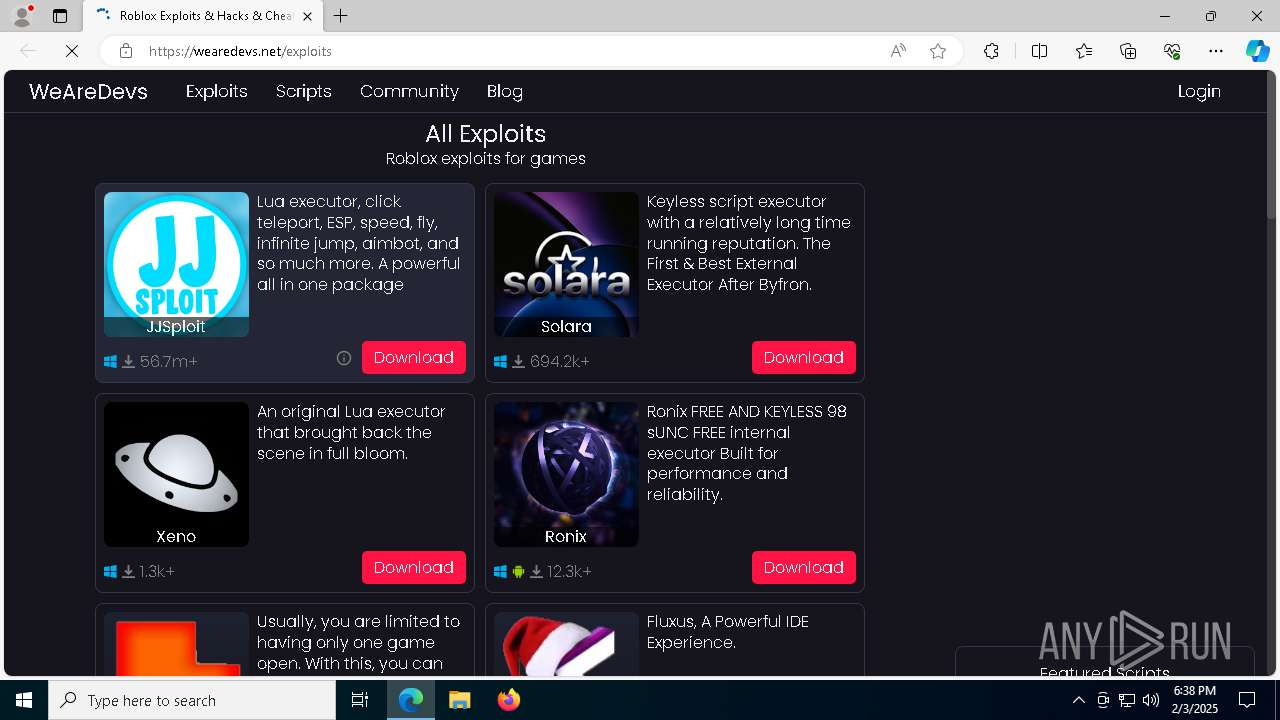
| URL: | https://wearedevs.net/exploits |
| Full analysis: | https://app.any.run/tasks/50dd9438-d0b3-4a29-91e1-53ea9234df23 |
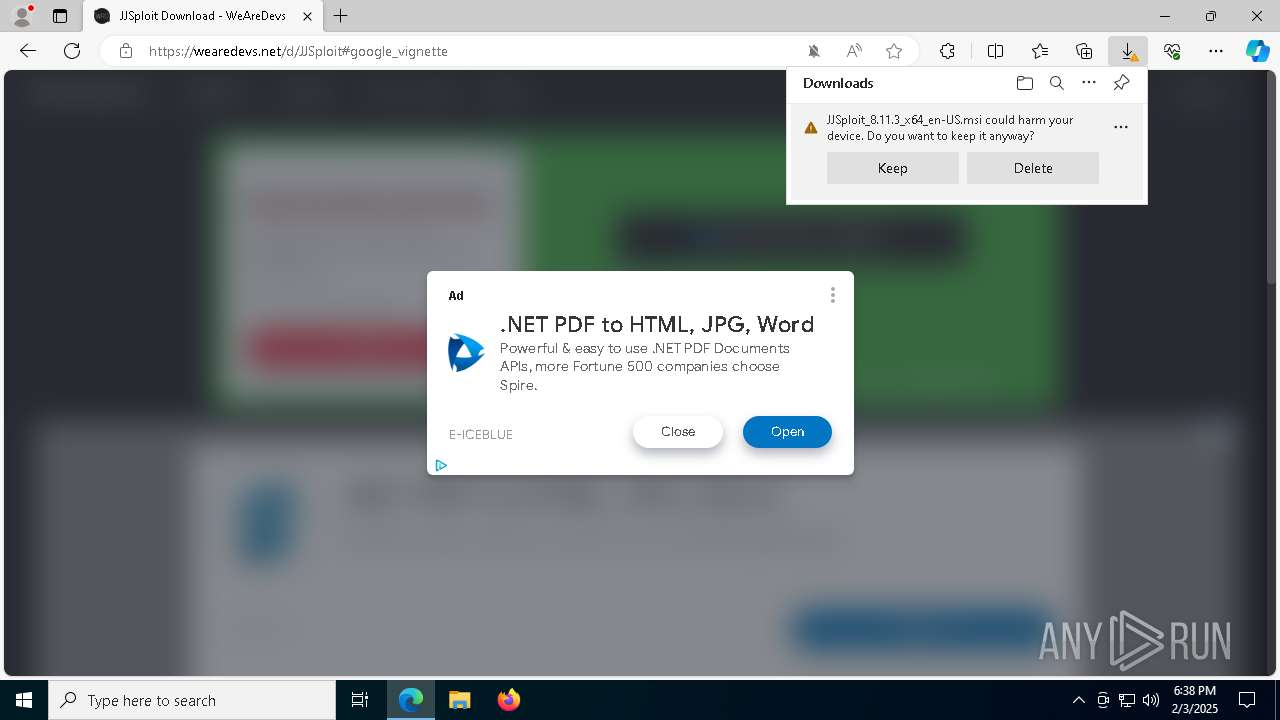
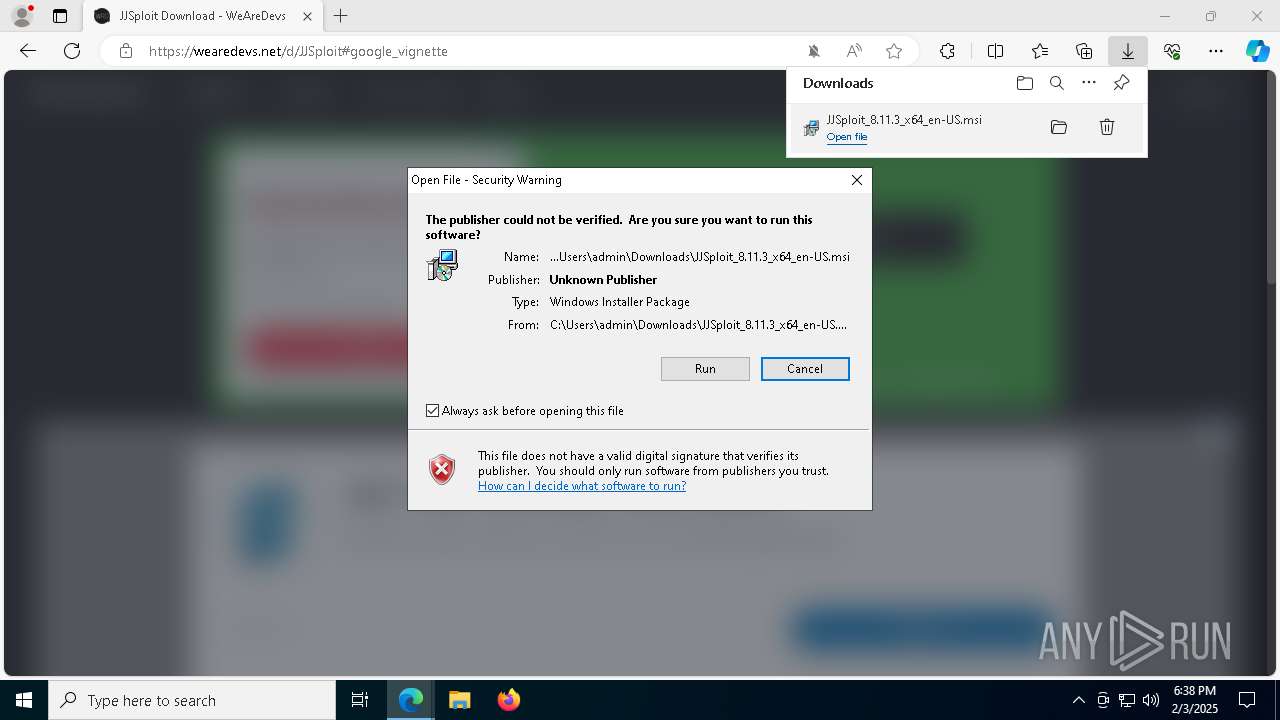
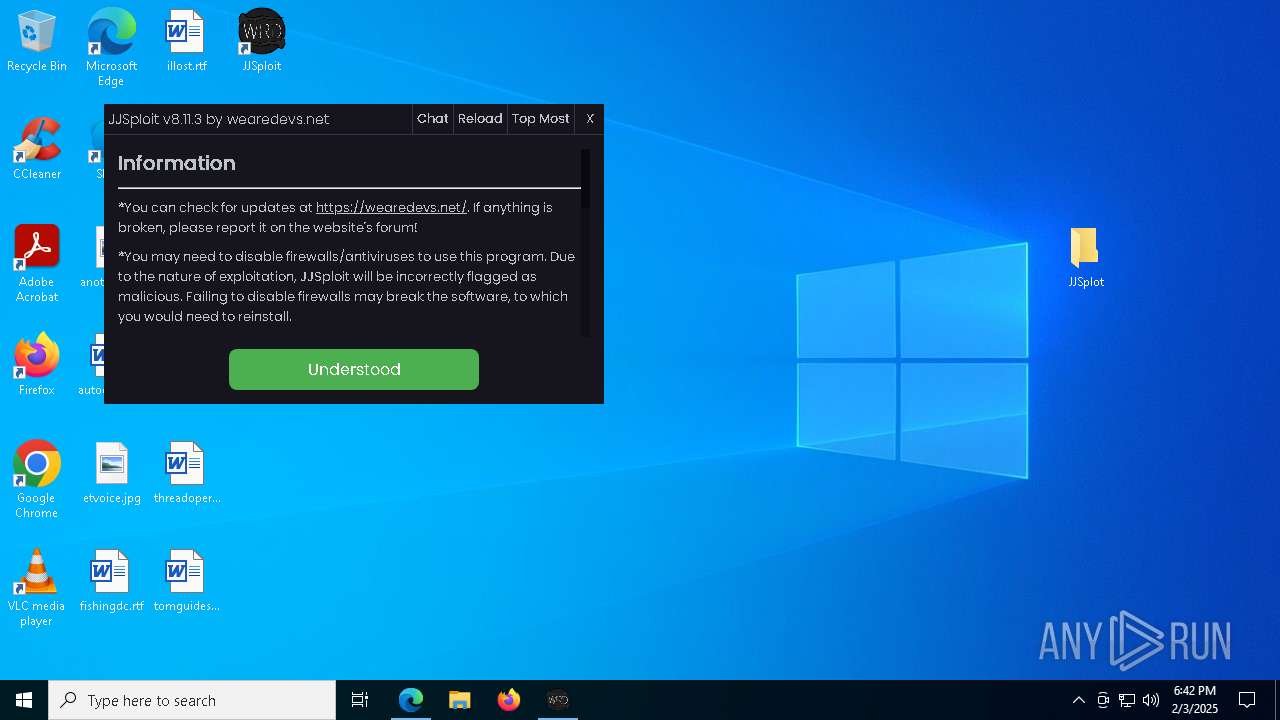
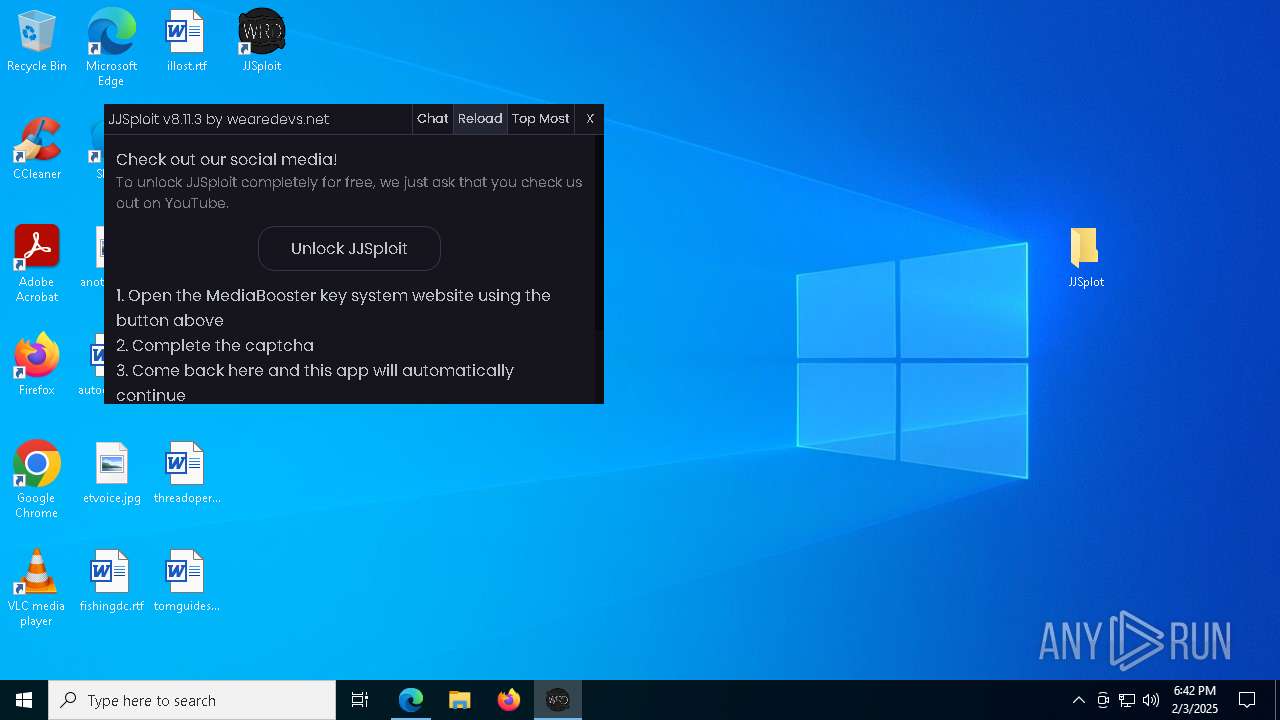
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2025, 18:37:51 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | A30BCDF6A2392436D6EB27CF9CCA01D6 |
| SHA1: | 6457EA1346387E57B5DD8097576710DF7A9FB266 |
| SHA256: | 7017467F047C32C773BD9A9CA012F5214812B39127EAA94043FB36D317C83CB3 |
| SSDEEP: | 3:N8R/BApKYEMw:25BuRw |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 8056)
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 7572)
The DLL Hijacking
- msedgewebview2.exe (PID: 7352)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 5652)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5256)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 5256)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 5256)
Starts process via Powershell
- powershell.exe (PID: 8056)
Downloads file from URI via Powershell
- powershell.exe (PID: 8056)
Manipulates environment variables
- powershell.exe (PID: 8056)
Executable content was dropped or overwritten
- powershell.exe (PID: 8056)
- MicrosoftEdgeWebview2Setup.exe (PID: 3732)
- MicrosoftEdgeUpdate.exe (PID: 7572)
- MicrosoftEdge_X64_132.0.2957.140.exe (PID: 1400)
- setup.exe (PID: 2456)
Process drops legitimate windows executable
- powershell.exe (PID: 8056)
- MicrosoftEdgeWebview2Setup.exe (PID: 3732)
- MicrosoftEdgeUpdate.exe (PID: 7572)
- MicrosoftEdge_X64_132.0.2957.140.exe (PID: 1400)
- setup.exe (PID: 2456)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 3732)
- MicrosoftEdgeUpdate.exe (PID: 7572)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1080)
- MicrosoftEdgeUpdate.exe (PID: 8124)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7452)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4188)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 7572)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 7572)
- MicrosoftEdgeUpdate.exe (PID: 6264)
- msiexec.exe (PID: 6212)
- msedgewebview2.exe (PID: 3900)
Checks Windows Trust Settings
- MicrosoftEdgeUpdate.exe (PID: 6264)
Application launched itself
- setup.exe (PID: 2456)
- MicrosoftEdgeUpdate.exe (PID: 6264)
- msedgewebview2.exe (PID: 3900)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 8056)
Creates a software uninstall entry
- setup.exe (PID: 2456)
Searches for installed software
- setup.exe (PID: 2456)
INFO
Reads the computer name
- identity_helper.exe (PID: 7800)
- msiexec.exe (PID: 5256)
- msiexec.exe (PID: 6212)
- MicrosoftEdgeUpdate.exe (PID: 7572)
- MicrosoftEdgeUpdate.exe (PID: 8124)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4188)
- MicrosoftEdgeUpdate.exe (PID: 7780)
- MicrosoftEdgeUpdate.exe (PID: 8012)
- MicrosoftEdgeUpdate.exe (PID: 6264)
- MicrosoftEdge_X64_132.0.2957.140.exe (PID: 1400)
- setup.exe (PID: 2456)
- MicrosoftEdgeUpdate.exe (PID: 2672)
- msedgewebview2.exe (PID: 3900)
- JJSploit.exe (PID: 7860)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1080)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7452)
- msedgewebview2.exe (PID: 7352)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6176)
- msiexec.exe (PID: 5256)
- msedge.exe (PID: 1556)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6504)
Checks supported languages
- msiexec.exe (PID: 6212)
- msiexec.exe (PID: 5256)
- identity_helper.exe (PID: 7800)
- MicrosoftEdgeWebview2Setup.exe (PID: 3732)
- MicrosoftEdgeUpdate.exe (PID: 7572)
- MicrosoftEdgeUpdate.exe (PID: 8124)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 1080)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 7452)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4188)
- MicrosoftEdgeUpdate.exe (PID: 7780)
- MicrosoftEdgeUpdate.exe (PID: 8012)
- MicrosoftEdgeUpdate.exe (PID: 6264)
- MicrosoftEdge_X64_132.0.2957.140.exe (PID: 1400)
- setup.exe (PID: 2456)
- setup.exe (PID: 8160)
- MicrosoftEdgeUpdate.exe (PID: 2672)
- JJSploit.exe (PID: 7860)
- msedgewebview2.exe (PID: 7352)
- msedgewebview2.exe (PID: 1612)
- msedgewebview2.exe (PID: 3900)
- msedgewebview2.exe (PID: 1296)
- msedgewebview2.exe (PID: 8052)
- msedgewebview2.exe (PID: 4540)
Manages system restore points
- SrTasks.exe (PID: 7936)
Creates a software uninstall entry
- msiexec.exe (PID: 5256)
Reads Environment values
- identity_helper.exe (PID: 7800)
- MicrosoftEdgeUpdate.exe (PID: 7780)
- MicrosoftEdgeUpdate.exe (PID: 2672)
- msedgewebview2.exe (PID: 3900)
Application launched itself
- msedge.exe (PID: 6504)
Disables trace logs
- powershell.exe (PID: 8056)
Checks proxy server information
- powershell.exe (PID: 8056)
- MicrosoftEdgeUpdate.exe (PID: 7780)
- MicrosoftEdgeUpdate.exe (PID: 6264)
- MicrosoftEdgeUpdate.exe (PID: 2672)
- msedgewebview2.exe (PID: 3900)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 3732)
The sample compiled with english language support
- powershell.exe (PID: 8056)
- MicrosoftEdgeWebview2Setup.exe (PID: 3732)
- MicrosoftEdgeUpdate.exe (PID: 7572)
- MicrosoftEdge_X64_132.0.2957.140.exe (PID: 1400)
- setup.exe (PID: 2456)
- msedge.exe (PID: 1556)
Create files in a temporary directory
- MicrosoftEdgeWebview2Setup.exe (PID: 3732)
- MicrosoftEdgeUpdate.exe (PID: 7572)
- msedgewebview2.exe (PID: 3900)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 7572)
- MicrosoftEdgeUpdate.exe (PID: 6264)
- MicrosoftEdge_X64_132.0.2957.140.exe (PID: 1400)
- setup.exe (PID: 8160)
- setup.exe (PID: 2456)
- msedgewebview2.exe (PID: 1296)
- msedgewebview2.exe (PID: 3900)
- JJSploit.exe (PID: 7860)
- msedgewebview2.exe (PID: 1612)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 7572)
- setup.exe (PID: 2456)
- msiexec.exe (PID: 6212)
- msedgewebview2.exe (PID: 3900)
- msedgewebview2.exe (PID: 4540)
Reads the software policy settings
- MicrosoftEdgeUpdate.exe (PID: 7780)
- MicrosoftEdgeUpdate.exe (PID: 6264)
- MicrosoftEdgeUpdate.exe (PID: 2672)
Detects Fody packer (YARA)
- powershell.exe (PID: 8056)
Reads the machine GUID from the registry
- MicrosoftEdgeUpdate.exe (PID: 6264)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
227
Monitored processes
88
Malicious processes
8
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 904 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=4288 --field-trial-handle=2276,i,10435834253746750080,1459851094774347583,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1080 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.43\MicrosoftEdgeUpdateComRegisterShell64.exe" /user | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.43\MicrosoftEdgeUpdateComRegisterShell64.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update COM Registration Helper Exit code: 0 Version: 1.3.195.43 Modules
| |||||||||||||||
| 1140 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | SrTasks.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1296 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\132.0.2957.140\msedgewebview2.exe --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Local\net.wearedevs\EBWebView /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Local\net.wearedevs\EBWebView\Crashpad --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=132.0.6834.160 --annotation=exe=C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\132.0.2957.140\msedgewebview2.exe --annotation=plat=Win64 "--annotation=prod=Edge WebView2" --annotation=ver=132.0.2957.140 --initial-client-data=0x184,0x188,0x18c,0x160,0x194,0x7ff81feeb078,0x7ff81feeb084,0x7ff81feeb090 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\132.0.2957.140\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 132.0.2957.140 Modules
| |||||||||||||||
| 1356 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7248 --field-trial-handle=2276,i,10435834253746750080,1459851094774347583,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1400 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{E0EE0768-F0A8-4DCF-98A0-E4D3CDD772C7}\MicrosoftEdge_X64_132.0.2957.140.exe" --msedgewebview --verbose-logging --do-not-launch-msedge --user-level | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{E0EE0768-F0A8-4DCF-98A0-E4D3CDD772C7}\MicrosoftEdge_X64_132.0.2957.140.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Exit code: 0 Version: 132.0.2957.140 Modules
| |||||||||||||||
| 1468 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6392 --field-trial-handle=2276,i,10435834253746750080,1459851094774347583,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1472 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=4240 --field-trial-handle=2276,i,10435834253746750080,1459851094774347583,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1556 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7224 --field-trial-handle=2276,i,10435834253746750080,1459851094774347583,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1612 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\132.0.2957.140\msedgewebview2.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --string-annotations --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\net.wearedevs\EBWebView" --webview-exe-name=JJSploit.exe --webview-exe-version=8.11.3 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --always-read-main-dll --field-trial-handle=1896,i,6707274218634706624,9853895484139892017,262144 --disable-features=msPdfOOUI,msSmartScreenProtection,msWebOOUI --variations-seed-version --mojo-platform-channel-handle=2092 /prefetch:3 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\132.0.2957.140\msedgewebview2.exe | msedgewebview2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 132.0.2957.140 Modules
| |||||||||||||||
Total events
26 839
Read events
23 892
Write events
2 862
Delete events
85
Modification events
| (PID) Process: | (6504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6504) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: DA24C779D78B2F00 | |||
| (PID) Process: | (6504) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 7226EA79D78B2F00 | |||
| (PID) Process: | (6504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721450 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E9005D91-AD73-441F-AA6C-2BA0CFD51A5C} | |||
| (PID) Process: | (6504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721450 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7011CD36-0E8E-416B-8A94-5C42A099DFB7} | |||
| (PID) Process: | (6504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721450 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A33D3E82-F134-4D47-A00F-54C9C551FB25} | |||
| (PID) Process: | (6504) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\721450 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {49855D11-4E84-4583-AD70-927EB3AF89C5} | |||
Executable files
232
Suspicious files
592
Text files
139
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF136fa5.TMP | — | |
MD5:— | SHA256:— | |||
| 6504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF136fa5.TMP | — | |
MD5:— | SHA256:— | |||
| 6504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF136fa5.TMP | — | |
MD5:— | SHA256:— | |||
| 6504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF136fa5.TMP | — | |
MD5:— | SHA256:— | |||
| 6504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF136fb5.TMP | — | |
MD5:— | SHA256:— | |||
| 6504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6504 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
155
DNS requests
152
Threats
40
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4308 | svchost.exe | GET | 200 | 95.101.78.32:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7788 | svchost.exe | HEAD | 200 | 95.101.78.16:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1739209070&P2=404&P3=2&P4=cRLrjMg0QmdqnIyNN6Q9PjRwsGSEFupqpZPqOXJQqt6C%2feedb5H0bz%2fjyY7ns5Ar44%2b0M2epijQg22UE8Ny9sw%3d%3d | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 104.75.232.13:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6324 | backgroundTaskHost.exe | GET | 200 | 104.75.232.13:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5496 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7788 | svchost.exe | GET | 206 | 95.101.78.16:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739209070&P2=404&P3=2&P4=VBh89hmEYf5ppTgduFk7mhtvr6zWjDOc9ESakDjxvo4ECDX%2fEV8poJqTNz4Isb%2bpOjSjB%2b1xNo98PZEThjChQQ%3d%3d | unknown | — | — | whitelisted |
7788 | svchost.exe | GET | 206 | 95.101.78.16:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1739209070&P2=404&P3=2&P4=cRLrjMg0QmdqnIyNN6Q9PjRwsGSEFupqpZPqOXJQqt6C%2feedb5H0bz%2fjyY7ns5Ar44%2b0M2epijQg22UE8Ny9sw%3d%3d | unknown | — | — | whitelisted |
7788 | svchost.exe | GET | 206 | 95.101.78.16:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1739209070&P2=404&P3=2&P4=cRLrjMg0QmdqnIyNN6Q9PjRwsGSEFupqpZPqOXJQqt6C%2feedb5H0bz%2fjyY7ns5Ar44%2b0M2epijQg22UE8Ny9sw%3d%3d | unknown | — | — | whitelisted |
7788 | svchost.exe | HEAD | 200 | 95.101.78.16:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739209070&P2=404&P3=2&P4=VBh89hmEYf5ppTgduFk7mhtvr6zWjDOc9ESakDjxvo4ECDX%2fEV8poJqTNz4Isb%2bpOjSjB%2b1xNo98PZEThjChQQ%3d%3d | unknown | — | — | whitelisted |
7788 | svchost.exe | GET | 206 | 95.101.78.16:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1739209070&P2=404&P3=2&P4=VBh89hmEYf5ppTgduFk7mhtvr6zWjDOc9ESakDjxvo4ECDX%2fEV8poJqTNz4Isb%2bpOjSjB%2b1xNo98PZEThjChQQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 104.75.232.13:80 | ocsp.digicert.com | Akamai International B.V. | FR | whitelisted |
4308 | svchost.exe | 95.101.78.32:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4308 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 104.75.232.13:80 | ocsp.digicert.com | Akamai International B.V. | FR | whitelisted |
1076 | svchost.exe | 23.213.166.81:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
6504 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
wearedevs.net |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6880 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6880 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6880 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6880 | msedge.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6880 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
6880 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
7788 | svchost.exe | Misc activity | ET INFO Packed Executable Download |
1612 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
1612 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
1612 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
Process | Message |
|---|---|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\net.wearedevs directory exists )
|
JJSploit.exe | Warning: AddWebResourceRequestedFilter without SourceKind parameter is deprecated! It does not behave as expected for iframes.Please use AddWebResourceRequestedFilterWithRequestSourceKinds instead. For more information, please see https://go.microsoft.com/fwlink/?linkid=2286319 |