| File name: | M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe |
| Full analysis: | https://app.any.run/tasks/812588ee-1c79-4ca7-9505-b13123e94c89 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2023, 17:01:01 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 24DF7AD59EABBE35724E792E7A2EE529 |
| SHA1: | 08EB769AE922185B7746FB358249CA11BF3916B9 |
| SHA256: | 6FBA3A266639DE2E75DEF408F50ED3C886F9541724BF8DB0F1FA276538E8C093 |
| SSDEEP: | 393216:RSFiOb2vyWNWPcCPMKxMnxE6X7HL6xEjccfLExHuDJsv6tWKFdu9CN:RSFiOb2H7HL6Sp |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the date of Windows installation
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 5844)
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 7000)
Application launched itself
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 5844)
Executable content was dropped or overwritten
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 7000)
- GORGEOUSqSystem.exe (PID: 7152)
The process creates files with name similar to system file names
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 7000)
INFO
The process checks LSA protection
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 5844)
- slui.exe (PID: 6608)
- GORGEOUSqSystem.exe (PID: 7152)
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 7000)
Process checks computer location settings
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 5844)
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 7000)
Checks supported languages
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 5844)
- GORGEOUSqSystem.exe (PID: 7152)
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 7000)
Reads the computer name
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 7000)
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 5844)
- GORGEOUSqSystem.exe (PID: 7152)
Creates files in the program directory
- M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe (PID: 7000)
- GORGEOUSqSystem.exe (PID: 7152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (35.6) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (34.4) |
| .exe | | | Win64 Executable (generic) (22.8) |
| .exe | | | Win32 Executable (generic) (3.7) |
| .exe | | | Generic Win/DOS Executable (1.6) |
EXIF
EXE
| ProductVersion: | 1.4.0.05 |
|---|---|
| ProductName: | GORGEOUS Seed SYSTEM |
| OriginalFileName: | GORGEOUSSeedSYSTEM.exe |
| LegalCopyright: | GORGEOUS Seed SYSTEM Company |
| InternalName: | GORGEOUSSeedSYSTEM.exe |
| FileVersion: | 1.4.0.05 |
| FileDescription: | GORGEOUS Seed SYSTEM |
| CompanyName: | GORGEOUS Seed |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.4.0.5 |
| FileVersionNumber: | 1.4.0.5 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5.1 |
| ImageVersion: | - |
| OSVersion: | 5.1 |
| EntryPoint: | 0xa7b3ae |
| UninitializedDataSize: | - |
| InitializedDataSize: | 3381248 |
| CodeSize: | 11520000 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, 32-bit |
| TimeStamp: | 2023:01:18 13:18:54+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 18-Jan-2023 13:18:54 |
| Detected languages: |
|
| CompanyName: | GORGEOUS Seed |
| FileDescription: | GORGEOUS Seed SYSTEM |
| FileVersion: | 1.4.0.05 |
| InternalName: | GORGEOUSSeedSYSTEM.exe |
| LegalCopyright: | GORGEOUS Seed SYSTEM Company |
| OriginalFilename: | GORGEOUSSeedSYSTEM.exe |
| ProductName: | GORGEOUS Seed SYSTEM |
| ProductVersion: | 1.4.0.05 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 18-Jan-2023 13:18:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00AFC701 | 0x00AFC800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60887 |
.rdata | 0x00AFE000 | 0x002CAE56 | 0x002CB000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.51849 |
.data | 0x00DC9000 | 0x00016E6C | 0x0000DE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.64857 |
.qtmetadL\x02 | 0x00DE0000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 3.15593 |
.rsrc | 0x00DE1000 | 0x00010E08 | 0x00011000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.87355 |
.reloc | 0x00DF2000 | 0x0004F5E4 | 0x0004F600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.63484 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.79597 | 346 | Latin 1 / Western European | English - United States | RT_MANIFEST |
IDI_ICON1 | 1.98048 | 20 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
CRYPT32.dll |
GDI32.dll |
IMM32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
WINMM.dll |
WLDAP32.dll |
Total processes
130
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5844 | "C:\Users\admin\AppData\Local\Temp\M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe" | C:\Users\admin\AppData\Local\Temp\M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | — | explorer.exe | |||||||||||
User: admin Company: GORGEOUS Seed Integrity Level: MEDIUM Description: GORGEOUS Seed SYSTEM Exit code: 0 Version: 1.4.0.05 Modules
| |||||||||||||||
| 6608 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7000 | "C:\Users\admin\AppData\Local\Temp\M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe" /restr | C:\Users\admin\AppData\Local\Temp\M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | ||||||||||||
User: admin Company: GORGEOUS Seed Integrity Level: HIGH Description: GORGEOUS Seed SYSTEM Exit code: 0 Version: 1.4.0.05 Modules
| |||||||||||||||
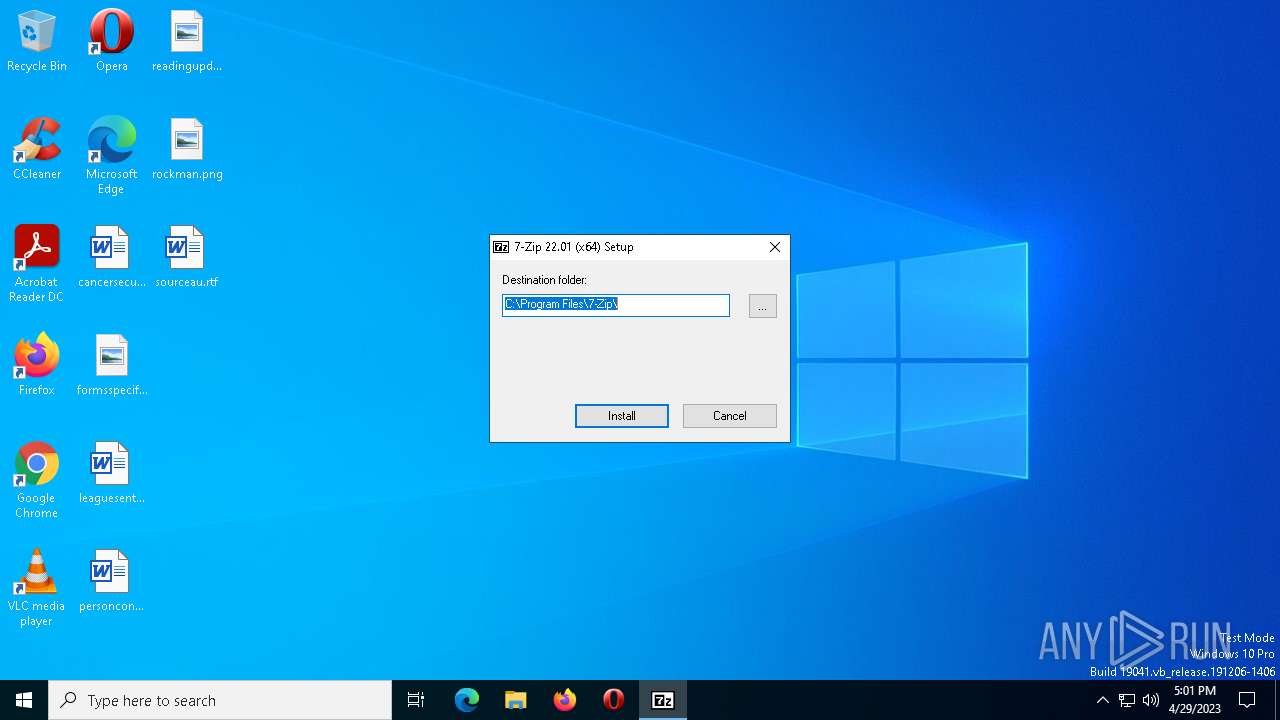
| 7152 | "C:\Program Files (x86)\GORGEOUSSeedphoSystem\GORGEOUSqSystem.exe" | C:\Program Files (x86)\GORGEOUSSeedphoSystem\GORGEOUSqSystem.exe | M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Installer Exit code: 0 Version: 22.01 Modules
| |||||||||||||||
Total events
4 310
Read events
4 278
Write events
32
Delete events
0
Modification events
| (PID) Process: | (5844) M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (5844) M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (5844) M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (5844) M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (7000) M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (7000) M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (7000) M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (7000) M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
20
Suspicious files
6
Text files
194
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7152 | GORGEOUSqSystem.exe | C:\Program Files\7-Zip\Lang\ar.txt | text | |
MD5:1C45E6A6ECB3B71A7316C466B6A77C1C | SHA256:972261B53289DE2BD8A65E787A6E7CD6DEFC2B5F7E344128F2FE0492ED30CCF1 | |||
| 7152 | GORGEOUSqSystem.exe | C:\Program Files\7-Zip\Lang\az.txt | text | |
MD5:81B732A8B4206FB747BFBFE524DDE192 | SHA256:CAEC460E73BD0403C2BCDE7E773459BEA9112D1BFACBE413D4F21E51A5762BA6 | |||
| 7152 | GORGEOUSqSystem.exe | C:\Program Files\7-Zip\Lang\ast.txt | text | |
MD5:1F86AE235BC747A279C9E9EC72675CE4 | SHA256:8FCD1B8CE6FED05F406C4B81AEA821132800BC494D3FD6F42A4258A81F8998EC | |||
| 7152 | GORGEOUSqSystem.exe | C:\Program Files\7-Zip\Lang\be.txt | text | |
MD5:3C21135144AC7452E7DB66F0214F9D68 | SHA256:D095879B8BBC67A1C9875C5E9896942BACF730BD76155C06105544408068C59E | |||
| 7152 | GORGEOUSqSystem.exe | C:\Program Files\7-Zip\7-zip.chm | chm | |
MD5:34208890A28244903621CD32CC3FBDFC | SHA256:4B6939646570C9DDB5BFD39B8503EED99D8C64337E72F6DD4F9DDCFB4AC76703 | |||
| 7152 | GORGEOUSqSystem.exe | C:\Program Files\7-Zip\Lang\af.txt | text | |
MD5:FBBE51ACB879B525CC6B19D386697924 | SHA256:3793FB69EE9FD958CF15A272B1ED54E4B3D75592836EBCD085DC0E7B1400D1CB | |||
| 7152 | GORGEOUSqSystem.exe | C:\Program Files\7-Zip\Lang\bg.txt | text | |
MD5:833AFB4F88FDB5F48245C9B65577DC19 | SHA256:4DCABCC8AB8069DB79143E4C62B6B76D2CF42666A09389EACFC35074B61779E3 | |||
| 7152 | GORGEOUSqSystem.exe | C:\Program Files\7-Zip\Lang\ca.txt | text | |
MD5:1657720023A267B5B625DE17BF292299 | SHA256:ED8748DA8FA99DB775FF621D3E801E2830E6C04DA42C0B701095580191A700A6 | |||
| 7152 | GORGEOUSqSystem.exe | C:\Program Files\7-Zip\Lang\an.txt | text | |
MD5:BF8564B2DAD5D2506887F87AEE169A0A | SHA256:0E8DD119DFA6C6C1B3ACA993715092CDF1560947871092876D309DBC1940A14A | |||
| 7152 | GORGEOUSqSystem.exe | C:\Program Files\7-Zip\Lang\bn.txt | text | |
MD5:D0E788F64268D15B4391F052B1F4B18A | SHA256:216CC780E371DC318C8B15B84DE8A5EC0E28F712B3109A991C8A09CDDAA2A81A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
40
DNS requests
13
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6392 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | binary | 409 b | whitelisted |
6392 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | binary | 418 b | whitelisted |
4736 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
7000 | M.Flight.Simulator.v1.19.9.0-P2P.file_260782.exe | 104.26.10.24:443 | mydownloadmanagersolutions.com | CLOUDFLARENET | US | shared |
6392 | SIHClient.exe | 40.127.169.103:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6392 | SIHClient.exe | 20.3.187.198:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6392 | SIHClient.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4736 | SearchApp.exe | 2.23.209.140:443 | www.bing.com | Akamai International B.V. | GB | suspicious |
4736 | SearchApp.exe | 2.23.209.130:443 | www.bing.com | Akamai International B.V. | GB | malicious |
— | — | 192.229.221.95:80 | — | EDGECAST | US | whitelisted |
— | — | 20.190.160.20:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 20.190.160.14:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
officeclient.microsoft.com |
| whitelisted |
mydownloadmanagersolutions.com |
| suspicious |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
r.bing.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |