| File name: | E20240100020510_Anexo_1.doc |
| Full analysis: | https://app.any.run/tasks/88f168b5-3c99-4180-8e58-cde1b5108f75 |
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2024, 00:40:10 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 4F85F572BCF007F2F2E8A7E7D87EE1D7 |
| SHA1: | E4A148507E0B53359A9DD6B767E07F52B691E37A |
| SHA256: | 6FF46C926D72BEB6BF985384FACF9A3F37CCD6EBA6F8C5D1403EFAAF962F4115 |
| SSDEEP: | 98304:lEWWTu8MhH3VWjtKxggDfU7Cy/CmKlAbYpB4RplQ94geo7HNR9dIofyxmxqMogIc:MB2YK3pIwf7AQJ |
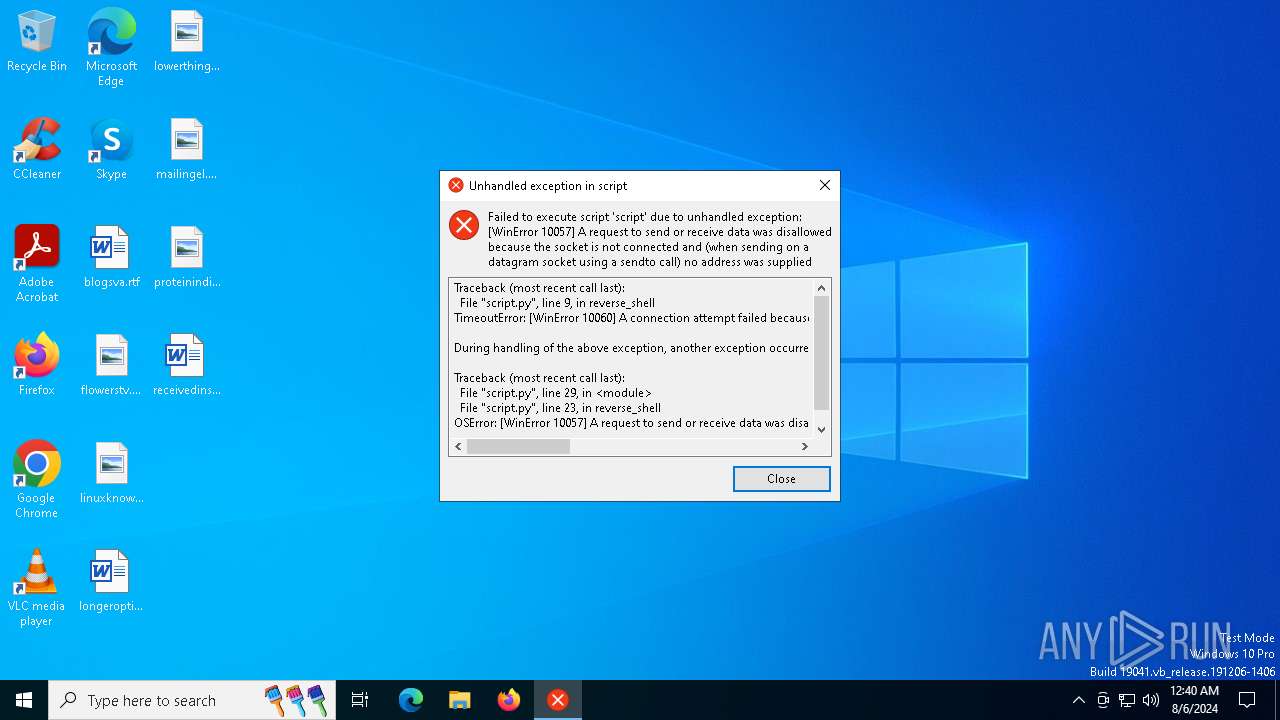
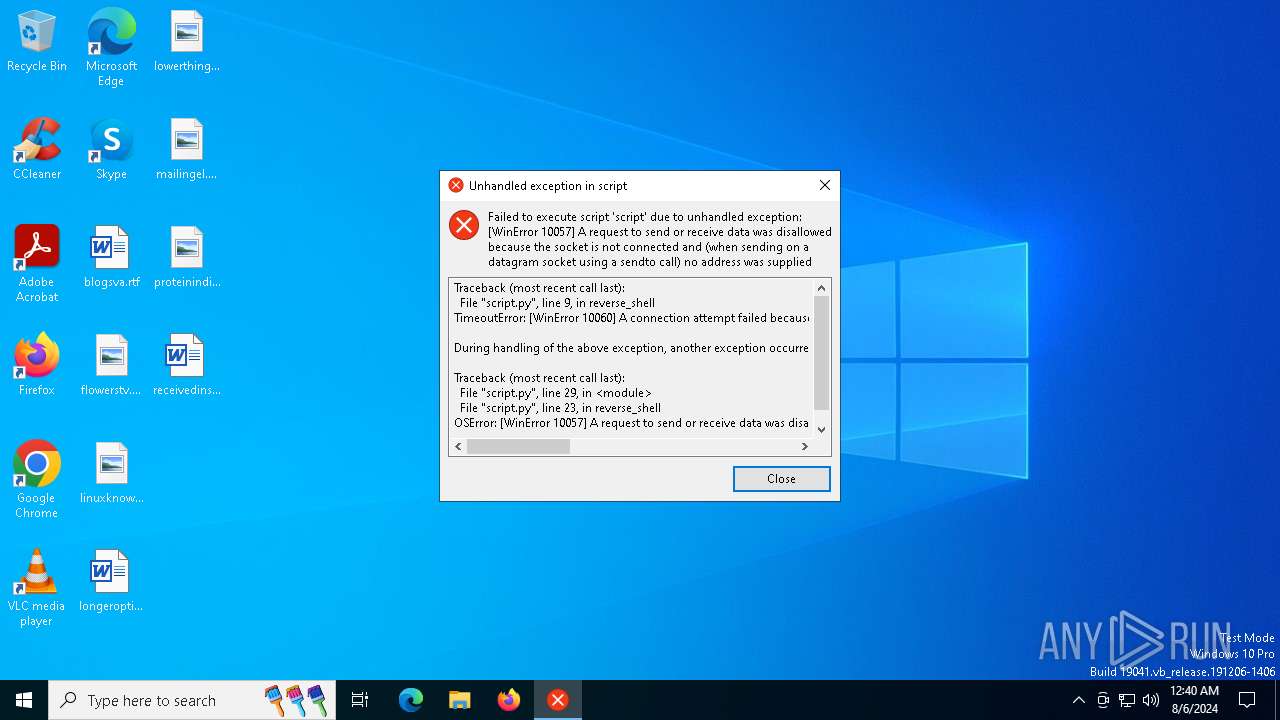
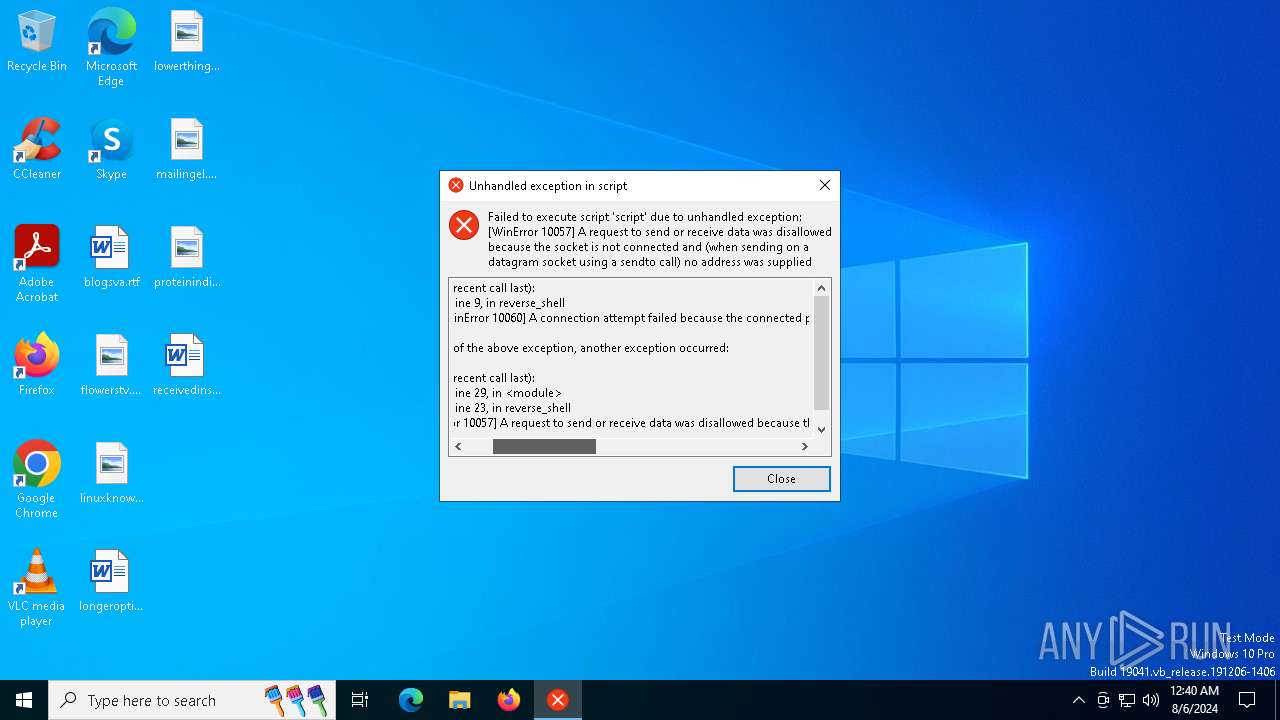
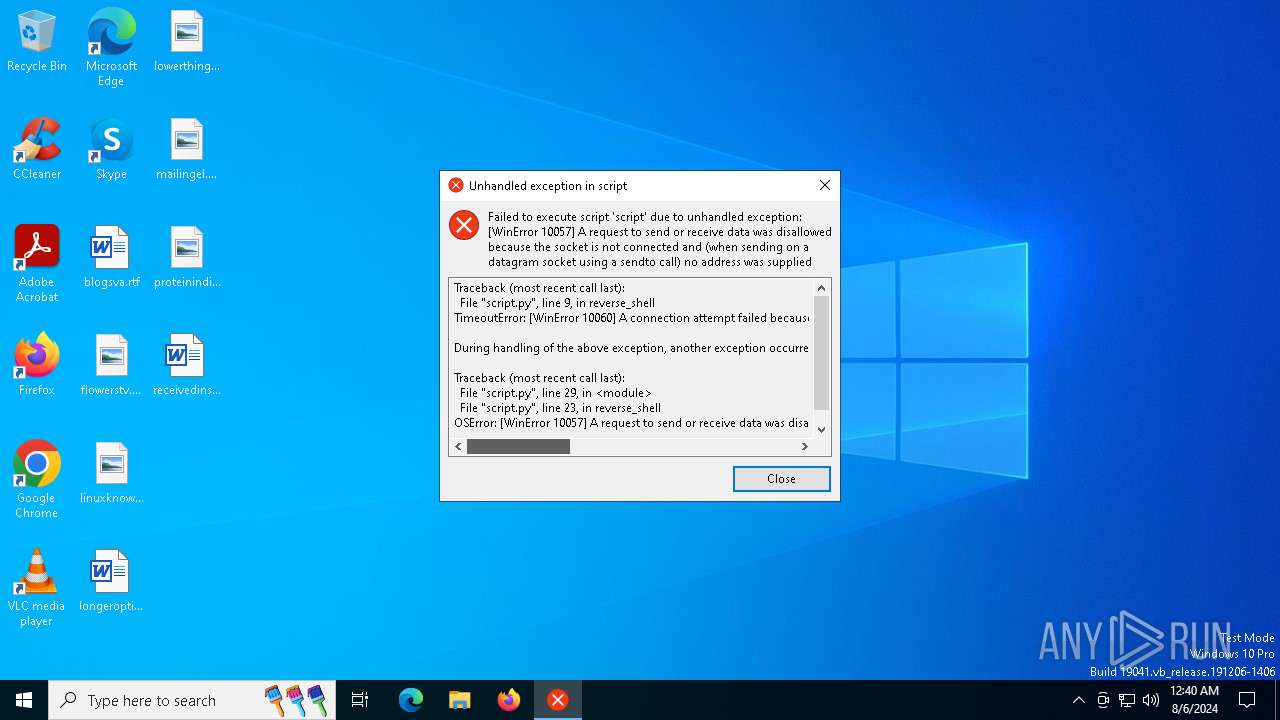
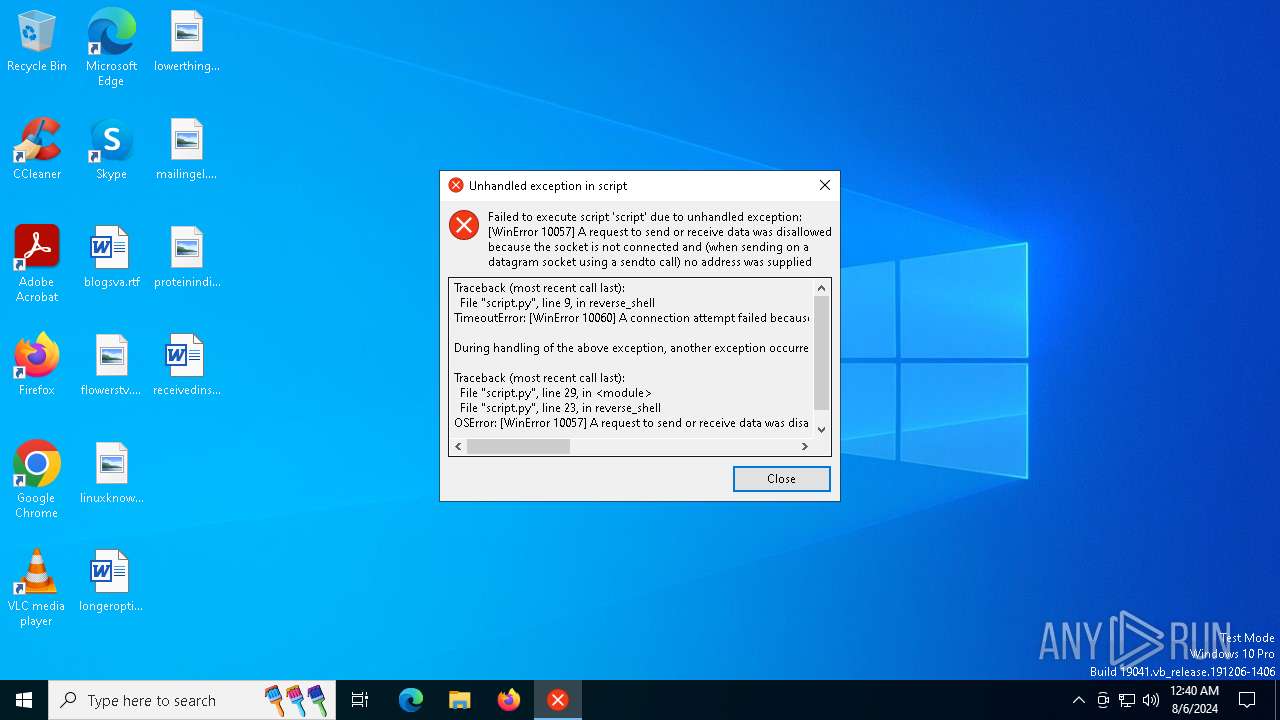
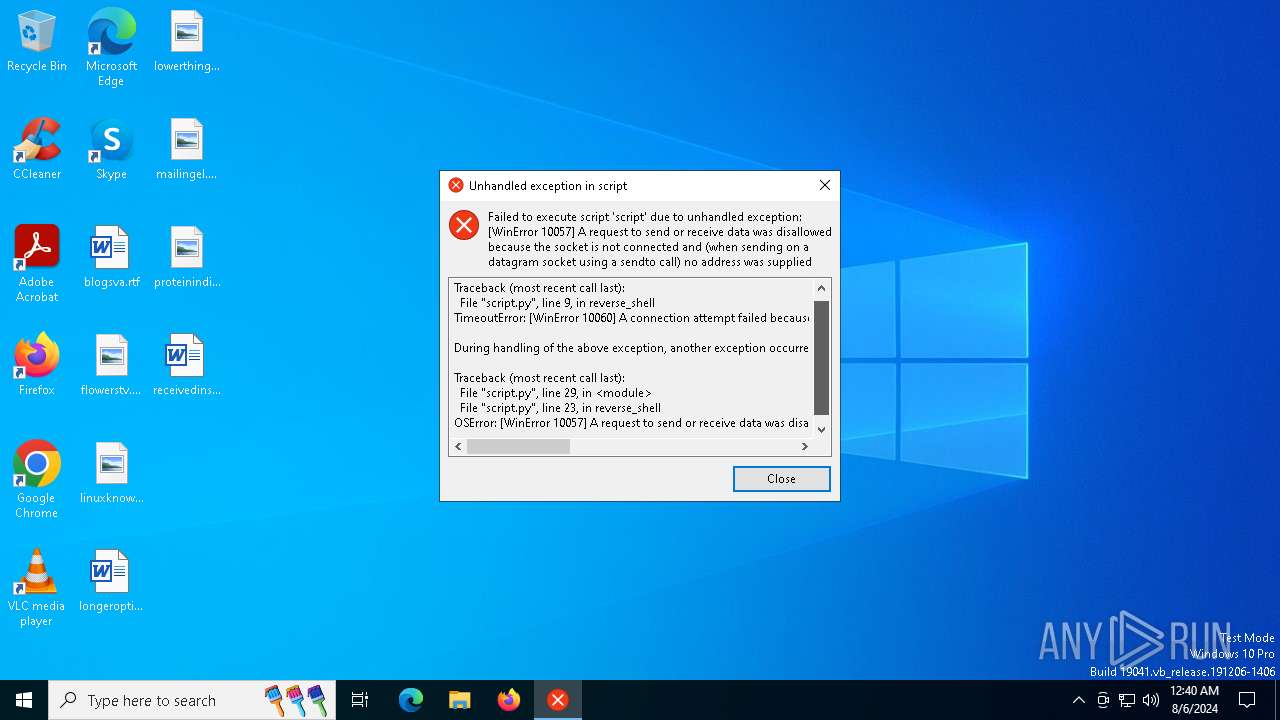
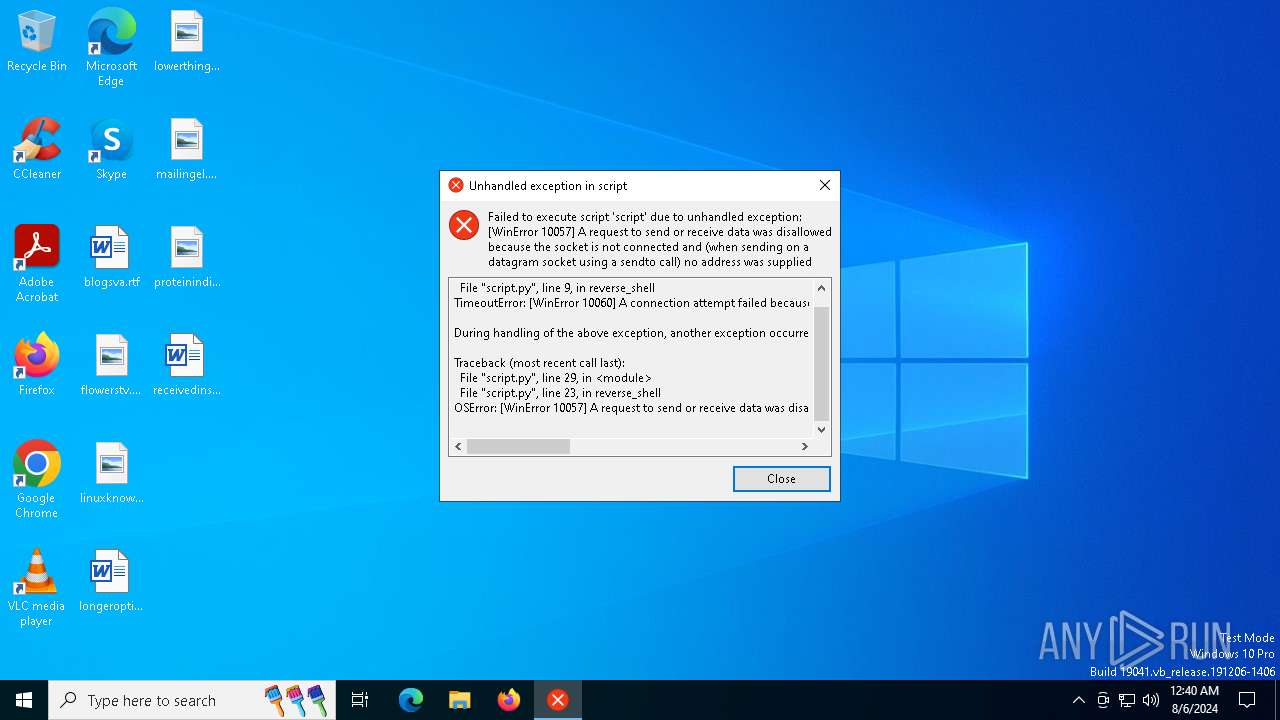
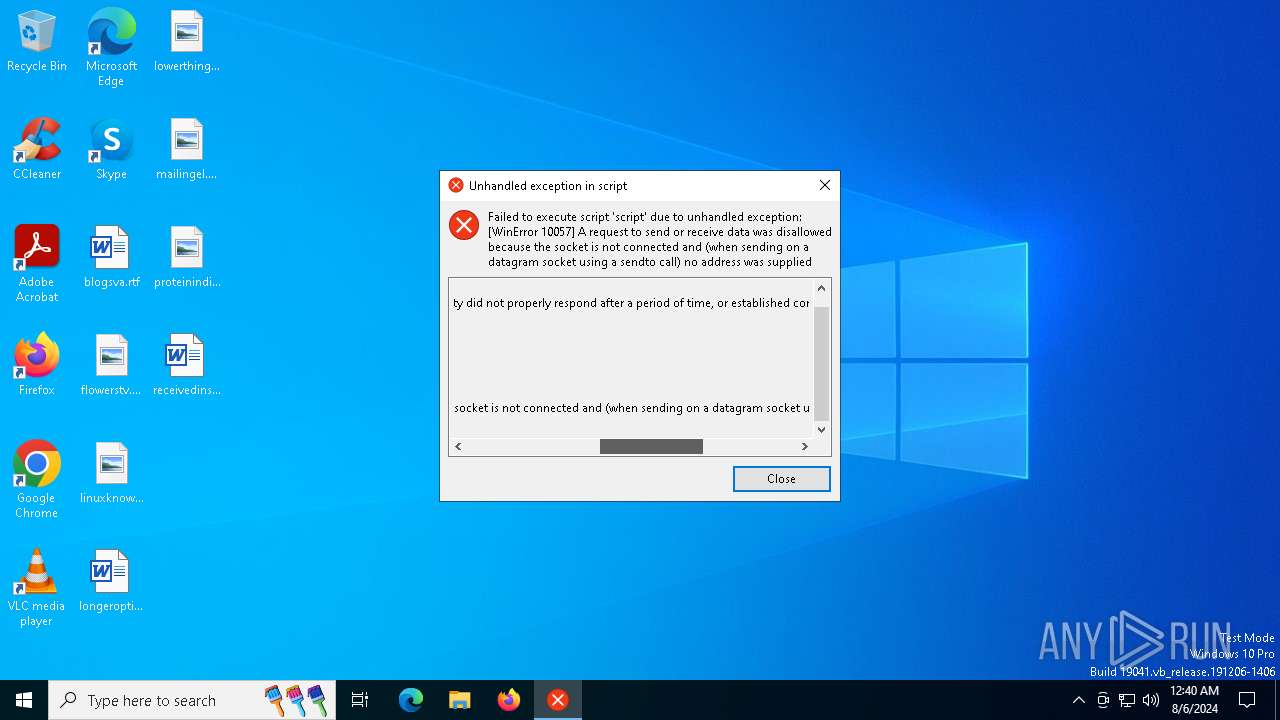
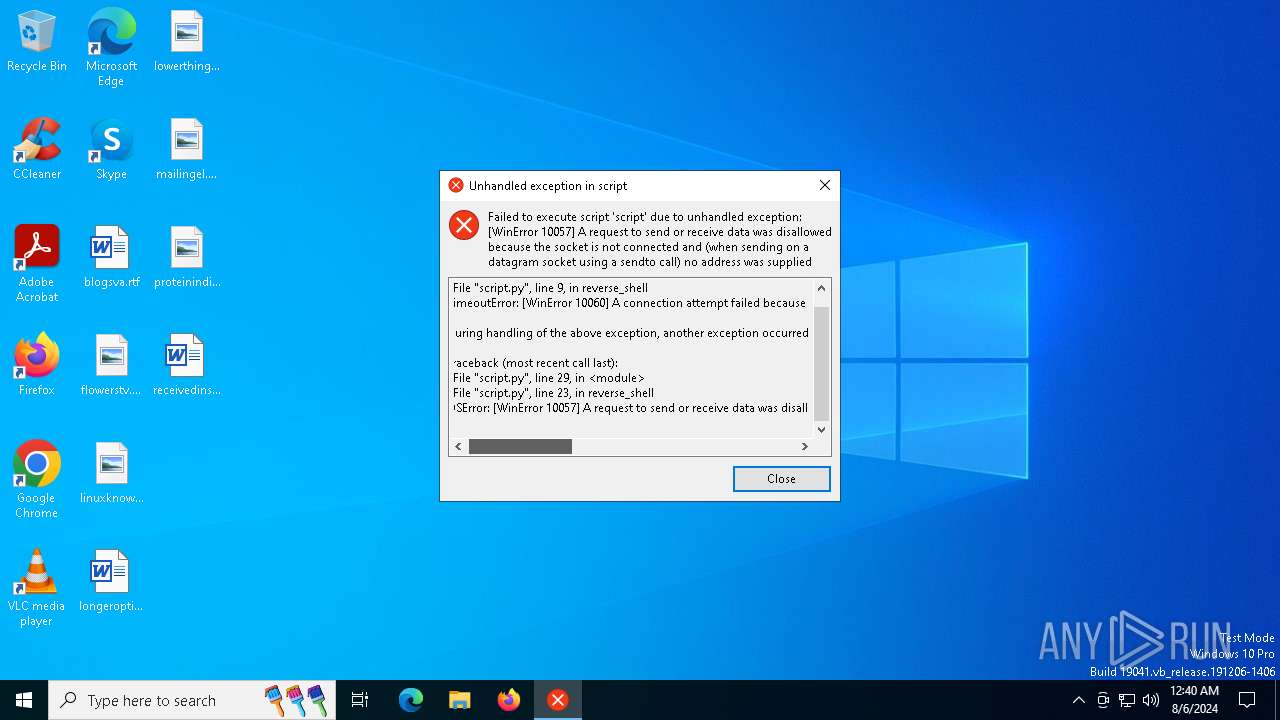
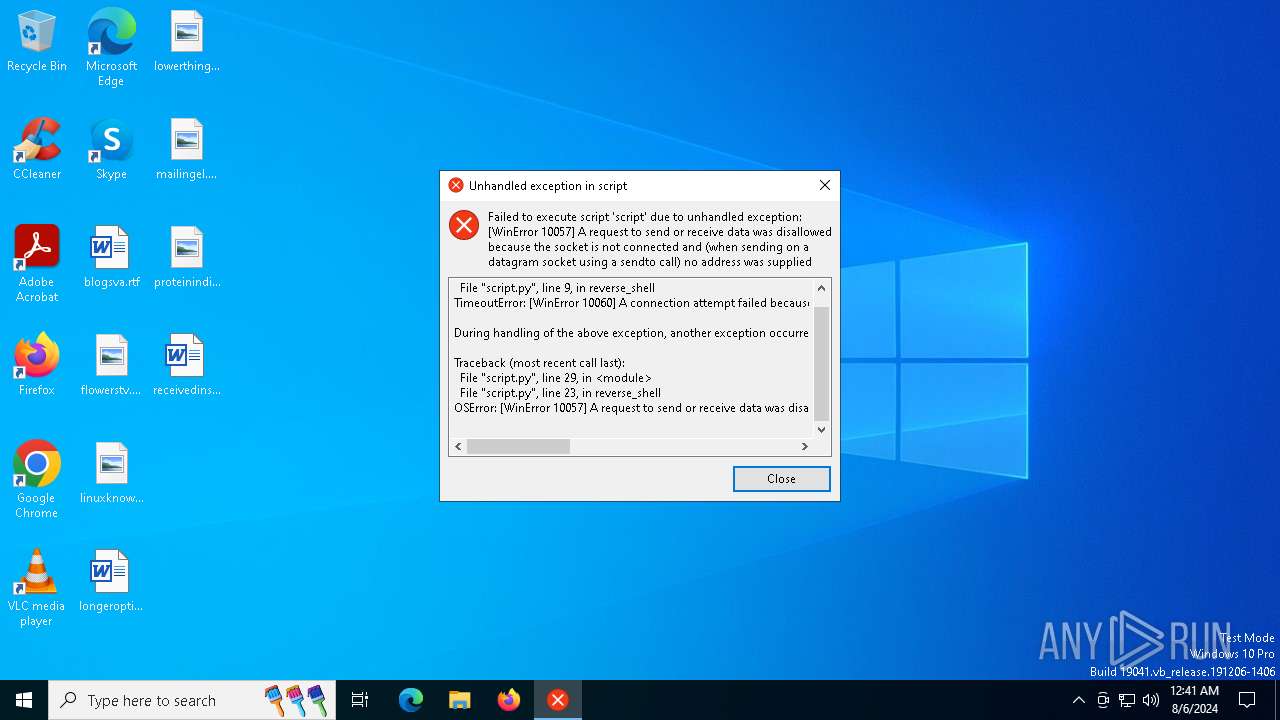
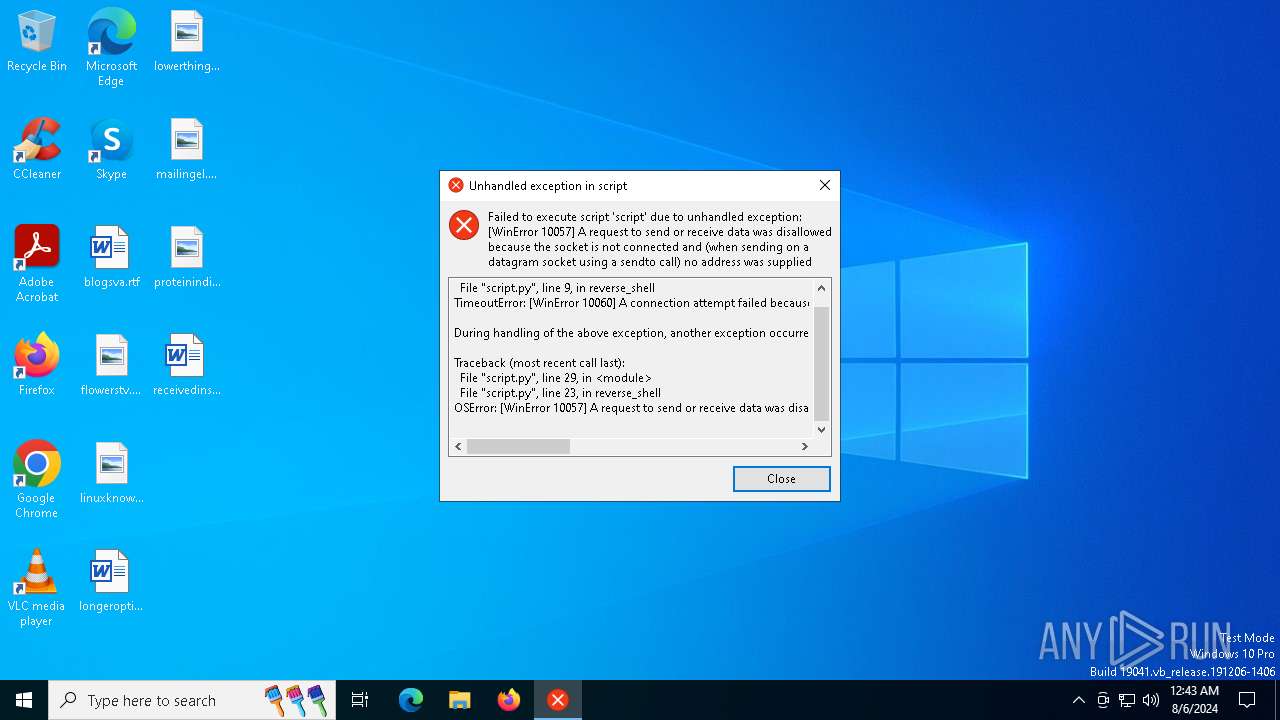
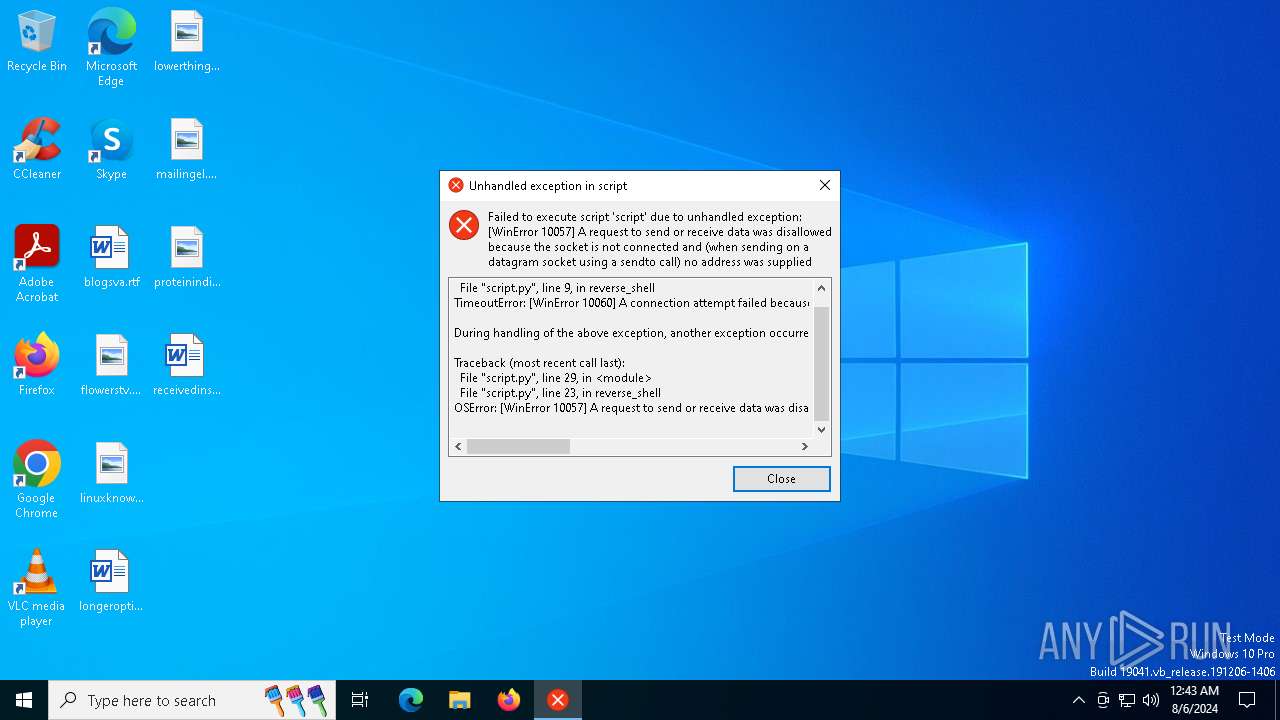
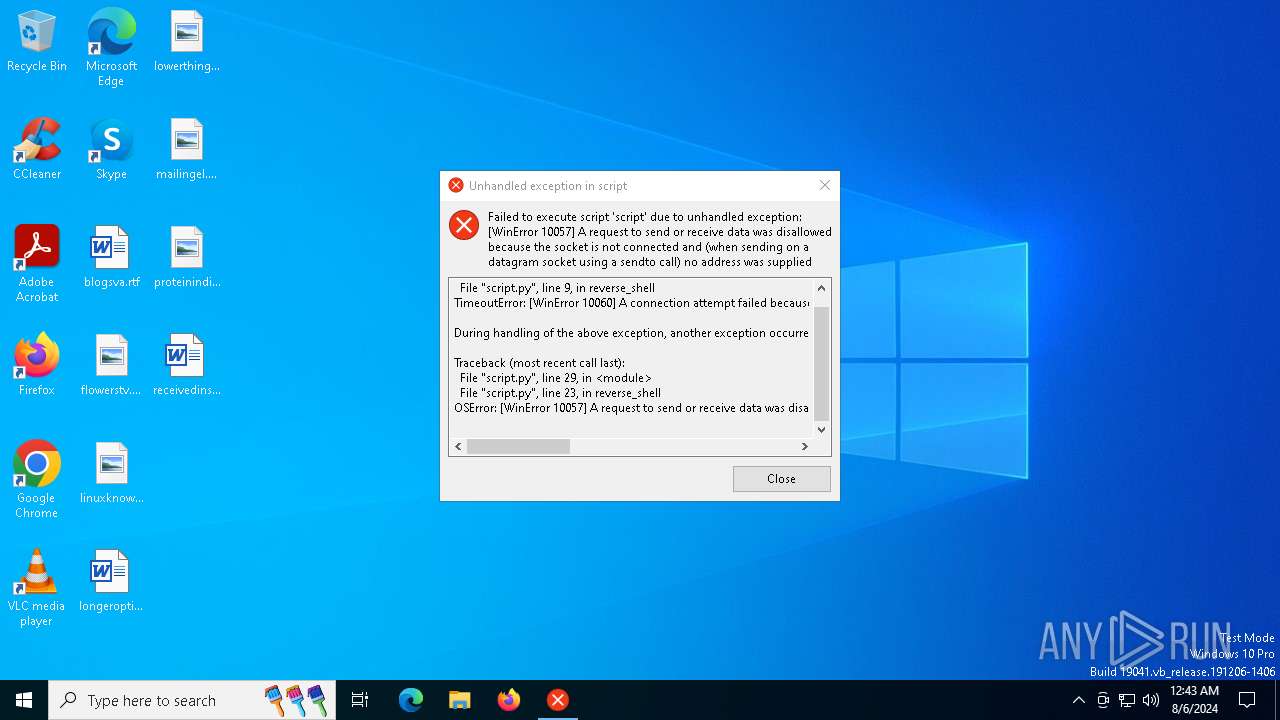
MALICIOUS
Drops the executable file immediately after the start
- E20240100020510_Anexo_1.doc.exe (PID: 6452)
SUSPICIOUS
Process drops legitimate windows executable
- E20240100020510_Anexo_1.doc.exe (PID: 6452)
The process drops C-runtime libraries
- E20240100020510_Anexo_1.doc.exe (PID: 6452)
Executable content was dropped or overwritten
- E20240100020510_Anexo_1.doc.exe (PID: 6452)
Process drops python dynamic module
- E20240100020510_Anexo_1.doc.exe (PID: 6452)
Application launched itself
- E20240100020510_Anexo_1.doc.exe (PID: 6452)
Loads Python modules
- E20240100020510_Anexo_1.doc.exe (PID: 6472)
INFO
Create files in a temporary directory
- E20240100020510_Anexo_1.doc.exe (PID: 6452)
Reads the computer name
- E20240100020510_Anexo_1.doc.exe (PID: 6452)
- E20240100020510_Anexo_1.doc.exe (PID: 6472)
Checks supported languages
- E20240100020510_Anexo_1.doc.exe (PID: 6452)
- E20240100020510_Anexo_1.doc.exe (PID: 6472)
Reads the machine GUID from the registry
- E20240100020510_Anexo_1.doc.exe (PID: 6472)
PyInstaller has been detected (YARA)
- E20240100020510_Anexo_1.doc.exe (PID: 6452)
- E20240100020510_Anexo_1.doc.exe (PID: 6472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:08:05 14:12:11+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 168960 |
| InitializedDataSize: | 99840 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc0d0 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
Total processes
138
Monitored processes
3
Malicious processes
1
Suspicious processes
0
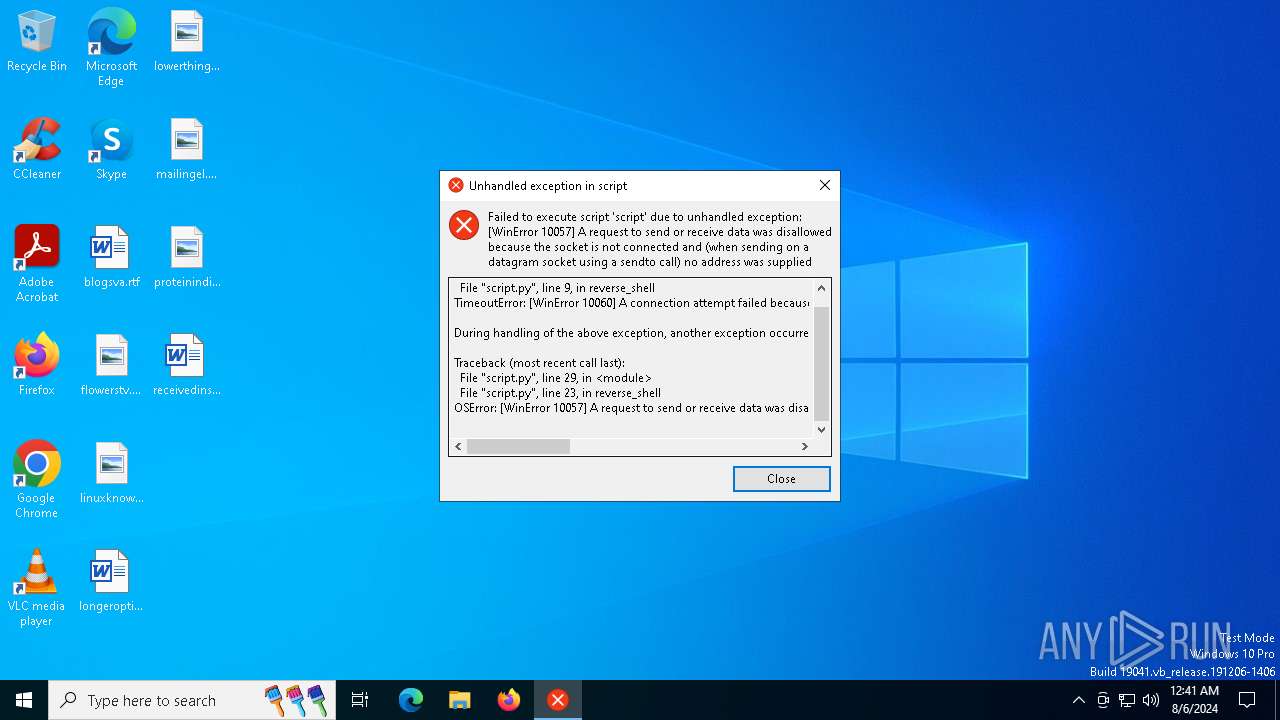
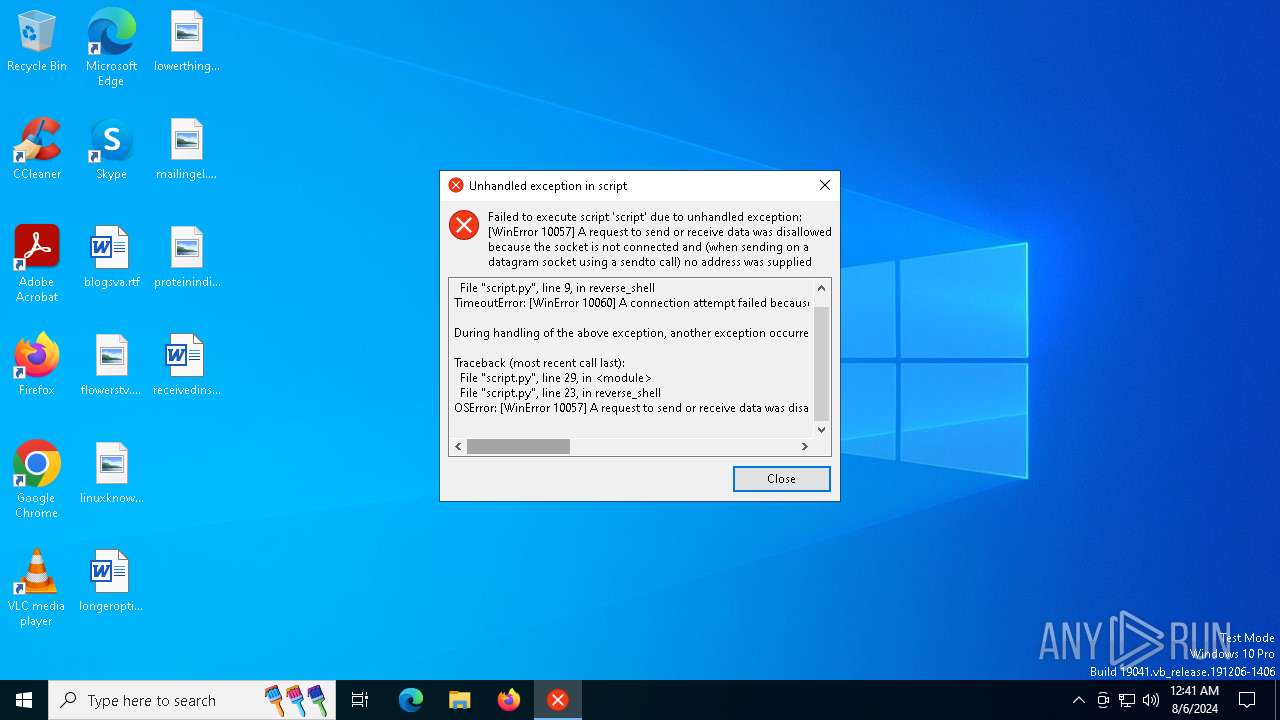
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3540 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6452 | "C:\Users\admin\AppData\Local\Temp\E20240100020510_Anexo_1.doc.exe" | C:\Users\admin\AppData\Local\Temp\E20240100020510_Anexo_1.doc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 6472 | "C:\Users\admin\AppData\Local\Temp\E20240100020510_Anexo_1.doc.exe" | C:\Users\admin\AppData\Local\Temp\E20240100020510_Anexo_1.doc.exe | E20240100020510_Anexo_1.doc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
Total events
314
Read events
314
Write events
0
Delete events
0
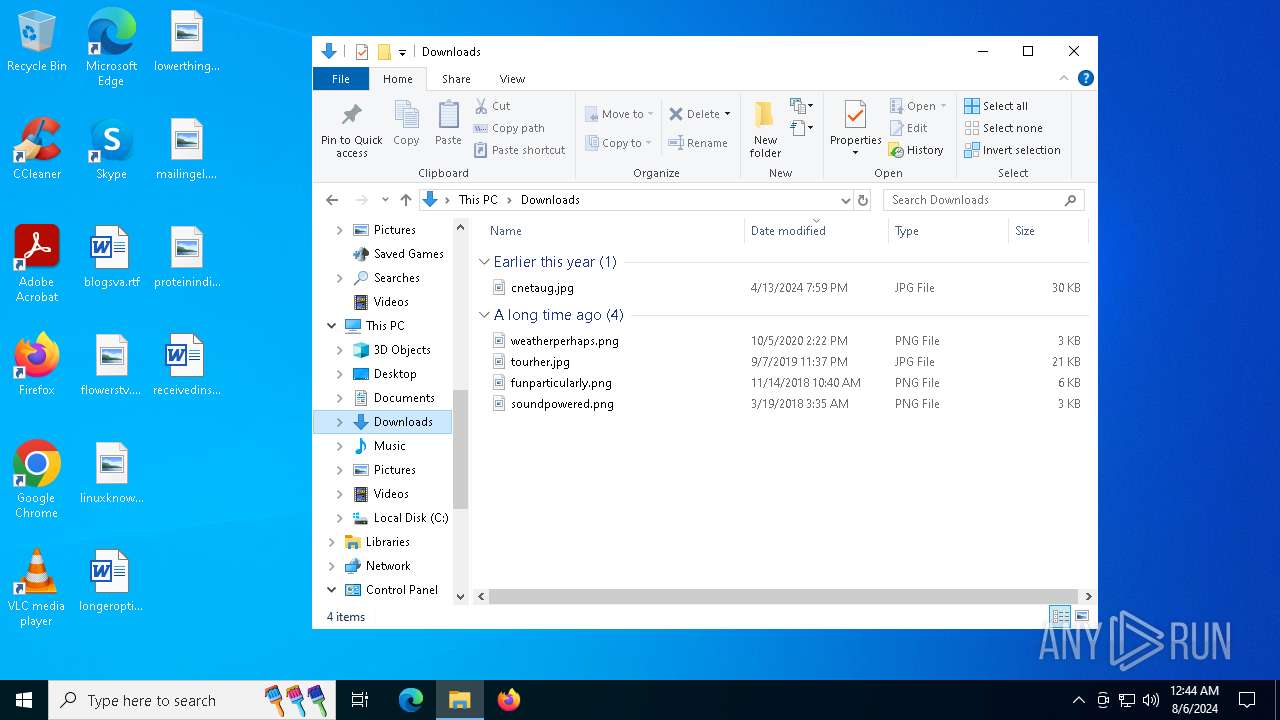
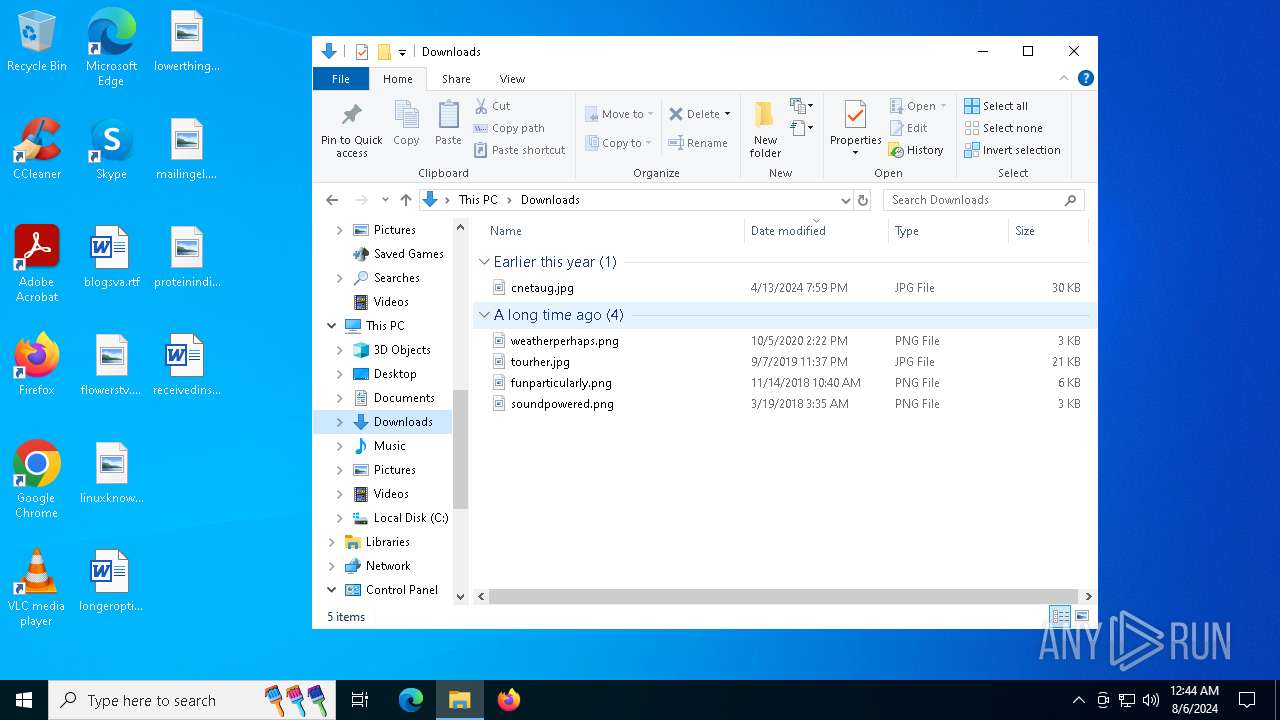
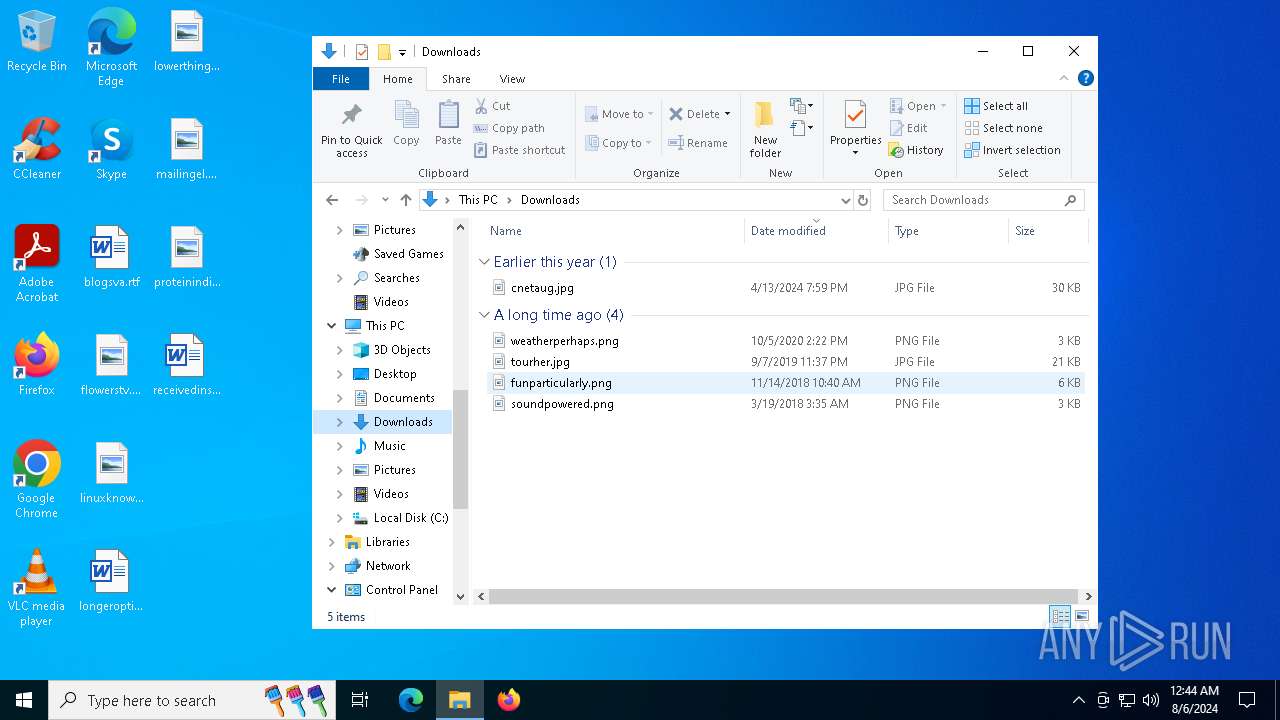
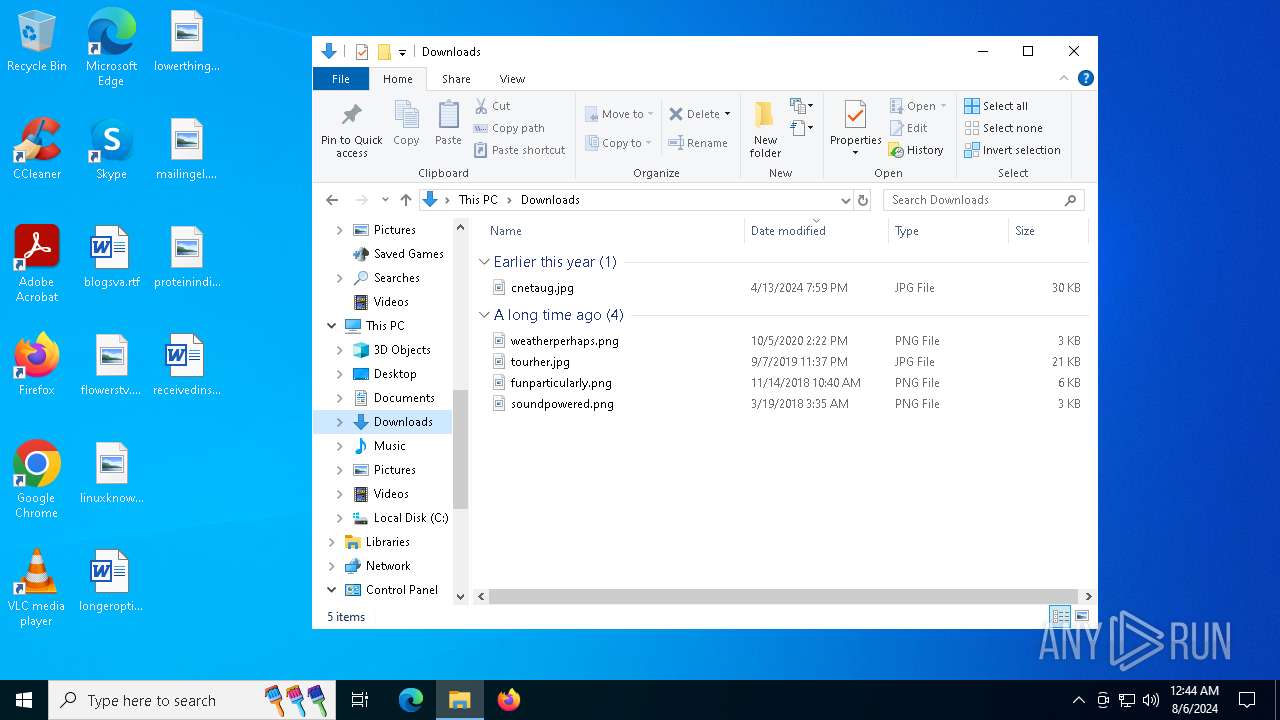
Modification events
Executable files
10
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6452 | E20240100020510_Anexo_1.doc.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\libcrypto-1_1.dll | executable | |
MD5:9D7A0C99256C50AFD5B0560BA2548930 | SHA256:9B7B4A0AD212095A8C2E35C71694D8A1764CD72A829E8E17C8AFE3A55F147939 | |||
| 6452 | E20240100020510_Anexo_1.doc.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\VCRUNTIME140.dll | executable | |
MD5:F34EB034AA4A9735218686590CBA2E8B | SHA256:9D2B40F0395CC5D1B4D5EA17B84970C29971D448C37104676DB577586D4AD1B1 | |||
| 6452 | E20240100020510_Anexo_1.doc.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\_lzma.pyd | executable | |
MD5:7447EFD8D71E8A1929BE0FAC722B42DC | SHA256:60793C8592193CFBD00FD3E5263BE4315D650BA4F9E4FDA9C45A10642FD998BE | |||
| 6452 | E20240100020510_Anexo_1.doc.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\_decimal.pyd | executable | |
MD5:20C77203DDF9FF2FF96D6D11DEA2EDCF | SHA256:9AAC010A424C757C434C460C3C0A6515D7720966AB64BAD667539282A17B4133 | |||
| 6452 | E20240100020510_Anexo_1.doc.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\python310.dll | executable | |
MD5:63A1FA9259A35EAEAC04174CECB90048 | SHA256:14B06796F288BC6599E458FB23A944AB0C843E9868058F02A91D4606533505ED | |||
| 6452 | E20240100020510_Anexo_1.doc.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\unicodedata.pyd | executable | |
MD5:81D62AD36CBDDB4E57A91018F3C0816E | SHA256:1FB2D66C056F69E8BBDD8C6C910E72697874DAE680264F8FB4B4DF19AF98AA2E | |||
| 6452 | E20240100020510_Anexo_1.doc.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\base_library.zip | compressed | |
MD5:01BD4F502A3CED4678E93CBB528DEBBB | SHA256:A69368C96CF351B44B7E709B431AE4691580E241FD2367541D2361F348949AF2 | |||
| 6452 | E20240100020510_Anexo_1.doc.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\select.pyd | executable | |
MD5:A653F35D05D2F6DEBC5D34DADDD3DFA1 | SHA256:DB85F2F94D4994283E1055057372594538AE11020389D966E45607413851D9E9 | |||
| 6452 | E20240100020510_Anexo_1.doc.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\_socket.pyd | executable | |
MD5:819166054FEC07EFCD1062F13C2147EE | SHA256:E6DEB751039CD5424A139708475CE83F9C042D43E650765A716CB4A924B07E4F | |||
| 6452 | E20240100020510_Anexo_1.doc.exe | C:\Users\admin\AppData\Local\Temp\_MEI64522\_bz2.pyd | executable | |
MD5:86D1B2A9070CD7D52124126A357FF067 | SHA256:62173A8FADD4BF4DD71AB89EA718754AA31620244372F0C5BBBAE102E641A60E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
56
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5540 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5540 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6796 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | unknown | — | — | whitelisted |
6764 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4016 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4084 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6472 | E20240100020510_Anexo_1.doc.exe | 89.116.167.5:443 | — | UAB Bite Lietuva | US | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4016 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5336 | SearchApp.exe | 104.126.37.153:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5336 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
th.bing.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |