| File name: | ExternalHack.exe |
| Full analysis: | https://app.any.run/tasks/ed764fe1-1d03-4a57-80e5-ef4f9ffd35f5 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2023, 12:01:03 |
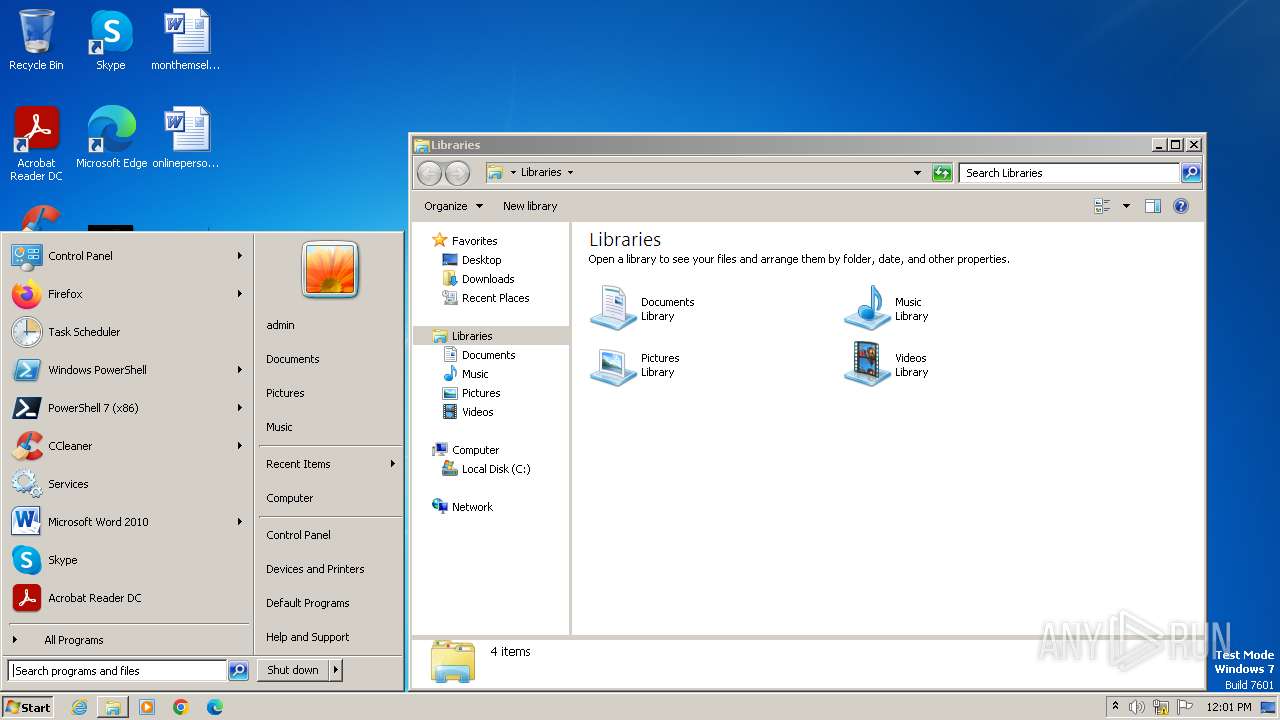
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 22AE9CF8C6C6C59605D44BCFB7B32BFD |
| SHA1: | 196537B863CA275B7C8986C4B6E33A7F2A7F91EB |
| SHA256: | 6EBA938B80264336509977E286CC361AE72142FCF91F2B44DEEBB4B78FBFCC18 |
| SSDEEP: | 98304:4yi3jYuwIChgYnb2Tg3Ve5itww8EC2XjCUlWfHQGDrx5VT6opVPk/GqolXYHV/Mw:5+sITy |
MALICIOUS
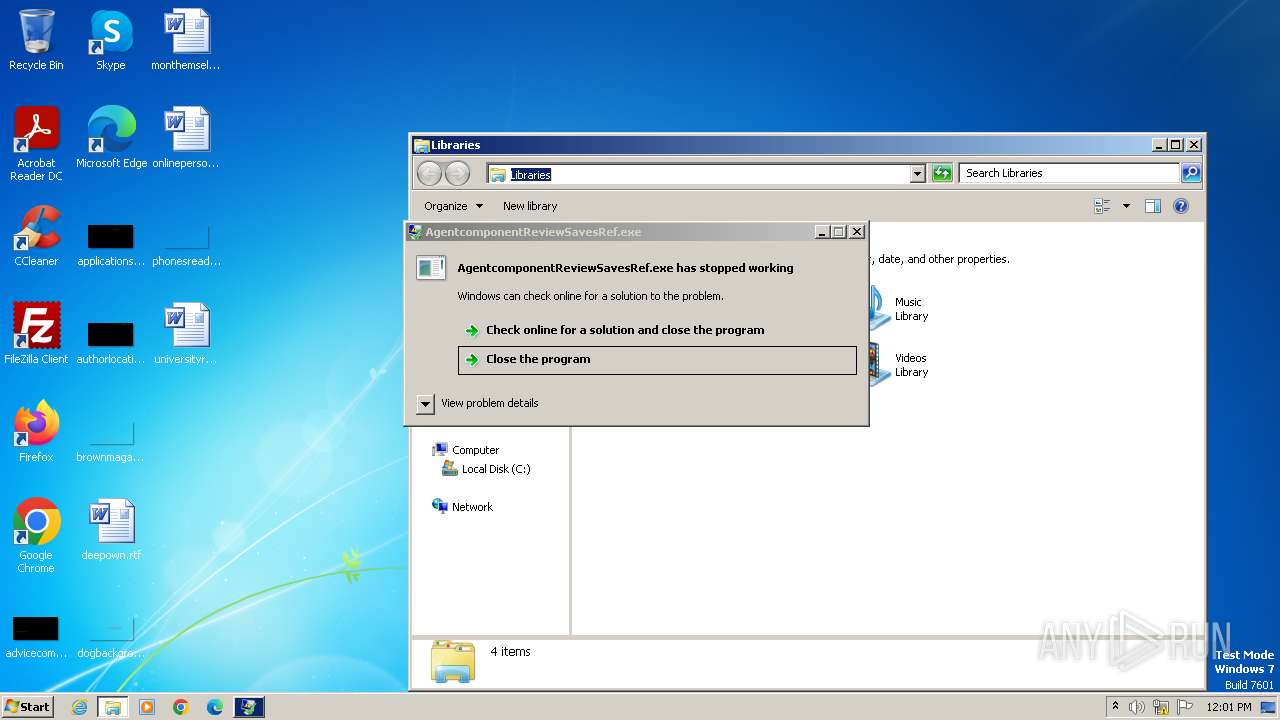
Drops the executable file immediately after the start
- ExternalHack.exe (PID: 564)
- AgentcomponentReviewSavesRef.exe (PID: 1852)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 2740)
SUSPICIOUS
Reads the Internet Settings
- wscript.exe (PID: 2740)
- ExternalHack.exe (PID: 564)
Executing commands from a ".bat" file
- wscript.exe (PID: 2740)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 2740)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2740)
INFO
Reads the computer name
- ExternalHack.exe (PID: 564)
- AgentcomponentReviewSavesRef.exe (PID: 1852)
Checks supported languages
- ExternalHack.exe (PID: 564)
- AgentcomponentReviewSavesRef.exe (PID: 1852)
Manual execution by a user
- explorer.exe (PID: 3796)
Reads the machine GUID from the registry
- AgentcomponentReviewSavesRef.exe (PID: 1852)
Reads Environment values
- AgentcomponentReviewSavesRef.exe (PID: 1852)
Reads product name
- AgentcomponentReviewSavesRef.exe (PID: 1852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:03:03 14:15:57+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.3 |
| CodeSize: | 203776 |
| InitializedDataSize: | 122368 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1f530 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
45
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Users\admin\AppData\Local\Temp\ExternalHack.exe" | C:\Users\admin\AppData\Local\Temp\ExternalHack.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
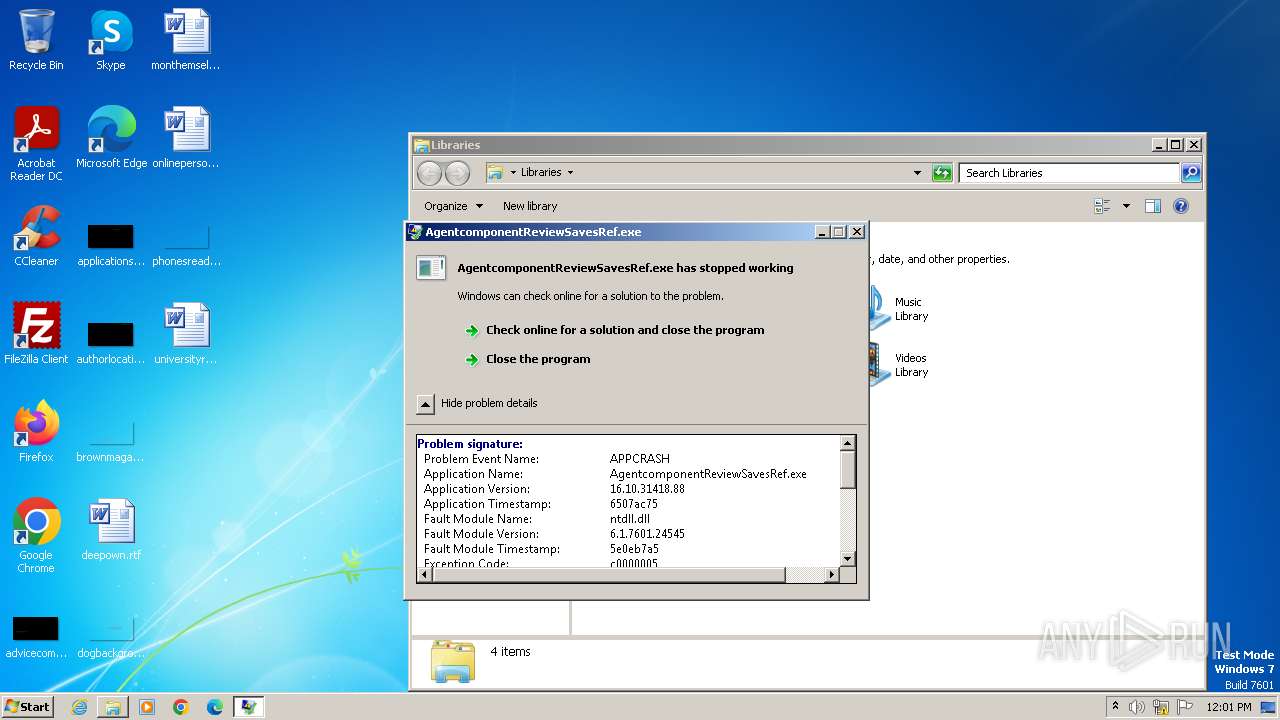
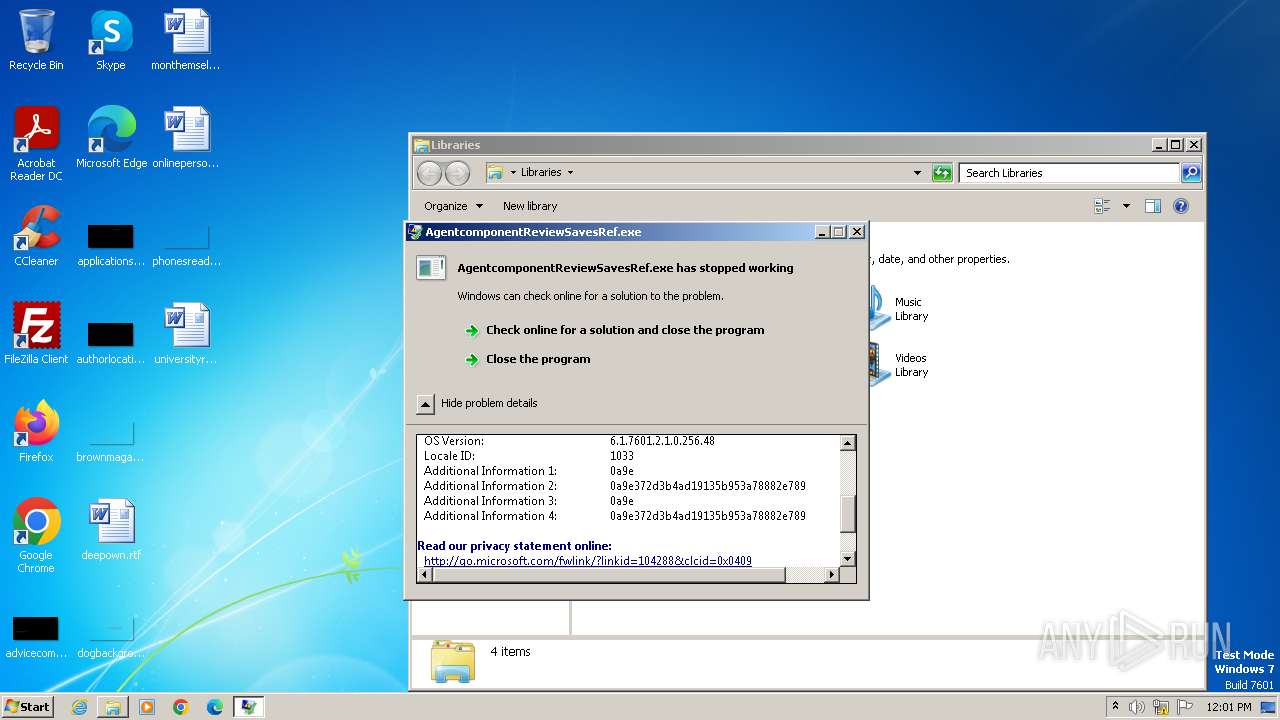
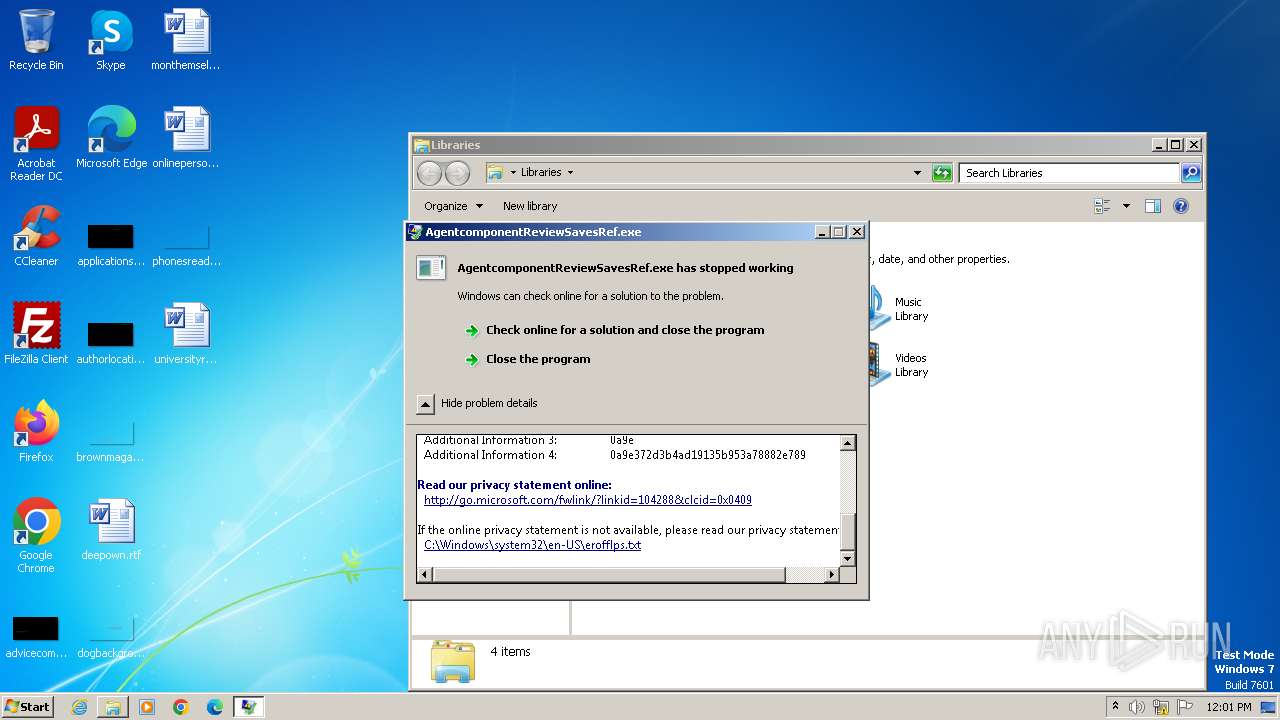
| 1852 | "C:\SavesBrokerCommonsvc/AgentcomponentReviewSavesRef.exe" | C:\SavesBrokerCommonsvc\AgentcomponentReviewSavesRef.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Version: 16.10.31418.88 Modules
| |||||||||||||||
| 2740 | "C:\Windows\System32\WScript.exe" "C:\SavesBrokerCommonsvc\t82PhDwVE2aS4WA6s0zAX4hZEeDJ4tOWBghh6FnyltCc9LKkawuotCUBp.vbe" | C:\Windows\System32\wscript.exe | — | ExternalHack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 3264 | C:\Windows\system32\cmd.exe /c ""C:\SavesBrokerCommonsvc\qqWrGhxyfBsLiPUtUDZQ7UkIWi0gI3jwOGwuE.bat" " | C:\Windows\System32\cmd.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 3221225477 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3796 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
531
Read events
503
Write events
28
Delete events
0
Modification events
| (PID) Process: | (564) ExternalHack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (564) ExternalHack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (564) ExternalHack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (564) ExternalHack.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (2740) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2740) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2740) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2740) wscript.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (1852) AgentcomponentReviewSavesRef.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
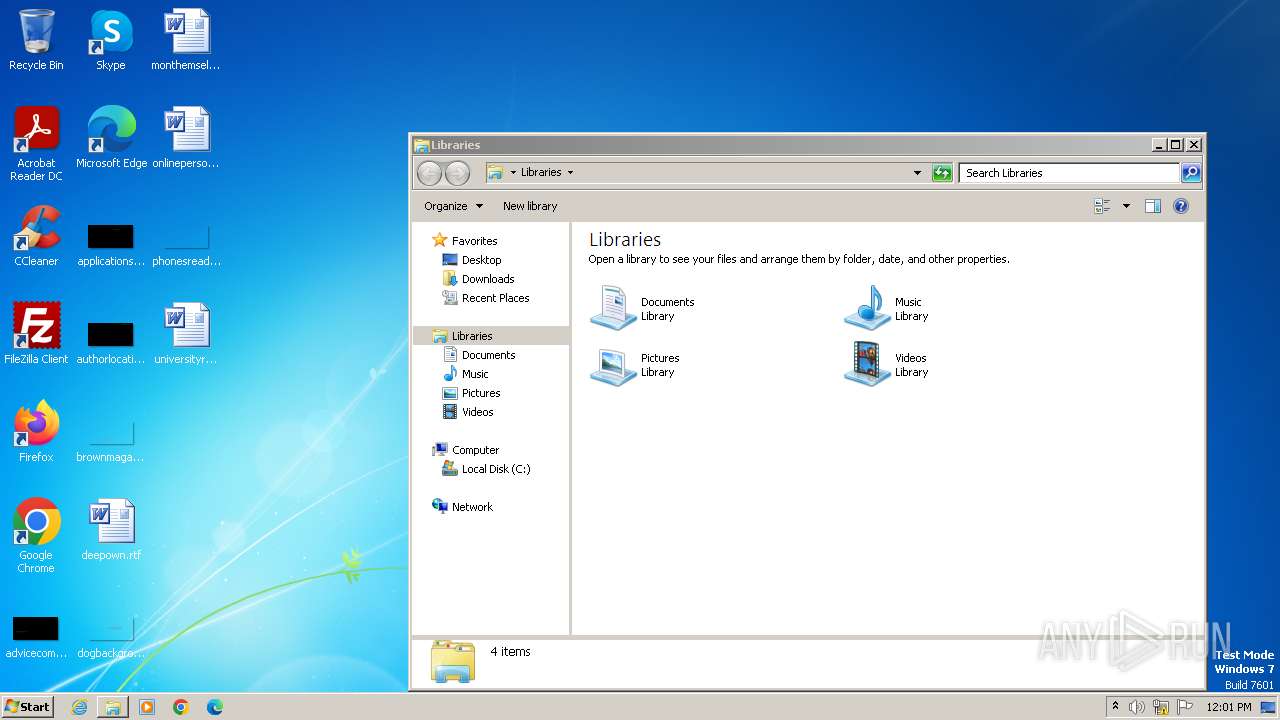
Executable files
2
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1852 | AgentcomponentReviewSavesRef.exe | C:\Users\admin\Desktop\oxBcArBf.log | — | |
MD5:— | SHA256:— | |||
| 564 | ExternalHack.exe | C:\SavesBrokerCommonsvc\qqWrGhxyfBsLiPUtUDZQ7UkIWi0gI3jwOGwuE.bat | text | |
MD5:9DB8A822DF1666629C7D197E64EDDC9F | SHA256:DCE3EDC18202B73B03737386E0D7D686B07A636AA268ABBFAF7722EFF3B43650 | |||
| 564 | ExternalHack.exe | C:\SavesBrokerCommonsvc\AgentcomponentReviewSavesRef.exe | executable | |
MD5:C5ECFEF00884CC26BF2EB5F740FA2515 | SHA256:D7B9D99F04331A0B4F88CFD701F3BC153376A3BE5412854E2D2A77021EB55B81 | |||
| 564 | ExternalHack.exe | C:\SavesBrokerCommonsvc\t82PhDwVE2aS4WA6s0zAX4hZEeDJ4tOWBghh6FnyltCc9LKkawuotCUBp.vbe | binary | |
MD5:C54A46BFA4766C63BFB7E7D9433B8054 | SHA256:24611CED2580AB981D3268DA9933ED54442E502DD9291CB765C85BA8C9B58890 | |||
| 1852 | AgentcomponentReviewSavesRef.exe | C:\Users\admin\Desktop\snrTHoBY.log | executable | |
MD5:D8BF2A0481C0A17A634D066A711C12E9 | SHA256:2B93377EA087225820A9F8E4F331005A0C600D557242366F06E0C1EAE003D669 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
5
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |