| download: | cbce4a |
| Full analysis: | https://app.any.run/tasks/41db9e03-6f3b-4b72-8684-47a21e46b939 |
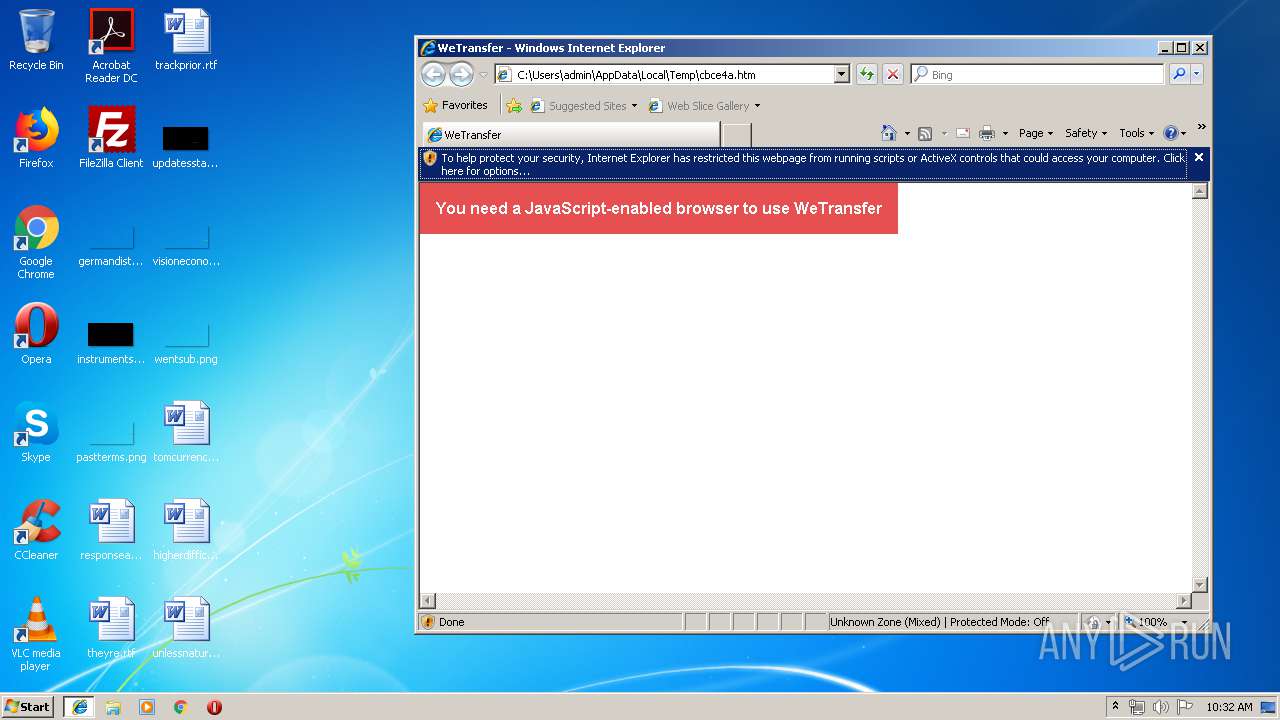
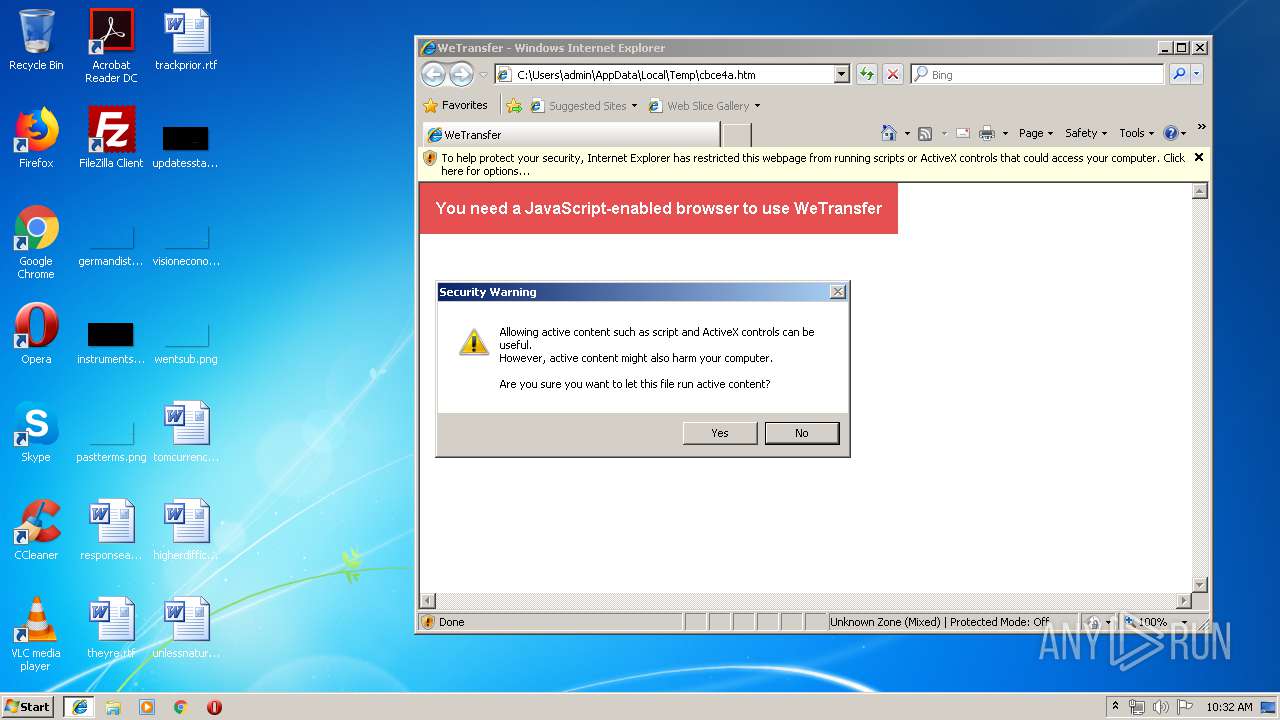
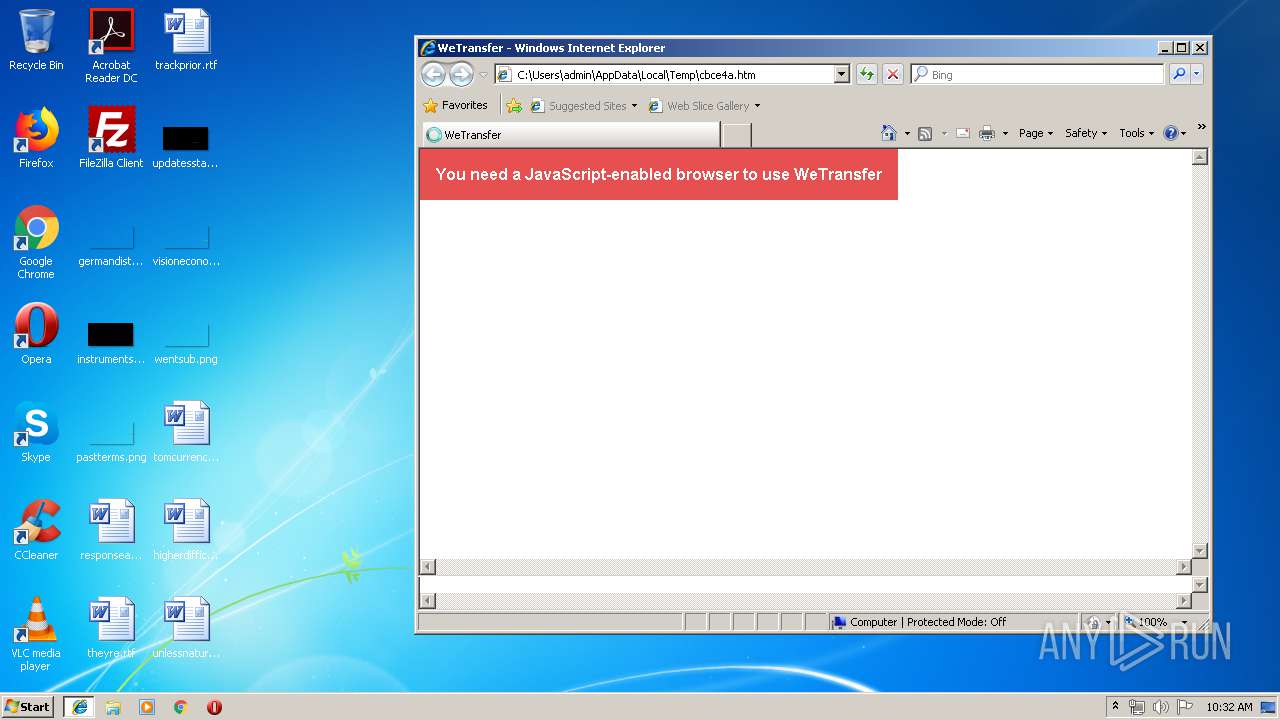
| Verdict: | Malicious activity |
| Analysis date: | May 15, 2019, 09:31:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | 8880E3256CEBB0A1ACEAD95F083C31B5 |
| SHA1: | 852F14181B8D232A60F8F162ED4D62E0E89DA8F6 |
| SHA256: | 6EC350A831C95E4AC3E839297646C3D4DEBD8514082548CA046343C895BECFE9 |
| SSDEEP: | 1536:U+E3a2W7flXB4eL2fCzbr2UdiU+Z702D6H:U+E3ax7daQ2crEZVD6H |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2940)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3516)
- iexplore.exe (PID: 2920)
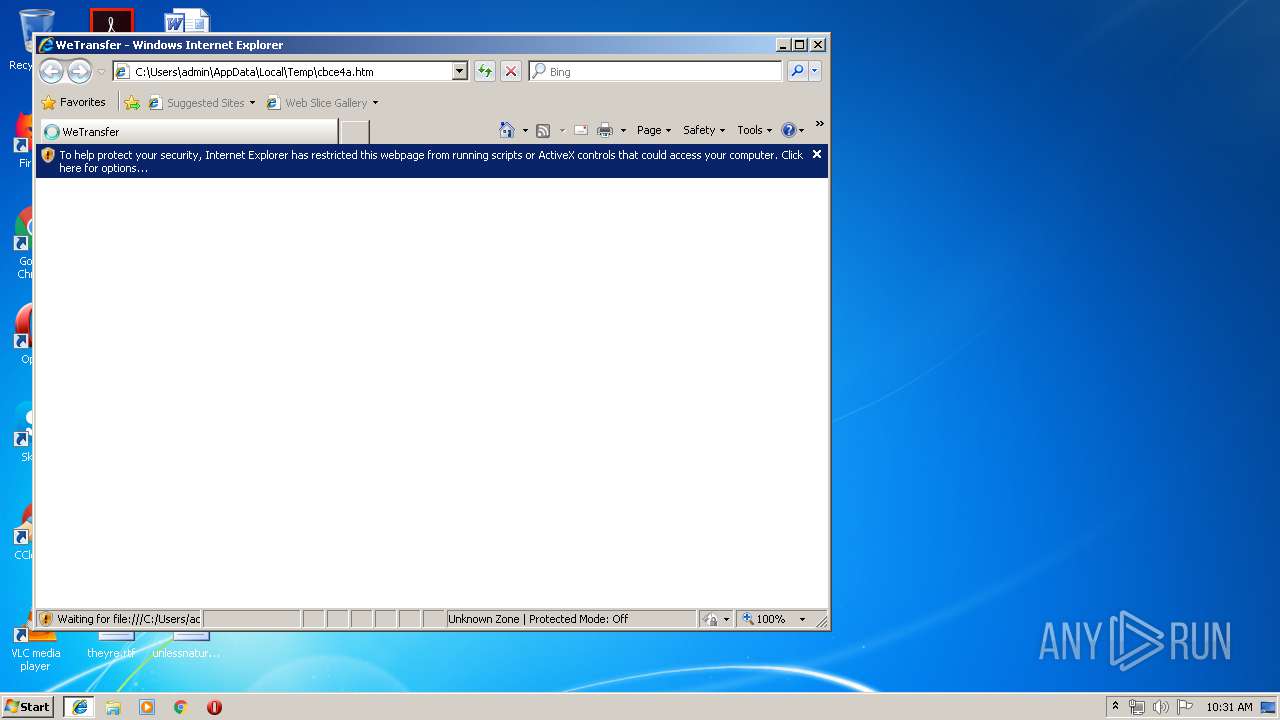
Changes internet zones settings
- iexplore.exe (PID: 2920)
Reads internet explorer settings
- iexplore.exe (PID: 3516)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3516)
Application launched itself
- iexplore.exe (PID: 2920)
- chrome.exe (PID: 2940)
Changes settings of System certificates
- iexplore.exe (PID: 3516)
Creates files in the user directory
- iexplore.exe (PID: 3516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| HTTPEquivXUACompatible: | IE=edge |
|---|---|
| viewport: | width=device-width, minimum-scale=1, initial-scale=1, user-scalable=no |
| pinterest: | nopin |
| referrer: | origin |
| Description: | WeTransfer is the simplest way to send your files around the world. Share large files up to 2GB for free. |
| Author: | WeTransfer |
| applicationName: | WeTransfer |
| csrfParam: | authenticity_token |
| csrfToken: | cpwlOOHWWzg87HEbLU3PL1Y4sNSR70lNYCm0uzj4KqslSzq/N2lAO1QPg8dUhDAxe5ytne7eNmEaH7wG2HPnUQ== |
| Title: | WeTransfer |
Total processes
58
Monitored processes
24
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,5260416551357936282,5854703180097418677,131072 --enable-features=PasswordImport --service-pipe-token=1939178179511860019 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1939178179511860019 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2208 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,5260416551357936282,5854703180097418677,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=3603841659940962451 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3603841659940962451 --renderer-client-id=19 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,5260416551357936282,5854703180097418677,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2369475085045719529 --mojo-platform-channel-handle=4188 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1208 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,5260416551357936282,5854703180097418677,131072 --enable-features=PasswordImport --service-pipe-token=17148769997358674601 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17148769997358674601 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2020 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1916 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,5260416551357936282,5854703180097418677,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=8700160726011016915 --mojo-platform-channel-handle=4740 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,5260416551357936282,5854703180097418677,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=1206027234268970543 --mojo-platform-channel-handle=2868 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2156 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,5260416551357936282,5854703180097418677,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5356174492772072317 --mojo-platform-channel-handle=4856 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2168 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,5260416551357936282,5854703180097418677,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12337332353932870866 --mojo-platform-channel-handle=4264 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,5260416551357936282,5854703180097418677,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3171512235432645167 --mojo-platform-channel-handle=2812 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2280 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=952,5260416551357936282,5854703180097418677,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5696999817413008951 --mojo-platform-channel-handle=944 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
988
Read events
805
Write events
172
Delete events
11
Modification events
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {3E1754CB-76F4-11E9-B63D-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2920) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307050003000F0009001F0029001701 | |||
Executable files
0
Suspicious files
68
Text files
216
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2920 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2920 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab12F4.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar12F5.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab1305.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar1306.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab13C3.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar13C4.tmp | — | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\070E0202839D9D67350CD2613E78E416 | binary | |
MD5:— | SHA256:— | |||
| 3516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\94308059B57B3142E455B38A6EB92015 | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
60
DNS requests
33
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3516 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 56.1 Kb | whitelisted |
2940 | chrome.exe | GET | 302 | 64.233.184.198:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
3516 | iexplore.exe | OPTIONS | 400 | 172.217.22.8:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3516 | iexplore.exe | OPTIONS | 400 | 172.217.22.8:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3516 | iexplore.exe | OPTIONS | 400 | 172.217.22.8:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3516 | iexplore.exe | OPTIONS | 400 | 172.217.22.8:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2920 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
3516 | iexplore.exe | OPTIONS | 400 | 172.217.22.8:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
3516 | iexplore.exe | OPTIONS | 400 | 172.217.22.8:80 | http://www.googletagmanager.com/ | US | html | 1.52 Kb | whitelisted |
2940 | chrome.exe | GET | 200 | 217.146.165.206:80 | http://r3---sn-oun-1gie.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=136.0.0.108&mm=28&mn=sn-oun-1gie&ms=nvh&mt=1557912476&mv=u&pl=27&shardbypass=yes | CH | crx | 842 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3516 | iexplore.exe | 143.204.101.79:443 | prod-cdn.wetransfer.net | — | US | suspicious |
3516 | iexplore.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2920 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3516 | iexplore.exe | 143.204.98.159:80 | x.ss2.us | — | US | suspicious |
4 | System | 172.217.22.8:445 | www.googletagmanager.com | Google Inc. | US | whitelisted |
4 | System | 143.204.98.156:445 | d19ptbnuzhibkh.cloudfront.net | — | US | malicious |
3516 | iexplore.exe | 172.217.22.8:80 | www.googletagmanager.com | Google Inc. | US | whitelisted |
4 | System | 143.204.98.19:445 | d19ptbnuzhibkh.cloudfront.net | — | US | suspicious |
4 | System | 143.204.98.208:445 | d19ptbnuzhibkh.cloudfront.net | — | US | suspicious |
4 | System | 143.204.98.115:445 | d19ptbnuzhibkh.cloudfront.net | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
prod-cdn.wetransfer.net |
| whitelisted |
x.ss2.us |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
d19ptbnuzhibkh.cloudfront.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
Threats
10 ETPRO signatures available at the full report