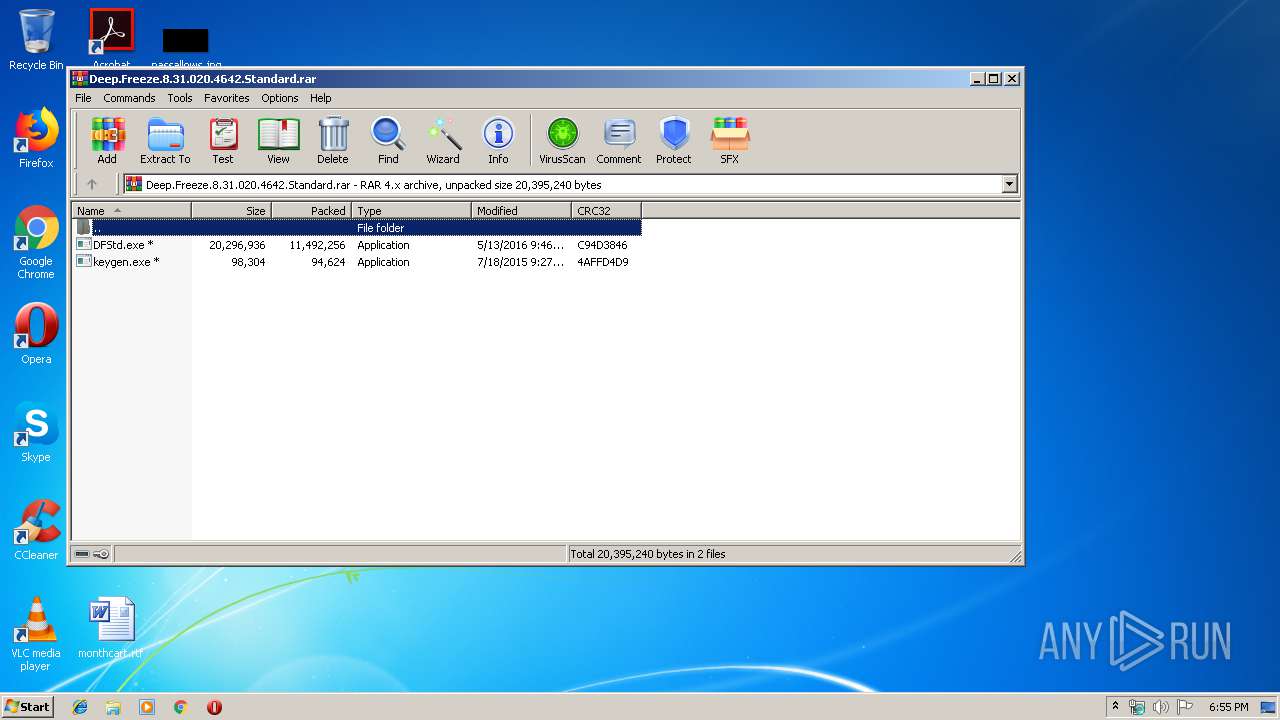
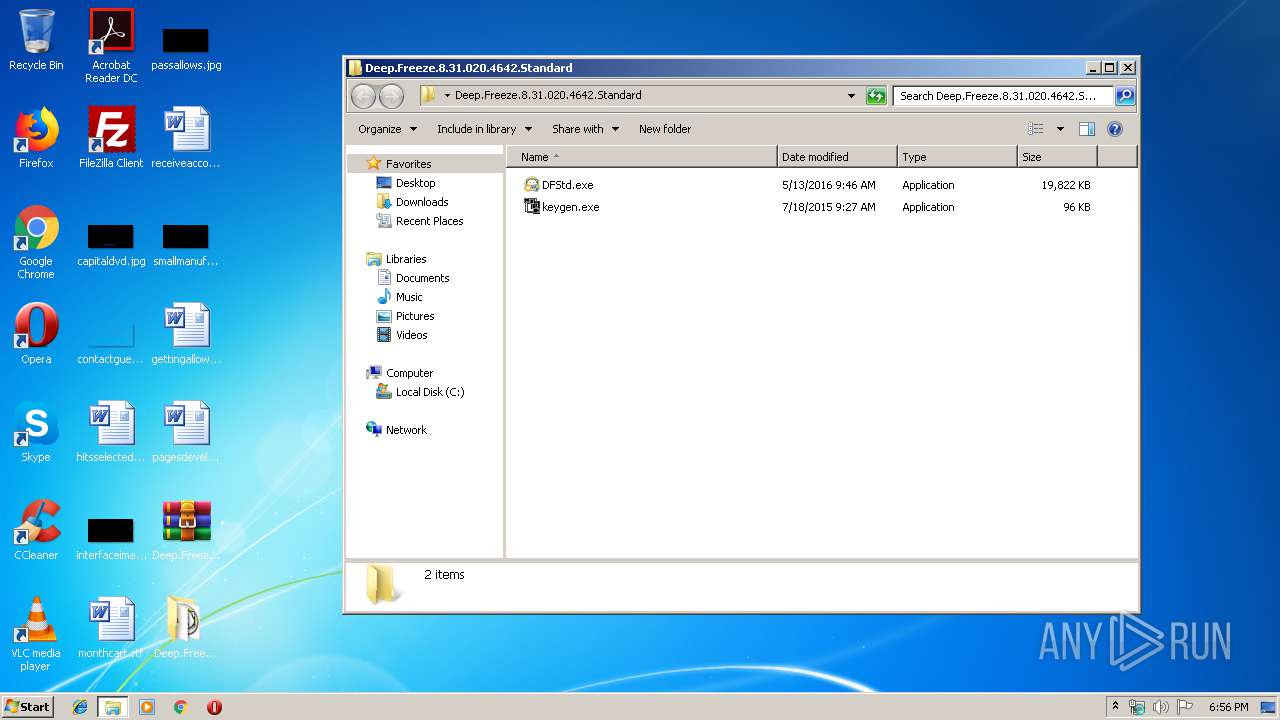
| File name: | Deep.Freeze.8.31.020.4642.Standard.rar |
| Full analysis: | https://app.any.run/tasks/e333abd5-3d5e-46c7-8fa5-adca35971db4 |
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2019, 18:55:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v4, os: Win32 |
| MD5: | D74B96E02809EEE1A743B671144D9AF2 |
| SHA1: | 5E00B8BABDEF7BCCA28E162AB2F7A92E81FE3714 |
| SHA256: | 6F3E705707CE3C180B0BFBD4A00023C674ACA961CFDCA360F55B3B6C85D0DE78 |
| SSDEEP: | 196608:c5iQN1Z5MOXPaGdAnvNtubqkDaOlLKGZa1sBi1qPjpz5SCYcxkiLGmXi:4N1Z5JSnltuJa51sB2I/rY+kILi |
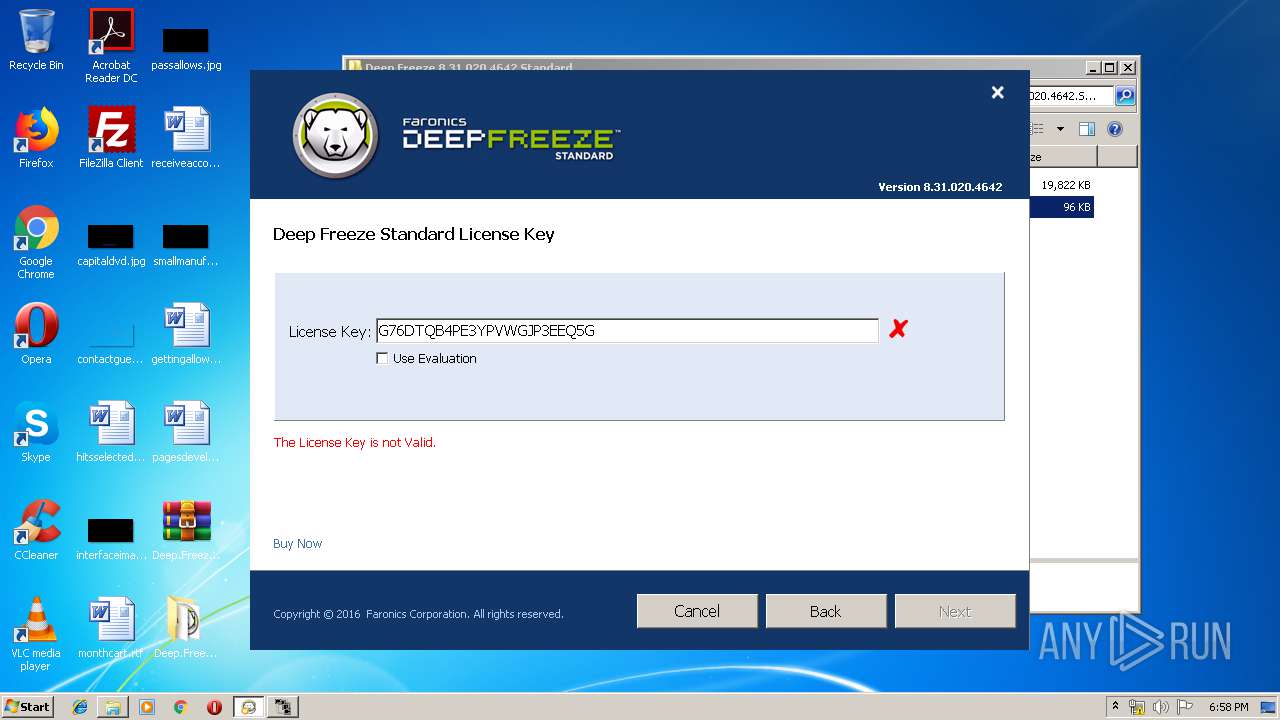
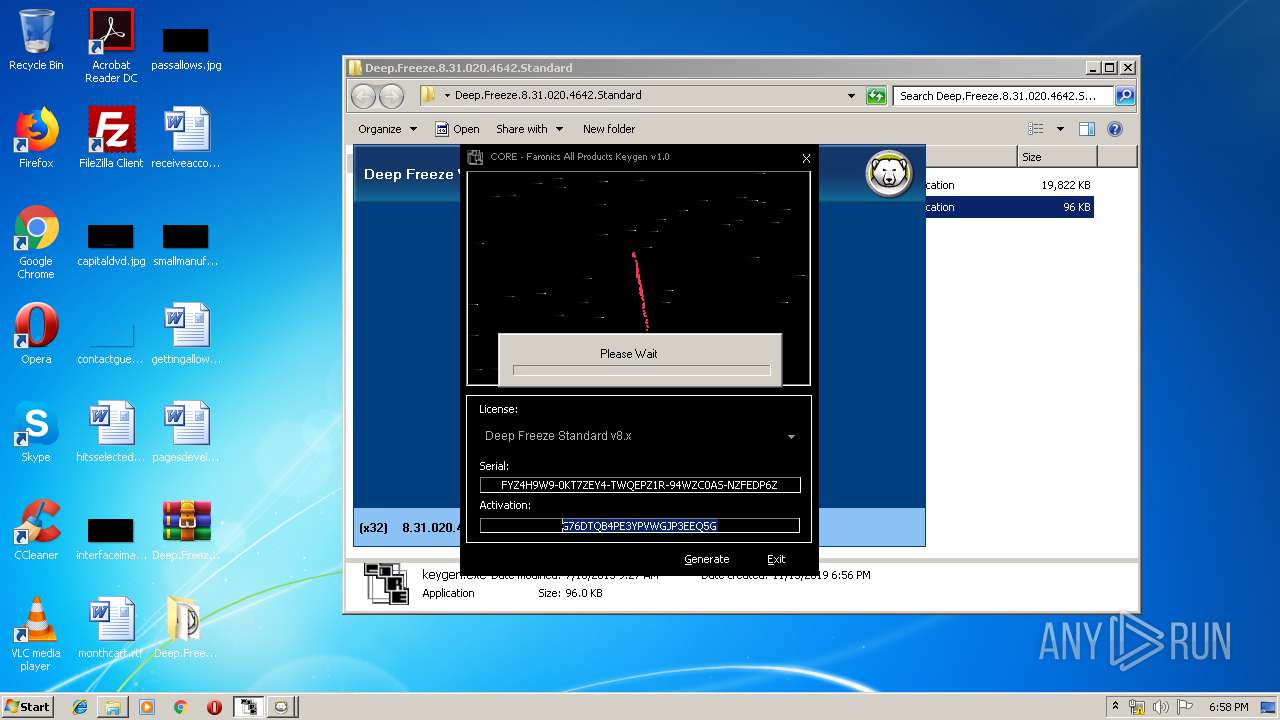
MALICIOUS
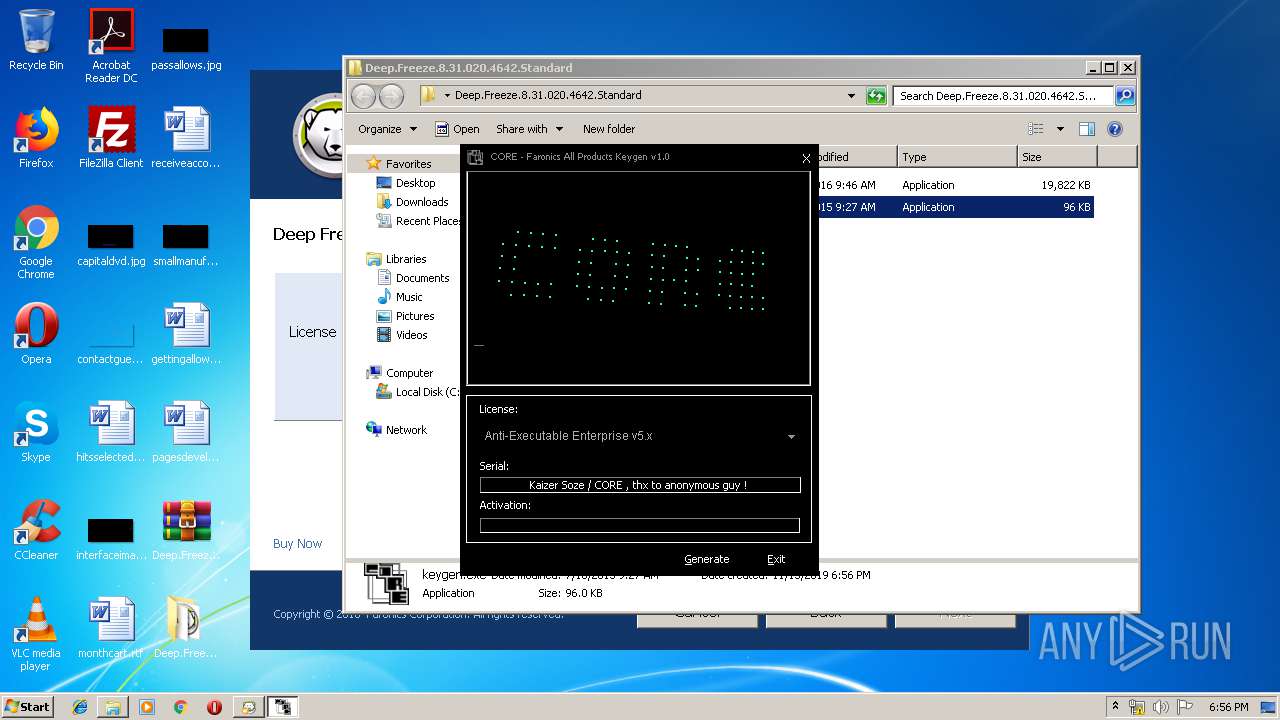
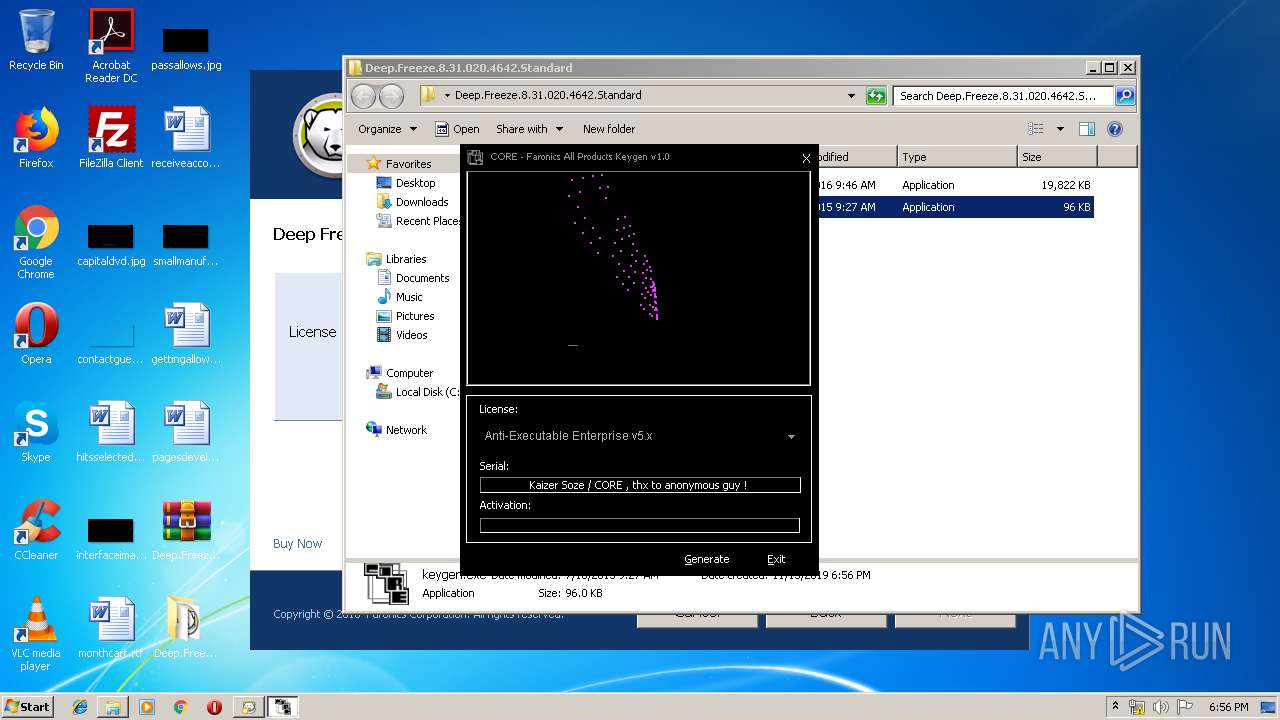
Loads dropped or rewritten executable
- keygen.exe (PID: 3780)
- regsvr32.exe (PID: 3548)
- regsvr32.exe (PID: 3968)
Application was dropped or rewritten from another process
- keygen.exe (PID: 3780)
- DFStd.exe (PID: 956)
- DFStd.exe (PID: 2084)
- DeepFreeze_C.exe (PID: 2668)
- DFServ.exe (PID: 292)
Registers / Runs the DLL via REGSVR32.EXE
- DeepFreeze_C.exe (PID: 2668)
SUSPICIOUS
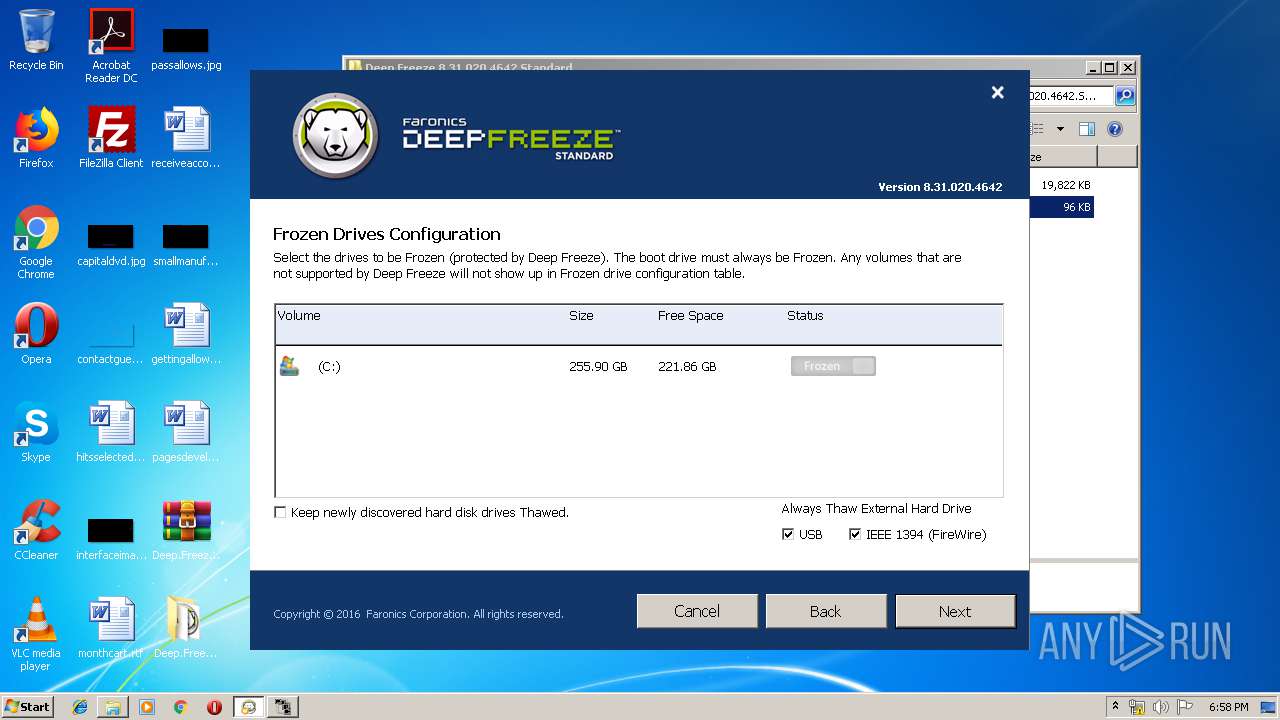
Creates files in the driver directory
- DeepFreeze_C.exe (PID: 2668)
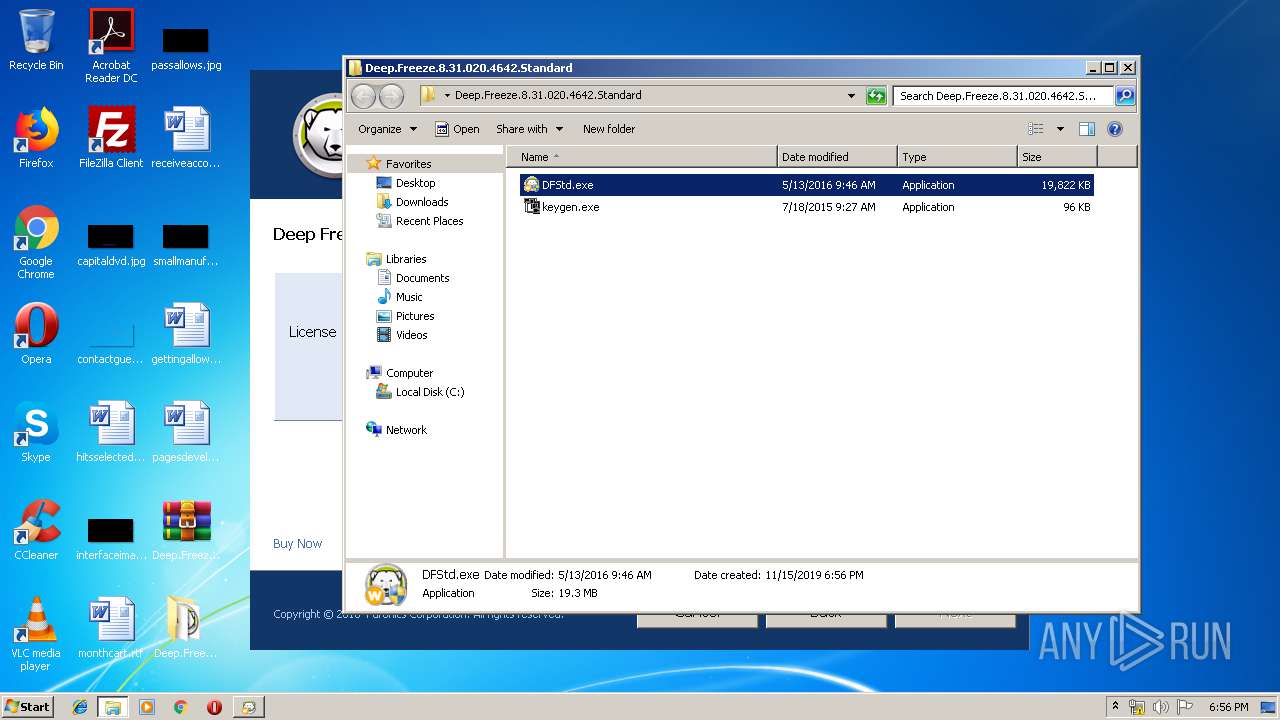
Executable content was dropped or overwritten
- keygen.exe (PID: 3780)
- WinRAR.exe (PID: 4012)
- DFStd.exe (PID: 2084)
- DeepFreeze_C.exe (PID: 2668)
Creates files in the Windows directory
- DeepFreeze_C.exe (PID: 2668)
Creates files in the program directory
- DeepFreeze_C.exe (PID: 2668)
Creates COM task schedule object
- regsvr32.exe (PID: 3968)
INFO
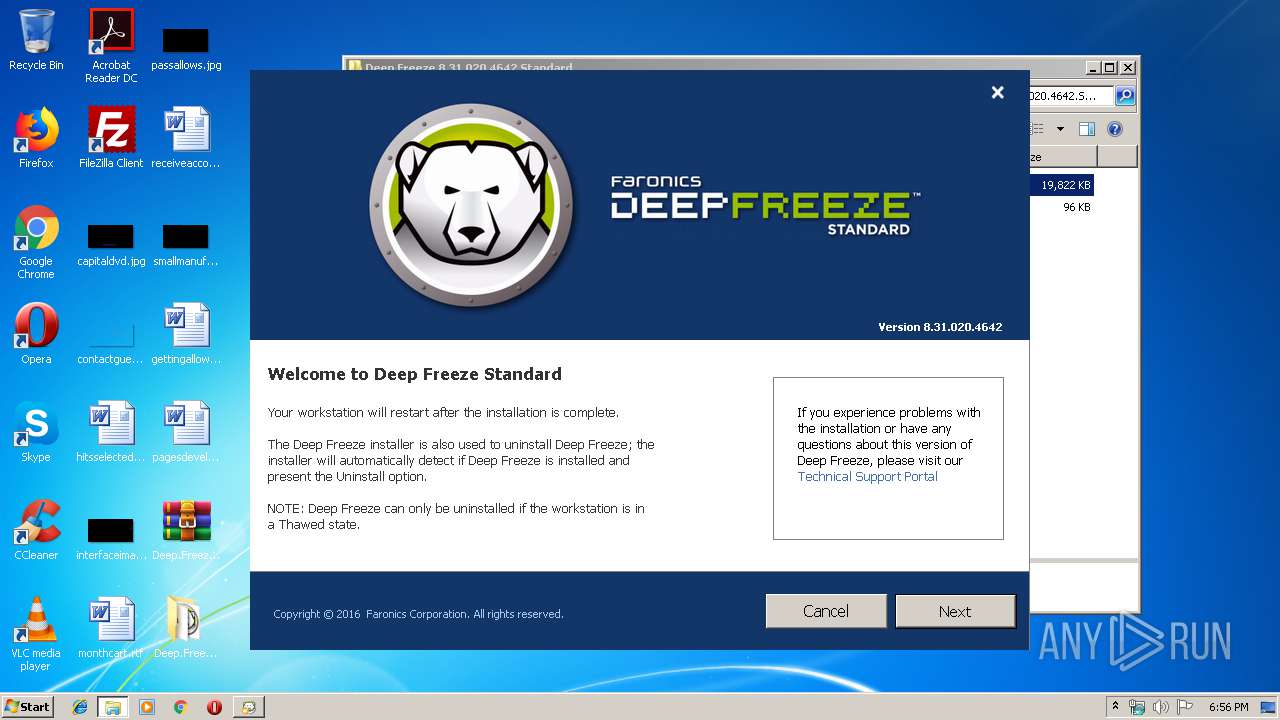
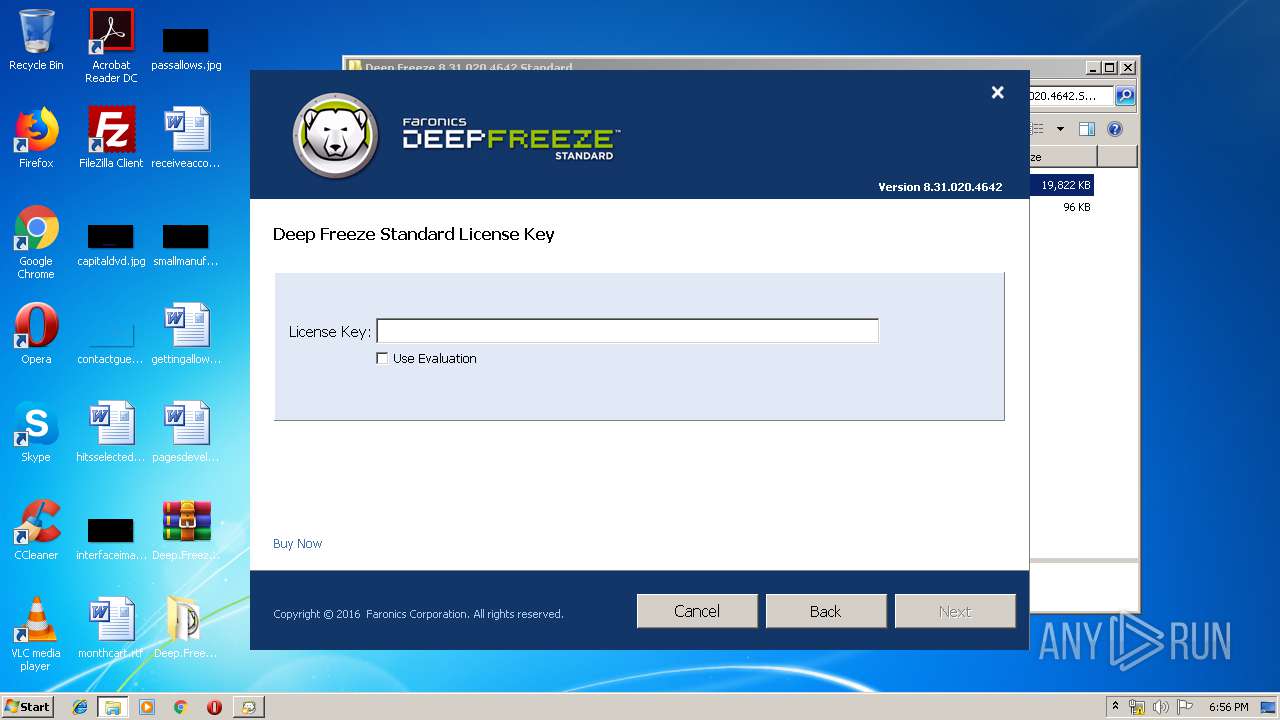
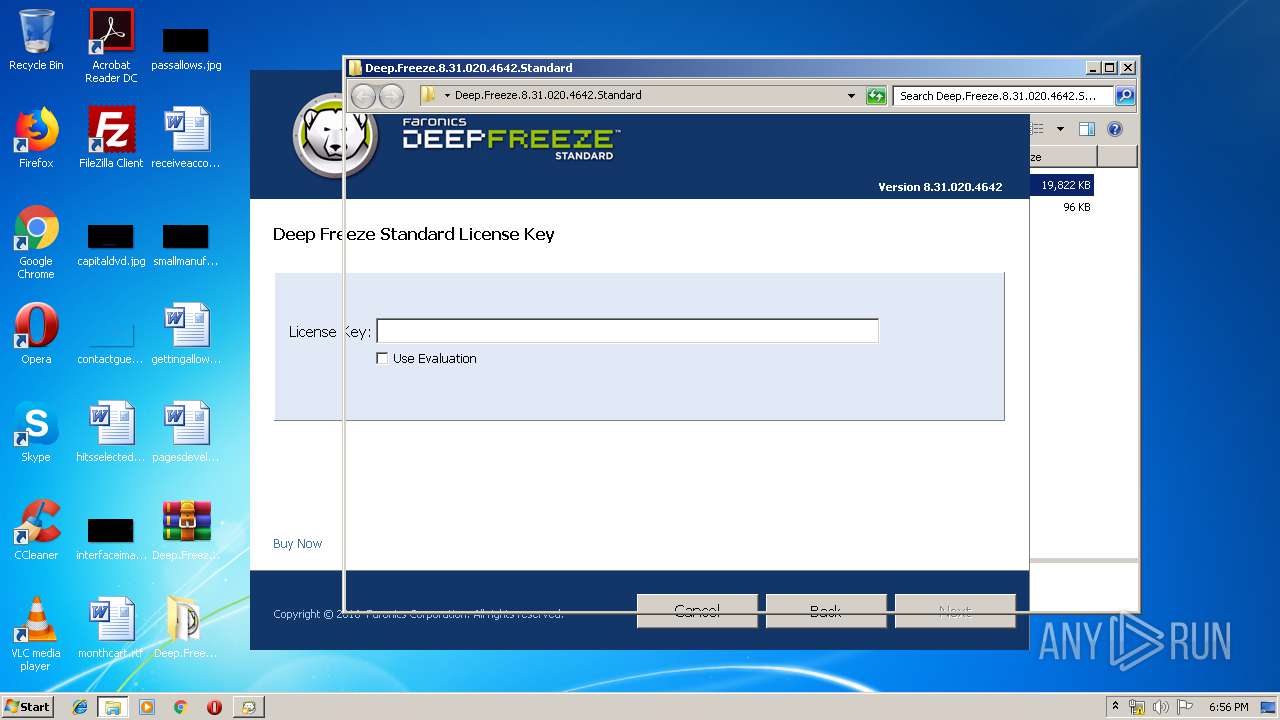
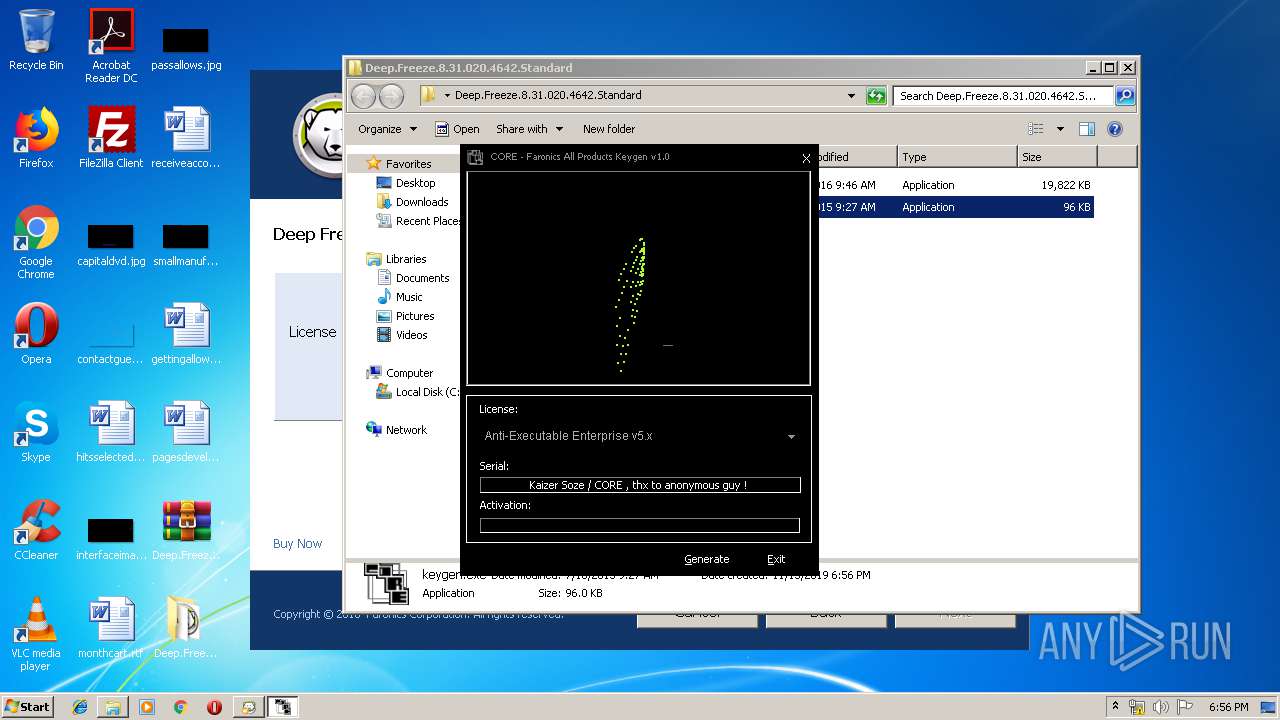
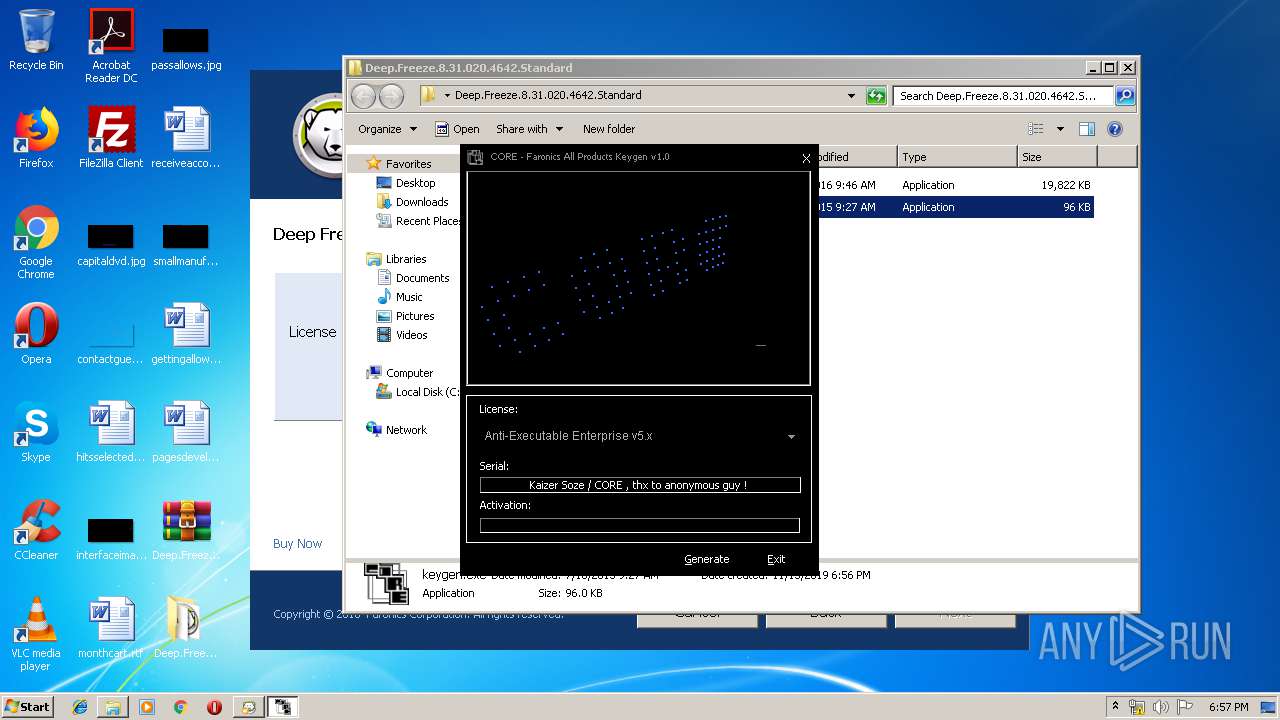
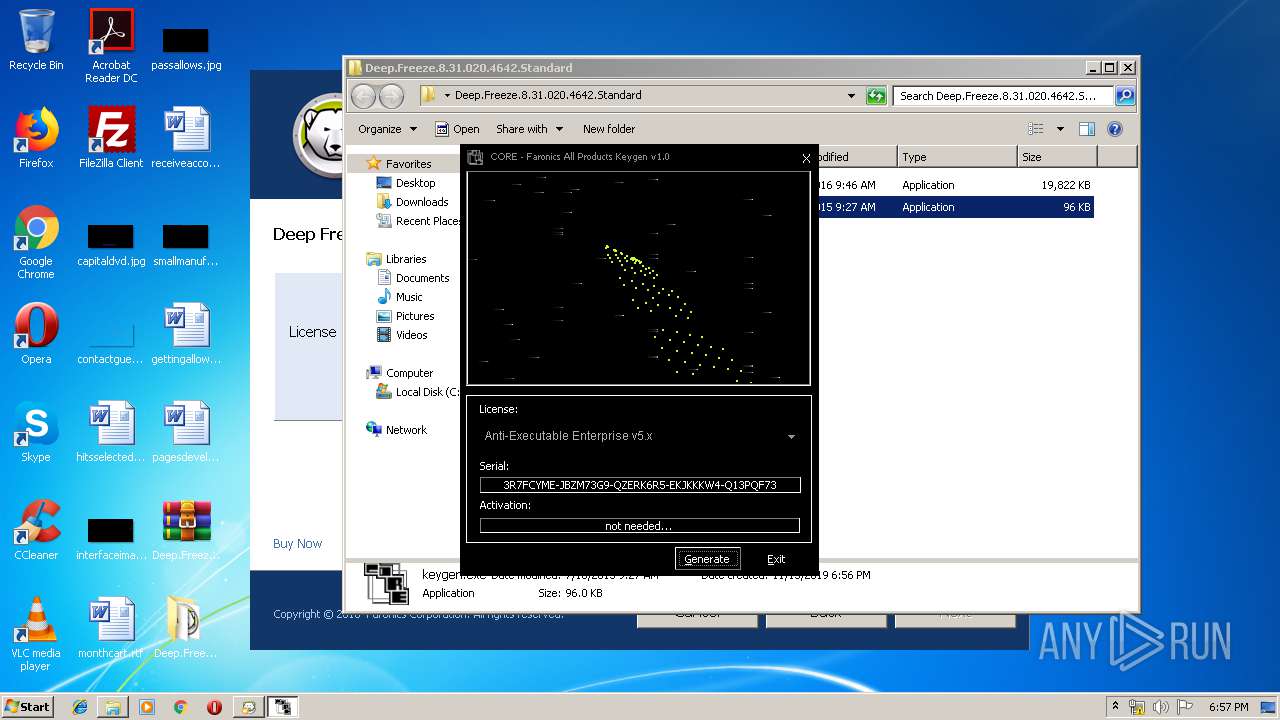
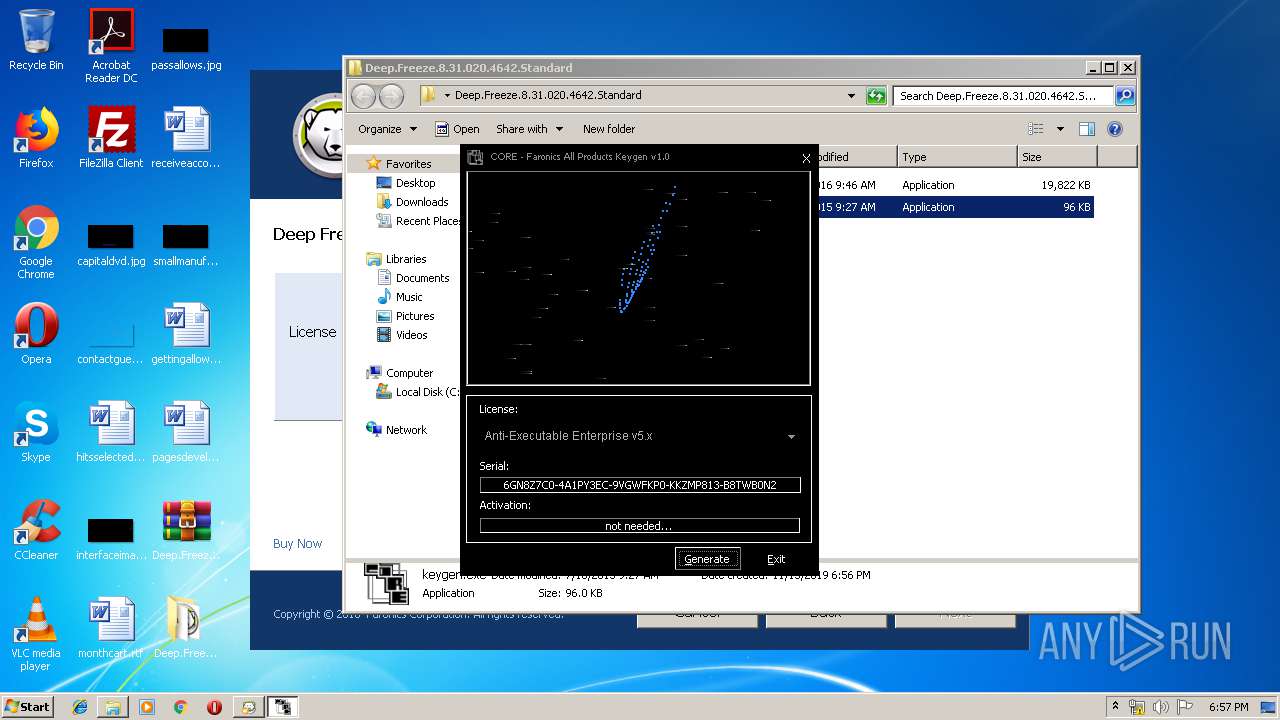
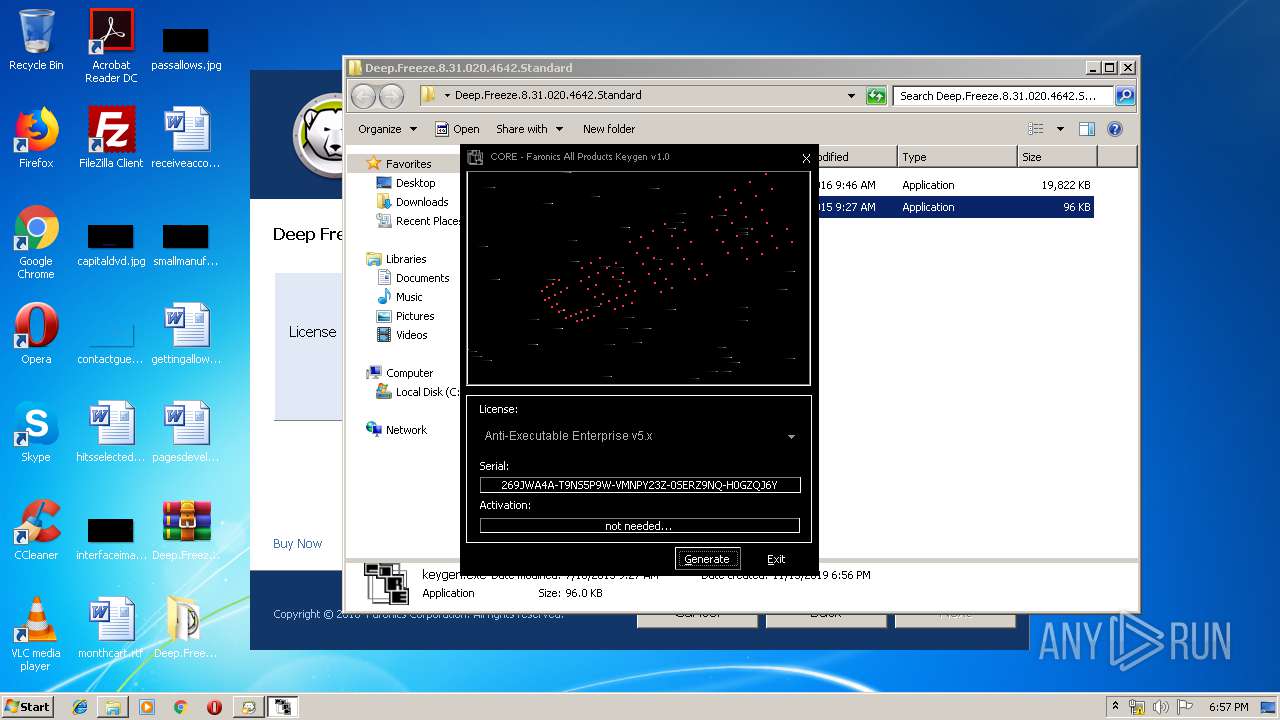
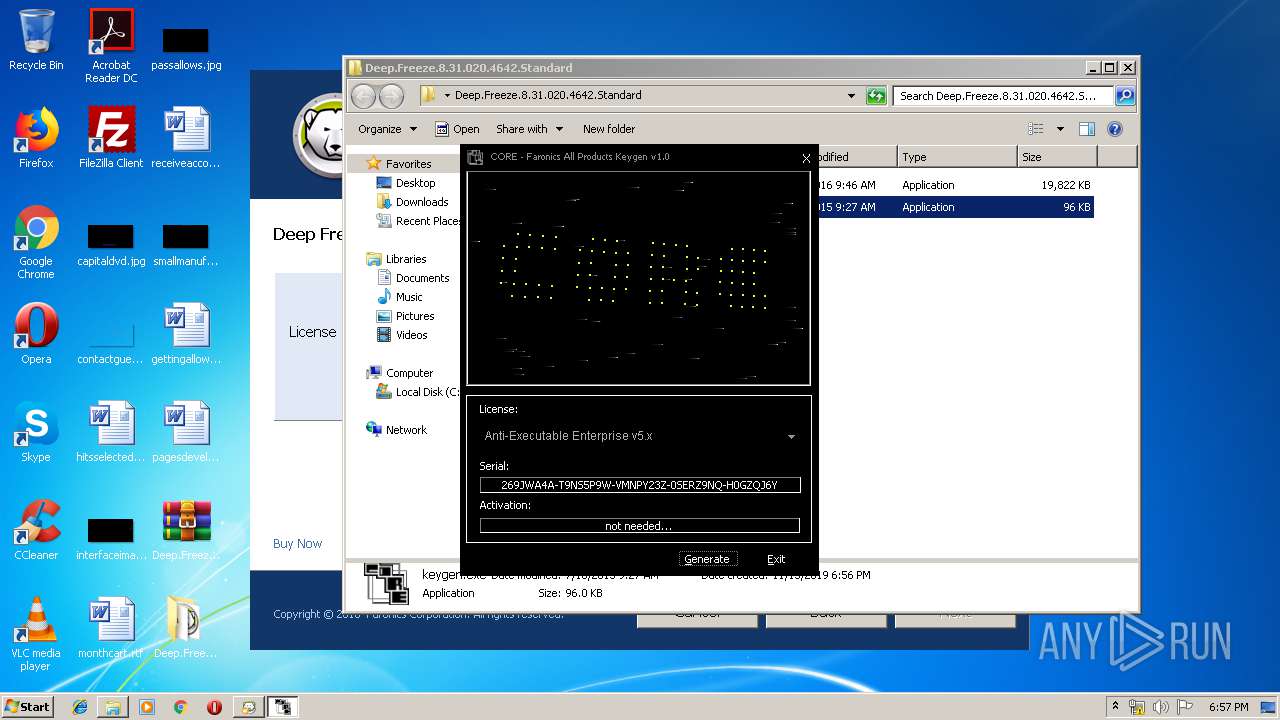
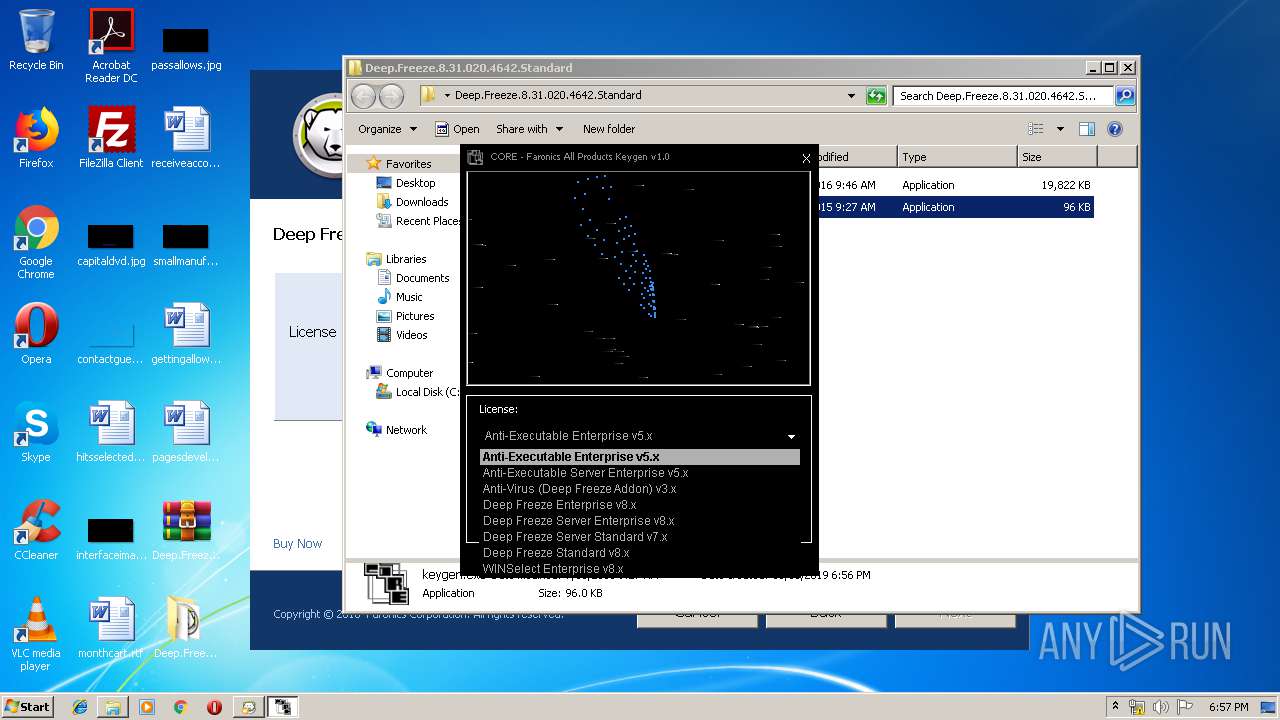
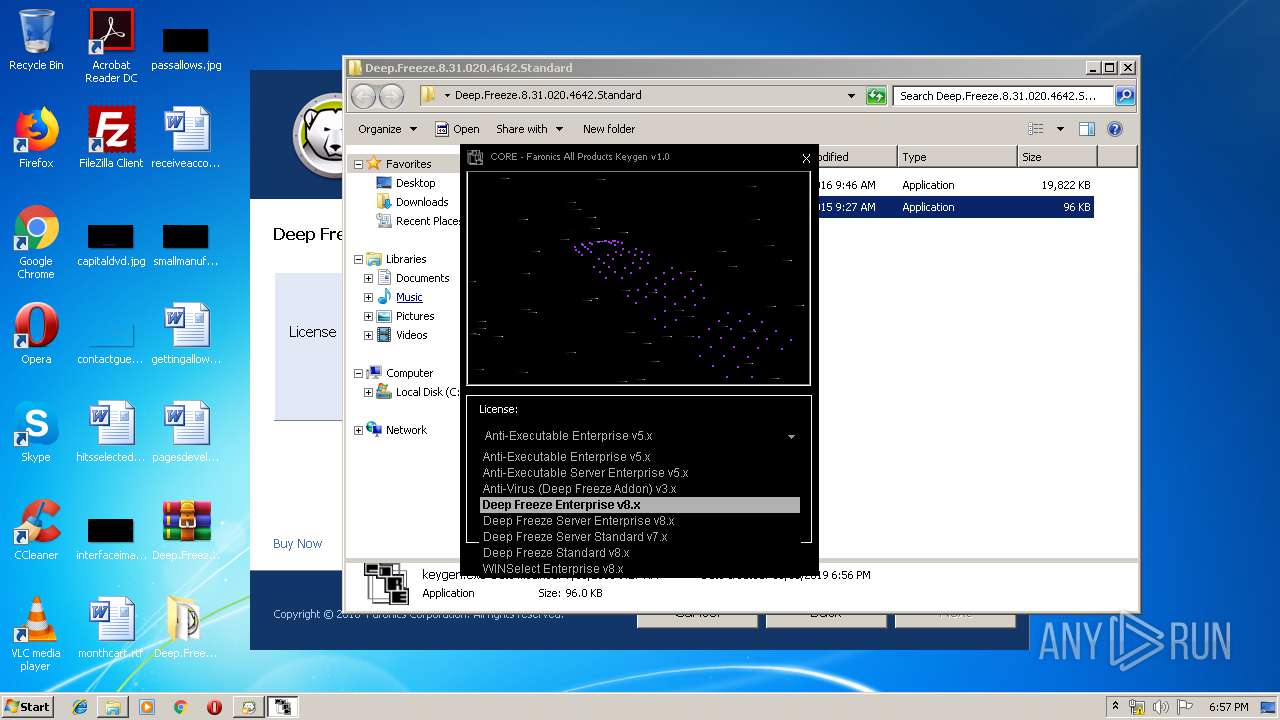
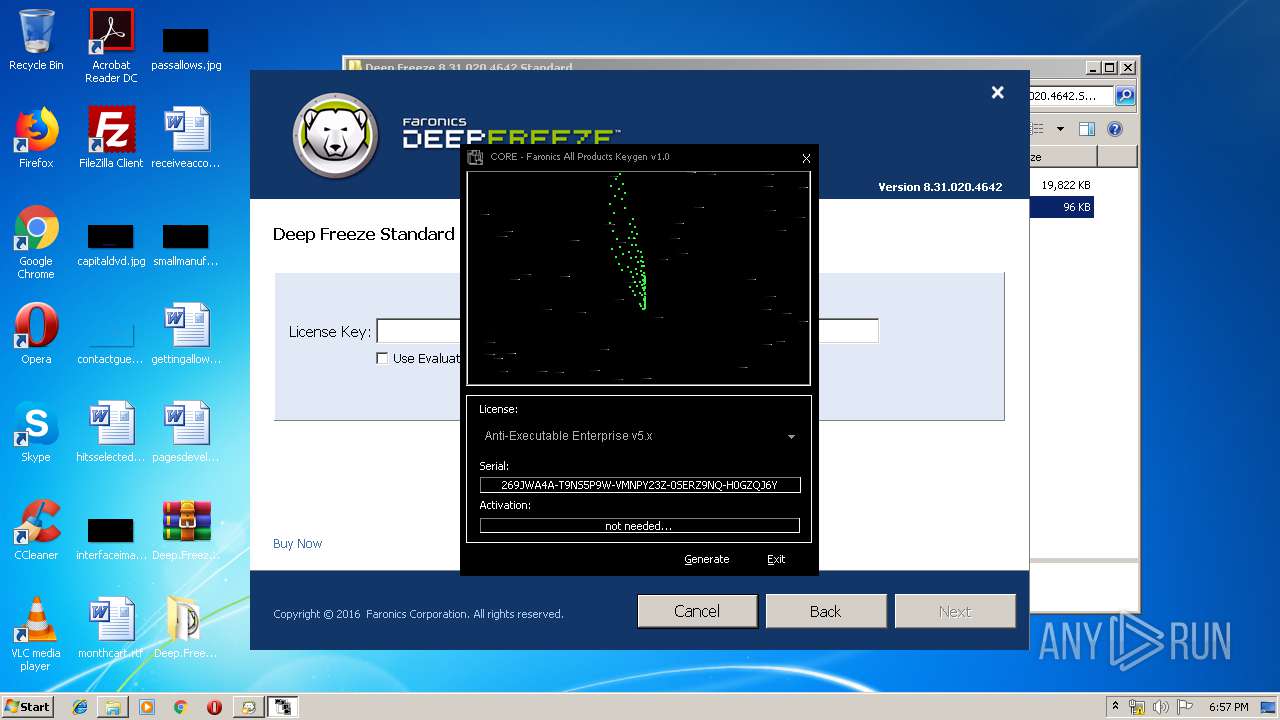
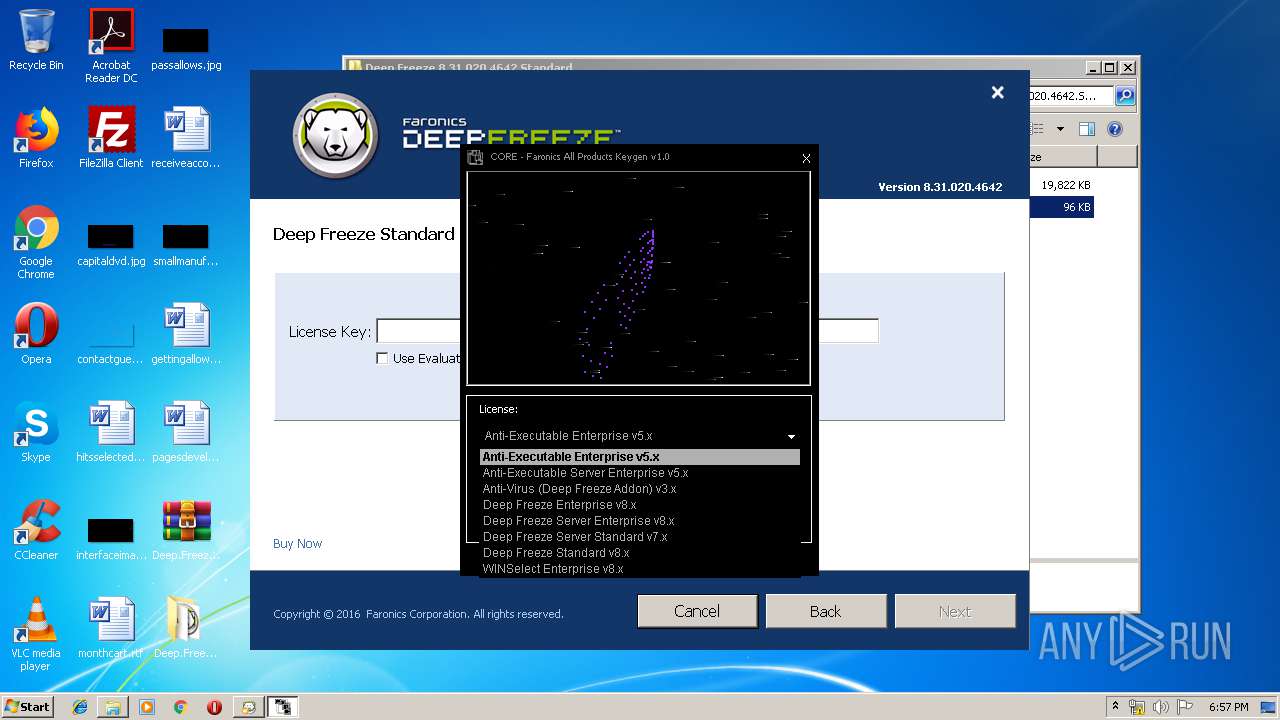
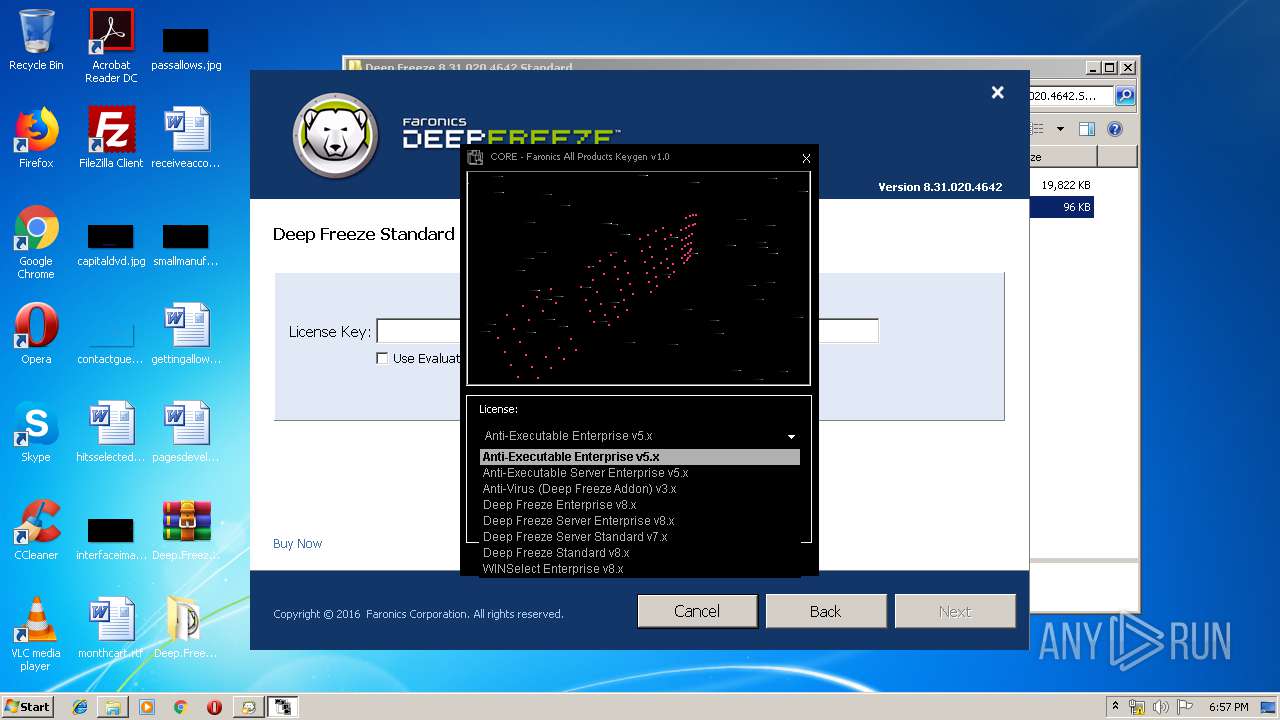
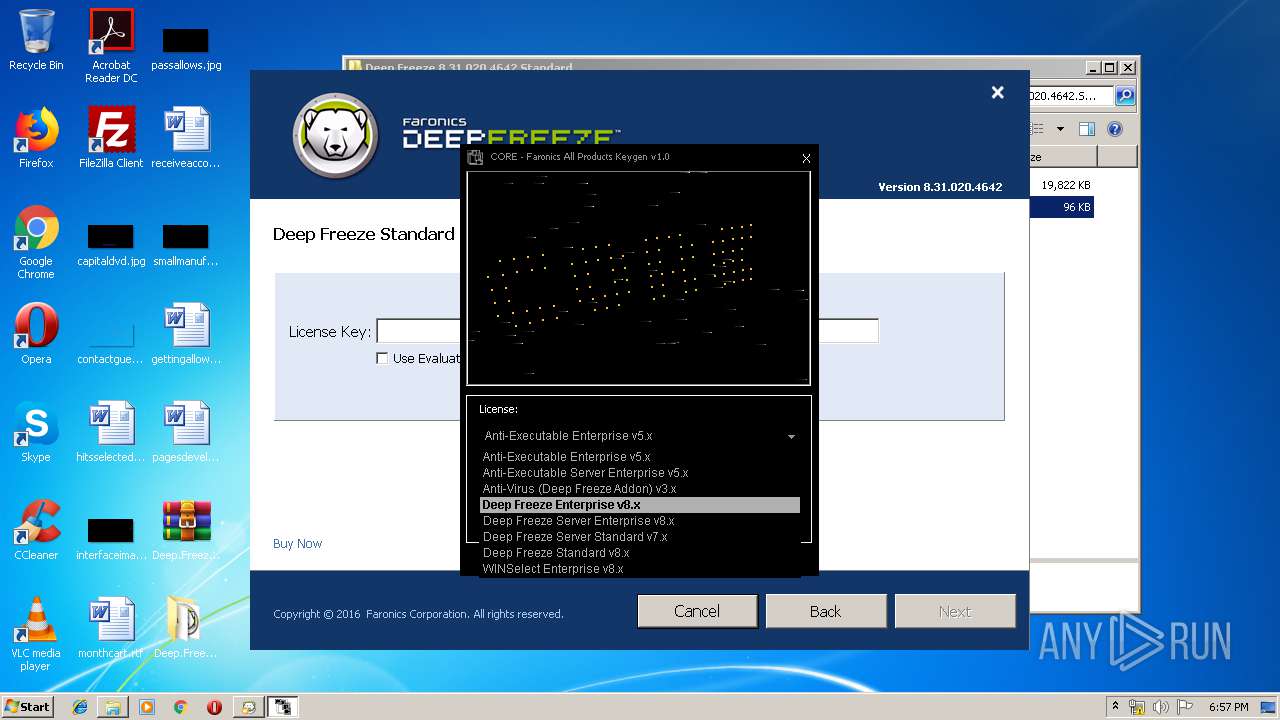
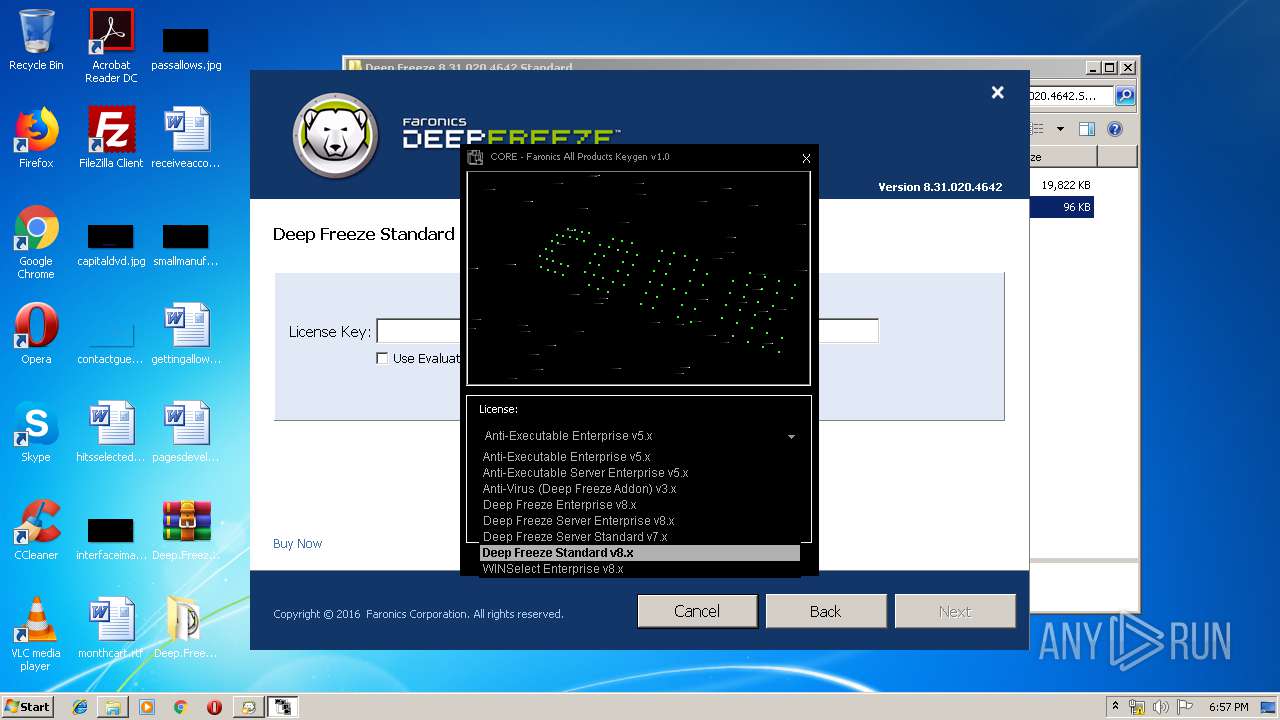
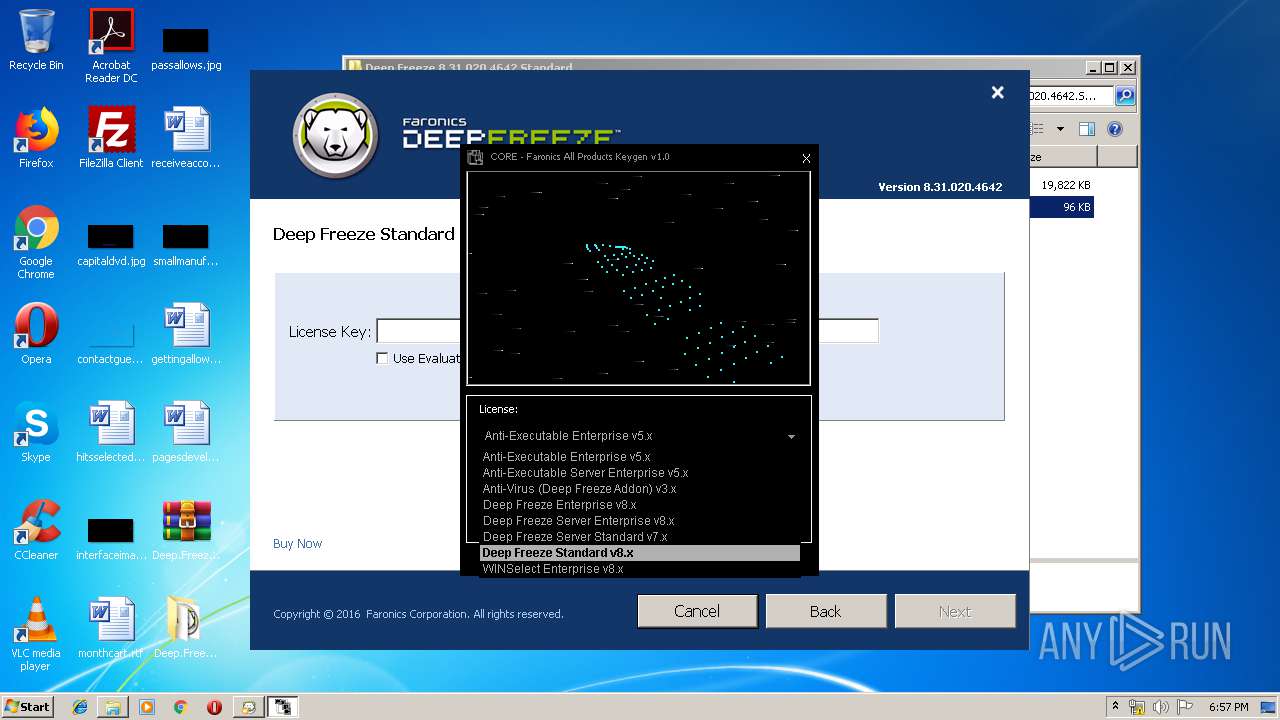
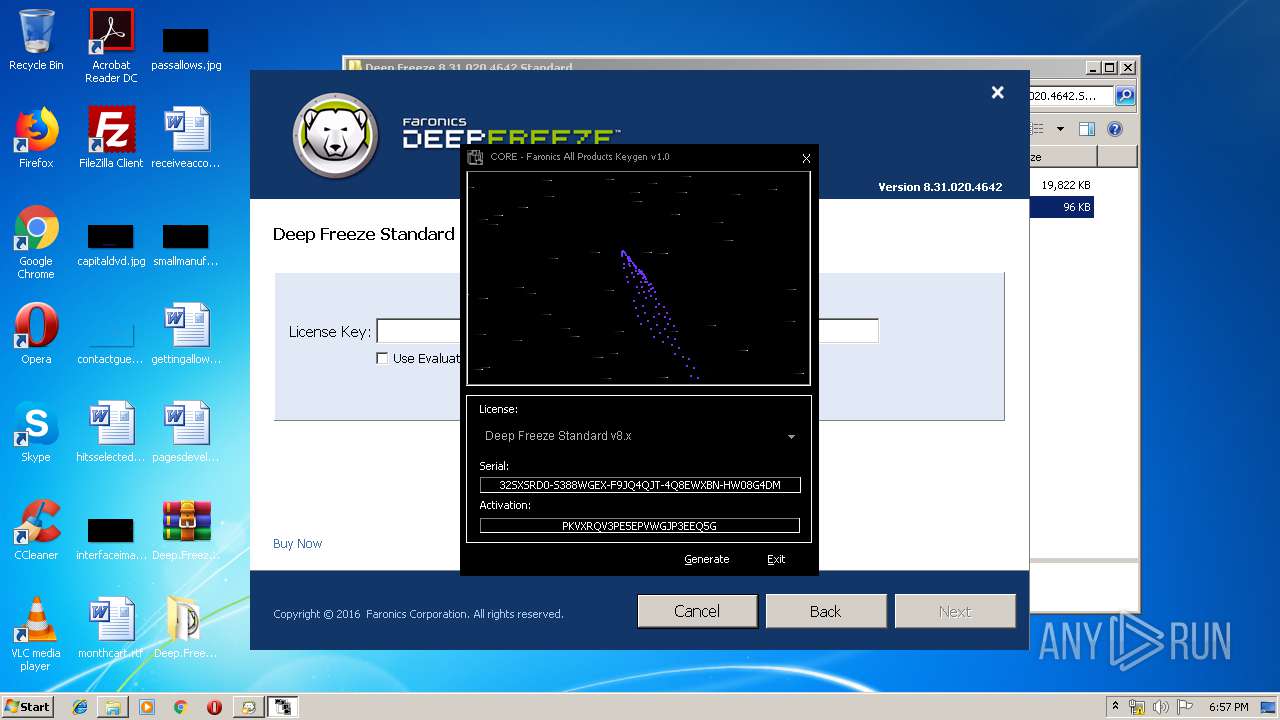
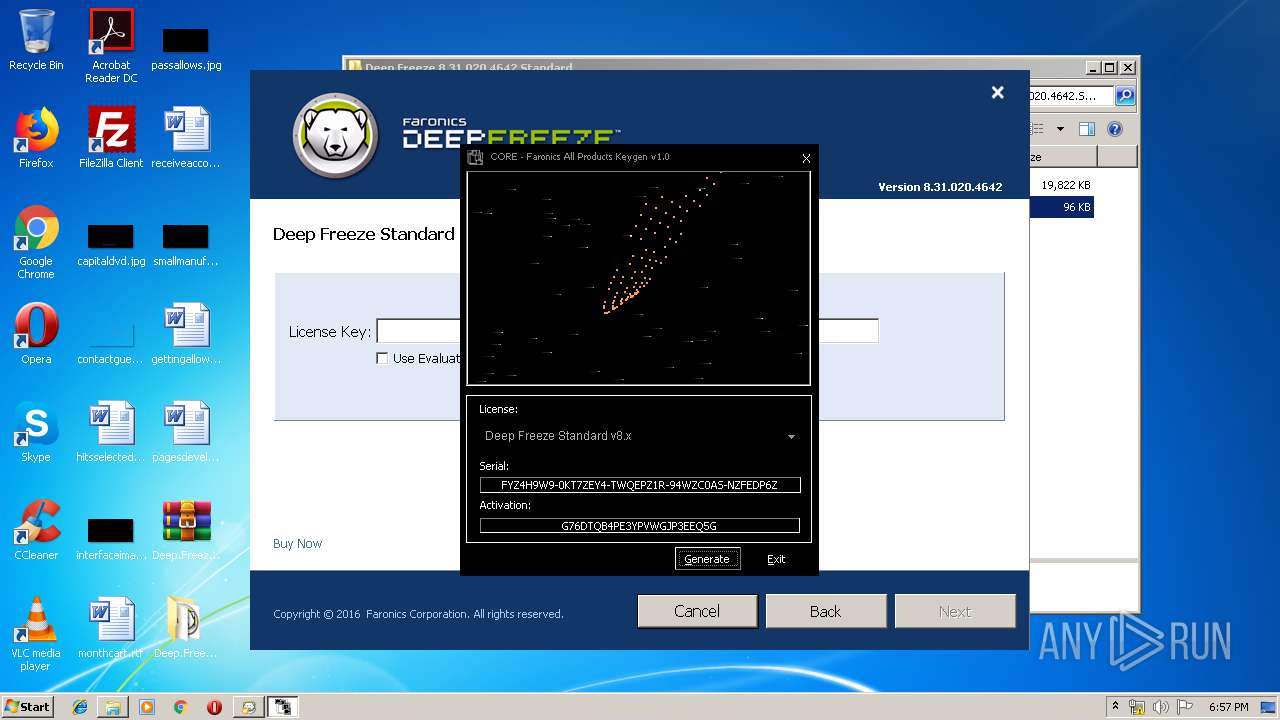
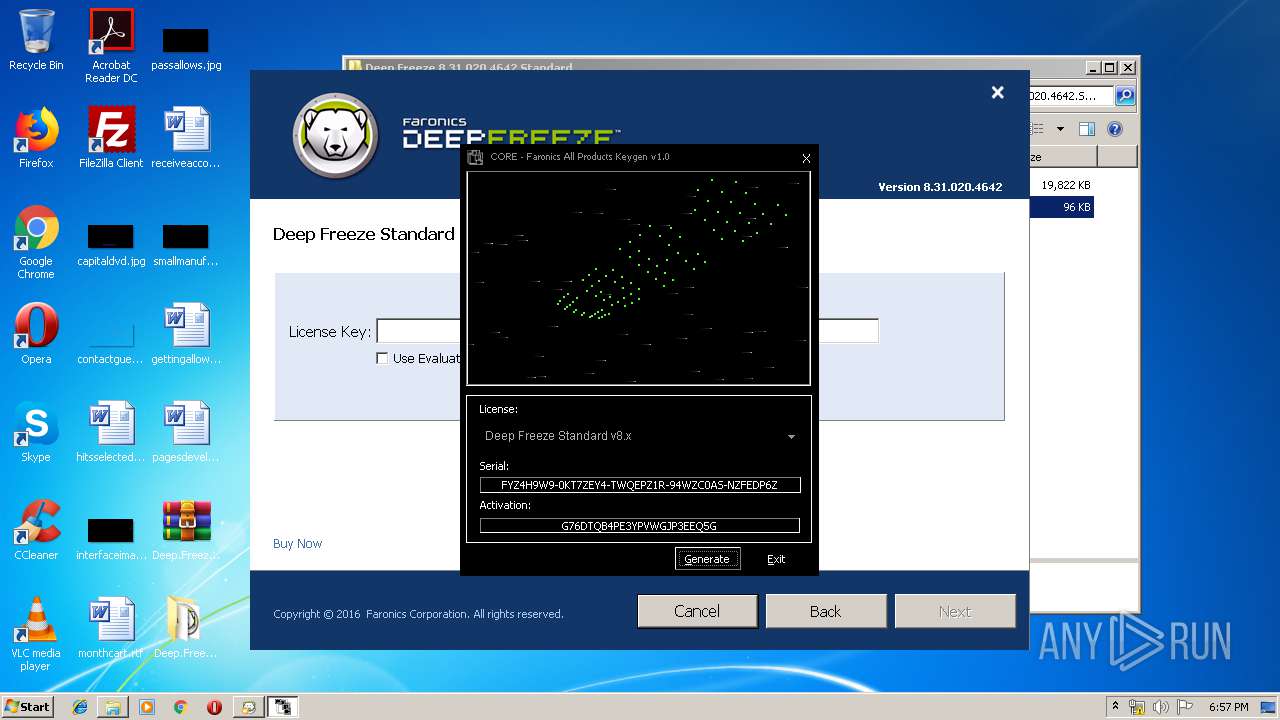
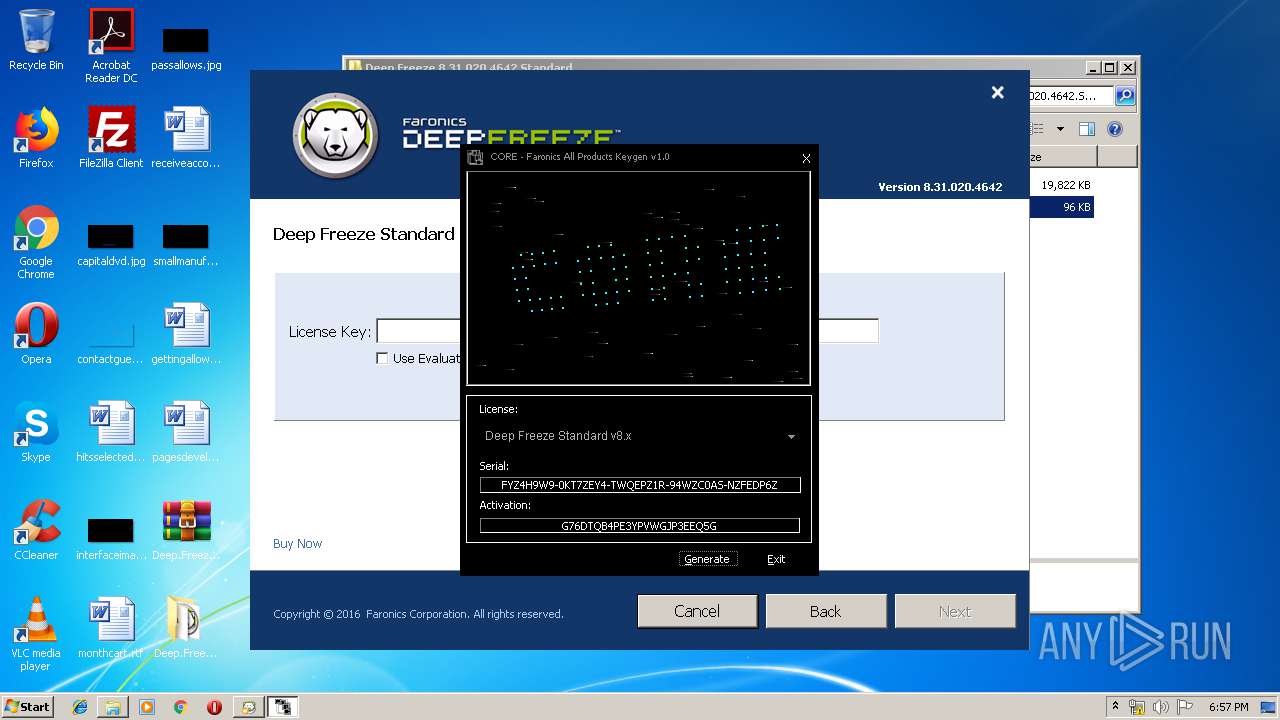
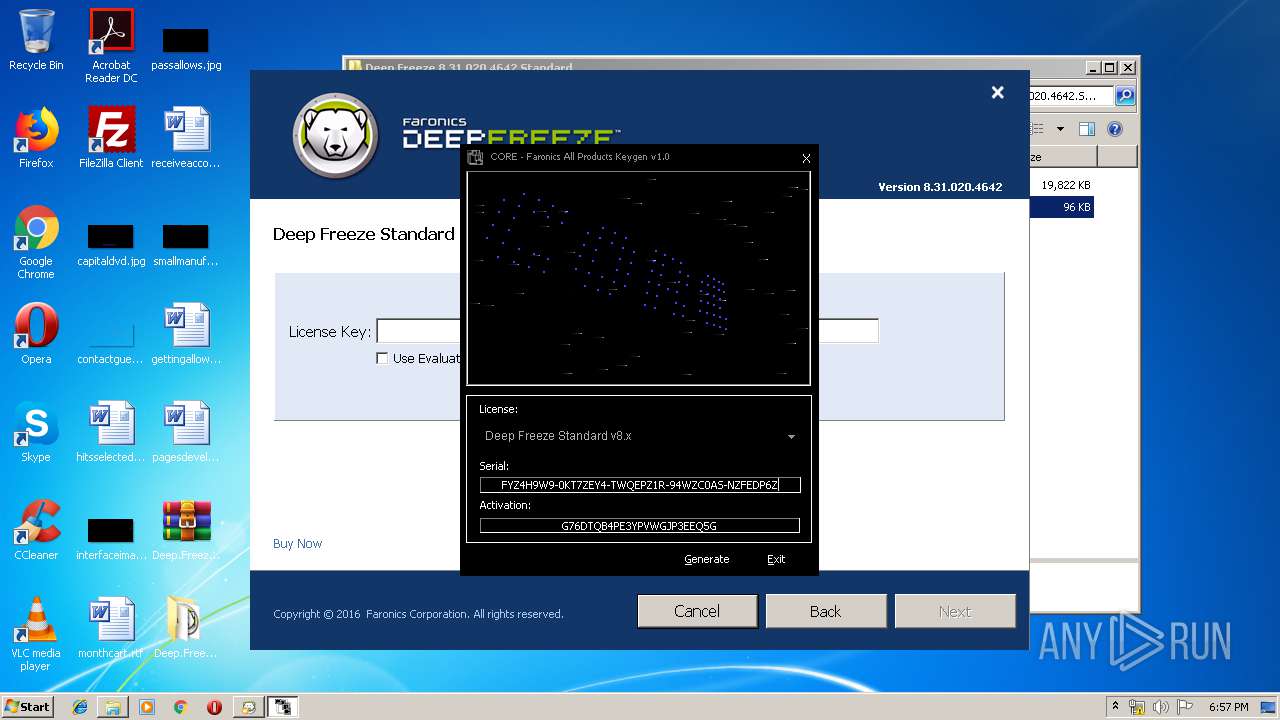
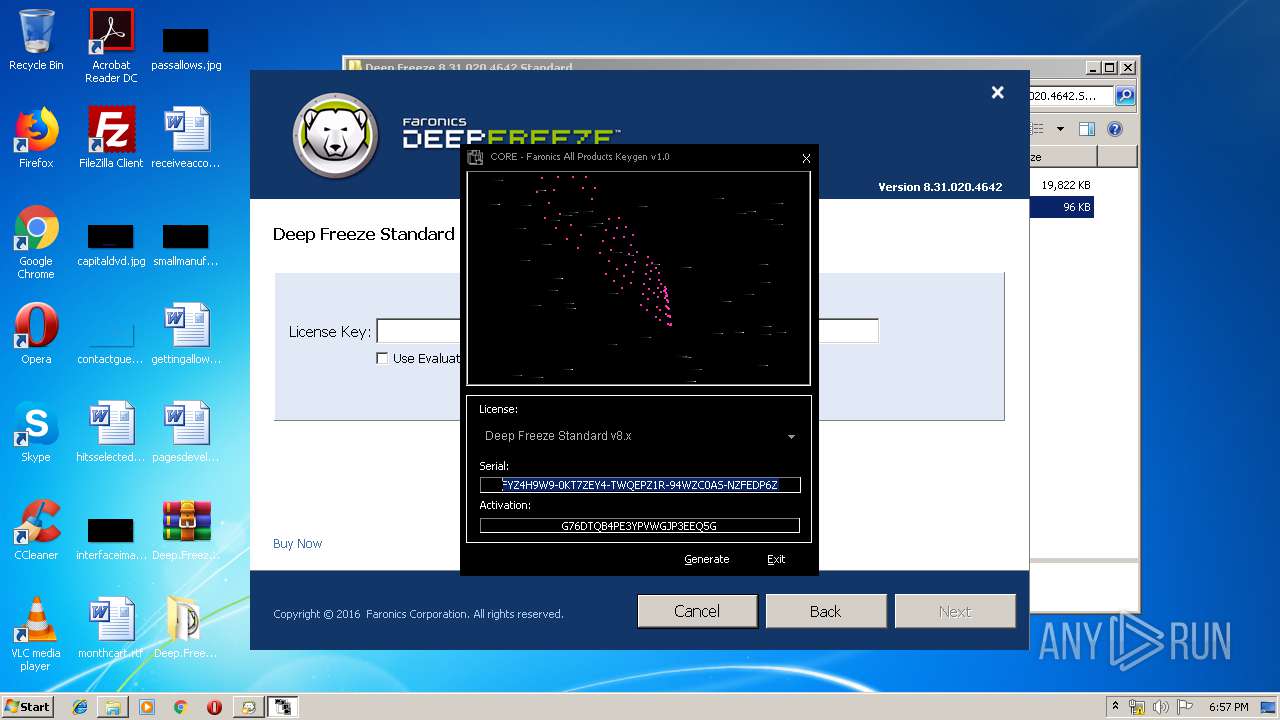
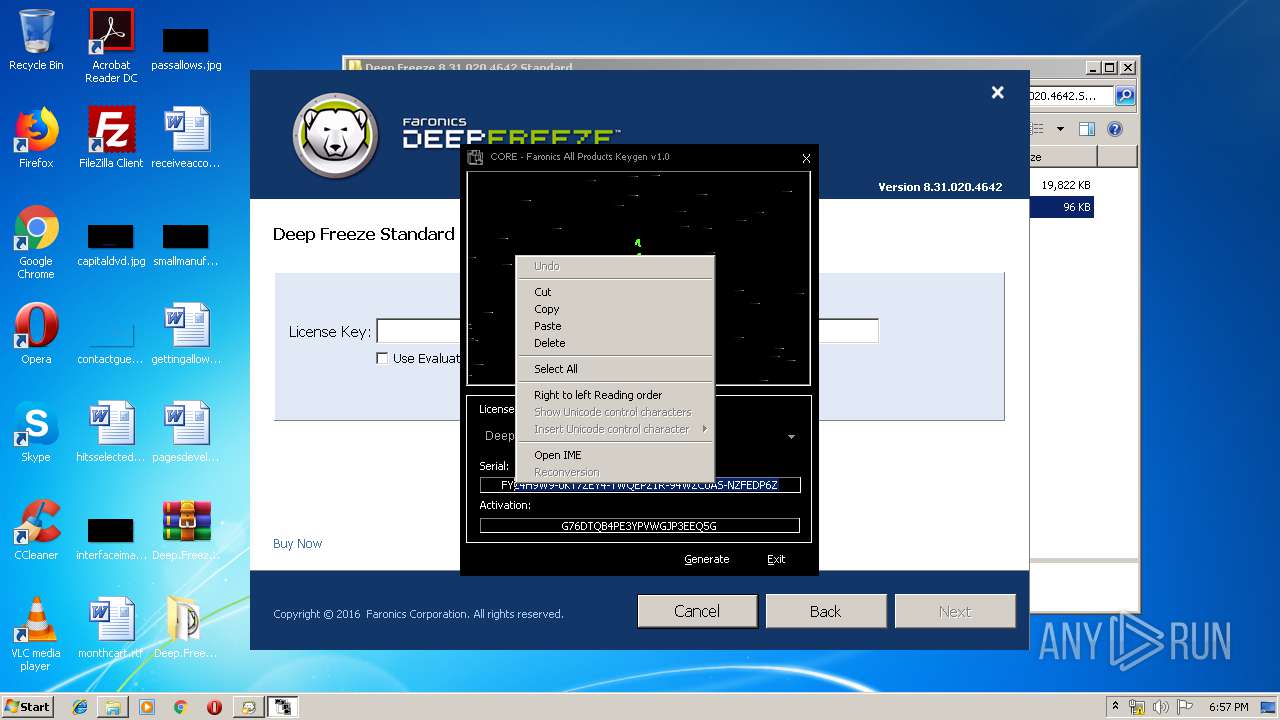
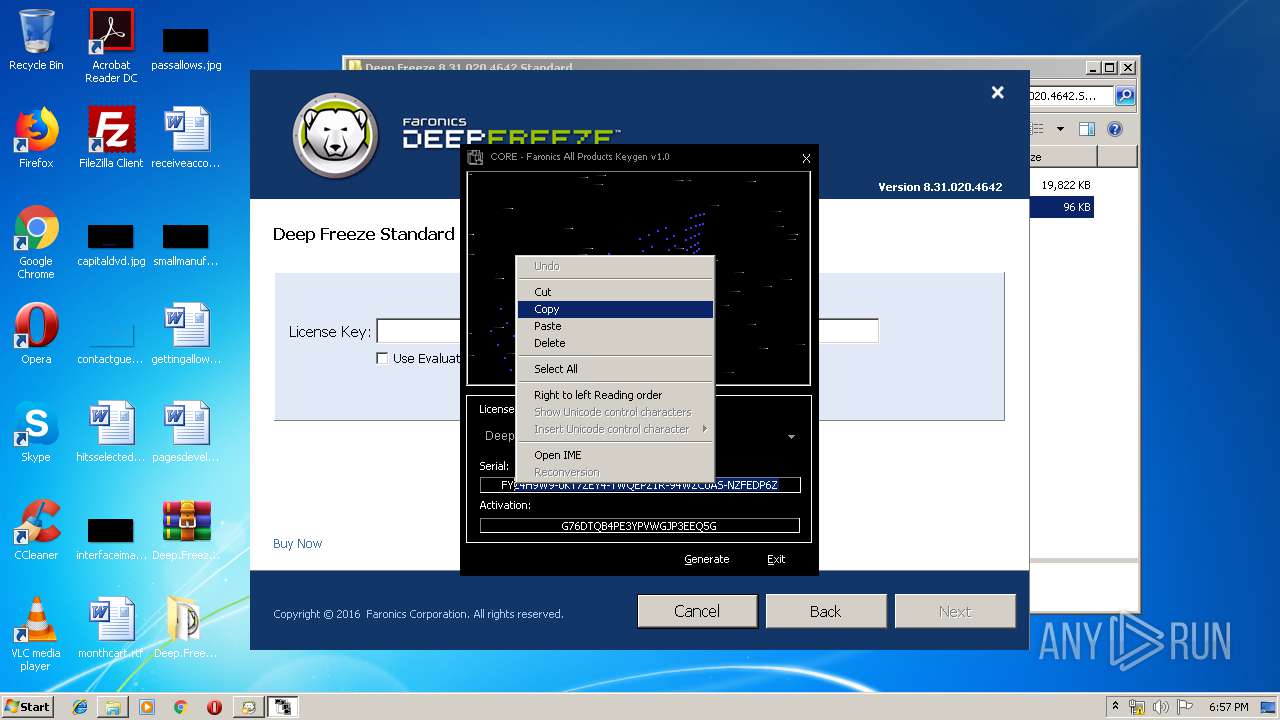
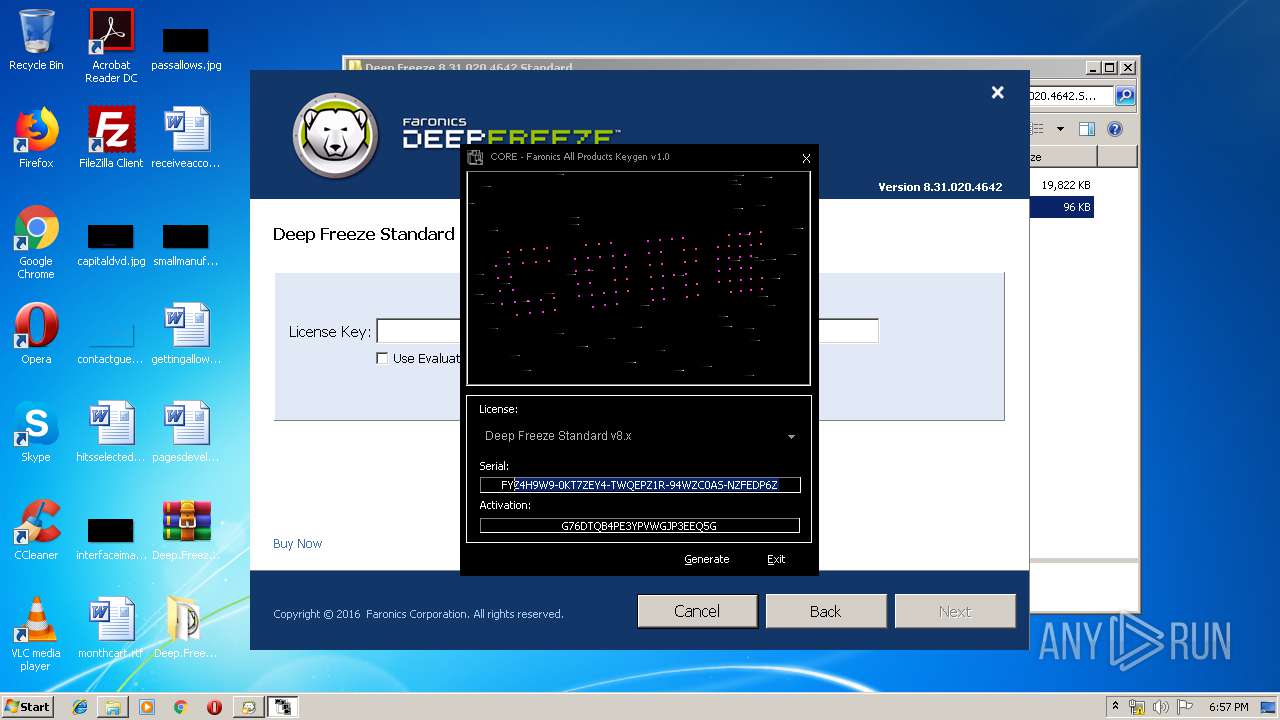
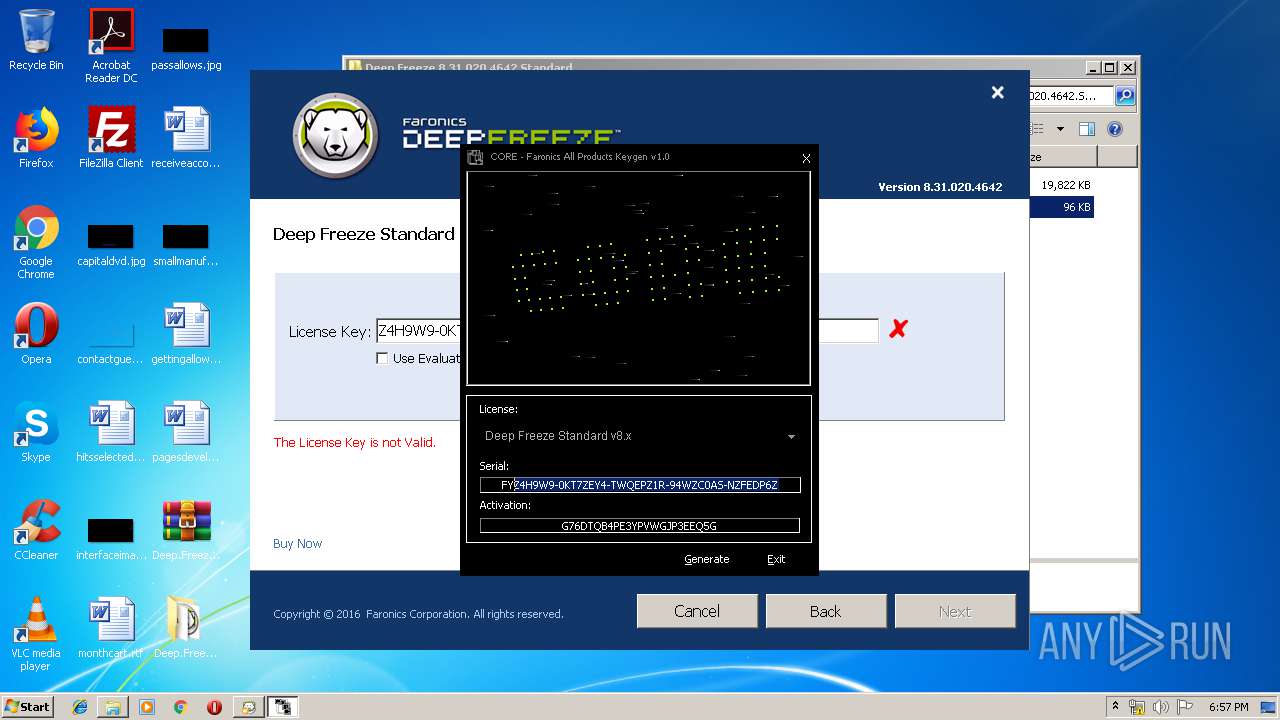
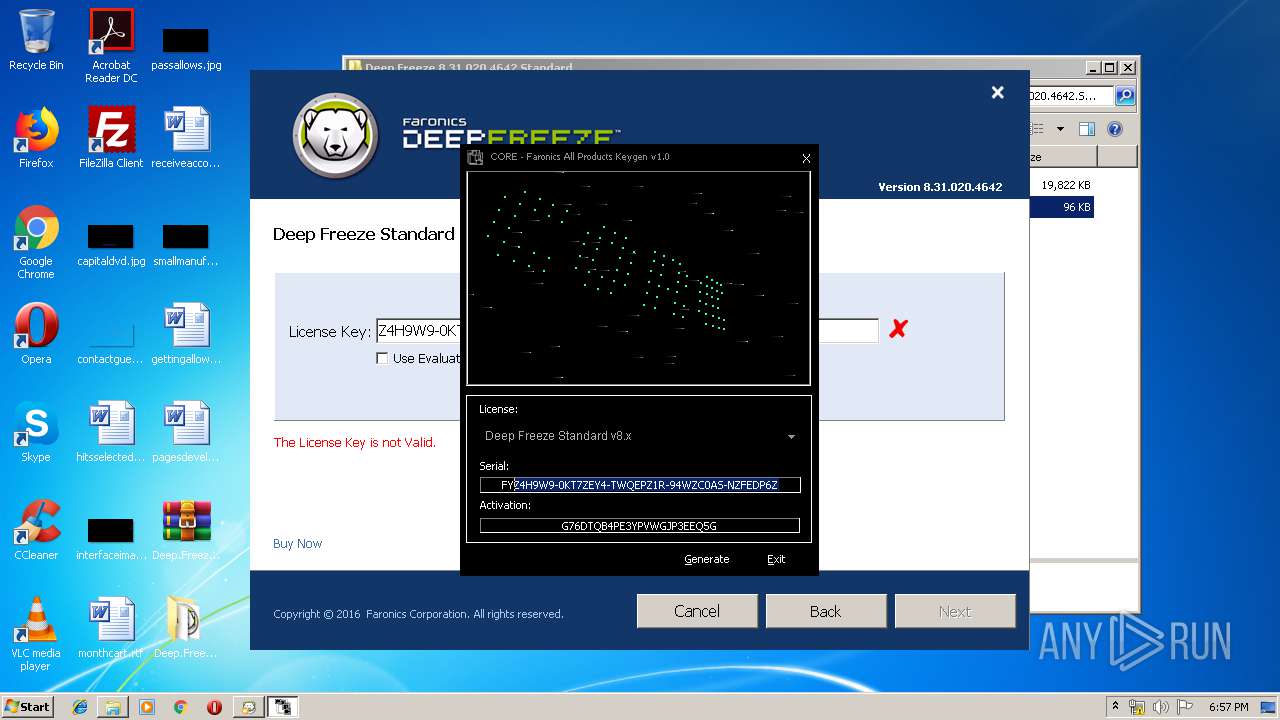
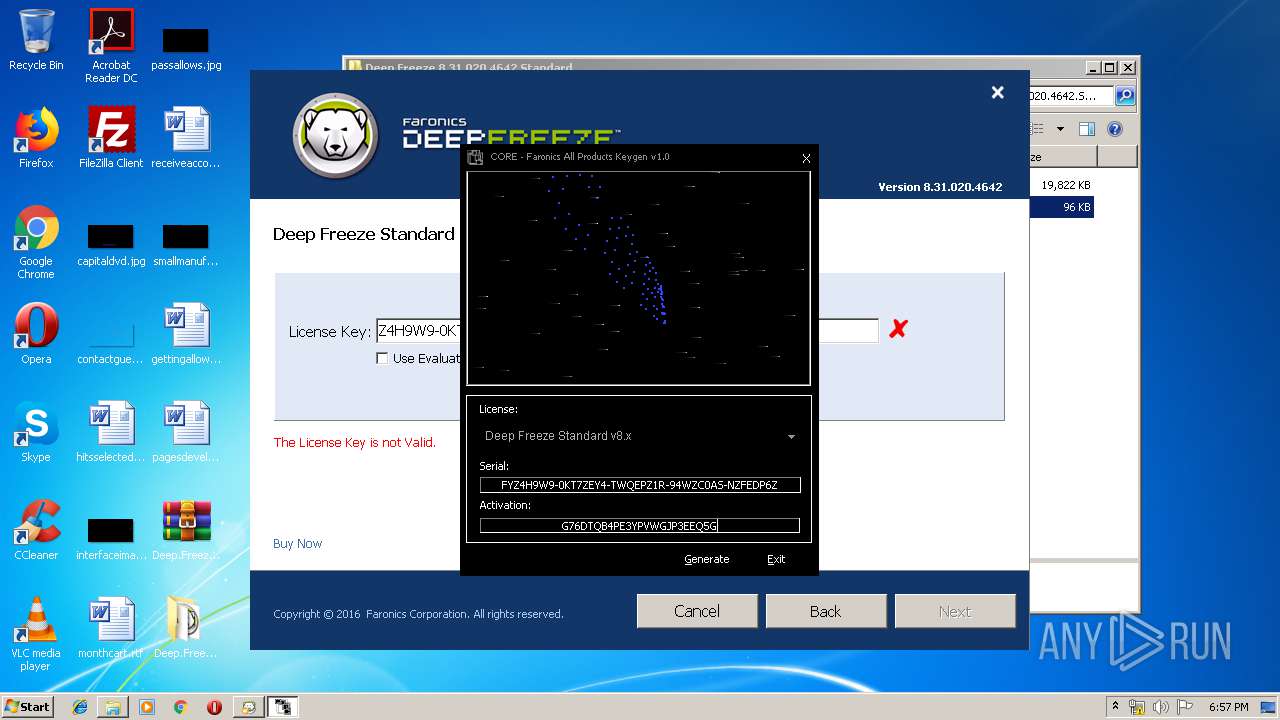
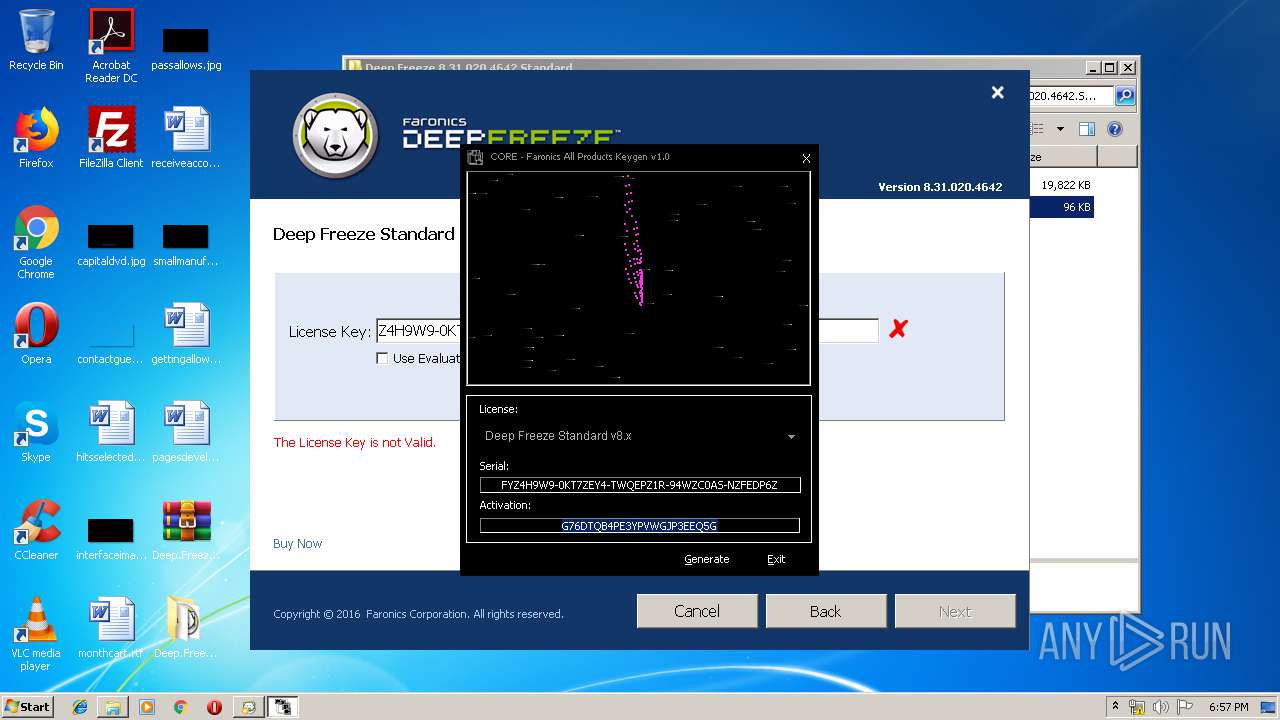
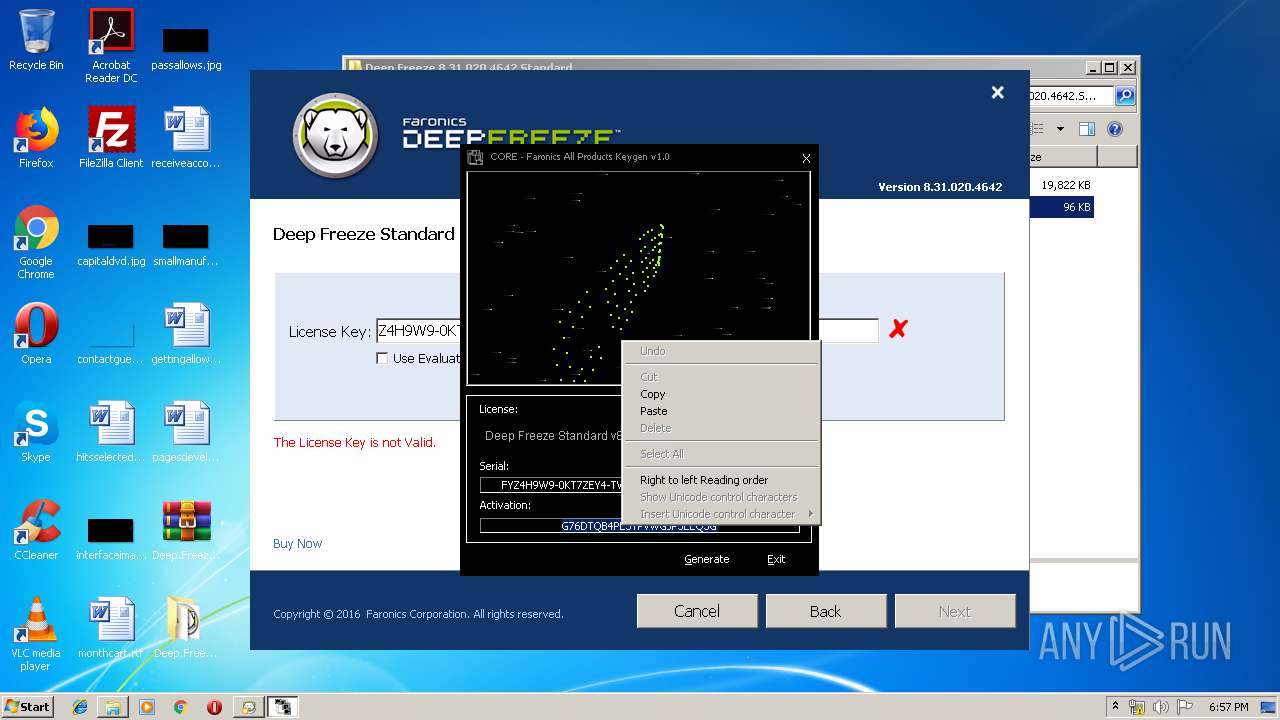
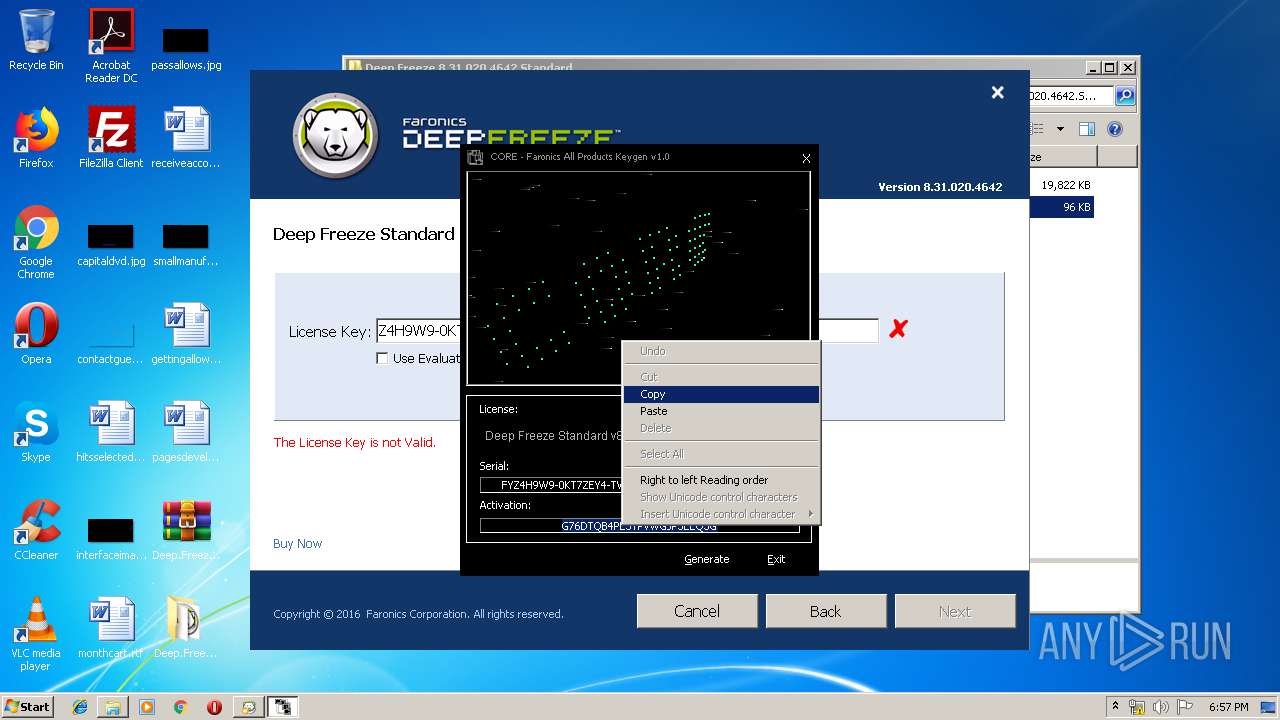
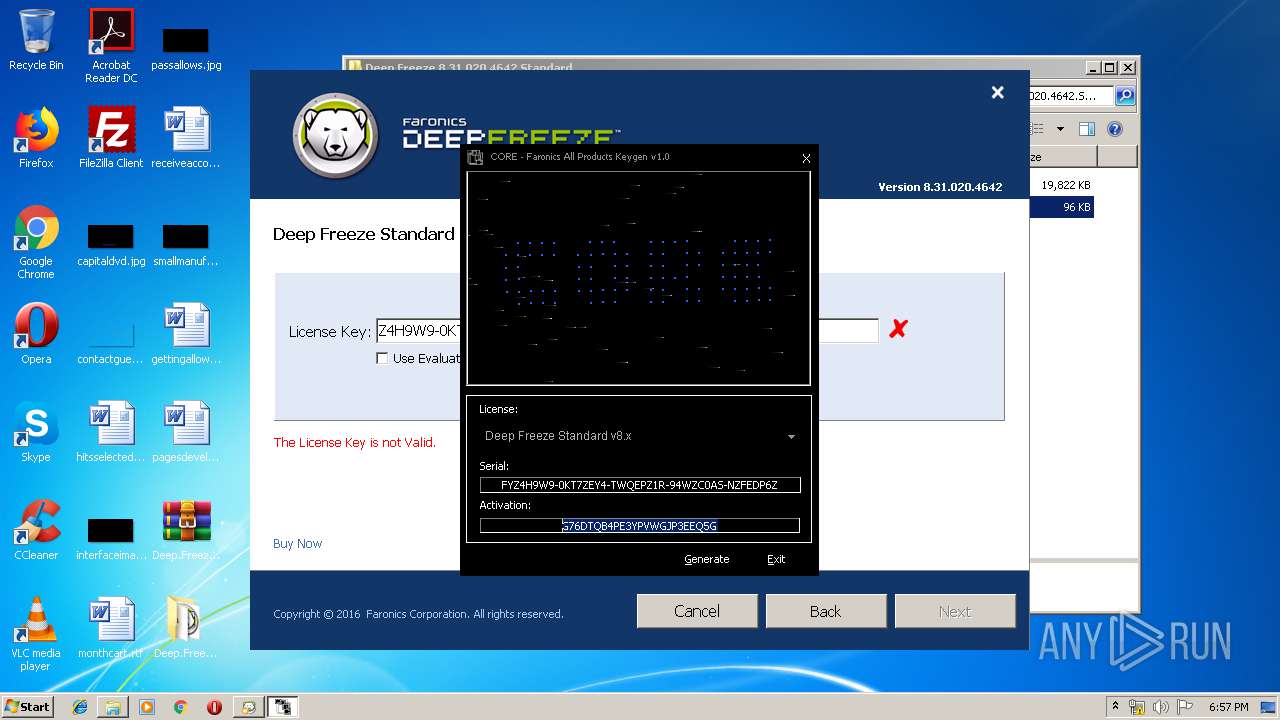
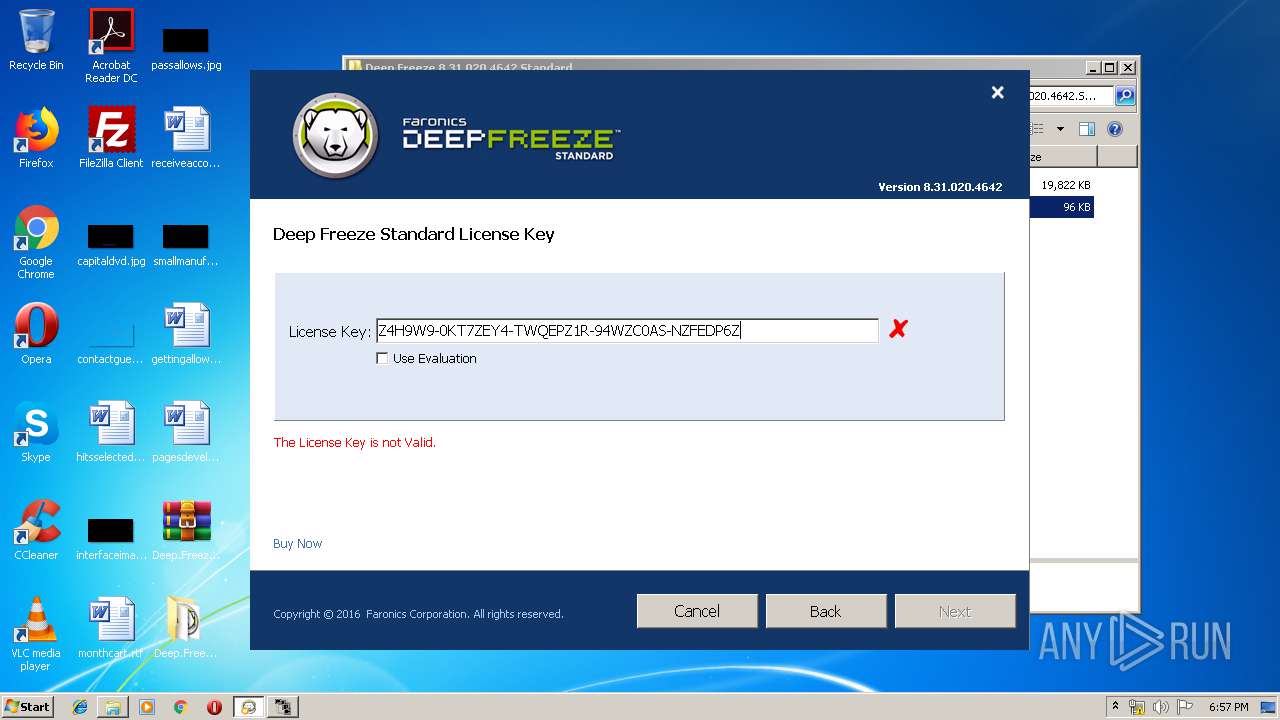
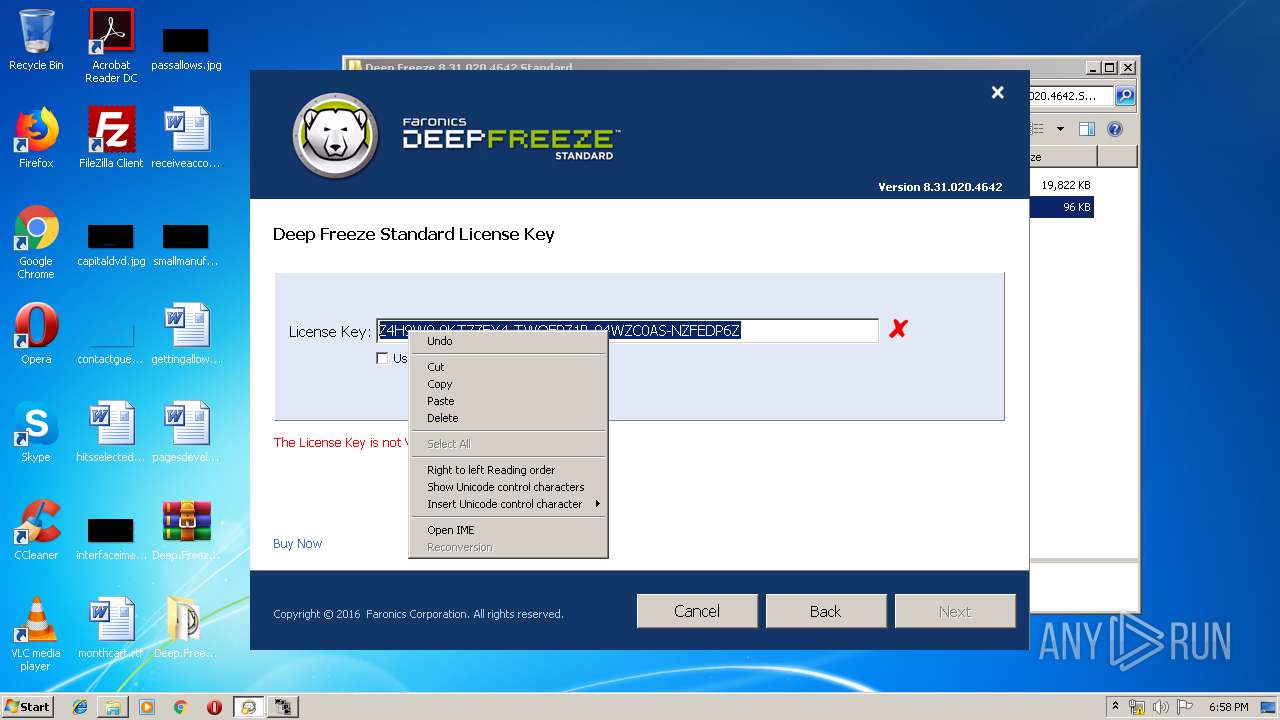
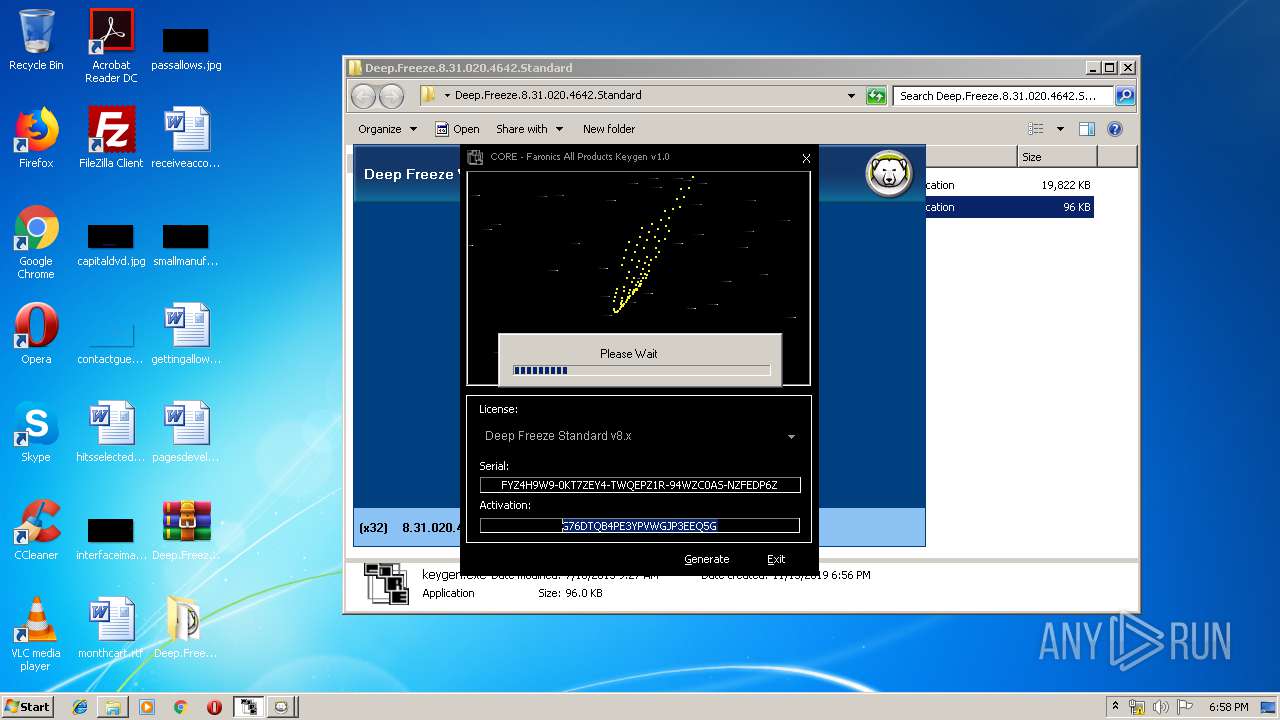
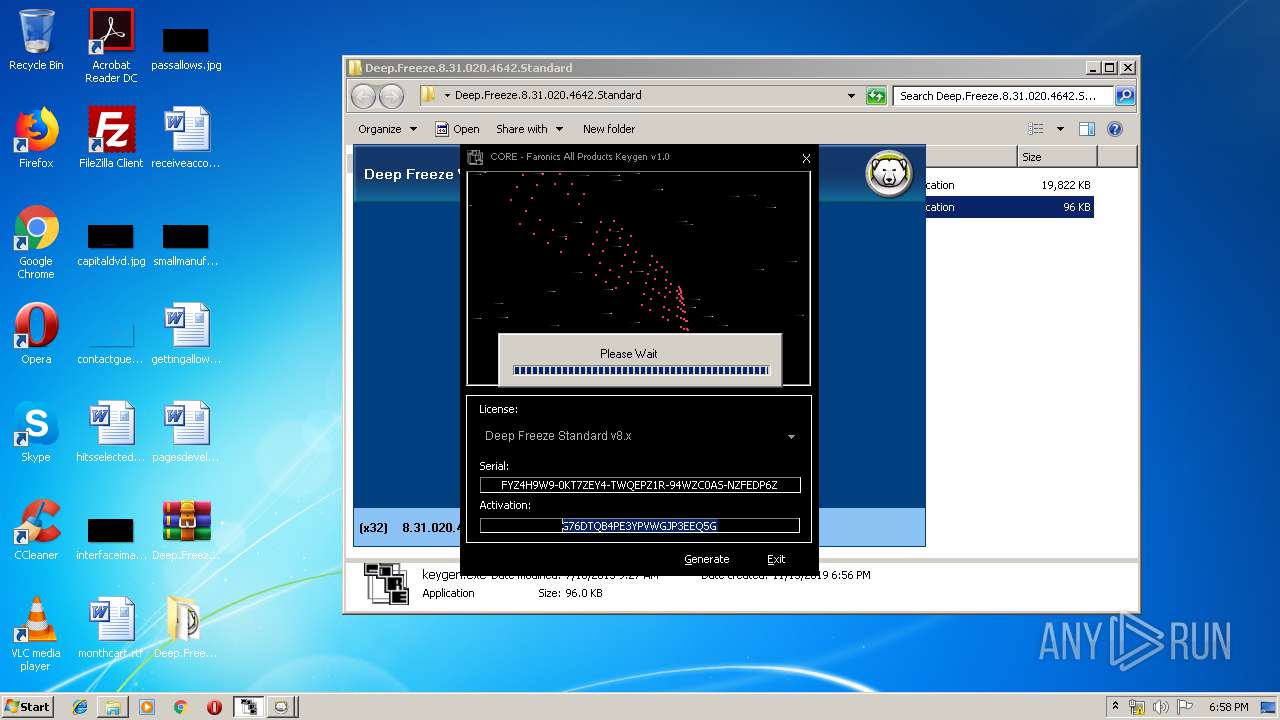
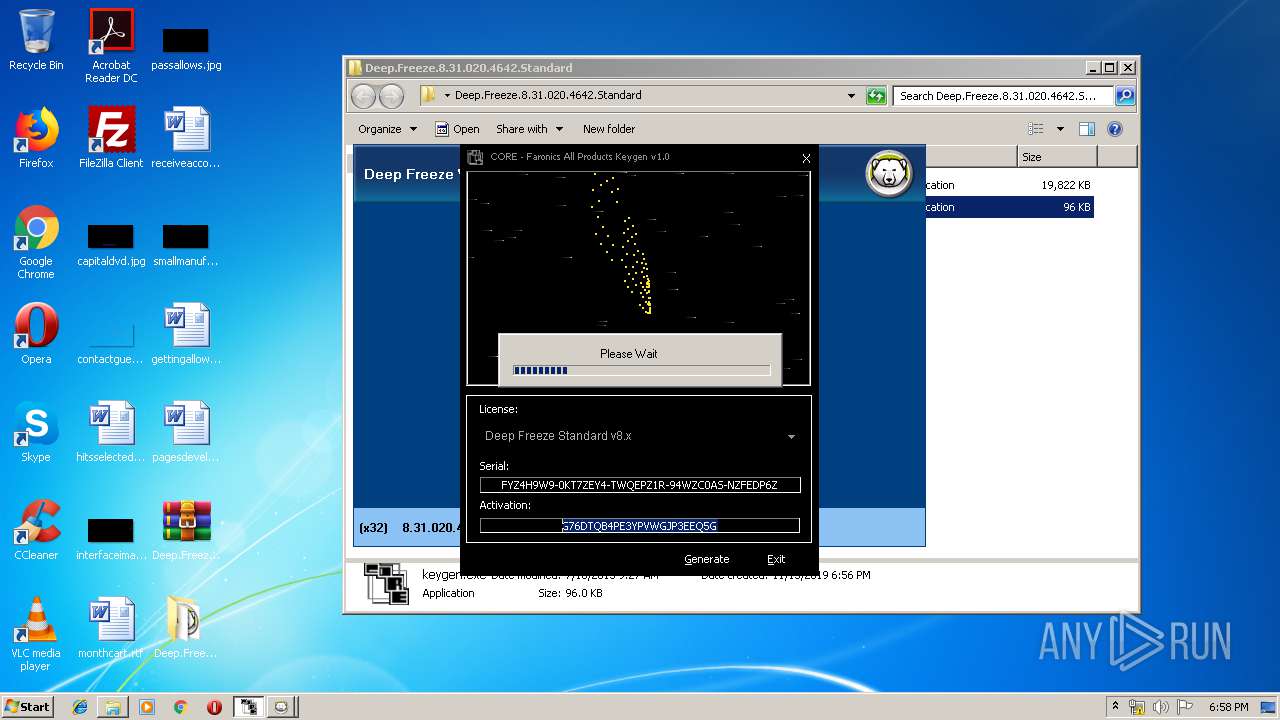
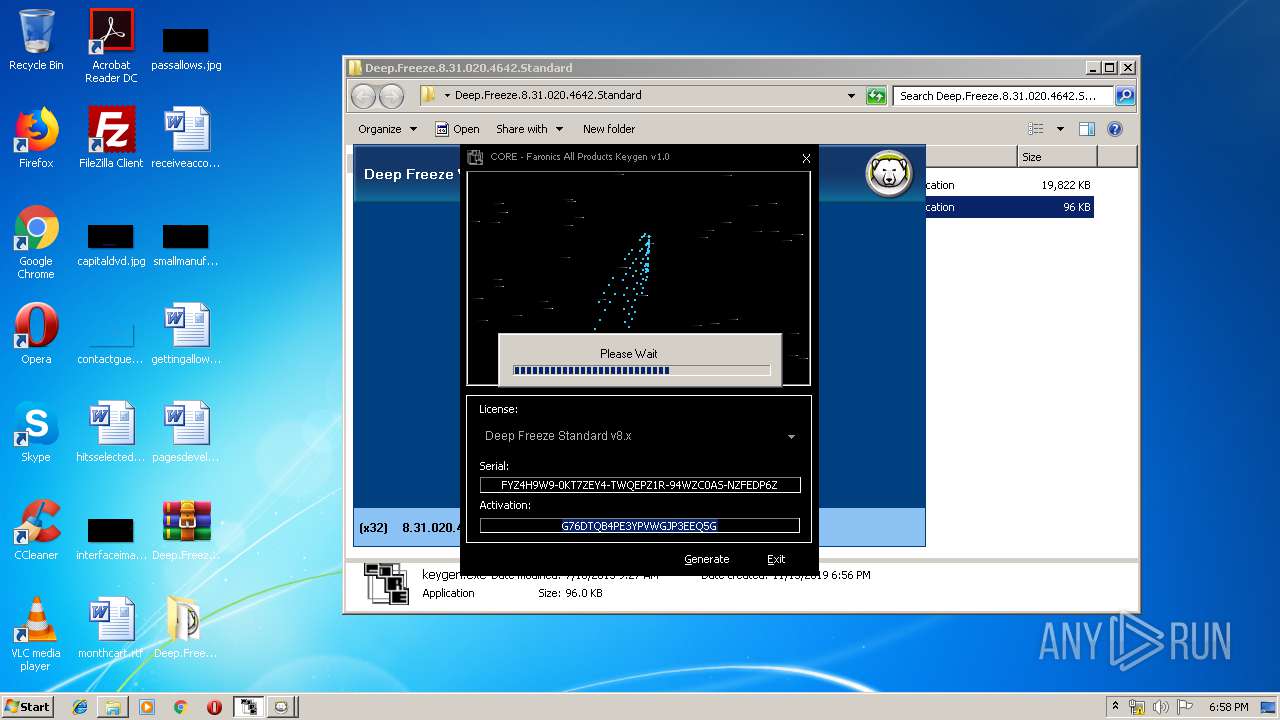
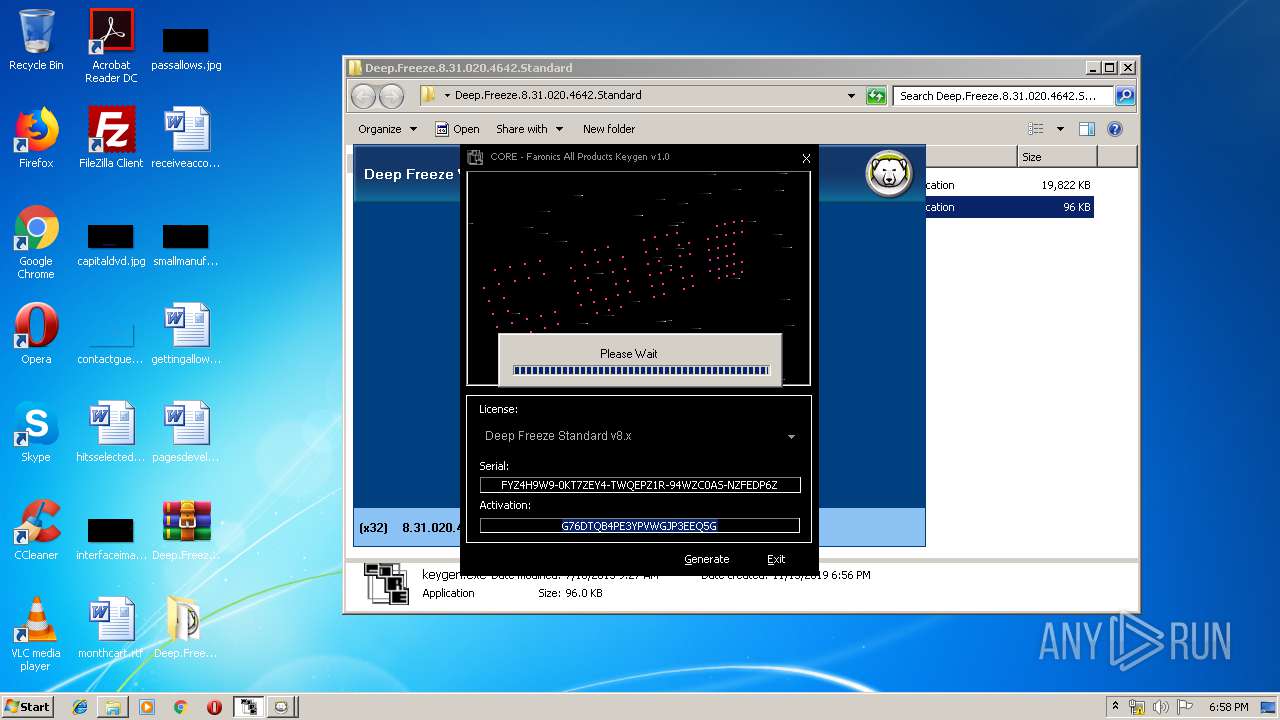
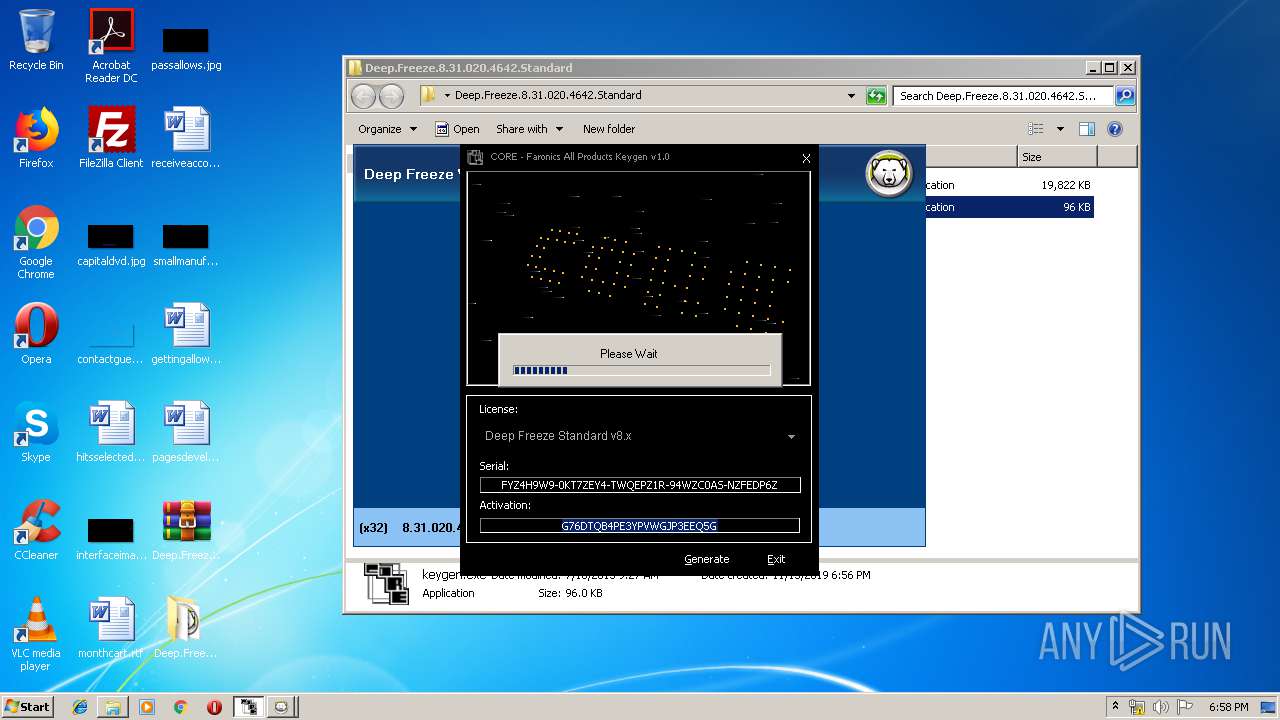
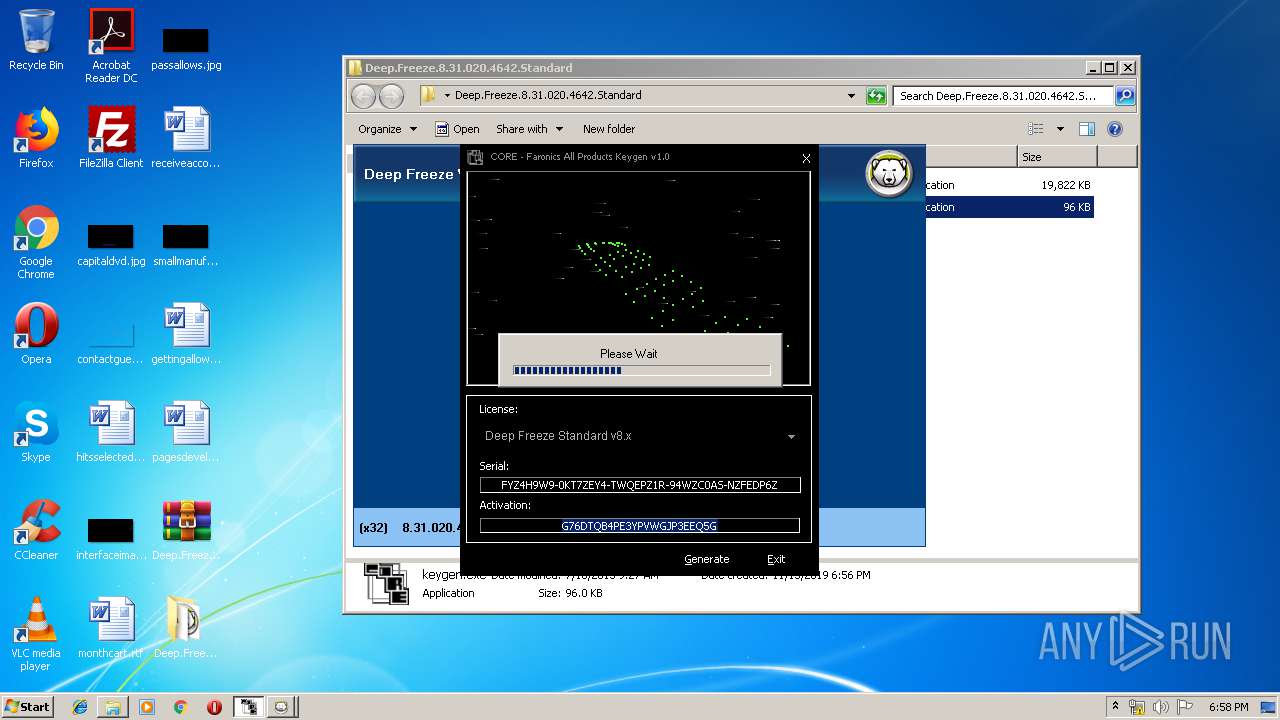
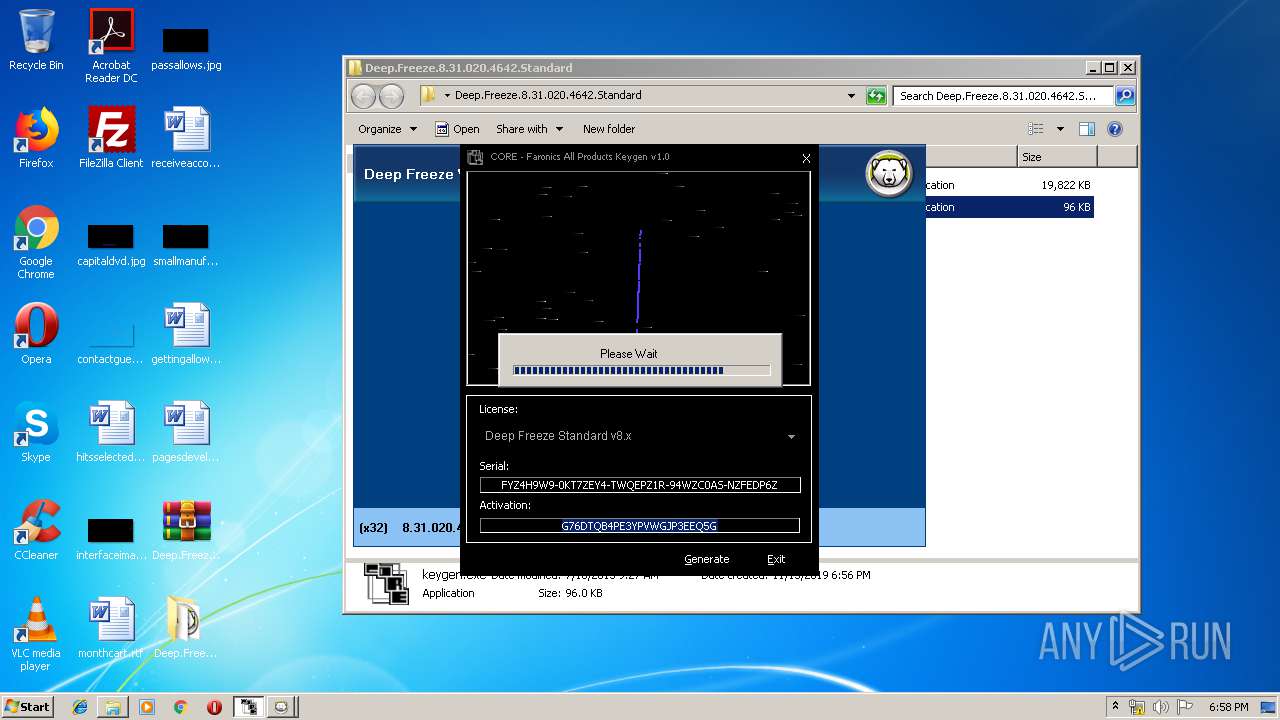
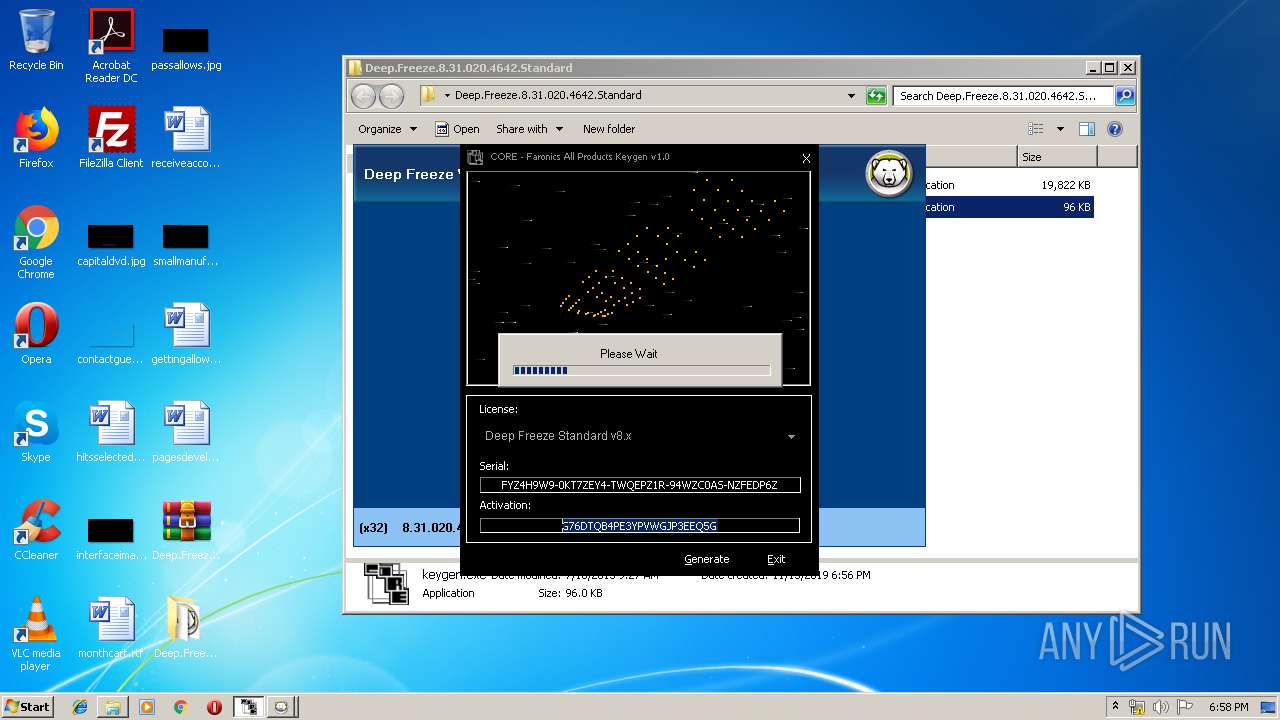
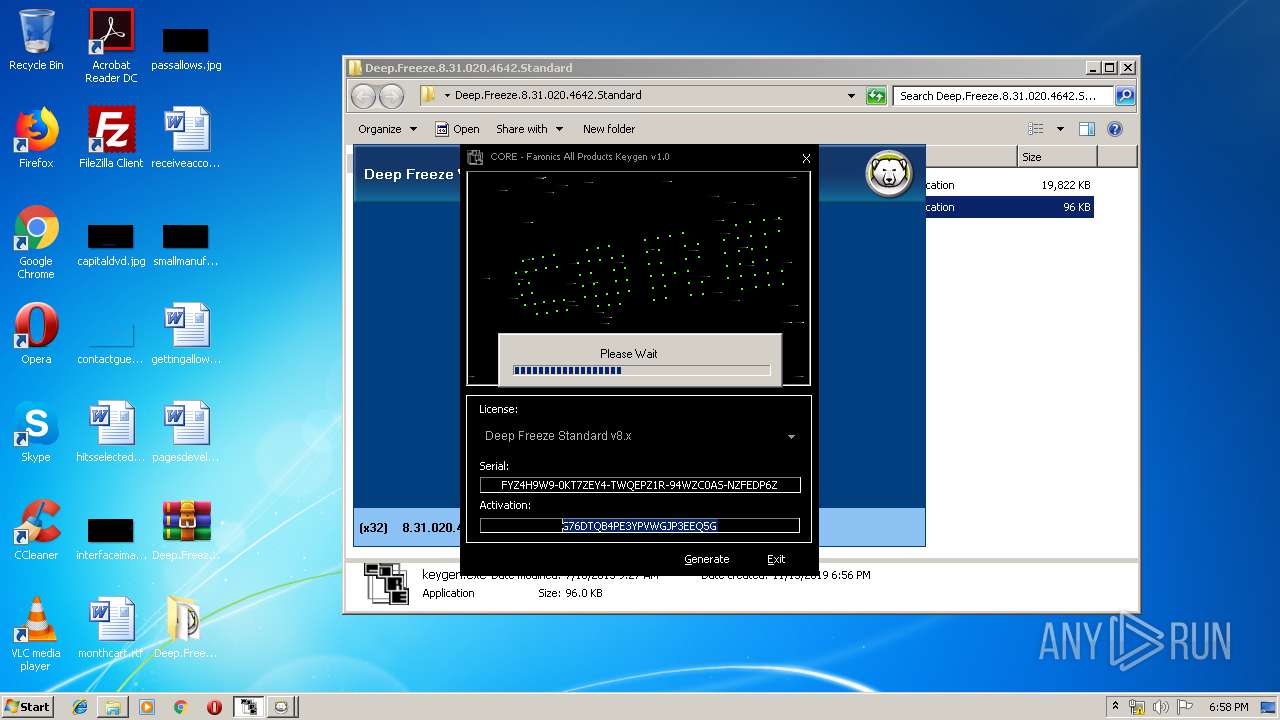
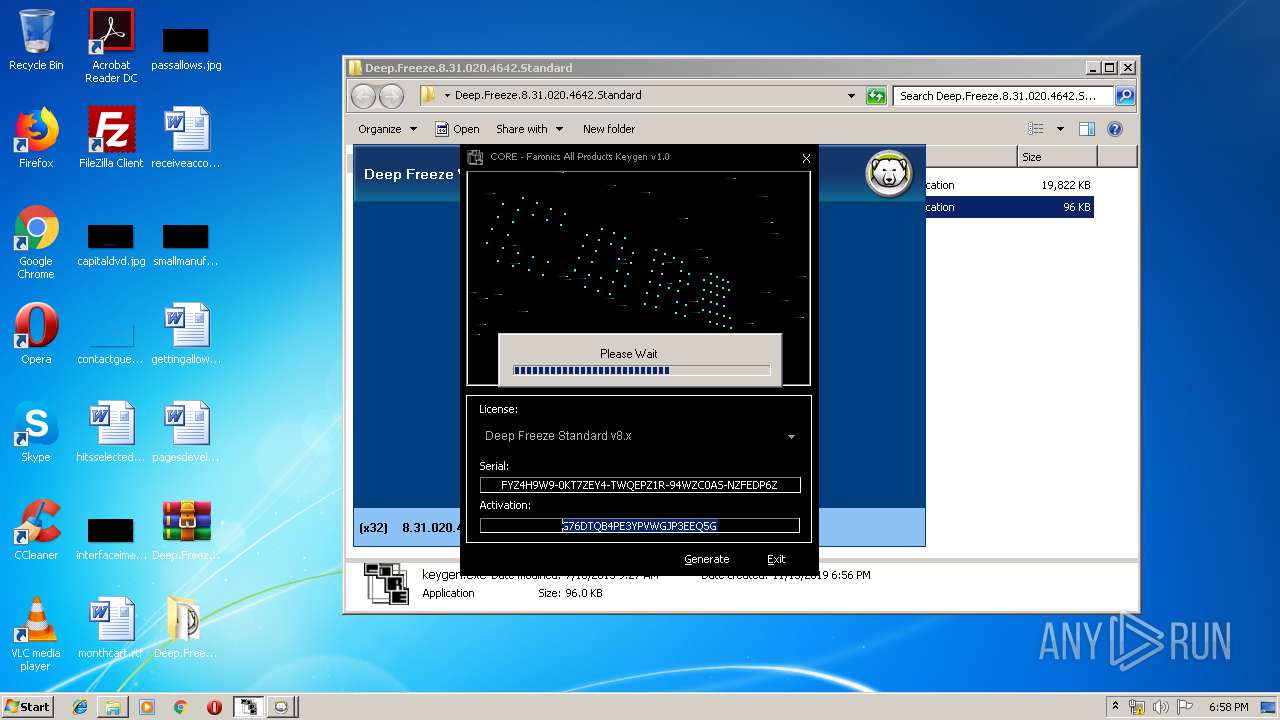
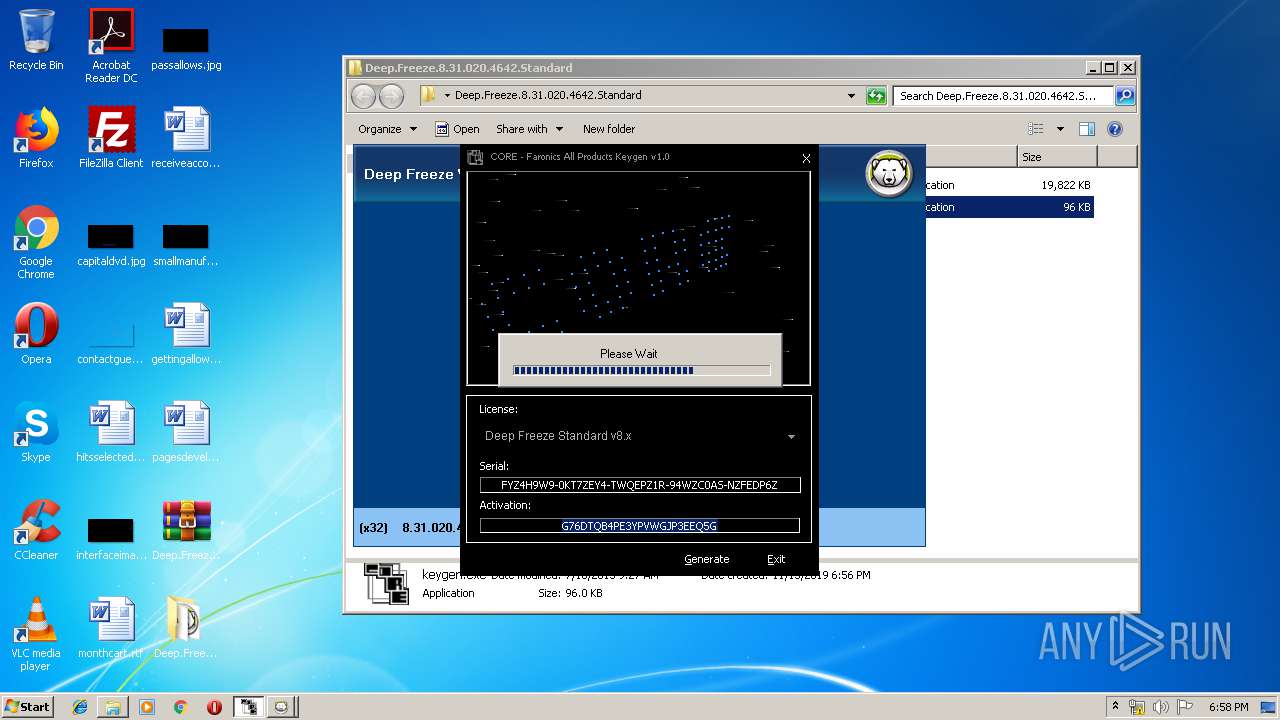
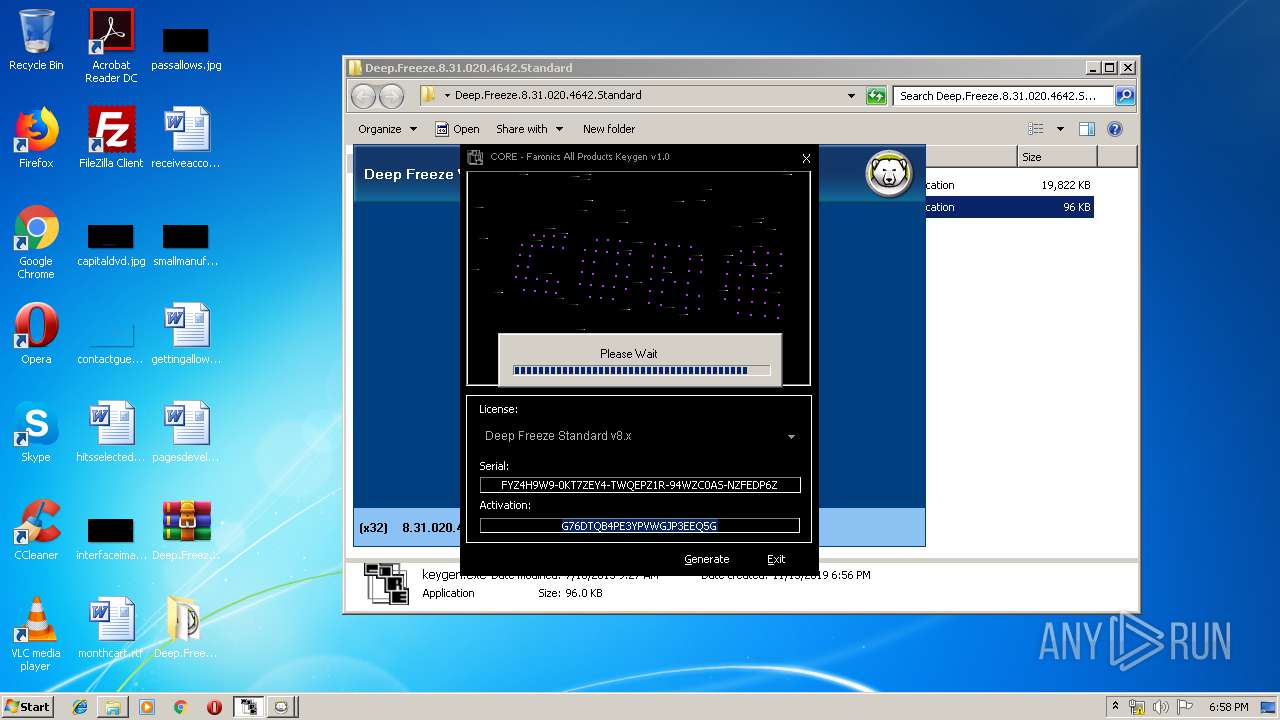
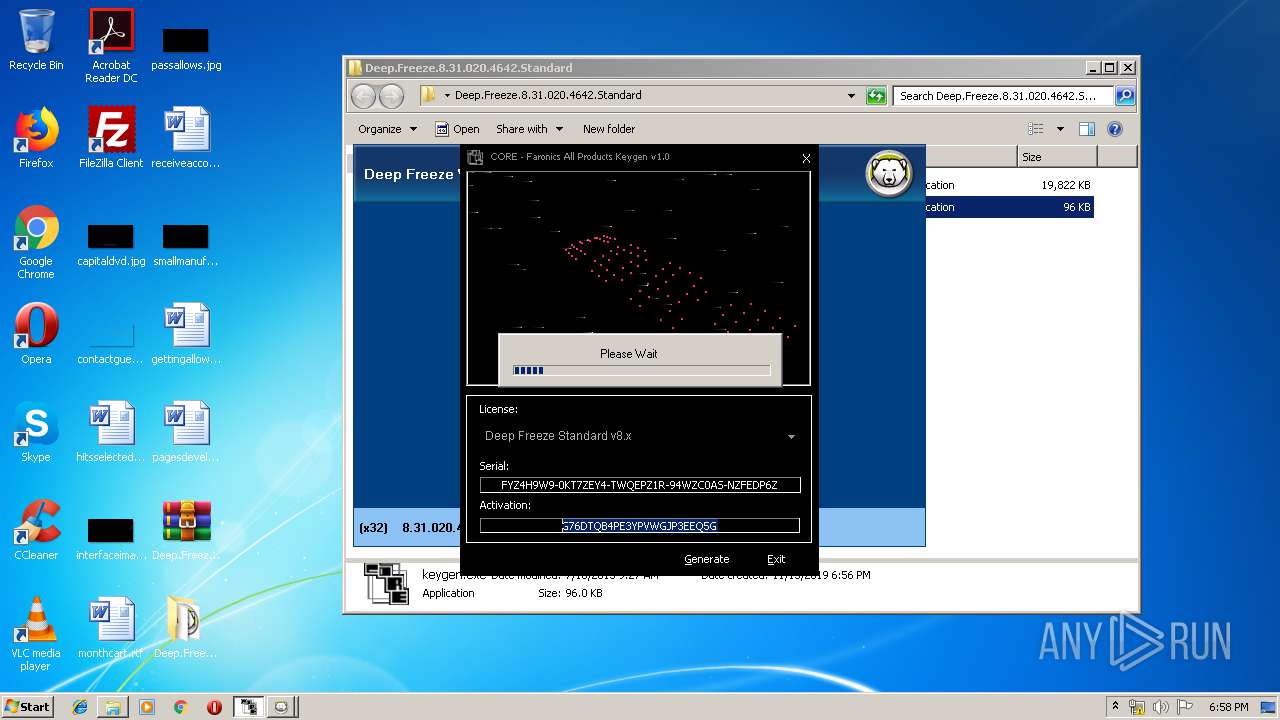
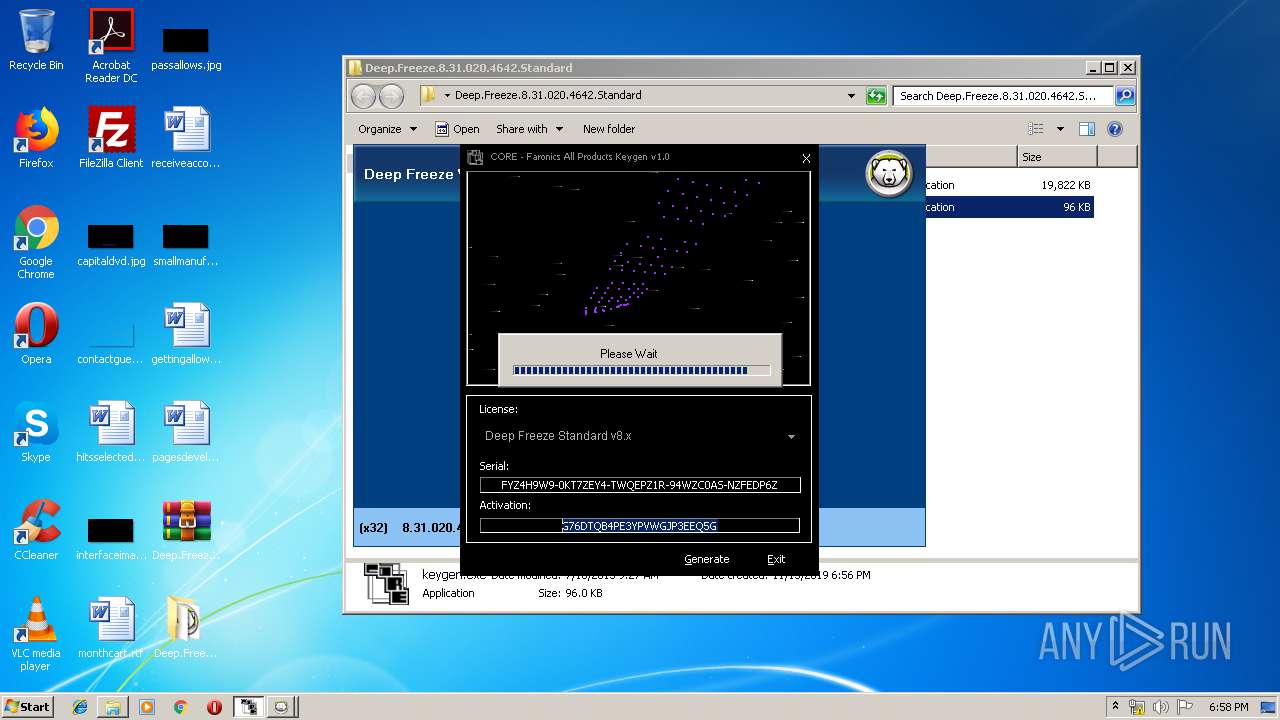
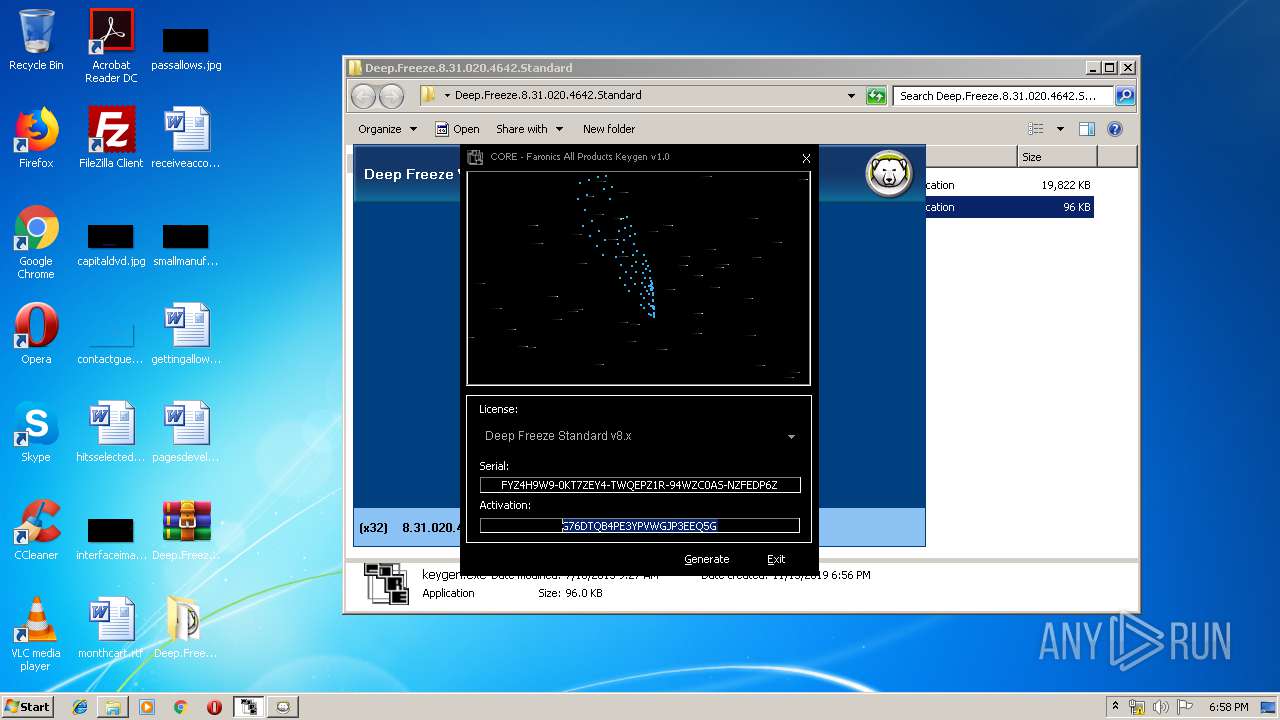
Manual execution by user
- keygen.exe (PID: 3780)
- DFStd.exe (PID: 2084)
- DFStd.exe (PID: 956)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v-4.x) (58.3) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (41.6) |
EXIF
ZIP
| CompressedSize: | 94668 |
|---|---|
| UncompressedSize: | 98304 |
| OperatingSystem: | Win32 |
| ModifyDate: | 2015:07:18 09:27:07 |
| PackingMethod: | Normal |
| ArchivedFileName: | keygen.exe |
Total processes
54
Monitored processes
8
Malicious processes
3
Suspicious processes
1
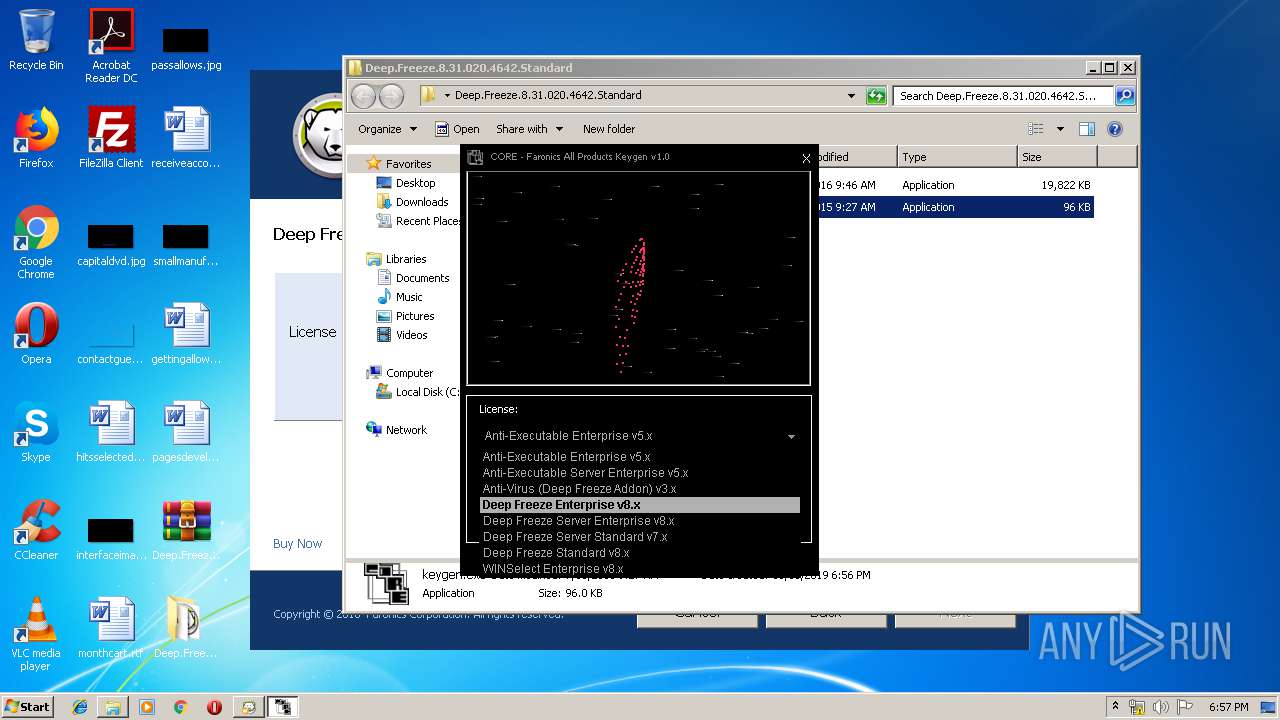
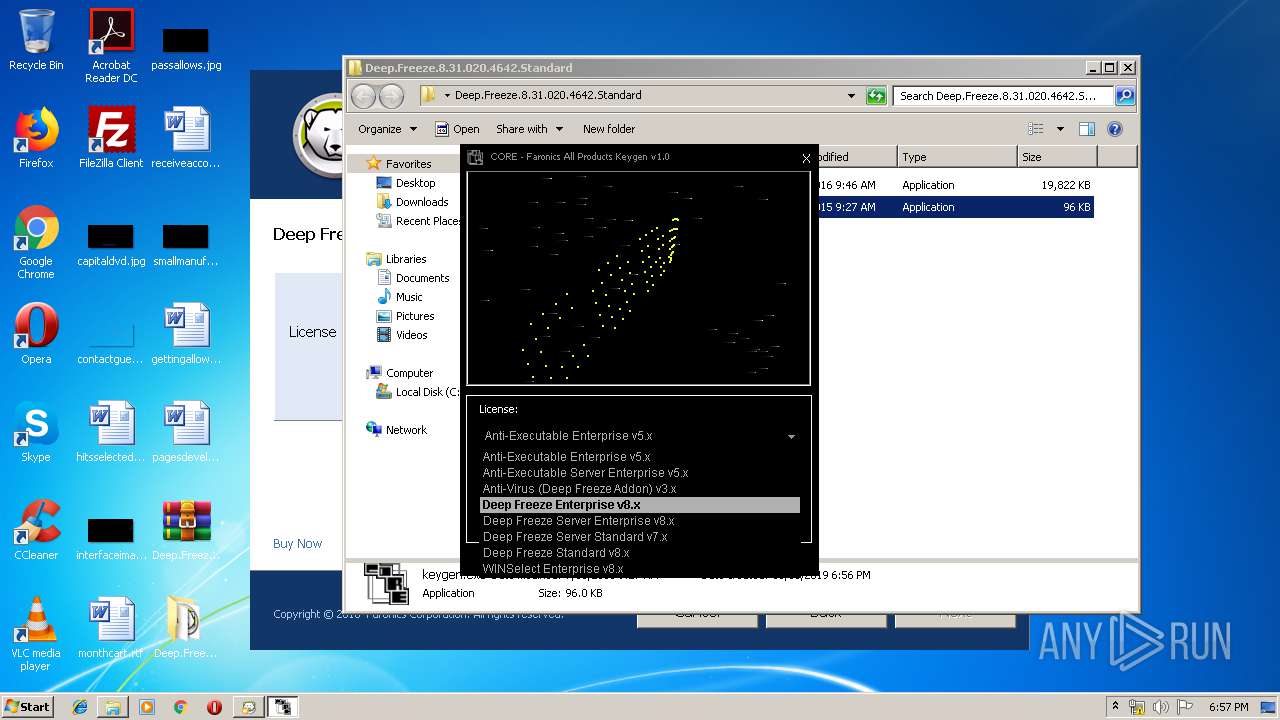
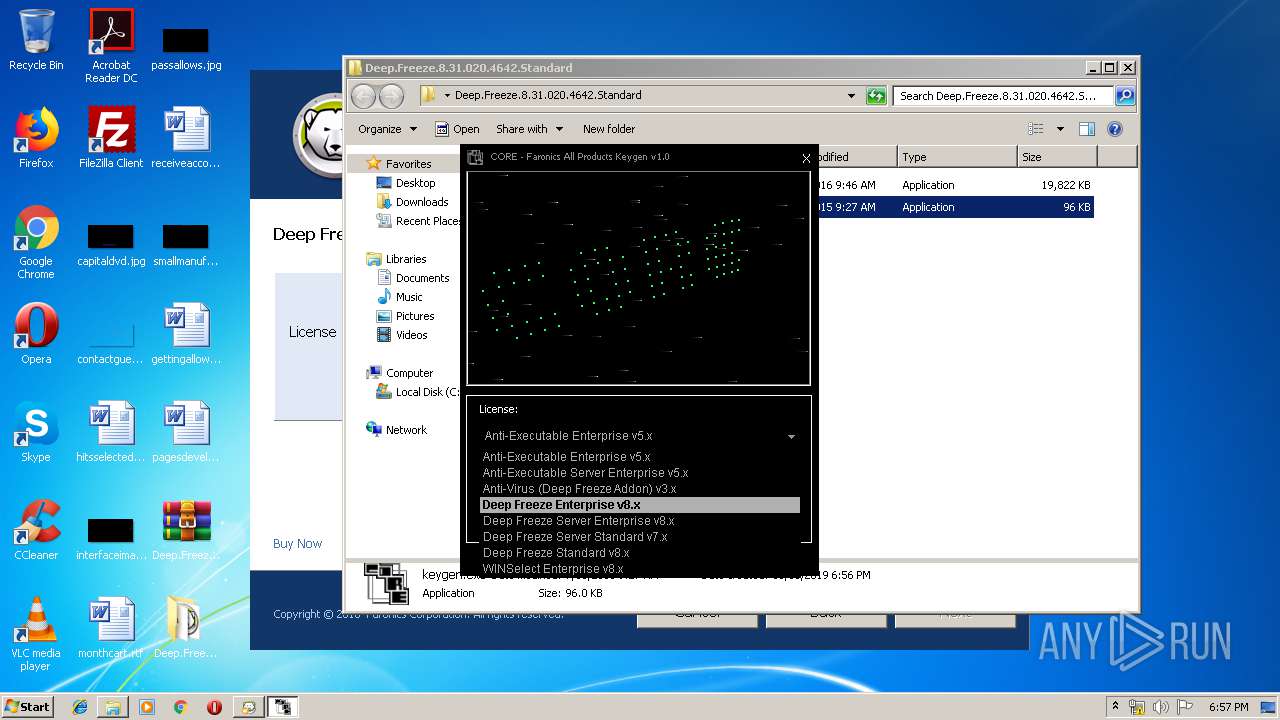
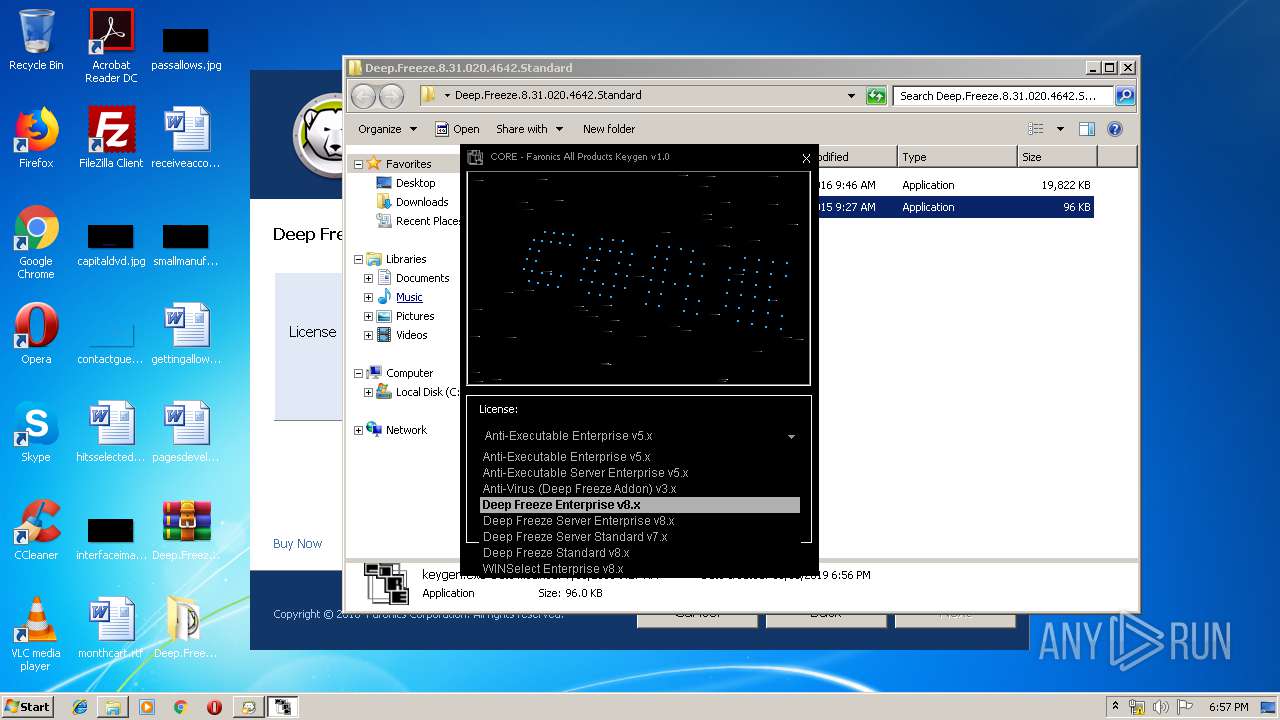
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Faronics\Deep Freeze\Install C-0\DFServ.exe" /INSTALL /SILENT | C:\Program Files\Faronics\Deep Freeze\Install C-0\DFServ.exe | — | DeepFreeze_C.exe | |||||||||||
User: admin Company: Faronics Corporation Integrity Level: HIGH Description: Deep Freeze service Exit code: 0 Version: 8,31,20,4642 Modules
| |||||||||||||||
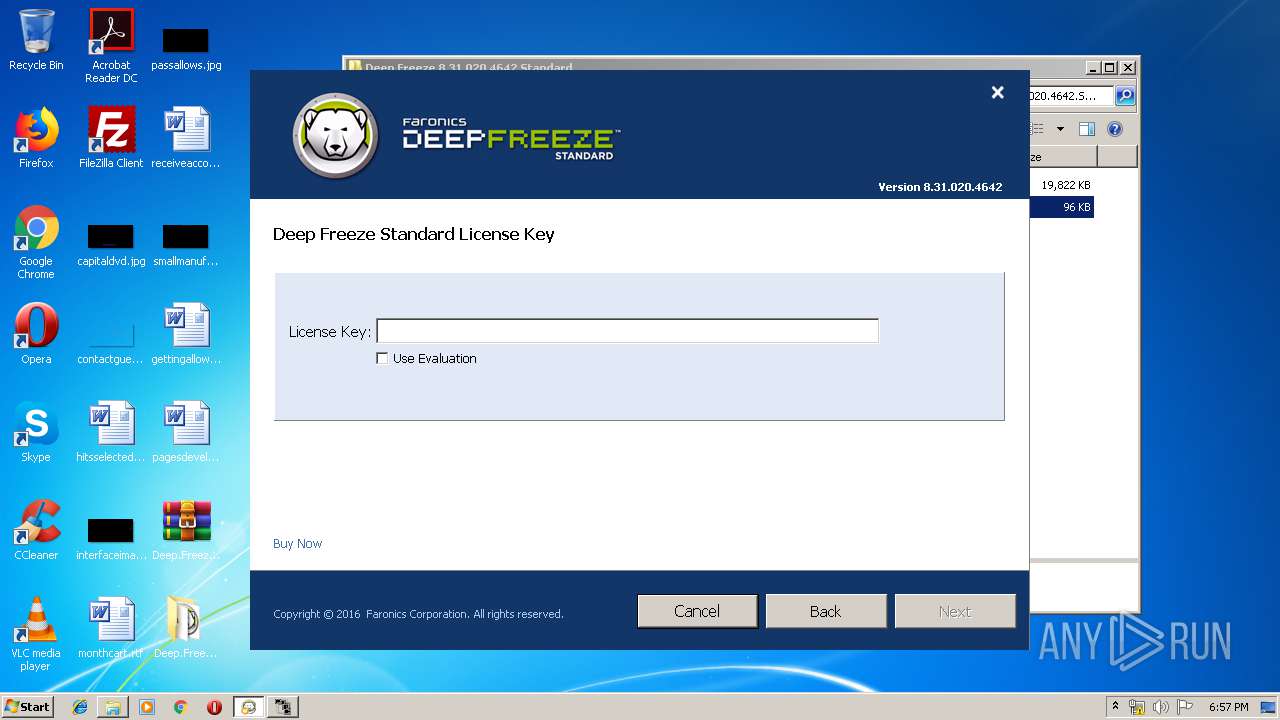
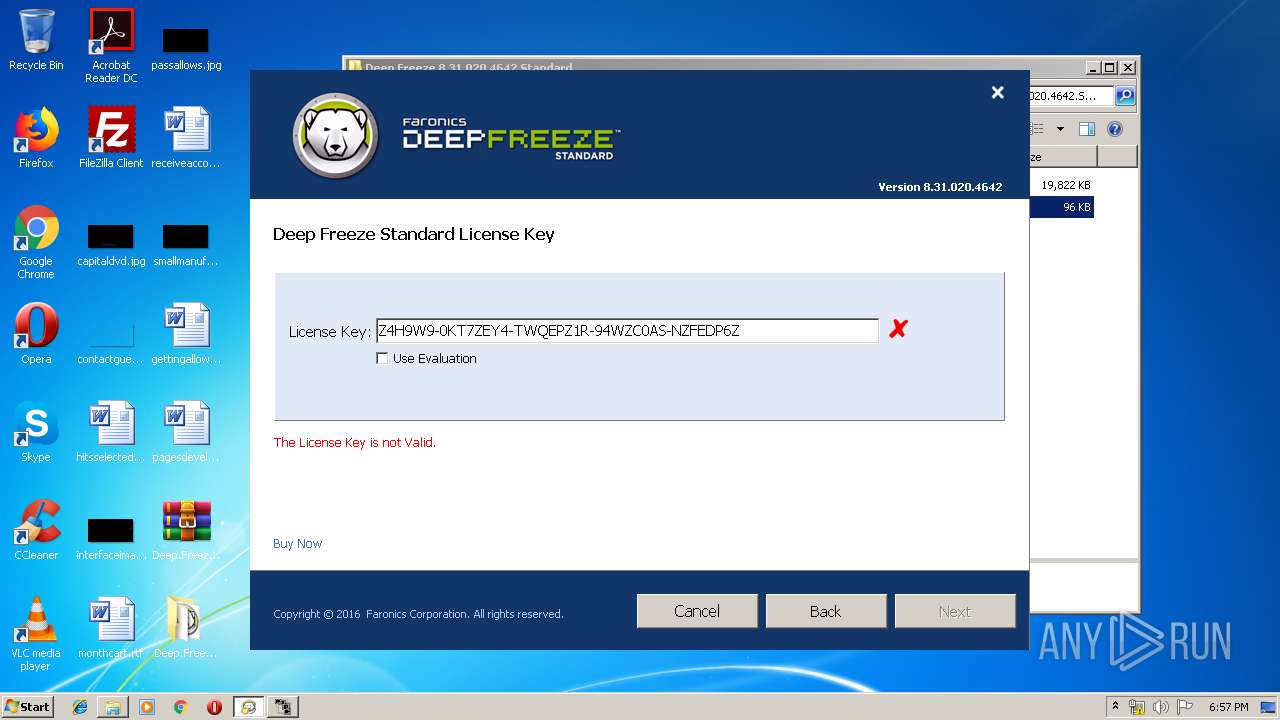
| 956 | "C:\Users\admin\Desktop\Deep.Freeze.8.31.020.4642.Standard\DFStd.exe" | C:\Users\admin\Desktop\Deep.Freeze.8.31.020.4642.Standard\DFStd.exe | — | explorer.exe | |||||||||||
User: admin Company: Faronics Corporation Integrity Level: MEDIUM Description: Install program for Deep Freeze Standard Exit code: 3221226540 Version: 8,31,20,4642 Modules
| |||||||||||||||
| 2084 | "C:\Users\admin\Desktop\Deep.Freeze.8.31.020.4642.Standard\DFStd.exe" | C:\Users\admin\Desktop\Deep.Freeze.8.31.020.4642.Standard\DFStd.exe | explorer.exe | ||||||||||||
User: admin Company: Faronics Corporation Integrity Level: HIGH Description: Install program for Deep Freeze Standard Exit code: 0 Version: 8,31,20,4642 Modules
| |||||||||||||||
| 2668 | C:\Users\admin\AppData\Local\Temp\DeepFreeze_C.exe /silent /nocloudagent | C:\Users\admin\AppData\Local\Temp\DeepFreeze_C.exe | DFStd.exe | ||||||||||||
User: admin Company: Faronics Corporation Integrity Level: HIGH Description: Workstation install program for Deep Freeze Cloud Exit code: 1073807364 Version: 8,31,20,4642 Modules
| |||||||||||||||
| 3548 | C:\Windows\system32\regsvr32.exe /s /u "C:\Program Files\Faronics\Deep Freeze\Install C-0\DeepFreezeAdapter.dll" | C:\Windows\system32\regsvr32.exe | — | DeepFreeze_C.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 5 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3780 | "C:\Users\admin\Desktop\Deep.Freeze.8.31.020.4642.Standard\keygen.exe" | C:\Users\admin\Desktop\Deep.Freeze.8.31.020.4642.Standard\keygen.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1073807364 Modules
| |||||||||||||||
| 3968 | C:\Windows\system32\regsvr32.exe /s "C:\Program Files\Faronics\Deep Freeze\Install C-0\DeepFreezeAdapter.dll" | C:\Windows\system32\regsvr32.exe | — | DeepFreeze_C.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
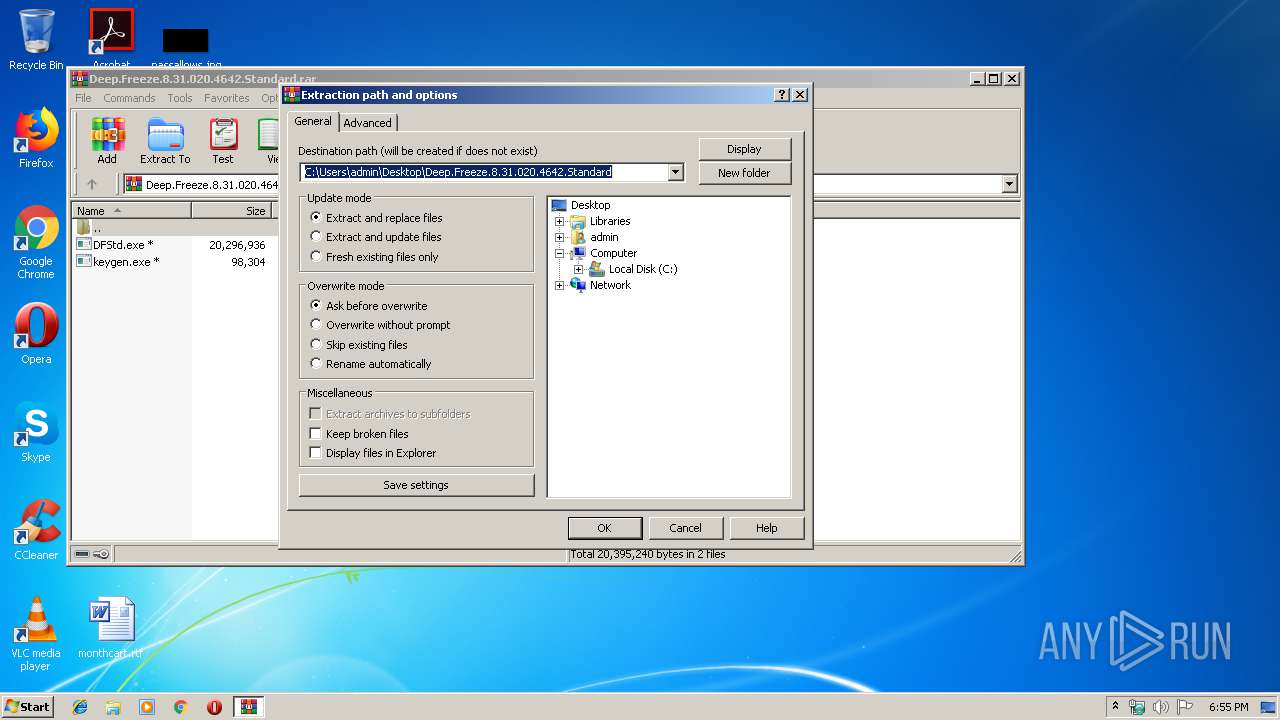
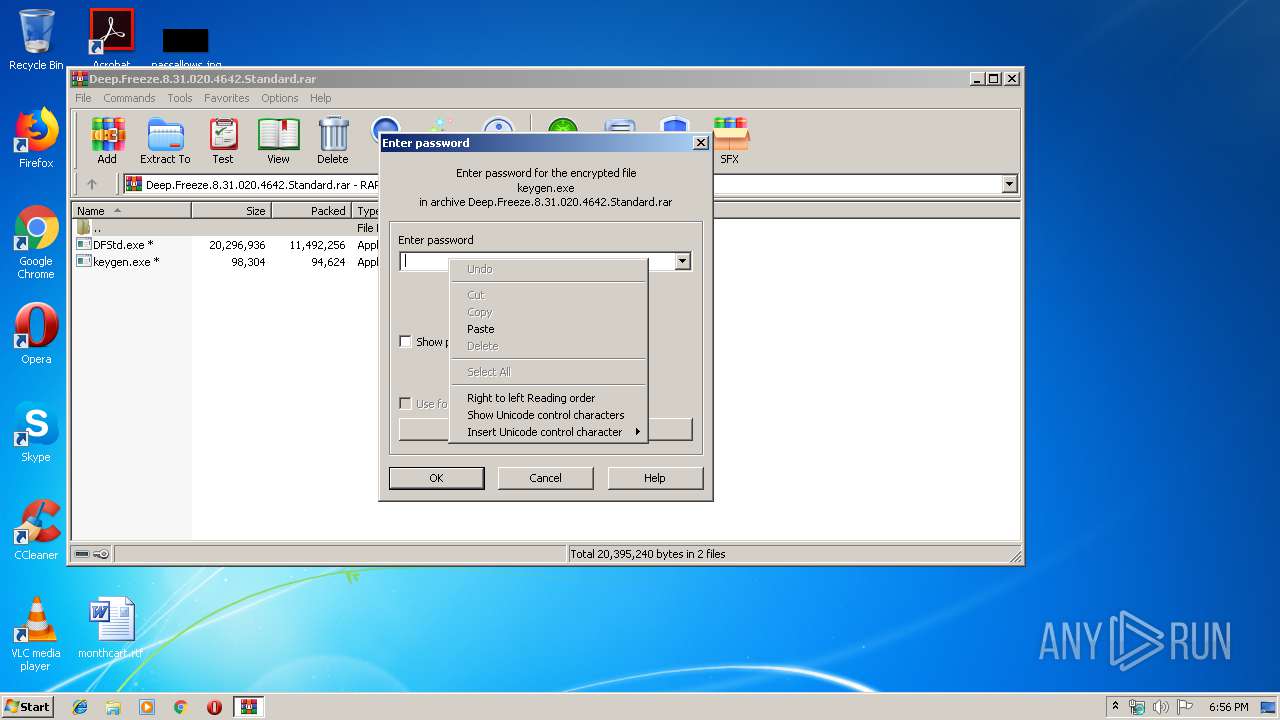
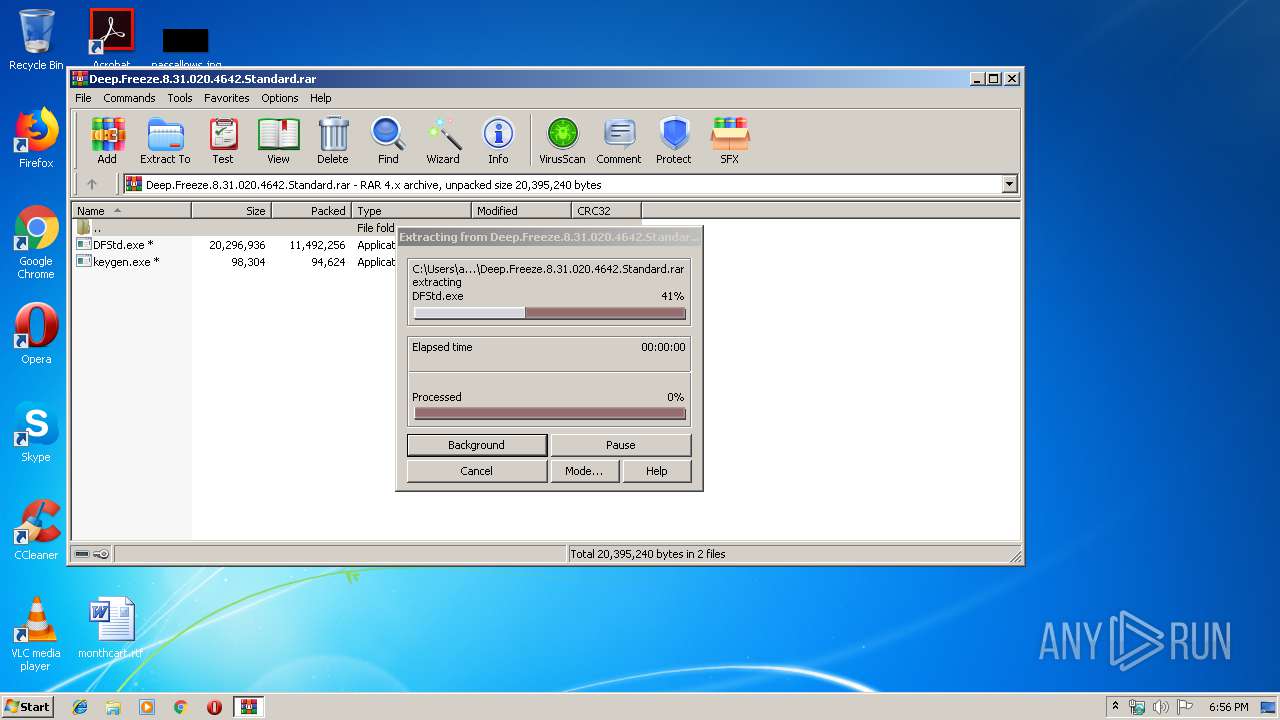
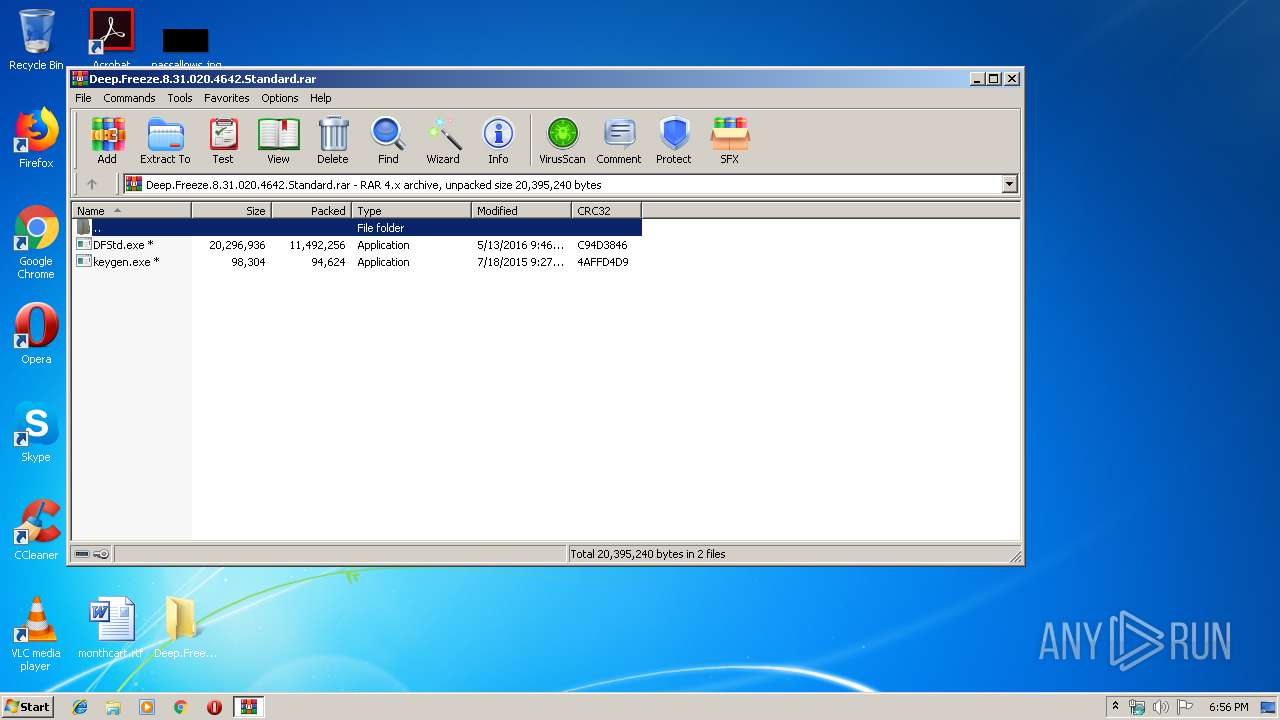
| 4012 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\Deep.Freeze.8.31.020.4642.Standard.rar" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
481
Read events
406
Write events
70
Delete events
5
Modification events
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Deep.Freeze.8.31.020.4642.Standard.rar | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\DialogEditHistory\ExtrPath |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Deep.Freeze.8.31.020.4642.Standard | |||
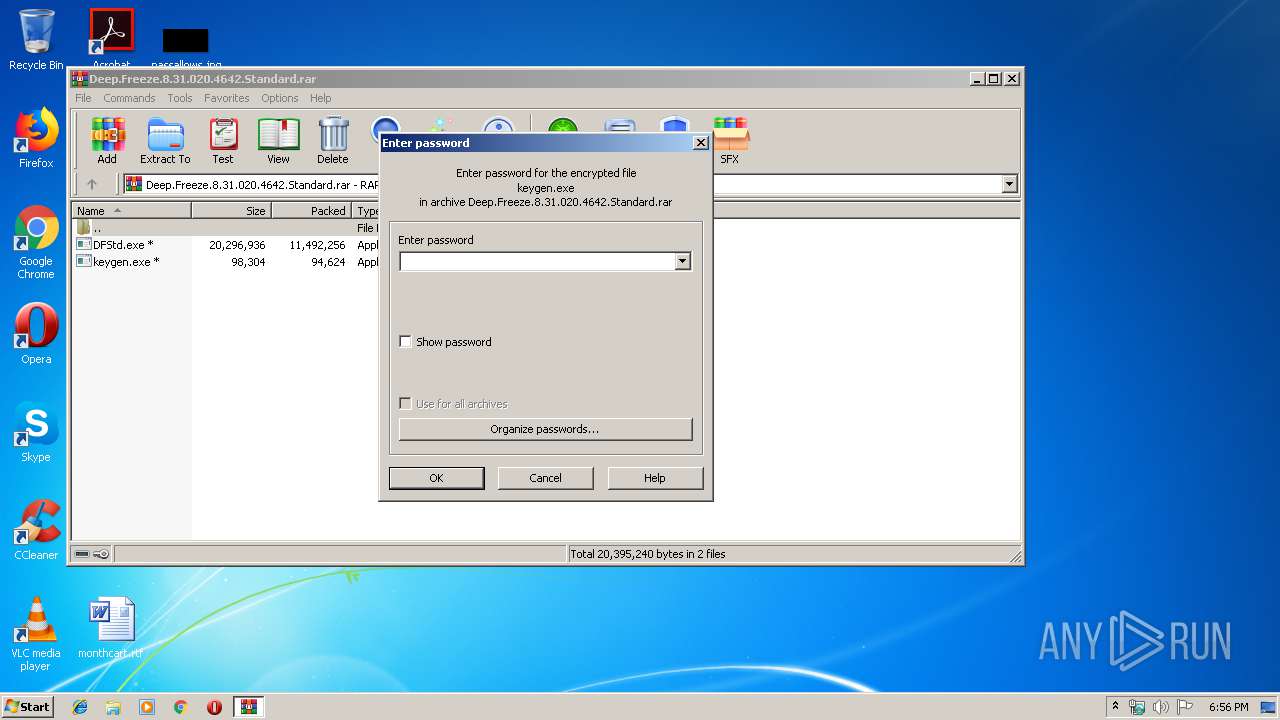
| (PID) Process: | (4012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
17
Suspicious files
5
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3780 | keygen.exe | C:\Users\admin\AppData\Local\Temp\Test.dat | — | |
MD5:— | SHA256:— | |||
| 2084 | DFStd.exe | C:\Users\admin\Desktop\Deep.Freeze.8.31.020.4642.Standard\$depfrz.rdx | — | |
MD5:— | SHA256:— | |||
| 2084 | DFStd.exe | C:\Users\admin\AppData\Local\Temp\dftemp{A787A7F2-A735-4C96-B71B-7E4DDEC5C0A9}\$depfrz.rdx | — | |
MD5:— | SHA256:— | |||
| 2668 | DeepFreeze_C.exe | C:\Users\admin\AppData\Local\Temp\DF5EADE.tmp\DFFilter.sys | executable | |
MD5:— | SHA256:— | |||
| 2084 | DFStd.exe | C:\Users\admin\AppData\Local\Temp\DeepFreeze_C.exe | executable | |
MD5:— | SHA256:— | |||
| 4012 | WinRAR.exe | C:\Users\admin\Desktop\Deep.Freeze.8.31.020.4642.Standard\DFStd.exe | executable | |
MD5:— | SHA256:— | |||
| 2668 | DeepFreeze_C.exe | C:\Users\admin\AppData\Local\Temp\_$Df\DFCloudWks.sib | binary | |
MD5:— | SHA256:— | |||
| 2668 | DeepFreeze_C.exe | C:\Users\admin\AppData\Local\Temp\DF5EADE.tmp\DepFrz.rdx | binary | |
MD5:— | SHA256:— | |||
| 2668 | DeepFreeze_C.exe | C:\Users\admin\AppData\Local\Temp\DF5EADE.tmp\DFServ.exe | executable | |
MD5:— | SHA256:— | |||
| 2668 | DeepFreeze_C.exe | C:\Persi0.sys | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report