| File name: | ÐплаÑа ÑÑÑаÑов.apk |
| Full analysis: | https://app.any.run/tasks/1c56da42-bab8-49f6-bce5-1591ff877b55 |
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2025, 21:30:53 |
| OS: | Android 14 |
| Tags: | |
| MIME: | application/vnd.android.package-archive |
| File info: | Android package (APK), with APK Signing Block |
| MD5: | E9059A49263C48101C843C4A403E5A81 |
| SHA1: | 97A914FE9CC1EA5A3D495CB4B5CC58888D72337D |
| SHA256: | 6FA272457CBCF5F200F58E9E8F46E0BD702E9E627F5DC2378A7E56B65D410E1D |
| SSDEEP: | 98304:XqTaY57w3mRap+5q5N/g1KDysYqEWRUsp8pkkndhaj9INTv1VBlSoTYrzIVNEXfF:75 |
MALICIOUS
Sends SMS messages
- app_process64 (PID: 4092)
Hides app icon from display
- app_process64 (PID: 4092)
SUSPICIOUS
Accesses system-level resources
- app_process64 (PID: 4092)
Retrieves Android OS build information
- app_process64 (PID: 4092)
Collects data about the device's environment (JVM version)
- app_process64 (PID: 4092)
Starts a service
- app_process64 (PID: 4092)
Creates a WakeLock to manage power state
- app_process64 (PID: 4092)
Acquires a wake lock to keep the device awake
- app_process64 (PID: 4092)
Launches a new activity
- app_process64 (PID: 4092)
Uses encryption API functions
- app_process64 (PID: 4092)
Connects to unusual port
- app_process64 (PID: 4092)
Reads messages from SMS inbox
- app_process64 (PID: 4092)
Updates data in the storage of application settings (SharedPreferences)
- app_process64 (PID: 4092)
Abuses foreground service for persistence
- app_process64 (PID: 4092)
INFO
Dynamically inspects or modifies classes, methods, and fields at runtime
- app_process64 (PID: 4092)
Stores data using SQLite database
- app_process64 (PID: 4092)
Dynamically loads a class in Java
- app_process64 (PID: 4092)
Dynamically registers broadcast event listeners
- app_process64 (PID: 4092)
Returns elapsed time since boot
- app_process64 (PID: 4092)
Retrieves data from storage of application settings (SharedPreferences)
- app_process64 (PID: 4092)
Loads a native library into the application
- app_process64 (PID: 4092)
Verifies presence of SIM card
- app_process64 (PID: 4092)
Verifies whether the device is connected to the internet
- app_process64 (PID: 4092)
Retrieves the value of a secure system setting
- app_process64 (PID: 4092)
Attempting to connect via WebSocket
- app_process64 (PID: 4092)
Gets file name without full path
- app_process64 (PID: 4092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .apk | | | Android Package (62.8) |
|---|---|---|
| .jar | | | Java Archive (17.3) |
| .vym | | | VYM Mind Map (14.9) |
| .zip | | | ZIP compressed archive (4.7) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0808 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:11:09 21:03:56 |
| ZipCRC: | 0x0e079941 |
| ZipCompressedSize: | 528 |
| ZipUncompressedSize: | 1888 |
| ZipFileName: | res/animator/mtrl_fab_transformation_sheet_collapse_spec.xml |
Total processes
163
Monitored processes
34
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 4092 | app.nklqr33.flqkfsr | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4124 | com.android.webview:webview_service | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4141 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4179 | com.android.webview:webview_apk | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4268 | org.chromium.chrome | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4355 | zygote64 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4381 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4395 | org.chromium.chrome:privileged_process0 | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4408 | com.android.adservices.api | /system/bin/app_process64 | — | app_process64 |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 4469 | org.chromium.chrome_zygote | /system/bin/app_process64 | — | app_process64 |
User: u0_a72 Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
14
Suspicious files
335
Text files
26
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4092 | app_process64 | /data/data/app.nklqr33.flqkfsr/no_backup/androidx.work.workdb-journal | binary | |
MD5:— | SHA256:— | |||
| 4092 | app_process64 | /data/data/app.nklqr33.flqkfsr/no_backup/androidx.work.workdb-wal | binary | |
MD5:— | SHA256:— | |||
| 4092 | app_process64 | /data/data/app.nklqr33.flqkfsr/app_webview/last-exit-info | binary | |
MD5:— | SHA256:— | |||
| 4092 | app_process64 | /data/data/app.nklqr33.flqkfsr/shared_prefs/WebViewChromiumPrefs.xml | xml | |
MD5:— | SHA256:— | |||
| 4092 | app_process64 | /data/data/app.nklqr33.flqkfsr/app_webview/Default/Web Data-journal | binary | |
MD5:— | SHA256:— | |||
| 4092 | app_process64 | /data/data/app.nklqr33.flqkfsr/app_webview/Default/Shared Dictionary/cache/index | binary | |
MD5:— | SHA256:— | |||
| 4092 | app_process64 | /data/data/app.nklqr33.flqkfsr/cache/WebView/Default/HTTP Cache/Code Cache/js/index | binary | |
MD5:— | SHA256:— | |||
| 4092 | app_process64 | /data/data/app.nklqr33.flqkfsr/cache/WebView/Default/HTTP Cache/Code Cache/wasm/index | binary | |
MD5:— | SHA256:— | |||
| 4092 | app_process64 | /data/data/app.nklqr33.flqkfsr/cache/WebView/Default/HTTP Cache/Code Cache/wasm/index-dir/temp-index | binary | |
MD5:— | SHA256:— | |||
| 4092 | app_process64 | /data/data/app.nklqr33.flqkfsr/cache/WebView/Default/HTTP Cache/Code Cache/js/index-dir/temp-index | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
43
DNS requests
42
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 216.58.206.68:80 | http://www.google.com/gen_204 | unknown | — | — | whitelisted |
1961 | app_process64 | GET | 204 | 142.250.186.131:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
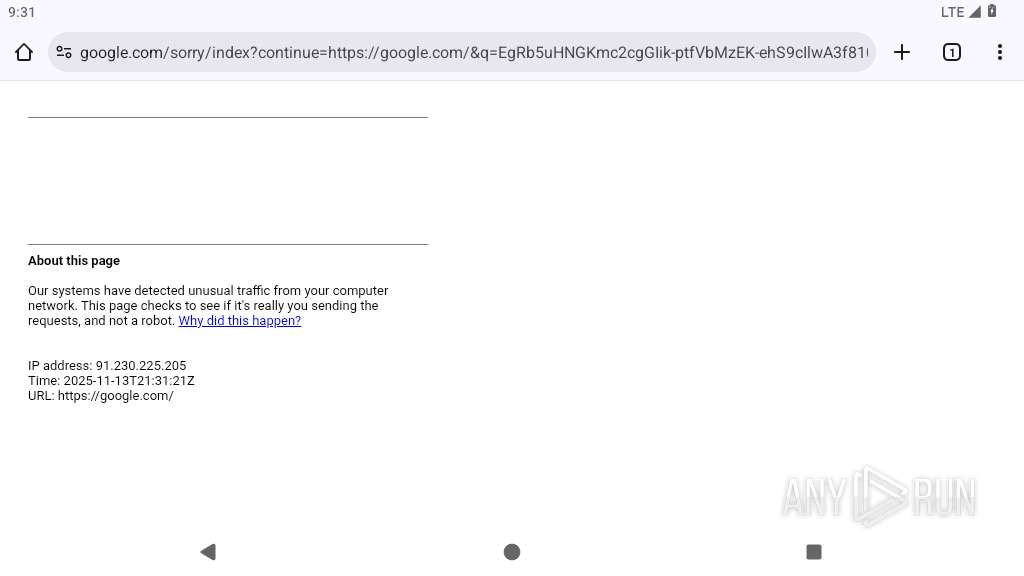
4092 | app_process64 | GET | 101 | 91.92.240.101:9997 | http://91.92.240.101:9997/ | unknown | — | — | unknown |
4268 | app_process64 | GET | 200 | 142.250.185.174:80 | http://clients2.google.com/time/1/current?cup2key=9:Szd_3hFc7Gc3GNzO1349sE9IwRFt8pbuA2wRX-LPHzg&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
4268 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acmmwq7dser4xm5sepzjv74g65vq_2023.7.28.10/cffplpkejcbdpfnfabnjikeicbedmifn_2023.07.28.10_all_acgbwixmcanakp2bkoppyszsbkrq.crx3 | unknown | — | — | whitelisted |
4268 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acpeapixpwuzscfa5h5j5m7c4xaa_2025.6.16.0/niikhdgajlphfehepabhhblakbdgeefj_2025.06.16.00_all_acgsomx5qtwgffxcrxwhoksfom7q.crx3 | unknown | — | — | whitelisted |
4268 | app_process64 | GET | — | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/obedbbhbpmojnkanicioggnmelmoomoc/e40bb820d29fb9a9bf8935fa5fbe77b363cf9c553cd0c1993bf0a9bec48686e4 | unknown | — | — | whitelisted |
4268 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/gcmjkmgdlgnkkcocmoeiminaijmmjnii/ba7f2b49c1b13a60fc1259ffa406b373a42b4e2bb8630f78077d8b0296c683aa | unknown | — | — | whitelisted |
4268 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzFkOTU2ODctM2JiNS00NDJhLTg2ZmEtYjM0ODZiM2YxNmVm/1.0.0.19_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | whitelisted |
4268 | app_process64 | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adeitchfjitjoozsqjoxybliouoq_1487/efniojlnjndmcbiieegkicadnoecjjef_1487_all_adnkaynv2sdnc5n6yk54xpps2u4q.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
453 | mdnsd | 224.0.0.251:5353 | — | — | — | whitelisted |
— | — | 216.58.206.68:80 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.250.186.131:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 216.58.206.68:443 | www.google.com | GOOGLE | US | whitelisted |
1961 | app_process64 | 142.250.186.131:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
1961 | app_process64 | 216.58.206.68:443 | www.google.com | GOOGLE | US | whitelisted |
583 | app_process64 | 216.239.35.4:123 | time.android.com | — | — | whitelisted |
2952 | app_process64 | 108.177.15.81:443 | staging-remoteprovisioning.sandbox.googleapis.com | GOOGLE | US | whitelisted |
4092 | app_process64 | 188.114.96.3:443 | photricity.com | CLOUDFLARENET | NL | whitelisted |
4179 | app_process32 | 142.250.185.227:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.google.com |
| whitelisted |
connectivitycheck.gstatic.com |
| whitelisted |
time.android.com |
| whitelisted |
staging-remoteprovisioning.sandbox.googleapis.com |
| whitelisted |
photricity.com |
| unknown |
update.googleapis.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
dl.google.com |
| whitelisted |
static.cloudflareinsights.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1961 | app_process64 | Misc activity | ET INFO Android Device Connectivity Check |
347 | netd | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
4092 | app_process64 | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 13 |
4092 | app_process64 | Not Suspicious Traffic | INFO [ANY.RUN] Websocket Upgrade Request |