| File name: | EShareClient.exe |
| Full analysis: | https://app.any.run/tasks/fb881f93-6c8c-4e96-80fa-237ee422e81c |
| Verdict: | Malicious activity |
| Analysis date: | April 10, 2020, 21:02:12 |
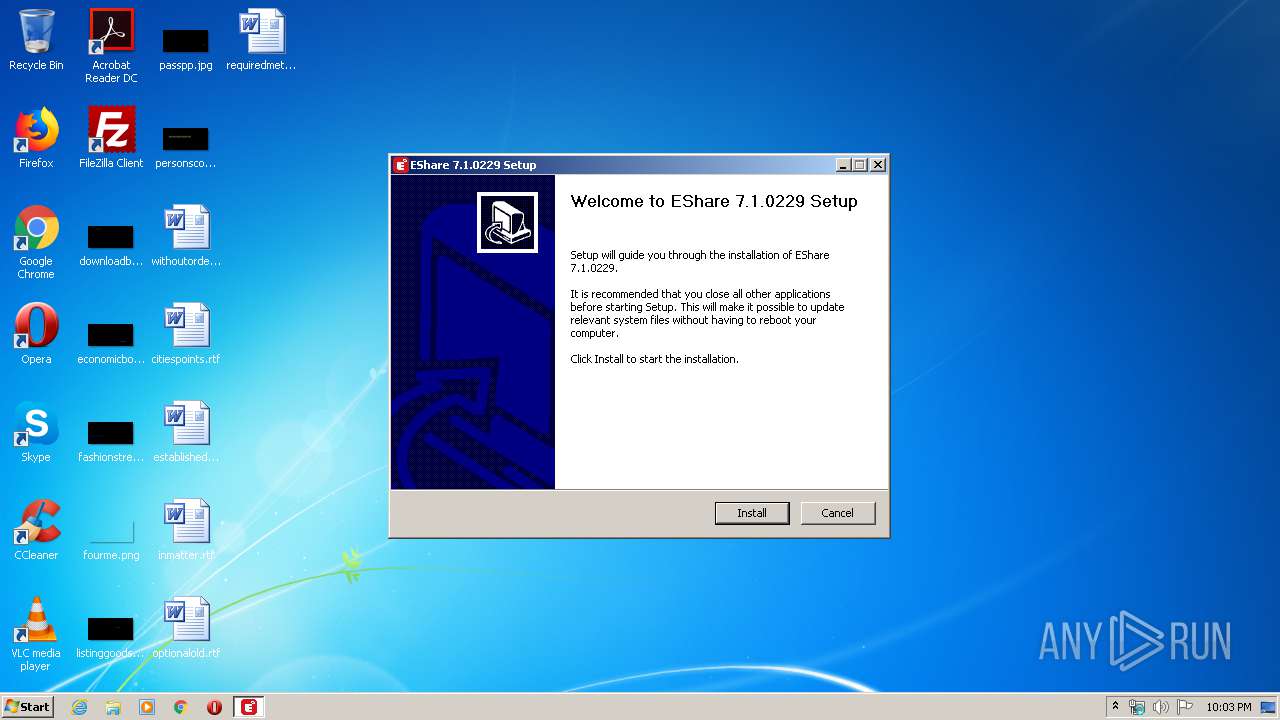
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
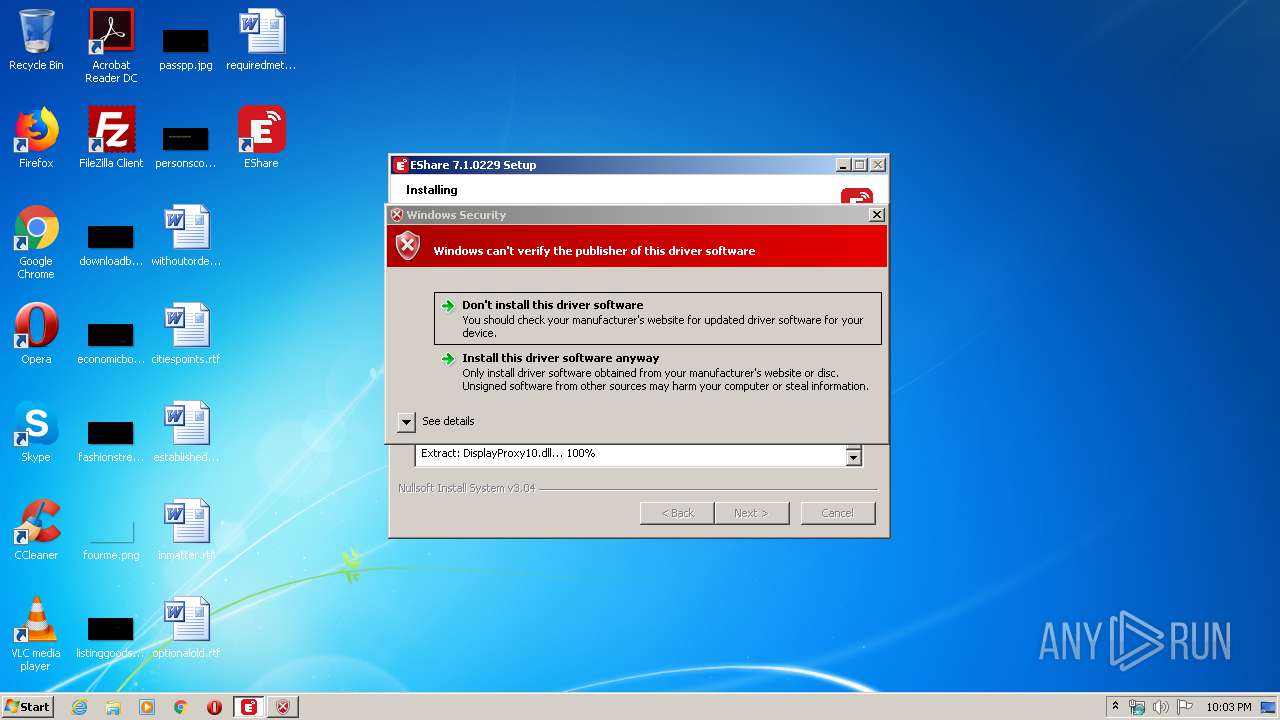
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A7EEB8BB6660F4A59F12ED16BA13CCB7 |
| SHA1: | DAF5871F458A9DB3C693470A8A73A6EA4B6C8609 |
| SHA256: | 6F4FDF8DAA7A504F273B76323FEDB43FBAB82D4AF344F2BEE54C397DA921EB89 |
| SSDEEP: | 393216:tOQTKshDYRBXkZ+2YWMgu87y6WX2jAQSTZC:gEK4YyL97qX2X2ZC |
MALICIOUS
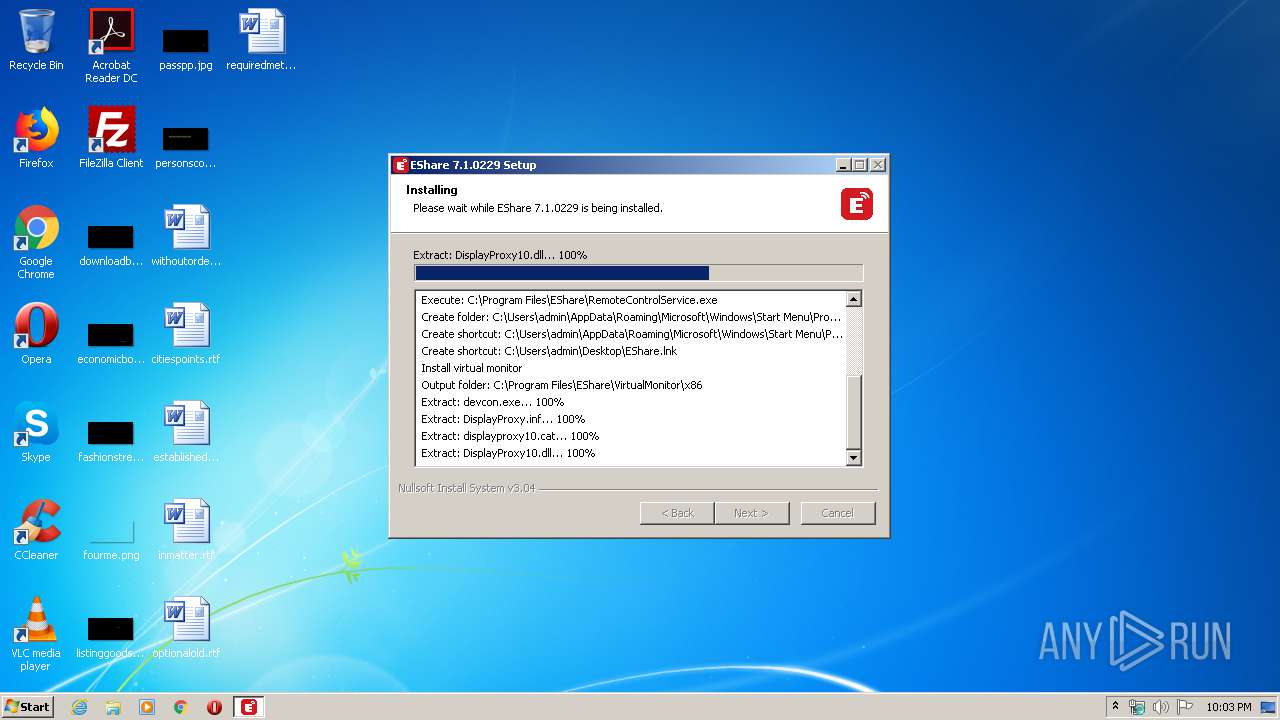
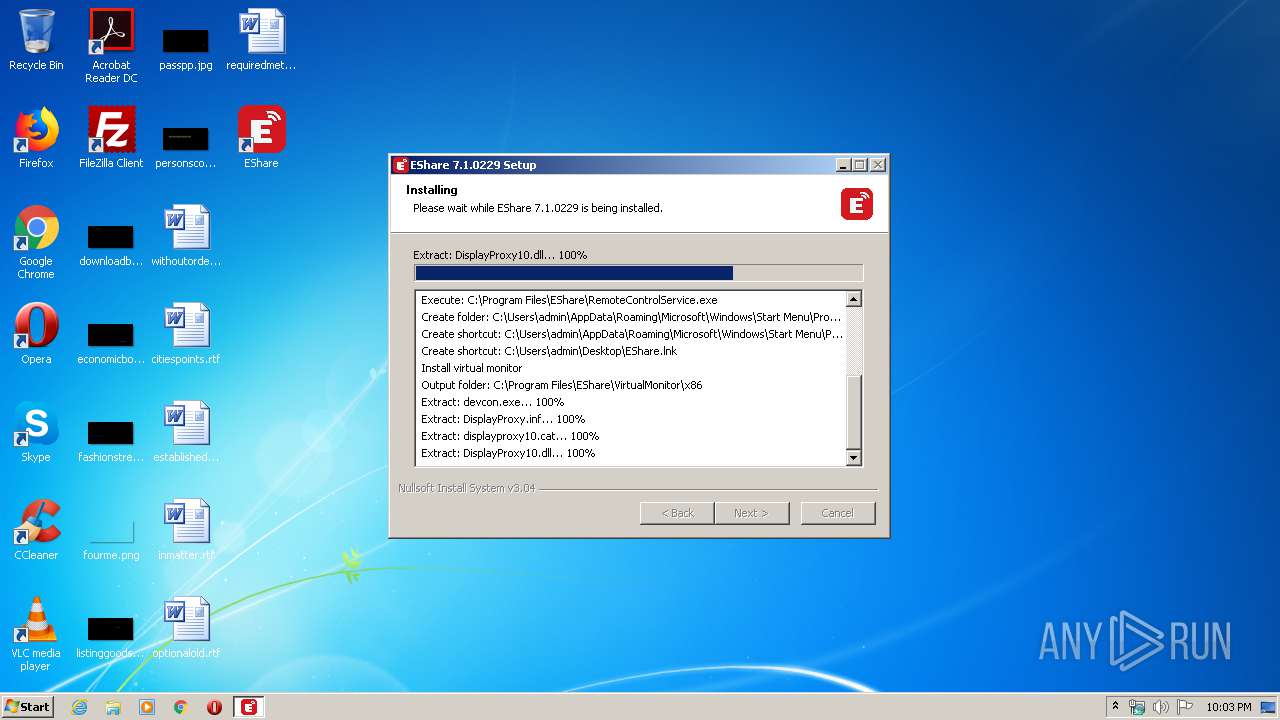
Loads dropped or rewritten executable
- EShareClient.exe (PID: 3232)
- RemoteControlService.exe (PID: 3388)
Application was dropped or rewritten from another process
- RemoteControlService.exe (PID: 3388)
- EDesktop.exe (PID: 608)
- EDesktopUAC.exe (PID: 772)
- ns70E0.tmp (PID: 2716)
- ns7296.tmp (PID: 2800)
- devcon.exe (PID: 2628)
- devcon.exe (PID: 3524)
- ESystemRemoteService.exe (PID: 3884)
SUSPICIOUS
Creates files in the program directory
- EShareClient.exe (PID: 3232)
- RemoteControlService.exe (PID: 3388)
Executable content was dropped or overwritten
- EShareClient.exe (PID: 3232)
- RemoteControlService.exe (PID: 3388)
- devcon.exe (PID: 3524)
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3252)
Executed as Windows Service
- ESystemRemoteService.exe (PID: 3884)
- vssvc.exe (PID: 3984)
Creates a software uninstall entry
- RemoteControlService.exe (PID: 3388)
- EShareClient.exe (PID: 3232)
Creates files in the user directory
- EShareClient.exe (PID: 3232)
Starts application with an unusual extension
- EShareClient.exe (PID: 3232)
Executed via COM
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3252)
Creates files in the driver directory
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3252)
Creates files in the Windows directory
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3252)
Removes files from Windows directory
- DrvInst.exe (PID: 3420)
- DrvInst.exe (PID: 3252)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 3420)
INFO
Reads settings of System Certificates
- devcon.exe (PID: 3524)
- DrvInst.exe (PID: 3252)
Low-level read access rights to disk partition
- vssvc.exe (PID: 3984)
Searches for installed software
- DrvInst.exe (PID: 3420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 23:24:27+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25600 |
| InitializedDataSize: | 141824 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3359 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:24:27 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:24:27 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000062A5 | 0x00006400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.43142 |
.rdata | 0x00008000 | 0x00001396 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.15971 |
.data | 0x0000A000 | 0x00020318 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.90464 |
.ndata | 0x0002B000 | 0x00012000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0003D000 | 0x00011730 | 0x00011800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.58516 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29734 | 1318 | UNKNOWN | English - United States | RT_MANIFEST |
103 | 1.98048 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
205 | 2.68733 | 494 | UNKNOWN | English - United States | RT_DIALOG |
206 | 2.86626 | 228 | UNKNOWN | English - United States | RT_DIALOG |
211 | 2.9304 | 218 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
55
Monitored processes
14
Malicious processes
4
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 608 | "C:/Program Files/ESystemRemoteService/EDesktop.exe" | C:\Program Files\ESystemRemoteService\EDesktop.exe | — | ESystemRemoteService.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 772 | "C:/Program Files/ESystemRemoteService/EDesktopUAC.exe" | C:\Program Files\ESystemRemoteService\EDesktopUAC.exe | — | ESystemRemoteService.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2628 | "C:\Program Files\EShare\VirtualMonitor\x86\devcon.exe" remove hid\vid_1b36&pid_0d11 | C:\Program Files\EShare\VirtualMonitor\x86\devcon.exe | — | ns70E0.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Setup API Exit code: 0 Version: 10.0.14393.0 (rs1_release.160715-1616) Modules
| |||||||||||||||
| 2716 | "C:\Users\admin\AppData\Local\Temp\nsxA0.tmp\ns70E0.tmp" "C:\Program Files\EShare\VirtualMonitor\x86\devcon.exe" remove hid\vid_1b36&pid_0d11 | C:\Users\admin\AppData\Local\Temp\nsxA0.tmp\ns70E0.tmp | — | EShareClient.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2800 | "C:\Users\admin\AppData\Local\Temp\nsxA0.tmp\ns7296.tmp" "C:\Program Files\EShare\VirtualMonitor\x86\devcon.exe" install "C:\Program Files\EShare\VirtualMonitor\x86\DisplayProxy.inf" hid\vid_1b36&pid_0d11 | C:\Users\admin\AppData\Local\Temp\nsxA0.tmp\ns7296.tmp | — | EShareClient.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 1 Modules
| |||||||||||||||
| 3168 | "C:\Users\admin\AppData\Local\Temp\EShareClient.exe" | C:\Users\admin\AppData\Local\Temp\EShareClient.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3232 | "C:\Users\admin\AppData\Local\Temp\EShareClient.exe" | C:\Users\admin\AppData\Local\Temp\EShareClient.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3252 | DrvInst.exe "2" "211" "ROOT\USB\0000" "C:\Windows\INF\oem4.inf" "displayproxy.inf:Standard.NTx86:MyDevice_Install:20.54.41.2:hid\vid_1b36&pid_0d11" "623aa307f" "000003FC" "000005DC" "000005E0" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3388 | "C:\Program Files\EShare\RemoteControlService.exe" | C:\Program Files\EShare\RemoteControlService.exe | EShareClient.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3420 | DrvInst.exe "4" "0" "C:\Users\admin\AppData\Local\Temp\{3848ad65-7b7a-1e8b-8b5b-446a8d201a1f}\displayproxy.inf" "0" "623aa307f" "000003FC" "WinSta0\Default" "000005C8" "208" "c:\program files\eshare\virtualmonitor\x86" | C:\Windows\system32\DrvInst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
686
Read events
492
Write events
194
Delete events
0
Modification events
| (PID) Process: | (3232) EShareClient.exe | Key: | HKEY_CURRENT_USER\Software\EShare |
| Operation: | write | Name: | audio |
Value: true | |||
| (PID) Process: | (3388) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\EDesktop.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\ESystemRemoteService\EDesktop.exe | |||
| (PID) Process: | (3388) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ESystemRemoteService |
| Operation: | write | Name: | DisplayName |
Value: ESystemRemoteService 1.0 | |||
| (PID) Process: | (3388) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ESystemRemoteService |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\ESystemRemoteService\uninst.exe | |||
| (PID) Process: | (3388) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ESystemRemoteService |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\ESystemRemoteService\EDesktop.exe | |||
| (PID) Process: | (3388) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ESystemRemoteService |
| Operation: | write | Name: | DisplayVersion |
Value: 1.0 | |||
| (PID) Process: | (3388) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ESystemRemoteService |
| Operation: | write | Name: | URLInfoAbout |
Value: www.ee-share.com | |||
| (PID) Process: | (3388) RemoteControlService.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\ESystemRemoteService |
| Operation: | write | Name: | Publisher |
Value: EShare | |||
| (PID) Process: | (3524) devcon.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\Setup\SetupapiLogStatus |
| Operation: | write | Name: | setupapi.dev.log |
Value: 4096 | |||
| (PID) Process: | (3524) devcon.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
25
Suspicious files
13
Text files
131
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3232 | EShareClient.exe | C:\Users\admin\AppData\Local\Temp\nsxA0.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3232 | EShareClient.exe | C:\Program Files\EShare\EShare.exe | executable | |
MD5:— | SHA256:— | |||
| 3232 | EShareClient.exe | C:\Program Files\EShare\RemoteControlService.exe | executable | |
MD5:— | SHA256:— | |||
| 3388 | RemoteControlService.exe | C:\Program Files\ESystemRemoteService\uninst.exe | executable | |
MD5:— | SHA256:— | |||
| 3388 | RemoteControlService.exe | C:\Program Files\ESystemRemoteService\ESystemRemoteService.exe | executable | |
MD5:— | SHA256:— | |||
| 3232 | EShareClient.exe | C:\Users\admin\AppData\Local\Temp\nsxA0.tmp\modern-wizard.bmp | image | |
MD5:CBE40FD2B1EC96DAEDC65DA172D90022 | SHA256:3AD2DC318056D0A2024AF1804EA741146CFC18CC404649A44610CBF8B2056CF2 | |||
| 3232 | EShareClient.exe | C:\Program Files\EShare\CrashRpt1402.dll | executable | |
MD5:E141809611224D72AA3AC12C53264D63 | SHA256:A3FB265AB3AC375F81BBBD2E67F8CBBD6DB30511D2A7C4CD511494FA78A53448 | |||
| 3232 | EShareClient.exe | C:\Program Files\EShare\CrashSender1402.exe | executable | |
MD5:870D76914C77619FD05F44BB732BA5F8 | SHA256:CA3CBD2F17F923961FFF0897D8095D4DA9435A2B70FC5C8788820034D618743A | |||
| 3388 | RemoteControlService.exe | C:\Program Files\ESystemRemoteService\EDesktop.exe | executable | |
MD5:FE782D4B47BF92D507B156BBEC62E097 | SHA256:B3CA4777736639A4672460A321E2C8A89A5B7B29BAAFFD96400615F3705B9C4C | |||
| 3232 | EShareClient.exe | C:\Program Files\EShare\VirtualAudioCable.exe | executable | |
MD5:428601614B64551A240494EF3997FFB0 | SHA256:5D12E2D9068F02109E149A9A114B1168F456B175D95E508F8C9511EF673FDEFD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report