| File name: | hamachi.msi |
| Full analysis: | https://app.any.run/tasks/8984a051-ed80-4688-8c50-29c330a97af7 |
| Verdict: | Malicious activity |
| Analysis date: | June 14, 2025, 07:00:27 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: Hamachi Installer, Author: LogMeIn, Inc., Keywords: Installer, Comments: This installer database contains the logic and data required to install Hamachi., Template: ;1033, Number of Pages: 200, Number of Words: 2, Security: 2, Revision Number: {C15EA8DB-41DF-4C48-8704-7D4FAB7D9EBB}, Create Time/Date: Mon Mar 25 12:38:25 2024, Last Saved Time/Date: Mon Mar 25 12:38:25 2024, Name of Creating Application: Windows Installer XML v2.0.5805.0 (candle/light) |
| MD5: | 909DB4061C32F798E94D746717782444 |
| SHA1: | 10F5FFFF17D2DD4476686A941A7BCC5F9B83B1B8 |
| SHA256: | 6EE98DB32852A2FF31A969D918BB7C730950BB15F24EA1BAF996697CEBC8B9FA |
| SSDEEP: | 98304:KUUWX6HsM1siJtvl9XBoK0hiUB8ootGdjSwwIbZOH8DrWZi7ykNKM+8I9yGg5e+C:4opYFffMzvMaXURWgyBBsuG3 |
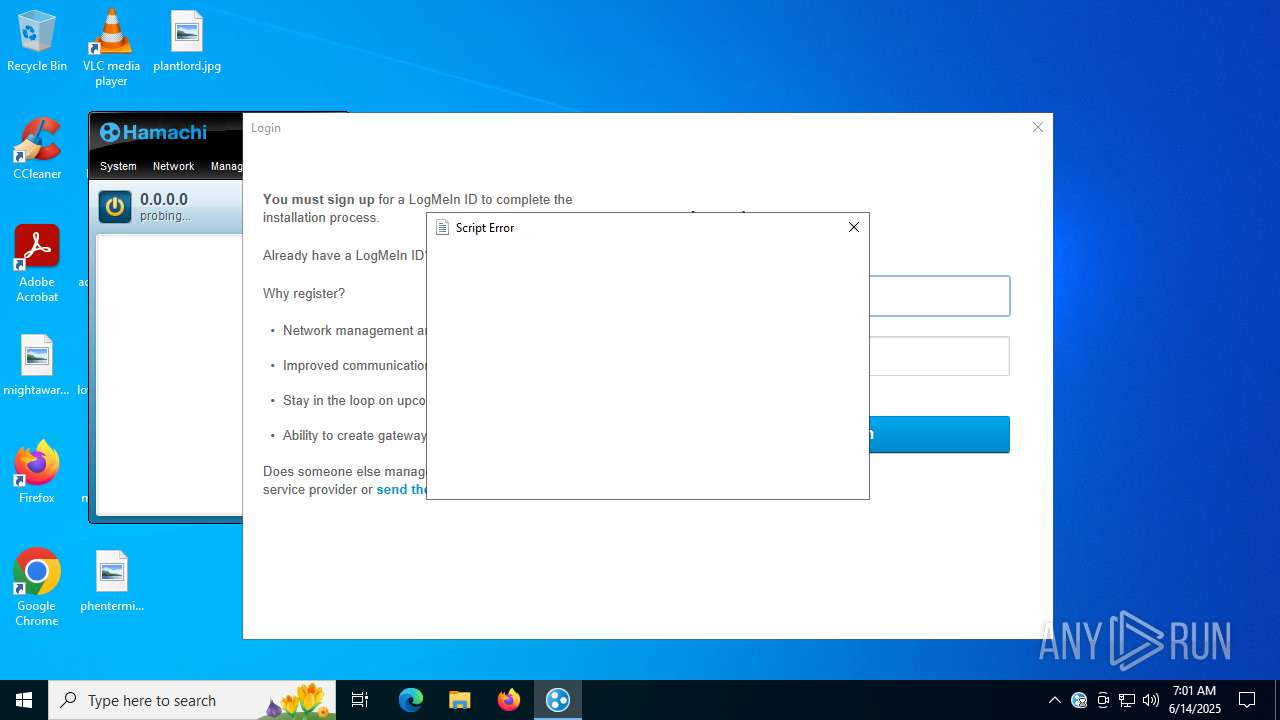
MALICIOUS
Executing a file with an untrusted certificate
- LMIGuardianSvc.exe (PID: 5968)
- LMIGuardianSvc.exe (PID: 6756)
- LMIGuardianSvc.exe (PID: 1932)
- LMIGuardianSvc.exe (PID: 6896)
- LMIGuardianSvc.exe (PID: 6380)
- LMIGuardianSvc.exe (PID: 3788)
- LMIGuardianSvc.exe (PID: 4816)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 7020)
- LMIGuardianSvc.exe (PID: 6896)
- hamachi-2.exe (PID: 1532)
- hamachi-2.exe (PID: 2276)
Drops a system driver (possible attempt to evade defenses)
- hamachi-2.exe (PID: 3608)
- msiexec.exe (PID: 6224)
- drvinst.exe (PID: 1964)
Executable content was dropped or overwritten
- hamachi-2.exe (PID: 3608)
- drvinst.exe (PID: 1964)
- drvinst.exe (PID: 416)
Suspicious use of NETSH.EXE
- hamachi-2.exe (PID: 3608)
- hamachi-2.exe (PID: 2276)
Windows service management via SC.EXE
- sc.exe (PID: 4888)
- sc.exe (PID: 3572)
Connects to unusual port
- hamachi-2.exe (PID: 2276)
INFO
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3752)
Manages system restore points
- SrTasks.exe (PID: 7060)
Executable content was dropped or overwritten
- msiexec.exe (PID: 6224)
- msiexec.exe (PID: 3752)
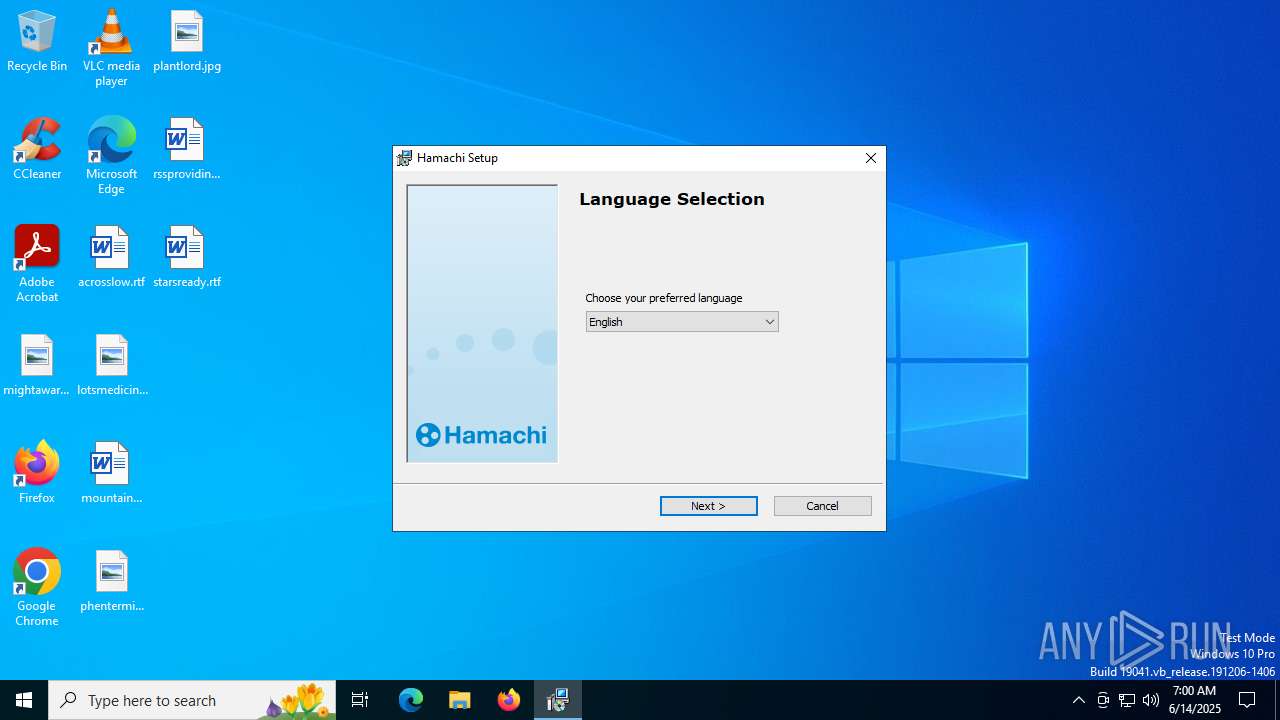
Checks supported languages
- msiexec.exe (PID: 1564)
- msiexec.exe (PID: 6224)
The sample compiled with english language support
- msiexec.exe (PID: 6224)
- msiexec.exe (PID: 3752)
Reads the software policy settings
- msiexec.exe (PID: 3752)
Checks proxy server information
- msiexec.exe (PID: 3752)
Reads the computer name
- msiexec.exe (PID: 6224)
- msiexec.exe (PID: 1564)
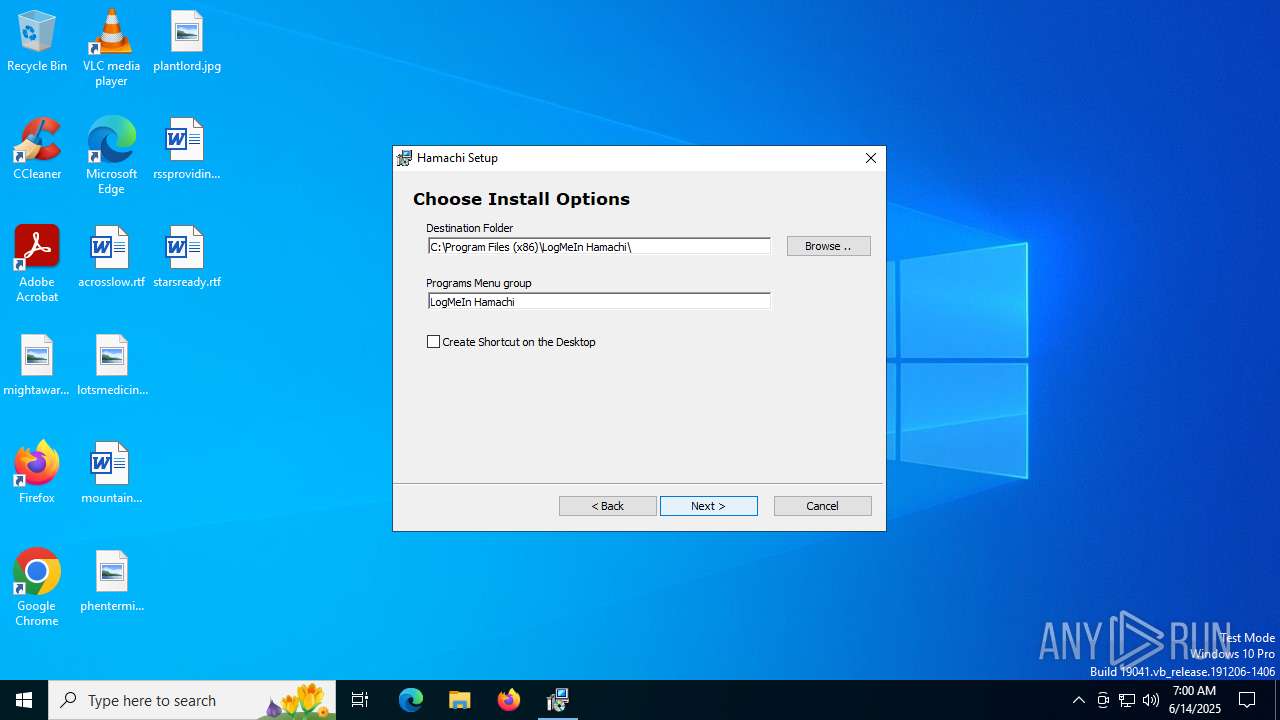
Create files in a temporary directory
- msiexec.exe (PID: 1564)
Creates files or folders in the user directory
- msiexec.exe (PID: 3752)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
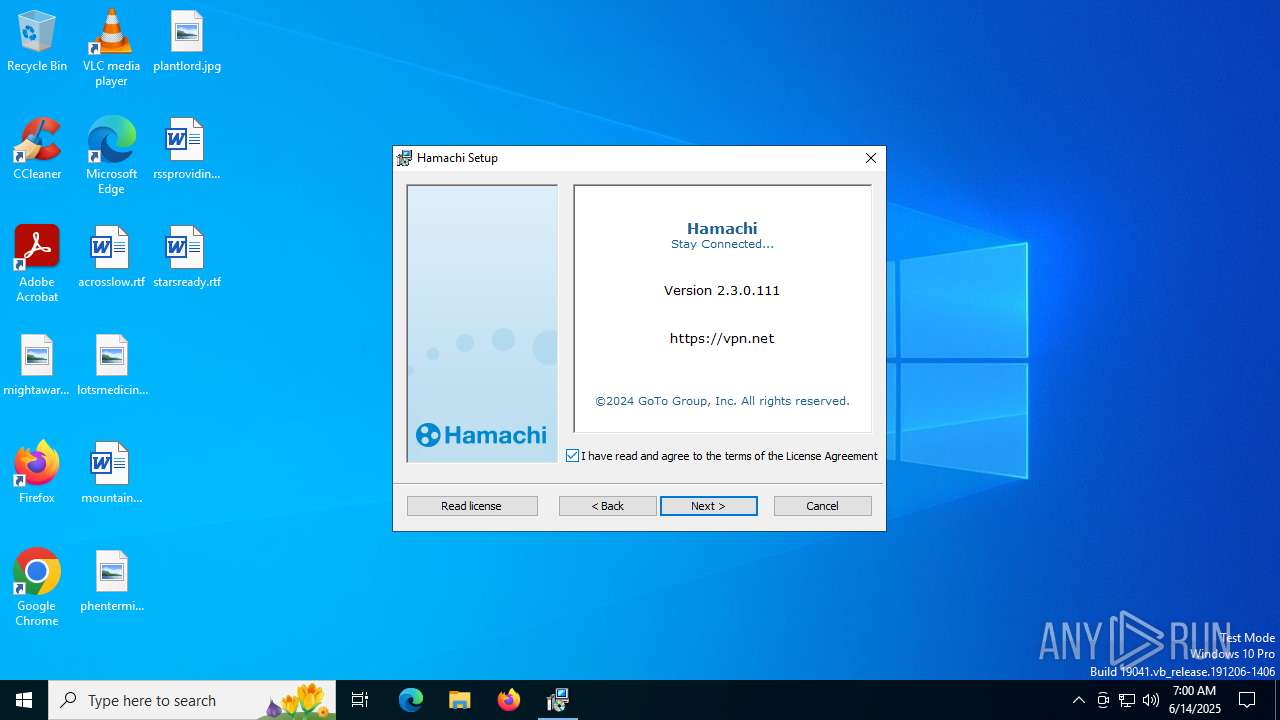
| Title: | Installation Database |
| Subject: | Hamachi Installer |
| Author: | LogMeIn, Inc. |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install Hamachi. |
| Template: | ;1033 |
| Pages: | 200 |
| Words: | 2 |
| Security: | Read-only recommended |
| RevisionNumber: | {C15EA8DB-41DF-4C48-8704-7D4FAB7D9EBB} |
| CreateDate: | 2024:03:25 12:38:25 |
| ModifyDate: | 2024:03:25 12:38:25 |
| Software: | Windows Installer XML v2.0.5805.0 (candle/light) |
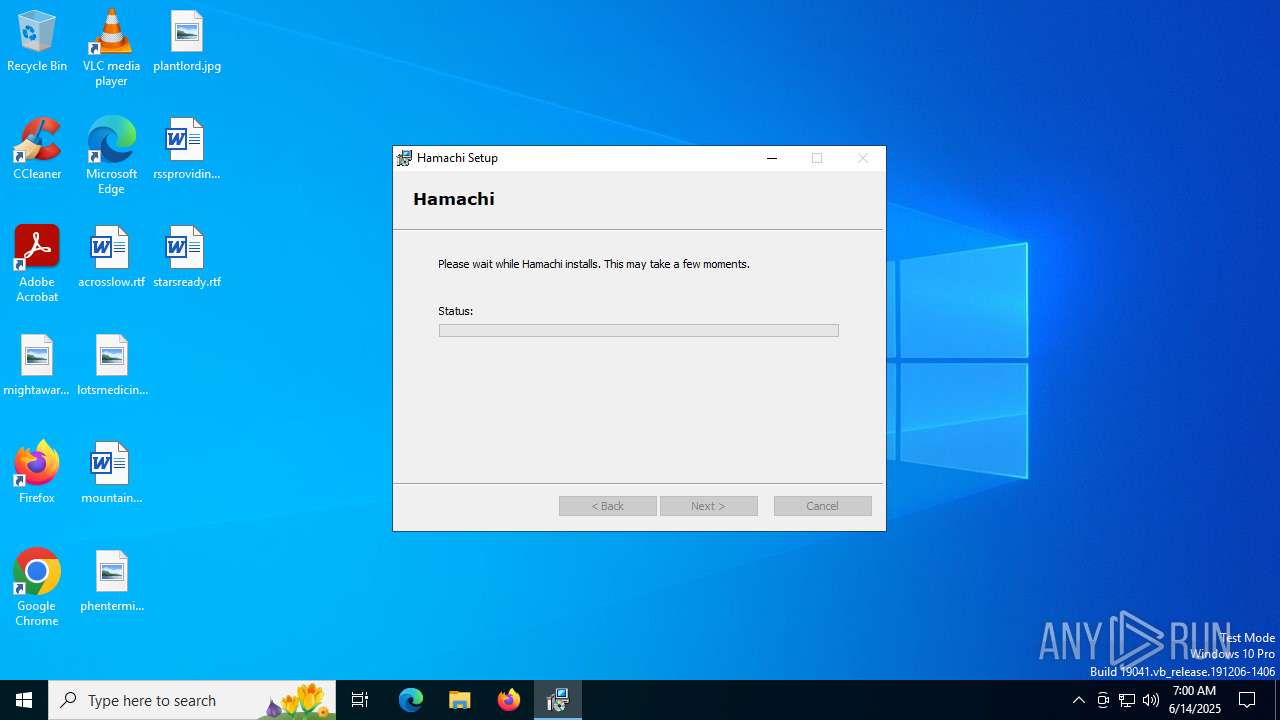
Total processes
190
Monitored processes
47
Malicious processes
5
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 416 | DrvInst.exe "2" "211" "ROOT\NET\0000" "C:\WINDOWS\INF\oem1.inf" "oem1.inf:db04a16c4ff220c2:Hamachi.ndi:15.28.40.464:hamachi," "42b53aaff" "00000000000001BC" | C:\Windows\System32\drvinst.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 620 | "C:\Program Files (x86)\LogMeIn Hamachi\x64\hamachi-2.exe" --config Hamachi 25.0.0.1 | C:\Program Files (x86)\LogMeIn Hamachi\x64\hamachi-2.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: LogMeIn Inc. Integrity Level: SYSTEM Description: Hamachi Client Tunneling Engine Exit code: 11 Version: 2, 3, 0, 111 Modules
| |||||||||||||||
| 1192 | netsh interface ipv6 add route ::/0 "24" 2620:9b::1900:1 metric=9000 publish=yes | C:\Windows\System32\netsh.exe | — | hamachi-2.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1204 | C:\Windows\syswow64\MsiExec.exe -Embedding AF71BD8586078718BC12CC1E73F544EC | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1380 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1532 | "C:\Program Files (x86)\LogMeIn Hamachi\x64\hamachi-2.exe" -s --get-config | C:\Program Files (x86)\LogMeIn Hamachi\x64\hamachi-2.exe | — | services.exe | |||||||||||
User: SYSTEM Company: LogMeIn Inc. Integrity Level: SYSTEM Description: Hamachi Client Tunneling Engine Exit code: 0 Version: 2, 3, 0, 111 Modules
| |||||||||||||||
| 1564 | C:\Windows\syswow64\MsiExec.exe -Embedding 13F0EFADE0010A06DAA00FBE283FDE0F C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1740 | netsh interface ipv6 add address interface="24" address=2620:9b::1905:c472 type=unicast store=persistent | C:\Windows\System32\netsh.exe | — | hamachi-2.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
24 559
Read events
24 123
Write events
416
Delete events
20
Modification events
| (PID) Process: | (6224) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 480000000000000049E99911FADCDB0150180000F8090000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6224) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 480000000000000049E99911FADCDB0150180000F8090000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6224) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000056B3BD11FADCDB0150180000F8090000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6224) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000056B3BD11FADCDB0150180000F8090000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6224) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000056B3BD11FADCDB0150180000F8090000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6224) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 48000000000000008E54C211FADCDB0150180000F8090000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6224) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 11 | |||
| (PID) Process: | (7020) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{a5a30fa2-3d06-4e9f-b5f4-a01df9d1fcba}\Elements\24000001 |
| Operation: | write | Name: | Element |
Value: {5b970157-8568-11eb-b45c-806e6f6e6963} | |||
| (PID) Process: | (7020) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{a5a30fa2-3d06-4e9f-b5f4-a01df9d1fcba}\Elements\25000004 |
| Operation: | write | Name: | Element |
Value: 0000000000000000 | |||
| (PID) Process: | (7020) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 48000000000000008B550012FADCDB016C1B000048120000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
36
Suspicious files
65
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6224 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 6224 | msiexec.exe | C:\Windows\Installer\17b1eb.msi | — | |
MD5:— | SHA256:— | |||
| 3752 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8EC9B1D0ABBD7F98B401D425828828CE_325DC716E4289E0AE281439314ED4BFA | binary | |
MD5:A4D179C1CB4ED4AAFB36D84405AF8FA9 | SHA256:555D8884A55275EF8297AF44DC7052FCE874776A1ADF3F1F720C1C3A7B1F376D | |||
| 6224 | msiexec.exe | C:\Windows\Installer\MSIB7CC.tmp | — | |
MD5:— | SHA256:— | |||
| 3752 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\C8E534EE129F27D55460CE17FD628216_1130D9B25898B0DB0D4F04DC5B93F141 | binary | |
MD5:3C473C00CADA495F53B86507555673AC | SHA256:516BBE8FD878D0C1E1EC1CF8AA6EED51C3775690518380B13E113A5A7824D2BE | |||
| 3752 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\698460A0B6E60F2F602361424D832905_8BB23D43DE574E82F2BEE0DF0EC47EEB | binary | |
MD5:5B5314F2E2860CCCC30EDFA949470AAB | SHA256:DDC71611A03B890BC4B5C8EF6F7689354E70CB82E24070E6FD5A9515EDEBBBDA | |||
| 3752 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI64B6.tmp | executable | |
MD5:3BC82080D6356DAE779EED5135FABF66 | SHA256:B076C9B888B130FB2FB5A74542C9A73322E78ED1F3F8476BE7A8209A20E56F7B | |||
| 6224 | msiexec.exe | C:\Windows\Installer\MSIB5F5.tmp | executable | |
MD5:3BC82080D6356DAE779EED5135FABF66 | SHA256:B076C9B888B130FB2FB5A74542C9A73322E78ED1F3F8476BE7A8209A20E56F7B | |||
| 3752 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI791C.tmp | executable | |
MD5:3BC82080D6356DAE779EED5135FABF66 | SHA256:B076C9B888B130FB2FB5A74542C9A73322E78ED1F3F8476BE7A8209A20E56F7B | |||
| 6224 | msiexec.exe | C:\Windows\Installer\MSIB4BA.tmp | executable | |
MD5:3BC82080D6356DAE779EED5135FABF66 | SHA256:B076C9B888B130FB2FB5A74542C9A73322E78ED1F3F8476BE7A8209A20E56F7B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
58
DNS requests
27
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3752 | msiexec.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
3752 | msiexec.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAjegkJ27mLaGBP72%2FEoqPs%3D | unknown | — | — | whitelisted |
3752 | msiexec.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
436 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.19:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6172 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
6172 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2708 | hamachi-2-ui.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
2708 | hamachi-2-ui.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6404 | RUXIMICS.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3752 | msiexec.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
436 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
436 | svchost.exe | 2.23.77.188:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 2.16.241.19:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
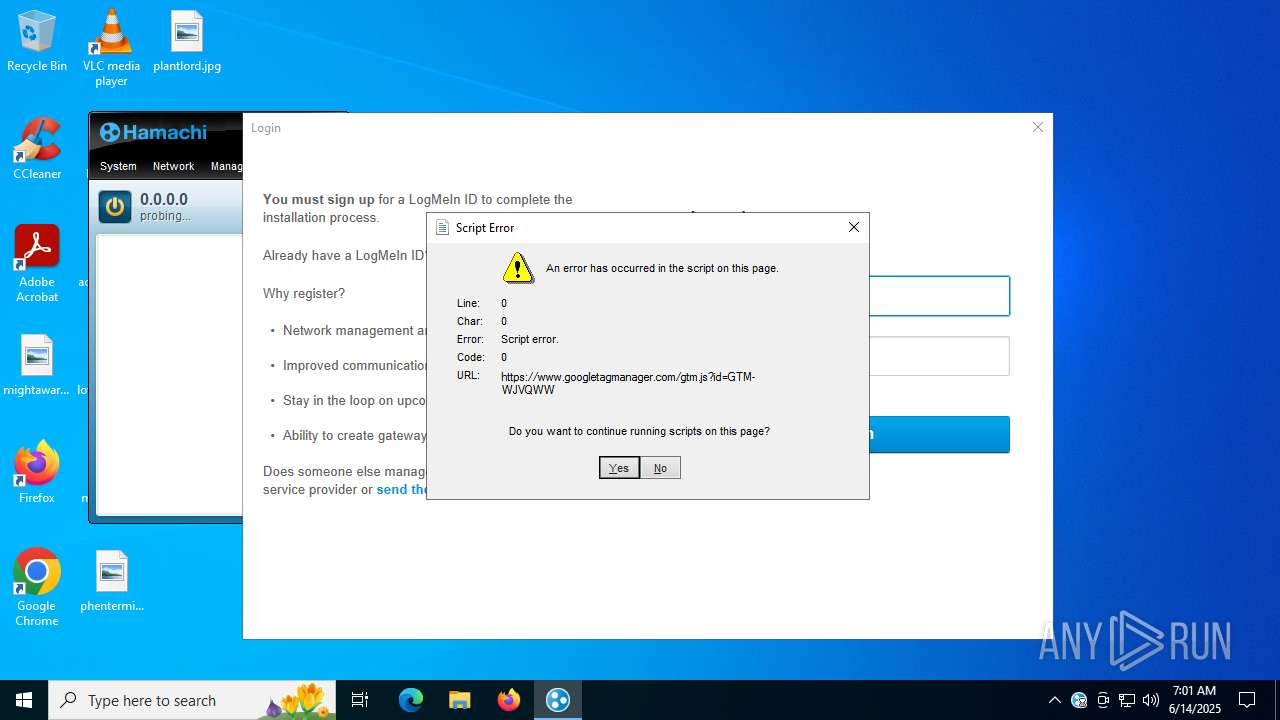
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |