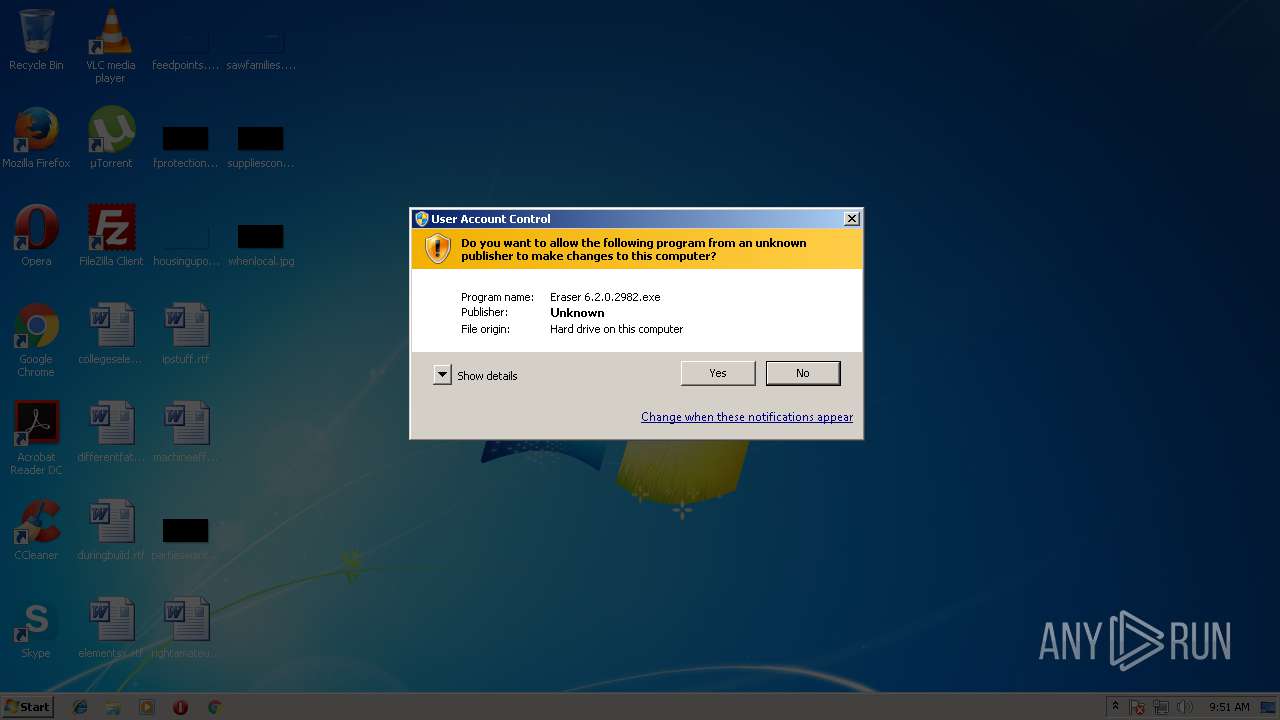
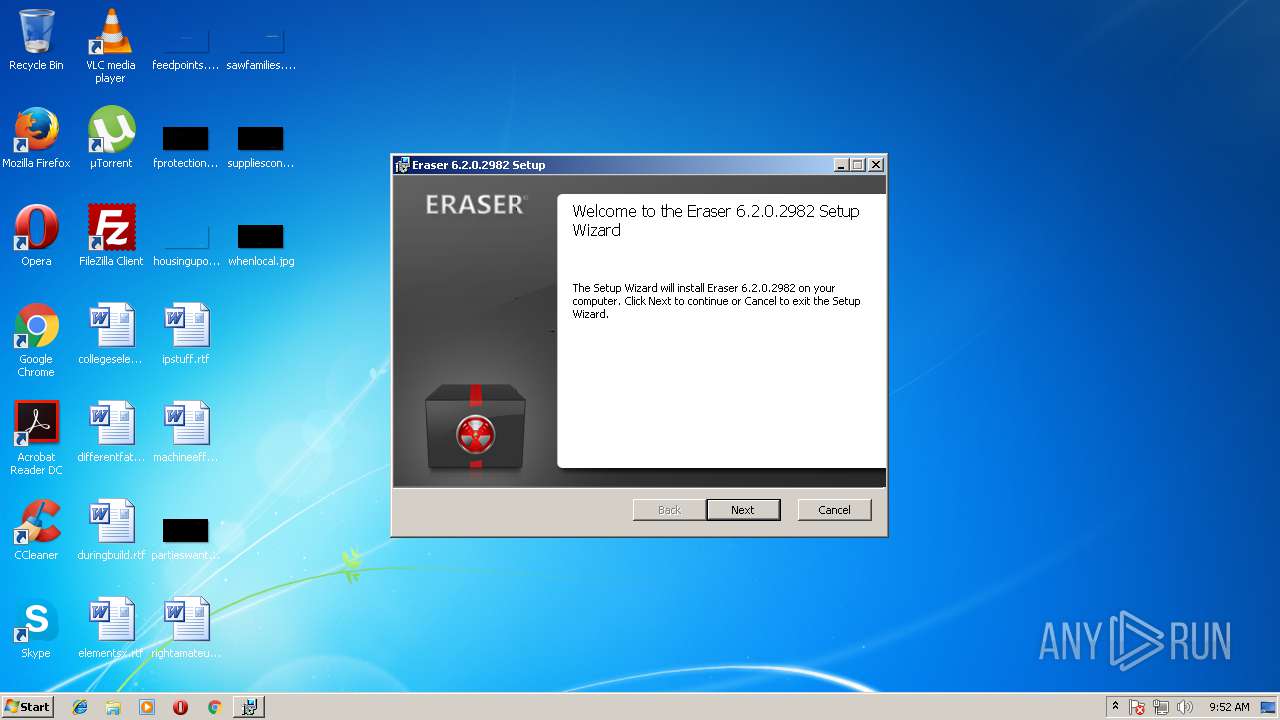
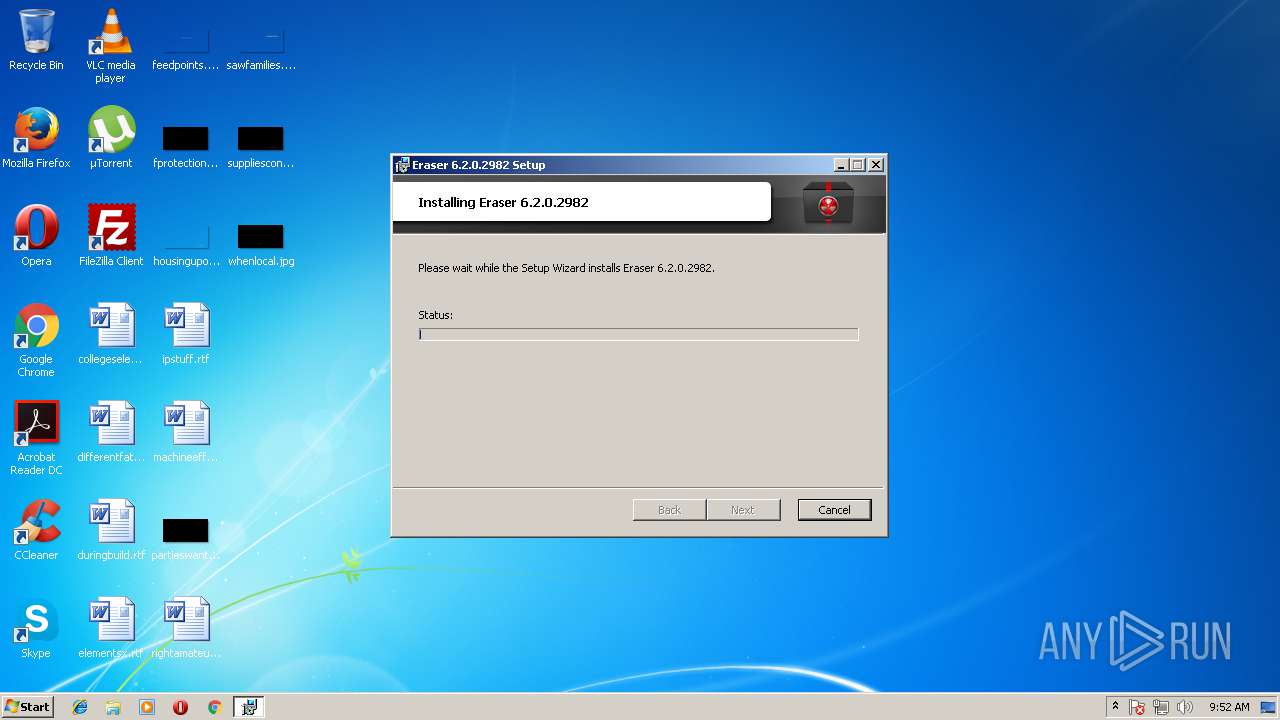
| File name: | Eraser 6.2.0.2982.exe |
| Full analysis: | https://app.any.run/tasks/36b9989c-1a6c-460f-bf3d-cbb99b1da879 |
| Verdict: | Suspicious activity |
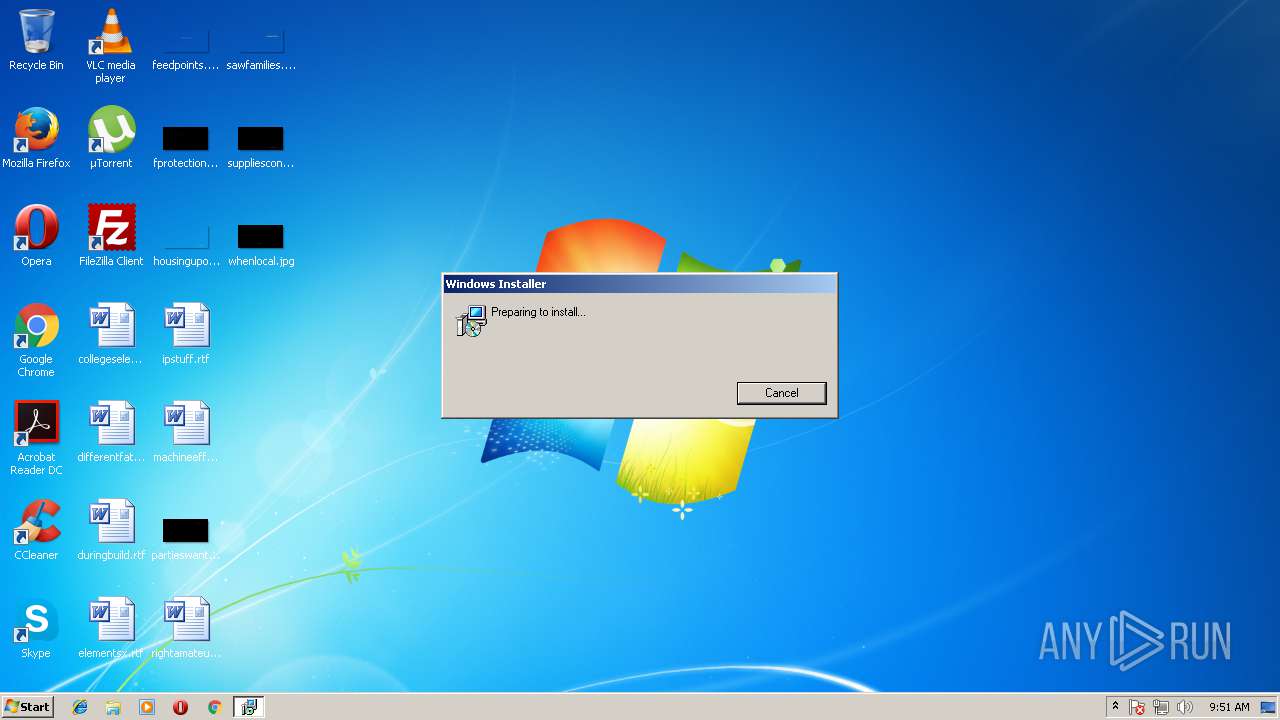
| Analysis date: | April 06, 2018, 08:51:01 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 9D9AF893CEDF69CF828B5350A15DB824 |
| SHA1: | 3481733B608B9C0A2827BA215CB9EDEB5F06272C |
| SHA256: | 6F7B1DF4C8B3CB176F5B9910736355F8FC9401ED8DE635B0DB20CC0A6D2076DC |
| SSDEEP: | 196608:JjTsTA1DZoDz0UTvpFEwVkbQOtnSiwuRzwO2WtNQMSMK9:F5OsupFEwKftnSiZzw92Z+9 |
MALICIOUS
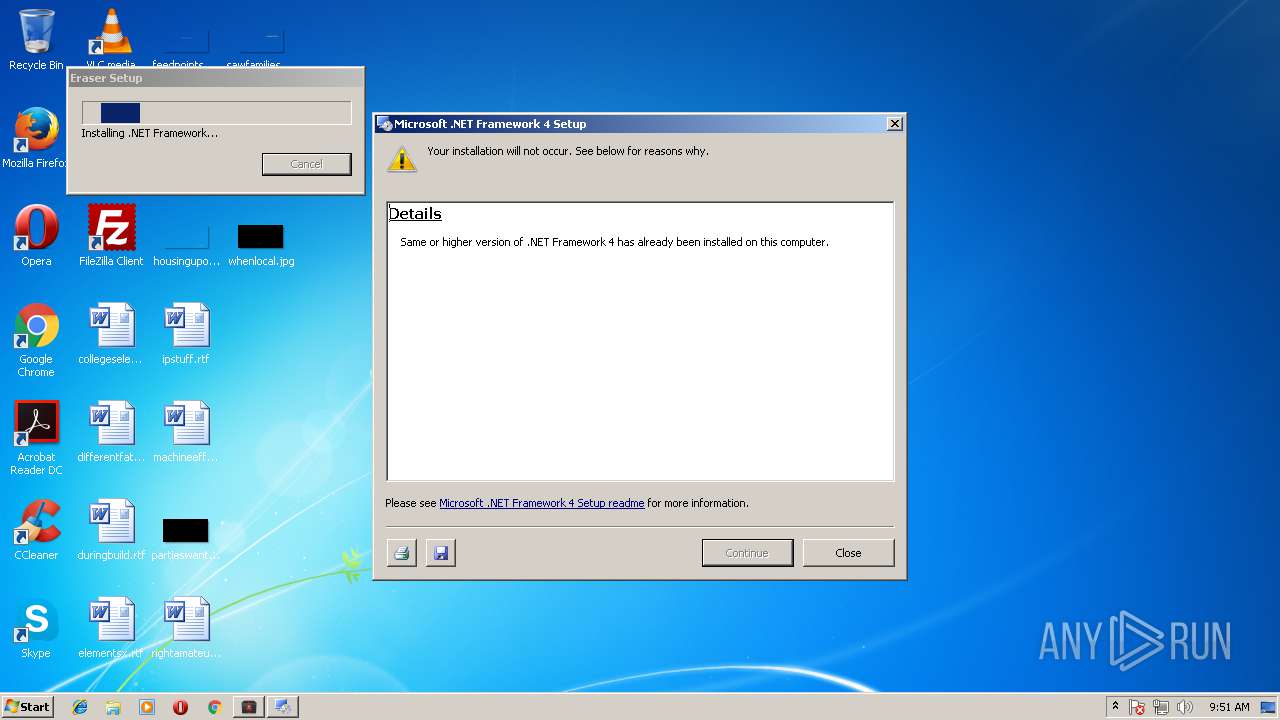
Application was dropped or rewritten from another process
- dotNetFx40_Full_setup.exe (PID: 124)
- Setup.exe (PID: 2844)
Application loaded dropped or rewritten executable
- Setup.exe (PID: 2844)
Changes settings of System certificates
- msiexec.exe (PID: 3228)
SUSPICIOUS
Adds / modifies Windows certificates
- msiexec.exe (PID: 3228)
INFO
Dropped object may contain URL's
- Setup.exe (PID: 2844)
- Eraser 6.2.0.2982.exe (PID: 2996)
- msiexec.exe (PID: 3228)
- dotNetFx40_Full_setup.exe (PID: 124)
Loads rich edit control libraries
- Setup.exe (PID: 2844)
- msiexec.exe (PID: 3228)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2628)
Creates or modifies windows services
- vssvc.exe (PID: 2628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:04 00:19:01+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 140288 |
| InitializedDataSize: | 8953856 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xfc96 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.2.0.2982 |
| ProductVersionNumber: | 6.2.0.2982 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | Eraser Setup Bootstrapper |
| CompanyName: | The Eraser Project |
| FileDescription: | Eraser Setup Bootstrapper |
| FileVersion: | 6.2.0.2982 |
| InternalName: | Eraser Setup Bootstrapper |
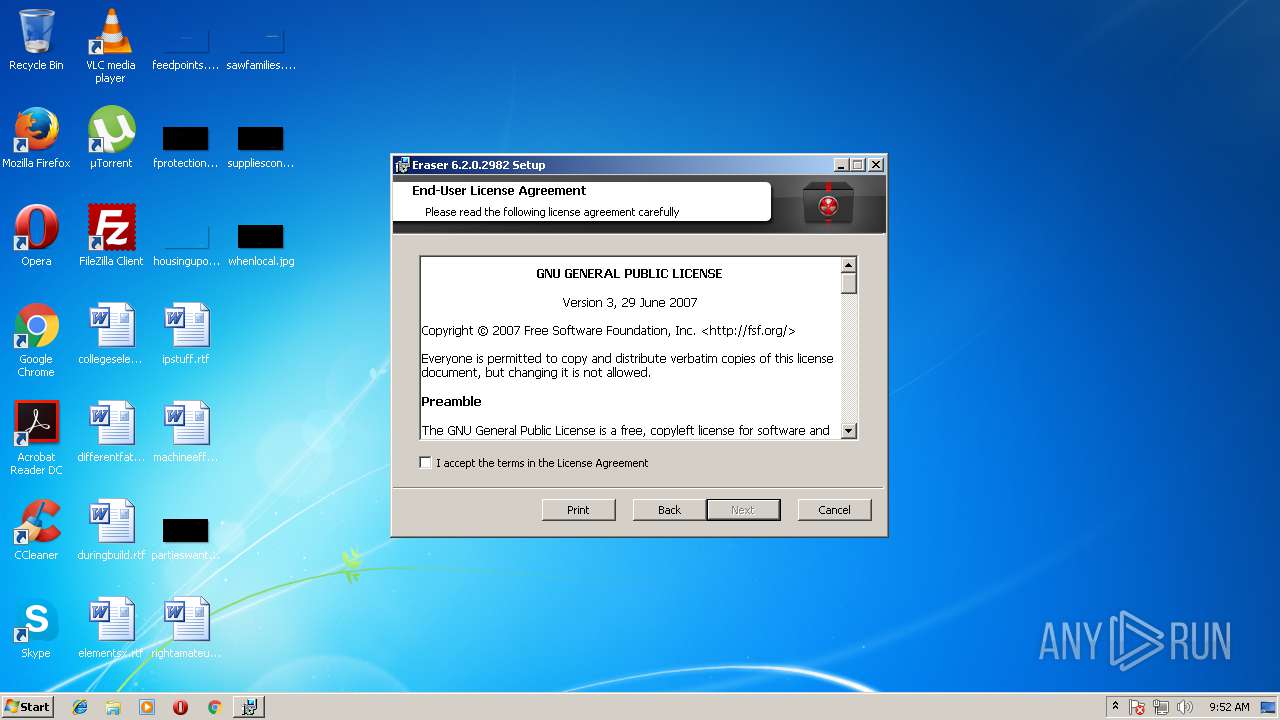
| LegalCopyright: | Copyright © 2008-2015 The Eraser Project |
| OriginalFileName: | Eraser Setup Bootstrapper |
| ProductVersion: | 6.2.0.2982 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 03-Jan-2018 23:19:01 |
| Detected languages: |
|
| Comments: | Eraser Setup Bootstrapper |
| CompanyName: | The Eraser Project |
| FileDescription: | Eraser Setup Bootstrapper |
| FileVersion: | 6.2.0.2982 |
| InternalName: | Eraser Setup Bootstrapper |
| LegalCopyright: | Copyright © 2008-2015 The Eraser Project |
| OriginalFilename: | Eraser Setup Bootstrapper |
| ProductVersion: | 6.2.0.2982 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 03-Jan-2018 23:19:01 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000222AB | 0x00022400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.62167 |
.rdata | 0x00024000 | 0x0000D75C | 0x0000D800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.39974 |
.data | 0x00032000 | 0x00003B60 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.24428 |
.gfids | 0x00036000 | 0x000001CC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.46809 |
.tls | 0x00037000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
.rsrc | 0x00038000 | 0x008793CC | 0x00879400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99981 |
.reloc | 0x008B2000 | 0x0000203C | 0x00002200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.45197 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11909 | 608 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.4813 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.28449 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 7.97982 | 34269 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.13976 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.09265 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.11893 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
100 | 2.71858 | 104 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
101 | 7.99998 | 8826289 | Latin 1 / Western European | Process Default Language | RT_RCDATA |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
Total processes
43
Monitored processes
6
Malicious processes
0
Suspicious processes
4
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 124 | "C:\Users\admin\AppData\Local\Temp\eraserInstallBootstrapper\dotNetFx40_Full_setup.exe" /norestart | C:\Users\admin\AppData\Local\Temp\eraserInstallBootstrapper\dotNetFx40_Full_setup.exe | Eraser 6.2.0.2982.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4 Setup Exit code: 0 Version: 4.0.30319.01 Modules
| |||||||||||||||
| 2628 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2844 | C:\5a3dc90043c0f212db6372\\Setup.exe /norestart /x86 /x64 /ia64 /web | C:\5a3dc90043c0f212db6372\Setup.exe | dotNetFx40_Full_setup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 10.0.30319.1 built by: RTMRel Modules
| |||||||||||||||
| 2996 | "C:\Users\admin\AppData\Local\Temp\Eraser 6.2.0.2982.exe" | C:\Users\admin\AppData\Local\Temp\Eraser 6.2.0.2982.exe | explorer.exe | ||||||||||||
User: admin Company: The Eraser Project Integrity Level: HIGH Description: Eraser Setup Bootstrapper Exit code: 0 Version: 6.2.0.2982 Modules
| |||||||||||||||
| 3228 | msiexec.exe /i "C:\Users\admin\AppData\Local\Temp\eraserInstallBootstrapper\Eraser (x86).msi" | C:\Windows\system32\msiexec.exe | — | Eraser 6.2.0.2982.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3440 | "C:\Users\admin\AppData\Local\Temp\Eraser 6.2.0.2982.exe" | C:\Users\admin\AppData\Local\Temp\Eraser 6.2.0.2982.exe | — | explorer.exe | |||||||||||
User: admin Company: The Eraser Project Integrity Level: MEDIUM Description: Eraser Setup Bootstrapper Exit code: 3221226540 Version: 6.2.0.2982 Modules
| |||||||||||||||
Total events
226
Read events
198
Write events
28
Delete events
0
Modification events
| (PID) Process: | (3228) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\92\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3228) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\92\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
| (PID) Process: | (3228) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\92\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\qagentrt.dll,-10 |
Value: System Health Authentication | |||
| (PID) Process: | (3228) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\92\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dnsapi.dll,-103 |
Value: Domain Name System (DNS) Server Trust | |||
| (PID) Process: | (3228) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\92\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-843 |
Value: BitLocker Drive Encryption | |||
| (PID) Process: | (3228) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\92\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\fveui.dll,-844 |
Value: BitLocker Data Recovery Agent | |||
| (PID) Process: | (3228) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\92\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\WindowsPowerShell\v1.0\powershell.exe,-124 |
Value: Document Encryption | |||
| (PID) Process: | (3228) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D69B561148F01C77C54578C10926DF5B856976AD |
| Operation: | write | Name: | Blob |
Value: 0F00000001000000200000005229BA15B31B0C6F4CCA89C2985177974327D1B689A3B935A0BD975532AF22AB090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030306082B0601050507030406082B06010505070308060A2B0601040182370A030406082B0601050507030606082B060105050703070B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D0020005200330000005300000001000000230000003021301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0620000000100000020000000CBB522D7B7F127AD6A0113865BDF1CD4102E7D0759AF635A7CF4720DC963C53B1400000001000000140000008FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC1D000000010000001000000001728E1ECF7A9D86FB3CEC8948ABA953030000000100000014000000D69B561148F01C77C54578C10926DF5B856976AD2000000001000000630300003082035F30820247A003020102020B04000000000121585308A2300D06092A864886F70D01010B0500304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3039303331383130303030305A170D3239303331383130303030305A304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E30820122300D06092A864886F70D01010105000382010F003082010A0282010100CC2576907906782216F5C083B684CA289EFD057611C5AD8872FC460243C7B28A9D045F24CB2E4BE1608246E152AB0C8147706CDD64D1EBF52CA30F823D0C2BAE97D7B614861079BB3B1380778C08E149D26A622F1F5EFA9668DF892795389F06D73EC9CB26590D73DEB0C8E9260E8315C6EF5B8BD20460CA49A628F6693BF6CBC82891E59D8A615737AC7414DC74E03AEE722F2E9CFBD0BBBFF53D00E10633E8822BAE53A63A16738CDD410E203AC0B4A7A1E9B24F902E3260E957CBB904926868E538266075B29F77FF9114EFAE2049FCAD401548D1023161195EB897EFAD77B7649A7ABF5FC113EF9B62FB0D6CE0546916A903DA6EE983937176C6698582170203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604148FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC300D06092A864886F70D01010B050003820101004B40DBC050AAFEC80CEFF796544549BB96000941ACB3138686280733CA6BE674B9BA002DAEA40AD3F5F1F10F8ABF73674A83C7447B78E0AF6E6C6F03298E333945C38EE4B9576CAAFC1296EC53C62DE4246CB99463FBDC536867563E83B8CF3521C3C968FECEDAC253AACC908AE9F05D468C95DD7A58281A2F1DDECD0037418FED446DD75328977EF367041E15D78A96B4D3DE4C27A44C1B737376F41799C21F7A0EE32D08AD0A1C2CFF3CAB550E0F917E36EBC35749BEE12E2D7C608BC3415113239DCEF7326B9401A899E72C331F3A3B25D28640CE3B2C8678C9612F14BAEEDB556FDF84EE05094DBD28D872CED36250651EEB92978331D9B3B5CA47583F5F | |||
| (PID) Process: | (3228) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\D69B561148F01C77C54578C10926DF5B856976AD |
| Operation: | write | Name: | Blob |
Value: 190000000100000010000000D0FD3C9C380D7B65E26B9A3FEDD39B8F0F00000001000000200000005229BA15B31B0C6F4CCA89C2985177974327D1B689A3B935A0BD975532AF22AB090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030306082B0601050507030406082B06010505070308060A2B0601040182370A030406082B0601050507030606082B060105050703070B000000010000003000000047006C006F00620061006C005300690067006E00200052006F006F00740020004300410020002D0020005200330000005300000001000000230000003021301F06092B06010401A032010130123010060A2B0601040182373C0101030200C0620000000100000020000000CBB522D7B7F127AD6A0113865BDF1CD4102E7D0759AF635A7CF4720DC963C53B1400000001000000140000008FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC1D000000010000001000000001728E1ECF7A9D86FB3CEC8948ABA953030000000100000014000000D69B561148F01C77C54578C10926DF5B856976AD2000000001000000630300003082035F30820247A003020102020B04000000000121585308A2300D06092A864886F70D01010B0500304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E301E170D3039303331383130303030305A170D3239303331383130303030305A304C3120301E060355040B1317476C6F62616C5369676E20526F6F74204341202D20523331133011060355040A130A476C6F62616C5369676E311330110603550403130A476C6F62616C5369676E30820122300D06092A864886F70D01010105000382010F003082010A0282010100CC2576907906782216F5C083B684CA289EFD057611C5AD8872FC460243C7B28A9D045F24CB2E4BE1608246E152AB0C8147706CDD64D1EBF52CA30F823D0C2BAE97D7B614861079BB3B1380778C08E149D26A622F1F5EFA9668DF892795389F06D73EC9CB26590D73DEB0C8E9260E8315C6EF5B8BD20460CA49A628F6693BF6CBC82891E59D8A615737AC7414DC74E03AEE722F2E9CFBD0BBBFF53D00E10633E8822BAE53A63A16738CDD410E203AC0B4A7A1E9B24F902E3260E957CBB904926868E538266075B29F77FF9114EFAE2049FCAD401548D1023161195EB897EFAD77B7649A7ABF5FC113EF9B62FB0D6CE0546916A903DA6EE983937176C6698582170203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604148FF04B7FA82E4524AE4D50FA639A8BDEE2DD1BBC300D06092A864886F70D01010B050003820101004B40DBC050AAFEC80CEFF796544549BB96000941ACB3138686280733CA6BE674B9BA002DAEA40AD3F5F1F10F8ABF73674A83C7447B78E0AF6E6C6F03298E333945C38EE4B9576CAAFC1296EC53C62DE4246CB99463FBDC536867563E83B8CF3521C3C968FECEDAC253AACC908AE9F05D468C95DD7A58281A2F1DDECD0037418FED446DD75328977EF367041E15D78A96B4D3DE4C27A44C1B737376F41799C21F7A0EE32D08AD0A1C2CFF3CAB550E0F917E36EBC35749BEE12E2D7C608BC3415113239DCEF7326B9401A899E72C331F3A3B25D28640CE3B2C8678C9612F14BAEEDB556FDF84EE05094DBD28D872CED36250651EEB92978331D9B3B5CA47583F5F | |||
| (PID) Process: | (2628) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007035199084CDD301440A0000840D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
31
Suspicious files
9
Text files
81
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2996 | Eraser 6.2.0.2982.exe | C:\Users\admin\AppData\Local\Temp\eraserInstallBootstrapper\Eraser (x64).msi | — | |
MD5:— | SHA256:— | |||
| 2996 | Eraser 6.2.0.2982.exe | C:\Users\admin\AppData\Local\Temp\eraserInstallBootstrapper\Eraser (x86).msi | — | |
MD5:— | SHA256:— | |||
| 124 | dotNetFx40_Full_setup.exe | C:\5a3dc90043c0f212db6372\header.bmp | image | |
MD5:514BFCD8DA66722A9639EB41ED3988B7 | SHA256:6B8201ED10CE18FFADE072B77C6D1FCACCF1D29ACB47D86F553D9BEEBD991290 | |||
| 124 | dotNetFx40_Full_setup.exe | C:\5a3dc90043c0f212db6372\Graphics\Print.ico | image | |
MD5:7E55DDC6D611176E697D01C90A1212CF | SHA256:FF542E32330B123486797B410621E19EAFB39DF3997E14701AFA4C22096520ED | |||
| 124 | dotNetFx40_Full_setup.exe | C:\5a3dc90043c0f212db6372\Graphics\Rotate4.ico | image | |
MD5:BB55B5086A9DA3097FB216C065D15709 | SHA256:8D82FF7970C9A67DA8134686560FE3A6C986A160CED9D1CC1392F2BA75C698AB | |||
| 124 | dotNetFx40_Full_setup.exe | C:\5a3dc90043c0f212db6372\Graphics\Rotate2.ico | image | |
MD5:8419CAA81F2377E09B7F2F6218E505AE | SHA256:DB89D8A45C369303C04988322B2774D2C7888DA5250B4DAB2846DEEF58A7DE22 | |||
| 124 | dotNetFx40_Full_setup.exe | C:\5a3dc90043c0f212db6372\SplashScreen.bmp | image | |
MD5:0966FCD5A4AB0DDF71F46C01EFF3CDD5 | SHA256:31C13ECFC0EB27F34036FB65CC0E735CD444EEC75376EEA2642F926AC162DCB3 | |||
| 124 | dotNetFx40_Full_setup.exe | C:\5a3dc90043c0f212db6372\DisplayIcon.ico | image | |
MD5:F9657D290048E169FFABBBB9C7412BE0 | SHA256:B74AD253B9B8F9FCADE725336509143828EE739CC2B24782BE3ECFF26F229160 | |||
| 124 | dotNetFx40_Full_setup.exe | C:\5a3dc90043c0f212db6372\watermark.bmp | image | |
MD5:B0075CEE80173D764C0237E840BA5879 | SHA256:AB18374B3AAB10E5979E080D0410579F9771DB888BA1B80A5D81BA8896E2D33A | |||
| 124 | dotNetFx40_Full_setup.exe | C:\5a3dc90043c0f212db6372\Graphics\Rotate1.ico | image | |
MD5:26A00597735C5F504CF8B3E7E9A7A4C1 | SHA256:37026C4EA2182D7908B3CF0CEF8A6F72BDDCA5F1CFBC702F35B569AD689CF0AF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
3
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 67.26.115.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 52.7 Kb | whitelisted |
— | — | GET | 200 | 104.31.75.124:80 | http://ocsp2.globalsign.com/rootr3/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDkgbagcm0ug%2FJgLUglrN | US | der | 1.47 Kb | whitelisted |
— | — | GET | 200 | 104.31.75.124:80 | http://ocsp2.globalsign.com/gscodesignsha2g3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRKkjBge%2BJXnExRoXTQ63uIpEYZkgQUDzrnrJSRdC2WAnODrZwuST8ZqlQCDGlrRF8ZgKOOGxCS1Q%3D%3D | US | der | 1.51 Kb | whitelisted |
— | — | GET | 200 | 67.26.115.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/D69B561148F01C77C54578C10926DF5B856976AD.crt | US | der | 867 b | whitelisted |
— | — | GET | 200 | 23.111.11.204:80 | http://repository.certum.pl/ctnca.cer | US | der | 959 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 67.26.115.254:80 | www.download.windowsupdate.com | Level 3 Communications, Inc. | US | unknown |
— | — | 104.31.75.124:80 | ocsp2.globalsign.com | Cloudflare Inc | US | shared |
— | — | 23.111.11.204:80 | repository.certum.pl | netDNA | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.download.windowsupdate.com |
| whitelisted |
ocsp2.globalsign.com |
| whitelisted |
repository.certum.pl |
| whitelisted |
Threats
Process | Message |
|---|---|
Setup.exe | The operation completed successfully.
|