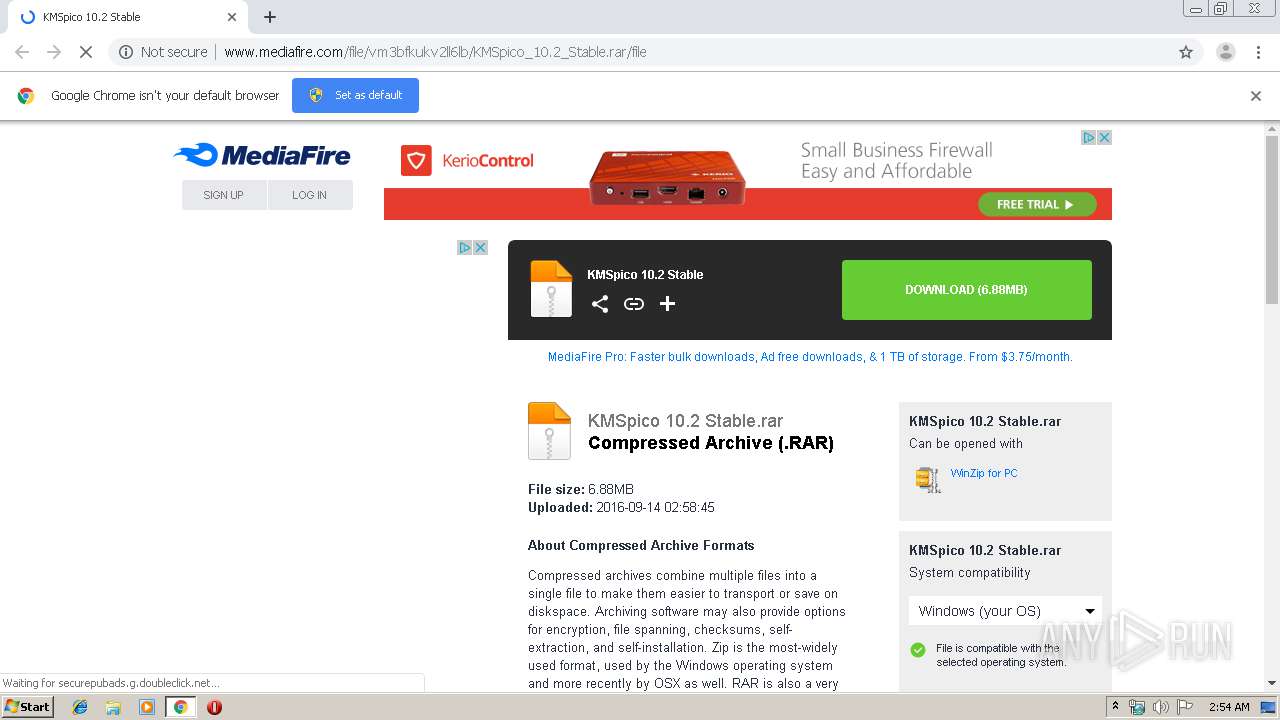
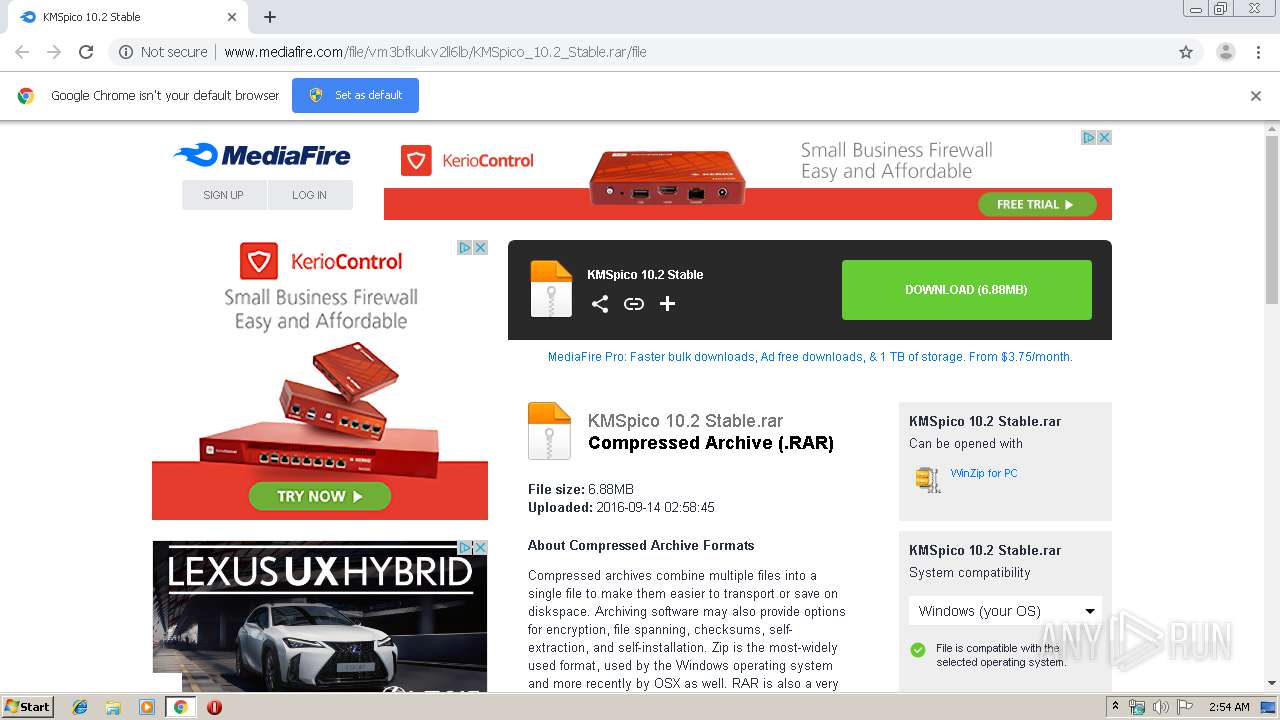
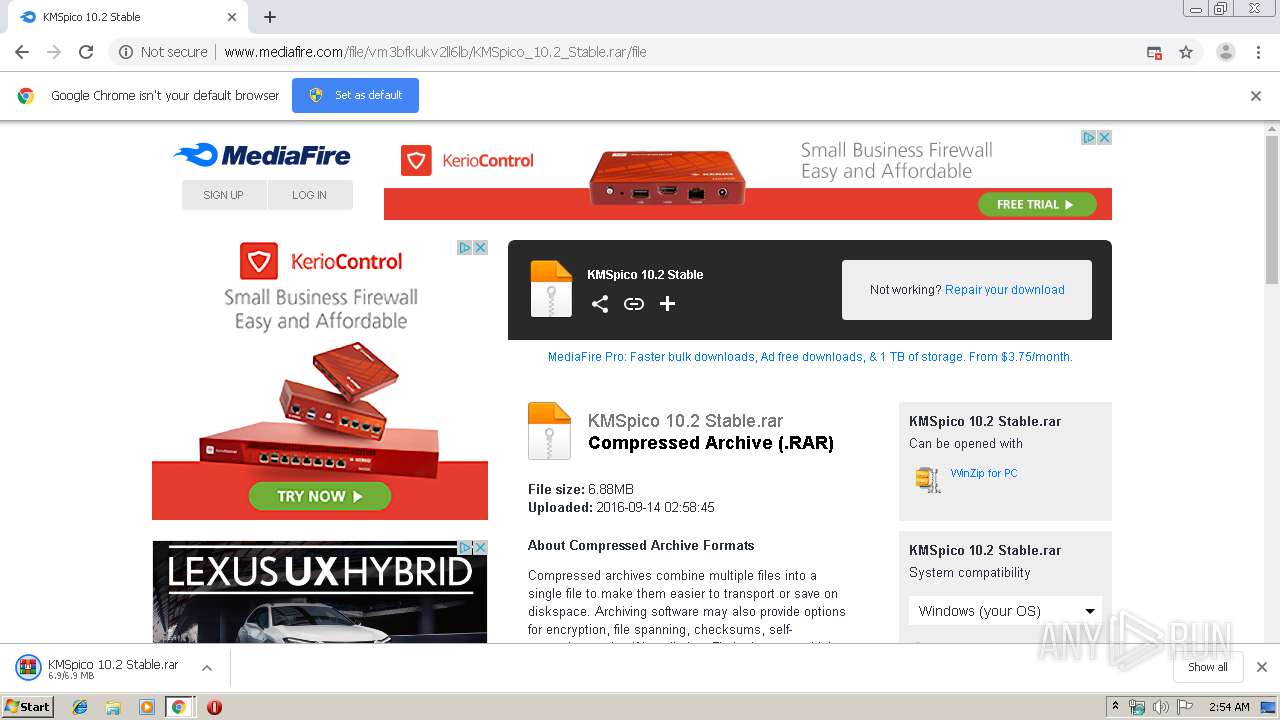
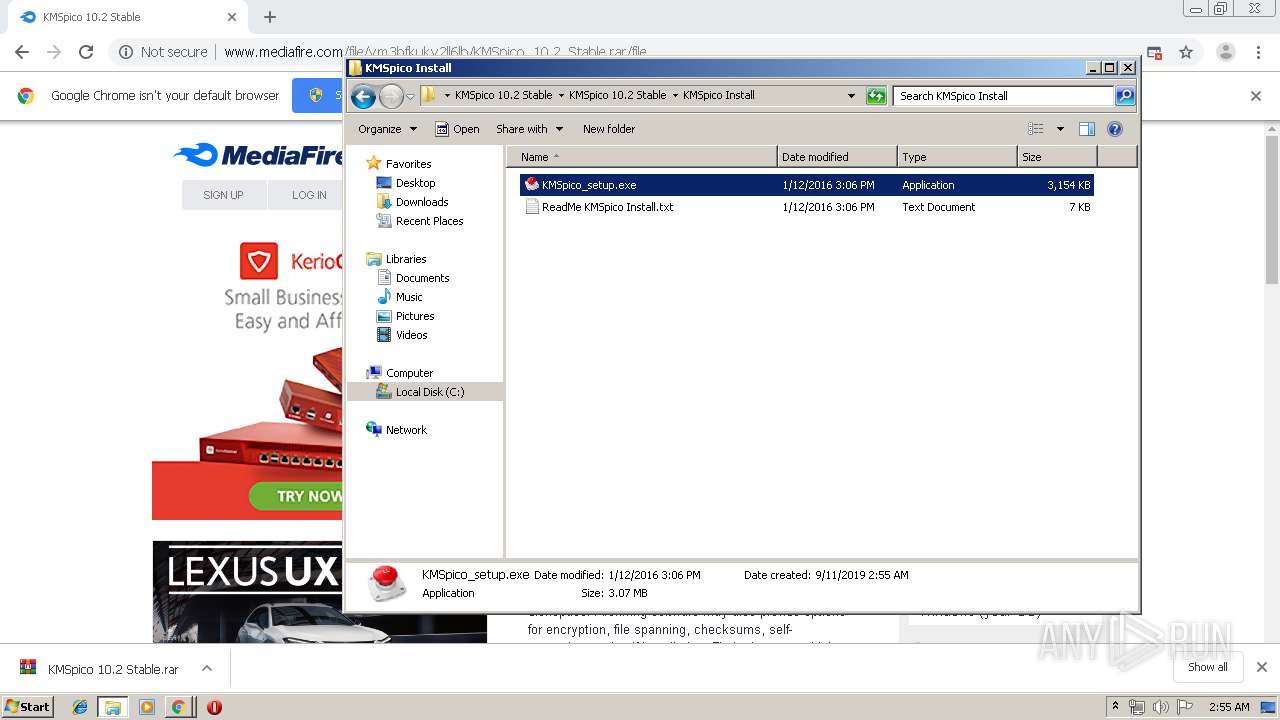
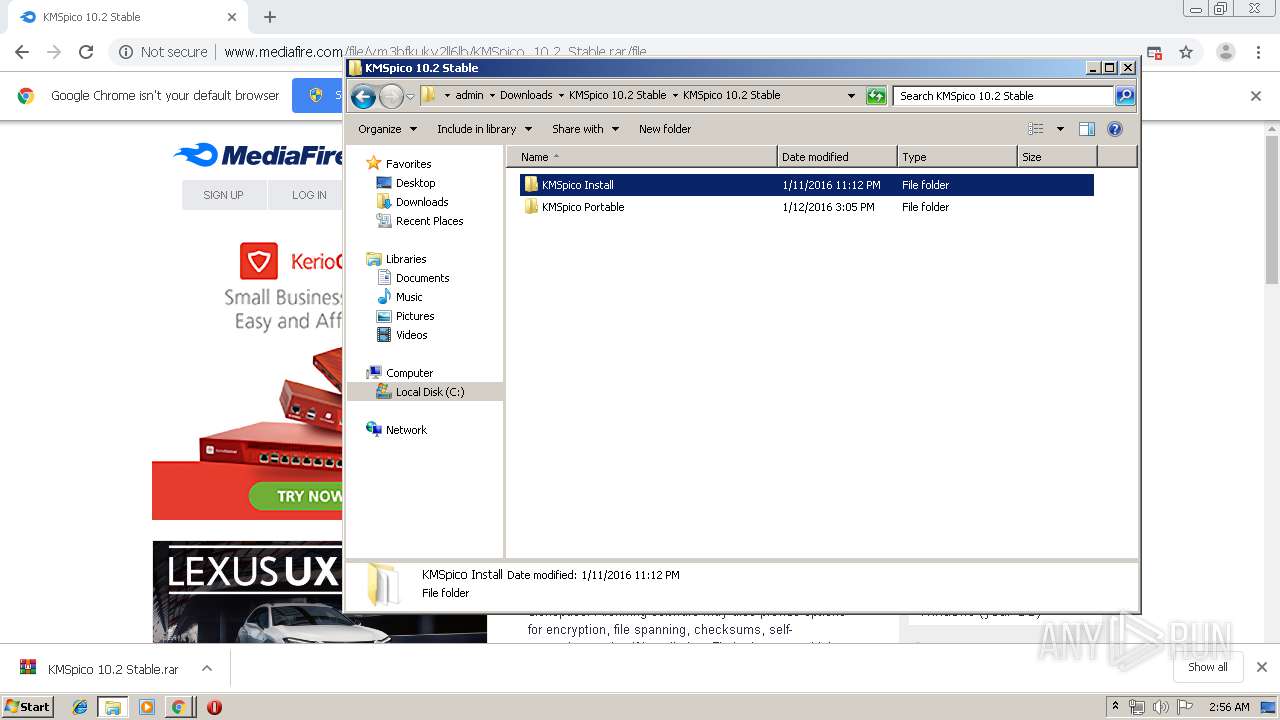
| URL: | http://www.mediafire.com/file/vm3bfkukv2ll6lb/KMSpico_10.2_Stable.rar/file |
| Full analysis: | https://app.any.run/tasks/7722635e-fd4c-4e63-82eb-6f5f3ff3ad6e |
| Verdict: | Malicious activity |
| Analysis date: | September 11, 2019, 01:54:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 865139D2403D1C7A107FE26E1D40EC62 |
| SHA1: | 81316FBED8399C077C630E3870682C0113BC126D |
| SHA256: | 6FFD0432F4275411ED1E046BBC50B434CB673D7CFEE2EB78DAC83CF1F54D202D |
| SSDEEP: | 3:N1KJS4w3eGUo/HyzJ1of4USIIA:Cc4w3eGbSzaZAA |
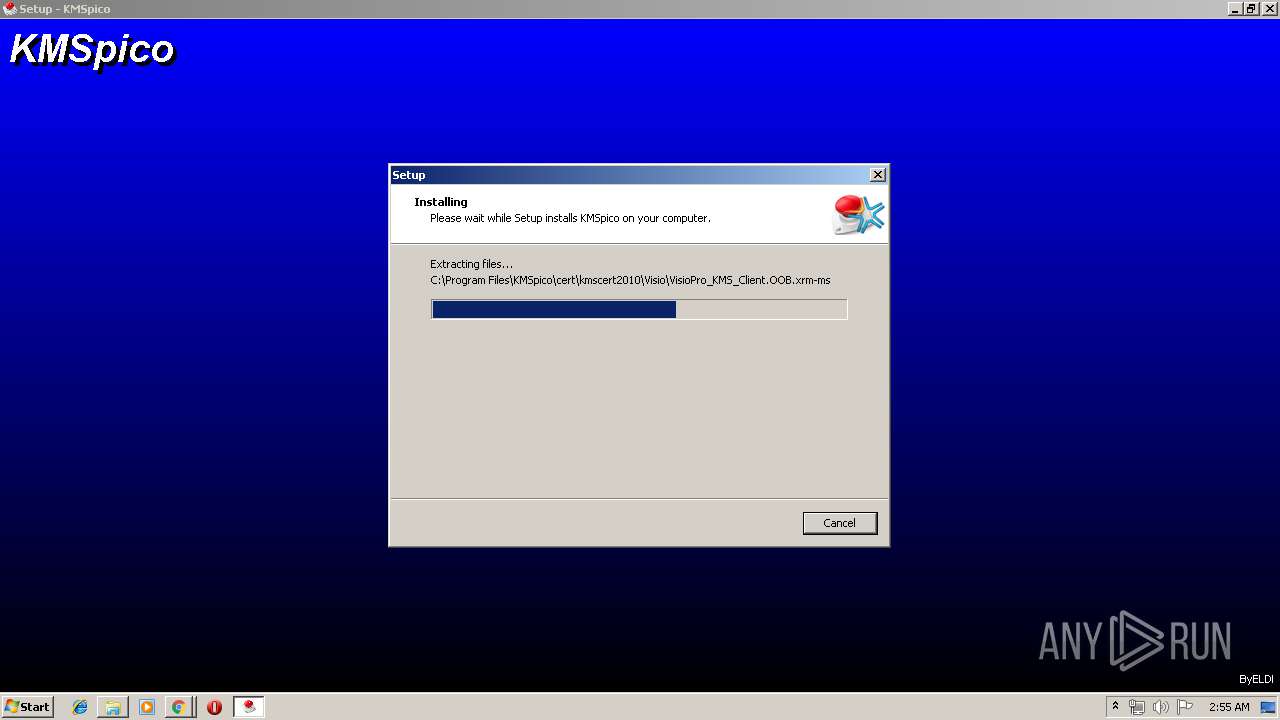
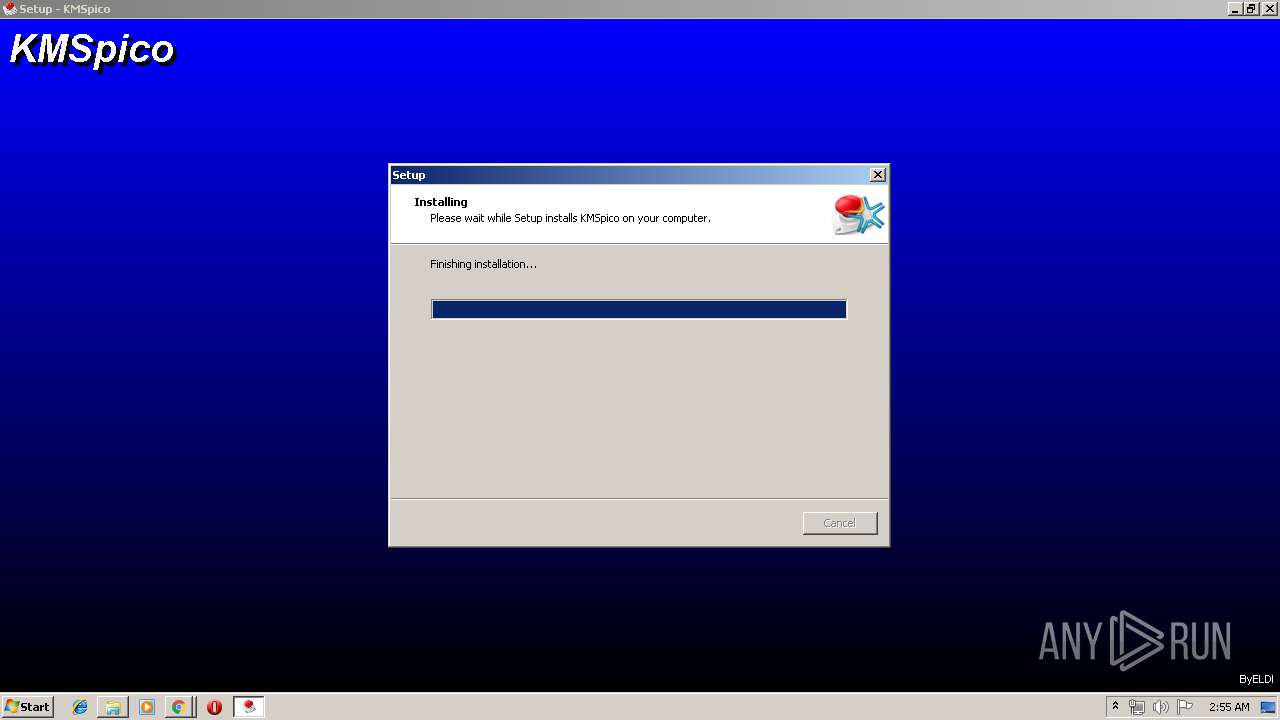
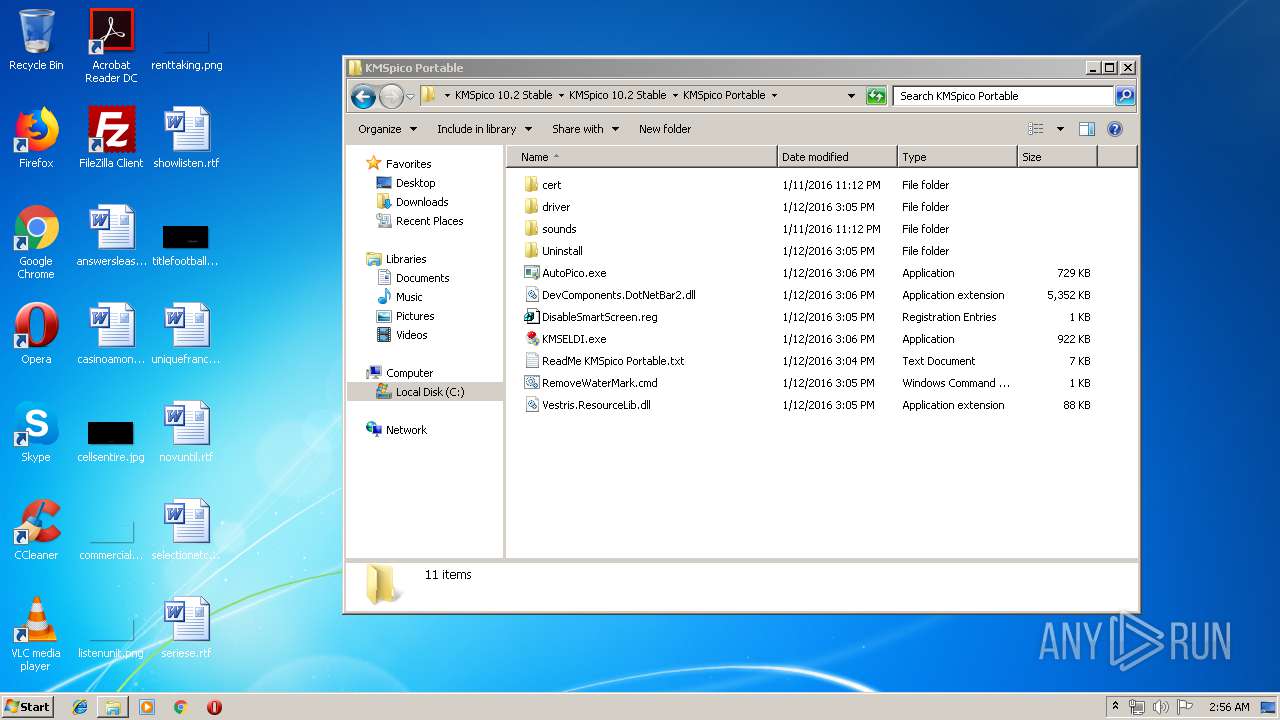
MALICIOUS
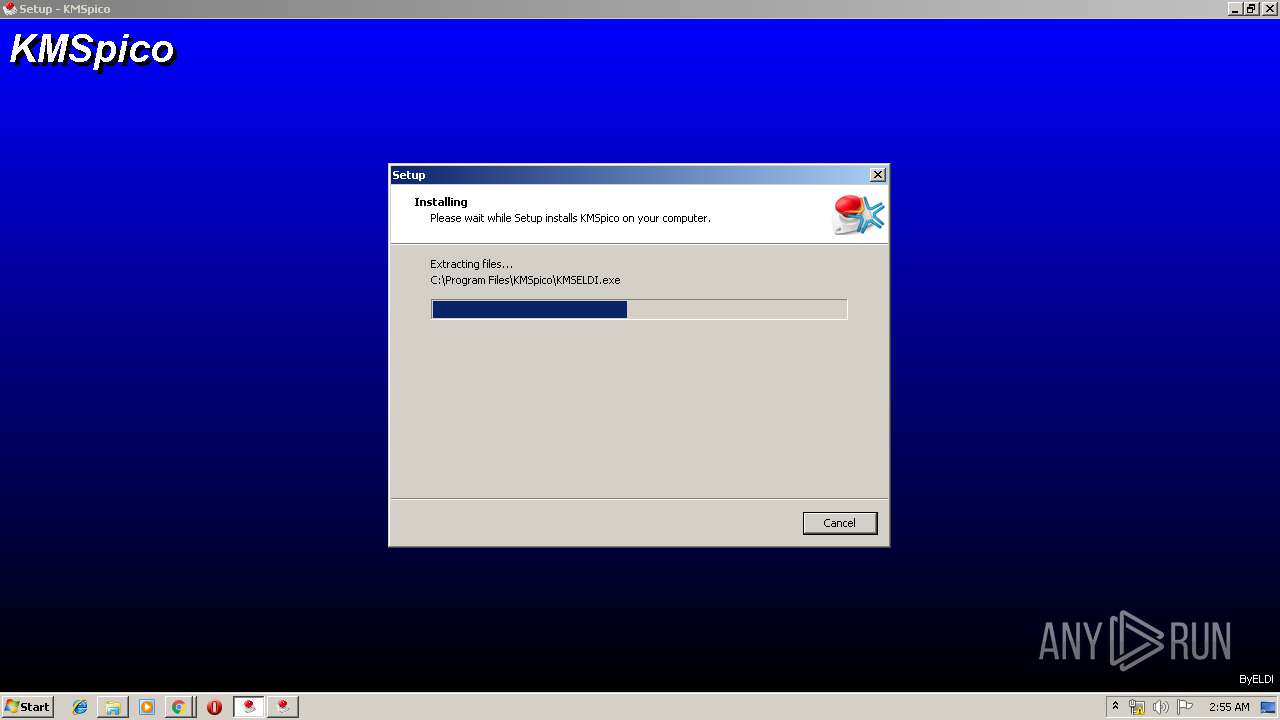
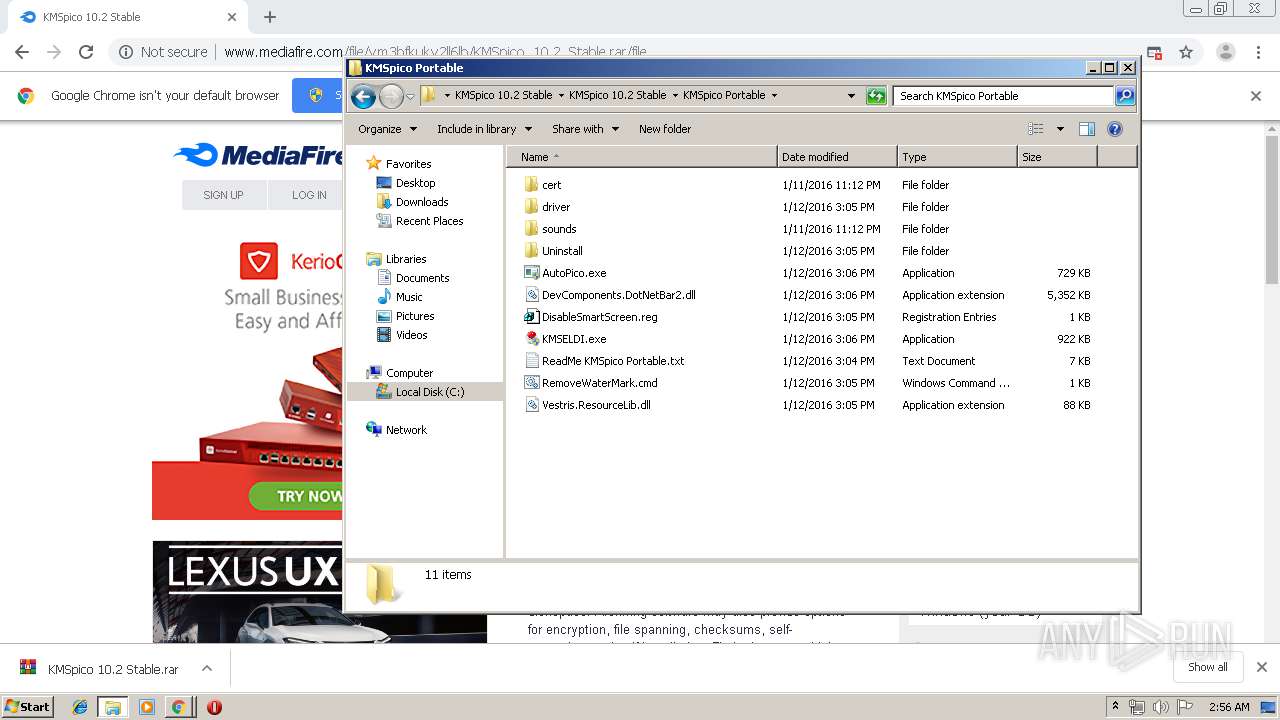
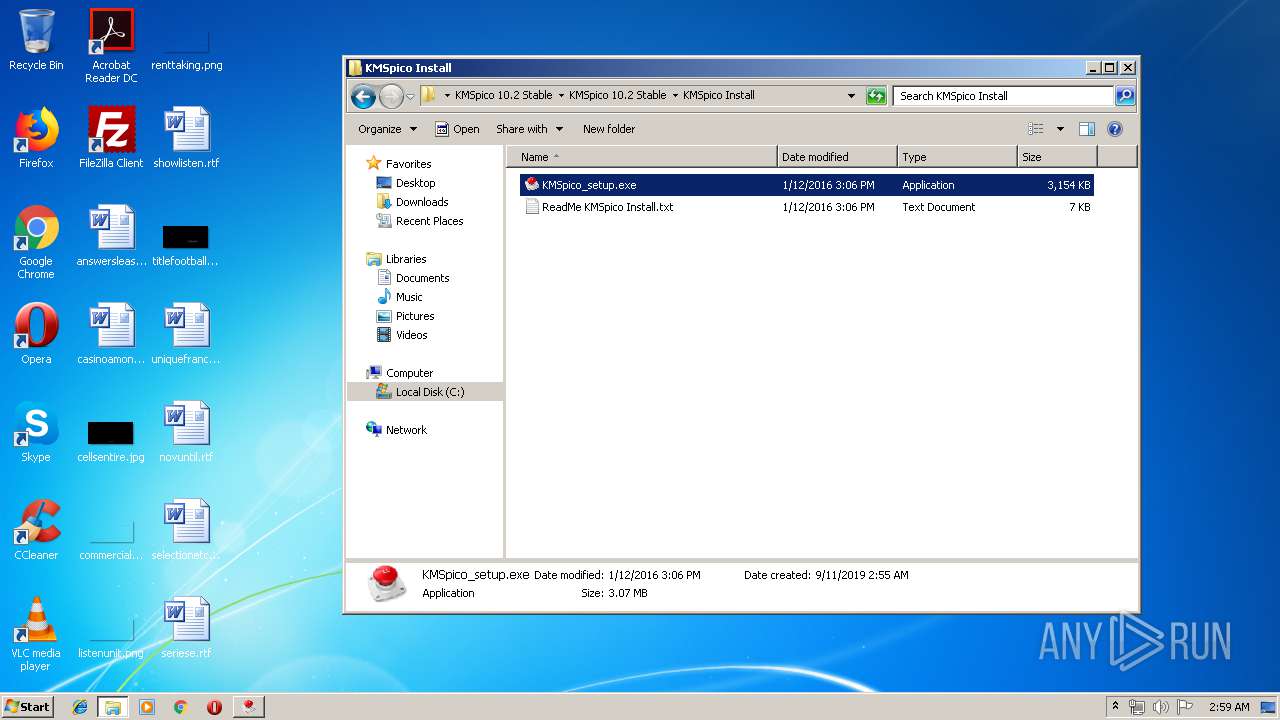
Application was dropped or rewritten from another process
- KMSpico_setup.exe (PID: 3916)
- KMSpico_setup.exe (PID: 3068)
- KMSpico_setup.exe (PID: 3960)
- KMSpico_setup.exe (PID: 2648)
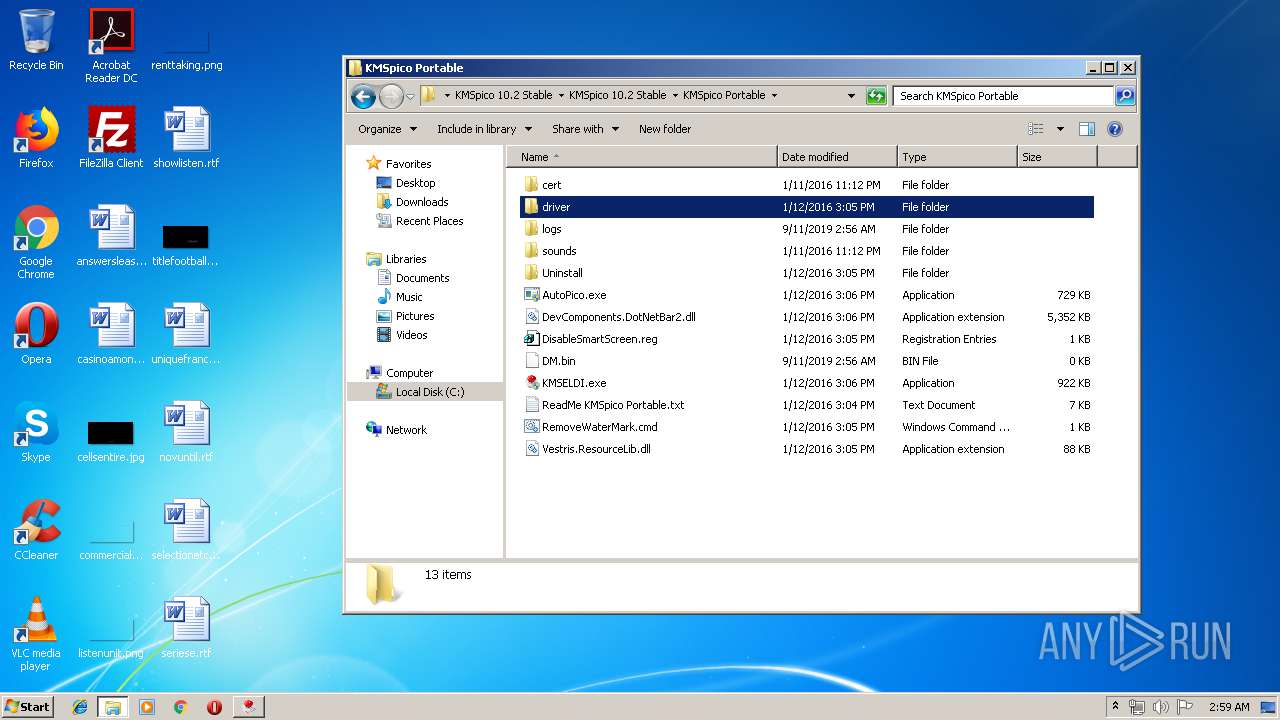
- KMSELDI.exe (PID: 4004)
- UninsHs.exe (PID: 2296)
- AutoPico.exe (PID: 3608)
- UninsHs.exe (PID: 3136)
- KMSELDI.exe (PID: 2196)
- AutoPico.exe (PID: 2828)
- KMSELDI.exe (PID: 1680)
- KMSELDI.exe (PID: 3820)
- KMSpico_setup.exe (PID: 3492)
- KMSpico_setup.exe (PID: 2440)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 1732)
- KMSELDI.exe (PID: 4004)
- KMSELDI.exe (PID: 2196)
- KMSELDI.exe (PID: 3820)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 3484)
- schtasks.exe (PID: 2856)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3624)
- cmd.exe (PID: 4040)
SUSPICIOUS
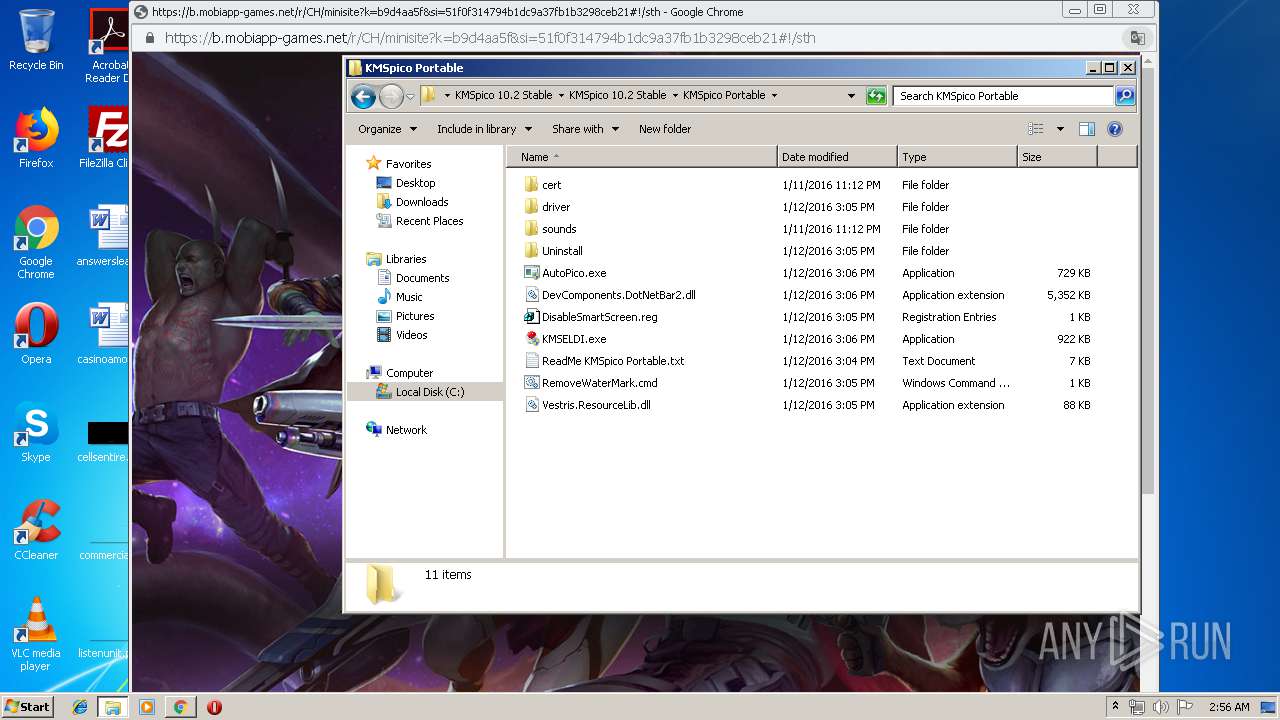
Modifies files in Chrome extension folder
- chrome.exe (PID: 3452)
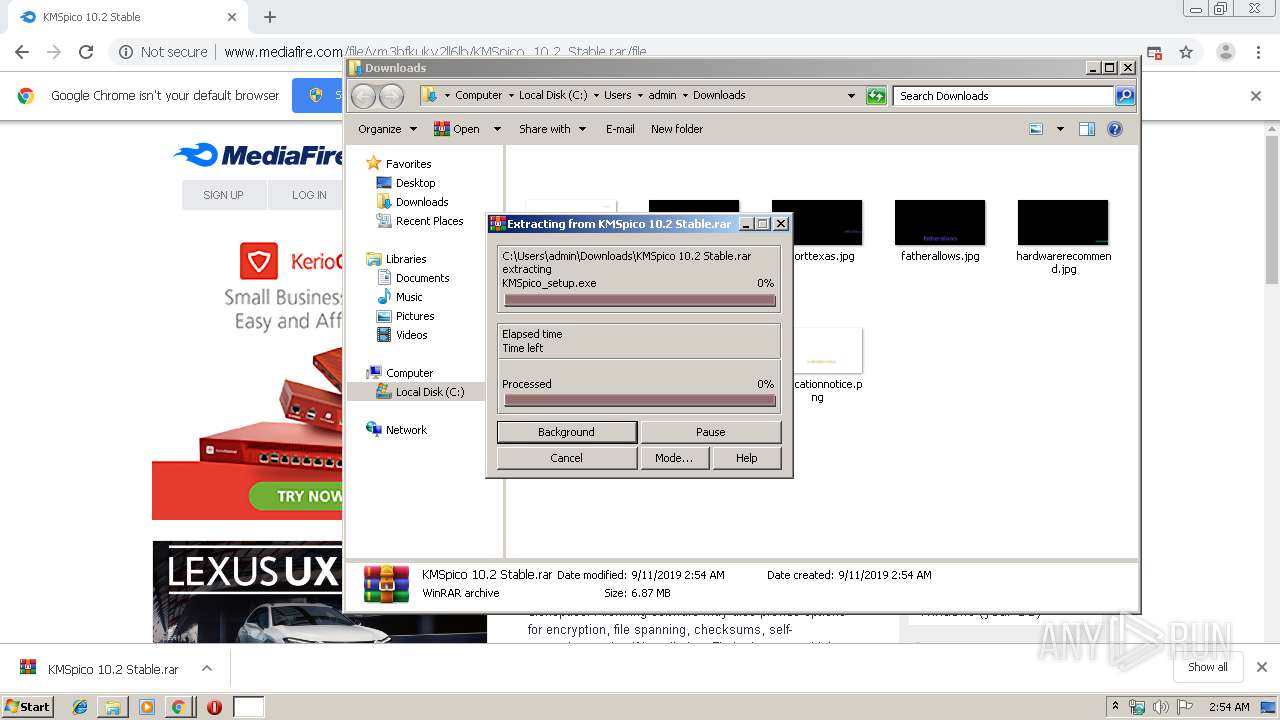
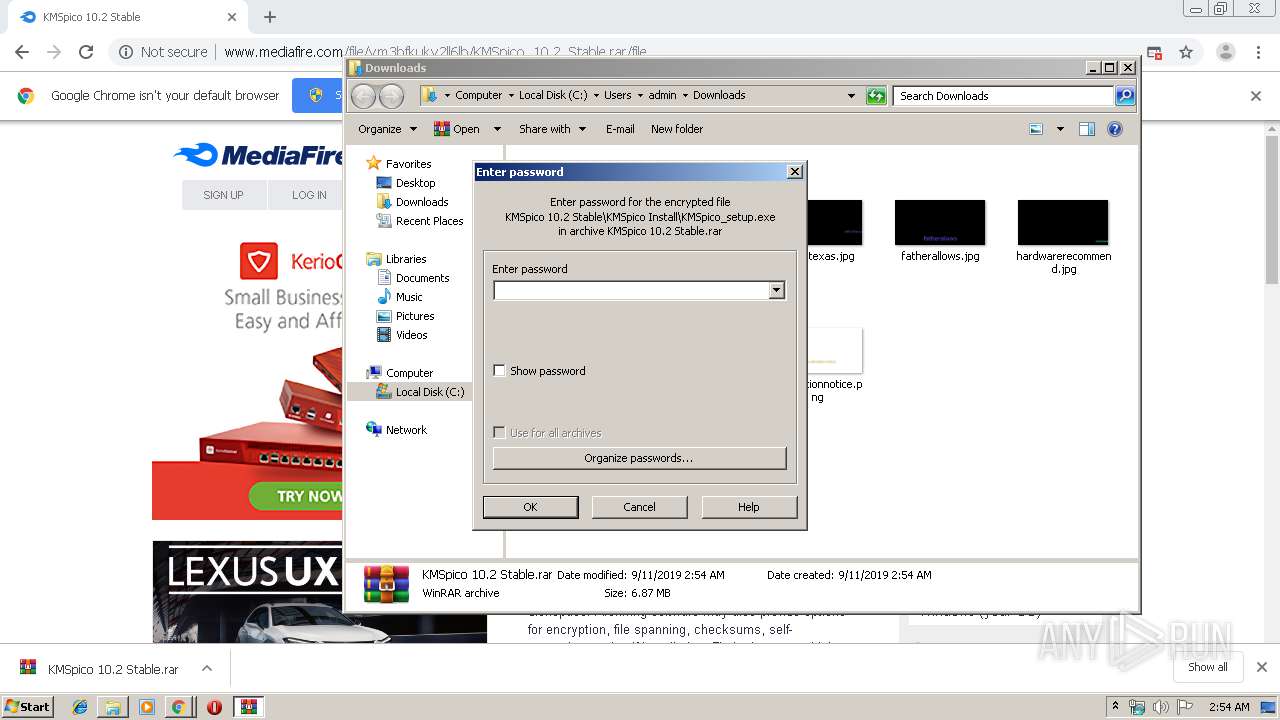
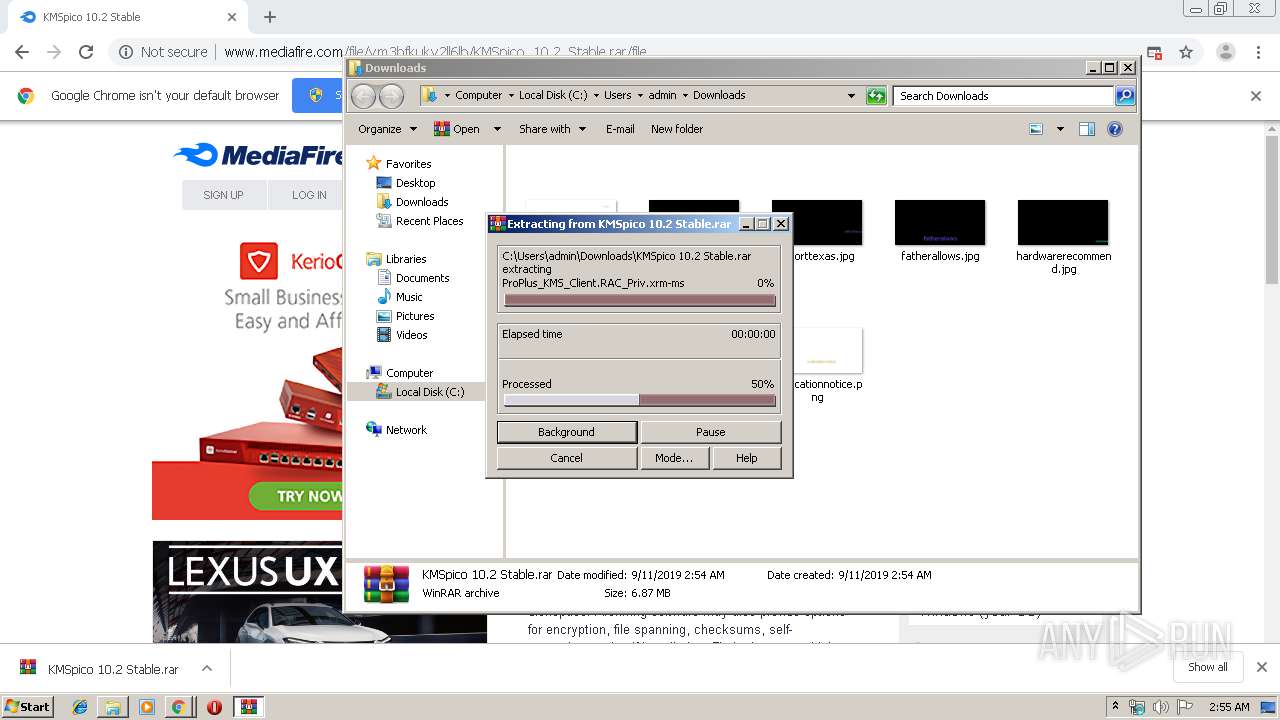
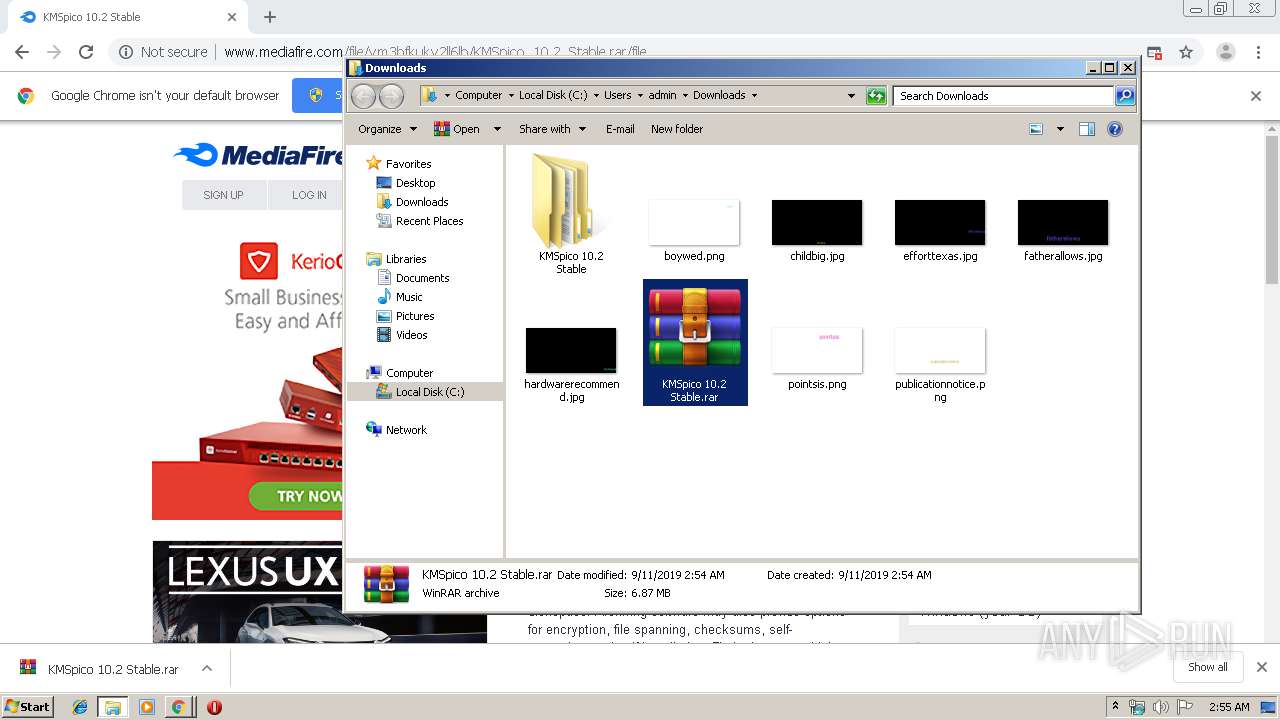
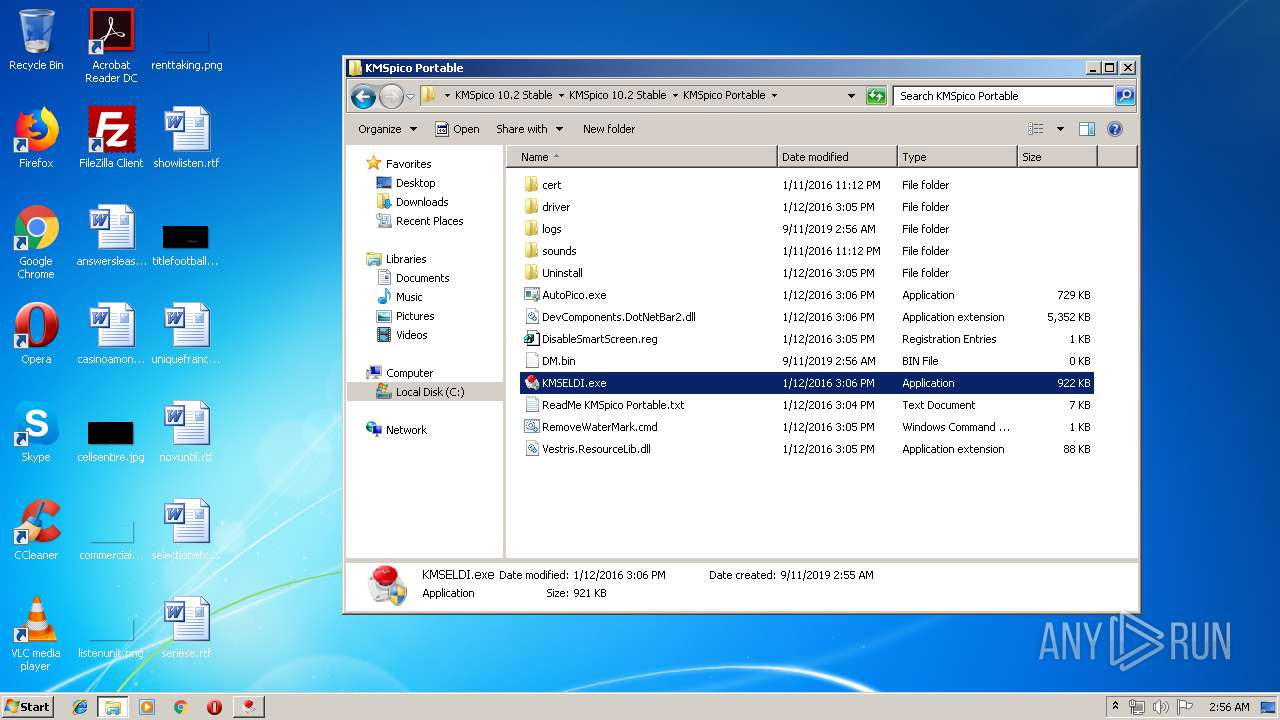
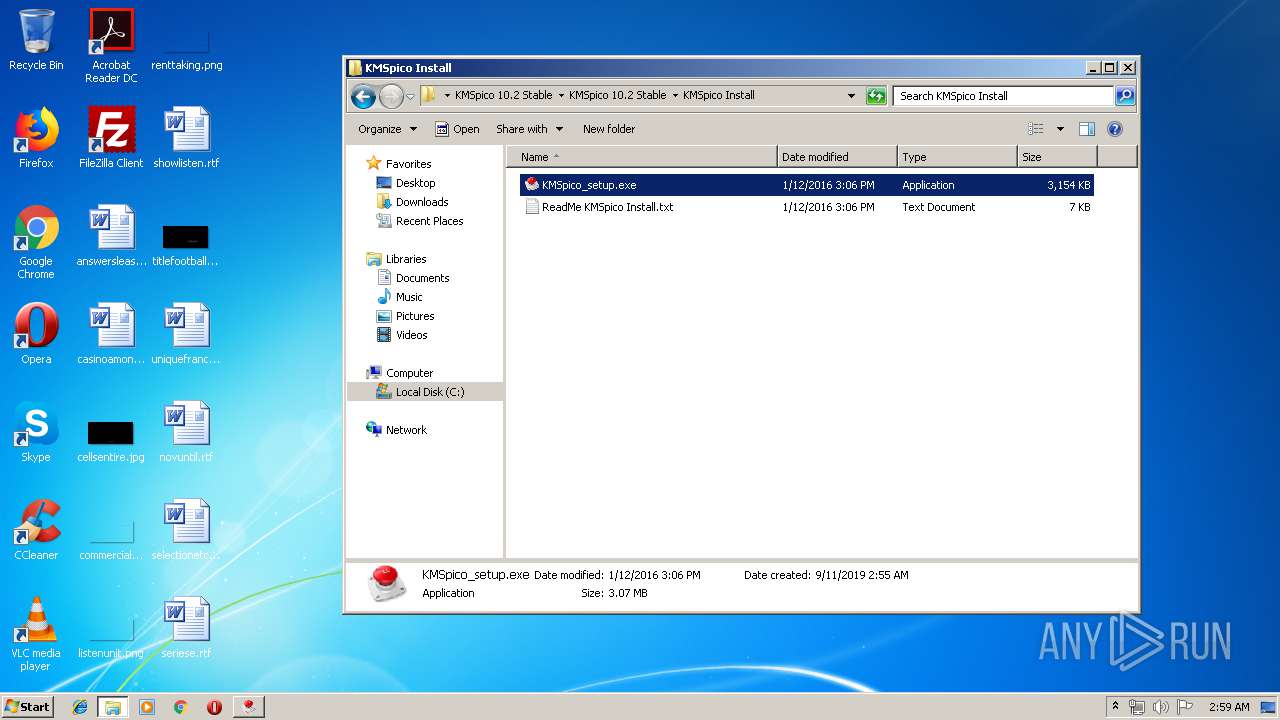
Executable content was dropped or overwritten
- KMSpico_setup.exe (PID: 2648)
- WinRAR.exe (PID: 2604)
- KMSpico_setup.exe (PID: 3960)
- KMSpico_setup.exe (PID: 3068)
- KMSpico_setup.tmp (PID: 2432)
- KMSpico_setup.exe (PID: 3916)
- KMSpico_setup.tmp (PID: 2804)
- KMSpico_setup.exe (PID: 3492)
- KMSpico_setup.exe (PID: 2440)
- KMSpico_setup.tmp (PID: 2304)
Modifies the phishing filter of IE
- KMSpico_setup.tmp (PID: 2432)
- KMSpico_setup.tmp (PID: 2804)
Starts CMD.EXE for commands execution
- KMSpico_setup.tmp (PID: 2432)
- KMSpico_setup.tmp (PID: 2804)
Starts SC.EXE for service management
- cmd.exe (PID: 2752)
- cmd.exe (PID: 1000)
Creates files in the Windows directory
- KMSpico_setup.tmp (PID: 2432)
- KMSpico_setup.tmp (PID: 2804)
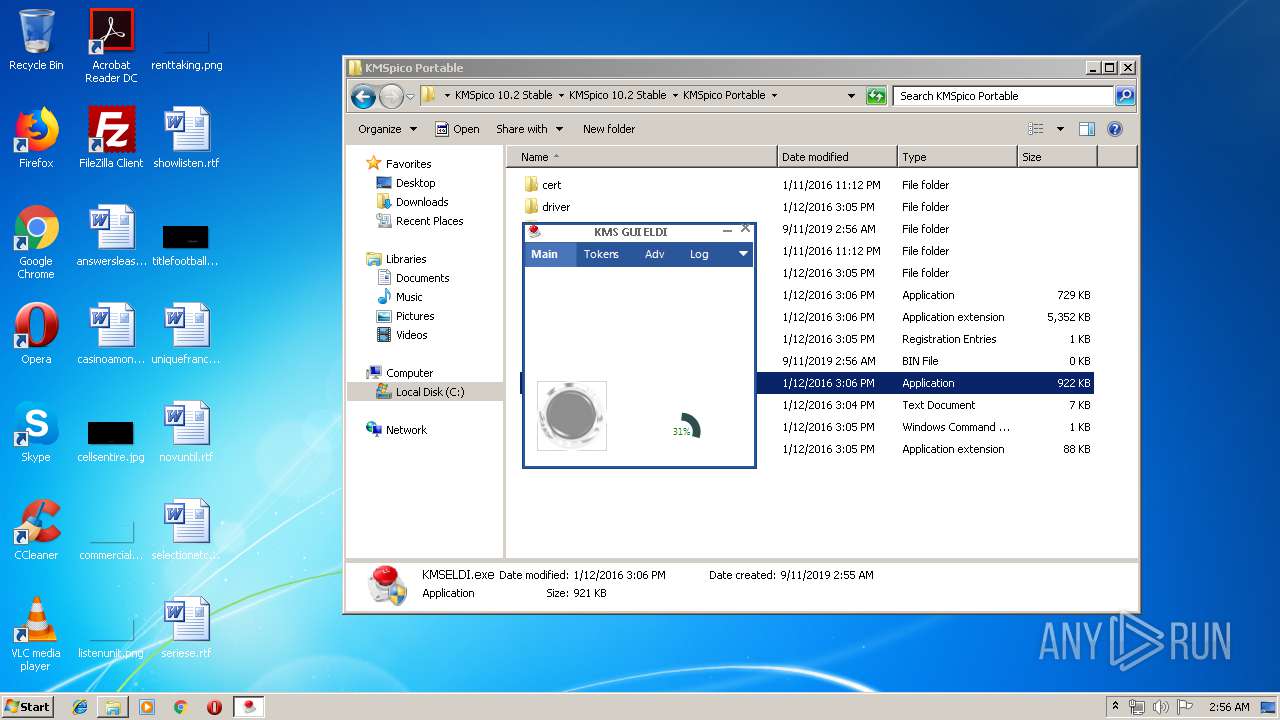
Creates or modifies windows services
- KMSELDI.exe (PID: 4004)
Reads Environment values
- KMSELDI.exe (PID: 4004)
- AutoPico.exe (PID: 3608)
- KMSELDI.exe (PID: 2196)
- AutoPico.exe (PID: 2828)
- KMSELDI.exe (PID: 3820)
Creates files in the program directory
- KMSELDI.exe (PID: 4004)
- AutoPico.exe (PID: 3608)
- AutoPico.exe (PID: 2828)
- KMSELDI.exe (PID: 2196)
Removes files from Windows directory
- KMSpico_setup.tmp (PID: 2804)
INFO
Reads the hosts file
- chrome.exe (PID: 2952)
- chrome.exe (PID: 3452)
Reads Internet Cache Settings
- chrome.exe (PID: 3452)
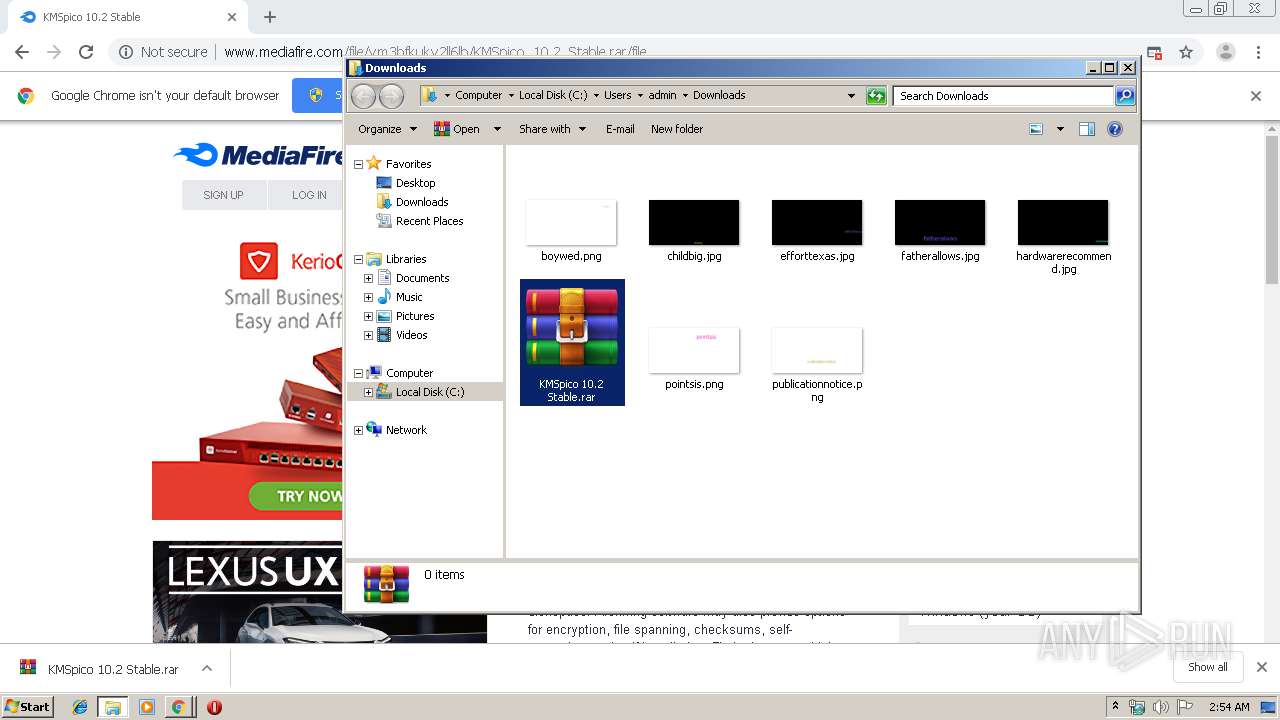
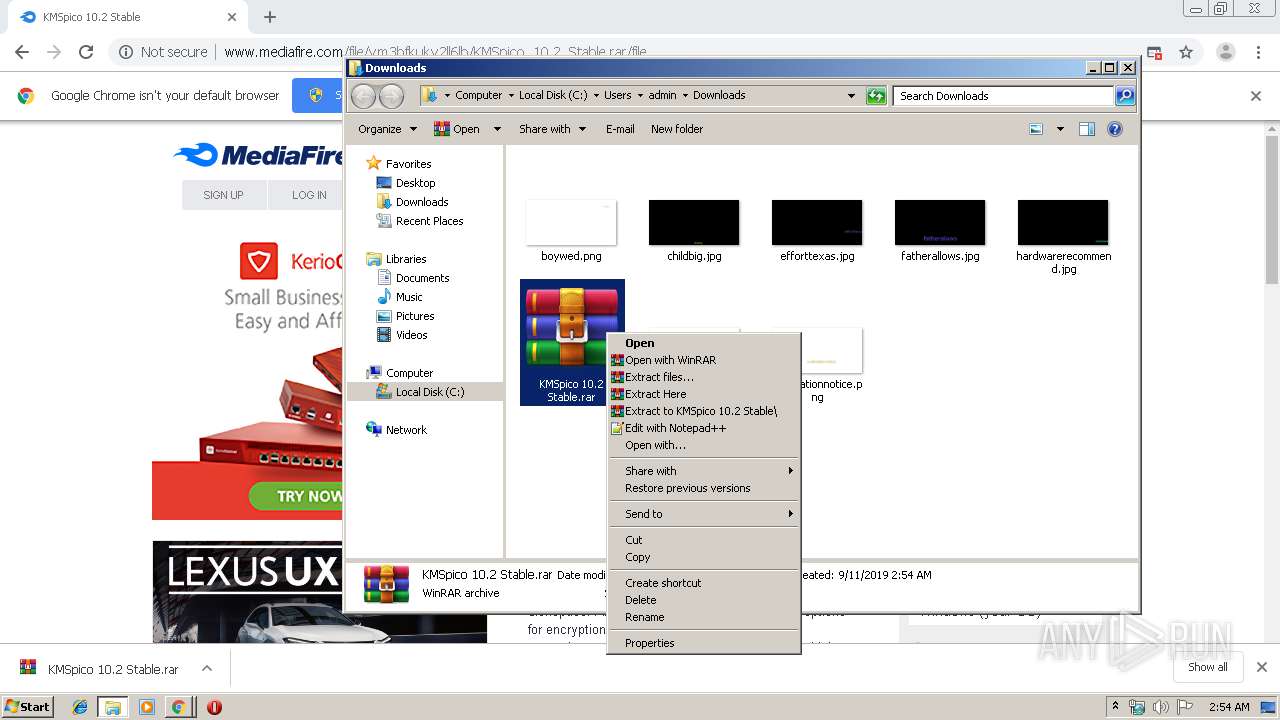
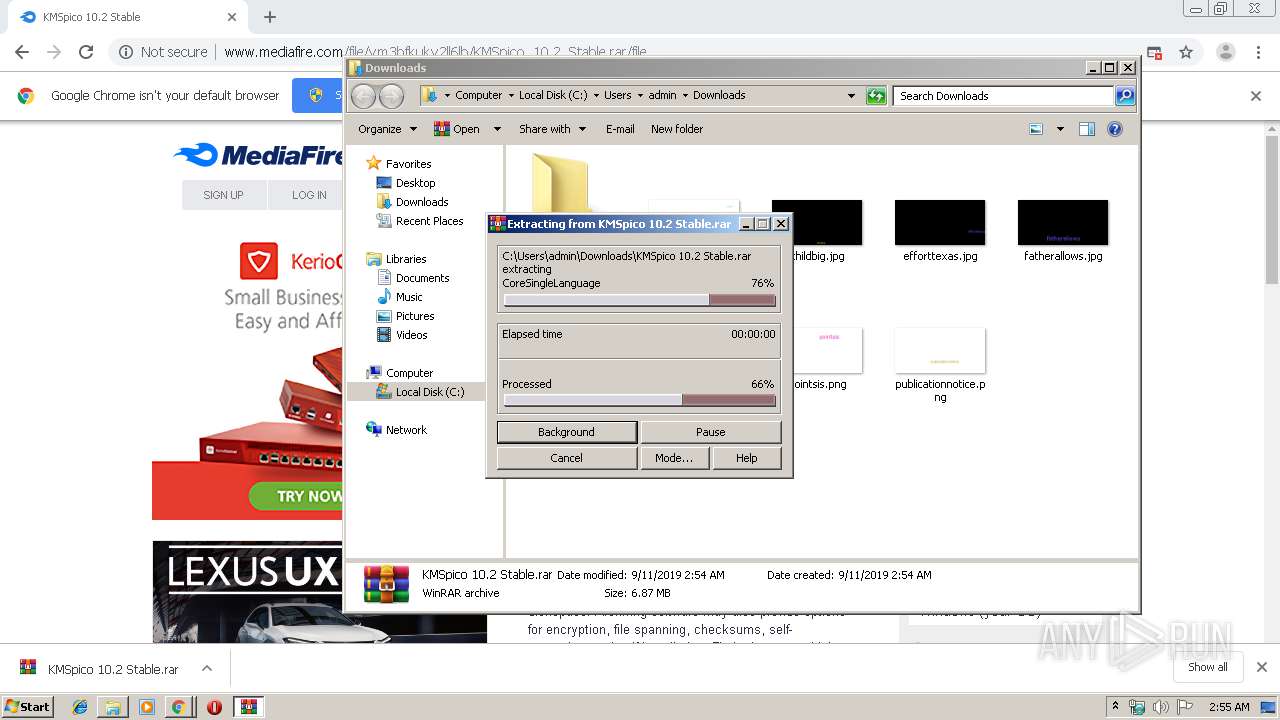
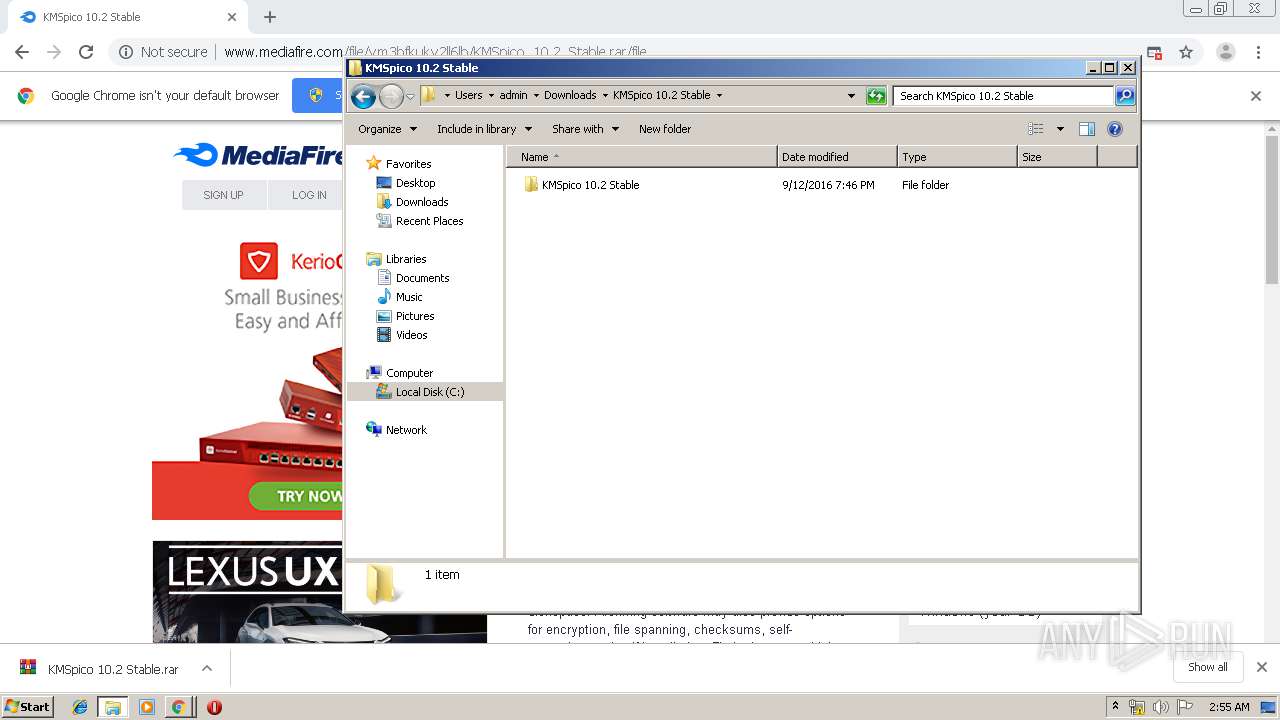
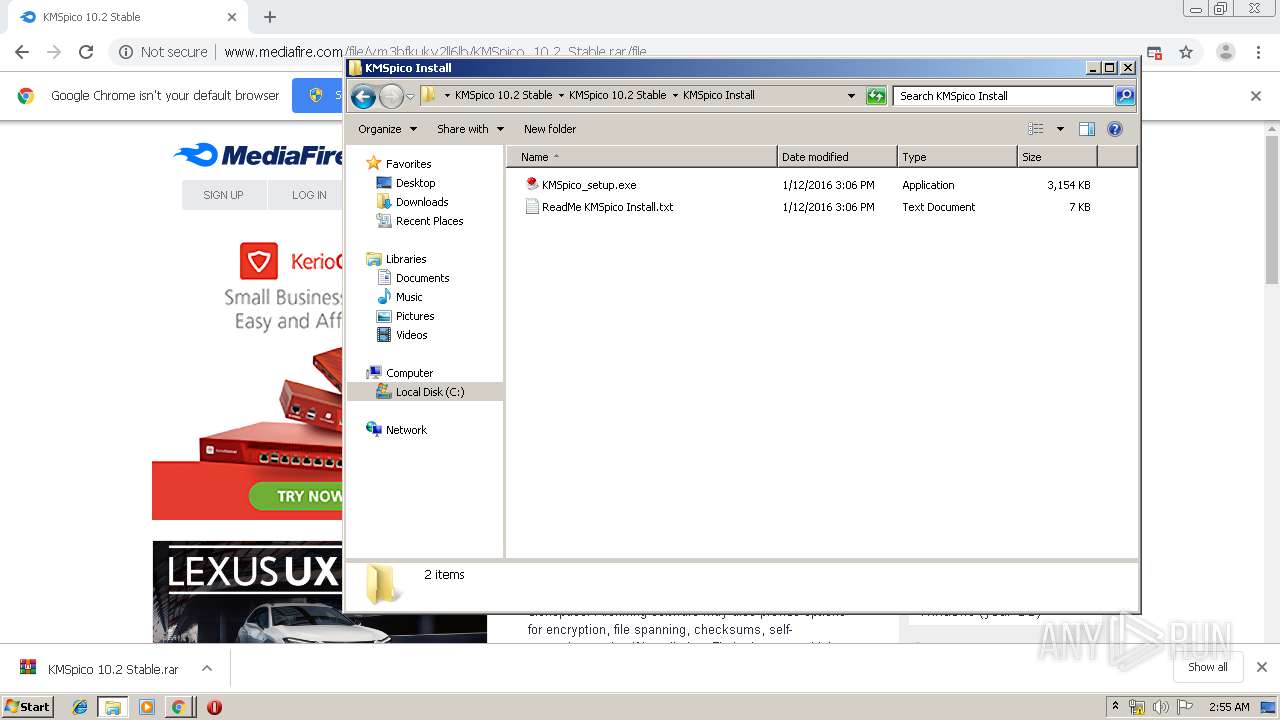
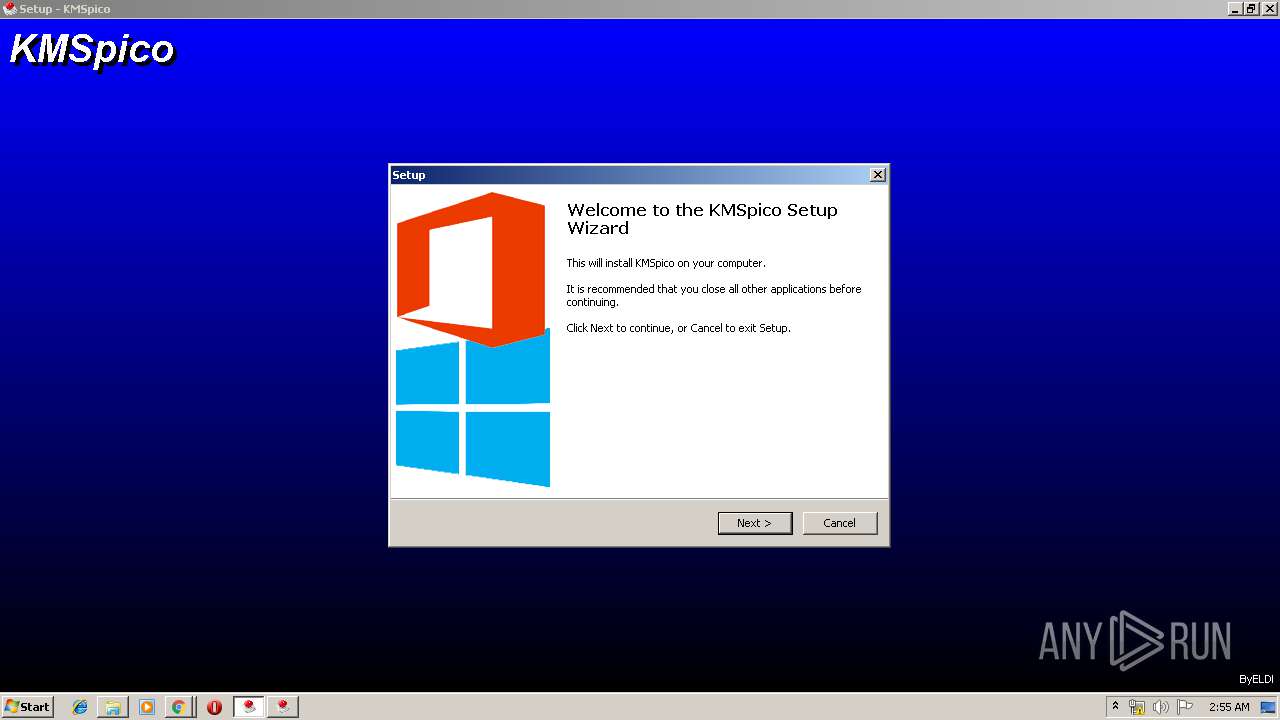
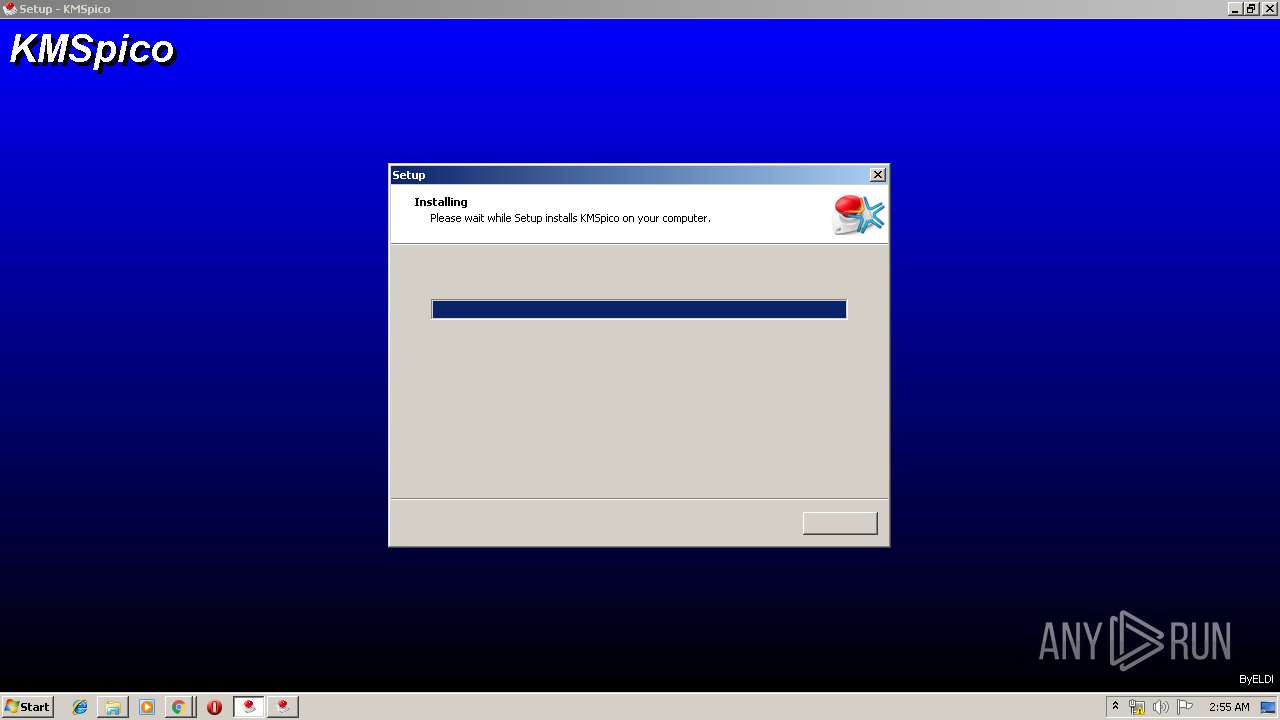
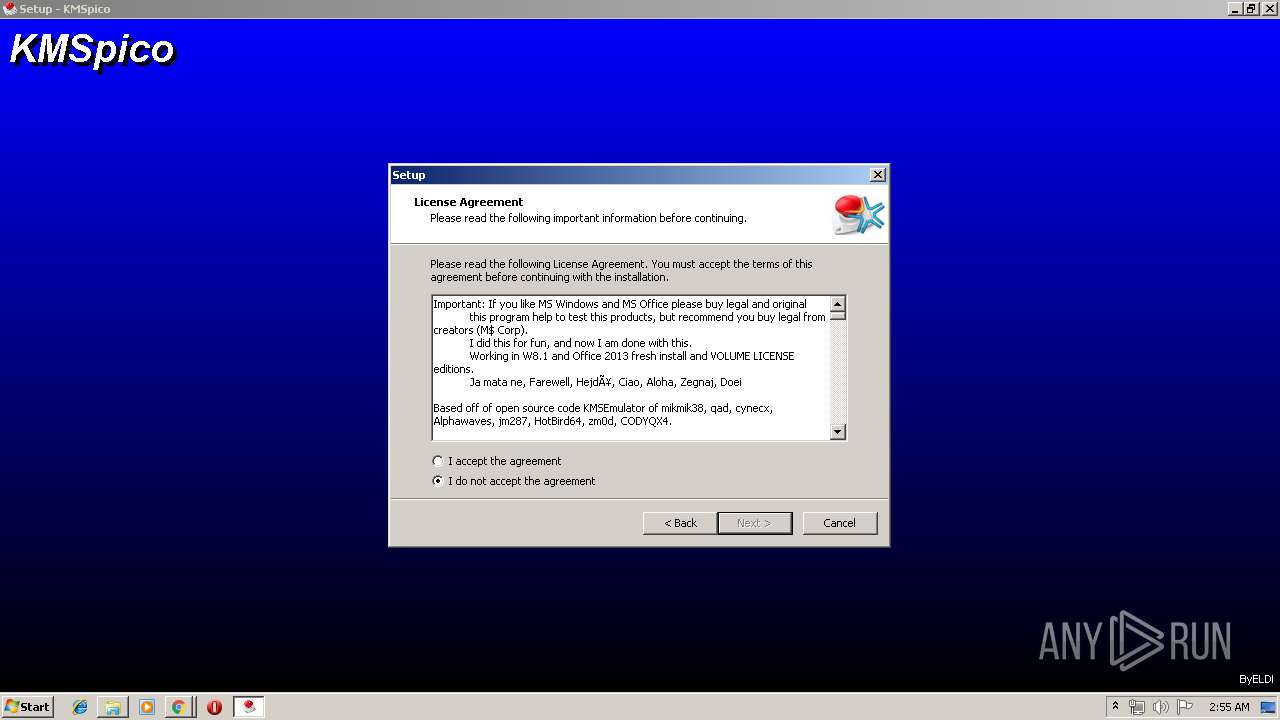
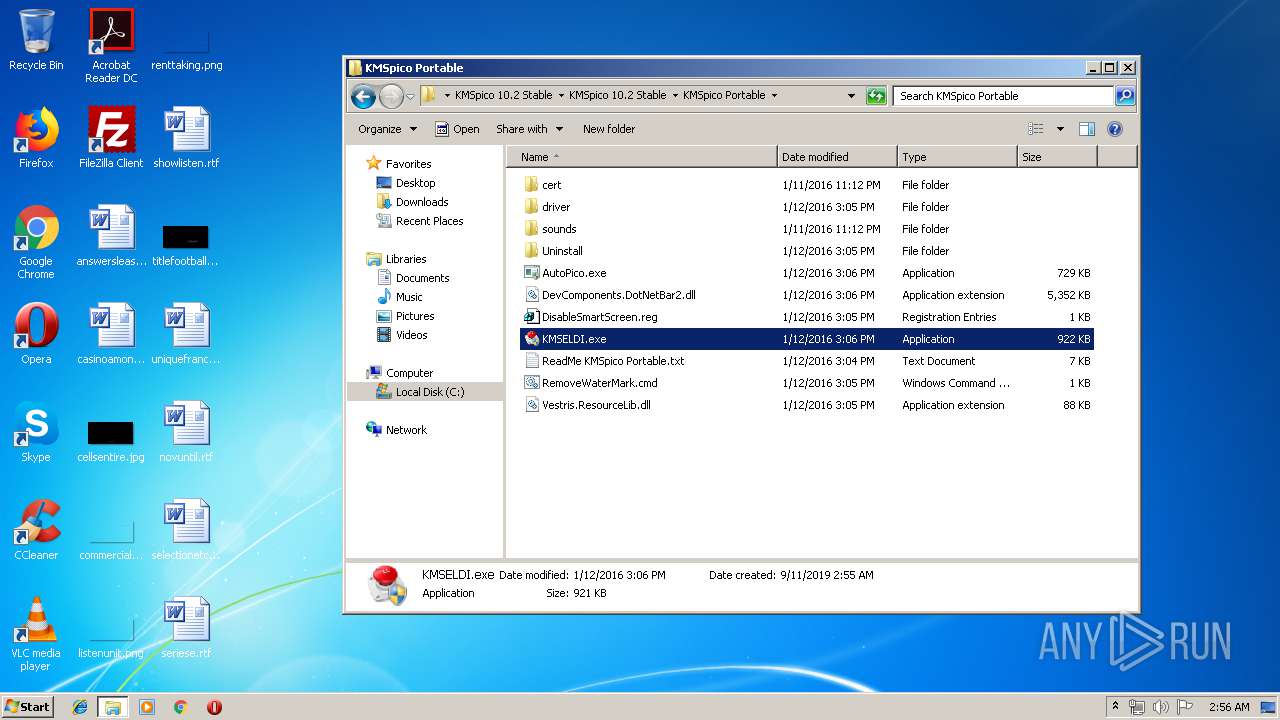
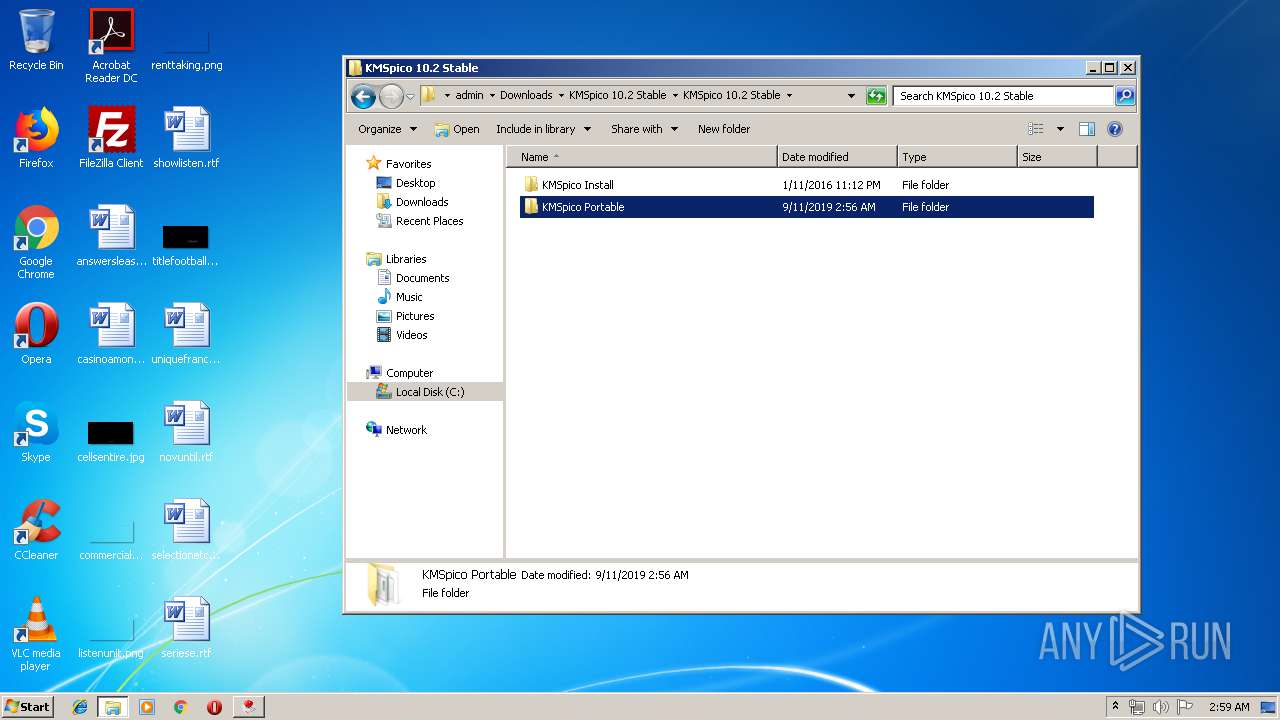
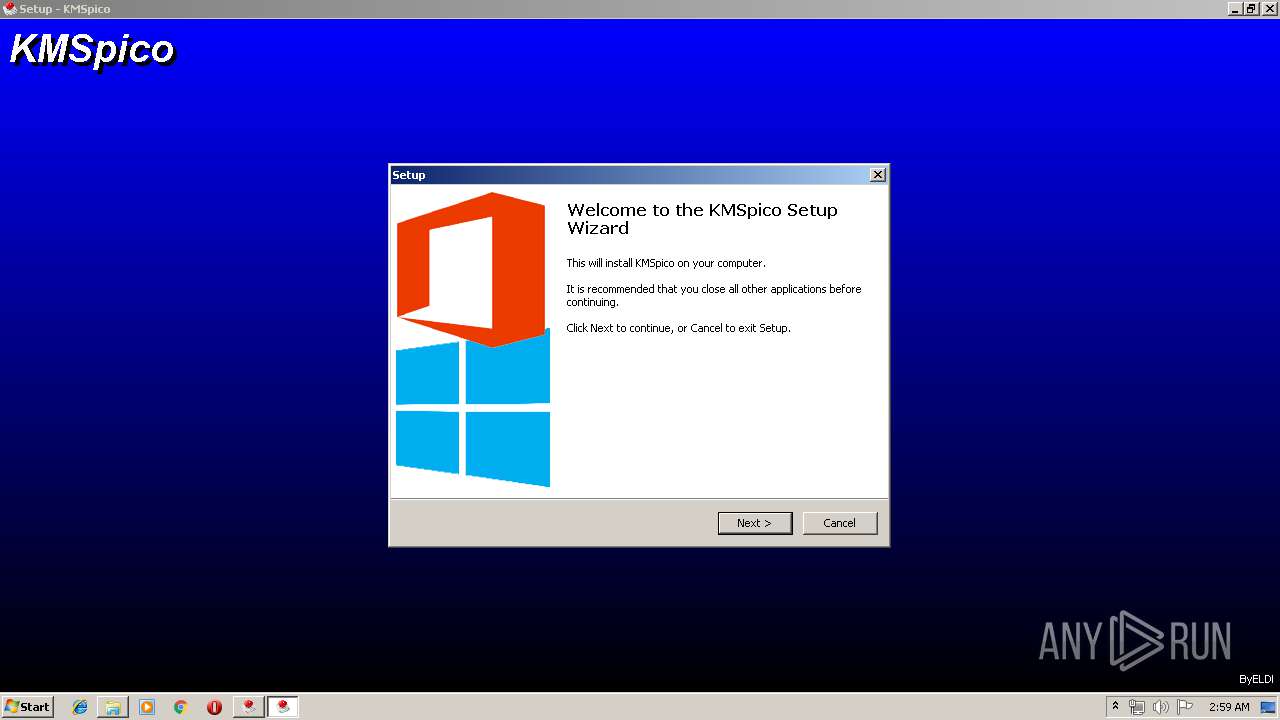
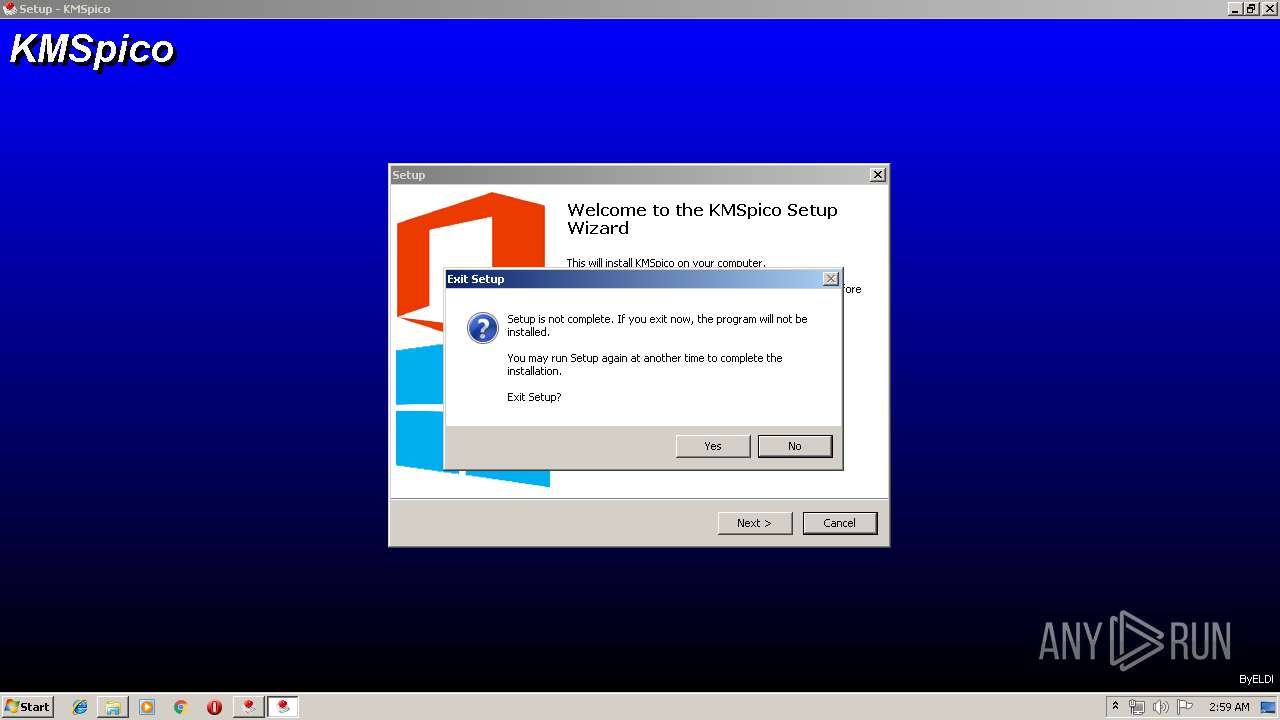
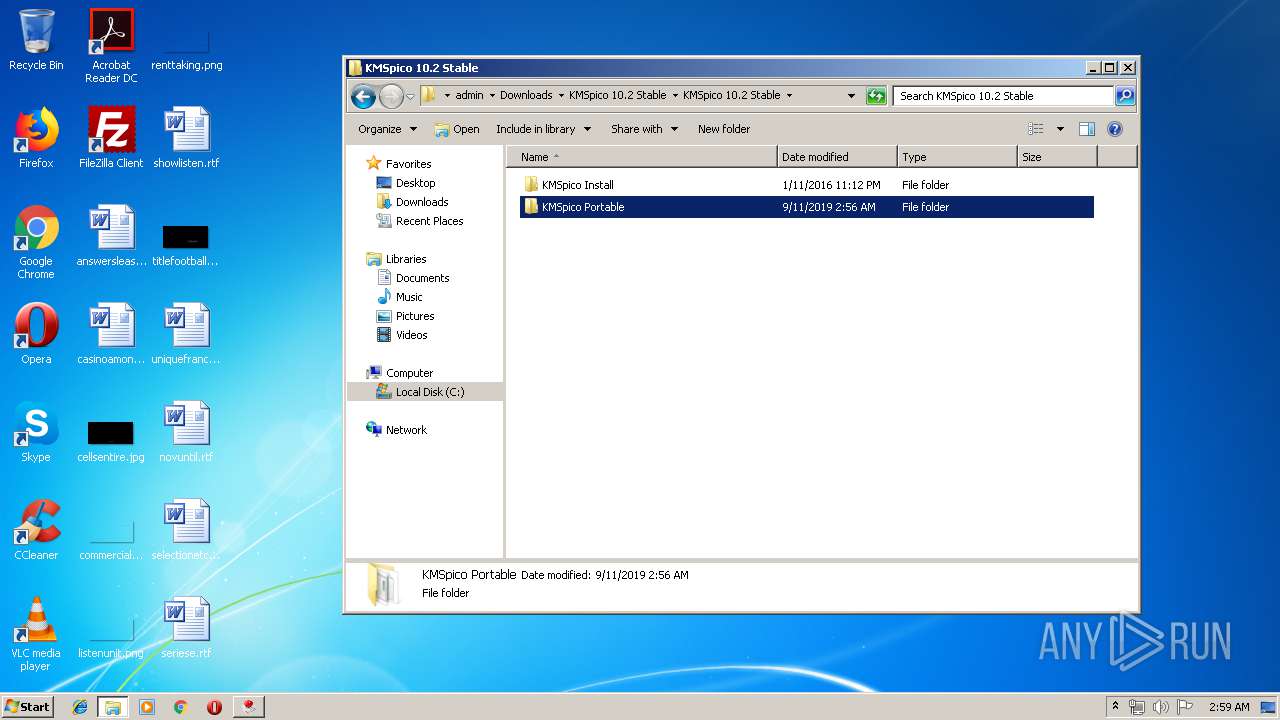
Manual execution by user
- KMSpico_setup.exe (PID: 3916)
- KMSpico_setup.exe (PID: 3068)
- WinRAR.exe (PID: 2604)
- KMSELDI.exe (PID: 1680)
- KMSELDI.exe (PID: 3820)
- KMSpico_setup.exe (PID: 3492)
Application was dropped or rewritten from another process
- KMSpico_setup.tmp (PID: 2340)
- KMSpico_setup.tmp (PID: 704)
- KMSpico_setup.tmp (PID: 2432)
- KMSpico_setup.tmp (PID: 2804)
- KMSpico_setup.tmp (PID: 2304)
- KMSpico_setup.tmp (PID: 1640)
Application launched itself
- chrome.exe (PID: 3452)
Loads dropped or rewritten executable
- KMSpico_setup.tmp (PID: 2804)
- KMSpico_setup.tmp (PID: 2432)
- KMSpico_setup.tmp (PID: 2304)
Creates a software uninstall entry
- KMSpico_setup.tmp (PID: 2432)
- KMSpico_setup.tmp (PID: 2804)
Reads Microsoft Office registry keys
- KMSELDI.exe (PID: 4004)
- AutoPico.exe (PID: 3608)
- KMSELDI.exe (PID: 2196)
- AutoPico.exe (PID: 2828)
- KMSELDI.exe (PID: 3820)
Creates files in the program directory
- KMSpico_setup.tmp (PID: 2432)
- KMSpico_setup.tmp (PID: 2804)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 3452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
117
Monitored processes
60
Malicious processes
11
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=75.0.3770.100 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fe6a9d0,0x6fe6a9e0,0x6fe6a9ec | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 704 | "C:\Users\admin\AppData\Local\Temp\is-OP6BT.tmp\KMSpico_setup.tmp" /SL5="$2020A,2952592,69120,C:\Users\admin\Downloads\KMSpico 10.2 Stable\KMSpico 10.2 Stable\KMSpico Install\KMSpico_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-OP6BT.tmp\KMSpico_setup.tmp | — | KMSpico_setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1000 | "C:\Windows\system32\cmd.exe" /C ""C:\Program Files\KMSpico\scripts\Install_Service.cmd"" | C:\Windows\system32\cmd.exe | — | KMSpico_setup.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1073 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1640 | "C:\Users\admin\AppData\Local\Temp\is-FCDB6.tmp\KMSpico_setup.tmp" /SL5="$501D6,2952592,69120,C:\Users\admin\Downloads\KMSpico 10.2 Stable\KMSpico 10.2 Stable\KMSpico Install\KMSpico_setup.exe" | C:\Users\admin\AppData\Local\Temp\is-FCDB6.tmp\KMSpico_setup.tmp | — | KMSpico_setup.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 2 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1680 | "C:\Users\admin\Downloads\KMSpico 10.2 Stable\KMSpico 10.2 Stable\KMSpico Portable\KMSELDI.exe" | C:\Users\admin\Downloads\KMSpico 10.2 Stable\KMSpico 10.2 Stable\KMSpico Portable\KMSELDI.exe | — | explorer.exe | |||||||||||
User: admin Company: @ByELDI Integrity Level: MEDIUM Description: KMS GUI ELDI Exit code: 3221226540 Version: 37.1.0.0 Modules
| |||||||||||||||
| 1732 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe2_ Global\UsGthrCtrlFltPipeMssGthrPipe2 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1028,8890798569603762802,16930373760533517230,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10994077478139035984 --mojo-platform-channel-handle=3528 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2196 | "C:\Program Files\KMSpico\KMSELDI.exe" /silent /backup | C:\Program Files\KMSpico\KMSELDI.exe | KMSpico_setup.tmp | ||||||||||||
User: admin Company: @ByELDI Integrity Level: HIGH Description: KMS GUI ELDI Exit code: 4294967295 Version: 37.1.0.0 Modules
| |||||||||||||||
| 2296 | "C:\Program Files\KMSpico\UninsHs.exe" /r0=KMSpico,default,C:\Users\admin\Downloads\KMSpico 10.2 Stable\KMSpico 10.2 Stable\KMSpico Install\KMSpico_setup.exe | C:\Program Files\KMSpico\UninsHs.exe | — | KMSpico_setup.tmp | |||||||||||
User: admin Company: Han-soft Integrity Level: HIGH Description: Uninstall for InnoSetup by Han-soft Exit code: 0 Version: 2.1.0.283 Modules
| |||||||||||||||
| 2304 | "C:\Users\admin\AppData\Local\Temp\is-Q8QE3.tmp\KMSpico_setup.tmp" /SL5="$602A4,2952592,69120,C:\Users\admin\Downloads\KMSpico 10.2 Stable\KMSpico 10.2 Stable\KMSpico Install\KMSpico_setup.exe" /SPAWNWND=$802BC /NOTIFYWND=$501D6 | C:\Users\admin\AppData\Local\Temp\is-Q8QE3.tmp\KMSpico_setup.tmp | KMSpico_setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 2 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
3 498
Read events
3 250
Write events
223
Delete events
25
Modification events
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3488) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3452-13212640458926125 |
Value: 259 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3452) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
34
Suspicious files
80
Text files
1 382
Unknown types
59
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\87f8e914-1650-4e4a-9436-287483f48191.tmp | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF169c64.TMP | text | |
MD5:— | SHA256:— | |||
| 3452 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
100
TCP/UDP connections
127
DNS requests
85
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2952 | chrome.exe | GET | 301 | 104.19.194.29:80 | http://www.mediafire.com/widgets/download_pro_upsell.php | US | — | — | shared |
2952 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://www.mediafire.com/file/vm3bfkukv2ll6lb/KMSpico_10.2_Stable.rar/file | US | html | 81.8 Kb | shared |
2952 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://www.mediafire.com/images/icons/svg_light/icons_sprite.svg | US | image | 8.19 Kb | shared |
2952 | chrome.exe | GET | 200 | 104.19.194.29:80 | http://www.mediafire.com/js/prebid1.30.0.js | US | text | 35.6 Kb | shared |
2952 | chrome.exe | GET | 200 | 23.45.108.178:80 | http://c.aaxads.com/aax.js?pub=AAX3221EY&hst=www.mediafire.com&ver=1.2 | NL | text | 97.8 Kb | whitelisted |
2952 | chrome.exe | GET | 200 | 104.19.195.29:80 | http://static.mediafire.com/images/backgrounds/download/apps_list_sprite-v4.png | US | image | 6.78 Kb | shared |
2952 | chrome.exe | GET | 200 | 172.217.16.206:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 727 b | whitelisted |
2952 | chrome.exe | GET | 200 | 172.217.18.98:80 | http://www.googletagservices.com/tag/js/gpt.js | US | text | 12.3 Kb | whitelisted |
2952 | chrome.exe | GET | 200 | 104.19.215.37:80 | http://cdn.otnolatrnup.com/Scripts/infinity.js.aspx?guid=5ff0fb62-0643-4ff1-aaee-c737f9ffc0e0 | US | text | 72.7 Kb | whitelisted |
2952 | chrome.exe | POST | 200 | 185.33.223.210:80 | http://ib.adnxs.com/ut/v3/prebid | unknown | text | 494 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2952 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 104.19.194.29:80 | www.mediafire.com | Cloudflare Inc | US | shared |
2952 | chrome.exe | 172.217.21.237:443 | accounts.google.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 172.217.16.206:80 | translate.google.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 172.217.18.98:80 | www.googletagservices.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 104.19.195.29:80 | www.mediafire.com | Cloudflare Inc | US | shared |
2952 | chrome.exe | 216.58.208.34:443 | adservice.google.com | Google Inc. | US | whitelisted |
2952 | chrome.exe | 172.217.22.34:443 | securepubads.g.doubleclick.net | Google Inc. | US | whitelisted |
2952 | chrome.exe | 104.19.215.37:80 | cdn.otnolatrnup.com | Cloudflare Inc | US | shared |
2952 | chrome.exe | 216.58.210.14:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.googletagmanager.com |
| whitelisted |
translate.google.com |
| whitelisted |
www.googletagservices.com |
| whitelisted |
c.aaxads.com |
| whitelisted |
static.mediafire.com |
| shared |
facebook.com |
| whitelisted |
download2267.mediafire.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2952 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |