| File name: | Winrar.exe |
| Full analysis: | https://app.any.run/tasks/214cb852-e095-4233-92b3-8598d84c7f24 |
| Verdict: | Malicious activity |
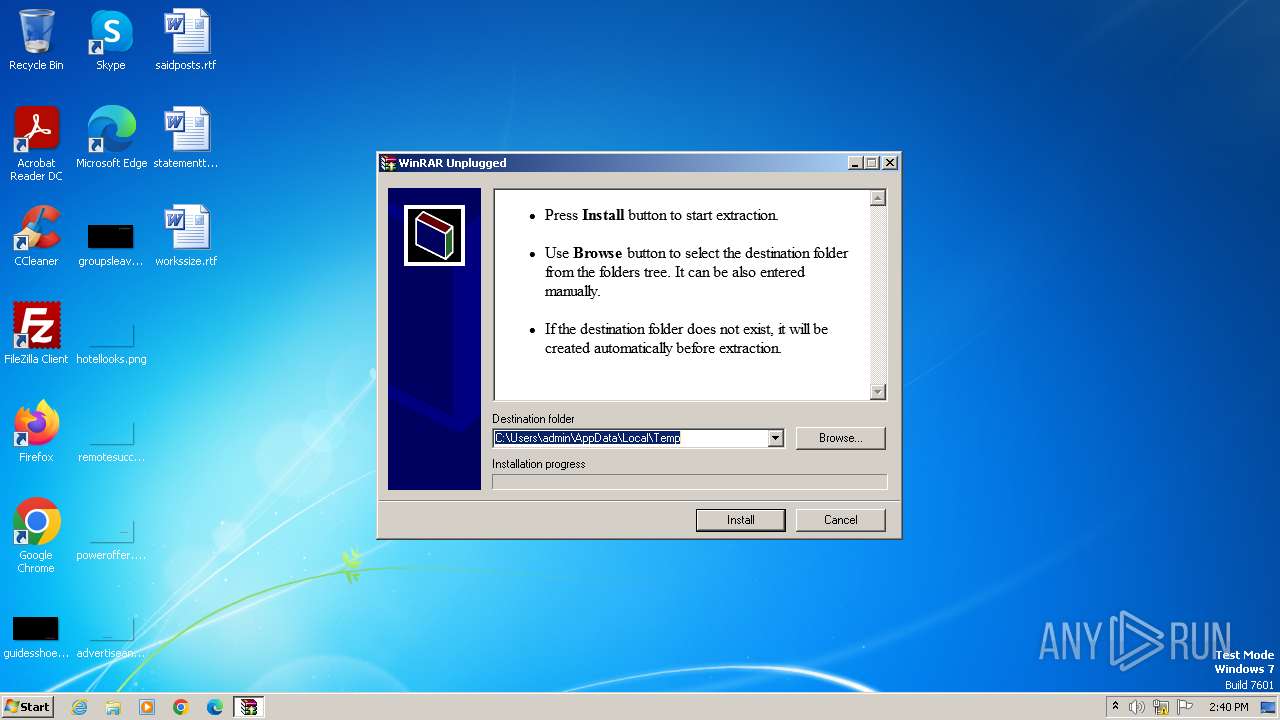
| Analysis date: | November 23, 2023, 14:40:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B08B6219961CAAC74B033C88233C67F6 |
| SHA1: | F4D8C562F51537B57B7C25FF552C736C383C2D60 |
| SHA256: | 6F74480D7DC6A91F5B77909ACFD1108EBB039B0EE1DE3C97B5152034303EB752 |
| SSDEEP: | 98304:IXrk7nG3HA7Z5vowfwbrcn12zr1zb/ux84asQU7z/oh6CuKpU9Z6BljYaY4po96q:p/YV |
MALICIOUS
Drops the executable file immediately after the start
- Winrar.exe (PID: 3428)
SUSPICIOUS
Reads Microsoft Outlook installation path
- Winrar.exe (PID: 3428)
Drops 7-zip archiver for unpacking
- Winrar.exe (PID: 3428)
Reads Internet Explorer settings
- Winrar.exe (PID: 3428)
Connects to unusual port
- Winrar.exe (PID: 3428)
Reads the Internet Settings
- Winrar.exe (PID: 3428)
INFO
Checks supported languages
- Winrar.exe (PID: 3428)
Reads the computer name
- Winrar.exe (PID: 3428)
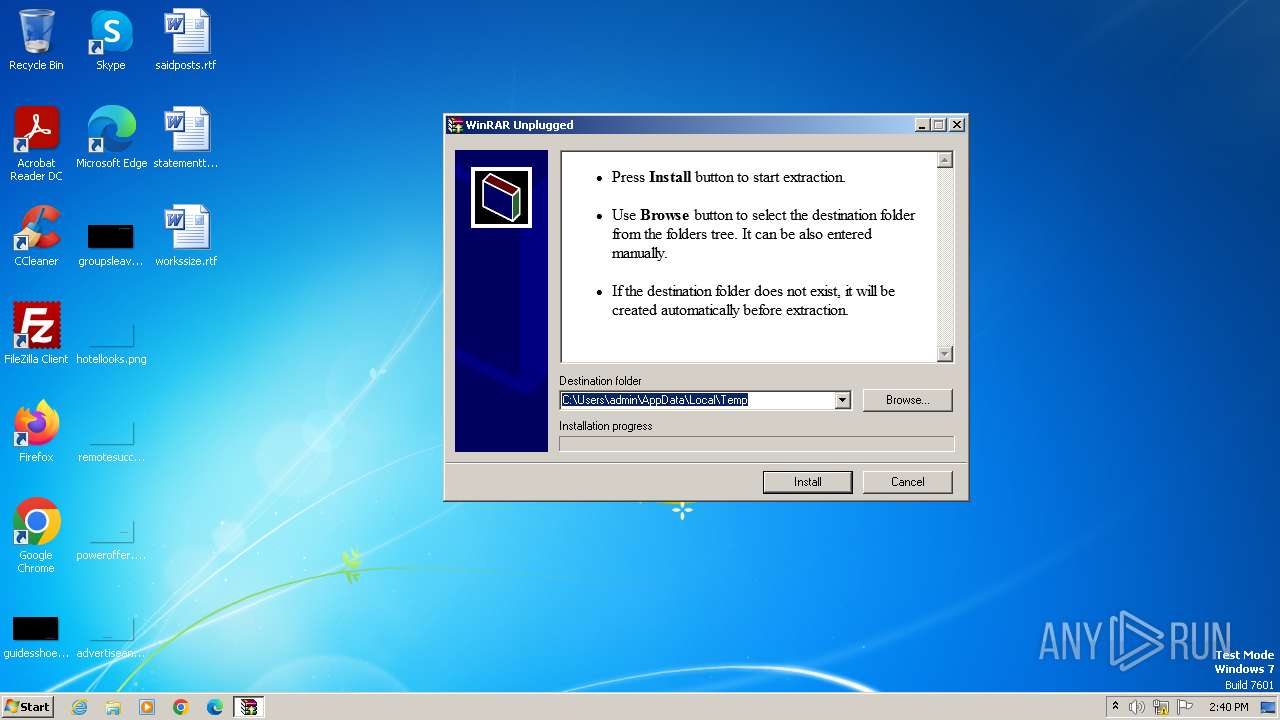
Create files in a temporary directory
- Winrar.exe (PID: 3428)
Checks proxy server information
- Winrar.exe (PID: 3428)
Reads the machine GUID from the registry
- Winrar.exe (PID: 3428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (52.5) |
|---|---|---|
| .scr | | | Windows screen saver (22) |
| .dll | | | Win32 Dynamic Link Library (generic) (11) |
| .exe | | | Win32 Executable (generic) (7.5) |
| .exe | | | Generic Win/DOS Executable (3.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:12 11:11:36+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 67584 |
| InitializedDataSize: | 72704 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7cb |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
34
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3428 | "C:\Users\admin\AppData\Local\Temp\Winrar.exe" | C:\Users\admin\AppData\Local\Temp\Winrar.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
478
Read events
466
Write events
12
Delete events
0
Modification events
| (PID) Process: | (3428) Winrar.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3428) Winrar.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000059010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A8016B000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3428) Winrar.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3428) Winrar.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3428) Winrar.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3428) Winrar.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3428) Winrar.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3428) Winrar.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
25
Suspicious files
2
Text files
24
Unknown types
0
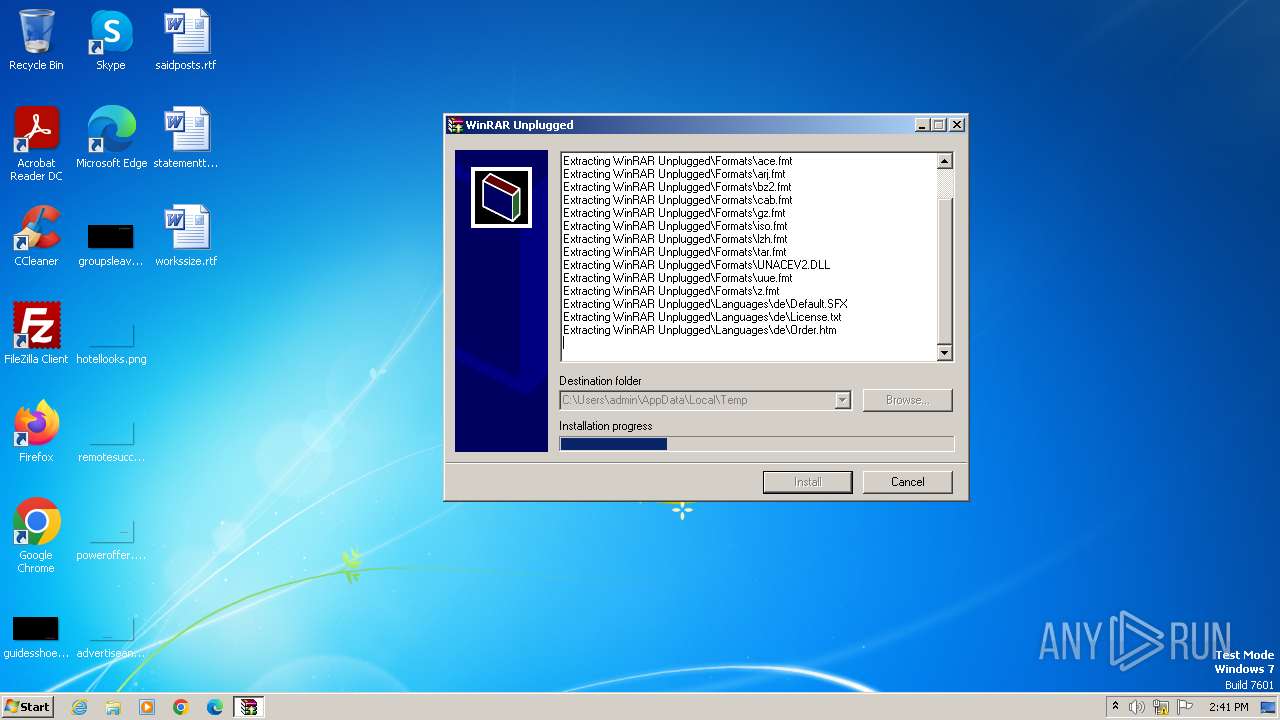
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3428 | Winrar.exe | C:\Users\admin\AppData\Local\Temp\WinRAR Unplugged\Descript.ion | text | |
MD5:B63259E35240A56947AC7D8B9E720EA0 | SHA256:3CAC074E2EDDF5B66D300C7416F6A18B43549453E36A191C31F5D64722F828EF | |||
| 3428 | Winrar.exe | C:\Users\admin\AppData\Local\Temp\WinRAR Unplugged\File_Id.diz | text | |
MD5:7C60099DB3D1D47E1D06EA2265FAD79B | SHA256:291DE4B8B0FE590EC82CBBD8255FC2BFDF41944A235391F41880A23512935188 | |||
| 3428 | Winrar.exe | C:\Users\admin\AppData\Local\Temp\WinRAR Unplugged\Formats\iso.fmt | executable | |
MD5:D6BF07CE6EF4196887A97BE29CD749CF | SHA256:A74C9FA10A7F137D1A66A929E09C2FEE31E508A6F18AF8D174D7A10924E08B61 | |||
| 3428 | Winrar.exe | C:\Users\admin\AppData\Local\Temp\WinRAR Unplugged\Formats\arj.fmt | executable | |
MD5:456603CB634FAA56F0603BA758475246 | SHA256:FAD9D84B1046BA83CC328729F527A2EC0B74CE367690D2324F04E665908429DF | |||
| 3428 | Winrar.exe | C:\Users\admin\AppData\Local\Temp\WinRAR Unplugged\Formats\cab.fmt | executable | |
MD5:B59ABD0918120B43E866B17100D29674 | SHA256:B7A35B47040BE0CB534385AD11975C7A1957366893466C97F6BBE8DEF597C281 | |||
| 3428 | Winrar.exe | C:\Users\admin\AppData\Local\Temp\WinRAR Unplugged\Languages\de\Order.htm | html | |
MD5:7FBA5F36E1592A9176BFD7F02FDFA179 | SHA256:97840C981426AC9785B08984E69D4EFBC79A62A84C2BF9693E68090C086951A4 | |||
| 3428 | Winrar.exe | C:\Users\admin\AppData\Local\Temp\WinRAR Unplugged\Formats\ace.fmt | executable | |
MD5:2D3FA60D3E7579AC9E45EC1DB7F27057 | SHA256:36DAFA540B5FC464638E2A98189B12813783E7567DD7B2D54FF9475251298AD9 | |||
| 3428 | Winrar.exe | C:\Users\admin\AppData\Local\Temp\WinRAR Unplugged\Languages\de\rar.lng | text | |
MD5:C6A697AF25C1747D2F26F30728225DFF | SHA256:803D03DCC4808DA4AC3E0245390987BB54F09B368D49429BA2DFE9CA7AEC6B8A | |||
| 3428 | Winrar.exe | C:\Users\admin\AppData\Local\Temp\WinRAR Unplugged\Formats\bz2.fmt | executable | |
MD5:30DDD664B909AF20AE8CEEA59C8EA60E | SHA256:770099458F9298B8A22C1CA44B9F7E635CA272D74E2387B7D58829632723BE9F | |||
| 3428 | Winrar.exe | C:\Users\admin\AppData\Local\Temp\WinRAR Unplugged\Formats\tar.fmt | executable | |
MD5:692E9335B118351035DEFDC7556B4D55 | SHA256:454BB9BC8BCC4065E0E9E17C2FFAA250E1B3B46D1AA97243A5ECDF31CCFBADF0 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3428 | Winrar.exe | 18.212.64.37:4444 | — | AMAZON-AES | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
868 | svchost.exe | 184.30.20.134:80 | armmf.adobe.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
armmf.adobe.com |
| whitelisted |