| URL: | https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=7&cad=rja&uact=8&ved=2ahUKEwj0xb3PmvzmAhXE1FkKHbaLBfwQFjAGegQIBhAB&url=https%3A%2F%2Fdepakschuur.nl%2Fcupones-de-cinepolis-2019.html&usg=AOvVaw3gtd5_1KVncx2MzKGmO2O_ |
| Full analysis: | https://app.any.run/tasks/7af45a31-f77c-491a-9ed0-d7d5dafc2221 |
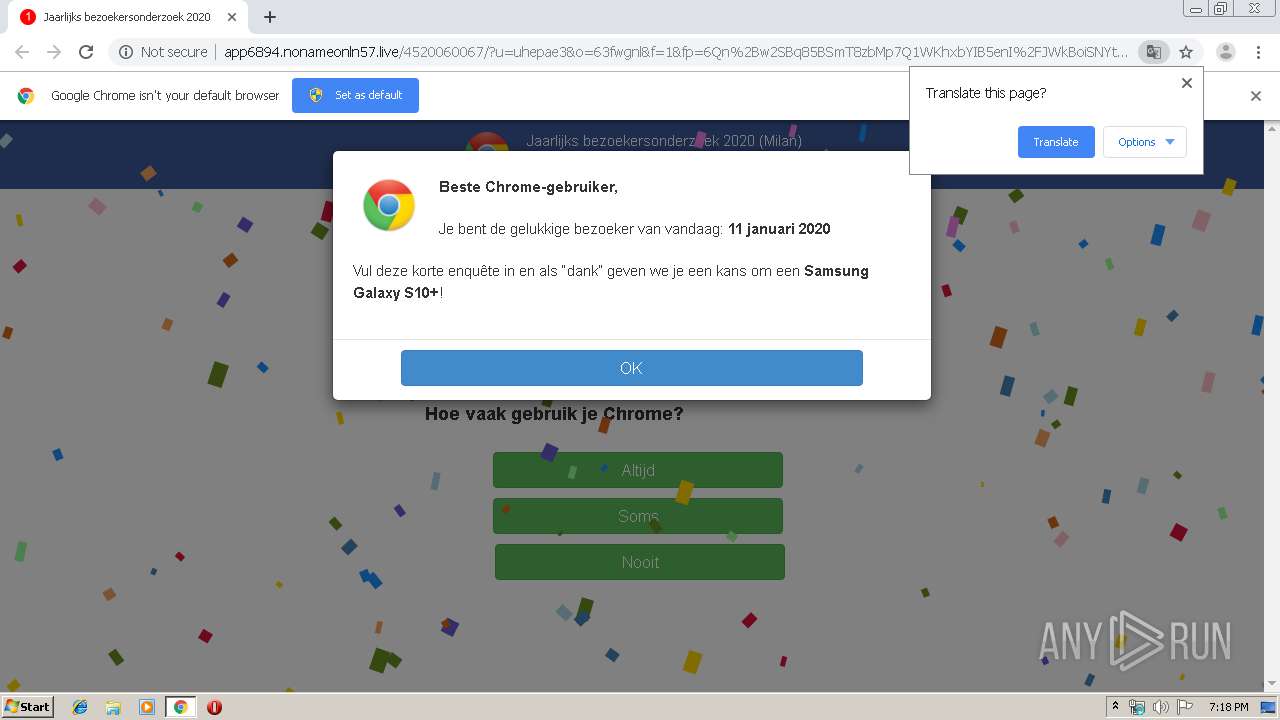
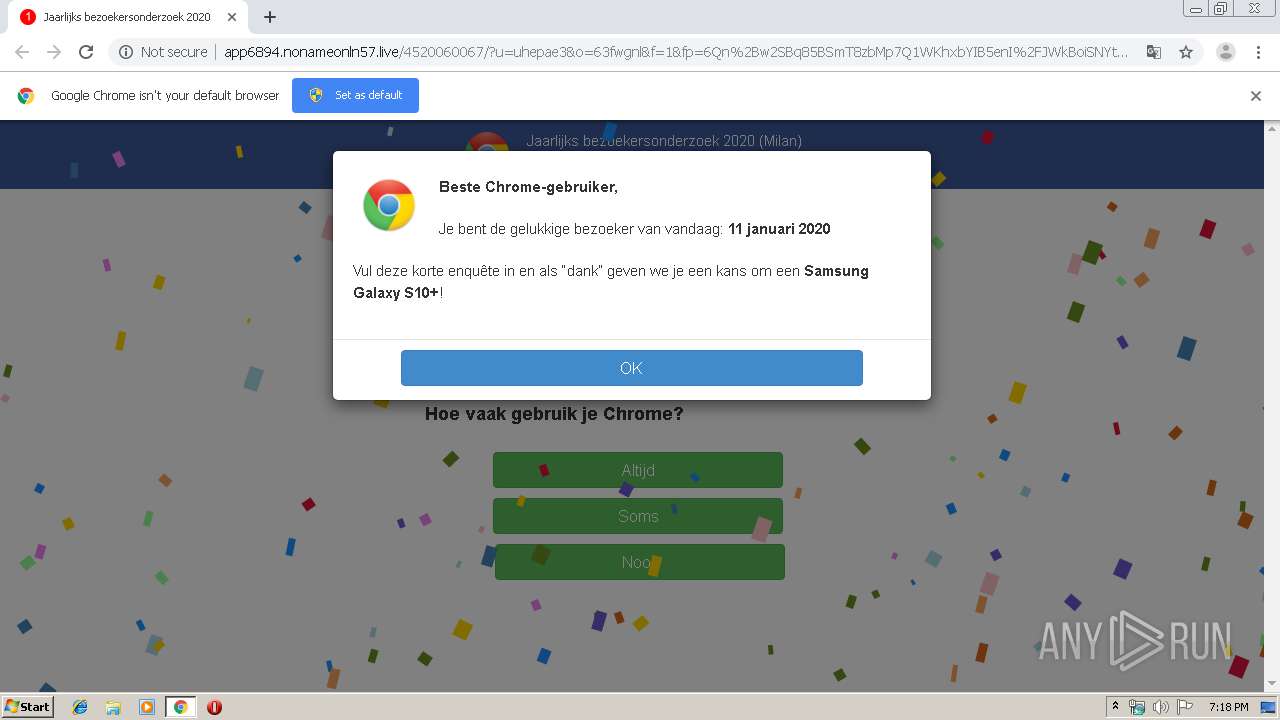
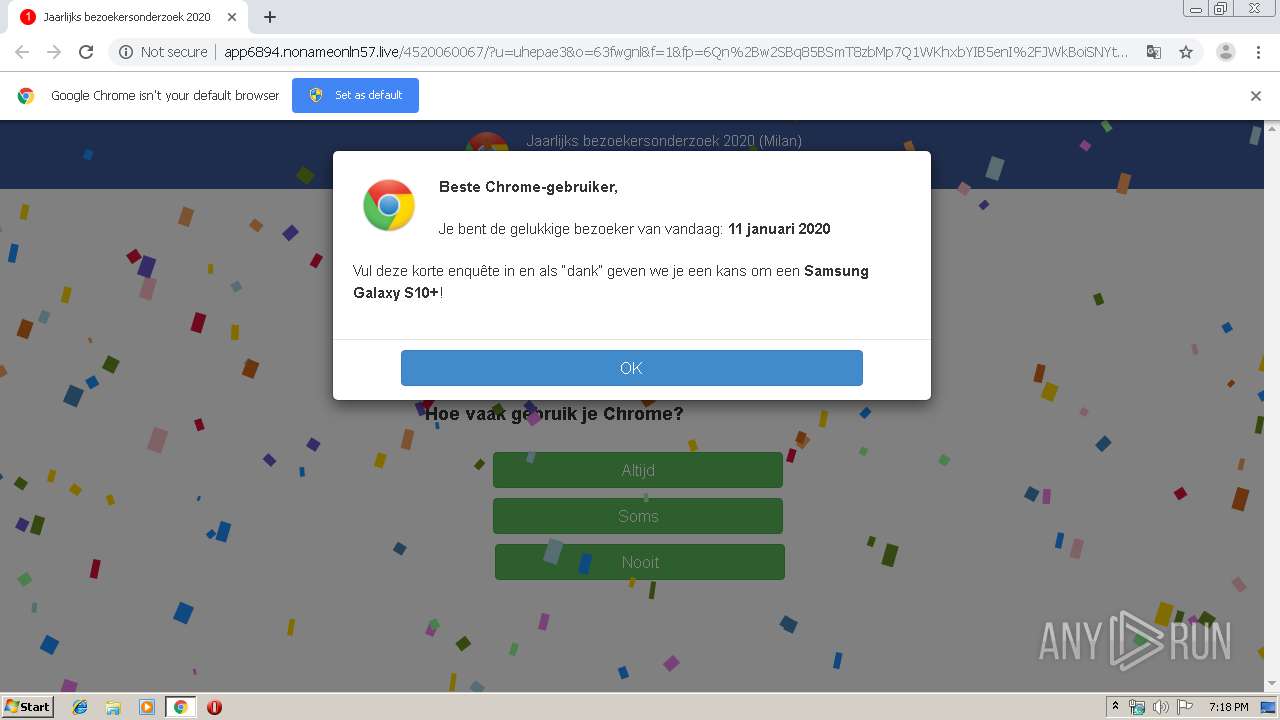
| Verdict: | Malicious activity |
| Analysis date: | January 11, 2020, 19:18:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 9FBA2EC34577C4A83DE7145125633096 |
| SHA1: | 350874C76AF2FA480B9D9568DD363679BCF91A5F |
| SHA256: | 6FC1A78D48689CC80DD335BAB058D81B3A252077755777088F171C0C989CEC40 |
| SSDEEP: | 6:2OLI2sq+wGw4pNXVR6DSwACwRR3zXOU2Jy6bBVF5RHSFMZ6:2V2AnNlRoS11nTAJy6bJYME |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2160)
INFO
Reads the hosts file
- chrome.exe (PID: 1884)
- chrome.exe (PID: 2160)
Application launched itself
- chrome.exe (PID: 2160)
Reads settings of System Certificates
- chrome.exe (PID: 1884)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11940689300443047227,3979153711746272832,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=836828994029065791 --renderer-client-id=26 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11940689300443047227,3979153711746272832,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14711940247028332161 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=996,11940689300443047227,3979153711746272832,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=3491870220119411935 --mojo-platform-channel-handle=1024 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11940689300443047227,3979153711746272832,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11282504543152881017 --mojo-platform-channel-handle=3488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1796 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11940689300443047227,3979153711746272832,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8074673424347332784 --mojo-platform-channel-handle=4336 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1884 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11940689300443047227,3979153711746272832,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=4193240747875990191 --mojo-platform-channel-handle=1568 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11940689300443047227,3979153711746272832,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15277973427481949836 --mojo-platform-channel-handle=4356 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1956 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11940689300443047227,3979153711746272832,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=797645181724077101 --mojo-platform-channel-handle=4460 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=996,11940689300443047227,3979153711746272832,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16009442890629388559 --mojo-platform-channel-handle=3788 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=996,11940689300443047227,3979153711746272832,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5604047678560909359 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3412 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
231
Read events
161
Write events
66
Delete events
4
Modification events
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2620) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2160-13223243905946750 |
Value: 259 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2160) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
23
Text files
181
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d337cc42-a8e5-4d78-9cec-c289082d50a6.tmp | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a8dd.TMP | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a90c.TMP | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2160 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39a90c.TMP | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
29
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
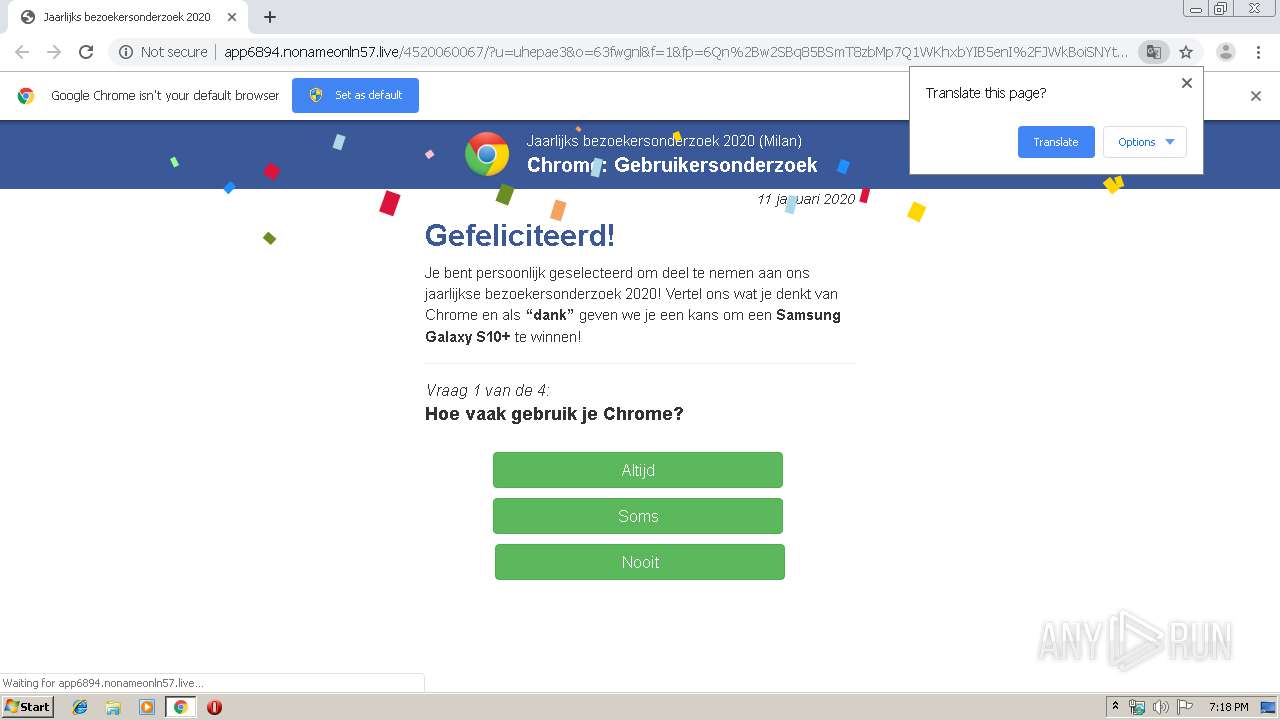
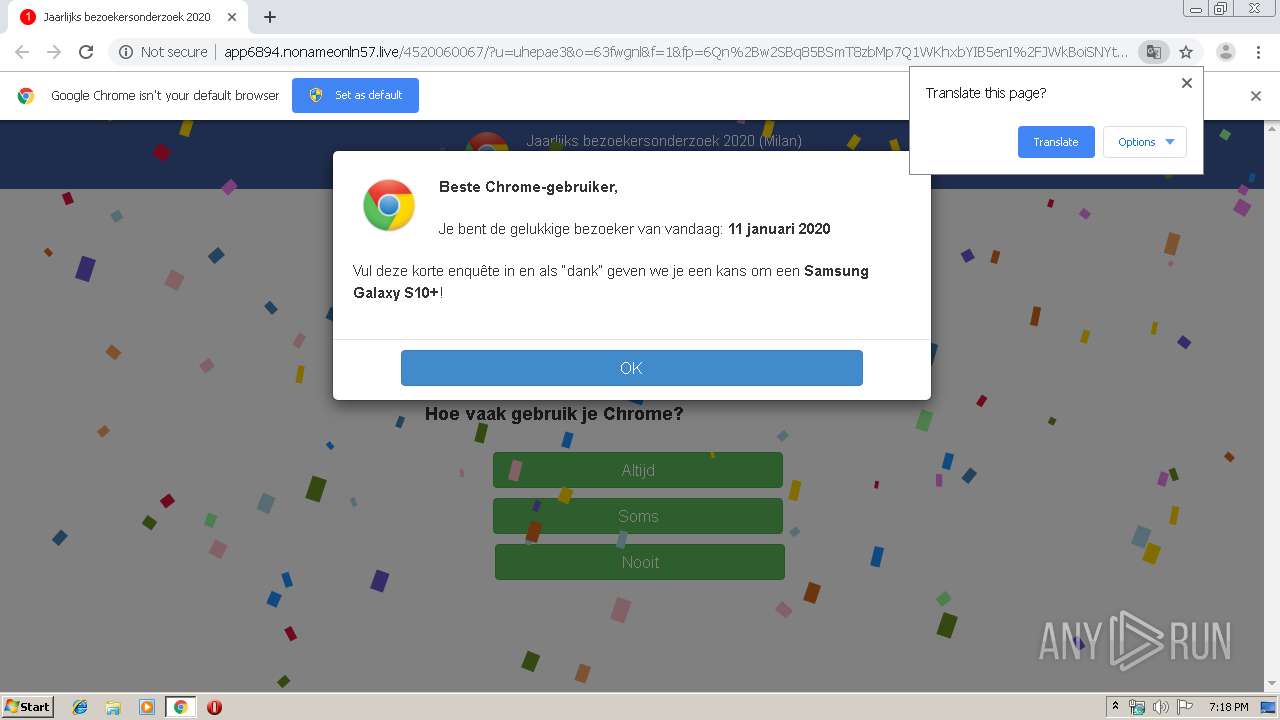
1884 | chrome.exe | GET | 302 | 212.224.112.133:80 | http://mainflow.website/?25F7&charset=utf-8&source=depakschuur.nl&keyword=cupones%20de%20cinepolis%202019 | DE | — | — | suspicious |
1884 | chrome.exe | GET | 200 | 185.89.102.47:80 | http://app6894.nonameonln57.live/media/mainstream/nl/wap/mobsurvey/modernizr-2.6.2-respond-1.1.0.min.js | UA | html | 17.8 Kb | unknown |
1884 | chrome.exe | GET | 200 | 5.8.35.161:80 | http://dekarperboer.online/?u=uhepae3&o=63fwgnl | NL | html | 46.8 Kb | suspicious |
1884 | chrome.exe | GET | 200 | 185.89.102.47:80 | http://app6894.nonameonln57.live/media/mainstream/nl/wap/mobsurvey/font-awesome.css | UA | text | 17.2 Kb | unknown |
1884 | chrome.exe | GET | 200 | 185.89.102.47:80 | http://app6894.nonameonln57.live/4520060067/?u=uhepae3&o=63fwgnl&f=1&fp=6Qn%2Bw2SBq85BSmT8zbMp7Q1WKhxbYIB5enI%2FJWkBoiSNYtLF0x9I6NLKC3VBxPnnIaYq4GCSPvmjicIi1skfkyUK%2F7ZsBf6QN89K4M4LL3XanXBzPoG9FjkLjTpPn7WbkiNV8sLZgkxpBhhYJqaFrZe8adoXTWViGM6AwHAgSoyP9ObUPthSXsOJLR0qbeRxMwroQZNRz4OulCLMLIPBxIkPCb7uTNJXsgmYZo3IUS0snfLpseo55w1awJ%2Bw35IVgL6zofMib8OQCqULid5tj38QFndbBkN2q7ArWFVYfXpIxoq1lMn4L6I2uWND72Yh8L3ArYISy1n2bhsbX5QaNKVud5ZU74CDYULat5ri9VV9gUe4C3lRPycAa11r%2FocwEMtCBFfr%2B8FIpN9HxTbeD3pxNhcSNBq89sLfaguK9ieDHCkknXESFIIWrguwhBQpF9dHtZruTbgBMKN68KxoxEYDX1PbTwrhYMkFr%2F3opr7Lpn7NTl56Kg6FsTU1m6scB%2FcamdICFSlQV%2FNxg48K43eudRaKWkxEYA0uOZX7brZsAsqEoZi1kysu6EYPTLbYVTMaYYLQcw57YxJC1TTkDqJrOa89FOKszUU0aN%2Fkf7XEgziNvpzE9fJjb9AEdbn%2FnVtvlOYwf6jU5UL4YAh9ULsXcvroHTKjIu4iyL2hdbA4oB7B7W6iREevKX6ruTjUa2n8w0I6bQQgI3LZ7%2FIZfEJ7y0E2nI6Gl0p8hPcxl5%2Bo0YMvtDfh%2FoPNAqUhFeNQWKMexwSrnRF2aMEbHGH8aA%3D%3D | UA | html | 16.7 Kb | unknown |
1884 | chrome.exe | GET | 200 | 185.89.102.47:80 | http://app6894.nonameonln57.live/media/mainstream/nl/wap/mobsurvey/main.css | UA | text | 7.03 Kb | unknown |
1884 | chrome.exe | GET | 200 | 185.89.102.47:80 | http://app6894.nonameonln57.live/media/mainstream/us/wap/mobsurvey/logo1.js | UA | text | 12.7 Kb | unknown |
1884 | chrome.exe | GET | 200 | 185.89.102.47:80 | http://app6894.nonameonln57.live/media/mainstream/nl/wap/mobsurvey/nl-en.js | UA | text | 5.03 Kb | unknown |
1884 | chrome.exe | GET | 302 | 216.58.206.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
1884 | chrome.exe | GET | 200 | 185.89.102.47:80 | http://app6894.nonameonln57.live/media/mainstream/us/wap/mobsurvey/comment.js | UA | text | 2.77 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1884 | chrome.exe | 172.217.22.10:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
1884 | chrome.exe | 104.27.184.207:443 | depakschuur.nl | Cloudflare Inc | US | unknown |
1884 | chrome.exe | 172.217.22.3:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1884 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
1884 | chrome.exe | 216.58.207.74:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1884 | chrome.exe | 83.140.30.11:443 | media4.picsearch.com | Availo Networks AB | SE | unknown |
1884 | chrome.exe | 204.79.197.200:443 | tse3.mm.bing.net | Microsoft Corporation | US | whitelisted |
— | — | 212.224.112.133:80 | mainflow.website | First Colo GmbH | DE | suspicious |
1884 | chrome.exe | 5.8.35.161:80 | dekarperboer.online | LLHost Inc | NL | suspicious |
1884 | chrome.exe | 185.89.102.47:80 | app6894.nonameonln57.live | LLHost Inc | UA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.google.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
depakschuur.nl |
| unknown |
translate.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
media4.picsearch.com |
| unknown |
tse3.mm.bing.net |
| whitelisted |
tse2.mm.bing.net |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report