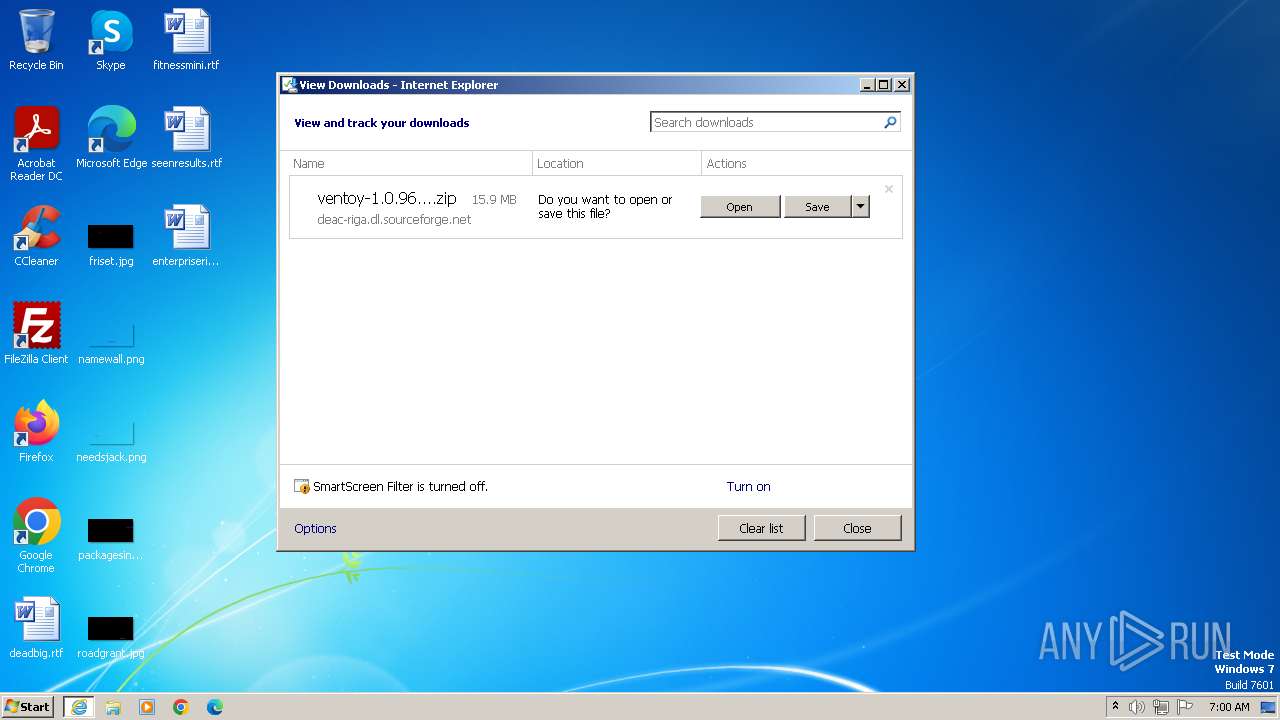
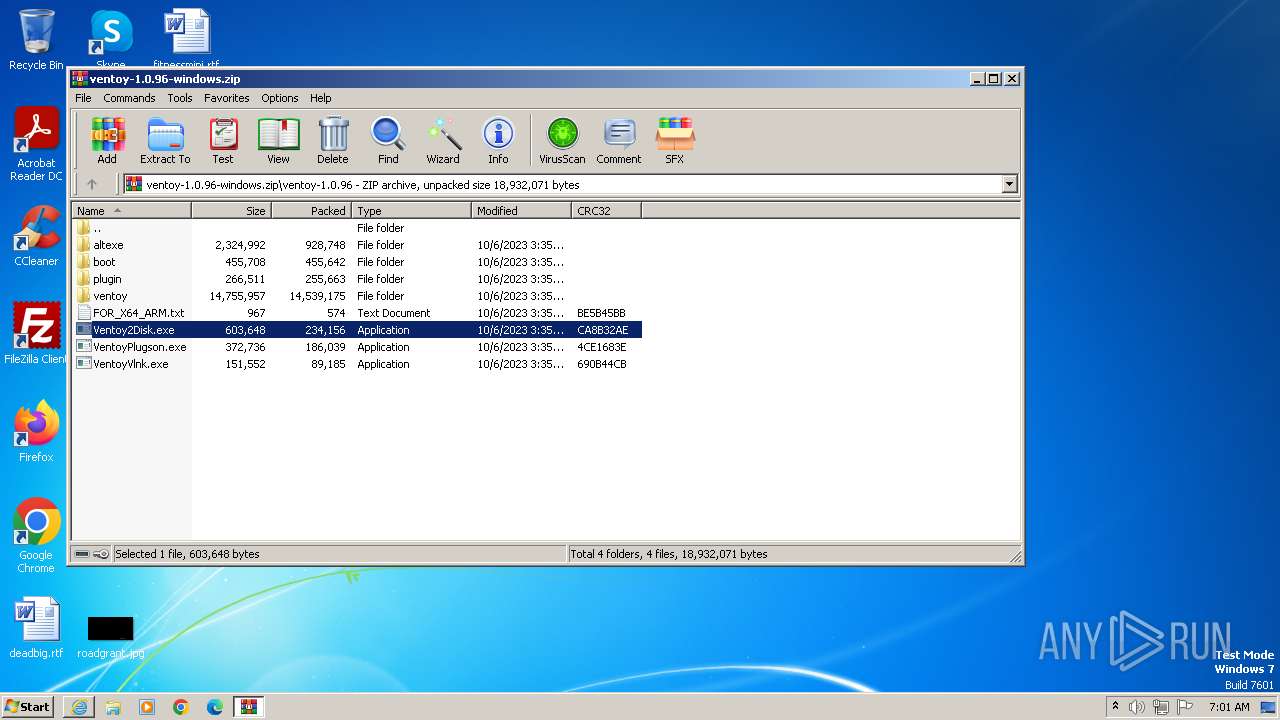
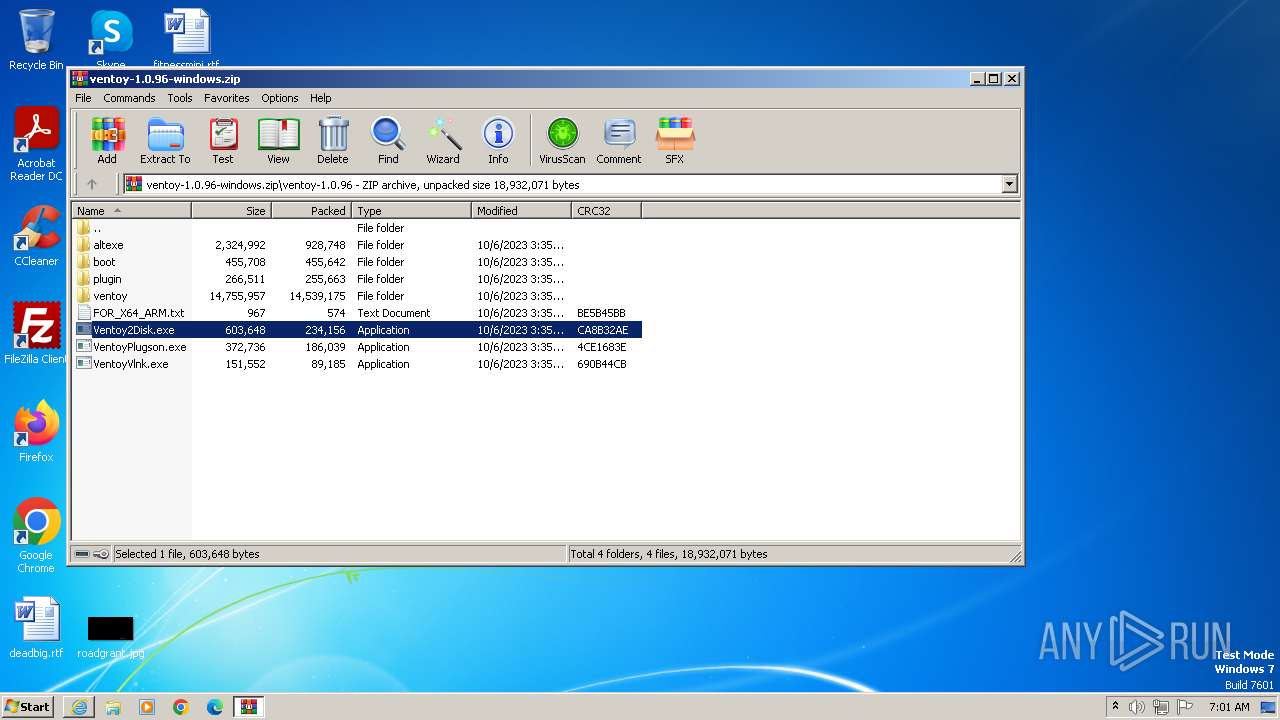
| URL: | https://deac-riga.dl.sourceforge.net/project/ventoy/v1.0.96/ventoy-1.0.96-windows.zip |
| Full analysis: | https://app.any.run/tasks/106116f4-6291-4468-aa14-54d0e10ef96c |
| Verdict: | Malicious activity |
| Analysis date: | October 24, 2023, 06:00:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | A9E7786A5F2E91CC0E036D7DF9AF334F11F4FBA5 |
| SHA256: | 6FA23368C44A4E74B30BEAD48D7D0999A78E9D937F44D04AC4A5762203C6EB68 |
| SSDEEP: | 3:N8YvqDiJ+2SuLAuUt9LRKcIUhLpT2POIISZ:2Yvl7nCtps2lCISZ |
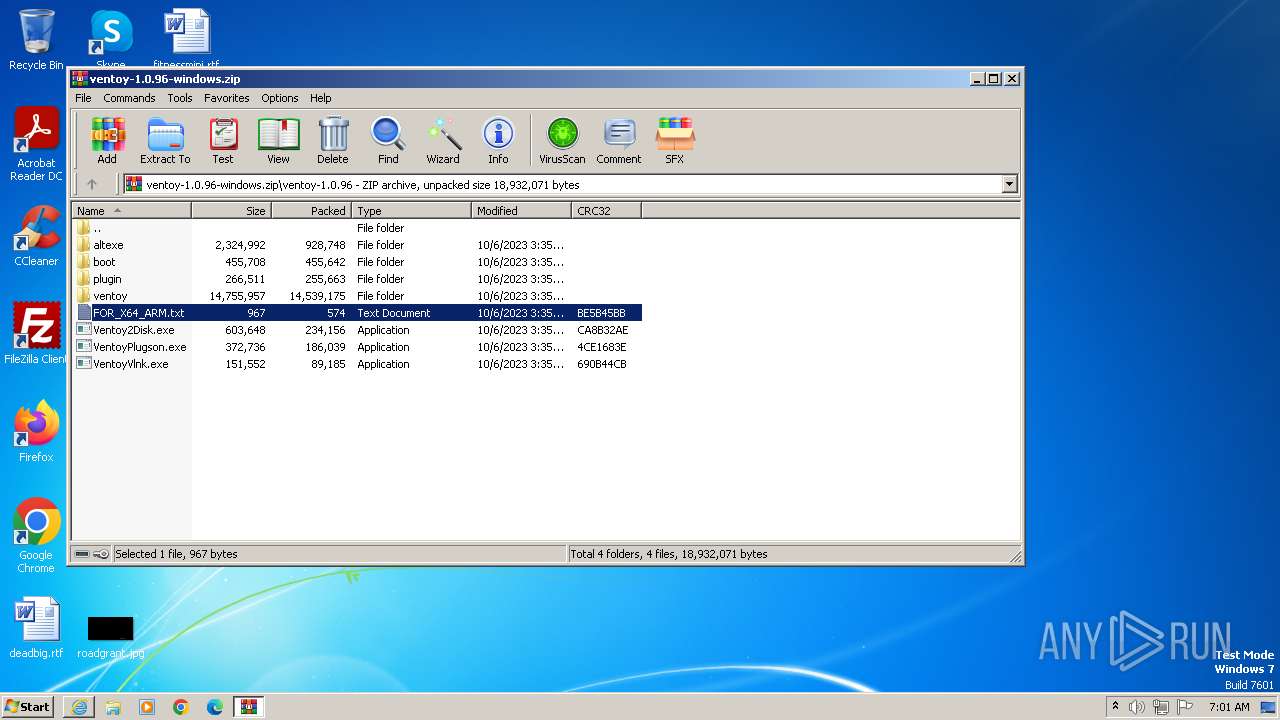
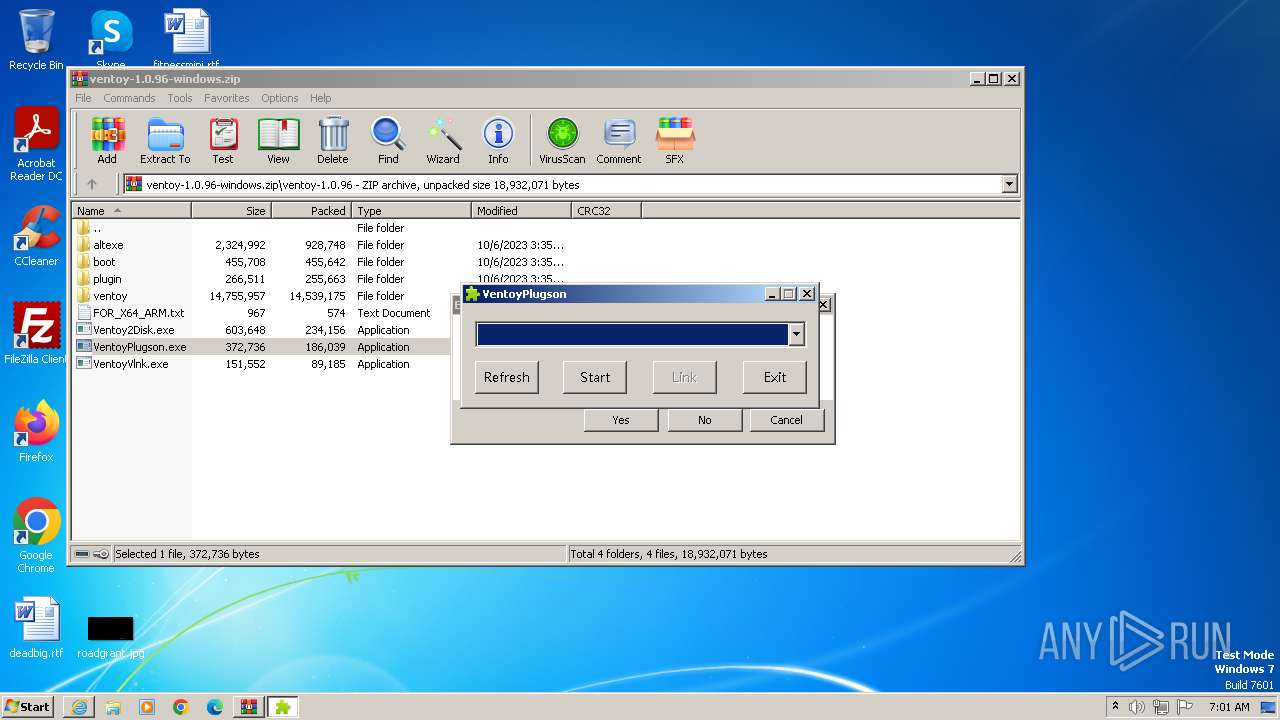
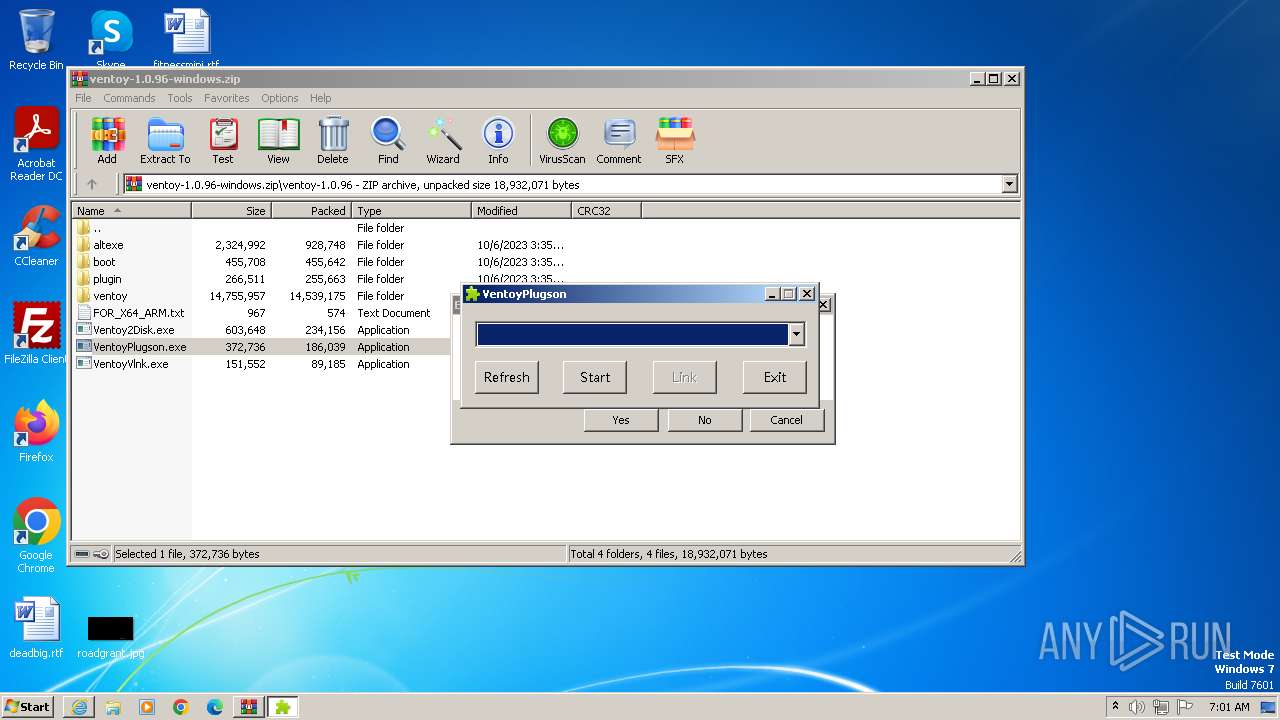
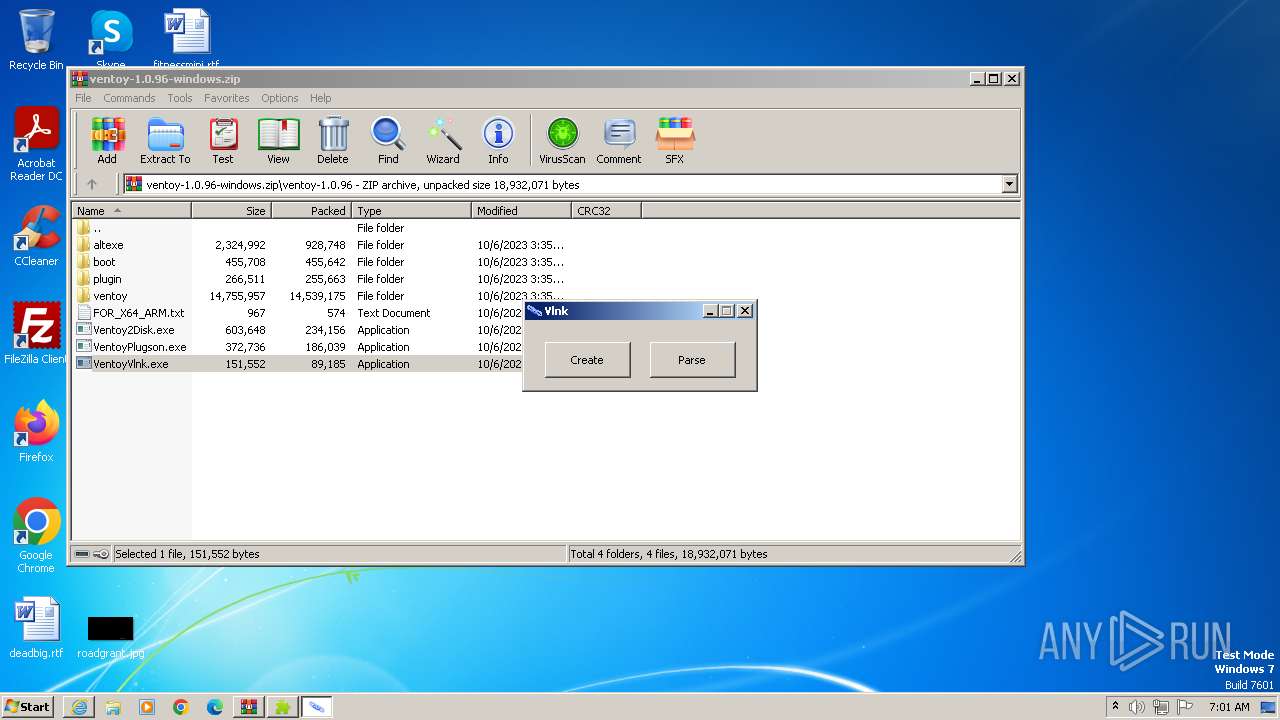
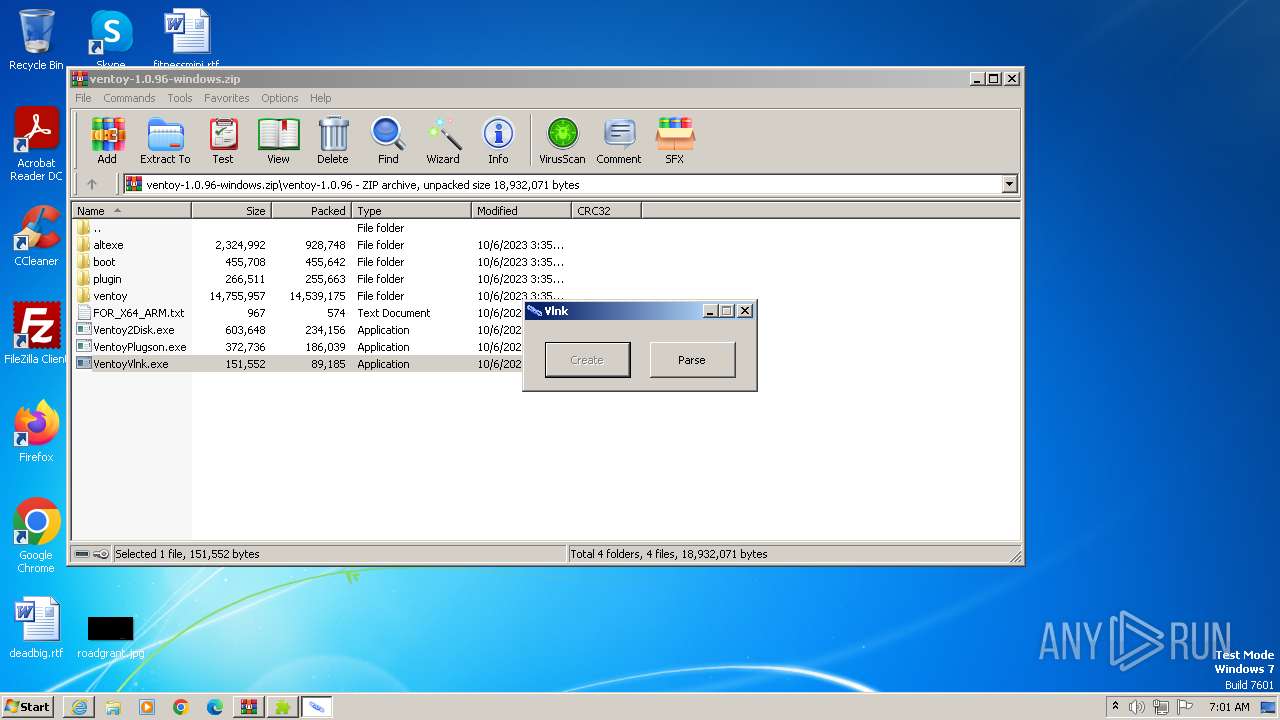
MALICIOUS
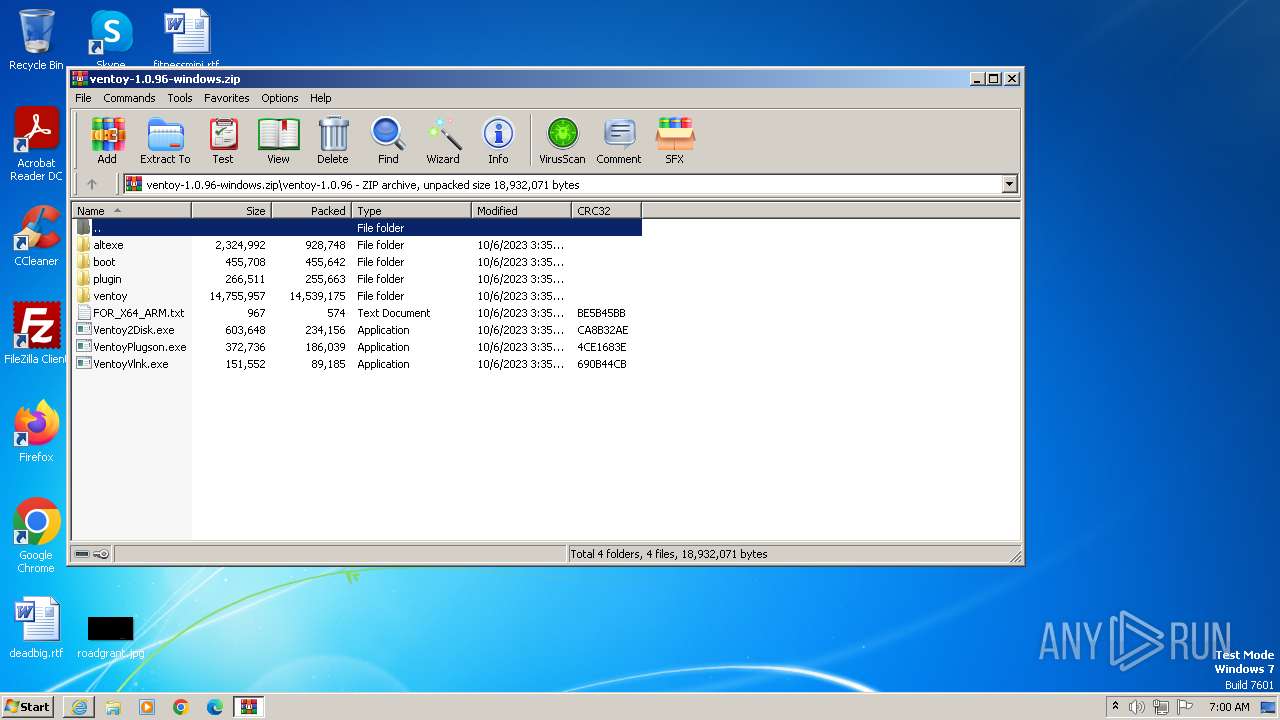
Application was dropped or rewritten from another process
- VentoyPlugson.exe (PID: 3884)
- Ventoy2Disk.exe (PID: 1484)
- VentoyPlugson.exe (PID: 4080)
- VentoyVlnk.exe (PID: 2288)
- Ventoy2Disk.exe (PID: 1832)
- VentoyVlnk.exe (PID: 2252)
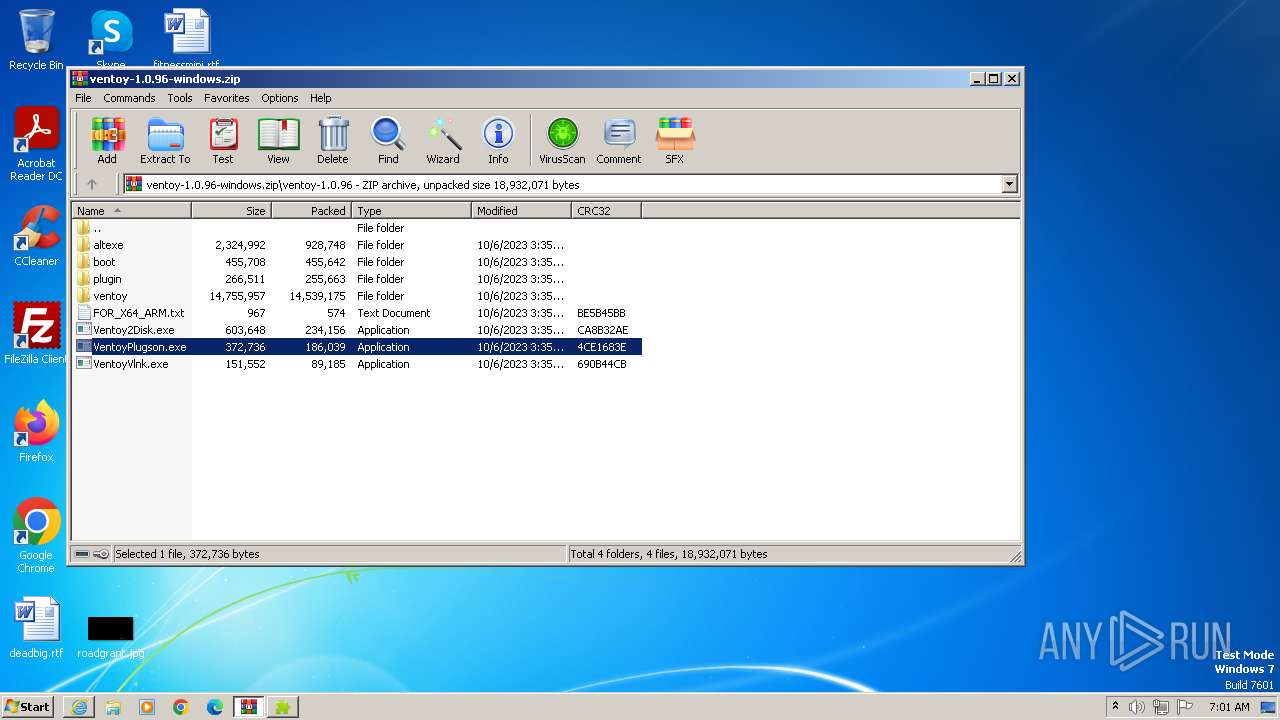
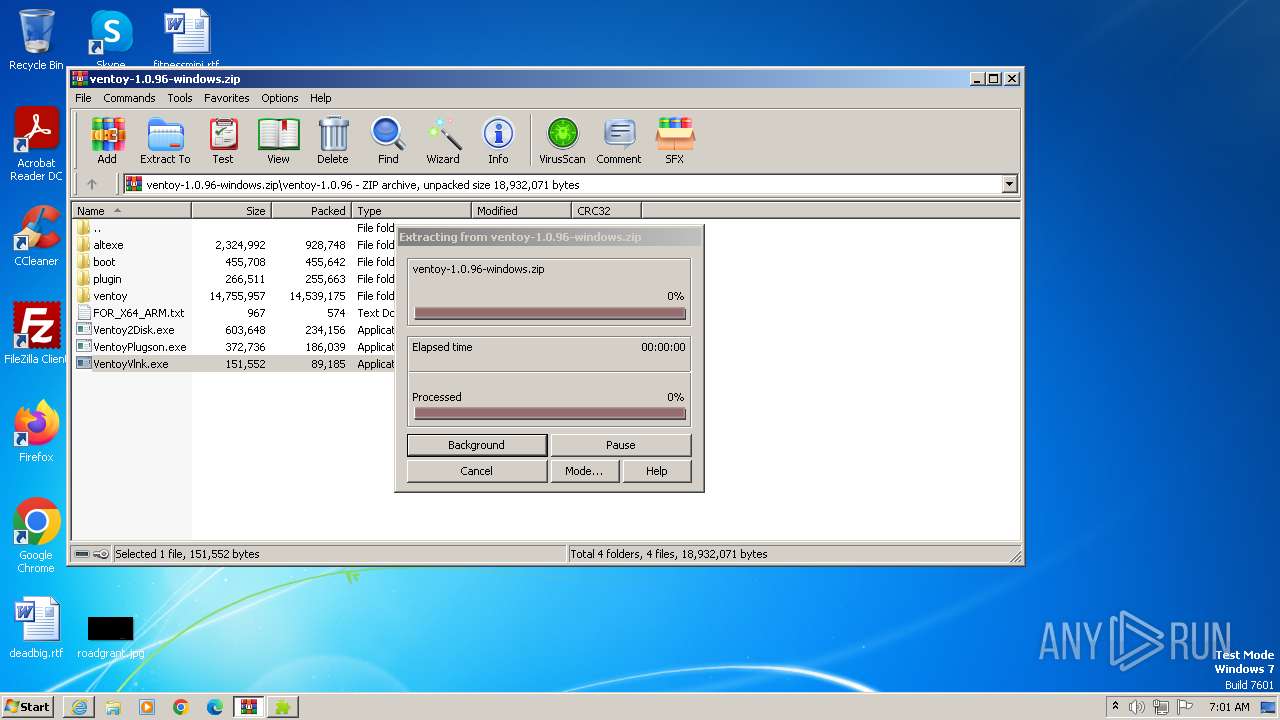
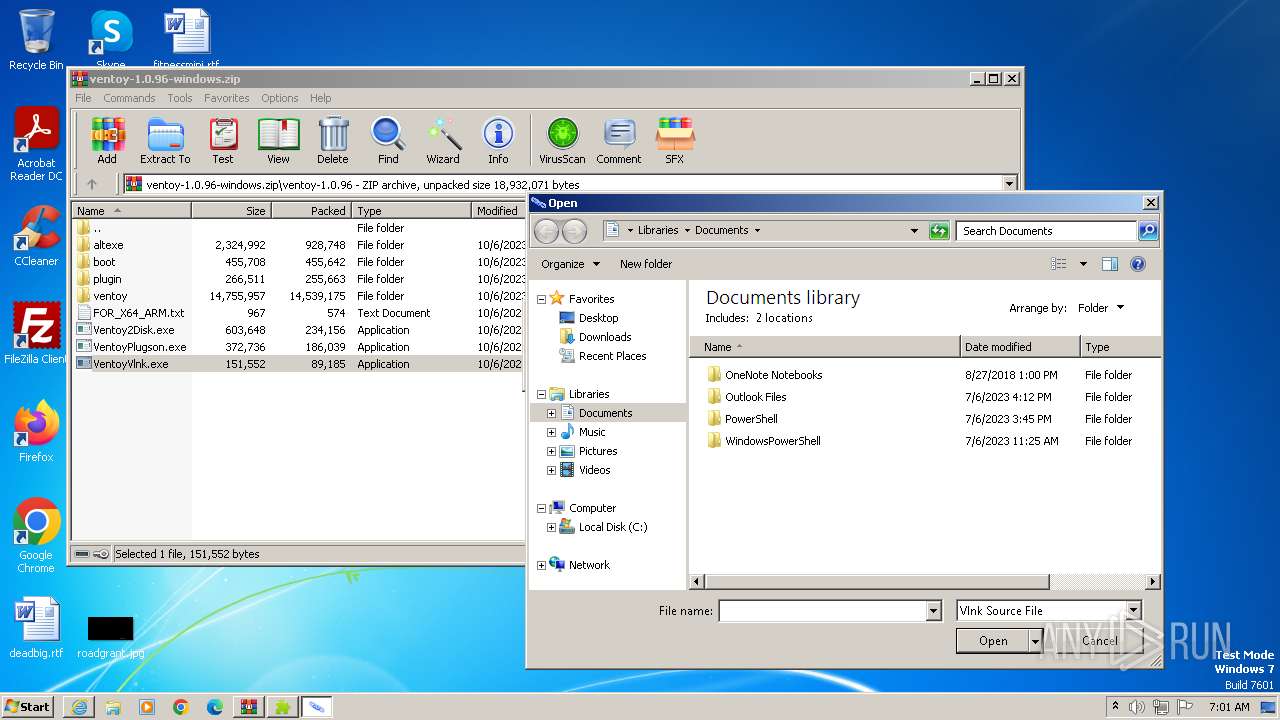
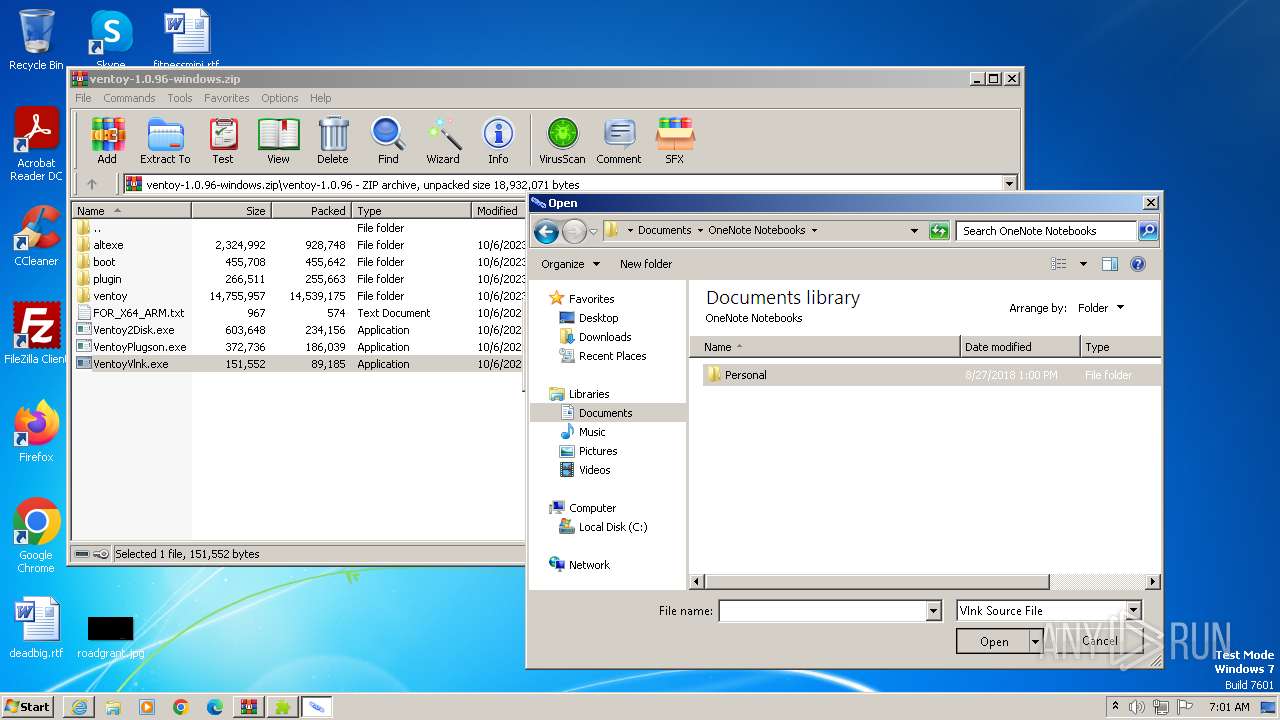
SUSPICIOUS
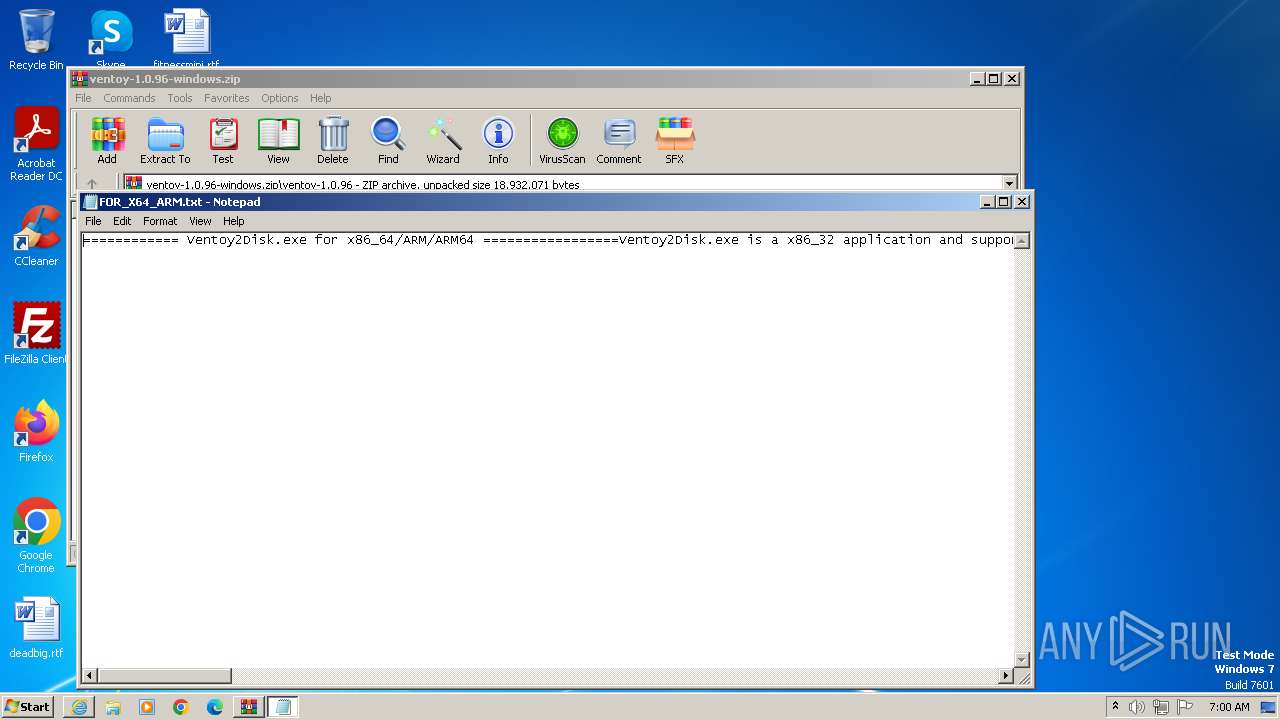
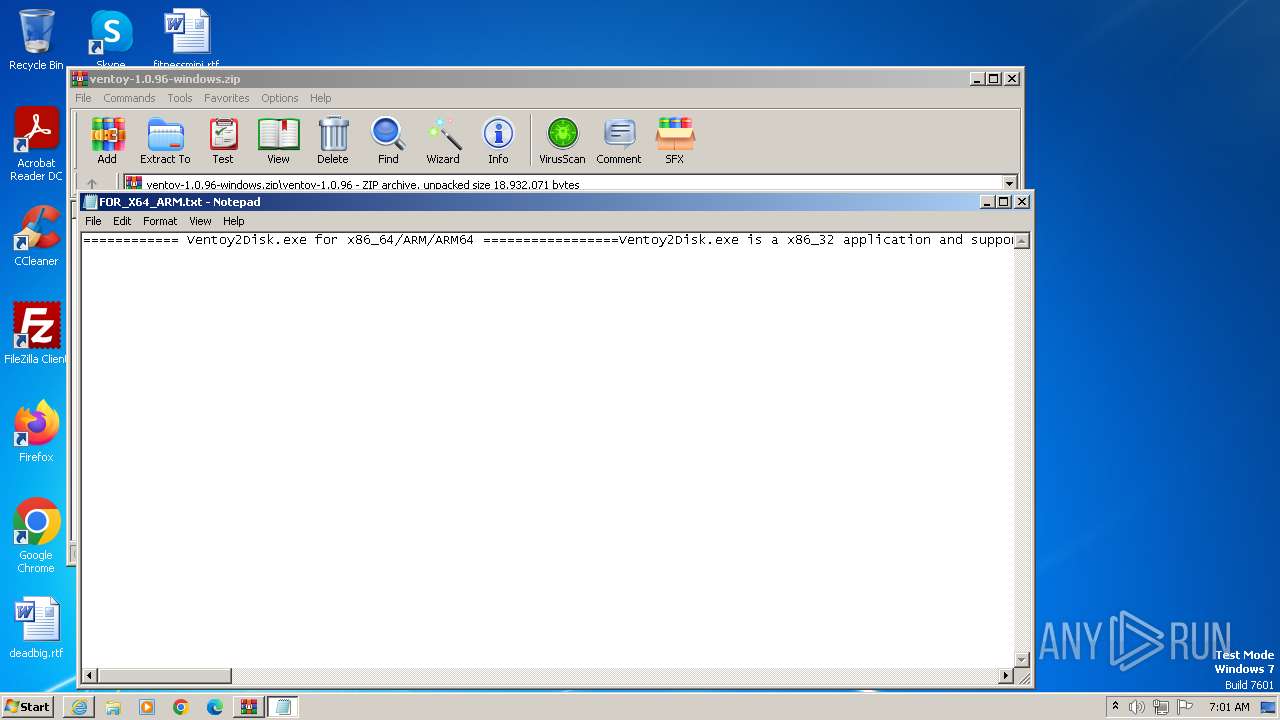
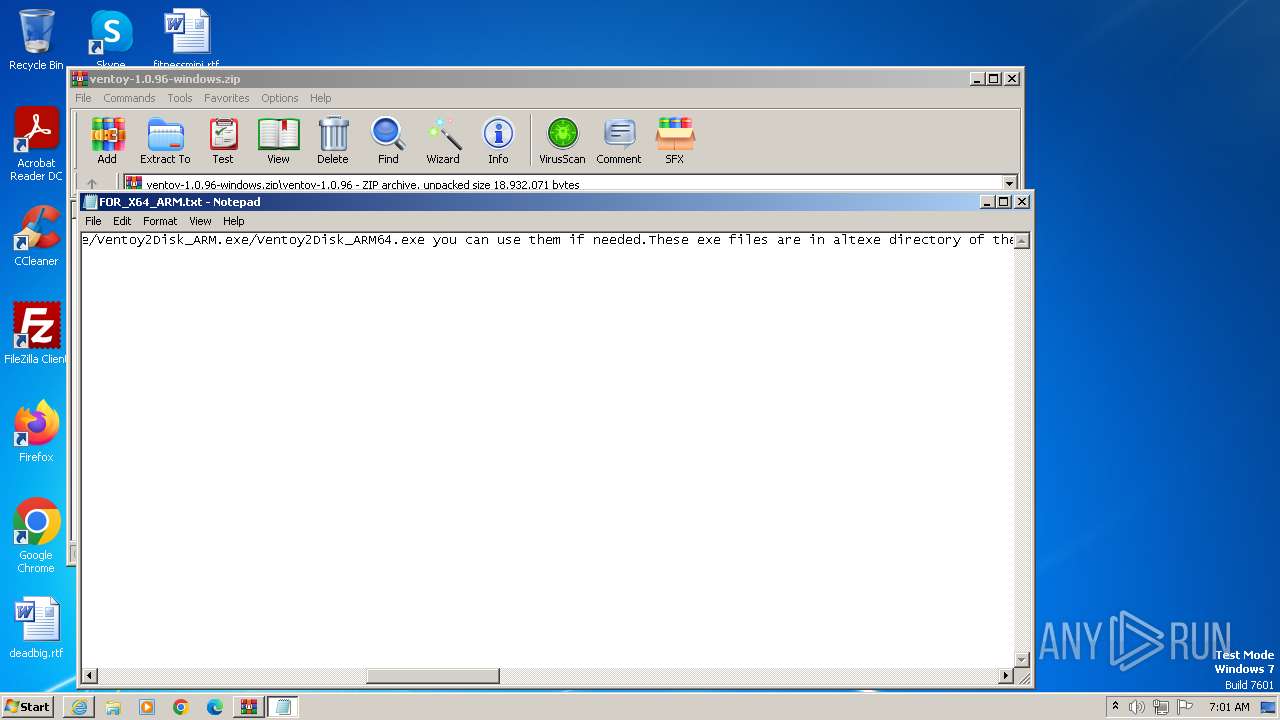
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 3112)
INFO
The process uses the downloaded file
- iexplore.exe (PID: 2464)
- WinRAR.exe (PID: 3112)
Application launched itself
- iexplore.exe (PID: 2464)
Checks supported languages
- VentoyPlugson.exe (PID: 4080)
- VentoyVlnk.exe (PID: 2288)
- Ventoy2Disk.exe (PID: 1832)
Create files in a temporary directory
- Ventoy2Disk.exe (PID: 1832)
- VentoyPlugson.exe (PID: 4080)
- VentoyVlnk.exe (PID: 2288)
Reads the machine GUID from the registry
- VentoyVlnk.exe (PID: 2288)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3112)
Reads the computer name
- VentoyVlnk.exe (PID: 2288)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
55
Monitored processes
10
Malicious processes
8
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
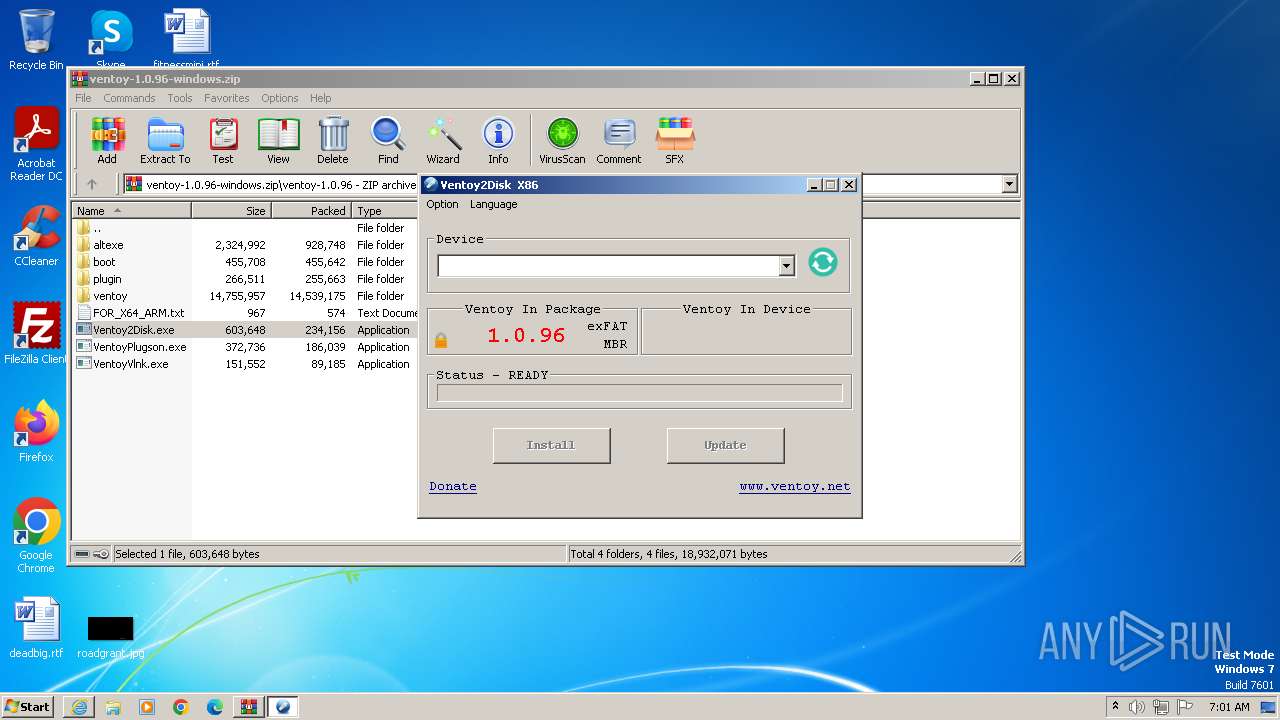
| 1484 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3112.25977\ventoy-1.0.96\Ventoy2Disk.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3112.25977\ventoy-1.0.96\Ventoy2Disk.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Ventoy2Disk Exit code: 3221226540 Version: 1.0.0.3 Modules
| |||||||||||||||
| 1832 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3112.25977\ventoy-1.0.96\Ventoy2Disk.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3112.25977\ventoy-1.0.96\Ventoy2Disk.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Ventoy2Disk Exit code: 0 Version: 1.0.0.3 Modules
| |||||||||||||||
| 2124 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2464 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2252 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3112.27601\ventoy-1.0.96\VentoyVlnk.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3112.27601\ventoy-1.0.96\VentoyVlnk.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2288 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3112.27601\ventoy-1.0.96\VentoyVlnk.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3112.27601\ventoy-1.0.96\VentoyVlnk.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2464 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://deac-riga.dl.sourceforge.net/project/ventoy/v1.0.96/ventoy-1.0.96-windows.zip" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
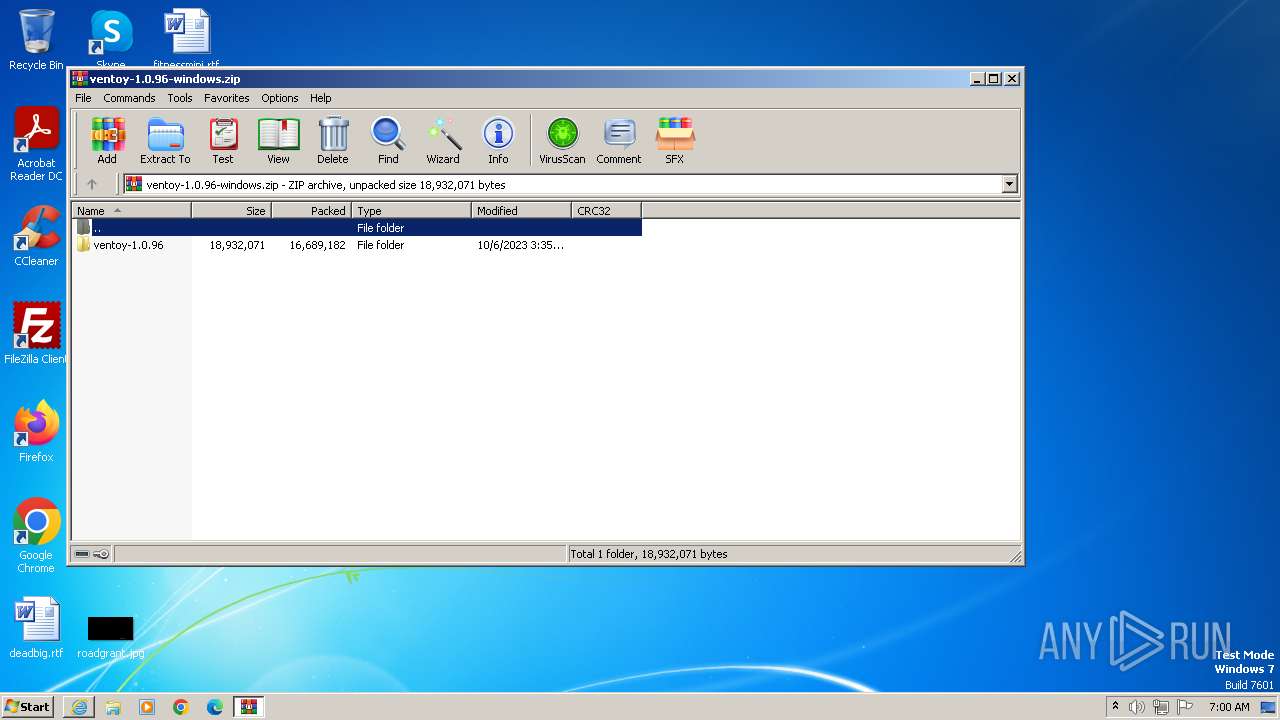
| 3112 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\ventoy-1.0.96-windows.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | iexplore.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3232 | "C:\Windows\system32\NOTEPAD.EXE" C:\Users\admin\AppData\Local\Temp\Rar$DIa3112.24235\FOR_X64_ARM.txt | C:\Windows\System32\notepad.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Notepad Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3884 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3112.26763\ventoy-1.0.96\VentoyPlugson.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3112.26763\ventoy-1.0.96\VentoyPlugson.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 4080 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3112.26763\ventoy-1.0.96\VentoyPlugson.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3112.26763\ventoy-1.0.96\VentoyPlugson.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
23 741
Read events
23 591
Write events
149
Delete events
1
Modification events
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000056010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2464) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
24
Suspicious files
35
Text files
101
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 2124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:0C0662D17F1435993C3E9F1E8CE89564 | SHA256:29102787AC49CAD7FF5462D86EC0615B736470F88067FB74DBEB0CC4F39F6977 | |||
| 2124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF5F2A8E1F99CE2C01.TMP | binary | |
MD5:1995BFCBE1EEBBD20643B33EE241467E | SHA256:D131D2AF0916A74A3643843650783F4D78D9CBA6A06AA9726CF9081510CD78C8 | |||
| 2124 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarBBB0.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{A9B3993B-7232-11EE-B150-12A9866C77DE}.dat | binary | |
MD5:AA7BDF0E4EABF86071E022B102CB9731 | SHA256:C24233A90A3BFDAB31E52395522D1E297615264760CAE44B4ADFE0006CFD798A | |||
| 2124 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:83491B2DFCA282FC4381849E04A65145 | SHA256:D7EBE741950339AF43DCE591CE61B6DB635CEA2C8AA74FC524035B93042E3F03 | |||
| 2124 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\ventoy-1.0.96-windows[1].zip | compressed | |
MD5:F987DF5BA3670AE68E6117EDC3BB618B | SHA256:4D31BE041C14B49708822E78C4E62CBB73E834135B7B4A11AF446EB11EFBF215 | |||
| 2464 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:2C63CDFF0CEB2CE74380B1A9186C3BDA | SHA256:FF60FDE3074297807DC4B19EB313AC0929A0D893D9D7C471BA2C6BB597099A9A | |||
| 2124 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\CabBBAD.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
11
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2124 | iexplore.exe | GET | 200 | 23.32.238.49:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMnIHvBRs74ntuzrMcAcl0GYA%3D%3D | unknown | der | 503 b | unknown |
2124 | iexplore.exe | GET | 200 | 67.26.139.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?a765e44f3a9a952c | unknown | compressed | 61.6 Kb | unknown |
2124 | iexplore.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
2124 | iexplore.exe | GET | 200 | 67.26.139.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?986b6bd513c67cbc | unknown | compressed | 61.6 Kb | unknown |
2464 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
2124 | iexplore.exe | GET | 200 | 67.26.139.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?be7e956f47863db5 | unknown | compressed | 4.66 Kb | unknown |
2124 | iexplore.exe | GET | 200 | 67.26.139.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?3a7e9332b34d5aaf | unknown | compressed | 4.66 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2124 | iexplore.exe | 67.26.139.254:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2124 | iexplore.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
2656 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
2124 | iexplore.exe | 23.32.238.49:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
2464 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
2464 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |