| File name: | hamachi.msi |
| Full analysis: | https://app.any.run/tasks/953f888d-0f00-4e12-bee8-9f58ba052863 |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 23:55:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
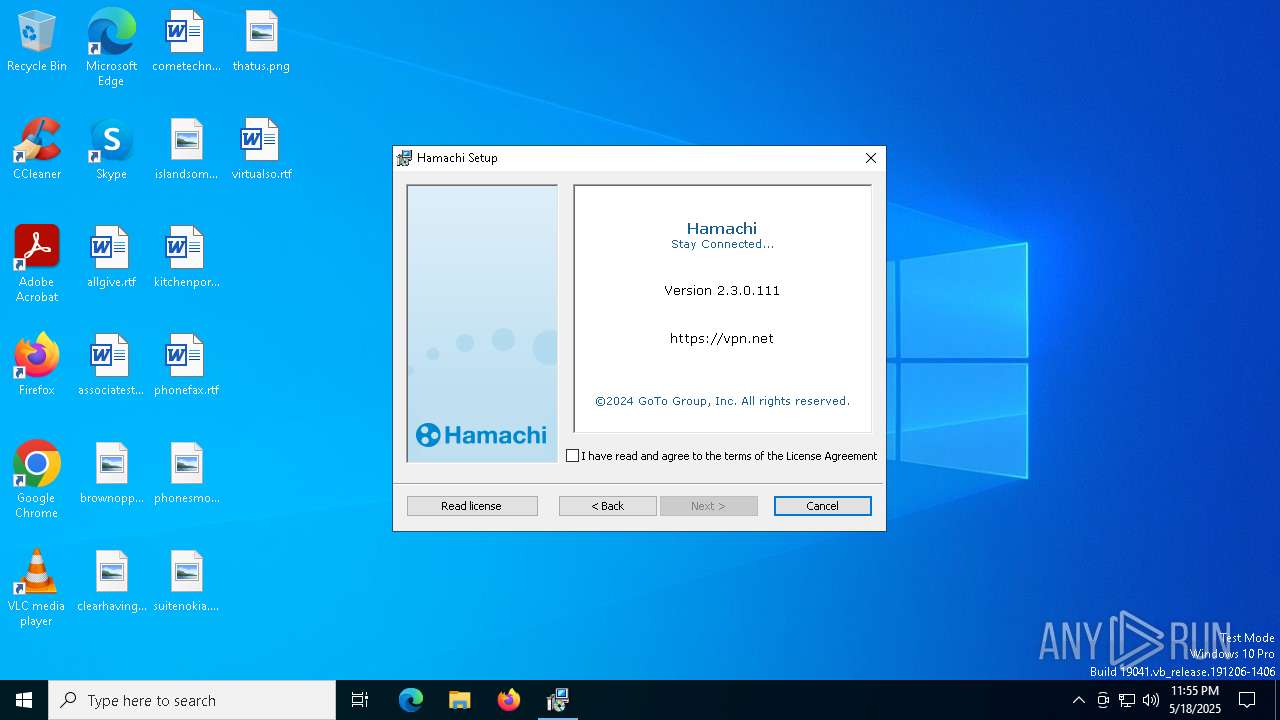
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Hamachi Installer, Author: LogMeIn, Inc., Keywords: Installer, Comments: This installer database contains the logic and data required to install Hamachi., Template: ;1033, Number of Pages: 200, Number of Words: 2, Security: 2, Revision Number: {C15EA8DB-41DF-4C48-8704-7D4FAB7D9EBB}, Create Time/Date: Mon Mar 25 12:38:25 2024, Last Saved Time/Date: Mon Mar 25 12:38:25 2024, Name of Creating Application: Windows Installer XML v2.0.5805.0 (candle/light) |
| MD5: | 909DB4061C32F798E94D746717782444 |
| SHA1: | 10F5FFFF17D2DD4476686A941A7BCC5F9B83B1B8 |
| SHA256: | 6EE98DB32852A2FF31A969D918BB7C730950BB15F24EA1BAF996697CEBC8B9FA |
| SSDEEP: | 98304:KUUWX6HsM1siJtvl9XBoK0hiUB8ootGdjSwwIbZOH8DrWZi7ykNKM+8I9yGg5e+C:4opYFffMzvMaXURWgyBBsuG3 |
MALICIOUS
Executing a file with an untrusted certificate
- LMIGuardianSvc.exe (PID: 7408)
- LMIGuardianSvc.exe (PID: 4696)
- LMIGuardianSvc.exe (PID: 5380)
- LMIGuardianSvc.exe (PID: 8156)
- LMIGuardianSvc.exe (PID: 8008)
- LMIGuardianSvc.exe (PID: 7572)
- LMIGuardianSvc.exe (PID: 2064)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 7688)
- LMIGuardianSvc.exe (PID: 4696)
- hamachi-2.exe (PID: 5588)
- hamachi-2.exe (PID: 4892)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 4812)
- hamachi-2.exe (PID: 1852)
- drvinst.exe (PID: 7476)
Executable content was dropped or overwritten
- hamachi-2.exe (PID: 1852)
- drvinst.exe (PID: 7476)
- drvinst.exe (PID: 7020)
Windows service management via SC.EXE
- sc.exe (PID: 7272)
- sc.exe (PID: 2344)
Suspicious use of NETSH.EXE
- hamachi-2.exe (PID: 4892)
- hamachi-2.exe (PID: 1852)
INFO
Checks proxy server information
- msiexec.exe (PID: 1760)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 1760)
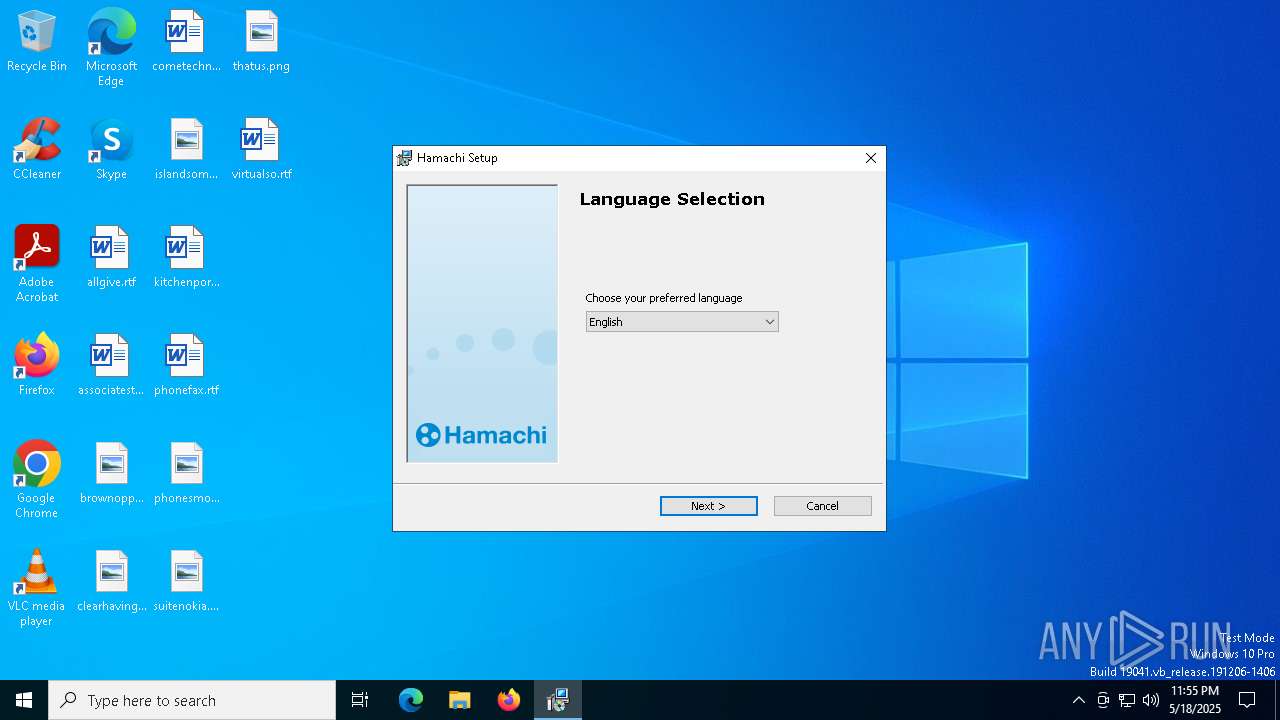
The sample compiled with english language support
- msiexec.exe (PID: 1760)
- msiexec.exe (PID: 4812)
Creates files or folders in the user directory
- msiexec.exe (PID: 1760)
Checks supported languages
- msiexec.exe (PID: 7200)
- msiexec.exe (PID: 4812)
Reads the computer name
- msiexec.exe (PID: 4812)
- msiexec.exe (PID: 7200)
Create files in a temporary directory
- msiexec.exe (PID: 7200)
Reads the software policy settings
- msiexec.exe (PID: 1760)
Executable content was dropped or overwritten
- msiexec.exe (PID: 1760)
- msiexec.exe (PID: 4812)
Manages system restore points
- SrTasks.exe (PID: 3100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | Hamachi Installer |
| Author: | LogMeIn, Inc. |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Hamachi. |
| Template: | ;1033 |
| Pages: | 200 |
| Words: | 2 |
| Security: | Read-only recommended |
| RevisionNumber: | {C15EA8DB-41DF-4C48-8704-7D4FAB7D9EBB} |
| CreateDate: | 2024:03:25 12:38:25 |
| ModifyDate: | 2024:03:25 12:38:25 |
| Software: | Windows Installer XML v2.0.5805.0 (candle/light) |
Total processes
173
Monitored processes
41
Malicious processes
4
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 732 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1760 | "C:\Windows\System32\msiexec.exe" /i C:\Users\admin\AppData\Local\Temp\hamachi.msi | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1852 | "C:\Program Files (x86)\LogMeIn Hamachi\x64\hamachi-2.exe" --add-tap-at-install Hamachi | C:\Program Files (x86)\LogMeIn Hamachi\x64\hamachi-2.exe | msiexec.exe | ||||||||||||
User: SYSTEM Company: LogMeIn Inc. Integrity Level: SYSTEM Description: Hamachi Client Tunneling Engine Exit code: 0 Version: 2, 3, 0, 111 Modules
| |||||||||||||||
| 2040 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=NetworkAvailable | C:\Windows\System32\slui.exe | — | SppExtComObj.Exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | "C:\Program Files (x86)\LogMeIn Hamachi\LMIGuardianSvc.exe" /escort 5020 /CUSTOM Hamachi | C:\Program Files (x86)\LogMeIn Hamachi\LMIGuardianSvc.exe | — | hamachi-2-ui.exe | |||||||||||
User: admin Company: LogMeIn, Inc. Integrity Level: MEDIUM Description: LMIGuardianSvc Exit code: 0 Version: 10.1.1742 Modules
| |||||||||||||||
| 2344 | sc config Hamachi2Svc depend= winmgmt | C:\Windows\SysWOW64\sc.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2616 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | hamachi-2.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3100 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3884 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4336 | netsh interface tcp set global rss=enabled | C:\Windows\SysWOW64\netsh.exe | — | hamachi-2.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
21 596
Read events
21 182
Write events
394
Delete events
20
Modification events
| (PID) Process: | (4812) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000683B946050C8DB01CC120000F81D0000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4812) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000683B946050C8DB01CC120000F81D0000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4812) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 48000000000000000EEDF56050C8DB01CC120000F81D0000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4812) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 480000000000000017D27D6150C8DB01CC120000F81D0000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4812) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000E935806150C8DB01CC120000901E0000E803000001000000000000000000000024B88ED7E9EEF94C8CAE36F53160755900000000000000000000000000000000 | |||
| (PID) Process: | (7688) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000BC1F8C6150C8DB01081E0000B01E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7688) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000BC1F8C6150C8DB01081E0000341E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7688) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000BC1F8C6150C8DB01081E0000381E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (7688) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000BC1F8C6150C8DB01081E0000B41E0000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4812) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000AB39F16050C8DB01CC120000F81D0000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
36
Suspicious files
38
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4812 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4812 | msiexec.exe | C:\Windows\Installer\112e31.msi | — | |
MD5:— | SHA256:— | |||
| 1760 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:13DAFCEA7479724B42C50BA3DD9C045E | SHA256:D926B42BDBEA8369FF8678271C709DE5FDDA8991647DAB0D91897EF93C68ADA8 | |||
| 4812 | msiexec.exe | C:\Windows\Installer\MSI377D.tmp | — | |
MD5:— | SHA256:— | |||
| 1760 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8EC9B1D0ABBD7F98B401D425828828CE_325DC716E4289E0AE281439314ED4BFA | binary | |
MD5:E6F5113BB529A75772EAB45FBB2491F7 | SHA256:3AE847675C7C6E470224C5EB21A321307D4765EC923765ADD2B665FCB85EDEB2 | |||
| 1760 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIC332.tmp | executable | |
MD5:3BC82080D6356DAE779EED5135FABF66 | SHA256:B076C9B888B130FB2FB5A74542C9A73322E78ED1F3F8476BE7A8209A20E56F7B | |||
| 1760 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:C7D00759503E0F506C5775FF24789A3B | SHA256:94FC525025F316570F4FF2F43C72D5180D17FD4EA8FC8DBB2B6F06A52378BF91 | |||
| 1760 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSICCCA.tmp | executable | |
MD5:3BC82080D6356DAE779EED5135FABF66 | SHA256:B076C9B888B130FB2FB5A74542C9A73322E78ED1F3F8476BE7A8209A20E56F7B | |||
| 4812 | msiexec.exe | C:\Windows\Installer\MSI35E6.tmp | executable | |
MD5:3BC82080D6356DAE779EED5135FABF66 | SHA256:B076C9B888B130FB2FB5A74542C9A73322E78ED1F3F8476BE7A8209A20E56F7B | |||
| 1760 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_325DC716E4289E0AE281439314ED4BFA | binary | |
MD5:202A2AACAADE78B7137B0E34CEBA7FD6 | SHA256:B8F78E16D807A10D9BD0AEDC54BC20C8A5B3D6DC33F92252C98D4081E017603A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
33
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.6:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1760 | msiexec.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
1760 | msiexec.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
1760 | msiexec.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAjegkJ27mLaGBP72%2FEoqPs%3D | unknown | — | — | whitelisted |
8048 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8048 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.6:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1760 | msiexec.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |