| File name: | qy8mtf.exe |
| Full analysis: | https://app.any.run/tasks/5b286d09-32bd-4af6-805c-6fbbd0993b16 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 15, 2019, 10:10:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | ECA32D9E3D5FD89DC690E8590A0198E7 |
| SHA1: | EF3EEB70323923AA70250C3D4E2D862C6CAC721E |
| SHA256: | 6FFE96F3ABEC30FB4A73271ED0AA96D9C994CCE3CA8529AB7543EEEC1102D2E1 |
| SSDEEP: | 3072:8KuT2ShlX/1SvgDJ6gwBq1Dn1xEWrXS8gg:8Ku/ho6JvwA1DnDNSX |
MALICIOUS
Emotet process was detected
- soundser.exe (PID: 2736)
EMOTET was detected
- soundser.exe (PID: 4044)
GOTKIT detected
- qy8mtf.exe (PID: 896)
Changes the autorun value in the registry
- soundser.exe (PID: 4044)
Connects to CnC server
- soundser.exe (PID: 4044)
SUSPICIOUS
Application launched itself
- qy8mtf.exe (PID: 3364)
- soundser.exe (PID: 2736)
Starts itself from another location
- qy8mtf.exe (PID: 896)
Connects to server without host name
- soundser.exe (PID: 4044)
Executable content was dropped or overwritten
- qy8mtf.exe (PID: 896)
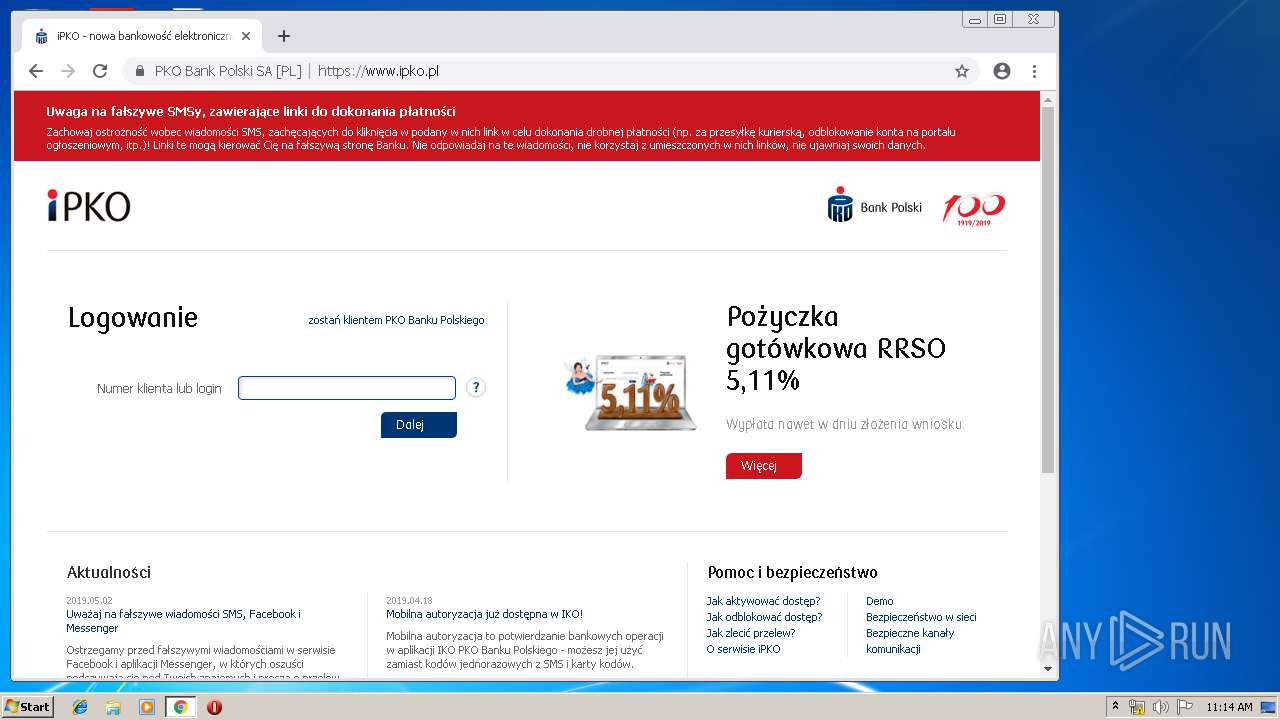
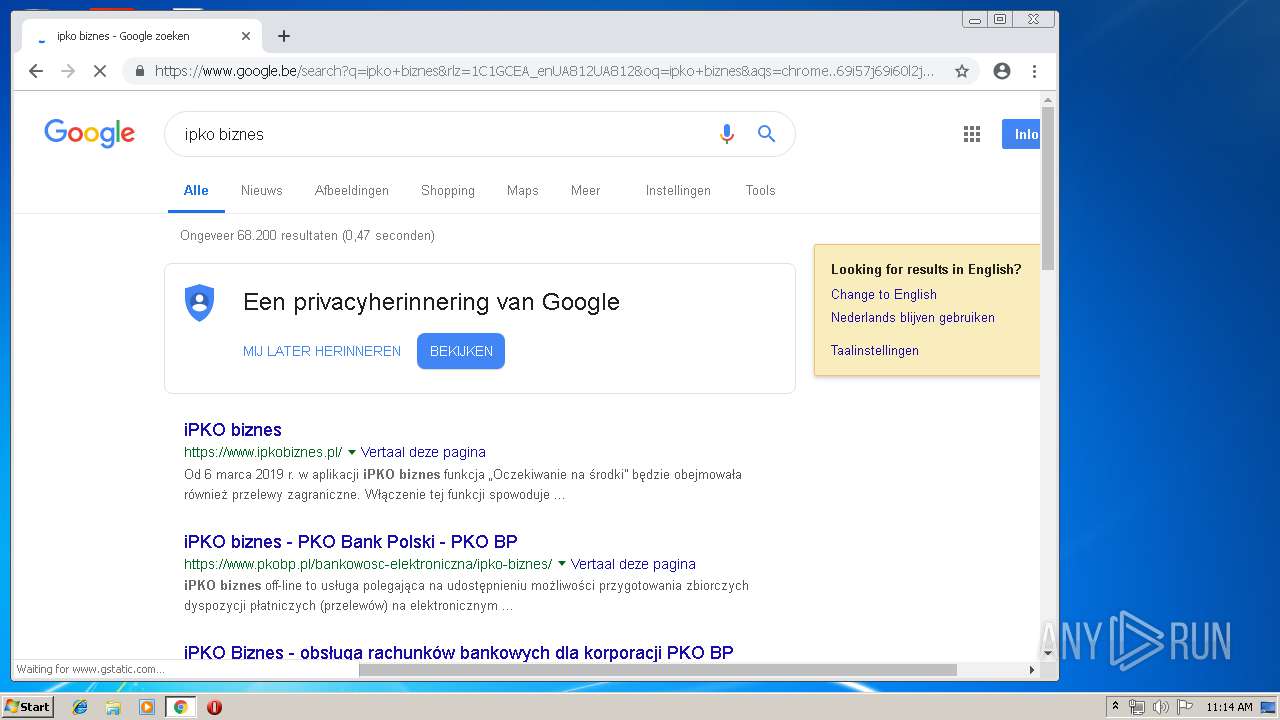
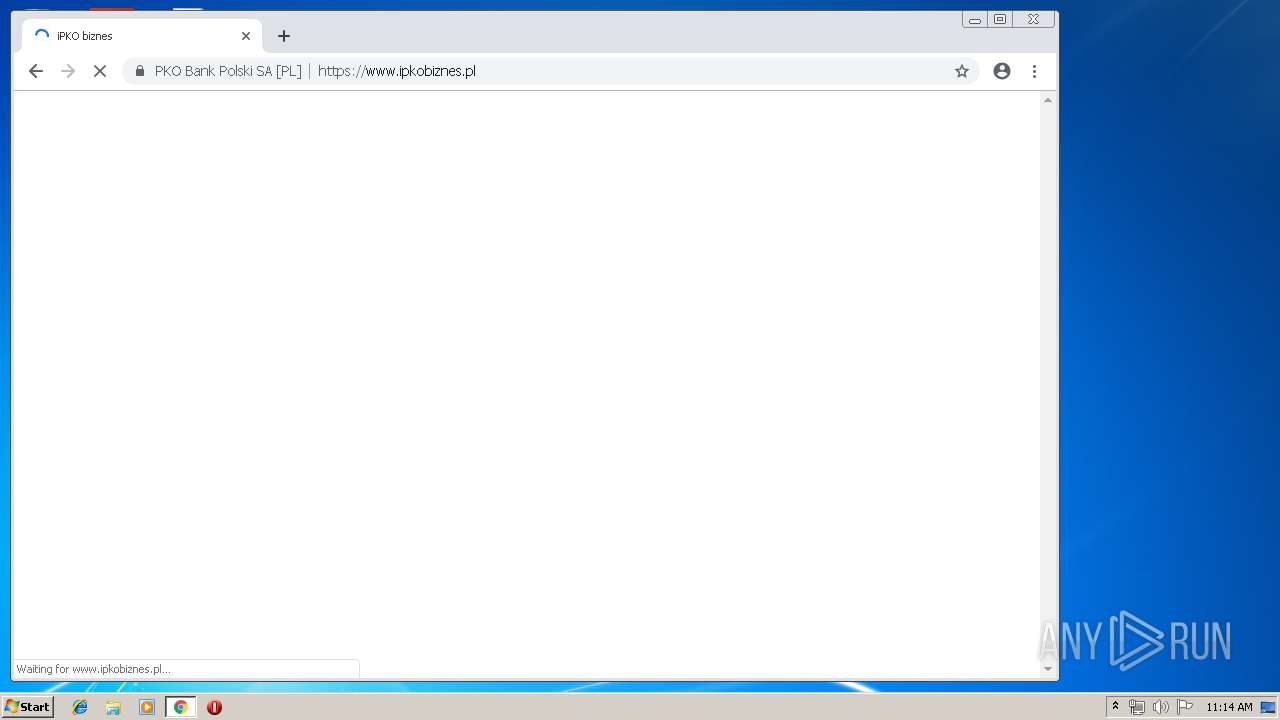
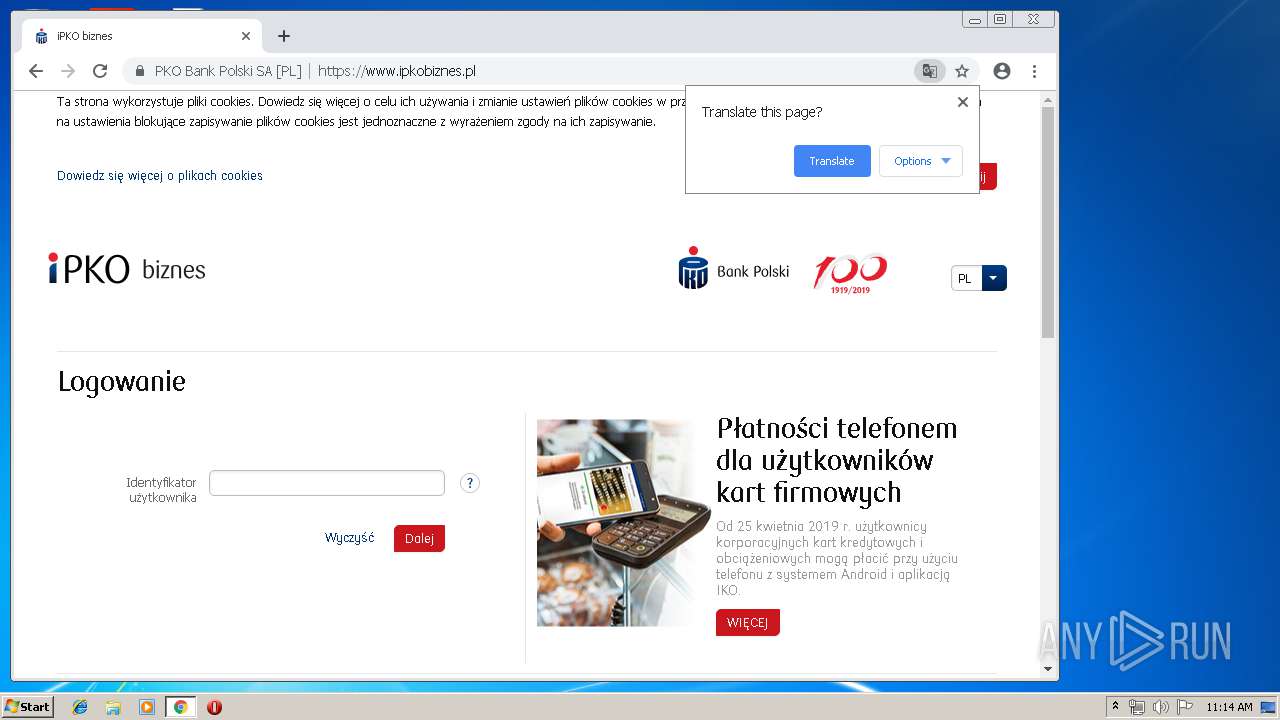
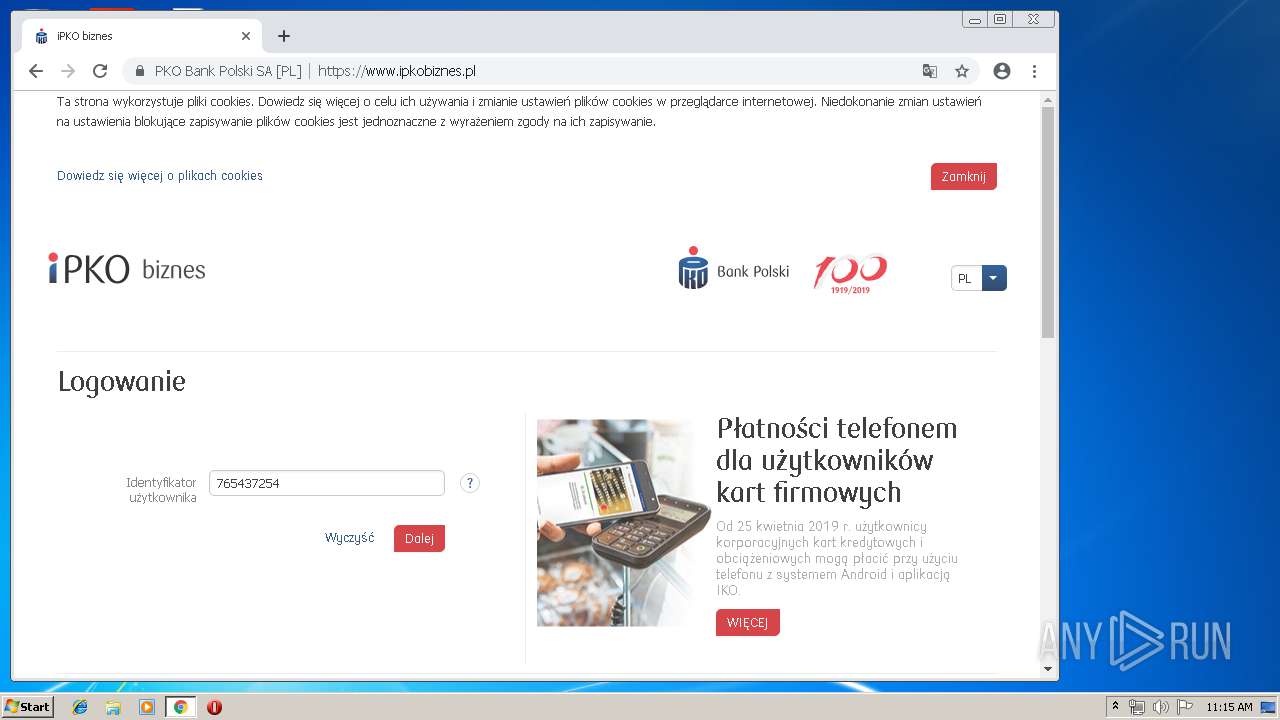
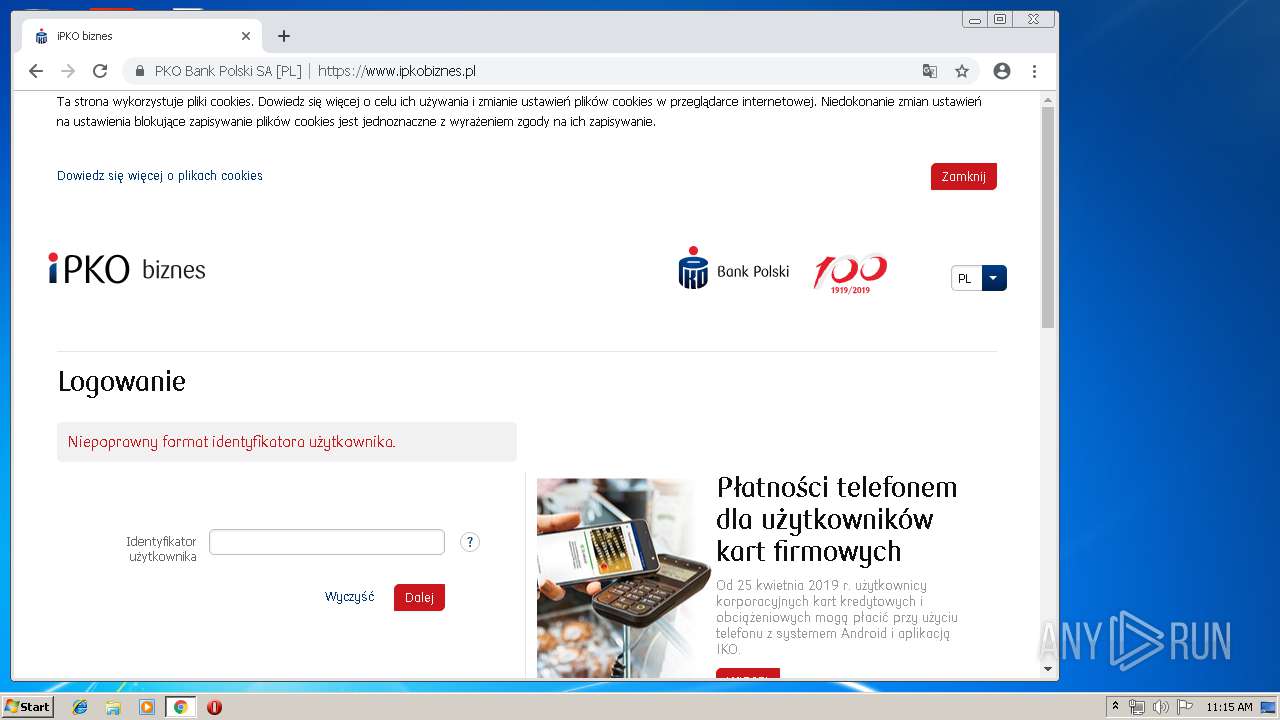
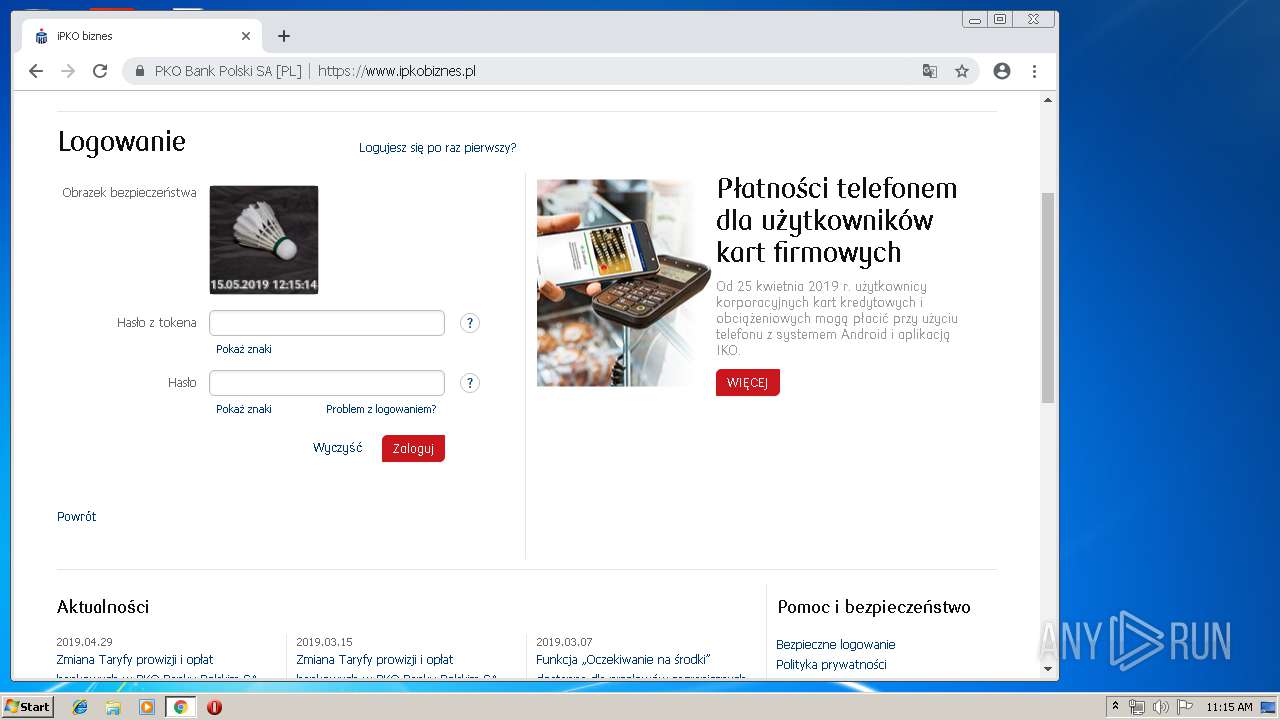
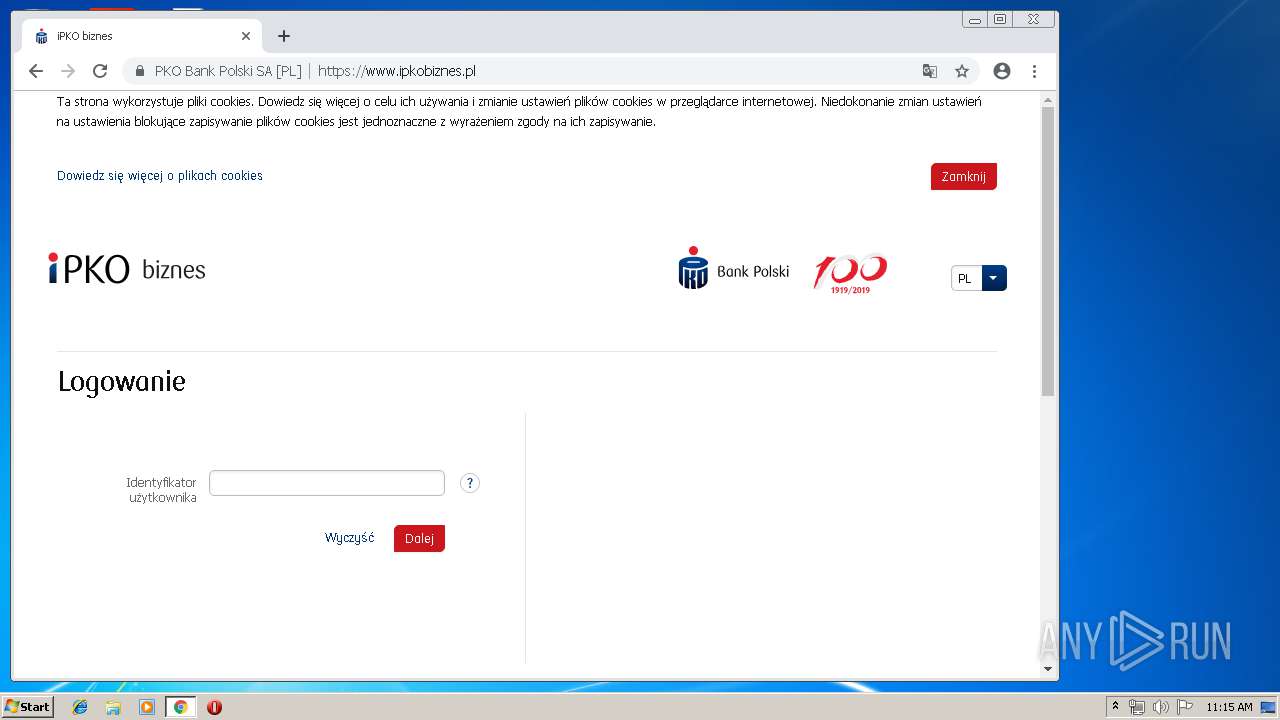
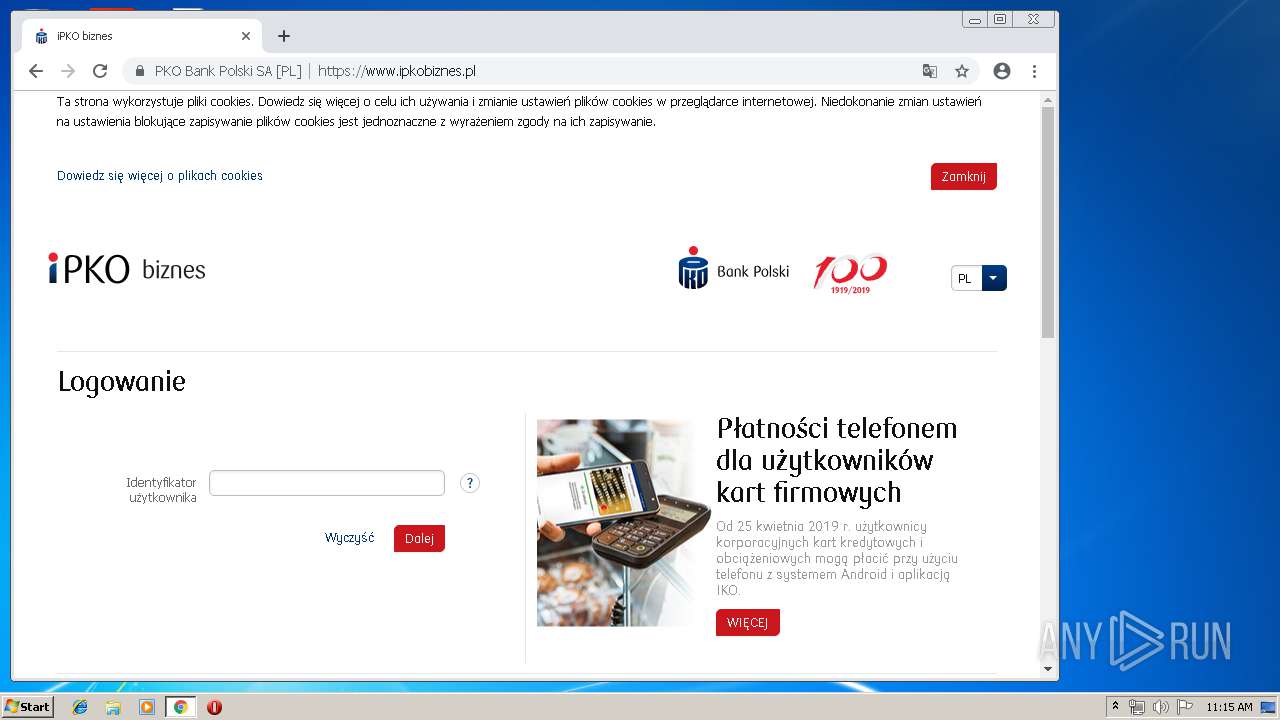
Modifies files in Chrome extension folder
- chrome.exe (PID: 4016)
INFO
Application launched itself
- chrome.exe (PID: 4016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ 4.x (60.1) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (13.9) |
| .exe | | | Win64 Executable (generic) (12.3) |
| .scr | | | Windows screen saver (5.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:05:15 07:24:18+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 7168 |
| InitializedDataSize: | 106496 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x28c8 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.2.7601.17514 |
| ProductVersionNumber: | 7.2.7601.17514 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Connection Manager Profile ikstaller |
| FileVersion: | 7.02.7601.17514 (win7sp1_rtm.101119-1850) |
| InternalName: | CMSTP |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFileName: | CMSTP.EXE |
| ProductName: | Microsoft(R) Connection Manager |
| ProductVersion: | 7.02.7601.17514 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-May-2018 05:24:18 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Connection Manager Profile ikstaller |
| FileVersion: | 7.02.7601.17514 (win7sp1_rtm.101119-1850) |
| InternalName: | CMSTP |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | CMSTP.EXE |
| ProductName: | Microsoft(R) Connection Manager |
| ProductVersion: | 7.02.7601.17514 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 15-May-2018 05:24:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00001A86 | 0x00001C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.60053 |
.rdata | 0x00003000 | 0x00004ECC | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02614 |
.data | 0x00008000 | 0x00014198 | 0x00014200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.45196 |
.rsrc | 0x0001D000 | 0x00000DA0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.64839 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.56398 | 944 | UNKNOWN | English - United States | RT_VERSION |
107 | 1.91924 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
5000 | 5.04236 | 351 | UNKNOWN | English - United States | REGINST |
Imports
ADVAPI32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
MSVCRT.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
62
Monitored processes
31
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16461707555057733063,5232832243341029434,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=858476253186553942 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=858476253186553942 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=5304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16461707555057733063,5232832243341029434,131072 --enable-features=PasswordImport --service-pipe-token=11416431660283968902 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11416431660283968902 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=960,16461707555057733063,5232832243341029434,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3631071335146329607 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3631071335146329607 --renderer-client-id=21 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2844 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 896 | --64f45753 | C:\Users\admin\AppData\Local\Temp\qy8mtf.exe | qy8mtf.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Connection Manager Profile ikstaller Exit code: 0 Version: 7.02.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3908 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,16461707555057733063,5232832243341029434,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1519617913349006823 --mojo-platform-channel-handle=4676 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1848 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,16461707555057733063,5232832243341029434,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2645714849781111557 --mojo-platform-channel-handle=4064 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,16461707555057733063,5232832243341029434,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1688778967715744566 --mojo-platform-channel-handle=4308 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=960,16461707555057733063,5232832243341029434,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=17210047858877545214 --mojo-platform-channel-handle=4892 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=960,16461707555057733063,5232832243341029434,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6824080965577875146 --mojo-platform-channel-handle=4824 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
657
Read events
543
Write events
109
Delete events
5
Modification events
| (PID) Process: | (4044) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4044) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4044) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4044) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4044) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4044) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (4044) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4044) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4044) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (4044) soundser.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\soundser_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
1
Suspicious files
172
Text files
254
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\39a152ea-b7f0-4a96-bb5d-17e2c6af356e.tmp | — | |
MD5:— | SHA256:— | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 4016 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
19
TCP/UDP connections
259
DNS requests
160
Threats
28
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
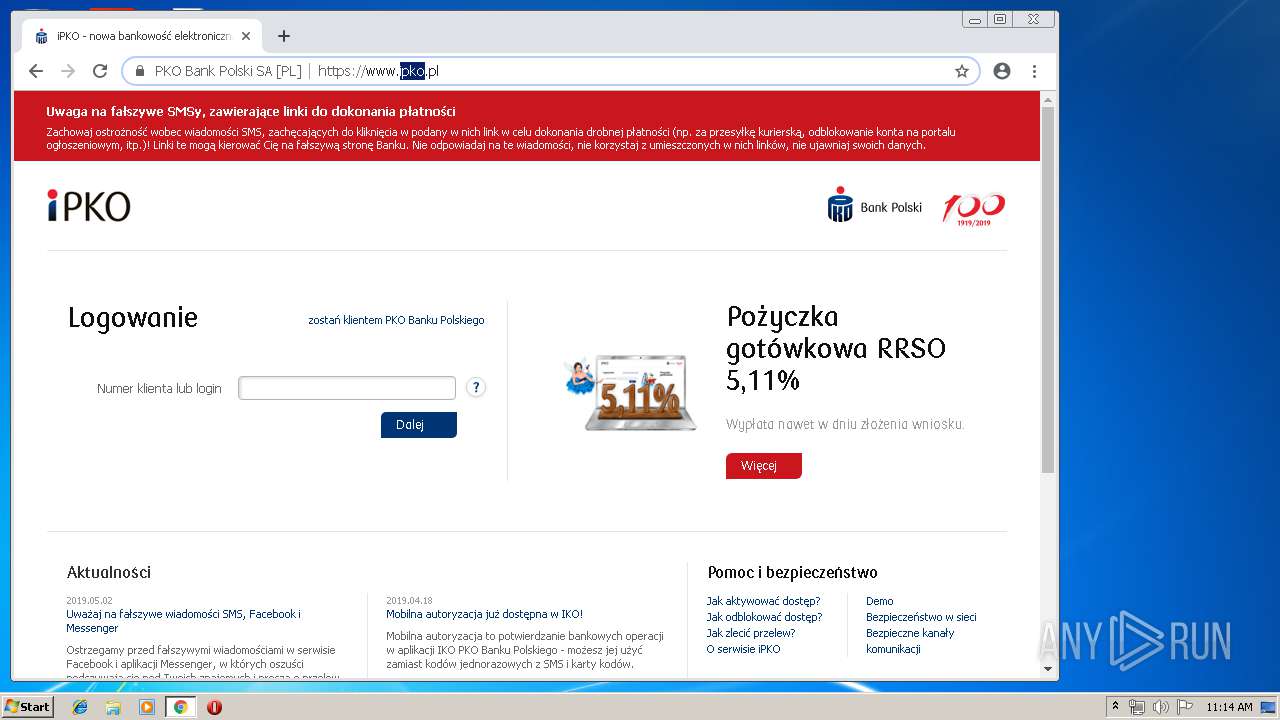
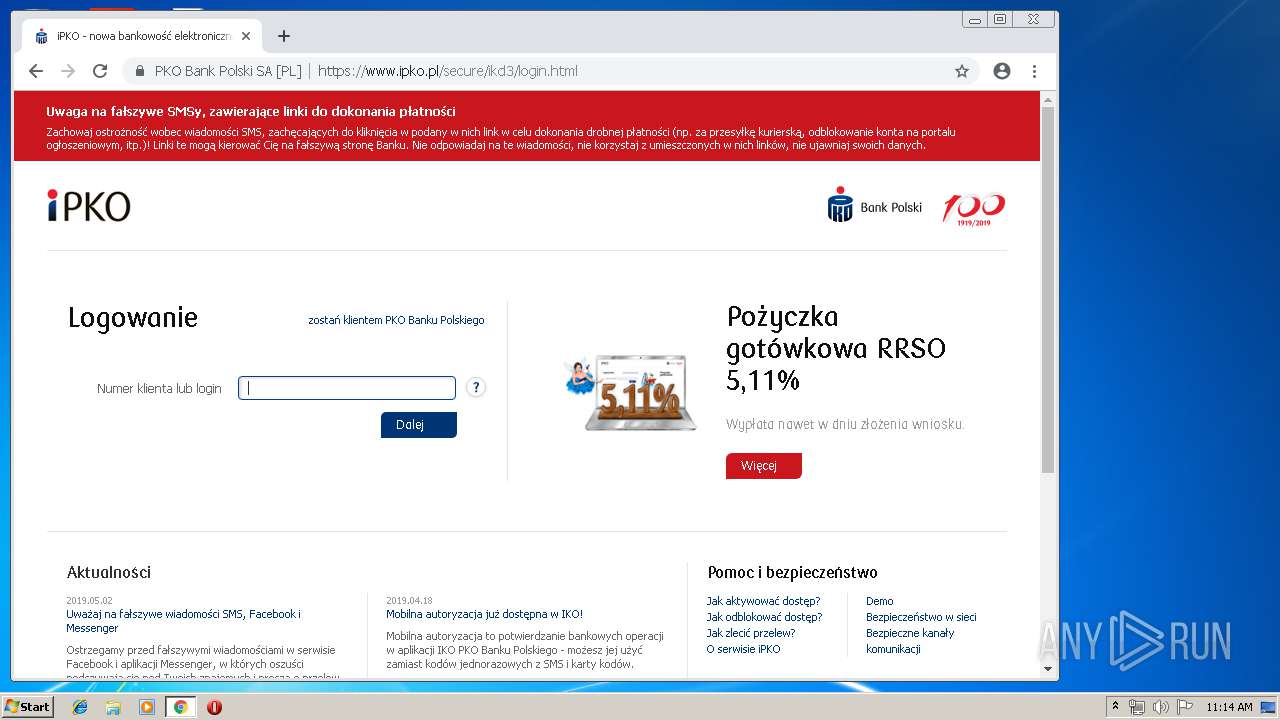
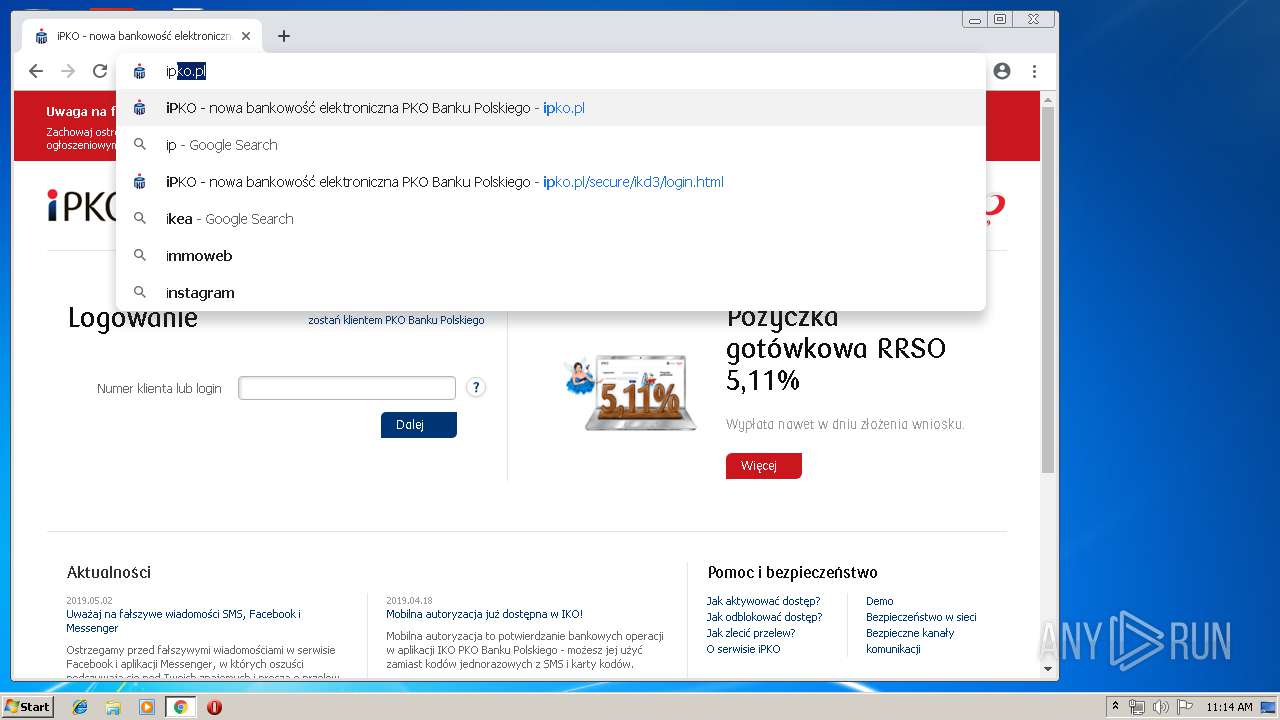
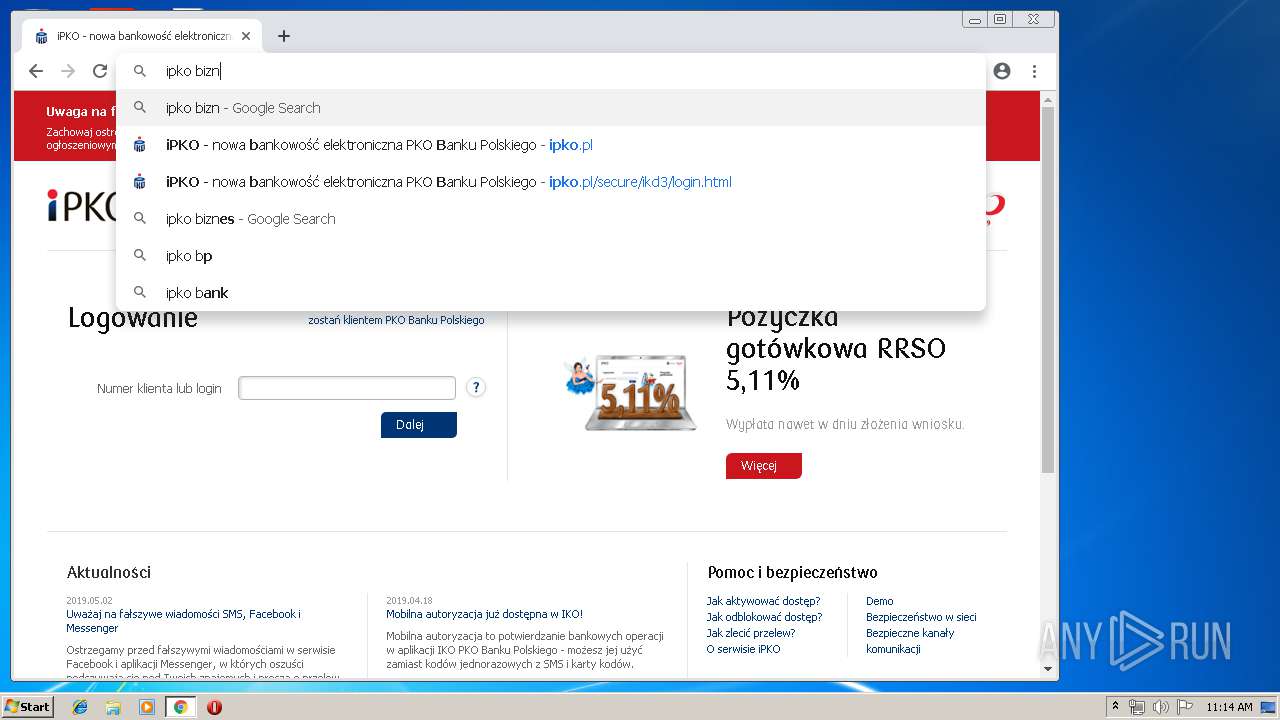
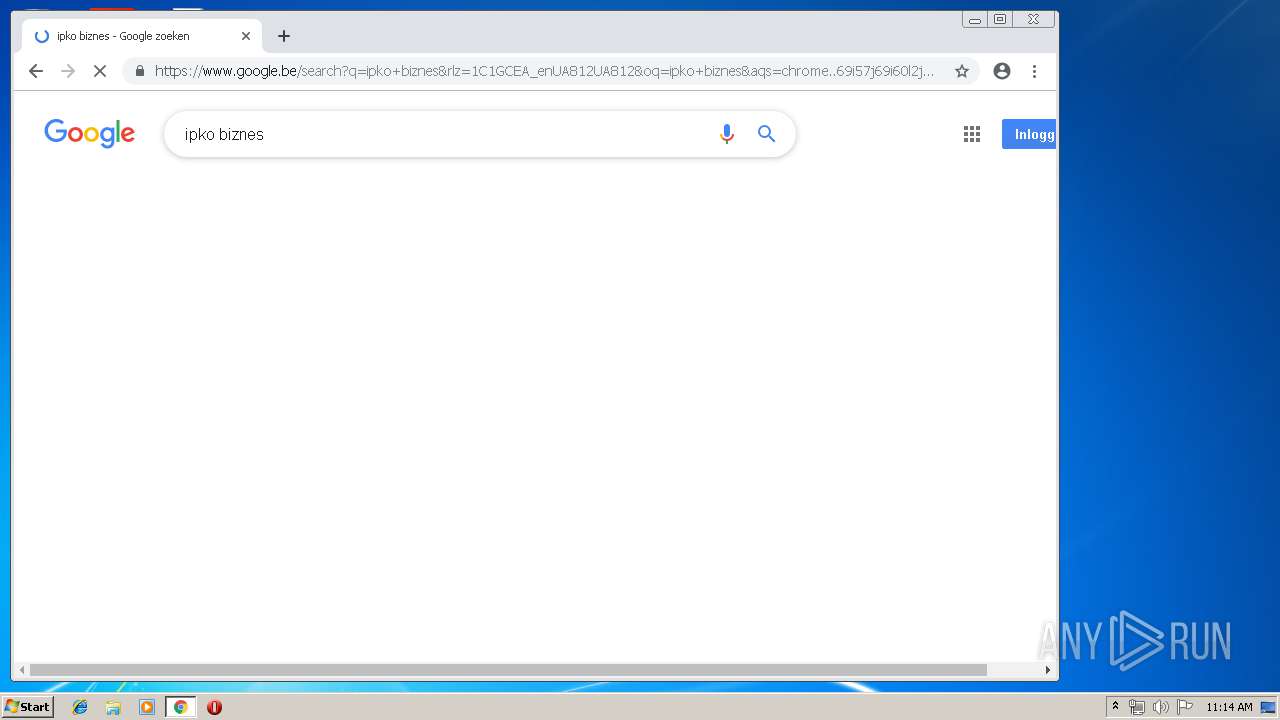
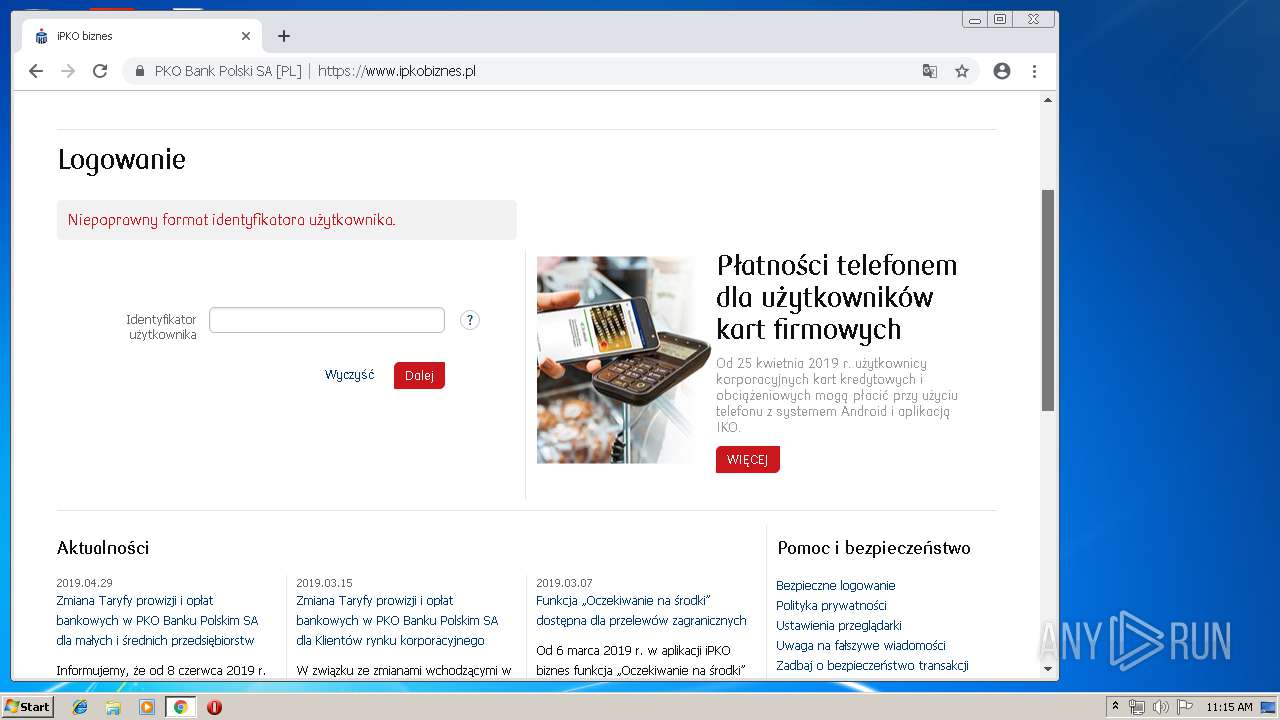
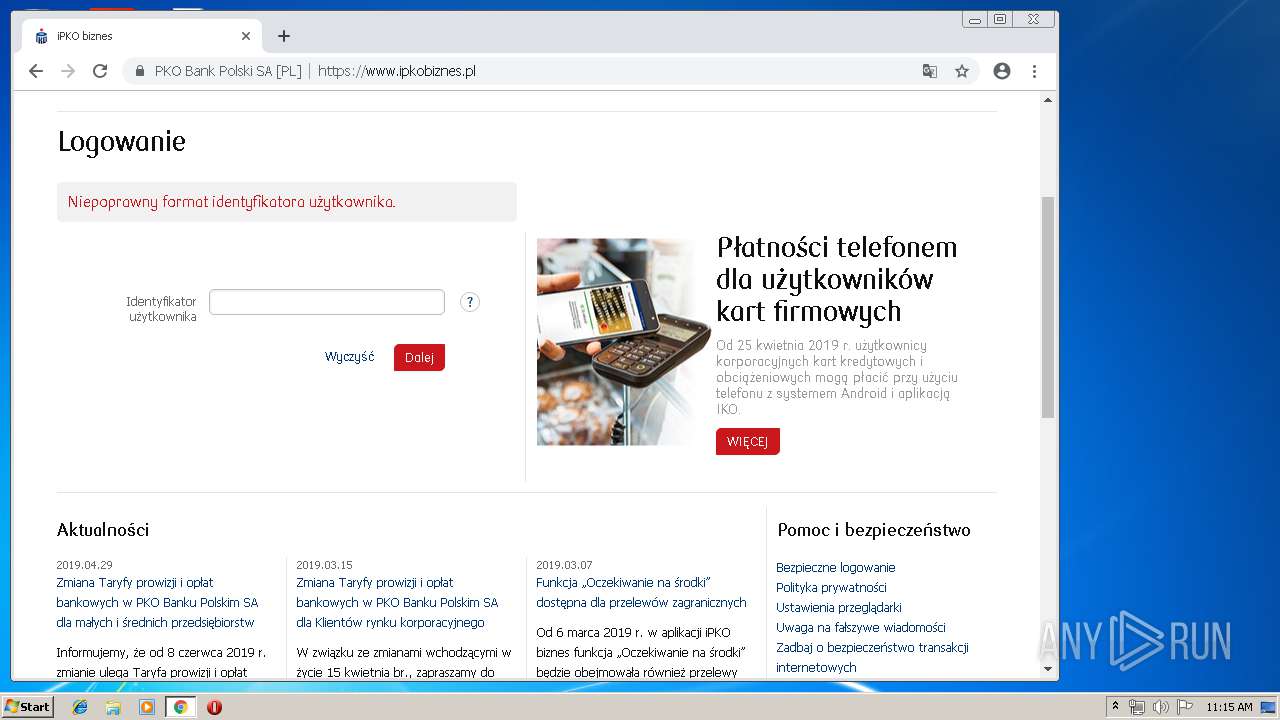
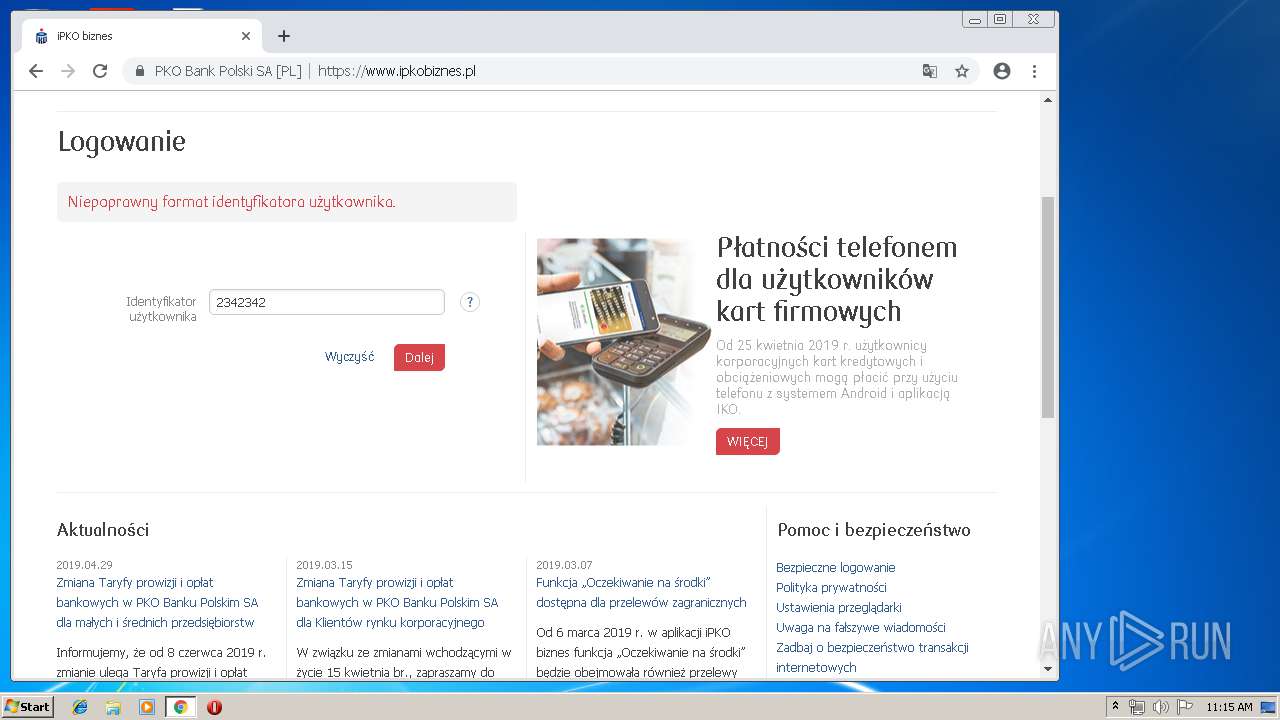
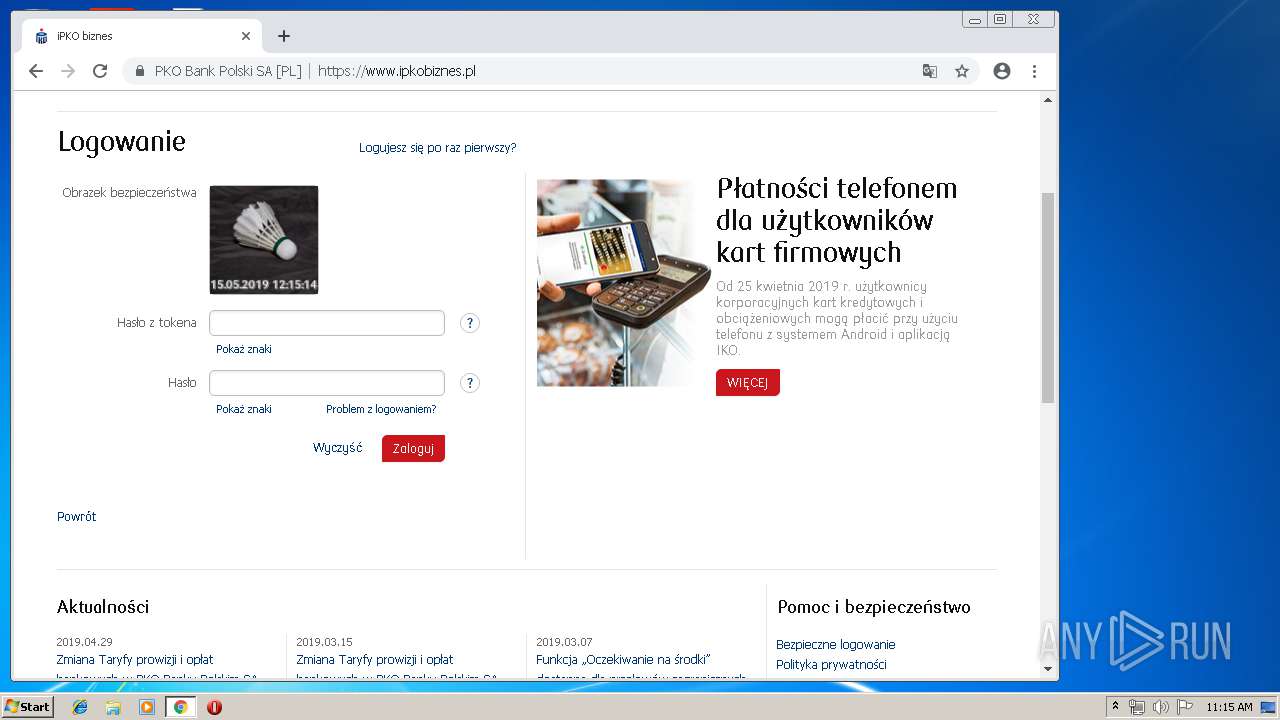
4016 | chrome.exe | GET | 301 | 193.109.225.71:80 | http://ipko.pl/ | PL | — | — | unknown |
4044 | soundser.exe | POST | — | 191.97.116.232:443 | http://191.97.116.232:443/loadan/ | AR | — | — | malicious |
4044 | soundser.exe | POST | — | 186.121.223.131:80 | http://186.121.223.131/child/symbols/ | BO | — | — | malicious |
4044 | soundser.exe | POST | 200 | 64.87.26.16:443 | http://64.87.26.16:443/walk/ | US | binary | 1.38 Mb | malicious |
4016 | chrome.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTYOkzrrCGQj08njZXbUQQpkoUmuQQUCHbNywf%2FJPbFze27kLzihDdGdfcCEQDFotP2600ZPBepCqOKKW5U | US | der | 1.66 Kb | whitelisted |
4016 | chrome.exe | GET | 200 | 151.139.236.246:80 | http://evcasha2.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRtQZmYkHWb1IbrrLPeqnPFYUM1OwQUufIi0SCS9aXhE3Wu4Hb4yfGtc48CECaXsfJE2hO7XUXuO9E%2BJhM%3D | US | der | 1.60 Kb | whitelisted |
4016 | chrome.exe | GET | 200 | 209.85.230.216:80 | http://r2---sn-aigs6n7r.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=194.187.251.125&mm=28&mn=sn-aigs6n7r&ms=nvh&mt=1557915163&mv=m&pl=24&shardbypass=yes | US | crx | 842 Kb | whitelisted |
4016 | chrome.exe | GET | 200 | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
4044 | soundser.exe | POST | 200 | 61.92.159.208:8080 | http://61.92.159.208:8080/loadan/site/ringin/ | HK | binary | 106 Kb | malicious |
4044 | soundser.exe | GET | 200 | 61.92.159.208:8080 | http://61.92.159.208:8080/whoami.php | HK | text | 15 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4044 | soundser.exe | 187.242.204.142:80 | — | Mega Cable, S.A. de C.V. | MX | malicious |
4044 | soundser.exe | 186.121.223.131:80 | — | AXS Bolivia S. A. | BO | malicious |
4044 | soundser.exe | 217.92.171.167:53 | — | Deutsche Telekom AG | DE | malicious |
4044 | soundser.exe | 191.97.116.232:443 | — | FEROGLIO JULIA ELENA | AR | malicious |
4016 | chrome.exe | 172.217.18.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 172.217.18.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 172.217.22.99:443 | www.gstatic.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 172.217.23.174:443 | apis.google.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 172.217.16.132:443 | www.google.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 216.58.206.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
dns.msftncsi.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4044 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4044 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4044 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4044 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
4044 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4044 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
4044 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4044 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
4044 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
4044 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
16 ETPRO signatures available at the full report