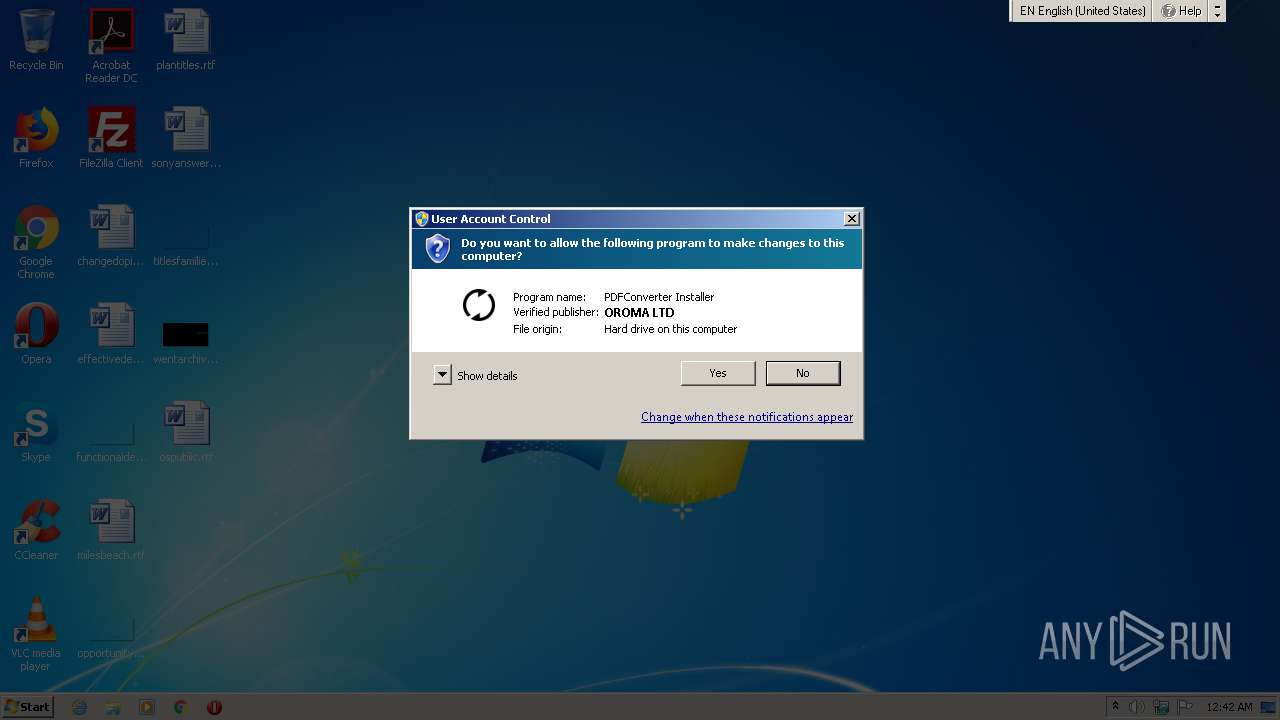
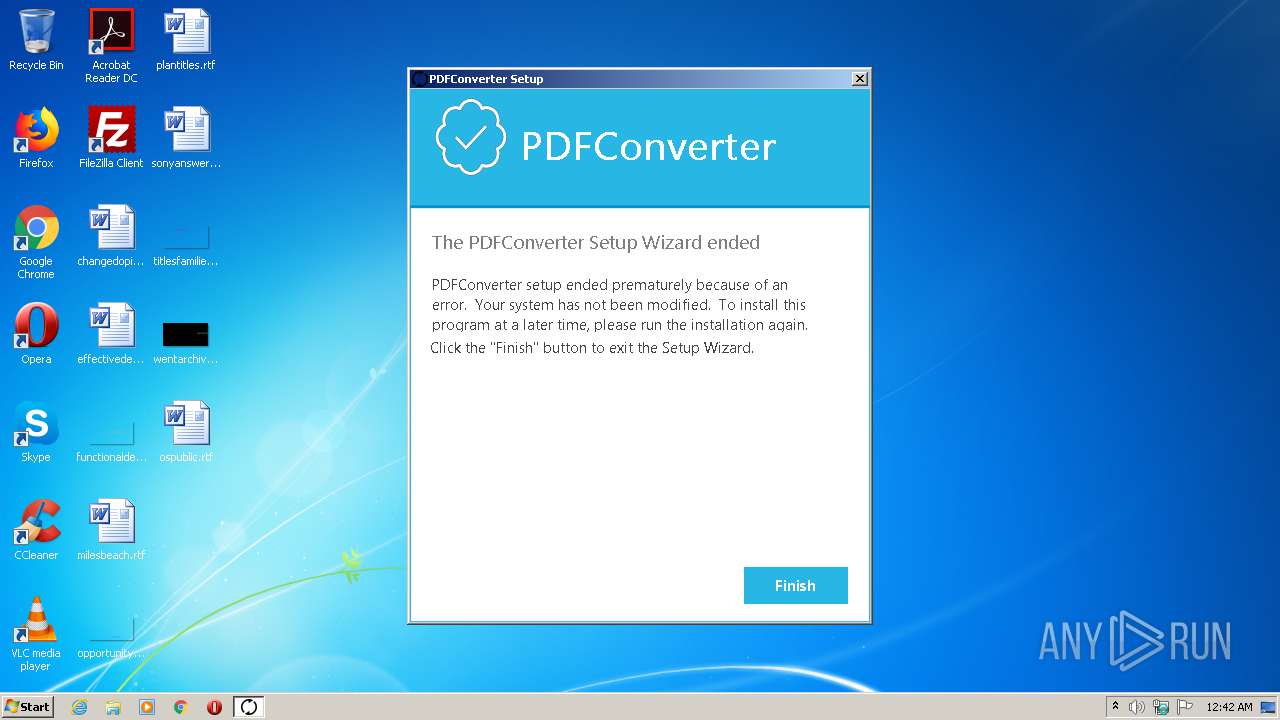
| File name: | PDFConverter Installation.exe |
| Full analysis: | https://app.any.run/tasks/8f23f64b-e061-4fdd-a88a-137470913793 |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2021, 23:41:41 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | CEBB4265722782A282058EACAF745964 |
| SHA1: | 5BEAE7B3D59B5633FEAD9012C328434B714F10F6 |
| SHA256: | 6F28EF3ED80C790A08FFBDA3DEF1C839E87D9FF5091B651A6FCDFF9C854FAB67 |
| SSDEEP: | 49152:wG8N6y19hpFMPDpKmXWUB4rcMruoxJrV/shPM6IMpctsd5jN8cqBFdBj9Vdkt0U+:oN6ynFMPDpKmj4rcExdBG2lSnWAx6 |
MALICIOUS
Changes settings of System certificates
- PDFConverter Installation.exe (PID: 664)
- MsiExec.exe (PID: 3744)
Drops executable file immediately after starts
- PDFConverter Installation.exe (PID: 664)
Loads dropped or rewritten executable
- PDFConverter Installation.exe (PID: 664)
Loads the Task Scheduler DLL interface
- MsiExec.exe (PID: 3744)
- PDFConverter Installation.exe (PID: 664)
SUSPICIOUS
Executable content was dropped or overwritten
- PDFConverter Installation.exe (PID: 664)
Creates files in the user directory
- PDFConverter Installation.exe (PID: 664)
Drops a file that was compiled in debug mode
- PDFConverter Installation.exe (PID: 664)
Adds / modifies Windows certificates
- PDFConverter Installation.exe (PID: 664)
- MsiExec.exe (PID: 3744)
INFO
Reads settings of System Certificates
- MsiExec.exe (PID: 3744)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3744)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| ProductVersion: | 1.0.0 |
|---|---|
| ProductName: | PDFConverter |
| OriginalFileName: | PDFConverter Installation.exe |
| LegalCopyright: | Copyright (C) 2021 PDFConverter |
| InternalName: | PDFConverter Installation |
| FileVersion: | 1.0.0 |
| FileDescription: | PDFConverter Installer |
| CompanyName: | PDFConverter |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Win32 |
| FileFlags: | Debug |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.0.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0x1228e7 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 672256 |
| CodeSize: | 1537024 |
| LinkerVersion: | 14.28 |
| PEType: | PE32 |
| TimeStamp: | 2021:01:25 16:26:02+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Jan-2021 15:26:02 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | PDFConverter |
| FileDescription: | PDFConverter Installer |
| FileVersion: | 1.0.0 |
| InternalName: | PDFConverter Installation |
| LegalCopyright: | Copyright (C) 2021 PDFConverter |
| OriginalFileName: | PDFConverter Installation.exe |
| ProductName: | PDFConverter |
| ProductVersion: | 1.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000108 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 25-Jan-2021 15:26:02 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0017721F | 0x00177400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.448 |
.rdata | 0x00179000 | 0x0005EA4C | 0x0005EC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.59253 |
.data | 0x001D8000 | 0x00006E40 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.06624 |
.rsrc | 0x001DF000 | 0x00026974 | 0x00026A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.74362 |
.reloc | 0x00206000 | 0x000196E0 | 0x00019800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.56137 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.18998 | 1909 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 1.0228 | 67624 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 1.14828 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 1.26819 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 1.38543 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 1.5584 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 3.37783 | 1116 | Latin 1 / Western European | English - United States | RT_STRING |
10 | 3.34881 | 836 | Latin 1 / Western European | English - United States | RT_STRING |
11 | 3.31743 | 760 | Latin 1 / Western European | English - United States | RT_STRING |
12 | 3.23118 | 1432 | Latin 1 / Western European | English - United States | RT_STRING |
Imports
KERNEL32.dll |
msi.dll (delay-loaded) |
Total processes
42
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 372 | "C:\Users\admin\AppData\Local\Temp\PDFConverter Installation.exe" | C:\Users\admin\AppData\Local\Temp\PDFConverter Installation.exe | — | explorer.exe | |||||||||||
User: admin Company: PDFConverter Integrity Level: MEDIUM Description: PDFConverter Installer Exit code: 3221226540 Version: 1.0.0 Modules
| |||||||||||||||
| 664 | "C:\Users\admin\AppData\Local\Temp\PDFConverter Installation.exe" | C:\Users\admin\AppData\Local\Temp\PDFConverter Installation.exe | explorer.exe | ||||||||||||
User: admin Company: PDFConverter Integrity Level: HIGH Description: PDFConverter Installer Exit code: 1602 Version: 1.0.0 Modules
| |||||||||||||||
| 3744 | C:\Windows\system32\MsiExec.exe -Embedding AAC41BF8F1244285C73963CEA3D2B29F C | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
217
Read events
184
Write events
32
Delete events
1
Modification events
| (PID) Process: | (664) PDFConverter Installation.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (664) PDFConverter Installation.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\2B8F1B57330DBBA2D07A6C51F70EE90DDAB9AD8E |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000001BFE69D191B71933A372A80FE155E5B50F000000010000003000000066B764A96581128168CF208E374DDA479D54E311F32457F4AEE0DBD2A6C8D171D531289E1CD22BFDBBD4CFD9796254830300000001000000140000002B8F1B57330DBBA2D07A6C51F70EE90DDAB9AD8E0B00000001000000100000005300650063007400690067006F0000001D0000000100000010000000885010358D29A38F059B028559C95F901400000001000000140000005379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB620000000100000020000000E793C9B02FD8AA13E21C31228ACCB08119643B749C898964B1746D46C3D4CBD253000000010000002600000030243022060C2B06010401B231010201050130123010060A2B0601040182373C0101030200C0090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B06010505070308060A2B0601040182370A030406082B0601050507030606082B06010505070307190000000100000010000000EA6089055218053DD01E37E1D806EEDF2000000001000000E2050000308205DE308203C6A003020102021001FD6D30FCA3CA51A81BBC640E35032D300D06092A864886F70D01010C0500308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F72697479301E170D3130303230313030303030305A170D3338303131383233353935395A308188310B3009060355040613025553311330110603550408130A4E6577204A6572736579311430120603550407130B4A65727365792043697479311E301C060355040A131554686520555345525452555354204E6574776F726B312E302C06035504031325555345525472757374205253412043657274696669636174696F6E20417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A028202010080126517360EC3DB08B3D0AC570D76EDCD27D34CAD508361E2AA204D092D6409DCCE899FCC3DA9ECF6CFC1DCF1D3B1D67B3728112B47DA39C6BC3A19B45FA6BD7D9DA36342B676F2A93B2B91F8E26FD0EC162090093EE2E874C918B491D46264DB7FA306F188186A90223CBCFE13F087147BF6E41F8ED4E451C61167460851CB8614543FBC33FE7E6C9CFF169D18BD518E35A6A766C87267DB2166B1D49B7803C0503AE8CCF0DCBC9E4CFEAF0596351F575AB7FFCEF93DB72CB6F654DDC8E7123A4DAE4C8AB75C9AB4B7203DCA7F2234AE7E3B68660144E7014E46539B3360F794BE5337907343F332C353EFDBAAFE744E69C76B8C6093DEC4C70CDFE132AECC933B517895678BEE3D56FE0CD0690F1B0FF325266B336DF76E47FA7343E57E0EA566B1297C3284635589C40DC19354301913ACD37D37A7EB5D3A6C355CDB41D712DAA9490BDFD8808A0993628EB566CF2588CD84B8B13FA4390FD9029EEB124C957CF36B05A95E1683CCB867E2E8139DCC5B82D34CB3ED5BFFDEE573AC233B2D00BF3555740949D849581A7F9236E651920EF3267D1C4D17BCC9EC4326D0BF415F40A94444F499E757879E501F5754A83EFD74632FB1506509E658422E431A4CB4F0254759FA041E93D426464A5081B2DEBE78B7FC6715E1C957841E0F63D6E962BAD65F552EEA5CC62808042539B80E2BA9F24C971C073F0D52F5EDEF2F820F0203010001A3423040301D0603551D0E041604145379BF5AAA2B4ACF5480E1D89BC09DF2B20366CB300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF300D06092A864886F70D01010C050003820201005CD47C0DCFF7017D4199650C73C5529FCBF8CF99067F1BDA43159F9E0255579614F1523C27879428ED1F3A0137A276FC5350C0849BC66B4EBA8C214FA28E556291F36915D8BC88E3C4AA0BFDEFA8E94B552A06206D55782919EE5F305C4B241155FF249A6E5E2A2BEE0B4D9F7FF70138941495430709FB60A9EE1CAB128CA09A5EA7986A596D8B3F08FBC8D145AF18156490120F73282EC5E2244EFC58ECF0F445FE22B3EB2F8ED2D9456105C1976FA876728F8B8C36AFBF0D05CE718DE6A66F1F6CA67162C5D8D083720CF16711890C9C134C7234DFBCD571DFAA71DDE1B96C8C3C125D65DABD5712B6436BFFE5DE4D661151CF99AEEC17B6E871918CDE49FEDD3571A21527941CCF61E326BB6FA36725215DE6DD1D0B2E681B3B82AFEC836785D4985174B1B9998089FF7F78195C794A602E9240AE4C372A2CC9C762C80E5DF7365BCAE0252501B4DD1A079C77003FD0DCD5EC3DD4FABB3FCC85D66F7FA92DDFB902F7F5979AB535DAC367B0874AA9289E238EFF5C276BE1B04FF307EE002ED45987CB524195EAF447D7EE6441557C8D590295DD629DC2B9EE5A287484A59BB790C70C07DFF589367432D628C1B0B00BE09C4CC31CD6FCE369B54746812FA282ABD3634470C48DFF2D33BAAD8F7BB57088AE3E19CF4028D8FCC890BB5D9922F552E658C51F883143EE881DD7C68E3C436A1DA718DE7D3D16F162F9CA90A8FD | |||
| (PID) Process: | (664) PDFConverter Installation.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\AFE5D244A8D1194230FF479FE2F897BBCD7A8CB4 |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000001B31B0714036CC143691ADC43EFDEC180F0000000100000030000000761613F4CD8607508C3D520FBEFE68773735FC73746F42A9FD6254BA3B72F0047994E5AF57677CF6D2C1965984965DF1030000000100000014000000AFE5D244A8D1194230FF479FE2F897BBCD7A8CB41D0000000100000010000000CB39C3D4272CDF63774E1DB810C5A89E140000000100000014000000BBAF7E023DFAA6F13C848EADEE3898ECD93232D462000000010000002000000052F0E1C4E58EC629291B60317F074671B85D7EA80D5B07273463534B32B4023453000000010000002600000030243022060C2B06010401B231010201050130123010060A2B0601040182373C0101030200C00B000000010000003A0000005300650063007400690067006F002000280066006F0072006D00650072006C007900200043006F006D006F0064006F0020004300410029000000090000000100000054000000305206082B0601050507030106082B0601050507030206082B0601050507030406082B0601050507030306082B06010505070308060A2B0601040182370A030406082B0601050507030606082B0601050507030719000000010000001000000082218FFB91733E64136BE5719F57C3A12000000001000000DC050000308205D8308203C0A00302010202104CAAF9CADB636FE01FF74ED85B03869D300D06092A864886F70D01010C0500308185310B3009060355040613024742311B30190603550408131247726561746572204D616E636865737465723110300E0603550407130753616C666F7264311A3018060355040A1311434F4D4F444F204341204C696D69746564312B302906035504031322434F4D4F444F205253412043657274696669636174696F6E20417574686F72697479301E170D3130303131393030303030305A170D3338303131383233353935395A308185310B3009060355040613024742311B30190603550408131247726561746572204D616E636865737465723110300E0603550407130753616C666F7264311A3018060355040A1311434F4D4F444F204341204C696D69746564312B302906035504031322434F4D4F444F205253412043657274696669636174696F6E20417574686F7269747930820222300D06092A864886F70D01010105000382020F003082020A028202010091E85492D20A56B1AC0D24DDC5CF446774992B37A37D23700071BC53DFC4FA2A128F4B7F1056BD9F7072B7617FC94B0F17A73DE3B00461EEFF1197C7F4863E0AFA3E5CF993E6347AD9146BE79CB385A0827A76AF7190D7ECFD0DFA9C6CFADFB082F4147EF9BEC4A62F4F7F997FB5FC674372BD0C00D689EB6B2CD3ED8F981C14AB7EE5E36EFCD8A8E49224DA436B62B855FDEAC1BC6CB68BF30E8D9AE49B6C6999F878483045D5ADE10D3C4560FC32965127BC67C3CA2EB66BEA46C7C720A0B11F65DE4808BAA44EA9F283463784EBE8CC814843674E722A9B5CBD4C1B288A5C227BB4AB98D9EEE05183C309464E6D3E99FA9517DA7C3357413C8D51ED0BB65CAF2C631ADF57C83FBCE95DC49BAF4599E2A35A24B4BAA9563DCF6FAAFF4958BEF0A8FFF4B8ADE937FBBAB8F40B3AF9E843421E89D884CB13F1D9BBE18960B88C2856AC141D9C0AE771EBCF0EDD3DA996A148BD3CF7AFB50D224CC01181EC563BF6D3A2E25BB7B204225295809369E88E4C65F191032D707402EA8B671529695202BBD7DF506A5546BFA0A328617F70D0C3A2AA2C21AA47CE289C064576BF821827B4D5AEB4CB50E66BF44C867130E9A6DF1686E0D8FF40DDFBD042887FA3333A2E5C1E41118163CE18716B2BECA68AB7315C3A6A47E0C37959D6201AAFF26A98AA72BC574AD24B9DBB10FCB04C41E5ED1D3D5E289D9CCCBFB351DAA747E584530203010001A3423040301D0603551D0E04160414BBAF7E023DFAA6F13C848EADEE3898ECD93232D4300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF300D06092A864886F70D01010C050003820201000AF1D54684B7AE51BB6CB24D411400934C9CCBE5C054CFA0258E02F9FDB0A20DF520983C132DAC56A2B0D67E1192E92EBA9E2E9A72B1BD19446C6135A29AB41612695A8CE1D73EA41AE82F03F4AE611D101B2AA48B7AC5FE05A6E1C0D6C8FE9EAE8F2BBA3D99F8D8730958466EA69CF4D727D395DA3783721CD373E0A2479903385DD5497900291CC7EC9B201C0724695778B239FC3A84A0B59C7C8DBF2E936227B739DA1718AEBD3C0968FF849B3CD5D60B03E3579E14F7D1EB4FC8BD8723B7B6494379855CBAEB920BA1C6E868A84C16B11A990AE8532C92BBA10918750C65A87BCB23B71AC22885C31BFFD02B62EFA47B099198678C1401CD68066A6321750380888A6E81C685F2A9A42DE7F4A524104783CACDF48D7958B1069BE71A2AD99D01D7947DED034ACAF0DBE8A9013EF55699C91E8E493DBBE509B9E04F49923D168240CCCC59C6E63AED122E693C6C95B1FDAA1D7B7F86BE1E0E3246FBFB138F757F4C8B4B4663FE00344070C1C3B9A1DDA670E204B341BCE98091EA649C7AE12203A99C6E6F0E654F6C87875EF36EA0F975A59B40E853B2279D4AB9C077218DFF87F2DEBC8CEF17DFB7490BD1F26E300B1A0E4E76ED11FCF5E956B27DBFC76D0A938CA5D0C0B61DBE3A4E94A2D76E6C0BC28A7CFA20F3C4E4E5CD0DA8CB9192B17C85ECB51469660E82E7CDCEC82DA6517F21C1355385064A5D9FADBB1B5F74 | |||
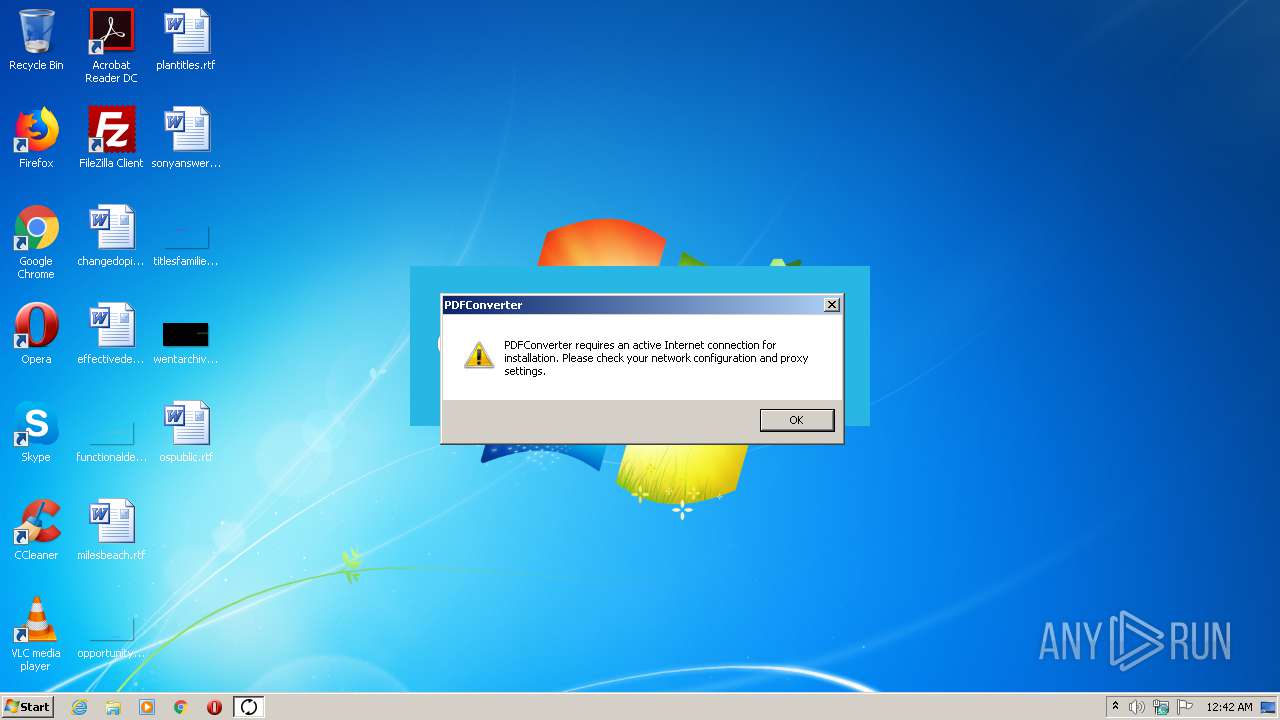
| (PID) Process: | (3744) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3744) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3744) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3744) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3744) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3744) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3744) MsiExec.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
8
Suspicious files
4
Text files
64
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 664 | PDFConverter Installation.exe | C:\Users\admin\AppData\Roaming\PDFConverter\PDFConverter 1.0.0\install\FD7DF1F\PDFConverter Installation.msi | — | |
MD5:— | SHA256:— | |||
| 664 | PDFConverter Installation.exe | C:\Users\admin\AppData\Local\Temp\MSI975A.tmp | — | |
MD5:— | SHA256:— | |||
| 664 | PDFConverter Installation.exe | C:\Users\admin\AppData\Local\Temp\MSI97D8.tmp | — | |
MD5:— | SHA256:— | |||
| 664 | PDFConverter Installation.exe | C:\Users\admin\AppData\Local\Temp\MSI97F8.tmp | — | |
MD5:— | SHA256:— | |||
| 664 | PDFConverter Installation.exe | C:\Users\admin\AppData\Local\Temp\MSI9847.tmp | — | |
MD5:— | SHA256:— | |||
| 664 | PDFConverter Installation.exe | C:\Users\admin\AppData\Local\Temp\MSI9897.tmp | — | |
MD5:— | SHA256:— | |||
| 664 | PDFConverter Installation.exe | C:\Users\admin\AppData\Local\Temp\MSI98C7.tmp | — | |
MD5:— | SHA256:— | |||
| 3744 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\Cab9C7A.tmp | — | |
MD5:— | SHA256:— | |||
| 3744 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\Tar9C7B.tmp | — | |
MD5:— | SHA256:— | |||
| 3744 | MsiExec.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\fa[1].htm | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3744 | MsiExec.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA1X0QsRKSo8Zt%2FNzzrovmU%3D | US | der | 471 b | whitelisted |
3744 | MsiExec.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3744 | MsiExec.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3744 | MsiExec.exe | 3.216.73.132:443 | didiserver.herokuapp.com | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
didiserver.herokuapp.com |
| unknown |
ocsp.digicert.com |
| whitelisted |