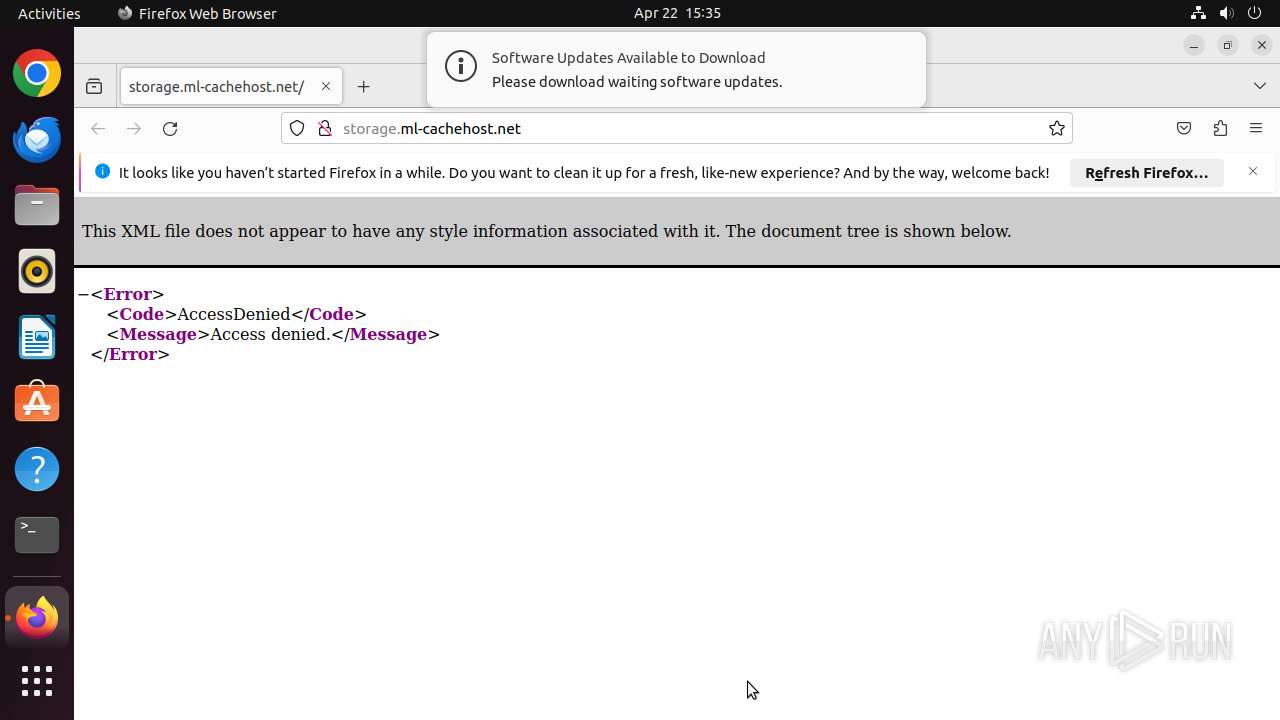
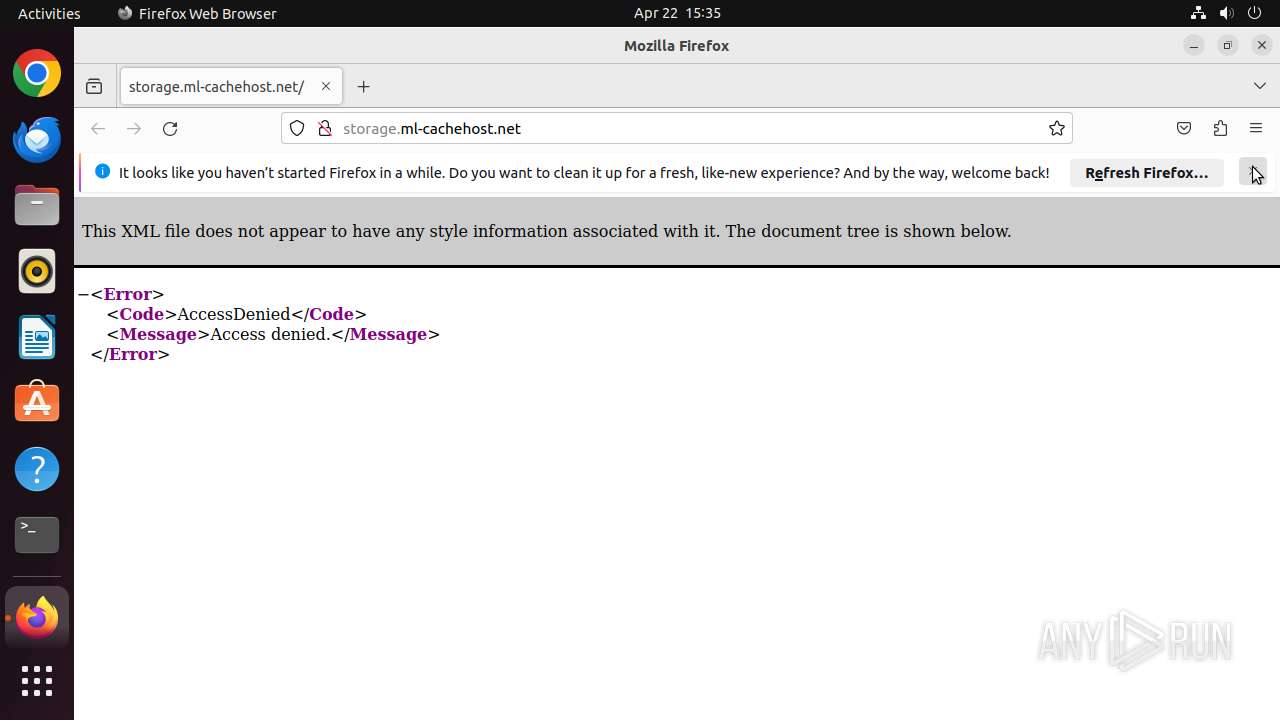
| URL: | storage.ml-cachehost.net |
| Full analysis: | https://app.any.run/tasks/63bdd0ca-a0db-4211-9884-c05cd874956d |
| Verdict: | Malicious activity |
| Analysis date: | April 22, 2025, 14:35:15 |
| OS: | Ubuntu 22.04.2 |
| MD5: | CACB097D5E8B7CA5D49FD492B89ED627 |
| SHA1: | B89DB9F43A4D3EA1A6F43F8604D4F9B82A213D2E |
| SHA256: | 6F34993A88565D369DAE496C81C925376E3B1F6B81EF49AD944A66068E6A2333 |
| SSDEEP: | 3:+wvS7R/0n:+dV/0 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Check the Environment Variables Related to System Identification (os-release)
- snapctl (PID: 40712)
- snapctl (PID: 40750)
- snapctl (PID: 40718)
- snapctl (PID: 40757)
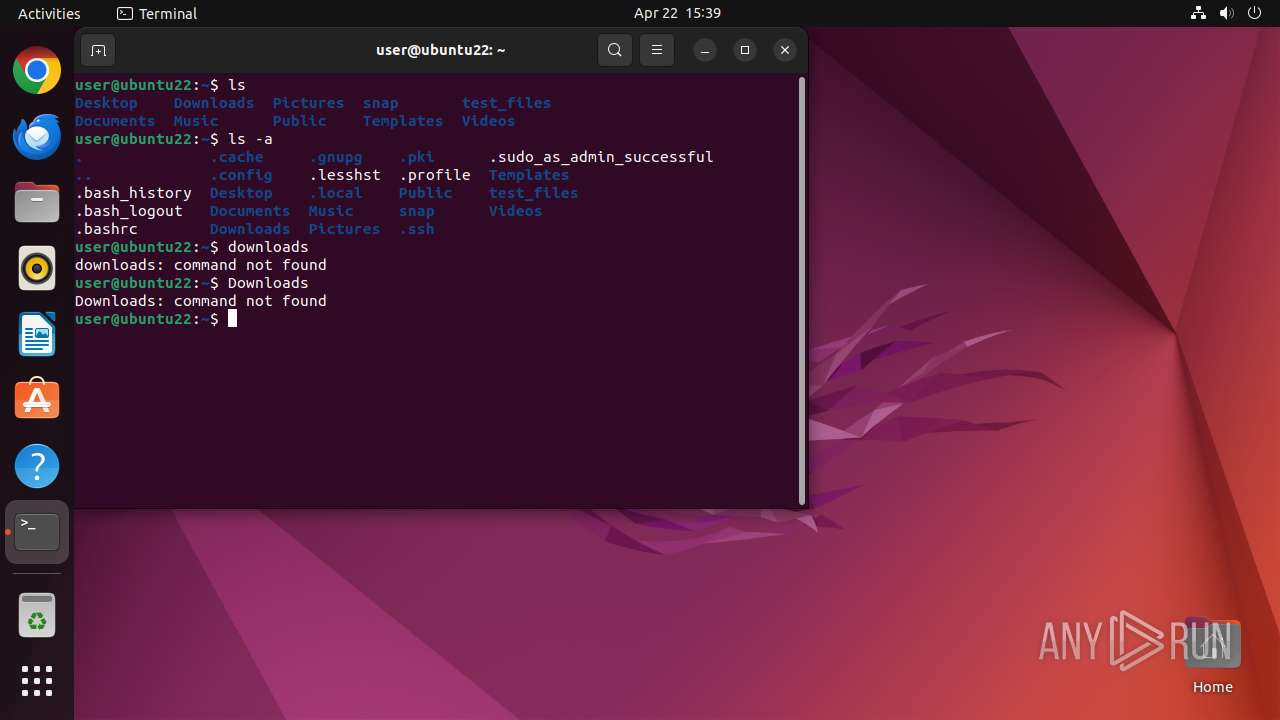
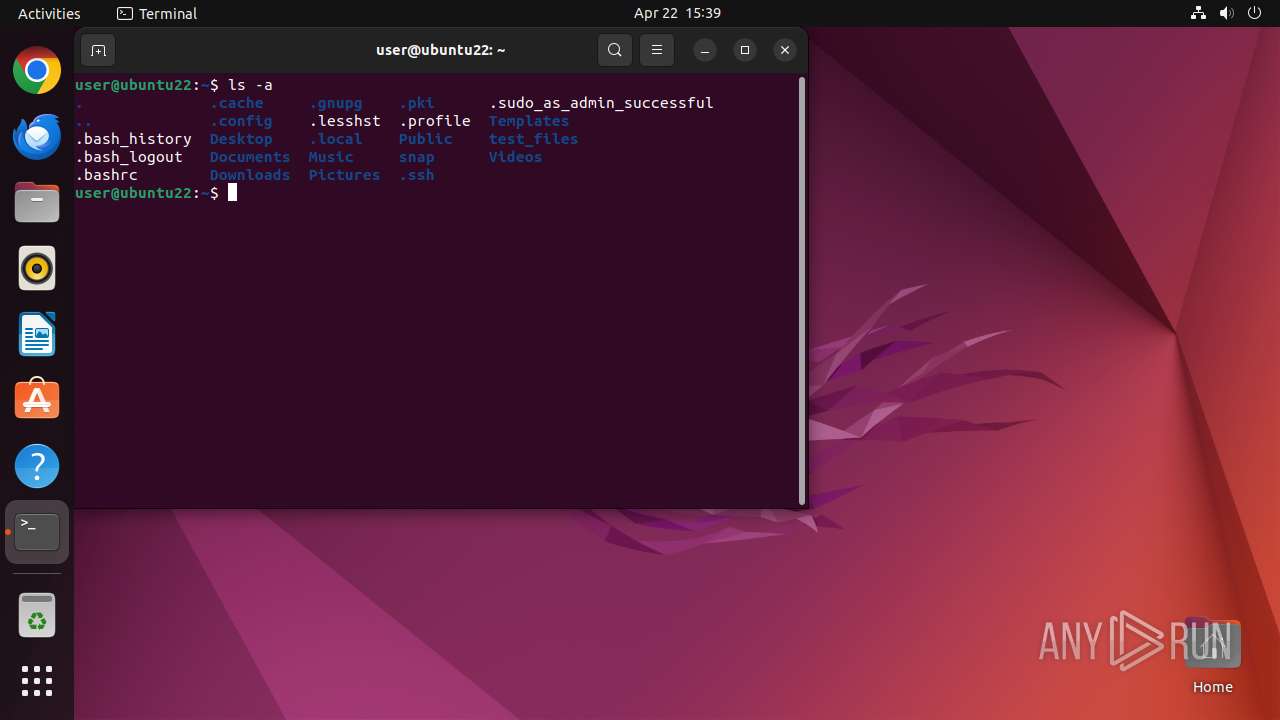
Executes commands using command-line interpreter
- sudo (PID: 40658)
- firefox (PID: 40659)
- gnome-terminal-server (PID: 41248)
Reads passwd file
- dumpe2fs (PID: 40690)
- dumpe2fs (PID: 40683)
- ls (PID: 41313)
INFO
Checks timezone
- dumpe2fs (PID: 40683)
- dumpe2fs (PID: 40690)
- python3.10 (PID: 41282)
- python3.10 (PID: 41241)
- python3.10 (PID: 41298)
- ls (PID: 41313)
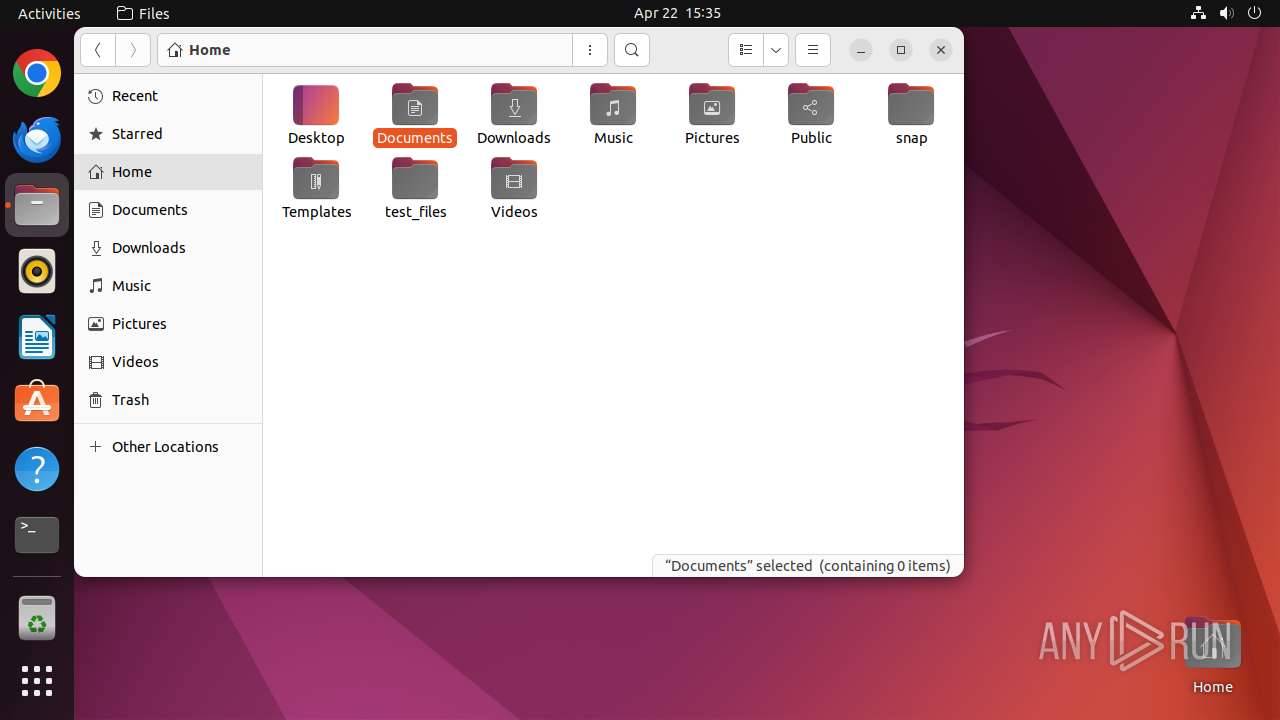
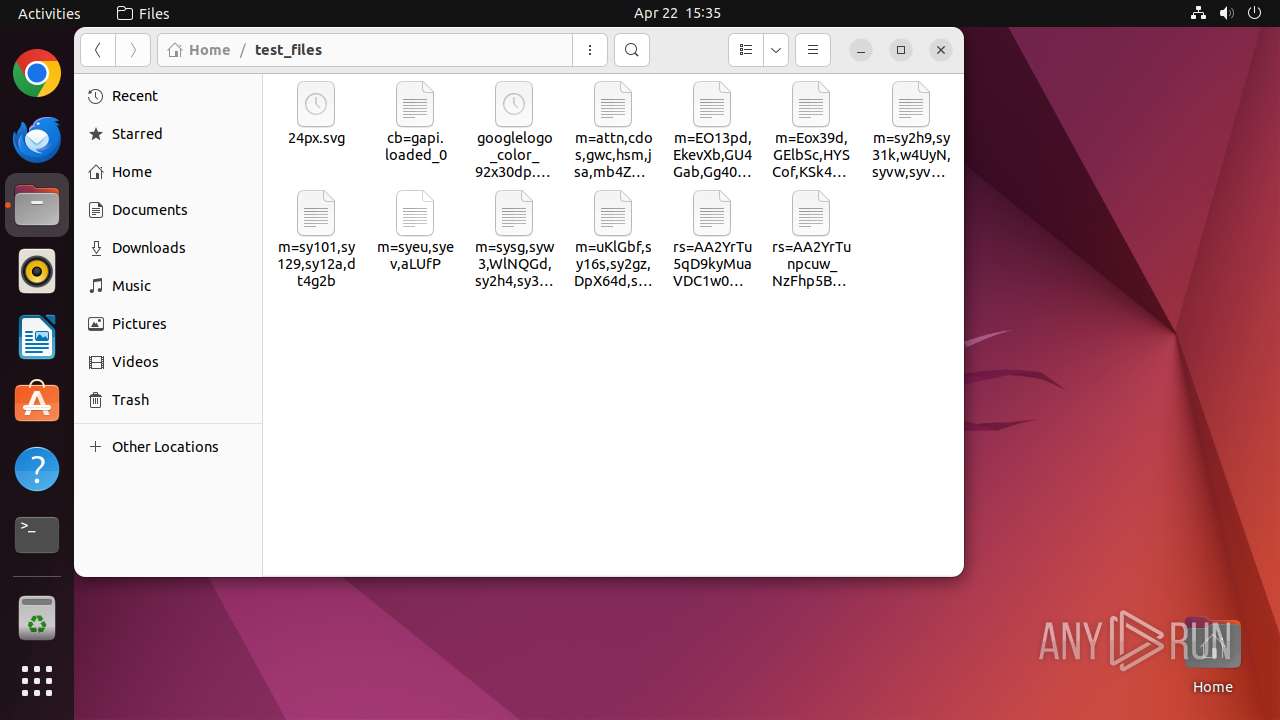
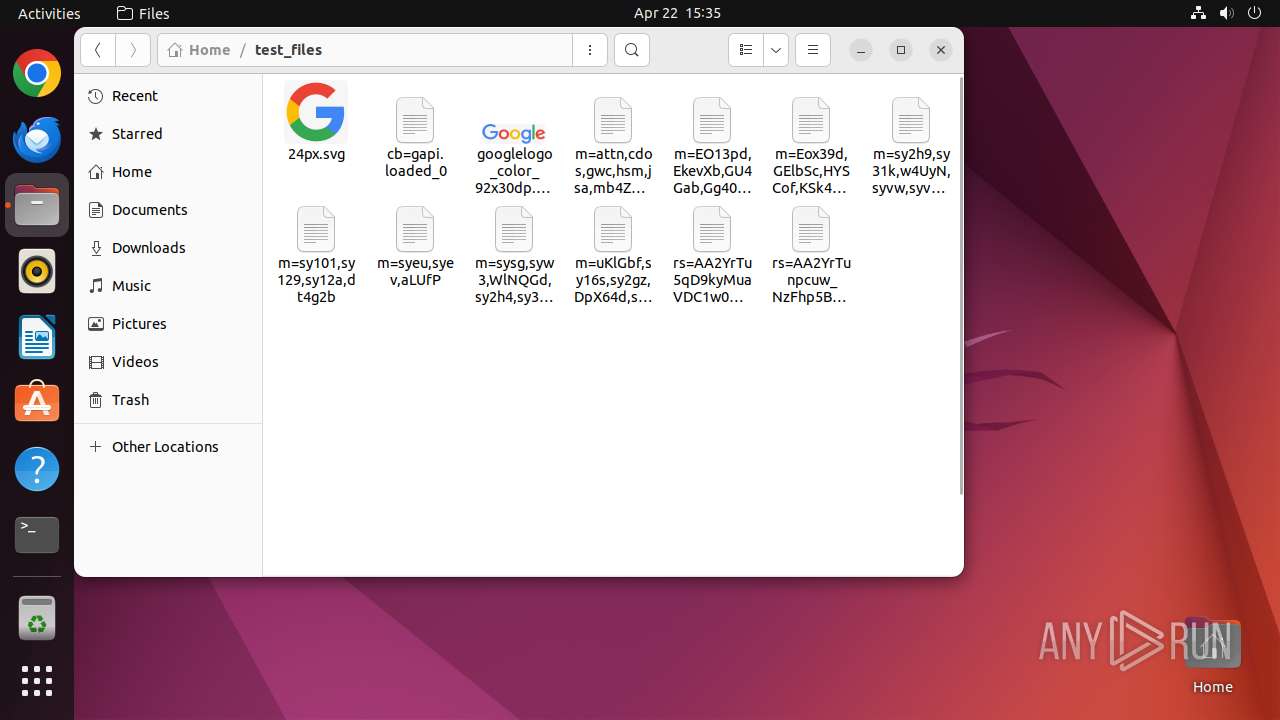
Creates file in the temporary folder
- nautilus (PID: 41165)
- gdk-pixbuf-thumbnailer (PID: 41193)
- gdk-pixbuf-thumbnailer (PID: 41196)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
423
Monitored processes
203
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 40657 | /bin/sh -c "DISPLAY=:0 sudo -iu user firefox storage\.ml-cachehost\.net " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40658 | sudo -iu user firefox storage.ml-cachehost.net | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40659 | /snap/firefox/3358/usr/lib/firefox/firefox storage.ml-cachehost.net | /snap/firefox/3358/usr/lib/firefox/firefox | sudo | |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40660 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | firefox |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40673 | /snap/snapd/20290/usr/lib/snapd/snap-seccomp version-info | /snap/snapd/20290/usr/lib/snapd/snap-seccomp | — | firefox |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40681 | /snap/snapd/20290/usr/lib/snapd/snap-confine --base core22 snap.firefox.firefox /usr/lib/snapd/snap-exec firefox storage.ml-cachehost.net | /snap/snapd/20290/usr/lib/snapd/snap-confine | — | firefox |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40682 | snap-update-ns --from-snap-confine firefox | /snap/snapd/20290/usr/lib/snapd/snap-update-ns | — | firefox |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40683 | dumpe2fs -h /dev/sda3 | /usr/sbin/dumpe2fs | — | udisksd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40689 | systemctl --user --global is-enabled snap.snapd-desktop-integration.snapd-desktop-integration.service | /usr/bin/systemctl | — | snapd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40690 | dumpe2fs -h /dev/sda3 | /usr/sbin/dumpe2fs | — | udisksd |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Executable files
0
Suspicious files
6
Text files
3
Unknown types
0
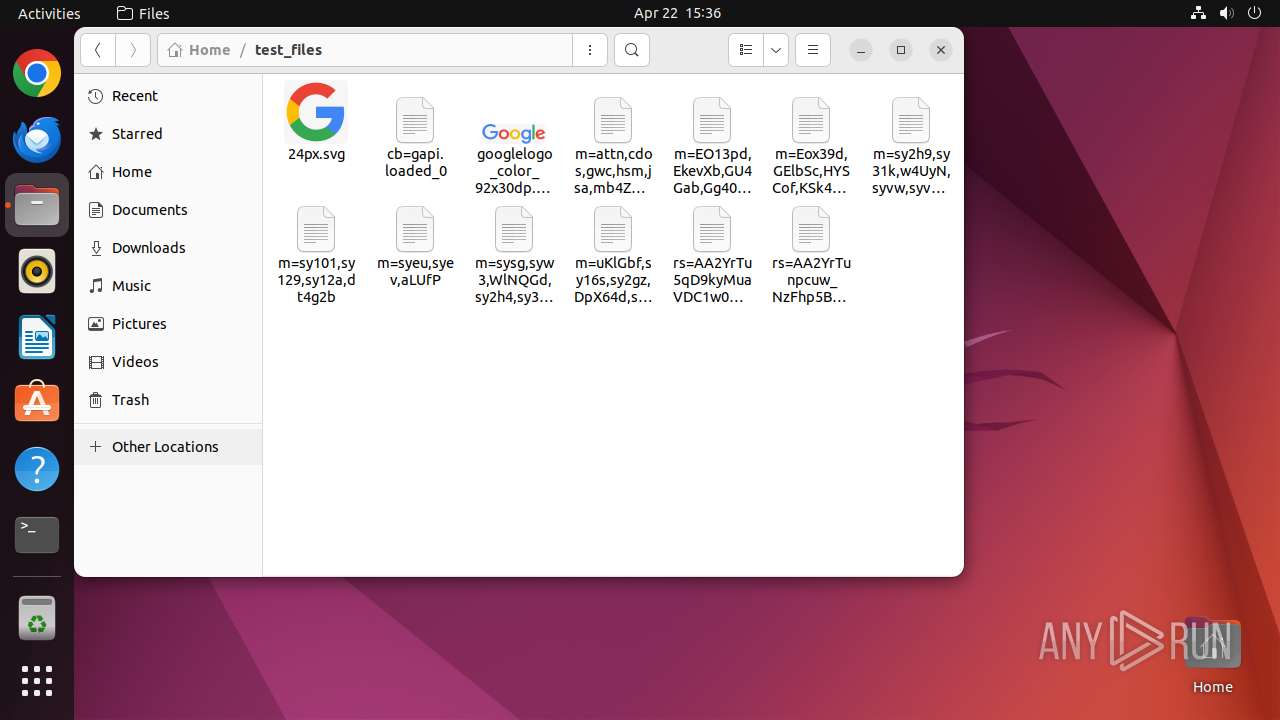
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 41165 | nautilus | /home/user/.local/share/nautilus/tags/meta.db | binary | |
MD5:— | SHA256:— | |||
| 41218 | nautilus | /home/user/.local/share/nautilus/tags/meta.db | binary | |
MD5:— | SHA256:— | |||
| 41165 | nautilus | /tmp/flatpak-seccomp-JCRI52 (deleted) | binary | |
MD5:— | SHA256:— | |||
| 41165 | nautilus | /home/user/.cache/thumbnails/large/91f8fe93870de6f6e9adc47aec9ebf49.png | image | |
MD5:— | SHA256:— | |||
| 41165 | nautilus | /tmp/flatpak-seccomp-1HWG52 (deleted) | binary | |
MD5:— | SHA256:— | |||
| 41165 | nautilus | /home/user/.cache/thumbnails/large/5cd4a5e7795cd851999fe442294e1503.png | image | |
MD5:— | SHA256:— | |||
| 41165 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-shm (deleted) | binary | |
MD5:— | SHA256:— | |||
| 41218 | nautilus | /home/user/.local/share/nautilus/tags/meta.db-shm (deleted) | binary | |
MD5:— | SHA256:— | |||
| 41266 | bash | /home/user/.bash_history | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
44
DNS requests
72
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 185.125.190.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
40659 | firefox | GET | 403 | 172.67.68.136:80 | http://storage.ml-cachehost.net/ | unknown | — | — | unknown |
40659 | firefox | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
40659 | firefox | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
40659 | firefox | POST | 200 | 2.16.206.148:80 | http://r10.o.lencr.org/ | unknown | — | — | whitelisted |
40659 | firefox | POST | 200 | 216.58.212.163:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
40659 | firefox | POST | 200 | 2.16.206.143:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
40659 | firefox | POST | 200 | 2.16.206.143:80 | http://r11.o.lencr.org/ | unknown | — | — | whitelisted |
40659 | firefox | POST | 200 | 216.58.212.163:80 | http://o.pki.goog/s/wr3/cgo | unknown | — | — | whitelisted |
40659 | firefox | GET | — | 172.67.68.136:80 | http://storage.ml-cachehost.net/favicon.ico | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 185.125.190.17:80 | — | Canonical Group Limited | GB | unknown |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.98:80 | — | Canonical Group Limited | GB | unknown |
— | — | 195.181.175.41:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.55:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40659 | firefox | 172.67.68.136:80 | storage.ml-cachehost.net | CLOUDFLARENET | US | unknown |
40659 | firefox | 34.36.137.203:443 | contile.services.mozilla.com | — | — | whitelisted |
40659 | firefox | 142.250.185.170:443 | safebrowsing.googleapis.com | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
storage.ml-cachehost.net |
| unknown |
detectportal.firefox.com |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
spocs.getpocket.com |
| whitelisted |