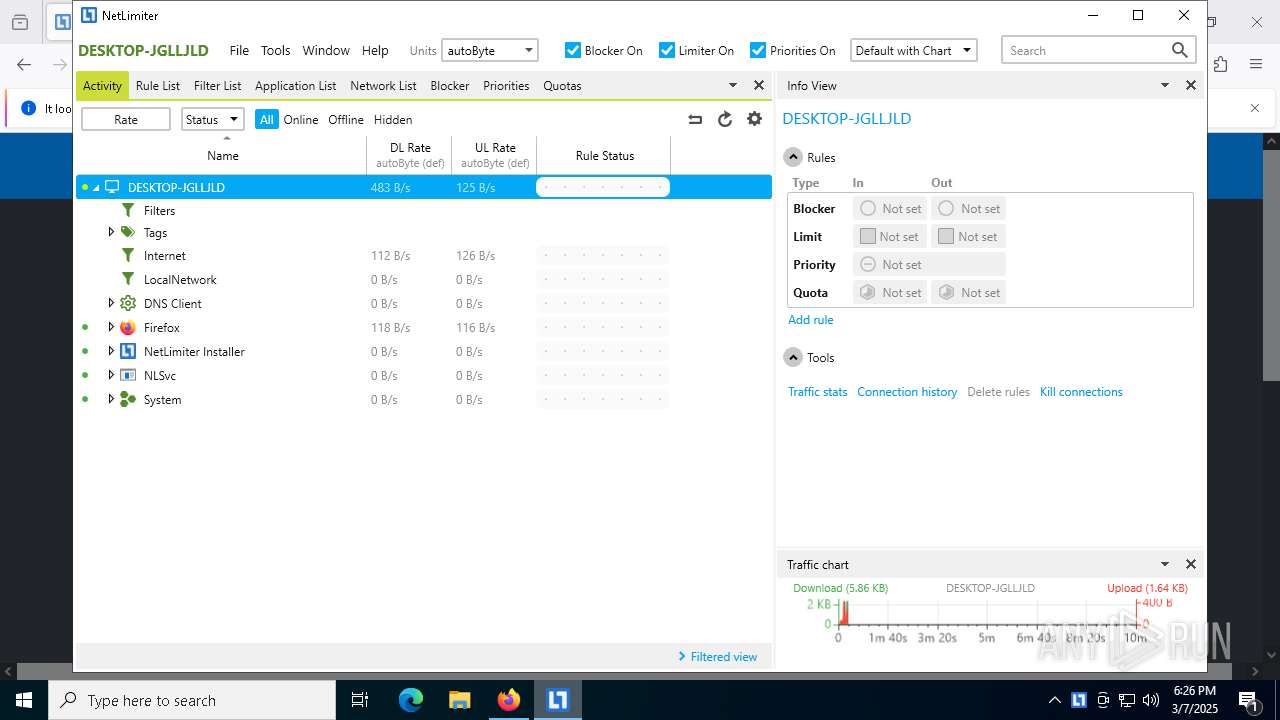
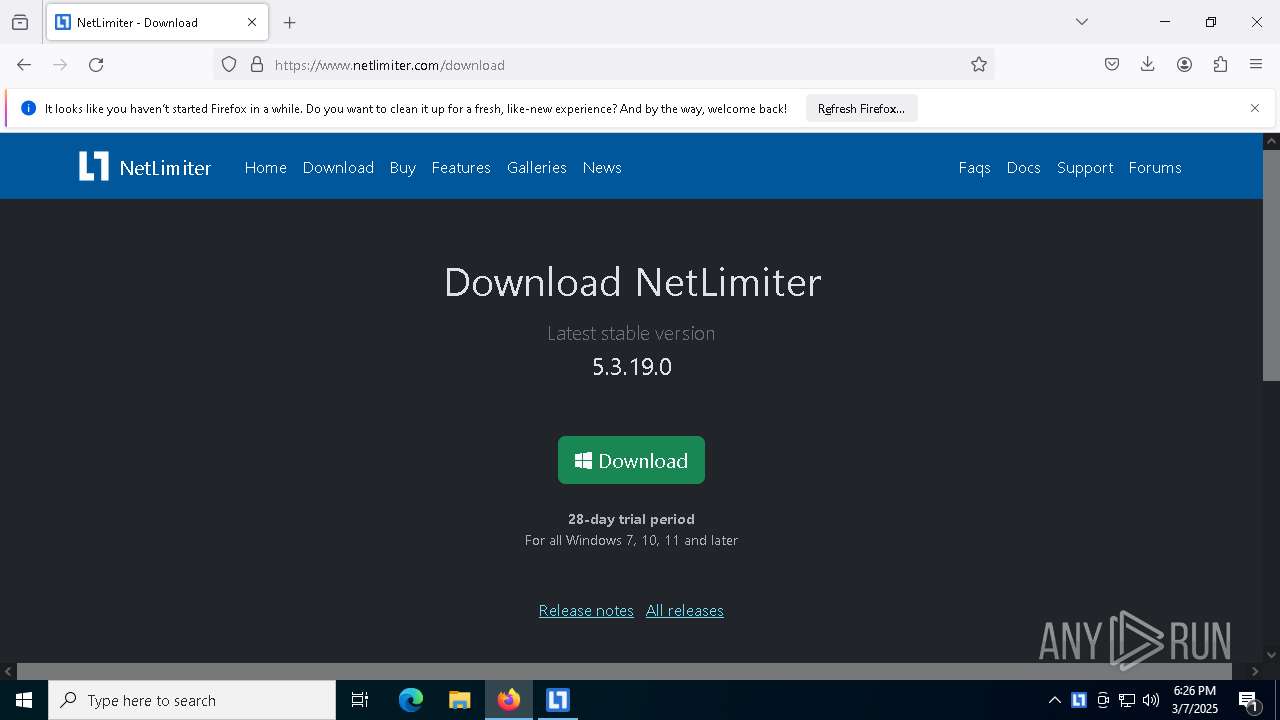
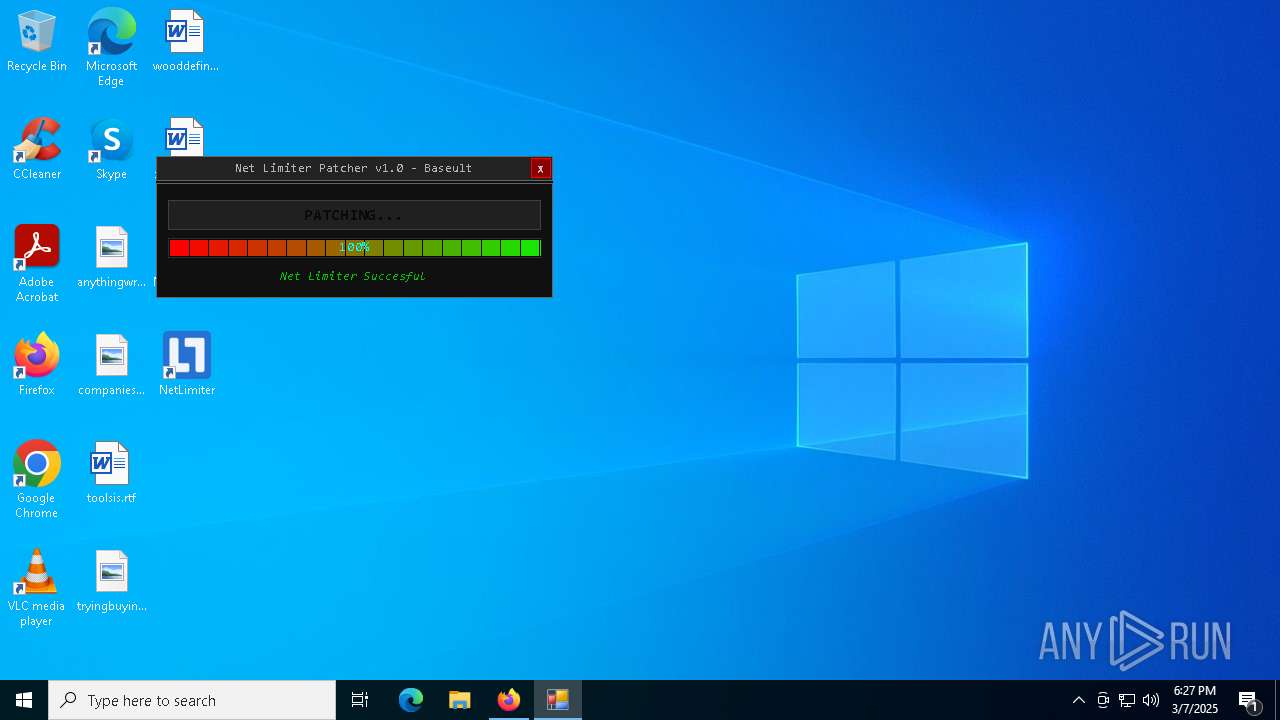
| File name: | NetLimiter.Crack.exe |
| Full analysis: | https://app.any.run/tasks/c4702628-8c6d-465c-af5b-3175f1a13e69 |
| Verdict: | Malicious activity |
| Analysis date: | March 07, 2025, 18:24:29 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 Mono/.Net assembly, for MS Windows, 2 sections |
| MD5: | 588E0E5A3FFCDFCEEA39E43B064D420C |
| SHA1: | 104261CDA9ED8B1D27C06F10F4CFC2AB112C0B1C |
| SHA256: | 6E95F6BEC847284D367390181E64985D4FB9E1A4A6FCC078F367E9579E4177B6 |
| SSDEEP: | 24576:OnuvAzsYj8TC7+8zFR635d5Yd+F++3Qc6VNE:+uvAzsYQTC7+8z7635d5Yd+F++oVN |
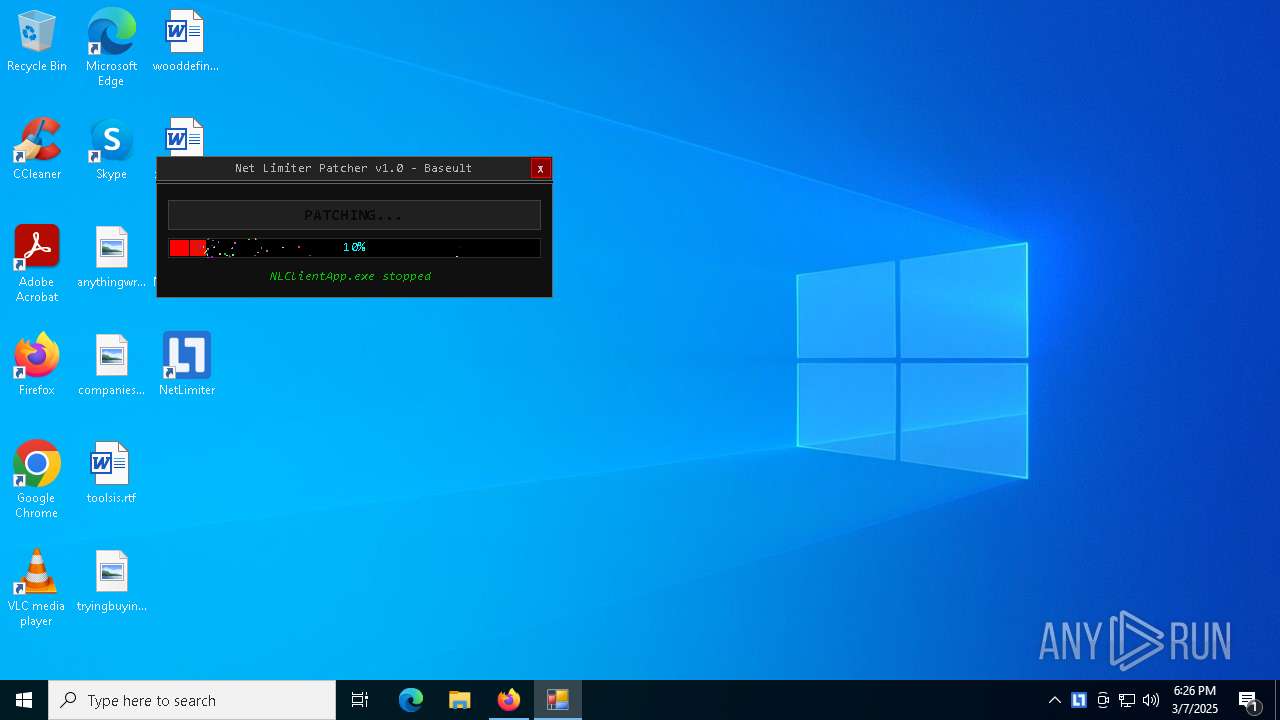
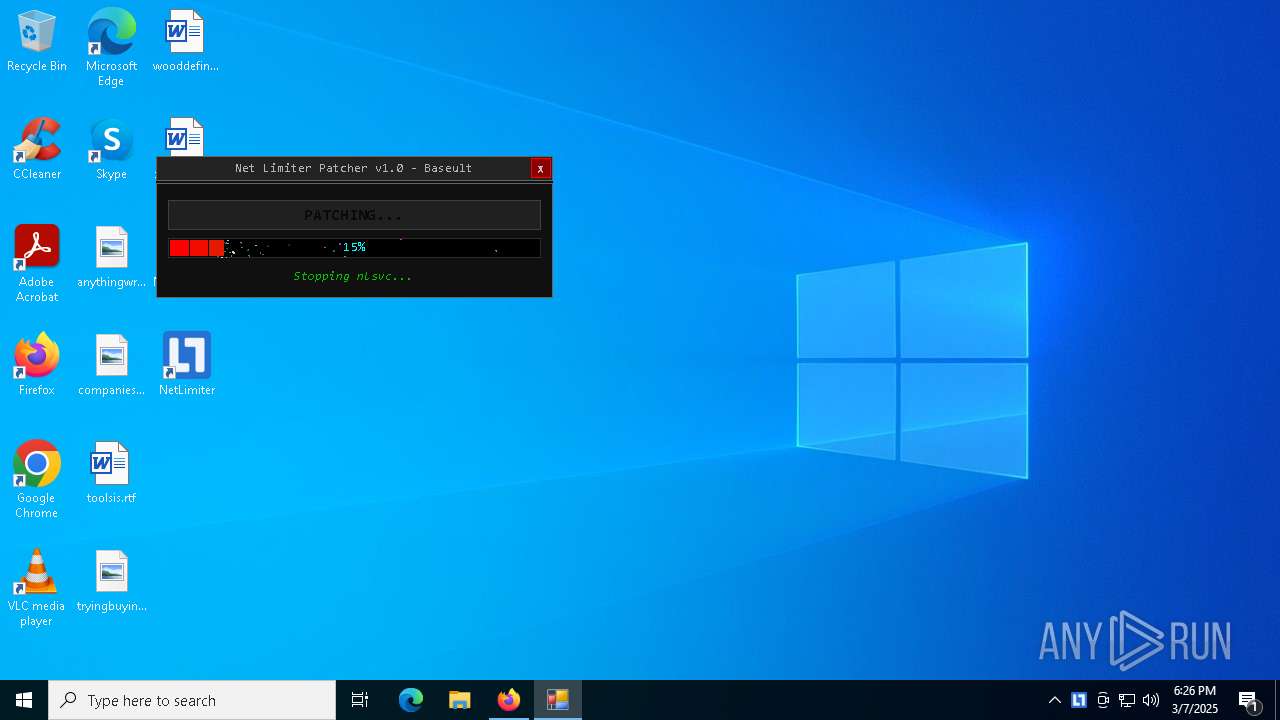
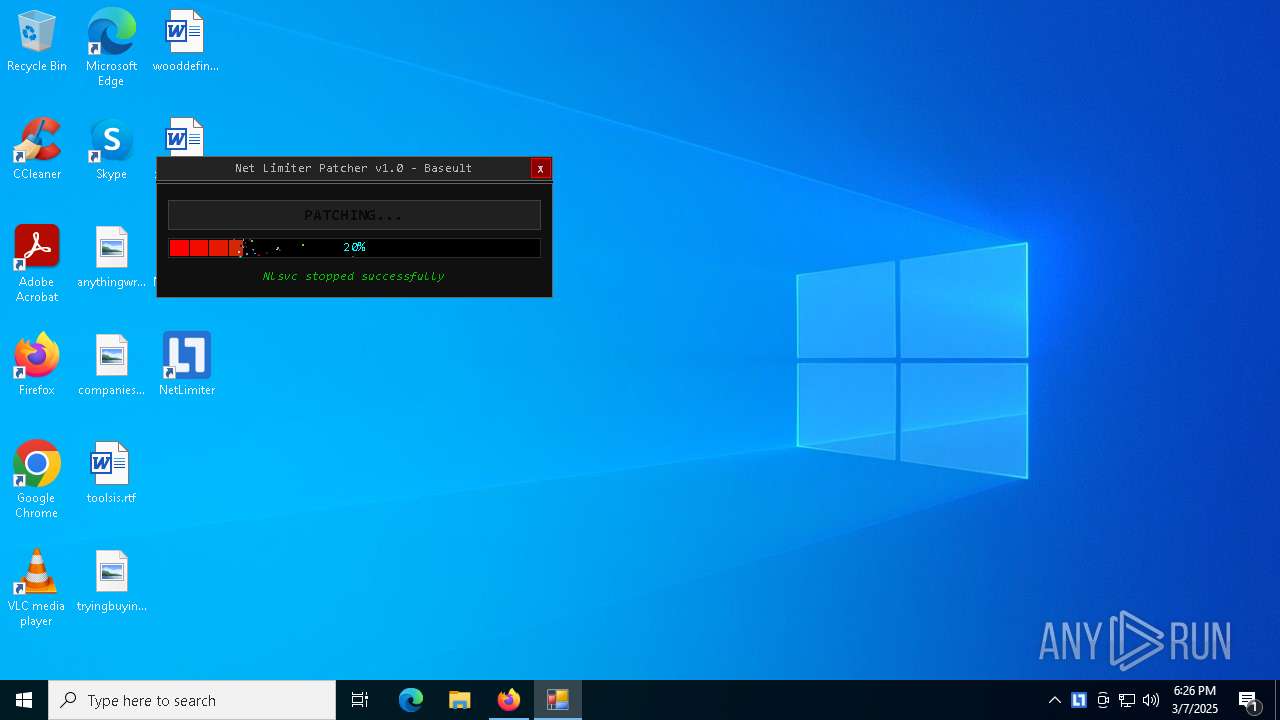
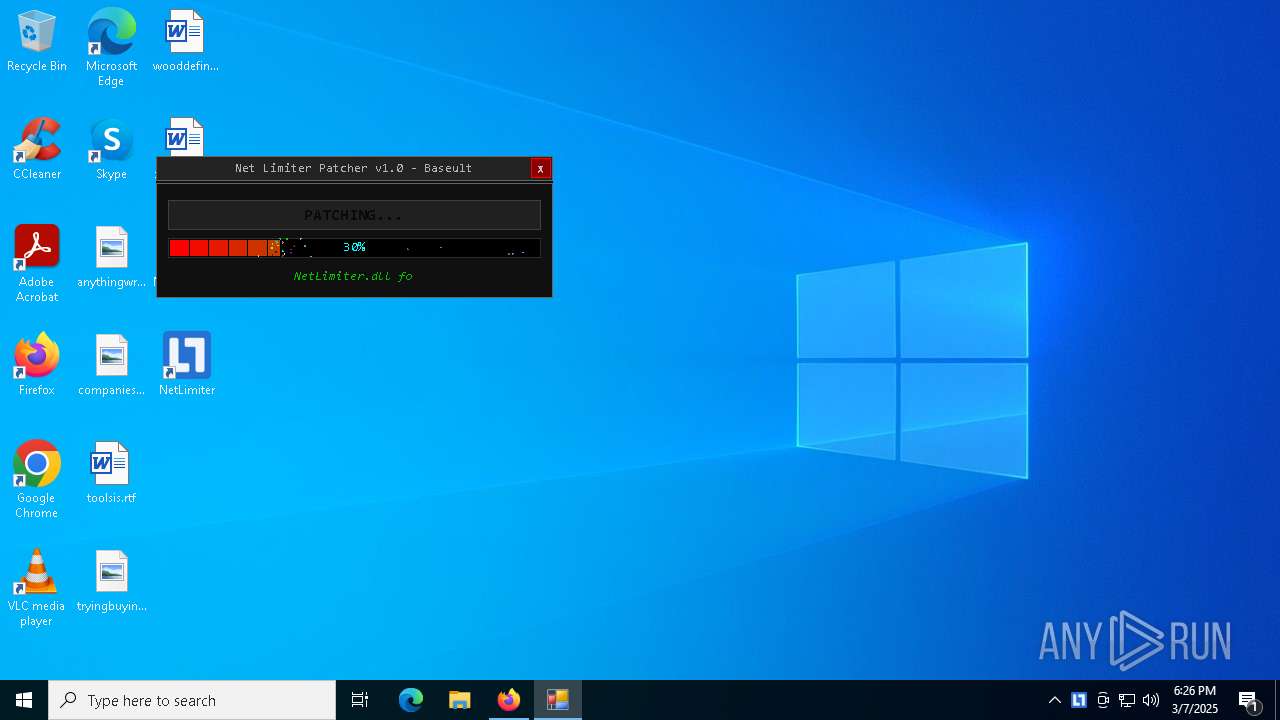
MALICIOUS
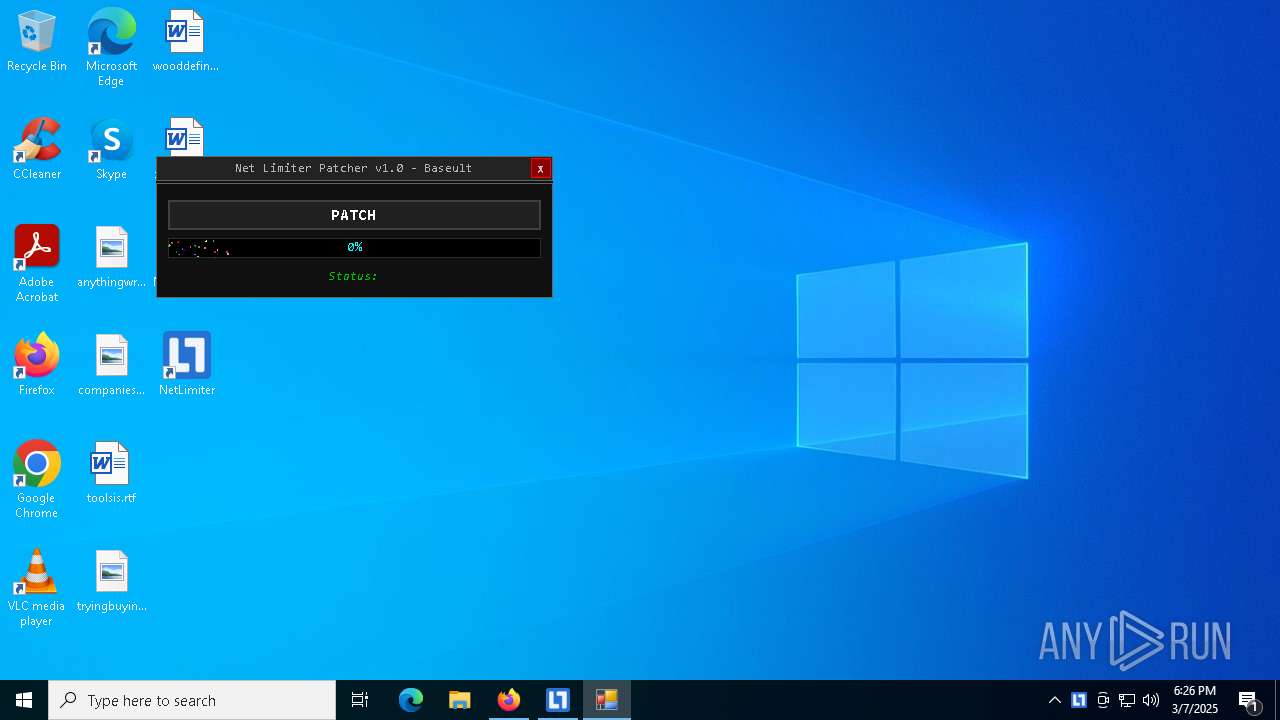
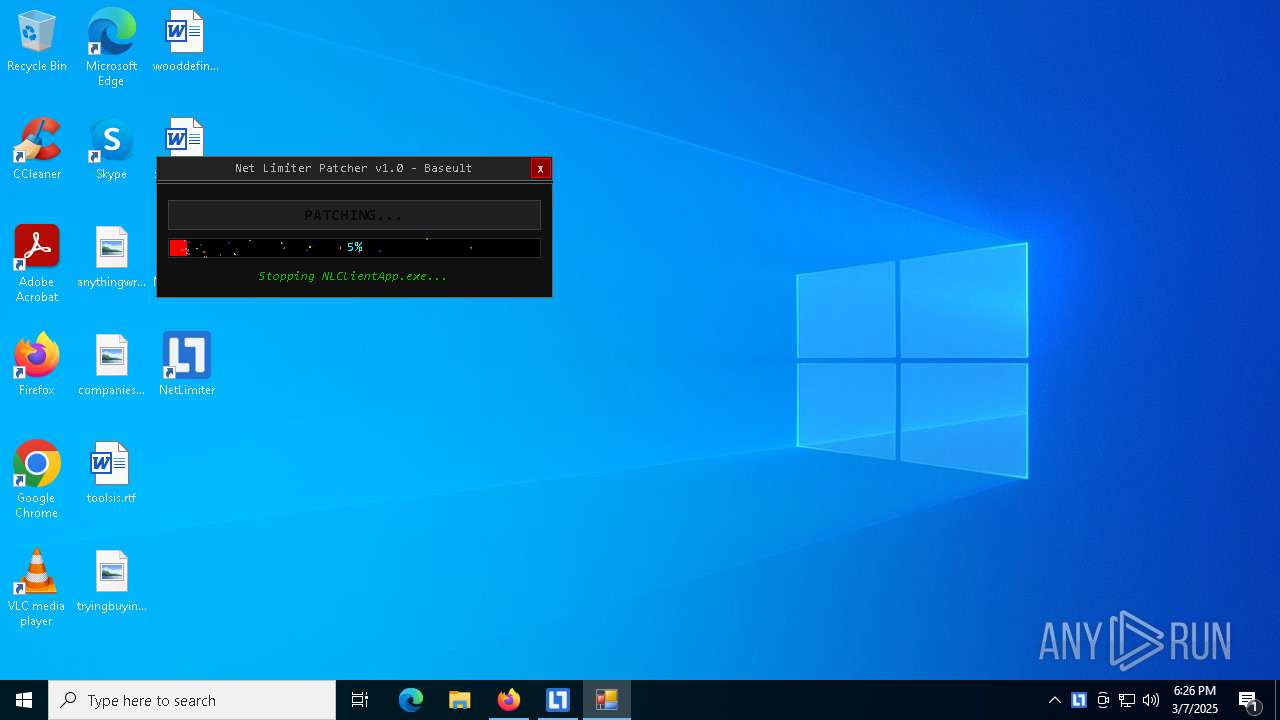
Starts NET.EXE for service management
- NetLimiter.Crack.exe (PID: 2320)
- net.exe (PID: 1188)
- NetLimiter.Crack.exe (PID: 6148)
- net.exe (PID: 9040)
- net.exe (PID: 4436)
Changes the autorun value in the registry
- msiexec.exe (PID: 7472)
SUSPICIOUS
Uses TASKKILL.EXE to kill process
- NetLimiter.Crack.exe (PID: 2320)
- NetLimiter.Crack.exe (PID: 6148)
Reads security settings of Internet Explorer
- NetLimiter.Crack.exe (PID: 2320)
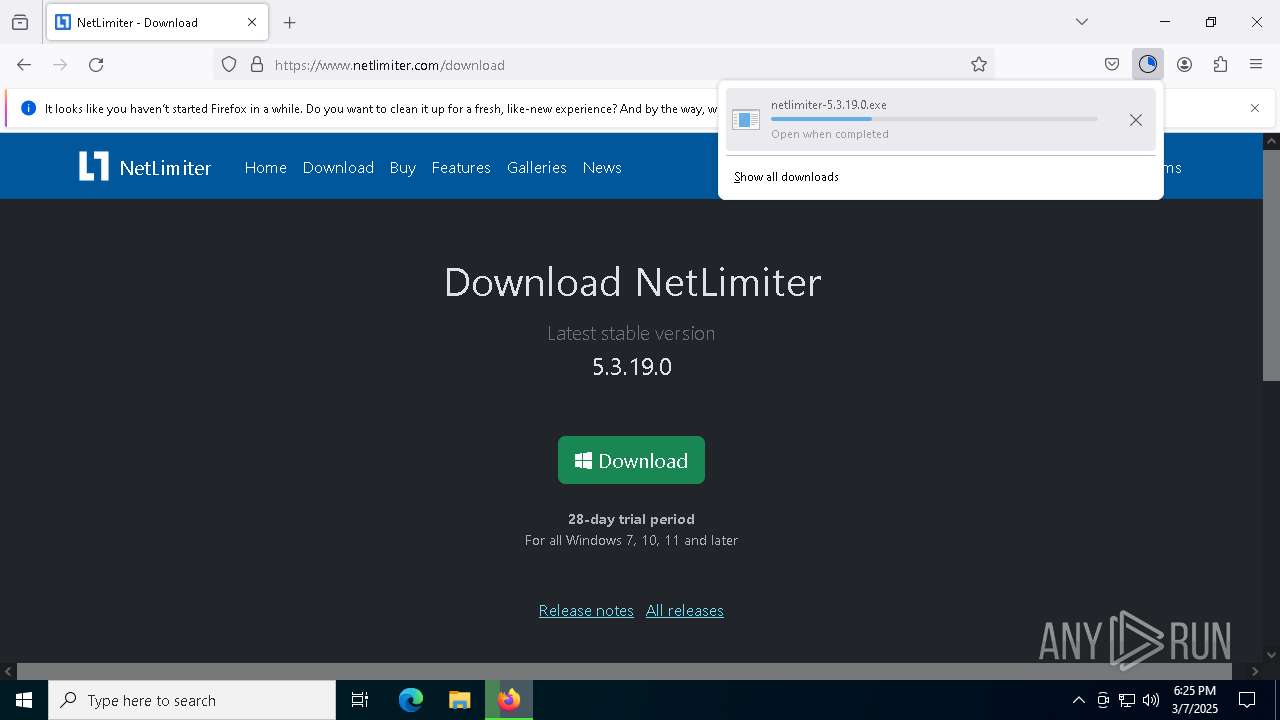
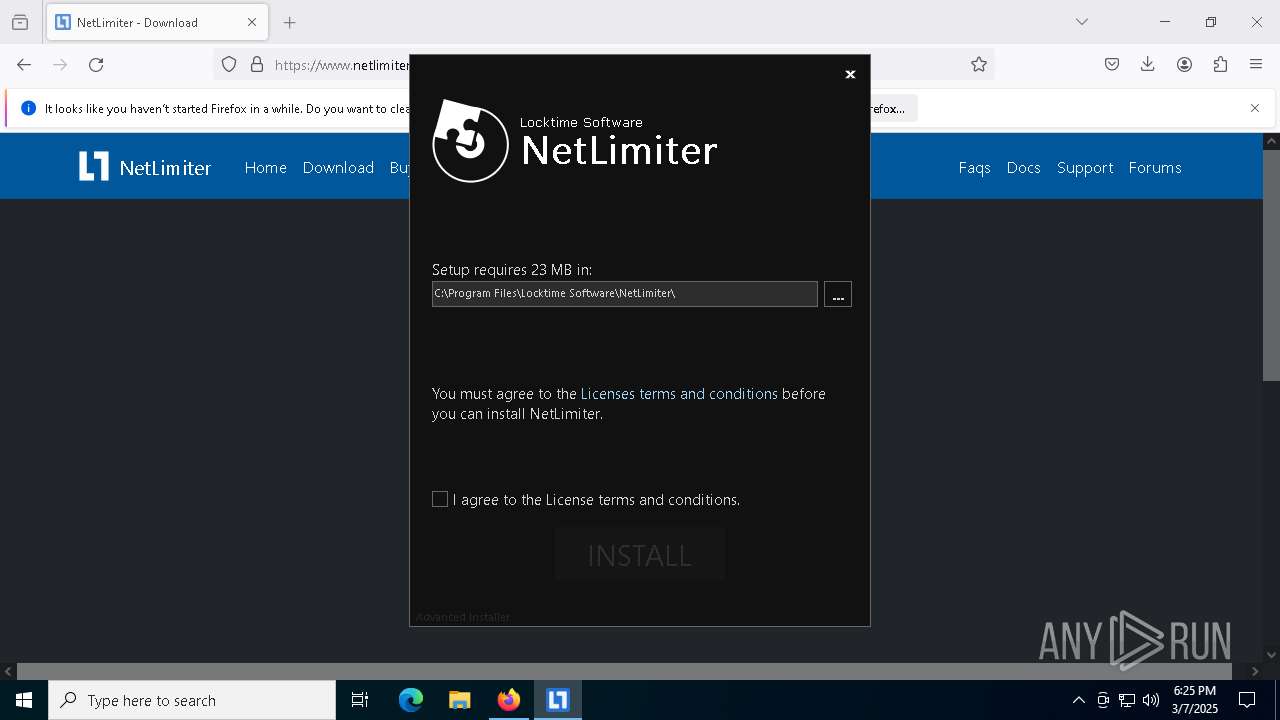
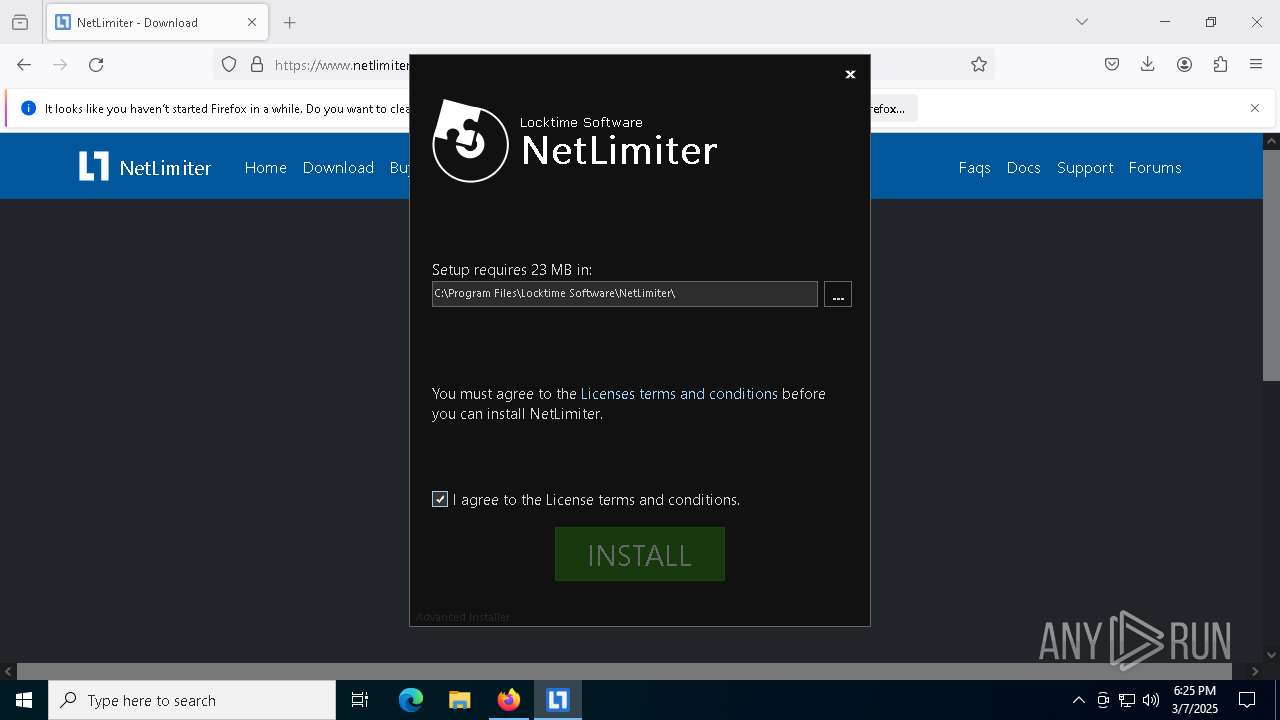
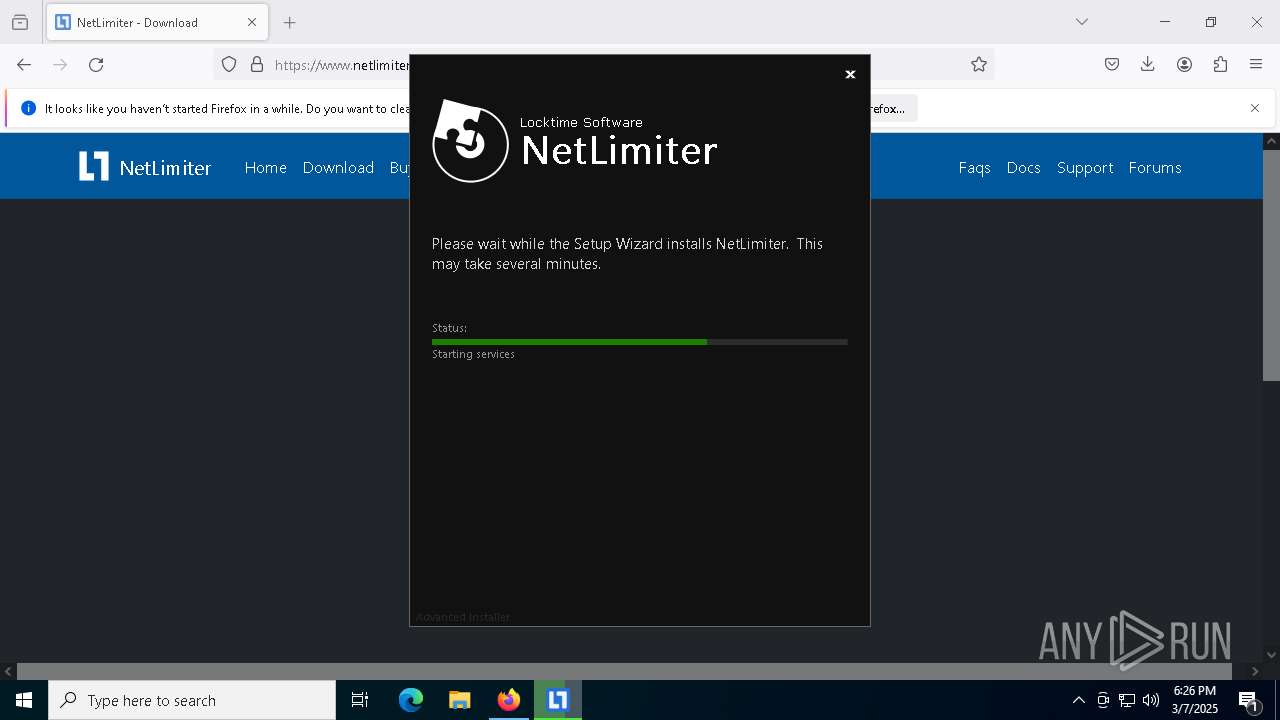
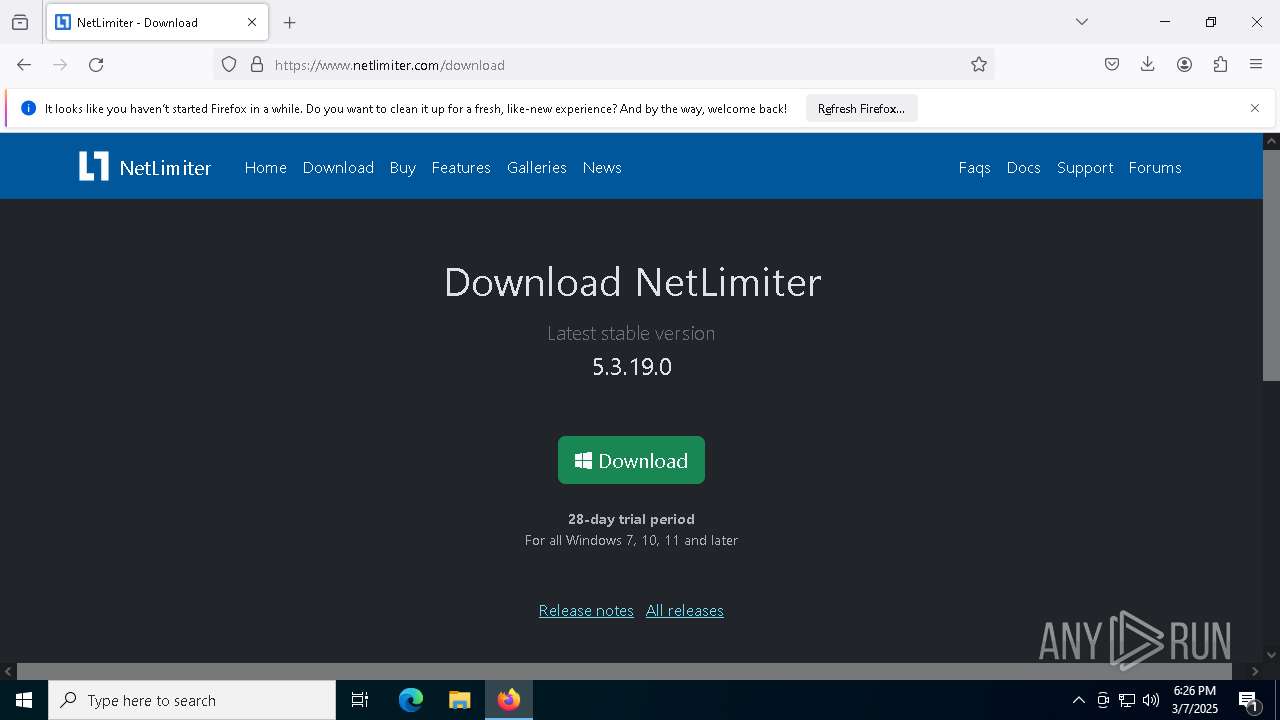
- netlimiter-5.3.19.0.exe (PID: 7600)
- netlimiter-5.3.19.0.exe (PID: 6044)
- NLSvc.exe (PID: 9152)
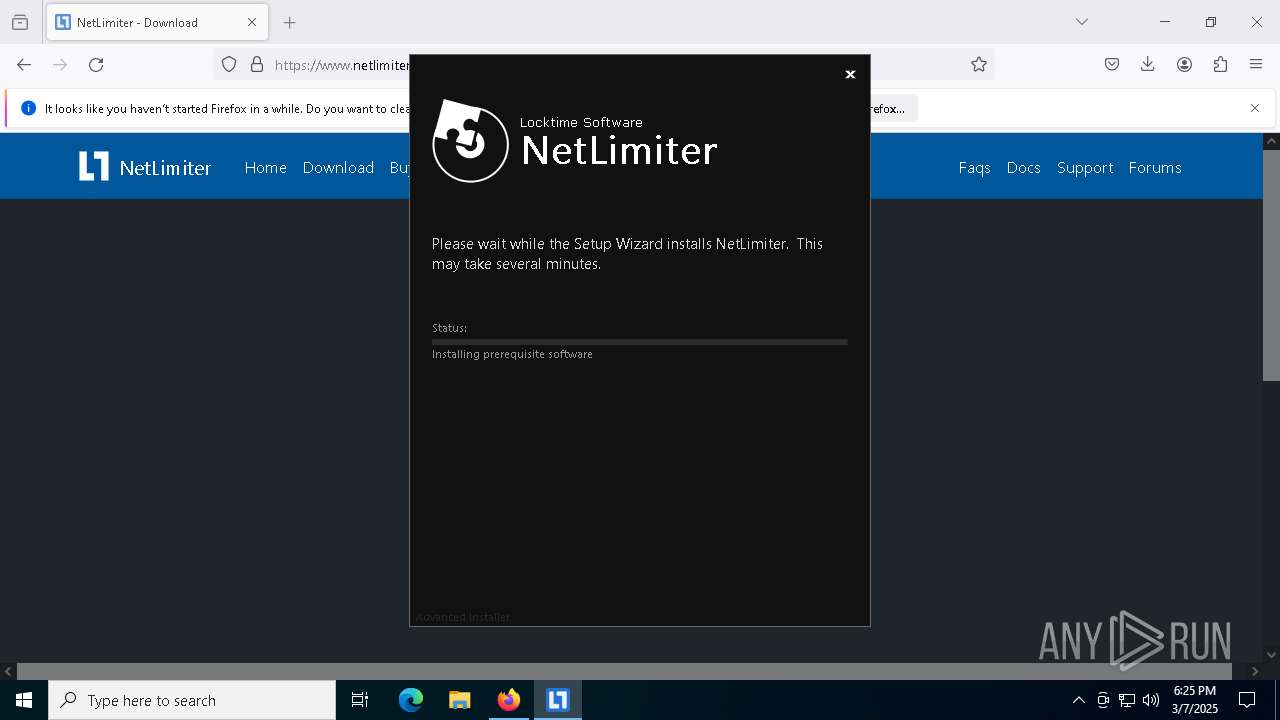
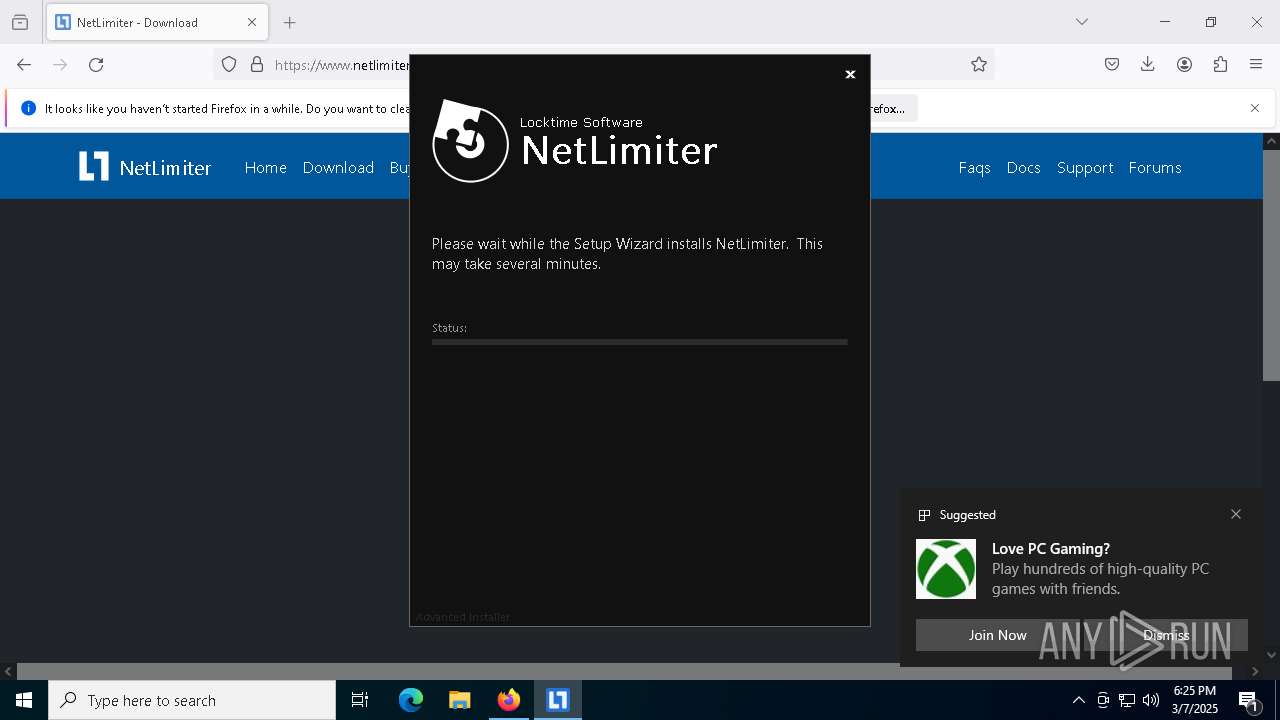
ADVANCEDINSTALLER mutex has been found
- netlimiter-5.3.19.0.exe (PID: 7600)
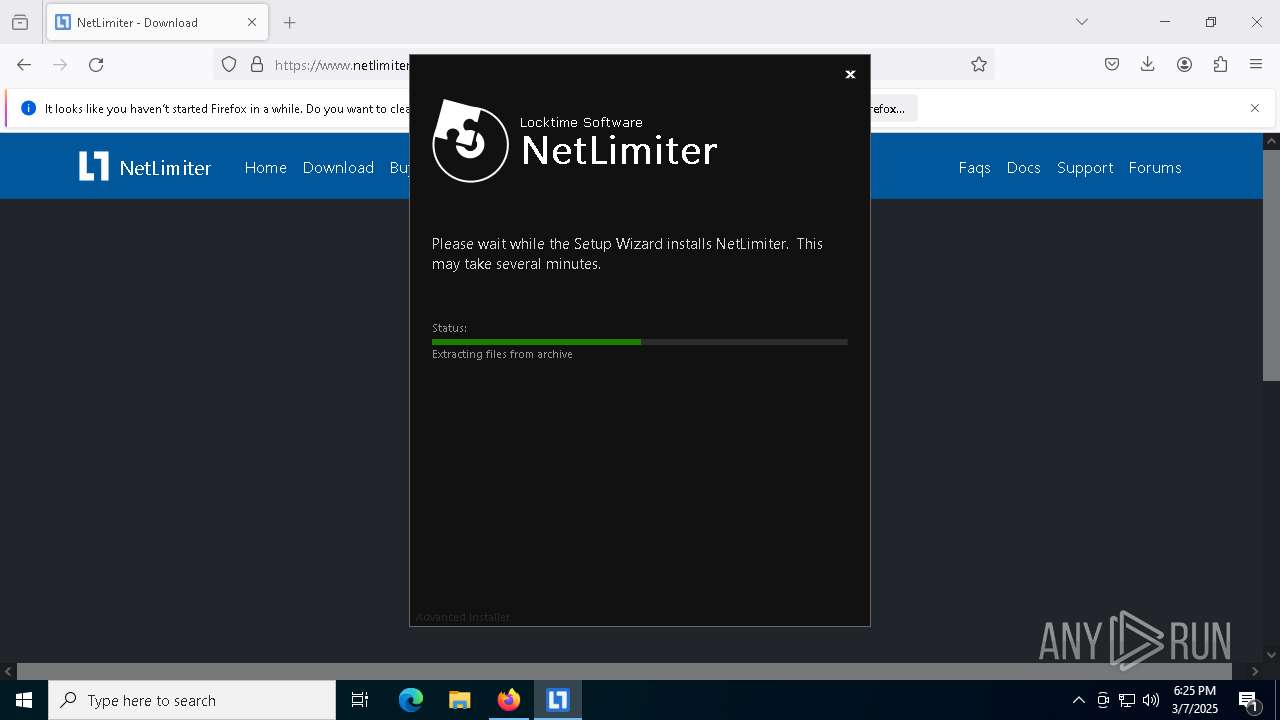
Executable content was dropped or overwritten
- netlimiter-5.3.19.0.exe (PID: 7600)
- netlimiter-5.3.19.0.exe (PID: 6044)
- NetLimiter.Crack.exe (PID: 6148)
Reads the Windows owner or organization settings
- netlimiter-5.3.19.0.exe (PID: 7600)
Process drops legitimate windows executable
- netlimiter-5.3.19.0.exe (PID: 7600)
- msiexec.exe (PID: 2416)
- netlimiter-5.3.19.0.exe (PID: 6044)
- msiexec.exe (PID: 8956)
- msiexec.exe (PID: 7472)
Reads Internet Explorer settings
- netlimiter-5.3.19.0.exe (PID: 7600)
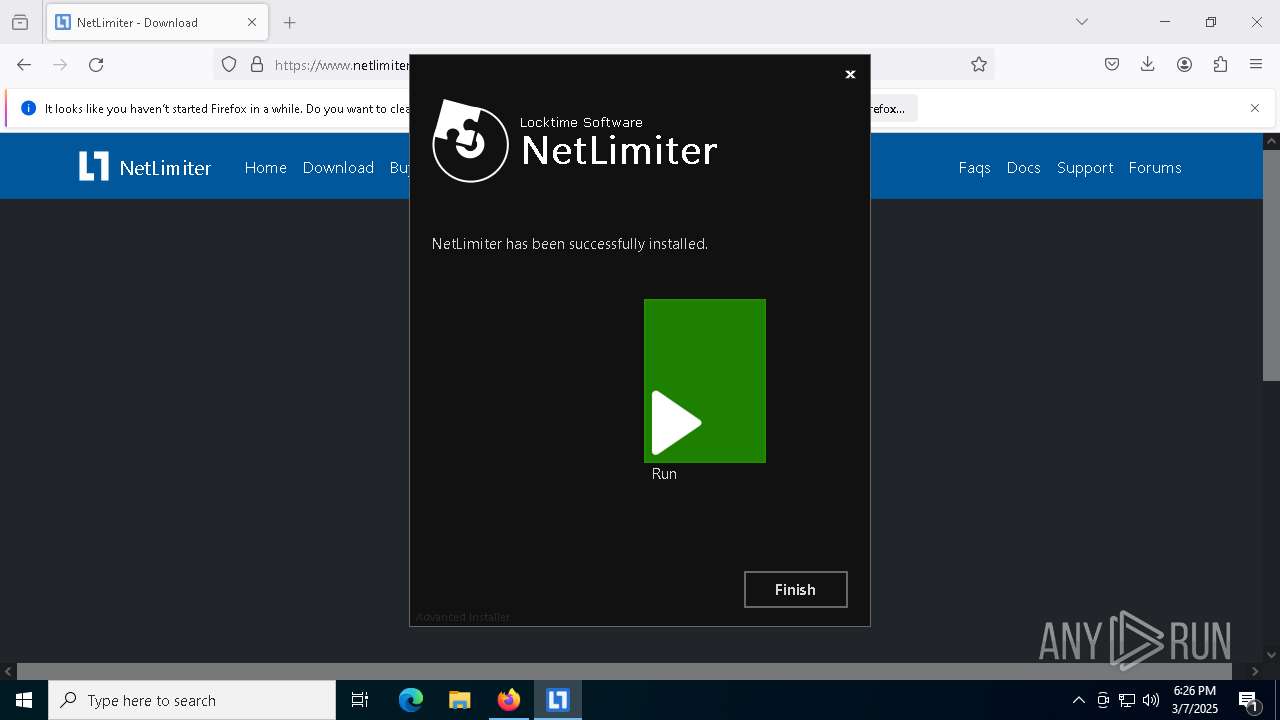
Application launched itself
- netlimiter-5.3.19.0.exe (PID: 7600)
The process drops C-runtime libraries
- msiexec.exe (PID: 2416)
- msiexec.exe (PID: 8956)
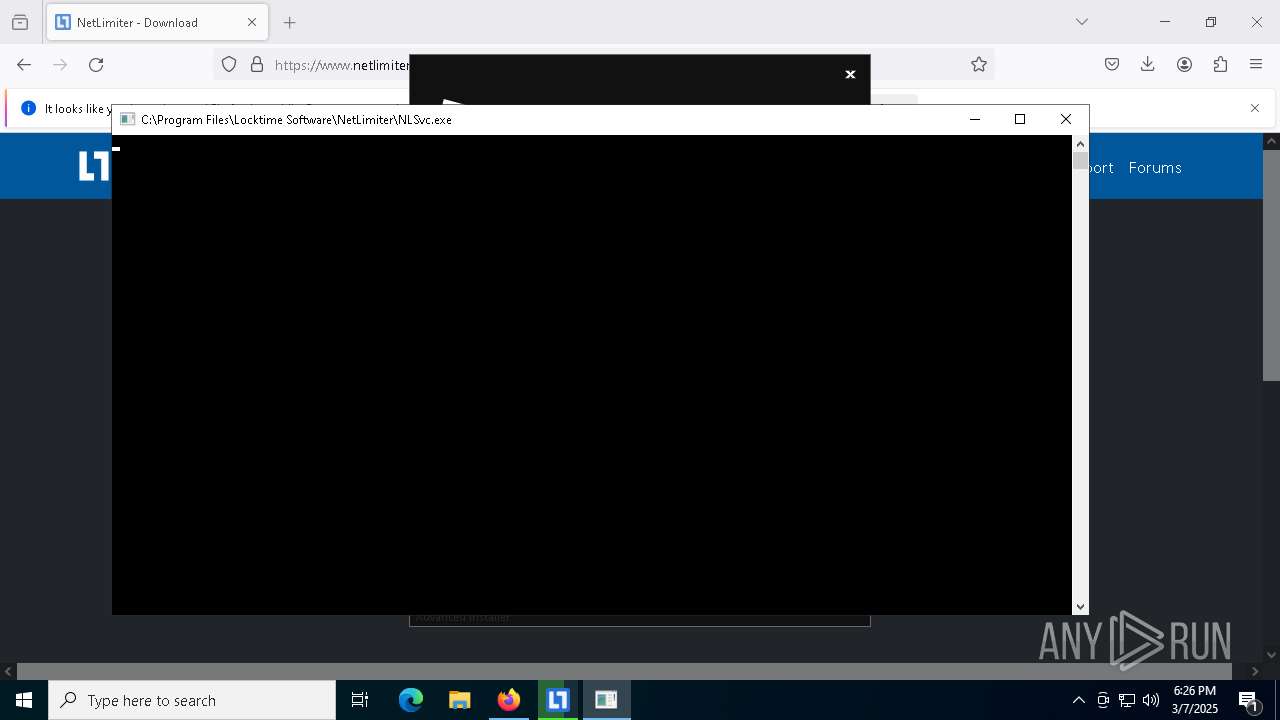
Executes as Windows Service
- VSSVC.exe (PID: 6244)
- NLSvc.exe (PID: 6656)
- NLSvc.exe (PID: 7600)
There is functionality for taking screenshot (YARA)
- netlimiter-5.3.19.0.exe (PID: 7600)
Detects AdvancedInstaller (YARA)
- netlimiter-5.3.19.0.exe (PID: 7600)
- msiexec.exe (PID: 7472)
Drops a system driver (possible attempt to evade defenses)
- netlimiter-5.3.19.0.exe (PID: 7600)
- msiexec.exe (PID: 7472)
INFO
Checks supported languages
- NetLimiter.Crack.exe (PID: 2320)
- netlimiter-5.3.19.0.exe (PID: 7600)
- msiexec.exe (PID: 2416)
- netlimiter-5.3.19.0.exe (PID: 6044)
- msiexec.exe (PID: 7472)
- ShellExperienceHost.exe (PID: 8416)
- NLSvc.exe (PID: 6656)
Reads the computer name
- NetLimiter.Crack.exe (PID: 2320)
- netlimiter-5.3.19.0.exe (PID: 7600)
- msiexec.exe (PID: 2416)
- netlimiter-5.3.19.0.exe (PID: 6044)
- ShellExperienceHost.exe (PID: 8416)
- NLSvc.exe (PID: 9152)
Creates files or folders in the user directory
- BackgroundTransferHost.exe (PID: 1184)
- netlimiter-5.3.19.0.exe (PID: 7600)
Reads the machine GUID from the registry
- NetLimiter.Crack.exe (PID: 2320)
- netlimiter-5.3.19.0.exe (PID: 7600)
- netlimiter-5.3.19.0.exe (PID: 6044)
- msiexec.exe (PID: 7472)
- NLSvc.exe (PID: 9152)
Checks proxy server information
- BackgroundTransferHost.exe (PID: 1184)
- netlimiter-5.3.19.0.exe (PID: 7600)
Reads security settings of Internet Explorer
- BackgroundTransferHost.exe (PID: 5776)
- BackgroundTransferHost.exe (PID: 1764)
- BackgroundTransferHost.exe (PID: 7148)
- BackgroundTransferHost.exe (PID: 6676)
- BackgroundTransferHost.exe (PID: 1184)
Reads the software policy settings
- BackgroundTransferHost.exe (PID: 1184)
- netlimiter-5.3.19.0.exe (PID: 7600)
- slui.exe (PID: 4180)
- msiexec.exe (PID: 7472)
- netlimiter-5.3.19.0.exe (PID: 6044)
- NLSvc.exe (PID: 9152)
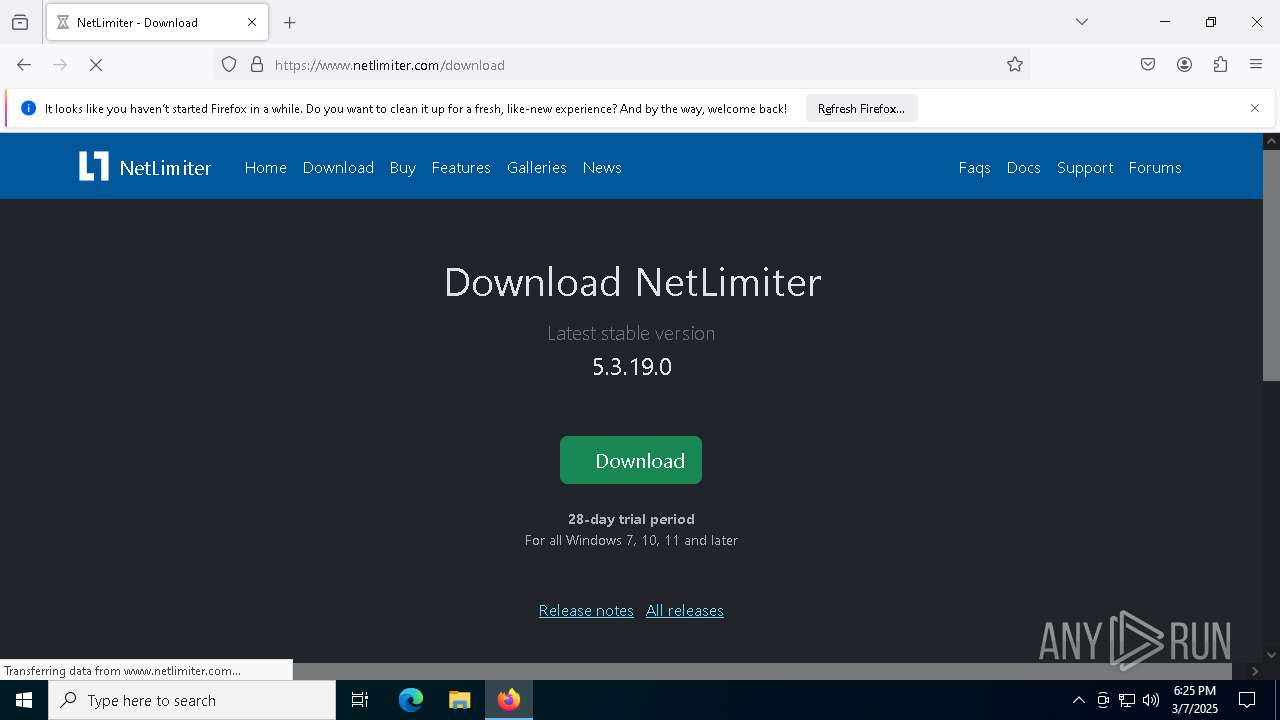
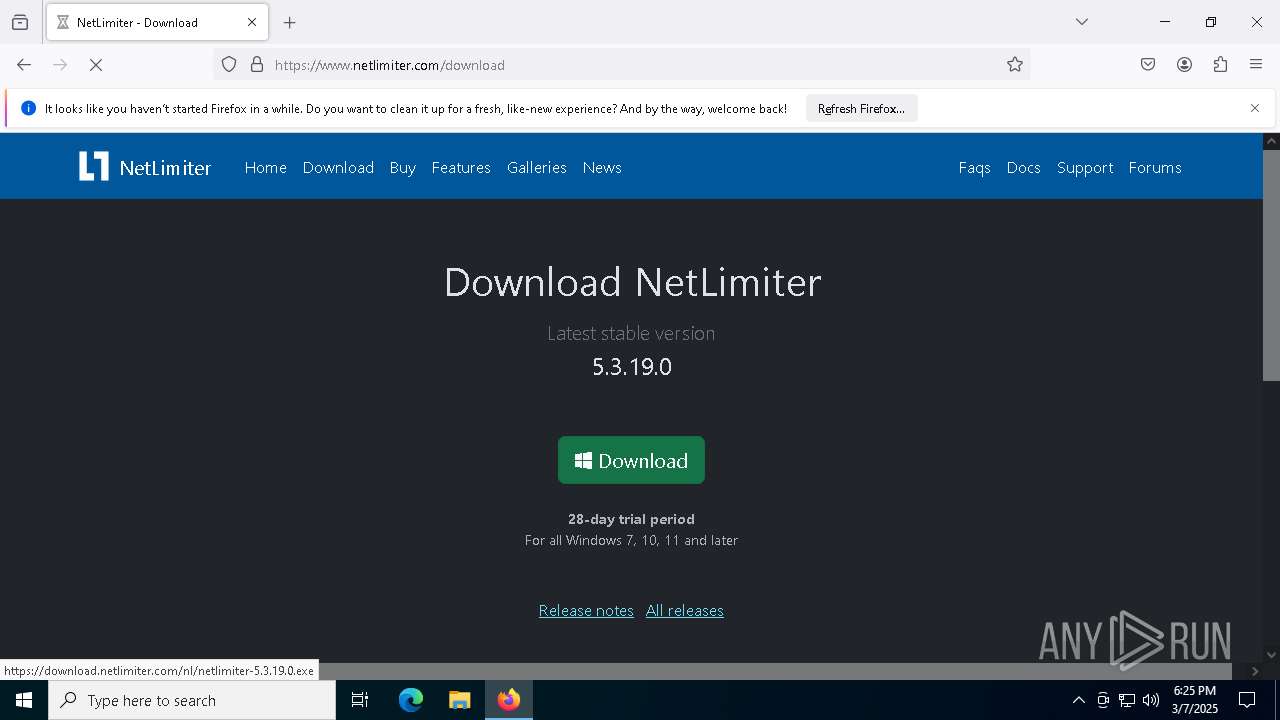
Manual execution by a user
- firefox.exe (PID: 4688)
- NLClientApp.exe (PID: 9168)
- NetLimiter.Crack.exe (PID: 5624)
- NetLimiter.Crack.exe (PID: 6148)
Application launched itself
- firefox.exe (PID: 4688)
- firefox.exe (PID: 4244)
Executable content was dropped or overwritten
- firefox.exe (PID: 4244)
- msiexec.exe (PID: 2416)
- msiexec.exe (PID: 7472)
- msiexec.exe (PID: 8956)
Reads Environment values
- netlimiter-5.3.19.0.exe (PID: 7600)
- msiexec.exe (PID: 2416)
- netlimiter-5.3.19.0.exe (PID: 6044)
The sample compiled with english language support
- netlimiter-5.3.19.0.exe (PID: 7600)
- msiexec.exe (PID: 2416)
- netlimiter-5.3.19.0.exe (PID: 6044)
- msiexec.exe (PID: 8956)
- msiexec.exe (PID: 7472)
Create files in a temporary directory
- netlimiter-5.3.19.0.exe (PID: 7600)
- msiexec.exe (PID: 2416)
- netlimiter-5.3.19.0.exe (PID: 6044)
Manages system restore points
- SrTasks.exe (PID: 8868)
Creates a software uninstall entry
- msiexec.exe (PID: 7472)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2083:02:18 07:48:03+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 48 |
| CodeSize: | 481280 |
| InitializedDataSize: | 5120 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x0000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | - |
| CompanyName: | - |
| FileDescription: | NetLimiter Crack |
| FileVersion: | 1.0.0.0 |
| InternalName: | NetLimiter Crack.exe |
| LegalCopyright: | Copyright © 2024 |
| LegalTrademarks: | - |
| OriginalFileName: | NetLimiter Crack.exe |
| ProductName: | NetLimiter Crack |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Total processes
204
Monitored processes
56
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 720 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2152 -parentBuildID 20240213221259 -prefsHandle 2144 -prefMapHandle 2132 -prefsLen 31031 -prefMapSize 244583 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {d1f022f0-e9b3-45ed-9bd9-aced3909fb08} 4244 "\\.\pipe\gecko-crash-server-pipe.4244" 1dc1f181310 socket | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 744 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 872 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1184 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "net" stop nlsvc | C:\Windows\System32\net.exe | — | NetLimiter.Crack.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | "BackgroundTransferHost.exe" -ServerName:BackgroundTransferHost.1 | C:\Windows\System32\BackgroundTransferHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Download/Upload Host Exit code: 1 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2236 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1912 -parentBuildID 20240213221259 -prefsHandle 1840 -prefMapHandle 1832 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {248de508-6098-4f8b-8a7e-ac29e500895c} 4244 "\\.\pipe\gecko-crash-server-pipe.4244" 1dc2bfeb710 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 2320 | "C:\Users\admin\AppData\Local\Temp\NetLimiter.Crack.exe" | C:\Users\admin\AppData\Local\Temp\NetLimiter.Crack.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: NetLimiter Crack Exit code: 1 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2416 | C:\Windows\syswow64\MsiExec.exe -Embedding E44D5FBD1DA50738956C4E17E5ED48ED C | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
57 487
Read events
56 918
Write events
540
Delete events
29
Modification events
| (PID) Process: | (5776) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (5776) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (5776) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1764) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1764) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1764) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1184) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1184) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1184) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7148) BackgroundTransferHost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\CurrentVersion\AppContainer\Storage\microsoft.windows.contentdeliverymanager_cw5n1h2txyewy\Internet Settings\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
Executable files
511
Suspicious files
255
Text files
155
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1184 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\4dce4c53-dd5b-4346-a0af-52ea59977f45.down_data | — | |
MD5:— | SHA256:— | |||
| 4244 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4244 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 1184 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\MetaData\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:B78E0E58B1FB5BDD6467DEA3E05365E5 | SHA256:8291DBBDADD29A6B0255B6B7BD9C31FD093DE7CA78ED277D6C5C4EC001131FBC | |||
| 1184 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\Microsoft\CryptnetUrlCache\Content\26C212D9399727259664BDFCA073966E_F9F7D6A7ECE73106D2A8C63168CDA10D | binary | |
MD5:7C48C30BA63B689902BB426C7A0DDC09 | SHA256:32716D5FC0139B83464450DC3B8550672E5530480DCA1050D2606F95DFDF67EB | |||
| 1184 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\8e3ac5d8-91b6-4d79-b449-b277b7fd2682.5cdd3d09-4315-4cd6-8847-5a620bf201f3.down_meta | binary | |
MD5:145DE145C540ADFFD0127A77CCA1DC6A | SHA256:288C5E716F3E5B5AF43DE711C84A6CB30E487AF41D7B997E09009D86EBC8F3D9 | |||
| 1184 | BackgroundTransferHost.exe | C:\Users\admin\AppData\Local\Packages\Microsoft.Windows.ContentDeliveryManager_cw5n1h2txyewy\AC\BackgroundTransferApi\8e3ac5d8-91b6-4d79-b449-b277b7fd2682.up_meta_secure | binary | |
MD5:650D4E5D5A1D079C3A4DD290109BF631 | SHA256:D528D1287C696BF344B7F9B0C18E54A304BBB360218DACFB2D12669C974EB73E | |||
| 4244 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 4244 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 4244 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
144
DNS requests
154
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4244 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://o.pki.goog/we2 | US | binary | 280 b | whitelisted |
4244 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://o.pki.goog/s/wr3/UTA | US | binary | 471 b | whitelisted |
4244 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://o.pki.goog/we2 | US | binary | 278 b | whitelisted |
4244 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://o.pki.goog/we2 | US | binary | 278 b | whitelisted |
4244 | firefox.exe | POST | 200 | 142.250.185.163:80 | http://o.pki.goog/we2 | US | binary | 280 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
672 | backgroundTaskHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | DE | binary | 471 b | whitelisted |
856 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
856 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
1184 | BackgroundTransferHost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 312 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 40.115.3.253:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 20.190.159.73:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
672 | backgroundTaskHost.exe | 20.74.47.205:443 | arc.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
672 | backgroundTaskHost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1184 | BackgroundTransferHost.exe | 104.126.37.163:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
arc.msn.com |
| whitelisted |
www.bing.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |