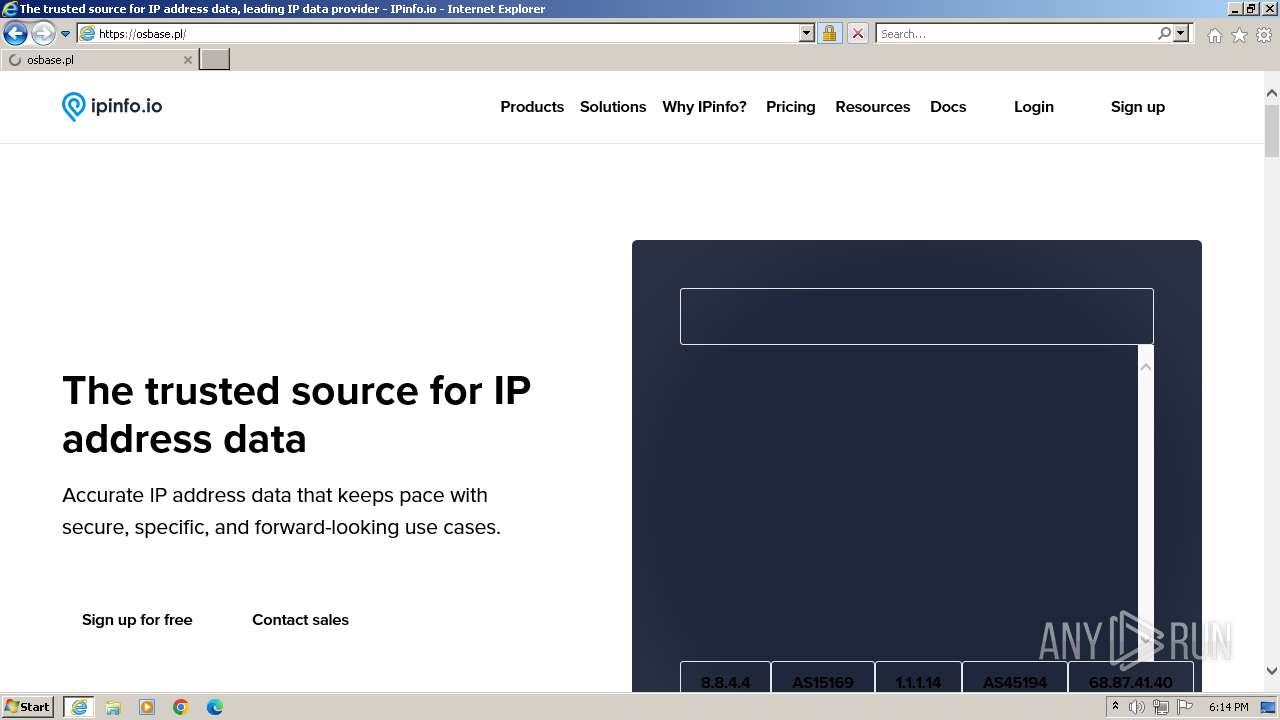
| URL: | https://ipinfo.io |
| Full analysis: | https://app.any.run/tasks/a8ec5991-b825-43f2-94f5-f5883a40851f |
| Verdict: | Malicious activity |
| Analysis date: | October 22, 2023, 17:13:35 |
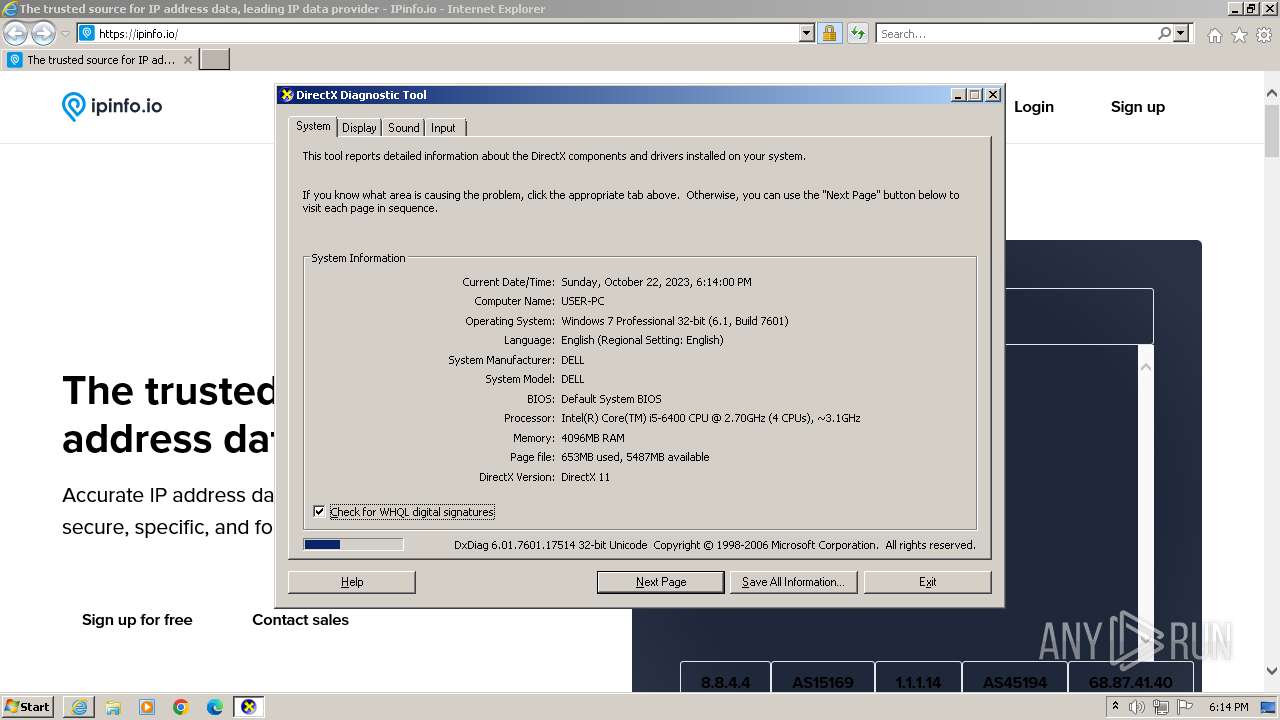
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | B80865FF16F1444C0614B2DB2073A800 |
| SHA1: | 6A185E4B4E075643277B24C5A5D7A9CF5D7FABD2 |
| SHA256: | 6F8D476AAA9E3670F3C64C01A4CD3470DC70FEC55325D1945DFCFA8F2DB59F47 |
| SSDEEP: | 3:N8g:2g |
MALICIOUS
No malicious indicators.SUSPICIOUS
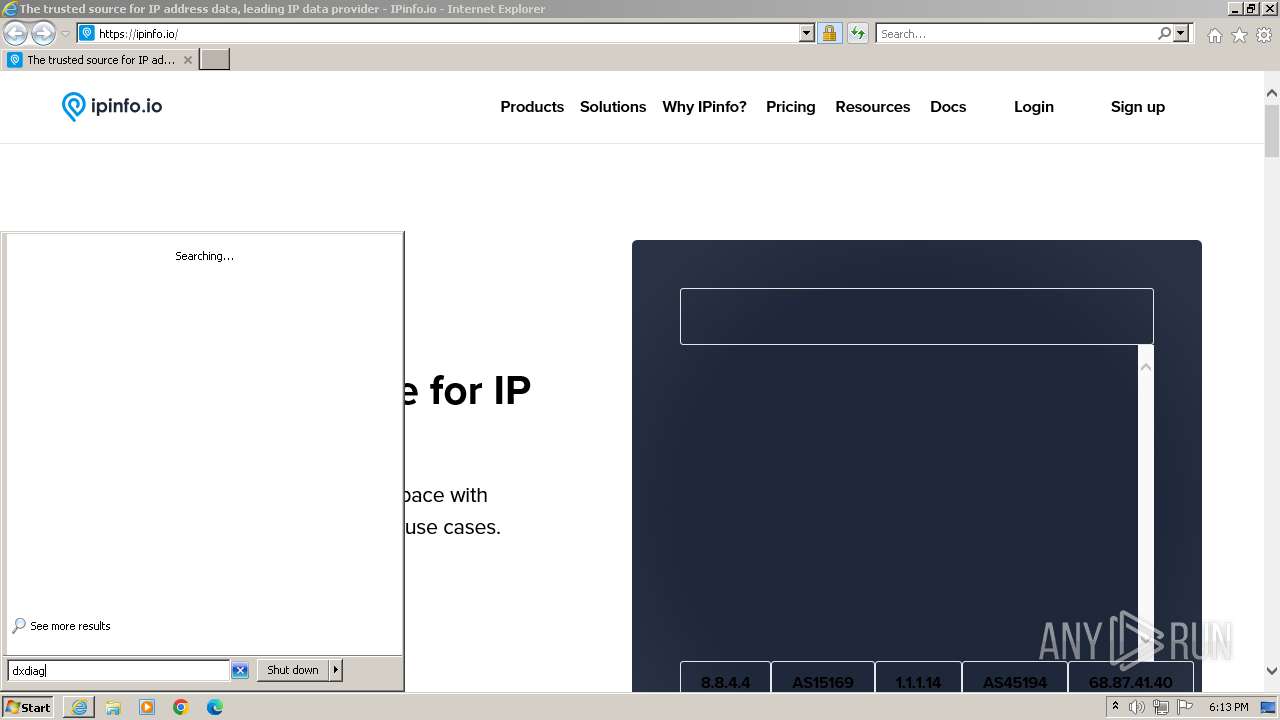
Reads settings of System Certificates
- dxdiag.exe (PID: 3124)
Reads the Internet Settings
- dxdiag.exe (PID: 3124)
INFO
Application launched itself
- iexplore.exe (PID: 1764)
Manual execution by a user
- dxdiag.exe (PID: 3124)
Reads security settings of Internet Explorer
- dxdiag.exe (PID: 3124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
41
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1764 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://ipinfo.io" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3124 | "C:\Windows\system32\dxdiag.exe" | C:\Windows\System32\dxdiag.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft DirectX Diagnostic Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3996 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1764 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
22 783
Read events
22 658
Write events
105
Delete events
20
Modification events
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1764) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
0
Suspicious files
49
Text files
97
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\TarC504.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_28DEA62A0AE77228DD387E155AD0BA27 | binary | |
MD5:549A71BC44F3F875163006644BEB5D66 | SHA256:280EC994FF1EF94217E3567745A836069E8D9C248DB0C5D28487920DDFEE8912 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\CAF4703619713E3F18D8A9D5D88D6288_45E3C223BCF135987E4038FB6B0DBA13 | binary | |
MD5:48592D3BB4C19E3F838368753DE24EE5 | SHA256:5DD761BCCC731DF222DC09D12CEB081D9F2844864E38C6D95D7FE0E899F9B2ED | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D421D8E11DE61D51F62696E8523817BC_035C24D4E04567272E6B557C7EB5C2B7 | binary | |
MD5:8701317C1BFC7DDD2A08810CC6A3E4D3 | SHA256:4770F4109F29F871DE8CA9342DA1BE8444C9B96FE979F4A79C257BC34A0A6122 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\adtech[1].jpeg | image | |
MD5:4575C419AD79419C5BB3D9A8CA16CD17 | SHA256:6F4B257256F863F2DEE9FFDAA42F67AE39923A6B8155319505986C0AA3028C48 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:12B7A2DE814954F656E7CE95F247559B | SHA256:E0B8CC9AC2DBA235340D4759C34F713D3809B8C589B0F62D8230CE2AEE5BA0A8 | |||
| 3996 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\77EC63BDA74BD0D0E0426DC8F8008506 | binary | |
MD5:2B23E7C9AD0F4F140700BD82996F7EB2 | SHA256:0B9B6B6680A43FD94168B042E9BA01914480B63FA434167998D57F039CC88C84 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
68
DNS requests
23
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3996 | iexplore.exe | GET | 200 | 8.241.9.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?ab6c62e3d2bbc5b0 | US | compressed | 4.66 Kb | unknown |
3996 | iexplore.exe | GET | 200 | 172.217.17.131:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEEVPiCzvQdHKEiO6fm6h1os%3D | US | binary | 471 b | unknown |
3996 | iexplore.exe | GET | 200 | 8.241.9.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?5a9de4fb6882b969 | US | compressed | 61.6 Kb | unknown |
3996 | iexplore.exe | GET | — | 172.217.17.131:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIAjrICMzZli2TN25s%3D | US | — | — | unknown |
3996 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | US | binary | 471 b | unknown |
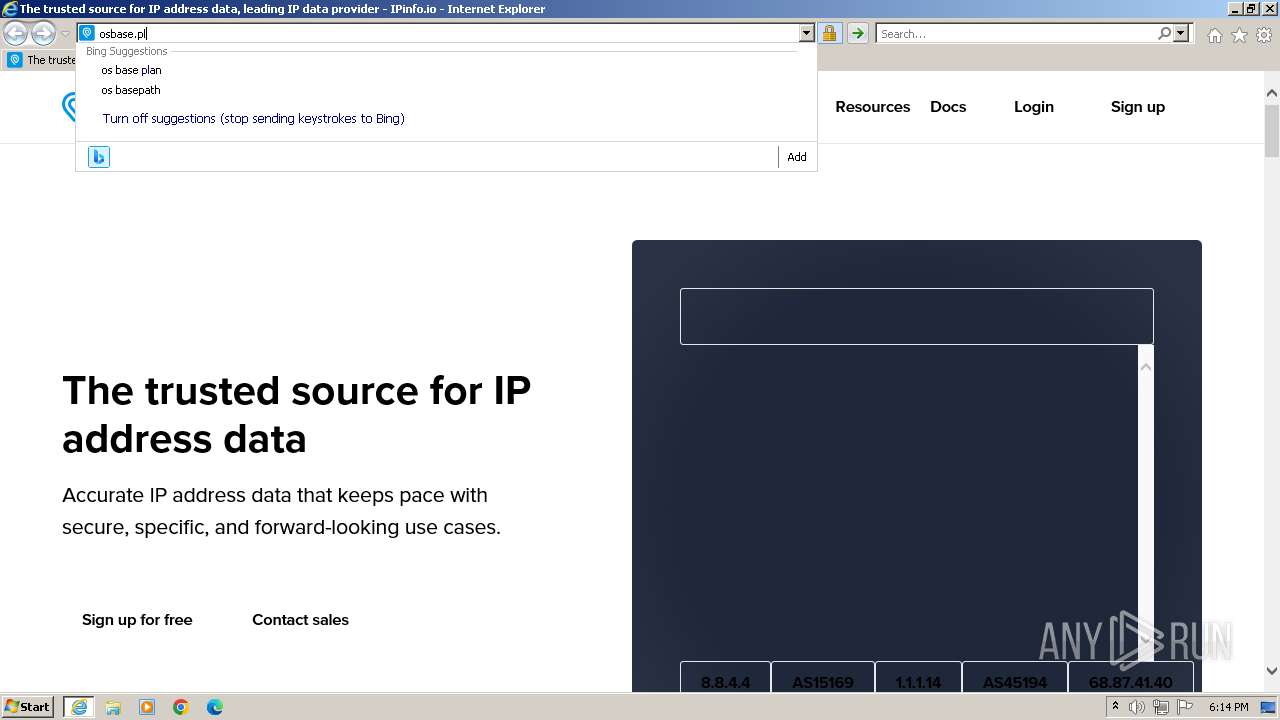
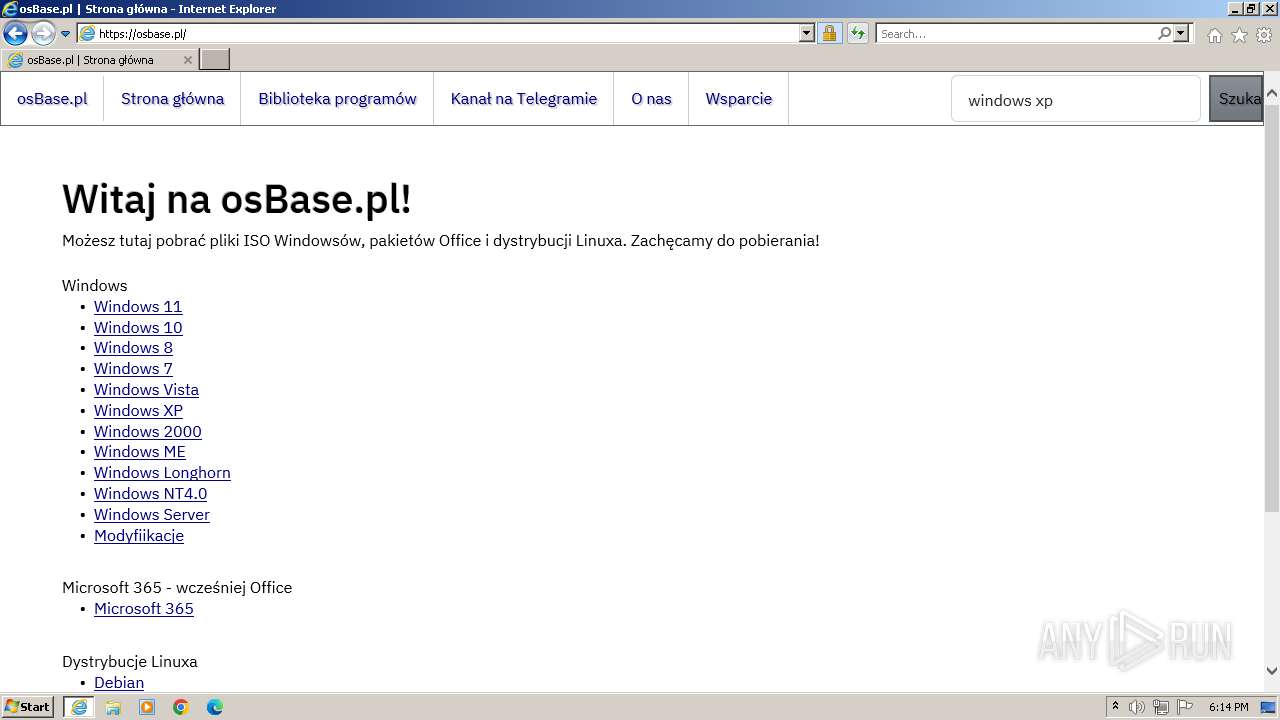
3996 | iexplore.exe | GET | 301 | 128.204.216.218:80 | http://osbase.pl/ | PL | html | 226 b | unknown |
3996 | iexplore.exe | GET | 200 | 23.32.238.27:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgSqaOCCrzeKr5FTM7O0jBoZtQ%3D%3D | DE | binary | 503 b | unknown |
3996 | iexplore.exe | GET | 200 | 8.241.9.126:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?060020e49c501eb3 | US | compressed | 4.66 Kb | unknown |
3996 | iexplore.exe | GET | 200 | 172.217.17.131:80 | http://ocsp.pki.goog/s/gts1d4/1N87hZBLcIw/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSMBFDqU0NJQdZdEGU3bkhj0FoRrQQUJeIYDrJXkZQq5dRdhpCD3lOzuJICEDFE1LJpADOnELhOSDtXEsU%3D | US | binary | 471 b | unknown |
3996 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | US | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3996 | iexplore.exe | 34.117.59.81:443 | — | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
3996 | iexplore.exe | 8.241.9.126:80 | ctldl.windowsupdate.com | LEVEL3 | US | unknown |
3996 | iexplore.exe | 23.206.95.234:80 | x1.c.lencr.org | AKAMAI-AS | NL | unknown |
3996 | iexplore.exe | 23.32.238.27:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
3996 | iexplore.exe | 34.160.152.12:443 | website-cdn.ipinfo.io | GOOGLE | US | unknown |
3996 | iexplore.exe | 104.18.41.69:443 | www.getapp.com | CLOUDFLARENET | — | shared |
3996 | iexplore.exe | 18.245.60.42:443 | assets.capterra.com | — | US | unknown |
3996 | iexplore.exe | 104.17.151.248:443 | www.g2.com | CLOUDFLARENET | — | unknown |
3996 | iexplore.exe | 172.217.17.131:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
3996 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
website-cdn.ipinfo.io |
| unknown |
www.getapp.com |
| unknown |
assets.capterra.com |
| shared |
www.g2.com |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
p.typekit.net |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3996 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
3996 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
3996 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
3996 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
3996 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
3996 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
3996 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
3996 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup Domain Observed in SNI (ipinfo. io) |
3996 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |
3996 | iexplore.exe | Device Retrieving External IP Address Detected | ET POLICY Possible External IP Lookup SSL Cert Observed (ipinfo.io) |