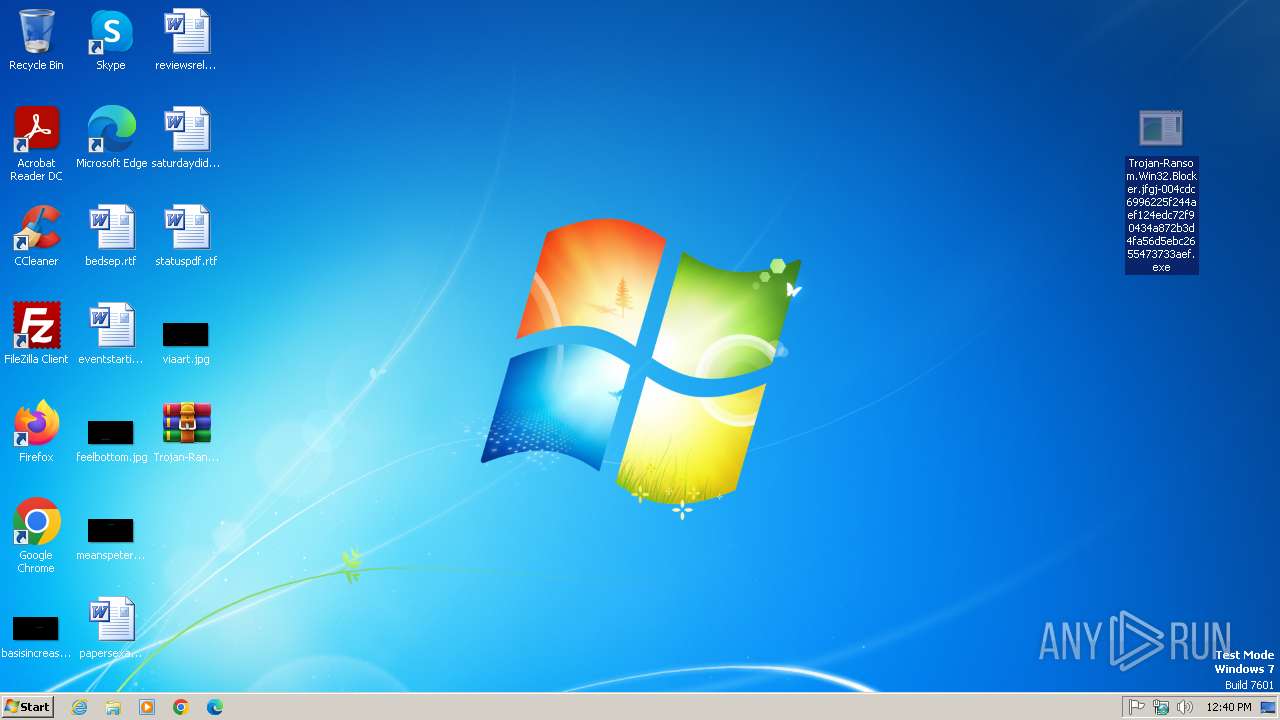
| File name: | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.7z |
| Full analysis: | https://app.any.run/tasks/567311f1-707d-4630-baa0-cdf3993c2c83 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 11:40:12 |
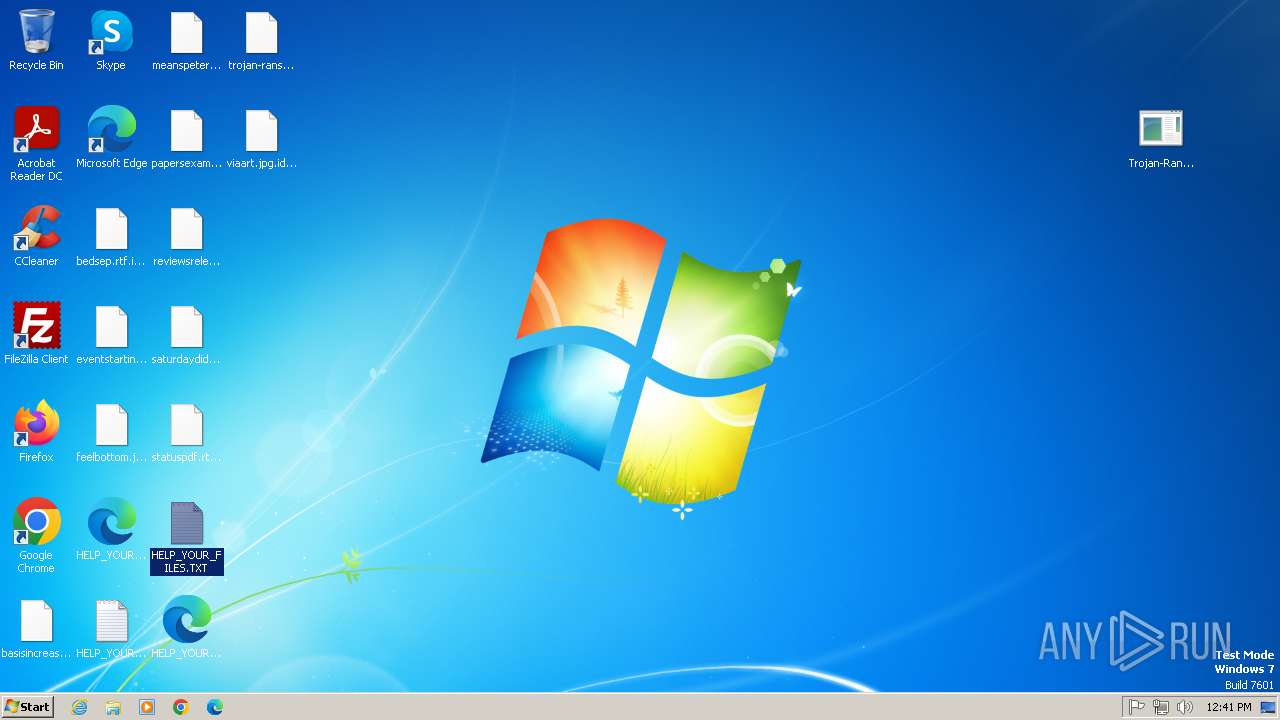
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
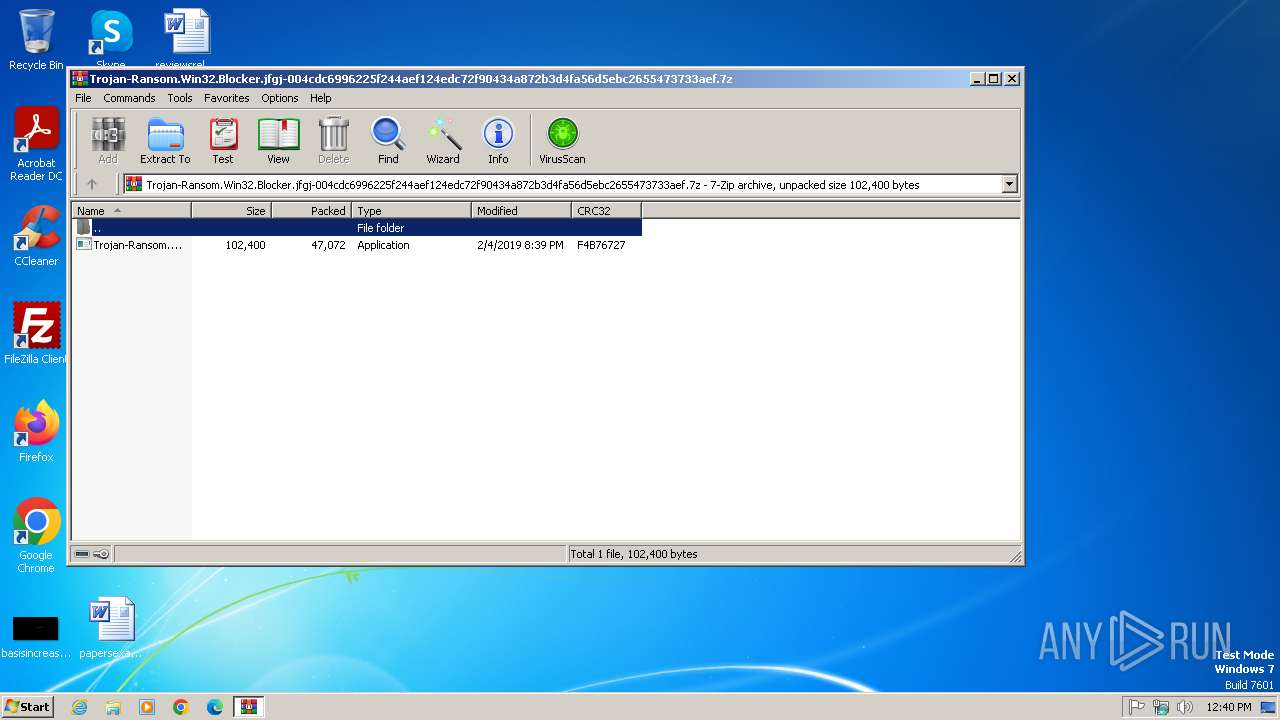
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 55F8292F5F4500A3184BA67E3DCC2A20 |
| SHA1: | F42F630D5178DF7DD30288F9E267ABE1AD5DB931 |
| SHA256: | 6F18470E1FC991AB2546FAA2AFEC800F5293B30D8053FB68135B203FA02269C2 |
| SSDEEP: | 1536:rcguFYT+Uem1E9xs4/mqA+sH1C2EBw185:rcg0sLem1uu4/mpx0Twu5 |
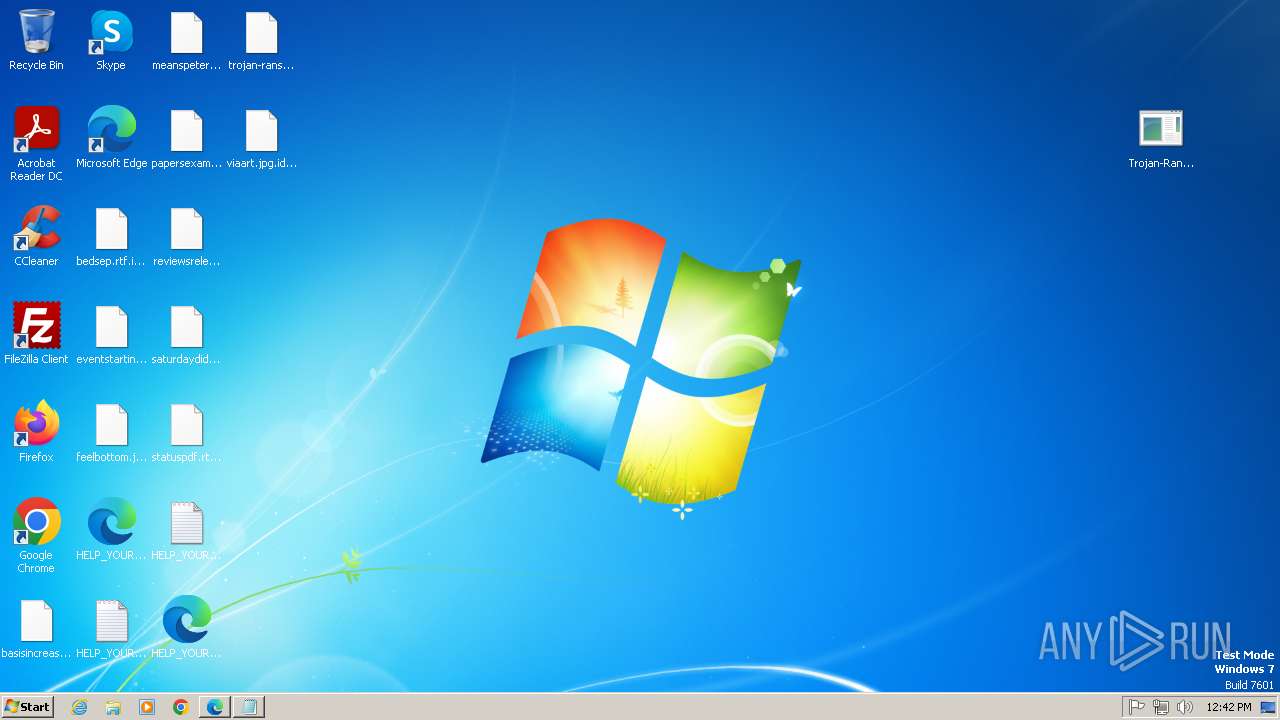
MALICIOUS
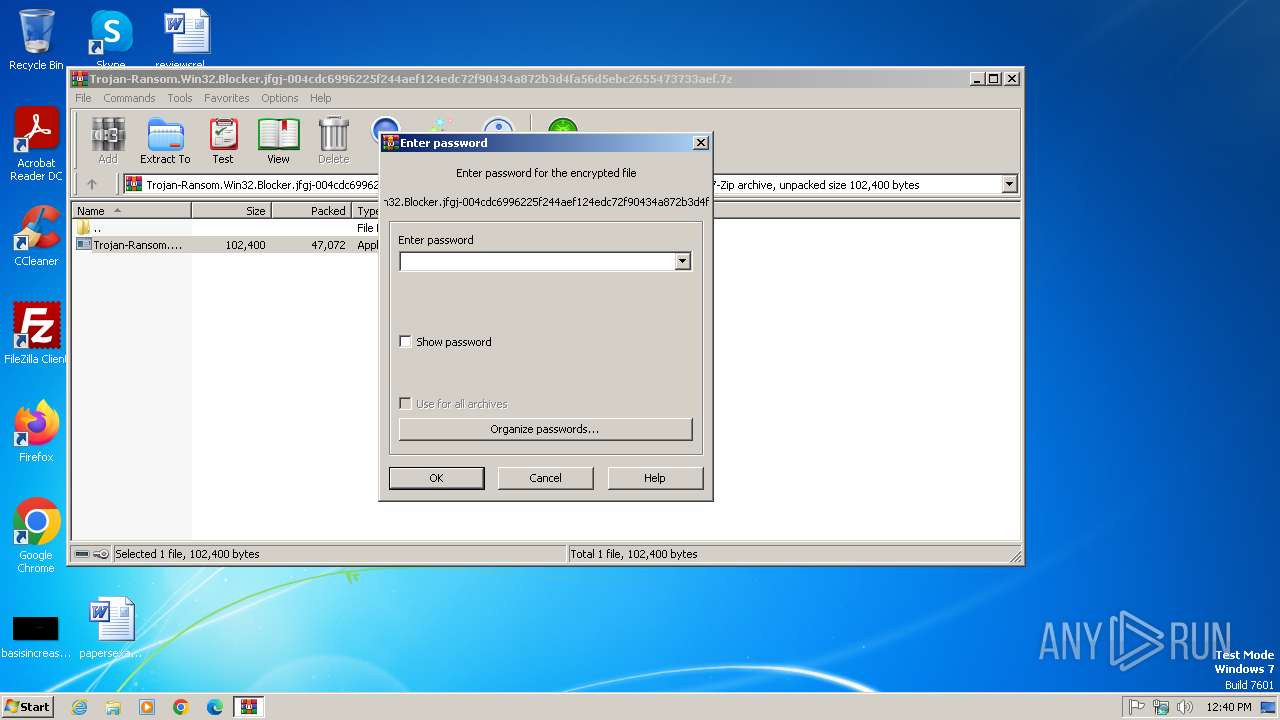
Generic archive extractor
- WinRAR.exe (PID: 2692)
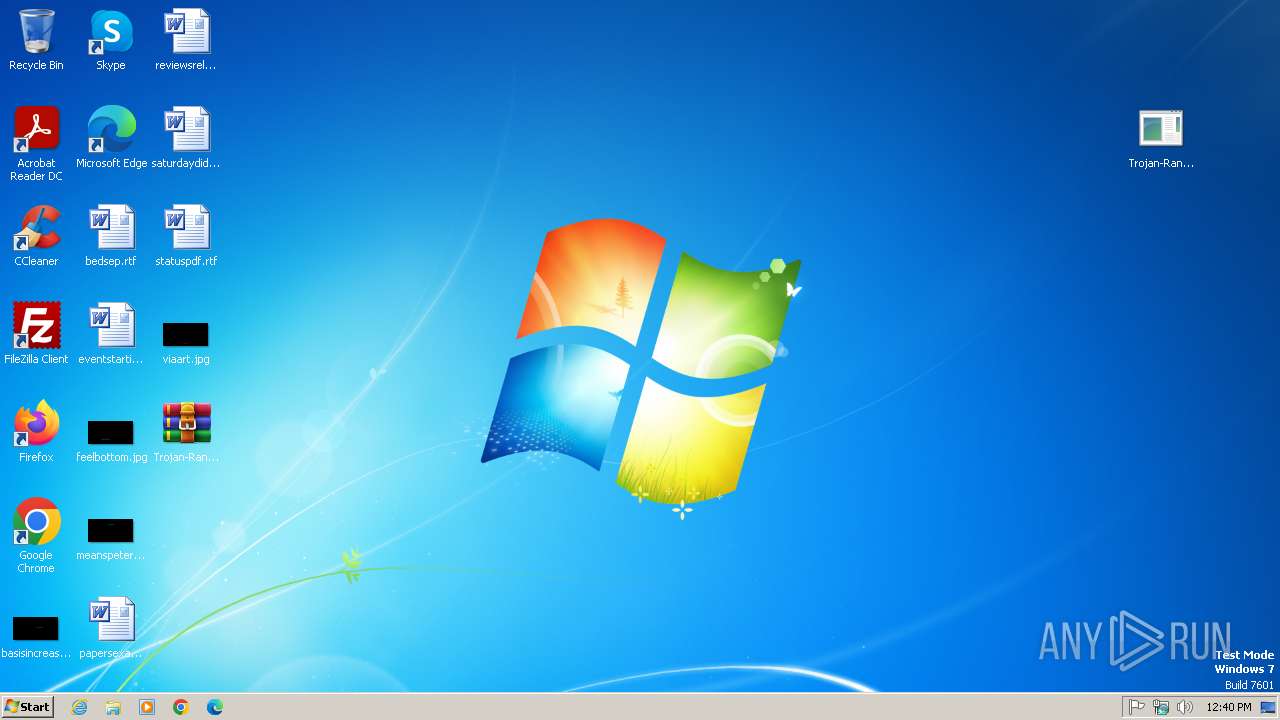
Changes the autorun value in the registry
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
SUSPICIOUS
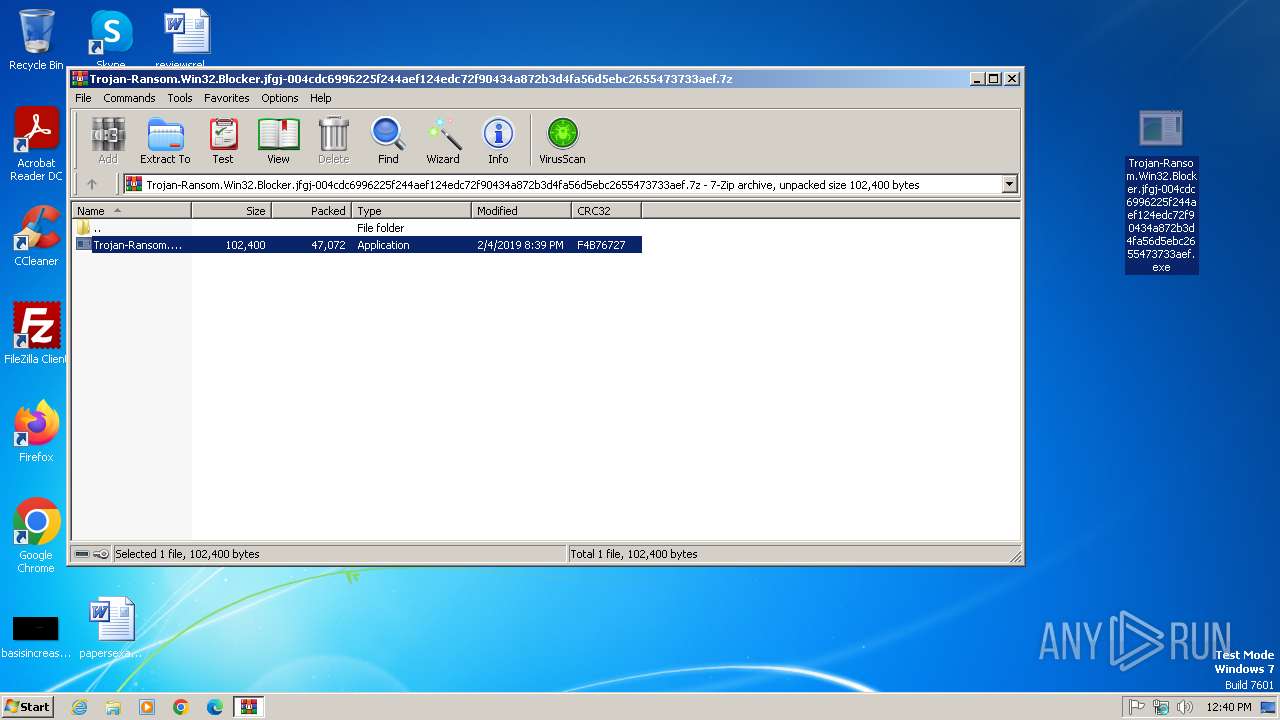
Executable content was dropped or overwritten
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
Reads the Internet Settings
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
Reads security settings of Internet Explorer
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
There is functionality for taking screenshot (YARA)
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
Likely accesses (executes) a file from the Public directory
- notepad.exe (PID: 3800)
- msedge.exe (PID: 3804)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2692)
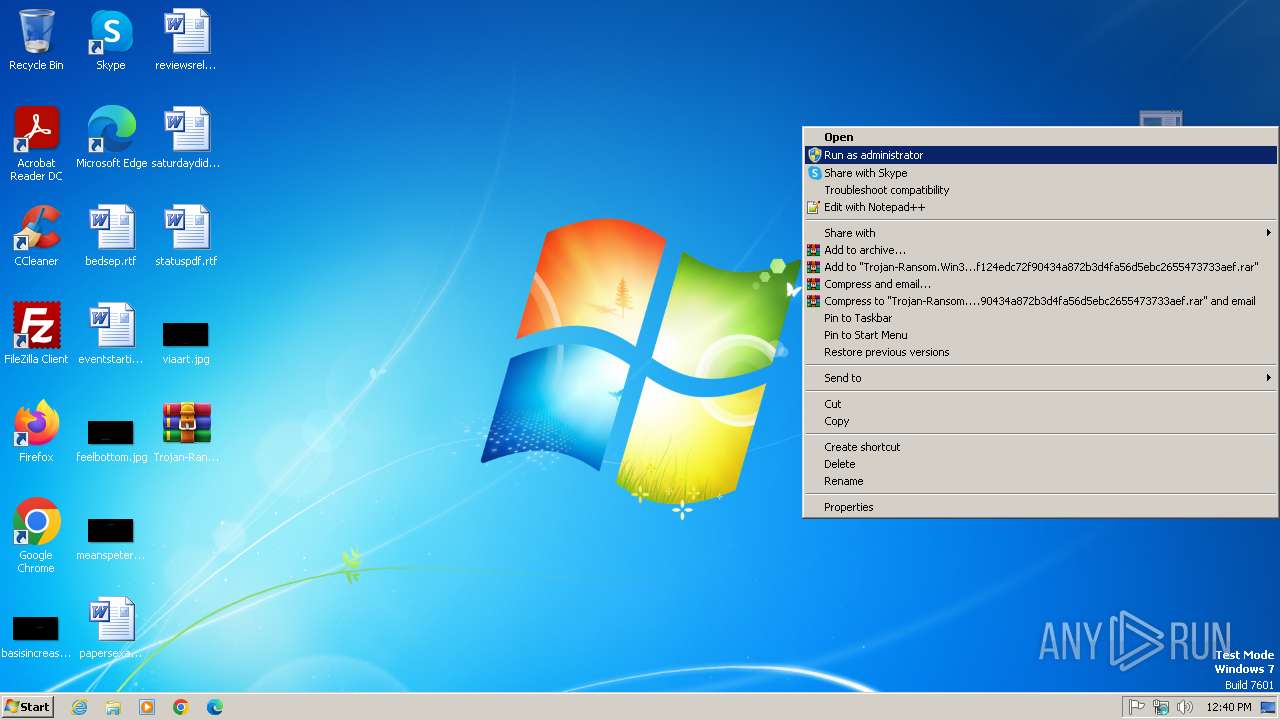
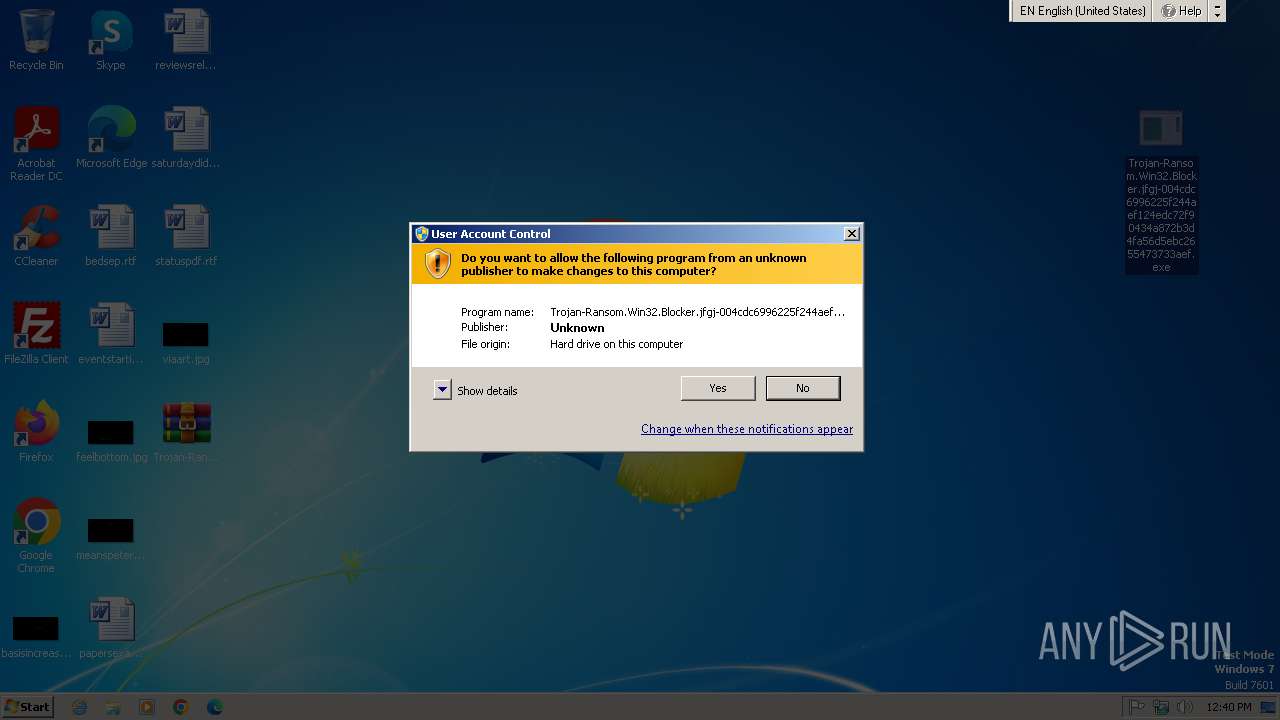
Manual execution by a user
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
- notepad.exe (PID: 3800)
- msedge.exe (PID: 3804)
The sample compiled with english language support
- WinRAR.exe (PID: 2692)
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
Checks supported languages
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
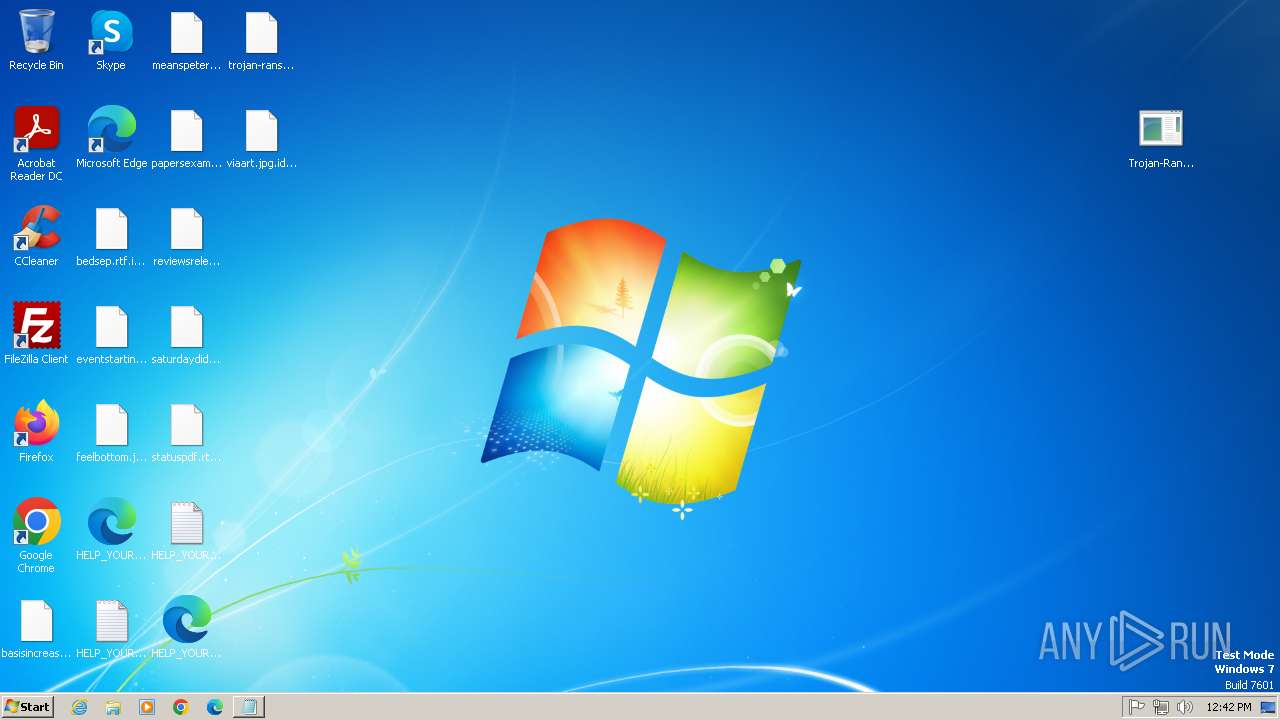
Creates files or folders in the user directory
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
Reads the computer name
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
Reads the machine GUID from the registry
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
Checks proxy server information
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
Application launched itself
- msedge.exe (PID: 3804)
- msedge.exe (PID: 3844)
Creates files in the program directory
- Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2019:02:04 20:39:52+00:00 |
| ArchivedFileName: | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe |
Total processes
62
Monitored processes
19
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3468 --field-trial-handle=1304,i,14142078821202527850,13342938108099500667,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6d15f598,0x6d15f5a8,0x6d15f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2076 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --disable-gpu-compositing --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=4212 --field-trial-handle=1304,i,14142078821202527850,13342938108099500667,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2692 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2888 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1280 --field-trial-handle=1304,i,14142078821202527850,13342938108099500667,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 2940 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3248 --field-trial-handle=1304,i,14142078821202527850,13342938108099500667,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 3028 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=1636 --field-trial-handle=1304,i,14142078821202527850,13342938108099500667,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 3096 | "C:\Users\admin\Desktop\Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe" | C:\Users\admin\Desktop\Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | explorer.exe | ||||||||||||
User: admin Company: SynapticosSoft, Corporation. Integrity Level: HIGH Description: KckataKm Version: 20,7,19,24 Modules
| |||||||||||||||
| 3136 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=109.0.5414.149 "--annotation=exe=C:\Program Files\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win32 "--annotation=prod=Microsoft Edge" --annotation=ver=109.0.1518.115 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd8,0x6d15f598,0x6d15f5a8,0x6d15f5b4 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 3192 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1468 --field-trial-handle=1304,i,14142078821202527850,13342938108099500667,131072 --enable-features=msMicrosoftRootStoreUsed /prefetch:2 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
Total events
5 333
Read events
5 229
Write events
91
Delete events
13
Modification events
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.7z | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2692) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
Executable files
2
Suspicious files
319
Text files
237
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | C:\Users\admin\AppData\Roaming\AdobeFlashPlayer_c4ba36471c9b74e8.exe | executable | |
MD5:A0FED8DE59E6F6CE77DA7788FAEF5489 | SHA256:004CDC6996225F244AEF124EDC72F90434A872B3D4FA56D5EBC2655473733AEF | |||
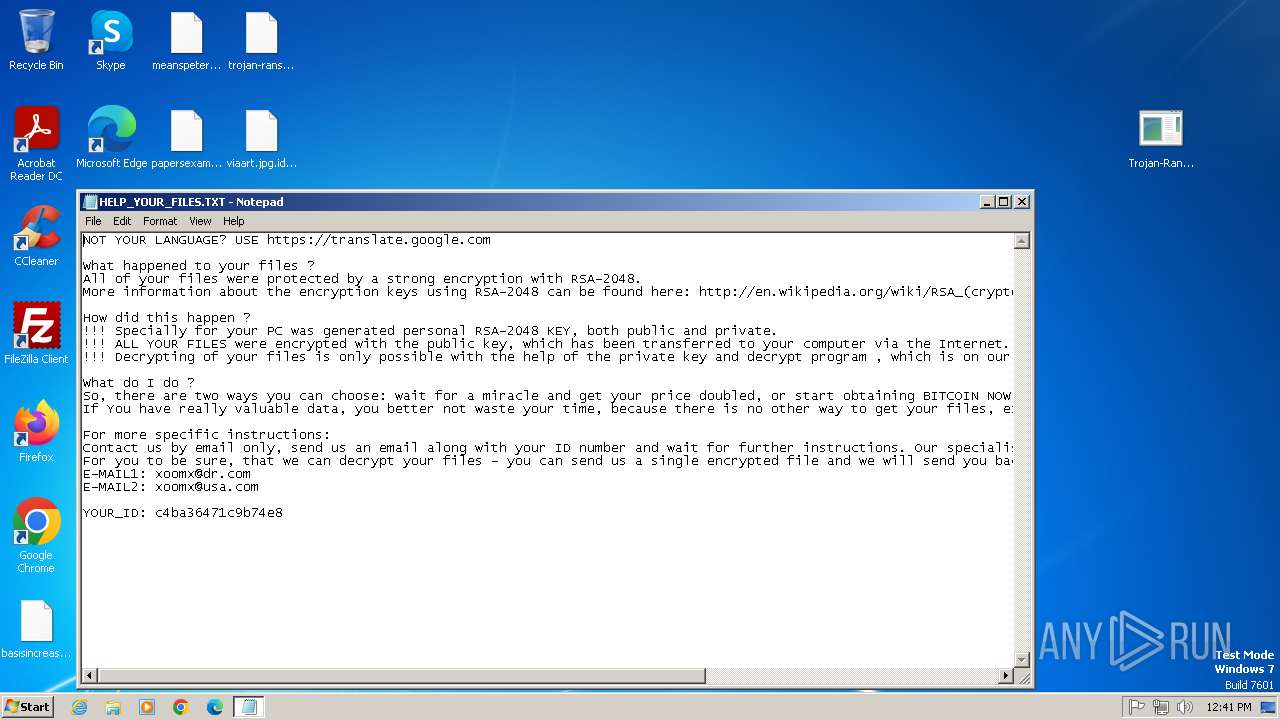
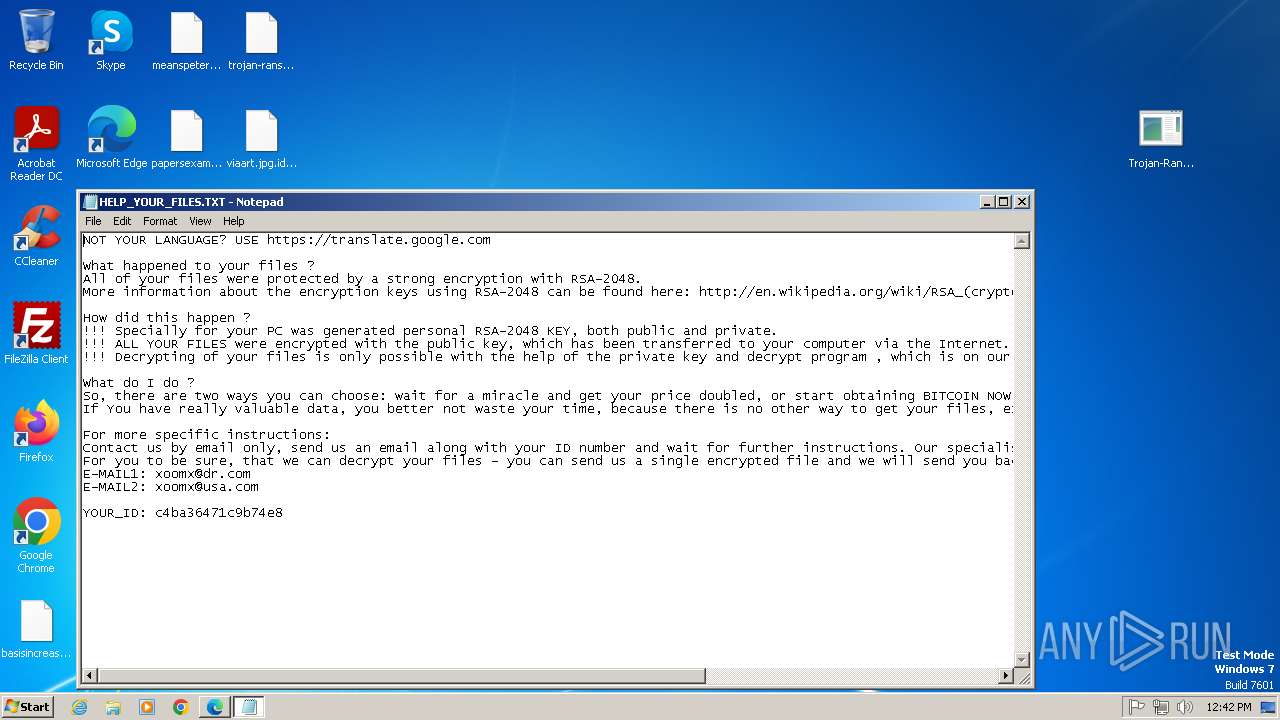
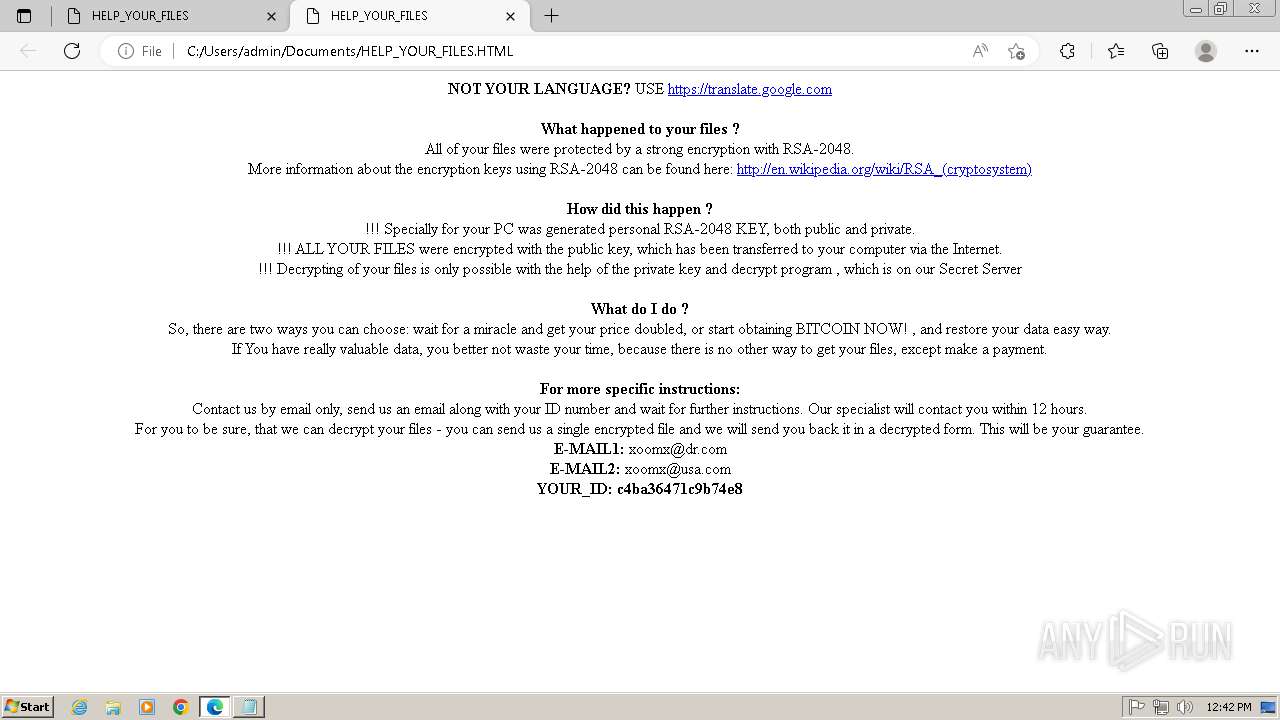
| 3096 | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | C:\ProgramData\Adobe\HELP_YOUR_FILES.TXT | binary | |
MD5:6405A6E4353774FFA79E5093311C20D2 | SHA256:F3A2CEE372CA3FD2CABB512528C4EB6D9A174594FACD6DDFBFC5004C6A8A6DB1 | |||
| 3096 | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | C:\Users\HELP_YOUR_FILES.TXT | binary | |
MD5:6405A6E4353774FFA79E5093311C20D2 | SHA256:F3A2CEE372CA3FD2CABB512528C4EB6D9A174594FACD6DDFBFC5004C6A8A6DB1 | |||
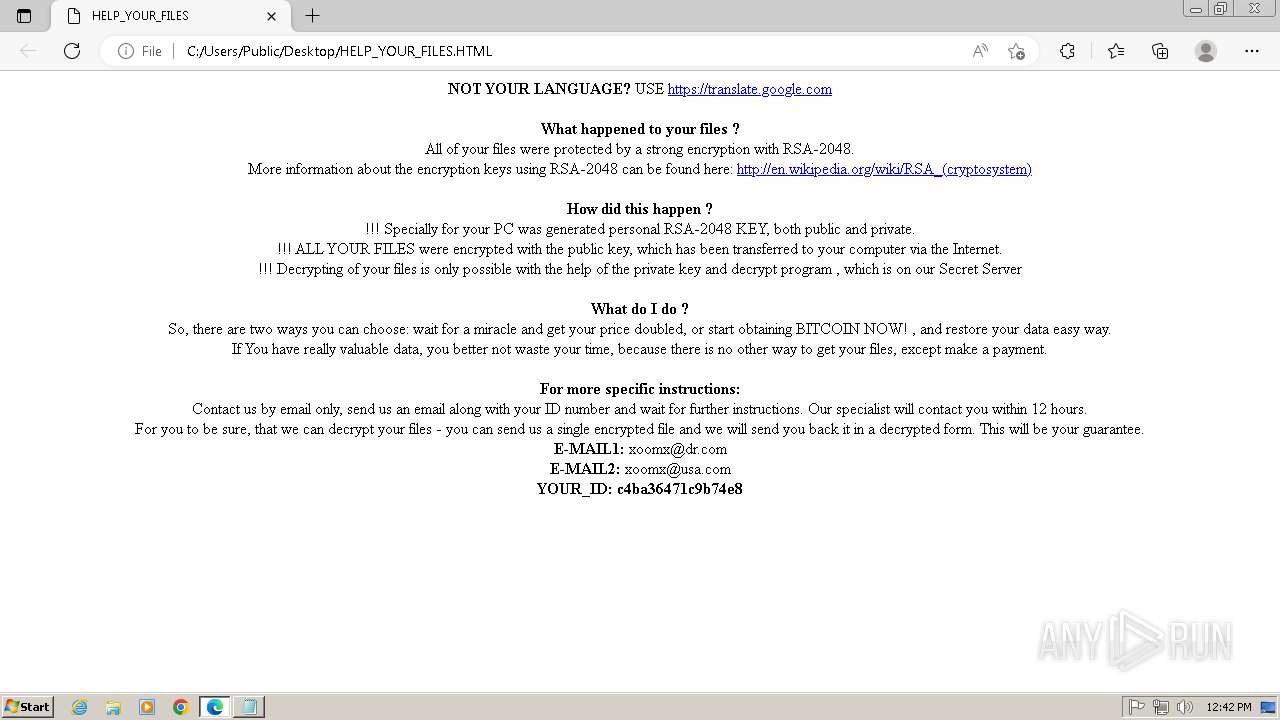
| 3096 | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | C:\ProgramData\HELP_YOUR_FILES.HTML | html | |
MD5:1CC8DE9A3F1C9DB03DED1CC265A66AEA | SHA256:280E2A5A17CAD970899357E6A2576EF1530950E862F6F606A2B2A179439E8D09 | |||
| 3096 | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | C:\PerfLogs\HELP_YOUR_FILES.TXT | binary | |
MD5:6405A6E4353774FFA79E5093311C20D2 | SHA256:F3A2CEE372CA3FD2CABB512528C4EB6D9A174594FACD6DDFBFC5004C6A8A6DB1 | |||
| 3096 | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | C:\$Recycle.Bin\HELP_YOUR_FILES.TXT | binary | |
MD5:6405A6E4353774FFA79E5093311C20D2 | SHA256:F3A2CEE372CA3FD2CABB512528C4EB6D9A174594FACD6DDFBFC5004C6A8A6DB1 | |||
| 3096 | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | C:\MSOCache\HELP_YOUR_FILES.TXT | binary | |
MD5:6405A6E4353774FFA79E5093311C20D2 | SHA256:F3A2CEE372CA3FD2CABB512528C4EB6D9A174594FACD6DDFBFC5004C6A8A6DB1 | |||
| 3096 | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | C:\$Recycle.Bin\HELP_YOUR_FILES.HTML | html | |
MD5:1CC8DE9A3F1C9DB03DED1CC265A66AEA | SHA256:280E2A5A17CAD970899357E6A2576EF1530950E862F6F606A2B2A179439E8D09 | |||
| 3096 | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | C:\Users\HELP_YOUR_FILES.HTML | html | |
MD5:1CC8DE9A3F1C9DB03DED1CC265A66AEA | SHA256:280E2A5A17CAD970899357E6A2576EF1530950E862F6F606A2B2A179439E8D09 | |||
| 3096 | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | C:\MSOCache\HELP_YOUR_FILES.HTML | html | |
MD5:1CC8DE9A3F1C9DB03DED1CC265A66AEA | SHA256:280E2A5A17CAD970899357E6A2576EF1530950E862F6F606A2B2A179439E8D09 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
18
DNS requests
10
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3096 | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | 13.107.246.59:80 | microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3096 | Trojan-Ransom.Win32.Blocker.jfgj-004cdc6996225f244aef124edc72f90434a872b3d4fa56d5ebc2655473733aef.exe | 46.8.45.174:80 | — | KTO OOO | RU | unknown |
3804 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3652 | msedge.exe | 13.107.43.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3652 | msedge.exe | 150.171.29.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3652 | msedge.exe | 92.123.104.28:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
Process | Message |
|---|---|
msedge.exe | [0429/124244.097:ERROR:exception_handler_server.cc(527)] ConnectNamedPipe: The pipe is being closed. (0xE8)
|