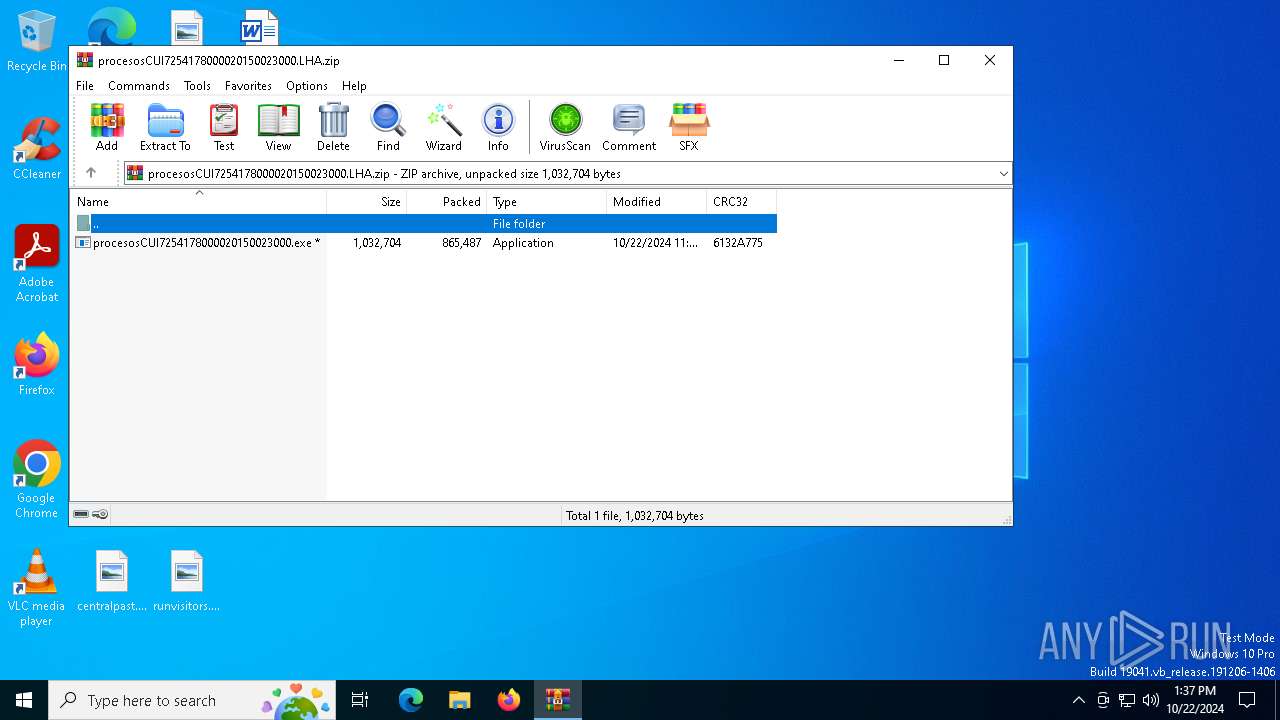
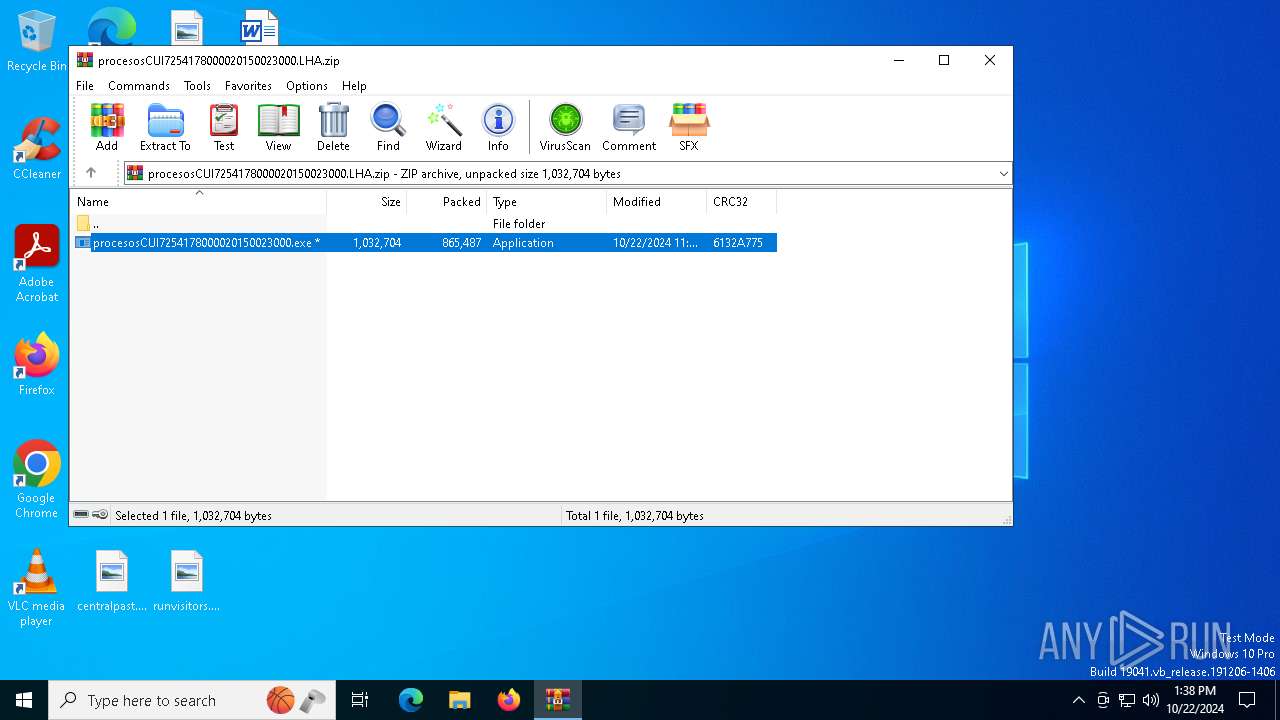
| File name: | procesosCUI7254178000020150023000.LHA |
| Full analysis: | https://app.any.run/tasks/240d52c4-2937-4031-ab7b-8fe4a14636a1 |
| Verdict: | Malicious activity |
| Analysis date: | October 22, 2024, 13:37:43 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
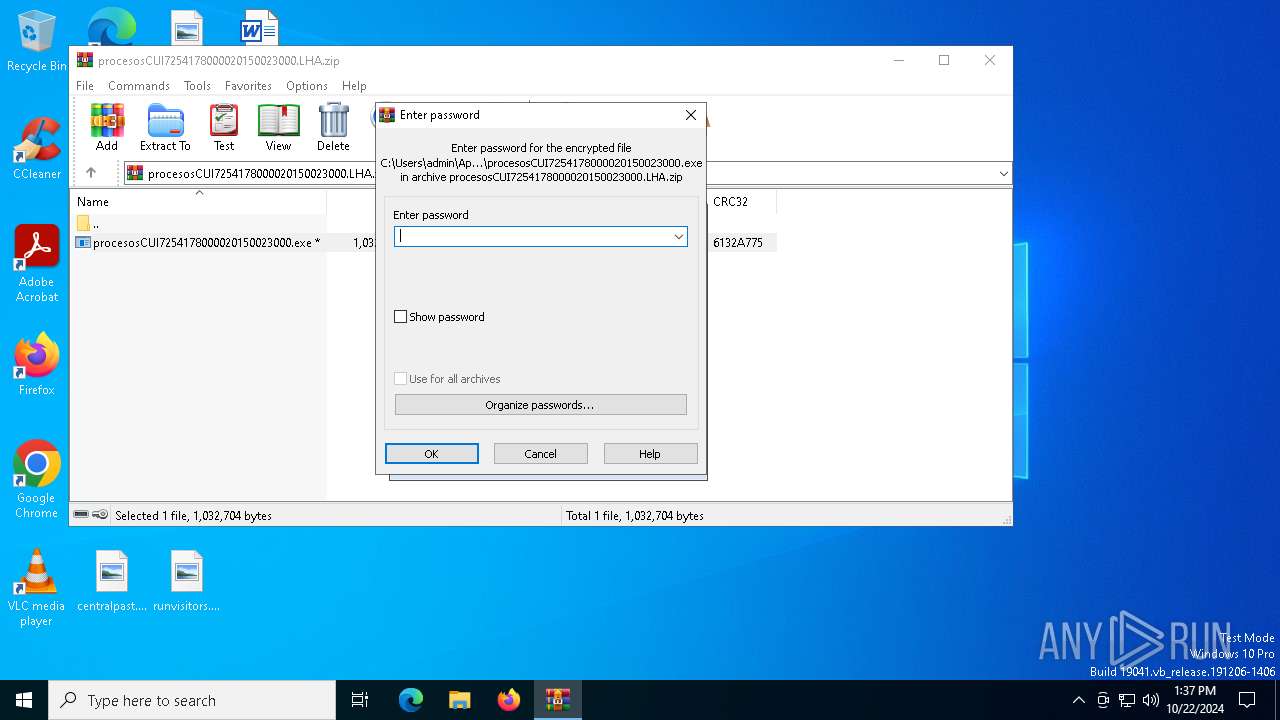
| File info: | Zip archive data, at least v2.0 to extract, compression method=AES Encrypted |
| MD5: | 995F6C6477D2B7D2AF848F4CFE95DDE6 |
| SHA1: | 67A72AD0262A06D00BBFCF0B56715EC9EF0E01FF |
| SHA256: | 6F08AAF3EBFB5B2AC552BB9811FDC7158D48C6C385C30F67D713728AA09063E4 |
| SSDEEP: | 24576:nJjJO26LGLZ3ojx+sQtciE0IuhcM34Xhel0+l97FhmesvswXhSWGRAHjm9JowlzN:JjJO2yGN3ojx+sQu70IuhcM34Xhel0+5 |
MALICIOUS
Uses Task Scheduler to run other applications
- procesosCUI7254178000020150023000.exe (PID: 6960)
- Vespre.exe (PID: 6992)
Connects to the CnC server
- Vespre.exe (PID: 6992)
SUSPICIOUS
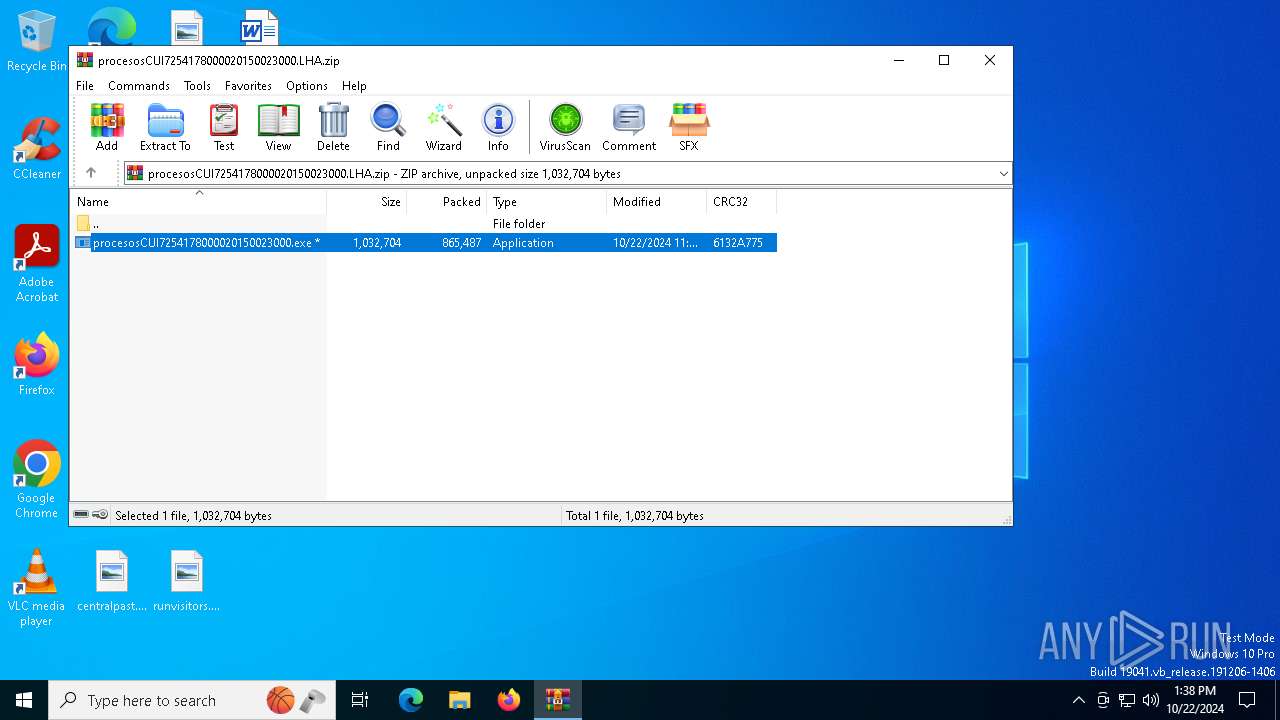
Executable content was dropped or overwritten
- procesosCUI7254178000020150023000.exe (PID: 6960)
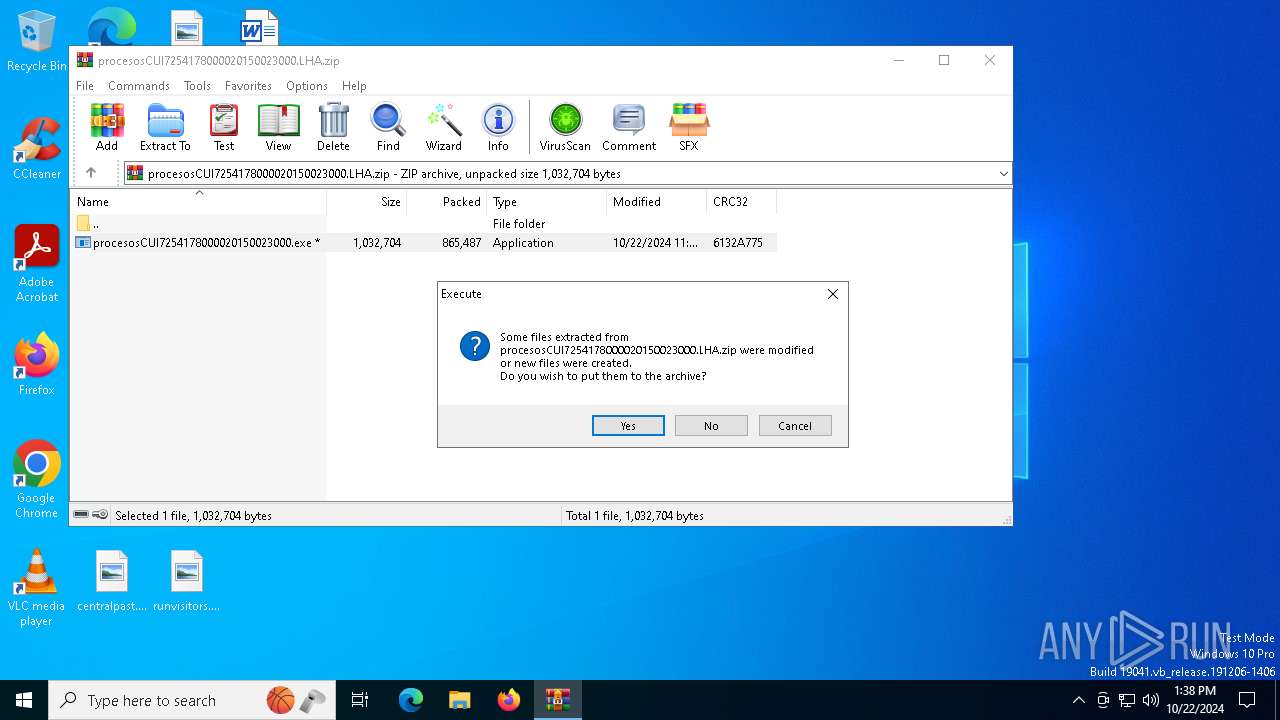
Application launched itself
- procesosCUI7254178000020150023000.exe (PID: 5160)
- Vespre.exe (PID: 2428)
Checks for external IP
- procesosCUI7254178000020150023000.exe (PID: 6960)
- svchost.exe (PID: 2172)
- Vespre.exe (PID: 6992)
Starts itself from another location
- procesosCUI7254178000020150023000.exe (PID: 6960)
Contacting a server suspected of hosting an CnC
- Vespre.exe (PID: 6992)
Connects to unusual port
- Vespre.exe (PID: 6992)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 6904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2024:10:22 06:46:36 |
| ZipCRC: | 0x6132a775 |
| ZipCompressedSize: | 865487 |
| ZipUncompressedSize: | 1032704 |
| ZipFileName: | procesosCUI7254178000020150023000.exe |
Total processes
135
Monitored processes
12
Malicious processes
2
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1452 | "C:\Users\admin\AppData\Roaming\GPret\Vespre.exe" | C:\Users\admin\AppData\Roaming\GPret\Vespre.exe | — | Vespre.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Version: 0.1.0.0 Modules
| |||||||||||||||
| 1572 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1700 | "C:\Users\admin\AppData\Roaming\GPret\Vespre.exe" | C:\Users\admin\AppData\Roaming\GPret\Vespre.exe | — | Vespre.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Version: 0.1.0.0 Modules
| |||||||||||||||
| 2172 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2428 | "C:\Users\admin\AppData\Roaming\GPret\Vespre.exe" | C:\Users\admin\AppData\Roaming\GPret\Vespre.exe | — | procesosCUI7254178000020150023000.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 0.1.0.0 Modules
| |||||||||||||||
| 4088 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | schtasks.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5160 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb6904.8671\procesosCUI7254178000020150023000.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb6904.8671\procesosCUI7254178000020150023000.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Version: 0.1.0.0 Modules
| |||||||||||||||
| 5976 | "schtasks" /create /tn "iceTelemetryLogtte" /SC MINUTE /MO 3 /tr "C:\Users\admin\AppData\Roaming\GPret\Vespre.exe" /f | C:\Windows\SysWOW64\schtasks.exe | — | Vespre.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6408 | "schtasks" /create /tn "iceTelemetryLogtte" /SC MINUTE /MO 3 /tr "C:\Users\admin\AppData\Local\Temp\Rar$EXb6904.8671\procesosCUI7254178000020150023000.exe" /f | C:\Windows\SysWOW64\schtasks.exe | — | procesosCUI7254178000020150023000.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6904 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\procesosCUI7254178000020150023000.LHA.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
8 106
Read events
8 069
Write events
37
Delete events
0
Modification events
| (PID) Process: | (6904) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\GoogleChromeEnterpriseBundle64.zip | |||
| (PID) Process: | (6904) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\procesosCUI7254178000020150023000.LHA.zip | |||
| (PID) Process: | (6904) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6904) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6904) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6904) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6904) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (6960) procesosCUI7254178000020150023000.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\procesosCUI7254178000020150023000_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (6960) procesosCUI7254178000020150023000.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\procesosCUI7254178000020150023000_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (6960) procesosCUI7254178000020150023000.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\procesosCUI7254178000020150023000_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
2
Suspicious files
1
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6960 | procesosCUI7254178000020150023000.exe | C:\Users\admin\AppData\Roaming\GPret\Vespre.exe | executable | |
MD5:FAD059261BF13A267732A9742A0D5B0C | SHA256:C337C576127FE086E6EE397CBA4382EAE7102DE3BC63EC9514A5A21B95857CFC | |||
| 6904 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6904.8671\procesosCUI7254178000020150023000.exe | executable | |
MD5:FAD059261BF13A267732A9742A0D5B0C | SHA256:C337C576127FE086E6EE397CBA4382EAE7102DE3BC63EC9514A5A21B95857CFC | |||
| 6960 | procesosCUI7254178000020150023000.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXb6904.8671\settings.xml | text | |
MD5:0670EA91A3FF99E765DE101BACC1CE56 | SHA256:7DC01C0F1C1D2AA56555D951562EBC455718D3CA7C8E25BD59D42AD5B46B2F2B | |||
| 6992 | Vespre.exe | C:\Users\admin\AppData\Roaming\GPrets\10-22-2024 | binary | |
MD5:90460169F71391D64AC447AD145FA792 | SHA256:2B1E86607271F474901C9C56575058BCF1981A7DC8734BD765F147118DA2FA40 | |||
| 6992 | Vespre.exe | C:\Users\admin\AppData\Roaming\GPret\settings.xml | text | |
MD5:0670EA91A3FF99E765DE101BACC1CE56 | SHA256:7DC01C0F1C1D2AA56555D951562EBC455718D3CA7C8E25BD59D42AD5B46B2F2B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
60
DNS requests
20
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5488 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7028 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6200 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6200 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6992 | Vespre.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | shared |
6960 | procesosCUI7254178000020150023000.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/json/ | unknown | — | — | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 2.16.164.114:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
5488 | MoUsoCoreWorker.exe | 2.16.164.114:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 2.23.209.153:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
5488 | MoUsoCoreWorker.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
6944 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4020 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2172 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Online Pastebin Text Storage |
6960 | procesosCUI7254178000020150023000.exe | A Network Trojan was detected | ET MALWARE Common RAT Connectivity Check Observed |
2172 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
6960 | procesosCUI7254178000020150023000.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2172 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
6992 | Vespre.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
2172 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to DynDNS Domain (linkpc .net) |
6992 | Vespre.exe | A Network Trojan was detected | ET MALWARE Common RAT Connectivity Check Observed |
6992 | Vespre.exe | Malware Command and Control Activity Detected | ET MALWARE VenomRAT CnC Server Keepalive |