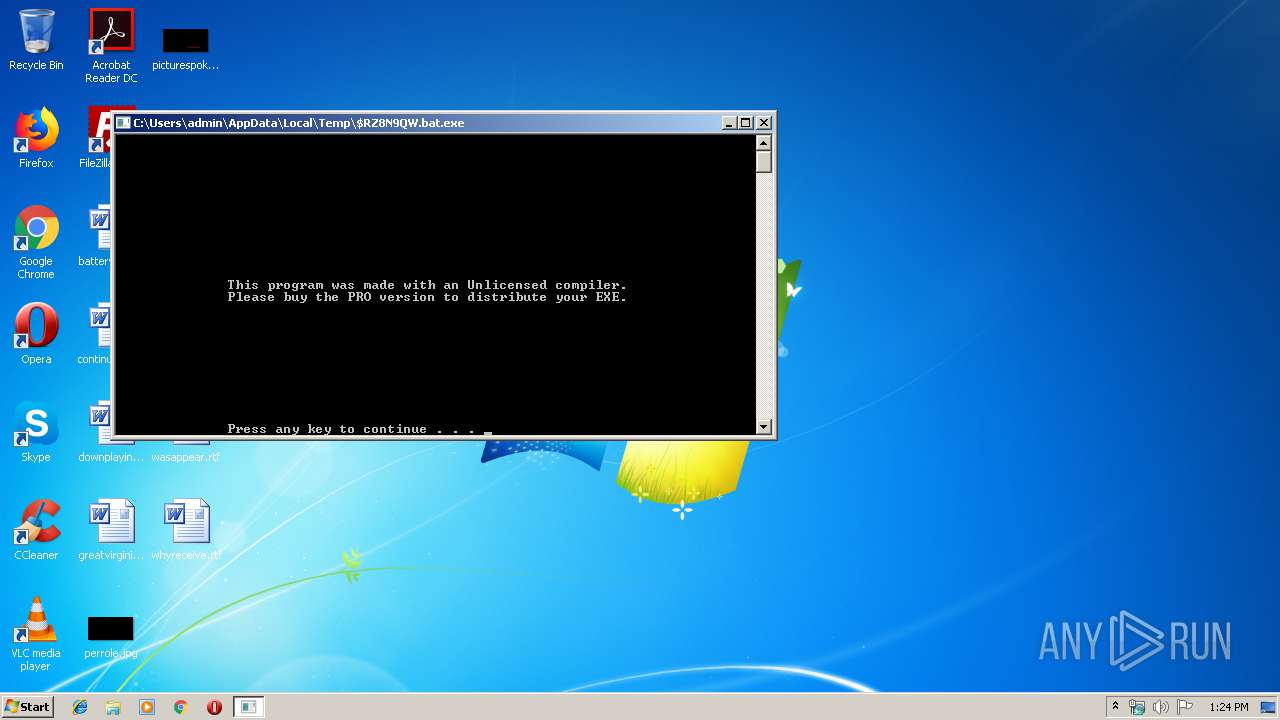
| File name: | $RZ8N9QW.bat.exe |
| Full analysis: | https://app.any.run/tasks/8ee9379e-5711-4d75-97f0-453499f7171a |
| Verdict: | Malicious activity |
| Analysis date: | March 22, 2019, 13:24:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (console) Intel 80386, for MS Windows |
| MD5: | 7A6C608FDB6AE6610971C6434727FBC2 |
| SHA1: | 47AA2BFCB452138EF908F1672E20FDD0E4E4F2A6 |
| SHA256: | 6EE12A891303B708E2F21DDD67758BD819D4B0A5F8E691F4F33937000E61874E |
| SSDEEP: | 1536:D6nKl2yk5Ca9GBj++0z0oNEs3tlmBd/JfafE/oSRi:D6ek4a9X+0z9ERdhyfE/o8i |
MALICIOUS
No malicious indicators.SUSPICIOUS
Starts CMD.EXE for commands execution
- $RZ8N9QW.bat.exe (PID: 2388)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 1548)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:01:08 19:34:33+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 61440 |
| InitializedDataSize: | 16384 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8b56 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
| ProductVersion: | 1.0.0.0 |
| FileDescription: | Product Description |
| CompanyName: | Your Company |
| LegalCopyright: | Copyright Info |
| ProductName: | Folder Temp |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_CUI |
| Compilation Date: | 08-Jan-2017 18:34:33 |
| FileVersion: | 1.0.0.0 |
| ProductVersion: | 1.0.0.0 |
| FileDescription: | Product Description |
| CompanyName: | Your Company |
| LegalCopyright: | Copyright Info |
| ProductName: | Folder Temp |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 08-Jan-2017 18:34:33 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000E6F6 | 0x0000F000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.31469 |
.rdata | 0x00010000 | 0x00000B84 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.43191 |
.data | 0x00011000 | 0x00B00F98 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.55306 |
.rsrc | 0x00B12000 | 0x000002A0 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.4213 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.25123 | 584 | Latin 1 / Western European | UNKNOWN | RT_VERSION |
Imports
KERNEL32.dll |
WINMM.dll |
Total processes
40
Monitored processes
10
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1548 | C:\Windows\system32\cmd.exe /c attrib +h C:\Users\admin\AppData\Local\Temp\xtmp | C:\Windows\system32\cmd.exe | — | $RZ8N9QW.bat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1628 | attrib +h C:\Users\admin\AppData\Local\Temp\xtmp | C:\Windows\system32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1980 | C:\Windows\system32\cmd.exe /c echo:0>C:\Users\admin\AppData\Local\Temp\is64.txt | C:\Windows\system32\cmd.exe | — | $RZ8N9QW.bat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2284 | C:\Windows\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\is64.bat | C:\Windows\system32\cmd.exe | — | $RZ8N9QW.bat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2388 | "C:\Users\admin\AppData\Local\Temp\$RZ8N9QW.bat.exe" | C:\Users\admin\AppData\Local\Temp\$RZ8N9QW.bat.exe | — | explorer.exe | |||||||||||
User: admin Company: Your Company Integrity Level: MEDIUM Description: Product Description Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2628 | C:\Windows\system32\cmd.exe /c | C:\Windows\system32\cmd.exe | — | $RZ8N9QW.bat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2784 | C:\Windows\system32\cmd.exe /c pause | C:\Windows\system32\cmd.exe | — | $RZ8N9QW.bat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2920 | C:\Windows\system32\cmd.exe /c | C:\Windows\system32\cmd.exe | — | $RZ8N9QW.bat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3080 | C:\Windows\system32\cmd.exe /c if not exist "C:\Users\admin\AppData\Local\Temp\efolder" mkdir "C:\Users\admin\AppData\Local\Temp\efolder" | C:\Windows\system32\cmd.exe | — | $RZ8N9QW.bat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3872 | C:\Windows\system32\cmd.exe /c if not exist "C:\Users\admin\AppData\Local\Temp\xtmp" mkdir "C:\Users\admin\AppData\Local\Temp\xtmp" | C:\Windows\system32\cmd.exe | — | $RZ8N9QW.bat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
48
Read events
48
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2388 | $RZ8N9QW.bat.exe | C:\Users\admin\AppData\Local\Temp\is64.bat | text | |
MD5:3CCDA7F84CE40901DECC54FA4C378B65 | SHA256:1414F69F5A7123543FFAA21CAB949B359DBA46741EAB3A5DCC9E57DA912B100E | |||
| 2284 | cmd.exe | C:\Users\admin\AppData\Local\Temp\is64.fil | text | |
MD5:D406619E40F52369E12AE4671B16A11A | SHA256:2E340D2B9CED6AD419C031400FB974FEED427CFABD0C167DEA26EC732D8579BE | |||
| 1980 | cmd.exe | C:\Users\admin\AppData\Local\Temp\is64.txt | text | |
MD5:21438EF4B9AD4FC266B6129A2F60DE29 | SHA256:13BF7B3039C63BF5A50491FA3CFD8EB4E699D1BA1436315AEF9CBE5711530354 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report