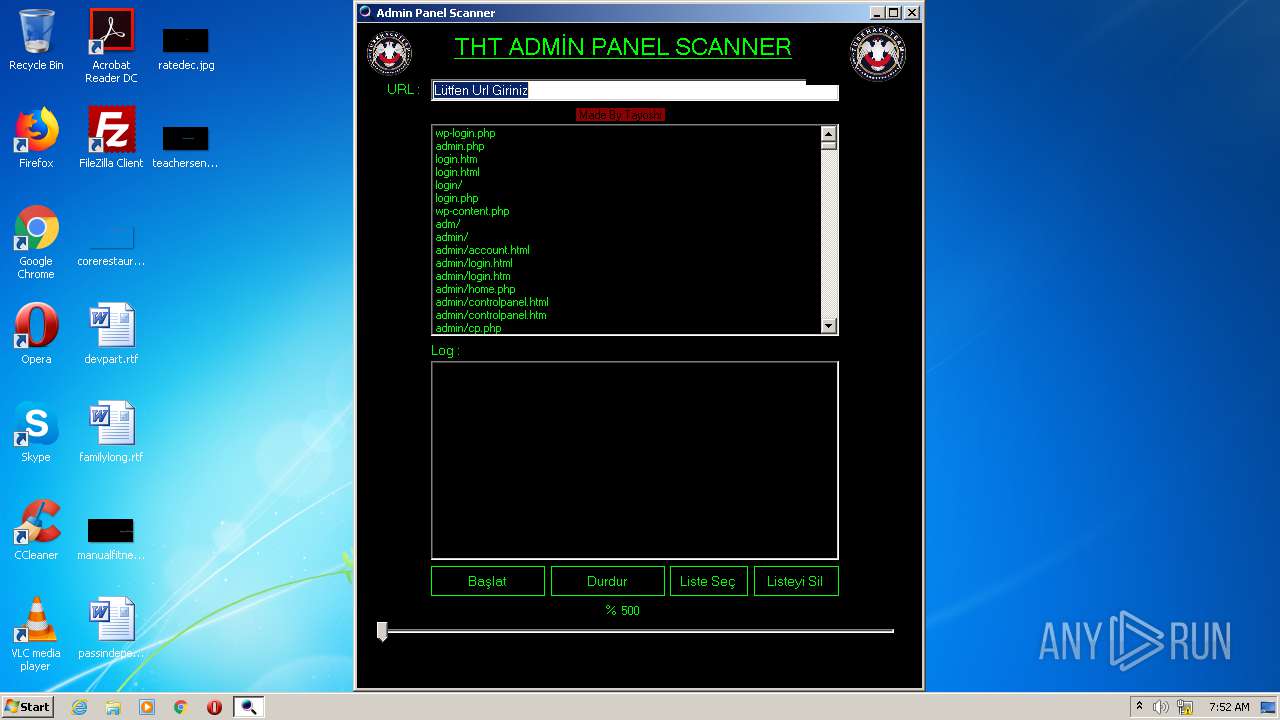
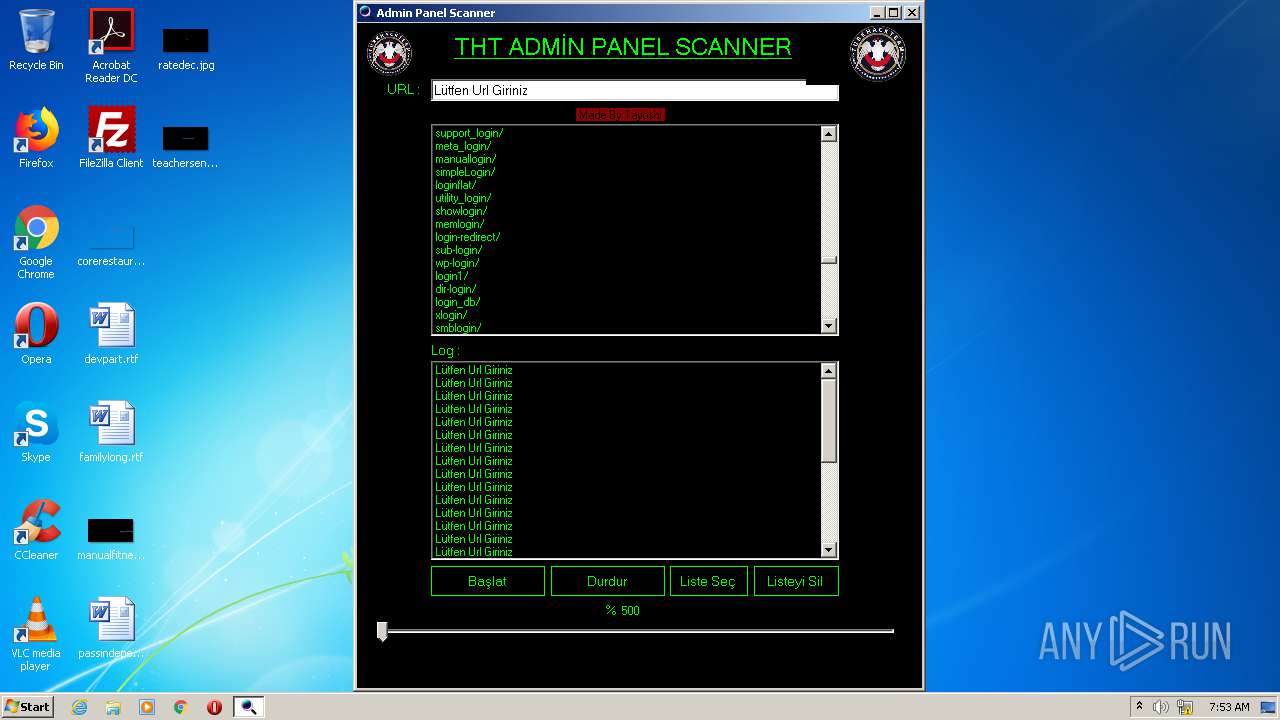
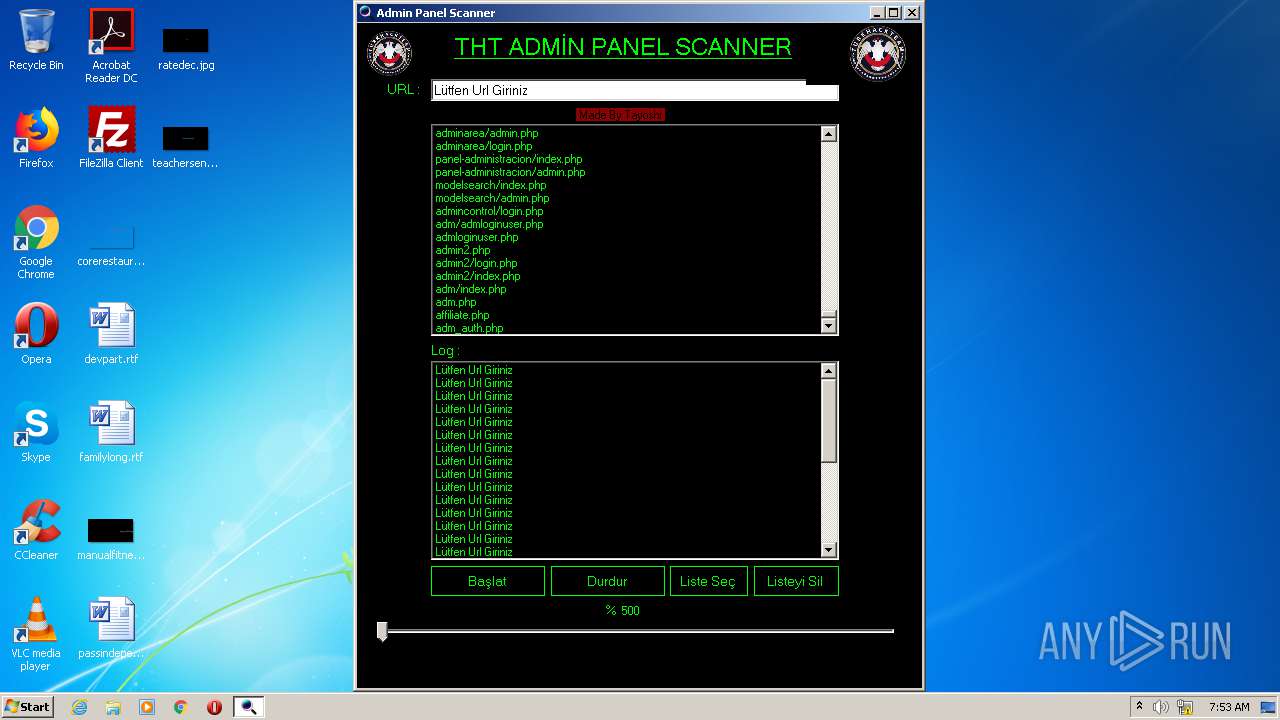
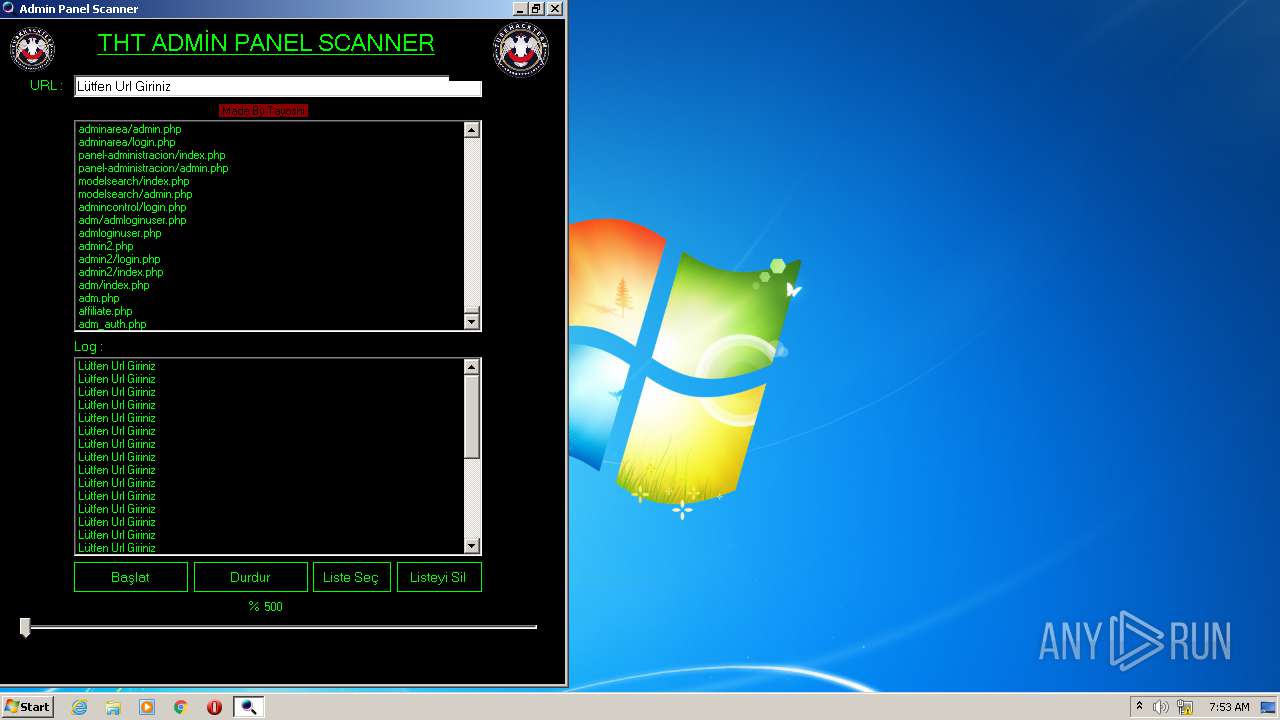
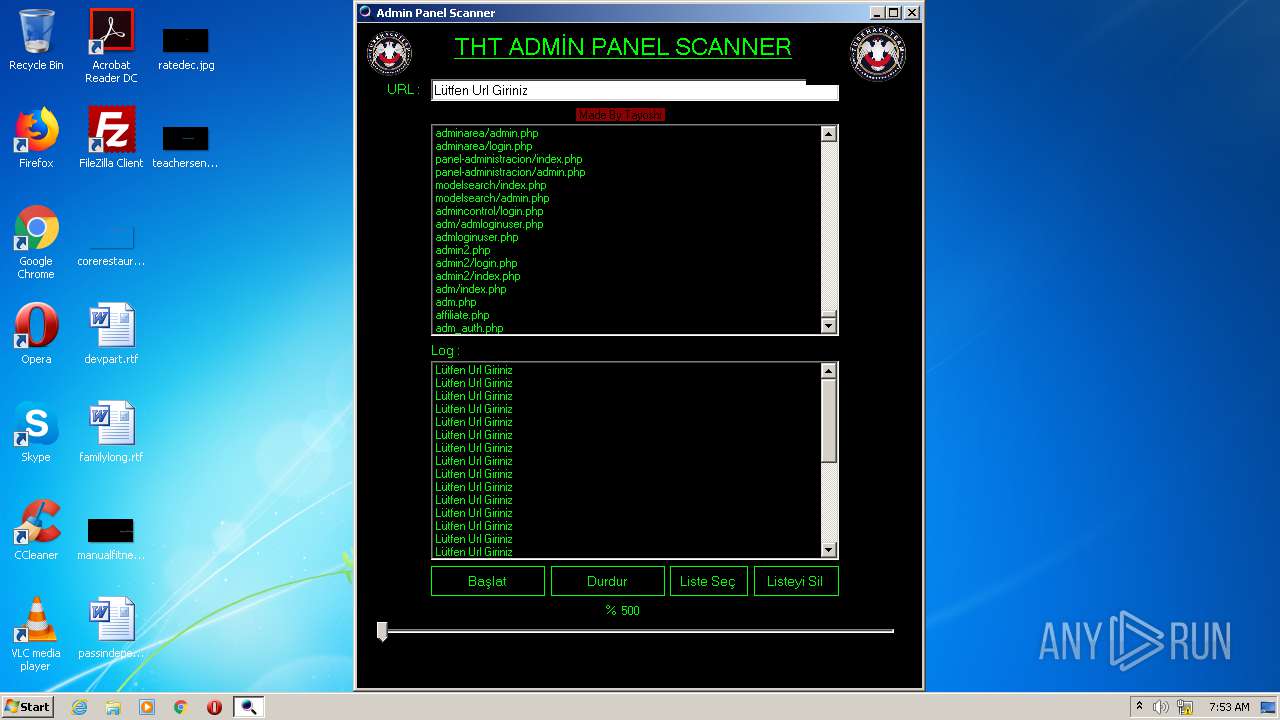
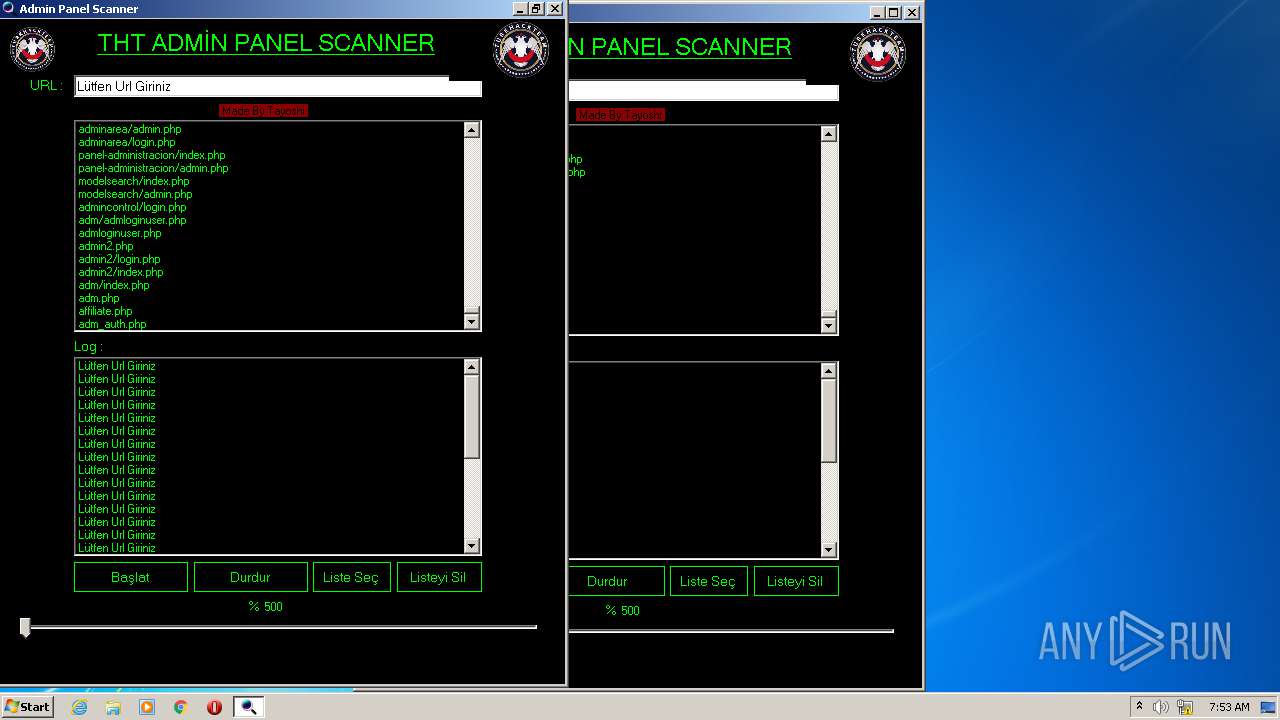
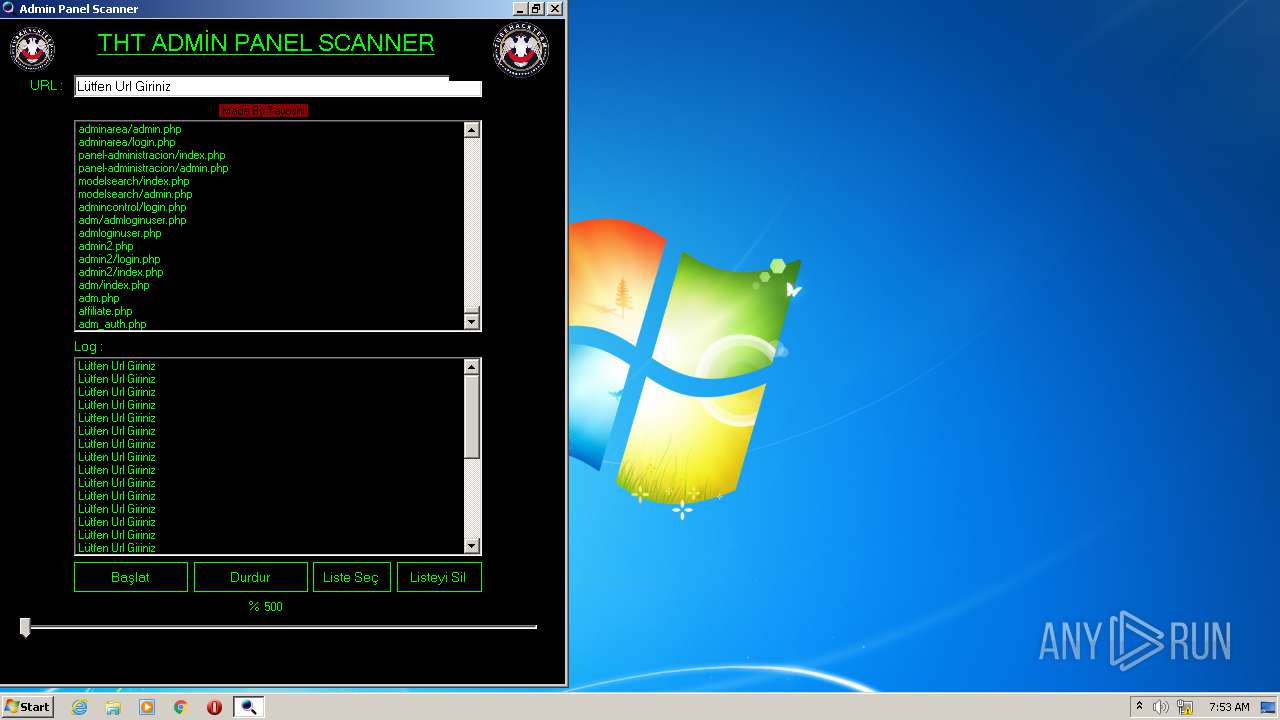
| File name: | Admin Panel Scanner.exe |
| Full analysis: | https://app.any.run/tasks/8973aa14-1867-471e-8f3f-ada89ce587aa |
| Verdict: | Malicious activity |
| Analysis date: | January 22, 2021, 07:52:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 073D88139045CF60F5541ACA31D4F48A |
| SHA1: | 10519B58B03E4A0388E229AFE3C1D105F1D01103 |
| SHA256: | 6F957865A923E98E1FC9EB9E42C0B0E5EAA8D0717C600231E9BACC08FBD5486F |
| SSDEEP: | 12288:cya0Y0SBsjcNHZJytVLROHZJytVLRWVaAnsZmt6xX:cypY6jQHDyLLcHDyLLIV6Z46x |
MALICIOUS
No malicious indicators.SUSPICIOUS
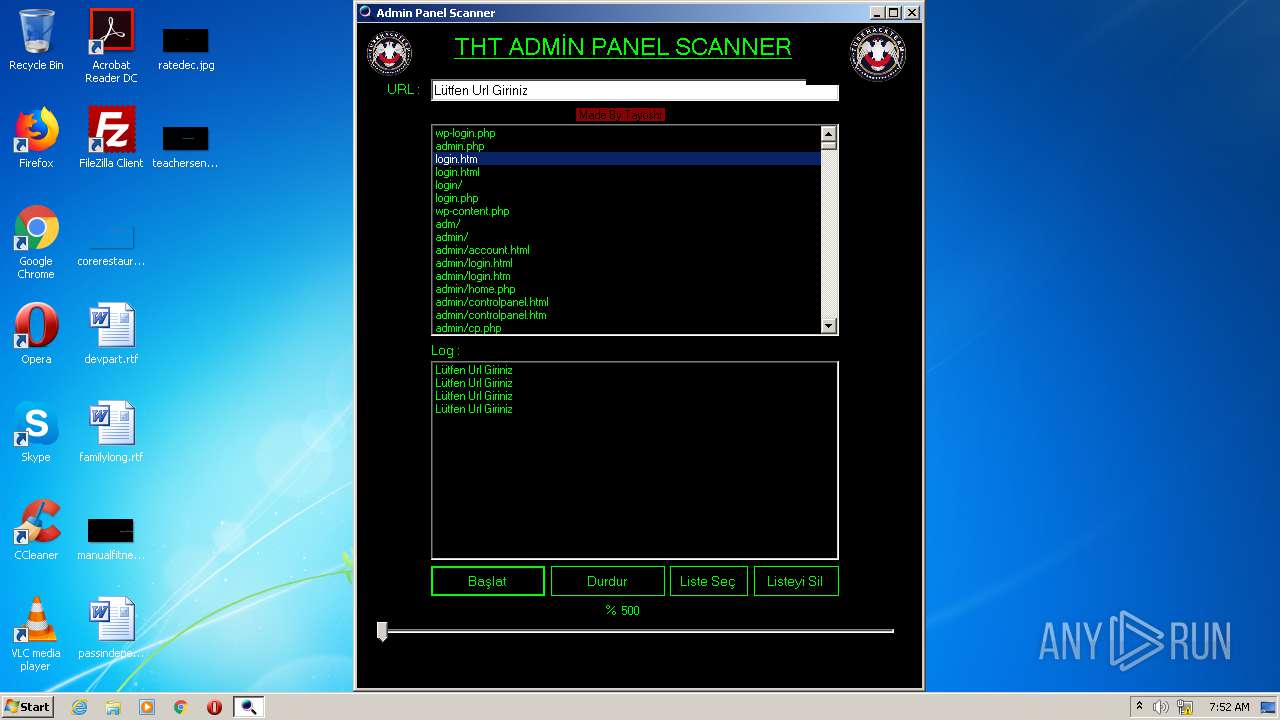
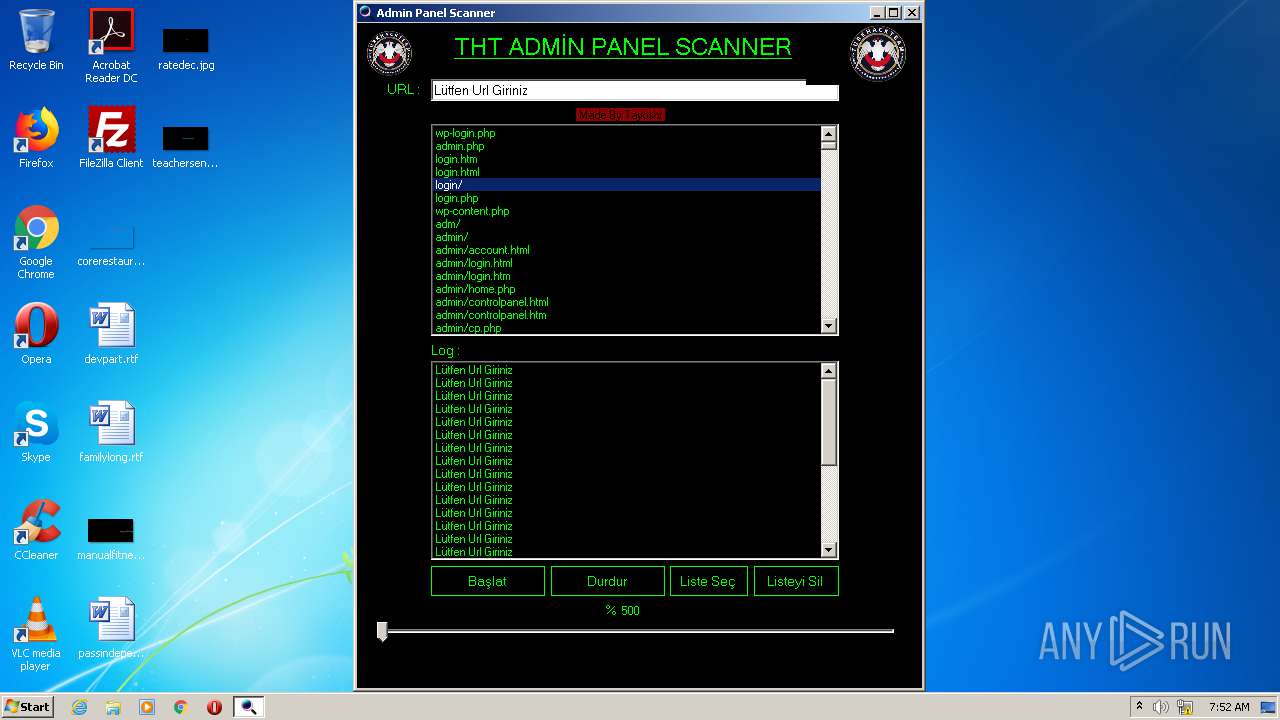
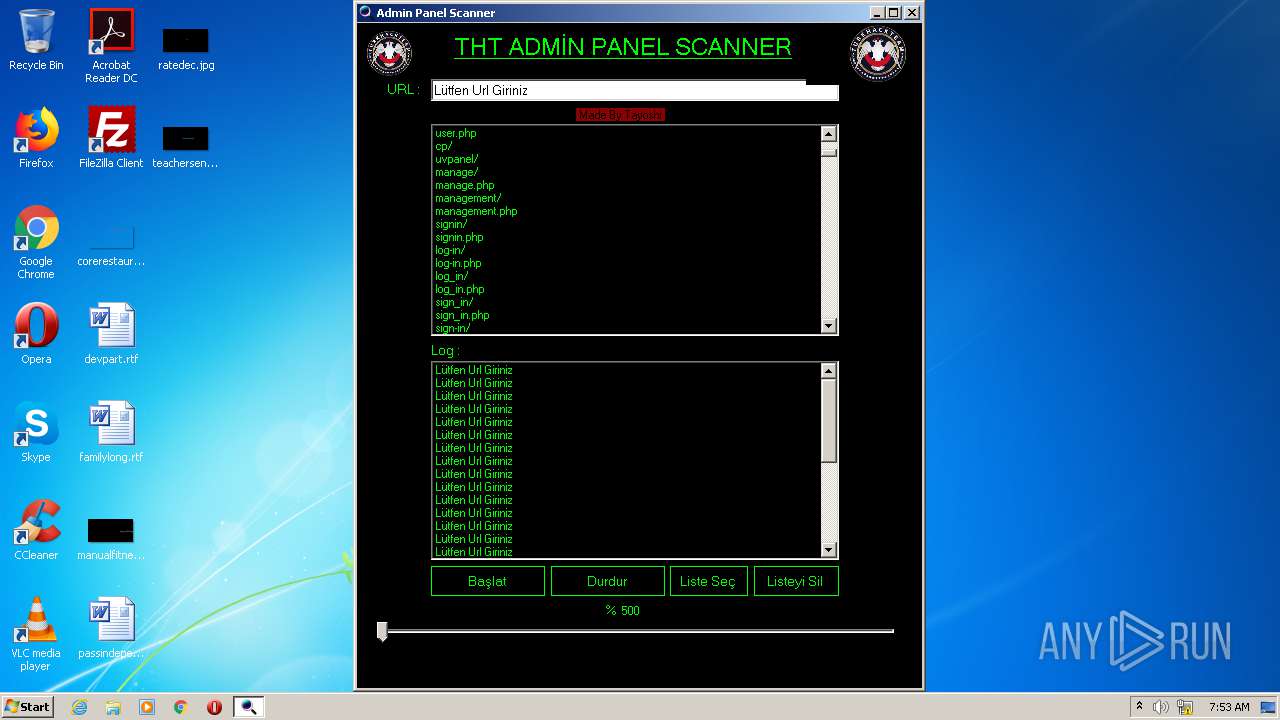
Reads internet explorer settings
- Admin Panel Scanner.exe (PID: 3484)
Creates files in the user directory
- Admin Panel Scanner.exe (PID: 3484)
INFO
Reads settings of System Certificates
- Admin Panel Scanner.exe (PID: 3484)
Dropped object may contain Bitcoin addresses
- Admin Panel Scanner.exe (PID: 3484)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (63.1) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.8) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.6) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Generic Win/DOS Executable (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:01:22 08:19:41+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 80 |
| CodeSize: | 454656 |
| InitializedDataSize: | 212480 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x70e12 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 3.4.4.6 |
| ProductVersionNumber: | 3.4.4.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | Admin Panel Scanner |
| CompanyName: | X - Y |
| FileDescription: | Admin Panel Scanner |
| FileVersion: | 3.4.4.6 |
| InternalName: | Admin Panel Scanner.exe |
| LegalCopyright: | Copyright © 2017 |
| LegalTrademarks: | Anon X - Y |
| OriginalFileName: | Admin Panel Scanner.exe |
| ProductName: | Admin Panel Scanner |
| ProductVersion: | 3.4.4.6 |
| AssemblyVersion: | 4.4.6.3 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Jan-2021 07:19:41 |
| Debug artifacts: |
|
| Comments: | Admin Panel Scanner |
| CompanyName: | X - Y |
| FileDescription: | Admin Panel Scanner |
| FileVersion: | 3.4.4.6 |
| InternalName: | Admin Panel Scanner.exe |
| LegalCopyright: | Copyright © 2017 |
| LegalTrademarks: | Anon X - Y |
| OriginalFilename: | Admin Panel Scanner.exe |
| ProductName: | Admin Panel Scanner |
| ProductVersion: | 3.4.4.6 |
| Assembly Version: | 4.4.6.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 22-Jan-2021 07:19:41 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0006EE18 | 0x0006F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.82648 |
.rsrc | 0x00072000 | 0x00033A2C | 0x00033C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.91522 |
.reloc | 0x000A6000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0815394 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
32512 | 2.16096 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
35
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3484 | "C:\Users\admin\AppData\Local\Temp\Admin Panel Scanner.exe" | C:\Users\admin\AppData\Local\Temp\Admin Panel Scanner.exe | explorer.exe | ||||||||||||
User: admin Company: X - Y Integrity Level: MEDIUM Description: Admin Panel Scanner Exit code: 0 Version: 3.4.4.6 Modules
| |||||||||||||||
Total events
239
Read events
220
Write events
19
Delete events
0
Modification events
| (PID) Process: | (3484) Admin Panel Scanner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3484) Admin Panel Scanner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3484) Admin Panel Scanner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3484) Admin Panel Scanner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3484) Admin Panel Scanner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3484) Admin Panel Scanner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3484) Admin Panel Scanner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3484) Admin Panel Scanner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
9
Text files
108
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3484 | Admin Panel Scanner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\98ZUFQW9.txt | — | |
MD5:— | SHA256:— | |||
| 3484 | Admin Panel Scanner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\002SK26M.txt | — | |
MD5:— | SHA256:— | |||
| 3484 | Admin Panel Scanner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\6HODU3ZW.txt | — | |
MD5:— | SHA256:— | |||
| 3484 | Admin Panel Scanner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\5EKRRF7E.txt | — | |
MD5:— | SHA256:— | |||
| 3484 | Admin Panel Scanner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\NHSPGOGP.txt | — | |
MD5:— | SHA256:— | |||
| 3484 | Admin Panel Scanner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Q7W7ODCI.txt | — | |
MD5:— | SHA256:— | |||
| 3484 | Admin Panel Scanner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\ZG6UE6VF.txt | — | |
MD5:— | SHA256:— | |||
| 3484 | Admin Panel Scanner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\J0112JCS.txt | — | |
MD5:— | SHA256:— | |||
| 3484 | Admin Panel Scanner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\B9P396N2.txt | — | |
MD5:— | SHA256:— | |||
| 3484 | Admin Panel Scanner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\WV57I8EZ.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 286
TCP/UDP connections
66
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3484 | Admin Panel Scanner.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rb/5q/cj,nj/ncOCq_AUYQfxAHwlVcRNOHvharw.js?bu=C-Ij8yLRBYIj5SOMI5Qj6SO4I6Ei7CM | US | text | 6.16 Kb | whitelisted |
3484 | Admin Panel Scanner.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rp/B1t1069l5xndLcm-F09xFfnJ7zc.gz.js | US | text | 7.97 Kb | whitelisted |
3484 | Admin Panel Scanner.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/search?q=L%C3%BCtfen+Url+Girinizlogin.htm&src=IE-TopResult&FORM=IE11TR&conversationid= | US | html | 40.5 Kb | whitelisted |
3484 | Admin Panel Scanner.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rp/w6Ib82JSGwjhDlWoen76TPCd0rE.gz.js | US | text | 425 b | whitelisted |
3484 | Admin Panel Scanner.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rp/pXscrbCrewUD-UetJTvW5F7YMxo.gz.js | US | text | 324 b | whitelisted |
3484 | Admin Panel Scanner.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rp/eF3rIdIG4fsLyPy7mzgRnjCDKIA.png | US | image | 11.8 Kb | whitelisted |
3484 | Admin Panel Scanner.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rp/5rqGloMo94v3vwNVR5OsxDNd8d0.svg | US | image | 461 b | whitelisted |
3484 | Admin Panel Scanner.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rp/oJo5q-2lXjm93atzl7HJ_6B3pIc.gz.js | US | text | 269 b | whitelisted |
3484 | Admin Panel Scanner.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/rp/n8-O_KIRNSMPFWQWrGjn0BRH6SM.gz.js | US | text | 824 b | whitelisted |
3484 | Admin Panel Scanner.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/fd/ls/l?IG=31BEFC59F7064D93B01CD85524E09CE0&CID=3F1C476E24656C8E3B7C48A9250E6DB4&Type=Event.CPT&DATA={"pp":{"S":"L","FC":109,"BC":109,"SE":-1,"TC":-1,"H":140,"BP":172,"CT":172,"IL":1},"ad":[-1,-1,4,4,1164,1463,0]}&P=SERP&DA=DUB02 | US | image | 11.8 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3484 | Admin Panel Scanner.exe | 40.126.31.141:443 | login.microsoftonline.com | Microsoft Corporation | US | suspicious |
3484 | Admin Panel Scanner.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
— | — | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3484 | Admin Panel Scanner.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3484 | Admin Panel Scanner.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3484 | Admin Panel Scanner.exe | 2.16.186.97:80 | a4.bing.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
a4.bing.com |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |