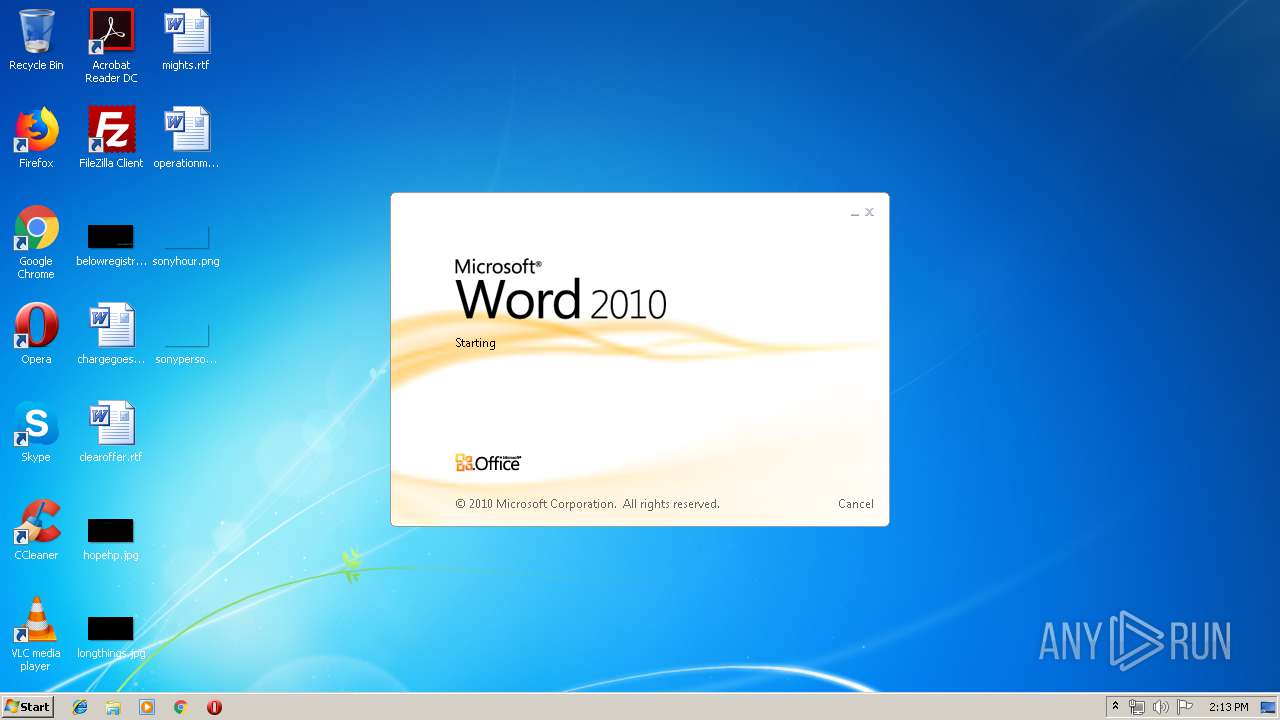
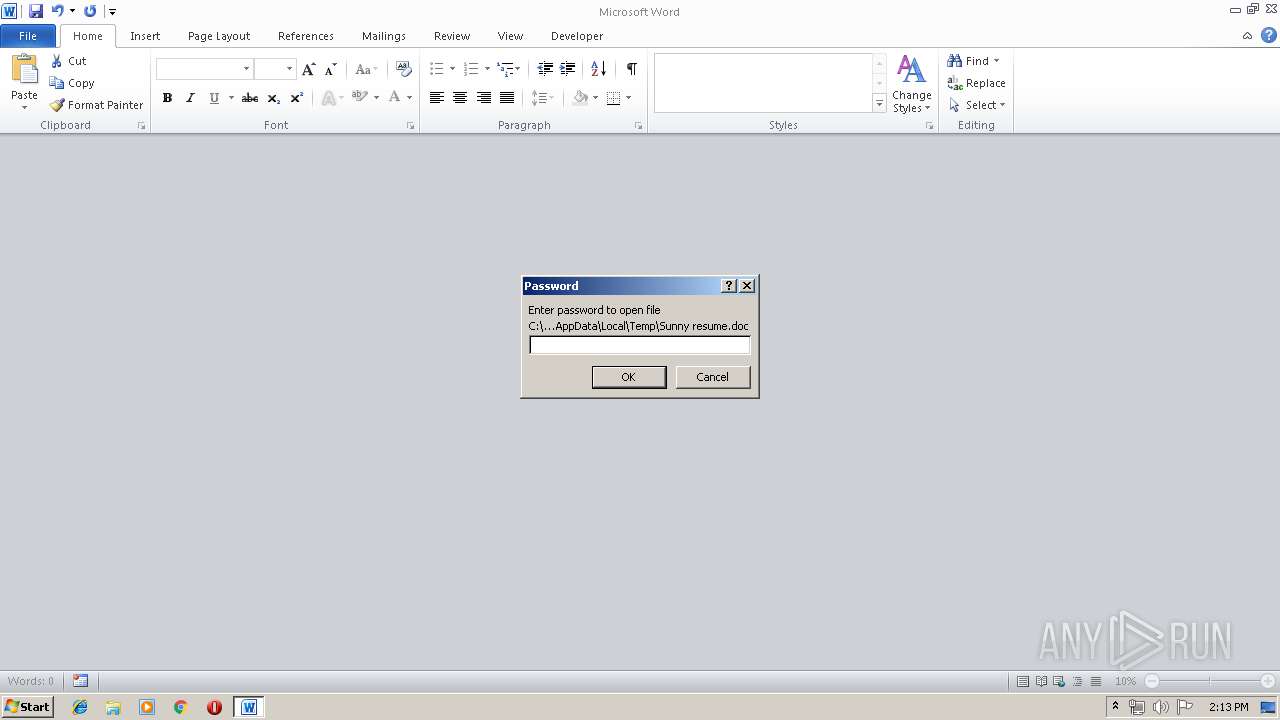
| File name: | Sunny resume.doc |
| Full analysis: | https://app.any.run/tasks/282b9605-f334-4182-bed9-74b7be5b22d9 |
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2019, 13:13:32 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Locale ID: 1033, Author: toebe, Subject: dbeoiusk |
| MD5: | 5FAAAD700199ADB6F13E83513ADEFD3C |
| SHA1: | A6974D5ACD119EA04DB398B0F5B561433463E90D |
| SHA256: | 6EDF9CC7DE21AD4AD20C366967B849A8F6DCE6AAD95DC774BA9D4930824F2A29 |
| SSDEEP: | 768:059Wn+KwdLHzK2jgqQ3wk1vY9ZXAaLvSe96ZLi1YDnEPSdA8jL3lLjTRMG0Gaaz+:7wdKWQjvY31vSJ57H3lb5rnomvl |
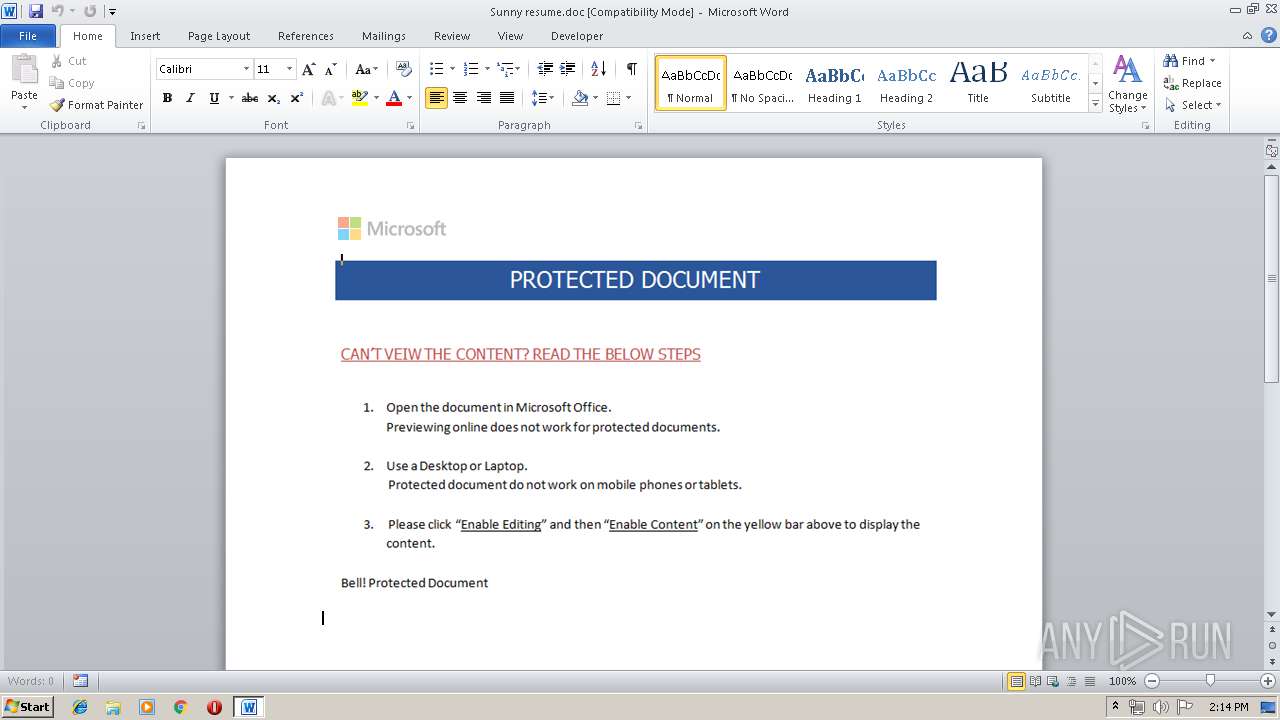
MALICIOUS
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 456)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 456)
Uses SVCHOST.EXE for hidden code execution
- nslookup.exe (PID: 2032)
Loads the Task Scheduler COM API
- svchost.exe (PID: 3512)
Application was dropped or rewritten from another process
- inboxmvprocessingpersianbearinglegitimate.exe (PID: 2368)
Loads dropped or rewritten executable
- inboxmvprocessingpersianbearinglegitimate.exe (PID: 2368)
SUSPICIOUS
Executable content was dropped or overwritten
- inboxmvprocessingpersianbearinglegitimate.exe (PID: 2368)
- svchost.exe (PID: 3512)
Reads Internet Cache Settings
- WINWORD.EXE (PID: 456)
Creates files in the program directory
- svchost.exe (PID: 3512)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 456)
Creates files in the user directory
- WINWORD.EXE (PID: 456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| LocaleIndicator: | 1033 |
| Author: | toebe |
| Subject: | dbeoiusk |
Total processes
36
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Sunny resume.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2032 | "C:\Windows\system32\nslookup.exe" | C:\Windows\system32\nslookup.exe | — | inboxmvprocessingpersianbearinglegitimate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: nslookup Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Users\admin\AppData\Local\Temp\inboxmvprocessingpersianbearinglegitimate.exe" | C:\Users\admin\AppData\Local\Temp\inboxmvprocessingpersianbearinglegitimate.exe | WINWORD.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3512 | C:\Windows\system32\svchost.exe | C:\Windows\system32\svchost.exe | nslookup.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 557
Read events
1 156
Write events
396
Delete events
5
Modification events
| (PID) Process: | (456) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2:= |
Value: 323A3D00C8010000010000000000000000000000 | |||
| (PID) Process: | (456) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (456) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (456) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419358 | |||
| (PID) Process: | (456) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419472 | |||
| (PID) Process: | (456) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1320419473 | |||
| (PID) Process: | (456) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: C8010000840466DC0D0FD50100000000 | |||
| (PID) Process: | (456) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | );= |
Value: 293B3D00C801000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (456) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | );= |
Value: 293B3D00C801000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (456) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
5
Suspicious files
1
Text files
2
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 456 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE12.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 456 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF0A95110DE1603ECC.TMP | — | |
MD5:— | SHA256:— | |||
| 456 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF34C350CEBE5186AE.TMP | — | |
MD5:— | SHA256:— | |||
| 456 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFA7905749AD57B83B.TMP | — | |
MD5:— | SHA256:— | |||
| 456 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF378179F084BA32EB.TMP | — | |
MD5:— | SHA256:— | |||
| 456 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\mso3215.tmp | — | |
MD5:— | SHA256:— | |||
| 456 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFD79F474ECAC52D76.TMP | — | |
MD5:— | SHA256:— | |||
| 456 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFEE89C5E626379312.TMP | — | |
MD5:— | SHA256:— | |||
| 456 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\39746E31.png | — | |
MD5:— | SHA256:— | |||
| 2368 | inboxmvprocessingpersianbearinglegitimate.exe | C:\Users\admin\AppData\Local\Temp\nsn480E.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
0
Threats
5
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
456 | WINWORD.EXE | 209.141.46.175:80 | — | FranTech Solutions | US | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
456 | WINWORD.EXE | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
456 | WINWORD.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M1 |
456 | WINWORD.EXE | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
456 | WINWORD.EXE | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from dotted Quad by MSXMLHTTP M2 |
456 | WINWORD.EXE | Potentially Bad Traffic | ET INFO SUSPICIOUS Dotted Quad Host MZ Response |