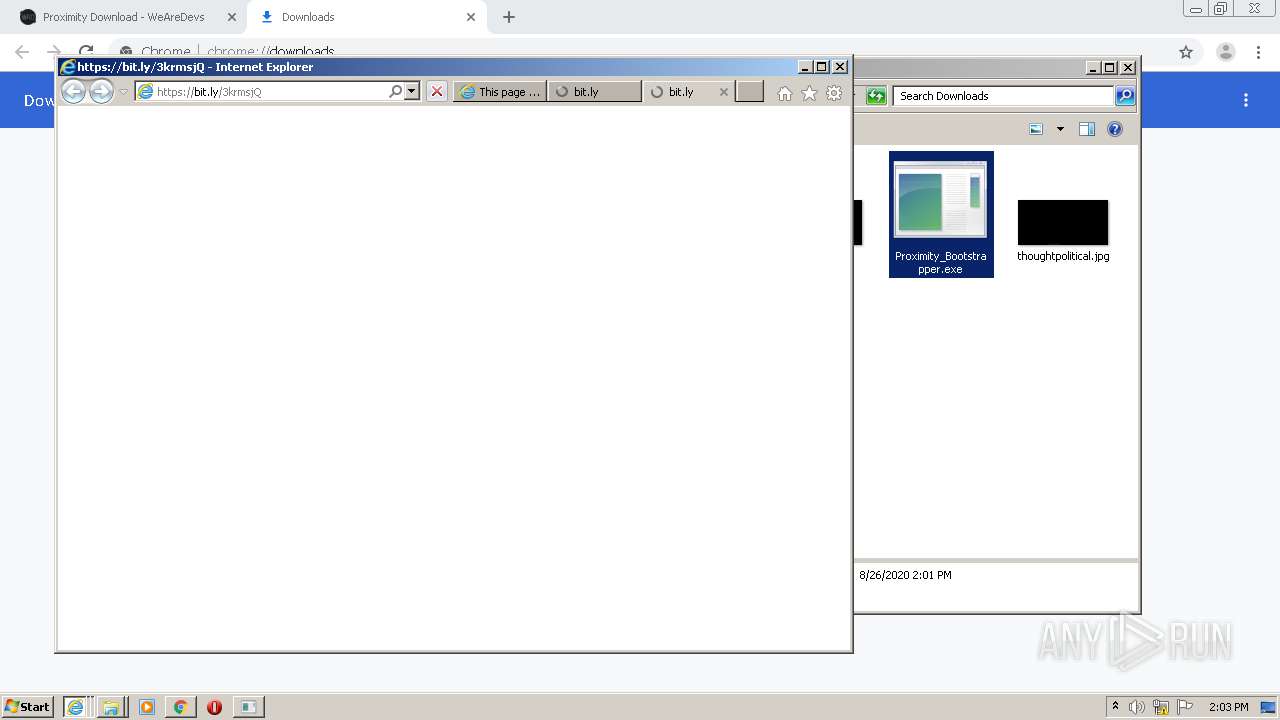
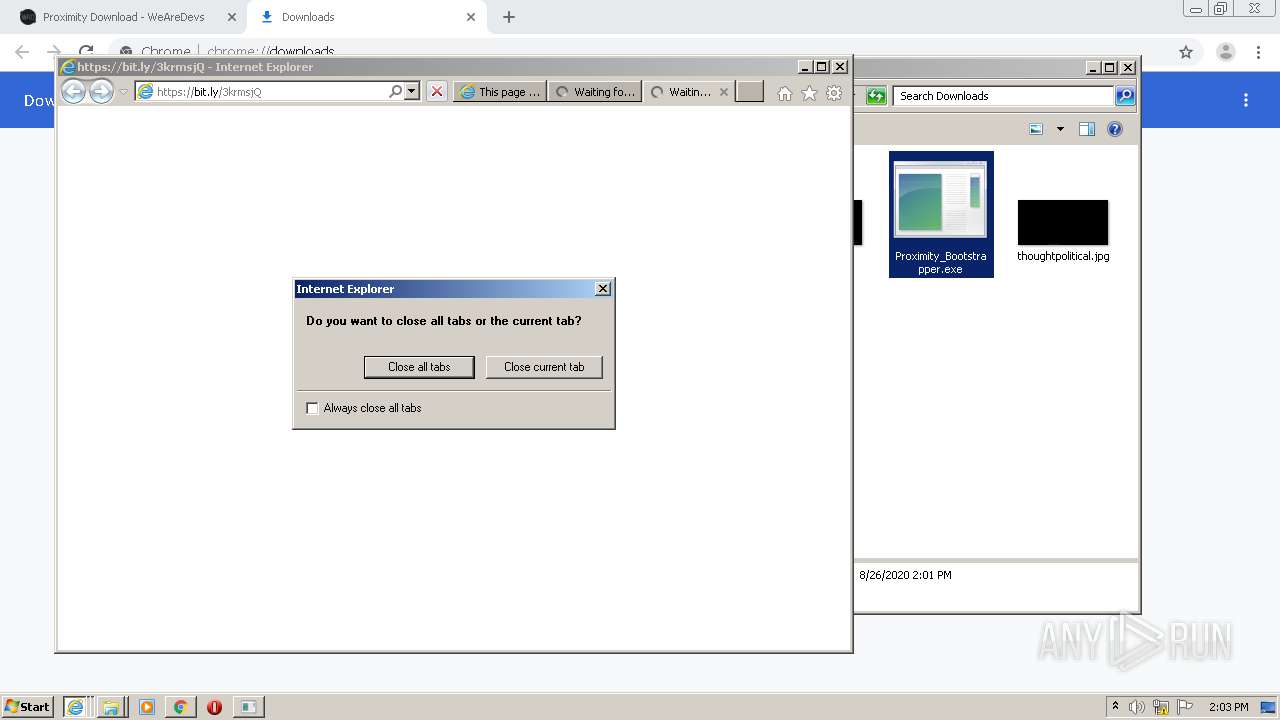
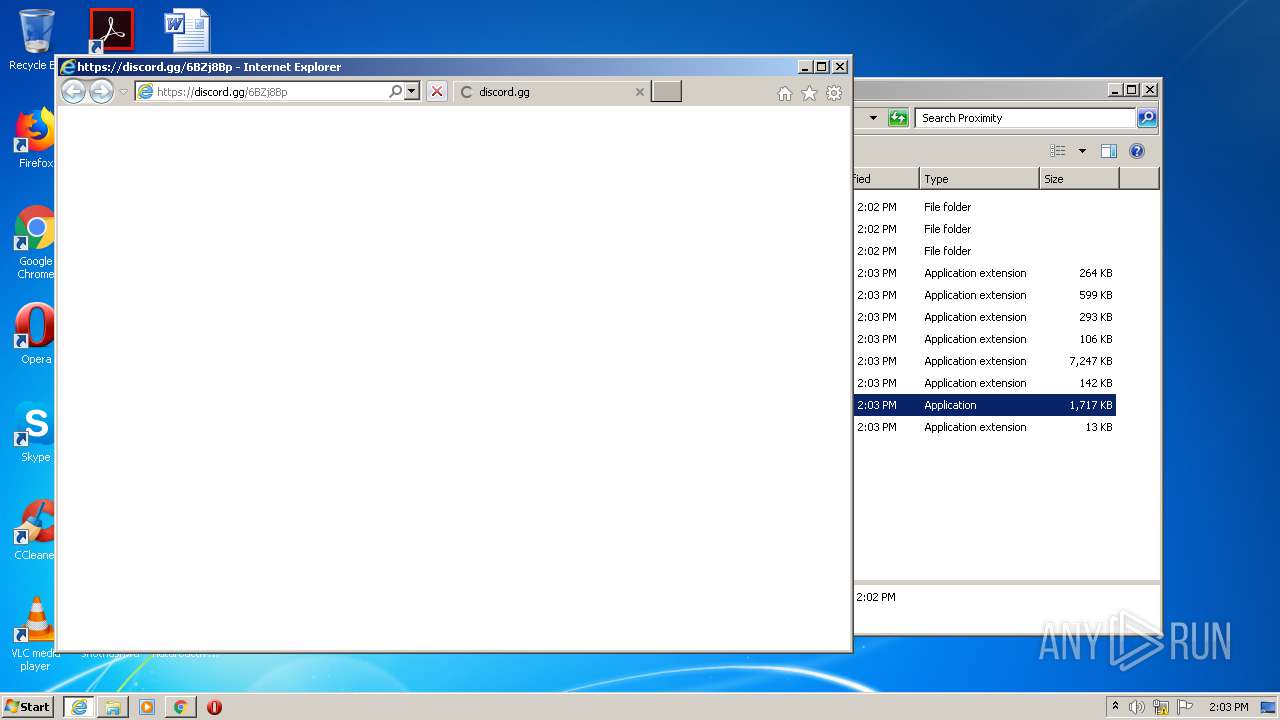
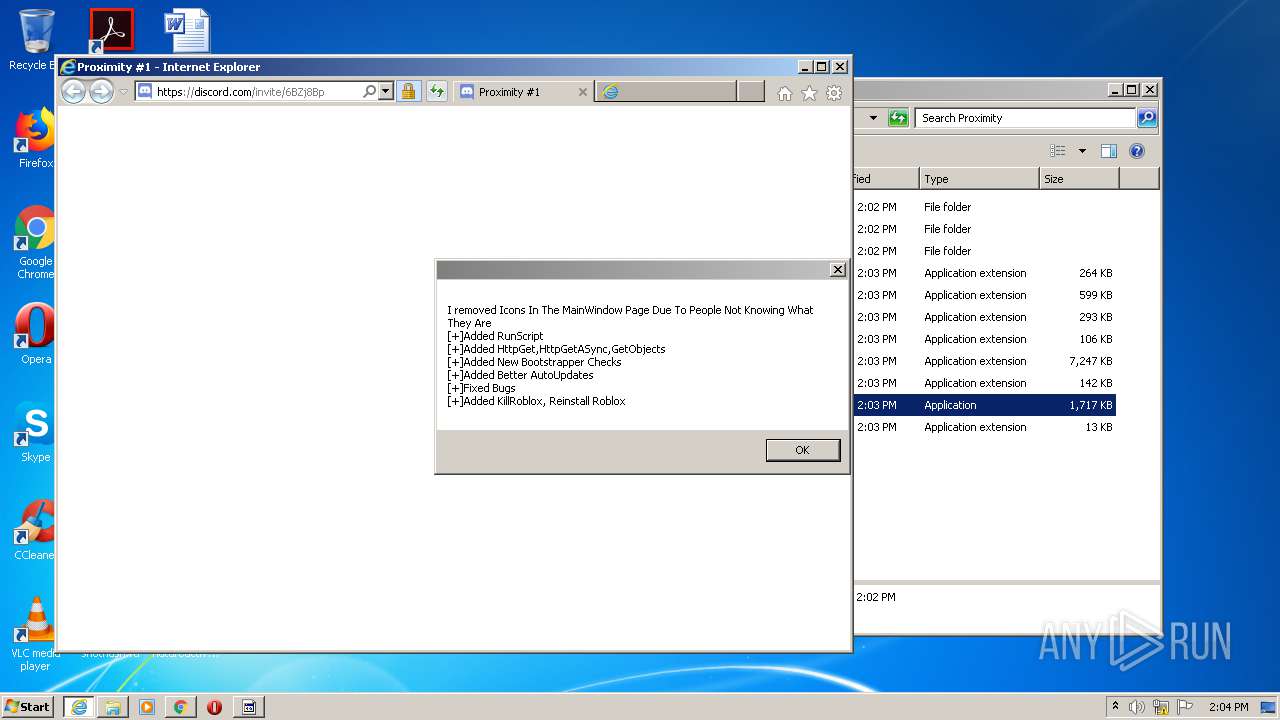
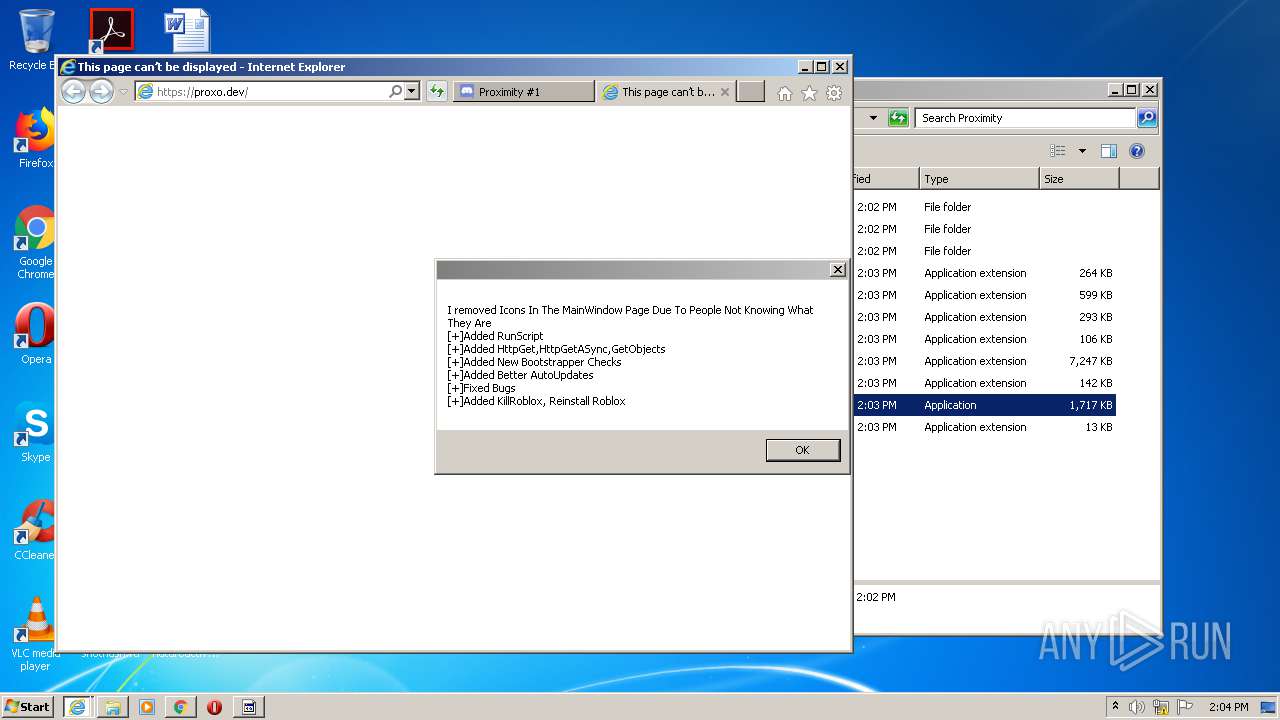
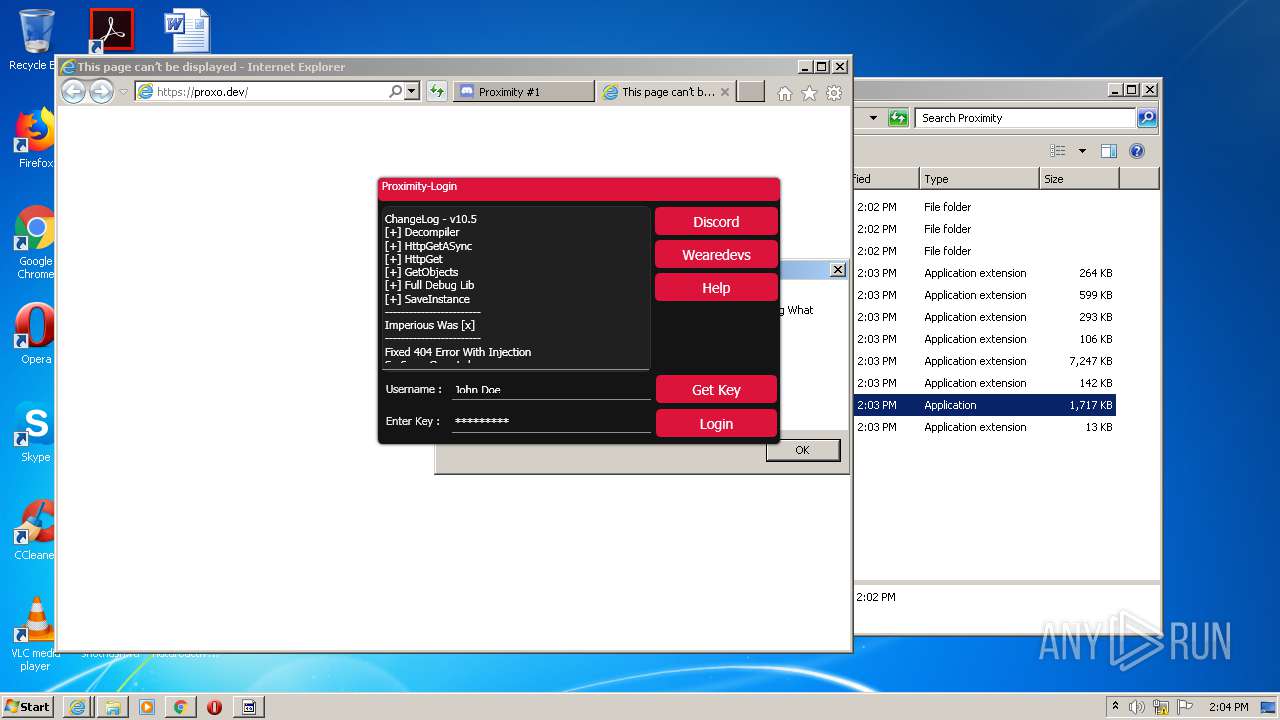
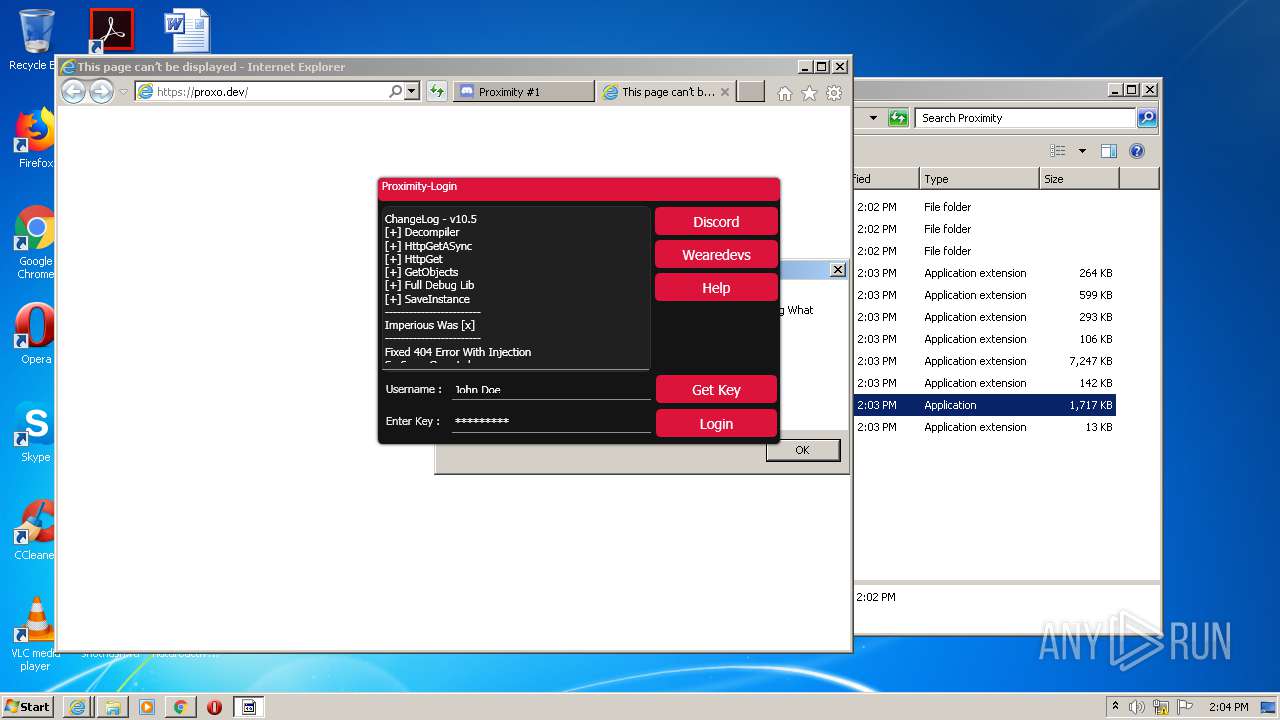
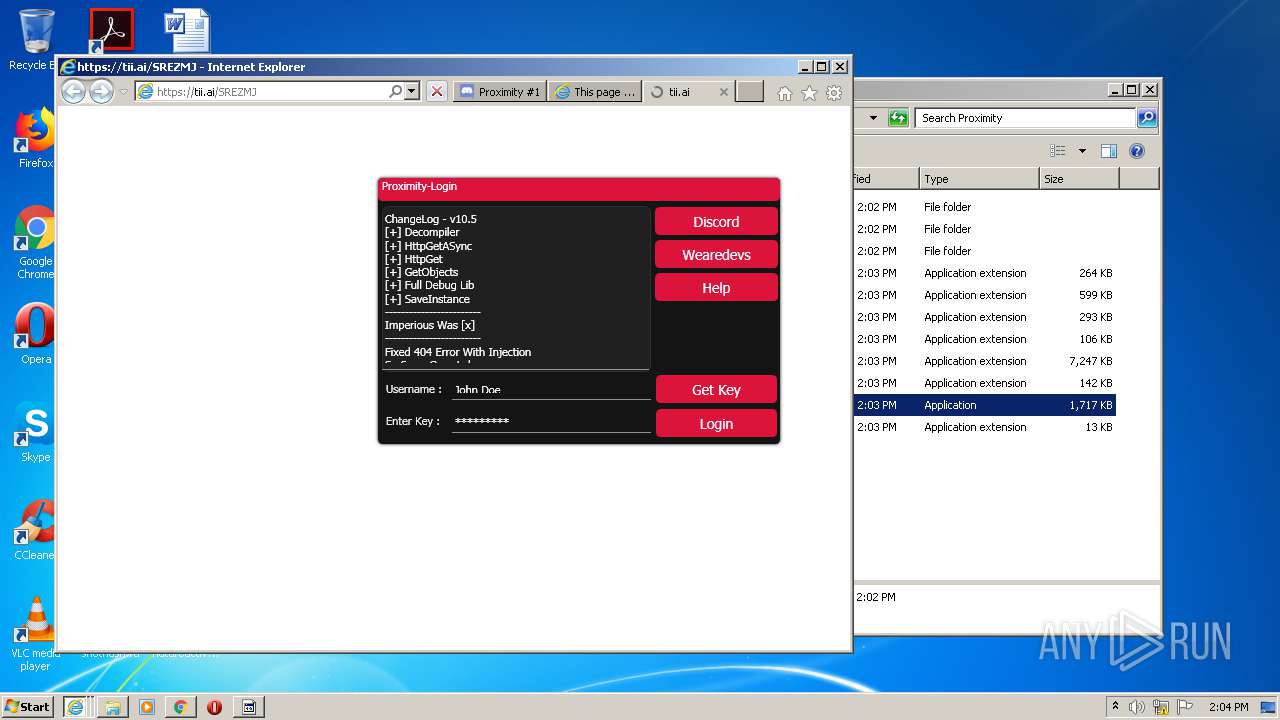
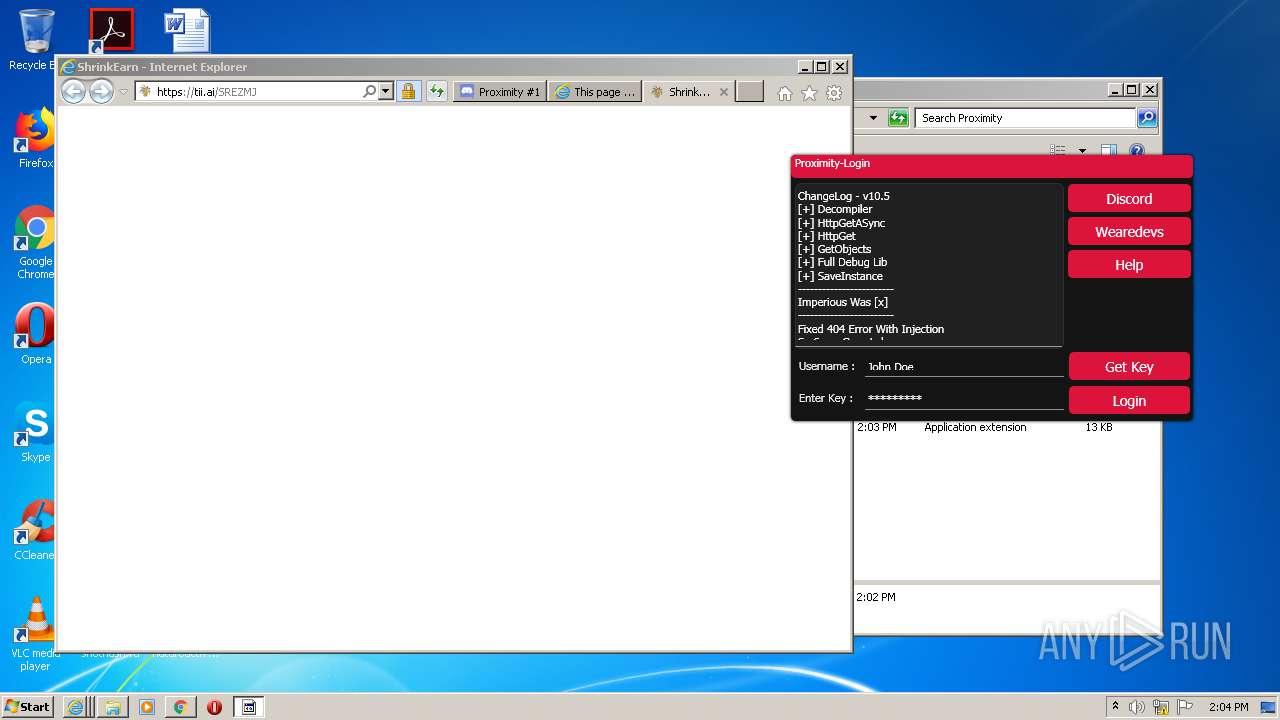
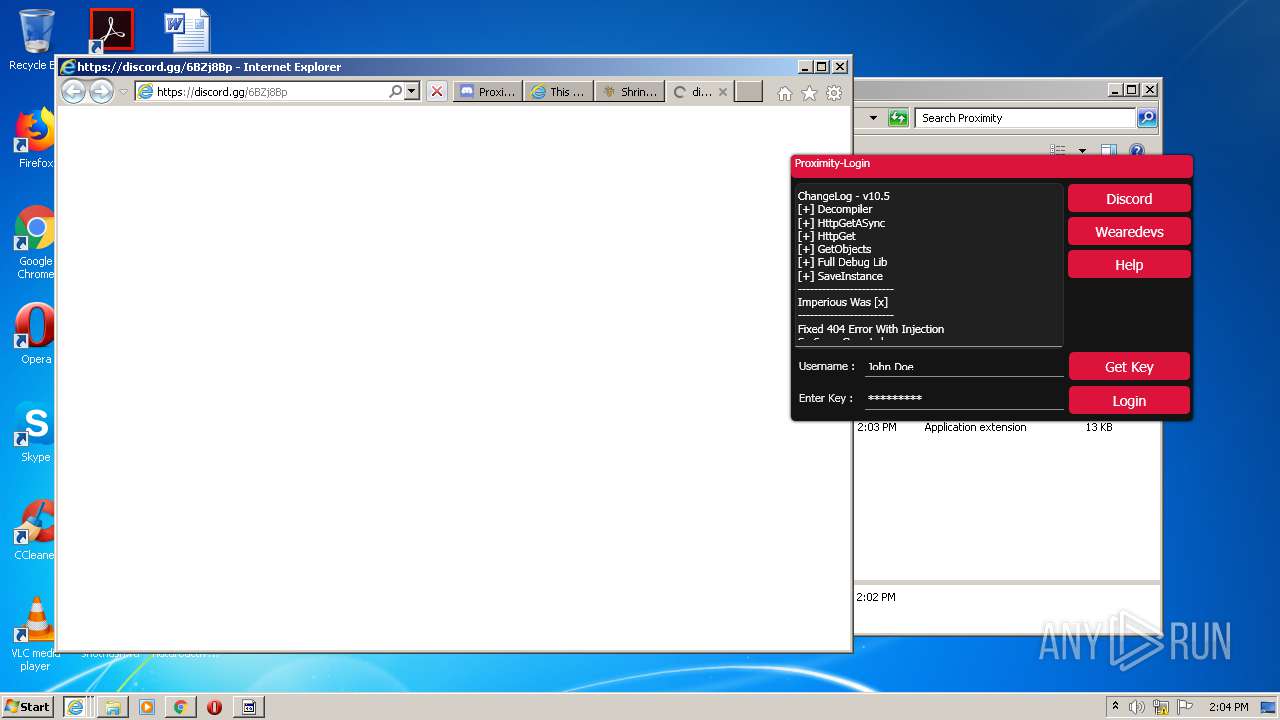
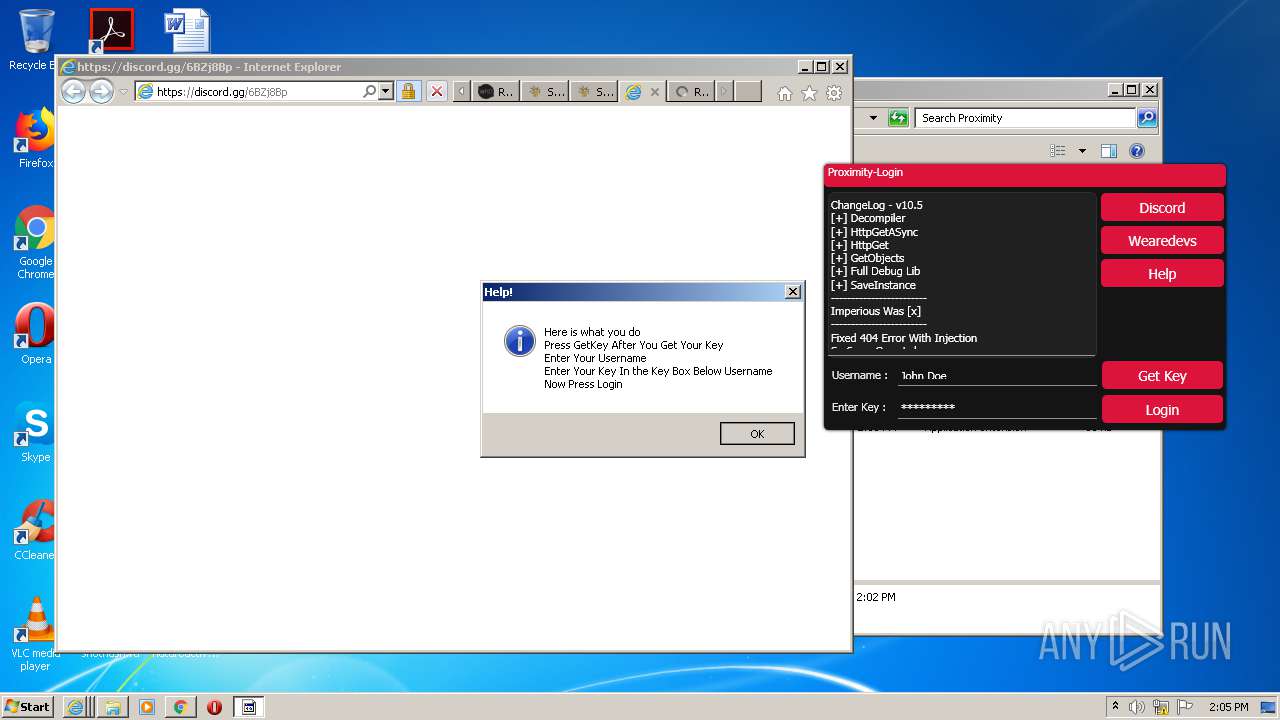
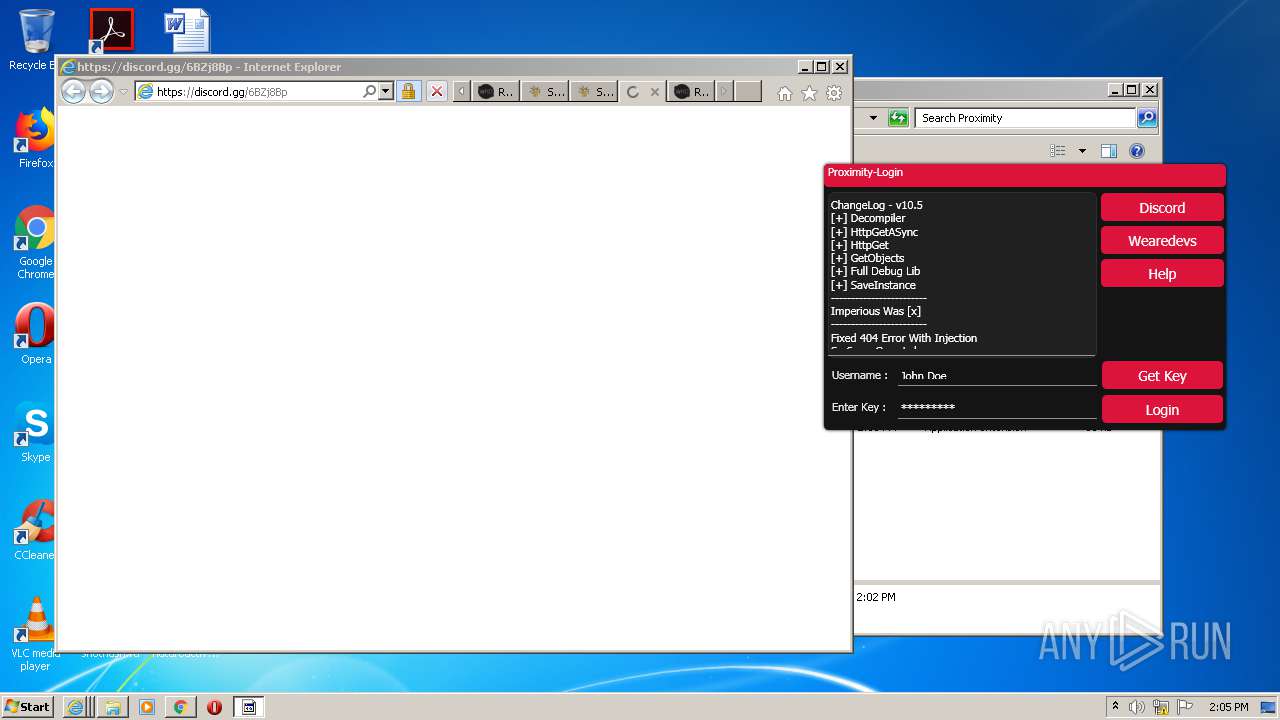
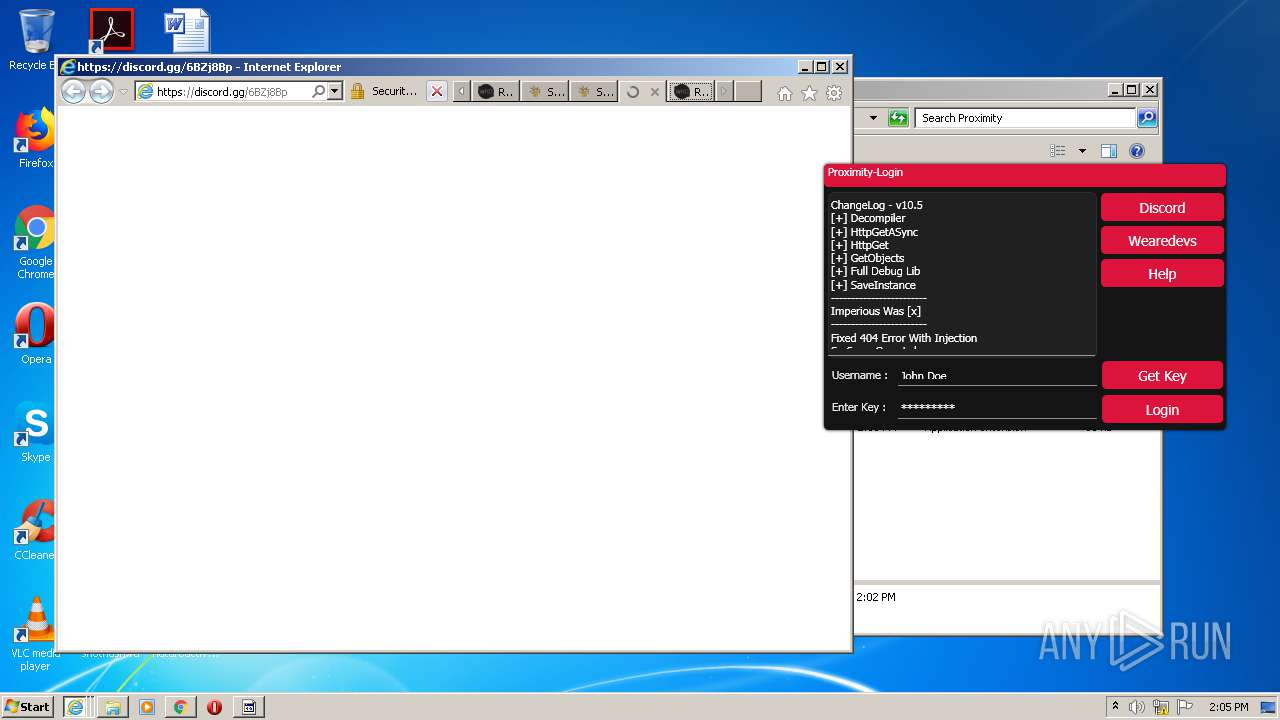
Starts Internet Explorer
- Proximity_Bootstrapper.exe (PID: 2336)
- Proximity_Bootstrapper.exe (PID: 1852)
- Proximity.exe (PID: 1080)
Reads Environment values
- Proximity.exe (PID: 1080)
Application launched itself
- Skype.exe (PID: 2392)
- Skype.exe (PID: 5784)
- Skype.exe (PID: 4824)
Reads CPU info
- Skype.exe (PID: 2392)
Uses REG.EXE to modify Windows registry
- Skype.exe (PID: 2392)
Creates files in the user directory
- Skype.exe (PID: 2392)
- Skype.exe (PID: 5784)
- Skype.exe (PID: 4824)
Modifies the open verb of a shell class
- Skype.exe (PID: 2392)
INFO
Application launched itself
- chrome.exe (PID: 2076)
- iexplore.exe (PID: 2388)
- iexplore.exe (PID: 1928)
- iexplore.exe (PID: 2420)
- iexplore.exe (PID: 636)
- iexplore.exe (PID: 2516)
- iexplore.exe (PID: 2404)
Reads settings of System Certificates
- chrome.exe (PID: 2980)
- iexplore.exe (PID: 2420)
- iexplore.exe (PID: 1596)
- Proximity_Bootstrapper.exe (PID: 1852)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 1592)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 1972)
- iexplore.exe (PID: 3452)
- iexplore.exe (PID: 3984)
- iexplore.exe (PID: 2824)
- iexplore.exe (PID: 4016)
- iexplore.exe (PID: 3620)
- Skype.exe (PID: 2392)
Reads the hosts file
- chrome.exe (PID: 2076)
- chrome.exe (PID: 2980)
- Skype.exe (PID: 2392)
Reads Internet Cache Settings
- chrome.exe (PID: 2076)
- iexplore.exe (PID: 1928)
- iexplore.exe (PID: 2420)
- iexplore.exe (PID: 2388)
- iexplore.exe (PID: 3640)
- iexplore.exe (PID: 3524)
- iexplore.exe (PID: 1596)
- iexplore.exe (PID: 636)
- iexplore.exe (PID: 2220)
- iexplore.exe (PID: 3656)
- iexplore.exe (PID: 1592)
- iexplore.exe (PID: 384)
- iexplore.exe (PID: 2516)
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 1972)
- iexplore.exe (PID: 3452)
- iexplore.exe (PID: 3984)
- iexplore.exe (PID: 2824)
- iexplore.exe (PID: 3620)
- iexplore.exe (PID: 4016)
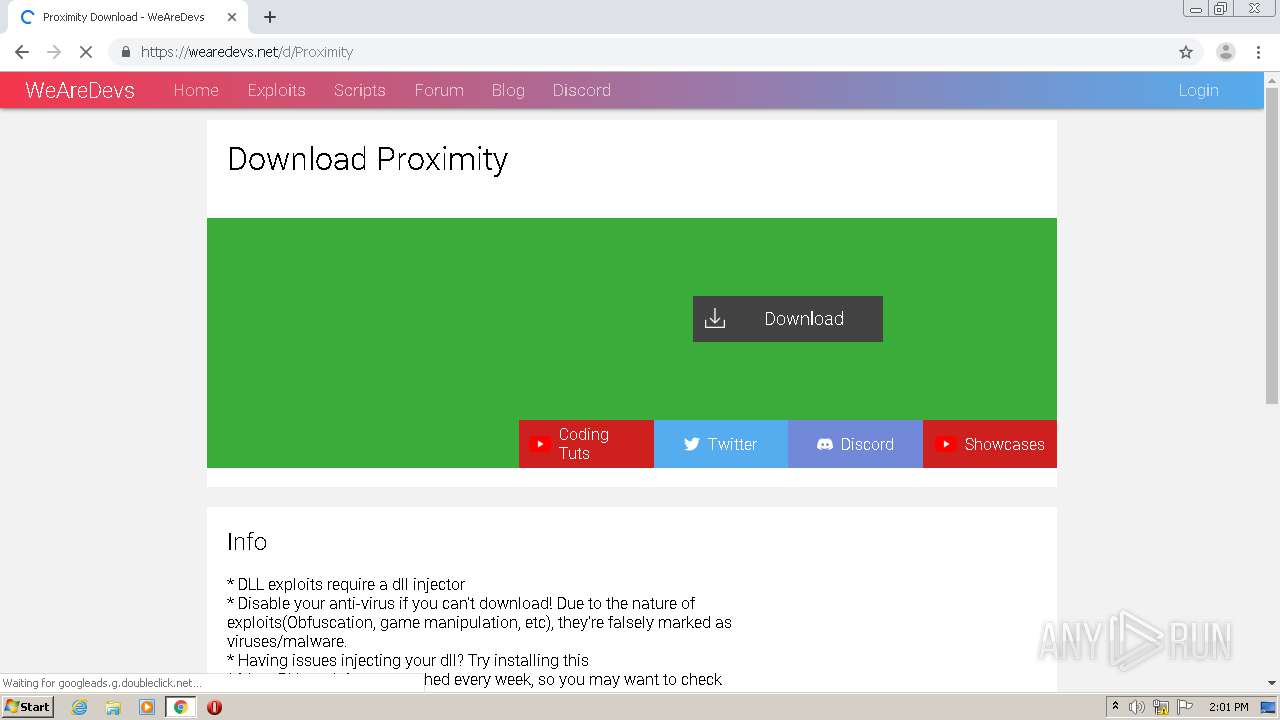
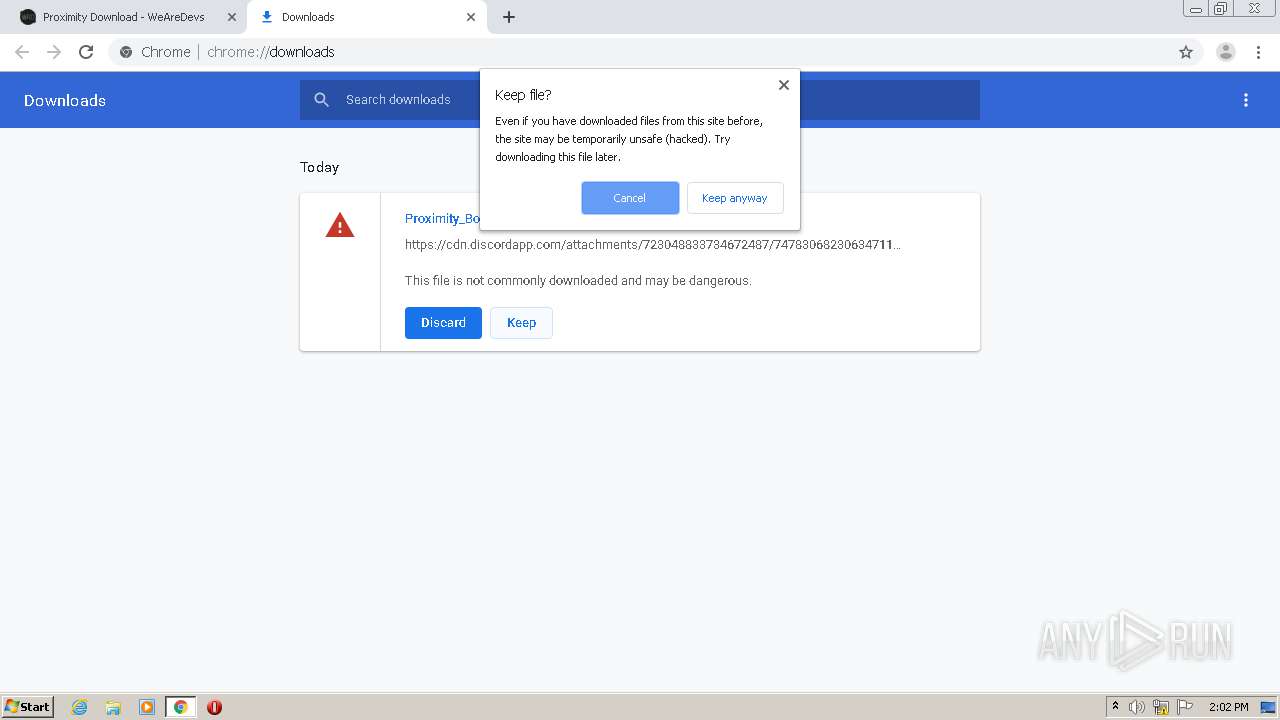
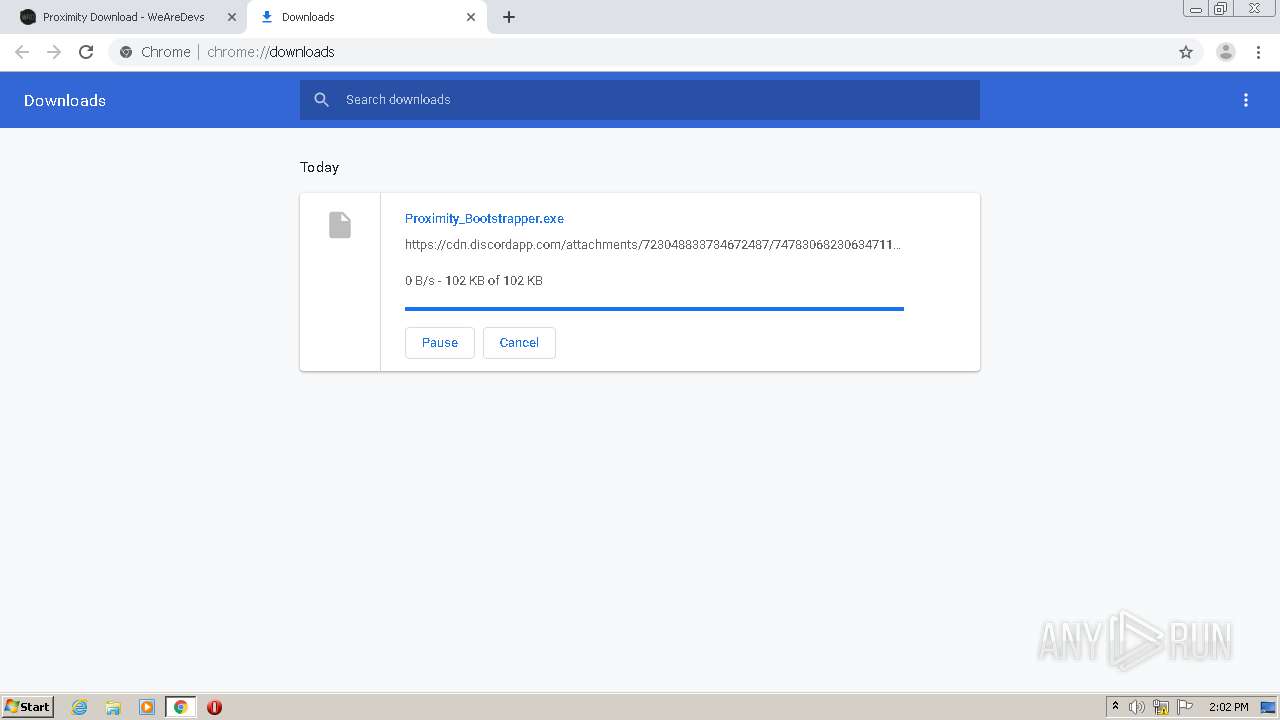
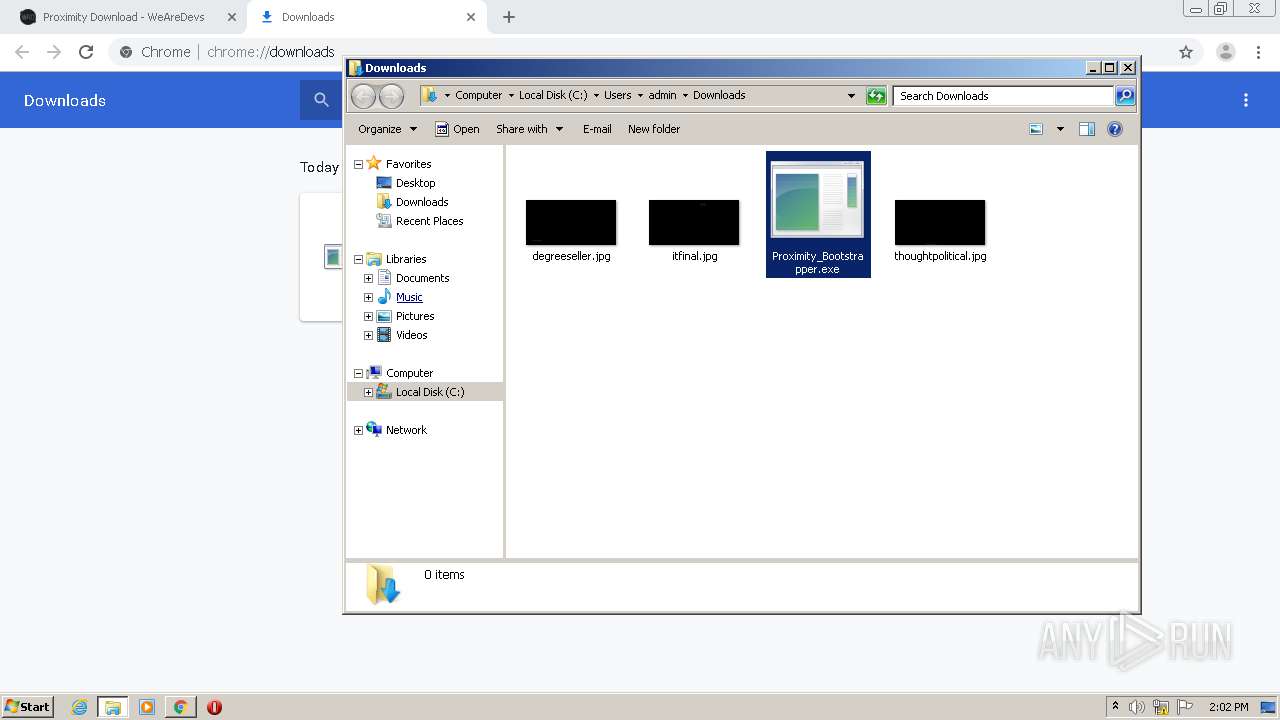
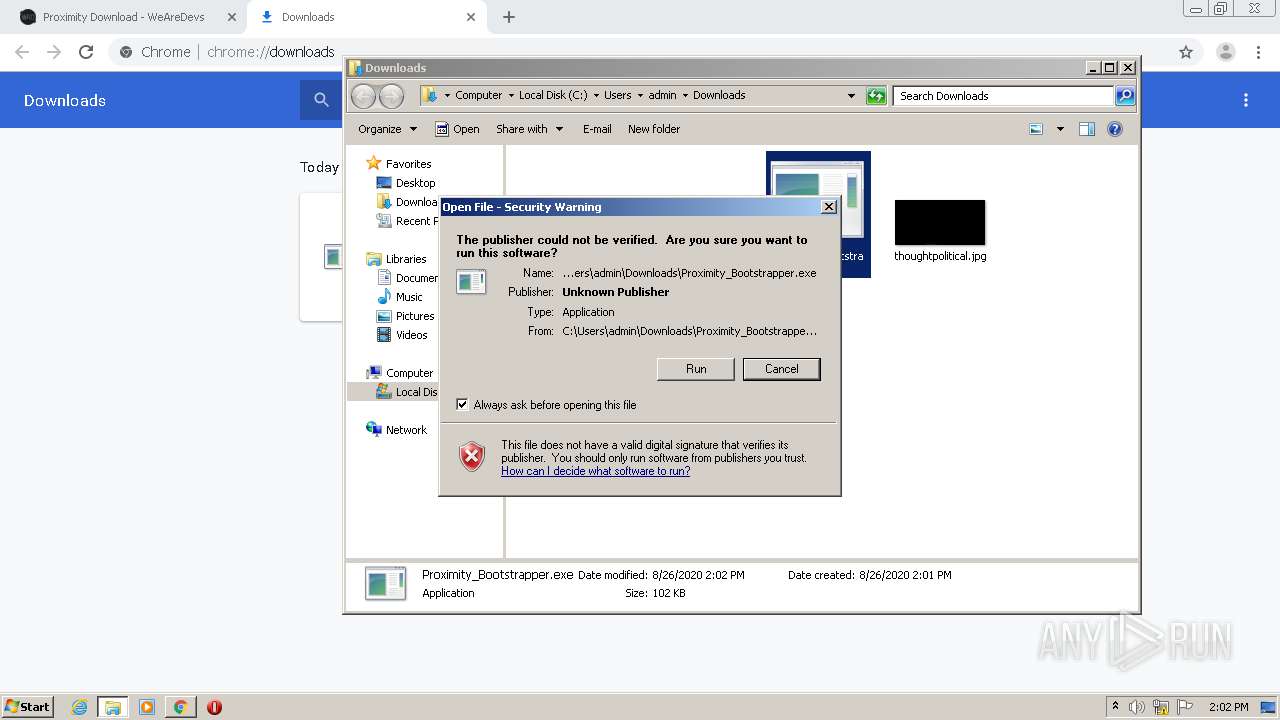
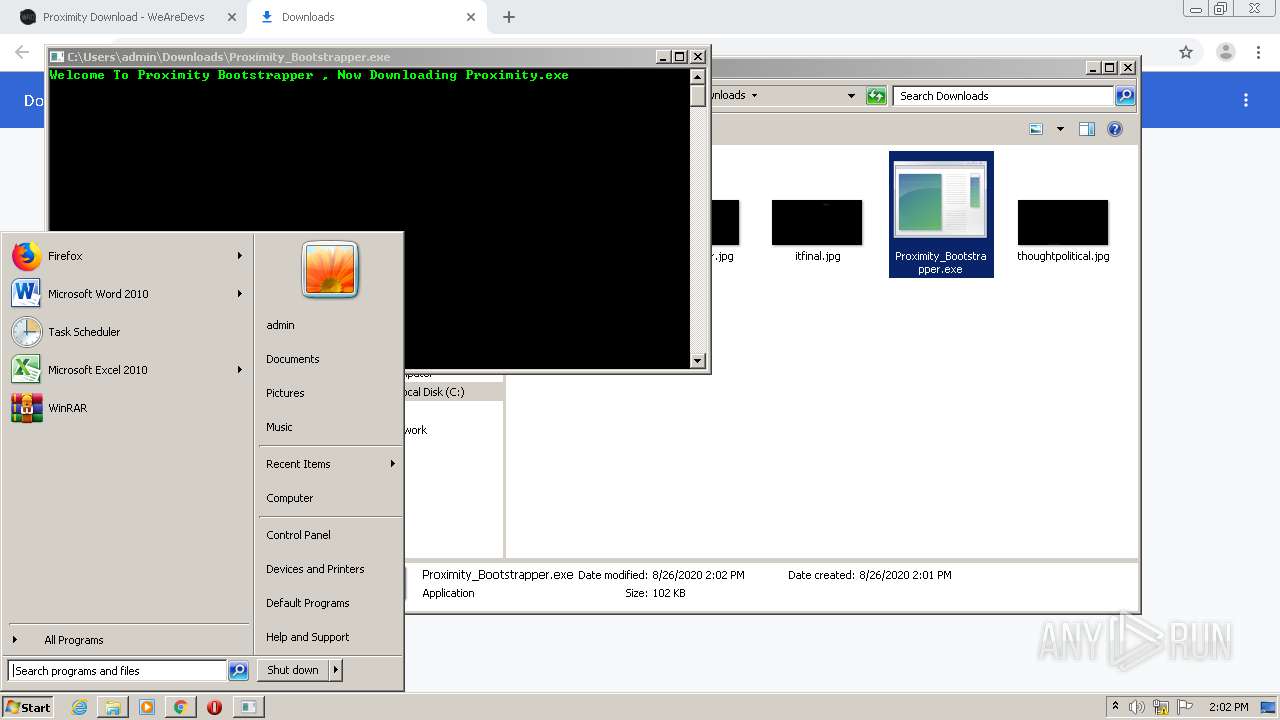
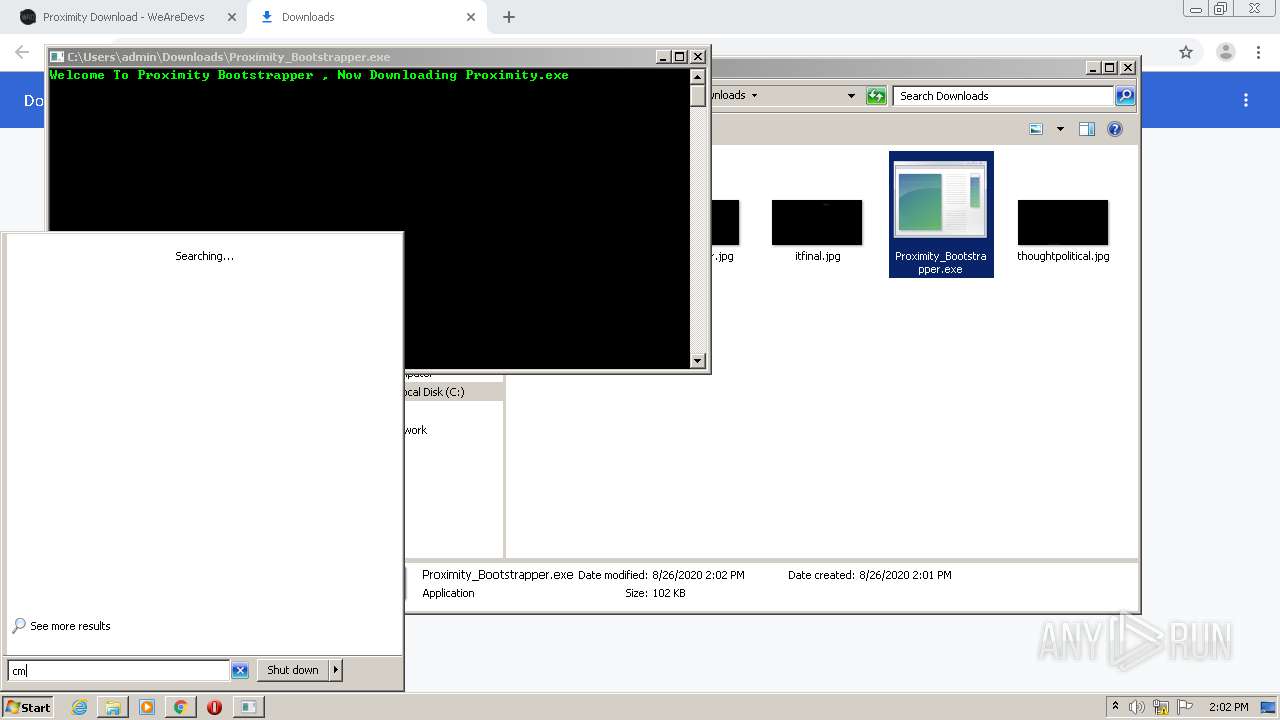
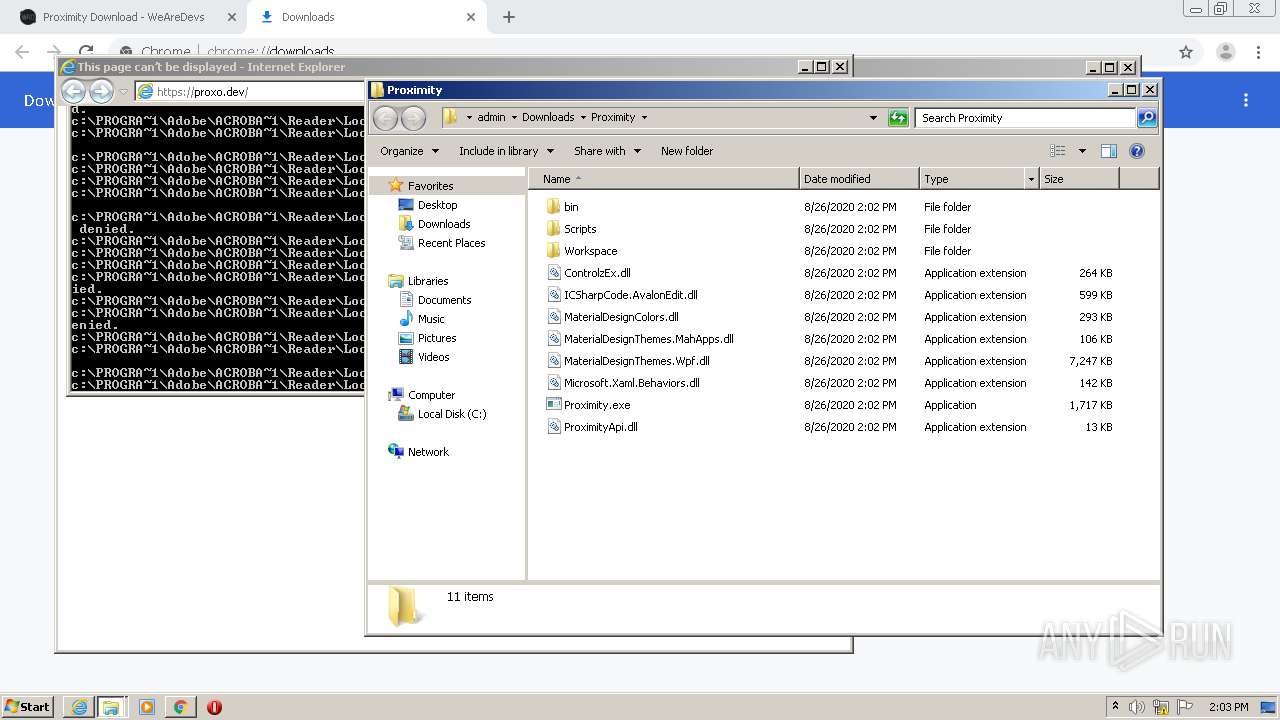
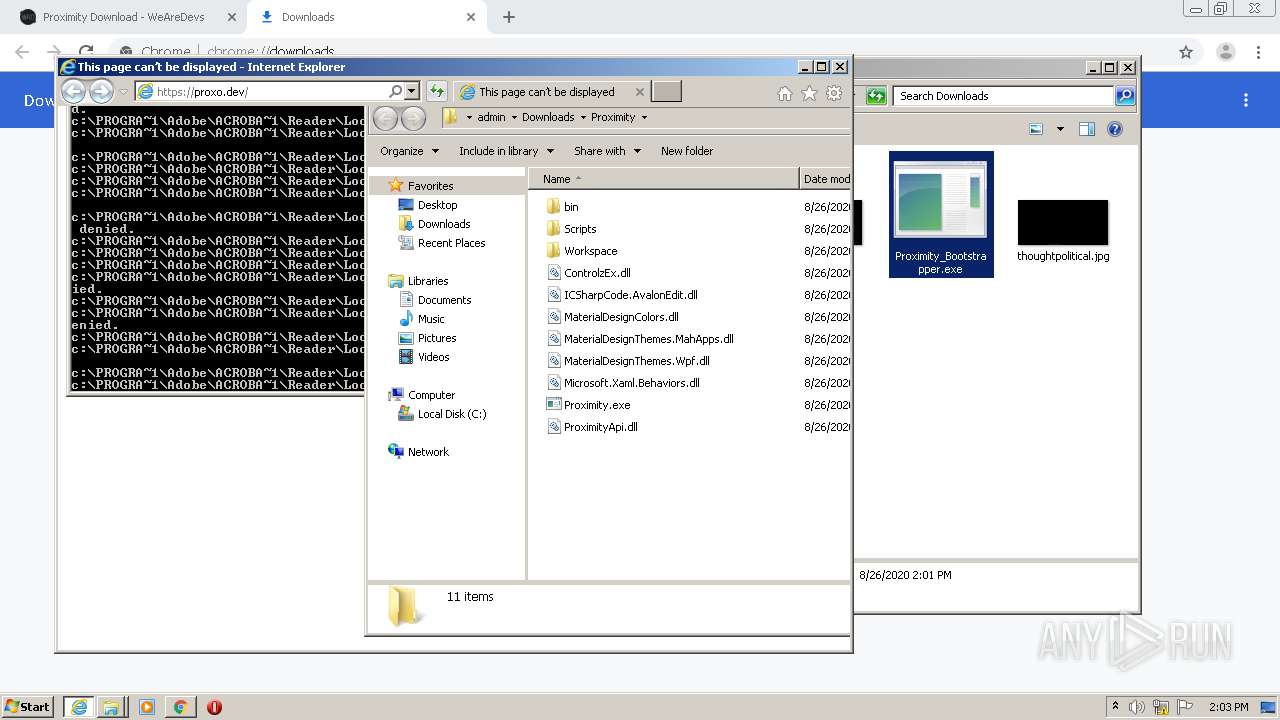
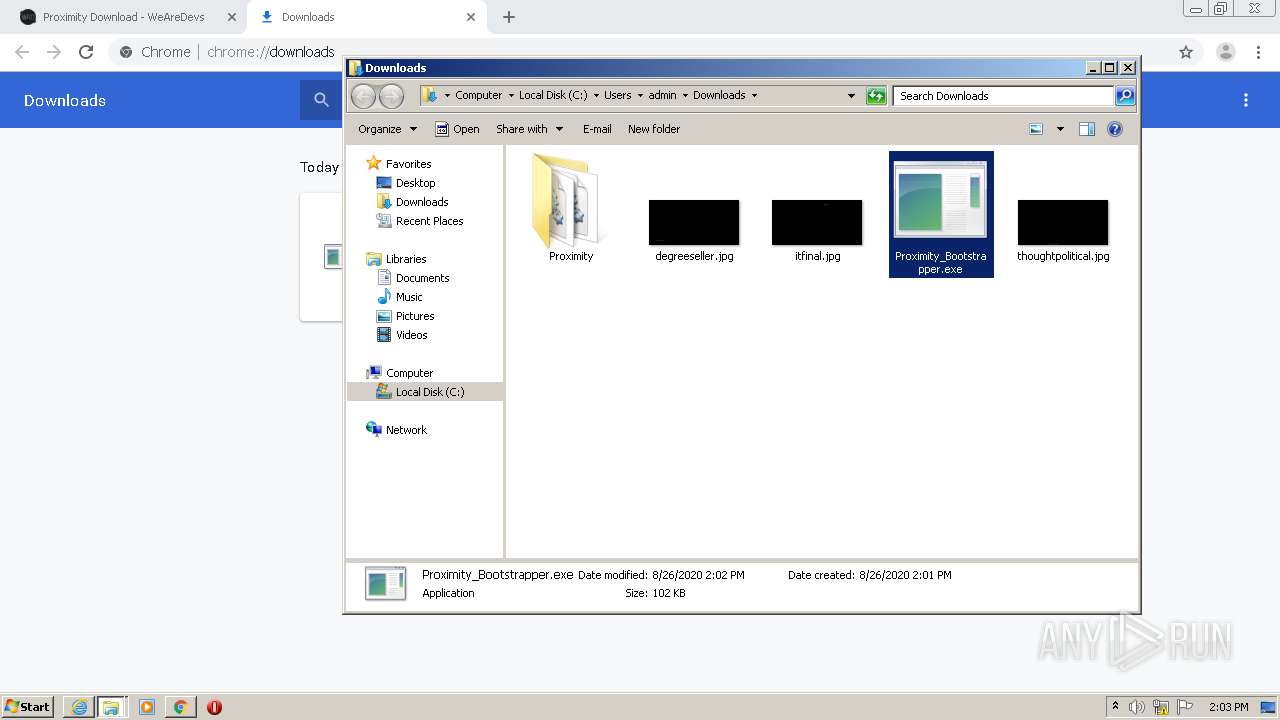
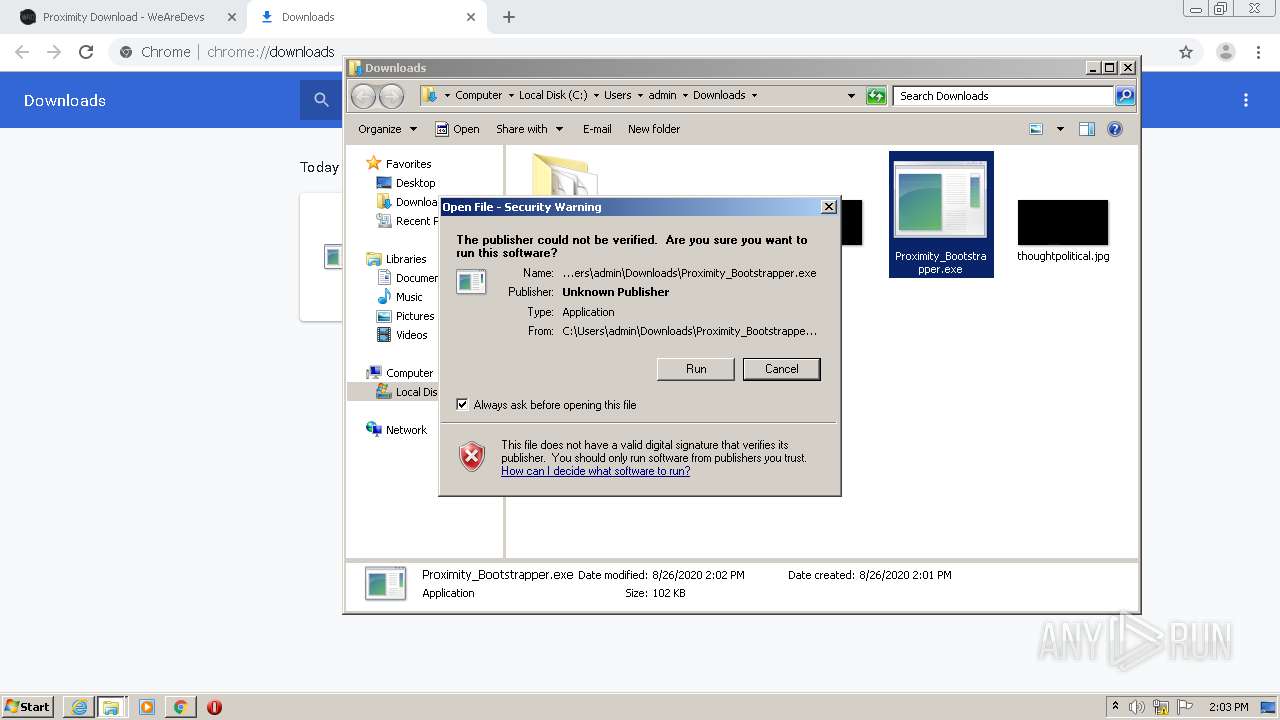
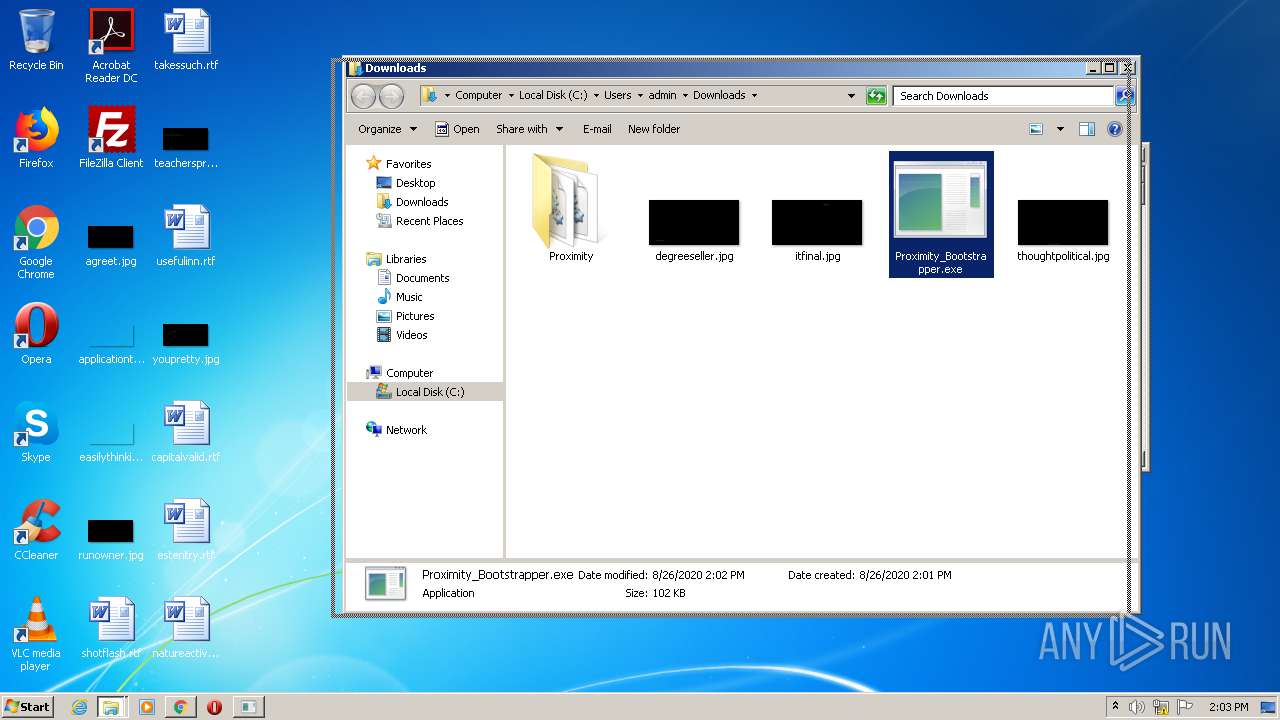
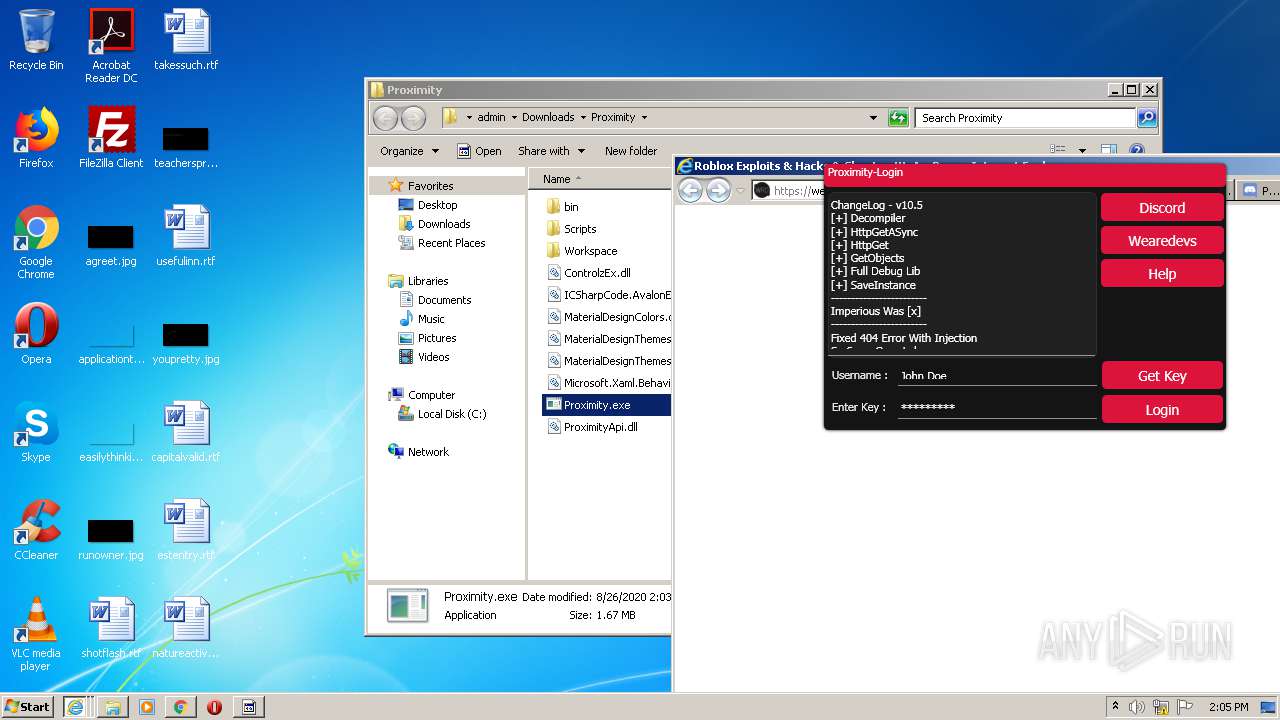
Manual execution by user
- Proximity_Bootstrapper.exe (PID: 2336)
- cmd.exe (PID: 3140)
- Proximity_Bootstrapper.exe (PID: 1852)
- Proximity.exe (PID: 1080)
- opera.exe (PID: 3892)
- Skype.exe (PID: 2392)
Changes internet zones settings
- iexplore.exe (PID: 2388)
- iexplore.exe (PID: 2420)
- iexplore.exe (PID: 1928)
- iexplore.exe (PID: 636)
- iexplore.exe (PID: 2516)
- iexplore.exe (PID: 2404)
Reads internet explorer settings
- iexplore.exe (PID: 3640)
- iexplore.exe (PID: 1596)
- iexplore.exe (PID: 2220)
- iexplore.exe (PID: 384)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 1972)
- iexplore.exe (PID: 3984)
- iexplore.exe (PID: 2824)
- iexplore.exe (PID: 3620)
- iexplore.exe (PID: 4016)
- iexplore.exe (PID: 3452)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2420)
- iexplore.exe (PID: 2404)
Creates files in the user directory
- iexplore.exe (PID: 2420)
- iexplore.exe (PID: 1596)
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 2404)
- iexplore.exe (PID: 1972)
- iexplore.exe (PID: 2632)
- iexplore.exe (PID: 2824)
- iexplore.exe (PID: 3984)
- iexplore.exe (PID: 3620)
- opera.exe (PID: 3892)
Changes settings of System certificates
- iexplore.exe (PID: 2420)
- iexplore.exe (PID: 2404)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2972)
- iexplore.exe (PID: 4016)
- iexplore.exe (PID: 3452)
- Skype.exe (PID: 2392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
106
Monitored processes
54
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Microsoft\Skype for Desktop\Skype.exe" --reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1 | C:\Program Files\Microsoft\Skype for Desktop\Skype.exe | Skype.exe | ||||||||||||
User: admin Company: Skype Technologies S.A. Integrity Level: MEDIUM Description: Skype Exit code: 0 Version: 8.29.0.50 Modules
| |||||||||||||||
| 384 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2516 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 636 | "C:\Program Files\Internet Explorer\iexplore.exe" https://proxo.dev/ | C:\Program Files\Internet Explorer\iexplore.exe | — | Proximity_Bootstrapper.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,13731867515022674250,13412339340815640534,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5480554137296068882 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1032,13731867515022674250,13412339340815640534,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8850908842071215559 --mojo-platform-channel-handle=4088 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
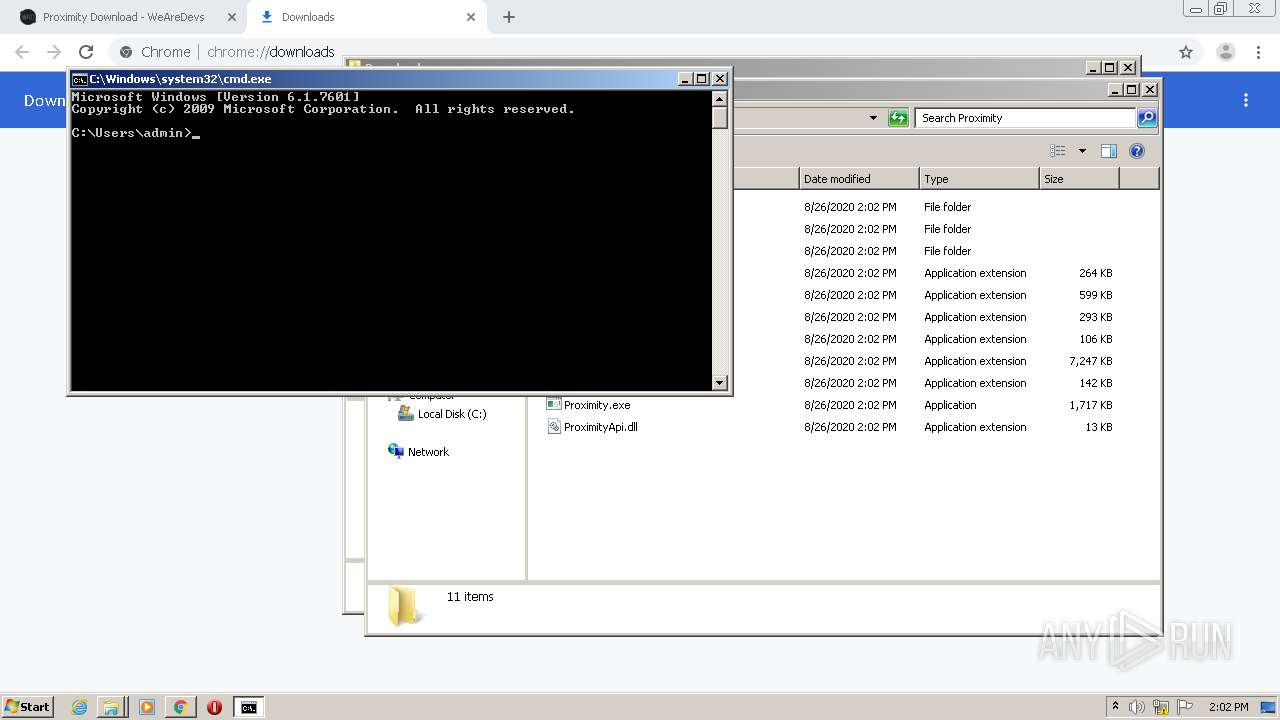
| 1080 | "C:\Users\admin\Downloads\Proximity\Proximity.exe" | C:\Users\admin\Downloads\Proximity\Proximity.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Proxo Remastered Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1592 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:636 CREDAT:2823433 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1596 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2420 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,13731867515022674250,13412339340815640534,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6246255960186629121 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1852 | "C:\Users\admin\Downloads\Proximity_Bootstrapper.exe" | C:\Users\admin\Downloads\Proximity_Bootstrapper.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Bootstrapper Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
9 442
Read events
8 486
Write events
939
Delete events
17
Modification events
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2076-13242920501503875 |
Value: 259 | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2832-13239195546717773 |
Value: 0 | |||
| (PID) Process: | (2076) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
20
Suspicious files
291
Text files
294
Unknown types
98
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\fb04c363-a868-4de5-84b5-0eb67f1f3ddc.tmp | — | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000032.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:1B8E44CB8872BF26BC5219E37A700F8A | SHA256:FD3D4BC8A7D28A05D1321F1D175FB59FC2BCC3532B92274A50133C22F0A0480A | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF15c83b.TMP | text | |
MD5:1B8E44CB8872BF26BC5219E37A700F8A | SHA256:FD3D4BC8A7D28A05D1321F1D175FB59FC2BCC3532B92274A50133C22F0A0480A | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:988975E56D776333B46F1BCAE6967C0E | SHA256:22186F0422A02BE70860975EF688A895EEA653C3A7259FFBA9114138A544E05A | |||
| 3312 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | gmc | |
MD5:B6D81B360A5672D80C27430F39153E2C | SHA256:30E14955EBF1352266DC2FF8067E68104607E750ABB9D3B36582B8AF909FCB58 | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:0CE1FA0314D44178816BA5E7133E07DD | SHA256:8D81EC8C4EFED885A0FF9267B0B388FB53316938EEDCDFABDC697E3610883714 | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15c9d1.TMP | — | |
MD5:— | SHA256:— | |||
| 2076 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:142AFC7F980CB38310D0680F2E8907CF | SHA256:3D5E5DF95E28CF65C77882748077EC52706AF02F8D869E188B6D16F782F82F44 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
70
TCP/UDP connections
293
DNS requests
98
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
1596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
1596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAqN7HPiQ2%2F4c3rdXE3uHG8%3D | US | der | 471 b | whitelisted |
1596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAFcAVODAkYfclFQEdIz38M%3D | US | der | 279 b | whitelisted |
2420 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEArLKLpGXuU5CHZ0cPPNxhI%3D | US | der | 471 b | whitelisted |
2388 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1596 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBReAhtobFzTvhaRmVeJ38QUchY9AwQUu69%2BAj36pvE8hI6t7jiY7NkyMtQCECsuburZdTZsFIpu26N8jAc%3D | US | der | 727 b | whitelisted |
1928 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
1596 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEArLKLpGXuU5CHZ0cPPNxhI%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2980 | chrome.exe | 216.58.205.226:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.18.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 216.58.206.2:443 | www.googletagservices.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.22.97:443 | tpc.googlesyndication.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 108.177.15.154:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2980 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.23.134:443 | s0.2mdn.net | Google Inc. | US | whitelisted |
2980 | chrome.exe | 172.217.16.163:443 | www.google.fr | Google Inc. | US | whitelisted |
— | — | 172.217.22.97:443 | tpc.googlesyndication.com | Google Inc. | US | whitelisted |
2980 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
wearedevs.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
cdn.wearedevs.net |
| whitelisted |
pagead2.googlesyndication.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
adservice.google.fr |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3524 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
3524 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2220 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
384 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2632 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
Process | Message |
|---|---|
Skype.exe | [272:3192:0826/140521.023:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [272:3192:0826/140521.024:VERBOSE1:crash_service.cc(300)] pipe name is \\.\pipe\skype-preview Crash Service
dumps at C:\Users\admin\AppData\Local\Temp\skype-preview Crashes
|
Skype.exe | [272:3192:0826/140521.024:VERBOSE1:crash_service.cc(304)] checkpoint is C:\Users\admin\AppData\Local\Temp\skype-preview Crashes\crash_checkpoint.txt
server is https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload
maximum 128 reports/day
reporter is electron-crash-service
|
Skype.exe | [272:3192:0826/140521.024:VERBOSE1:crash_service.cc(145)] window handle is 000204C2
|
Skype.exe | [272:3192:0826/140521.025:VERBOSE1:crash_service_main.cc(94)] Ready to process crash requests
|
Skype.exe | [272:3868:0826/140521.025:VERBOSE1:crash_service.cc(333)] client start. pid = 2392
|
Skype.exe | [272:3868:0826/140523.142:VERBOSE1:crash_service.cc(333)] client start. pid = 5784
|
Skype.exe | [5412:5424:0826/140523.371:VERBOSE1:crash_service_main.cc(78)] Session start. cmdline is [--reporter-url=https://rink.hockeyapp.net/api/2/apps/a741743329d94bc08826af367733939d/crashes/upload --application-name=skype-preview "--crashes-directory=C:\Users\admin\AppData\Local\Temp\skype-preview Crashes" --v=1]
|
Skype.exe | [5412:5424:0826/140523.372:ERROR:crash_service.cc(311)] could not start dumper
|
Skype.exe | [5412:5424:0826/140523.372:VERBOSE1:crash_service.cc(145)] window handle is 000104E0
|