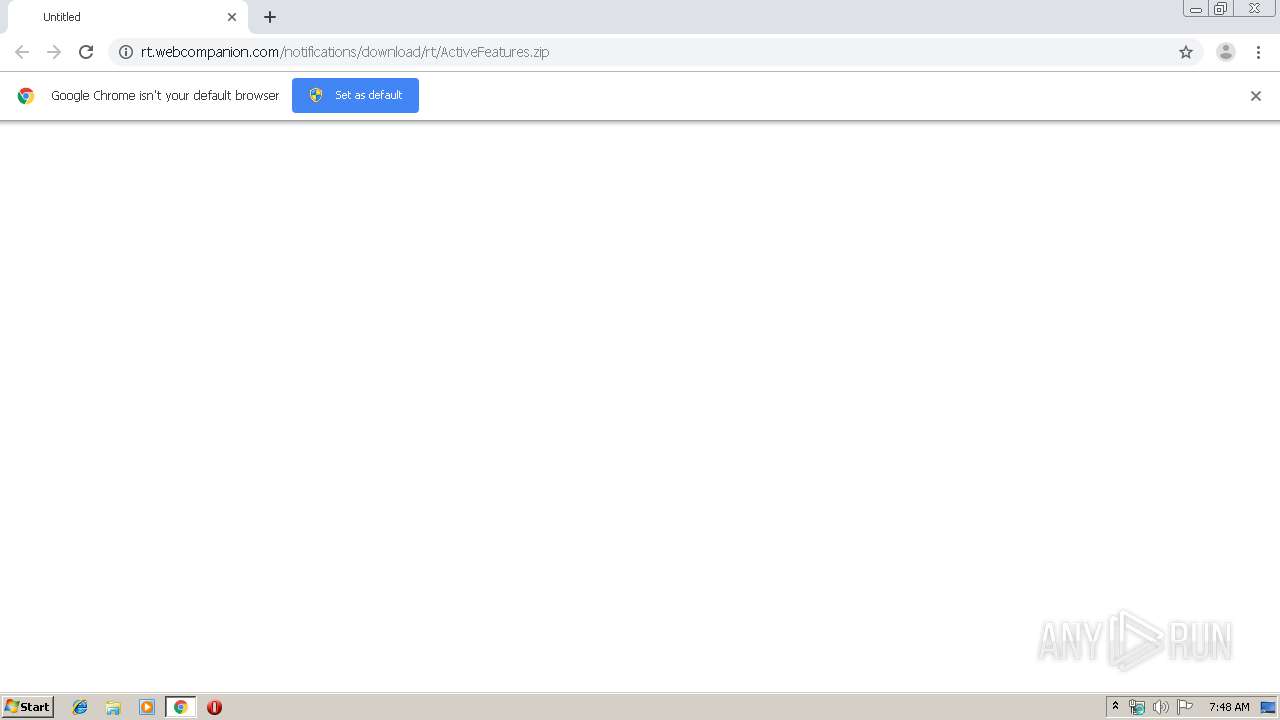
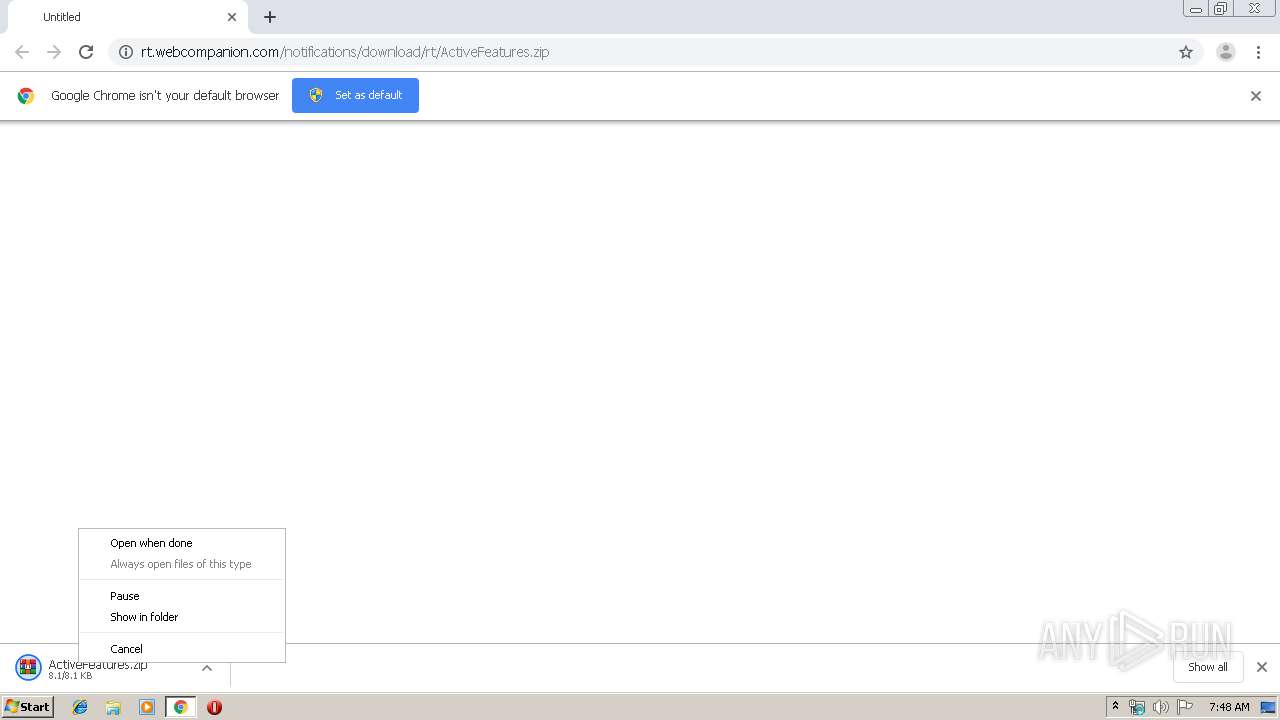
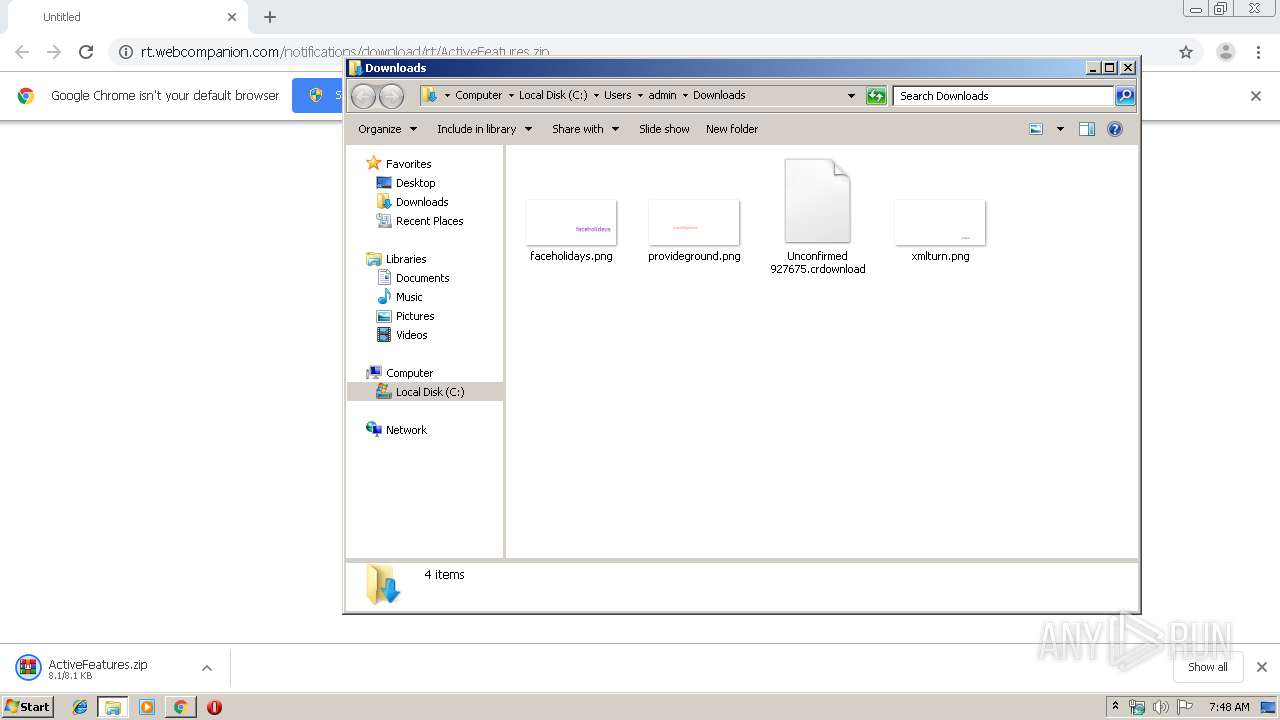
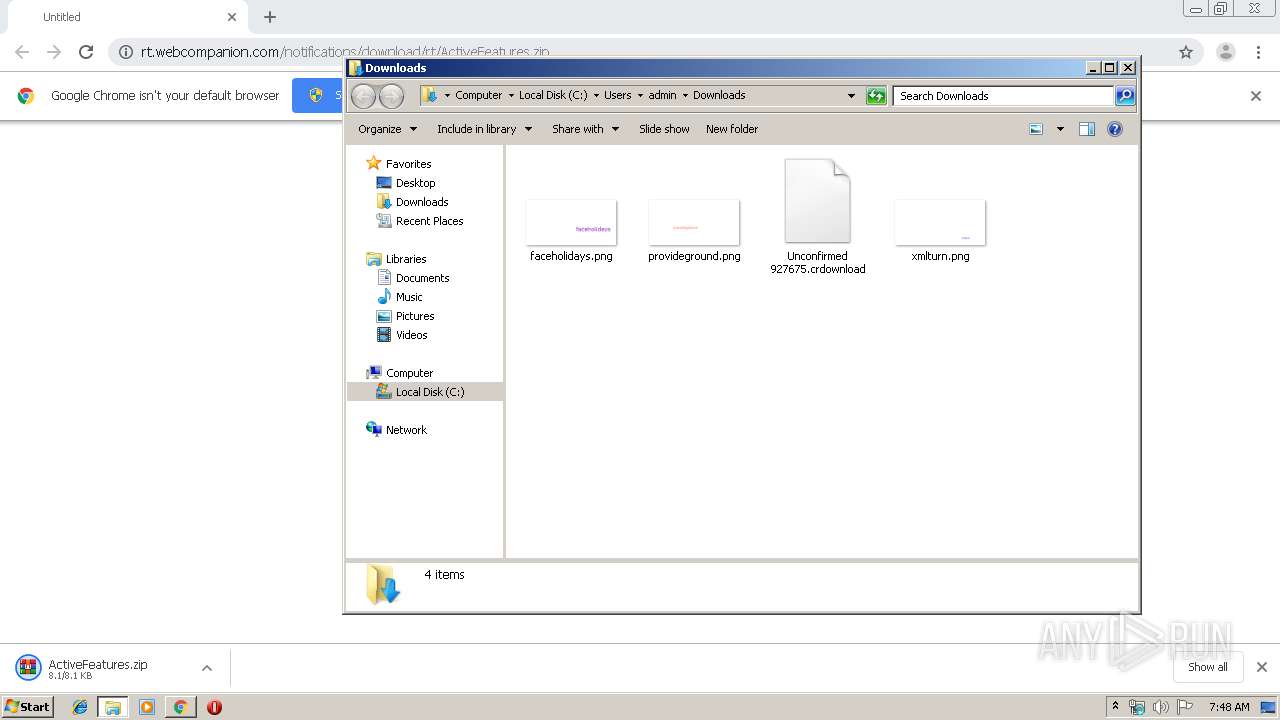
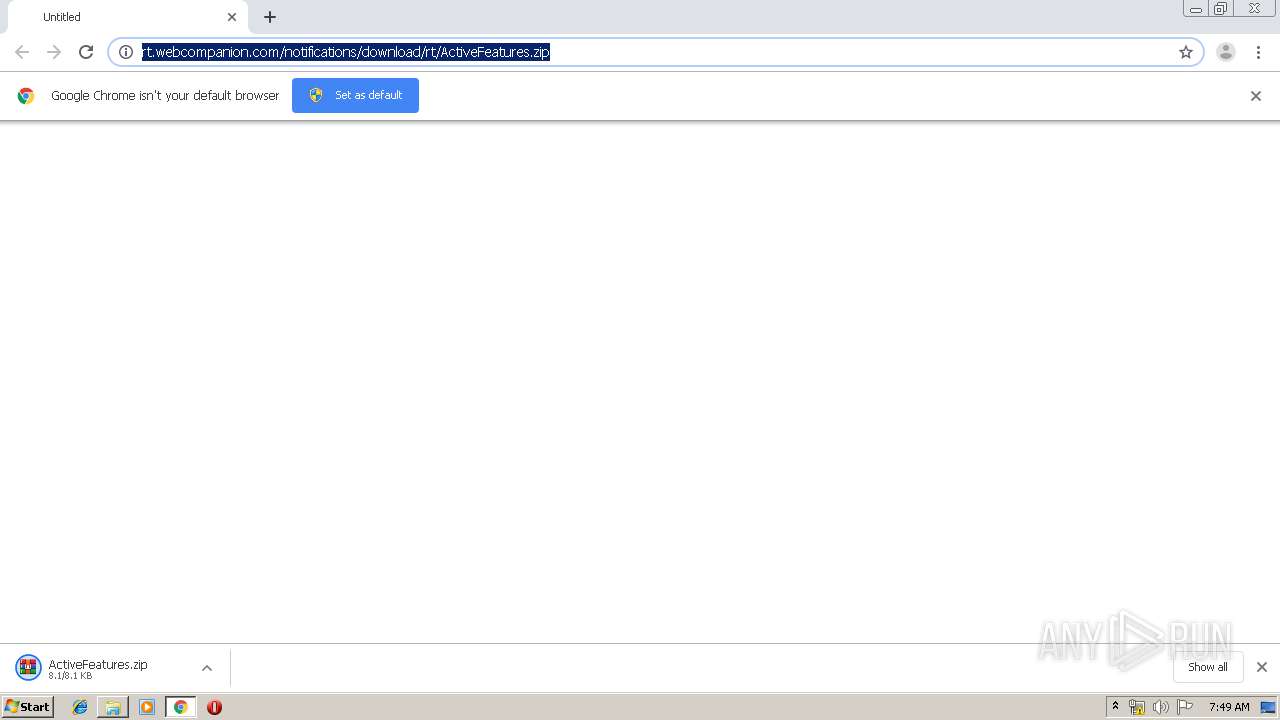
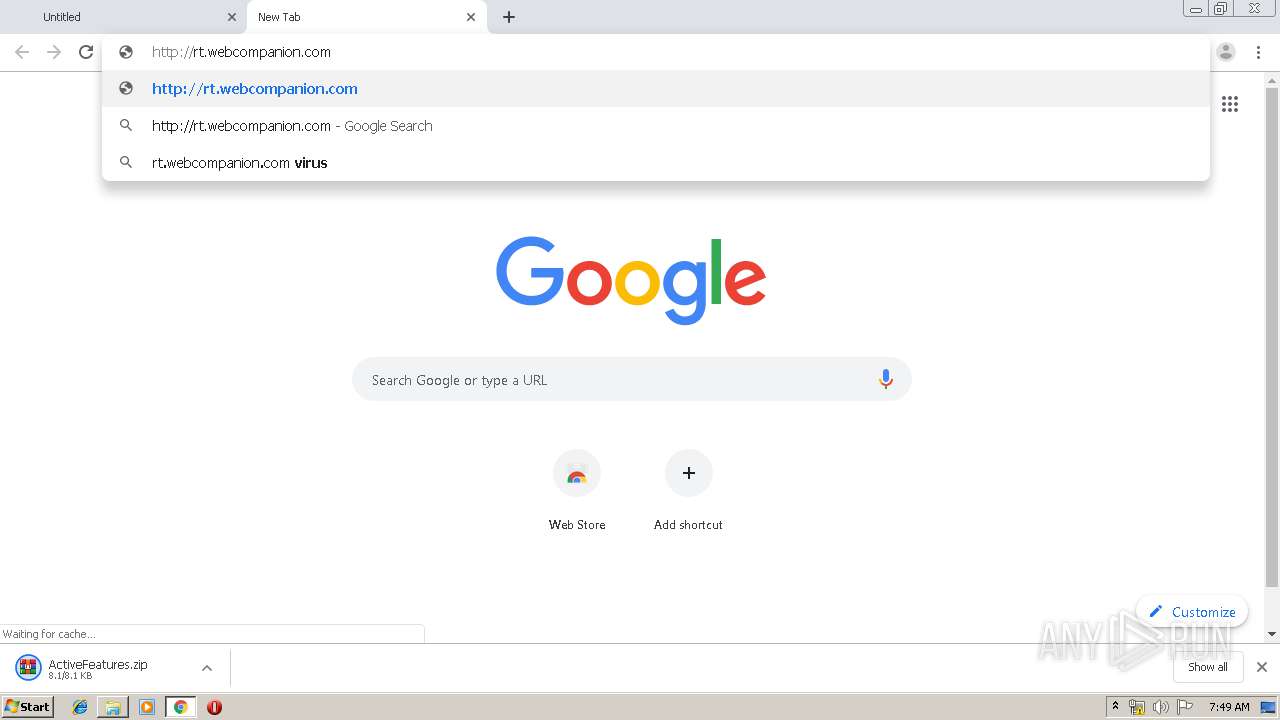
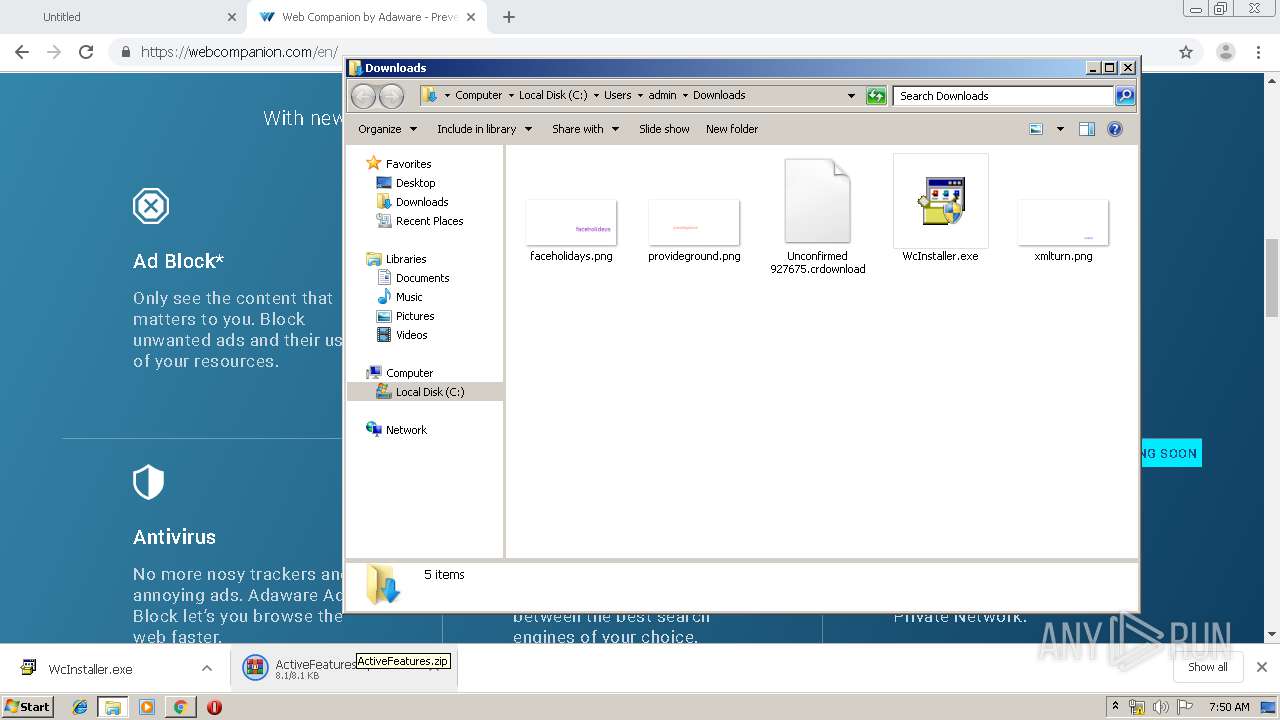
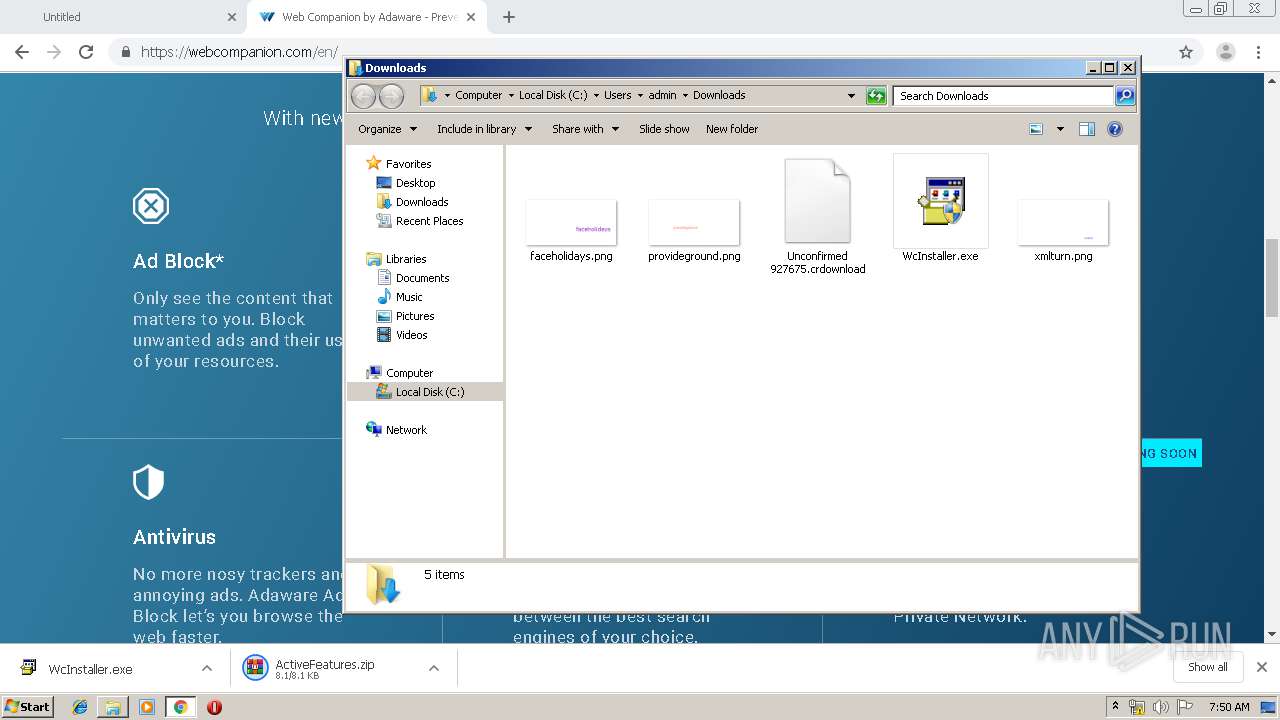
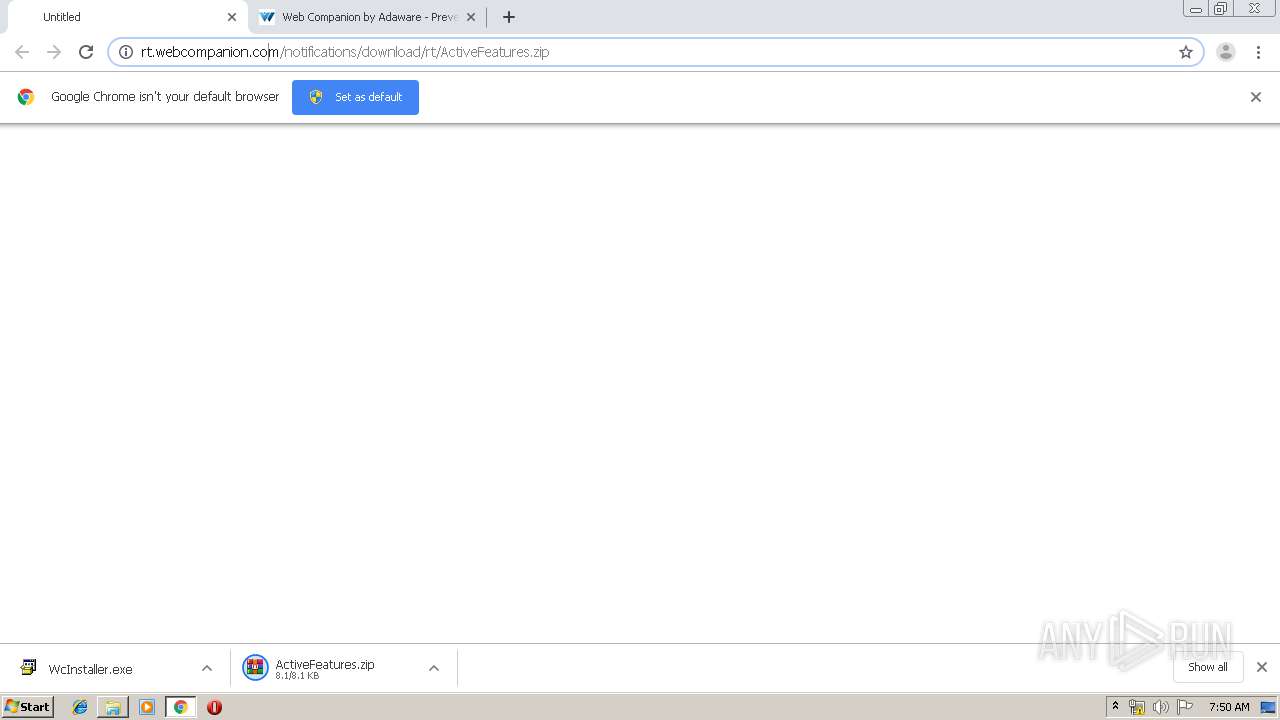
| URL: | http://rt.webcompanion.com/notifications/download/rt/ActiveFeatures.zip |
| Full analysis: | https://app.any.run/tasks/d33e230a-d1f4-42b7-a12f-86ee8c26feec |
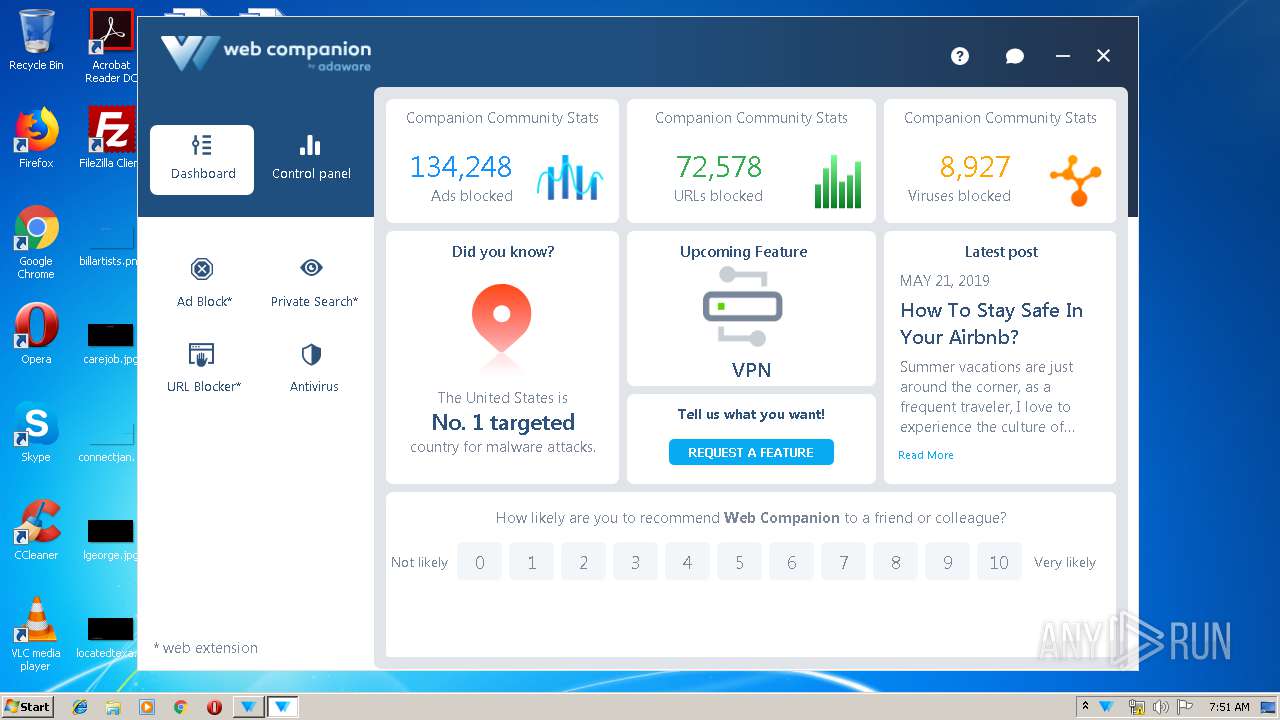
| Verdict: | Malicious activity |
| Analysis date: | November 27, 2019, 07:48:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BEA848BD4155ECFC0248E2192B50A60F |
| SHA1: | 97BDA121D498255561B2D51109A2D460D5471512 |
| SHA256: | 6F1429749D5AE19AFD3498E27E0A44235710208ED3813C25243D845E8EA3811A |
| SSDEEP: | 3:N1KMxDKQXGWaJLm1k2Xz4:CMx+mk6s |
MALICIOUS
Application was dropped or rewritten from another process
- WcInstaller.exe (PID: 324)
- WcInstaller.exe (PID: 2688)
- WebCompanionInstaller.exe (PID: 2764)
- WebCompanion.exe (PID: 3644)
- Lavasoft.WCAssistant.WinService.exe (PID: 2560)
- WebCompanion.exe (PID: 1880)
Loads dropped or rewritten executable
- WebCompanionInstaller.exe (PID: 2764)
- WebCompanion.exe (PID: 3644)
- Lavasoft.WCAssistant.WinService.exe (PID: 2560)
- WebCompanion.exe (PID: 1880)
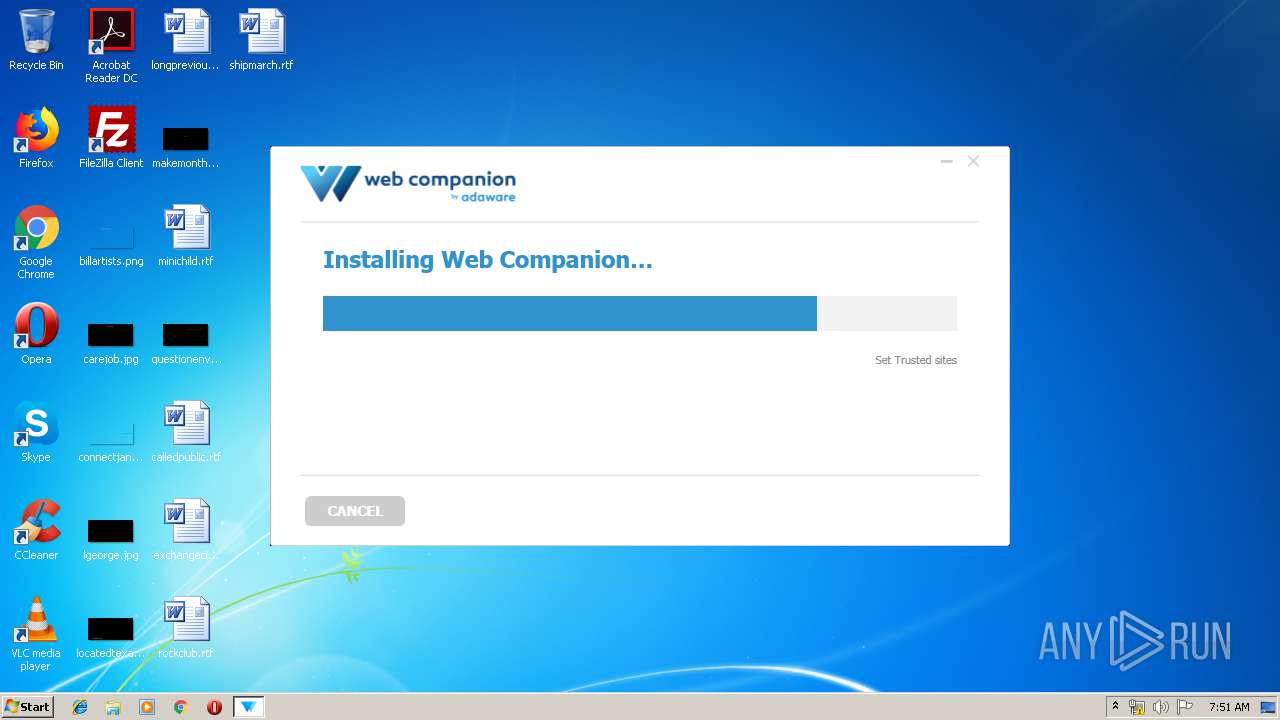
Changes internet zones settings
- WebCompanionInstaller.exe (PID: 2764)
Changes the autorun value in the registry
- WebCompanion.exe (PID: 3644)
Starts Visual C# compiler
- WebCompanion.exe (PID: 3644)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 184)
- WcInstaller.exe (PID: 2688)
- WebCompanionInstaller.exe (PID: 2764)
- chrome.exe (PID: 2600)
Executed as Windows Service
- PresentationFontCache.exe (PID: 2264)
- Lavasoft.WCAssistant.WinService.exe (PID: 2560)
Starts SC.EXE for service management
- WebCompanionInstaller.exe (PID: 2764)
Creates a software uninstall entry
- WebCompanionInstaller.exe (PID: 2764)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2600)
Starts CMD.EXE for commands execution
- WebCompanionInstaller.exe (PID: 2764)
- Lavasoft.WCAssistant.WinService.exe (PID: 2560)
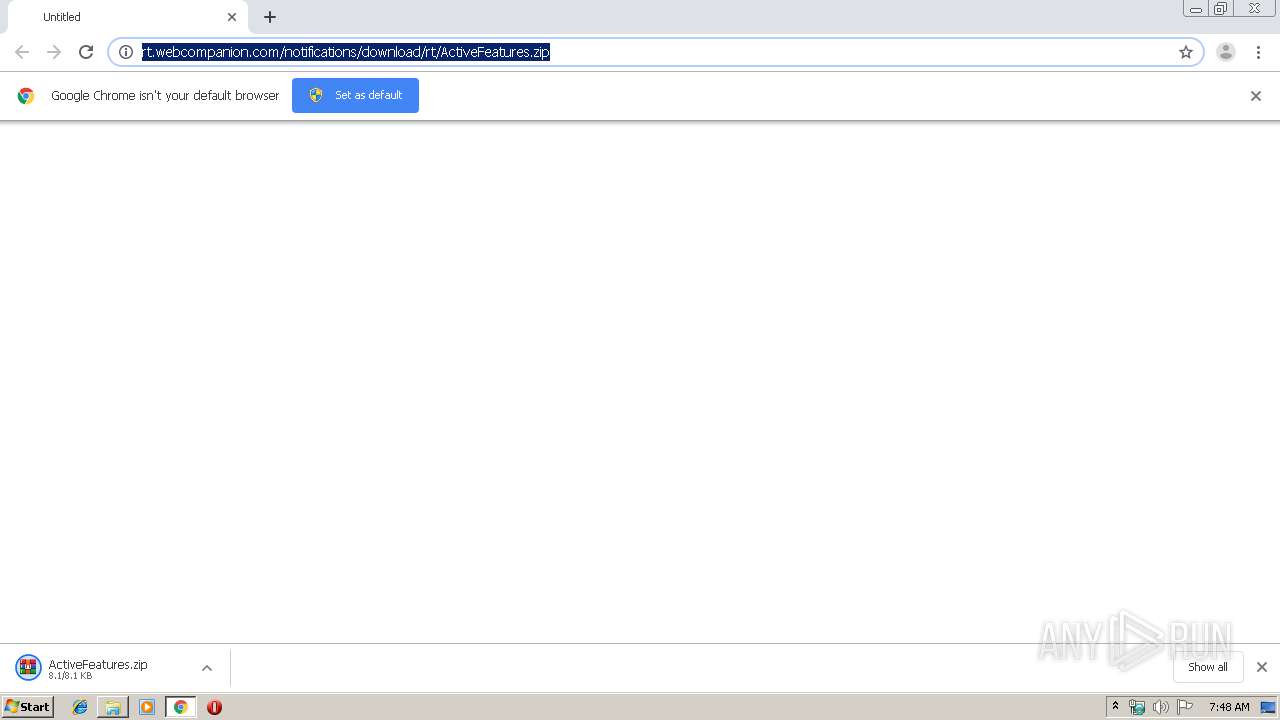
Creates files in the user directory
- WebCompanionInstaller.exe (PID: 2764)
- WebCompanion.exe (PID: 3644)
Creates files in the program directory
- WebCompanionInstaller.exe (PID: 2764)
- WebCompanion.exe (PID: 3644)
- Lavasoft.WCAssistant.WinService.exe (PID: 2560)
Uses NETSH.EXE for network configuration
- cmd.exe (PID: 2916)
- cmd.exe (PID: 4012)
Creates files in the Windows directory
- Lavasoft.WCAssistant.WinService.exe (PID: 2560)
- WebCompanion.exe (PID: 3644)
Removes files from Windows directory
- Lavasoft.WCAssistant.WinService.exe (PID: 2560)
INFO
Application launched itself
- chrome.exe (PID: 2600)
Reads the hosts file
- chrome.exe (PID: 2600)
- chrome.exe (PID: 184)
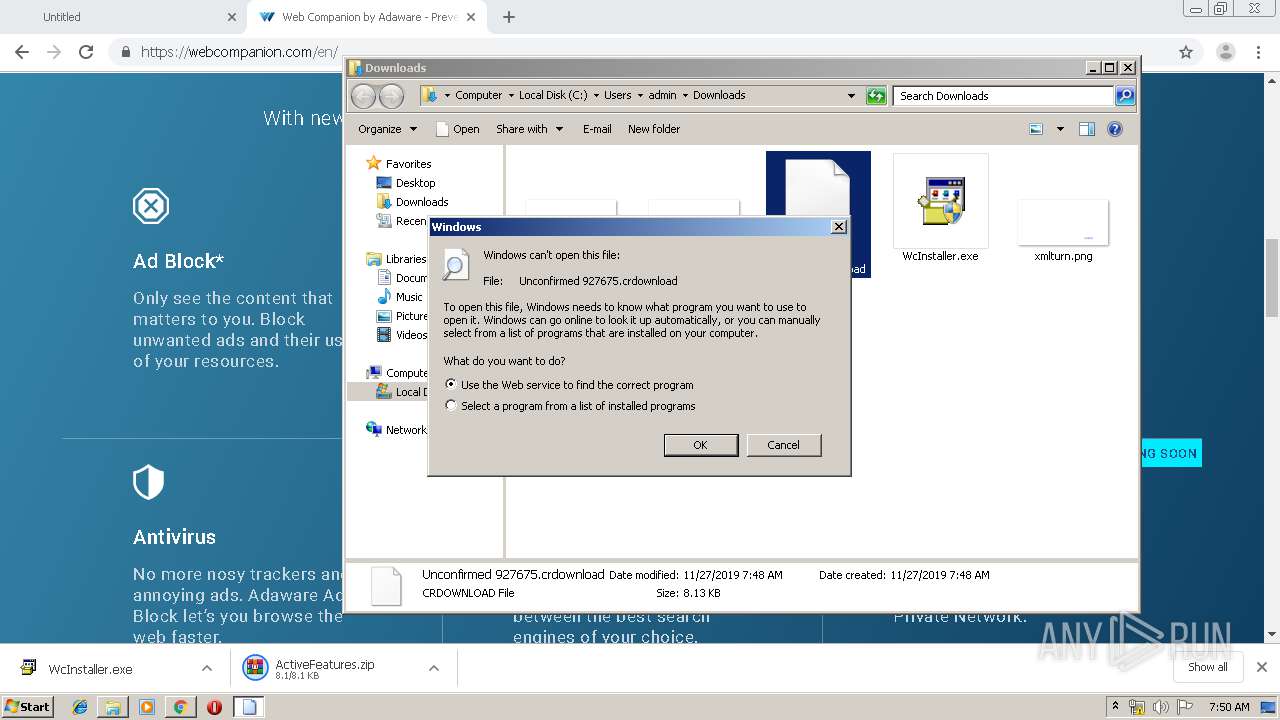
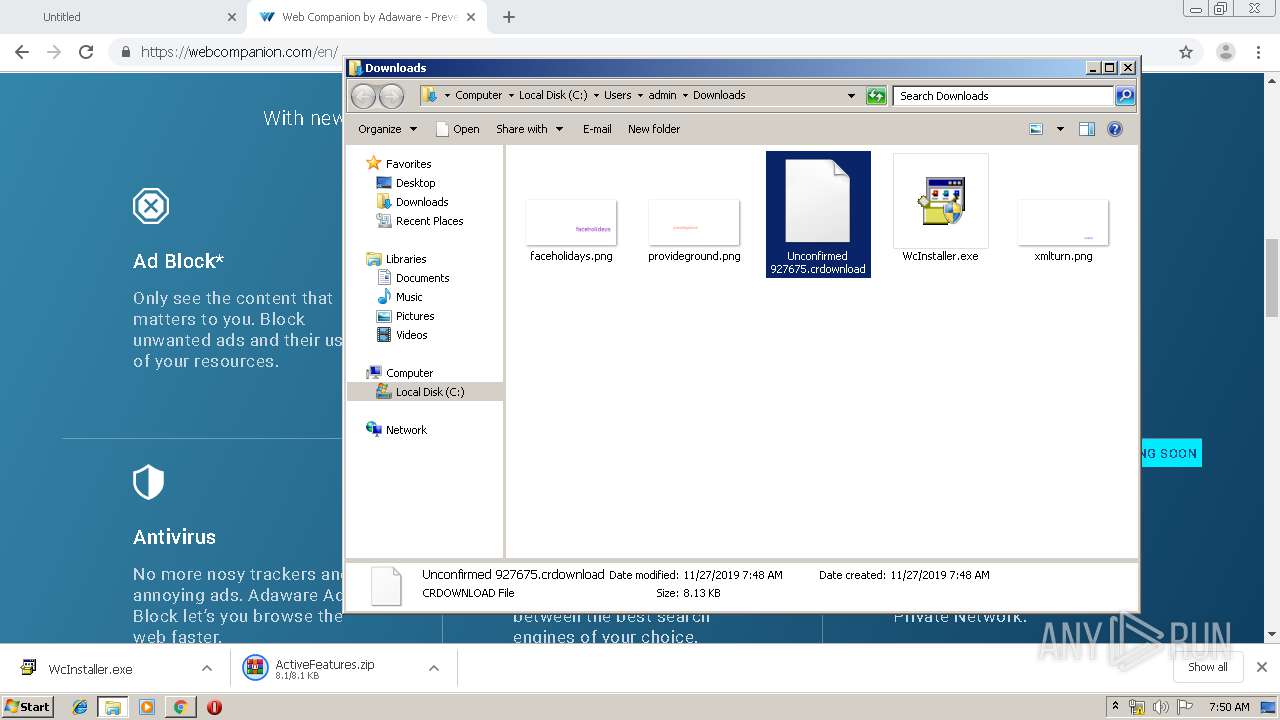
Manual execution by user
- rundll32.exe (PID: 2108)
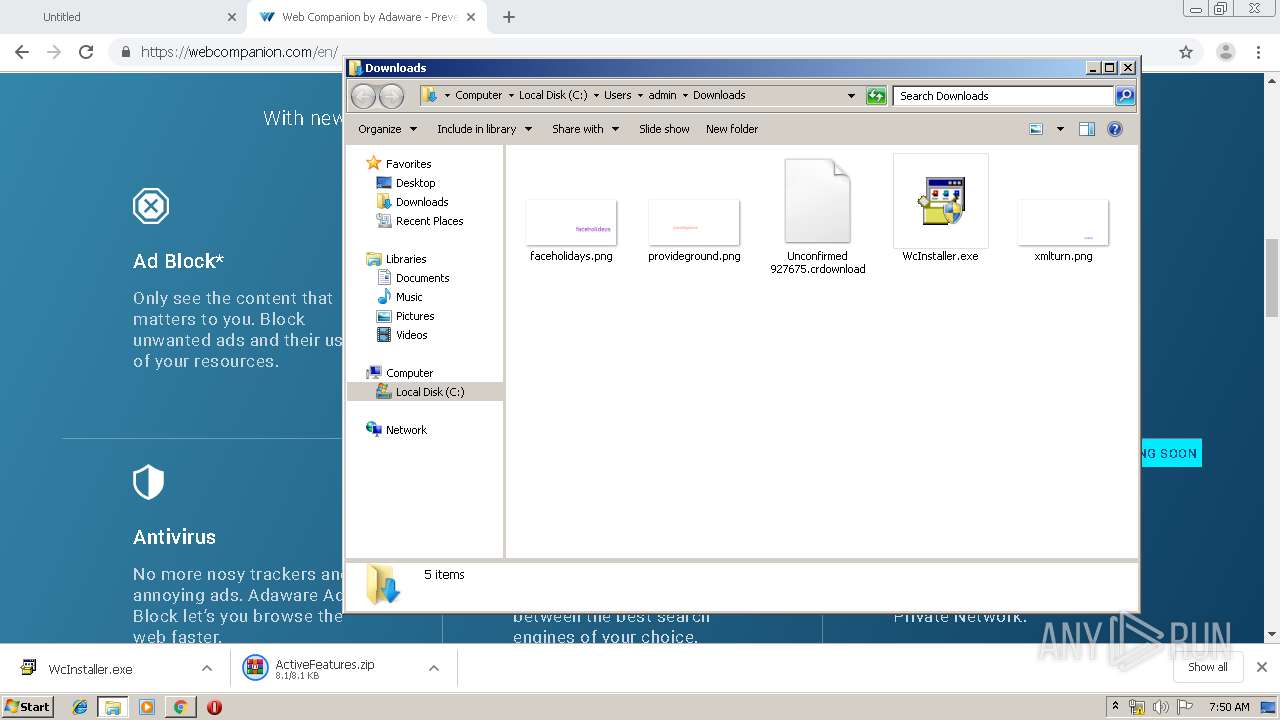
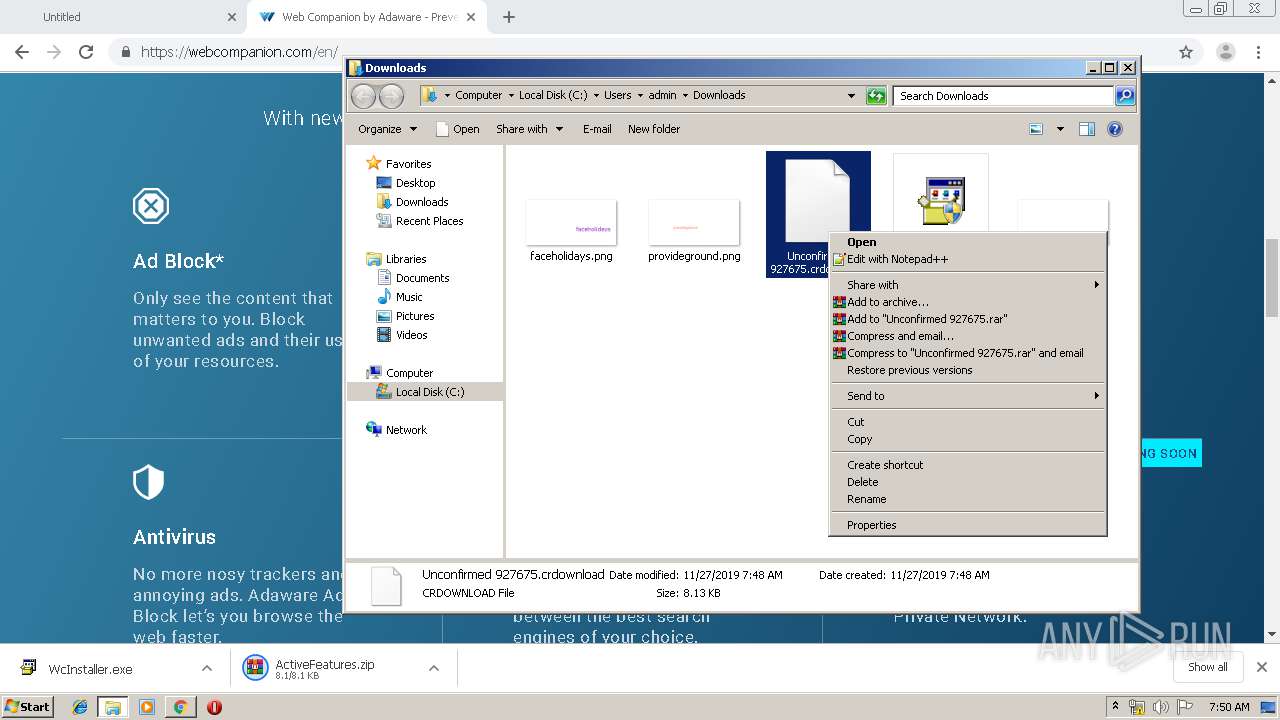
- WcInstaller.exe (PID: 324)
- WcInstaller.exe (PID: 2688)
Reads Internet Cache Settings
- chrome.exe (PID: 2600)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
101
Monitored processes
51
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=6486894602075807188 --mojo-platform-channel-handle=1556 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12749389527705012712 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2960 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 324 | "C:\Users\admin\Downloads\WcInstaller.exe" | C:\Users\admin\Downloads\WcInstaller.exe | — | explorer.exe | |||||||||||
User: admin Company: Adaware Software Canada Integrity Level: MEDIUM Description: Adaware WebCompanion Exit code: 3221226540 Version: 5.1.1035.1047 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3793715577585276990 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2220 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 952 | "sc.exe" failure WCAssistantService reset= 30 actions= restart/60000 | C:\Windows\system32\sc.exe | — | WebCompanionInstaller.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17282032303467235603 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3773717676821586092 --renderer-client-id=11 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=572 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1316 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9416880646155365422 --mojo-platform-channel-handle=1380 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
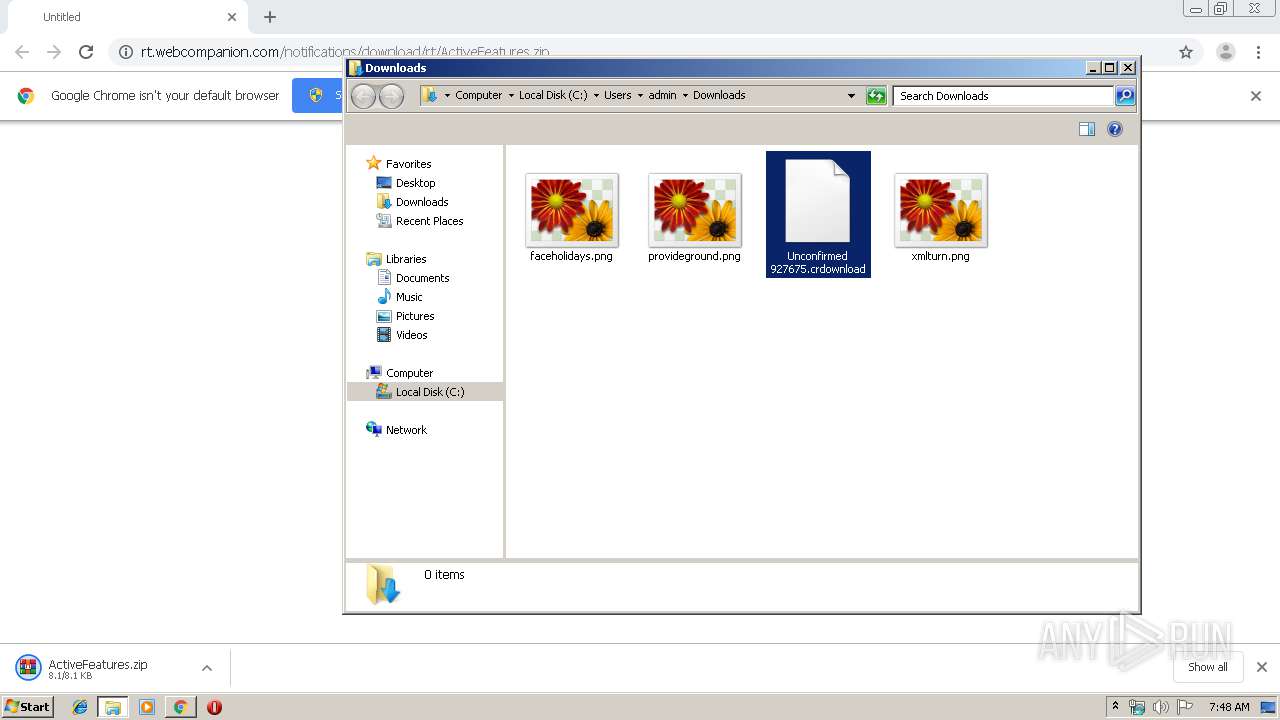
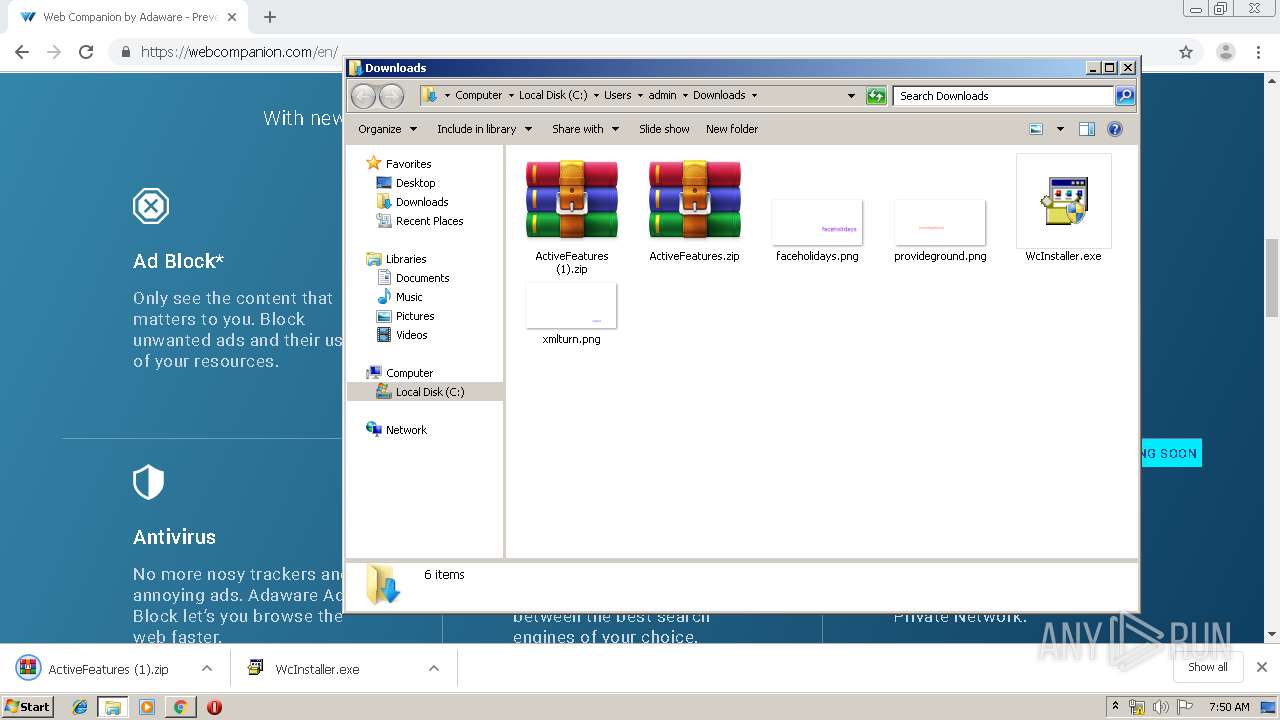
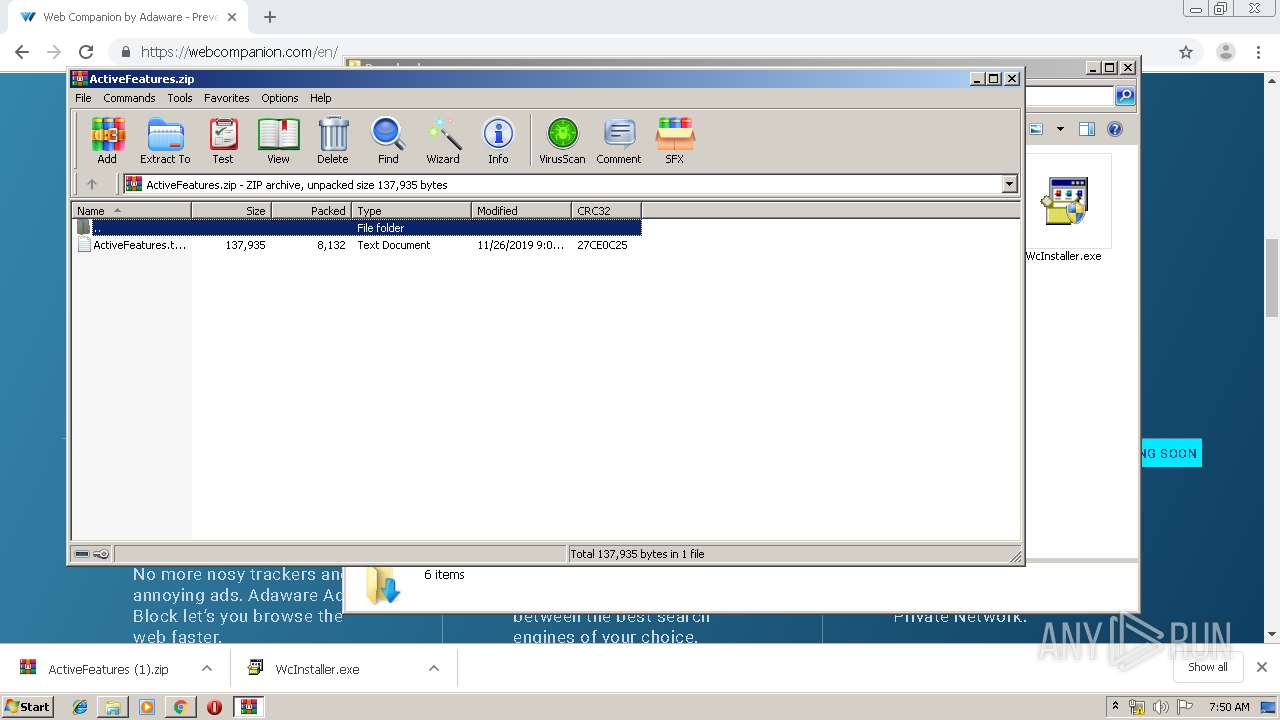
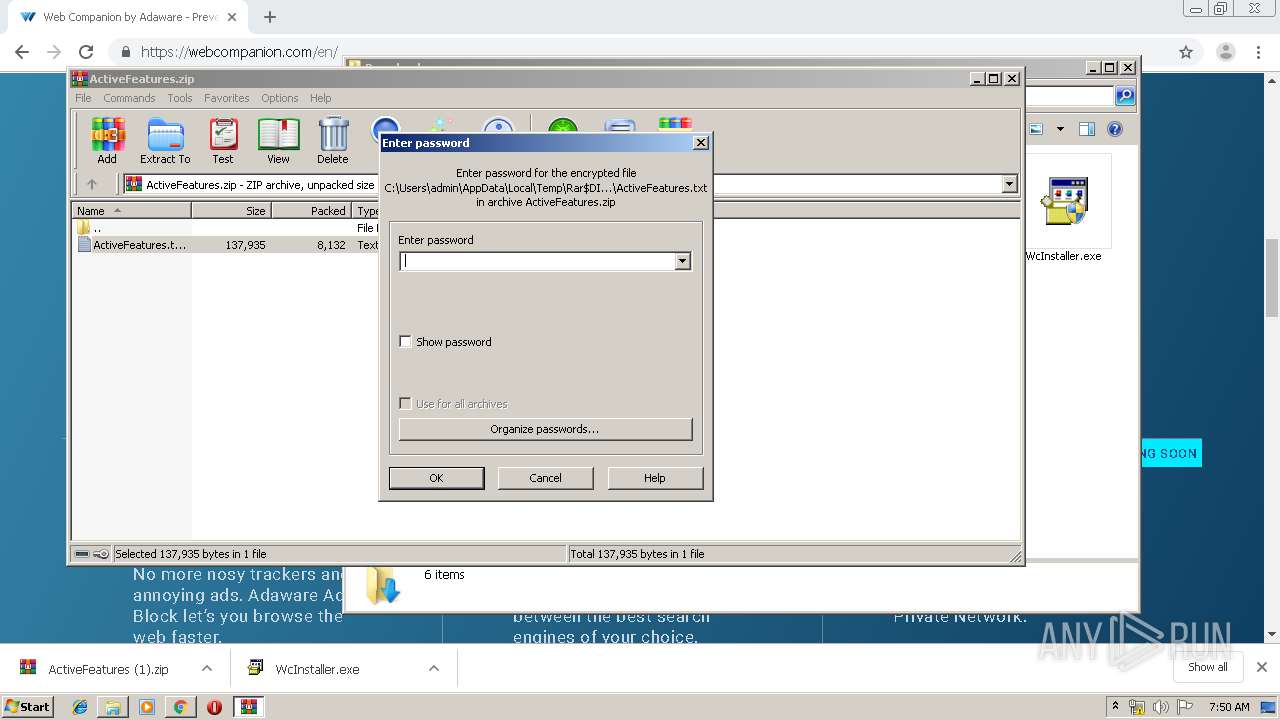
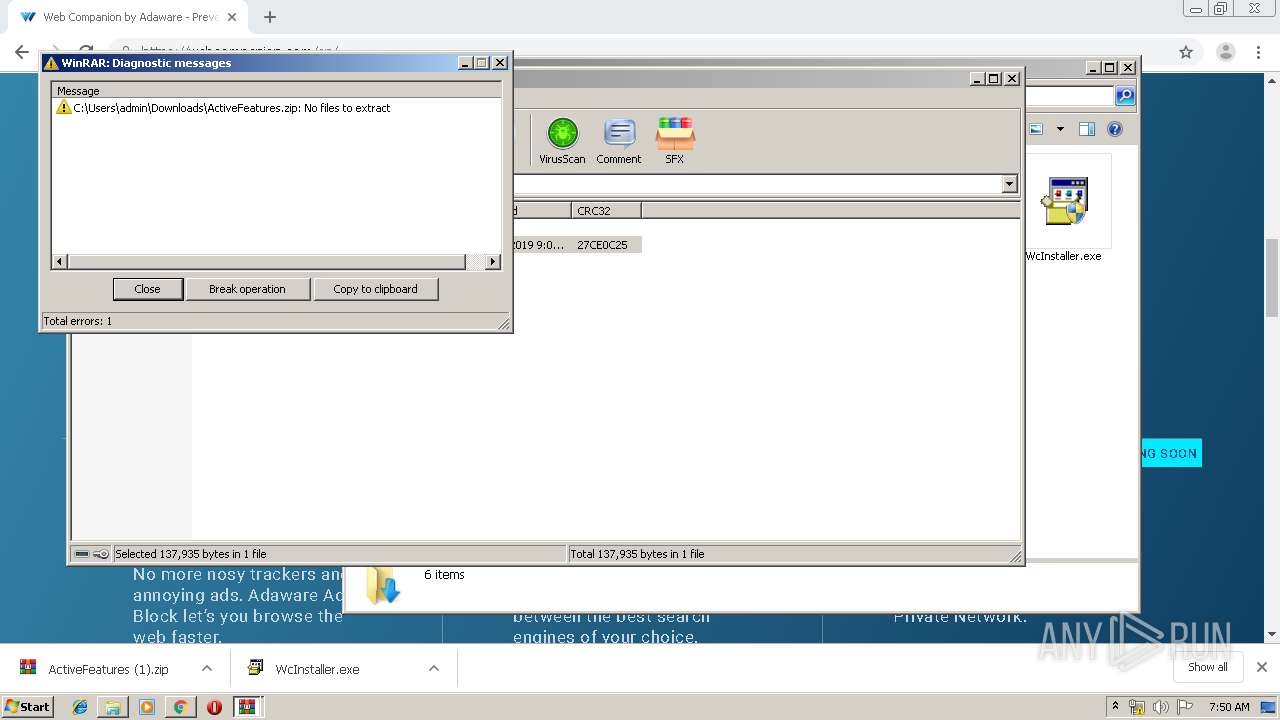
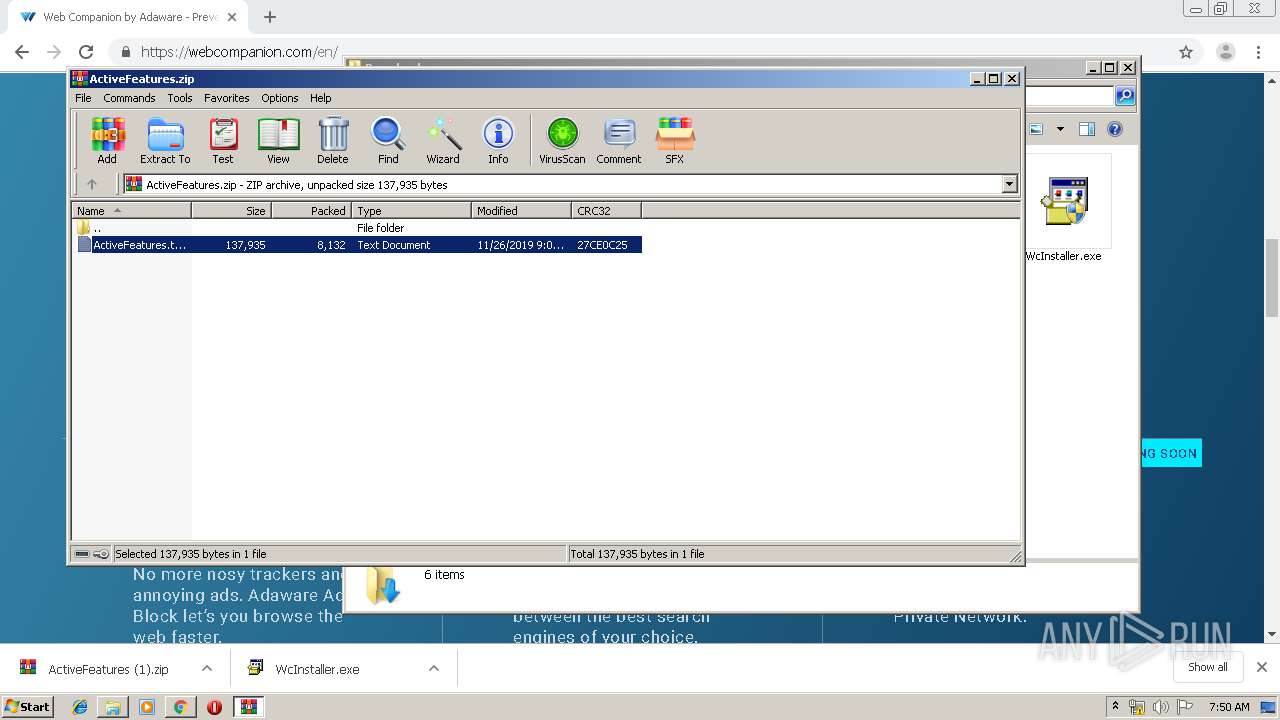
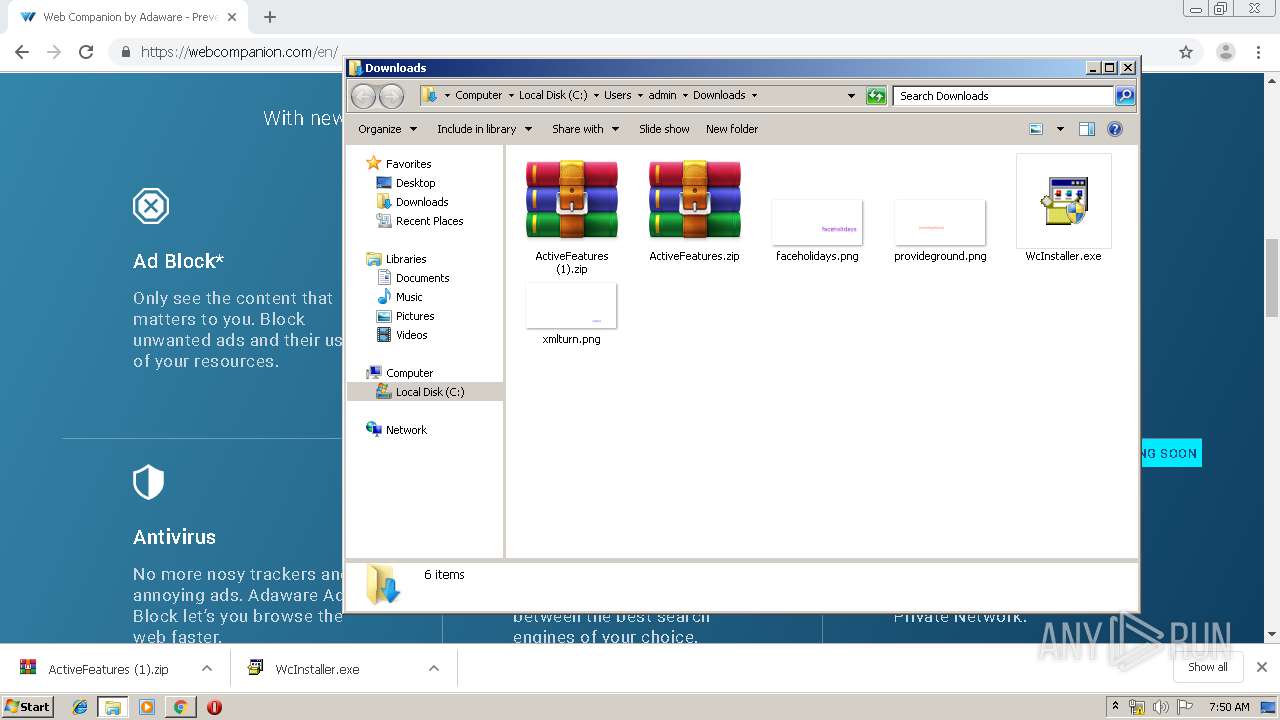
| 1544 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\ActiveFeatures.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | chrome.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,18050591135156919140,2177277621110513208,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9445929496667477755 --mojo-platform-channel-handle=3152 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 185
Read events
1 853
Write events
327
Delete events
5
Modification events
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2172) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2600-13219314500493125 |
Value: 259 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2600) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
81
Suspicious files
80
Text files
847
Unknown types
48
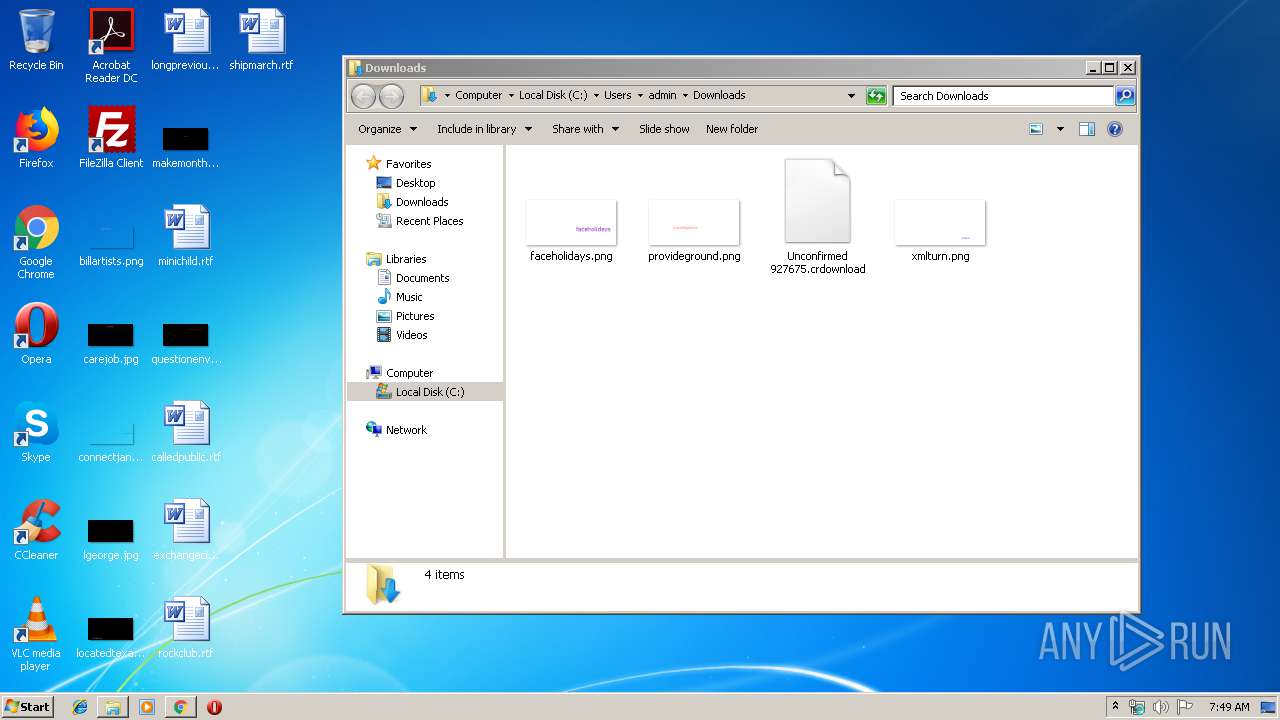
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0b4af30d-eca9-41a6-9bda-73a6ca218ede.tmp | — | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a969.TMP | text | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a90c.TMP | text | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\000001.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2600 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
39
TCP/UDP connections
55
DNS requests
40
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
184 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 510 b | whitelisted |
184 | chrome.exe | GET | 302 | 172.217.18.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
184 | chrome.exe | GET | 200 | 104.17.177.102:80 | http://rt.webcompanion.com/notifications/download/rt/ActiveFeatures.zip | US | compressed | 8.14 Kb | malicious |
2764 | WebCompanionInstaller.exe | POST | 200 | 64.18.87.81:80 | http://wc-update-service.lavasoft.com/update.asmx | CA | xml | 1.43 Kb | whitelisted |
2764 | WebCompanionInstaller.exe | GET | 200 | 104.18.87.101:80 | http://wcdownloadercdn.lavasoft.com/5.1.1035.1047/WebCompanion-5.1.1035.1047-prod.zip | US | compressed | 14.6 Mb | whitelisted |
2764 | WebCompanionInstaller.exe | POST | 200 | 64.18.87.81:80 | http://wc-tracking.lavasoft.com/Install.asmx | CA | xml | 294 b | whitelisted |
184 | chrome.exe | GET | 200 | 185.38.0.205:80 | http://r2---sn-4ox-uh2e.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mip=196.244.192.14&mm=28&mn=sn-4ox-uh2e&ms=nvh&mt=1574840966&mv=m&mvi=1&pl=24&shardbypass=yes | FI | crx | 293 Kb | whitelisted |
2764 | WebCompanionInstaller.exe | POST | 200 | 64.18.87.81:80 | http://wc-tracking.lavasoft.com/Install.asmx | CA | xml | 294 b | whitelisted |
184 | chrome.exe | GET | 302 | 104.17.177.102:80 | http://rt.webcompanion.com/ | US | text | 3 b | malicious |
2764 | WebCompanionInstaller.exe | POST | 200 | 64.18.87.81:80 | http://wc-tracking.lavasoft.com/Install.asmx | CA | xml | 294 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
184 | chrome.exe | 104.17.177.102:80 | rt.webcompanion.com | Cloudflare Inc | US | shared |
184 | chrome.exe | 216.58.207.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.23.109:443 | accounts.google.com | Google Inc. | US | suspicious |
184 | chrome.exe | 104.17.178.102:80 | rt.webcompanion.com | Cloudflare Inc | US | shared |
184 | chrome.exe | 216.58.208.35:443 | www.google.se | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.22.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.16.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.18.3:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
184 | chrome.exe | 172.217.18.110:443 | apis.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rt.webcompanion.com |
| malicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.google.se |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
Process | Message |
|---|---|
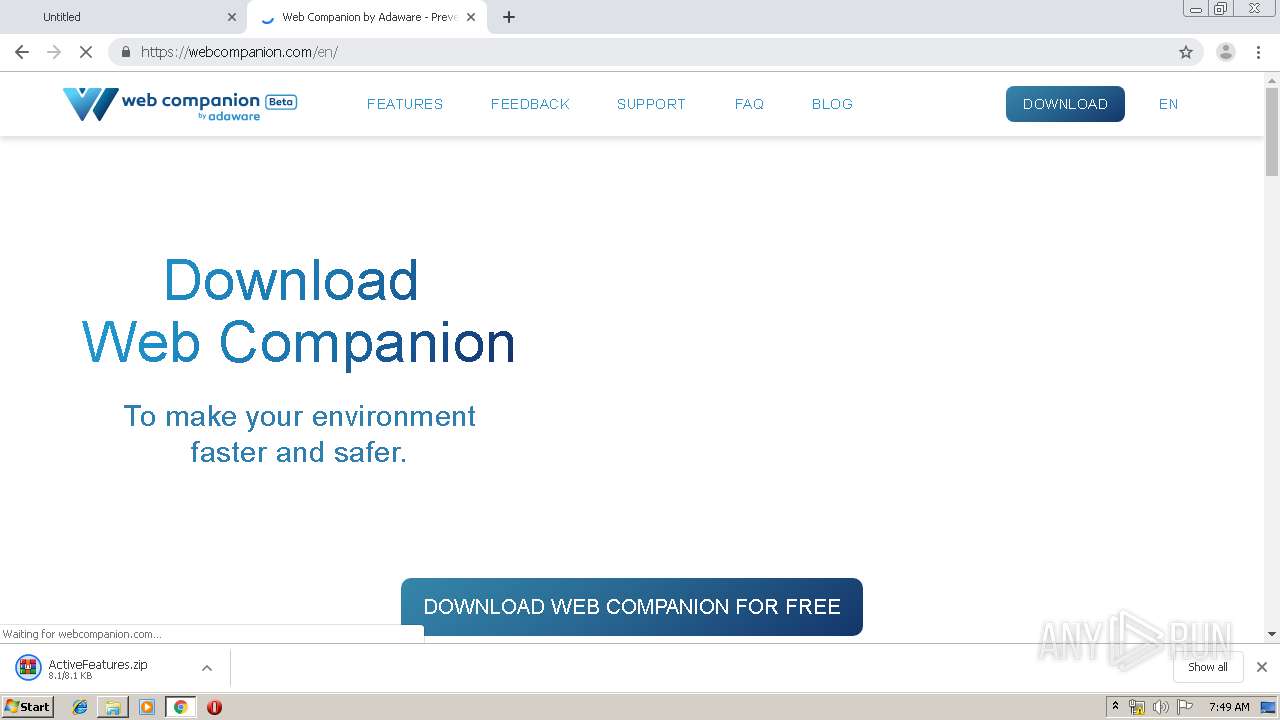
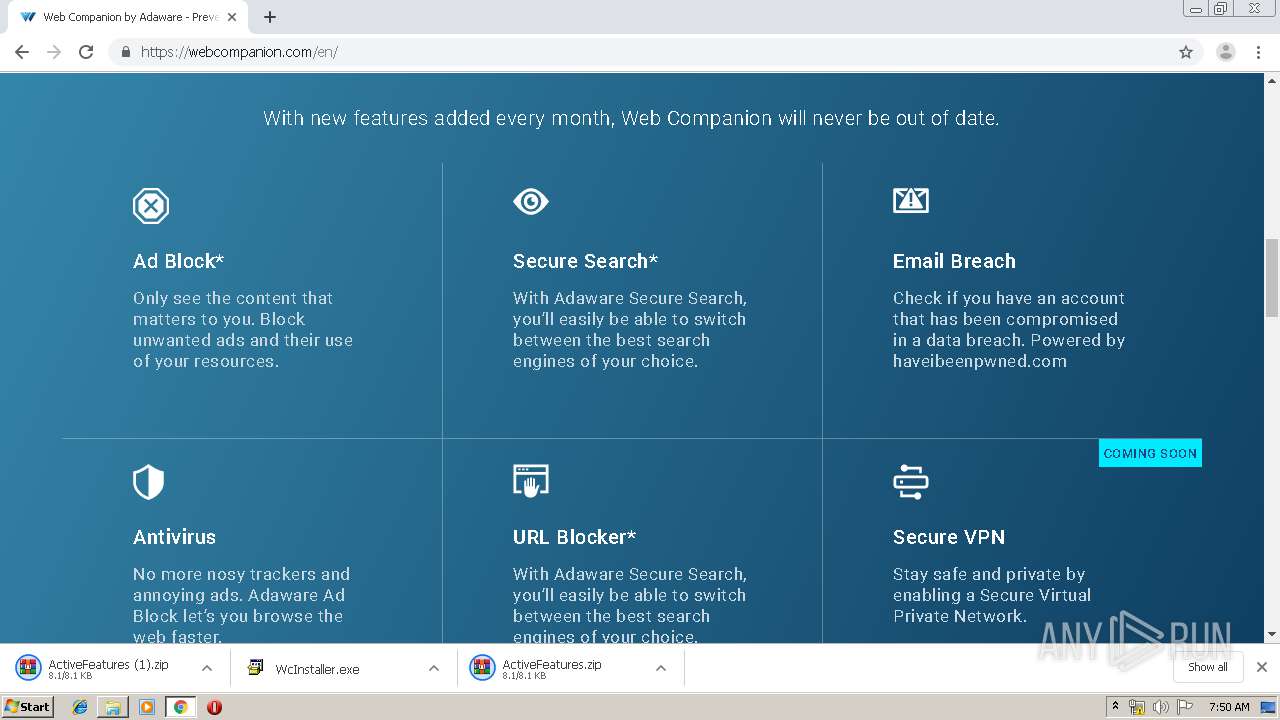
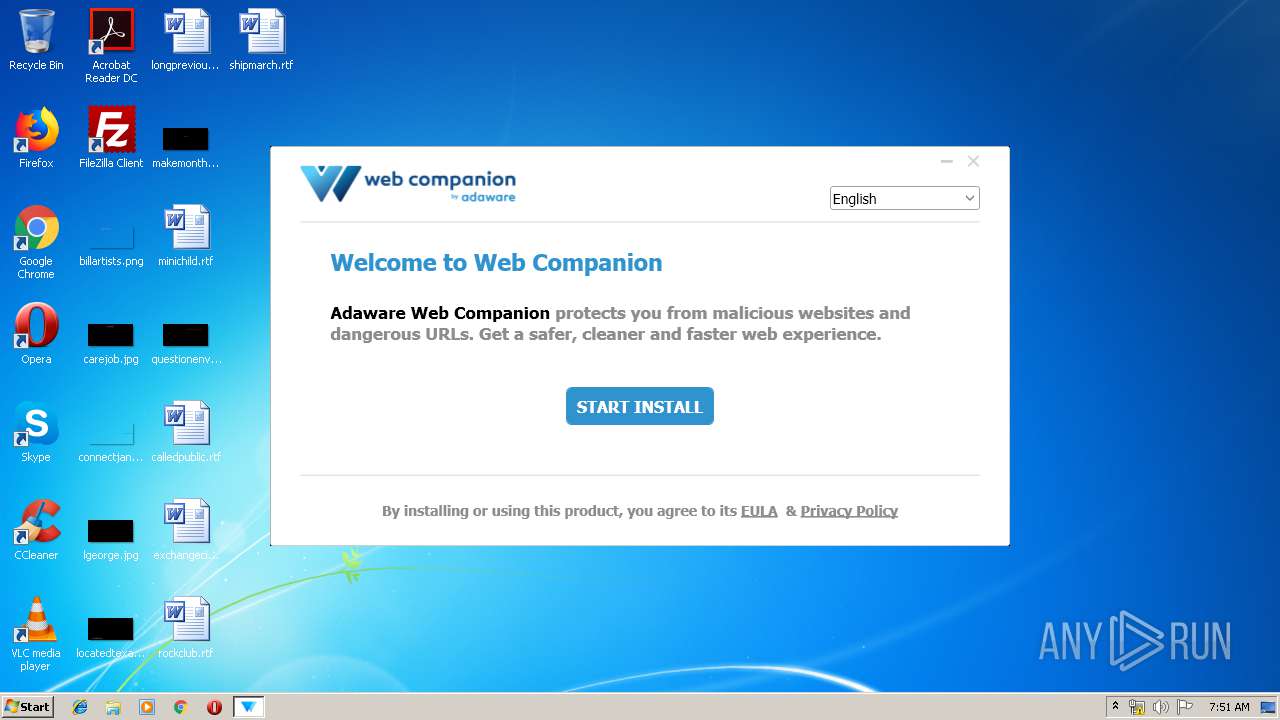
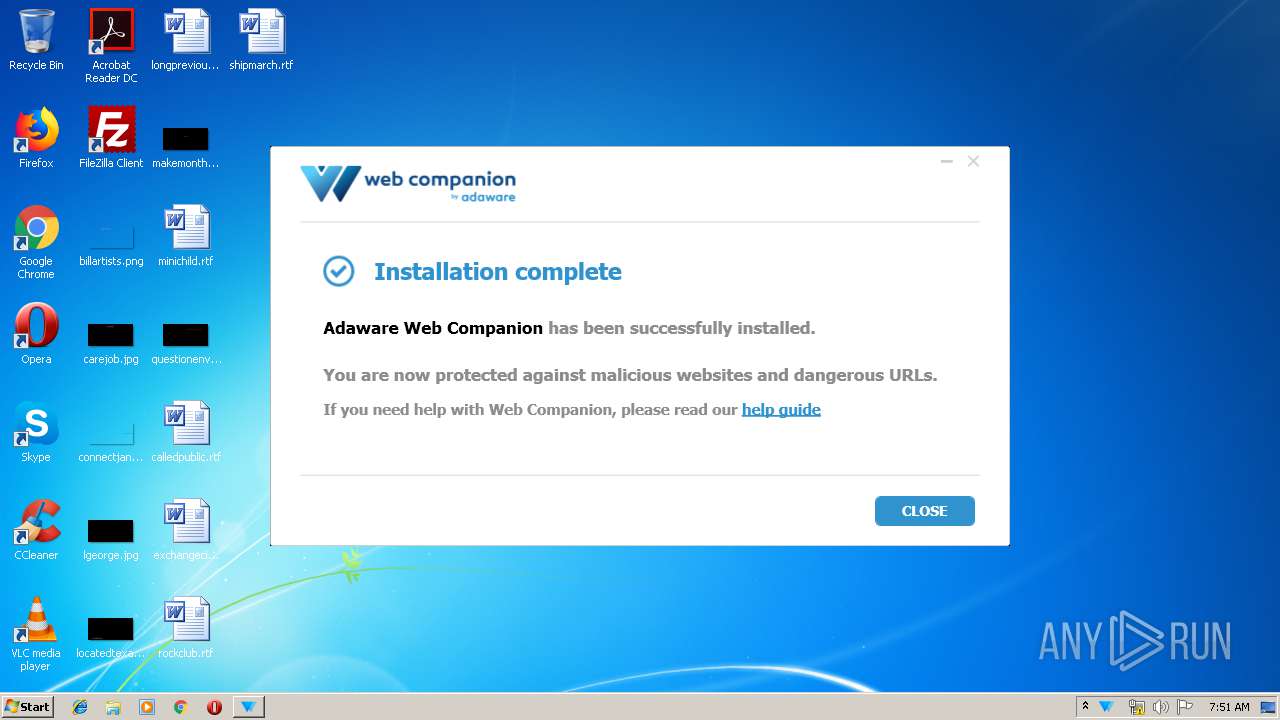
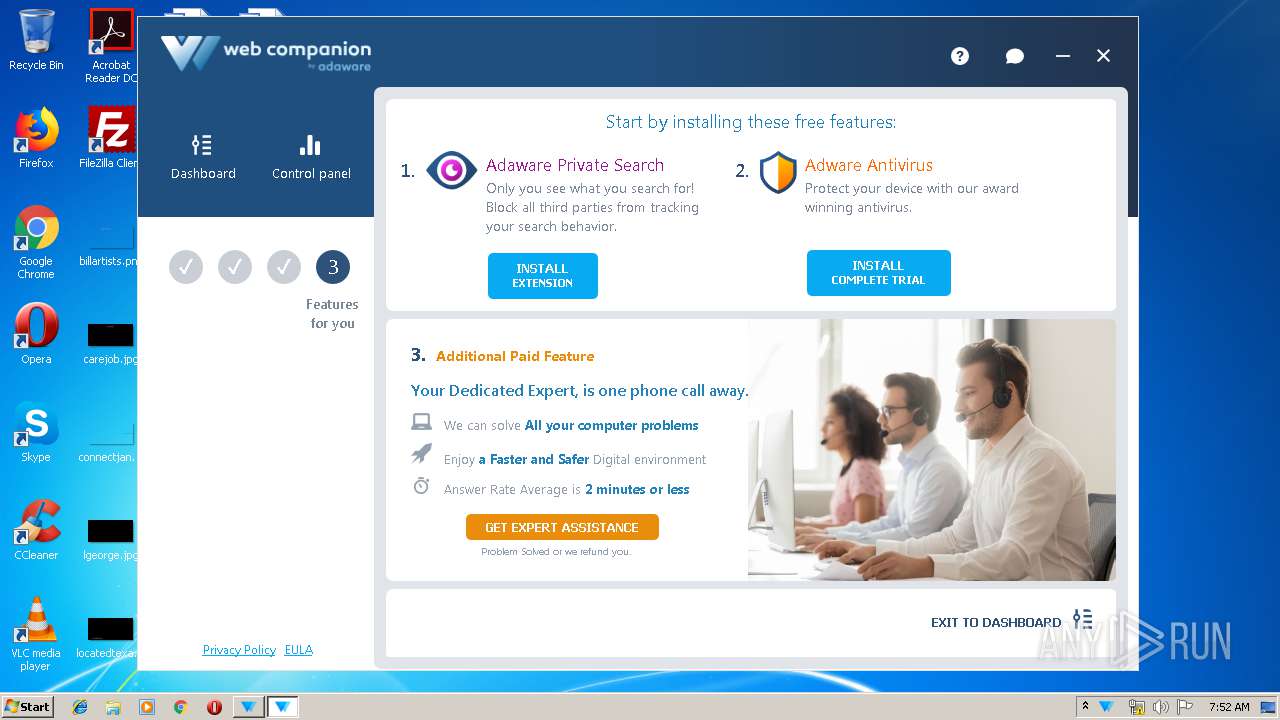
WebCompanionInstaller.exe | Detecting windows culture
|
WebCompanionInstaller.exe | 11/27/2019 7:50:58 AM :-> Starting installer 5.1.1035.1047 with: .\WebCompanionInstaller.exe --partner=newwebsite --version=5.0.15.1003 --version=5.1.1035.1047 --prod, Run as admin: True
|
WebCompanionInstaller.exe | Preparing for installing Web Companion
|
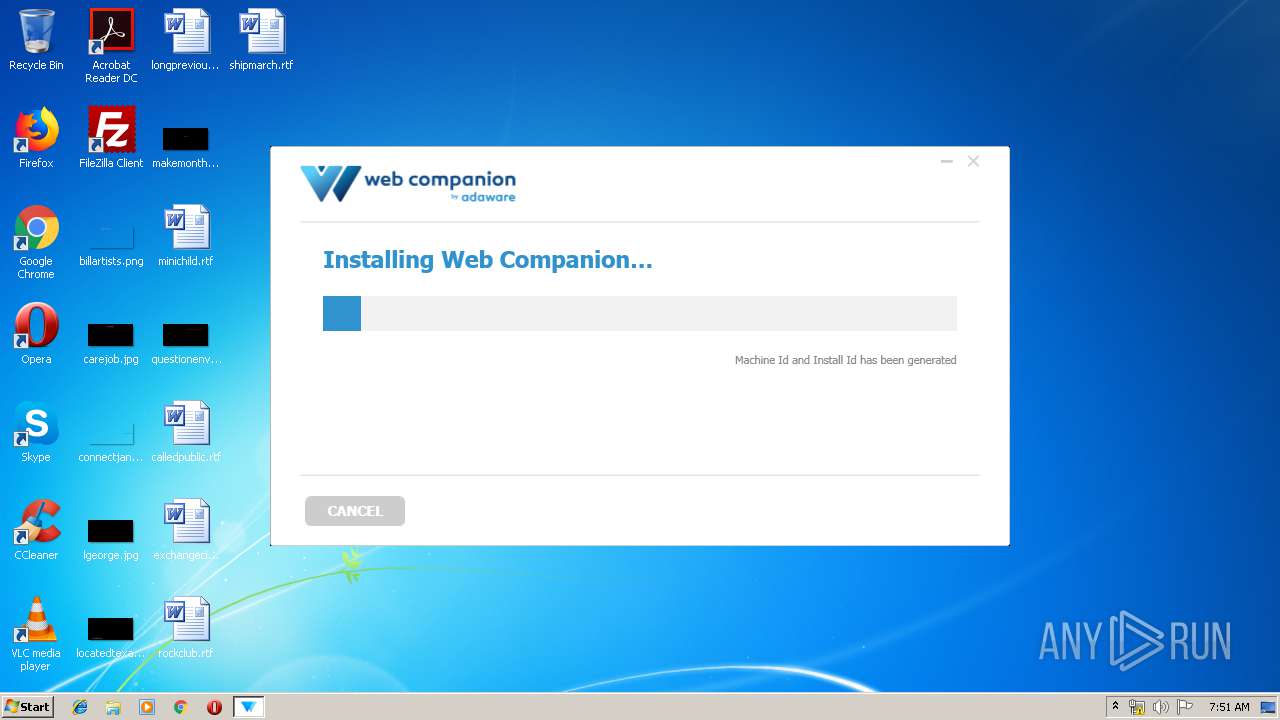
WebCompanionInstaller.exe | 11/27/2019 7:51:07 AM :-> Generating Machine and Install Id ...
|
WebCompanionInstaller.exe | 11/27/2019 7:51:07 AM :-> Machine Id and Install Id has been generated
|
WebCompanionInstaller.exe | 11/27/2019 7:51:07 AM :-> Checking prerequisites ...
|
WebCompanionInstaller.exe | 11/27/2019 7:51:07 AM :-> Antivirus not detected
|
WebCompanionInstaller.exe | 11/27/2019 7:51:07 AM :-> vm_check False
|
WebCompanionInstaller.exe | 11/27/2019 7:51:08 AM :-> reg_check :False
|
WebCompanionInstaller.exe | 11/27/2019 7:51:08 AM :-> Installed .Net framework is V40
|