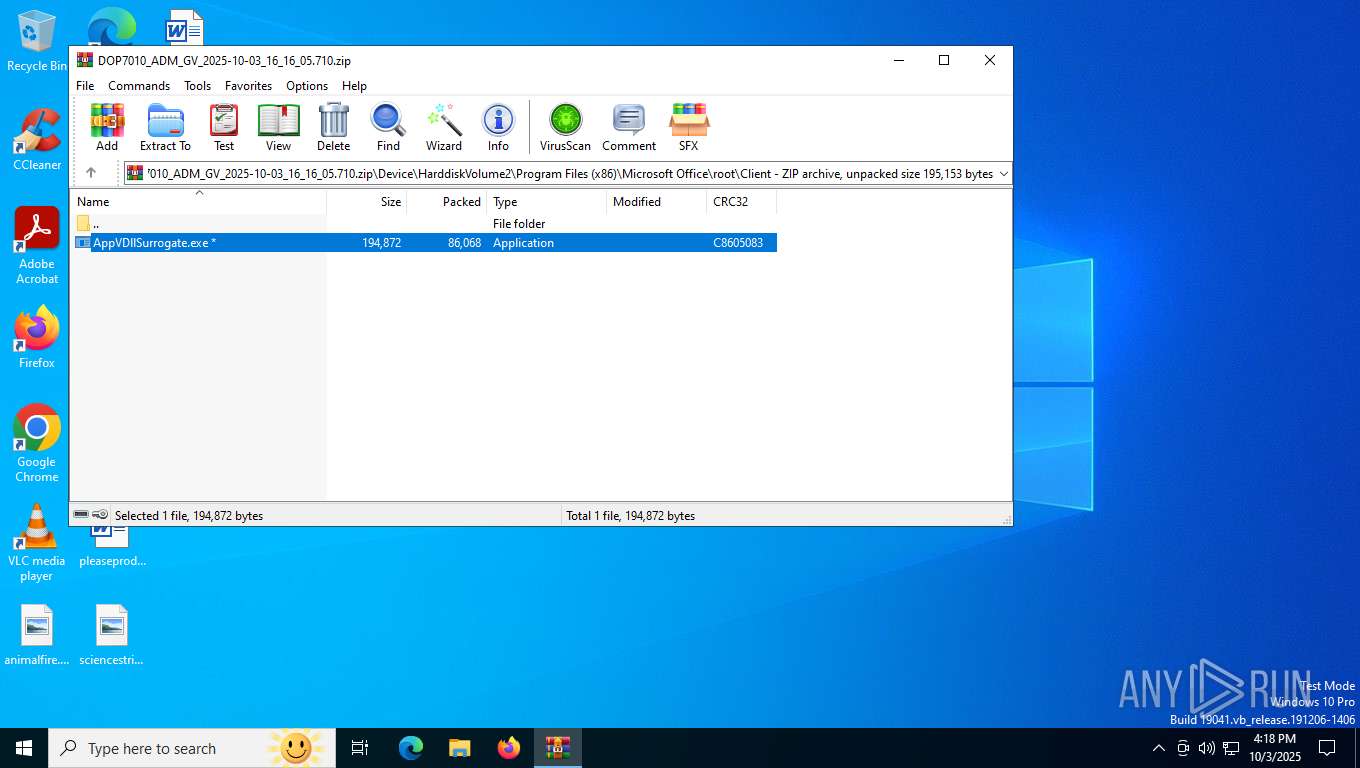
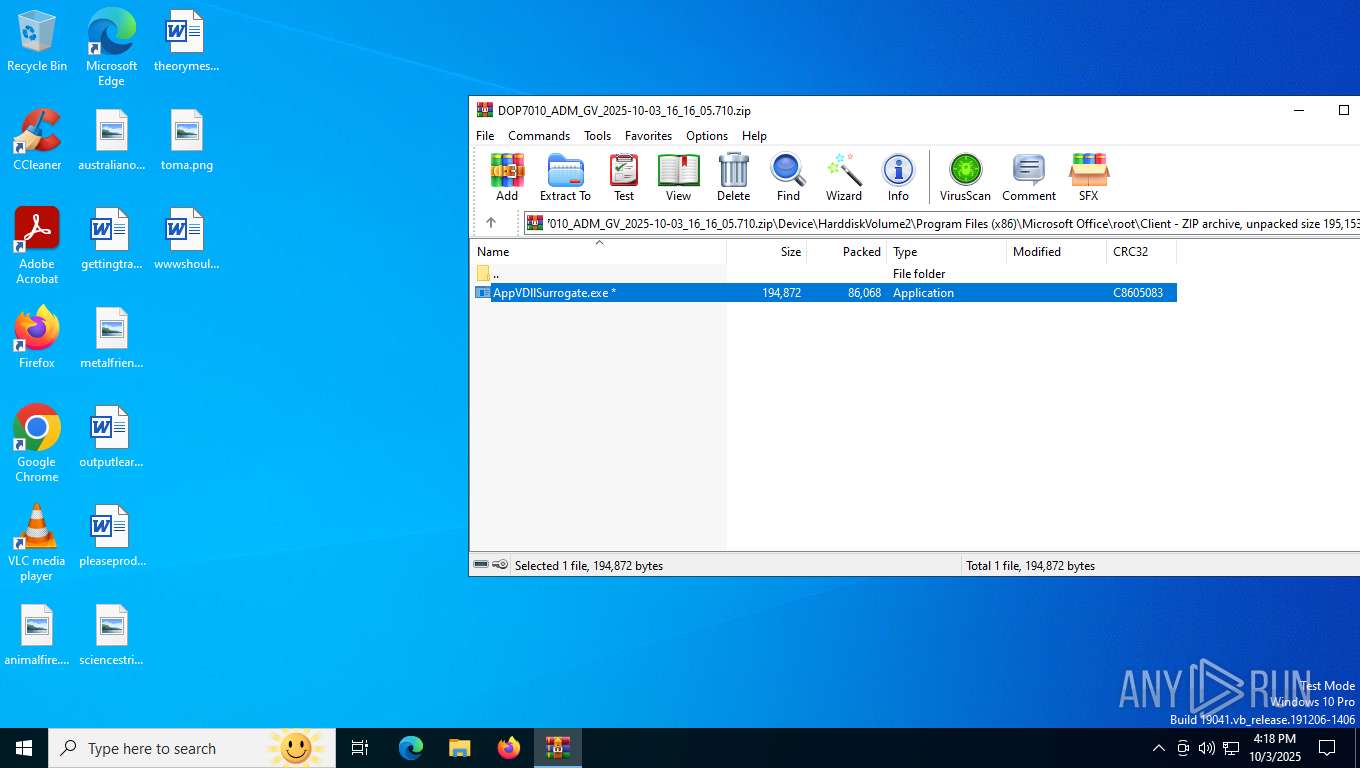
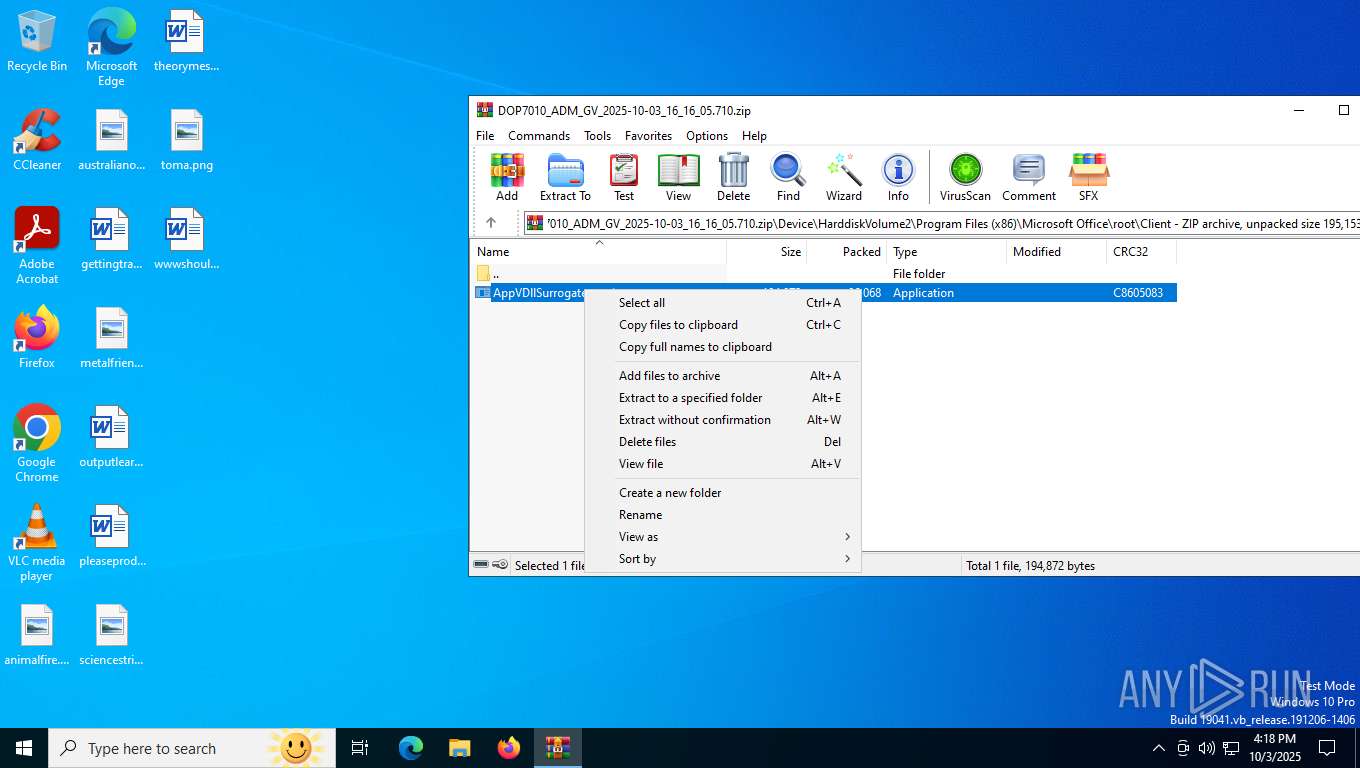
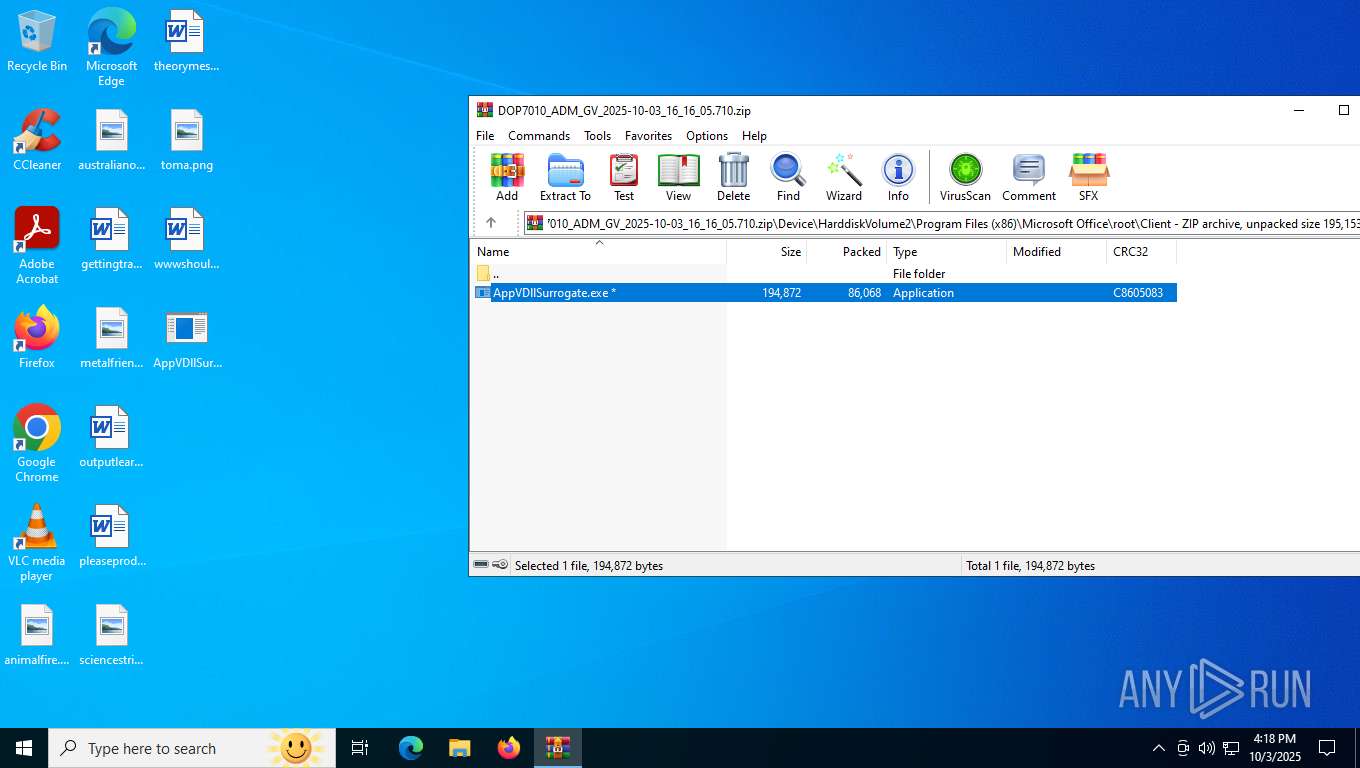
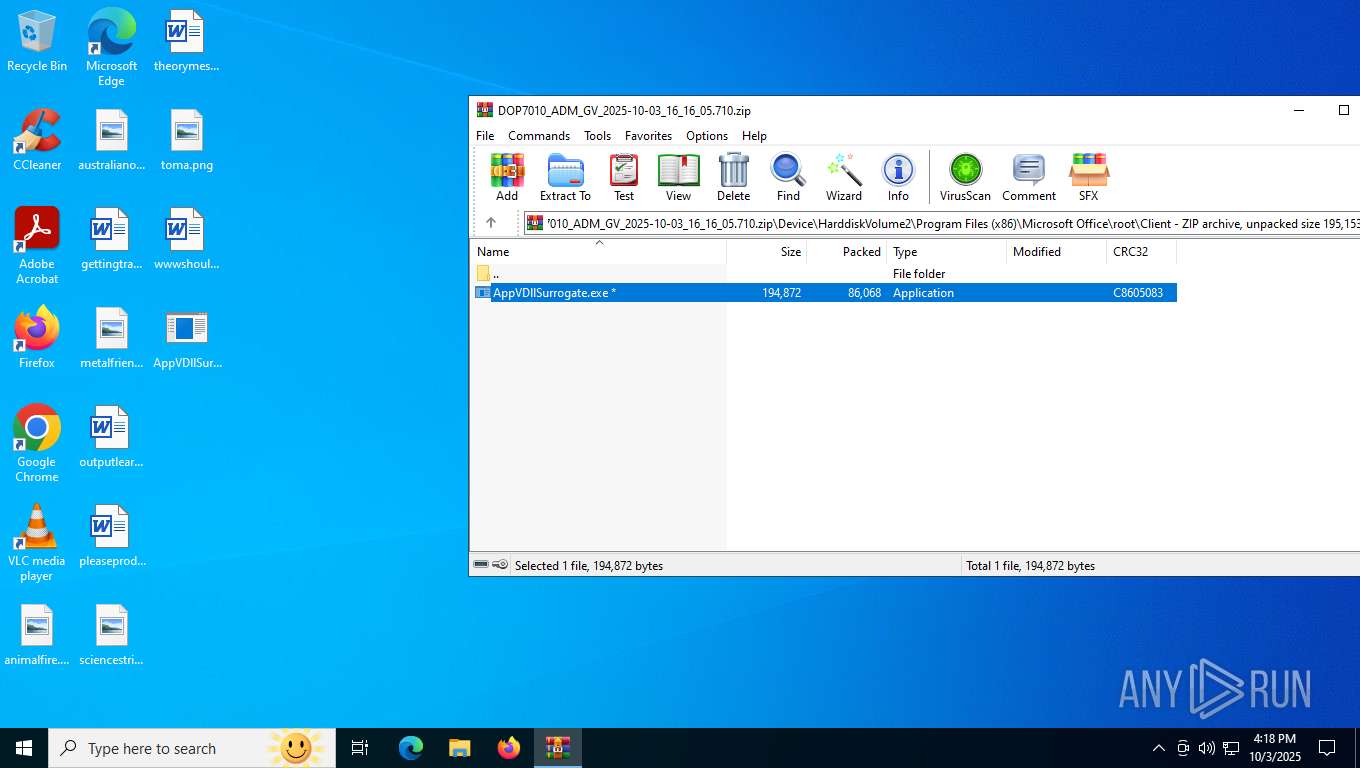
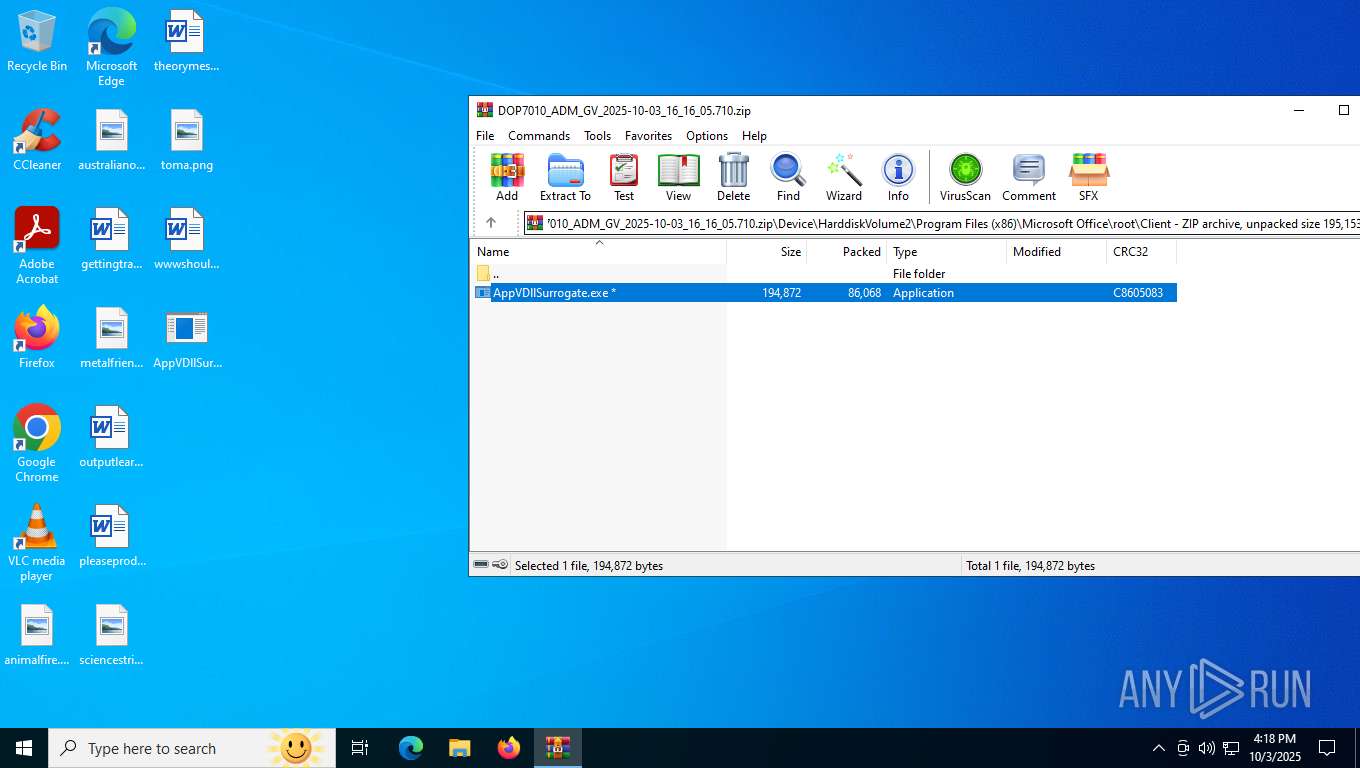
| File name: | DOP7010_ADM_GV_2025-10-03_16_16_05.710.zip |
| Full analysis: | https://app.any.run/tasks/bce5df5e-2e73-4433-b892-0258e45ab12b |
| Verdict: | Malicious activity |
| Analysis date: | October 03, 2025, 16:17:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v4.5 to extract, compression method=deflate |
| MD5: | 10A4AA2FD2B7B7DA745F222BF8D6A57E |
| SHA1: | 069C1878D51847676F07502331EAD2C526510E35 |
| SHA256: | 6F322ABDA69F4208109C4B76957E4E58F638F7880C8C3F700D686045C1F9093D |
| SSDEEP: | 3072:bg27IUtWSgntS4ojGcEyoNjjjgaXnRLa1O6650iKEh2m:nIrSgntrgGHtjsUnRL7665V2m |
MALICIOUS
NESHTA mutex has been found
- AppVDllSurrogate.exe (PID: 4440)
- AppVDllSurrogate.exe (PID: 8056)
- AppVDllSurrogate.exe (PID: 2004)
SUSPICIOUS
Process drops legitimate windows executable
- AppVDllSurrogate.exe (PID: 2004)
- AppVDllSurrogate.exe (PID: 4440)
- AppVDllSurrogate.exe (PID: 8056)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 5368)
- AppVDllSurrogate.exe (PID: 2004)
- AppVDllSurrogate.exe (PID: 4440)
- AppVDllSurrogate.exe (PID: 8056)
Mutex name with non-standard characters
- AppVDllSurrogate.exe (PID: 2004)
- AppVDllSurrogate.exe (PID: 4440)
- AppVDllSurrogate.exe (PID: 8056)
Starts a Microsoft application from unusual location
- AppVDllSurrogate.exe (PID: 4036)
- AppVDllSurrogate.exe (PID: 4256)
- AppVDllSurrogate.exe (PID: 7000)
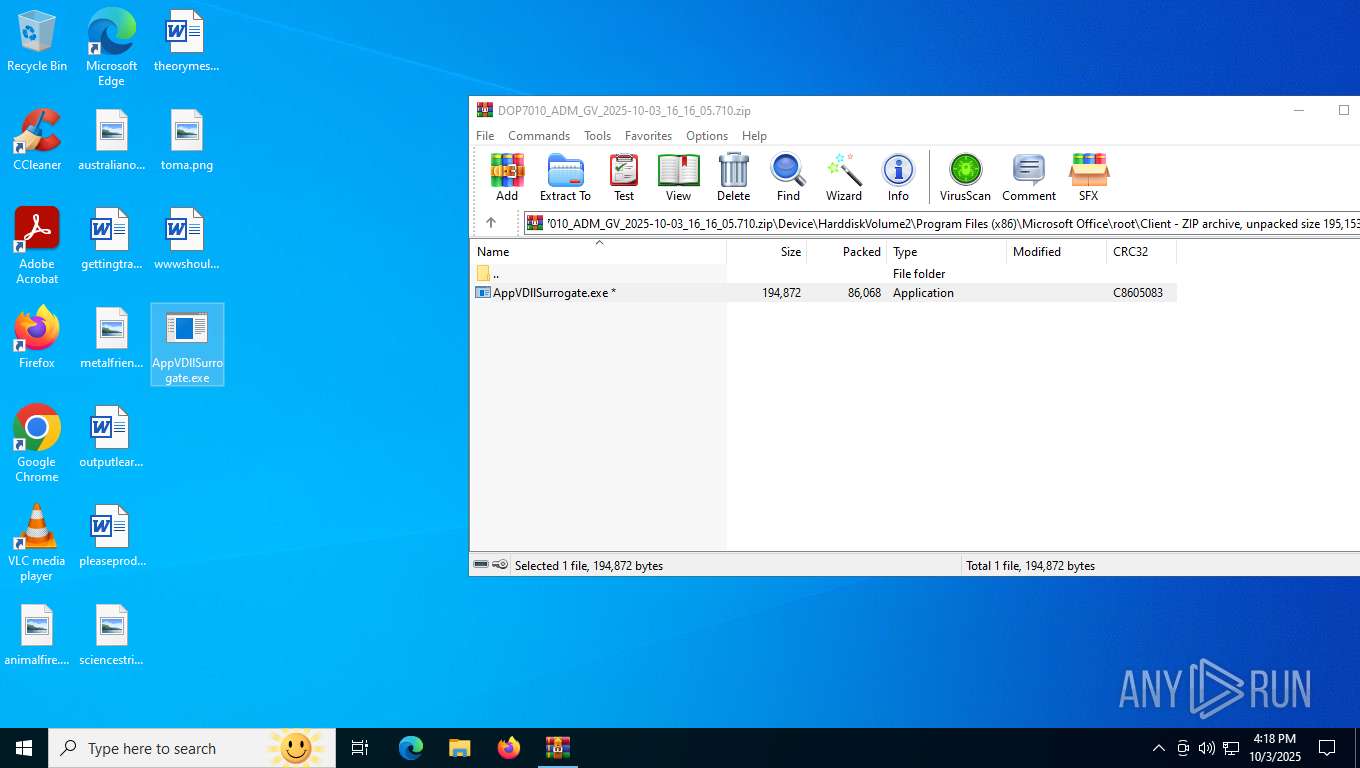
Executable content was dropped or overwritten
- AppVDllSurrogate.exe (PID: 2004)
- AppVDllSurrogate.exe (PID: 4440)
- AppVDllSurrogate.exe (PID: 8056)
INFO
Create files in a temporary directory
- AppVDllSurrogate.exe (PID: 2004)
- AppVDllSurrogate.exe (PID: 4440)
- AppVDllSurrogate.exe (PID: 8056)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5368)
Process checks computer location settings
- AppVDllSurrogate.exe (PID: 2004)
- AppVDllSurrogate.exe (PID: 4440)
- AppVDllSurrogate.exe (PID: 8056)
Checks supported languages
- AppVDllSurrogate.exe (PID: 4036)
- AppVDllSurrogate.exe (PID: 2004)
- AppVDllSurrogate.exe (PID: 4440)
- AppVDllSurrogate.exe (PID: 4256)
- AppVDllSurrogate.exe (PID: 8056)
- AppVDllSurrogate.exe (PID: 7000)
Reads the computer name
- AppVDllSurrogate.exe (PID: 2004)
- AppVDllSurrogate.exe (PID: 4440)
- AppVDllSurrogate.exe (PID: 8056)
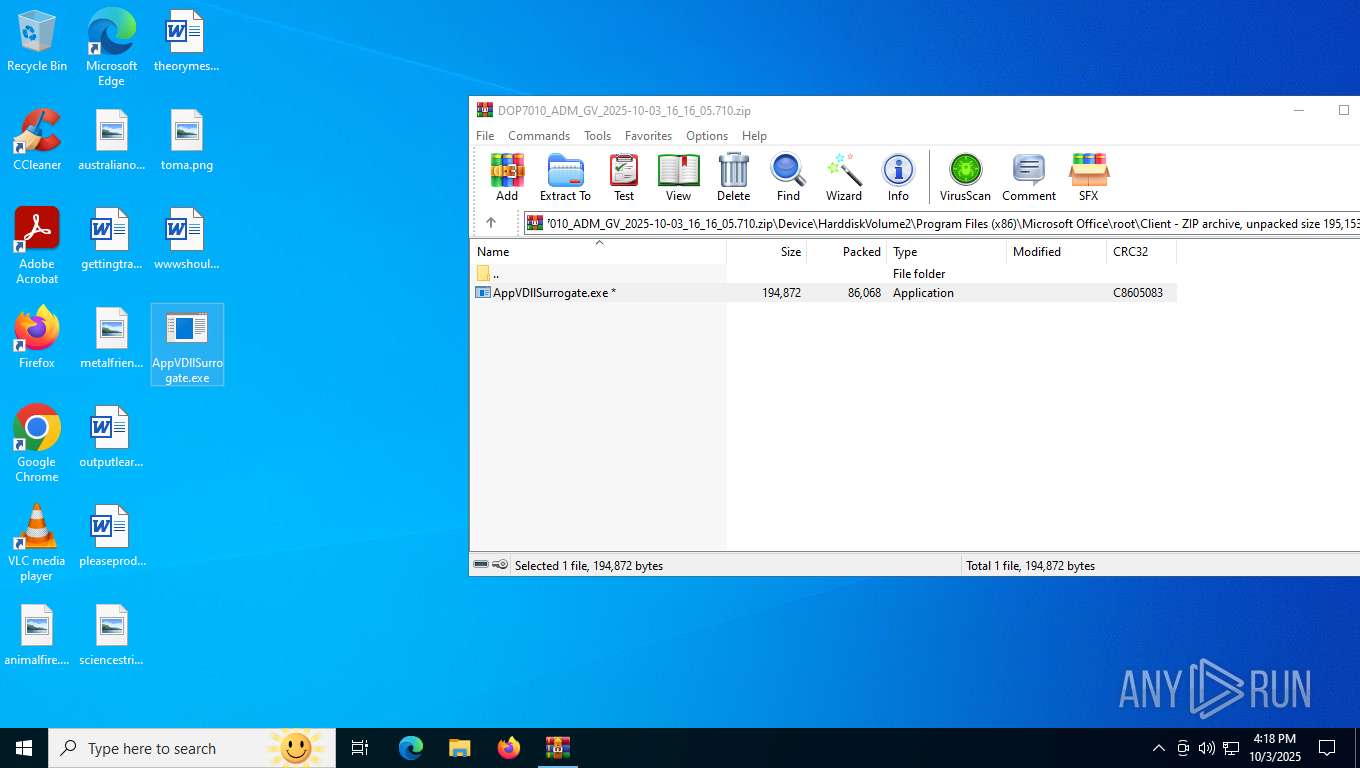
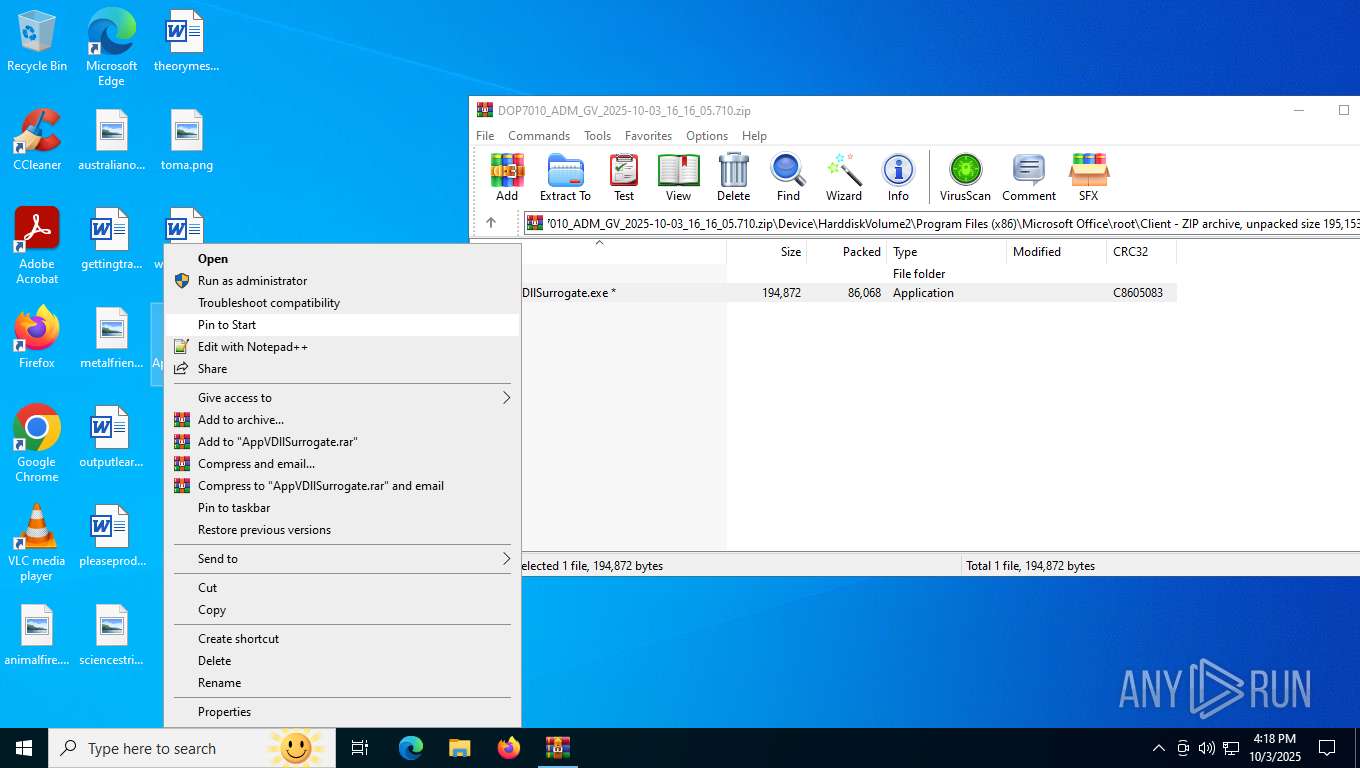
Manual execution by a user
- AppVDllSurrogate.exe (PID: 4440)
- AppVDllSurrogate.exe (PID: 8056)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
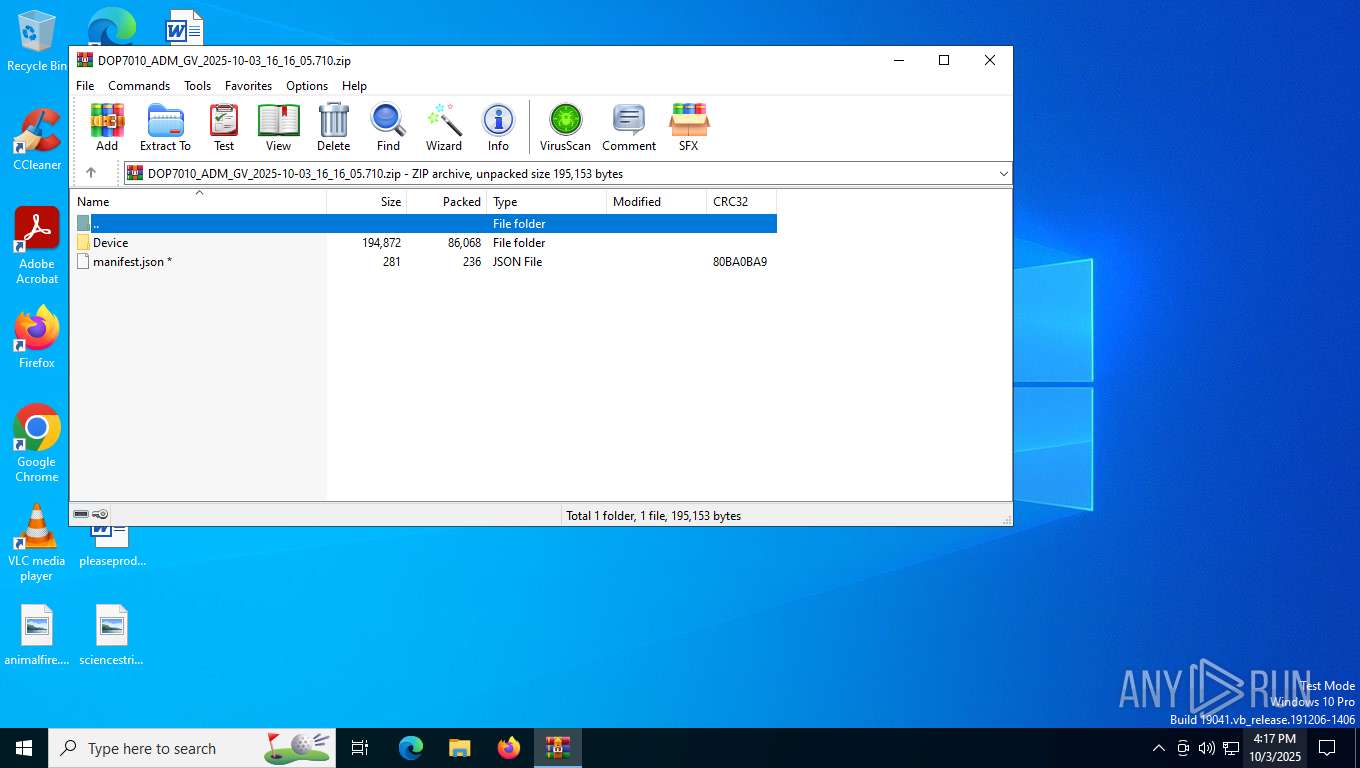
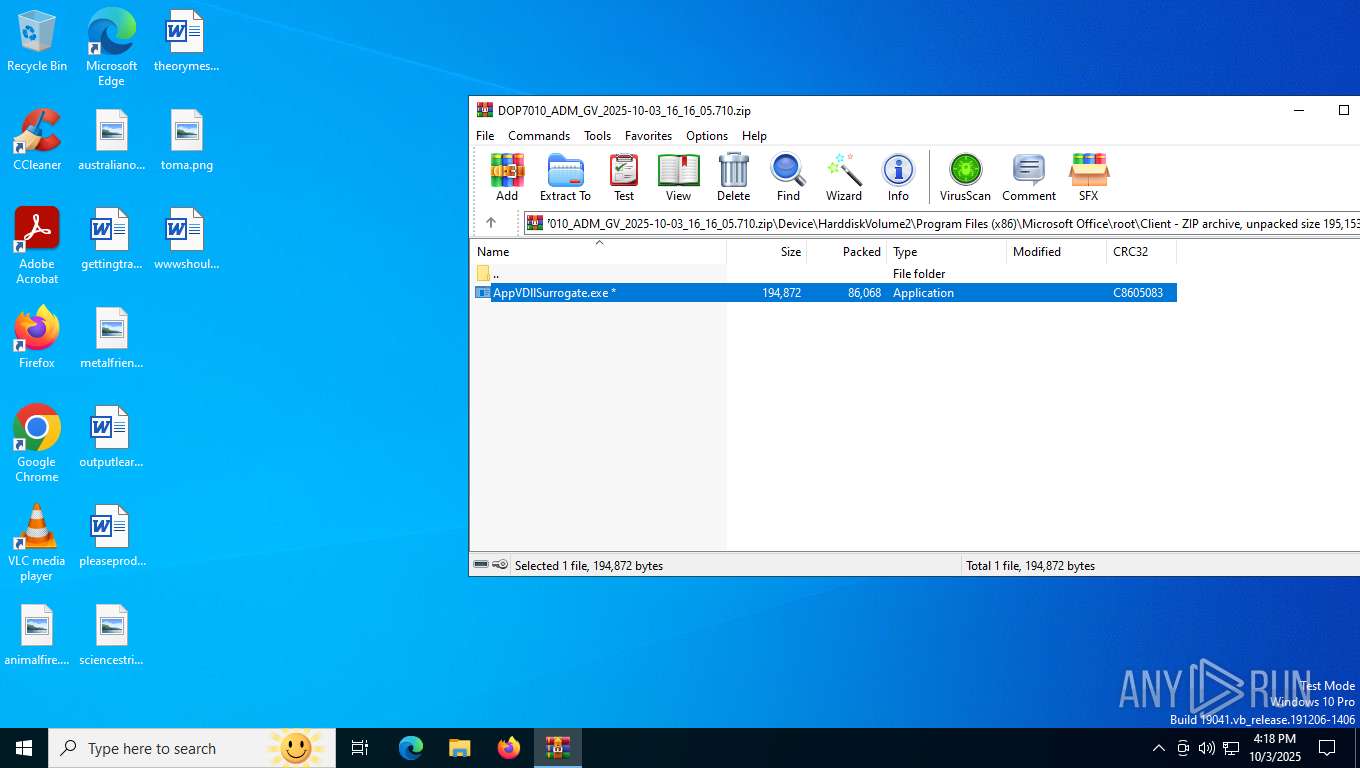
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0801 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:00:00 00:00:00 |
| ZipCRC: | 0xc8605083 |
| ZipCompressedSize: | 86068 |
| ZipUncompressedSize: | 194872 |
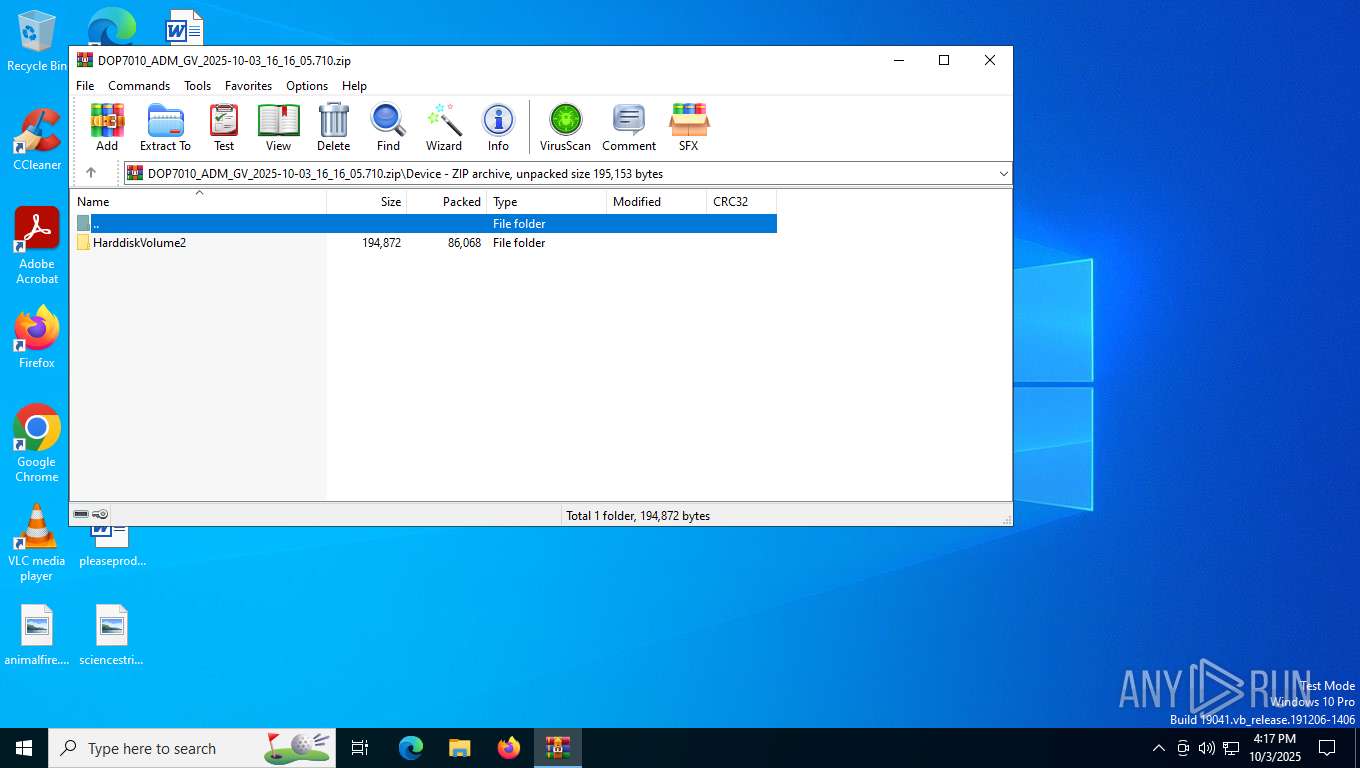
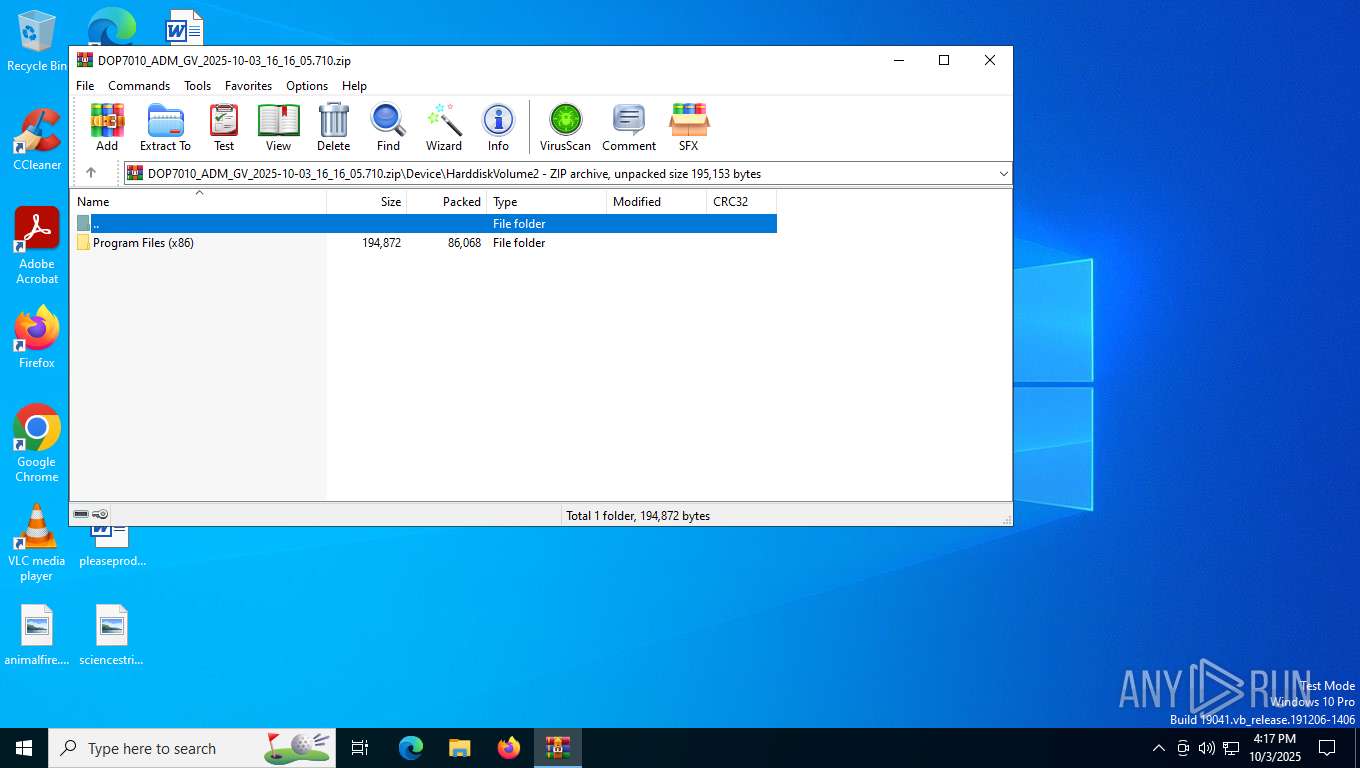
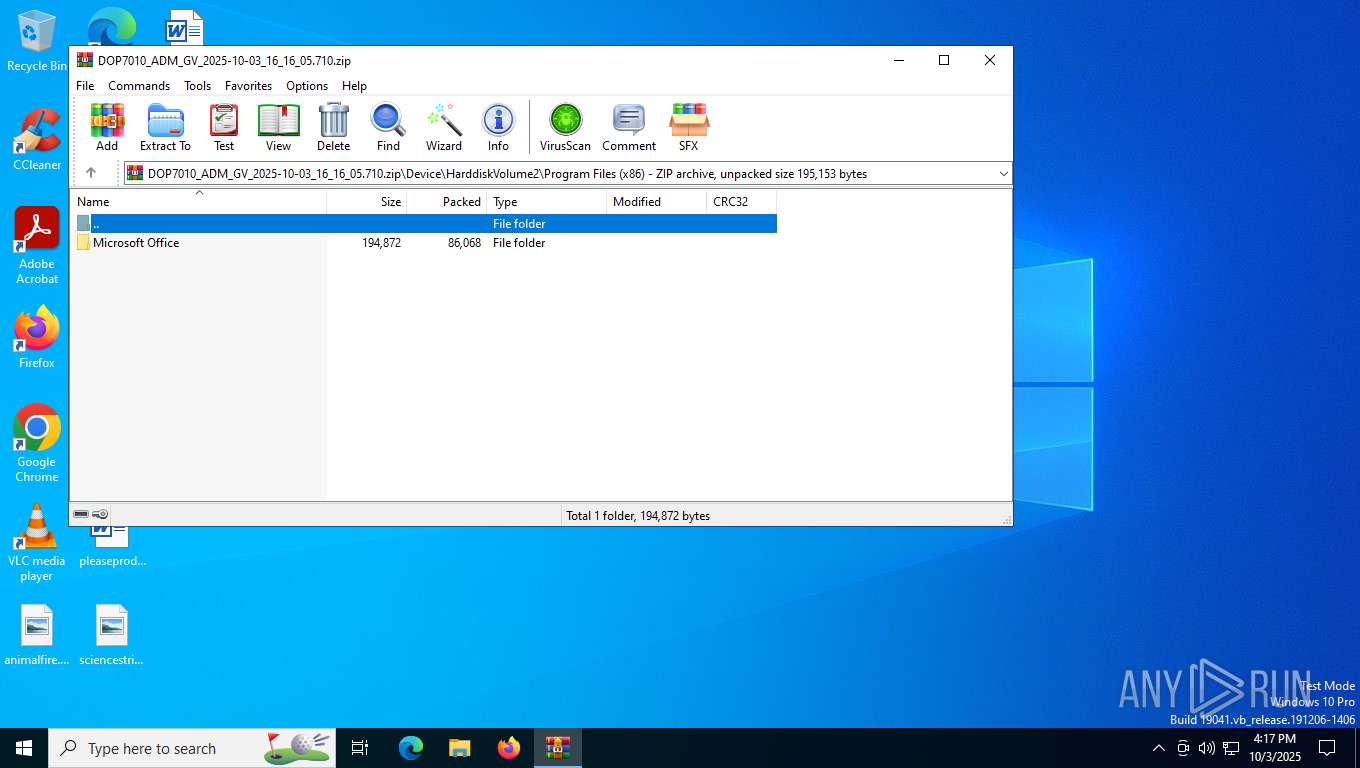
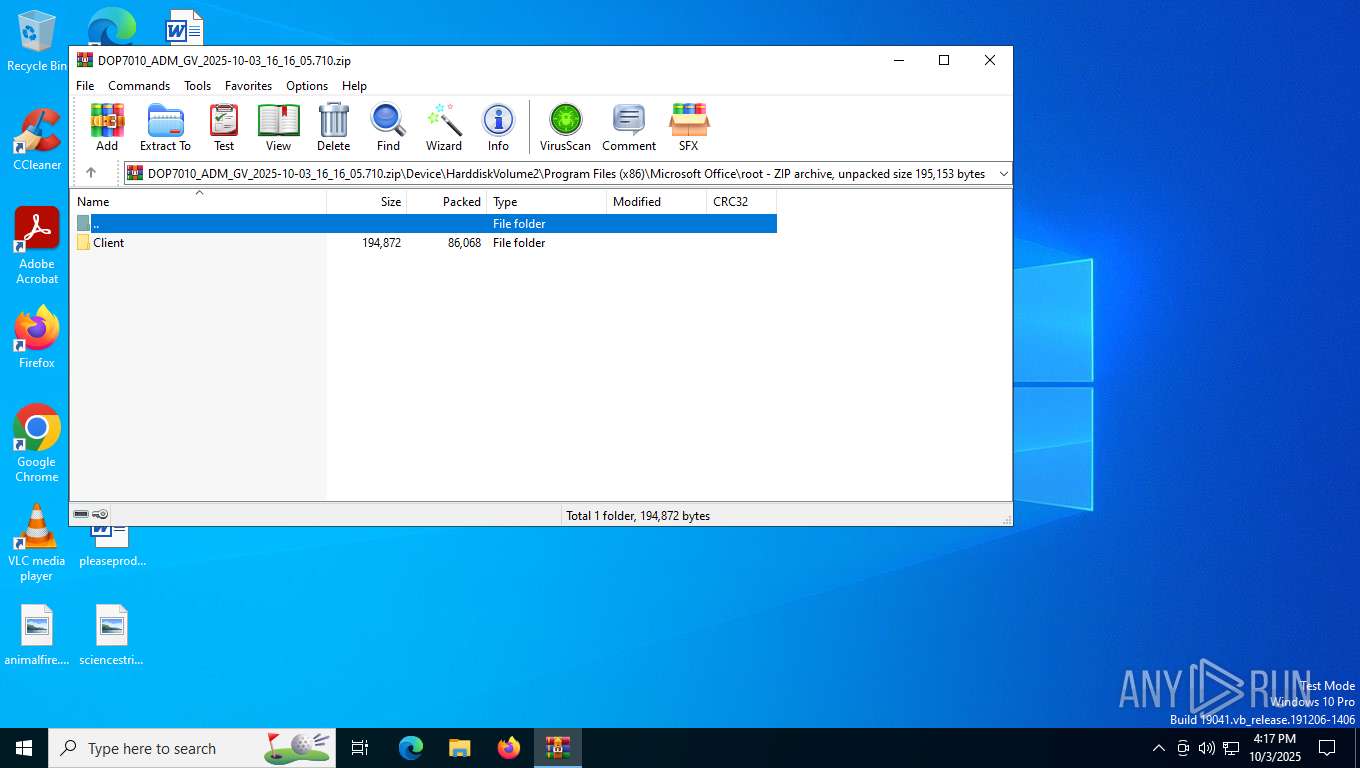
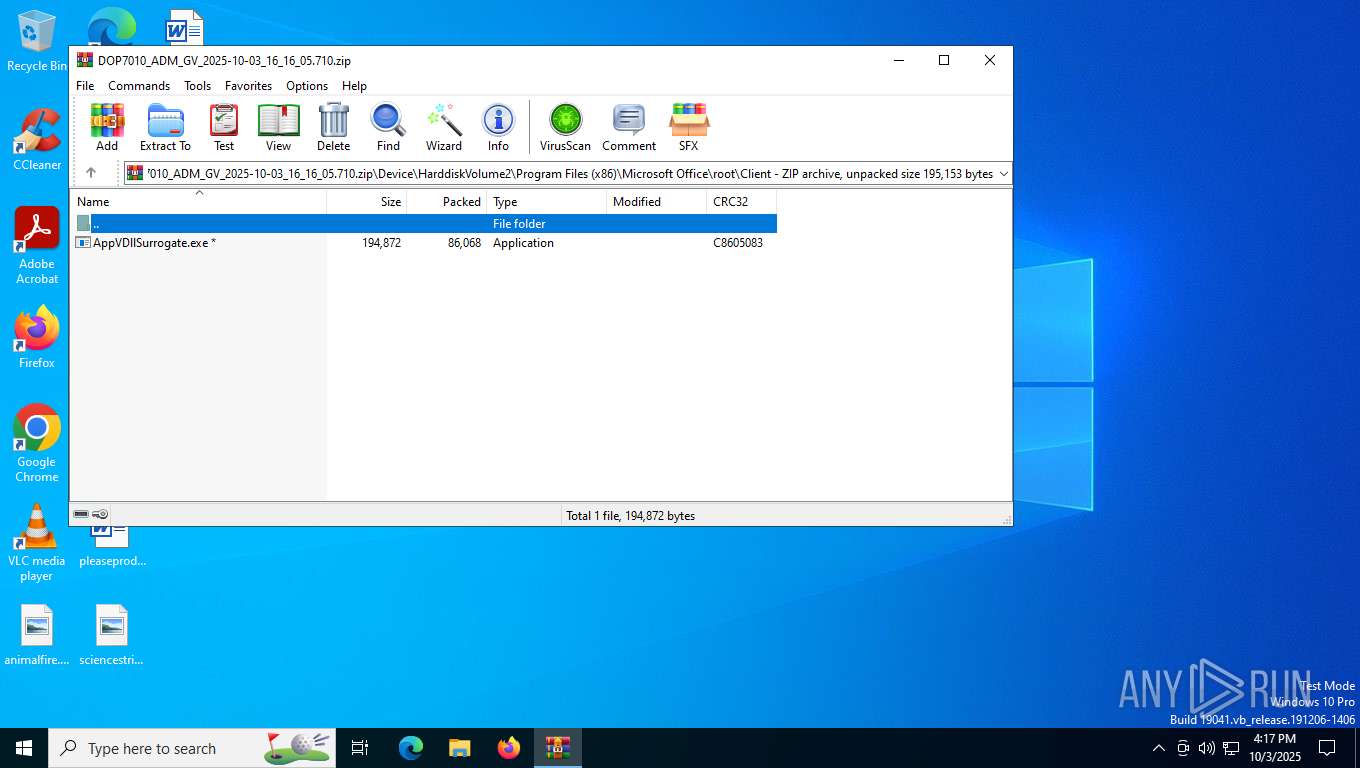
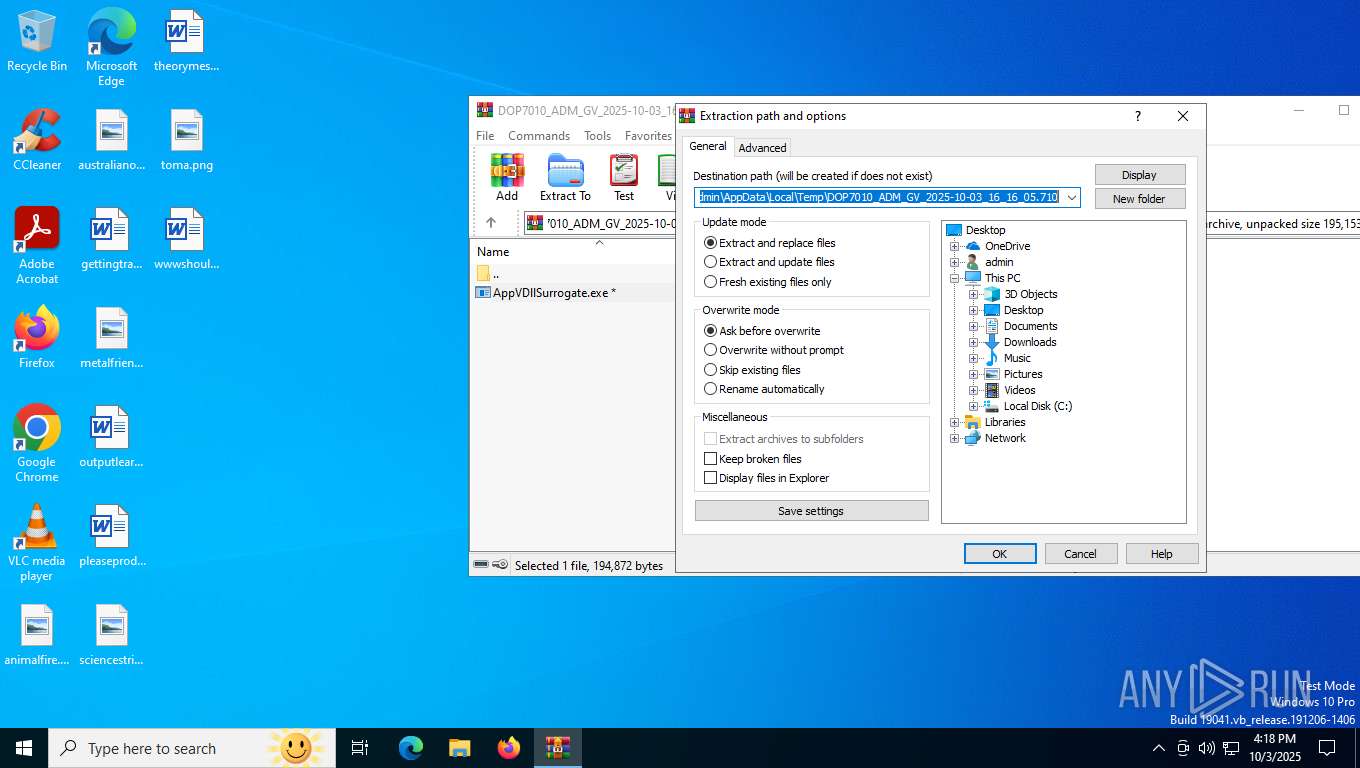
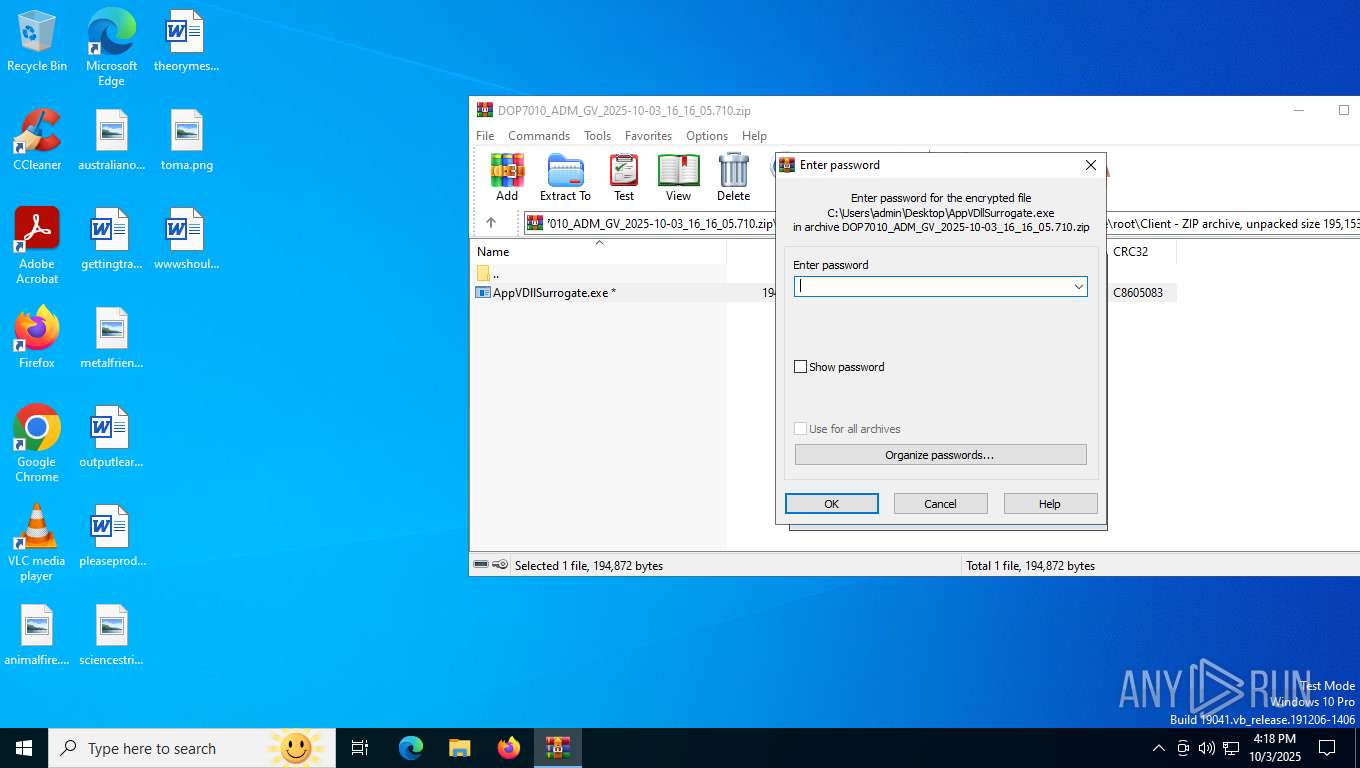
| ZipFileName: | Device/HarddiskVolume2/Program Files (x86)/Microsoft Office/root/Client/AppVDllSurrogate.exe |
Total processes
180
Monitored processes
11
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
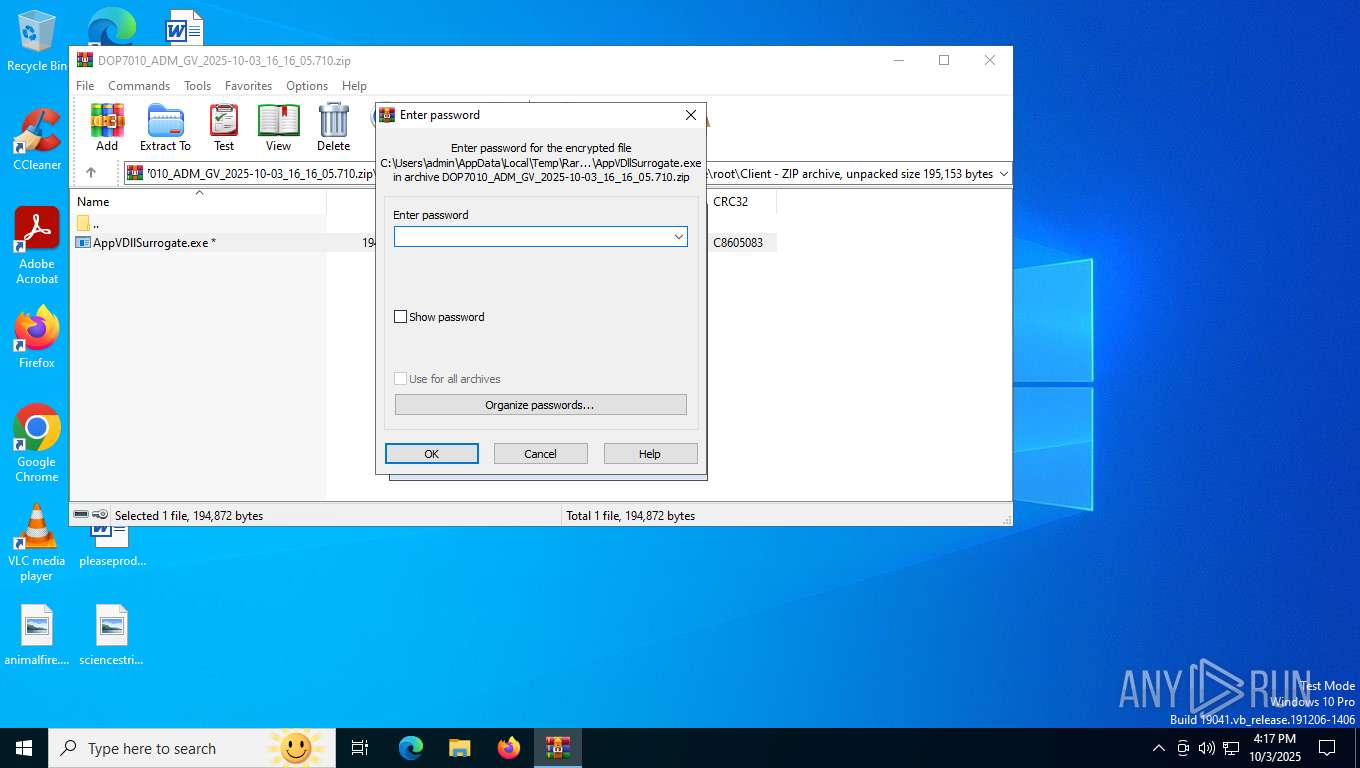
| 2004 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb5368.40805\Device\HarddiskVolume2\Program Files (x86)\Microsoft Office\root\Client\AppVDllSurrogate.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb5368.40805\Device\HarddiskVolume2\Program Files (x86)\Microsoft Office\root\Client\AppVDllSurrogate.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 3096 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AppVDllSurrogate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4036 | "C:\Users\admin\AppData\Local\Temp\3582-490\AppVDllSurrogate.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\AppVDllSurrogate.exe | — | AppVDllSurrogate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Client DLL Surrogate Host Exit code: 2147942487 Version: 16.0.18925.20022 Modules
| |||||||||||||||
| 4256 | "C:\Users\admin\AppData\Local\Temp\3582-490\AppVDllSurrogate.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\AppVDllSurrogate.exe | — | AppVDllSurrogate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Client DLL Surrogate Host Exit code: 2147942487 Version: 16.0.18925.20022 Modules
| |||||||||||||||
| 4440 | "C:\Users\admin\Desktop\AppVDllSurrogate.exe" | C:\Users\admin\Desktop\AppVDllSurrogate.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5368 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\DOP7010_ADM_GV_2025-10-03_16_16_05.710.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
| 7000 | "C:\Users\admin\AppData\Local\Temp\3582-490\AppVDllSurrogate.exe" | C:\Users\admin\AppData\Local\Temp\3582-490\AppVDllSurrogate.exe | — | AppVDllSurrogate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Client DLL Surrogate Host Exit code: 2147942487 Version: 16.0.18925.20022 Modules
| |||||||||||||||
| 8028 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AppVDllSurrogate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8028 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | AppVDllSurrogate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 092
Read events
8 064
Write events
15
Delete events
13
Modification events
| (PID) Process: | (5368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (5368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (5368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (5368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (5368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (5368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DOP7010_ADM_GV_2025-10-03_16_16_05.710.zip | |||
| (PID) Process: | (5368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (5368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (5368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (5368) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
46
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5368 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5368.40805\manifest.json | text | |
MD5:B9783470808E8960C3A4C94F07CFC3F1 | SHA256:F4E95FAAE5FA047262E02DCC7D1E7BF83990B137392FC8F3516B6B097E1907DB | |||
| 2004 | AppVDllSurrogate.exe | C:\ProgramData\Adobe\ARM\S\388\AdobeARMHelper.exe | executable | |
MD5:85A67D34298E33D2D5A9EC789B6AB594 | SHA256:1DEE143B4F88F2375B85C6271A58E2E78FED081BEAE4090678CB2DD7A37FB2D4 | |||
| 5368 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb5368.40805\Device\HarddiskVolume2\Program Files (x86)\Microsoft Office\root\Client\AppVDllSurrogate.exe | executable | |
MD5:A7EB2DE93C075F99BF0BA05A3E3F111A | SHA256:B092257DE304A8C8E4DE3F7BC9E297745416CE0291CCCCD8905840384833E523 | |||
| 8056 | AppVDllSurrogate.exe | C:\Program Files (x86)\Common Files\Java\Java Update\jaureg.exe | executable | |
MD5:6D55E9A1D506D4472409FC2E2D553DAD | SHA256:A171E0A4C806B17CC289B96370BD42F3AC088D286BA8B919F2FFAEF45B681A14 | |||
| 5368 | WinRAR.exe | C:\Users\admin\Desktop\AppVDllSurrogate.exe | executable | |
MD5:A7EB2DE93C075F99BF0BA05A3E3F111A | SHA256:B092257DE304A8C8E4DE3F7BC9E297745416CE0291CCCCD8905840384833E523 | |||
| 8056 | AppVDllSurrogate.exe | C:\Program Files (x86)\Common Files\Adobe\ARM\1.0\AdobeARM.exe | executable | |
MD5:5472D788E7E6FD34BA00A09C65C2A63F | SHA256:ECA506C548581FC94E4E85054B1E98816495E210AEFE30705FEAB530ECB5C1D5 | |||
| 8056 | AppVDllSurrogate.exe | C:\Program Files (x86)\Common Files\Adobe\ARM\1.0\armsvc.exe | executable | |
MD5:1ED48298892B0D8B9BB0BAAC7CD2EDAF | SHA256:ACD5D3A79BF76E2BFAB3D50A3A336C301BF24C8A352C68273351234F4C5F8606 | |||
| 8056 | AppVDllSurrogate.exe | C:\Program Files (x86)\Common Files\Java\Java Update\jusched.exe | executable | |
MD5:BCAC3CBF6DF41FB1562B295AD30DE227 | SHA256:0D663EEBF01B4B5DDDBED809B35F85EBF7D04EC9911CA090E136490C531399E8 | |||
| 8056 | AppVDllSurrogate.exe | C:\Windows\svchost.com | executable | |
MD5:36FD5E09C417C767A952B4609D73A54B | SHA256:980BAC6C9AFE8EFC9C6FE459A5F77213B0D8524EB00DE82437288EB96138B9A2 | |||
| 8056 | AppVDllSurrogate.exe | C:\Program Files (x86)\Common Files\Java\Java Update\jucheck.exe | executable | |
MD5:B3DF9BF318BAB4EECA2F61C3576FBEF3 | SHA256:55DF504E055F2F93E8F59947347594267F33D01EBE169715071085E434A538F1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
31
DNS requests
16
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5276 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5276 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
2856 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
6988 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
4372 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3404 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6016 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5224 | SearchApp.exe | 92.123.104.51:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5276 | svchost.exe | 20.190.159.2:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5276 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
6988 | backgroundTaskHost.exe | 92.123.104.42:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
6988 | backgroundTaskHost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
3464 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |