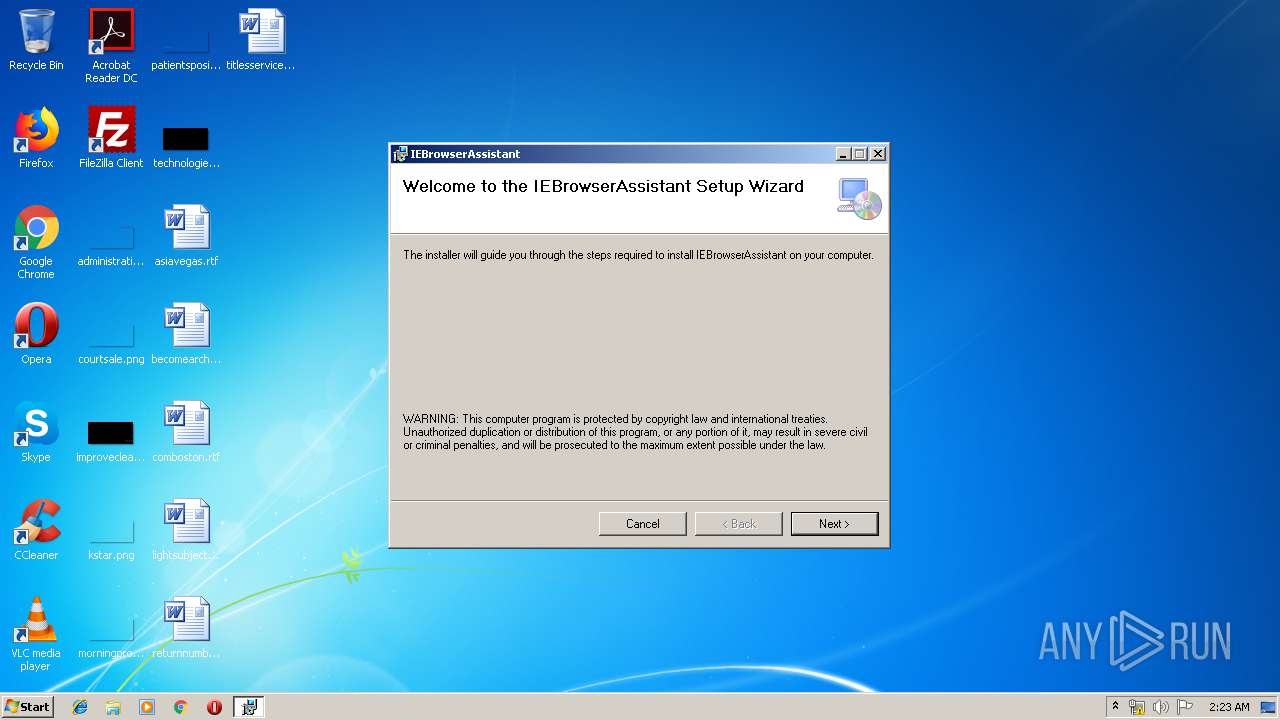
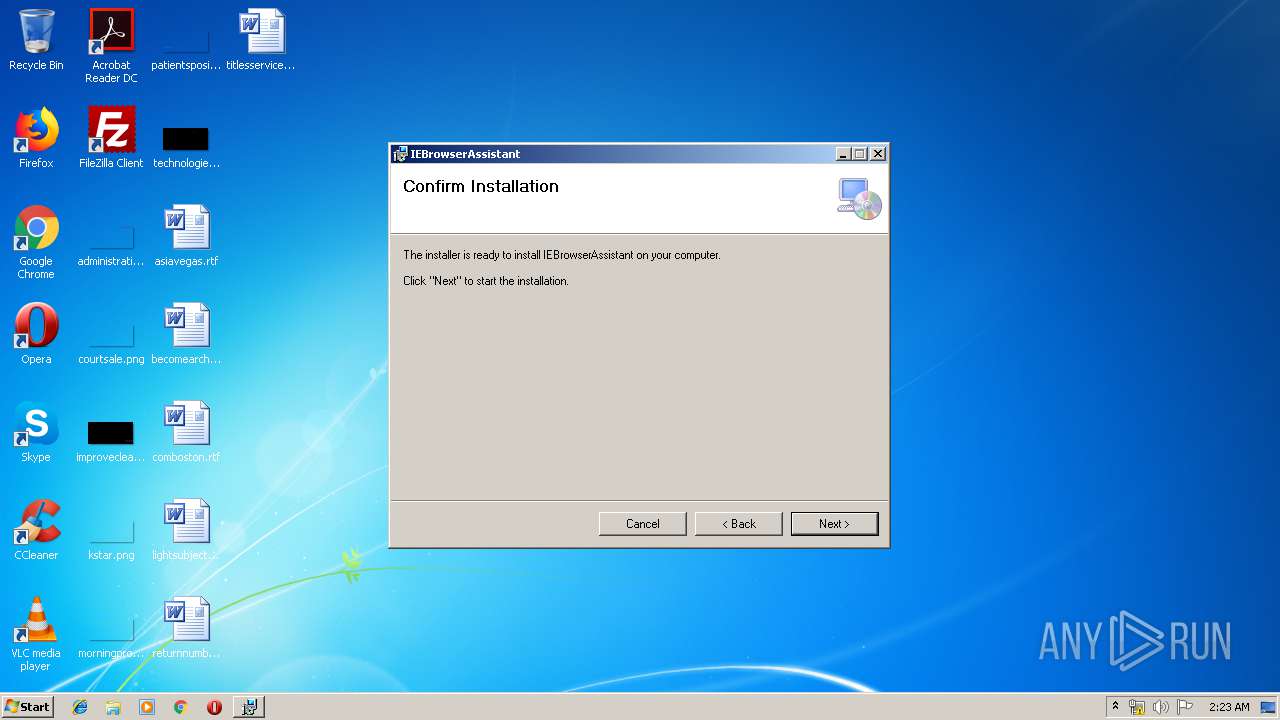
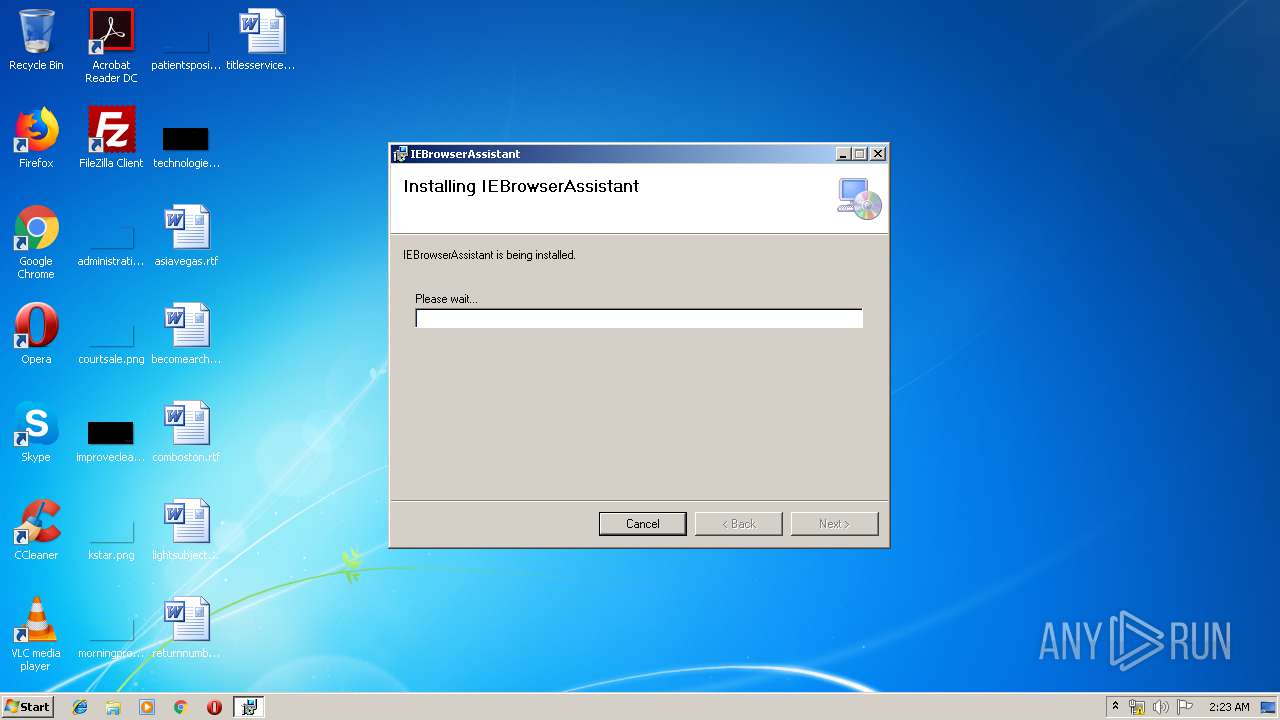
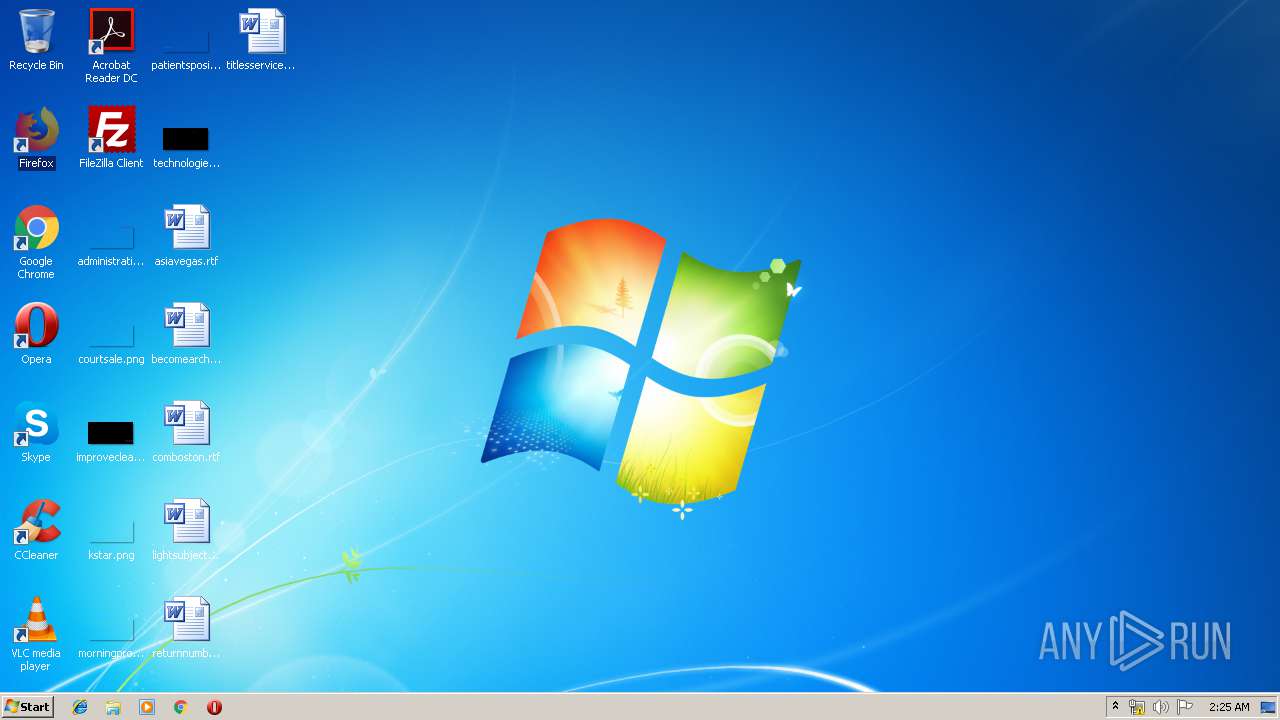
| File name: | IEBrowserAssistantSetup.msi |
| Full analysis: | https://app.any.run/tasks/5ead493d-9afe-4ee1-9bbc-5b73f9adaac8 |
| Verdict: | Suspicious activity |
| Analysis date: | May 08, 2019, 01:22:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Create Time/Date: Mon Jun 21 08:00:00 1999, Name of Creating Application: Windows Installer, Security: 1, Code page: 1252, Template: Intel;0, Number of Pages: 200, Revision Number: {BFBA8AA2-8479-4E6B-ABA2-88228A0C3CCB}, Title: IEBrowserAssistant, Author: Realistic Media Inc., Comments: IEBrowserAssistant, Number of Words: 2, Last Saved Time/Date: Wed Nov 28 03:24:31 2018, Last Printed: Wed Nov 28 03:24:31 2018 |
| MD5: | 24A4DCBC841170F0A4508DBA66A0A37C |
| SHA1: | FE509DB0A2DA578B906C2A0E42BAD421E9C3A0CA |
| SHA256: | 6FC9F60F790C1A46385F7294D8911736D46B26BB041B0E1D4E52C7B020621976 |
| SSDEEP: | 98304:9amtb6Am1RxUtsahuHuZ1JEZ8PeSrgm51CtTxAnOHbg1jEkeWbVWNvpr:kmtO5h+JEZ8WSUldxUOHAjEK |
MALICIOUS
Application was dropped or rewritten from another process
- adxregistrator.exe (PID: 1816)
Loads dropped or rewritten executable
- adxregistrator.exe (PID: 1816)
SUSPICIOUS
Executable content was dropped or overwritten
- msiexec.exe (PID: 3644)
- msiexec.exe (PID: 2080)
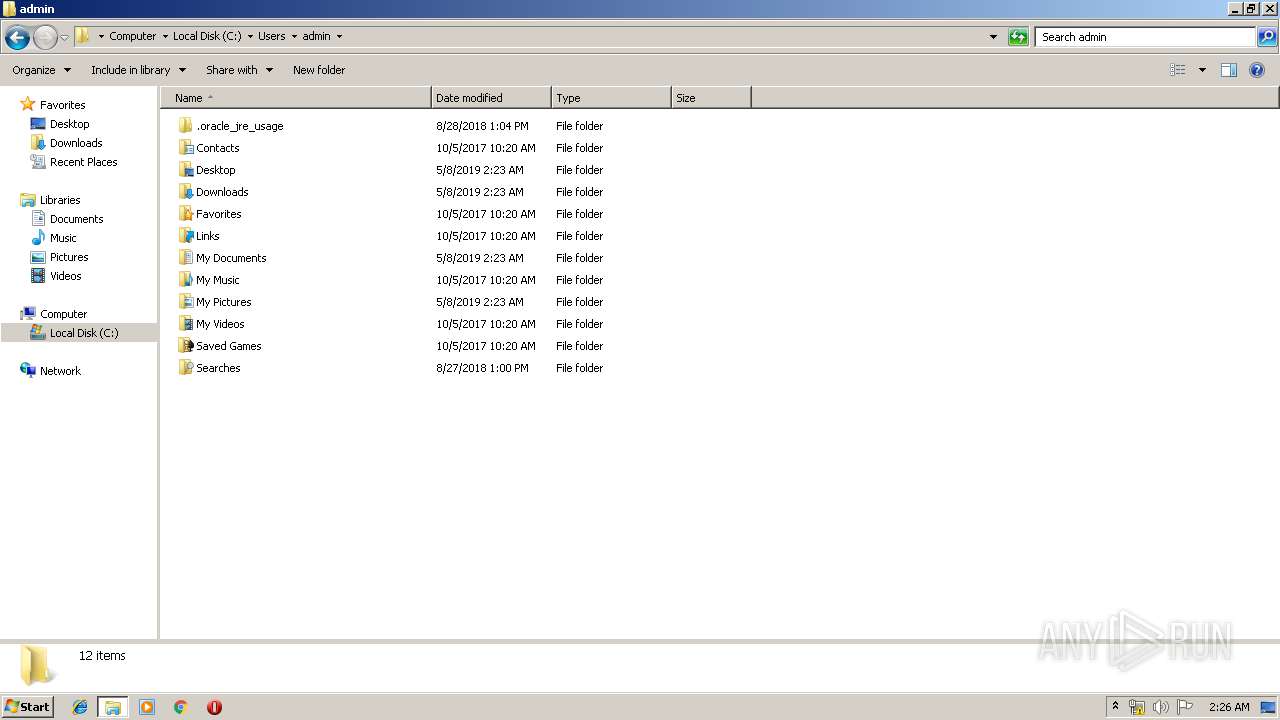
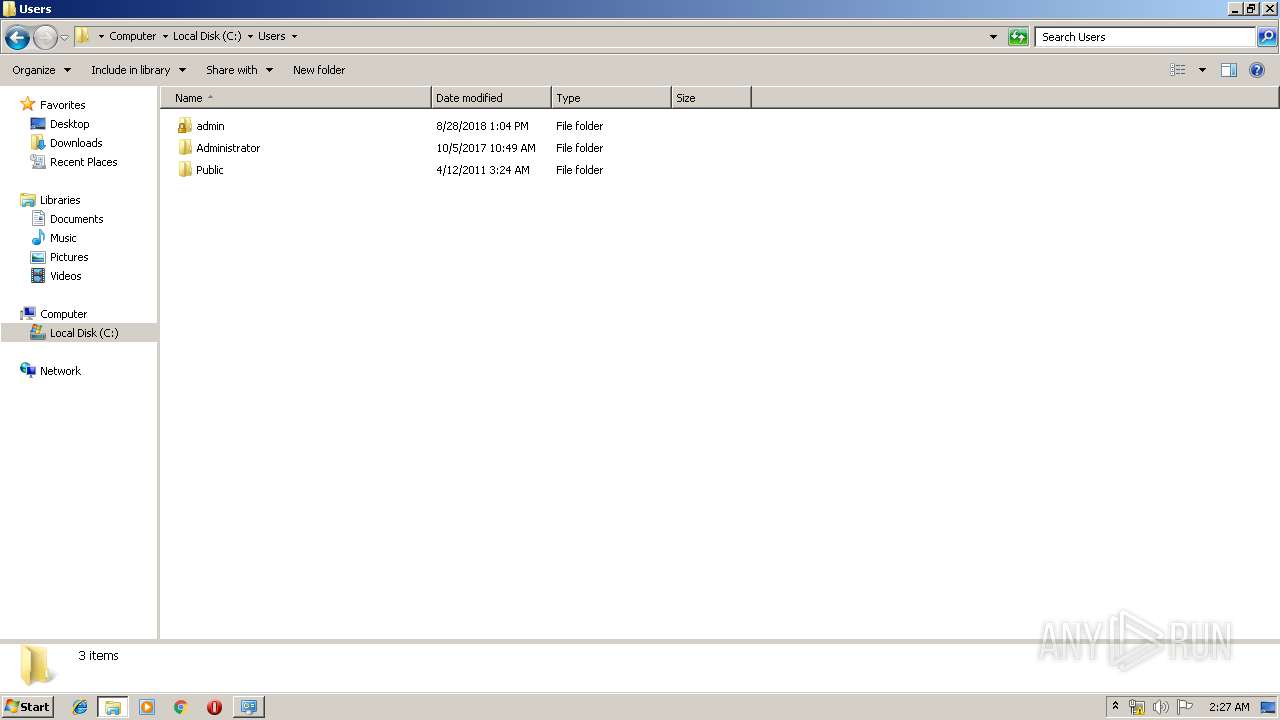
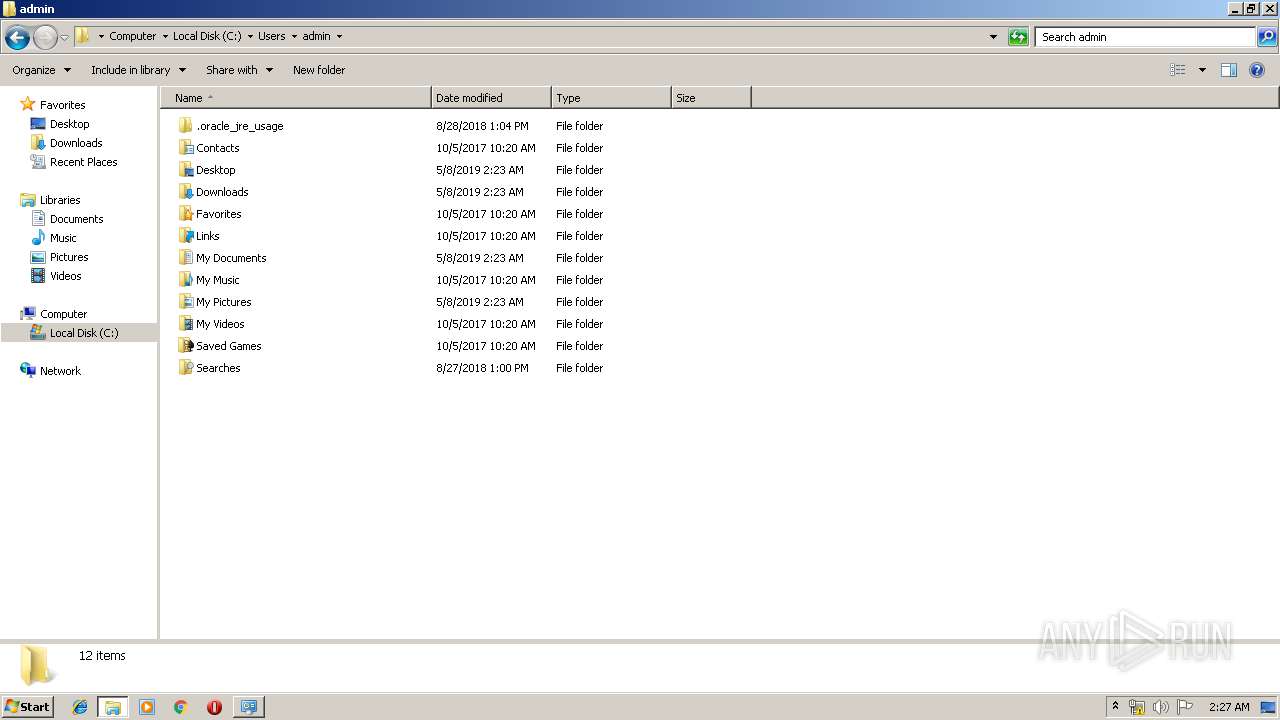
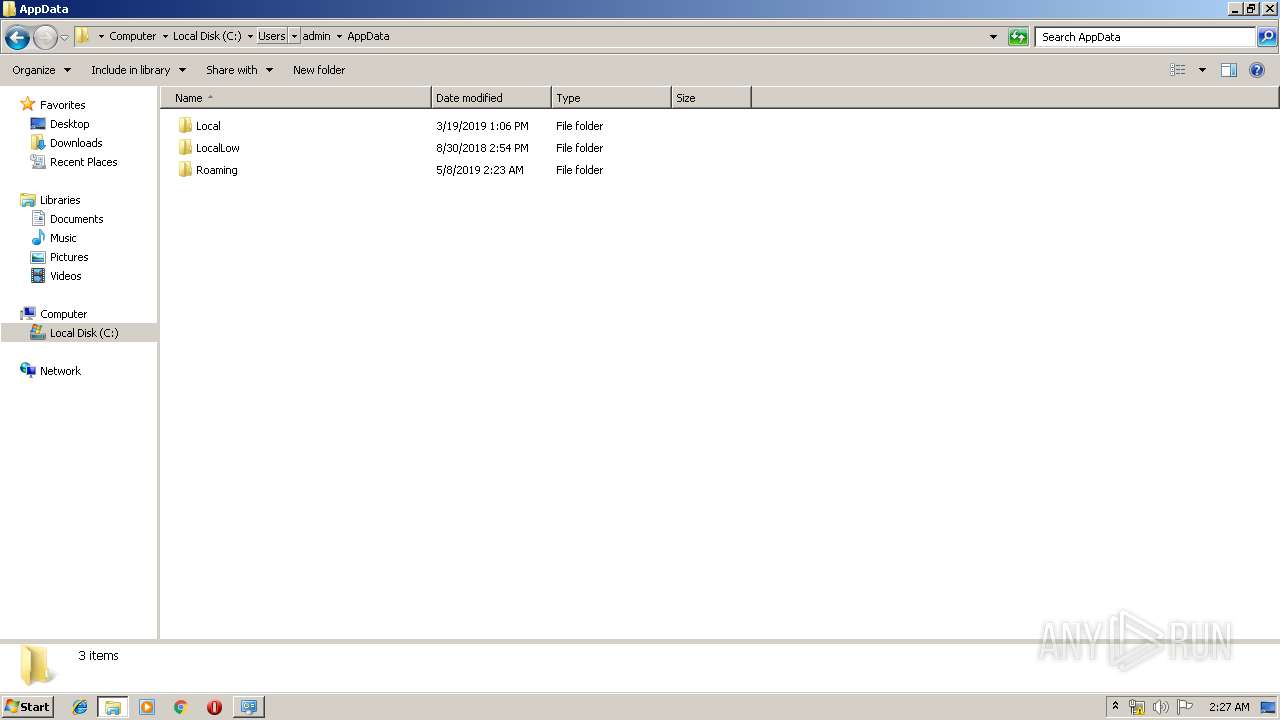
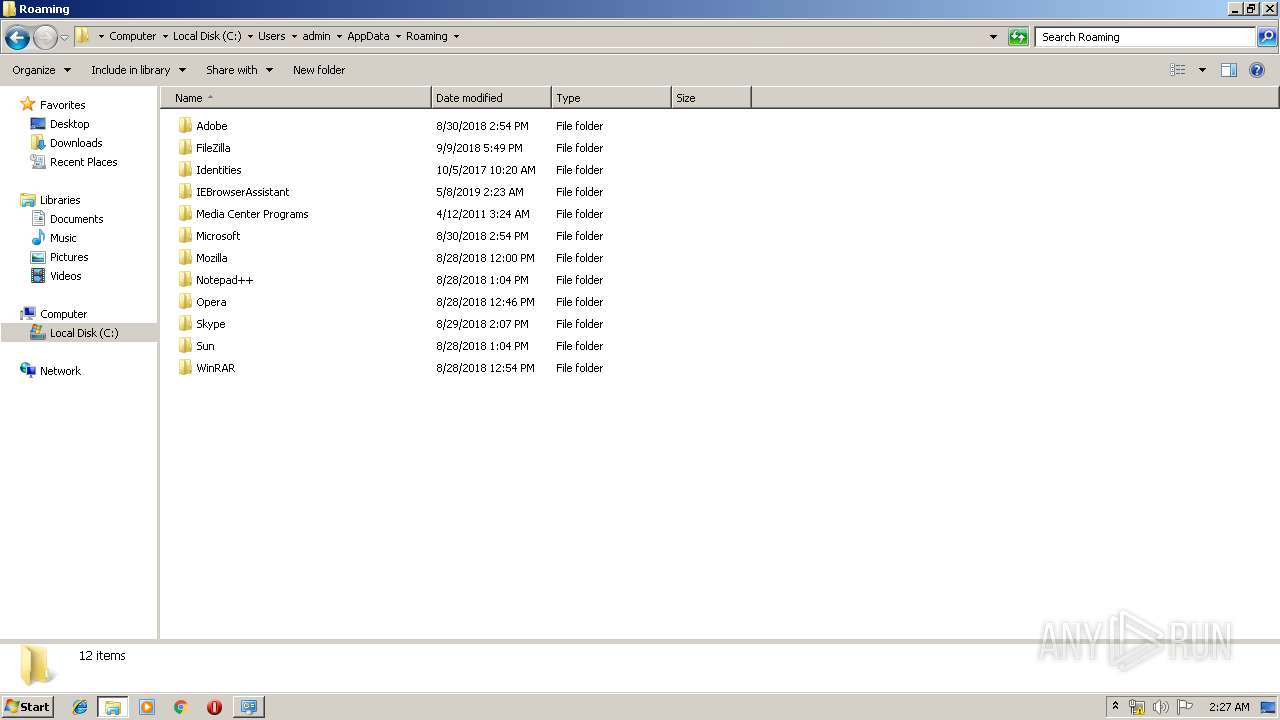
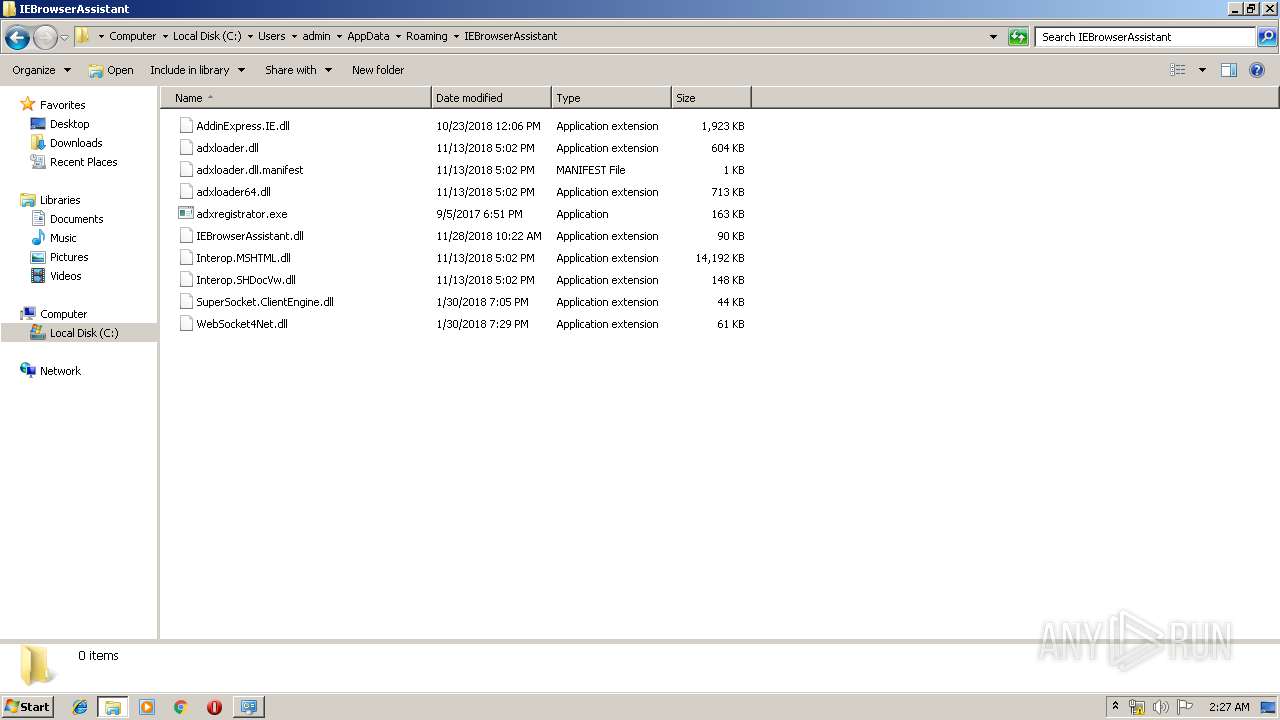
Creates files in the user directory
- msiexec.exe (PID: 2080)
INFO
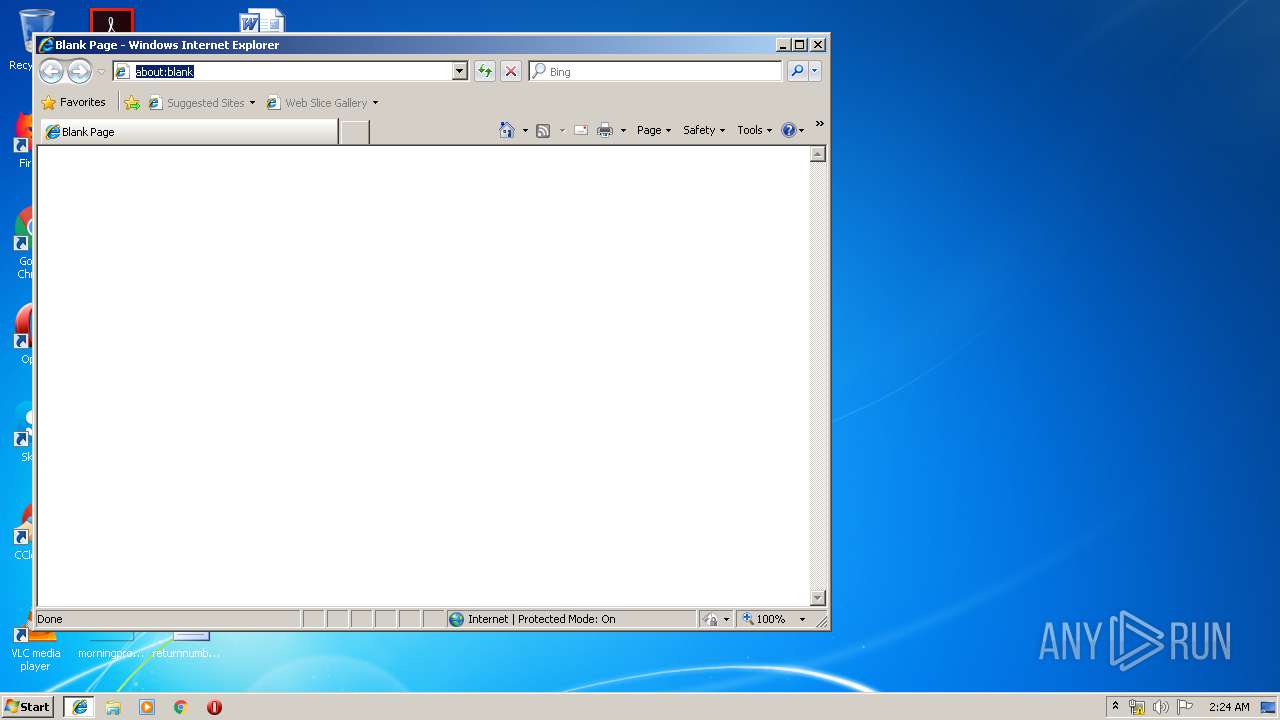
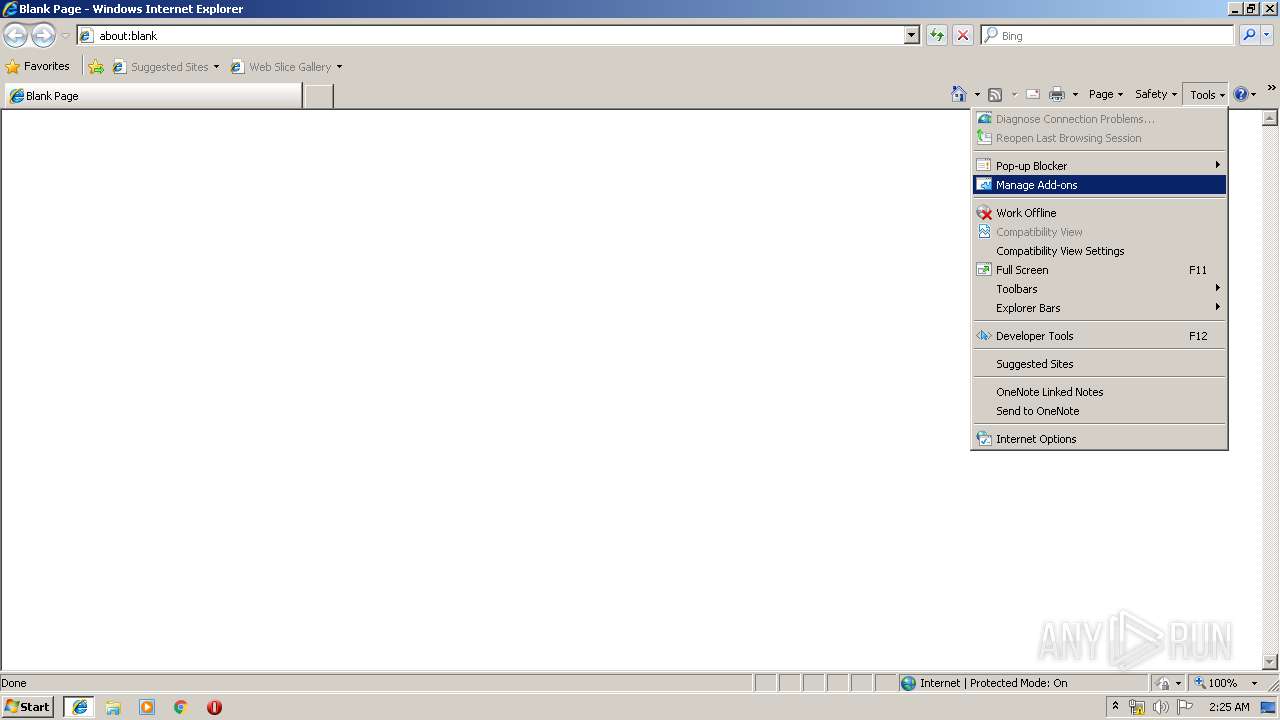
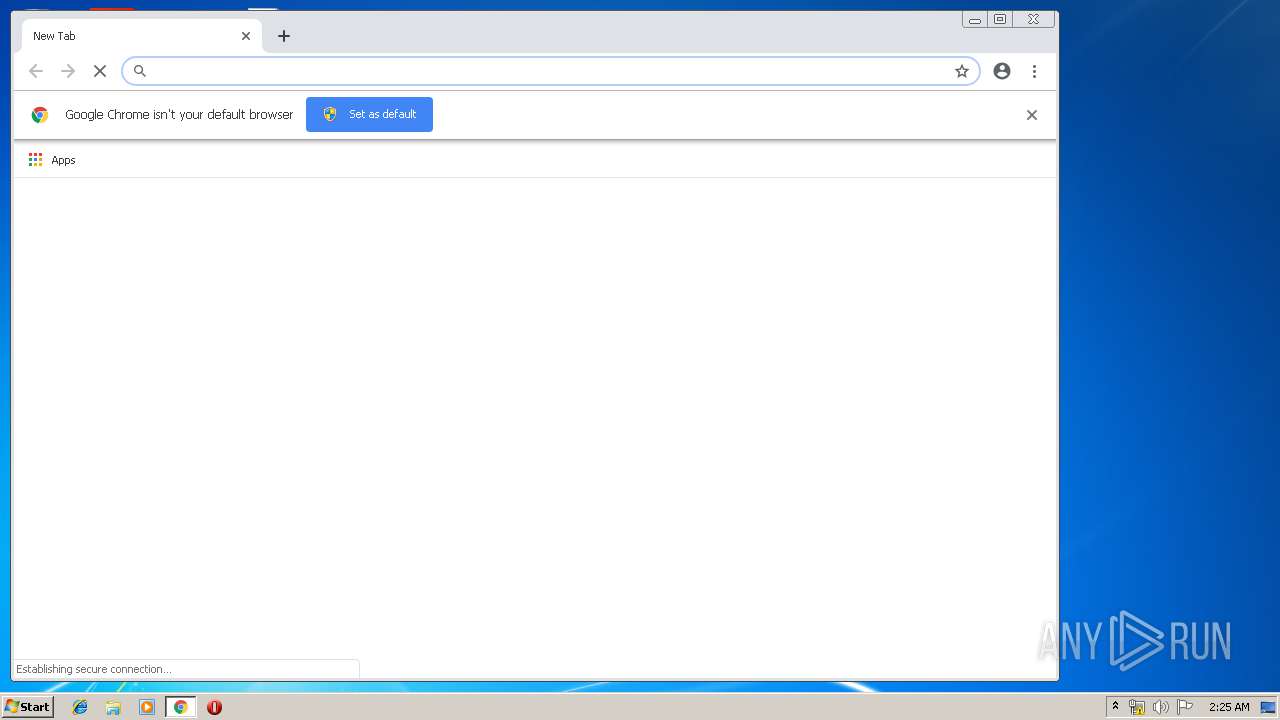
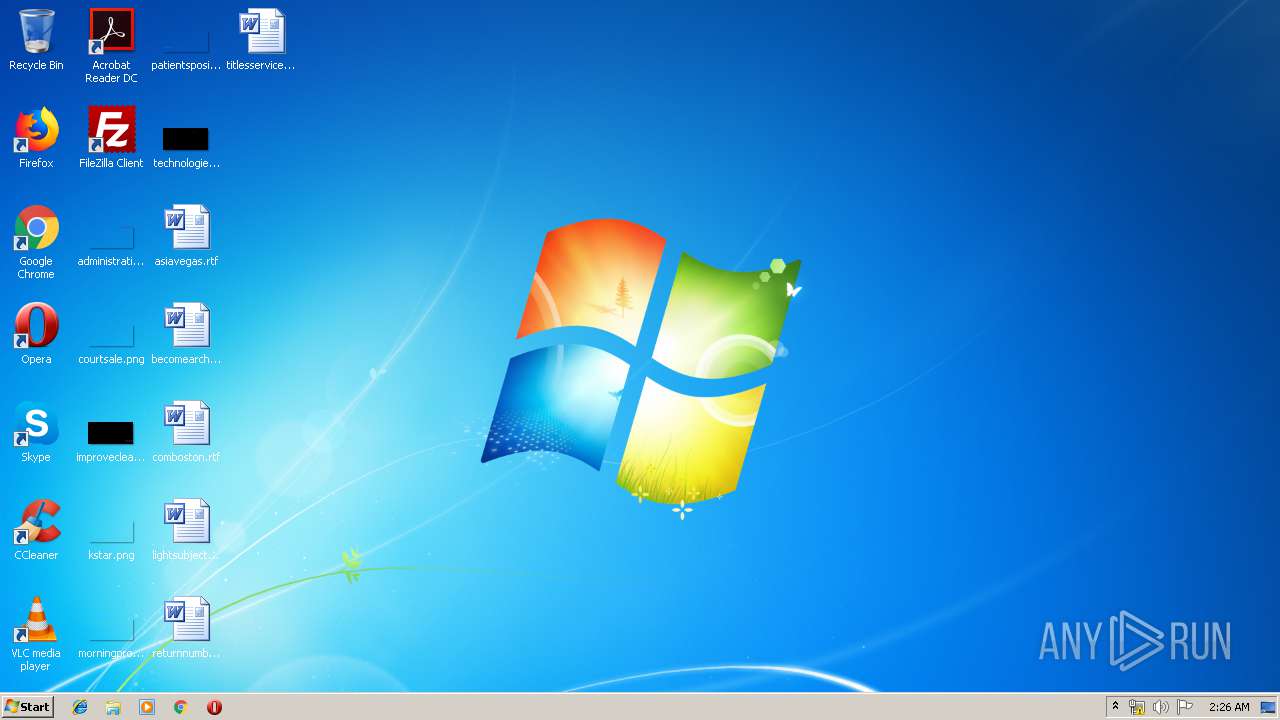
Application launched itself
- msiexec.exe (PID: 2080)
- iexplore.exe (PID: 936)
- chrome.exe (PID: 4016)
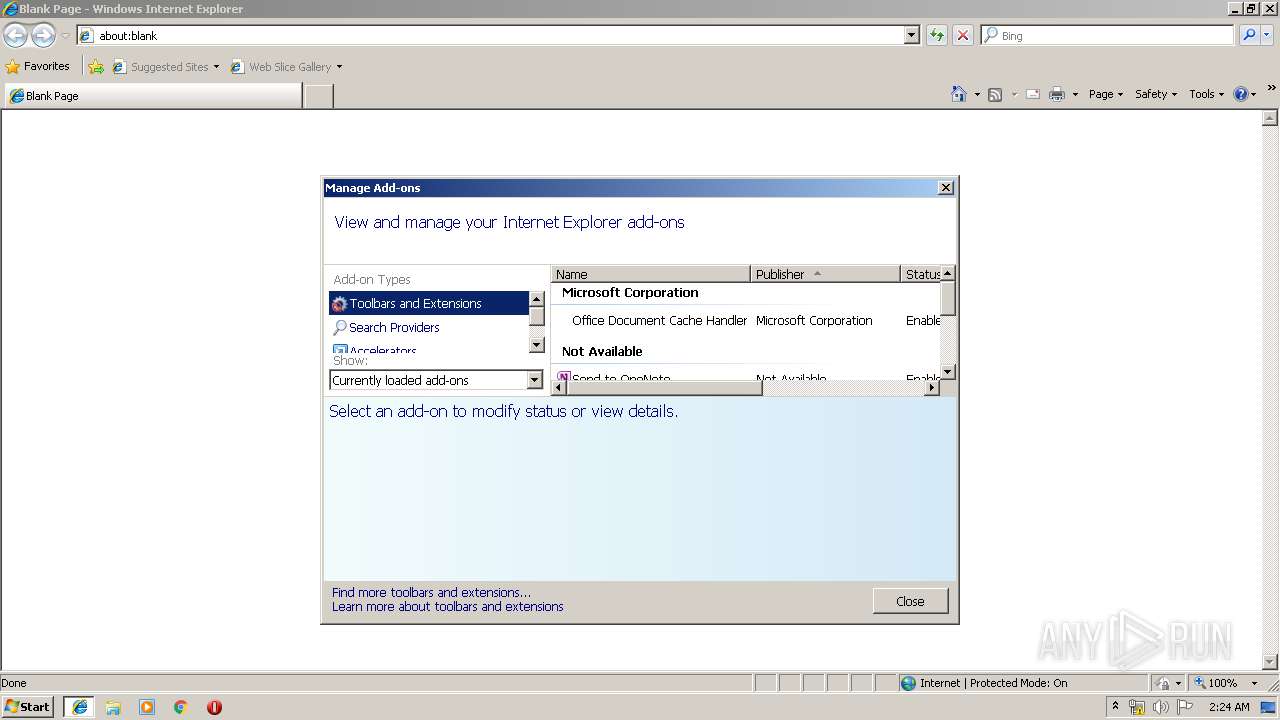
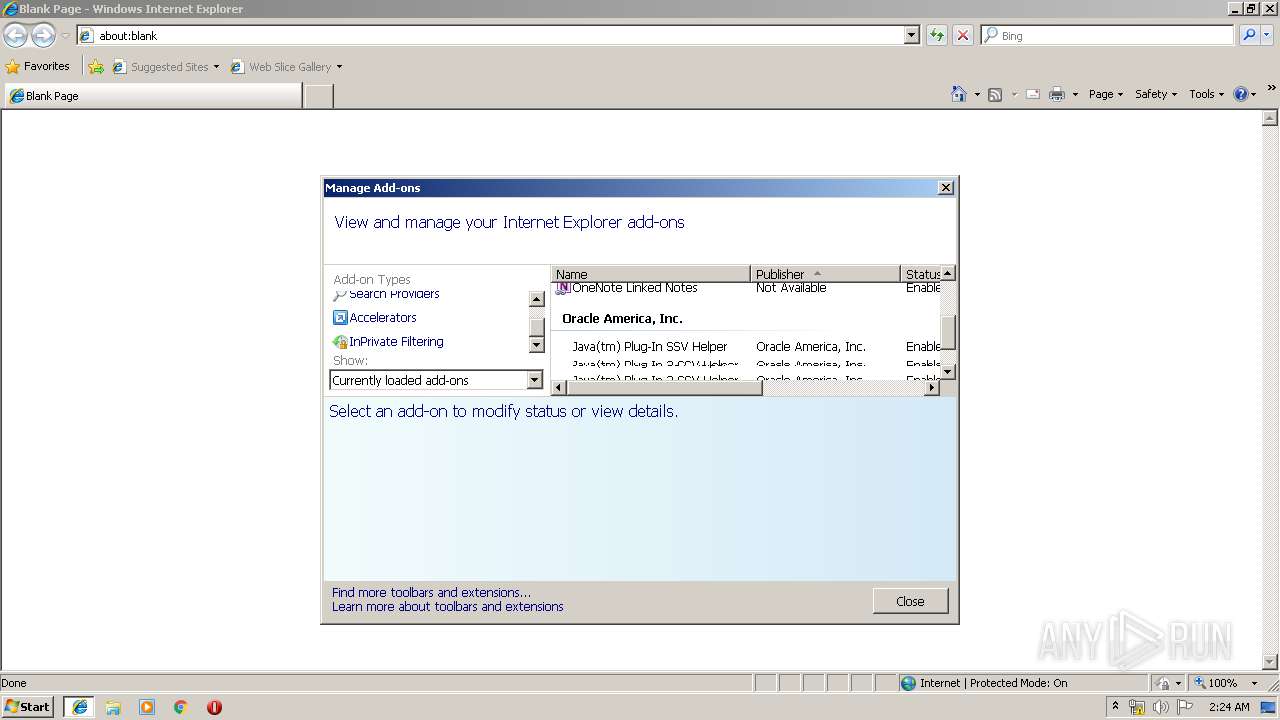
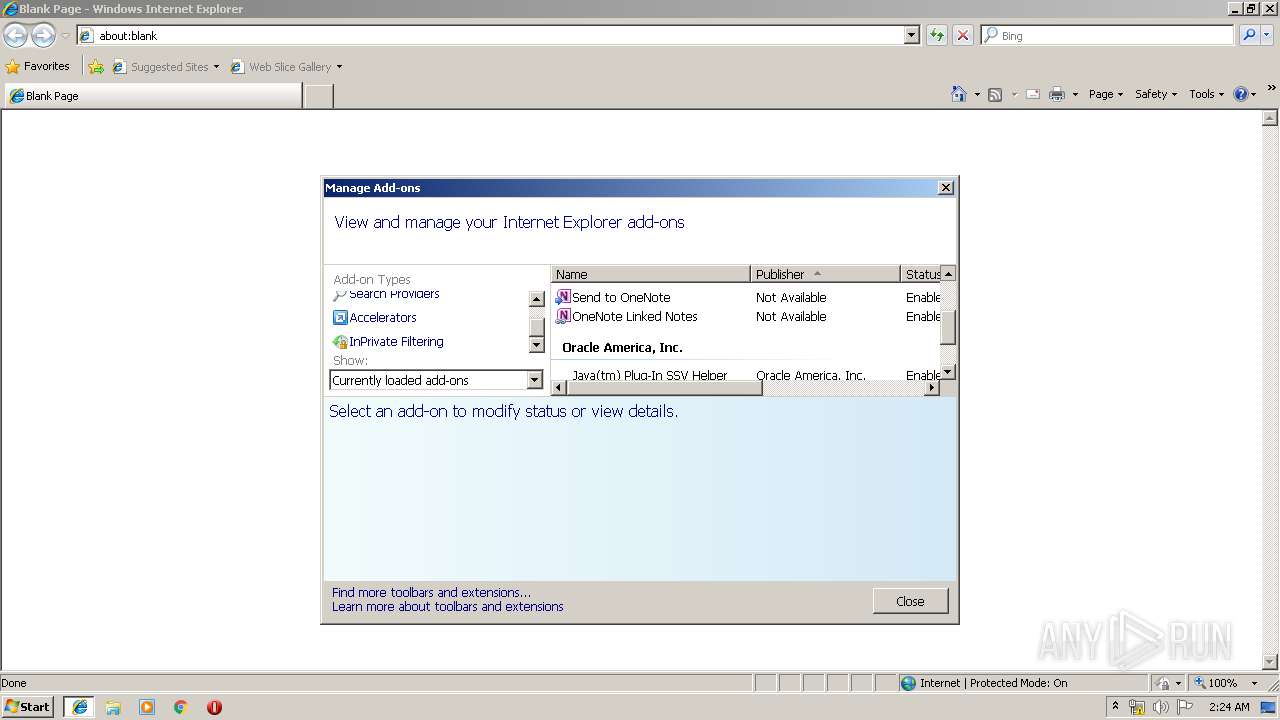
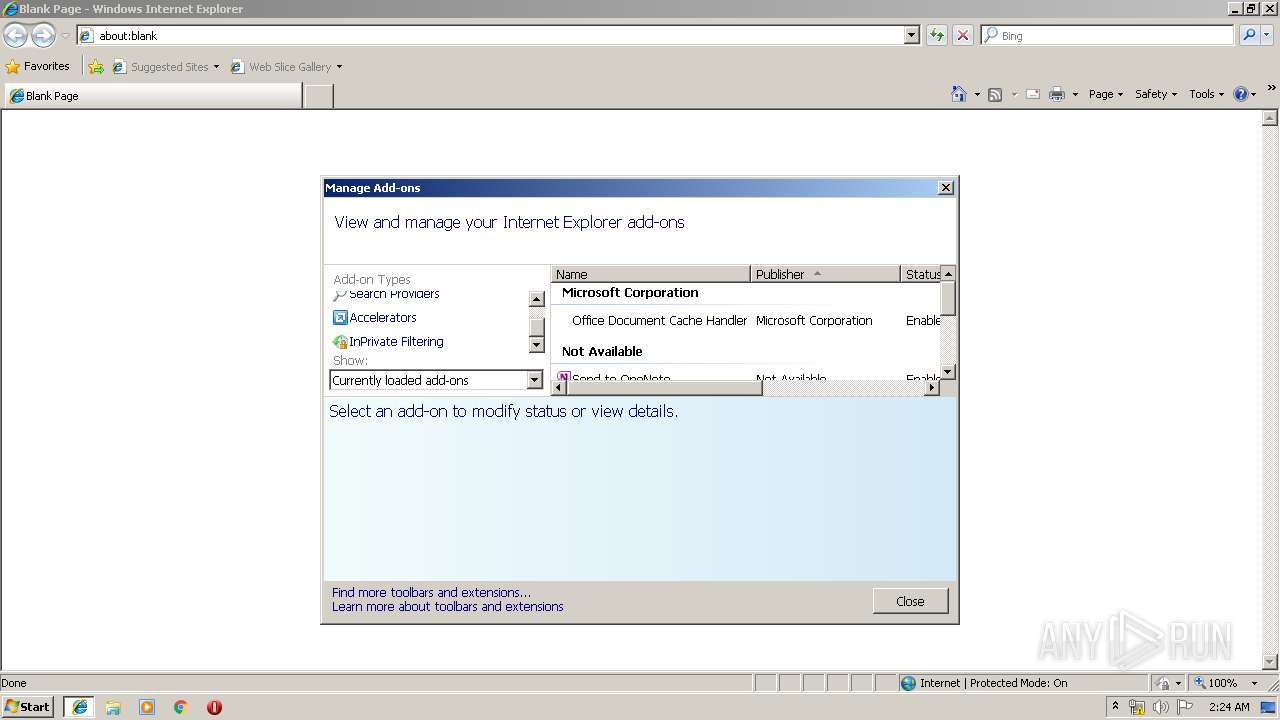
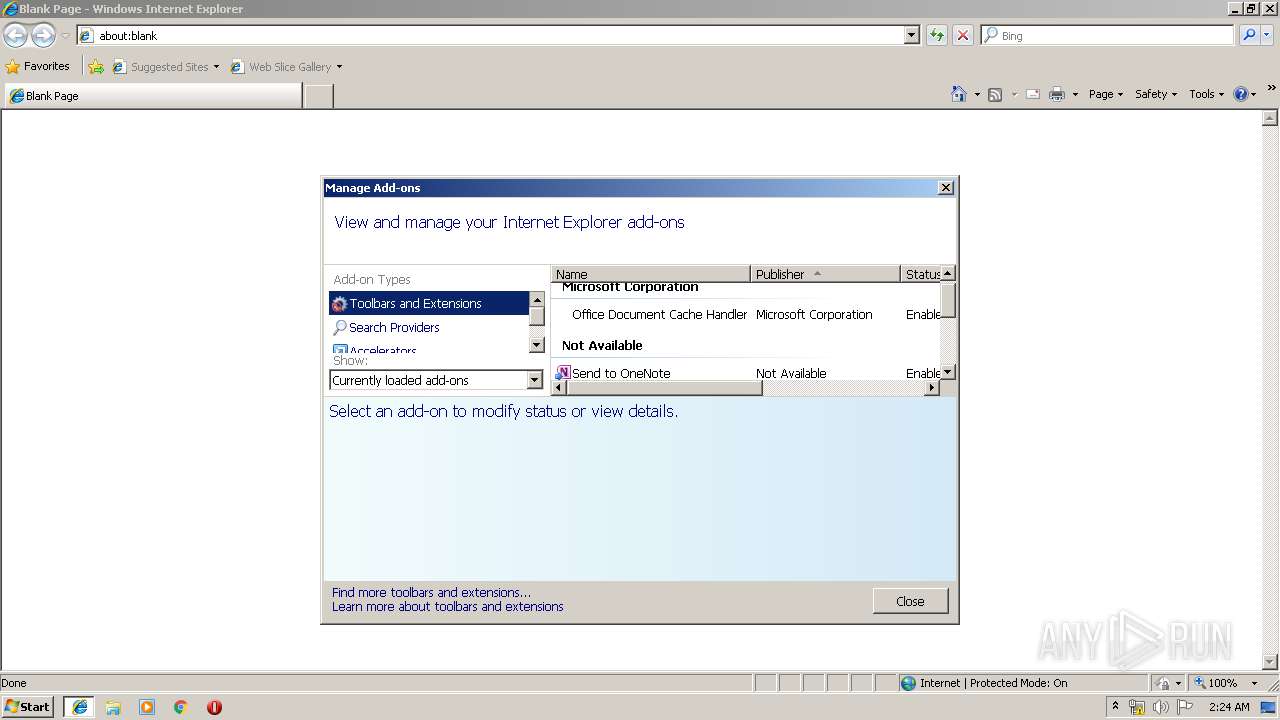
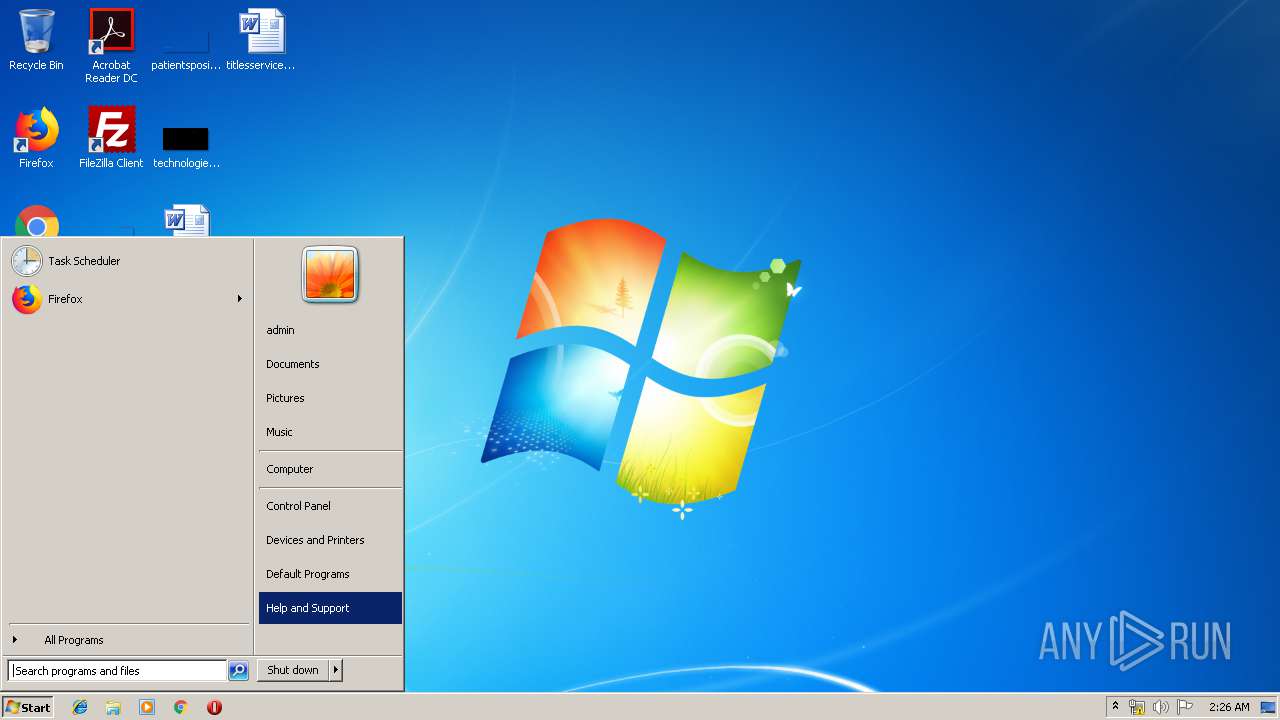
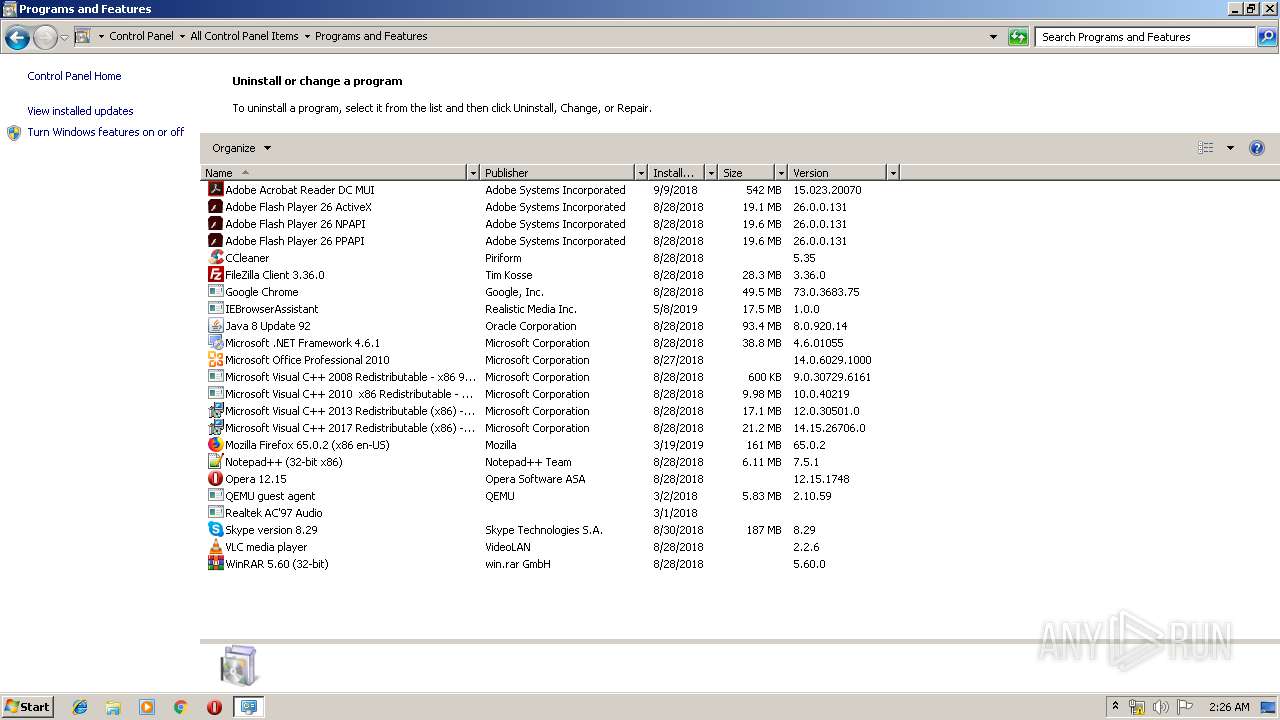
Searches for installed software
- msiexec.exe (PID: 2080)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3808)
Changes settings of System certificates
- DrvInst.exe (PID: 2616)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 320)
- MsiExec.exe (PID: 3852)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 2616)
Reads settings of System Certificates
- iexplore.exe (PID: 936)
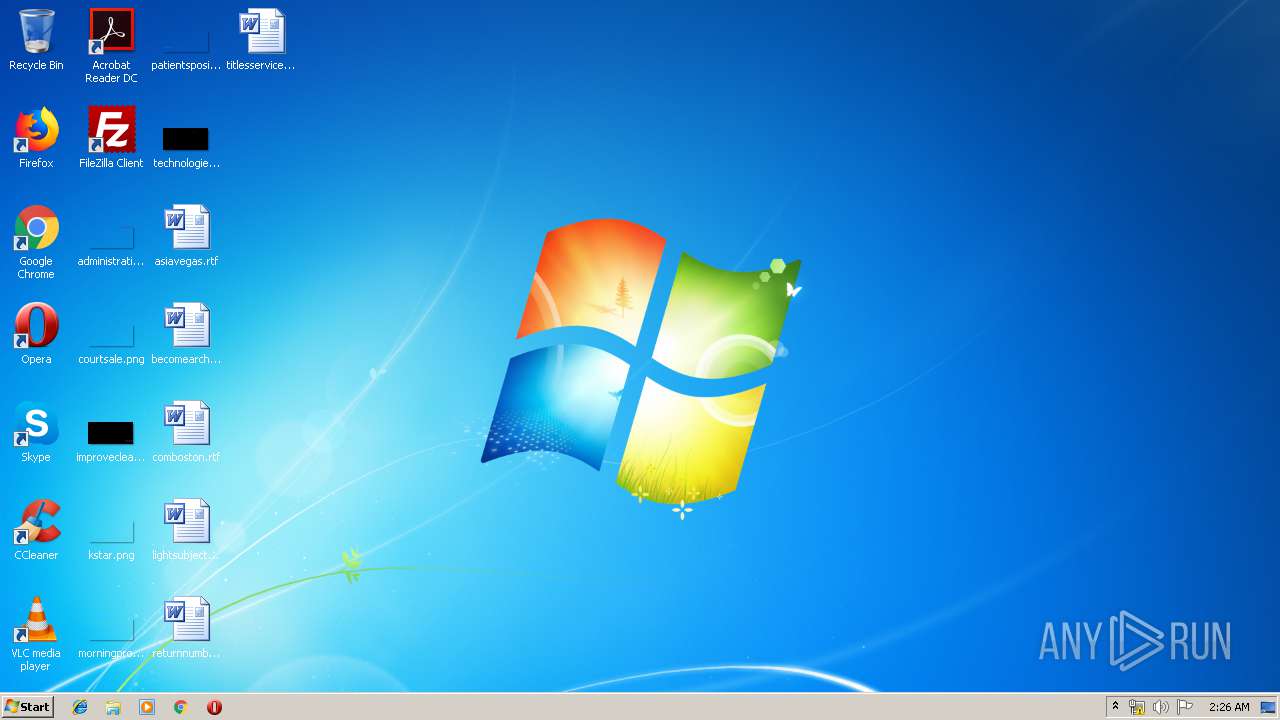
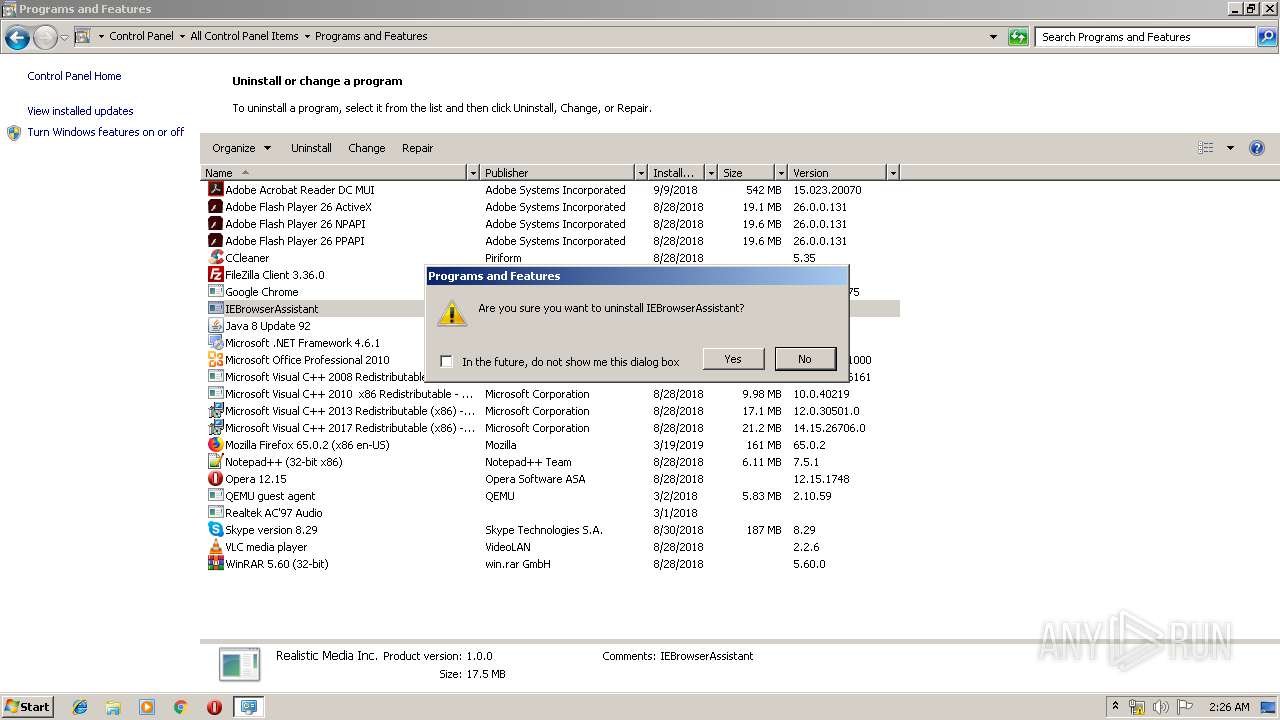
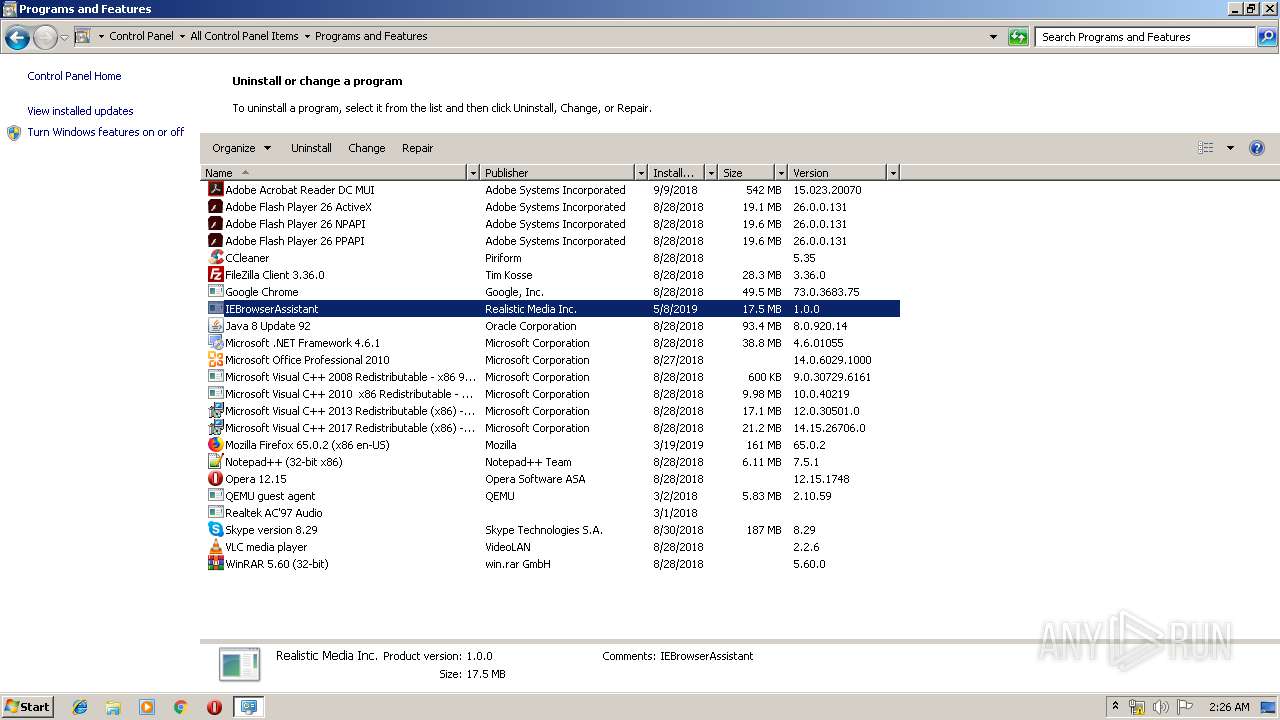
Creates a software uninstall entry
- msiexec.exe (PID: 2080)
Creates files in the user directory
- iexplore.exe (PID: 3496)
- iexplore.exe (PID: 936)
Reads Internet Cache Settings
- iexplore.exe (PID: 3496)
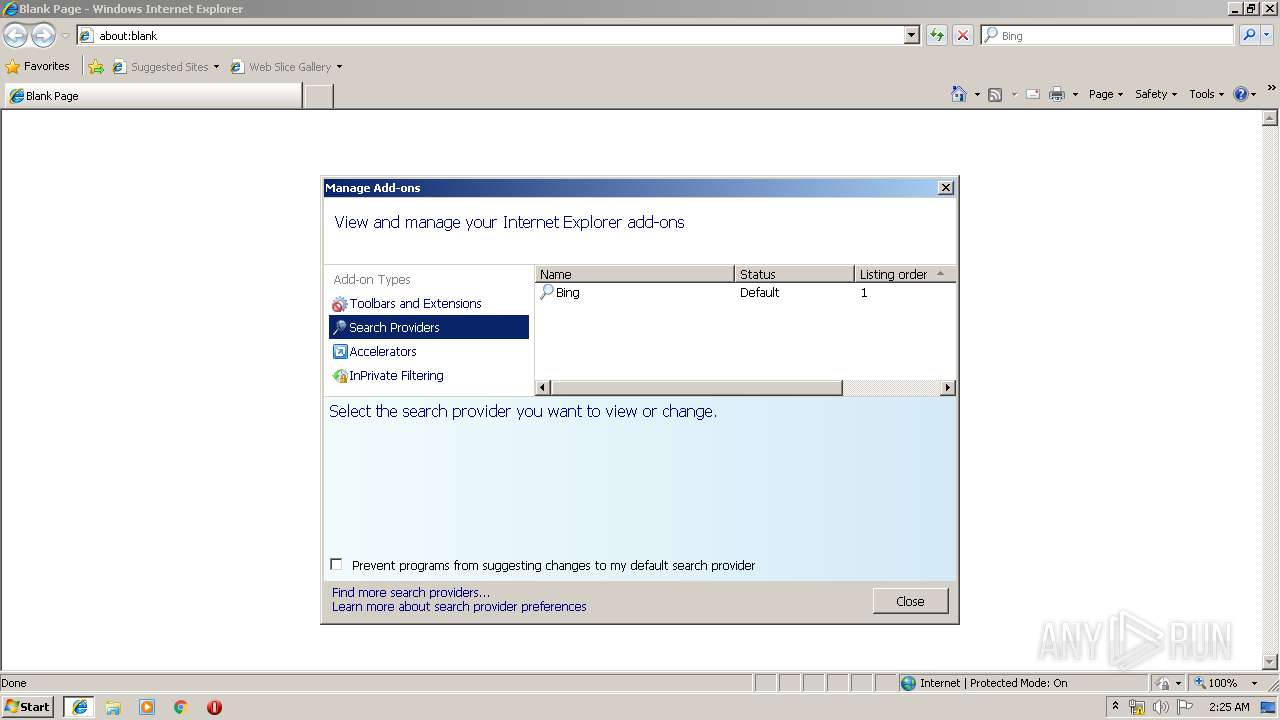
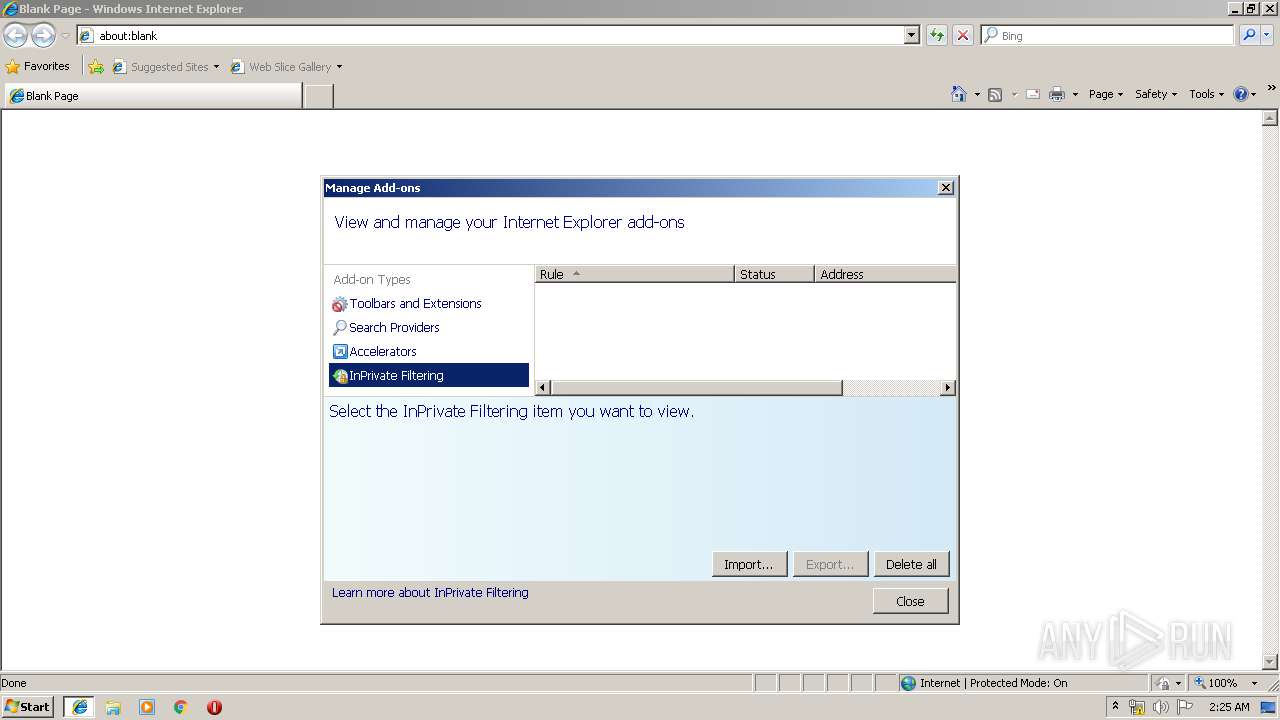
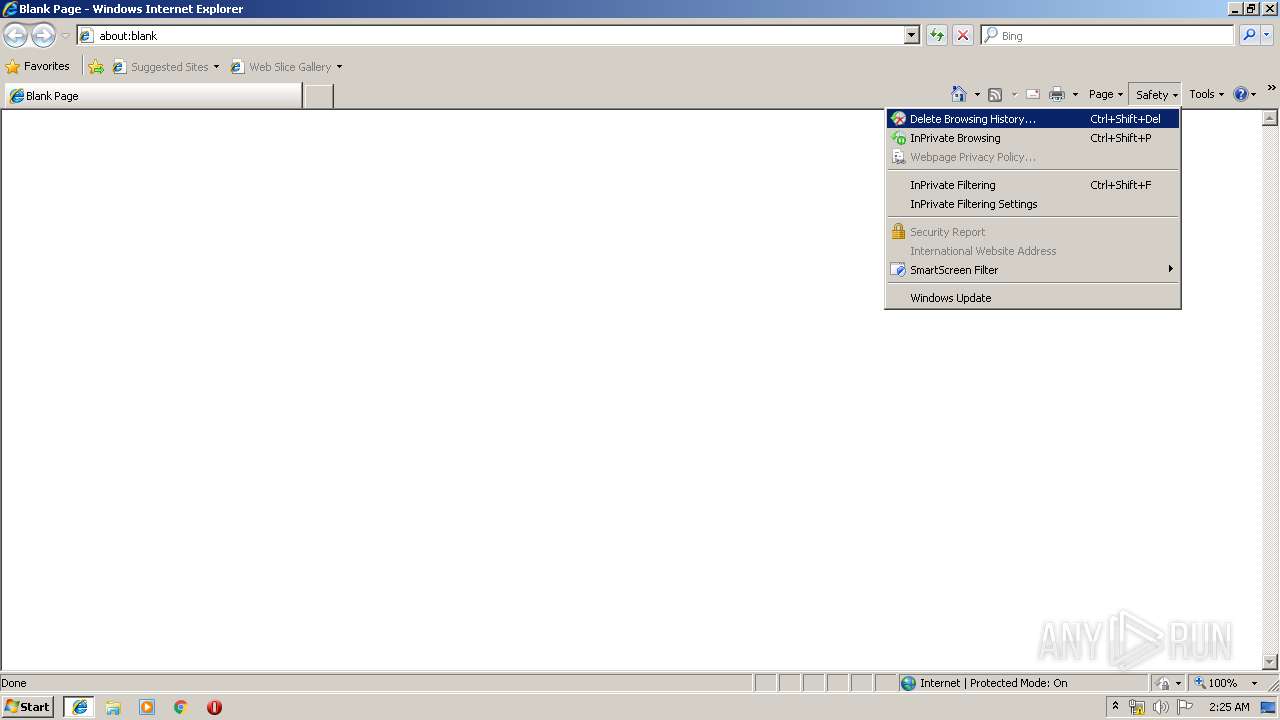
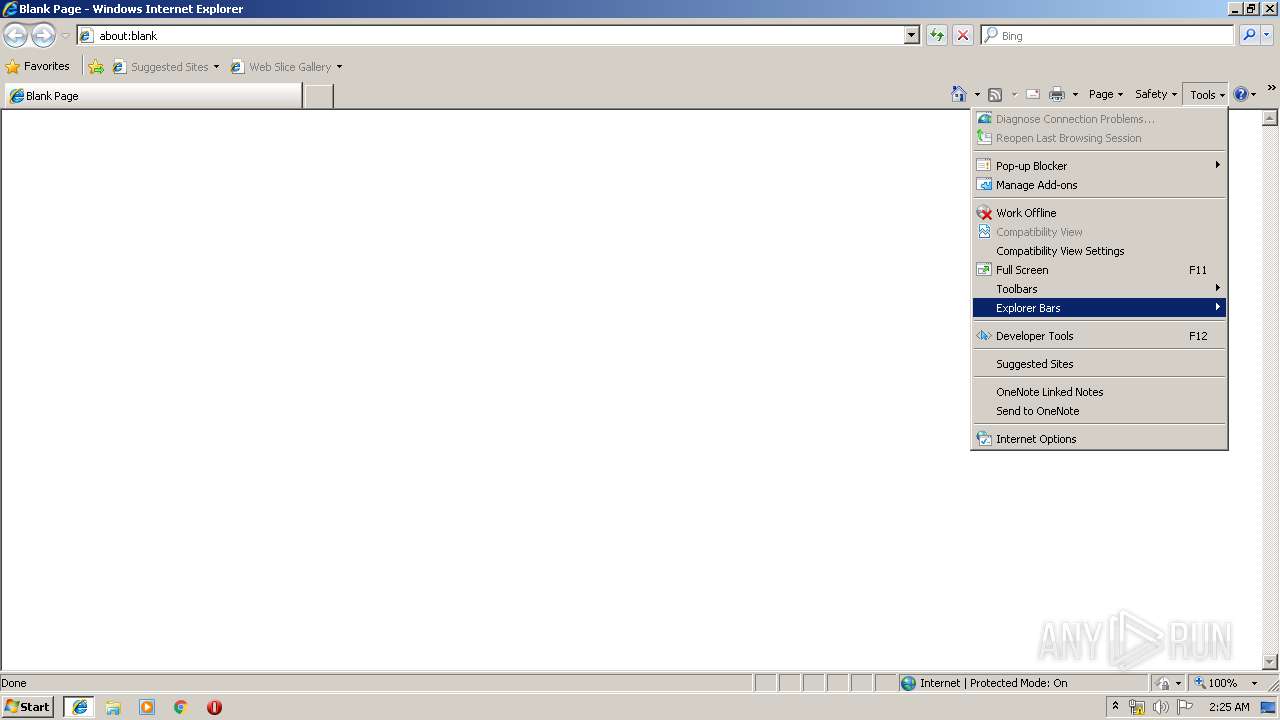
Reads internet explorer settings
- iexplore.exe (PID: 3496)
Changes internet zones settings
- iexplore.exe (PID: 936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (90.2) |
|---|---|---|
| .msp | | | Windows Installer Patch (8.4) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CreateDate: | 1999:06:21 07:00:00 |
|---|---|
| Software: | Windows Installer |
| Security: | Password protected |
| CodePage: | Windows Latin 1 (Western European) |
| Template: | Intel;0 |
| Pages: | 200 |
| RevisionNumber: | {BFBA8AA2-8479-4E6B-ABA2-88228A0C3CCB} |
| Title: | IEBrowserAssistant |
| Subject: | - |
| Author: | Realistic Media Inc. |
| Keywords: | - |
| Comments: | IEBrowserAssistant |
| Words: | 2 |
| ModifyDate: | 2018:11:28 03:24:31 |
| LastPrinted: | 2018:11:28 03:24:31 |
Total processes
57
Monitored processes
18
Malicious processes
2
Suspicious processes
0
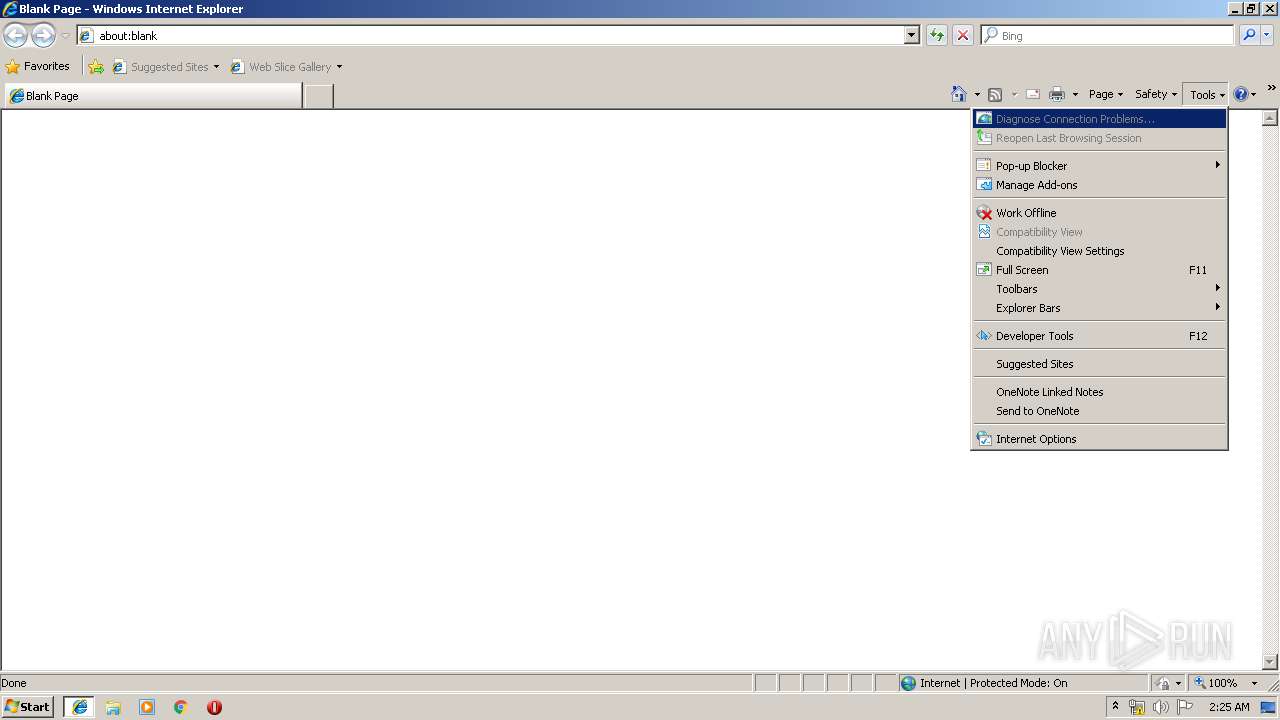
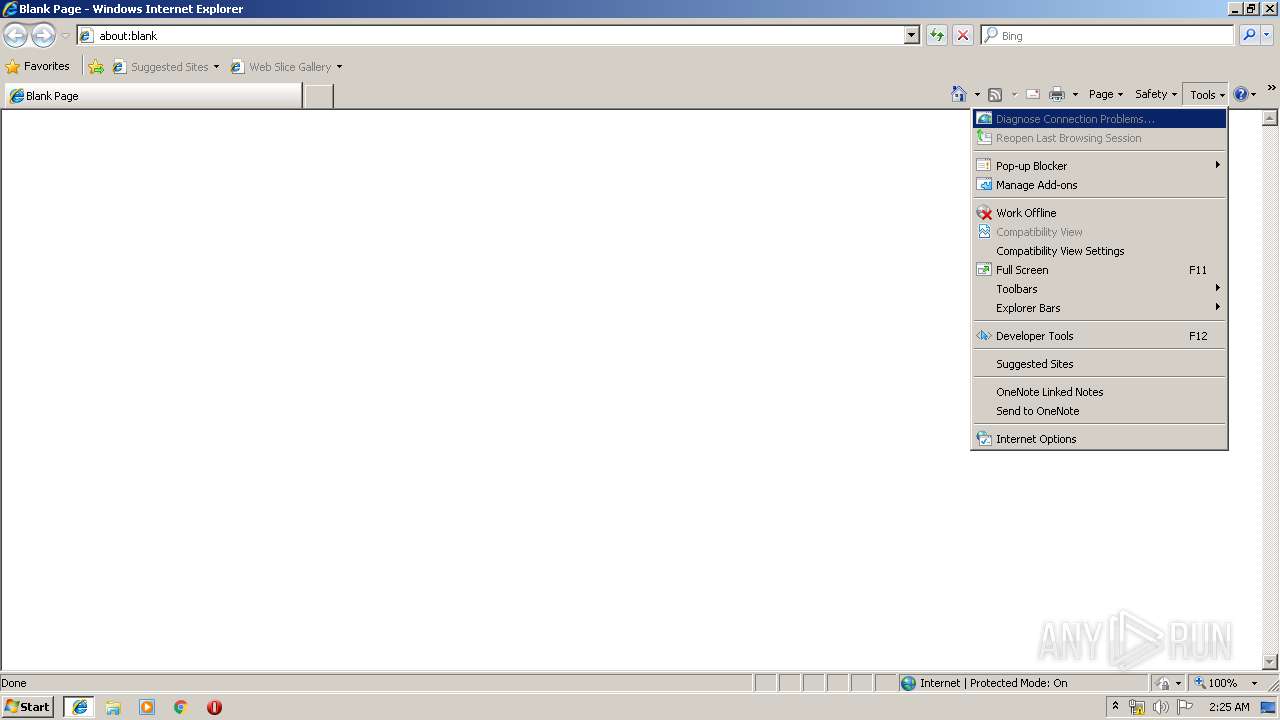
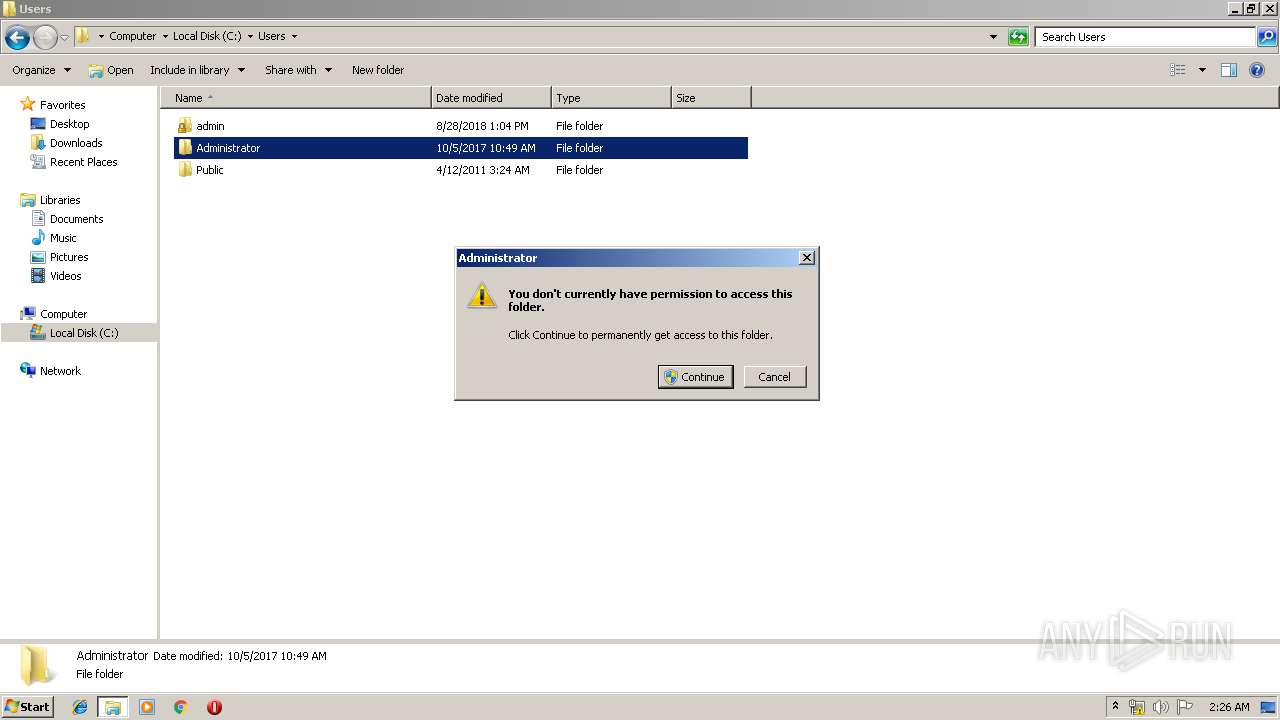
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | C:\Windows\system32\MsiExec.exe -Embedding D00F17DD432756DBB2A3F85FC1F5BBA4 C | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,5214538559057777761,14540555770932386255,131072 --enable-features=PasswordImport --service-pipe-token=17644999048343374584 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17644999048343374584 --renderer-client-id=3 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2112 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1792 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
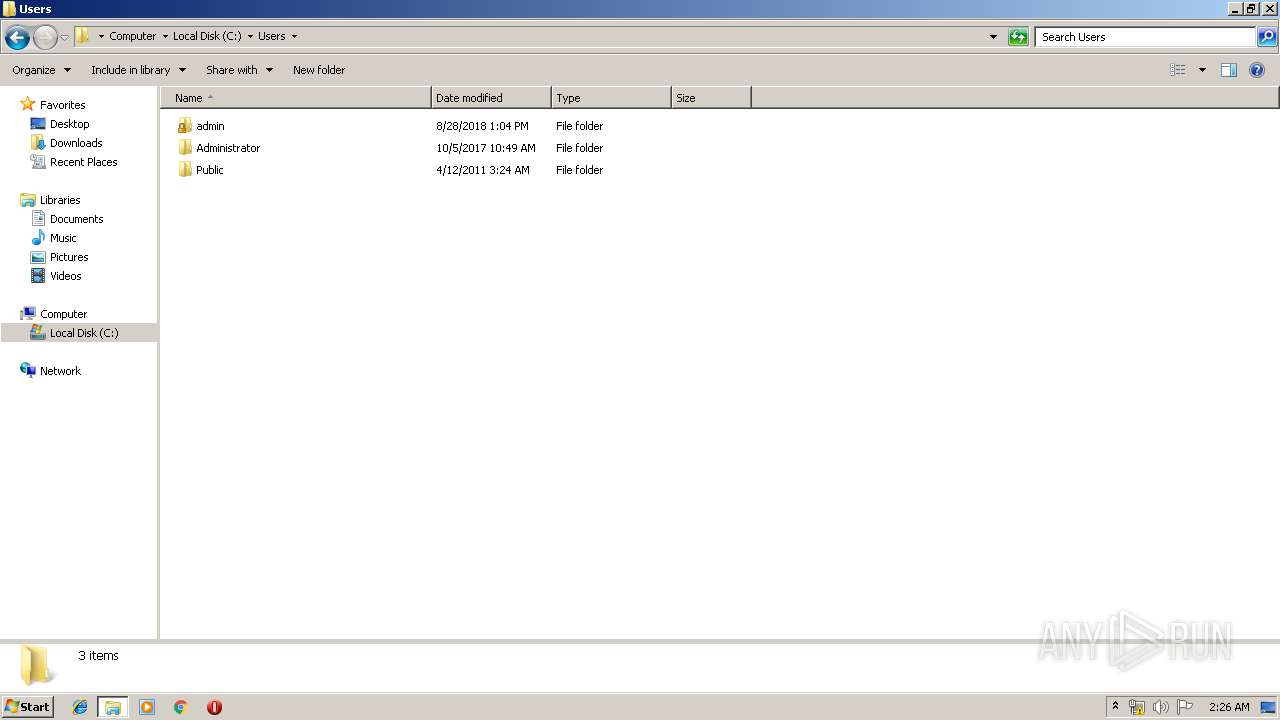
| 1816 | "C:\Users\admin\AppData\Roaming\IEBrowserAssistant\adxregistrator.exe" /install="IEBrowserAssistant.dll" /privileges=admin | C:\Users\admin\AppData\Roaming\IEBrowserAssistant\adxregistrator.exe | — | msiexec.exe | |||||||||||
User: admin Company: Add-in Express Ltd. Integrity Level: MEDIUM Description: adxregistrator Exit code: 0 Version: 9.6.6130.0 Modules
| |||||||||||||||
| 1916 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6e950f18,0x6e950f28,0x6e950f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2080 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,5214538559057777761,14540555770932386255,131072 --enable-features=PasswordImport --service-pipe-token=10338378988806278097 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10338378988806278097 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1984 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2616 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot18" "" "" "6792c44eb" "00000000" "000004C0" "000004AC" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 246
Read events
791
Write events
439
Delete events
16
Modification events
| (PID) Process: | (3644) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2080) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000F6F79AA43C05D5012008000038040000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2080) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000F6F79AA43C05D5012008000038040000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2080) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 20 | |||
| (PID) Process: | (2080) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000003EF216A53C05D5012008000038040000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2080) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000985419A53C05D5012008000028010000E803000001000000000000000000000075C17CD4B7F8A34582D4C277590F3D9A0000000000000000 | |||
| (PID) Process: | (3808) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C2C92EA53C05D501E00E0000240E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3808) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C2C92EA53C05D501E00E000074080000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3808) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C2C92EA53C05D501E00E0000880C0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3808) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4000000000000000C2C92EA53C05D501E00E0000B0090000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
11
Suspicious files
28
Text files
143
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3644 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI7A7C.tmp | — | |
MD5:— | SHA256:— | |||
| 2080 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2080 | msiexec.exe | C:\Windows\Installer\eee15.msi | — | |
MD5:— | SHA256:— | |||
| 2080 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{d47cc175-f8b7-45a3-82d4-c277590f3d9a}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 2616 | DrvInst.exe | C:\Windows\INF\setupapi.ev1 | binary | |
MD5:— | SHA256:— | |||
| 2080 | msiexec.exe | C:\Windows\Installer\MSIF588.tmp | — | |
MD5:— | SHA256:— | |||
| 2080 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DF35706F24941D71CB.TMP | — | |
MD5:— | SHA256:— | |||
| 3808 | vssvc.exe | C: | — | |
MD5:— | SHA256:— | |||
| 2616 | DrvInst.exe | C:\Windows\INF\setupapi.dev.log | ini | |
MD5:— | SHA256:— | |||
| 2080 | msiexec.exe | C:\Windows\Installer\eee18.msi | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
5
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
936 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4016 | chrome.exe | 216.58.215.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
4016 | chrome.exe | 216.58.198.196:443 | www.google.com | Google Inc. | US | whitelisted |
936 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4016 | chrome.exe | 172.217.18.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
4016 | chrome.exe | 216.58.204.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |