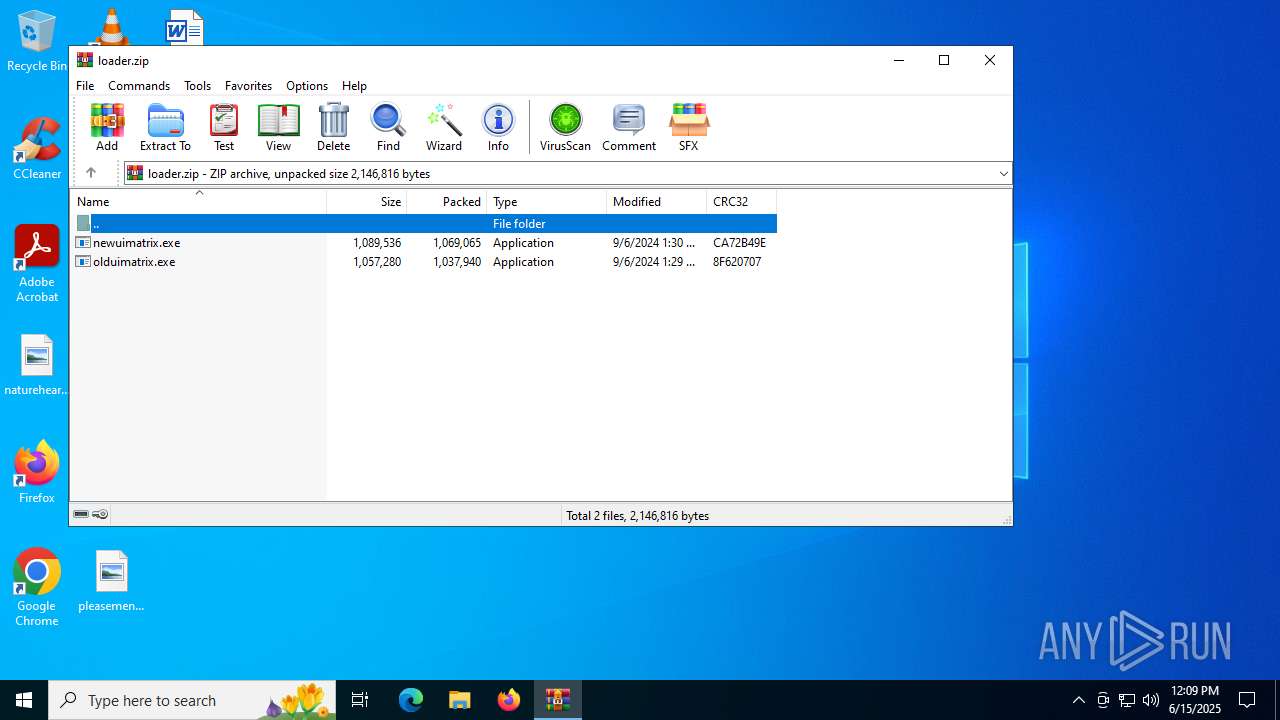
| File name: | loader.zip |
| Full analysis: | https://app.any.run/tasks/cc3f0d5b-6de2-45f0-9cc4-28e35a47cbdc |
| Verdict: | Malicious activity |
| Analysis date: | June 15, 2025, 12:08:51 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | D5A0710422F411DB980E3DA726986C80 |
| SHA1: | 035BA8661562ADD61E6AF6D3306B5ED178442962 |
| SHA256: | 6FB0DC970C9F32A9D3442FDD3D4838CEDA9CE5D4EF26D8A21F70EA6FEB05900D |
| SSDEEP: | 98304:W2jByvoFt7LlK+7aBZFAJgHAK2fkyHk2lBN80pJPTI9X9/gQnH5wM+SX1pTjFFR9:XF9w |
MALICIOUS
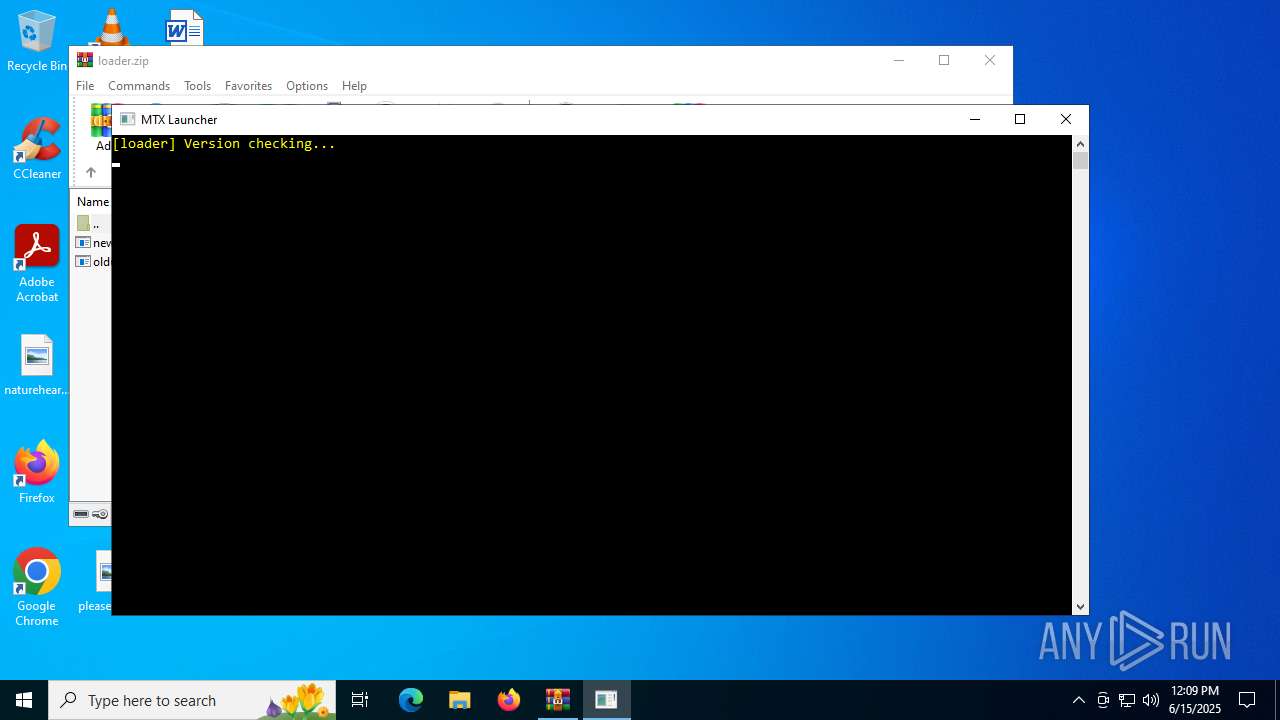
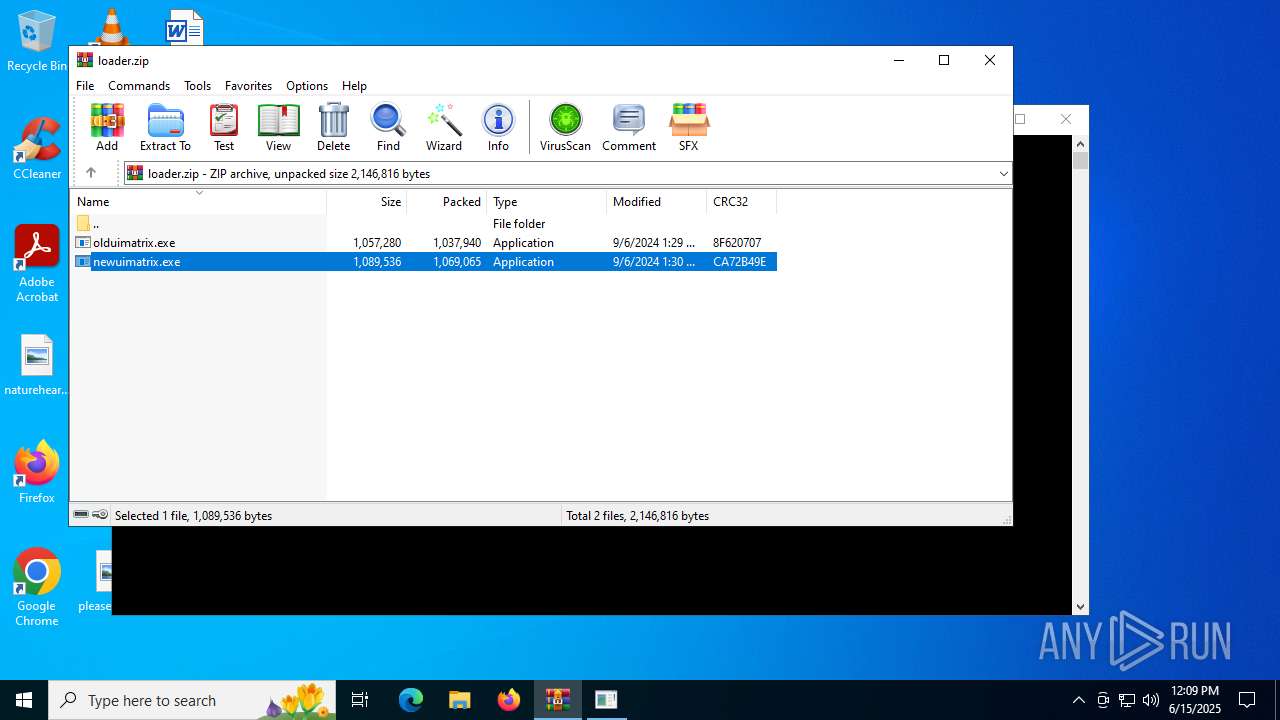
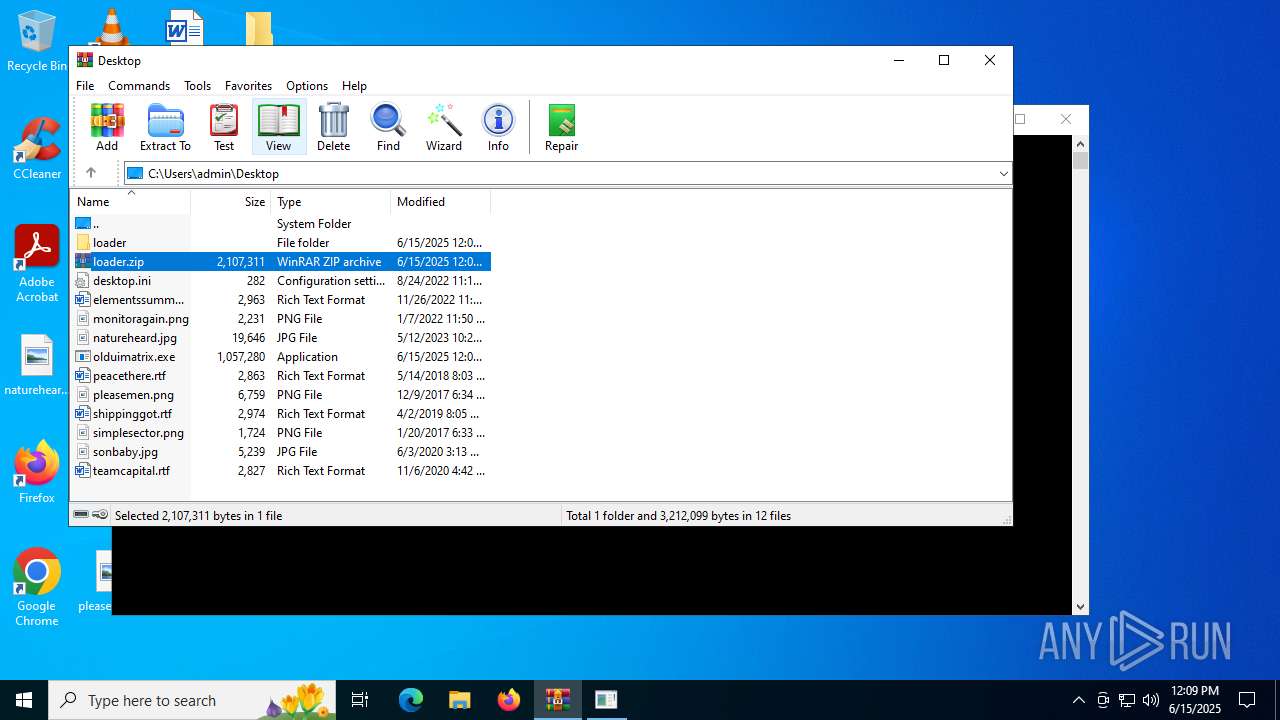
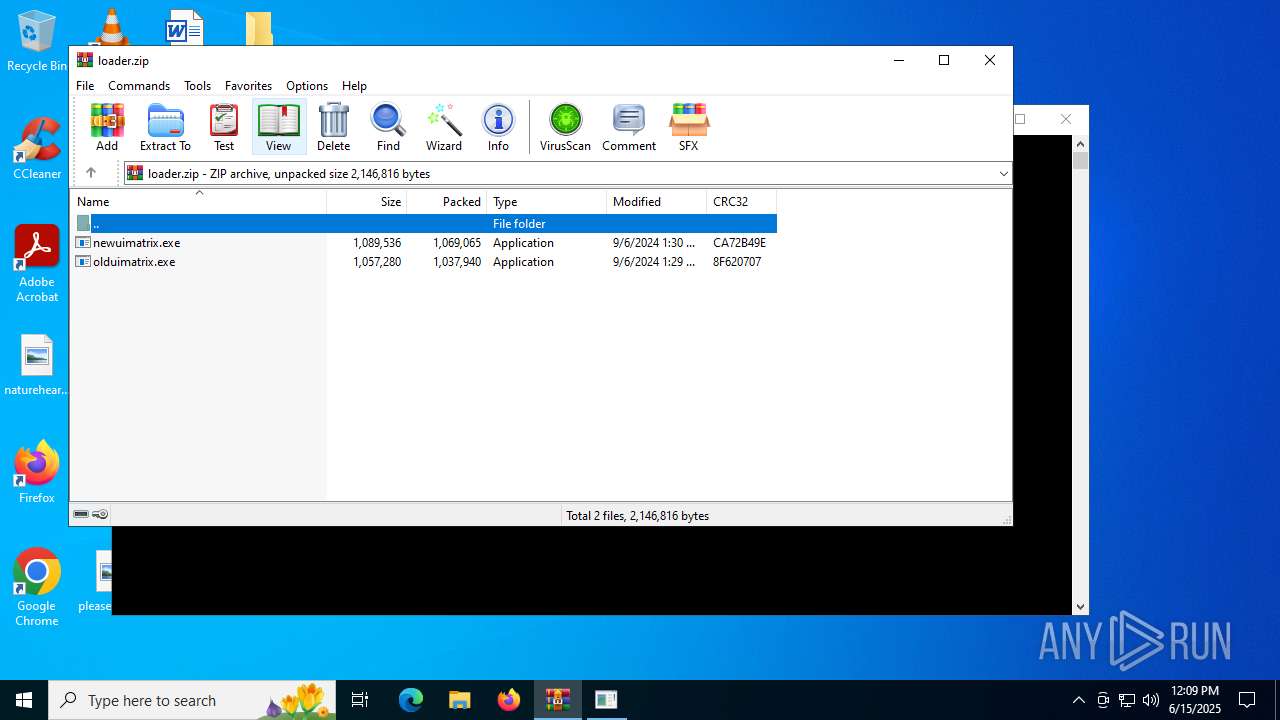
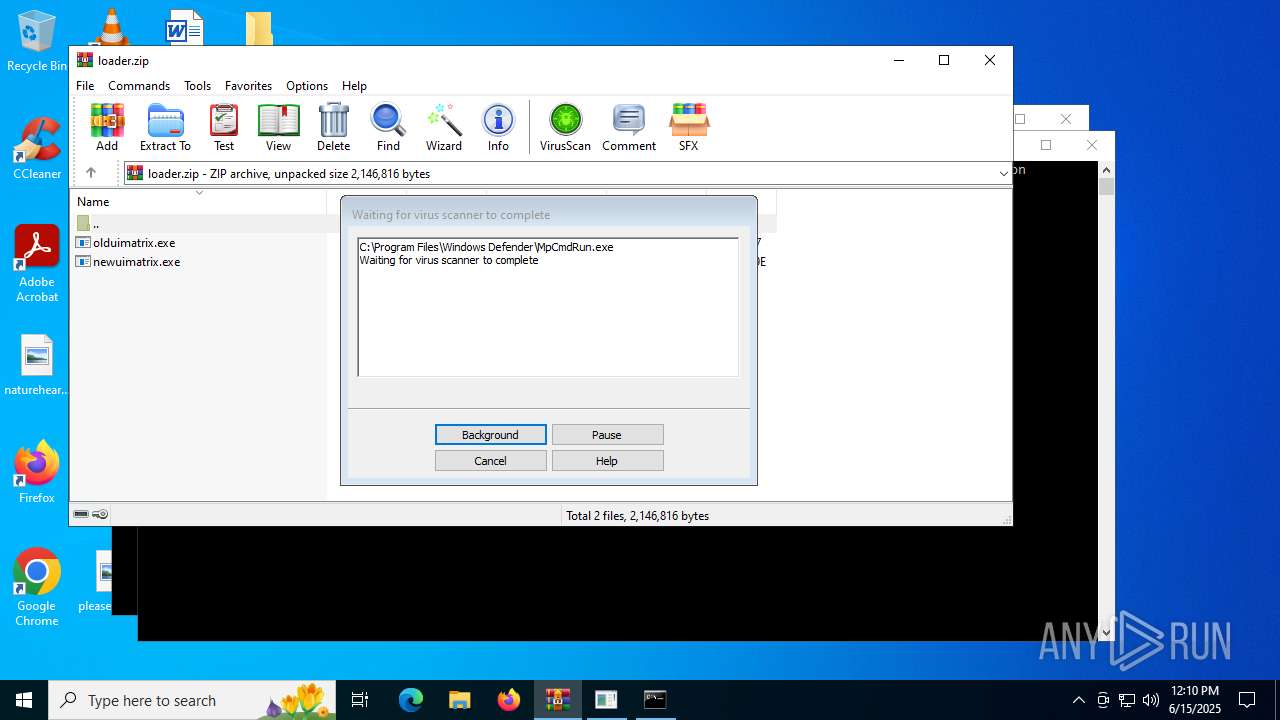
Generic archive extractor
- WinRAR.exe (PID: 1568)
Runs injected code in another process
- olduimatrix.exe (PID: 7116)
Application was injected by another process
- explorer.exe (PID: 4772)
SUSPICIOUS
Connects to the server without a host name
- olduimatrix.exe (PID: 7116)
Modifies hosts file to alter network resolution
- olduimatrix.exe (PID: 7116)
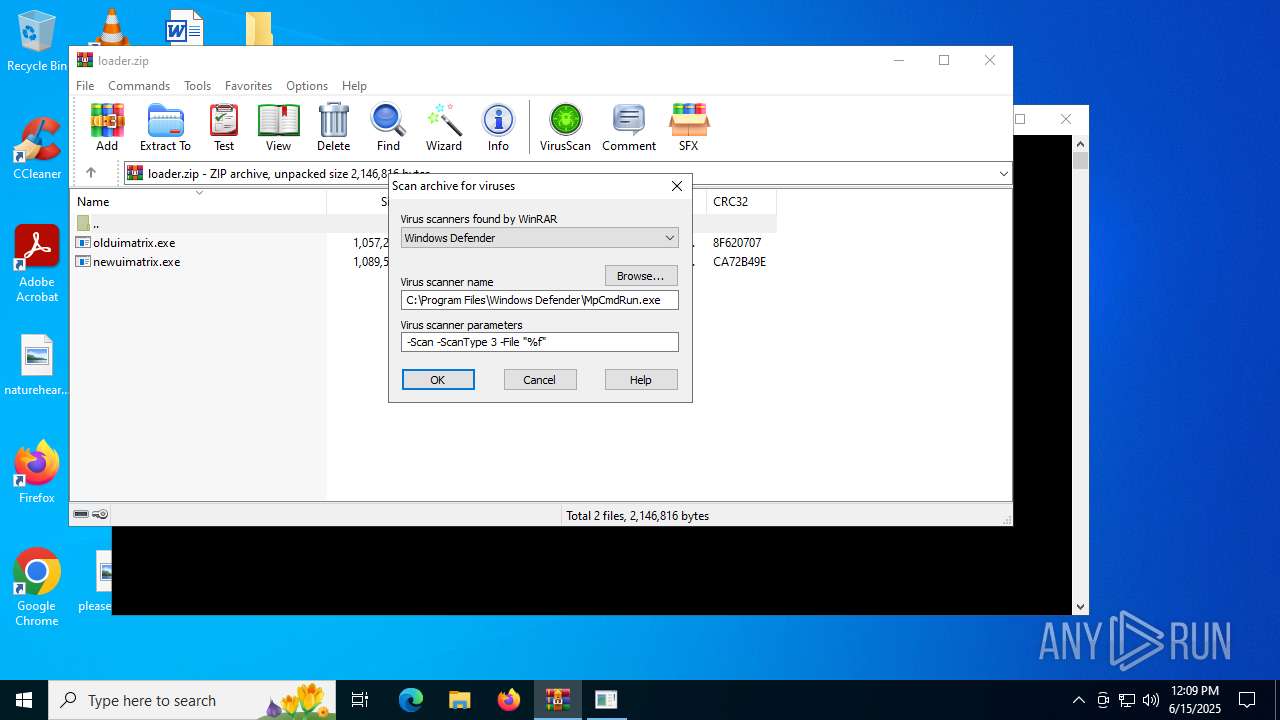
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 1568)
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 1568)
Executing commands from a ".bat" file
- WinRAR.exe (PID: 1568)
INFO
Manual execution by a user
- olduimatrix.exe (PID: 7116)
- olduimatrix.exe (PID: 2804)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4772)
Reads the computer name
- olduimatrix.exe (PID: 7116)
- MpCmdRun.exe (PID: 2804)
Checks supported languages
- olduimatrix.exe (PID: 7116)
- MpCmdRun.exe (PID: 2804)
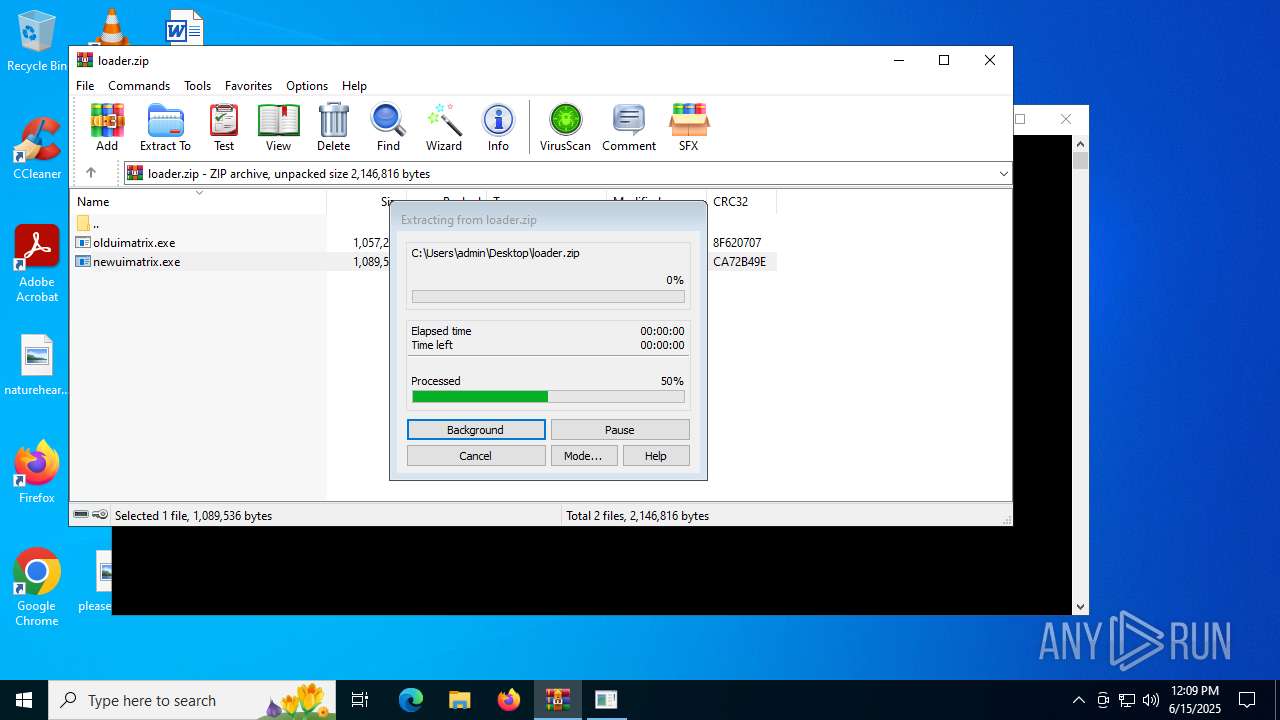
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1568)
Create files in a temporary directory
- MpCmdRun.exe (PID: 2804)
Reads the software policy settings
- slui.exe (PID: 5124)
Checks proxy server information
- slui.exe (PID: 5124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:09:06 20:29:46 |
| ZipCRC: | 0x8f620707 |
| ZipCompressedSize: | 1037940 |
| ZipUncompressedSize: | 1057280 |
| ZipFileName: | olduimatrix.exe |
Total processes
140
Monitored processes
9
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1568 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\loader.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 2804 | "C:\Users\admin\Desktop\olduimatrix.exe" | C:\Users\admin\Desktop\olduimatrix.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2804 | "C:\Program Files\Windows Defender\MpCmdRun.exe" -Scan -ScanType 3 -File "C:\Users\admin\AppData\Local\Temp\Rar$VR1568.21720" | C:\Program Files\Windows Defender\MpCmdRun.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Malware Protection Command Line Utility Exit code: 2 Version: 4.18.1909.6 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3624 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | olduimatrix.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3740 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$VR1568.21720\Rar$Scan65588.bat" " | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4772 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5124 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7116 | "C:\Users\admin\Desktop\olduimatrix.exe" | C:\Users\admin\Desktop\olduimatrix.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
6 794
Read events
6 738
Write events
43
Delete events
13
Modification events
| (PID) Process: | (1568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\loader.zip | |||
| (PID) Process: | (1568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1568) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000702C8 |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\Shell\Bags\1\Desktop |
| Operation: | write | Name: | IconLayouts |
Value: 00000000000000000000000000000000030001000100010011000000000000002C000000000000003A003A007B00360034003500460046003000340030002D0035003000380031002D0031003000310042002D0039004600300038002D003000300041004100300030003200460039003500340045007D003E002000200000001000000000000000430043006C00650061006E00650072002E006C006E006B003E0020007C0000001500000000000000410064006F006200650020004100630072006F006200610074002E006C006E006B003E0020007C00000013000000000000006E0061007400750072006500680065006100720064002E006A00700067003E002000200000000F00000000000000460069007200650066006F0078002E006C006E006B003E0020007C000000150000000000000047006F006F0067006C00650020004300680072006F006D0065002E006C006E006B003E0020007C000000180000000000000056004C00430020006D006500640069006100200070006C0061007900650072002E006C006E006B003E0020007C00000016000000000000004D006900630072006F0073006F0066007400200045006400670065002E006C006E006B003E0020007C000000170000000000000065006C0065006D0065006E0074007300730075006D006D006100720079002E007200740066003E0020002000000014000000000000006D006F006E00690074006F00720061006700610069006E002E0070006E0067003E00200020000000120000000000000070006500610063006500740068006500720065002E007200740066003E00200020000000110000000000000070006C0065006100730065006D0065006E002E0070006E0067003E0020002000000013000000000000007300680069007000700069006E00670067006F0074002E007200740066003E002000200000001400000000000000730069006D0070006C00650073006500630074006F0072002E0070006E0067003E002000200000000F0000000000000073006F006E0062006100620079002E006A00700067003E0020002000000013000000000000007400650061006D006300610070006900740061006C002E007200740066003E002000200000000E000000000000006C006F0061006400650072002E007A00690070003E00200020000000010000000000000002000100000000000000000001000000000000000200010000000000000000001100000006000000010000001100000000000000000000000000000000000000803F0000004008000000803F000040400900000000000000404003000000803F000080400A000000803F0000A0400B0000000040000000000C00000000400000803F0D0000000040000000400E0000000040000040400F00000000000000803F01000000000000000040020000000000000080400400000000000000A04005000000803F0000000006000000803F0000803F070000000040000080401000 | |||
Executable files
3
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7116 | olduimatrix.exe | C:\Windows\System32\version.dat | — | |
MD5:— | SHA256:— | |||
| 4772 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 2804 | MpCmdRun.exe | C:\Users\admin\AppData\Local\Temp\MpCmdRun.log | text | |
MD5:D64536EBBA26841FFB1F1606BCBC6342 | SHA256:2C11F0FE86616F2484F9AB399A403C75DB33E3A730886EBC0C99ED02B5A0873B | |||
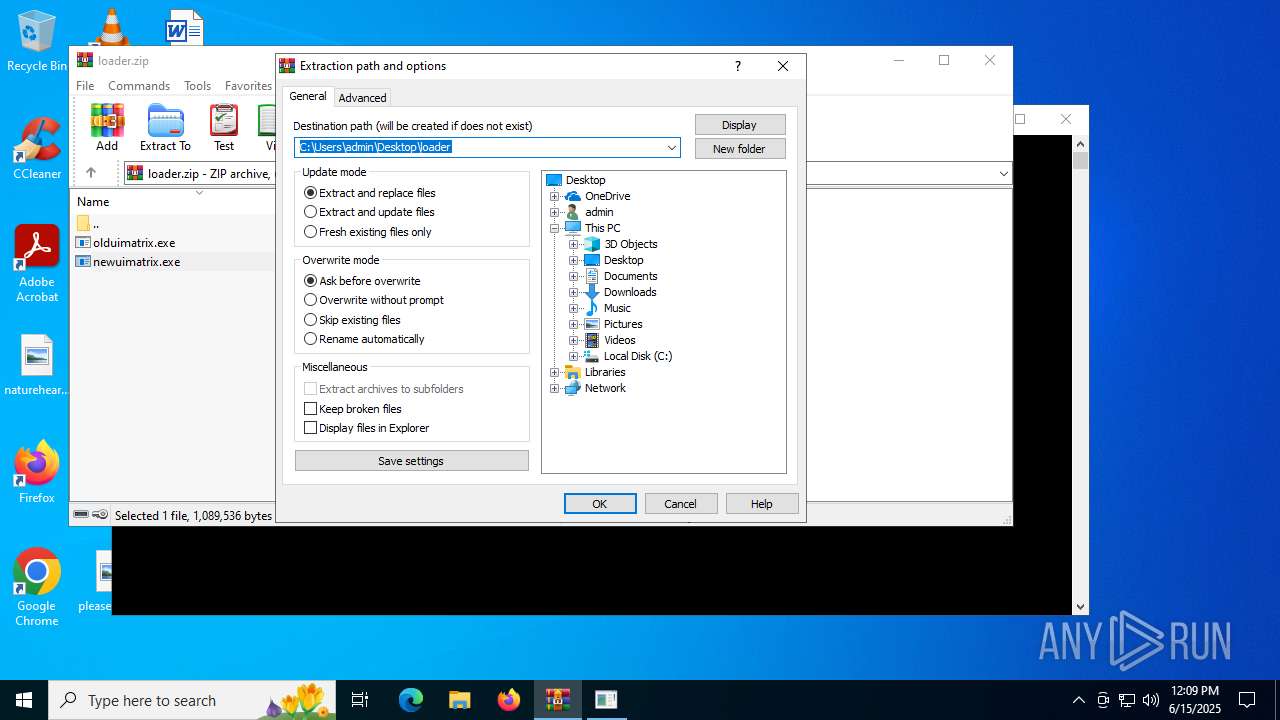
| 1568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1568.21720\loader.zip\newuimatrix.exe | executable | |
MD5:4A6EB12EA7764C04FDFED398F0A95828 | SHA256:E7687D570F1DCBB97C9BC188C79EA94662CDD12335400F73080321CC8DBEC63D | |||
| 1568 | WinRAR.exe | C:\Users\admin\Desktop\loader\newuimatrix.exe | executable | |
MD5:4A6EB12EA7764C04FDFED398F0A95828 | SHA256:E7687D570F1DCBB97C9BC188C79EA94662CDD12335400F73080321CC8DBEC63D | |||
| 1568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1568.21720\loader.zip\olduimatrix.exe | executable | |
MD5:66658E3FA325E09A6F4D444FCDB0F62F | SHA256:09E084DAD788D42508ED8EF49A62A949A4F89BA2678E42415C3808A95BD7FA55 | |||
| 1568 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$VR1568.21720\Rar$Scan65588.bat | text | |
MD5:87717E4E73006C500E6E883ED58BDA85 | SHA256:7A2A2237C1ECBB2241E33FB40BC299D5C82E38DEE53824CC7D4DAAD5AF4C5CC9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
25
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6232 | RUXIMICS.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6232 | RUXIMICS.exe | GET | 304 | 184.25.54.100:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 184.25.54.100:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 302 | 140.82.121.3:443 | https://github.com/manggoapi/ep/raw/refs/heads/main/attachments-000000004D2079D1 | unknown | — | — | unknown |
5944 | MoUsoCoreWorker.exe | GET | 200 | 184.25.54.100:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7116 | olduimatrix.exe | GET | 200 | 64.235.58.101:80 | http://64.235.58.101/~matrixhu/getdownloadfile.php?key=null&action=check | unknown | — | — | unknown |
— | — | GET | 200 | 140.82.121.3:443 | https://raw.githubusercontent.com/manggoapi/ep/refs/heads/main/attachments-000000004D2079D1 | unknown | binary | 14.7 Mb | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6232 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6232 | RUXIMICS.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 184.25.54.100:80 | www.microsoft.com | Telgua | SV | whitelisted |
5944 | MoUsoCoreWorker.exe | 184.25.54.100:80 | www.microsoft.com | Telgua | SV | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
raw.githubusercontent.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |