| File name: | 6fa10ca9f0adf98e3a7b15f96cde4f0d39a400377a4b99bdcbb42b9ace46d01d |
| Full analysis: | https://app.any.run/tasks/45dbb547-8977-46c2-a491-824da3bfca61 |
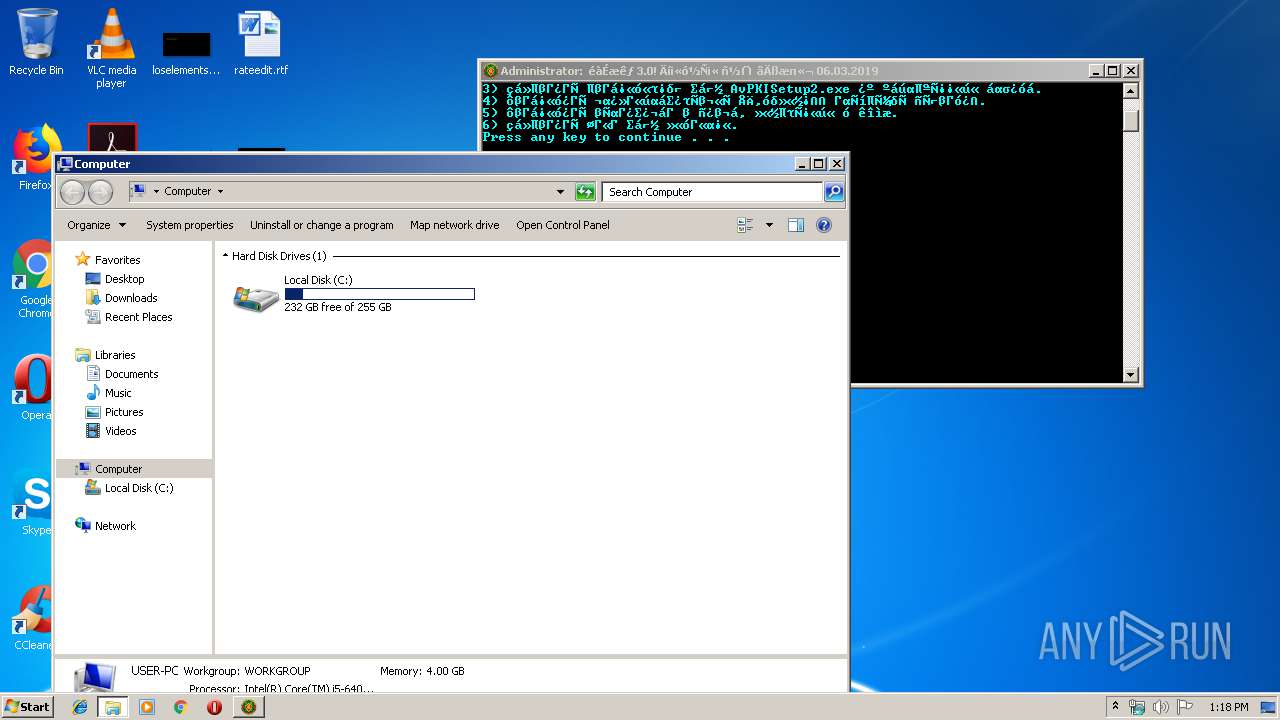
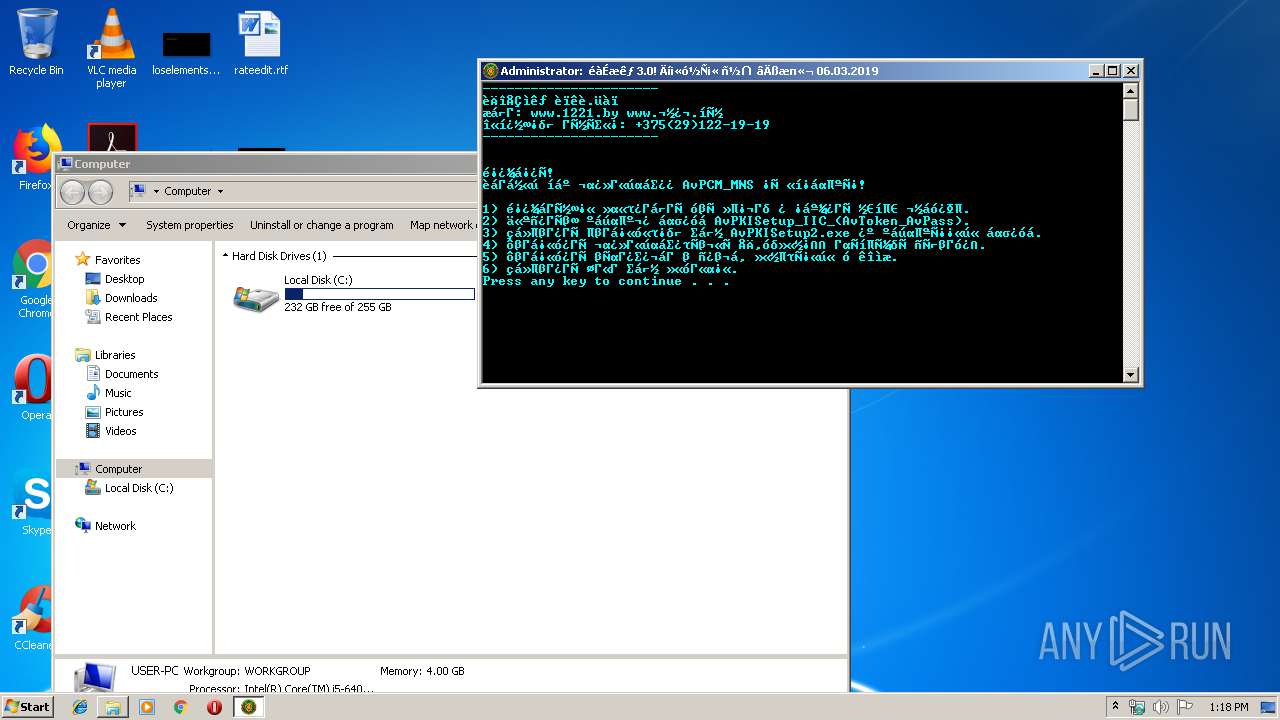
| Verdict: | Malicious activity |
| Analysis date: | July 16, 2019, 12:17:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 9DDBEB4D4DEFD19CFB8CC166BA1549DA |
| SHA1: | 940C969B78C6A44140962141FC51BD887C383E7C |
| SHA256: | 6FA10CA9F0ADF98E3A7B15F96CDE4F0D39A400377A4B99BDCBB42B9ACE46D01D |
| SSDEEP: | 1536:WDwUvyK+twm87HjWtg9VW1wUDrv3jDHffOSkbF:GvyJwUtg9AHnOSS |
MALICIOUS
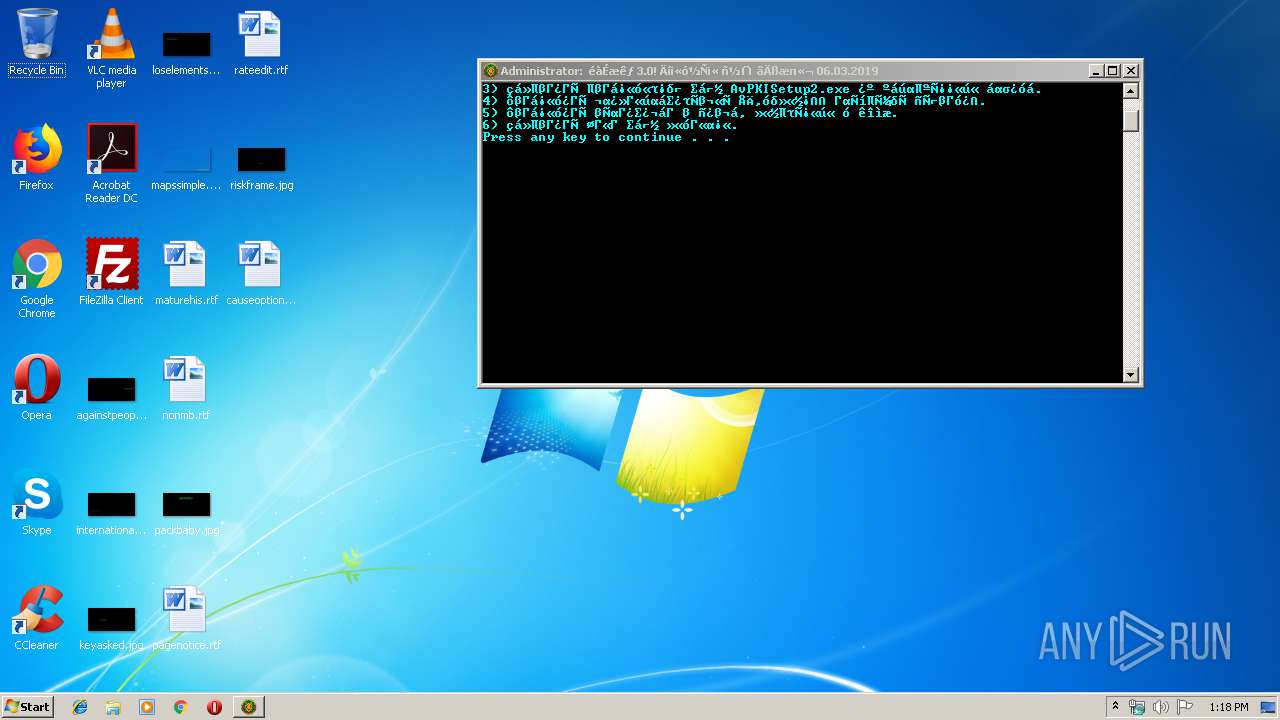
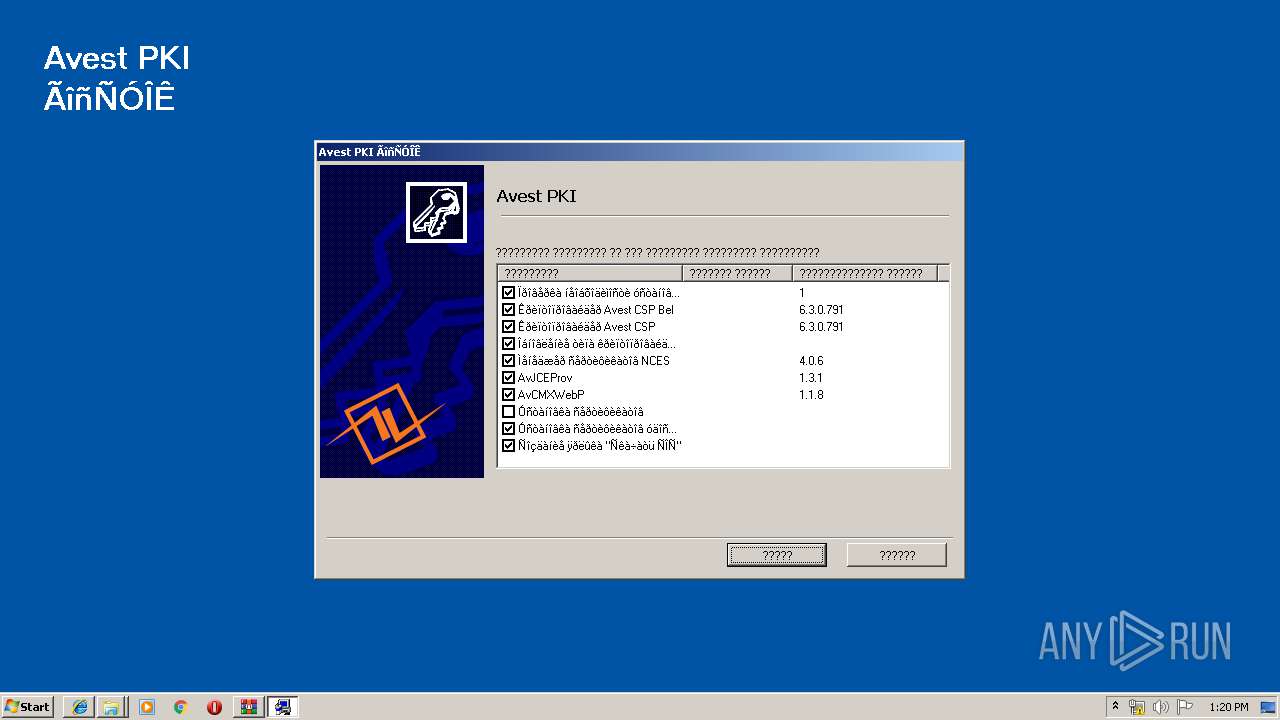
Application was dropped or rewritten from another process
- AvPKISetup2.exe (PID: 2408)
- AvPKISetup2.exe (PID: 1400)
Loads dropped or rewritten executable
- AvPKISetup2.exe (PID: 1400)
- SearchProtocolHost.exe (PID: 2588)
SUSPICIOUS
Executed via COM
- explorer.exe (PID: 2412)
- explorer.exe (PID: 2868)
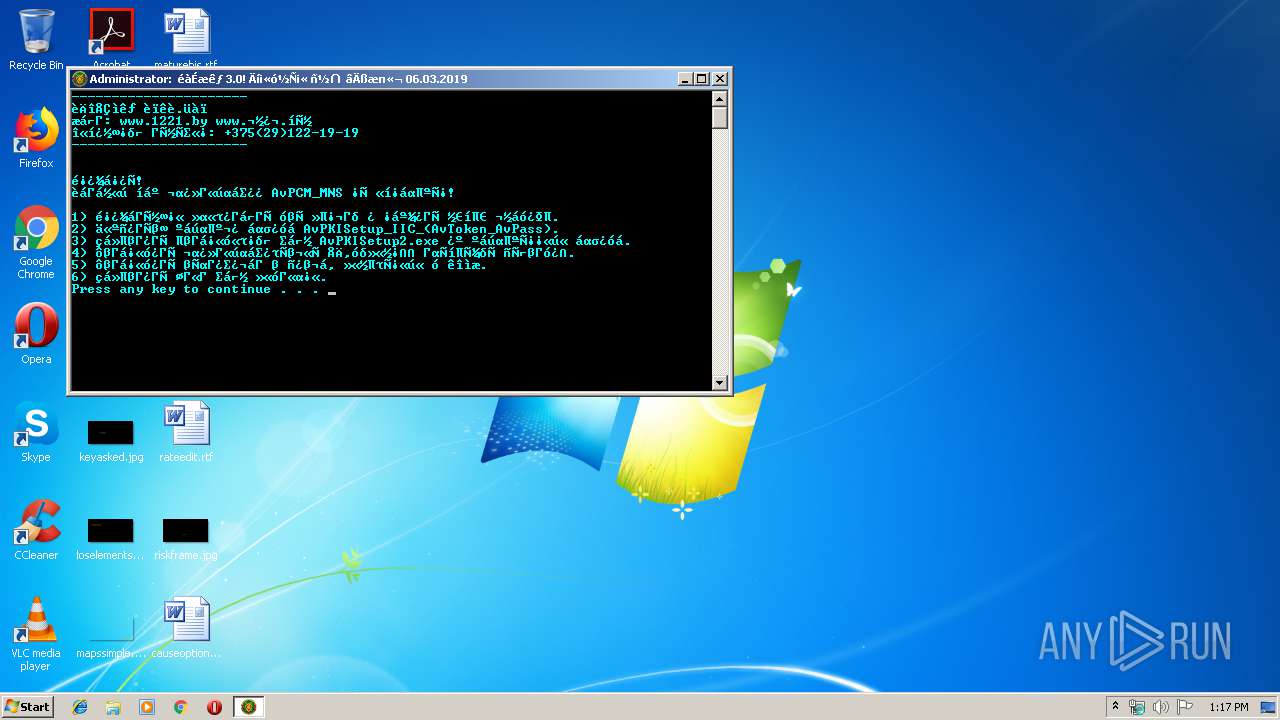
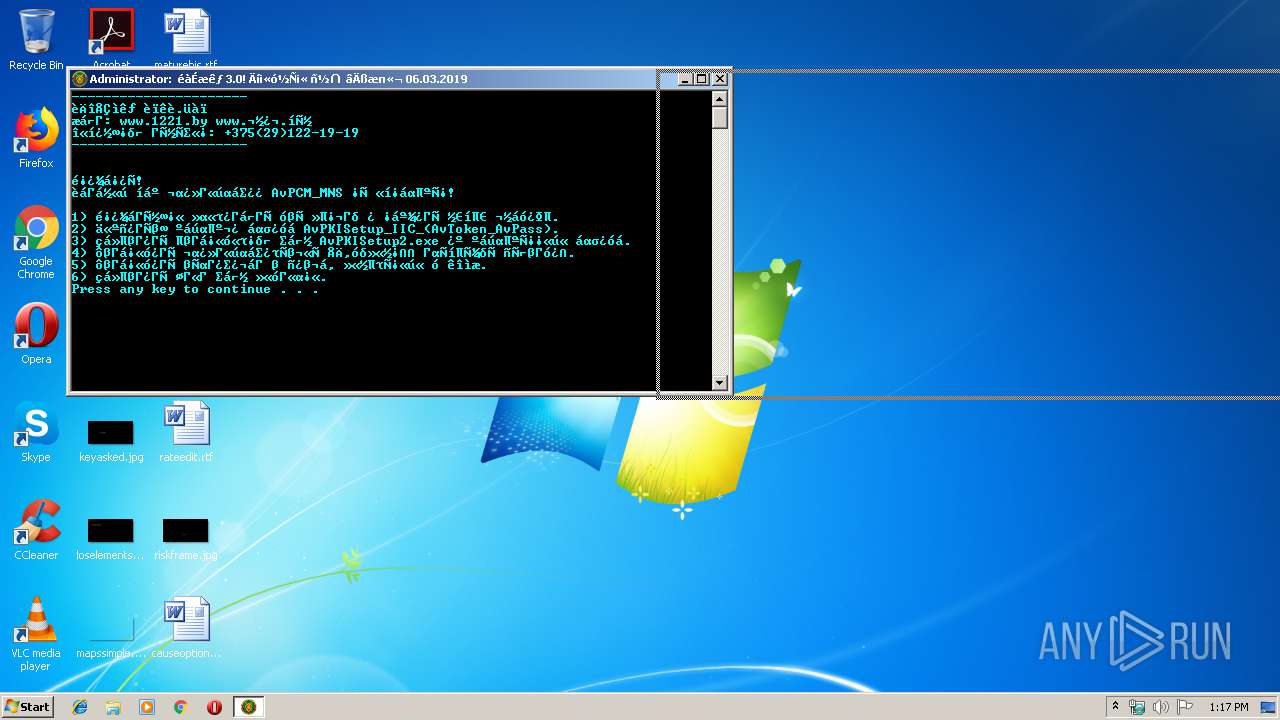
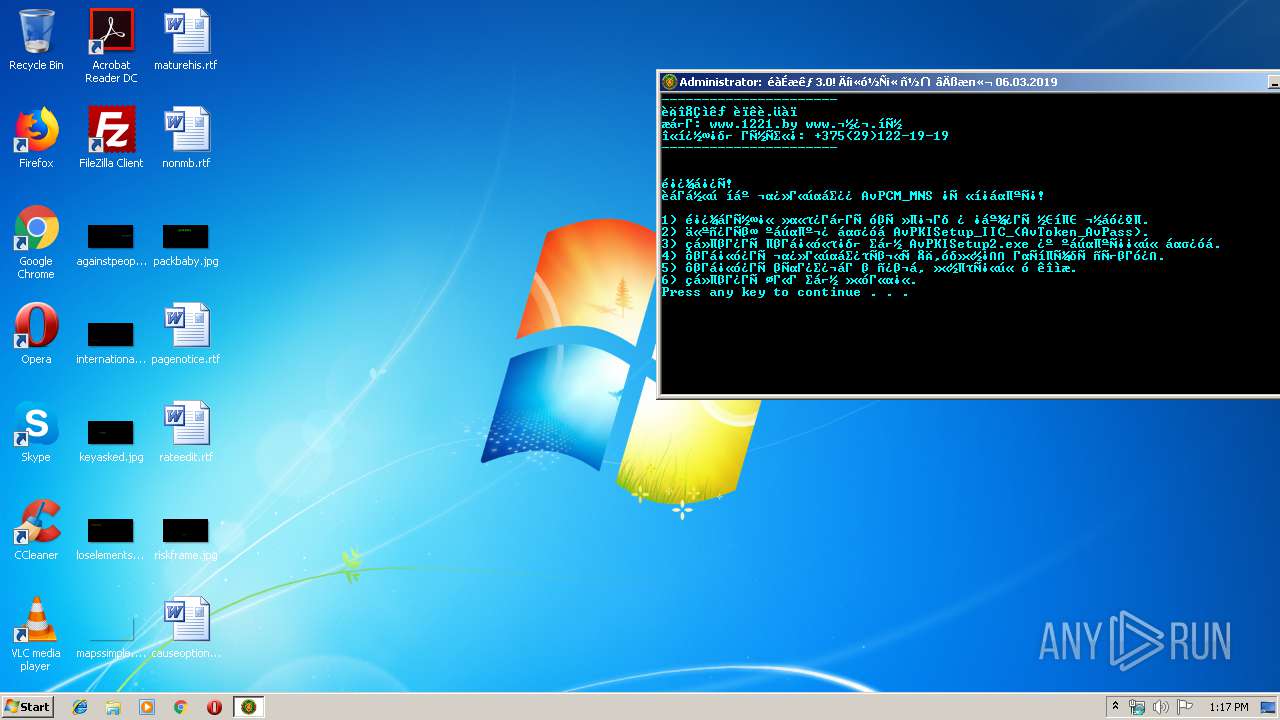
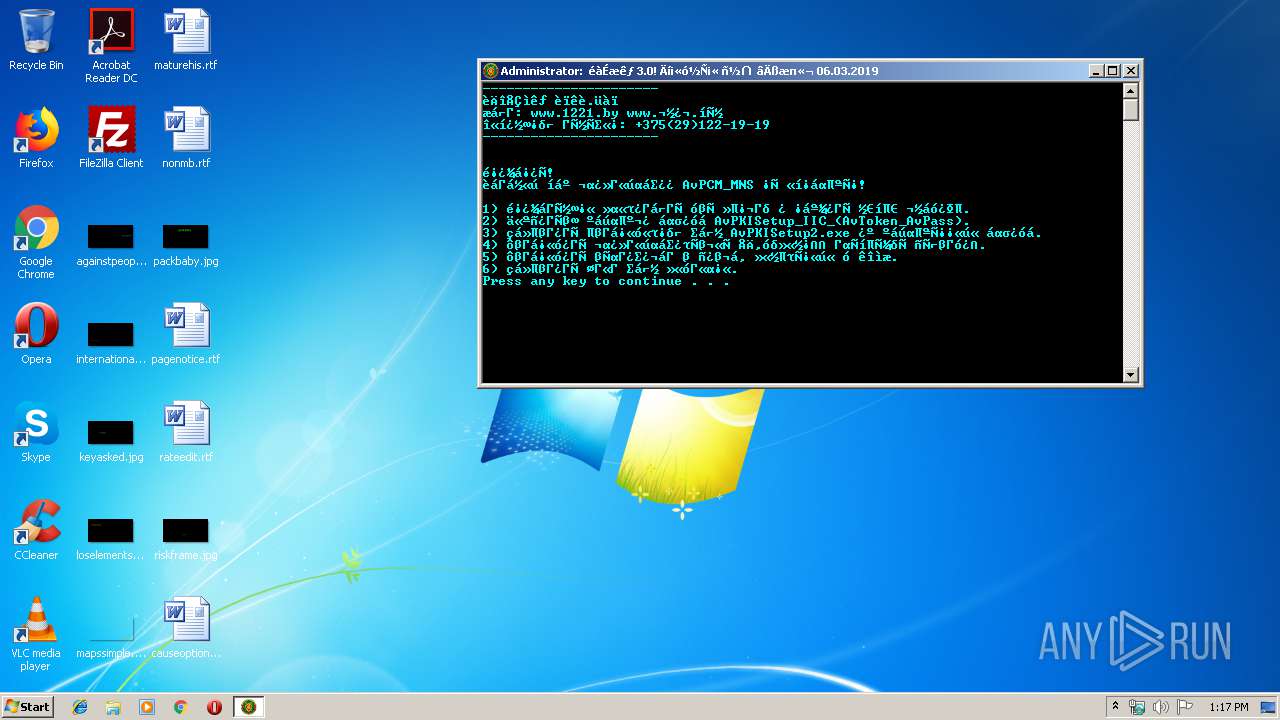
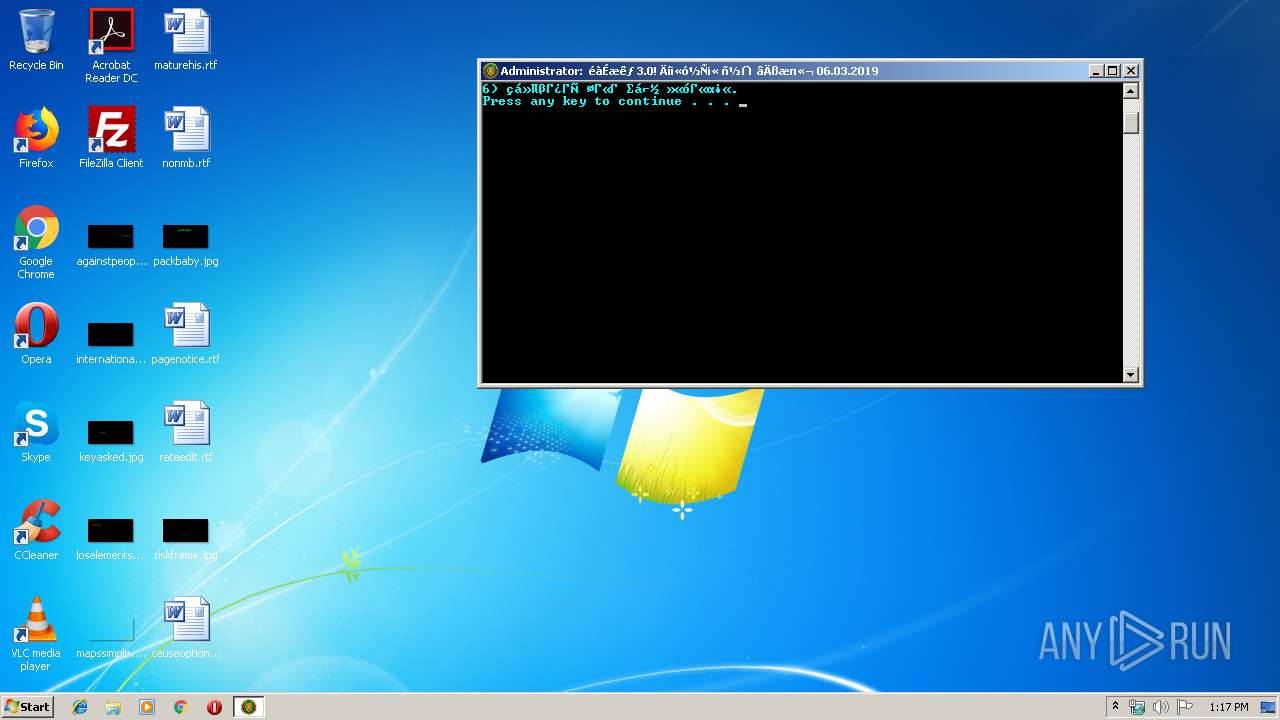
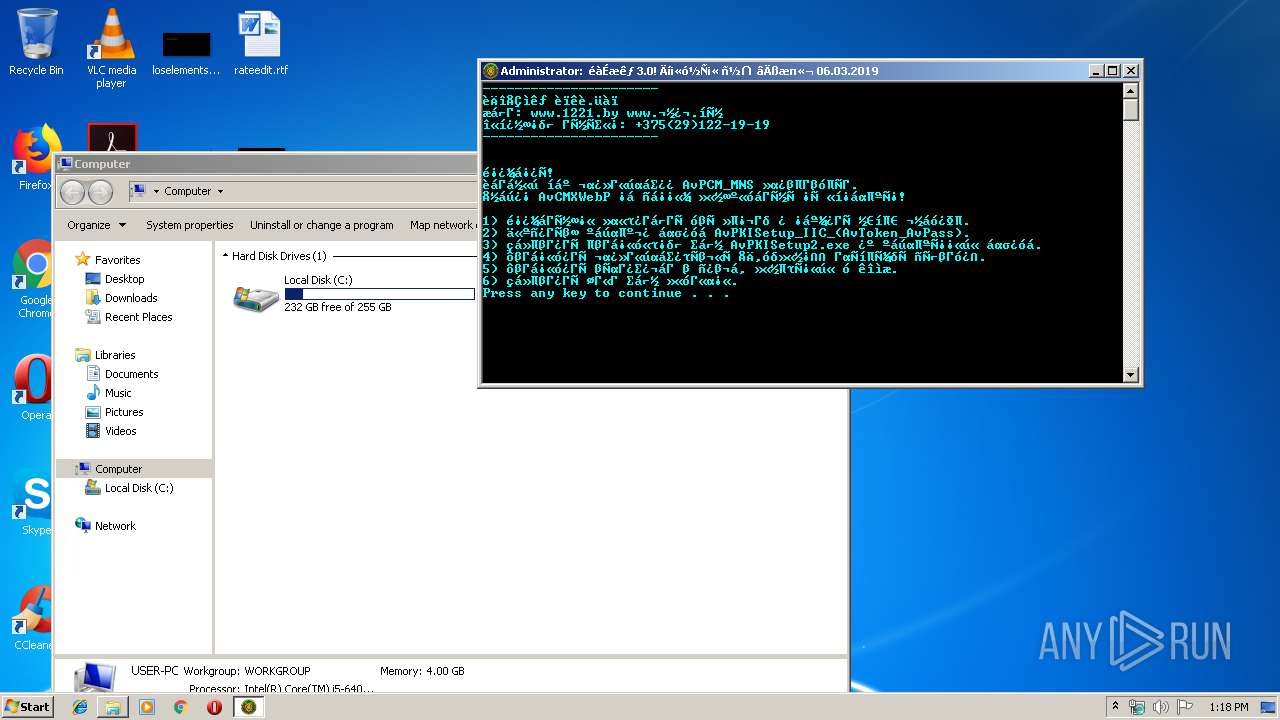
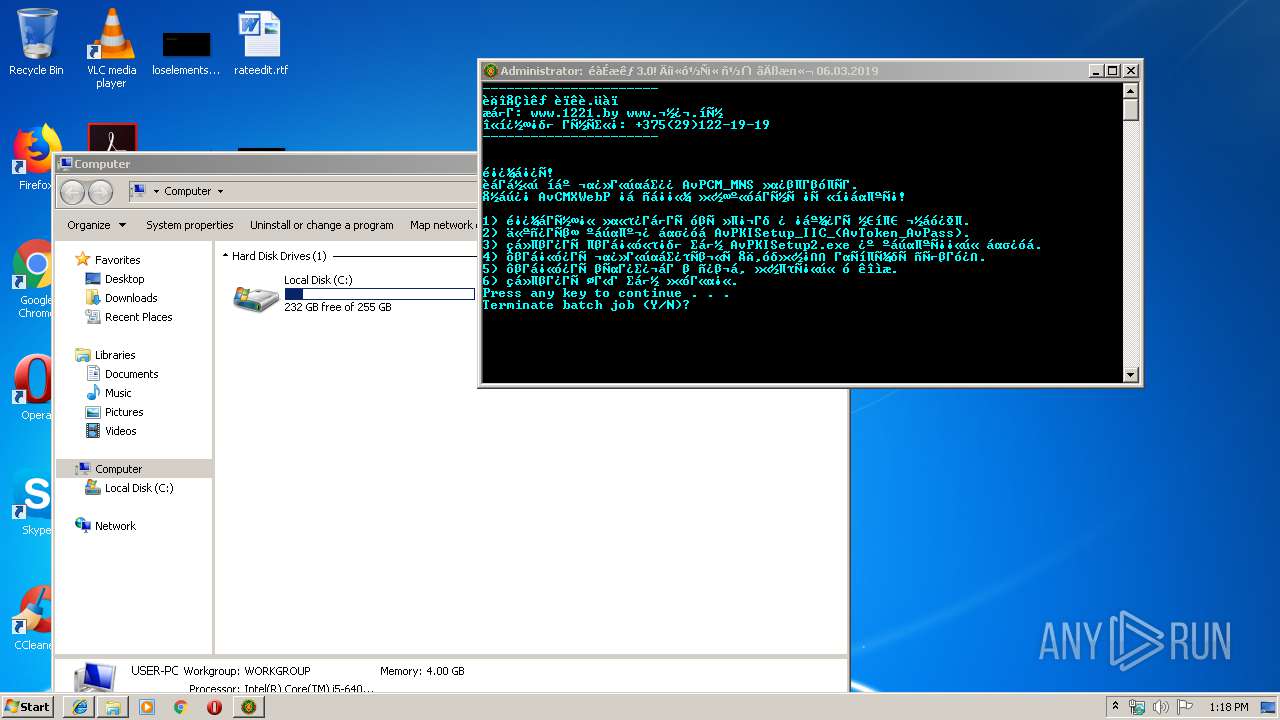
Starts CMD.EXE for commands execution
- 6fa10ca9f0adf98e3a7b15f96cde4f0d39a400377a4b99bdcbb42b9ace46d01d.exe (PID: 3860)
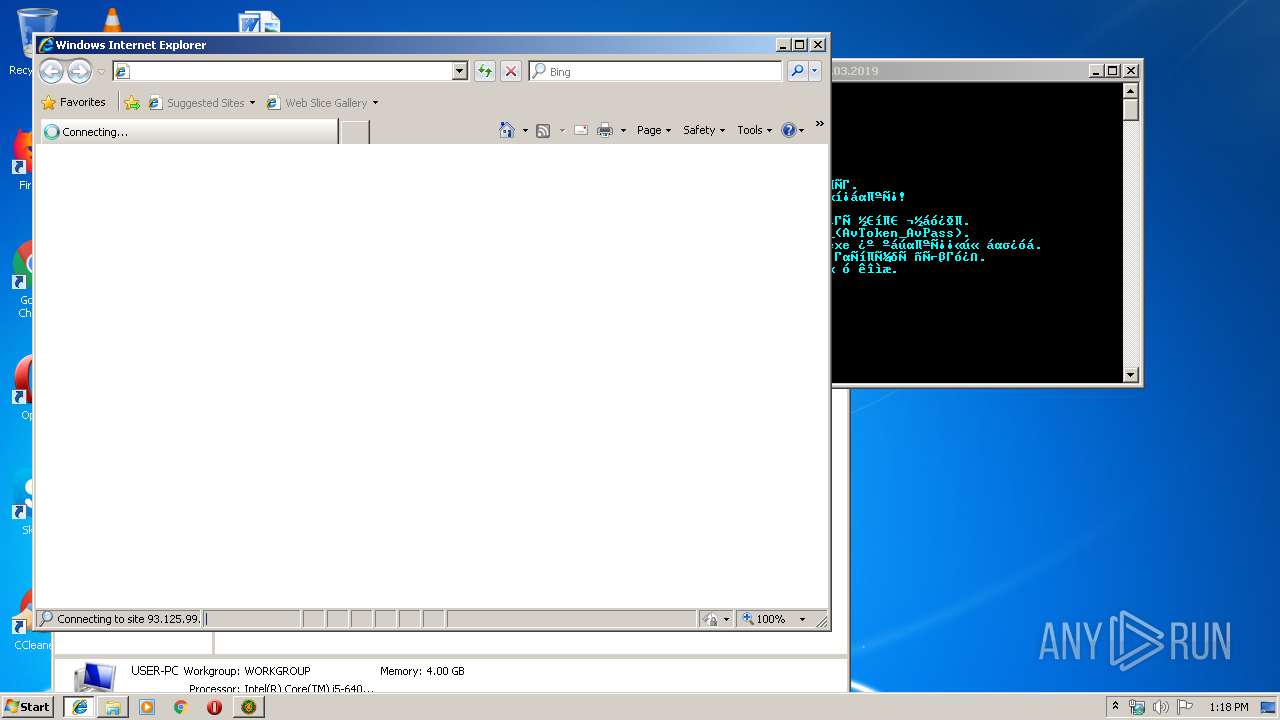
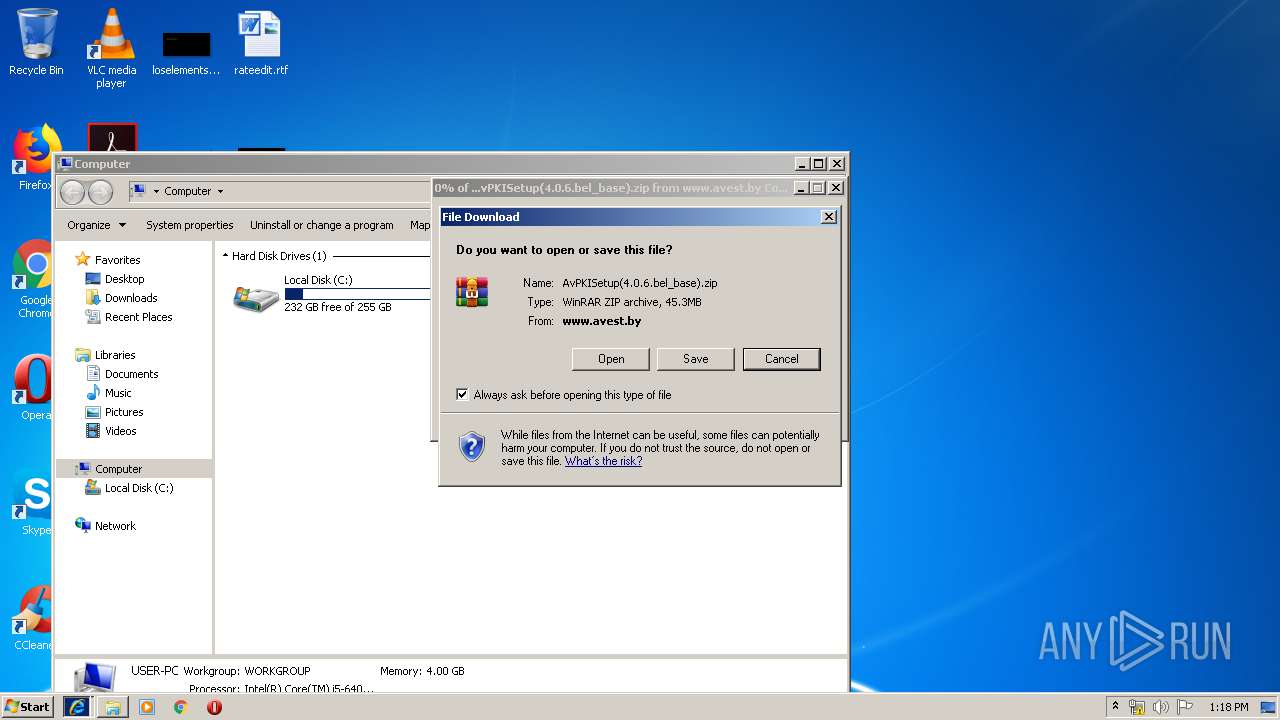
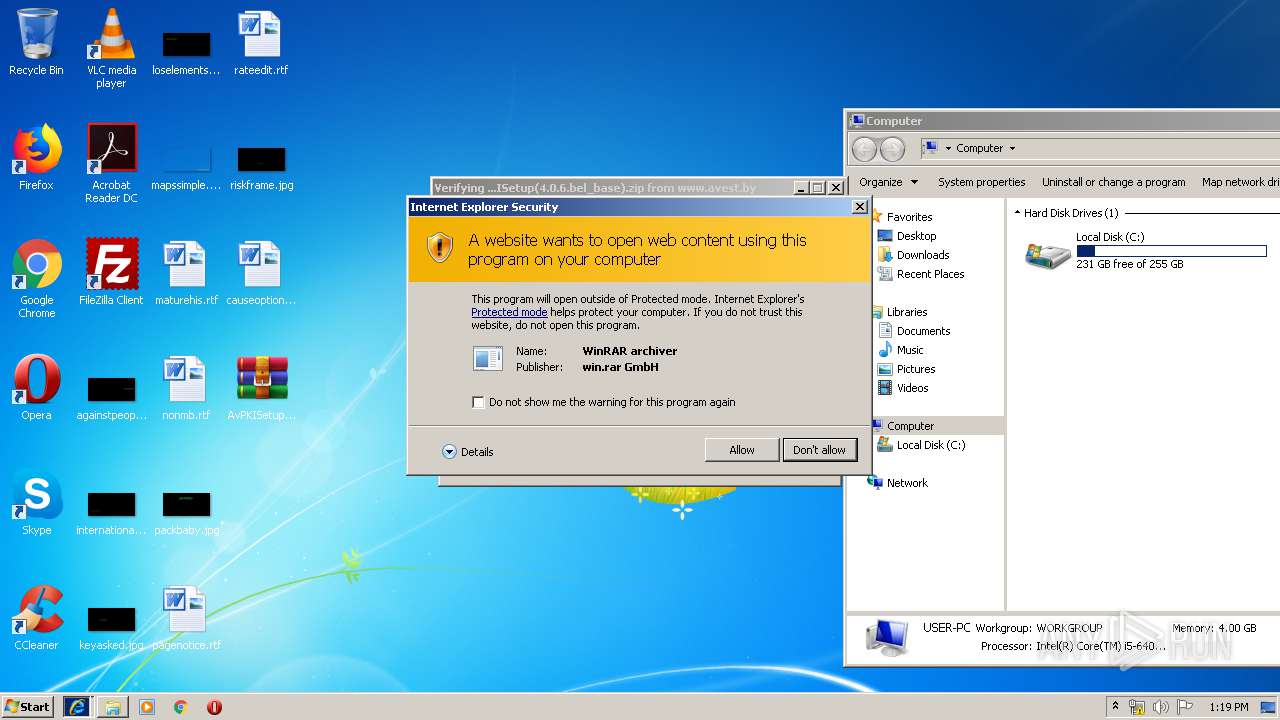
Starts Internet Explorer
- explorer.exe (PID: 2412)
- explorer.exe (PID: 2868)
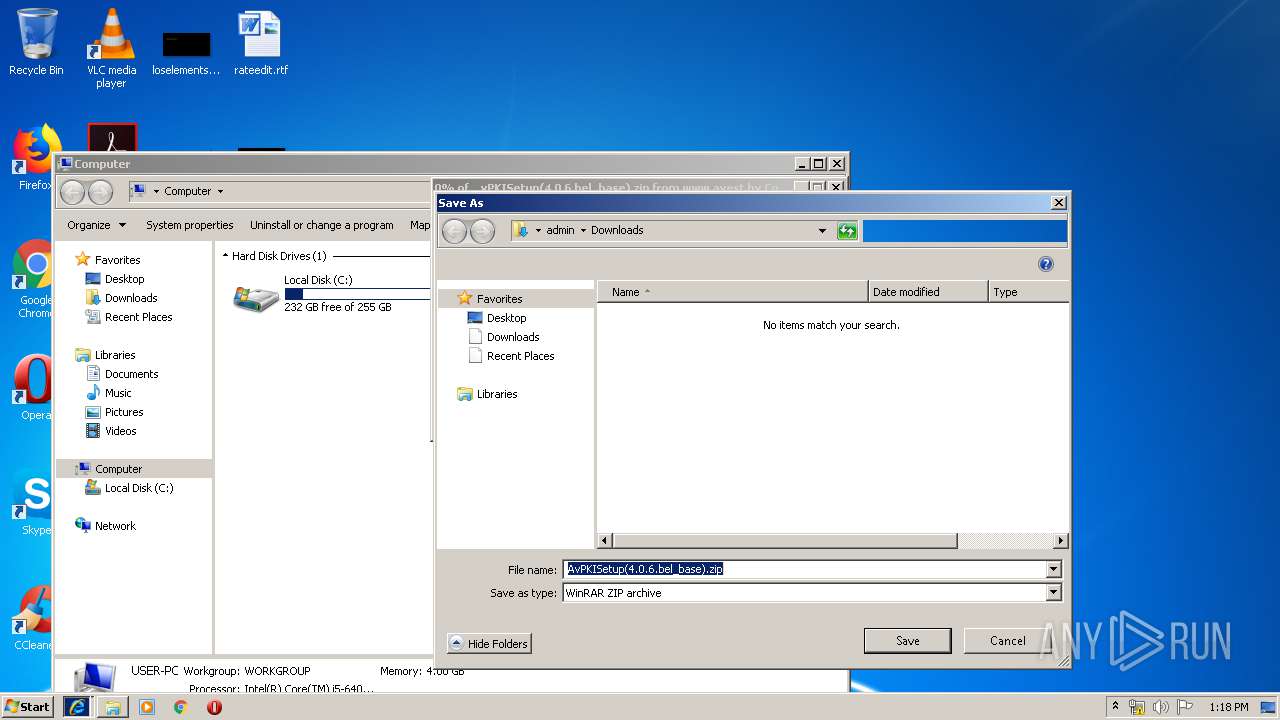
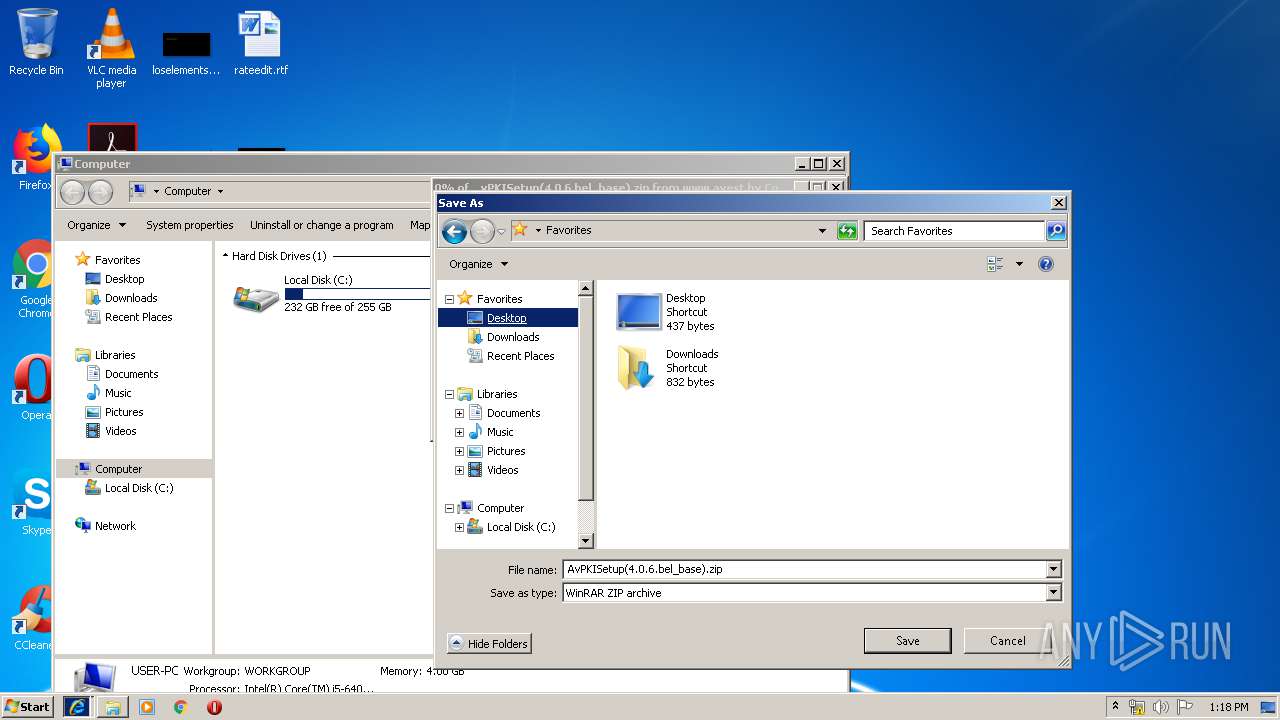
Creates files in the user directory
- explorer.exe (PID: 3220)
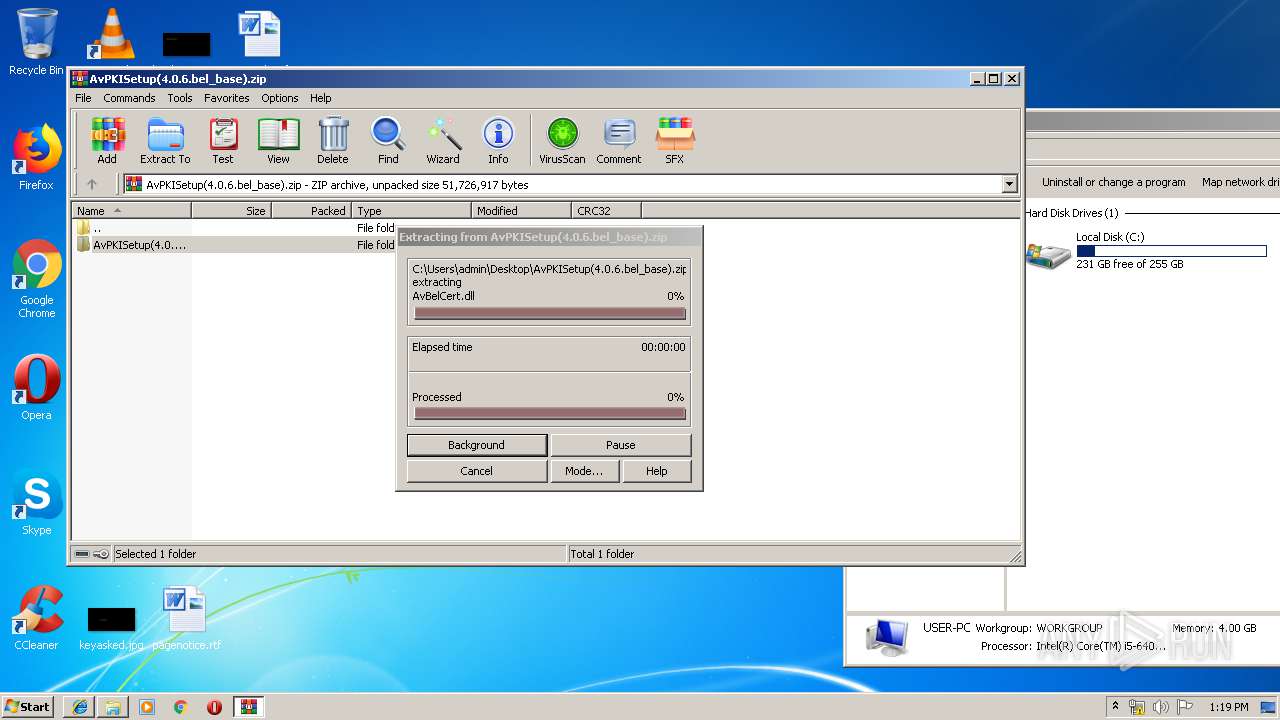
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3672)
Creates files in the program directory
- AvPKISetup2.exe (PID: 1400)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3704)
- iexplore.exe (PID: 4020)
Creates files in the user directory
- iexplore.exe (PID: 3960)
Reads Internet Cache Settings
- iexplore.exe (PID: 3960)
- iexplore.exe (PID: 2276)
- iexplore.exe (PID: 4020)
Reads settings of System Certificates
- iexplore.exe (PID: 4020)
Manual execution by user
- AvPKISetup2.exe (PID: 2408)
- AvPKISetup2.exe (PID: 1400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (30.9) |
| .scr | | | Windows screen saver (14.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.3) |
| .exe | | | Win32 Executable (generic) (5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2016:01:26 09:23:16+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 54272 |
| InitializedDataSize: | 117760 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 26-Jan-2016 08:23:16 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 26-Jan-2016 08:23:16 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.code | 0x00001000 | 0x00002FC8 | 0x00003000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 4.70438 |
.text | 0x00004000 | 0x0000A2F0 | 0x0000A400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.57283 |
.rdata | 0x0000F000 | 0x0000098E | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.61567 |
.data | 0x00010000 | 0x000019B4 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.19799 |
.rsrc | 0x00012000 | 0x0001AAF8 | 0x0001AC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.65855 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.09999 | 668 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
B | 5.37969 | 103856 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
D | 3.46772 | 14 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
N | 3 | 8 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
O | 0.918296 | 6 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
COMCTL32.DLL |
GDI32.DLL |
KERNEL32.dll |
MSVCRT.dll |
OLE32.DLL |
SHELL32.DLL |
SHLWAPI.DLL |
USER32.DLL |
WINMM.DLL |
Total processes
62
Monitored processes
15
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
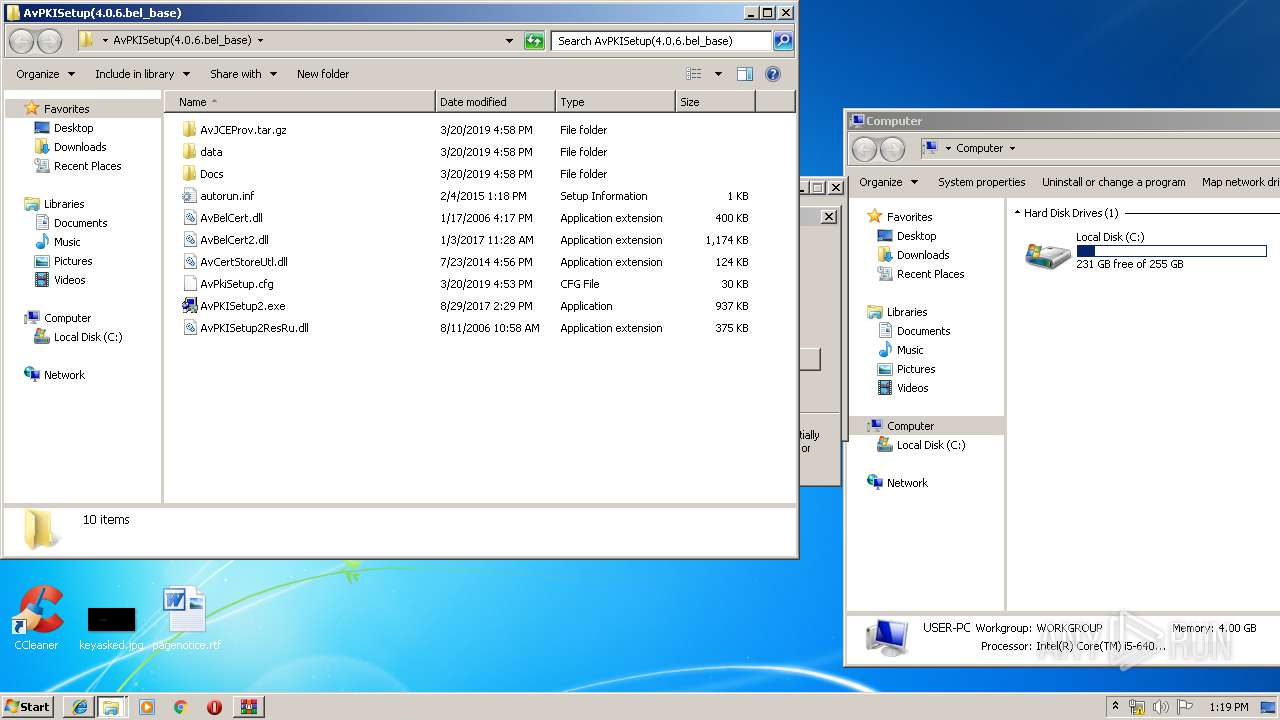
| 1400 | "C:\Users\admin\Desktop\AvPKISetup(4.0.6.bel_base)\AvPKISetup2.exe" | C:\Users\admin\Desktop\AvPKISetup(4.0.6.bel_base)\AvPKISetup2.exe | explorer.exe | ||||||||||||
User: admin Company: AVEST Integrity Level: HIGH Exit code: 0 Version: 0.5.24.137 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4020 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2408 | "C:\Users\admin\Desktop\AvPKISetup(4.0.6.bel_base)\AvPKISetup2.exe" | C:\Users\admin\Desktop\AvPKISetup(4.0.6.bel_base)\AvPKISetup2.exe | — | explorer.exe | |||||||||||
User: admin Company: AVEST Integrity Level: MEDIUM Exit code: 3221226540 Version: 0.5.24.137 Modules
| |||||||||||||||
| 2412 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2588 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe9_ Global\UsGthrCtrlFltPipeMssGthrPipe9 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2772 | "cmd" /c "C:\Users\admin\AppData\Local\Temp\EADF.tmp\ecfh.bat "C:\Users\admin\AppData\Local\Temp\6fa10ca9f0adf98e3a7b15f96cde4f0d39a400377a4b99bdcbb42b9ace46d01d.exe"" | C:\Windows\system32\cmd.exe | — | 6fa10ca9f0adf98e3a7b15f96cde4f0d39a400377a4b99bdcbb42b9ace46d01d.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2868 | C:\Windows\explorer.exe /factory,{75dff2b7-6936-4c06-a8bb-676a7b00b24b} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3220 | explorer "http://www.avest.by/crypto/download/avpki/AvPKISetup(4.0.6.bel_base).zip" | C:\Windows\explorer.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3304 | explorer "http://www.avest.by/crypto/download/avpki/AvPKISetup(4.0.6.bel_base).zip" | C:\Windows\explorer.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3508 | "C:\Users\admin\AppData\Local\Temp\6fa10ca9f0adf98e3a7b15f96cde4f0d39a400377a4b99bdcbb42b9ace46d01d.exe" | C:\Users\admin\AppData\Local\Temp\6fa10ca9f0adf98e3a7b15f96cde4f0d39a400377a4b99bdcbb42b9ace46d01d.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
2 140
Read events
1 930
Write events
206
Delete events
4
Modification events
| (PID) Process: | (3704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000077000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {CA3818D1-A7C3-11E9-B506-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (3704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (3704) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070700020010000C0012001100E802 | |||
Executable files
13
Suspicious files
3
Text files
18
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3704 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3704 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3704 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF516B78C14E9B7A99.TMP | — | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF394F22EFFD1A1104.TMP | — | |
MD5:— | SHA256:— | |||
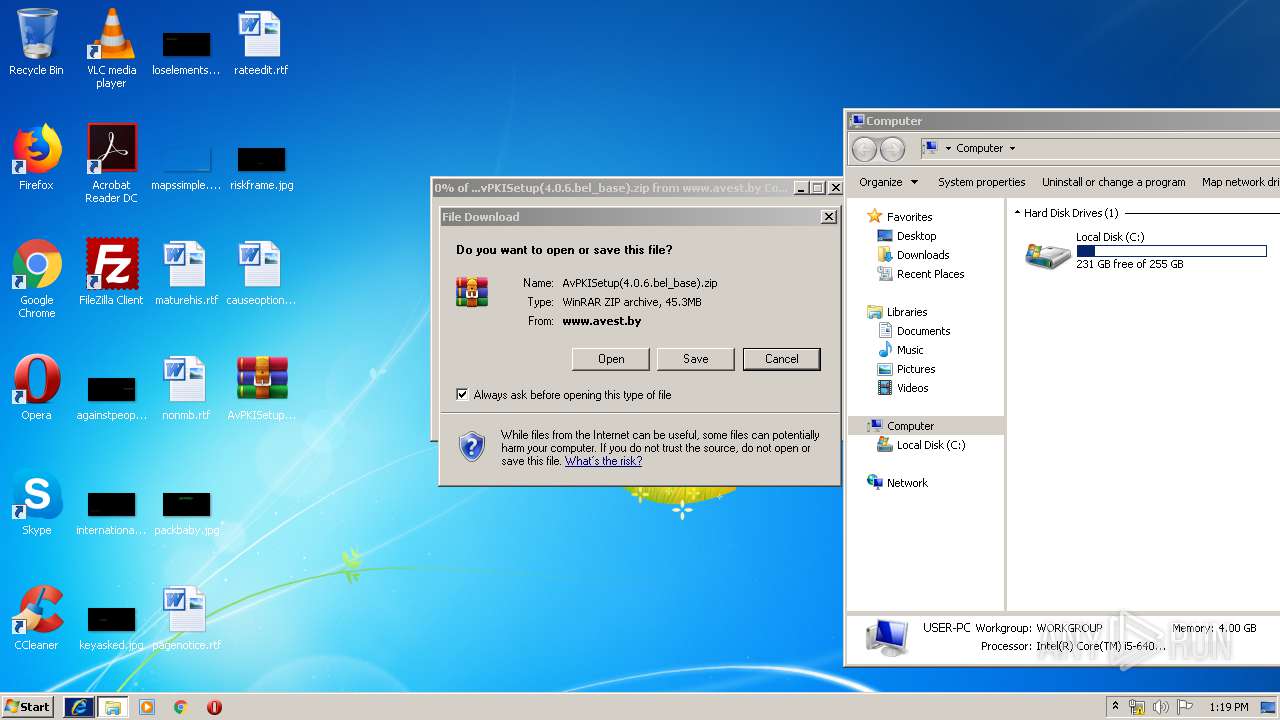
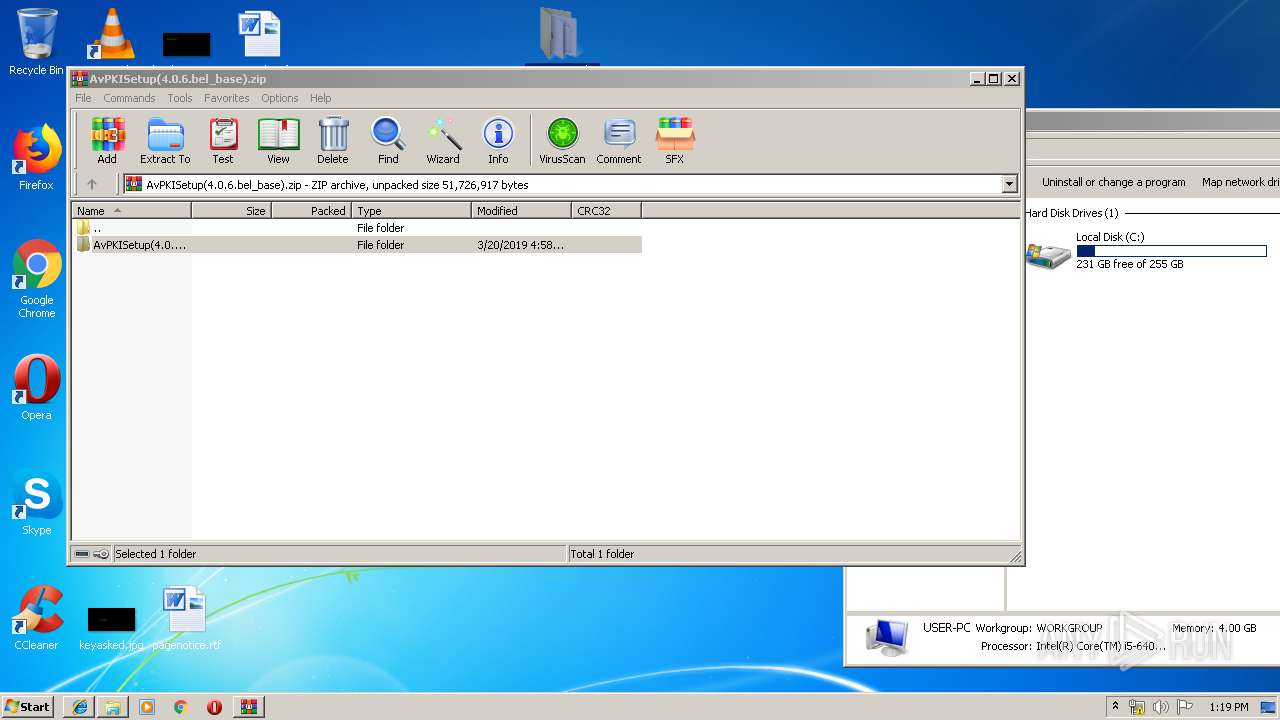
| 2276 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\FI5BJFBK\AvPKISetup(4.0.6.bel_base)[2].zip | — | |
MD5:— | SHA256:— | |||
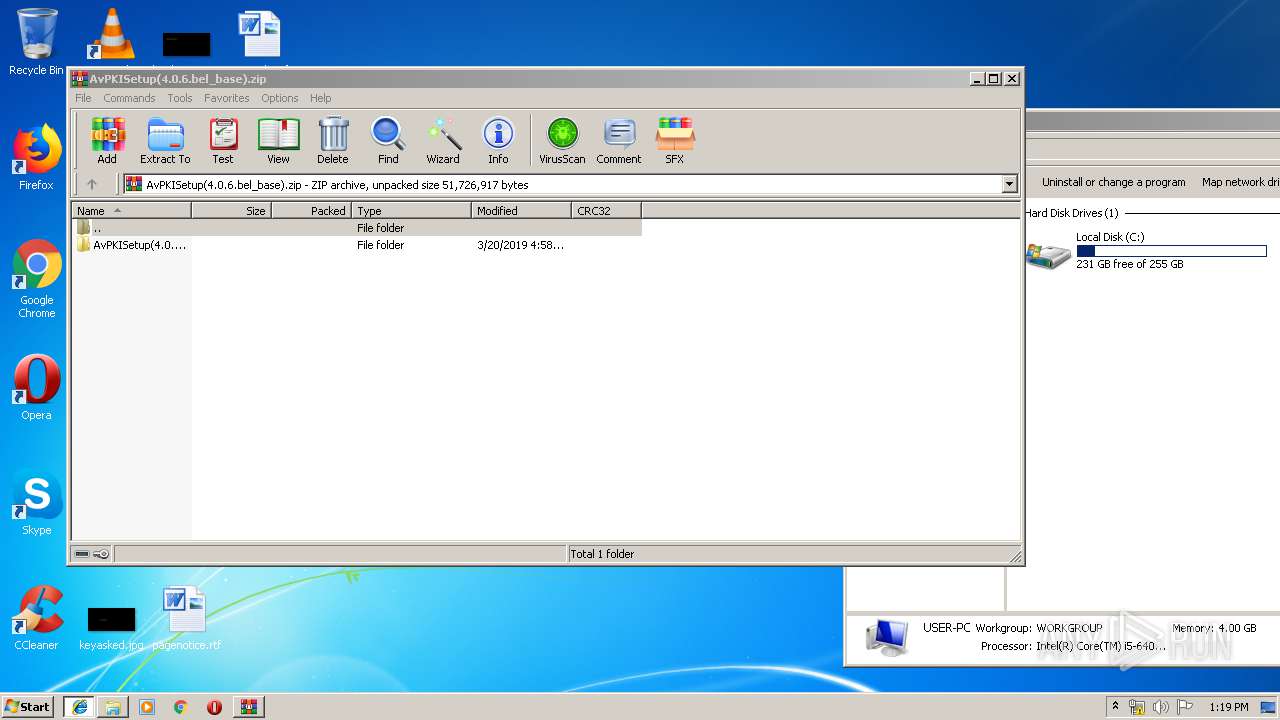
| 4020 | iexplore.exe | C:\Users\admin\Desktop\AvPKISetup(4.0.6.bel_base).zip | — | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFD2F5BF3A59B44C7F.TMP | — | |
MD5:— | SHA256:— | |||
| 4020 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{D286CA69-A7C3-11E9-B506-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
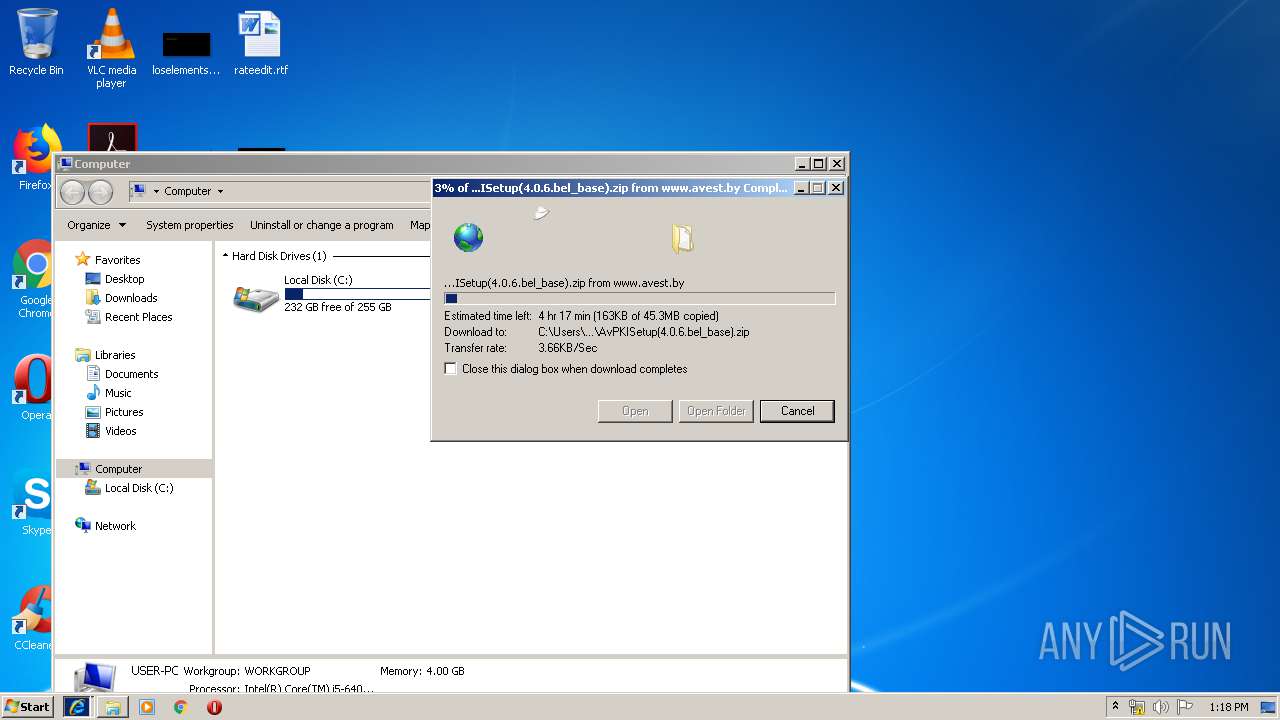
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
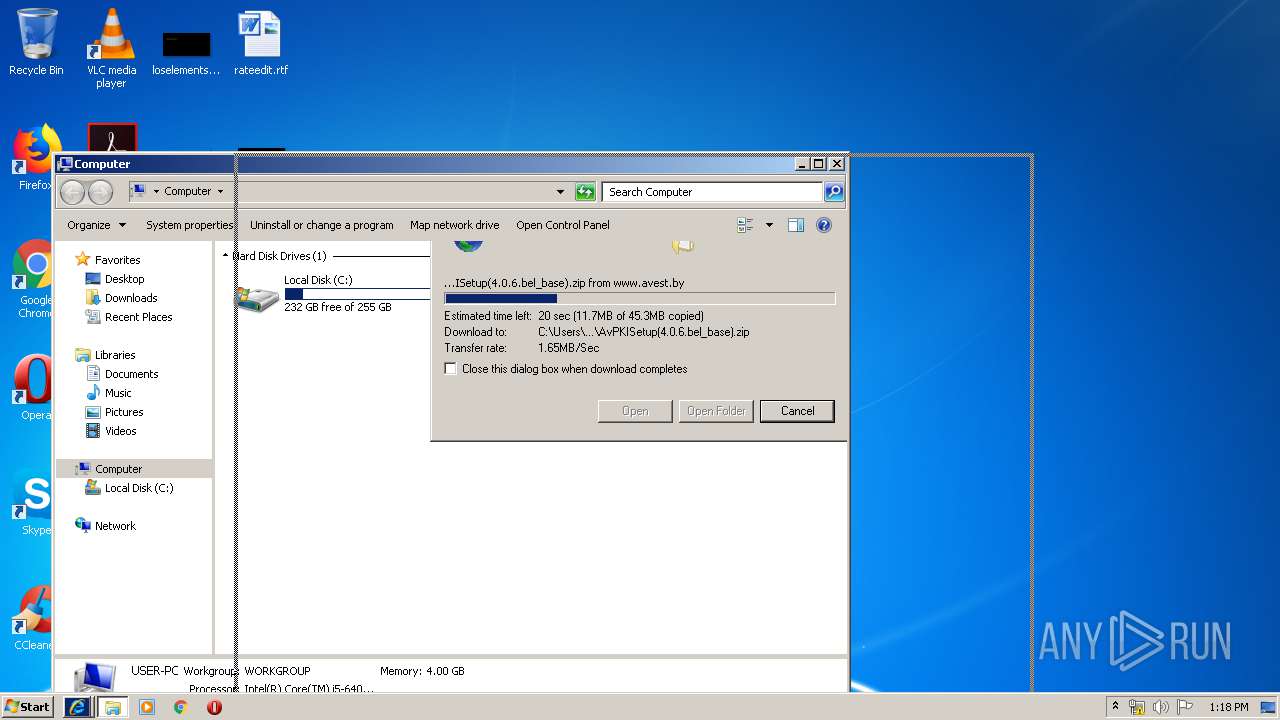
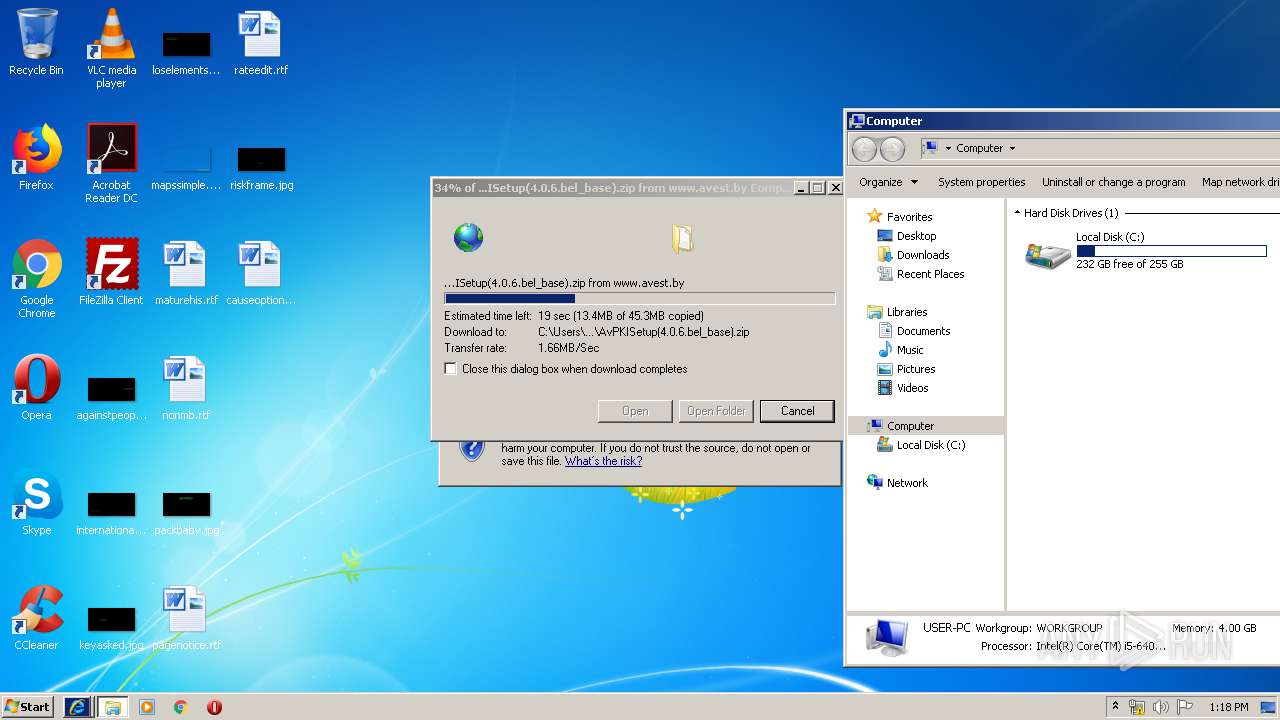
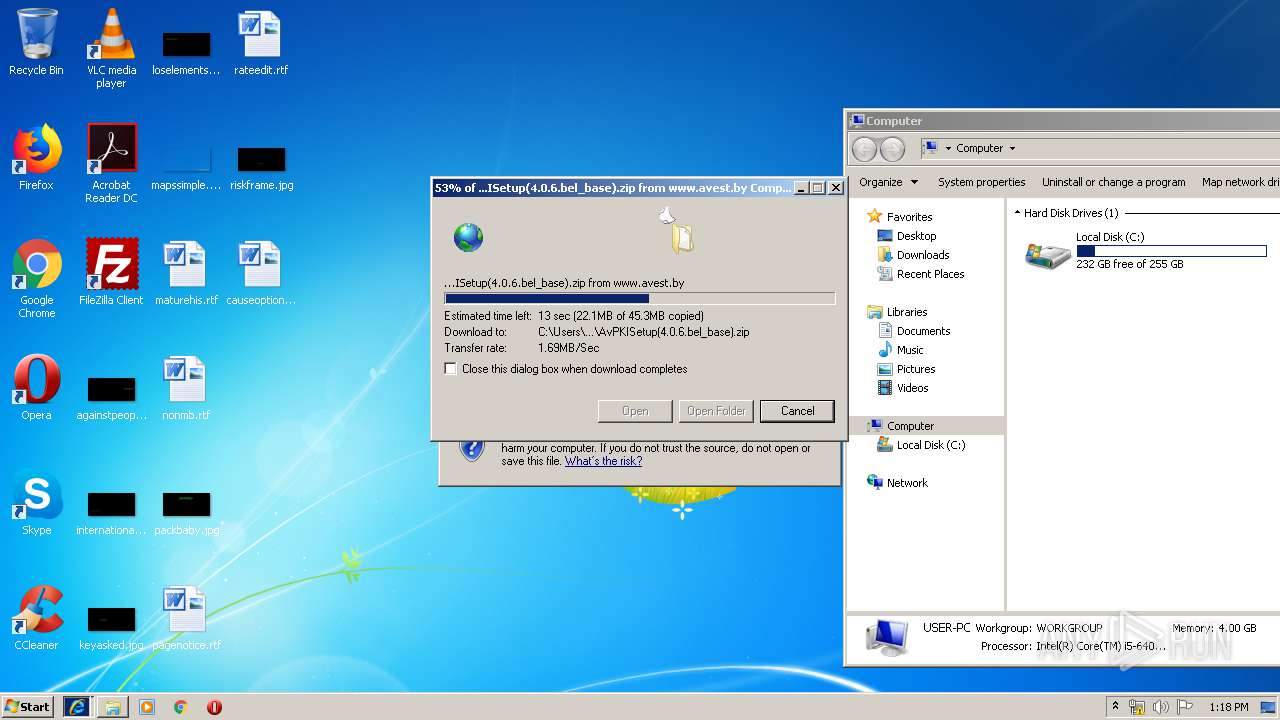
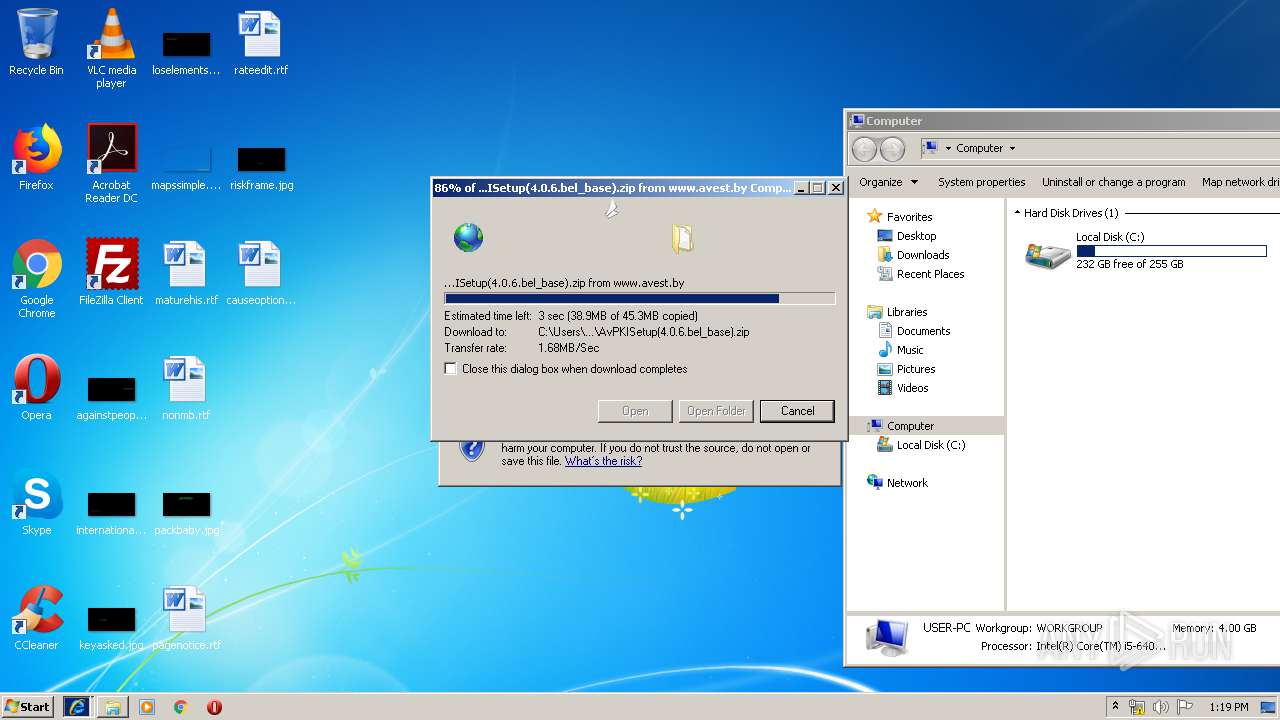
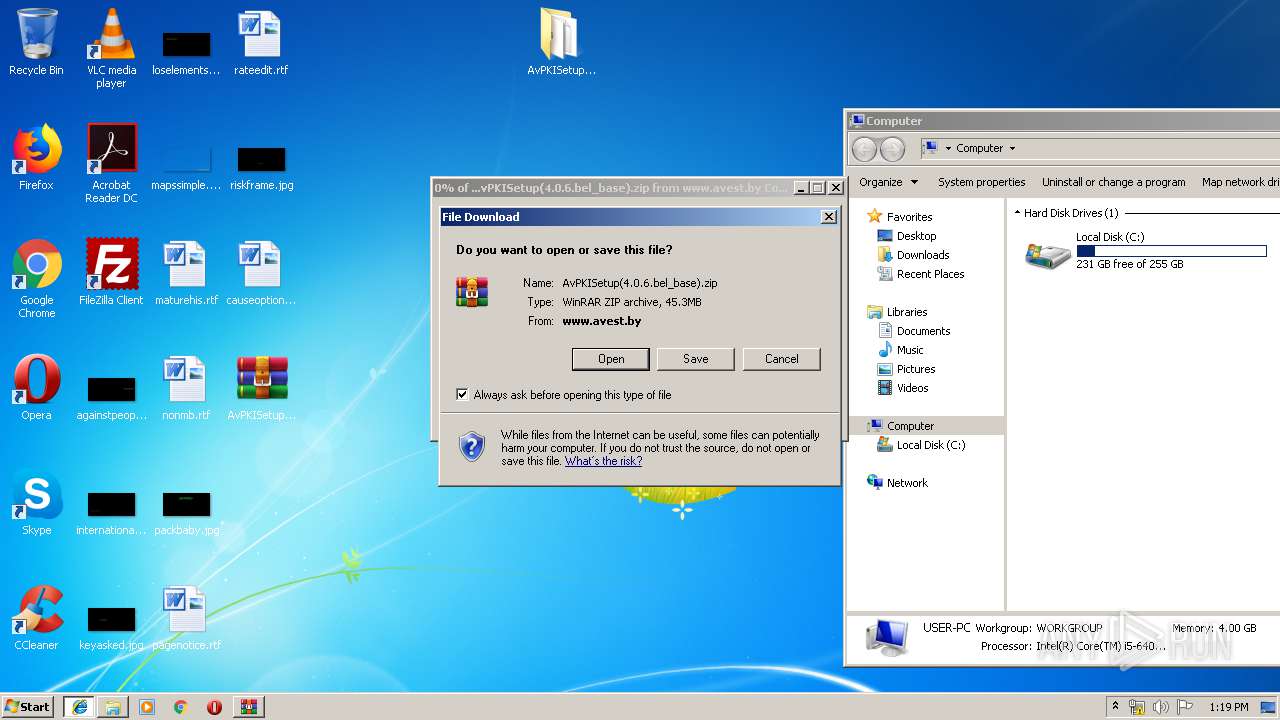
3960 | iexplore.exe | GET | — | 93.125.99.117:80 | http://www.avest.by/crypto/download/avpki/AvPKISetup(4.0.6.bel_base).zip | BY | — | — | malicious |
2276 | iexplore.exe | GET | 200 | 93.125.99.117:80 | http://www.avest.by/crypto/download/avpki/AvPKISetup(4.0.6.bel_base).zip | BY | compressed | 45.3 Mb | malicious |
3704 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
4020 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3704 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
4020 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3960 | iexplore.exe | 93.125.99.117:80 | www.avest.by | Republican Unitary Telecommunication Enterprise Beltelecom | BY | malicious |
2276 | iexplore.exe | 93.125.99.117:80 | www.avest.by | Republican Unitary Telecommunication Enterprise Beltelecom | BY | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.avest.by |
| malicious |
Threats
Process | Message |
|---|---|
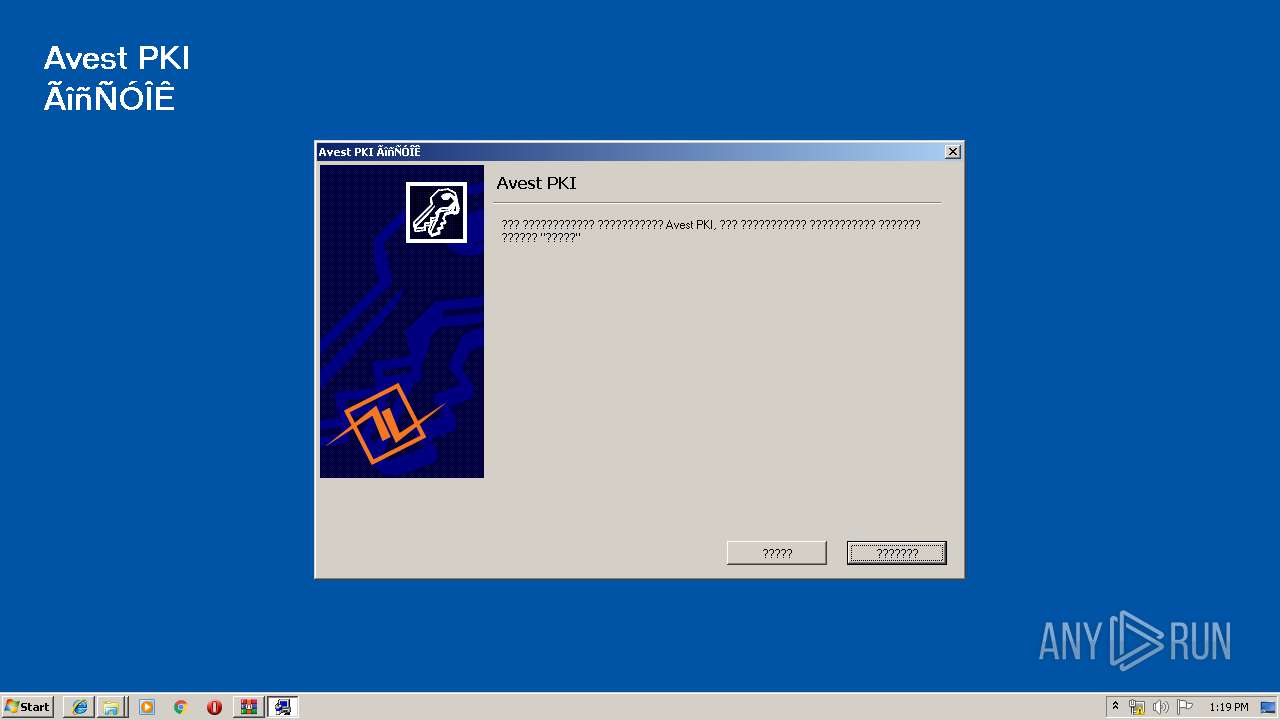
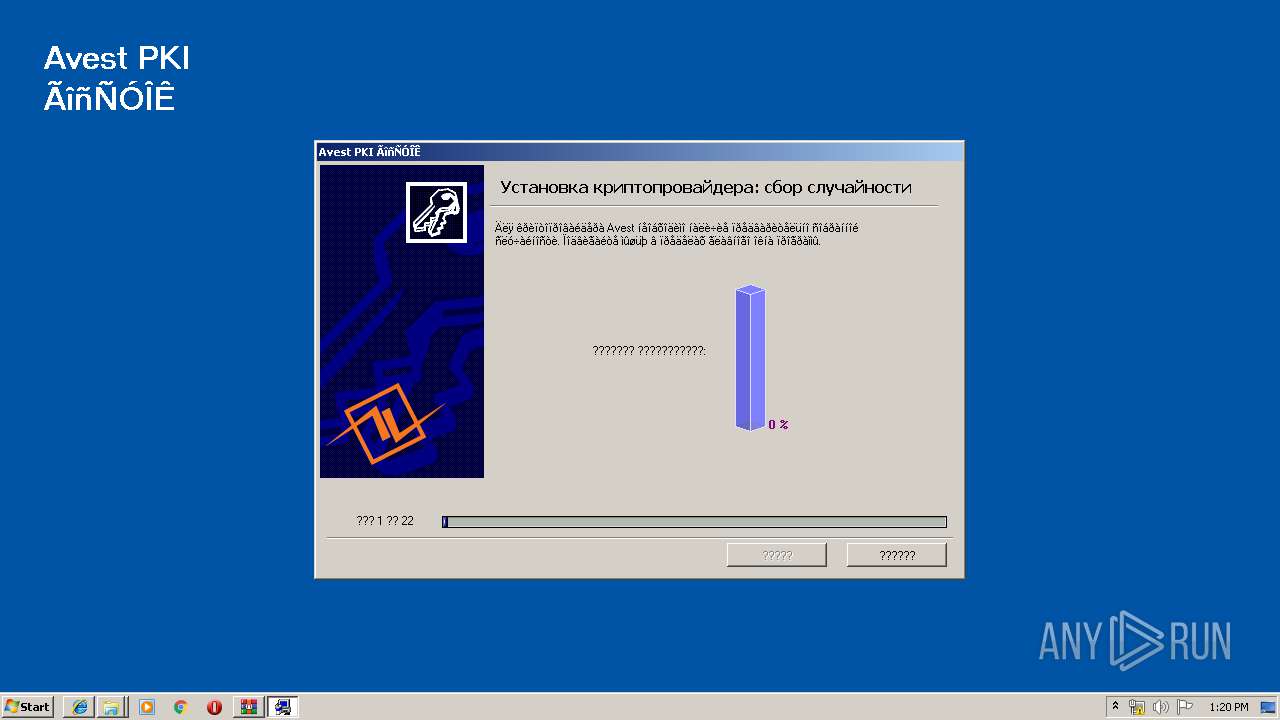
AvPKISetup2.exe | 6.1|True |
AvPKISetup2.exe | Processing node: SOFTWARE\AVEST\Avest CSP\1.0.0\Avest CSP\devices |
AvPKISetup2.exe | Processing node: SOFTWARE\AVEST\Avest CSP\1.0.0\Avest CSP Base\devices |
AvPKISetup2.exe | got container list: |
AvPKISetup2.exe | 6.1|True |
AvPKISetup2.exe | ***** DoRegValuesExist start, section: STEP1 |
AvPKISetup2.exe | ExistsRegKey1=HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KB2836198\DisplayName |
AvPKISetup2.exe | cheking existance |
AvPKISetup2.exe | key does not exist \SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\KB2836198 |
AvPKISetup2.exe | ExistsRegKey2= |