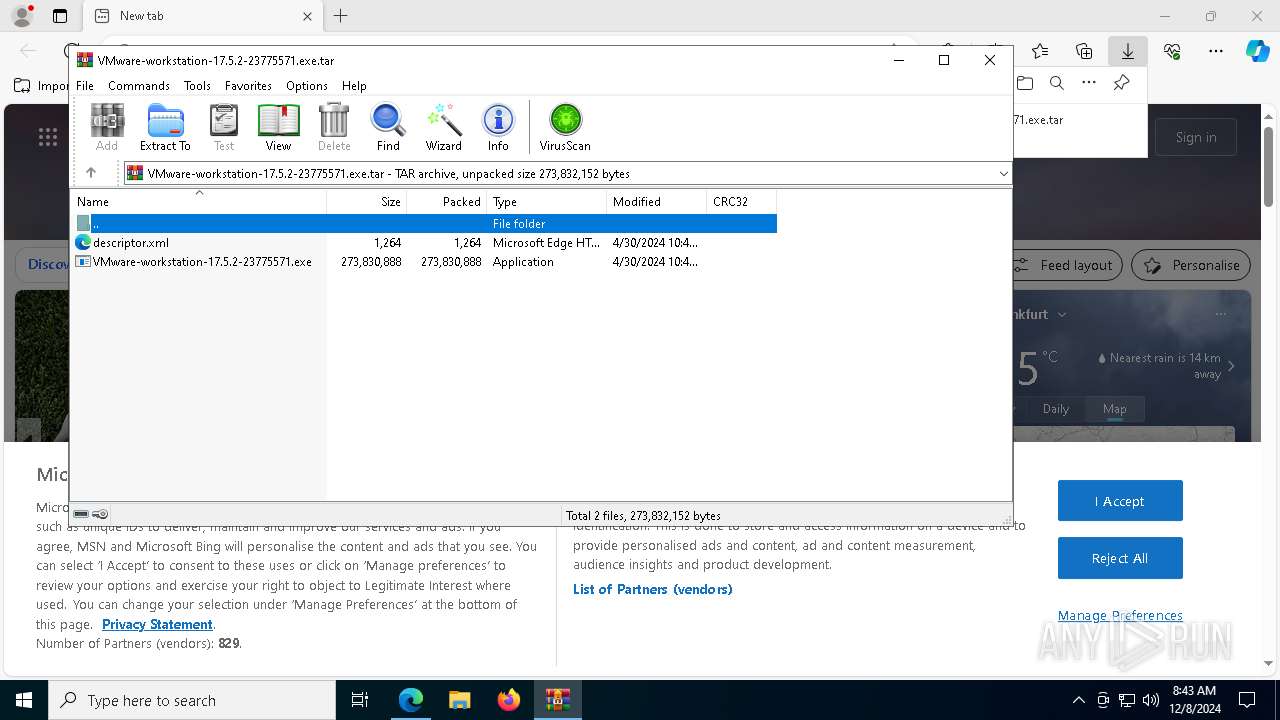
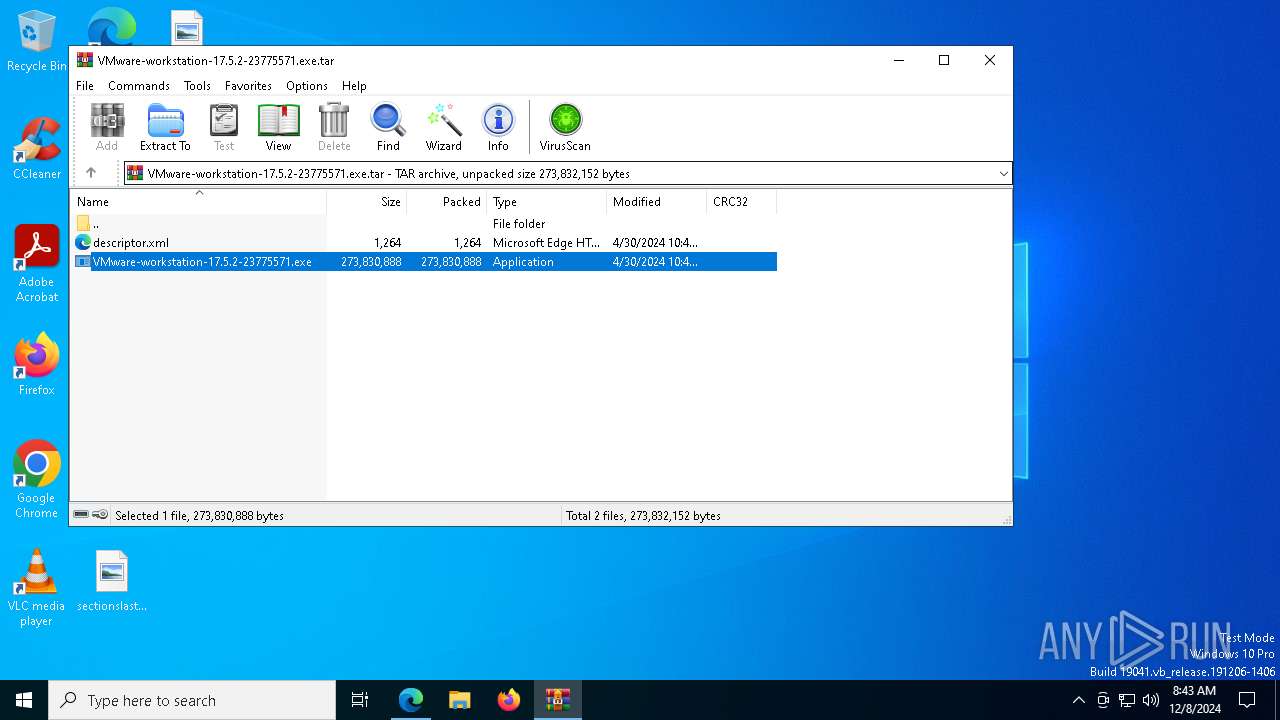
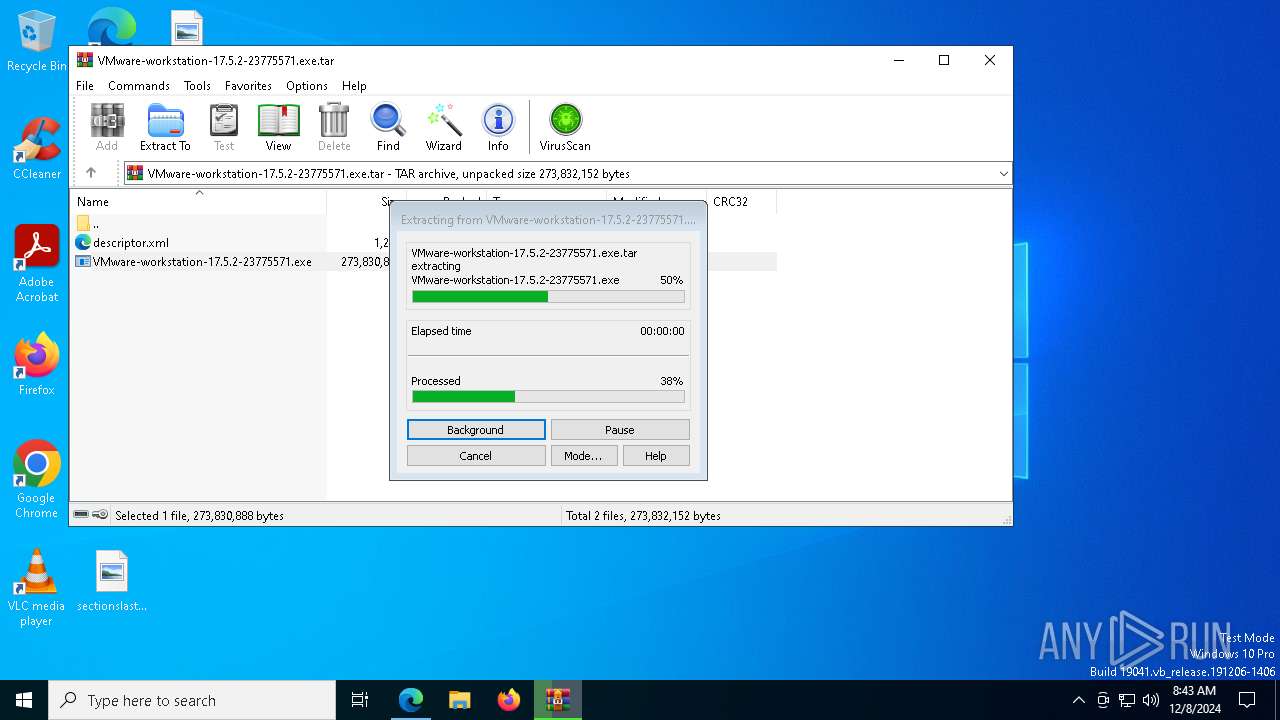
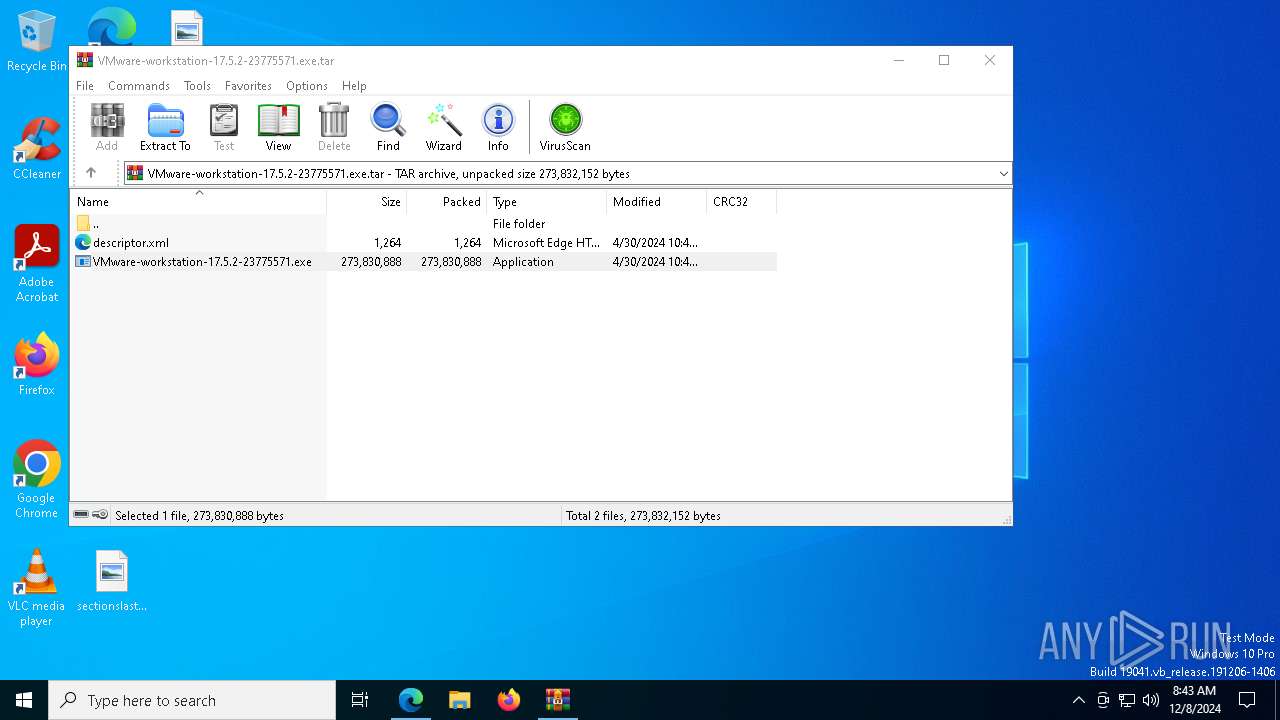
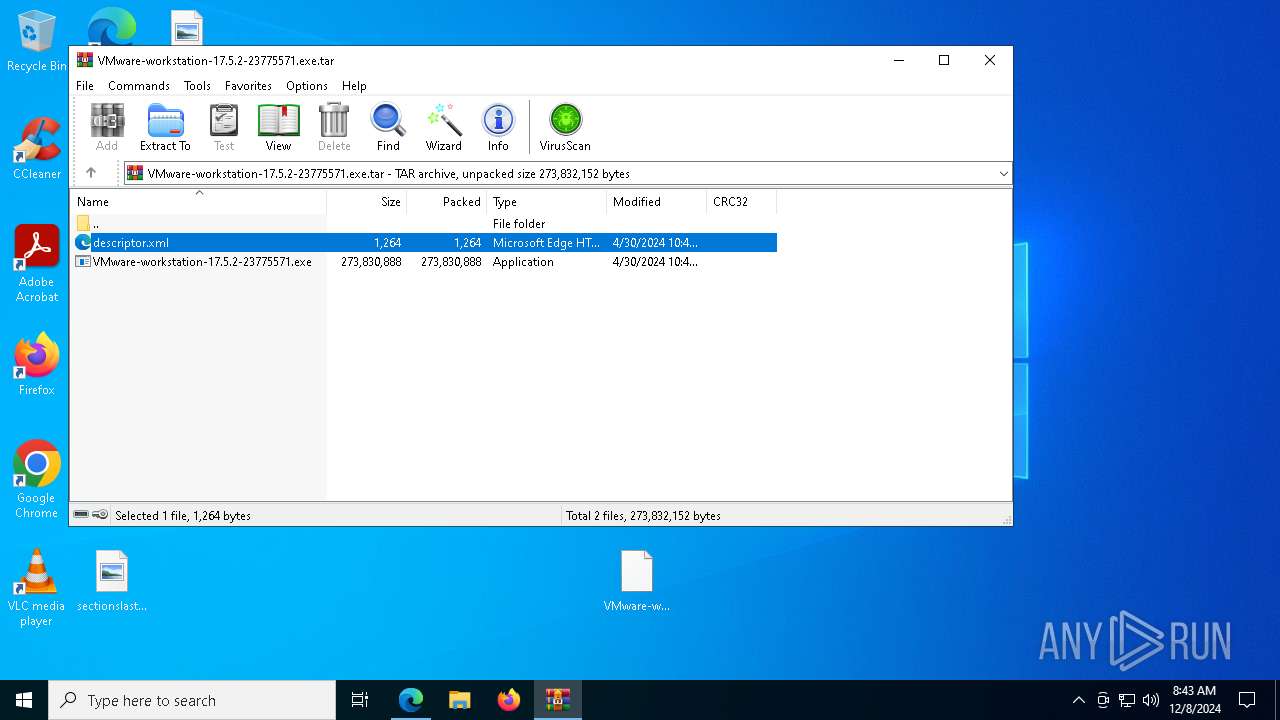
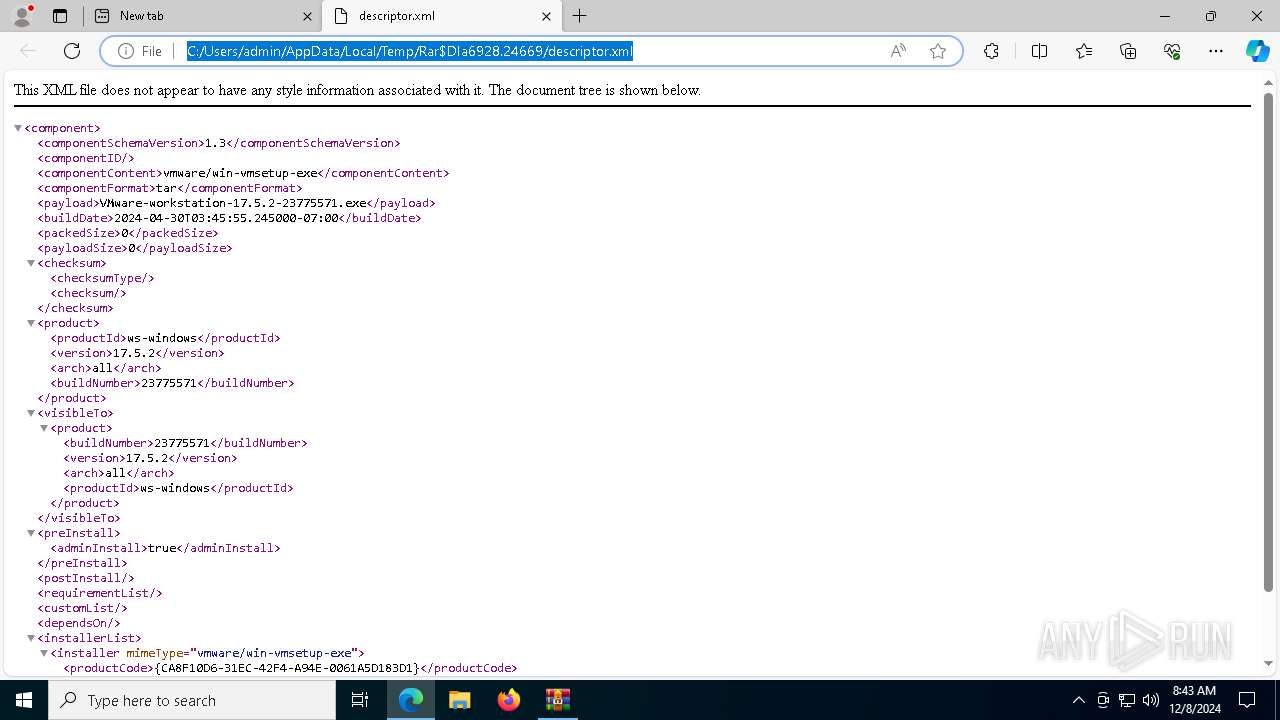
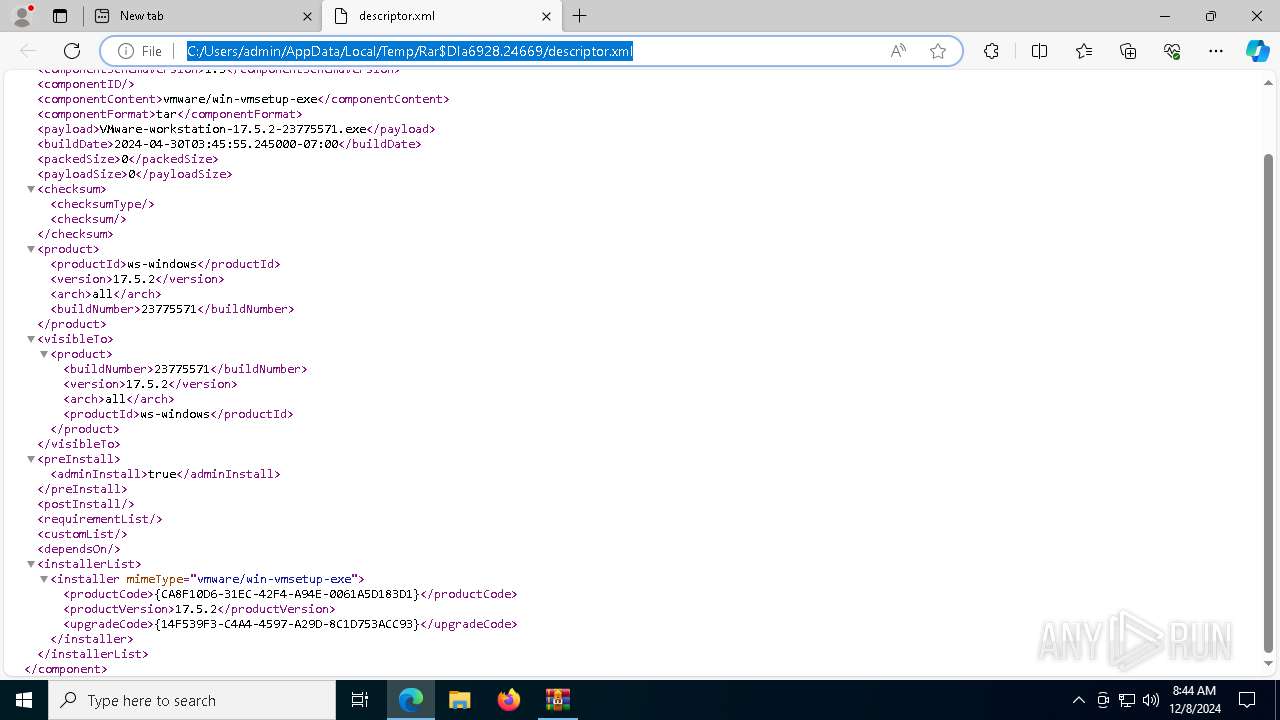
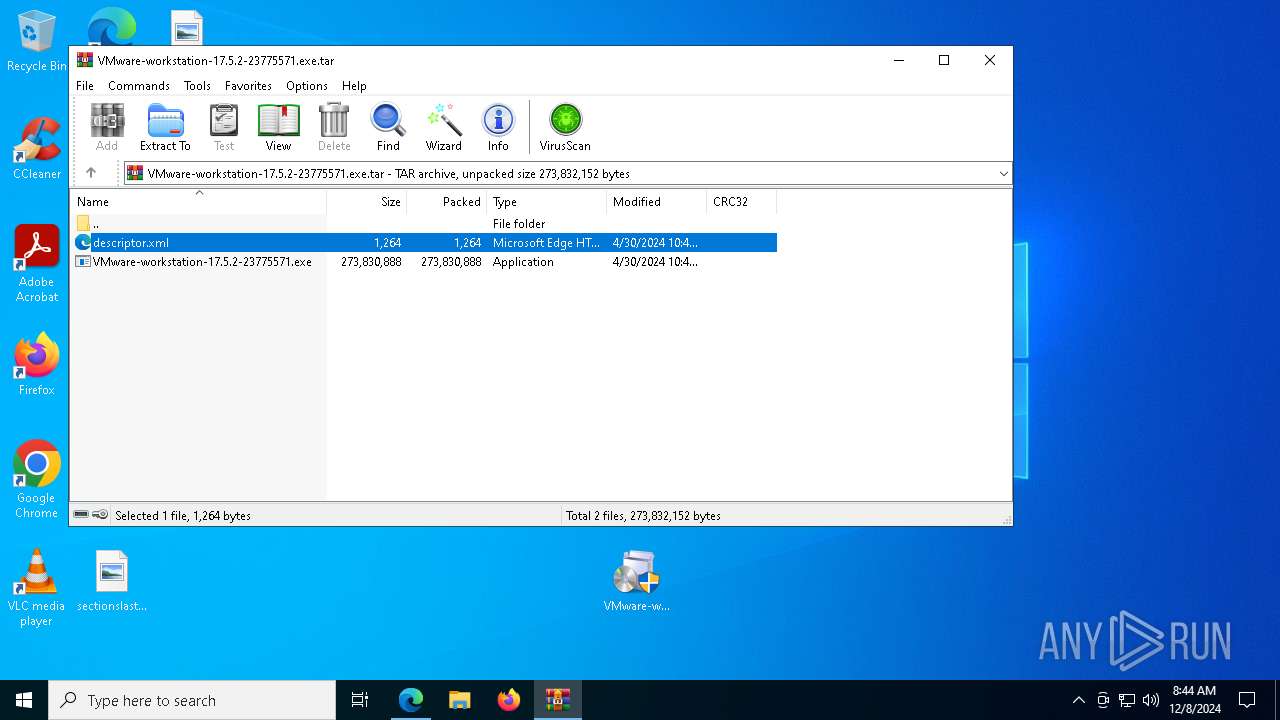
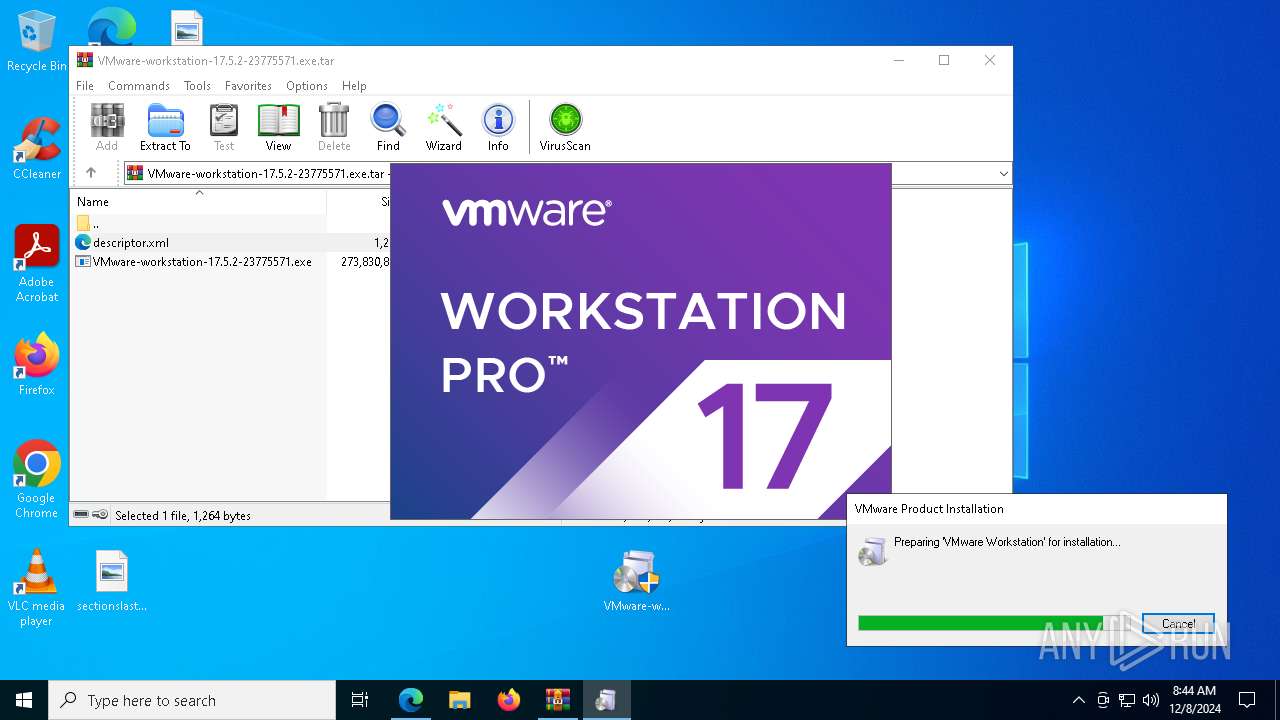
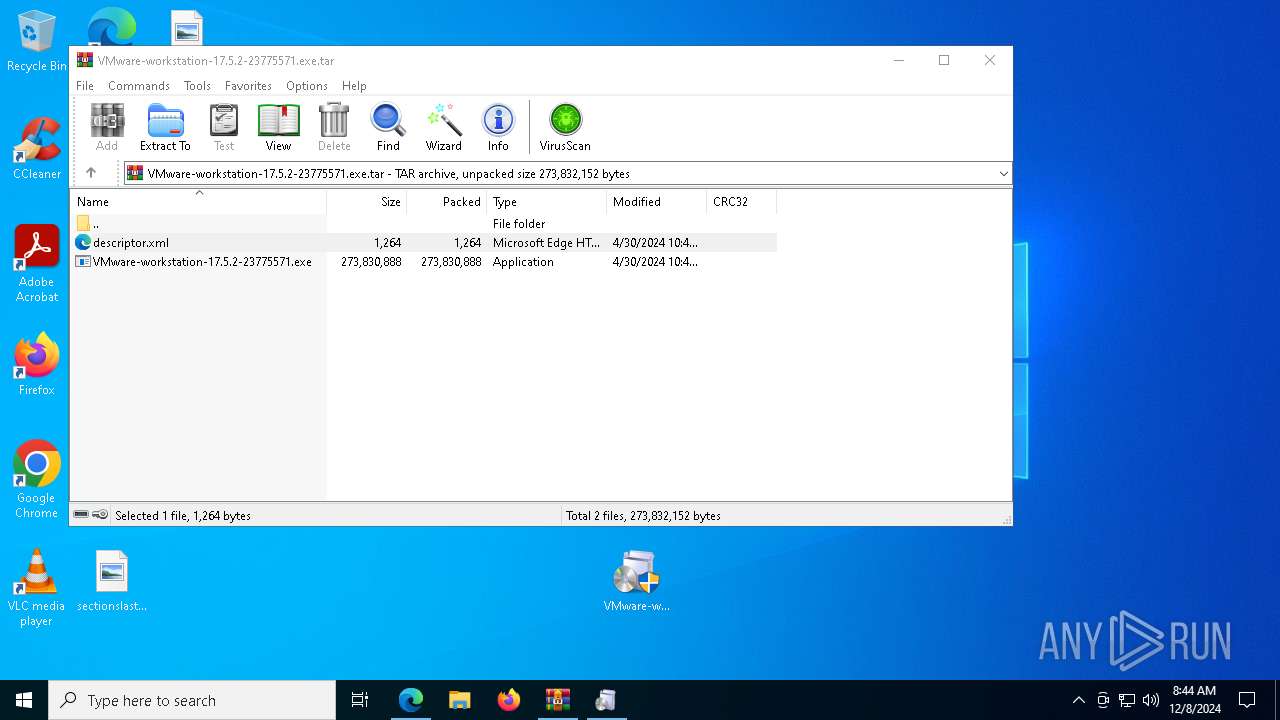
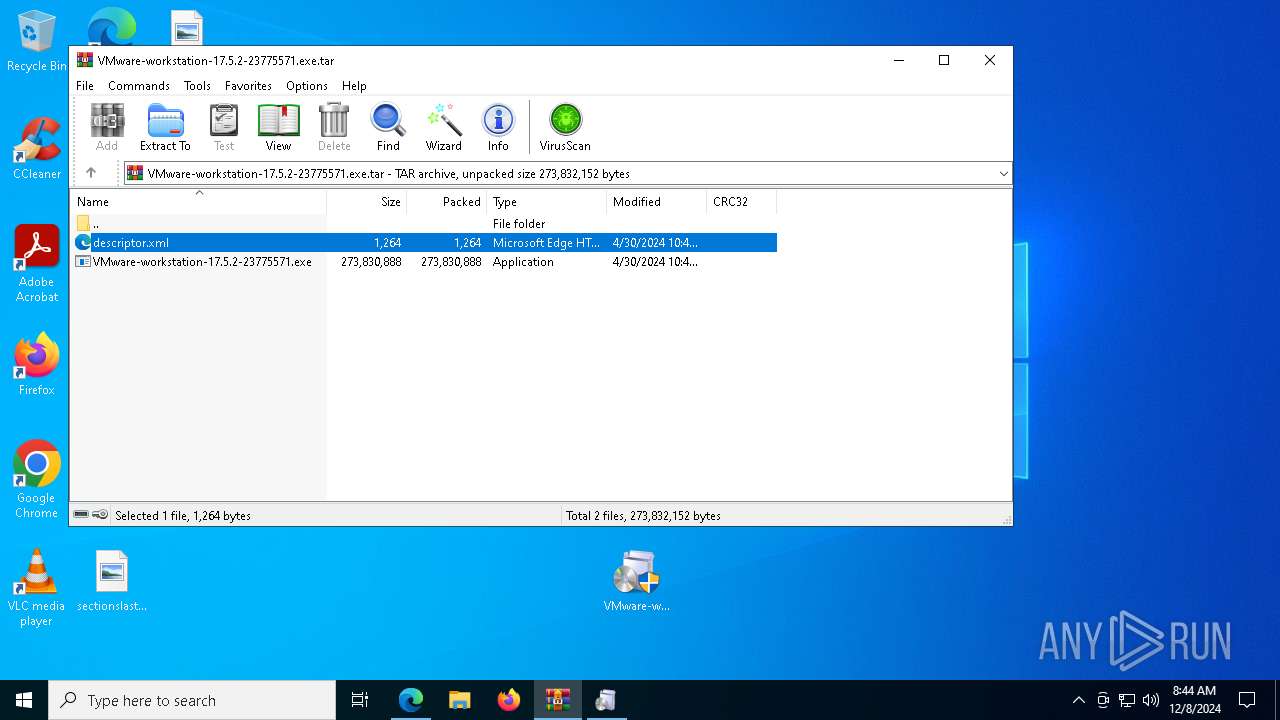
| URL: | https://softwareupdate.vmware.com/cds/vmw-desktop/ws/17.5.2/23775571/windows/core/VMware-workstation-17.5.2-23775571.exe.tar |
| Full analysis: | https://app.any.run/tasks/cfad881a-6b9c-4276-8b77-937a4de96b46 |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2024, 08:42:35 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 14627CE5CC9530708D8ADE53031455A8 |
| SHA1: | 0E16AA6CB9C245978DB05BE9C7AD1A824ECDA8D0 |
| SHA256: | 6FE93822AFEBFA6E551ADA1770A97C86AA3EA5A443C79C038F47D02DC635B534 |
| SSDEEP: | 3:N8HlL+AZ2BWKTo+OKSWRSsnK/kKfEvOWfK8LCnFnLAdu0n:22BWmO9sHLWeLCFLAdu0n |
MALICIOUS
Changes the autorun value in the registry
- VC_redist.x86.exe (PID: 8176)
- VC_redist.x64.exe (PID: 7372)
- msiexec.exe (PID: 6300)
- msiexec.exe (PID: 6192)
Reads a specific registry key of the VM
- msiexec.exe (PID: 1888)
- vnetlib64.exe (PID: 2680)
- msiexec.exe (PID: 6300)
- vnetlib64.exe (PID: 4624)
- vnetlib64.exe (PID: 4908)
- vnetlib64.exe (PID: 5456)
- vnetlib64.exe (PID: 7192)
- vnetlib64.exe (PID: 5340)
- vnetlib64.exe (PID: 1348)
- vnetlib64.exe (PID: 7048)
- vnetlib64.exe (PID: 3888)
- vnetlib64.exe (PID: 6160)
- vnetlib64.exe (PID: 7136)
- vnetlib64.exe (PID: 7488)
- vnetlib64.exe (PID: 2380)
- msiexec.exe (PID: 7660)
- vnetlib64.exe (PID: 7216)
- vnetlib64.exe (PID: 7264)
- vnetlib64.exe (PID: 7720)
- vnetlib64.exe (PID: 6896)
- vnetlib64.exe (PID: 6564)
- vnetlib64.exe (PID: 7148)
- vnetlib64.exe (PID: 6936)
- vnetlib64.exe (PID: 4444)
- vnetlib64.exe (PID: 8084)
- vnetlib64.exe (PID: 7916)
- vnetlib64.exe (PID: 6072)
- vnetlib64.exe (PID: 6248)
- vnetlib64.exe (PID: 6304)
- vnetlib64.exe (PID: 6928)
- vmnat.exe (PID: 8164)
- vnetlib64.exe (PID: 3992)
- drvinst.exe (PID: 7416)
- vnetlib64.exe (PID: 7760)
- drvinst.exe (PID: 7908)
- vnetlib64.exe (PID: 2132)
- msiexec.exe (PID: 6192)
- vmware-authd.exe (PID: 8008)
- vmware.exe (PID: 6304)
- vmware.exe (PID: 1404)
- vmware-tray.exe (PID: 6920)
- vmware.exe (PID: 6220)
Starts NET.EXE for service management
- net.exe (PID: 3812)
- msiexec.exe (PID: 1888)
- net.exe (PID: 2792)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6928)
- vcredist_x86.exe (PID: 6320)
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- vcredist_x64.exe (PID: 7268)
- vmware.exe (PID: 6304)
- vmware.exe (PID: 1404)
- vmware.exe (PID: 6220)
Starts a Microsoft application from unusual location
- vcredist_x86.exe (PID: 2800)
- vcredist_x86.exe (PID: 6320)
- VC_redist.x86.exe (PID: 8176)
- vcredist_x64.exe (PID: 7268)
- vcredist_x64.exe (PID: 4640)
- VC_redist.x64.exe (PID: 7372)
Process drops legitimate windows executable
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- vcredist_x86.exe (PID: 2800)
- vcredist_x86.exe (PID: 6320)
- vcredist_x64.exe (PID: 4640)
- vcredist_x64.exe (PID: 7268)
- msiexec.exe (PID: 6192)
- msiexec.exe (PID: 6300)
Executable content was dropped or overwritten
- vcredist_x86.exe (PID: 2800)
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- vcredist_x86.exe (PID: 6320)
- vcredist_x64.exe (PID: 4640)
- vcredist_x64.exe (PID: 7268)
- drvinst.exe (PID: 3992)
- vnetlib64.exe (PID: 4624)
Searches for installed software
- vcredist_x86.exe (PID: 6320)
- dllhost.exe (PID: 7084)
- vcredist_x64.exe (PID: 7268)
Starts itself from another location
- vcredist_x86.exe (PID: 6320)
- vcredist_x64.exe (PID: 7268)
Executes as Windows Service
- VSSVC.exe (PID: 7132)
- vmnat.exe (PID: 8164)
- vmnetdhcp.exe (PID: 1228)
- vmware-usbarbitrator64.exe (PID: 6760)
- vmware-authd.exe (PID: 8008)
Checks Windows Trust Settings
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- msiexec.exe (PID: 6300)
- drvinst.exe (PID: 3992)
- vnetlib64.exe (PID: 4624)
- drvinst.exe (PID: 4300)
- vnetlib64.exe (PID: 6304)
- drvinst.exe (PID: 3632)
- drvinst.exe (PID: 7416)
- drvinst.exe (PID: 7908)
- vnetlib64.exe (PID: 2132)
- msiexec.exe (PID: 6192)
Reads the Windows owner or organization settings
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- msiexec.exe (PID: 6300)
Executes application which crashes
- msiexec.exe (PID: 7824)
Process checks presence of unattended files
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- msiexec.exe (PID: 6300)
Drops 7-zip archiver for unpacking
- msiexec.exe (PID: 6300)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 6300)
- drvinst.exe (PID: 3992)
- vnetlib64.exe (PID: 4624)
- msiexec.exe (PID: 6192)
Creates files in the driver directory
- drvinst.exe (PID: 3992)
- vnetlib64.exe (PID: 4624)
- vnetlib64.exe (PID: 6072)
- vnetlib64.exe (PID: 6304)
- drvinst.exe (PID: 4300)
- drvinst.exe (PID: 3632)
- drvinst.exe (PID: 7416)
- vnetlib64.exe (PID: 2132)
- drvinst.exe (PID: 5316)
- drvinst.exe (PID: 3536)
- msiexec.exe (PID: 6192)
Creates or modifies Windows services
- vnetlib64.exe (PID: 4624)
- vnetlib64.exe (PID: 6072)
- vnetlib64.exe (PID: 6304)
- drvinst.exe (PID: 7416)
- vnetlib64.exe (PID: 2132)
- drvinst.exe (PID: 7908)
- drvinst.exe (PID: 3536)
The process checks if it is being run in the virtual environment
- msiexec.exe (PID: 7660)
- vnetlib64.exe (PID: 7916)
- vnetlib64.exe (PID: 6304)
- drvinst.exe (PID: 7416)
- vnetlib64.exe (PID: 2132)
- drvinst.exe (PID: 3536)
Creates/Modifies COM task schedule object
- vnetlib64.exe (PID: 6072)
- msiexec.exe (PID: 1888)
Starts NET.EXE for network exploration
- msiexec.exe (PID: 1888)
- net.exe (PID: 2792)
Reads Internet Explorer settings
- vmware.exe (PID: 6304)
- vmware.exe (PID: 6220)
- vmware.exe (PID: 1404)
Reads Microsoft Outlook installation path
- vmware.exe (PID: 6304)
INFO
The process uses the downloaded file
- iexplore.exe (PID: 1876)
- msedge.exe (PID: 6740)
- msedge.exe (PID: 6336)
- WinRAR.exe (PID: 6928)
- vcredist_x86.exe (PID: 6320)
- vcredist_x64.exe (PID: 7268)
Checks supported languages
- identity_helper.exe (PID: 7836)
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- vcredist_x86.exe (PID: 6320)
- vcredist_x86.exe (PID: 2800)
- VC_redist.x86.exe (PID: 8176)
- vcredist_x64.exe (PID: 4640)
- vcredist_x64.exe (PID: 7268)
- msiexec.exe (PID: 6300)
- msiexec.exe (PID: 7824)
- msiexec.exe (PID: 7980)
- msiexec.exe (PID: 1888)
- msiexec.exe (PID: 7368)
- msiexec.exe (PID: 6192)
- msiexec.exe (PID: 7660)
- vnetlib64.exe (PID: 6928)
- VC_redist.x64.exe (PID: 7372)
- vnetlib64.exe (PID: 4624)
- vnetlib64.exe (PID: 5456)
- vnetlib64.exe (PID: 7192)
- vnetlib64.exe (PID: 5340)
- vnetlib64.exe (PID: 1348)
- vnetlib64.exe (PID: 3888)
- vnetlib64.exe (PID: 6160)
- vnetlib64.exe (PID: 7136)
- vnetlib64.exe (PID: 7048)
- vnetlib64.exe (PID: 7488)
- vnetlib64.exe (PID: 7216)
- vnetlib64.exe (PID: 7264)
- vnetlib64.exe (PID: 7720)
- vnetlib64.exe (PID: 2380)
- vnetlib64.exe (PID: 6896)
- vnetlib64.exe (PID: 7148)
- vnetlib64.exe (PID: 6564)
- vnetlib64.exe (PID: 6936)
- drvinst.exe (PID: 3992)
- vnetlib64.exe (PID: 2680)
- vnetlib64.exe (PID: 6248)
- vnetlib64.exe (PID: 4444)
- vnetlib64.exe (PID: 8084)
- vnetlib64.exe (PID: 7916)
- vnetlib64.exe (PID: 6072)
- drvinst.exe (PID: 4300)
- vnetlib64.exe (PID: 6304)
- vmnat.exe (PID: 8164)
- vnetlib64.exe (PID: 3992)
- drvinst.exe (PID: 3632)
- vnetlib64.exe (PID: 4908)
- drvinst.exe (PID: 7416)
- vnetlib64.exe (PID: 7760)
- drvinst.exe (PID: 7908)
- vnetlib64.exe (PID: 2132)
- drvinst.exe (PID: 5316)
- vmware-usbarbitrator64.exe (PID: 6760)
- drvinst.exe (PID: 3536)
- vmware-authd.exe (PID: 8008)
- vmware.exe (PID: 6304)
- vmware.exe (PID: 1404)
- vmware.exe (PID: 6220)
- vmware-tray.exe (PID: 6920)
- vmnetdhcp.exe (PID: 1228)
Reads the computer name
- identity_helper.exe (PID: 7836)
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- vcredist_x86.exe (PID: 6320)
- VC_redist.x86.exe (PID: 8176)
- vcredist_x64.exe (PID: 7268)
- VC_redist.x64.exe (PID: 7372)
- msiexec.exe (PID: 6300)
- msiexec.exe (PID: 7824)
- msiexec.exe (PID: 1888)
- msiexec.exe (PID: 7368)
- msiexec.exe (PID: 6192)
- msiexec.exe (PID: 7660)
- vnetlib64.exe (PID: 2680)
- vnetlib64.exe (PID: 6928)
- drvinst.exe (PID: 3992)
- vnetlib64.exe (PID: 4908)
- msiexec.exe (PID: 7980)
- vnetlib64.exe (PID: 4624)
- vnetlib64.exe (PID: 7192)
- vnetlib64.exe (PID: 5456)
- vnetlib64.exe (PID: 5340)
- vnetlib64.exe (PID: 1348)
- vnetlib64.exe (PID: 3888)
- vnetlib64.exe (PID: 7048)
- vnetlib64.exe (PID: 6160)
- vnetlib64.exe (PID: 7136)
- vnetlib64.exe (PID: 7488)
- vnetlib64.exe (PID: 7216)
- vnetlib64.exe (PID: 2380)
- vnetlib64.exe (PID: 7264)
- vnetlib64.exe (PID: 7720)
- vnetlib64.exe (PID: 6896)
- vnetlib64.exe (PID: 7148)
- vnetlib64.exe (PID: 6936)
- vnetlib64.exe (PID: 6564)
- vnetlib64.exe (PID: 4444)
- vnetlib64.exe (PID: 6248)
- vnetlib64.exe (PID: 8084)
- vnetlib64.exe (PID: 7916)
- vnetlib64.exe (PID: 6072)
- vnetlib64.exe (PID: 6304)
- drvinst.exe (PID: 4300)
- vmnat.exe (PID: 8164)
- vmnetdhcp.exe (PID: 1228)
- vnetlib64.exe (PID: 3992)
- drvinst.exe (PID: 3632)
- drvinst.exe (PID: 7416)
- vnetlib64.exe (PID: 7760)
- drvinst.exe (PID: 7908)
- vnetlib64.exe (PID: 2132)
- drvinst.exe (PID: 5316)
- drvinst.exe (PID: 3536)
- vmware-usbarbitrator64.exe (PID: 6760)
- vmware-authd.exe (PID: 8008)
- vmware.exe (PID: 6304)
- vmware.exe (PID: 1404)
- vmware.exe (PID: 6220)
Sends debugging messages
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- vmnat.exe (PID: 8164)
- vmnetdhcp.exe (PID: 1228)
- vmware-usbarbitrator64.exe (PID: 6760)
- vmware.exe (PID: 6304)
- vmware-tray.exe (PID: 6920)
- vmware.exe (PID: 1404)
- vmware.exe (PID: 6220)
Application launched itself
- msedge.exe (PID: 6336)
- msiexec.exe (PID: 6300)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6336)
- WinRAR.exe (PID: 6928)
Create files in a temporary directory
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- vcredist_x86.exe (PID: 6320)
- vcredist_x64.exe (PID: 7268)
- msiexec.exe (PID: 6192)
- vmware.exe (PID: 1404)
- vmware.exe (PID: 6220)
- vmware.exe (PID: 6304)
Reads Environment values
- identity_helper.exe (PID: 7836)
- vmware-usbarbitrator64.exe (PID: 6760)
Process checks computer location settings
- vcredist_x86.exe (PID: 6320)
- vcredist_x64.exe (PID: 7268)
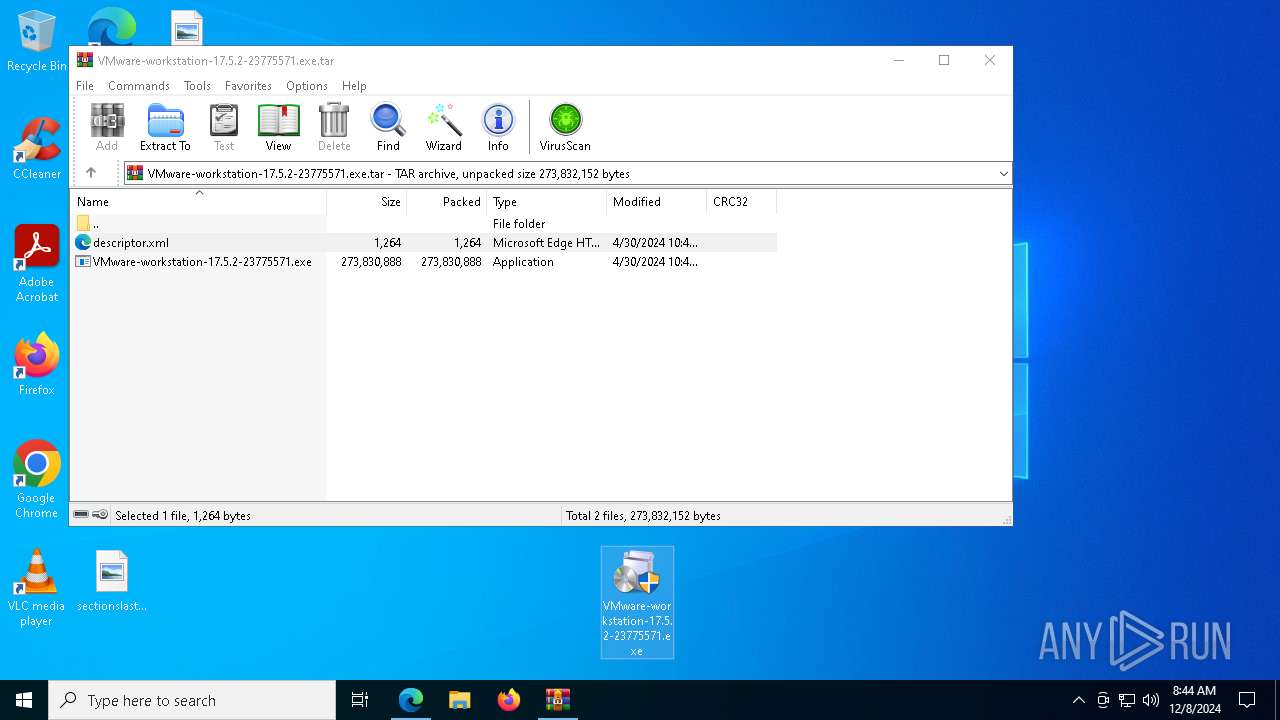
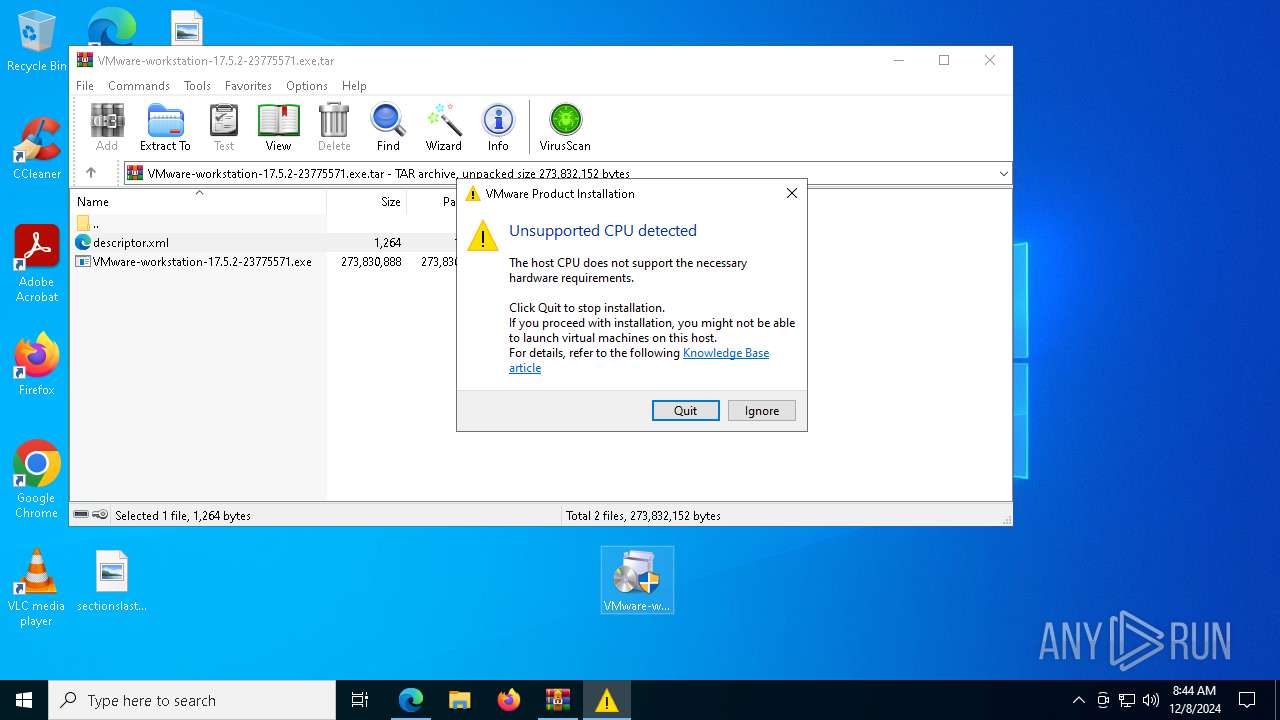
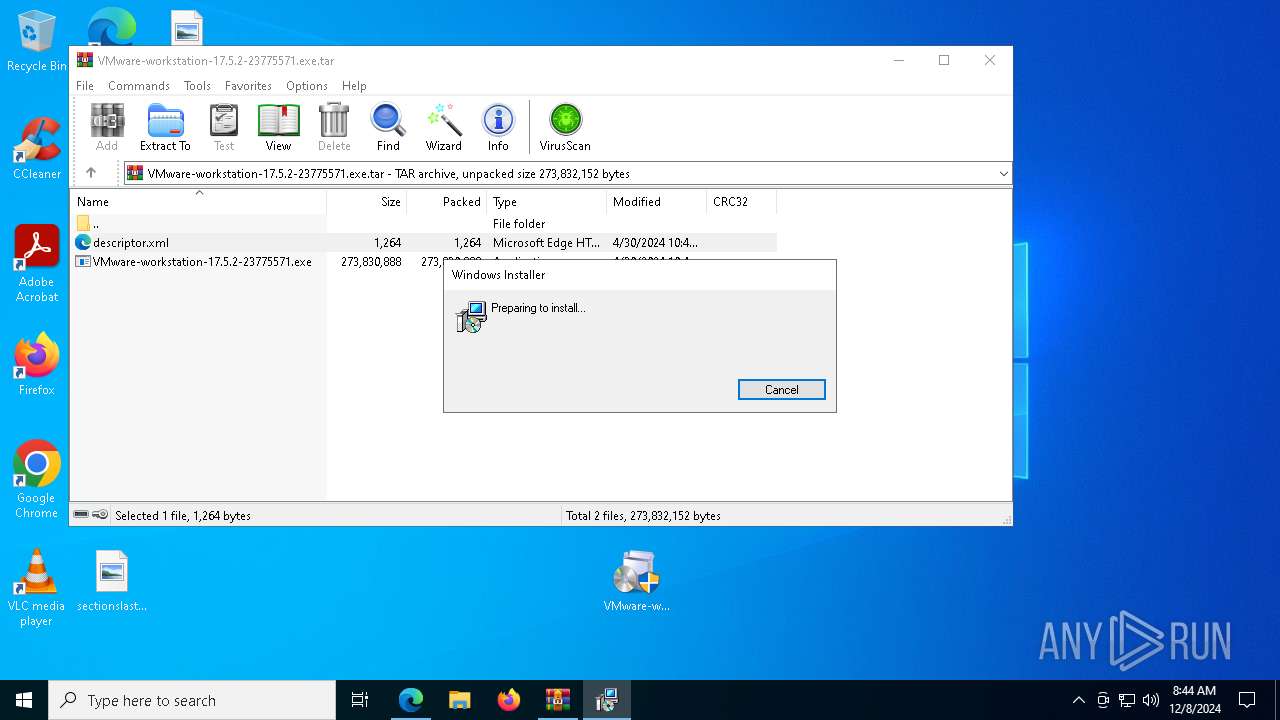
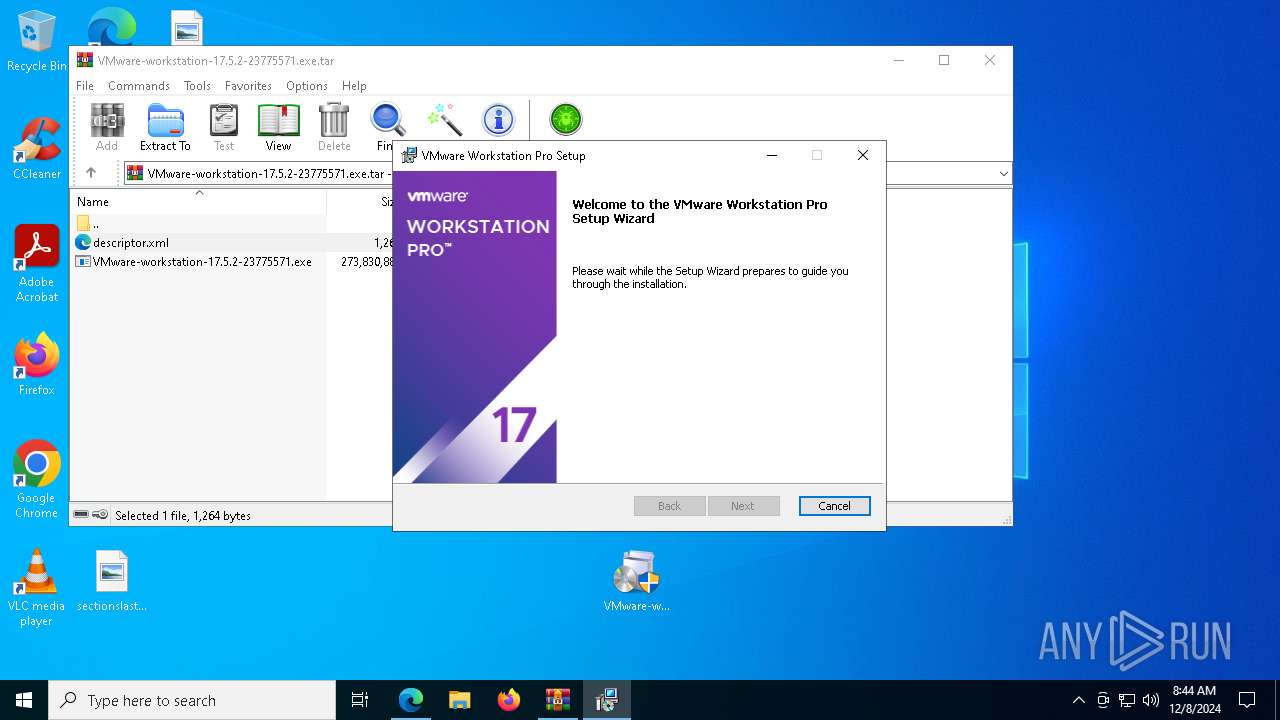
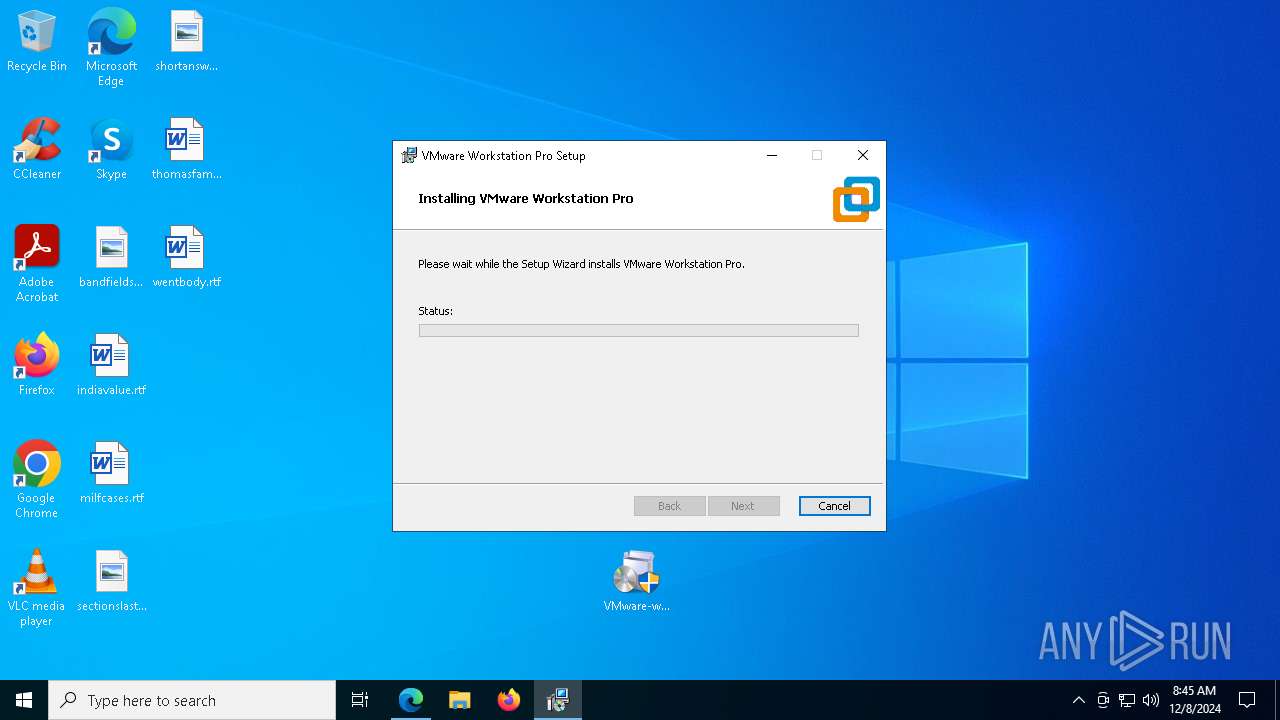
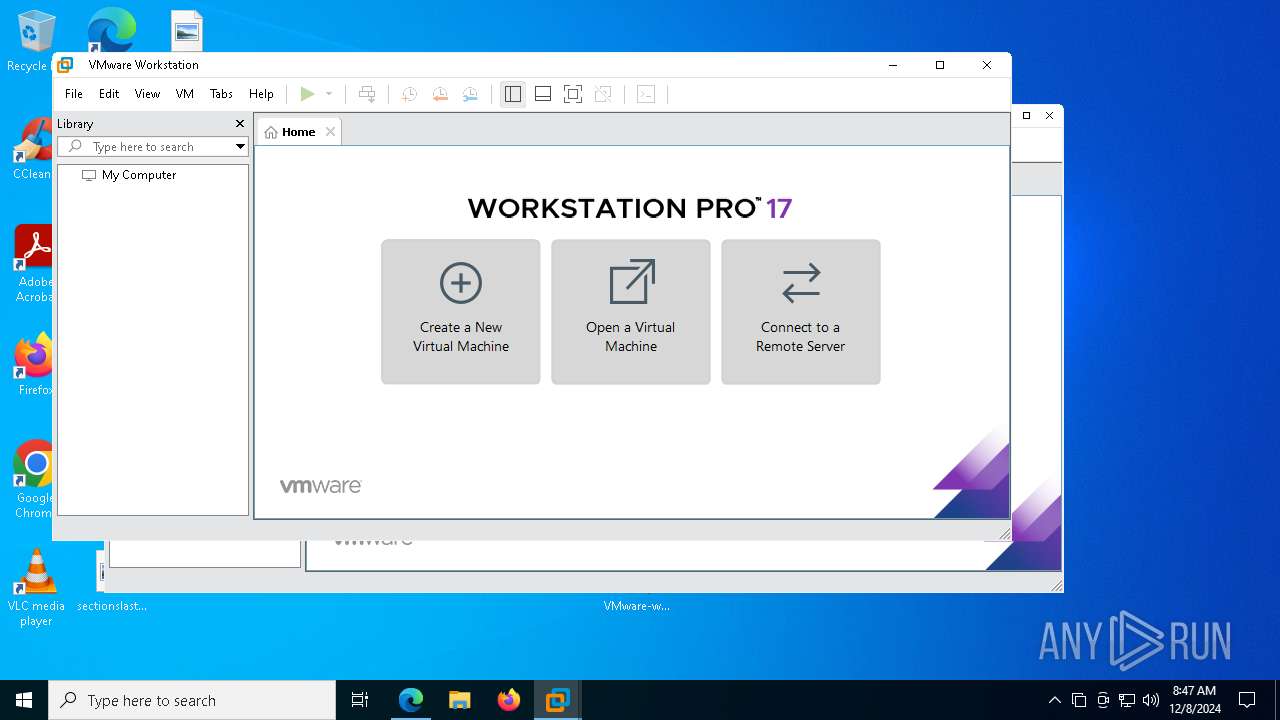
Manual execution by a user
- VMware-workstation-17.5.2-23775571.exe (PID: 2008)
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- vmware.exe (PID: 6304)
- vmware.exe (PID: 1404)
- vmware.exe (PID: 6220)
Executable content was dropped or overwritten
- msedge.exe (PID: 4984)
- msiexec.exe (PID: 6300)
- msiexec.exe (PID: 6192)
- msiexec.exe (PID: 7660)
Manages system restore points
- SrTasks.exe (PID: 7140)
- SrTasks.exe (PID: 6876)
- SrTasks.exe (PID: 7992)
Creates files or folders in the user directory
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- WerFault.exe (PID: 6184)
- vmware.exe (PID: 6304)
- vmware.exe (PID: 6220)
- vmware.exe (PID: 1404)
Reads the software policy settings
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- msiexec.exe (PID: 6300)
- drvinst.exe (PID: 3992)
- vnetlib64.exe (PID: 4624)
- drvinst.exe (PID: 4300)
- vnetlib64.exe (PID: 6304)
- drvinst.exe (PID: 7416)
- drvinst.exe (PID: 7908)
- vnetlib64.exe (PID: 2132)
- msiexec.exe (PID: 6192)
- drvinst.exe (PID: 5316)
- vmware.exe (PID: 6304)
- vmware.exe (PID: 1404)
- vmware.exe (PID: 6220)
- drvinst.exe (PID: 3632)
Checks proxy server information
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- vmware.exe (PID: 6304)
- vmware.exe (PID: 1404)
Reads the machine GUID from the registry
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- msiexec.exe (PID: 6300)
- msiexec.exe (PID: 7660)
- drvinst.exe (PID: 3992)
- vnetlib64.exe (PID: 4624)
- drvinst.exe (PID: 4300)
- vnetlib64.exe (PID: 6304)
- drvinst.exe (PID: 3632)
- drvinst.exe (PID: 7416)
- drvinst.exe (PID: 7908)
- drvinst.exe (PID: 5316)
- vnetlib64.exe (PID: 2132)
- msiexec.exe (PID: 6192)
- vmware.exe (PID: 6304)
- vmware.exe (PID: 1404)
- vmware.exe (PID: 6220)
Creates files in the program directory
- VMware-workstation-17.5.2-23775571.exe (PID: 7896)
- vmware-usbarbitrator64.exe (PID: 6760)
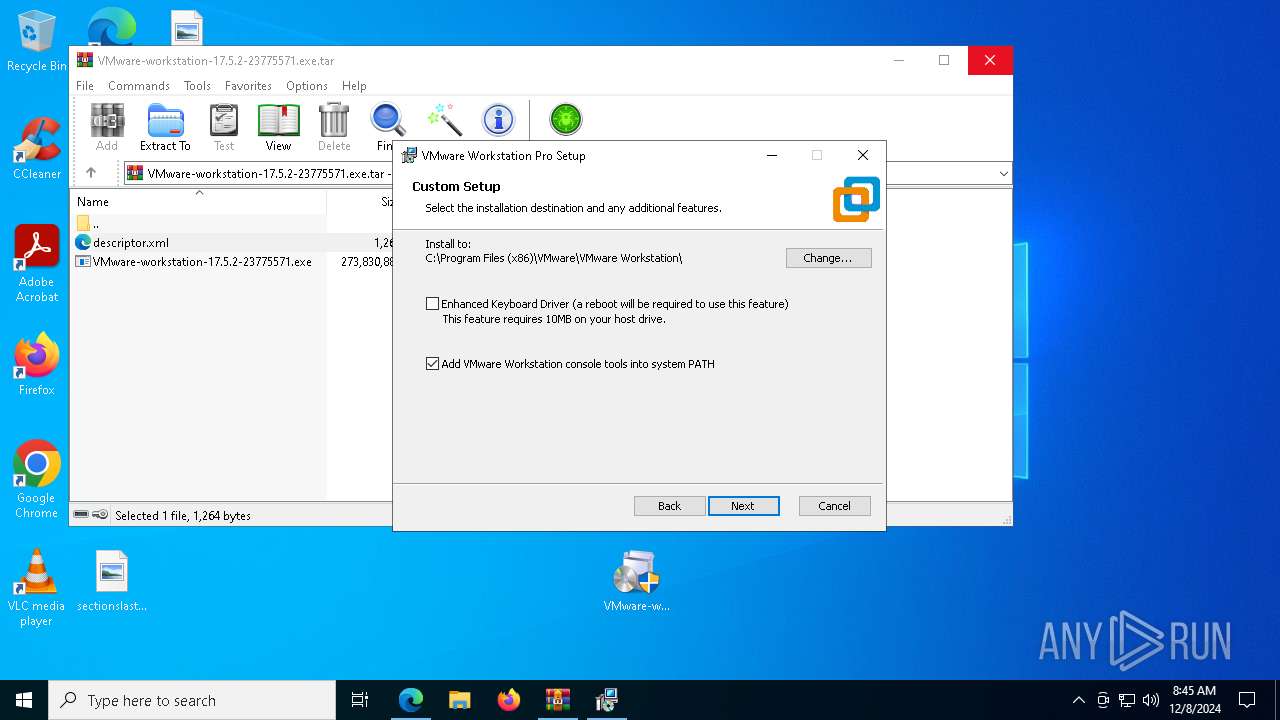
Creates a software uninstall entry
- msiexec.exe (PID: 6300)
Creates or modifies Windows services
- msiexec.exe (PID: 6192)
Reads CPU info
- vmware.exe (PID: 1404)
- vmware.exe (PID: 6304)
- vmware.exe (PID: 6220)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
285
Monitored processes
135
Malicious processes
24
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=32 --mojo-platform-channel-handle=6948 --field-trial-handle=2312,i,13299618522981046413,4780255963041059798,262144 --variations-seed-version /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 640 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Exit code: 0 Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1228 | C:\WINDOWS\SysWOW64\vmnetdhcp.exe | C:\Windows\SysWOW64\vmnetdhcp.exe | services.exe | ||||||||||||
User: SYSTEM Company: VMware, Inc. Integrity Level: SYSTEM Description: VMware VMnet DHCP service Version: 17.5.2 build-23775571 Modules
| |||||||||||||||
| 1304 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7632 --field-trial-handle=2312,i,13299618522981046413,4780255963041059798,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1348 | "C:\Program Files (x86)\VMware\VMware Workstation\vnetlib64.exe" -- remove adapter vmnet4 | C:\Program Files (x86)\VMware\VMware Workstation\vnetlib64.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: VMware, Inc. Integrity Level: SYSTEM Description: VMware network install library executable Exit code: 4 Version: 17.5.2 build-23775571 Modules
| |||||||||||||||
| 1404 | "C:\Program Files (x86)\VMware\VMware Workstation\vmware.exe" | C:\Program Files (x86)\VMware\VMware Workstation\vmware.exe | explorer.exe | ||||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware Workstation Version: 17.5.2 build-23775571 | |||||||||||||||
| 1544 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1876 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://softwareupdate.vmware.com/cds/vmw-desktop/ws/17.5.2/23775571/windows/core/VMware-workstation-17.5.2-23775571.exe.tar" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1888 | C:\Windows\syswow64\MsiExec.exe -Embedding 70C29B900B43836FF4C0A5029F3AFEF0 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2008 | "C:\Users\admin\Desktop\VMware-workstation-17.5.2-23775571.exe" | C:\Users\admin\Desktop\VMware-workstation-17.5.2-23775571.exe | — | explorer.exe | |||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware installation launcher Exit code: 3221226540 Version: 17.5.2 Modules
| |||||||||||||||
Total events
85 720
Read events
83 928
Write events
1 667
Delete events
125
Modification events
| (PID) Process: | (6336) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4E57A28354872F00 | |||
| (PID) Process: | (6336) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8673AA8354872F00 | |||
| (PID) Process: | (6336) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328350 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {32A6DCF3-C348-4B9F-8403-7F6D1470ED1D} | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1876) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (6336) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
Executable files
263
Suspicious files
1 353
Text files
809
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6336 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF135826.TMP | — | |
MD5:— | SHA256:— | |||
| 6336 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6336 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF135826.TMP | — | |
MD5:— | SHA256:— | |||
| 6336 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6336 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF135826.TMP | — | |
MD5:— | SHA256:— | |||
| 6336 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6336 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF135835.TMP | — | |
MD5:— | SHA256:— | |||
| 6336 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6336 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF135845.TMP | — | |
MD5:— | SHA256:— | |||
| 6336 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
141
DNS requests
148
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2736 | svchost.exe | GET | 200 | 2.16.164.9:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7896 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5268 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1733655554&P2=404&P3=2&P4=TrGLEBJ4qtY43hxO2iymROXXIjYRf4MfqmkJJ0Bplsf%2b6%2fQ5colnIZSz7Lu90OSSn0MmK7xctpPQafF4gkcyuA%3d%3d | unknown | — | — | whitelisted |
5268 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1733655554&P2=404&P3=2&P4=TrGLEBJ4qtY43hxO2iymROXXIjYRf4MfqmkJJ0Bplsf%2b6%2fQ5colnIZSz7Lu90OSSn0MmK7xctpPQafF4gkcyuA%3d%3d | unknown | — | — | whitelisted |
6580 | msedge.exe | GET | 304 | 2.23.197.184:80 | http://x1.i.lencr.org/ | unknown | — | — | whitelisted |
5268 | svchost.exe | GET | 206 | 199.232.210.172:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/c08f1970-45bc-4dbe-8166-4ecef7a1f617?P1=1733655554&P2=404&P3=2&P4=TrGLEBJ4qtY43hxO2iymROXXIjYRf4MfqmkJJ0Bplsf%2b6%2fQ5colnIZSz7Lu90OSSn0MmK7xctpPQafF4gkcyuA%3d%3d | unknown | — | — | whitelisted |
6580 | msedge.exe | GET | 304 | 2.23.197.184:80 | http://r3.i.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2736 | svchost.exe | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.16.164.9:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
2736 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.135:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
softwareupdate.vmware.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6580 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6580 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
6580 | msedge.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
6580 | msedge.exe | Misc activity | SUSPICIOUS [ANY.RUN] Tracking Service (.popin .cc) |
Process | Message |
|---|---|
VMware-workstation-17.5.2-23775571.exe | Start Pre-load DLLs.
|
VMware-workstation-17.5.2-23775571.exe | Win32U_GetFileAttributes: GetFileAttributesExW("C:\Users\admin\Desktop\1033.bmp", ...) failed, error: 2
|
VMware-workstation-17.5.2-23775571.exe | Win32U_GetFileAttributes: GetFileAttributesExW("C:\Users\admin\AppData\Local\Temp\{CA8F10D6-31EC-42F4-A94E-0061A5D183D1}~setup\", ...) failed, error: 2
|
vmnat.exe | CodeSet_Init: no ICU
|
vmnetdhcp.exe | CodeSet_Init: no ICU
|
vmware-usbarbitrator64.exe | CodeSet_Init: no ICU
|
vmware.exe | VMListReg::Listener - Initial registry scan completed. |
vmware-tray.exe | VMListReg::Listener - Initial registry scan completed. |
vmware.exe | VMListReg::Listener - Initial registry scan completed. |
vmware.exe | VMListReg::Listener - Initial registry scan completed. |