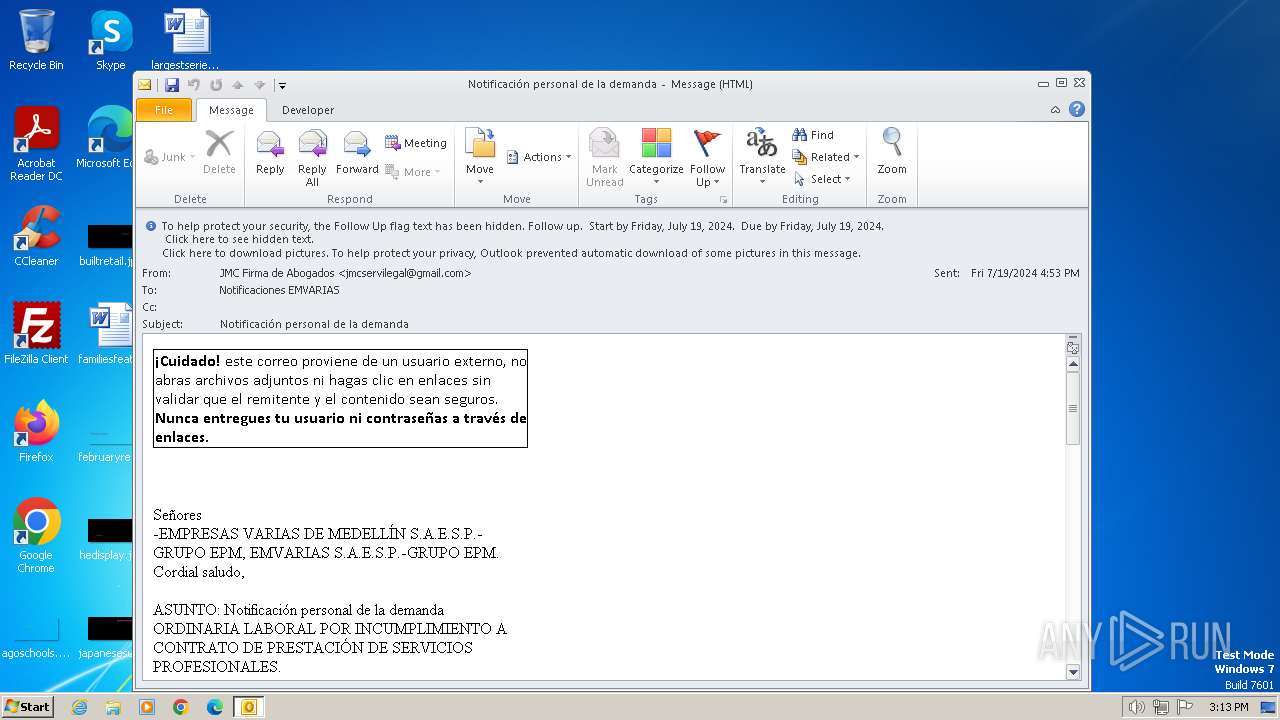
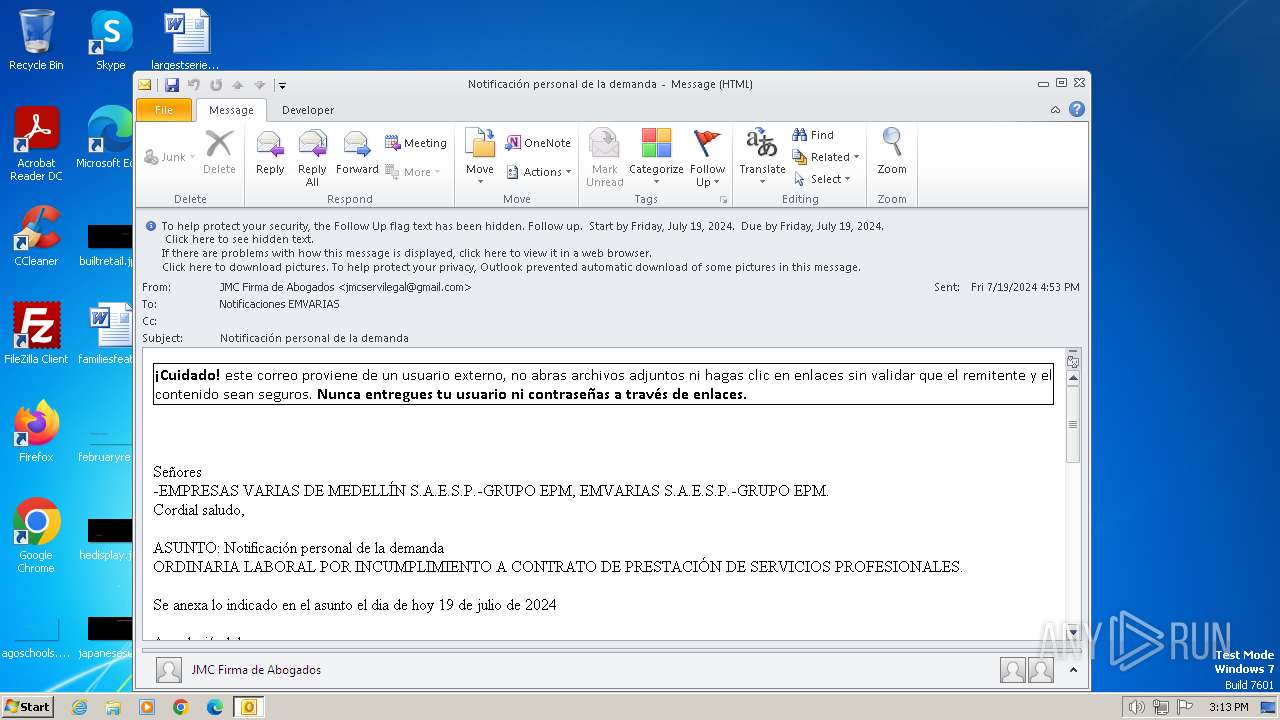
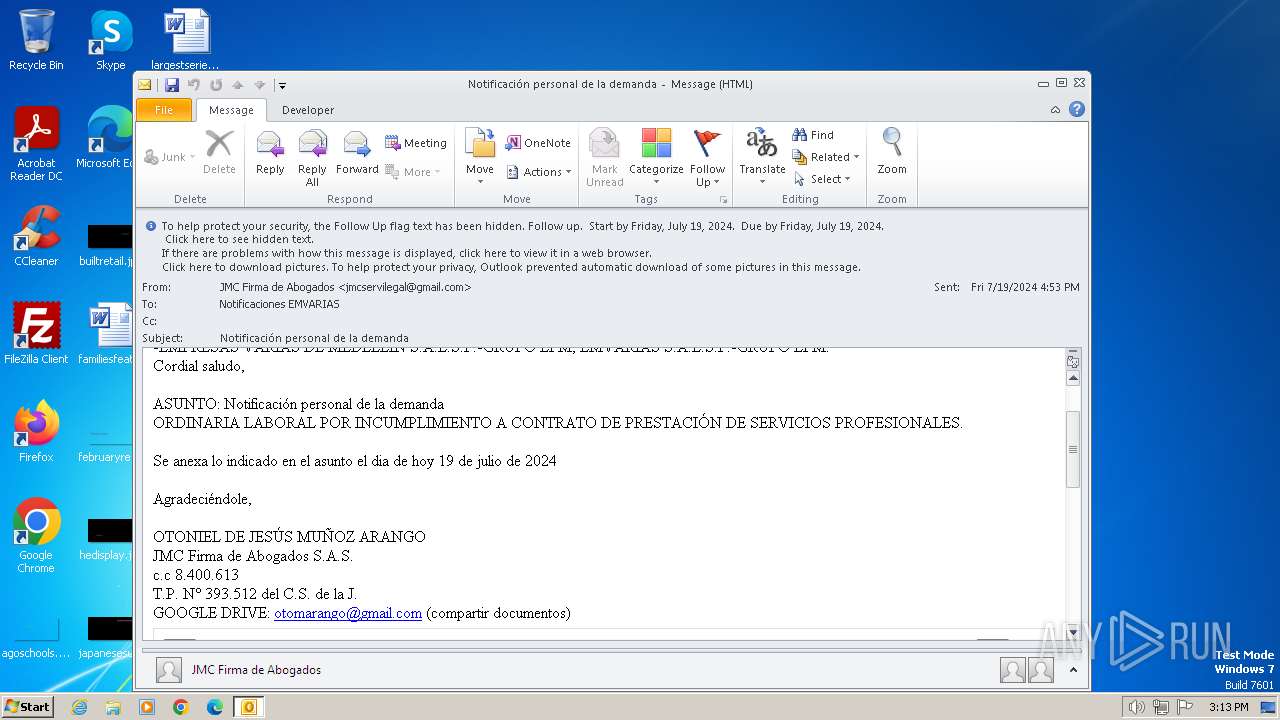
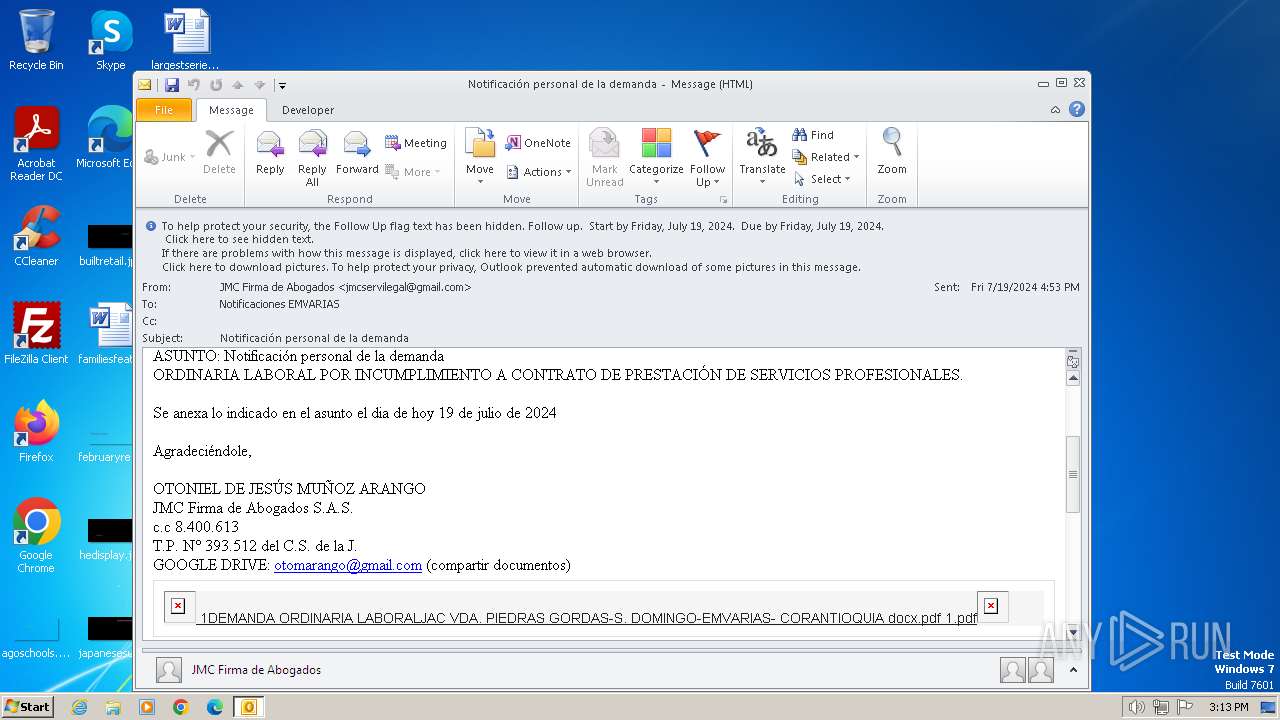
| File name: | Notificación personal de la demanda.msg |
| Full analysis: | https://app.any.run/tasks/31b4bbe0-4af2-4adb-b51b-48db78f9c252 |
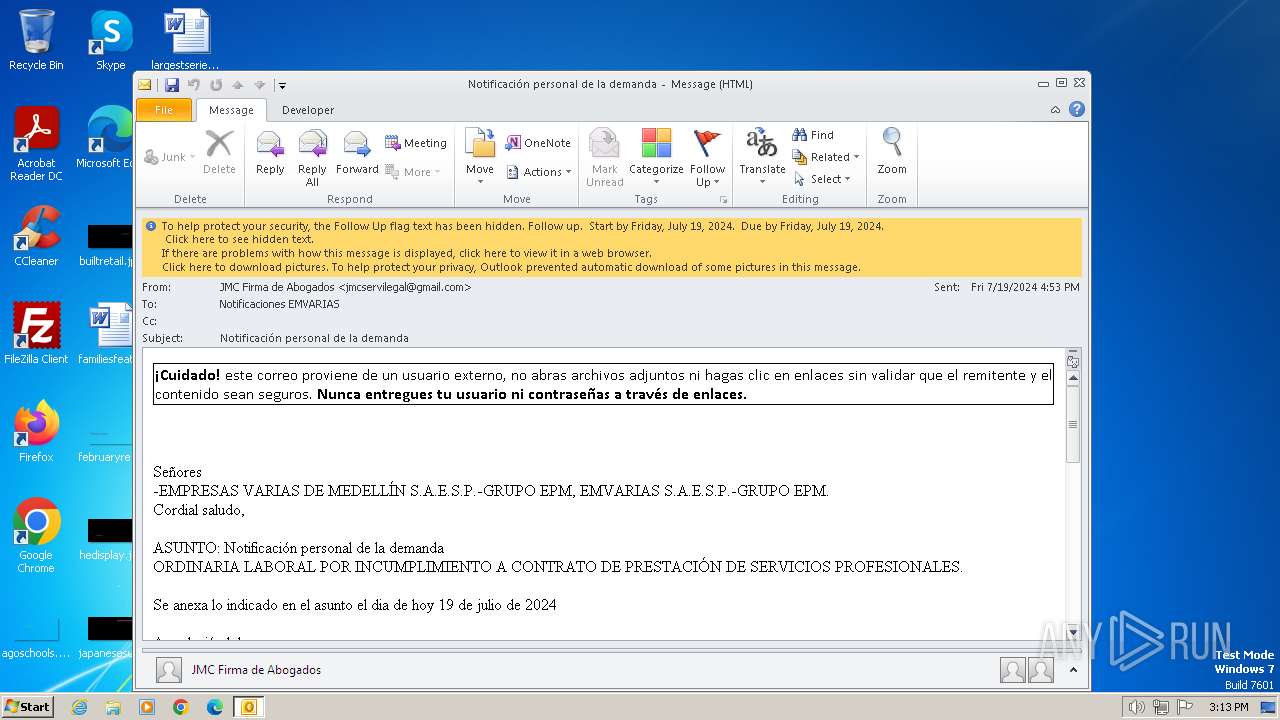
| Verdict: | Malicious activity |
| Analysis date: | July 23, 2024, 14:12:55 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 75EA442A3AEE37B98EE6313DB7989A69 |
| SHA1: | 91B63AF499BE471AB267BE49B153ED6E5FEF5E8E |
| SHA256: | 6FE72F7E696D8C96367CF7AA8B56879EB76FA3F3557907111A2AE878BC84D3EF |
| SSDEEP: | 3072:MQxd7fUxOJ5Oms47n7RXEiqlUsTETENUZ/wHjM1:M4rt0Zi/w |
MALICIOUS
No malicious indicators.SUSPICIOUS
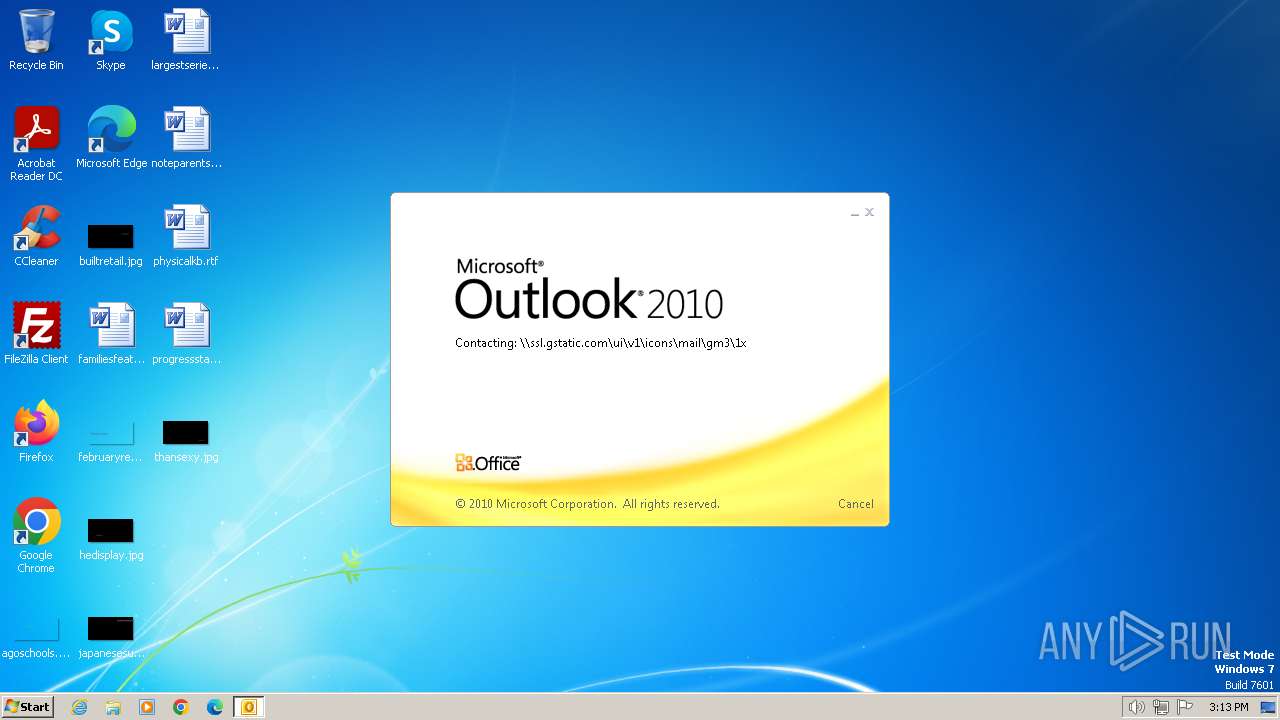
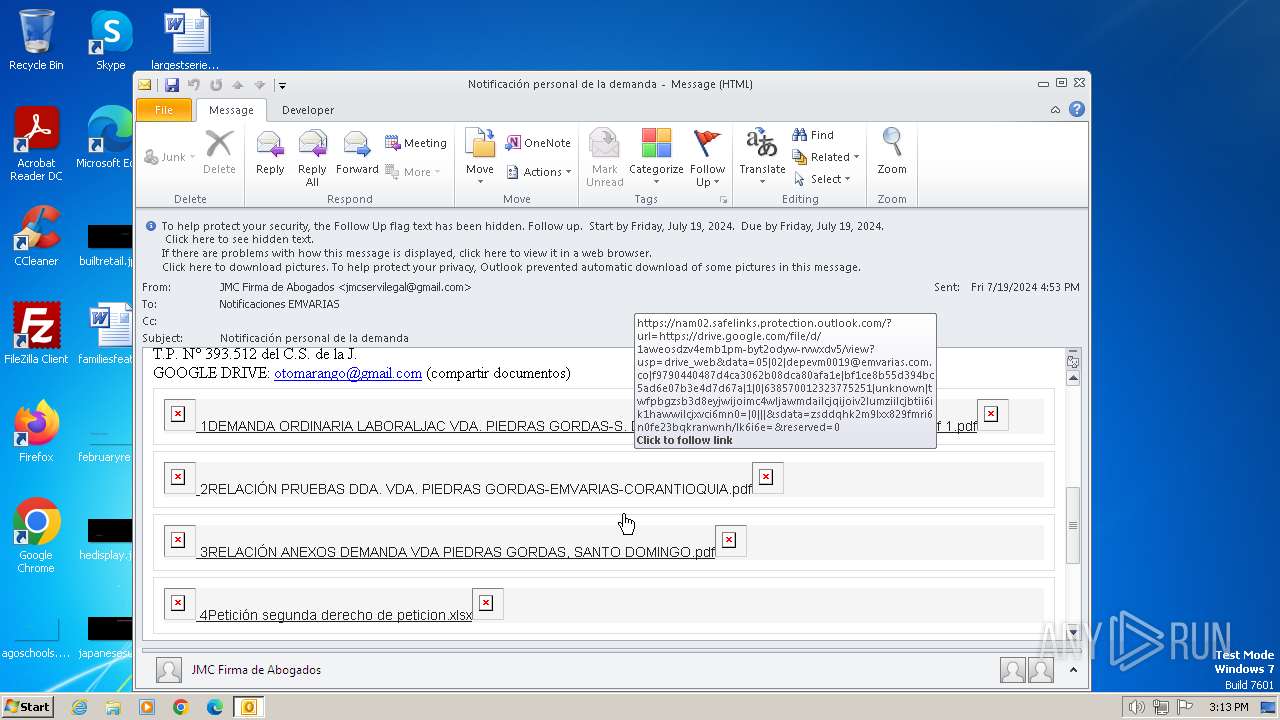
Attempting to connect via WebDav
- OUTLOOK.EXE (PID: 3152)
Uses pipe srvsvc via SMB (transferring data)
- OUTLOOK.EXE (PID: 3152)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
40
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3152 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Notificación personal de la demanda.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Version: 14.0.6025.1000 Modules
| |||||||||||||||
Total events
9 505
Read events
8 960
Write events
515
Delete events
30
Modification events
| (PID) Process: | (3152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3152) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
1
Text files
2
Unknown types
0
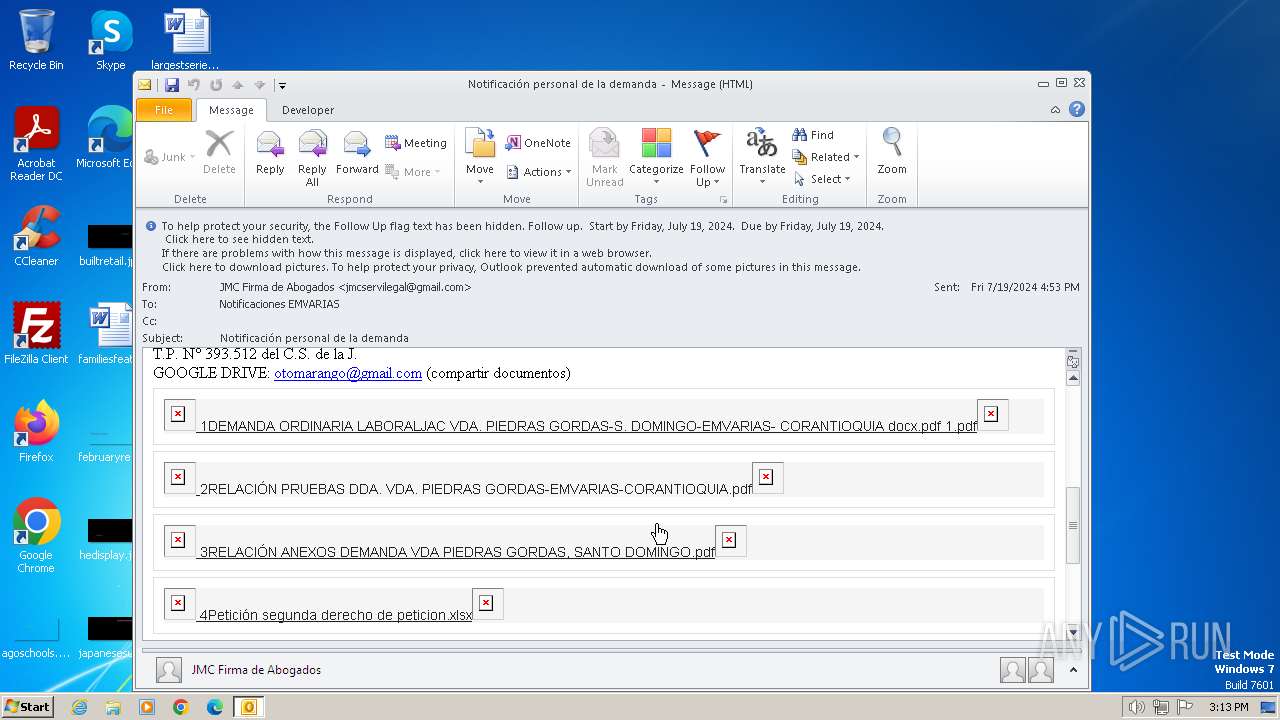
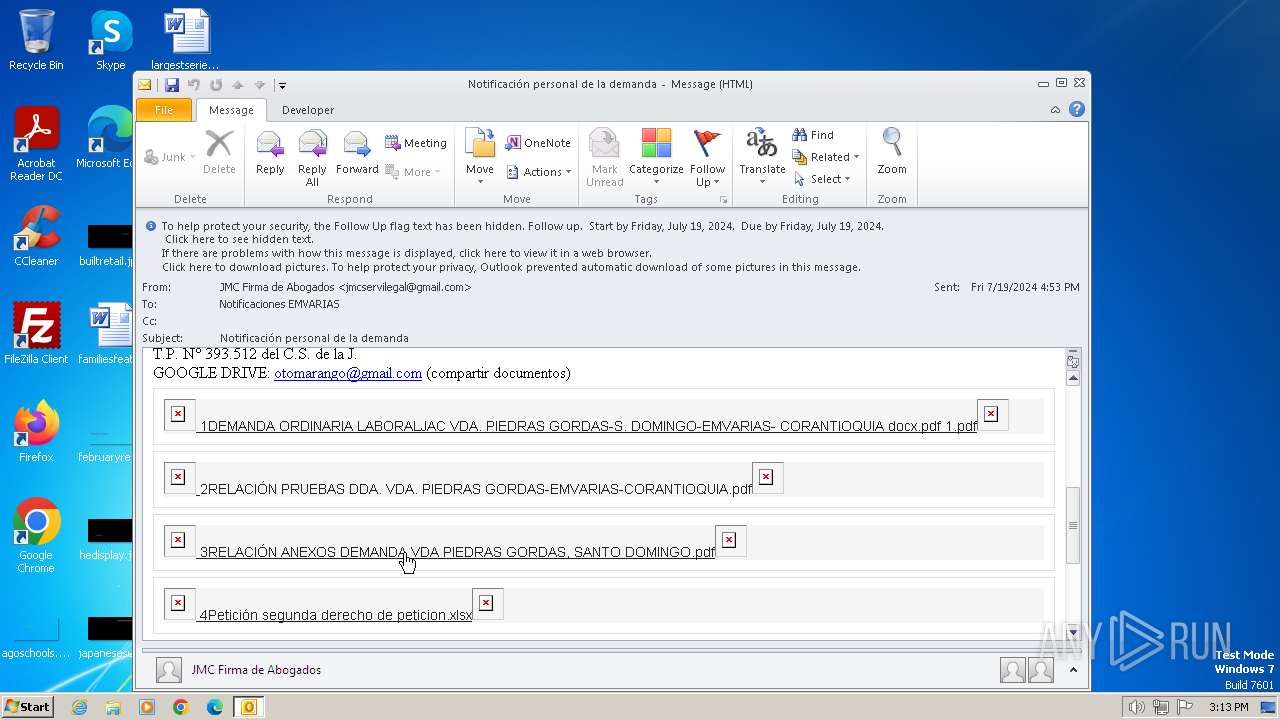
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR8B8E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3152 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3152 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:AD4E65712A73B5056E3EC8435DB127A3 | SHA256:8806E08C134E21D71B5F8042575E5D1D125E8E194F41F34FEE6EDD5520F5B5E8 | |||
| 3152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{6E281E75-B388-44E3-B2DD-D588BC415D67}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 3152 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
18
DNS requests
11
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1372 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3152 | OUTLOOK.EXE | OPTIONS | 404 | 142.250.186.35:80 | http://ssl.gstatic.com/ | unknown | — | — | whitelisted |
3152 | OUTLOOK.EXE | OPTIONS | 404 | 142.250.186.35:80 | http://ssl.gstatic.com/ | unknown | — | — | whitelisted |
3152 | OUTLOOK.EXE | OPTIONS | 404 | 142.250.186.35:80 | http://ssl.gstatic.com/ | unknown | — | — | whitelisted |
3152 | OUTLOOK.EXE | OPTIONS | 404 | 142.250.186.35:80 | http://ssl.gstatic.com/ | unknown | — | — | whitelisted |
3152 | OUTLOOK.EXE | OPTIONS | 404 | 142.250.186.35:80 | http://ssl.gstatic.com/ | unknown | — | — | whitelisted |
3152 | OUTLOOK.EXE | OPTIONS | 404 | 142.250.186.35:80 | http://ssl.gstatic.com/ | unknown | — | — | whitelisted |
3152 | OUTLOOK.EXE | OPTIONS | 404 | 142.250.186.35:80 | http://ssl.gstatic.com/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
1372 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 142.250.186.35:445 | ssl.gstatic.com | GOOGLE | US | whitelisted |
1372 | svchost.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | unknown |
1372 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
3152 | OUTLOOK.EXE | 142.250.186.35:80 | ssl.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
dns.msftncsi.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.messenger.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
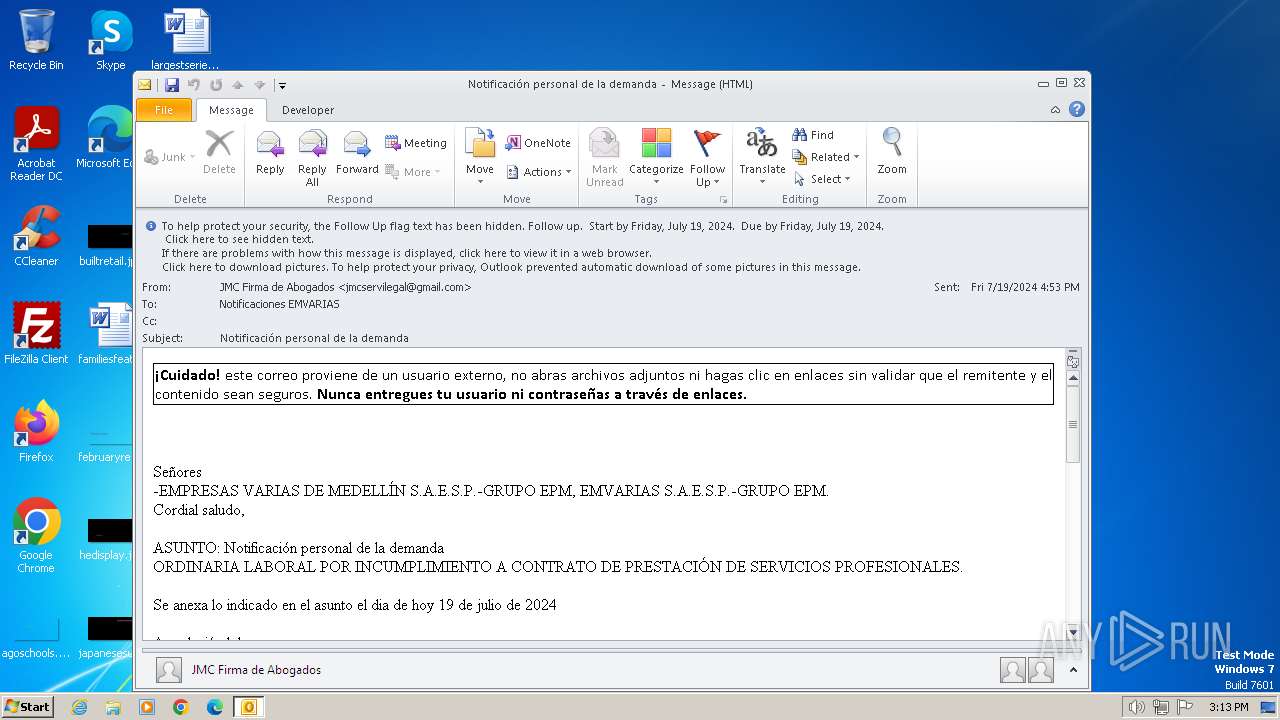
4 | System | Potential Corporate Privacy Violation | POLICY [ANY.RUN] Attempt to connect to an external SMB server |
16 ETPRO signatures available at the full report