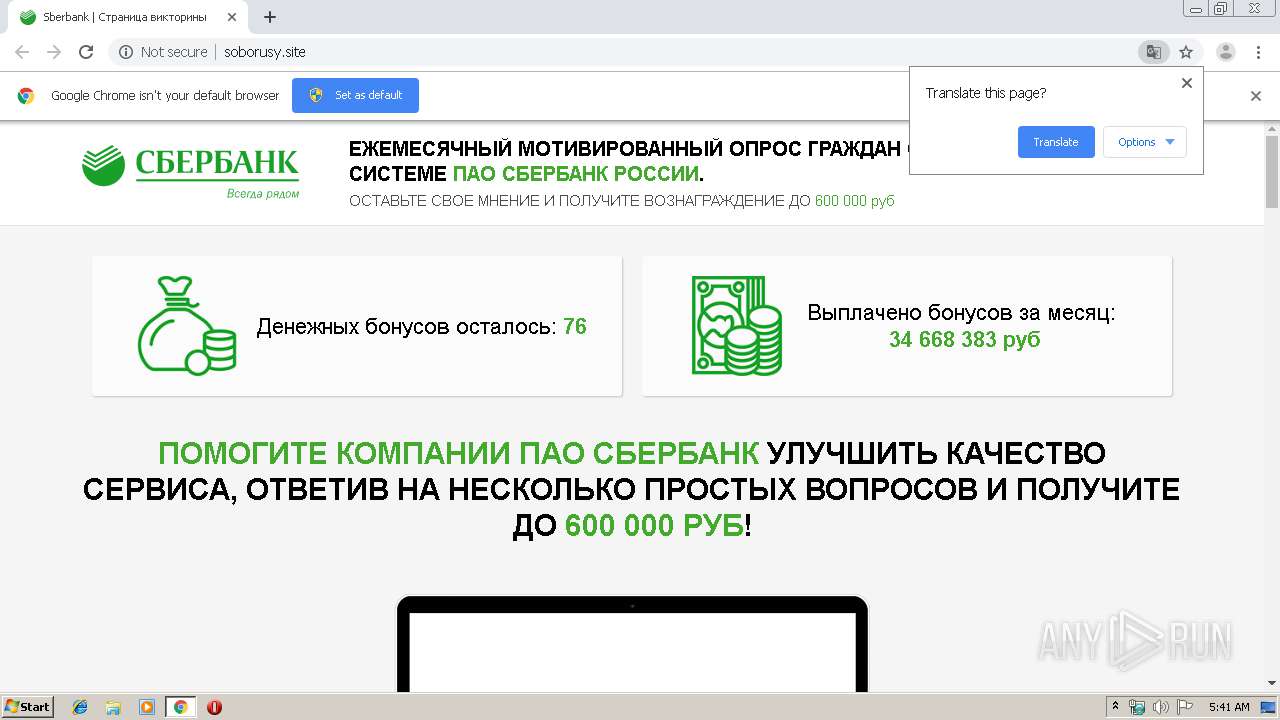
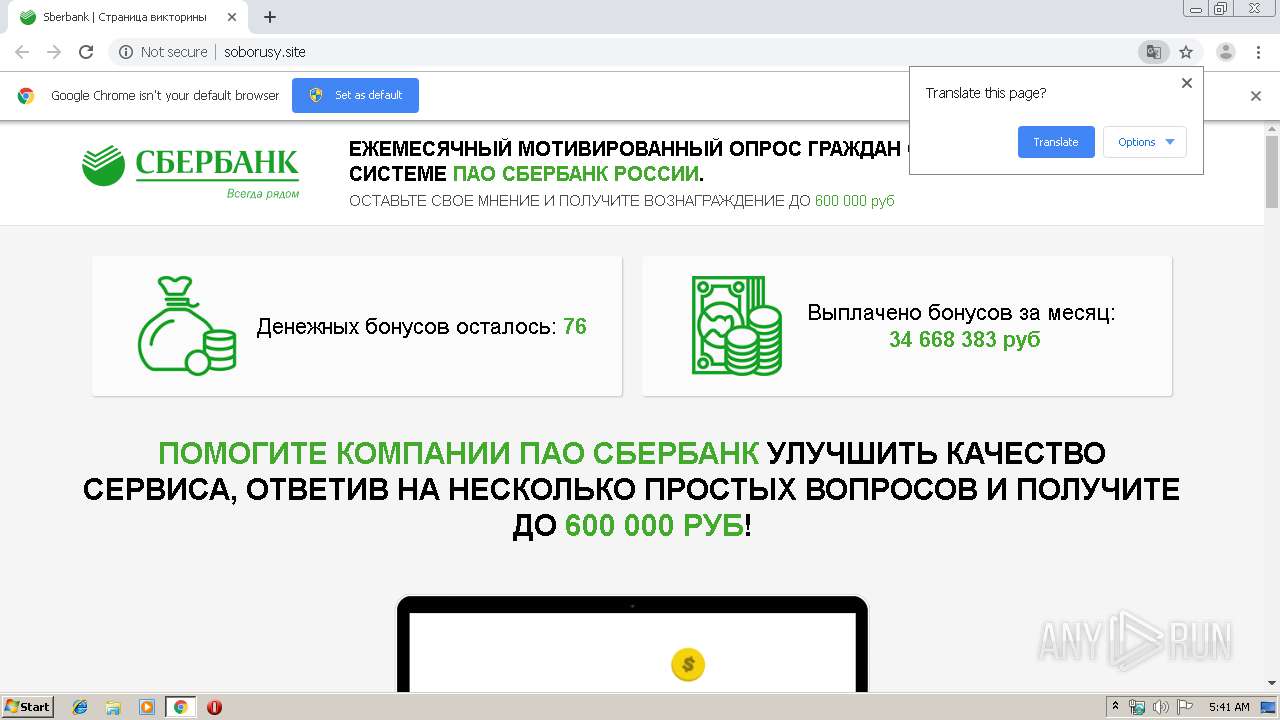
| URL: | http://soborusy.site |
| Full analysis: | https://app.any.run/tasks/ad133377-86e1-4fc4-97ce-c9e2954b606d |
| Verdict: | Malicious activity |
| Analysis date: | November 16, 2019, 05:41:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 189B17B277848D1A04E5541F9B9885F5 |
| SHA1: | 6F8FF328A2B65F5932EDE3987C27297DCD2912BB |
| SHA256: | 6F2F11590CA82FB8C2600BC51CB0F26AC8D24E2D7750E7BCFAAD9F91628725FD |
| SSDEEP: | 3:N1KNKtm:CY8 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 992)
Reads the hosts file
- chrome.exe (PID: 992)
- chrome.exe (PID: 1876)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
57
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://soborusy.site" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18074830552748054838 --mojo-platform-channel-handle=3956 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=2223008568748137655 --mojo-platform-channel-handle=1540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1880 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15255416904491273378 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1952 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4804557001160552424 --mojo-platform-channel-handle=4168 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2600 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14522108910399060820 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2228 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18030182373137088141 --mojo-platform-channel-handle=3876 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17682179735803924083 --mojo-platform-channel-handle=3924 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,9774082435878774697,761561899173309344,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15087134091966564224 --mojo-platform-channel-handle=3564 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
168
Read events
130
Write events
35
Delete events
3
Modification events
| (PID) Process: | (2364) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 992-13218356478809000 |
Value: 259 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (992) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
17
Text files
216
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\a27f2d00-626c-4a0a-8161-f120ec669b4c.tmp | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF39aa25.TMP | text | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39aa15.TMP | text | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF39ab00.TMP | text | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 992 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
21
TCP/UDP connections
27
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1876 | chrome.exe | GET | 200 | 188.165.252.220:80 | http://soborusy.site/img/mir-logo-h229px.png | FR | image | 11.0 Kb | suspicious |
1876 | chrome.exe | GET | 200 | 188.165.252.220:80 | http://soborusy.site/img/p/m20.jpg | FR | image | 40.1 Kb | suspicious |
1876 | chrome.exe | GET | 200 | 188.165.252.220:80 | http://soborusy.site/img/p/m22.jpg | FR | image | 46.7 Kb | suspicious |
1876 | chrome.exe | GET | 200 | 188.165.252.220:80 | http://soborusy.site/img/p/m21.jpg | FR | image | 34.6 Kb | suspicious |
1876 | chrome.exe | GET | 200 | 188.165.252.220:80 | http://soborusy.site/img/piggy-bank.png | FR | image | 3.81 Kb | suspicious |
1876 | chrome.exe | GET | 200 | 188.165.252.220:80 | http://soborusy.site/img/p/w20.jpg | FR | image | 39.5 Kb | suspicious |
1876 | chrome.exe | GET | 200 | 188.165.252.220:80 | http://soborusy.site/img/p/w19.jpg | FR | image | 36.7 Kb | suspicious |
1876 | chrome.exe | GET | 200 | 188.165.252.220:80 | http://soborusy.site/img/coin.gif | FR | image | 183 Kb | suspicious |
1876 | chrome.exe | GET | 200 | 188.165.252.220:80 | http://soborusy.site/js/redirect.js | FR | text | 3.71 Kb | suspicious |
1876 | chrome.exe | GET | 200 | 188.165.252.220:80 | http://soborusy.site/css/animate.min.css | FR | text | 3.74 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 188.165.252.220:80 | soborusy.site | OVH SAS | FR | suspicious |
1876 | chrome.exe | 188.165.252.220:80 | soborusy.site | OVH SAS | FR | suspicious |
1876 | chrome.exe | 172.217.18.100:443 | www.google.com | Google Inc. | US | whitelisted |
1876 | chrome.exe | 172.217.22.74:443 | translate.googleapis.com | Google Inc. | US | whitelisted |
1876 | chrome.exe | 172.217.16.206:443 | clients2.google.com | Google Inc. | US | whitelisted |
1876 | chrome.exe | 172.217.18.110:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
1876 | chrome.exe | 172.217.22.65:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1876 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
1876 | chrome.exe | 185.180.12.140:80 | r1---sn-n02xgoxufvg3-8pxe.gvt1.com | Datacamp Limited | AT | whitelisted |
— | — | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
soborusy.site |
| suspicious |
accounts.google.com |
| shared |
api-maps.yandex.ru |
| whitelisted |
www.google.com |
| malicious |
translate.googleapis.com |
| whitelisted |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r3---sn-n02xgoxufvg3-8pxe.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |