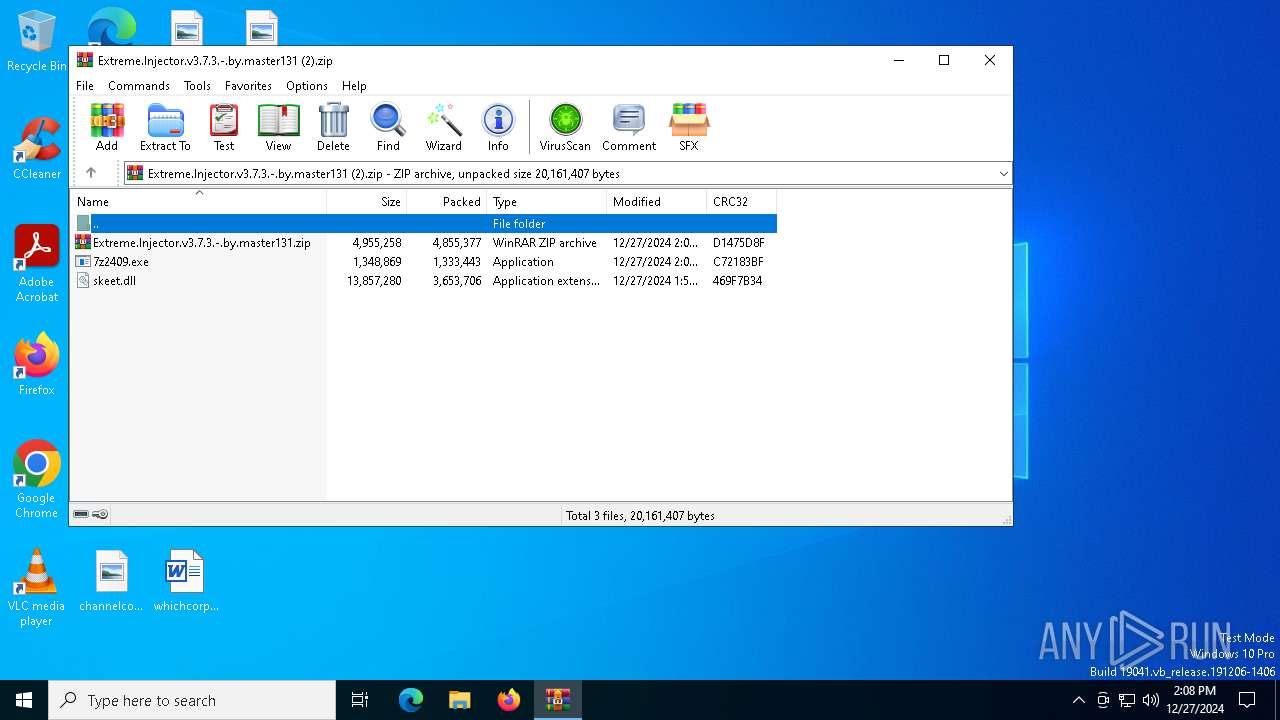
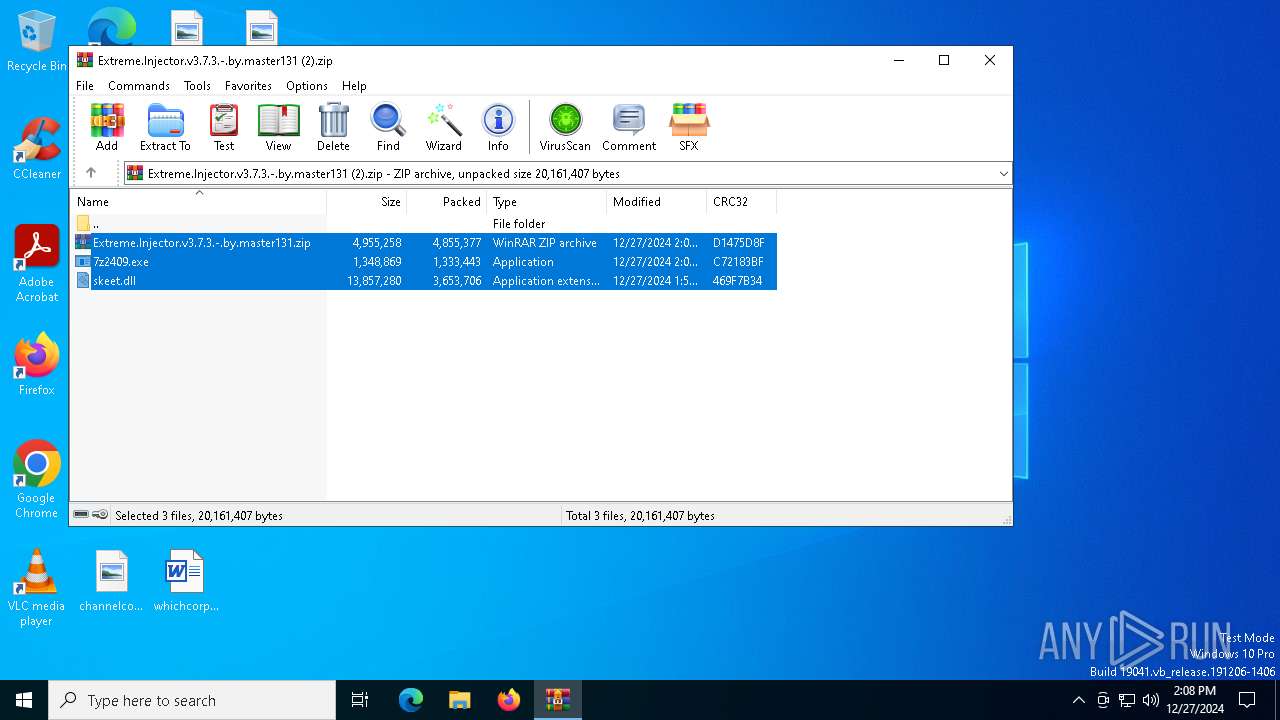
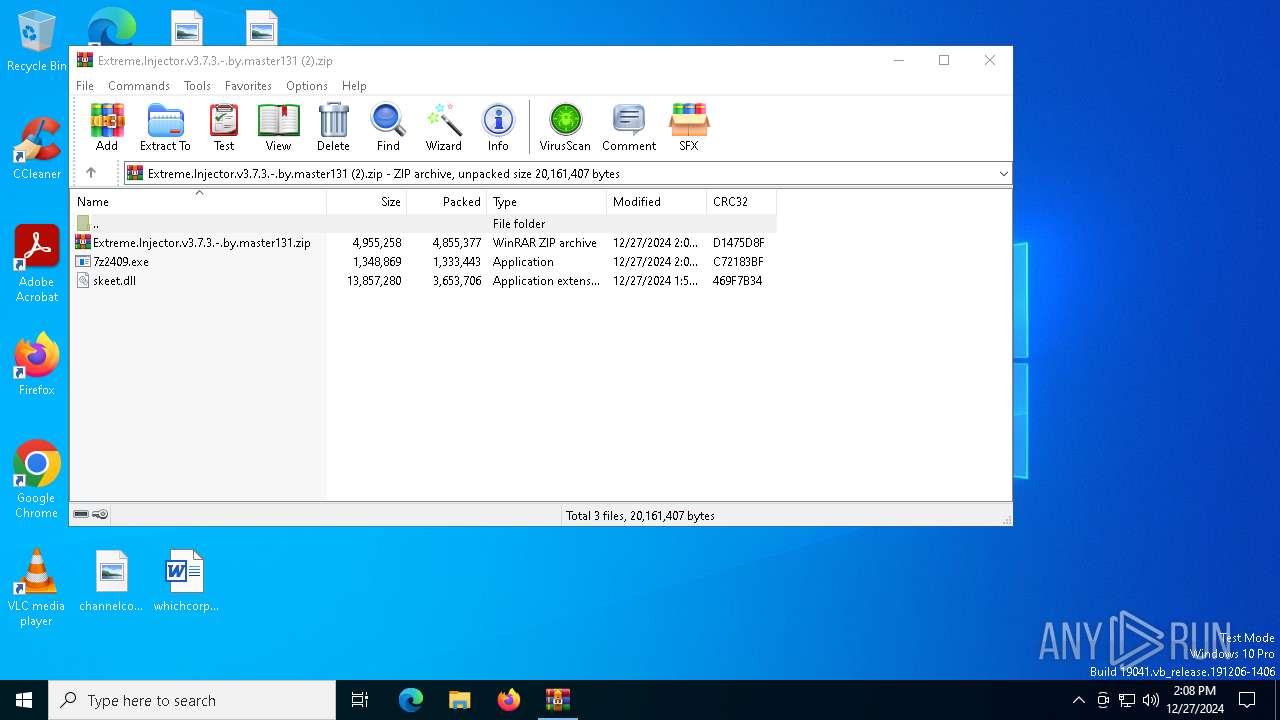
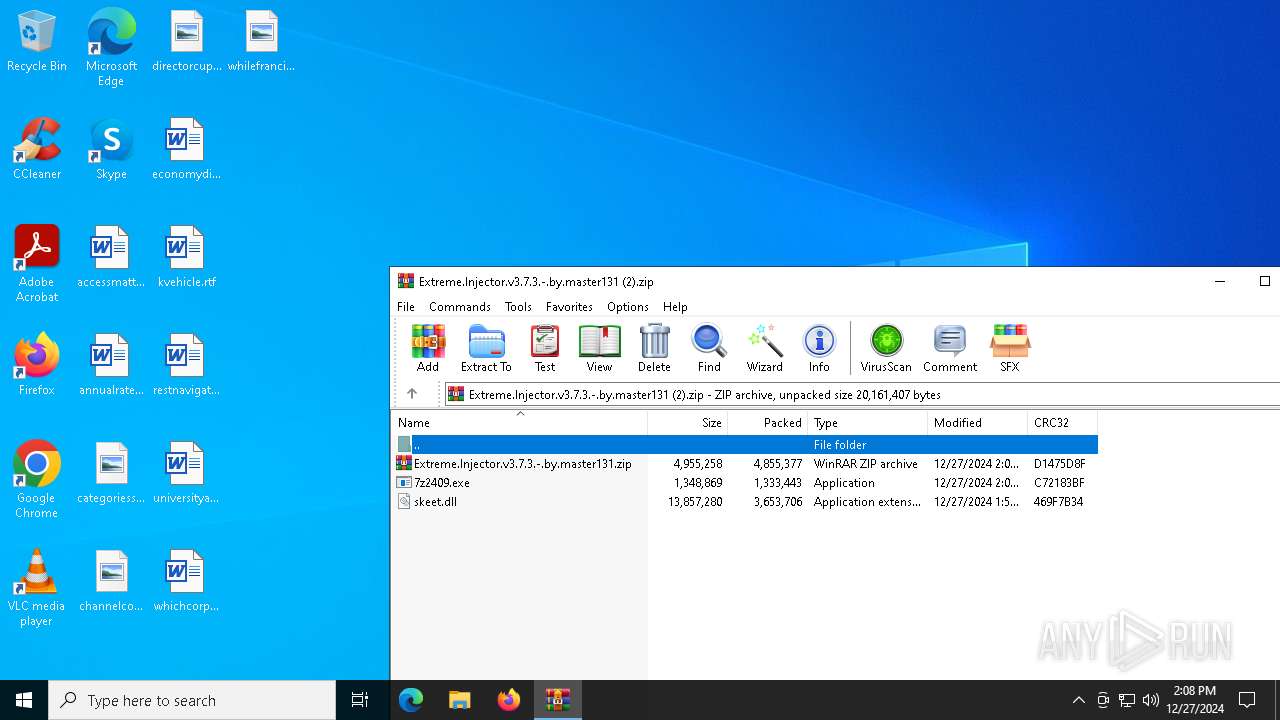
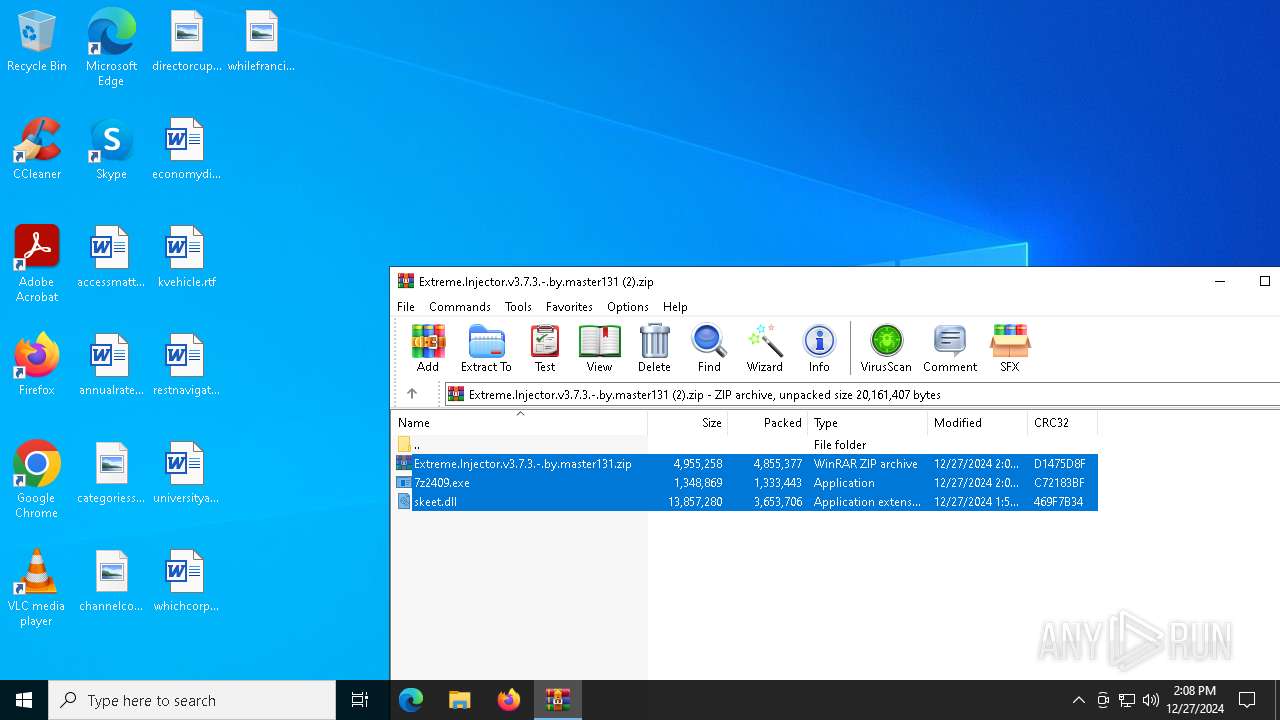
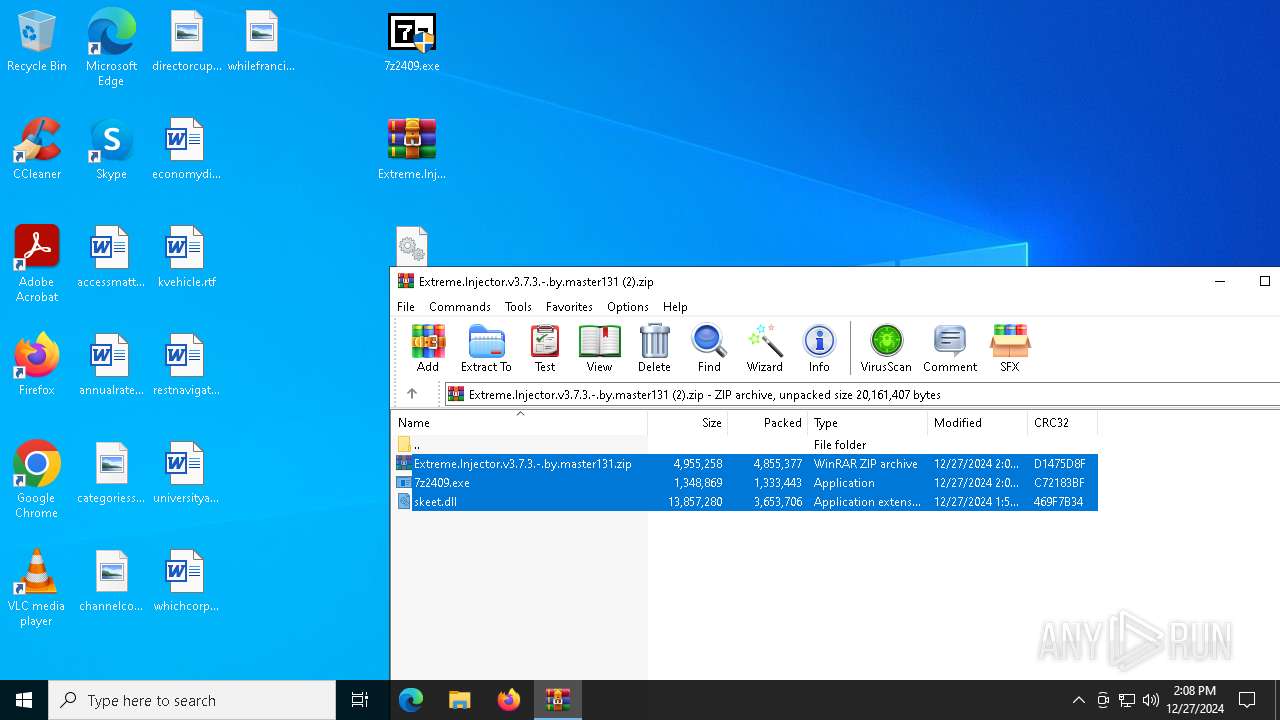
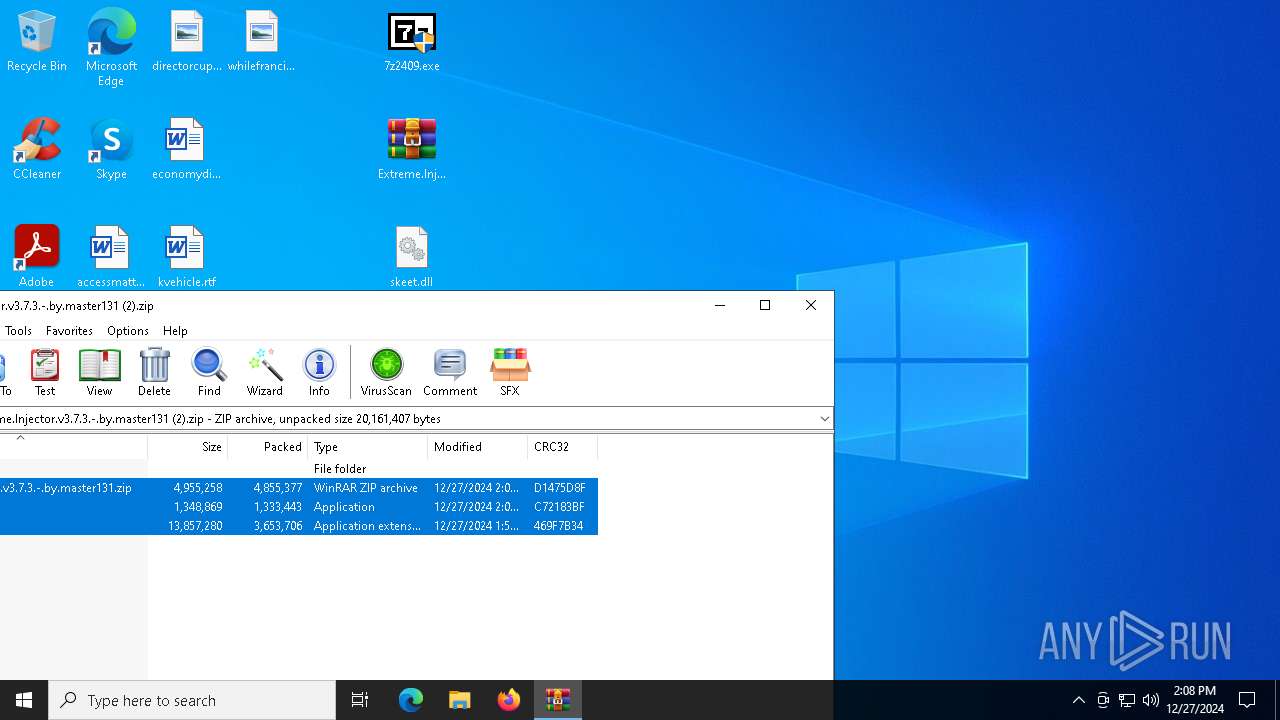
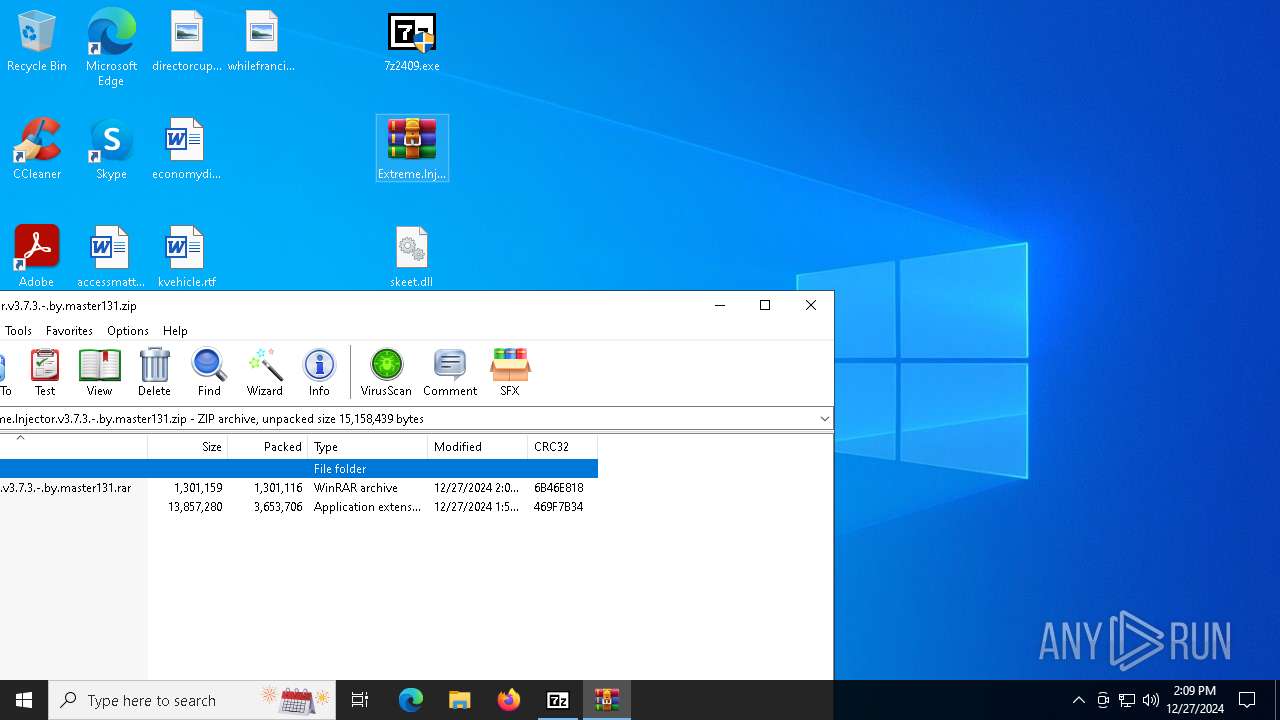
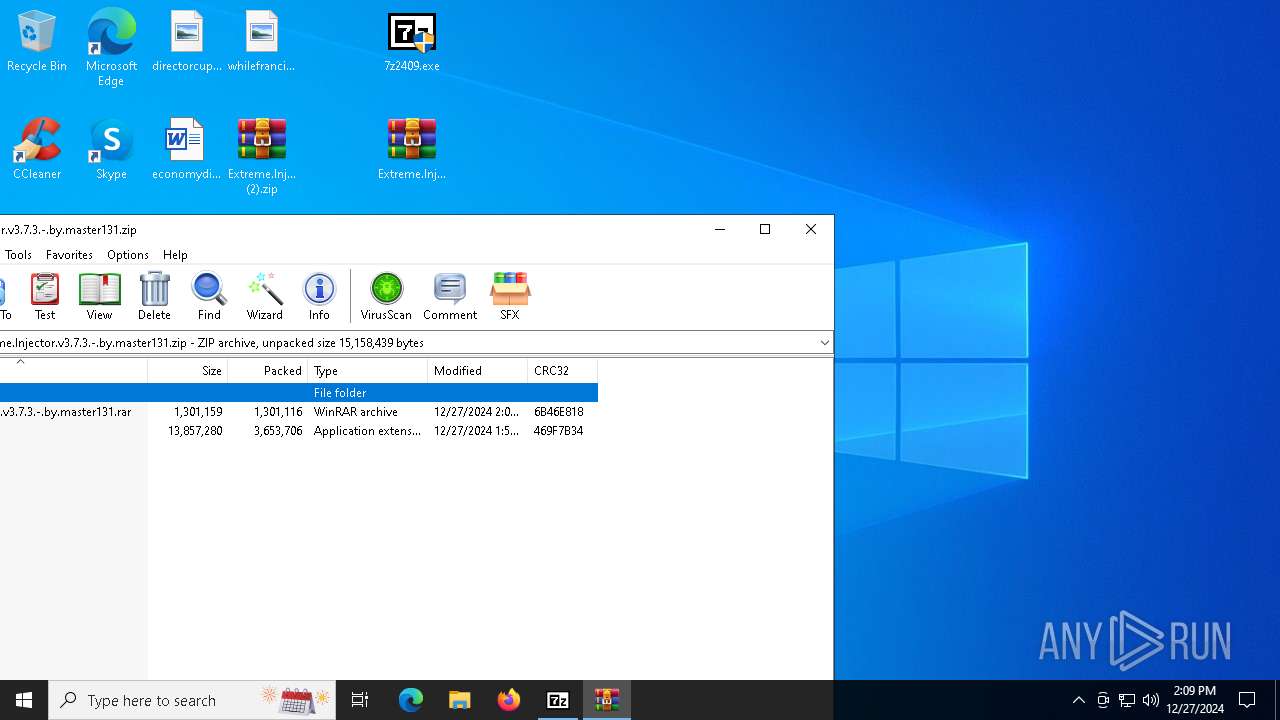
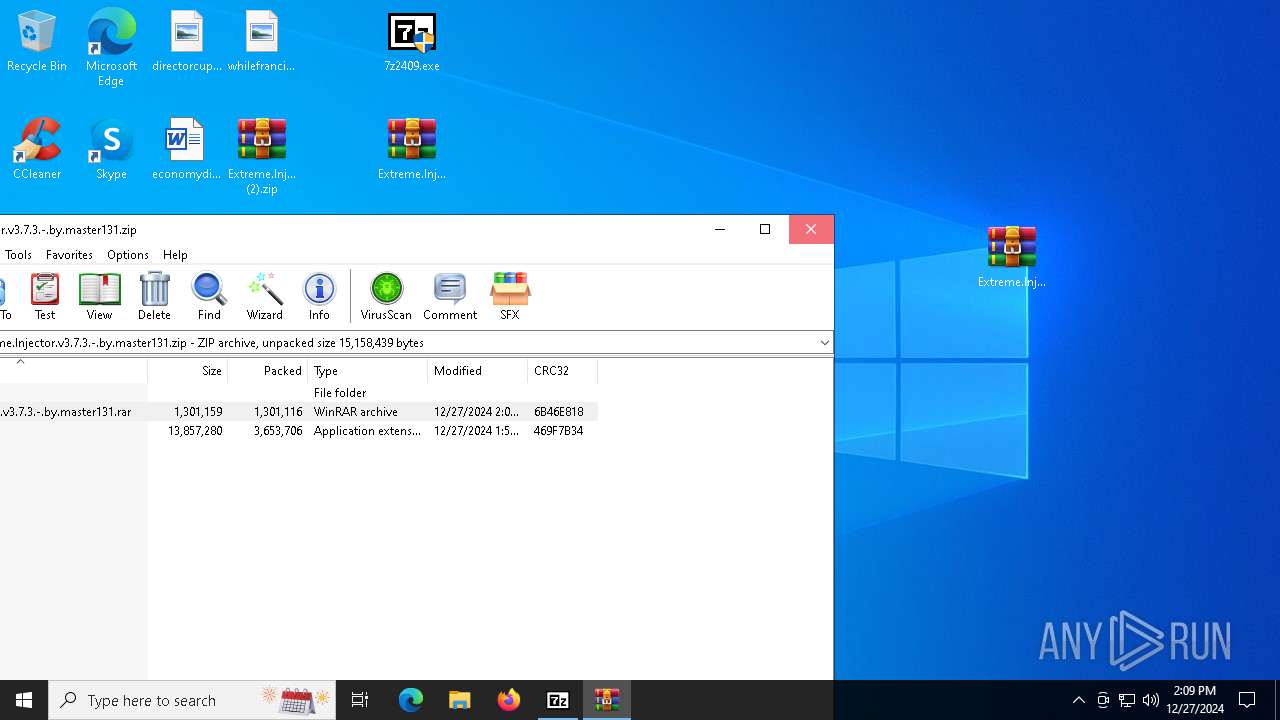
| File name: | Extreme.Injector.v3.7.3.-.by.master131 (2).zip |
| Full analysis: | https://app.any.run/tasks/04a6aef3-7d8b-4fe9-9889-7b88e3960bf3 |
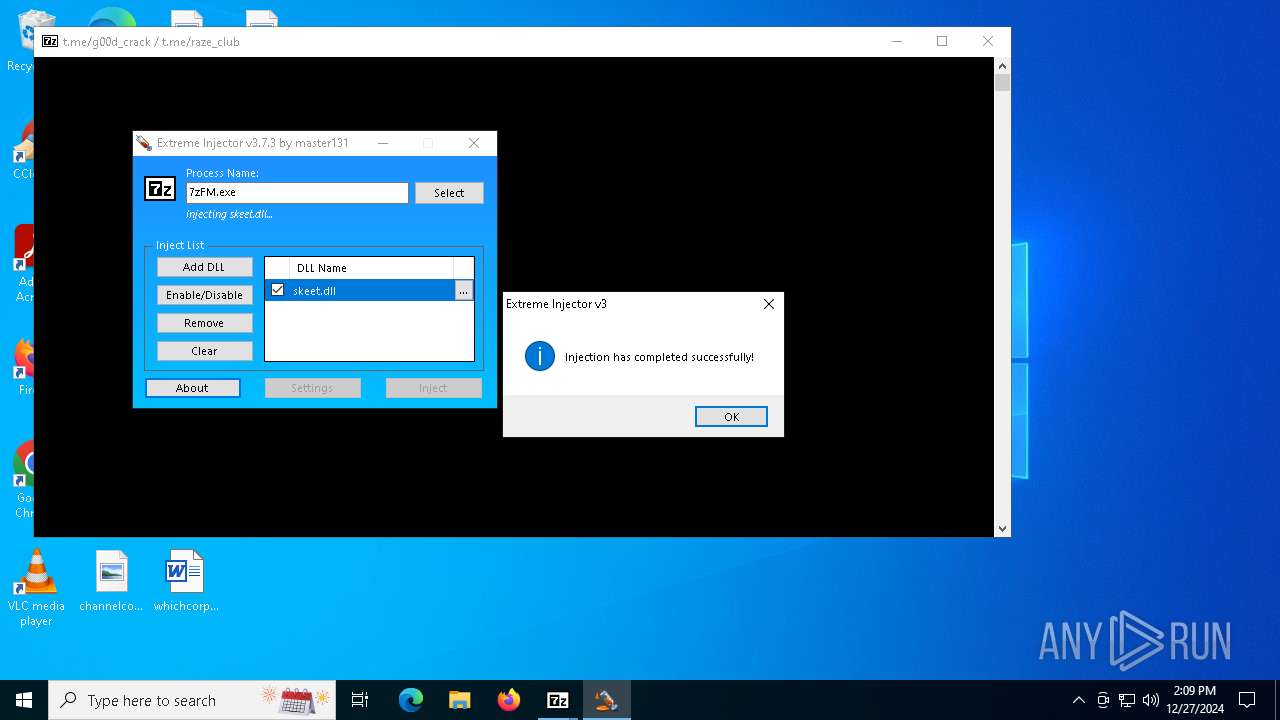
| Verdict: | Malicious activity |
| Analysis date: | December 27, 2024, 14:07:57 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 455B4CF4A08A3C30FC7F4E2AE10E34B8 |
| SHA1: | E34416430E491F8F1CFDD3751C62936F4116DEE6 |
| SHA256: | 6F10E780EDC0587BD07844930A94D6613AD03BC646899456BBE26F9B97602E4B |
| SSDEEP: | 98304:NMnR0Rokyfi0nnr6y1AwggxNpZ7Fgnk1SFpUofWKK+aSqRi9dZ4irwlcducmn+7q:N23i/dCwbXg |
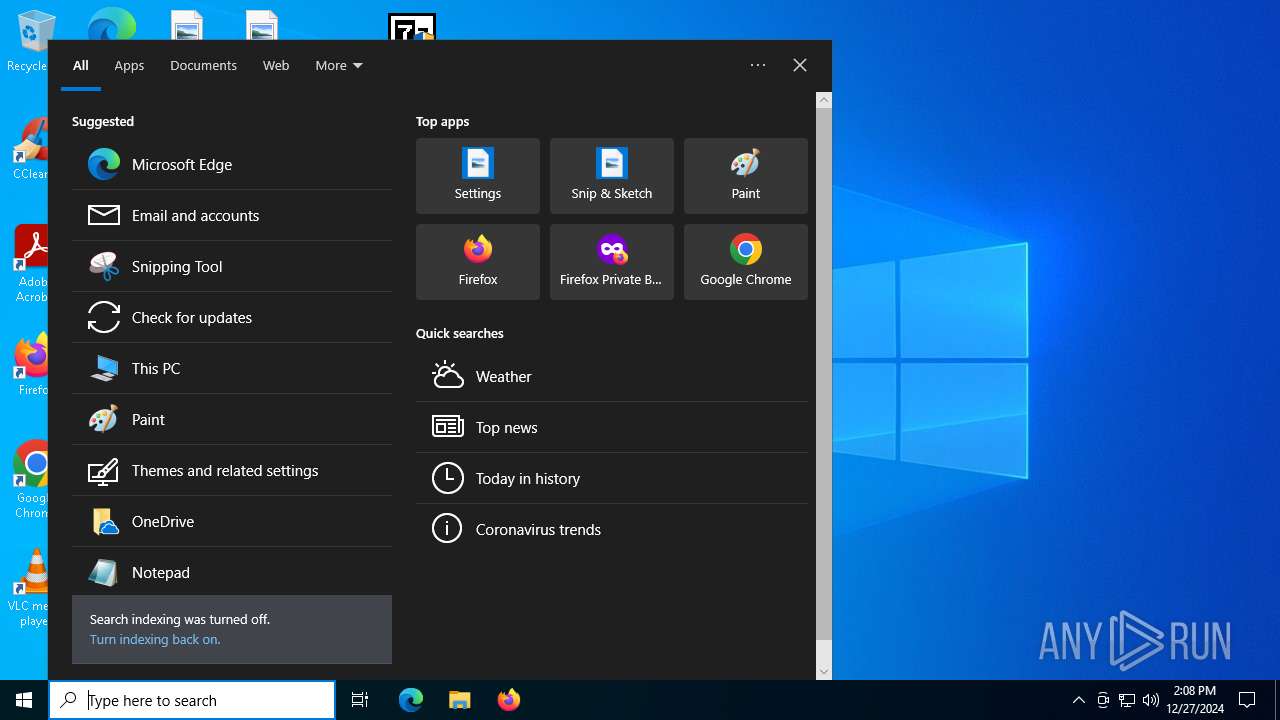
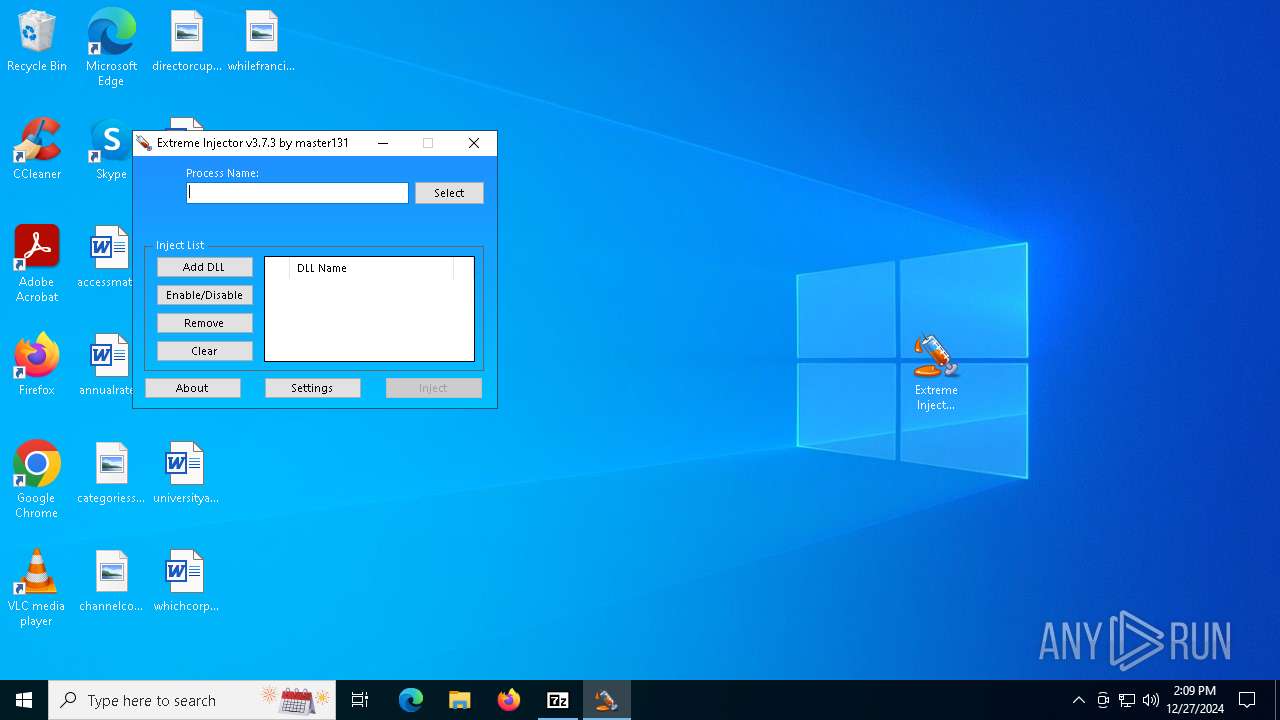
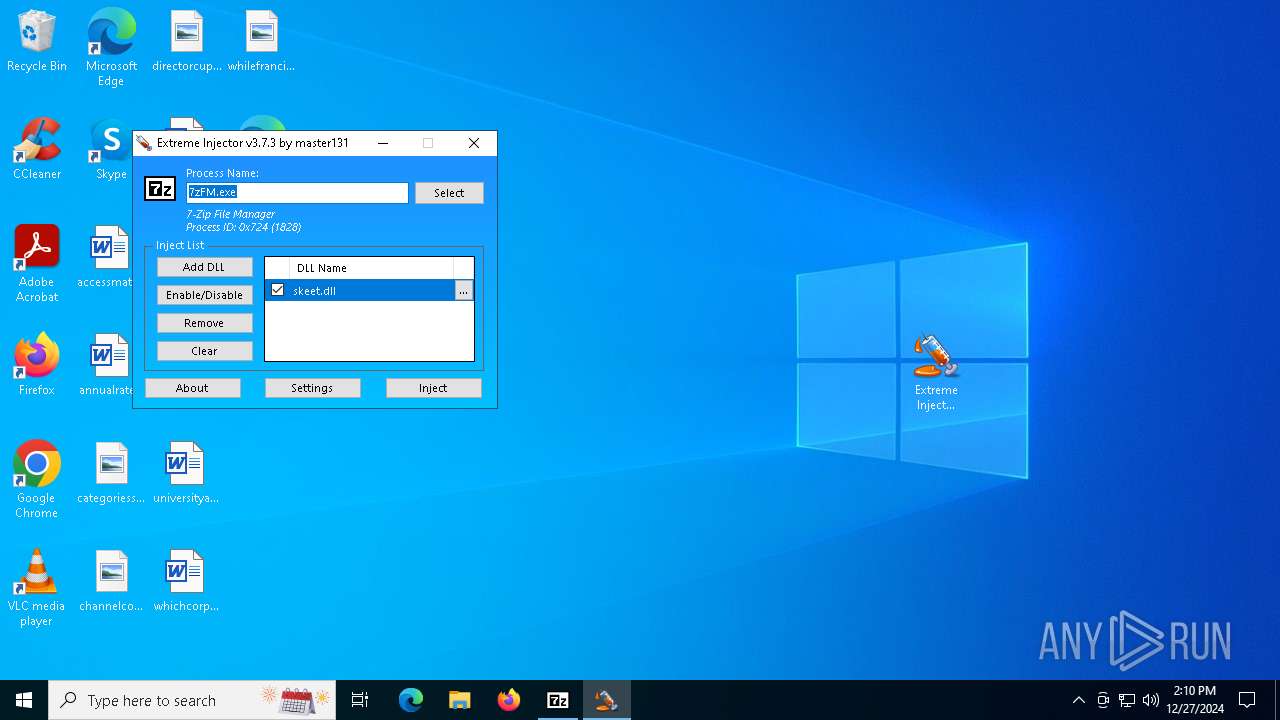
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6560)
SUSPICIOUS
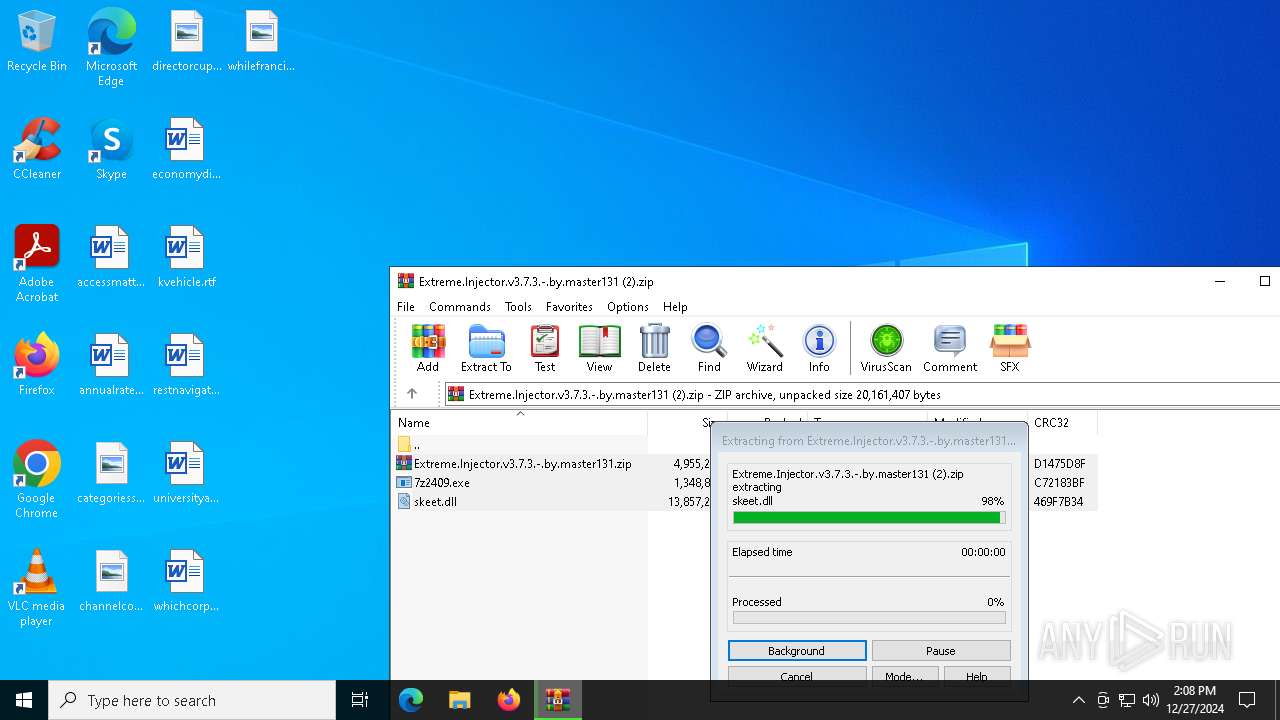
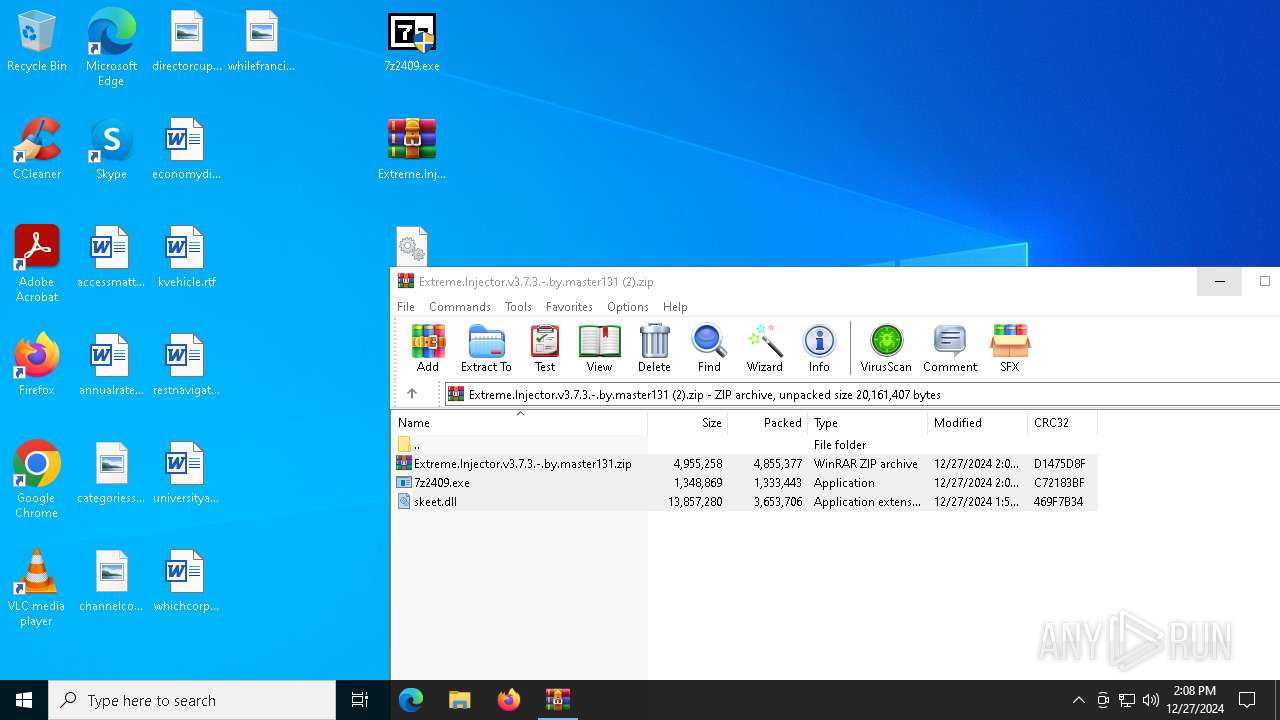
Executable content was dropped or overwritten
- 7z2409.exe (PID: 4764)
Creates/Modifies COM task schedule object
- 7z2409.exe (PID: 4764)
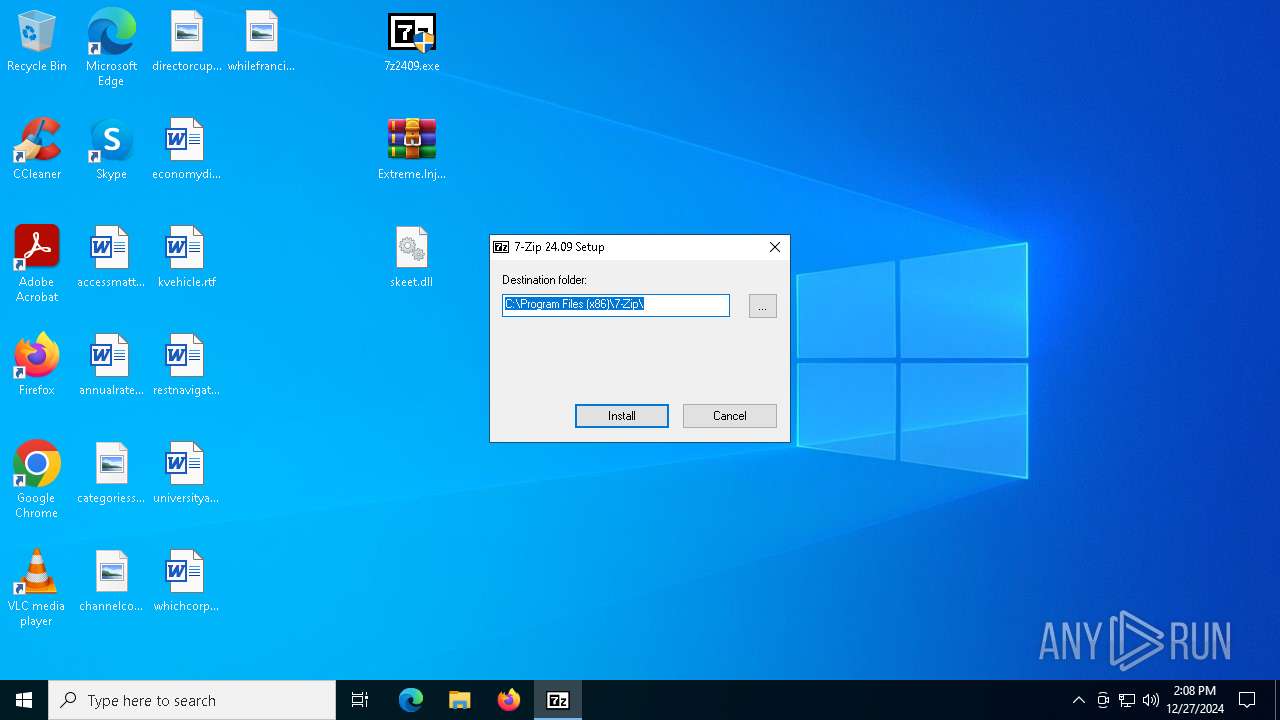
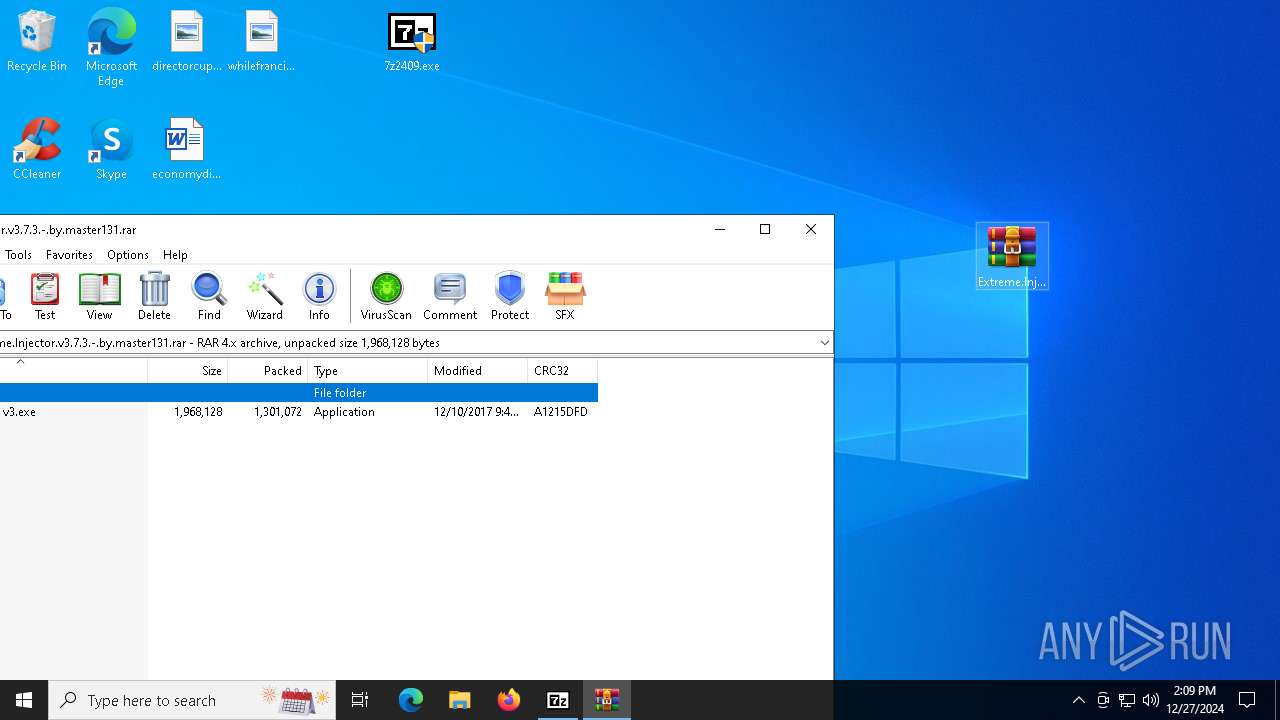
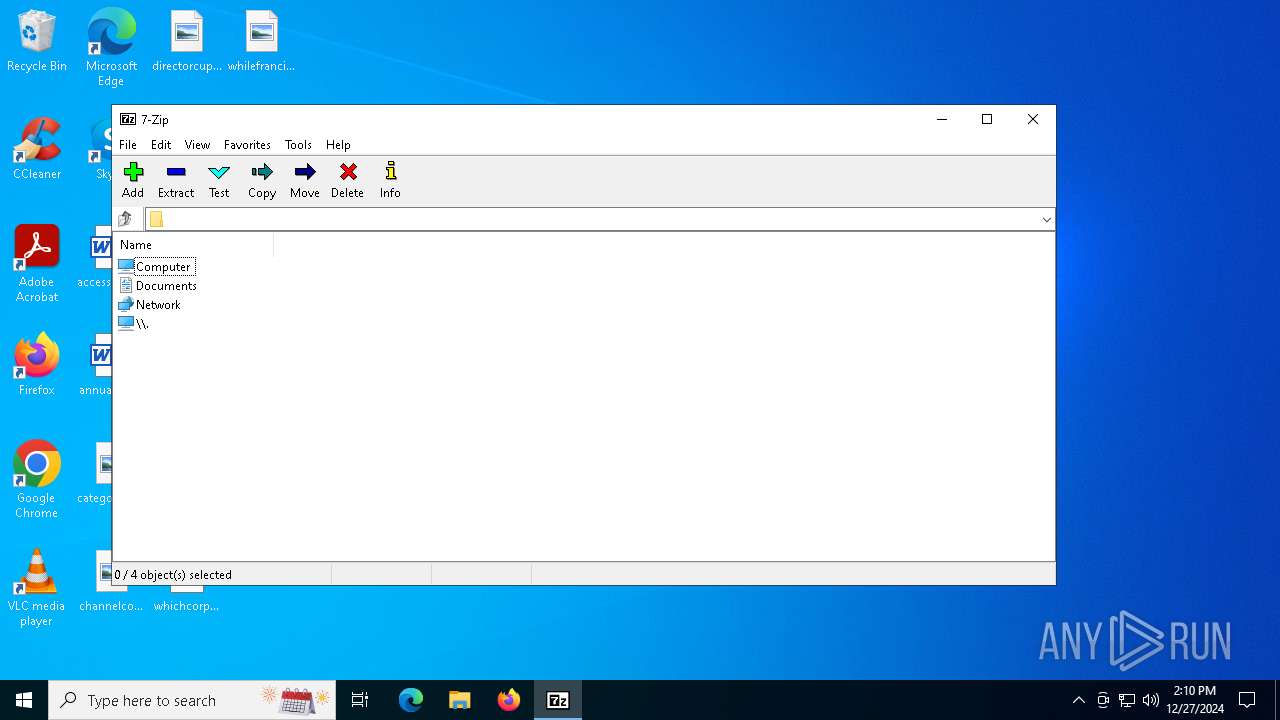
Drops 7-zip archiver for unpacking
- WinRAR.exe (PID: 6560)
- 7z2409.exe (PID: 4764)
Creates a software uninstall entry
- 7z2409.exe (PID: 4764)
Reads the date of Windows installation
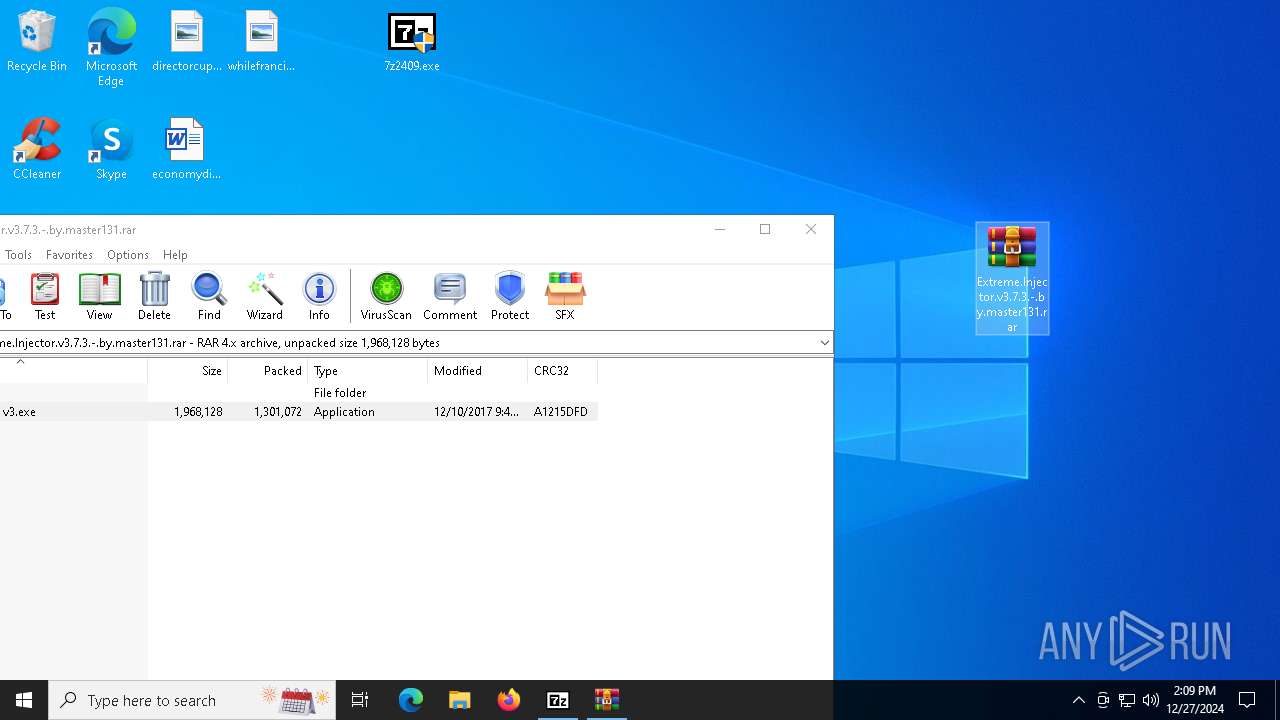
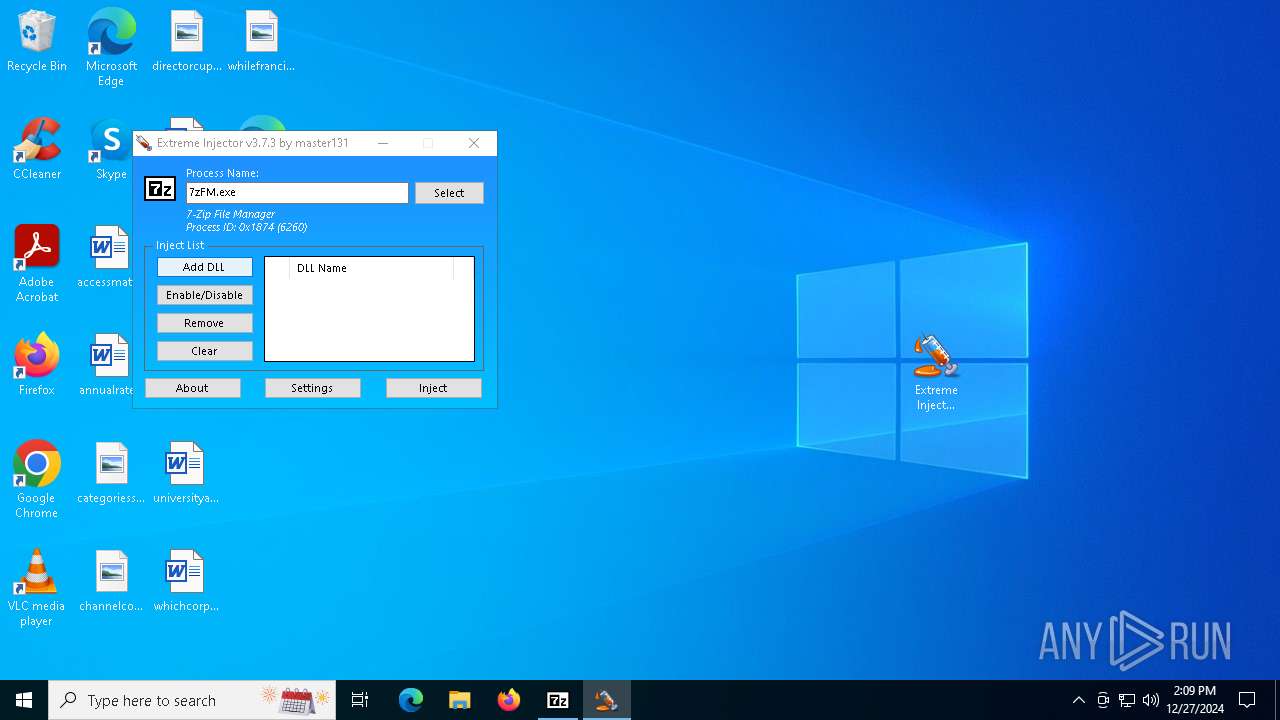
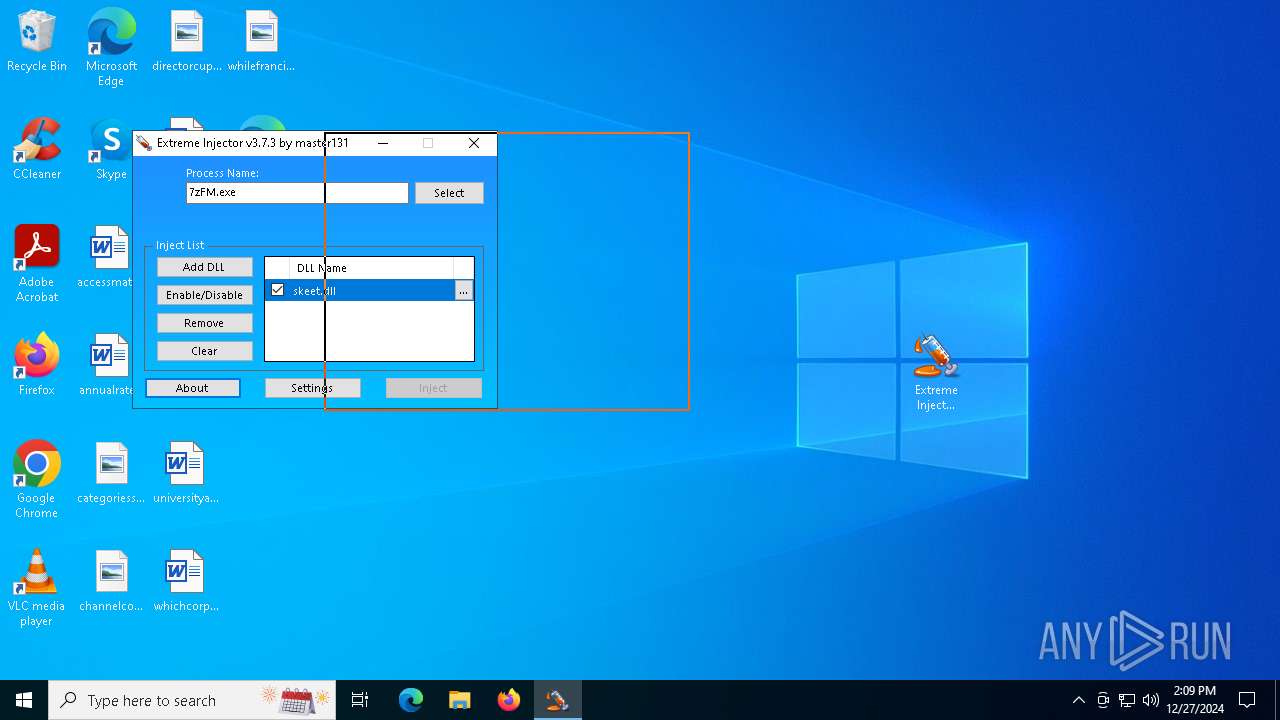
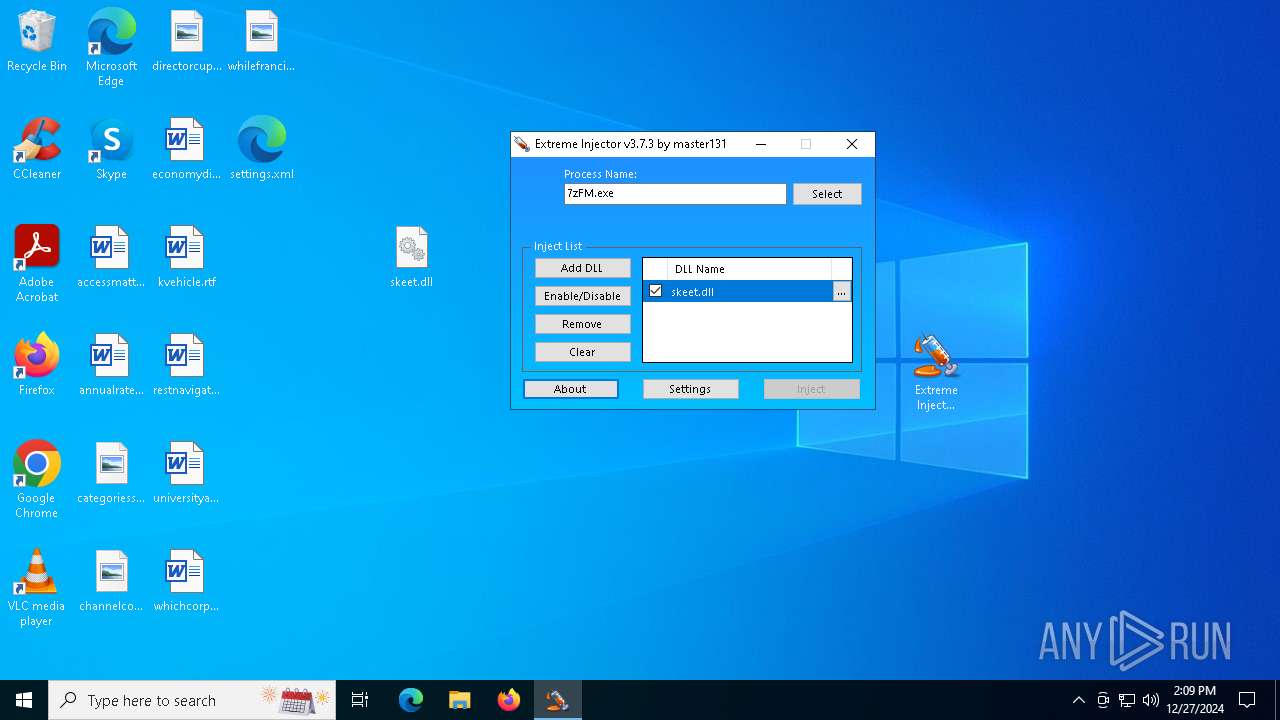
- Extreme Injector v3.exe (PID: 5092)
- Extreme Injector v3.exe (PID: 6284)
Application launched itself
- Extreme Injector v3.exe (PID: 5092)
- Extreme Injector v3.exe (PID: 6284)
Reads security settings of Internet Explorer
- Extreme Injector v3.exe (PID: 5092)
- Extreme Injector v3.exe (PID: 4400)
- Extreme Injector v3.exe (PID: 6284)
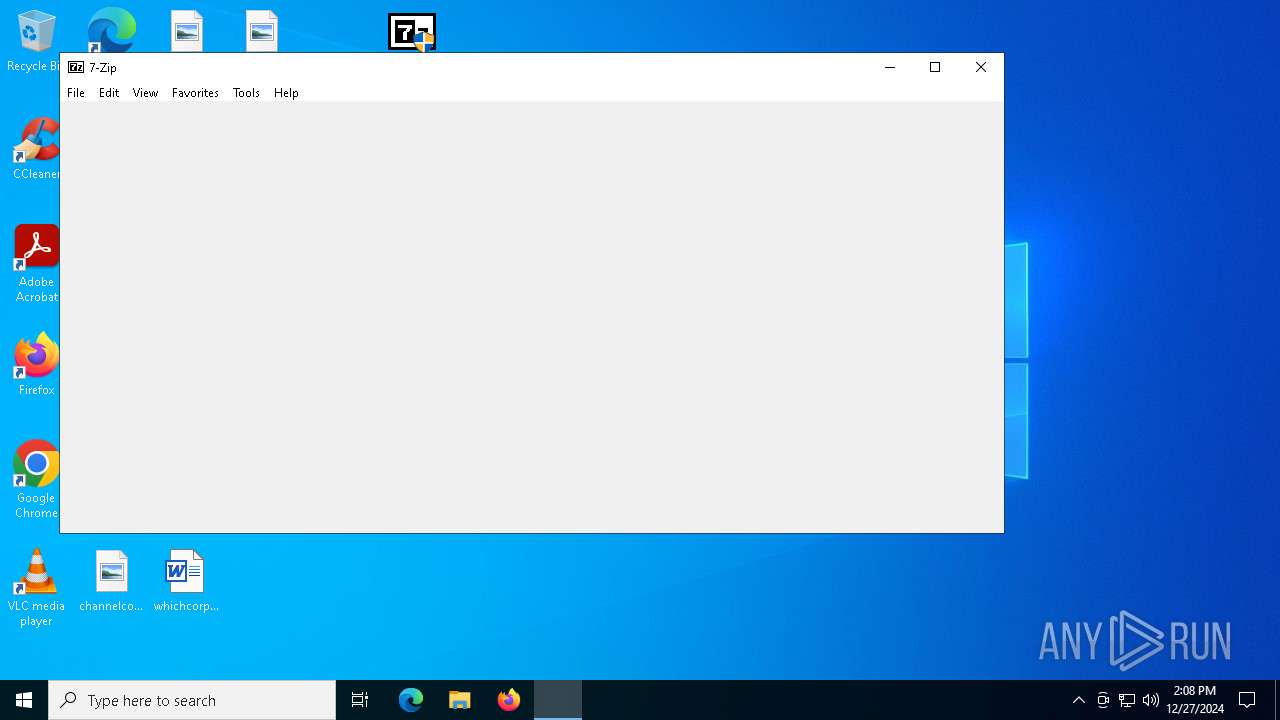
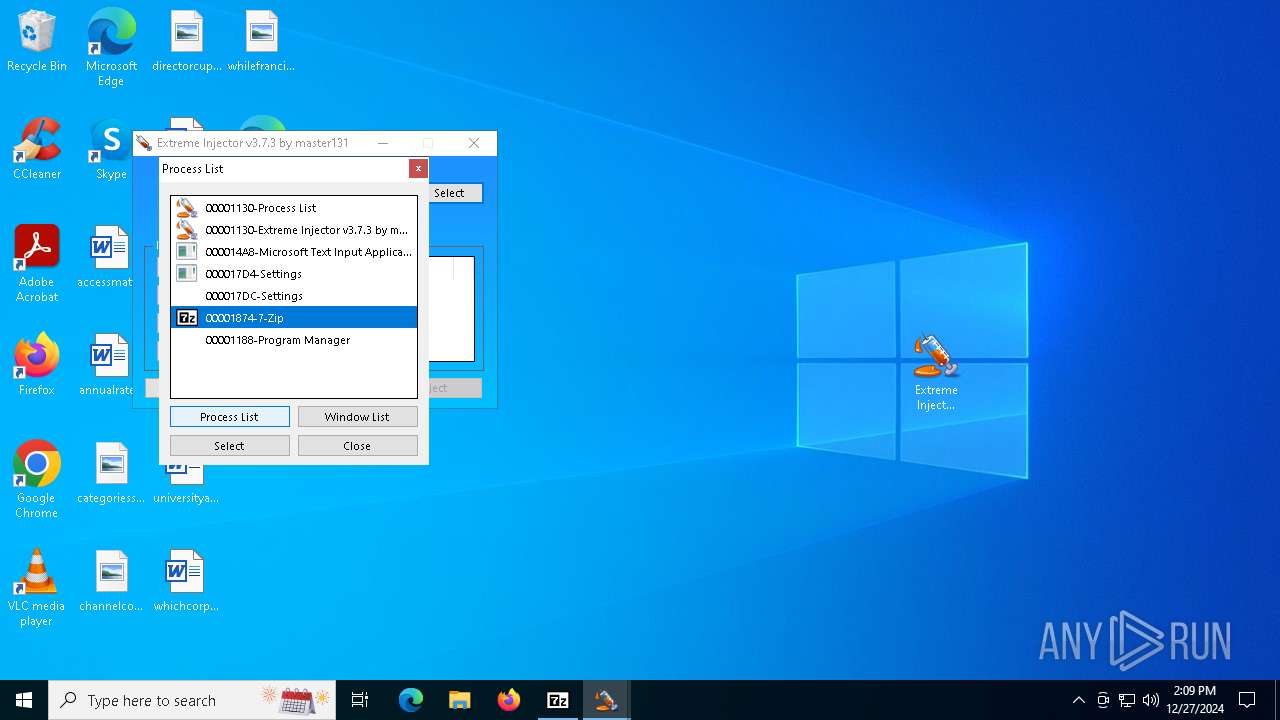
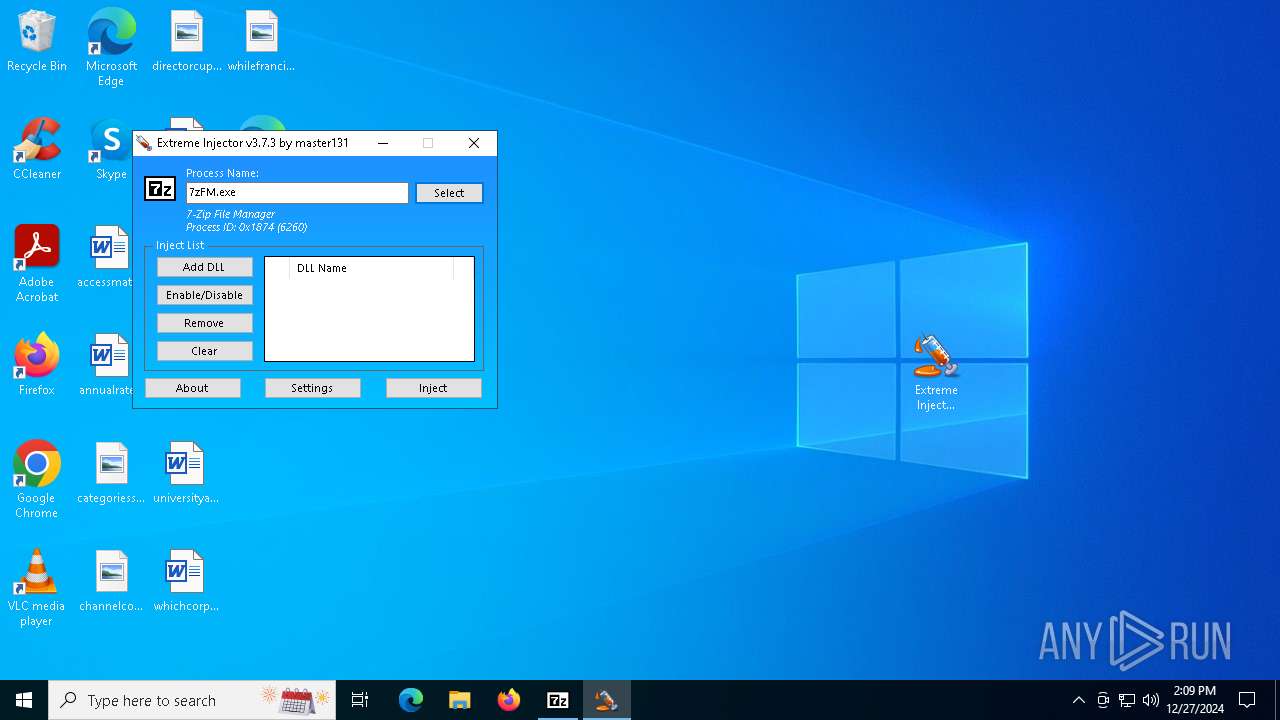
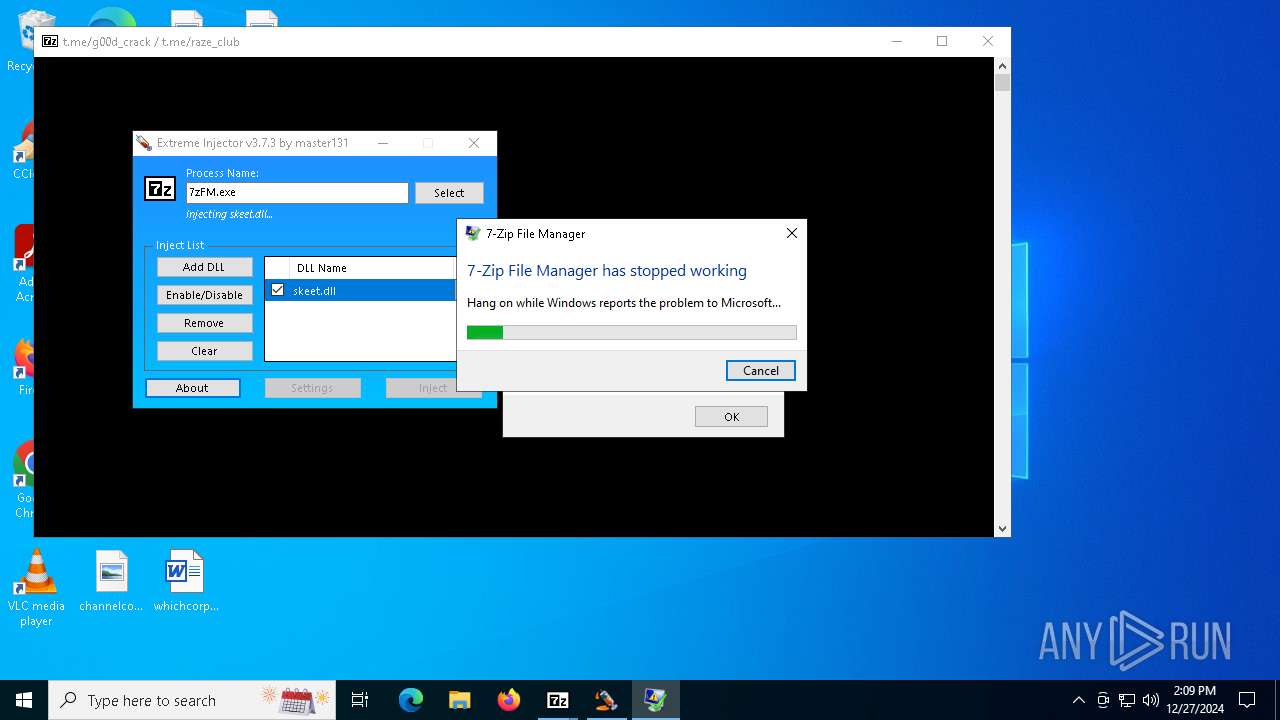
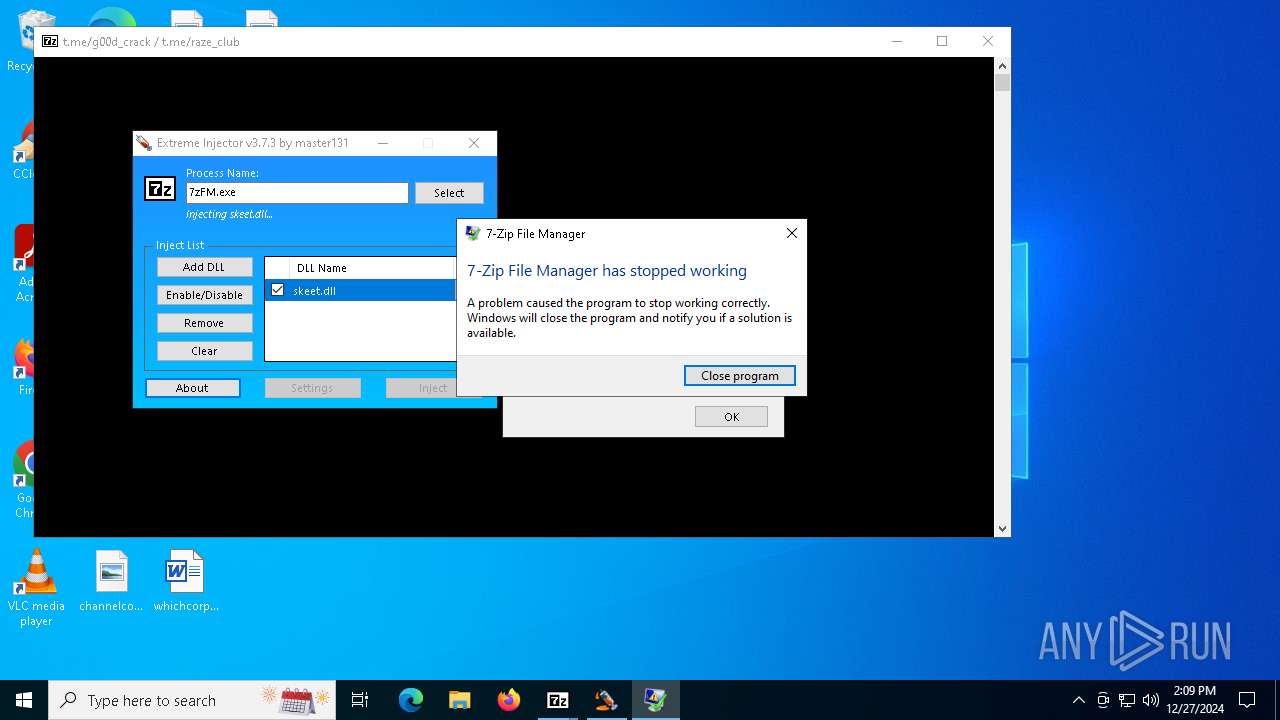
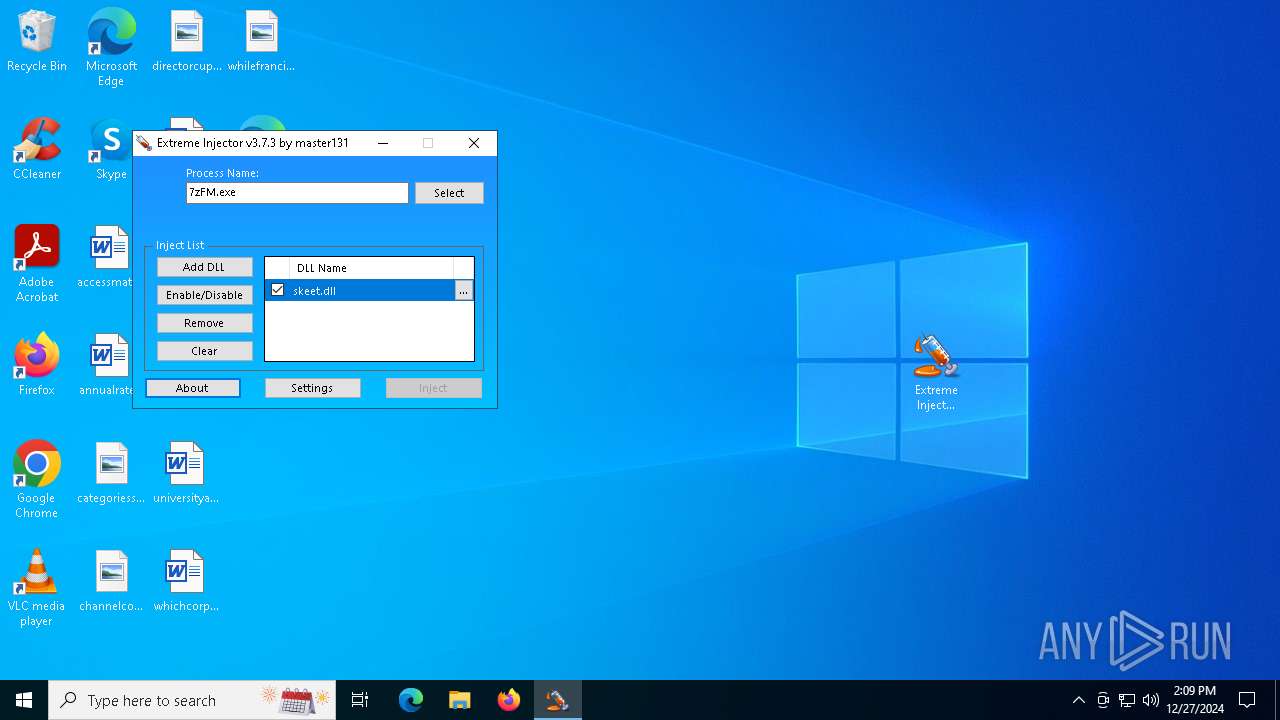
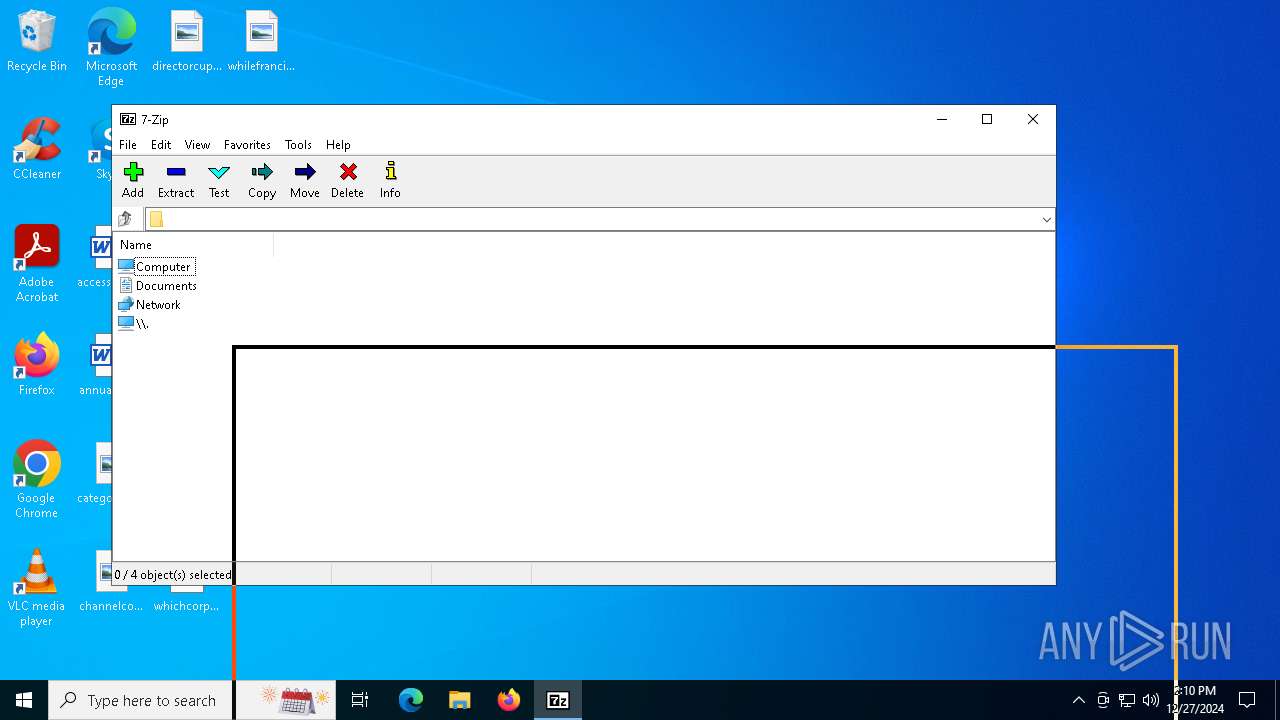
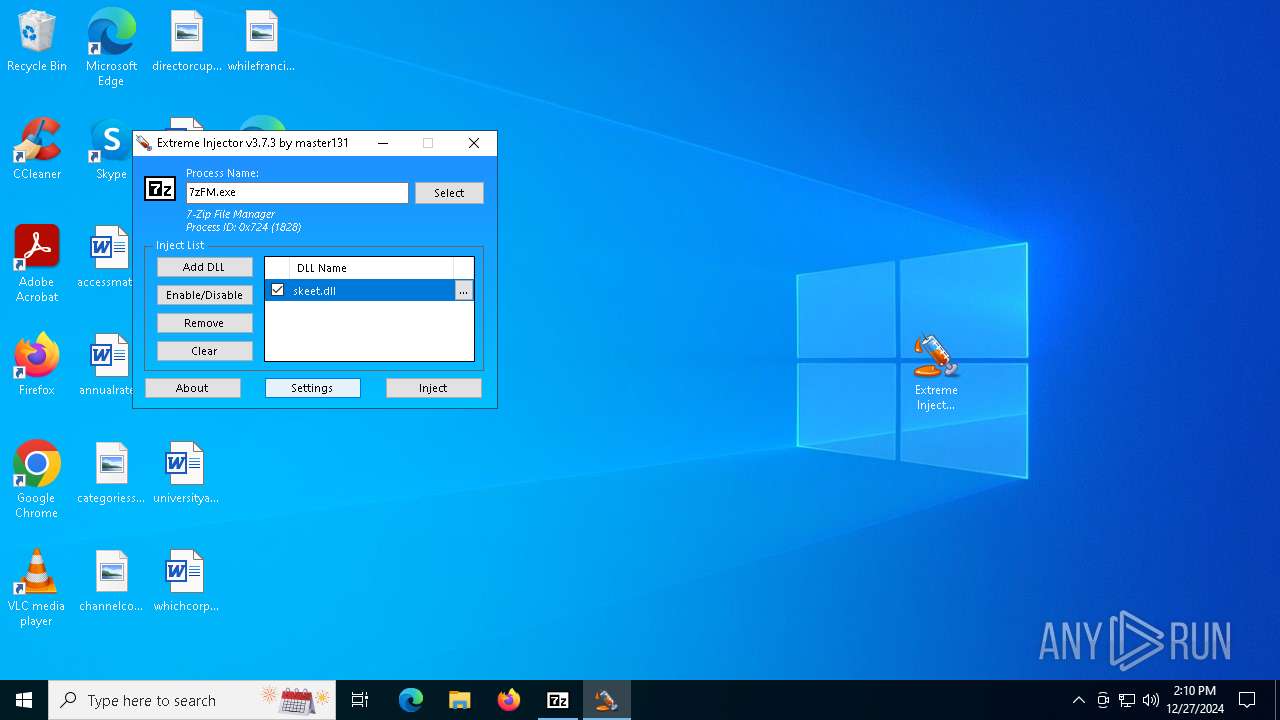
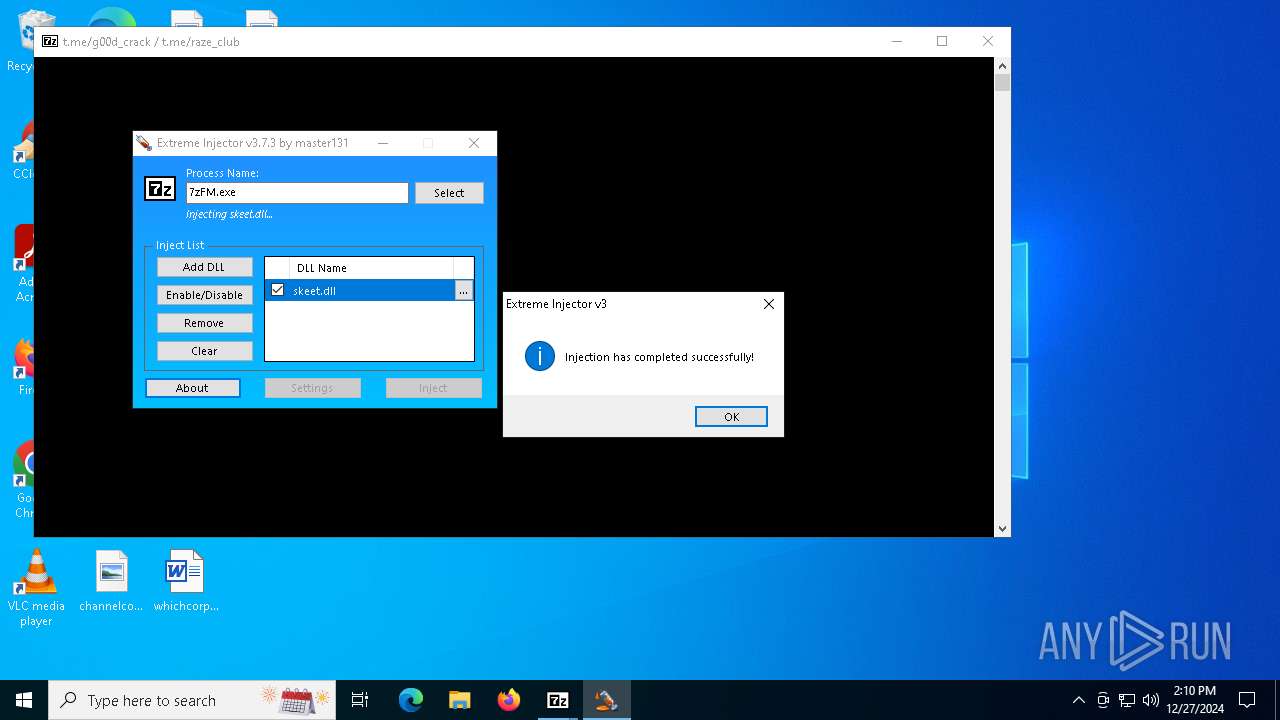
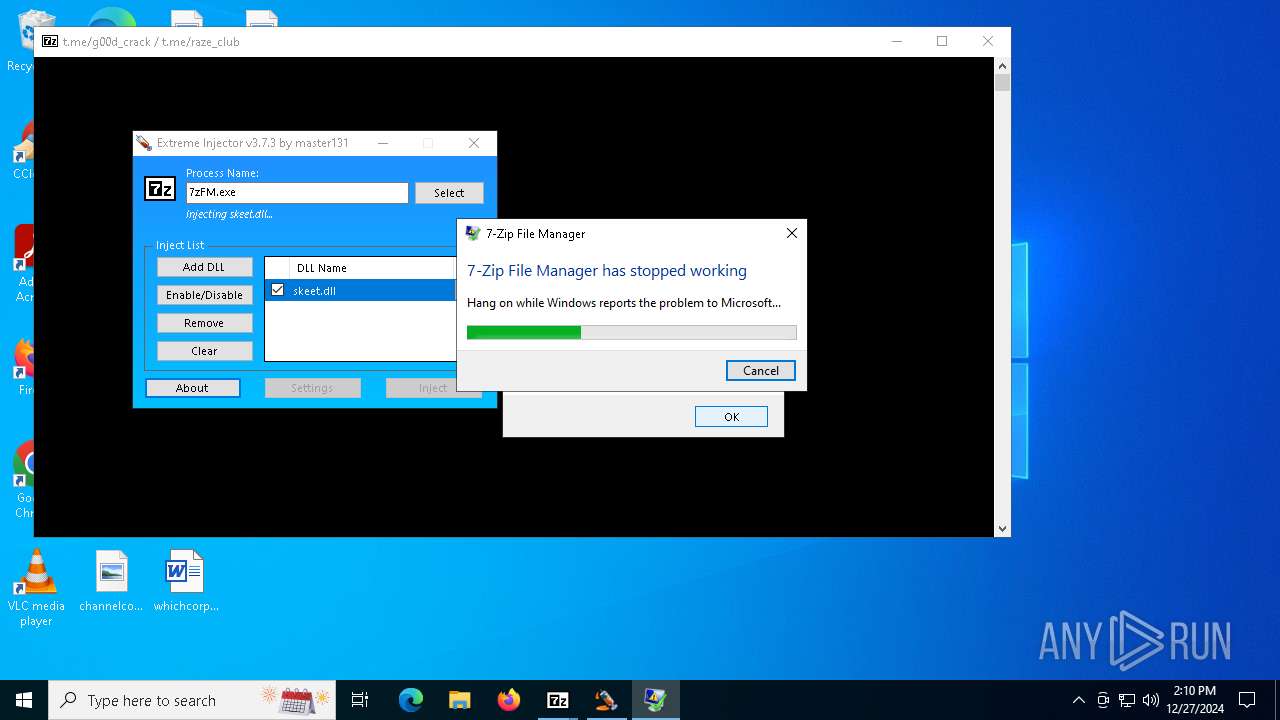
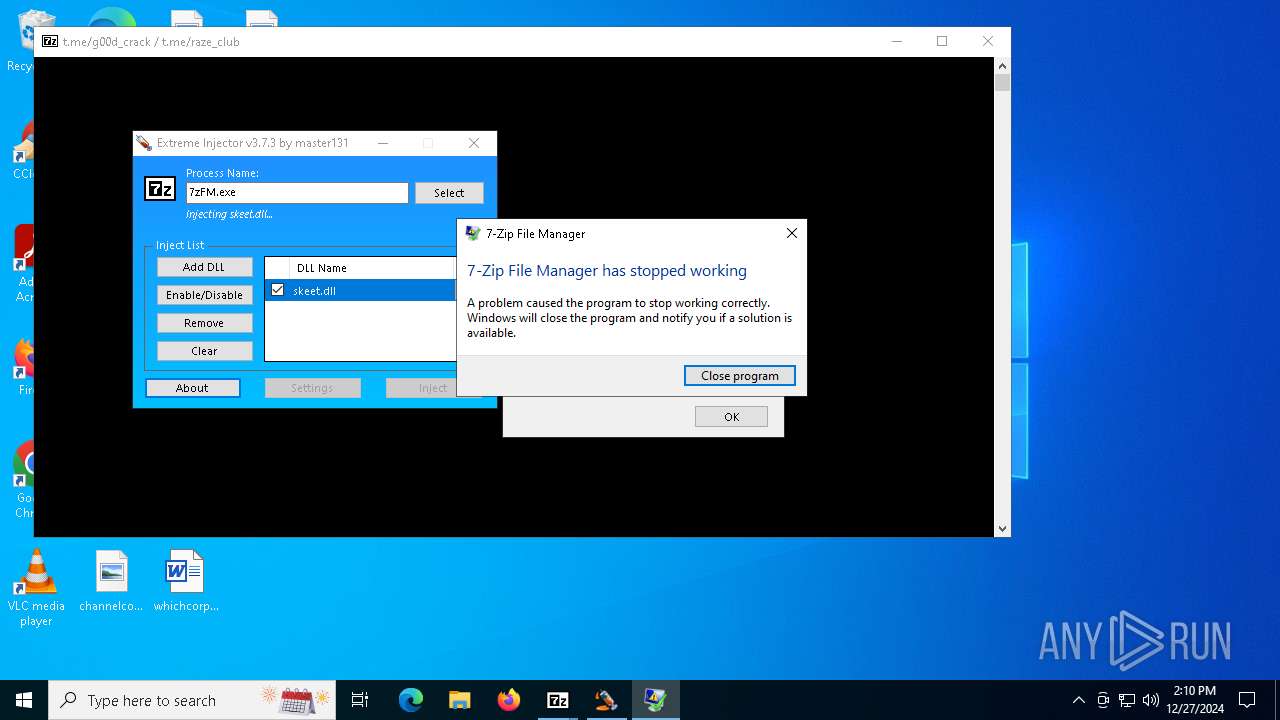
Executes application which crashes
- 7zFM.exe (PID: 6260)
- 7zFM.exe (PID: 1828)
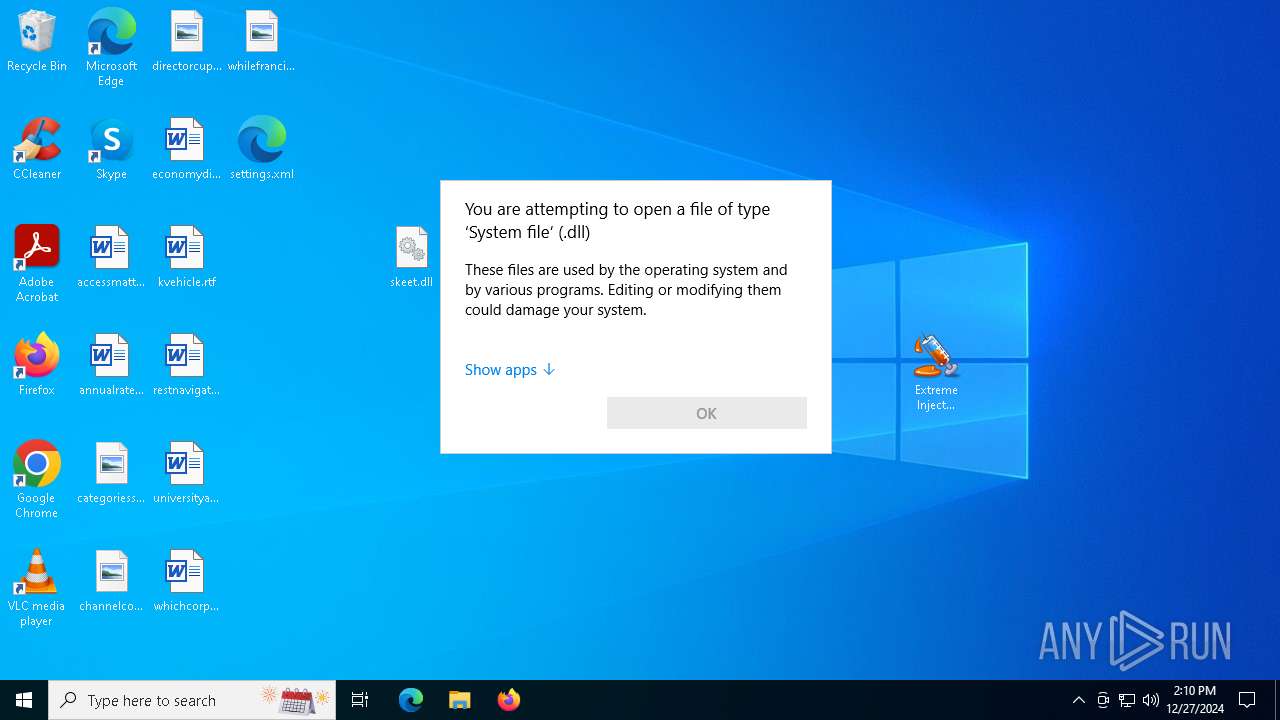
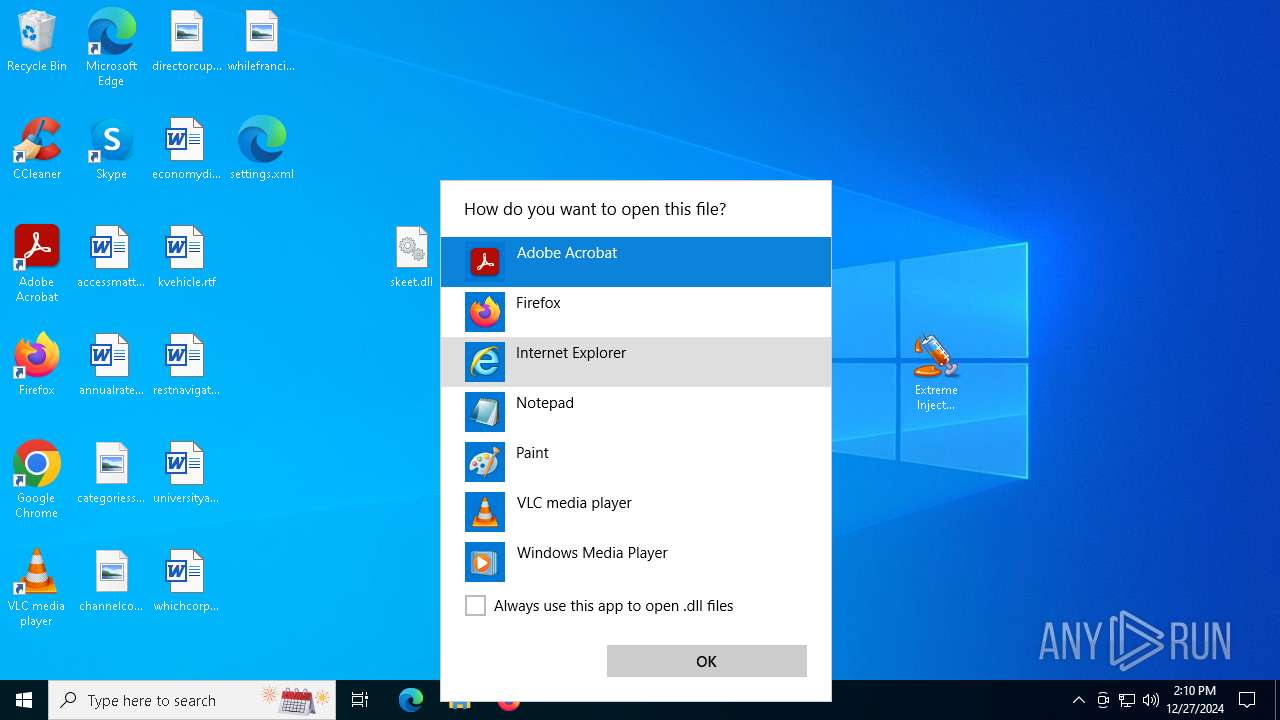
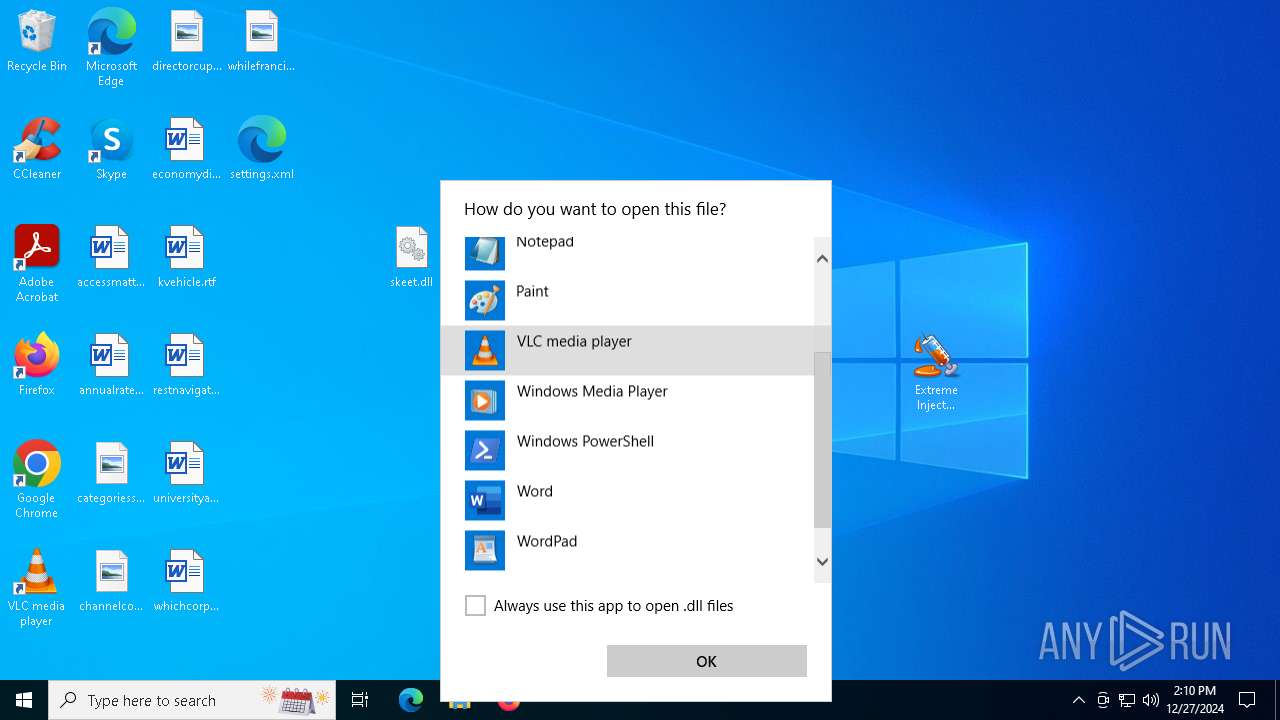
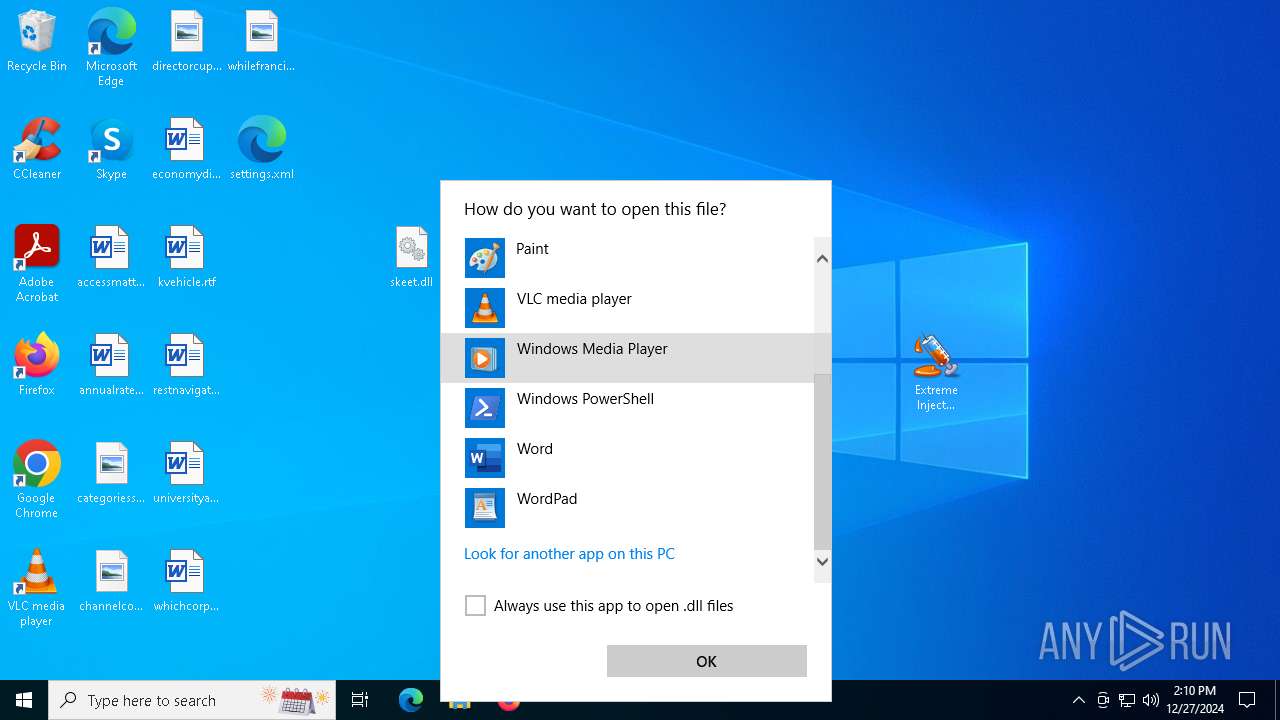
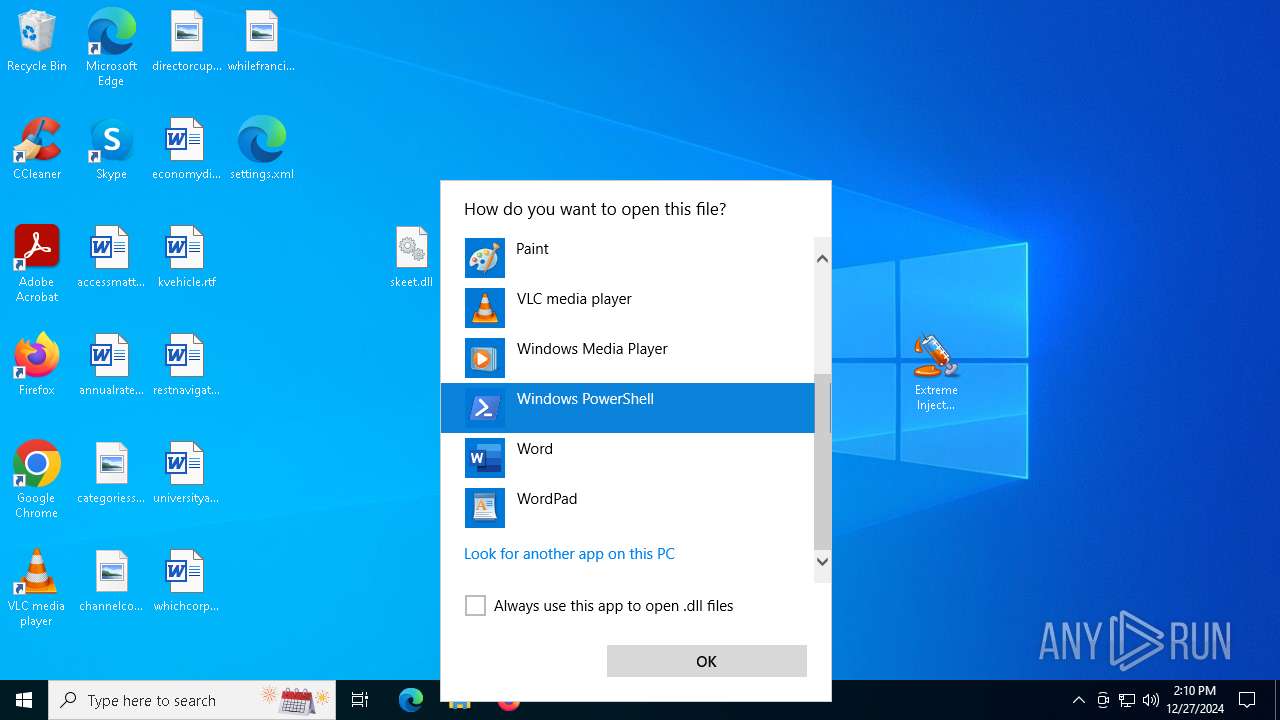
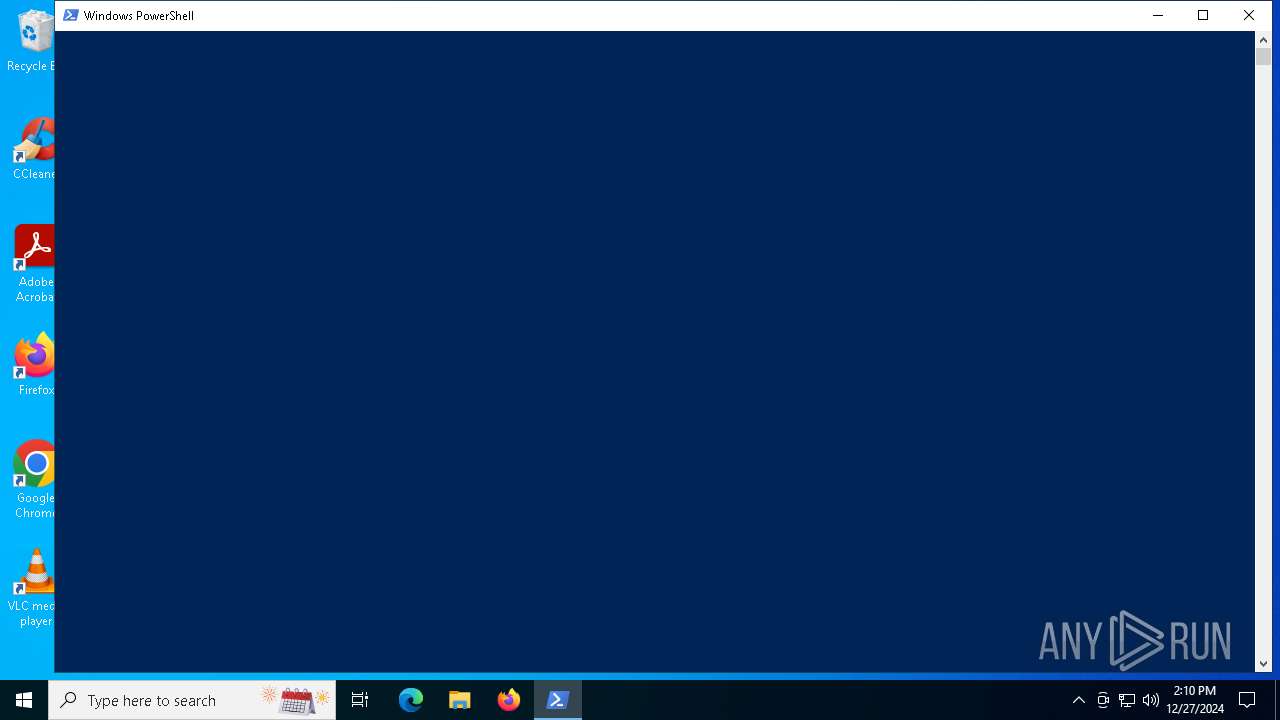
Starts POWERSHELL.EXE for commands execution
- OpenWith.exe (PID: 5604)
INFO
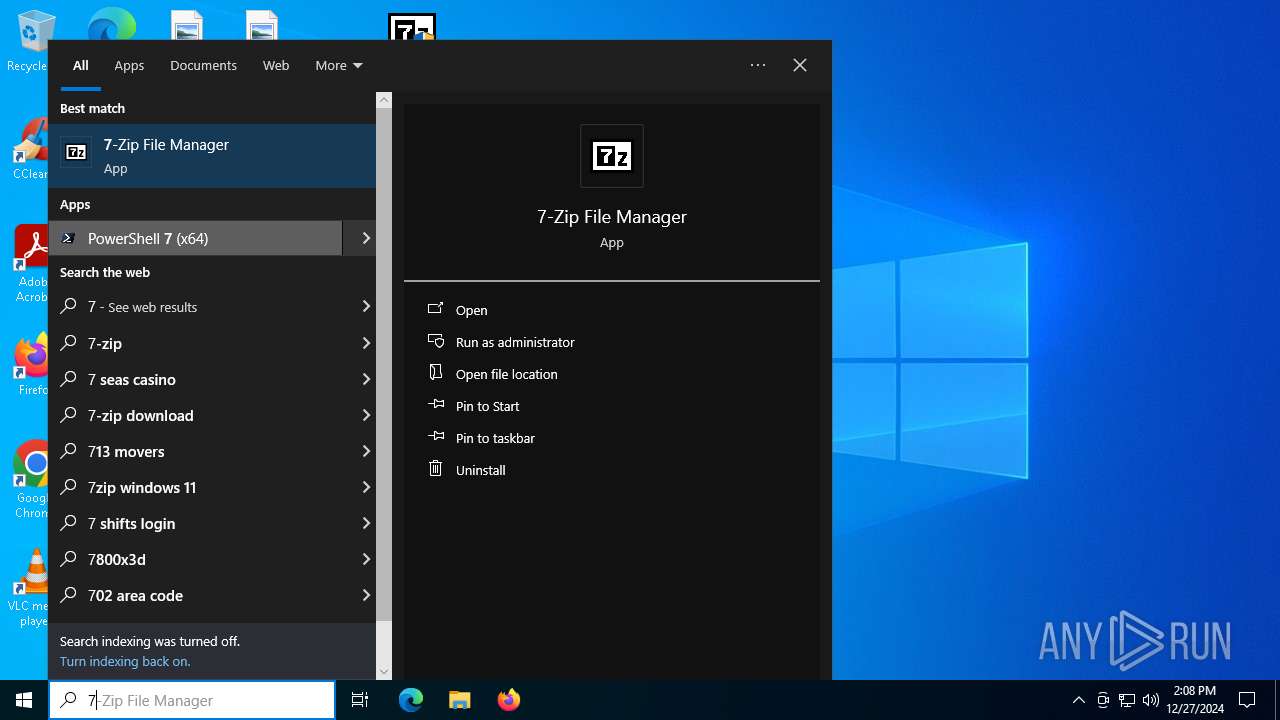
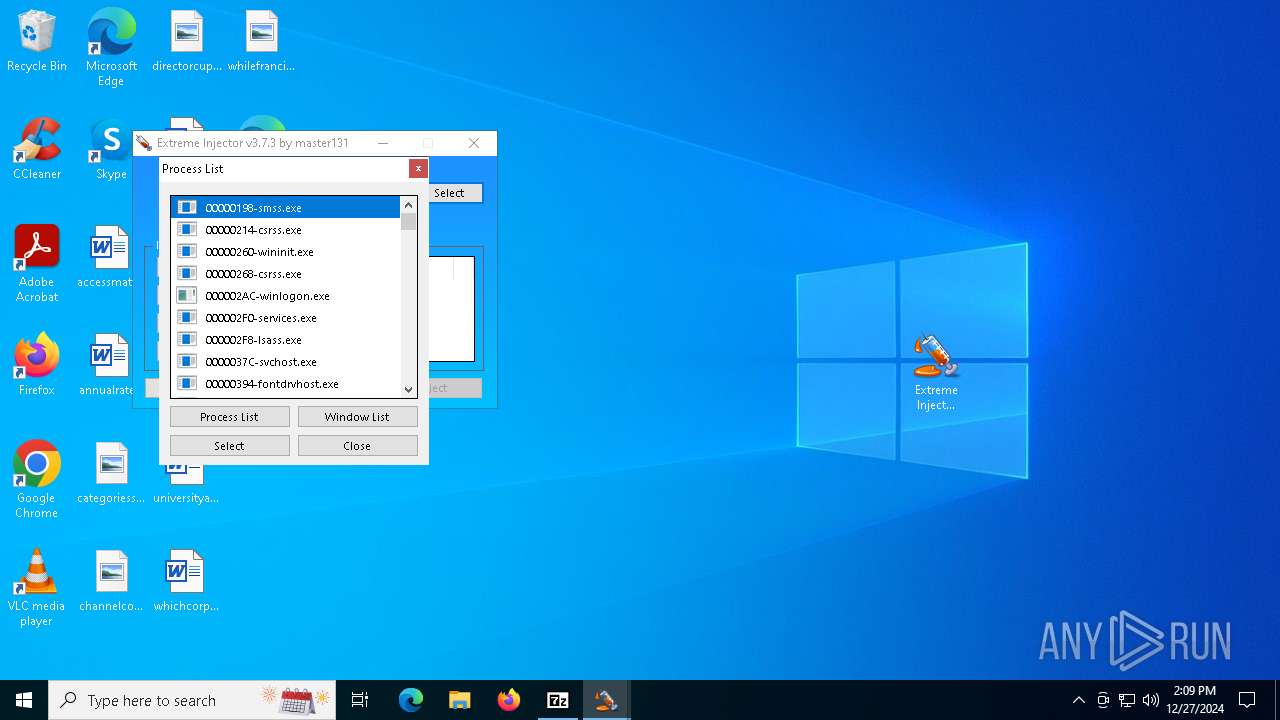
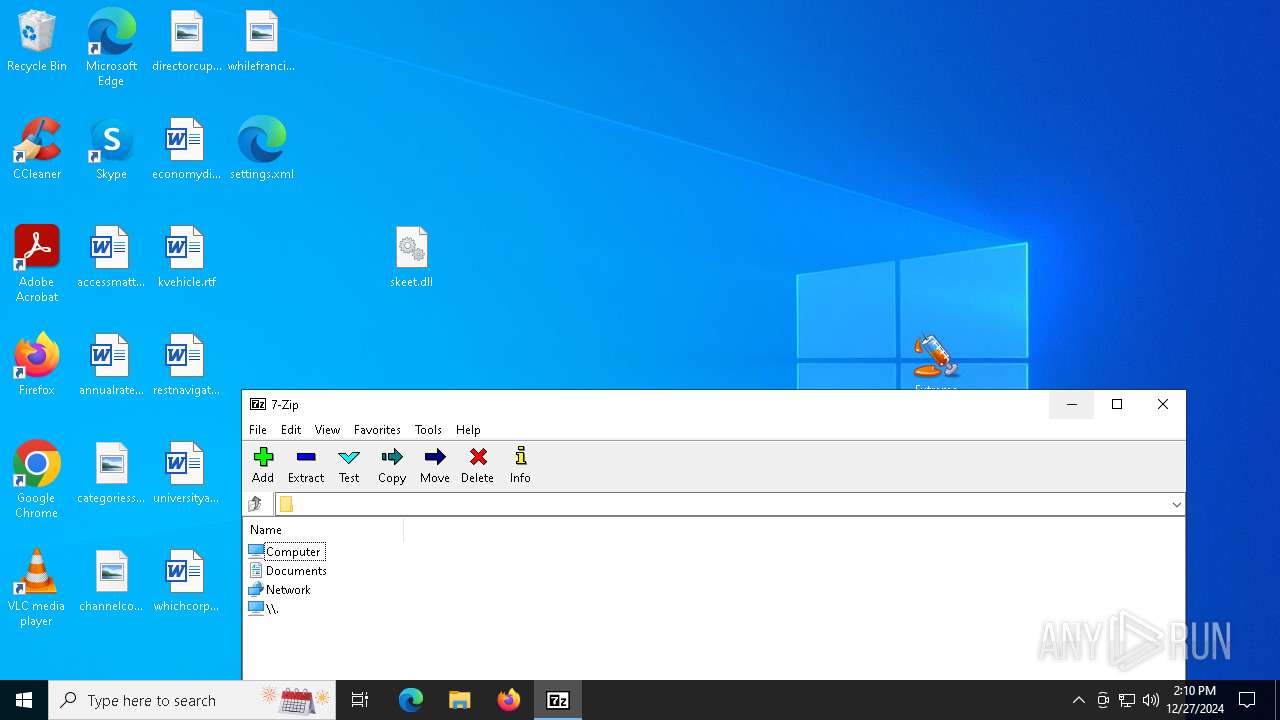
Manual execution by a user
- 7z2409.exe (PID: 4604)
- 7z2409.exe (PID: 4764)
- 7zFM.exe (PID: 6260)
- WinRAR.exe (PID: 6516)
- WinRAR.exe (PID: 6292)
- Extreme Injector v3.exe (PID: 5092)
- 7zFM.exe (PID: 1828)
- Extreme Injector v3.exe (PID: 6284)
The sample compiled with english language support
- 7z2409.exe (PID: 4764)
- WinRAR.exe (PID: 6560)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6560)
- WinRAR.exe (PID: 6516)
Creates files in the program directory
- 7z2409.exe (PID: 4764)
Reads the computer name
- 7z2409.exe (PID: 4764)
- 7zFM.exe (PID: 6260)
- Extreme Injector v3.exe (PID: 4400)
- Extreme Injector v3.exe (PID: 6272)
The process uses the downloaded file
- WinRAR.exe (PID: 6560)
- WinRAR.exe (PID: 6292)
- WinRAR.exe (PID: 6516)
- OpenWith.exe (PID: 5604)
- Extreme Injector v3.exe (PID: 6284)
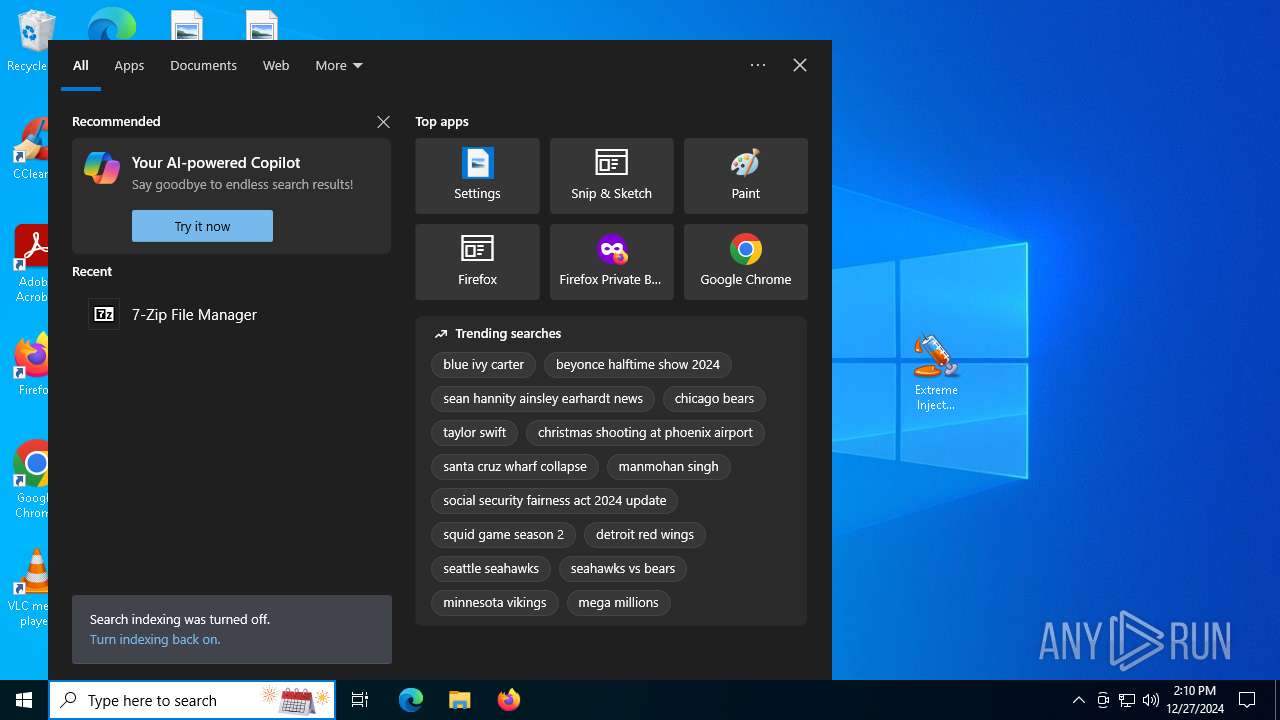
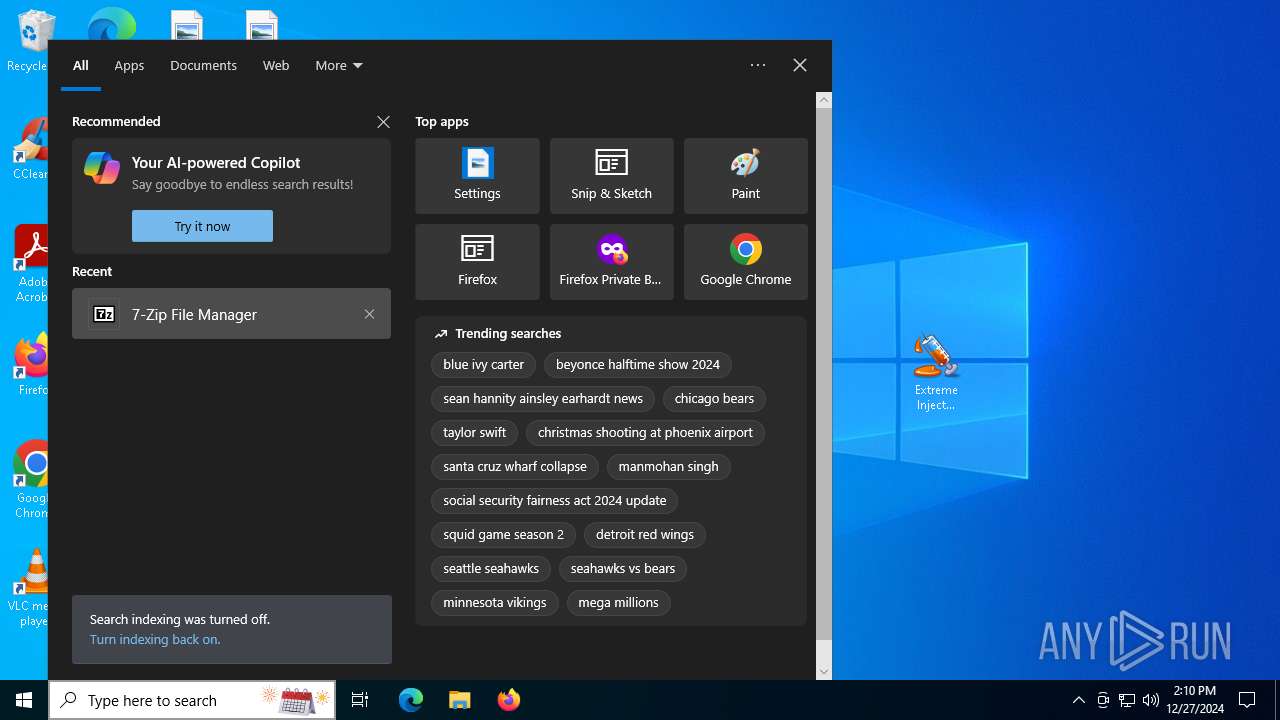
Checks supported languages
- SearchApp.exe (PID: 5064)
- 7zFM.exe (PID: 6260)
- Extreme Injector v3.exe (PID: 5092)
- 7zFM.exe (PID: 1828)
- Extreme Injector v3.exe (PID: 6284)
- Extreme Injector v3.exe (PID: 4400)
- Extreme Injector v3.exe (PID: 6272)
Reads the machine GUID from the registry
- SearchApp.exe (PID: 5064)
- Extreme Injector v3.exe (PID: 4400)
- Extreme Injector v3.exe (PID: 6272)
Reads the software policy settings
- SearchApp.exe (PID: 5064)
- Extreme Injector v3.exe (PID: 4400)
Process checks computer location settings
- Extreme Injector v3.exe (PID: 5092)
- SearchApp.exe (PID: 5064)
- Extreme Injector v3.exe (PID: 6284)
Creates files or folders in the user directory
- WerFault.exe (PID: 5496)
Checks proxy server information
- WerFault.exe (PID: 5496)
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 5604)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6268)
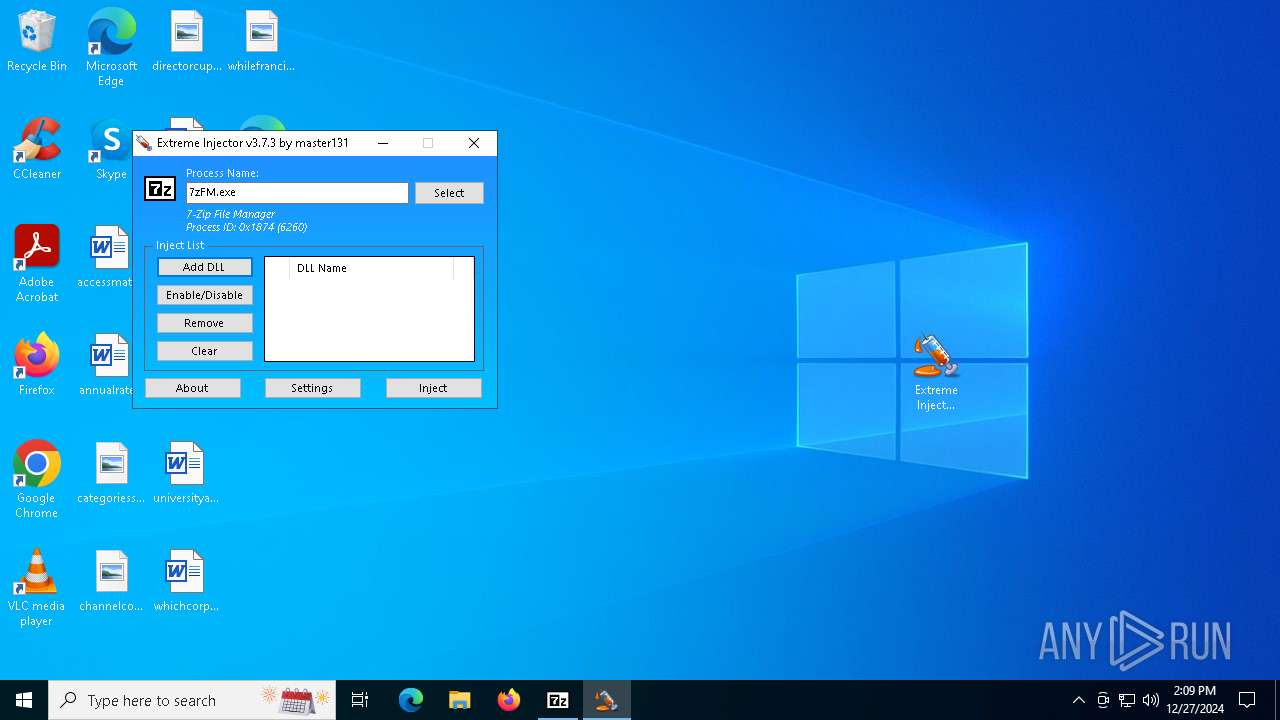
Disables trace logs
- Extreme Injector v3.exe (PID: 4400)
Reads Environment values
- Extreme Injector v3.exe (PID: 4400)
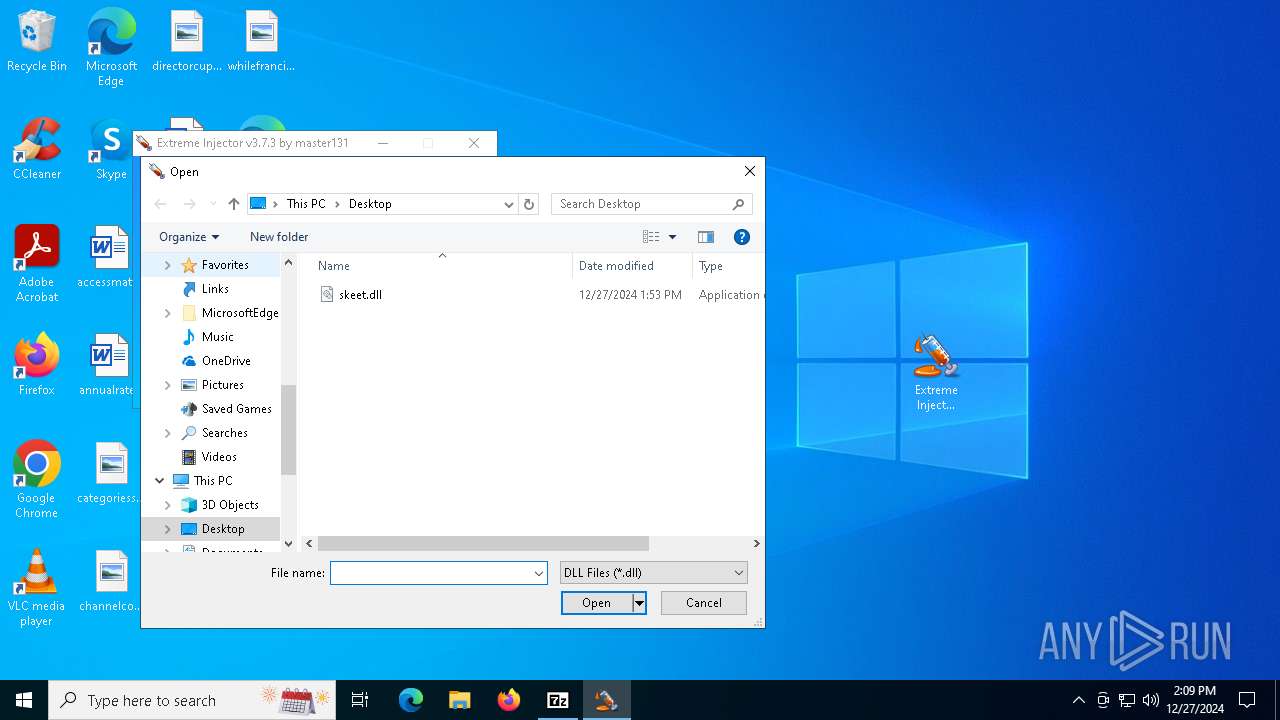
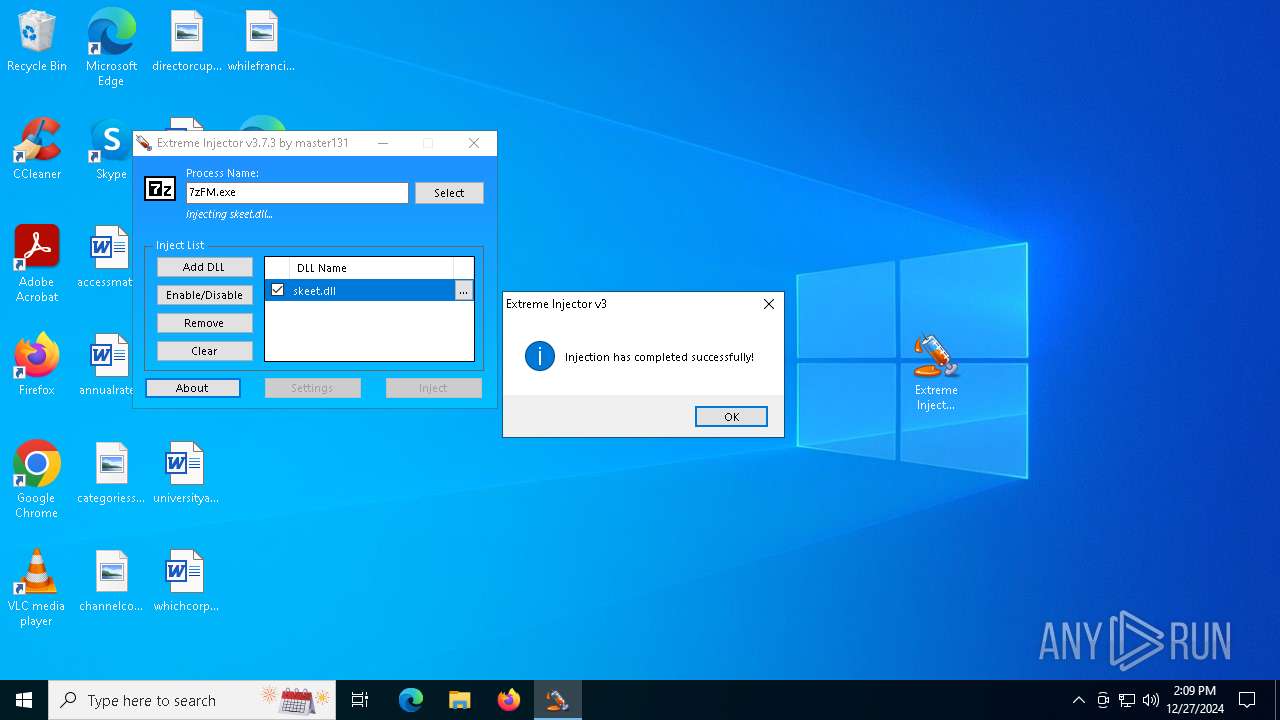
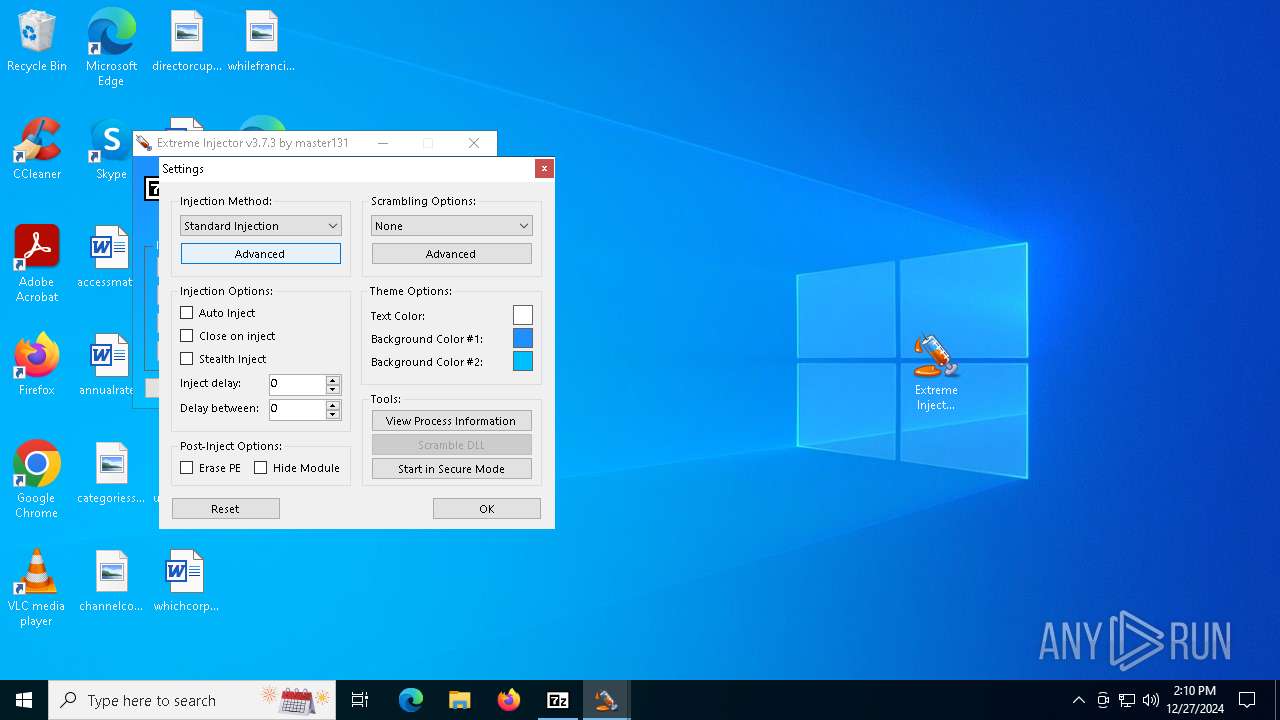
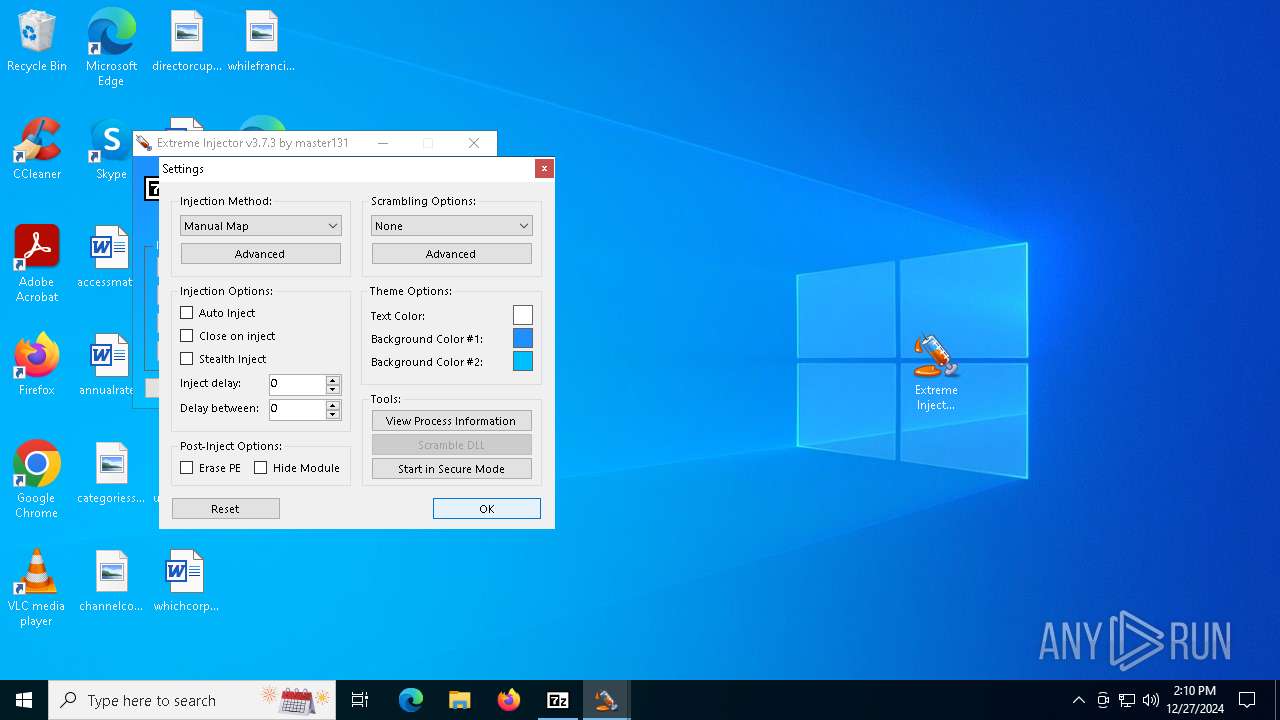
Potential library load (Base64 Encoded 'LoadLibrary')
- Extreme Injector v3.exe (PID: 4400)
Potential access to remote process (Base64 Encoded 'OpenProcess')
- Extreme Injector v3.exe (PID: 4400)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 5604)
Create files in a temporary directory
- Extreme Injector v3.exe (PID: 6272)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0008 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:12:27 06:01:44 |
| ZipCRC: | 0xd1475d8f |
| ZipCompressedSize: | 4855377 |
| ZipUncompressedSize: | 4955258 |
| ZipFileName: | Extreme.Injector.v3.7.3.-.by.master131.zip |
Total processes
157
Monitored processes
19
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1828 | "C:\Program Files (x86)\7-Zip\7zFM.exe" | C:\Program Files (x86)\7-Zip\7zFM.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip File Manager Version: 24.09 Modules
| |||||||||||||||
| 2548 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | 7zFM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3032 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4400 | "C:\Users\admin\Desktop\Extreme Injector v3.exe" | C:\Users\admin\Desktop\Extreme Injector v3.exe | Extreme Injector v3.exe | ||||||||||||
User: admin Company: master131 Integrity Level: HIGH Description: Extreme Injector Exit code: 0 Version: 3.7.3.0 Modules
| |||||||||||||||
| 4604 | "C:\Users\admin\Desktop\7z2409.exe" | C:\Users\admin\Desktop\7z2409.exe | — | explorer.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Installer Exit code: 3221226540 Version: 24.09 Modules
| |||||||||||||||
| 4764 | "C:\Users\admin\Desktop\7z2409.exe" | C:\Users\admin\Desktop\7z2409.exe | explorer.exe | ||||||||||||
User: admin Company: Igor Pavlov Integrity Level: HIGH Description: 7-Zip Installer Exit code: 0 Version: 24.09 Modules
| |||||||||||||||
| 5064 | "C:\WINDOWS\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe" -ServerName:CortanaUI.AppX8z9r6jm96hw4bsbneegw0kyxx296wr9t.mca | C:\Windows\SystemApps\Microsoft.Windows.Search_cw5n1h2txyewy\SearchApp.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Search application Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5092 | "C:\Users\admin\Desktop\Extreme Injector v3.exe" | C:\Users\admin\Desktop\Extreme Injector v3.exe | — | explorer.exe | |||||||||||
User: admin Company: master131 Integrity Level: MEDIUM Description: Extreme Injector Exit code: 0 Version: 3.7.3.0 Modules
| |||||||||||||||
| 5496 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 6260 -s 1204 | C:\Windows\SysWOW64\WerFault.exe | 7zFM.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5604 | C:\WINDOWS\system32\OpenWith.exe -Embedding | C:\Windows\System32\OpenWith.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Pick an app Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
32 023
Read events
31 773
Write events
244
Delete events
6
Modification events
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.search_cw5n1h2txyewy\Internet Explorer\DOMStorage\bing.com |
| Operation: | write | Name: | Total |
Value: 50667 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\ConstraintIndex |
| Operation: | write | Name: | CurrentConstraintIndexCabPath |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C005000610063006B0061006700650073005C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E005300650061007200630068005F006300770035006E003100680032007400780079006500770079005C004C006F00630061006C00530074006100740065005C0043006F006E00730074007200610069006E00740049006E006400650078005C0049006E007000750074005F007B00380033003200620036003800640032002D0037006600650032002D0034006500370031002D0061003300610064002D003200360031003600360062003600350036006500630036007D000000BF3F7EC16858DB01 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\AppsConstraintIndex |
| Operation: | write | Name: | LatestConstraintIndexFolder |
Value: 43003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C004C006F00630061006C005C005000610063006B0061006700650073005C004D006900630072006F0073006F00660074002E00570069006E0064006F00770073002E005300650061007200630068005F006300770035006E003100680032007400780079006500770079005C004C006F00630061006C00530074006100740065005C0043006F006E00730074007200610069006E00740049006E006400650078005C0041007000700073005F007B00360064003600310063006400660063002D0036003500300062002D0034006200310031002D0061006600370063002D006100660031003200620038006200300039006600650036007D000000BF3F7EC16858DB01 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\AppsConstraintIndex |
| Operation: | write | Name: | LastConstraintIndexBuildCompleted |
Value: 18FE7EC16858DB01BF3F7EC16858DB01 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | CurrentConstraintIndexCabPath |
Value: C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Input_{832b68d2-7fe2-4e71-a3ad-26166b656ec6} | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | LatestConstraintIndexFolder |
Value: C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Apps_{6d61cdfc-650b-4b11-af7c-af12b8b09fe6} | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\SearchSettings |
| Operation: | write | Name: | SafeSearchMode |
Value: 1 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Search\Microsoft.Windows.Search_cw5n1h2txyewy\AppsConstraintIndex |
| Operation: | write | Name: | IndexedLanguage |
Value: en-US | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\AppIndexer |
| Operation: | write | Name: | LatestCacheFileName |
Value: 410070007000430061006300680065003100330033003700390037003800320030003800330030003500350031003500340039002E007400780074000000BF3F7EC16858DB01 | |||
| (PID) Process: | (5064) SearchApp.exe | Key: | \REGISTRY\A\{ee080948-b2ea-145a-6870-f9164b908eb9}\LocalState\AppIndexer |
| Operation: | write | Name: | InstalledWin32AppsRevision |
Value: 7B00450032003000380036003700350034002D0043003400310046002D0034003800450038002D0041003200340044002D004200370043003000320044003900370039004100450031007D000000BF3F7EC16858DB01 | |||
Executable files
14
Suspicious files
75
Text files
312
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Apps_{6d61cdfc-650b-4b11-af7c-af12b8b09fe6}\Apps.ft | binary | |
MD5:AB5CF5D309581951ACE7978FF8DF0FF0 | SHA256:CA45CAA7DE38CB805EC43EDC8B9332E1E95124A27FBB6E5BD3DDD5E8A526AFC7 | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Apps_{6d61cdfc-650b-4b11-af7c-af12b8b09fe6}\0.2.filtertrie.intermediate.txt | text | |
MD5:C204E9FAAF8565AD333828BEFF2D786E | SHA256:D65B6A3BF11A27A1CED1F7E98082246E40CF01289FD47FE4A5ED46C221F2F73F | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\LocalState\ConstraintIndex\Apps_{6d61cdfc-650b-4b11-af7c-af12b8b09fe6}\0.1.filtertrie.intermediate.txt | text | |
MD5:34BD1DFB9F72CF4F86E6DF6DA0A9E49A | SHA256:8E1E6A3D56796A245D0C7B0849548932FEE803BBDB03F6E289495830E017F14C | |||
| 4764 | 7z2409.exe | C:\Program Files (x86)\7-Zip\Lang\an.txt | text | |
MD5:F16218139E027338A16C3199091D0600 | SHA256:3AB9F7AACD38C4CDE814F86BC37EEC2B9DF8D0DDDB95FC1D09A5F5BCB11F0EEB | |||
| 4764 | 7z2409.exe | C:\Program Files (x86)\7-Zip\Lang\af.txt | text | |
MD5:DF216FAE5B13D3C3AFE87E405FD34B97 | SHA256:9CF684EA88EA5A479F510750E4089AEE60BBB2452AA85285312BAFCC02C10A34 | |||
| 4764 | 7z2409.exe | C:\Program Files (x86)\7-Zip\7-zip.chm | binary | |
MD5:A7BA50E8A23BF4A17F827C69BDB8F6AB | SHA256:94561A6DD2E91B42D566846270B9D8915C30DD9200E7AAB3A4E37547C0042491 | |||
| 4764 | 7z2409.exe | C:\Program Files (x86)\7-Zip\Lang\ba.txt | text | |
MD5:387FF78CF5F524FC44640F3025746145 | SHA256:8A85C3FCB5F81157490971EE4F5E6B9E4F80BE69A802EBED04E6724CE859713F | |||
| 4764 | 7z2409.exe | C:\Program Files (x86)\7-Zip\Lang\bg.txt | text | |
MD5:2D0C8197D84A083EF904F8F5608AFE46 | SHA256:62C6F410D011A109ABECB79CAA24D8AEB98B0046D329D611A4D07E66460EEF3F | |||
| 5064 | SearchApp.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.Search_cw5n1h2txyewy\AC\Microsoft\Internet Explorer\DOMStore\ZWUI0EBX\www.bing[1].xml | text | |
MD5:1E69623DF896BCAE55A831FAA429436D | SHA256:60D266D9AC5D8D4483A919C776E060ED067D1E5390DAD47A049E82A008267CFF | |||
| 6560 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa6560.32919\7z2409.exe | executable | |
MD5:00CBEF9691EFAD7A56332FBCF51AA762 | SHA256:E35E4374100B52E697E002859AEFDD5533BCBF4118E5D2210FAE6DE318947C41 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
52
DNS requests
34
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.177:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 1.01 Kb | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
6360 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
6504 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 418 b | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | US | binary | 471 b | whitelisted |
6504 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
5496 | WerFault.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 973 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.48.23.177:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 184.86.251.20:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1176 | svchost.exe | 40.126.32.74:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1076 | svchost.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |