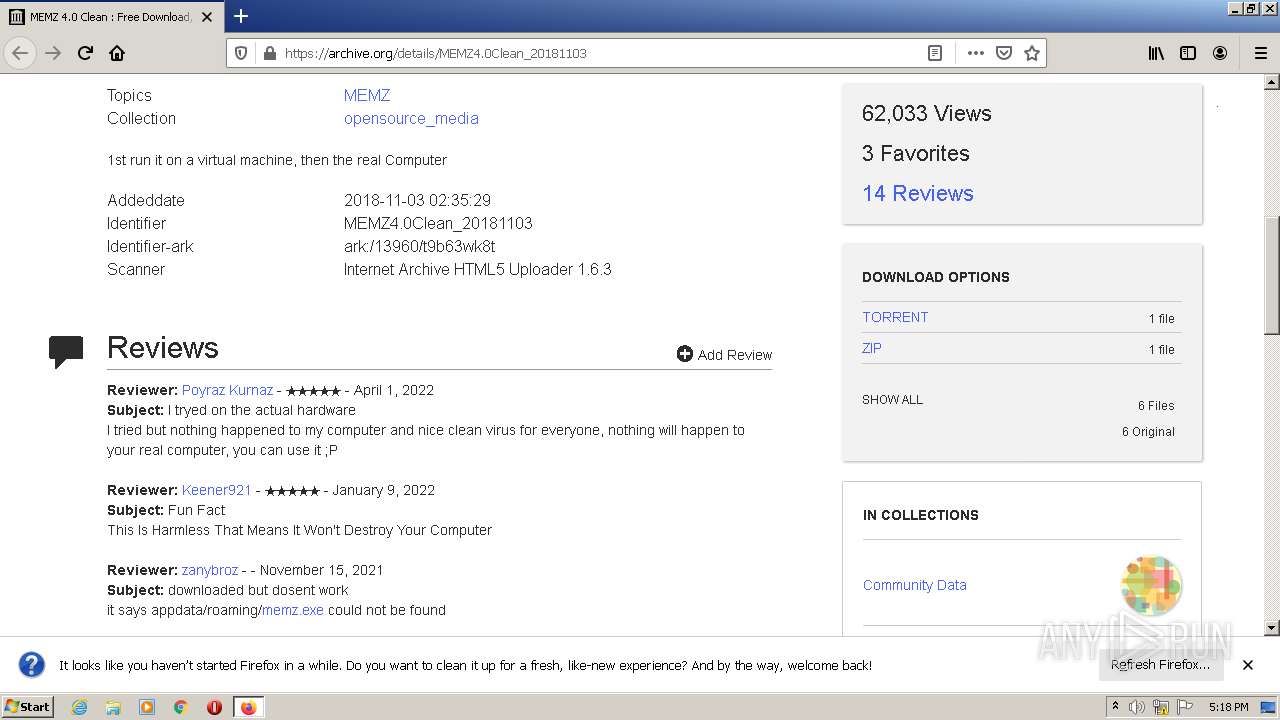
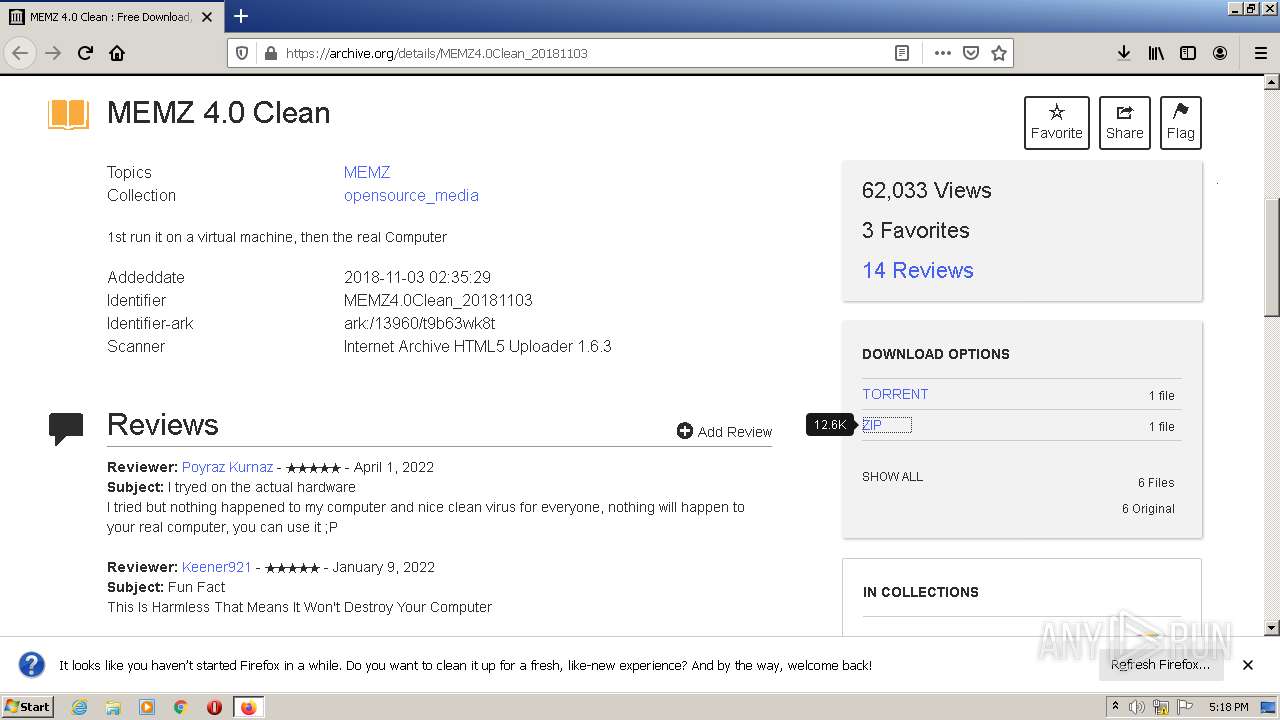
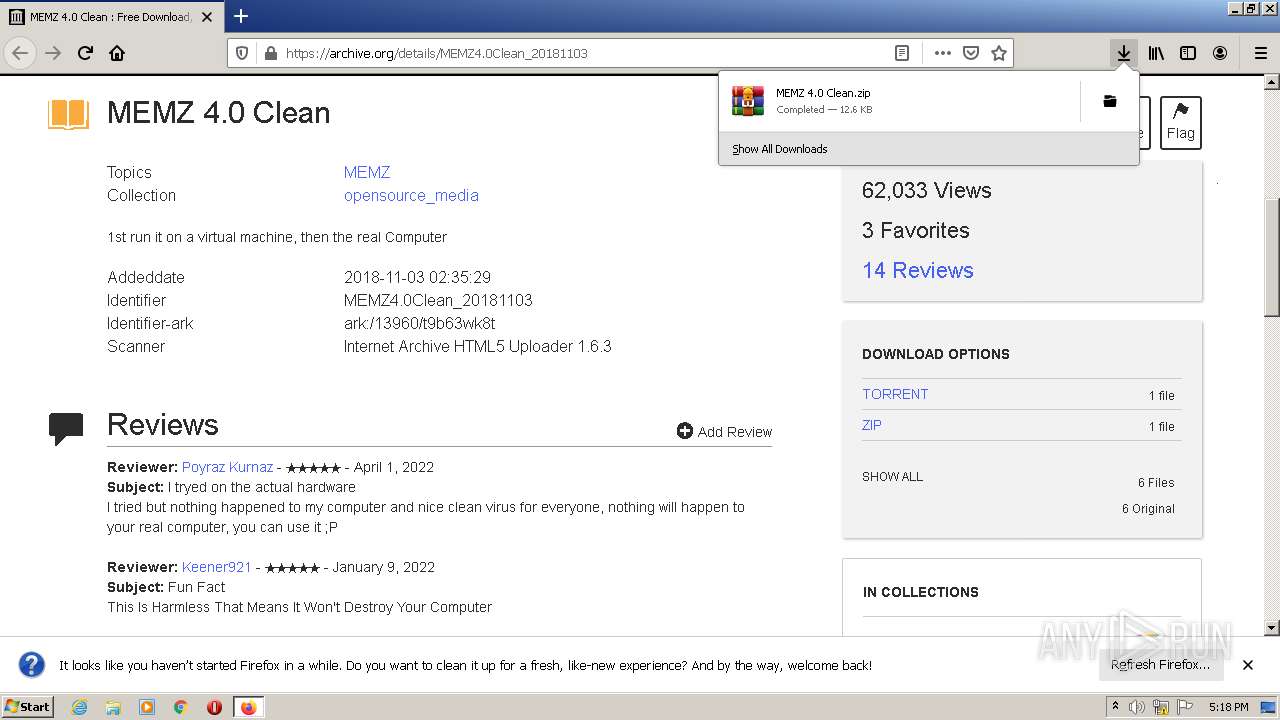
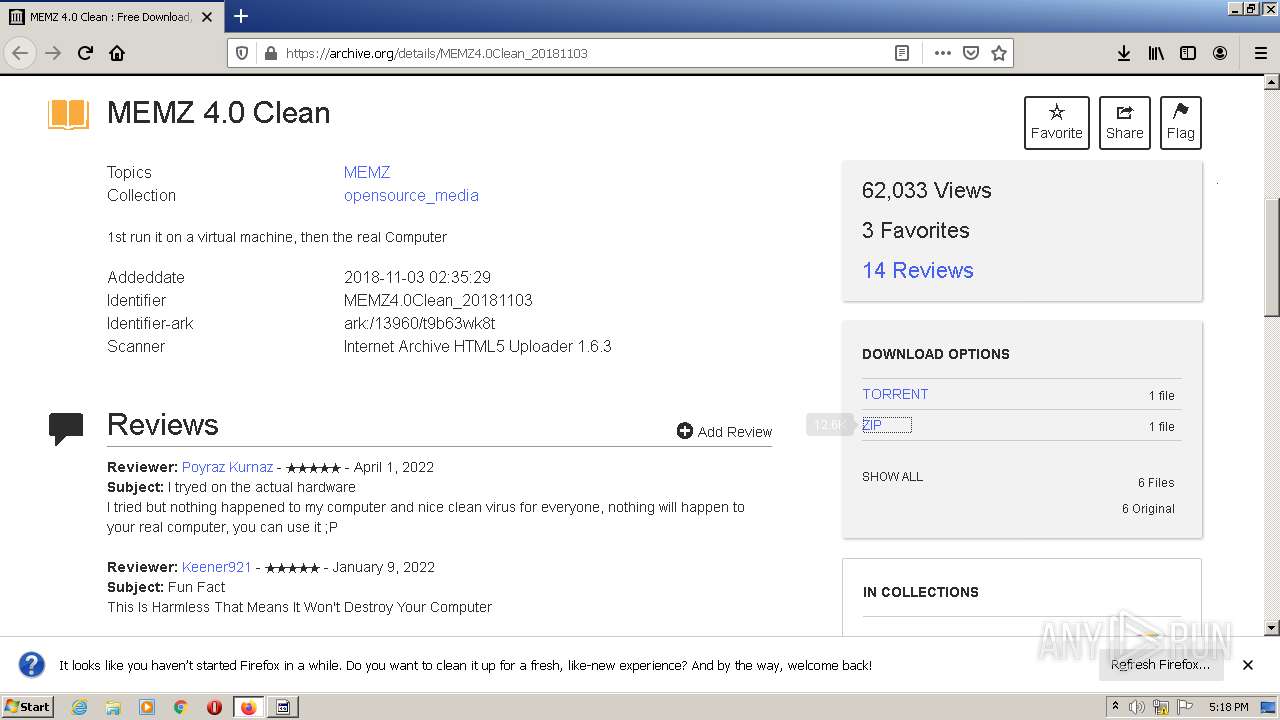
| URL: | https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=&cad=rja&uact=8&ved=2ahUKEwiK7Y-sn8b3AhXCJkQIHV8ABuUQFnoECAMQAQ&url=https%3A%2F%2Farchive.org%2Fdetails%2FMEMZ4.0Clean_20181103&usg=AOvVaw3fZvyxiPtOvz66R0xNMJgN |
| Full analysis: | https://app.any.run/tasks/60986cf5-7af2-418b-bc64-840d3139e9a3 |
| Verdict: | Malicious activity |
| Analysis date: | May 04, 2022, 16:17:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 52E5980B2E77F150A424EAE4200369FE |
| SHA1: | 659060305B1D481E33178DF7E737B618D0FD7D64 |
| SHA256: | 6E8D7DEC27168D3EA327D80E787A12E7862EC2590E11822B36FD3D2D6F4F4778 |
| SSDEEP: | 6:2OLI2sq+wp1w4pNpnLOJYNRR3z+XLXUmZ8d5Sjf2Cr:2V2JnNVLOJY5yXz58d5jo |
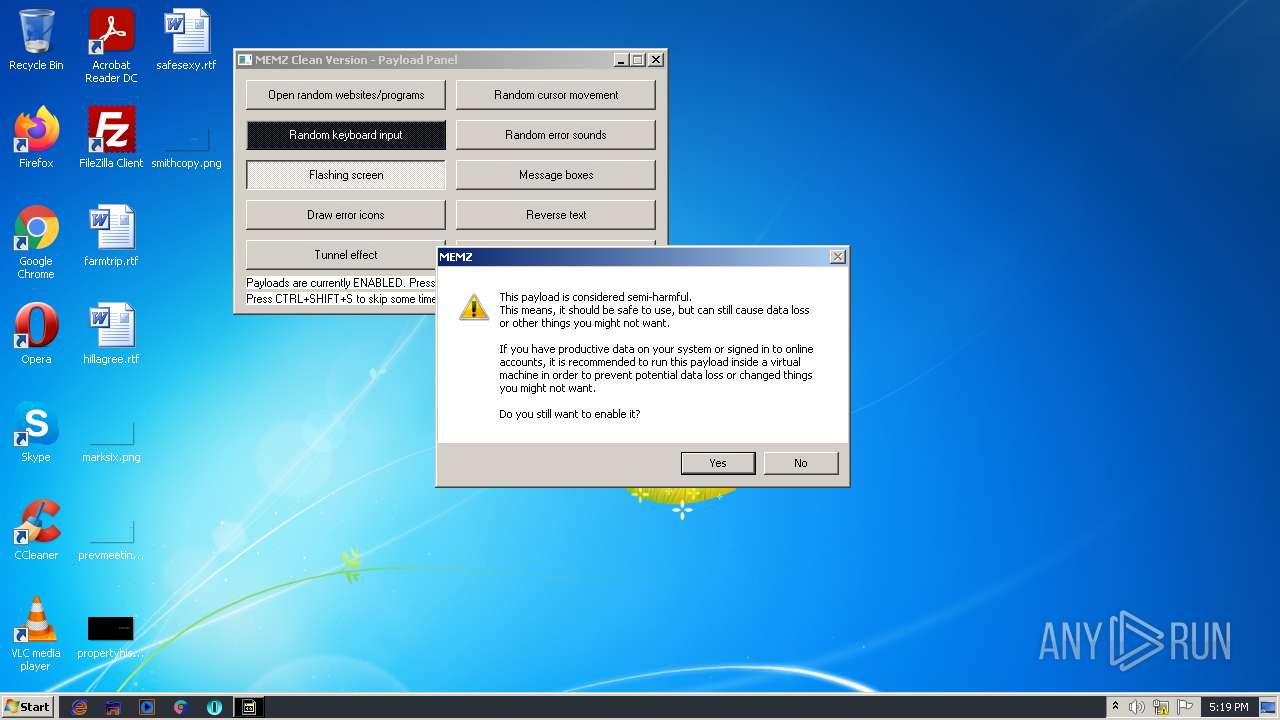
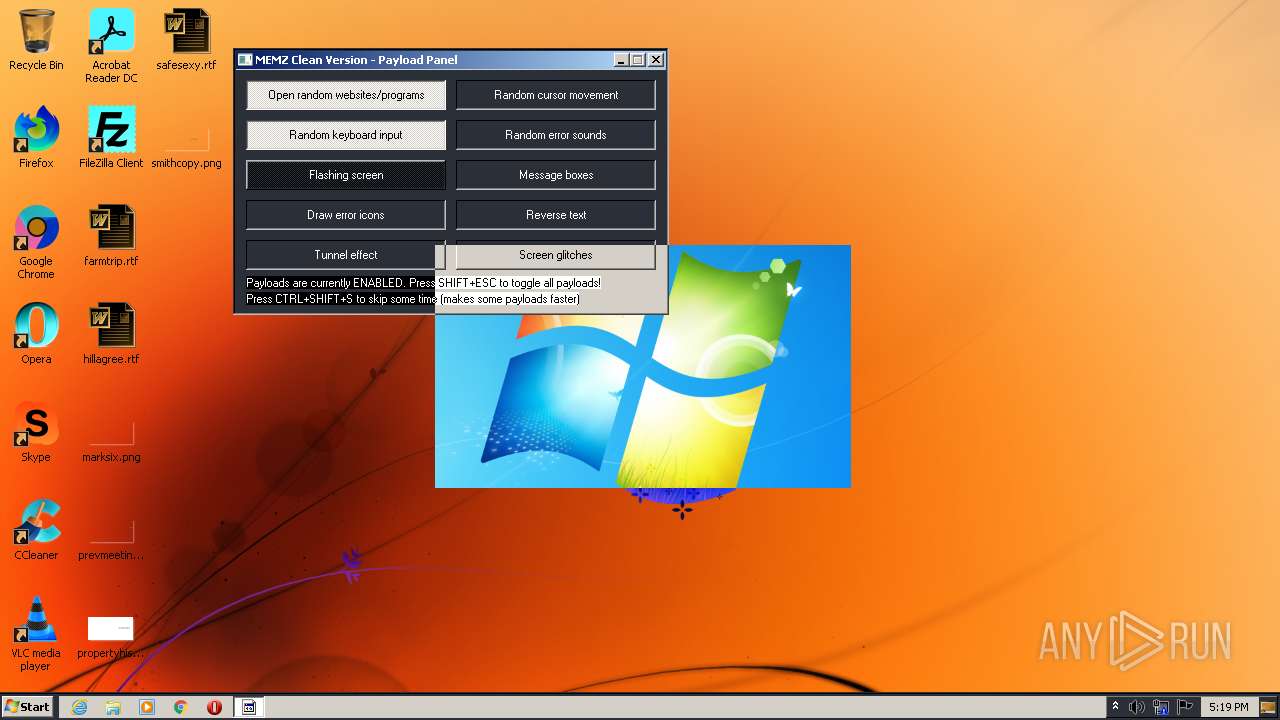
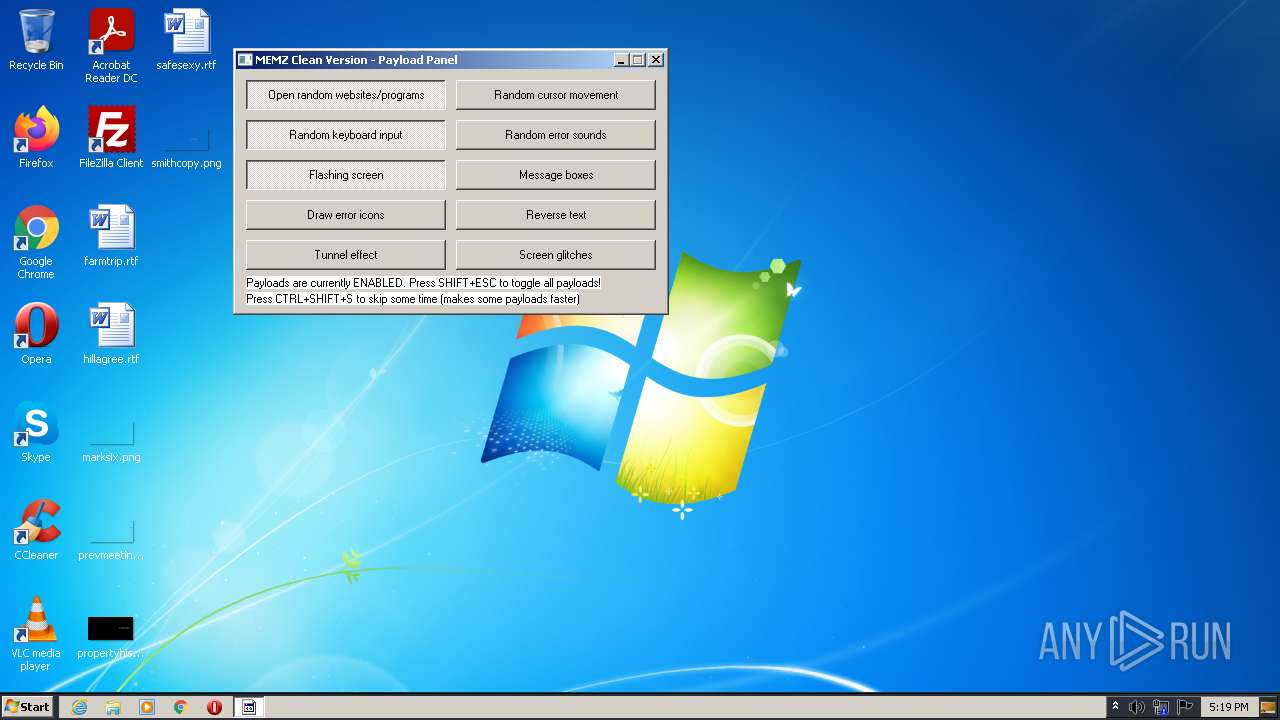
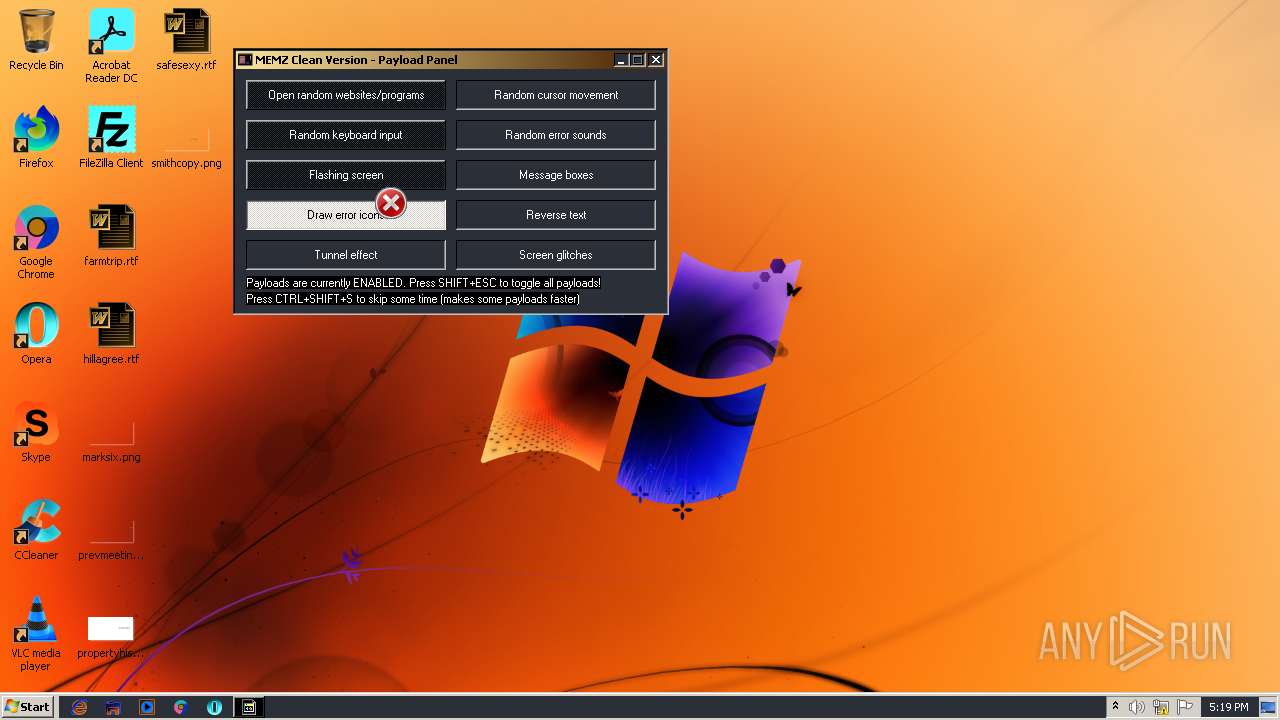
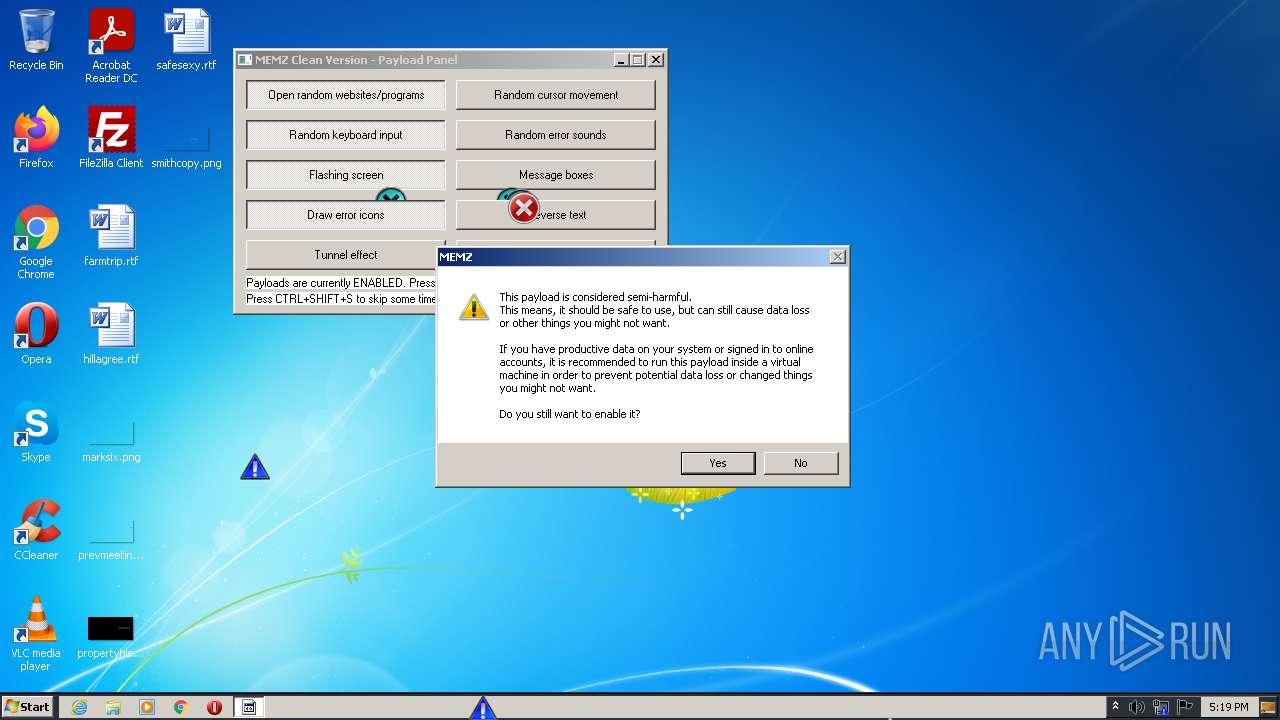
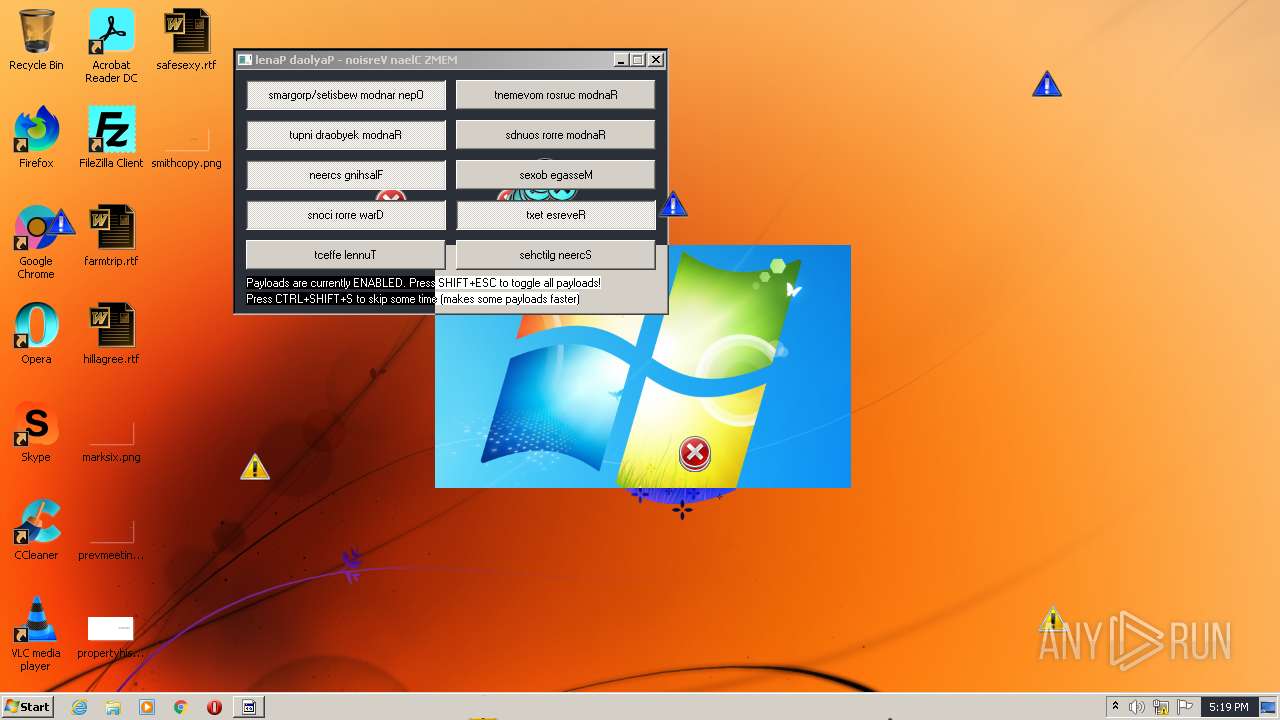
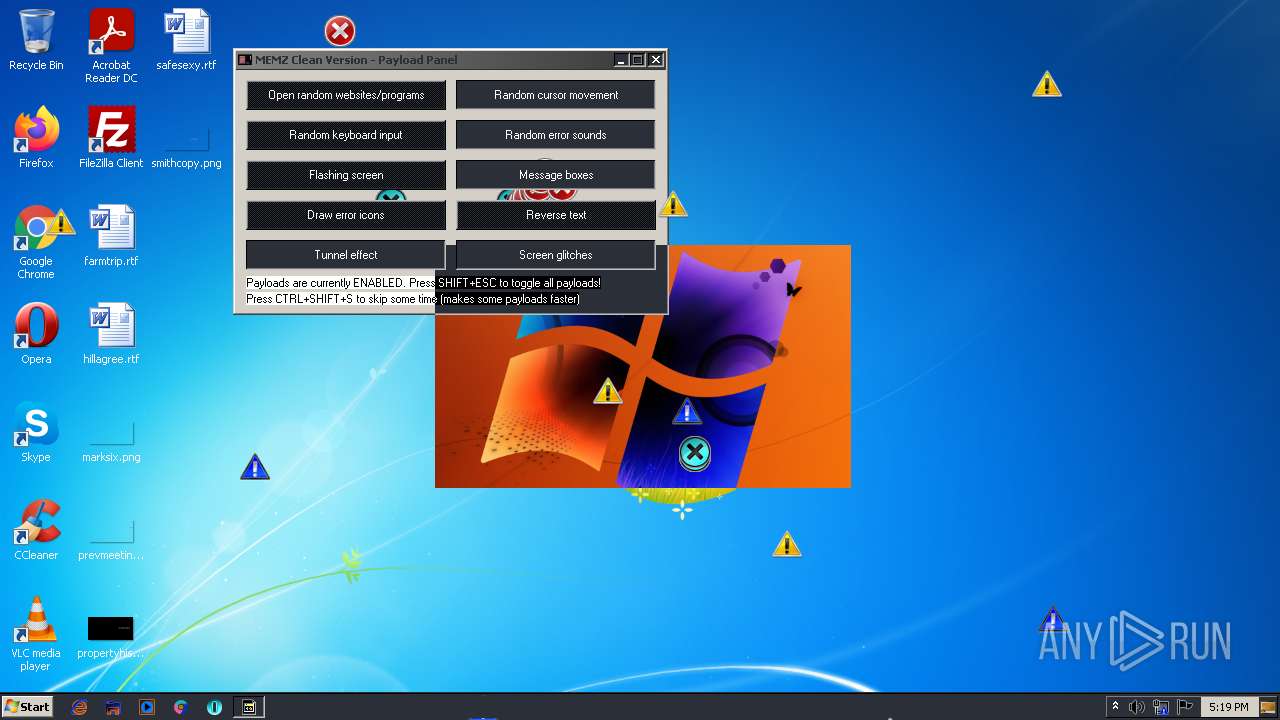
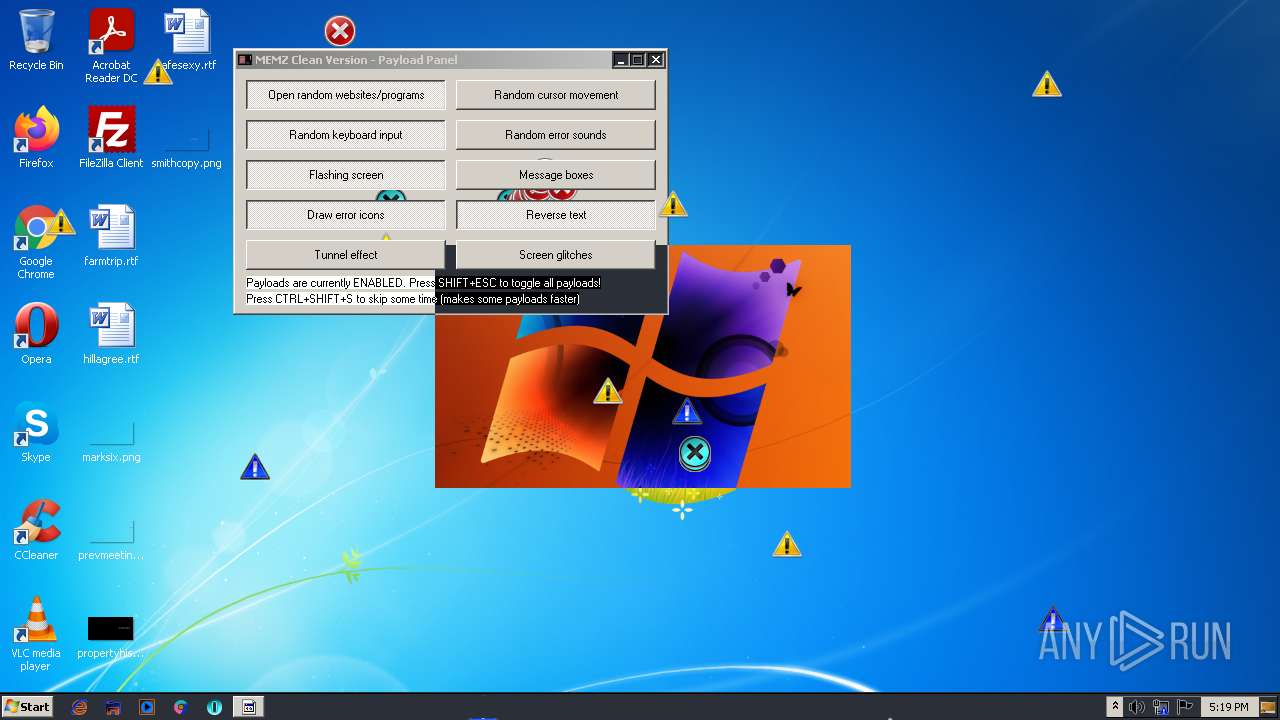
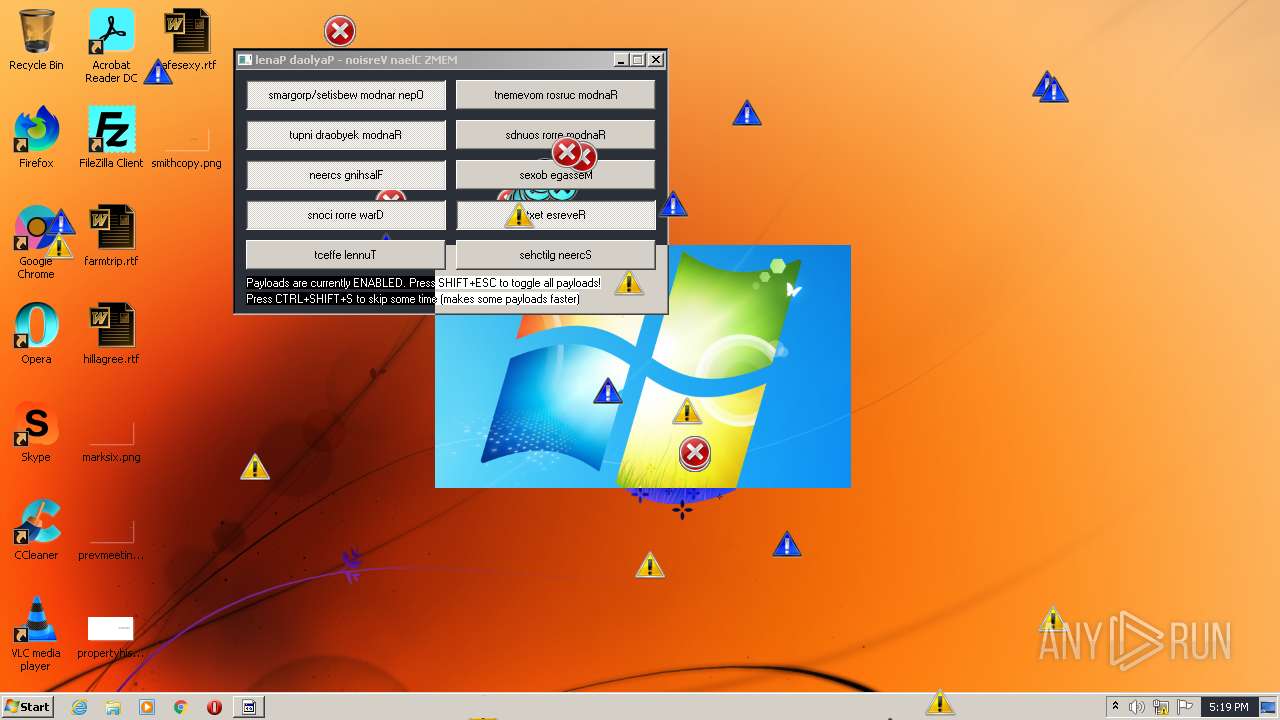
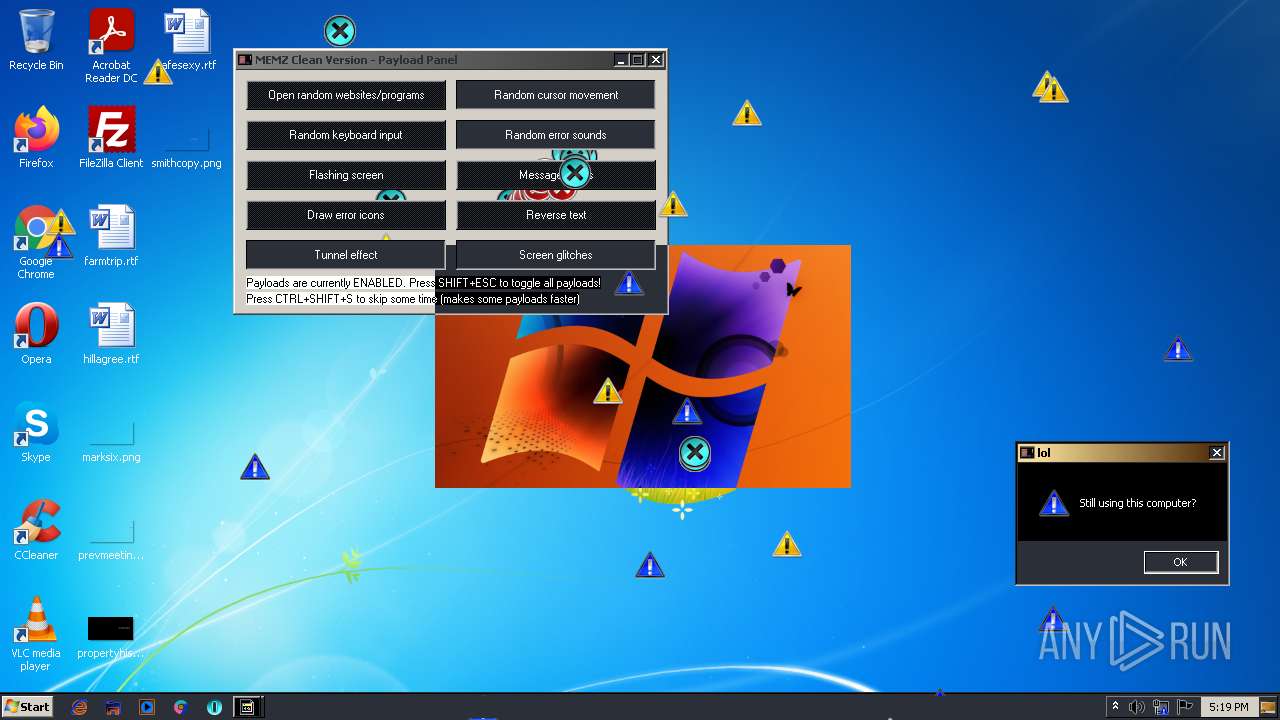
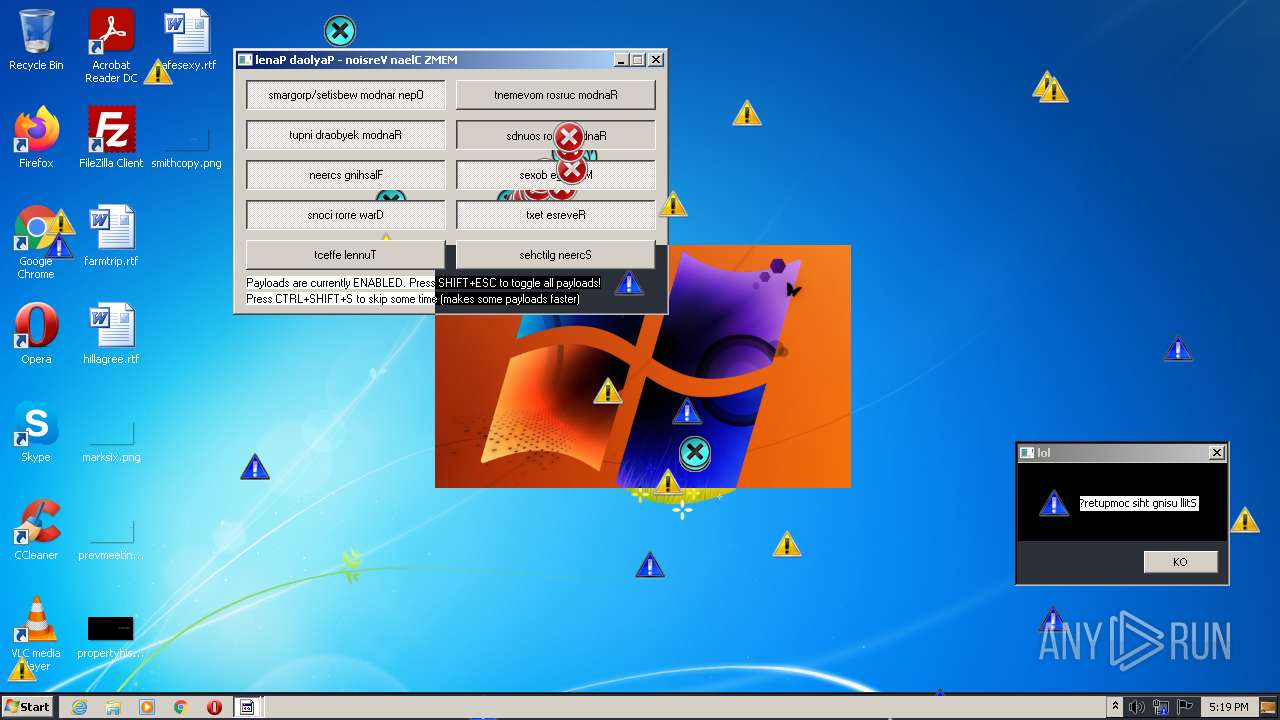
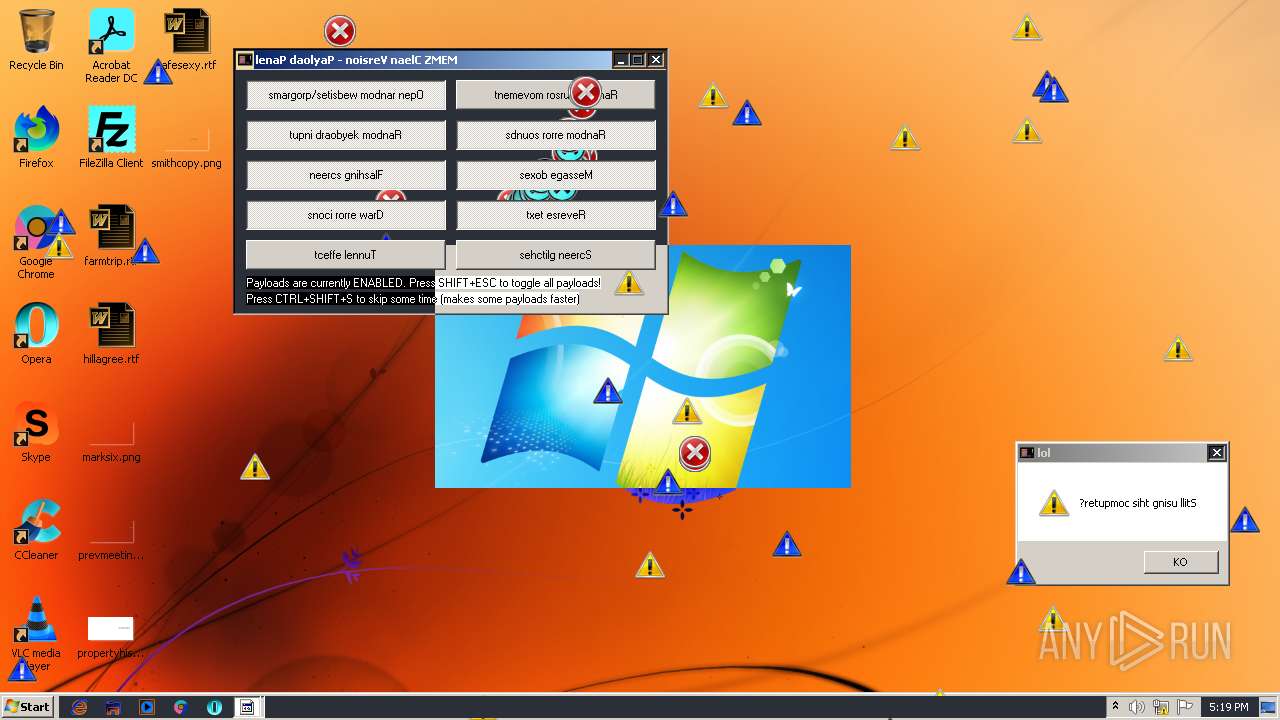
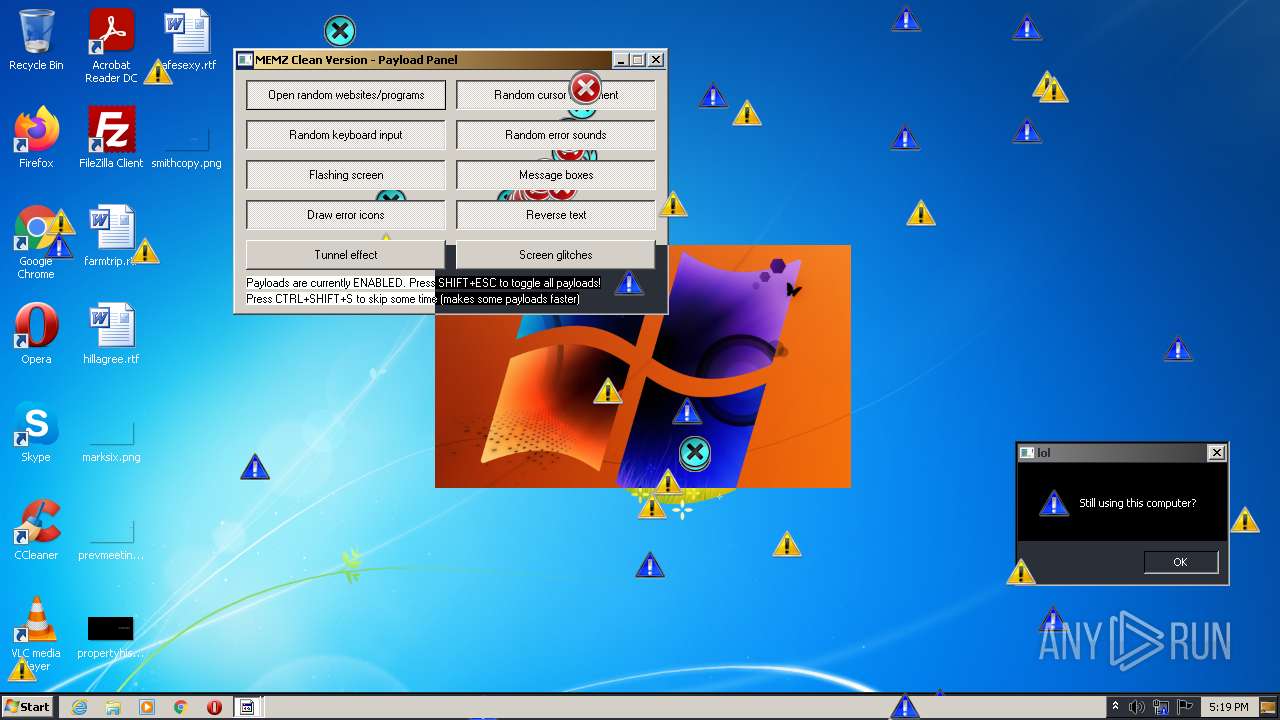
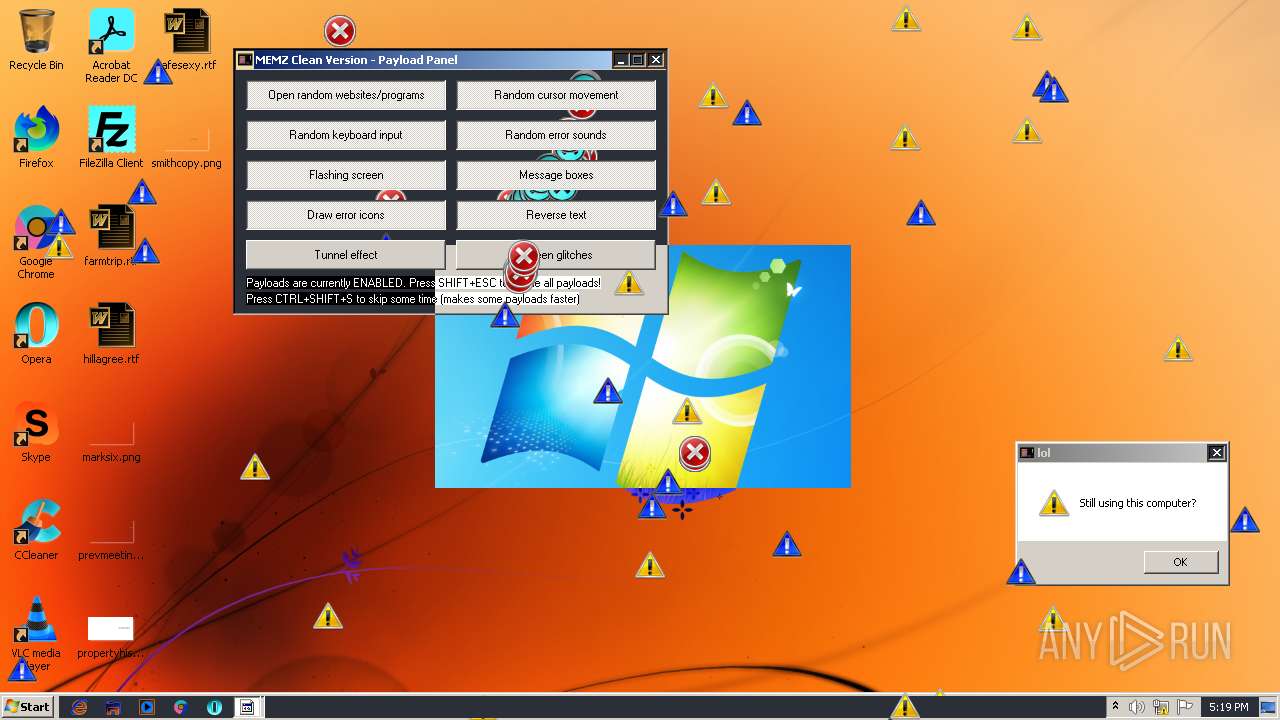
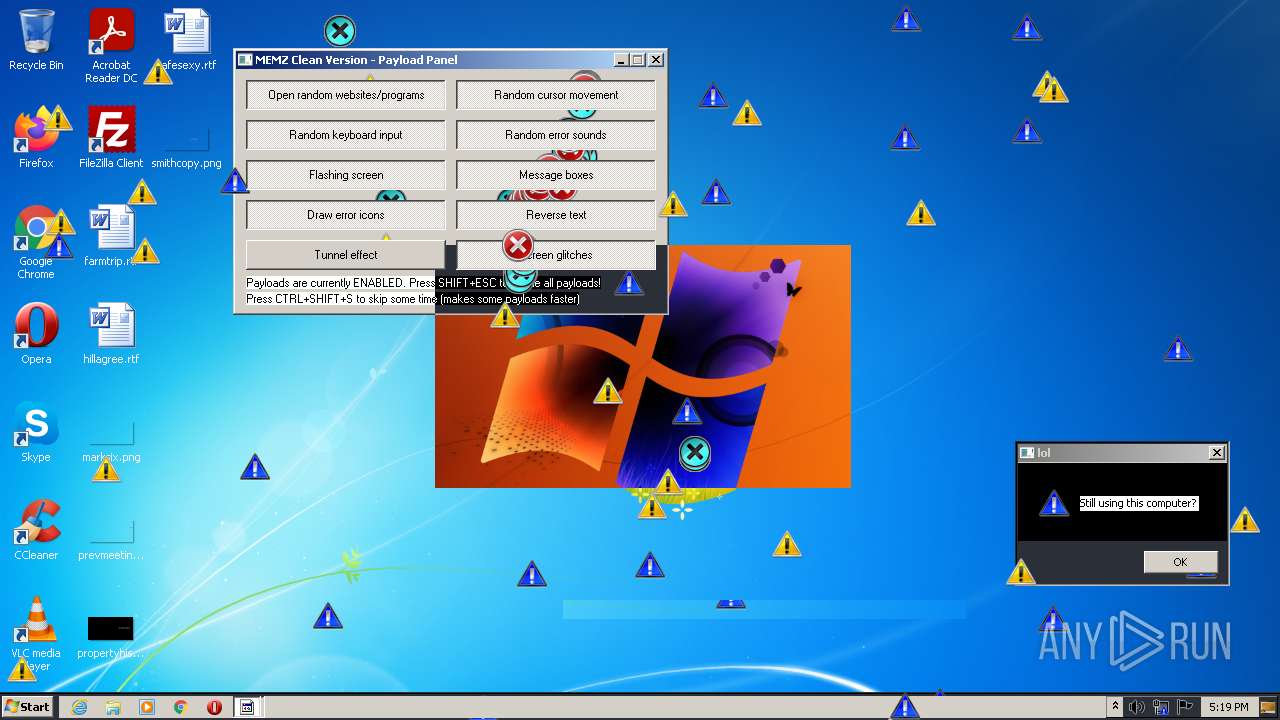
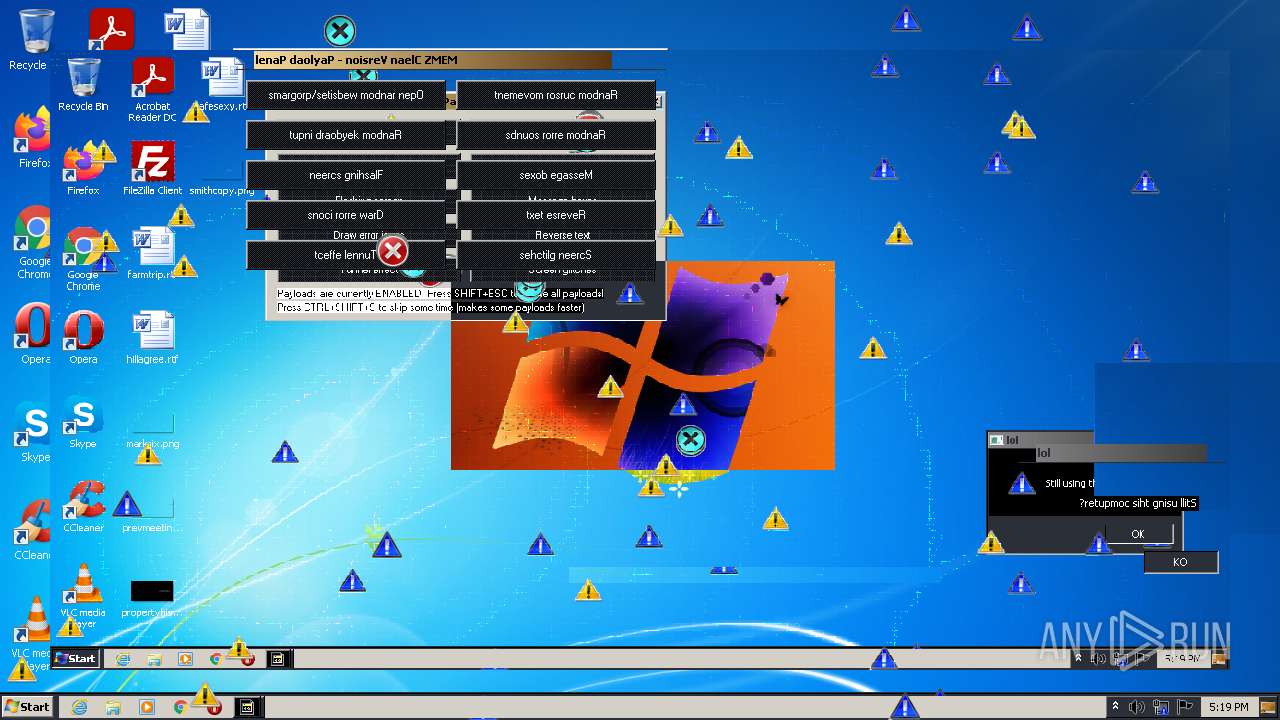
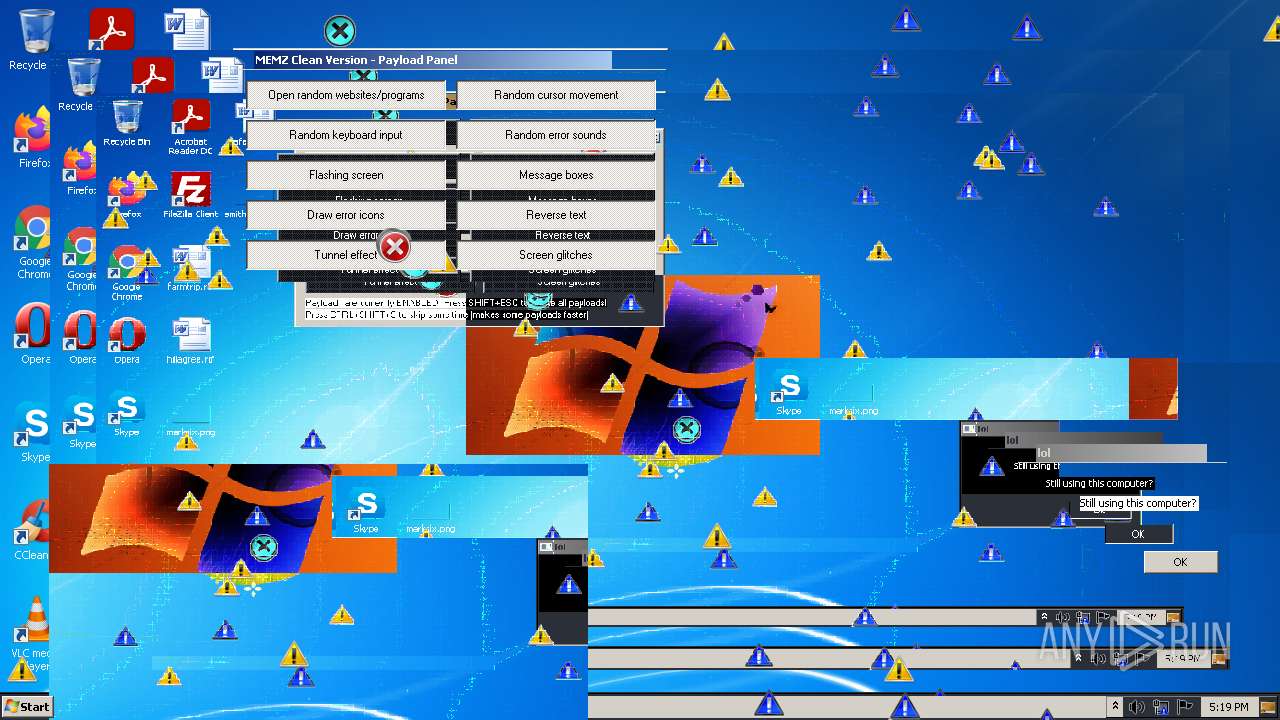
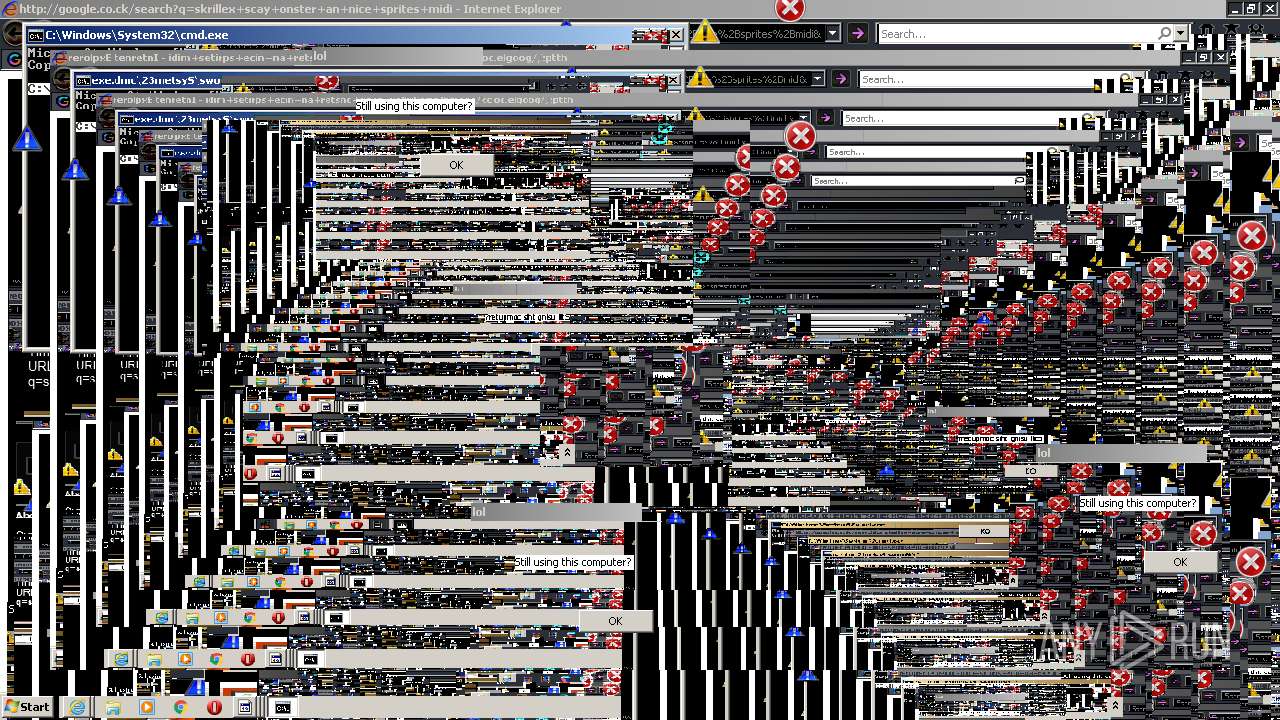
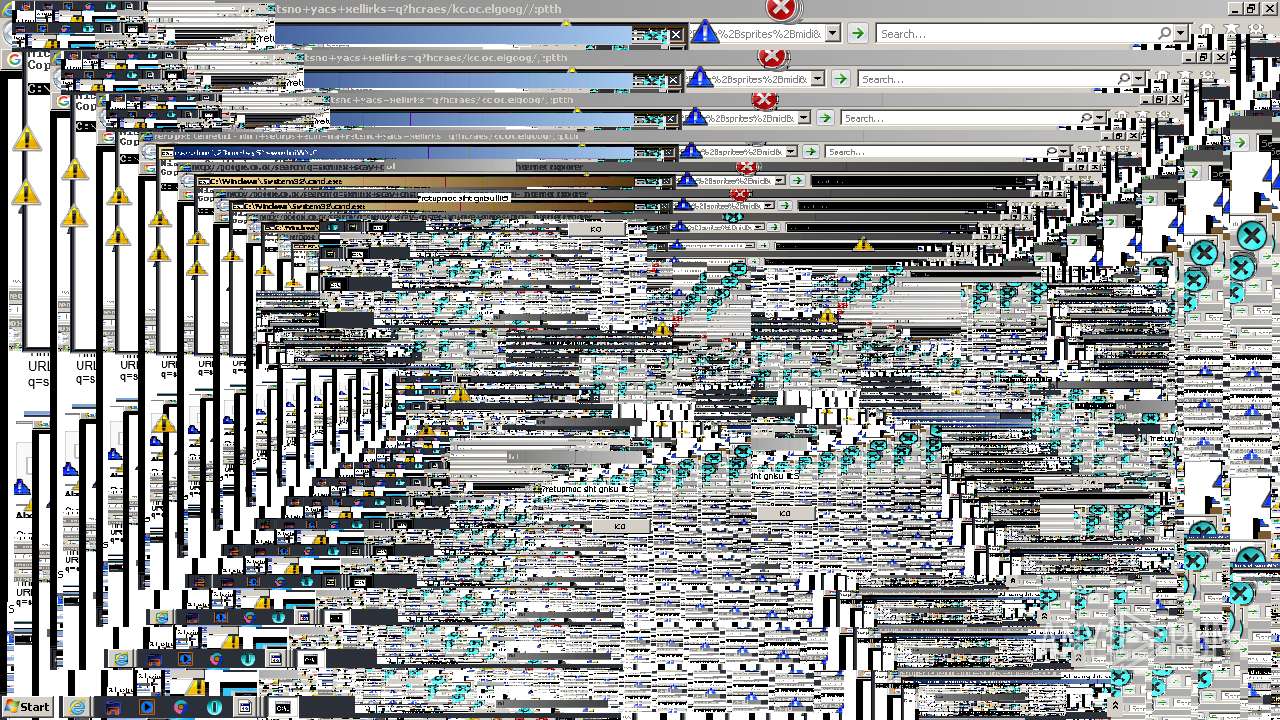
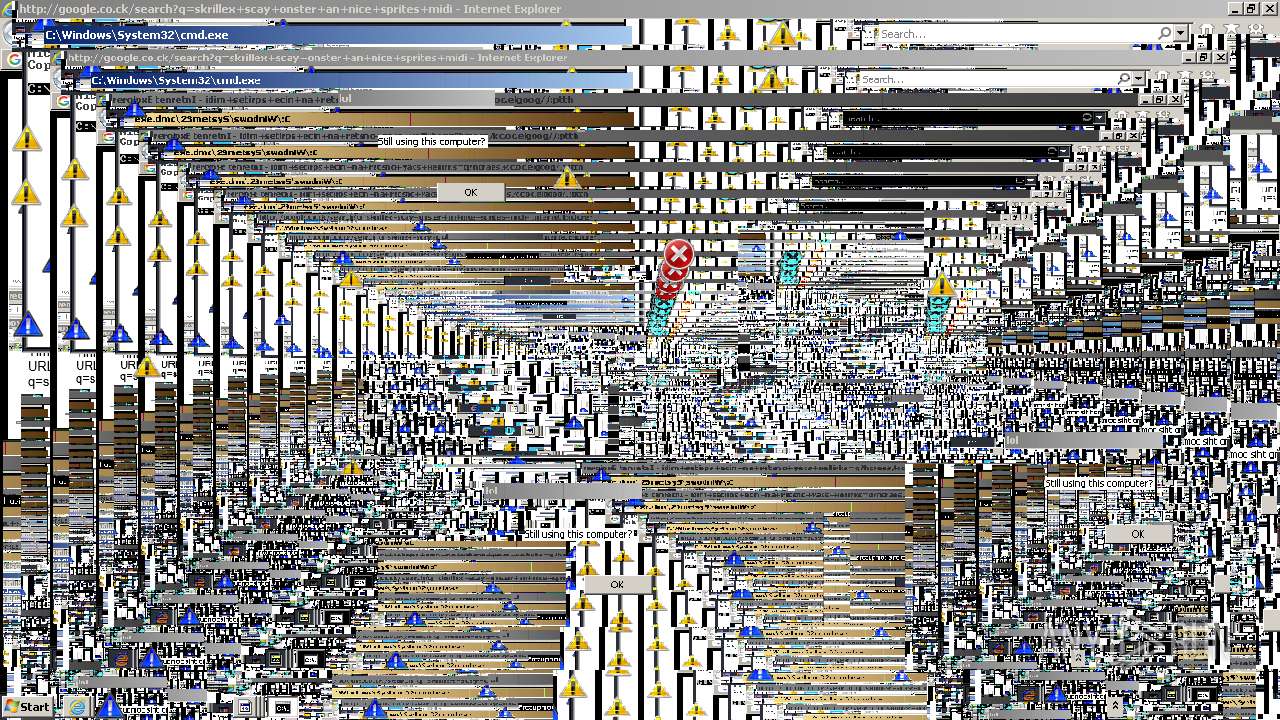
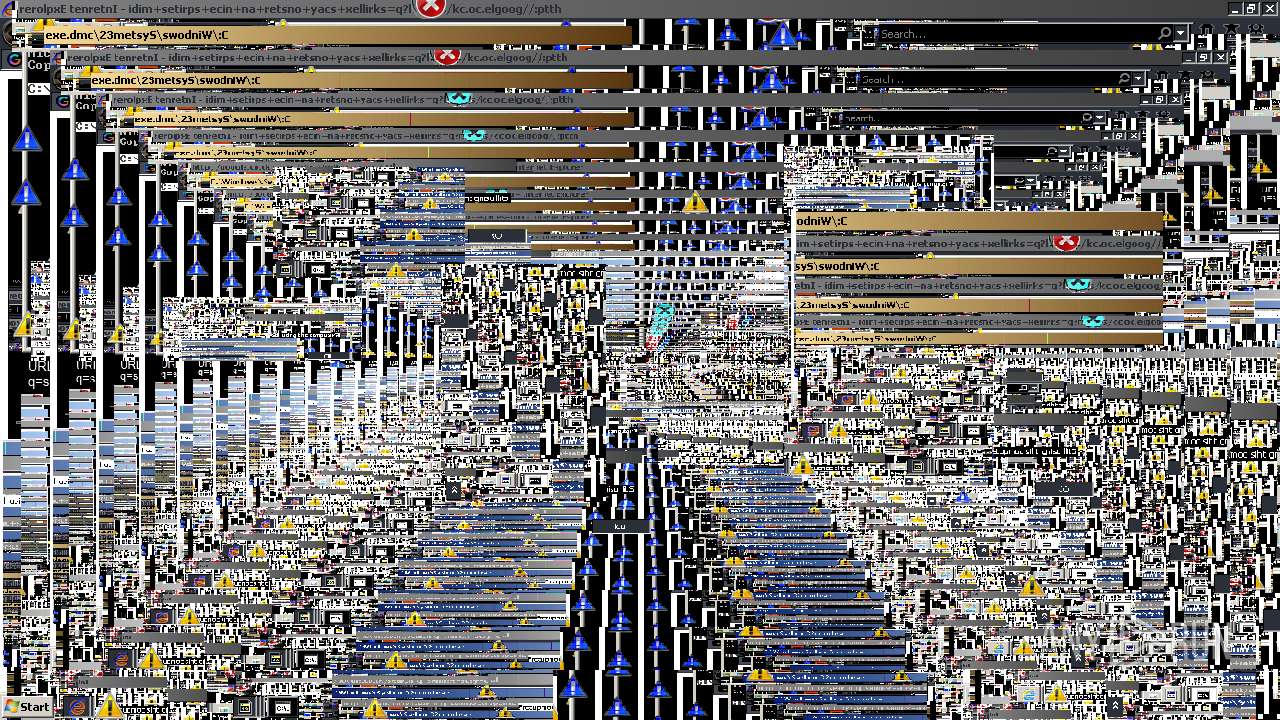
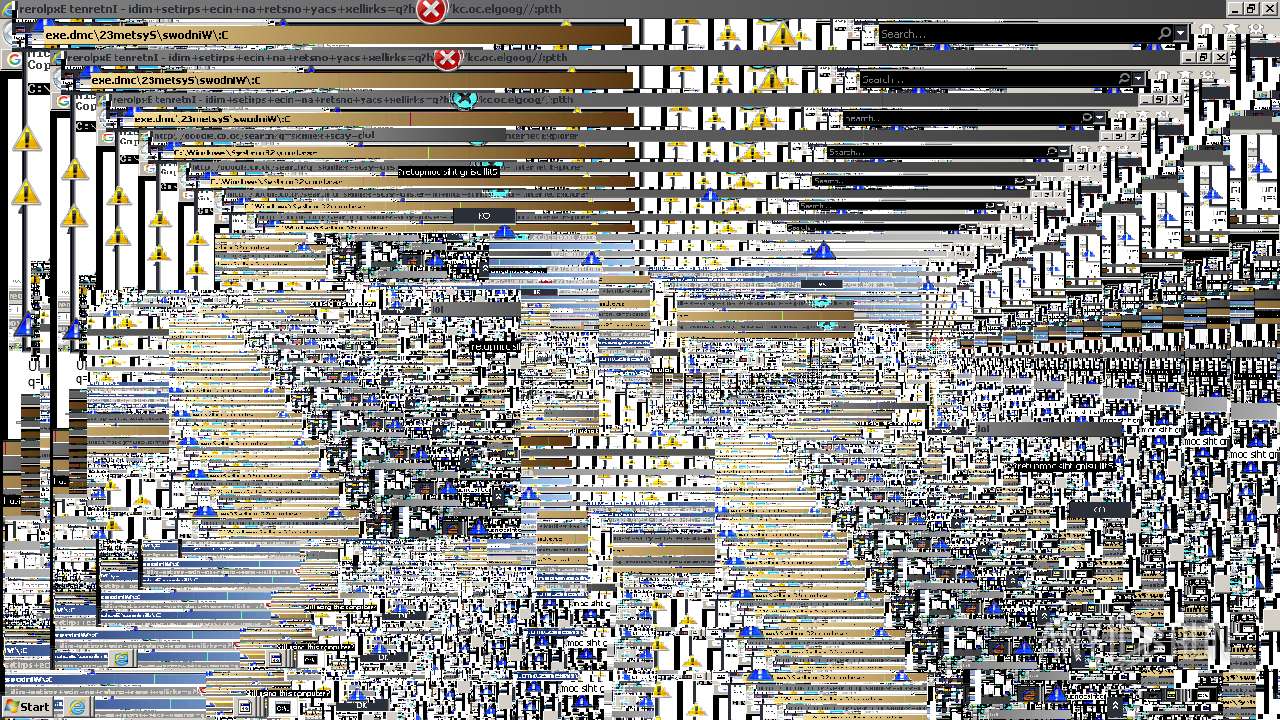
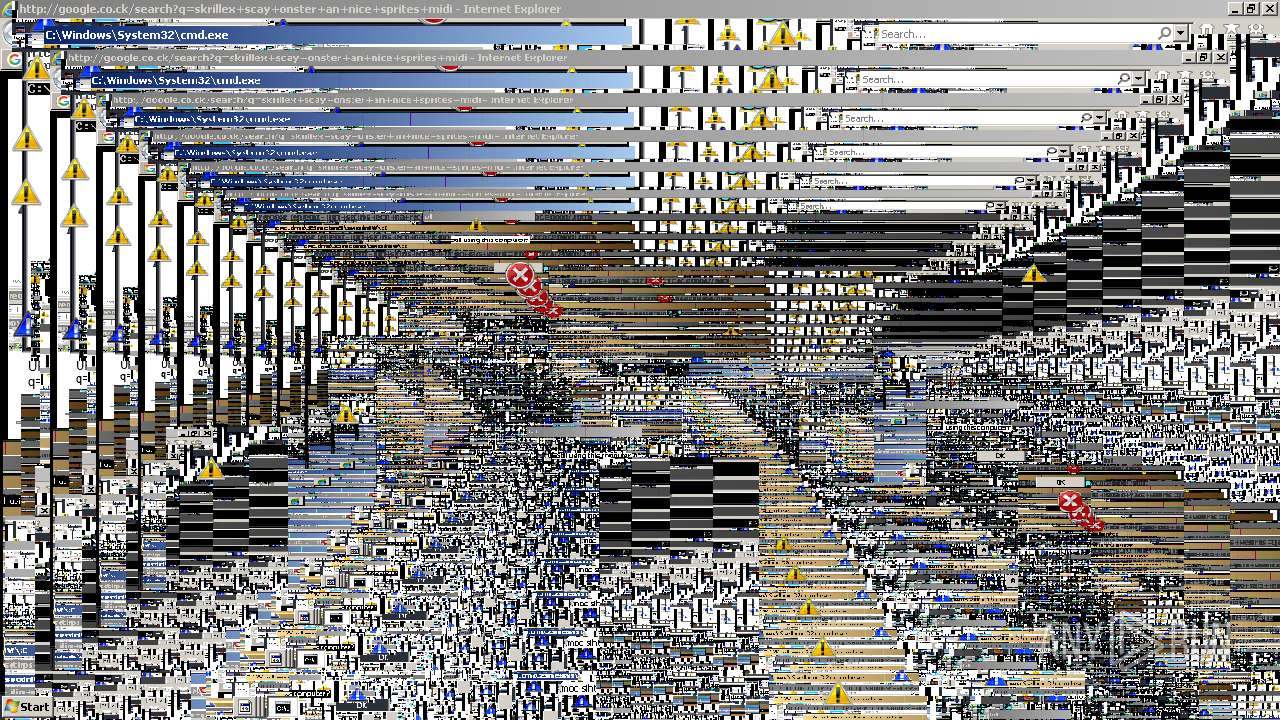
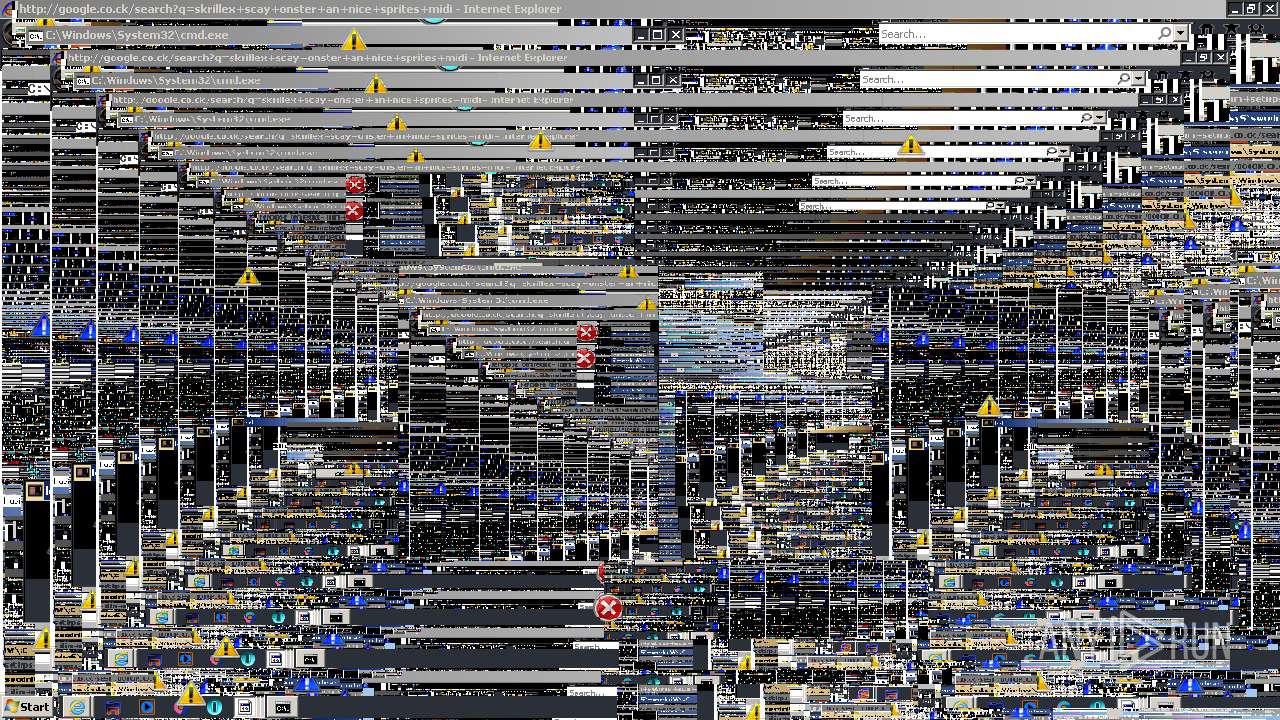
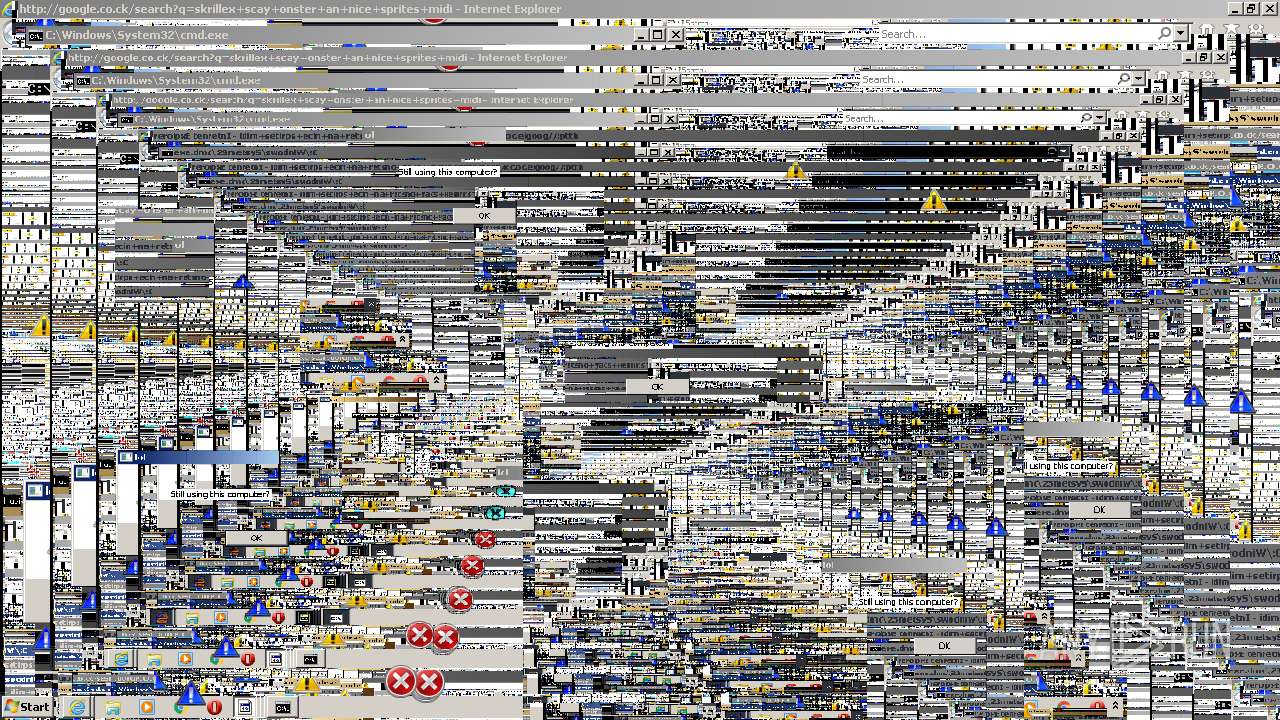
MALICIOUS
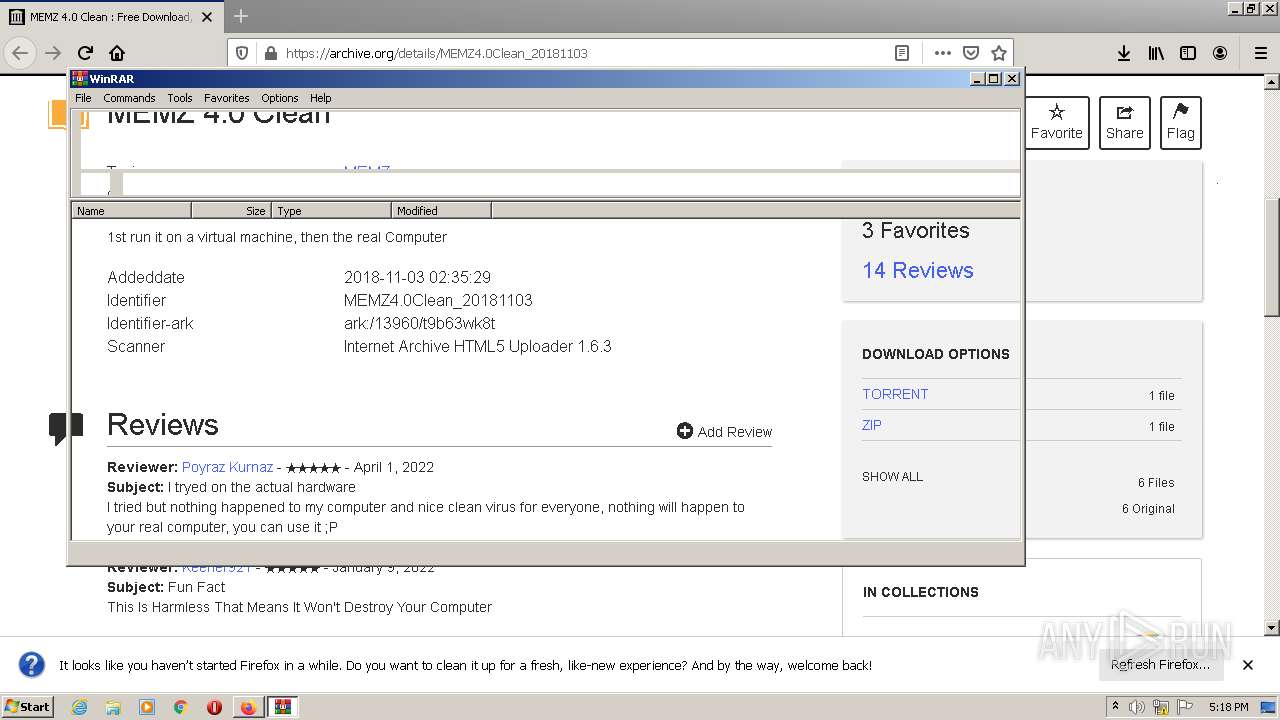
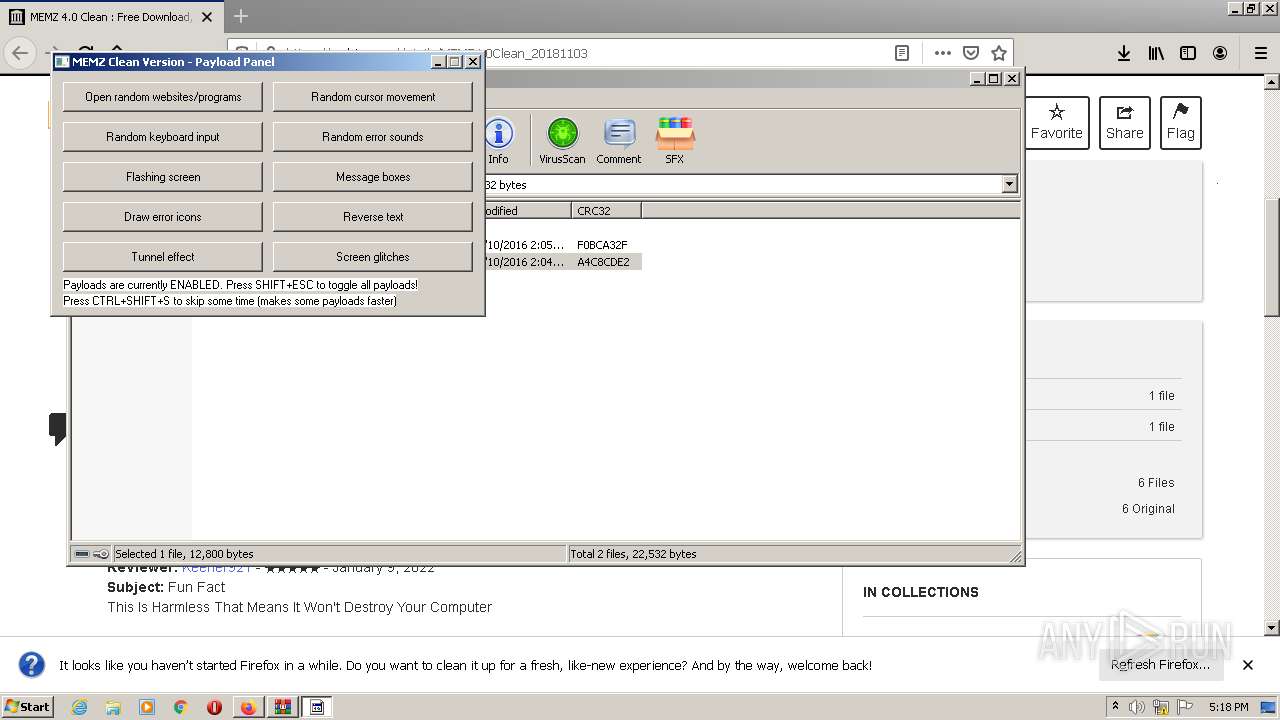
Drops executable file immediately after starts
- WinRAR.exe (PID: 2488)
Application was dropped or rewritten from another process
- MEMZ-Clean.exe (PID: 3080)
Runs app for hidden code execution
- MEMZ-Clean.exe (PID: 3080)
SUSPICIOUS
Checks supported languages
- WinRAR.exe (PID: 2488)
- MEMZ-Clean.exe (PID: 3080)
- cmd.exe (PID: 2244)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2488)
Reads the computer name
- WinRAR.exe (PID: 2488)
- MEMZ-Clean.exe (PID: 3080)
Drops a file with a compile date too recent
- WinRAR.exe (PID: 2488)
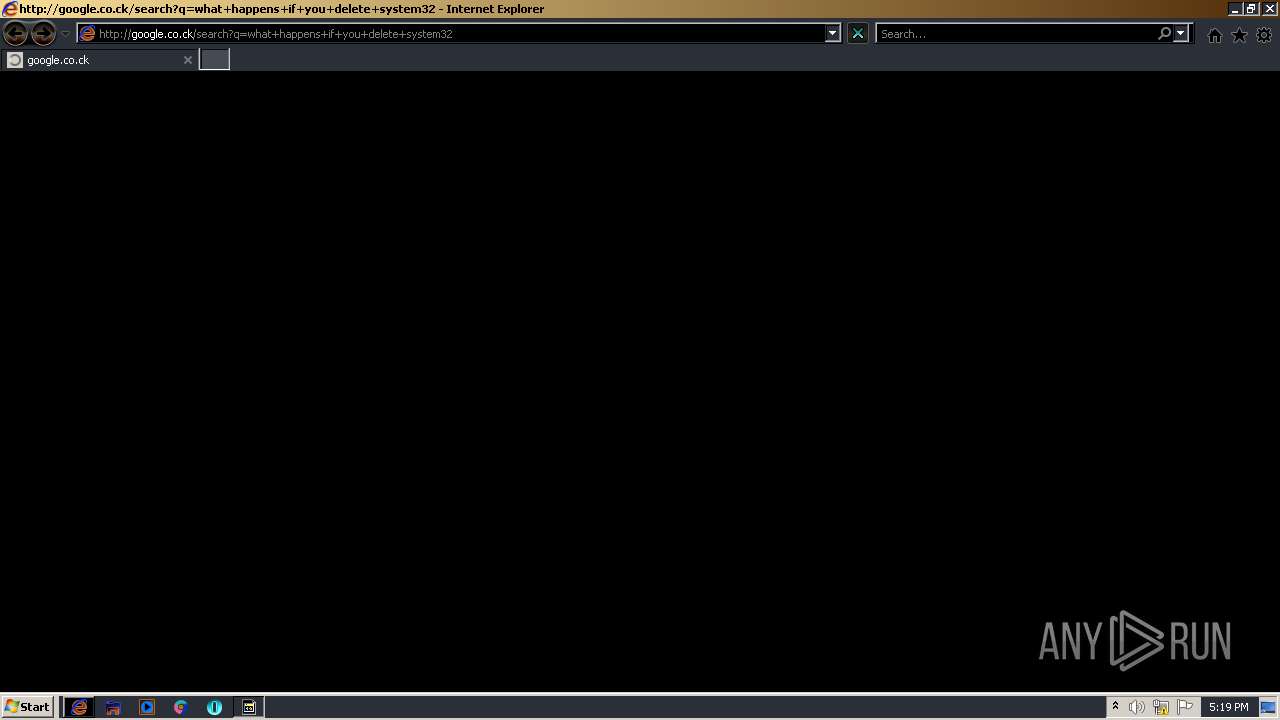
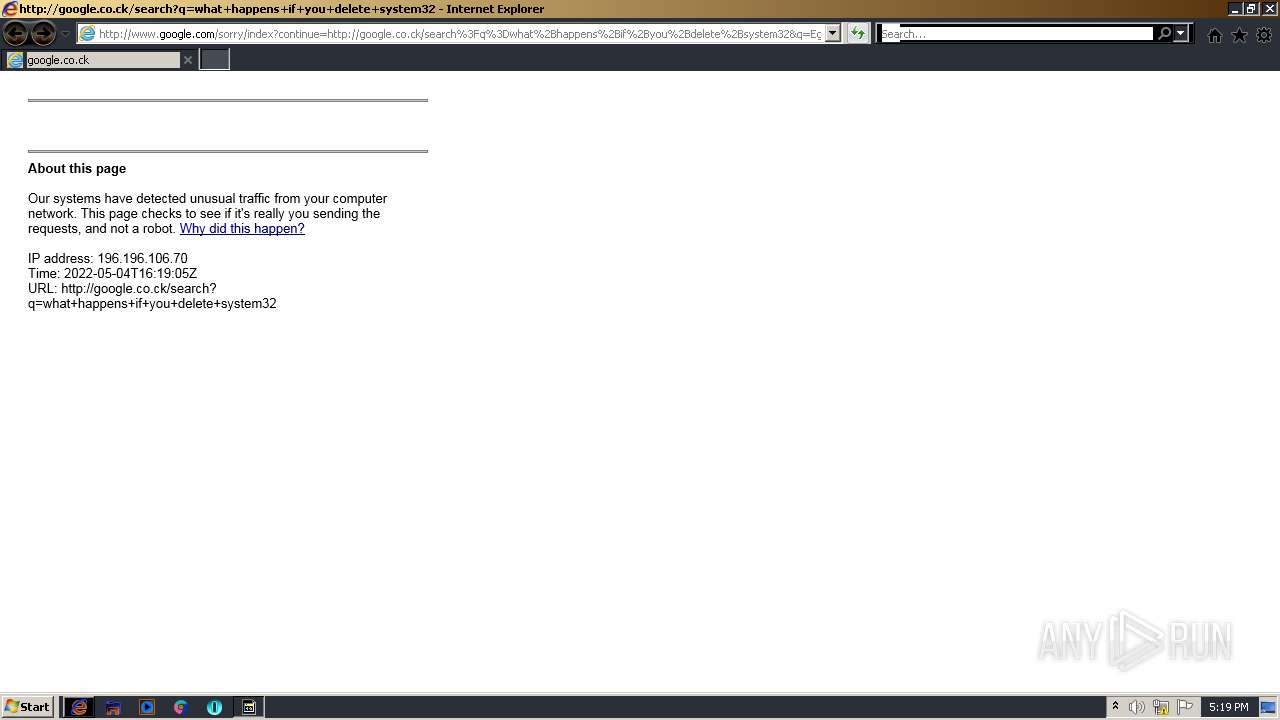
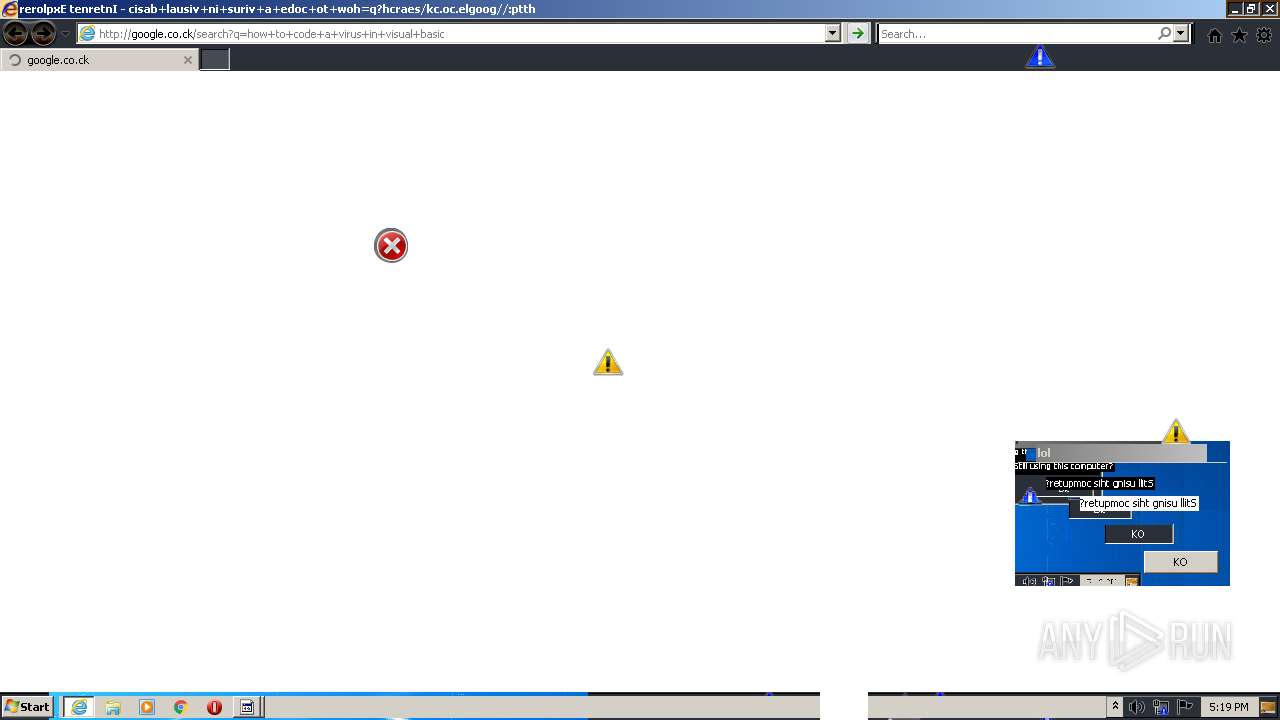
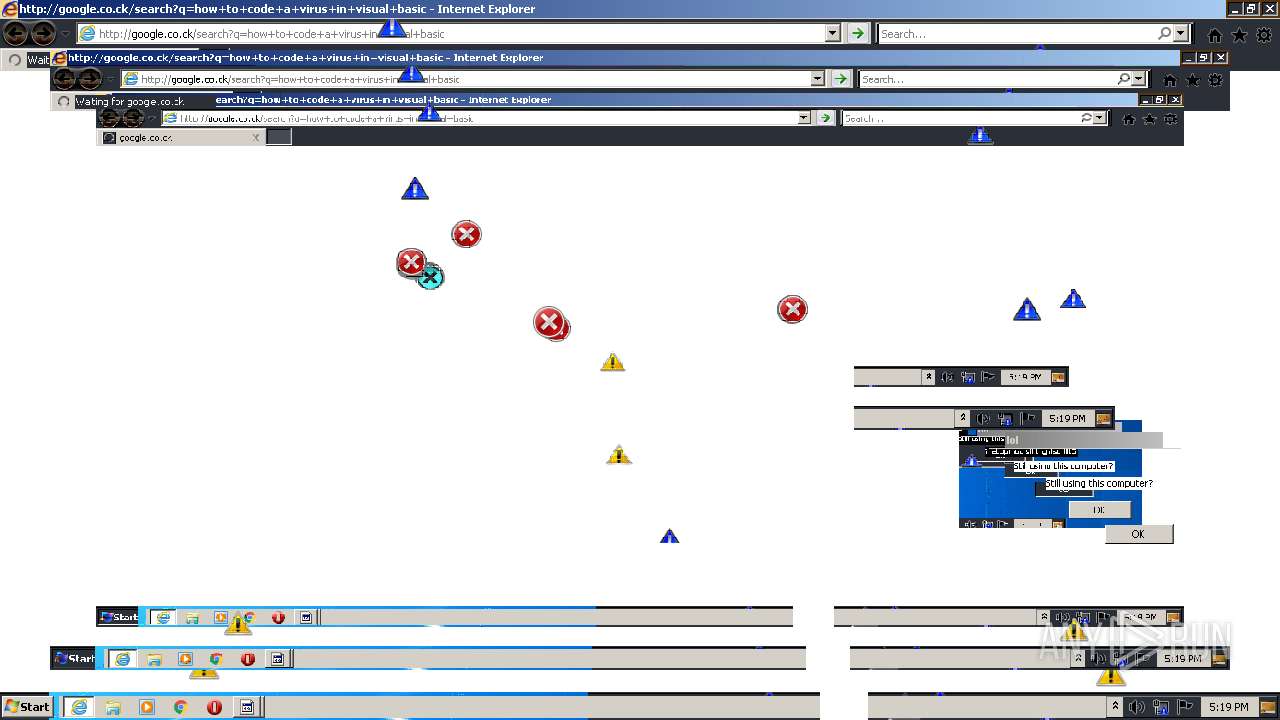
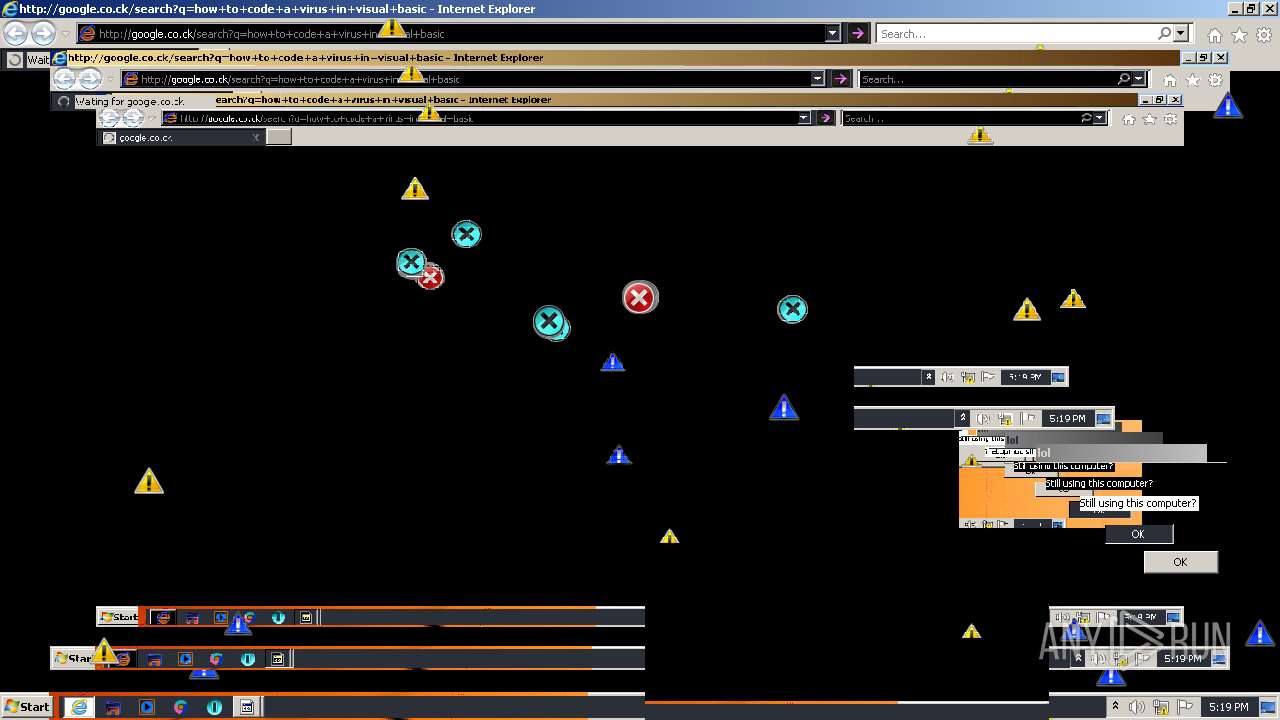
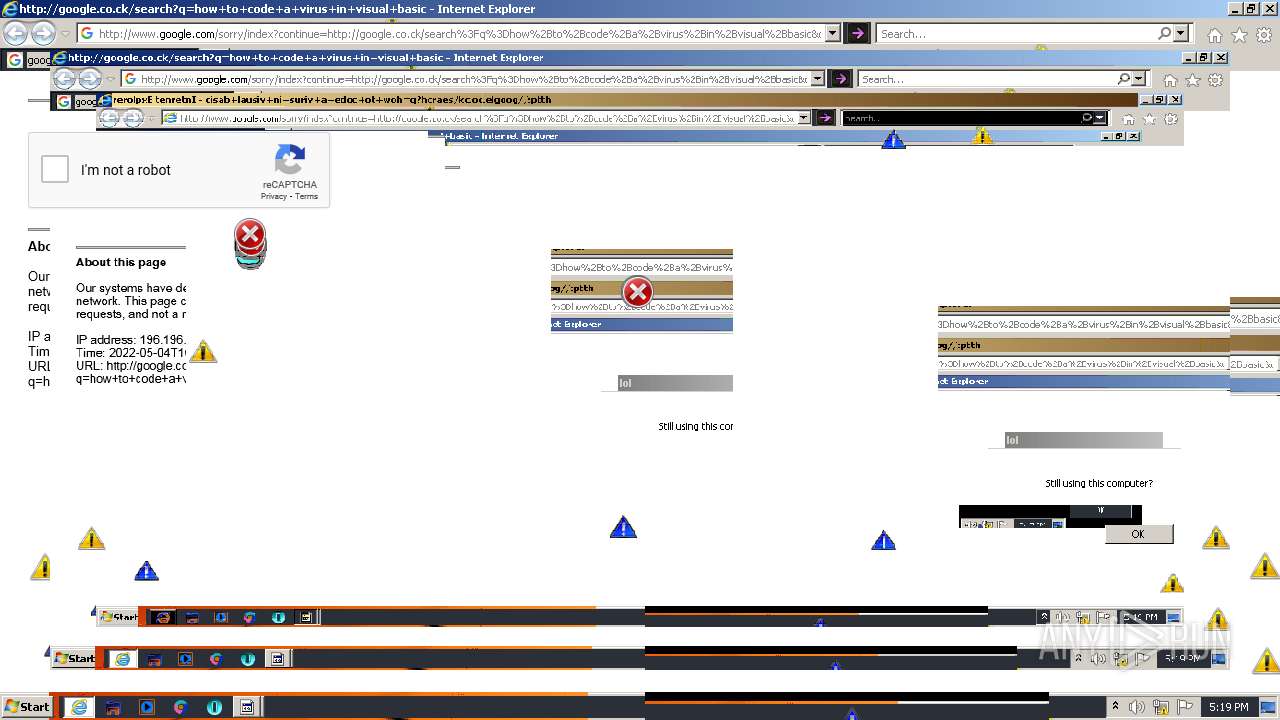
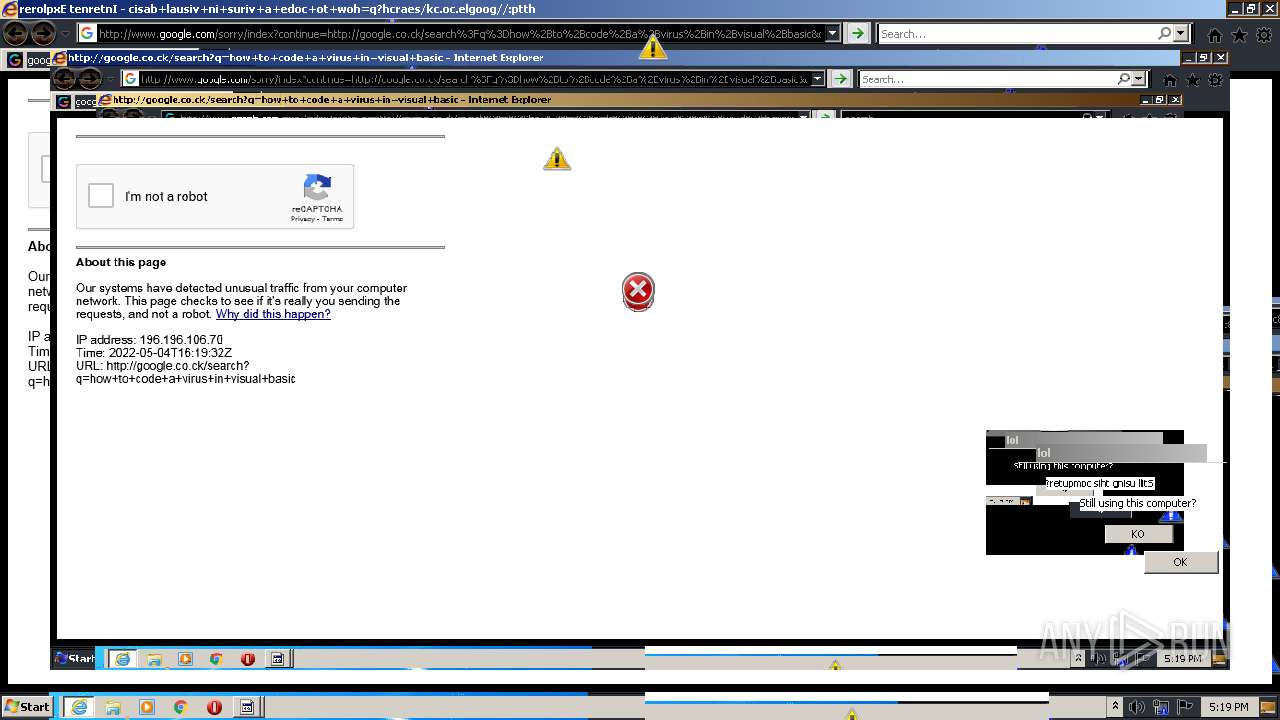
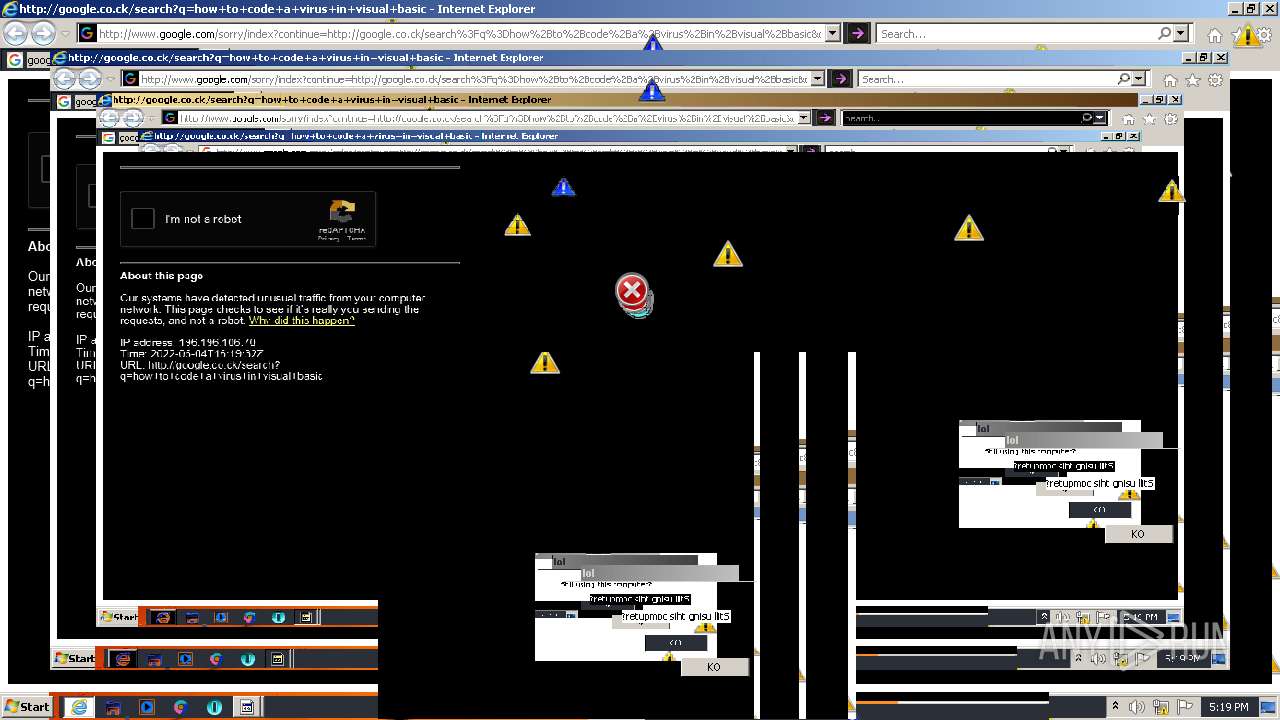
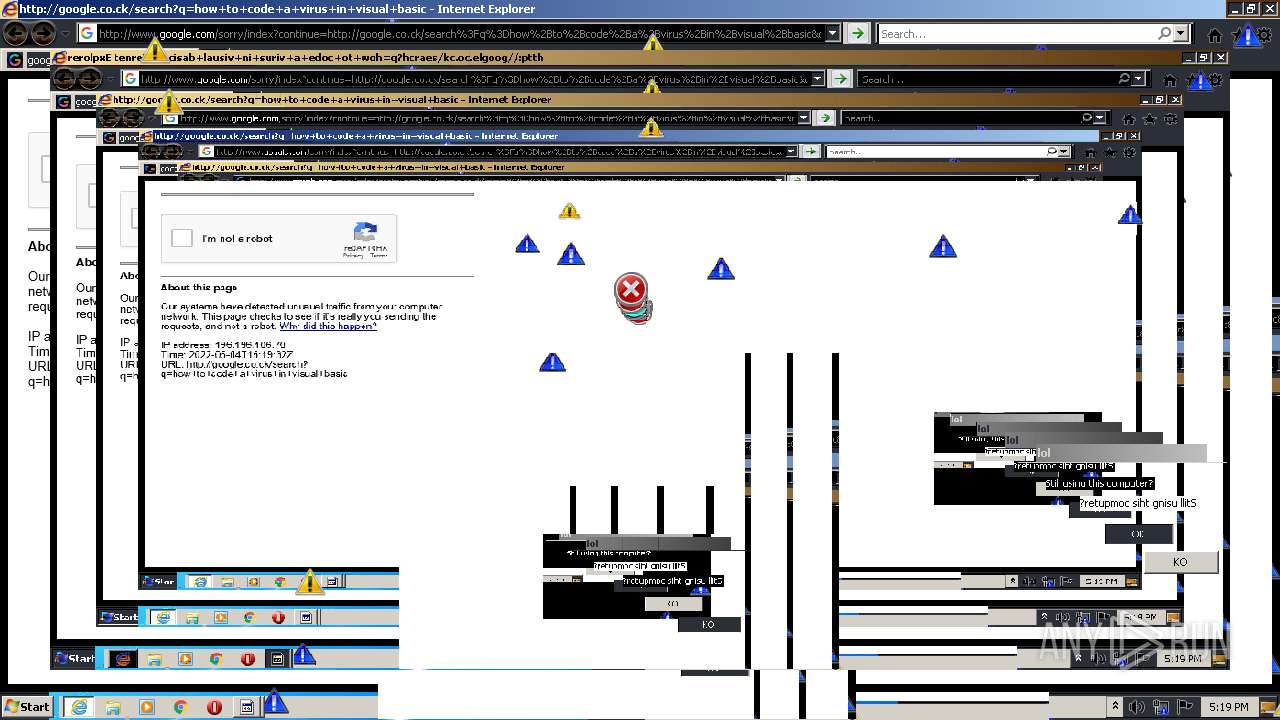
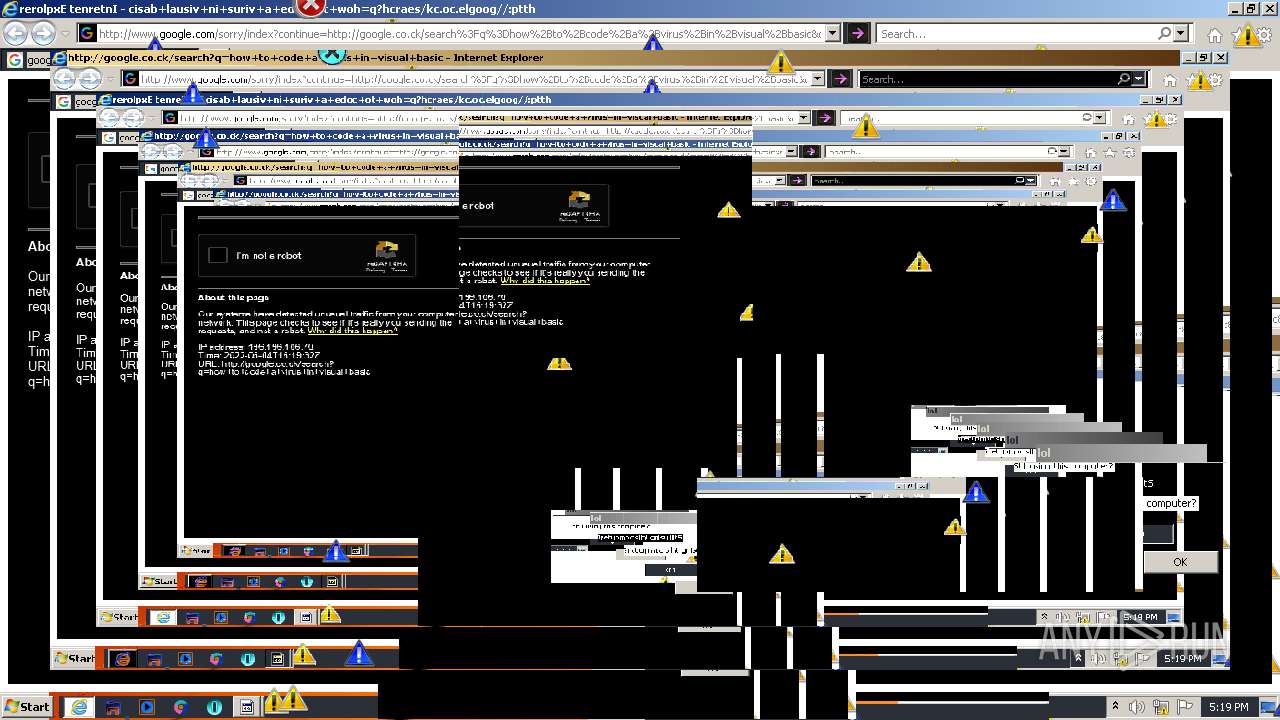
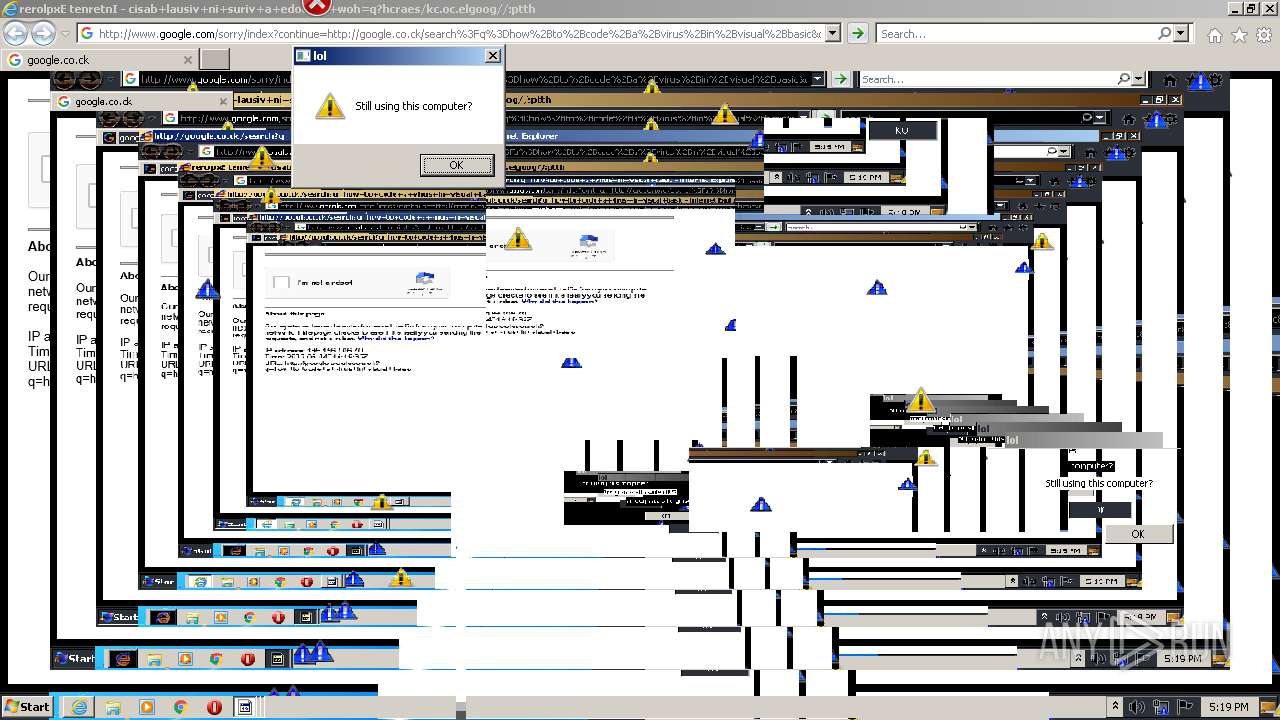
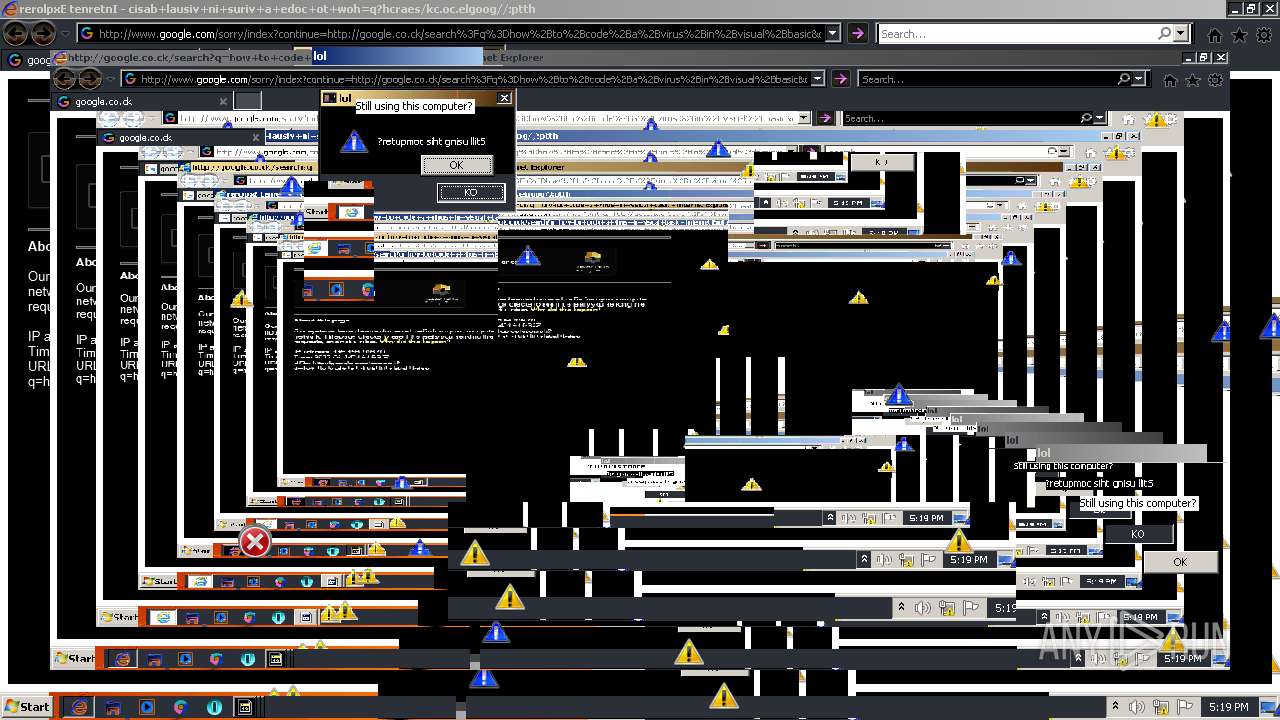
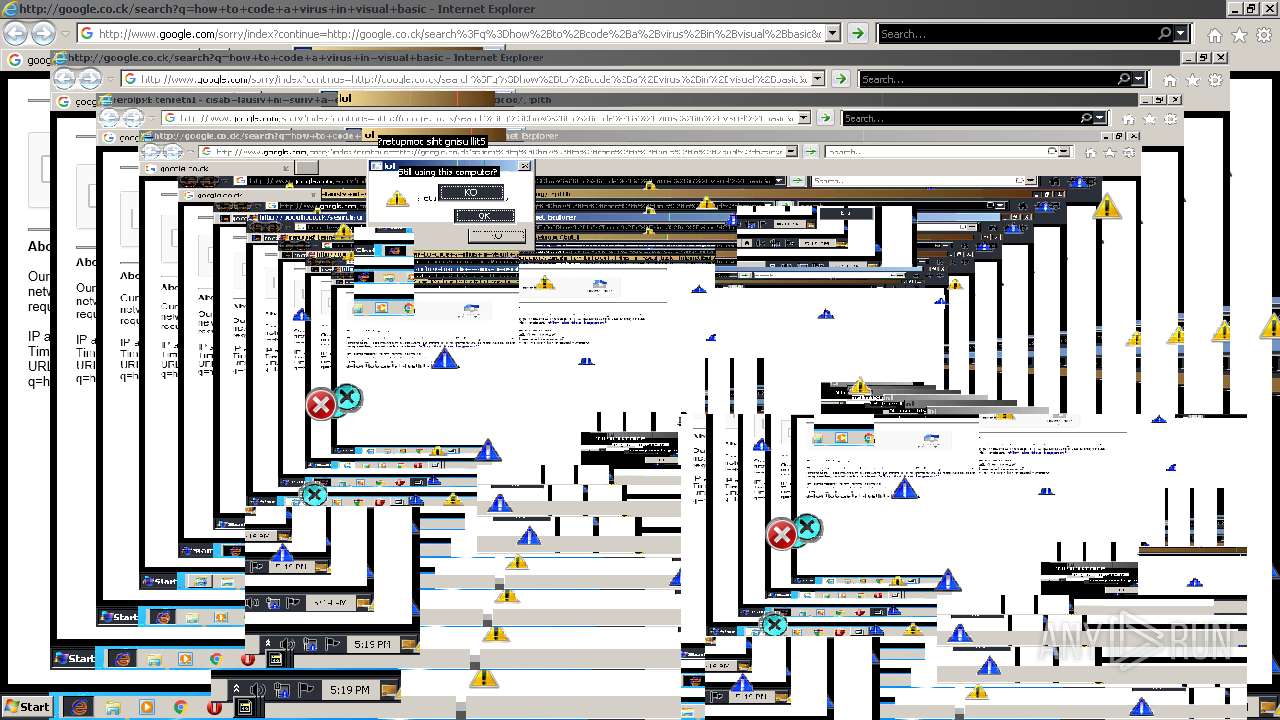
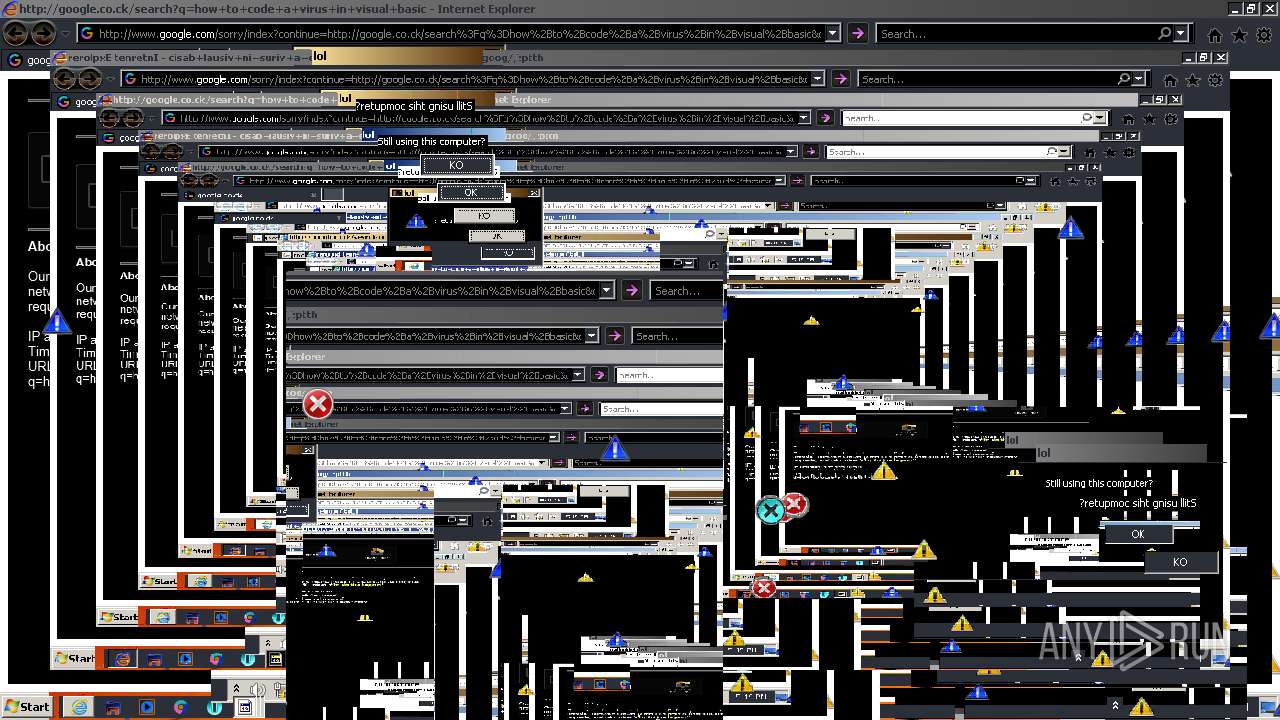
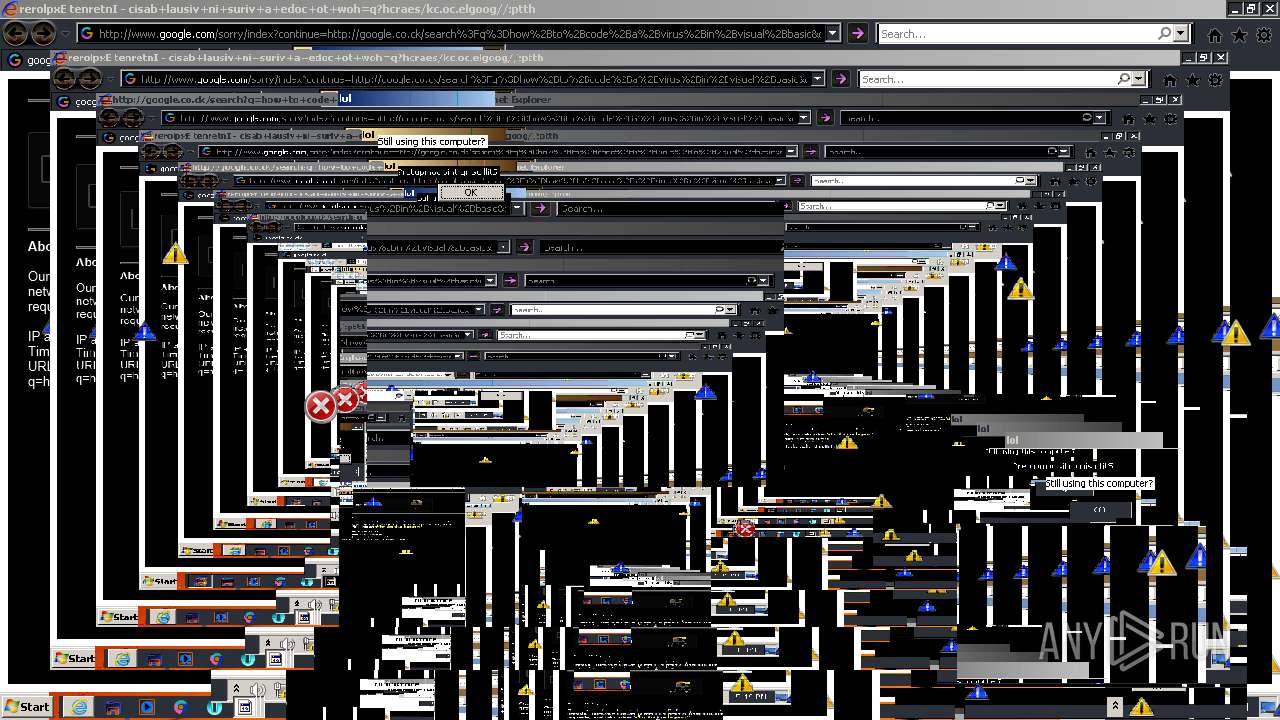
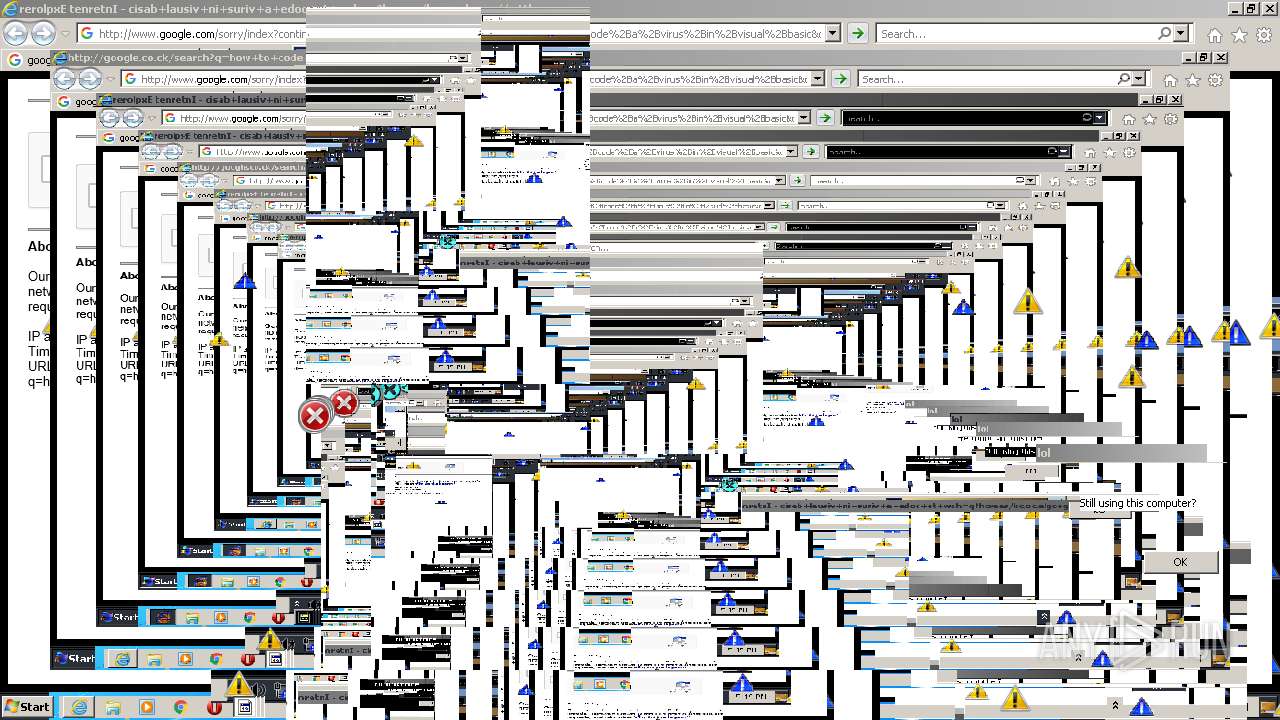
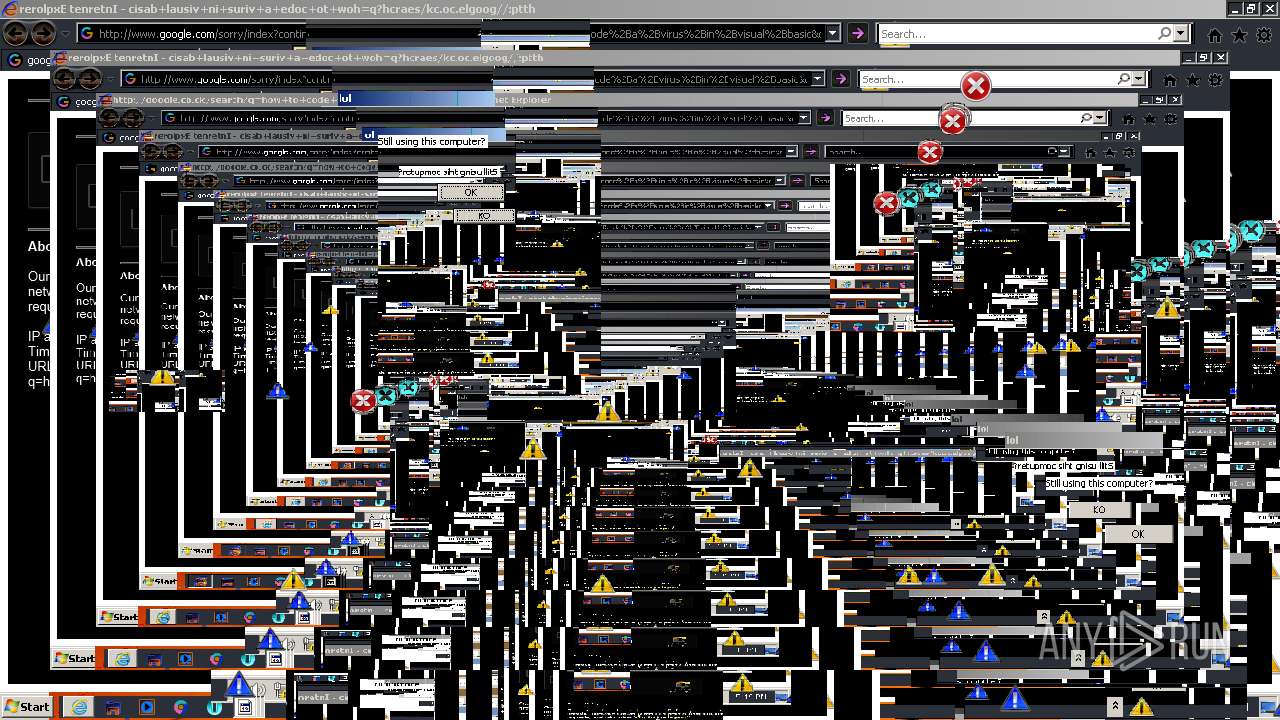
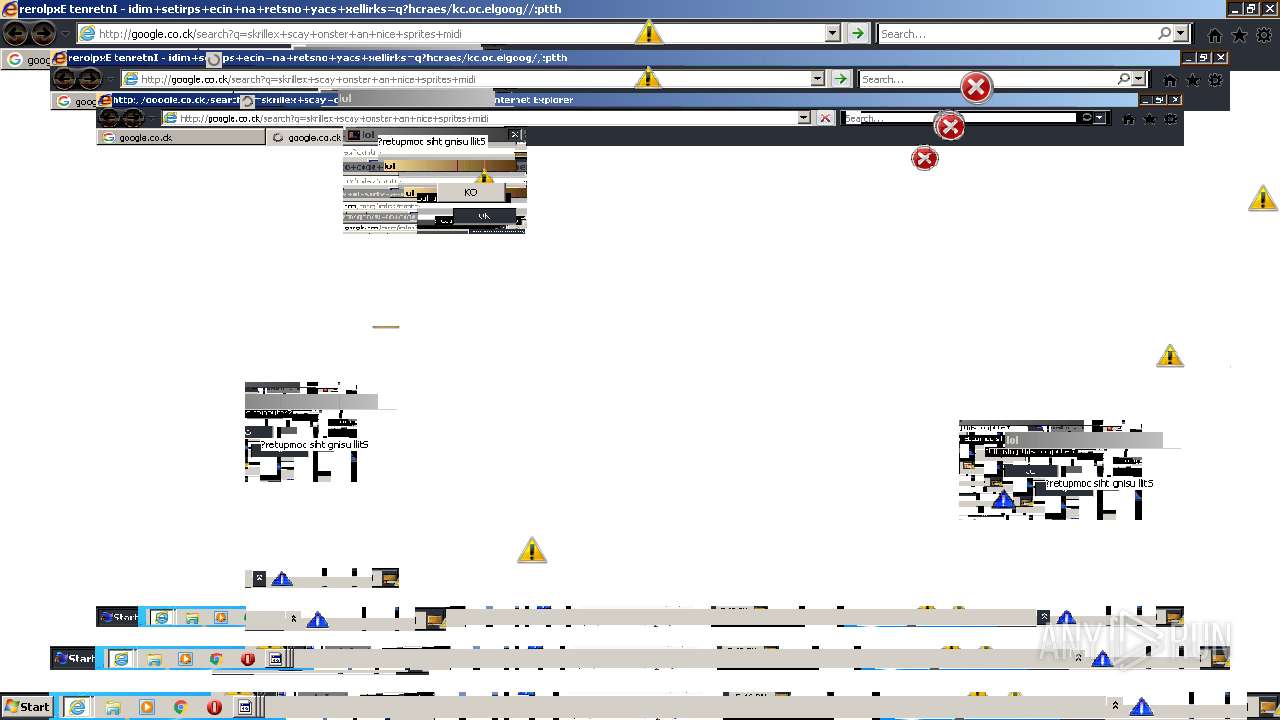
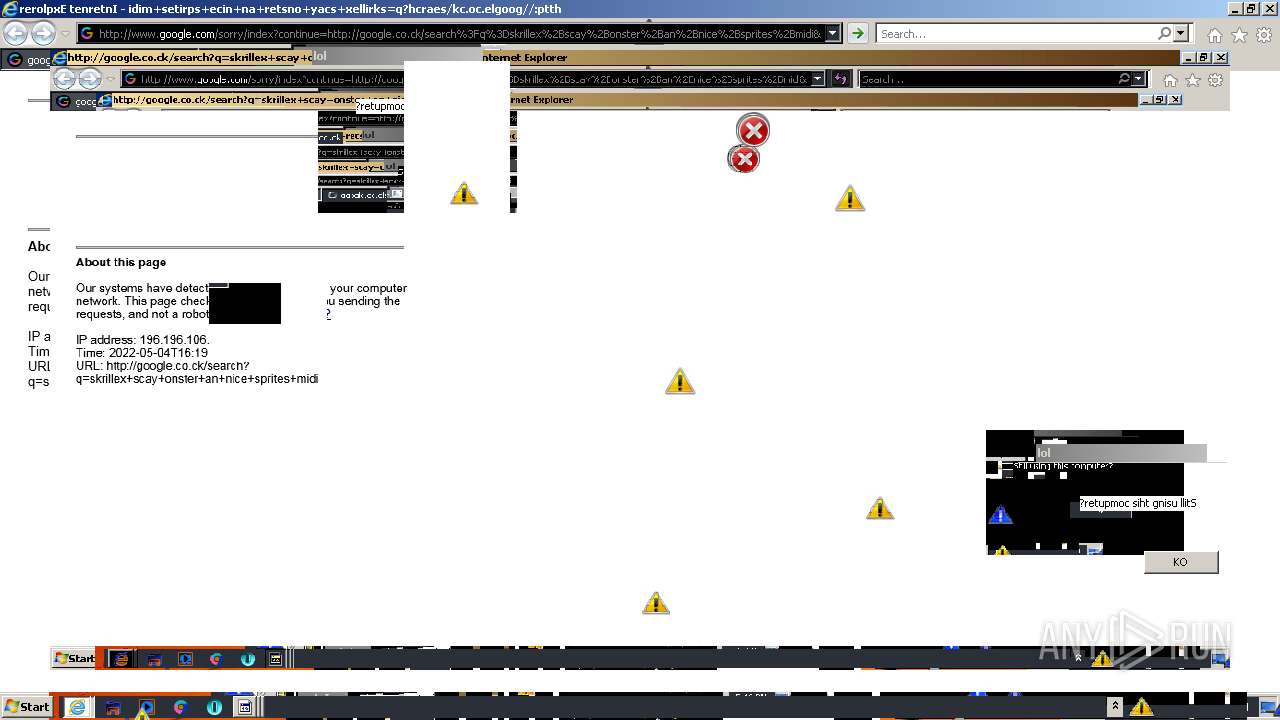
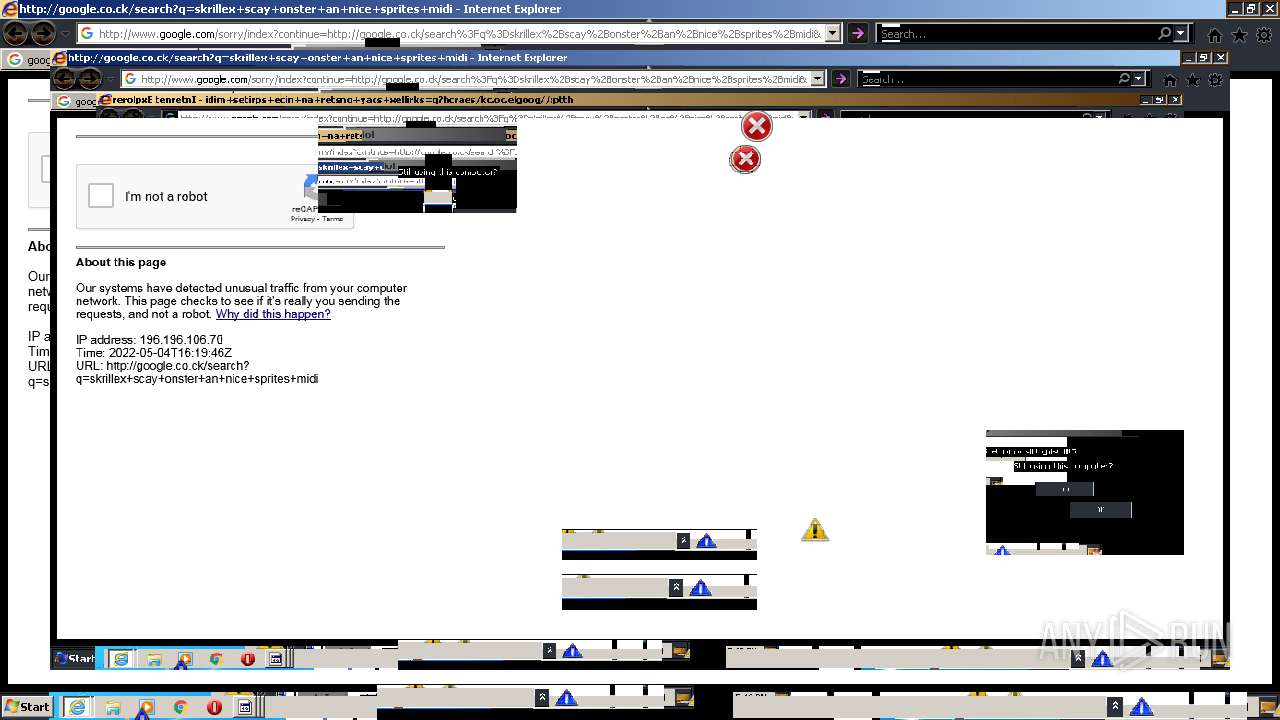
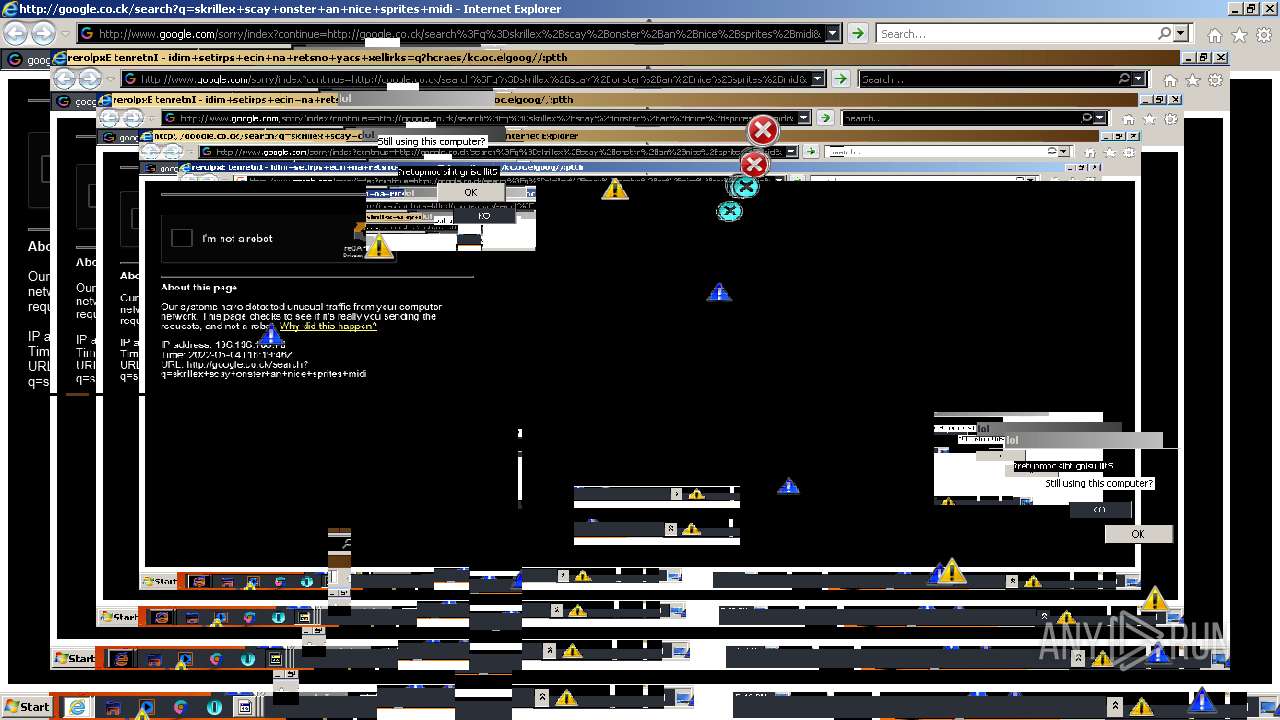
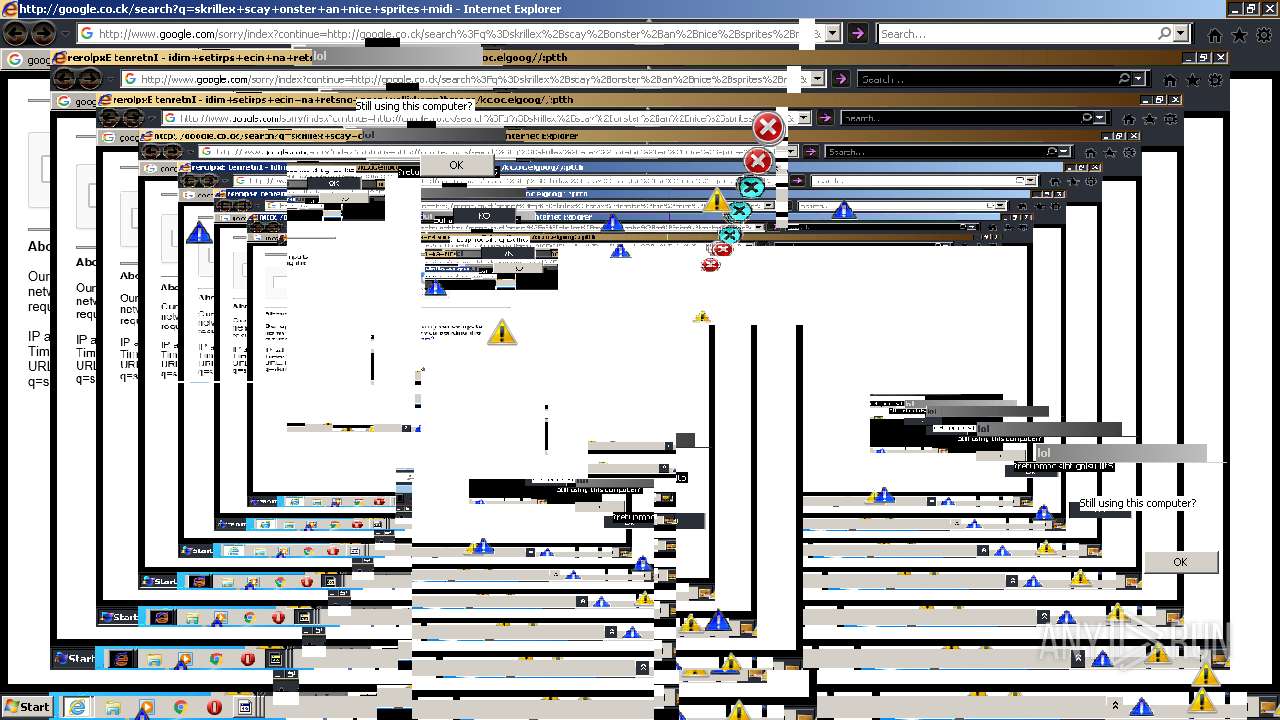
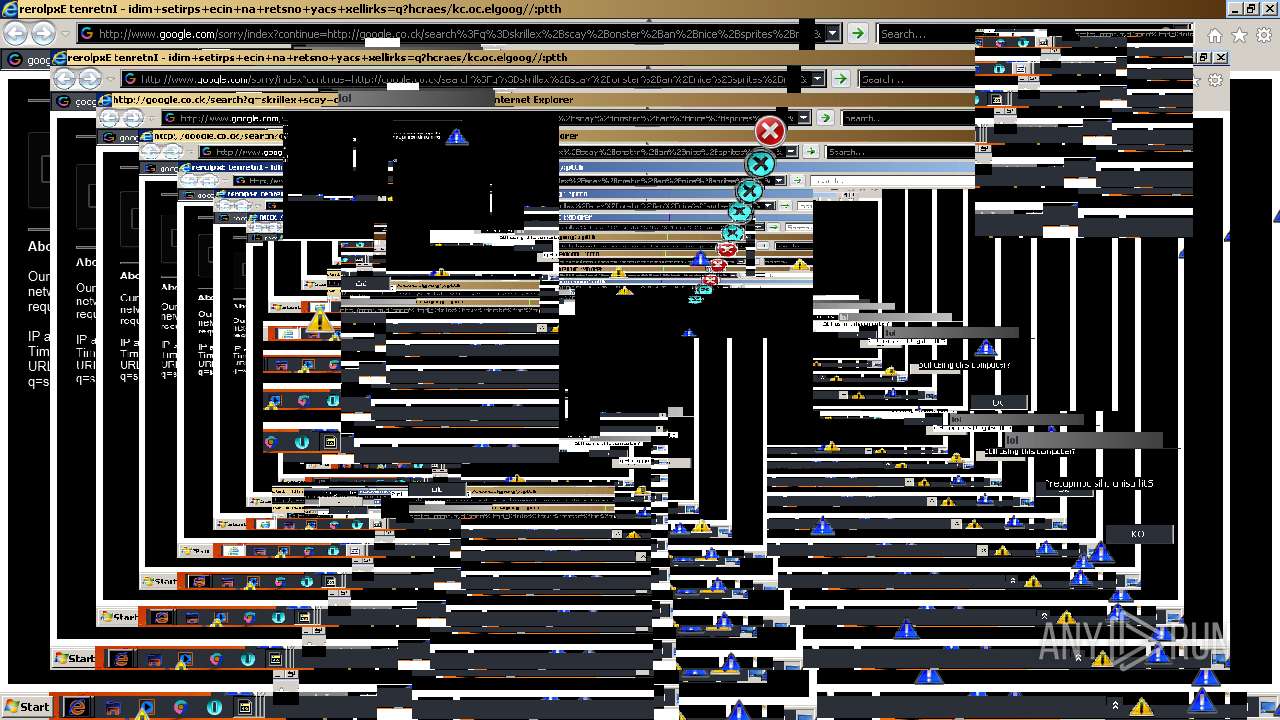
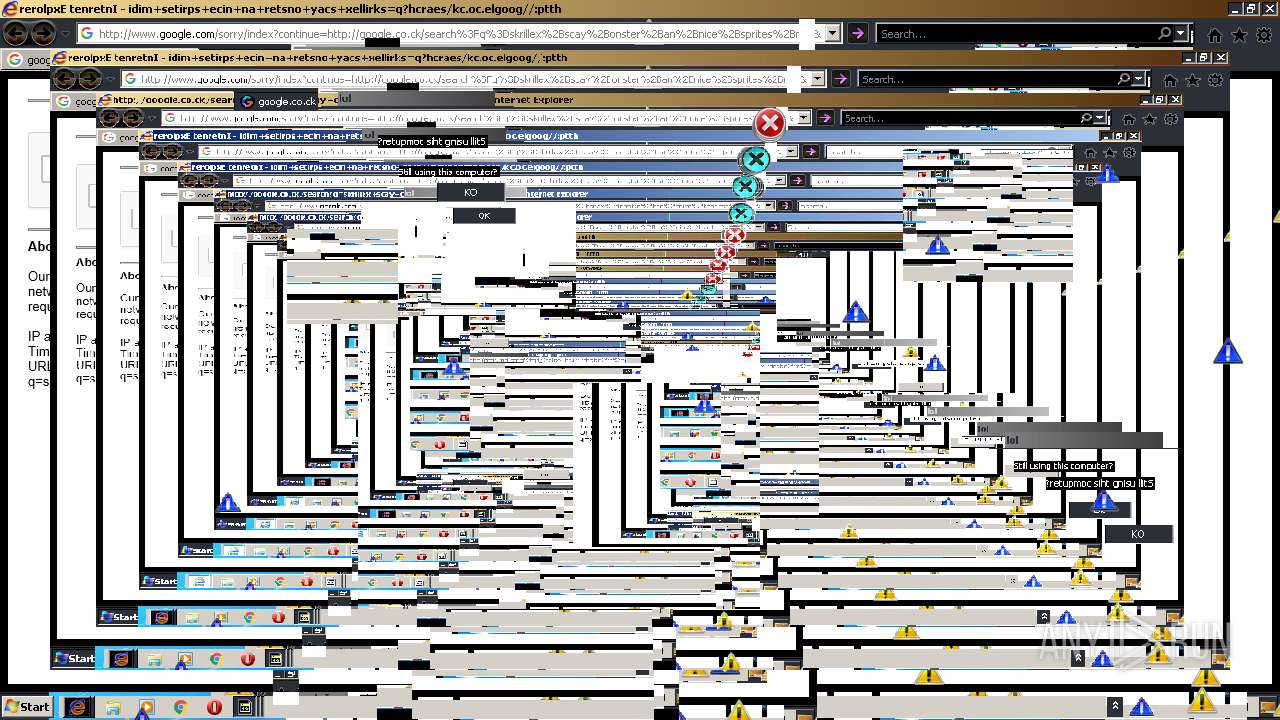
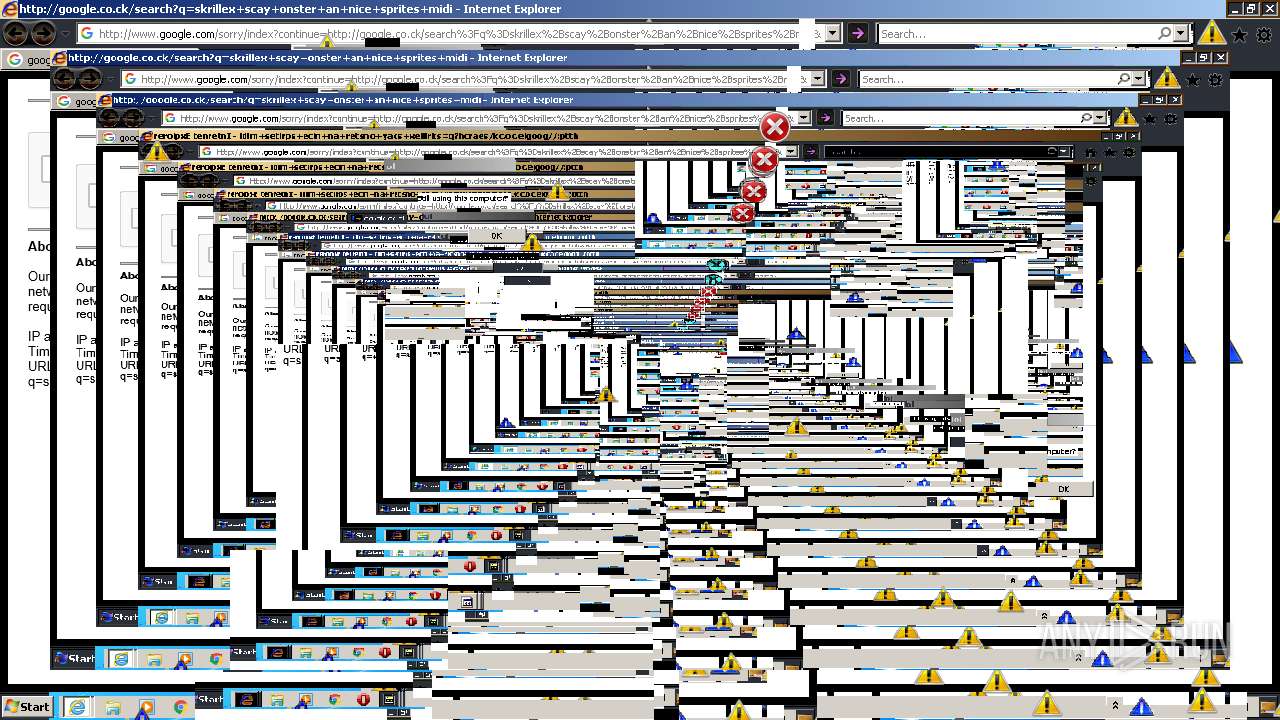
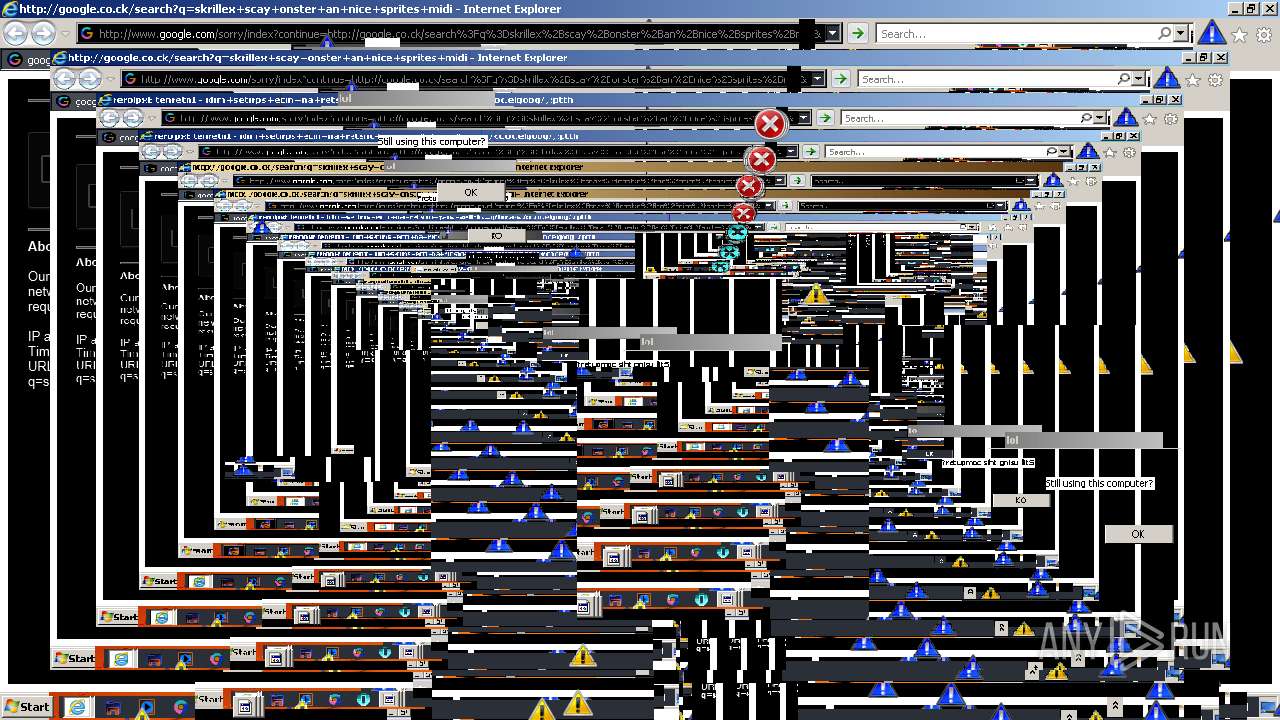
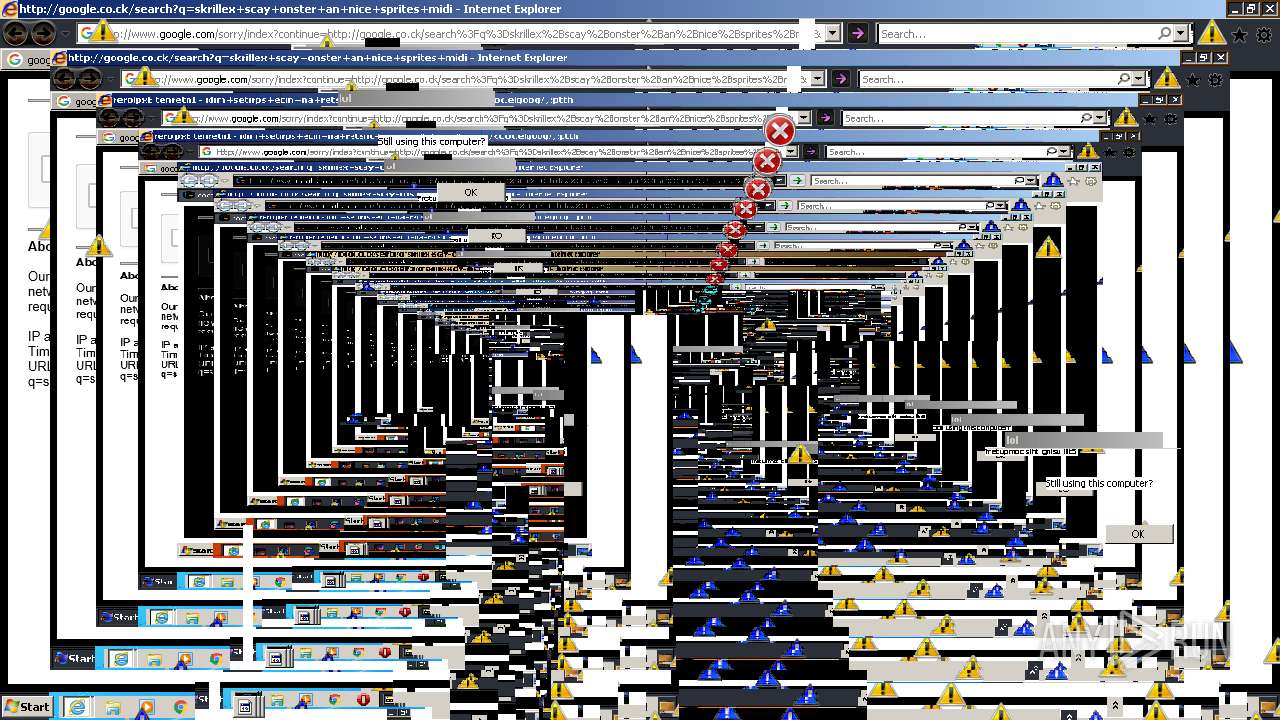
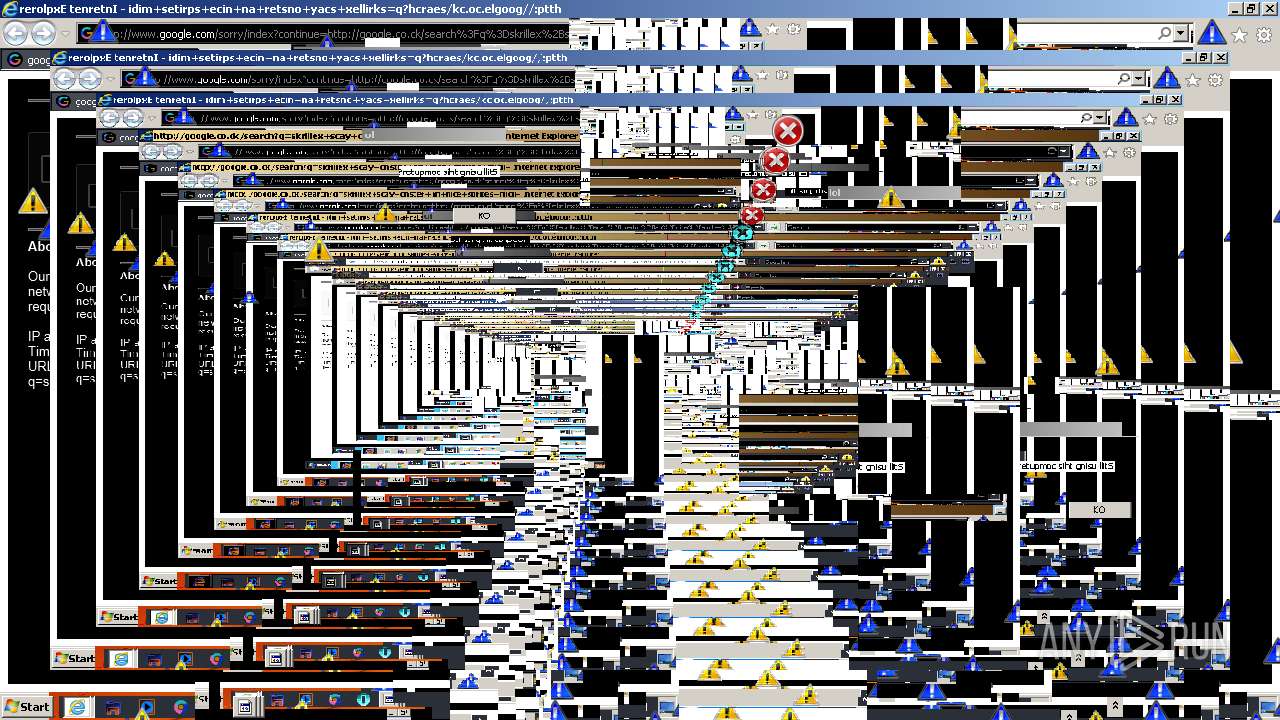
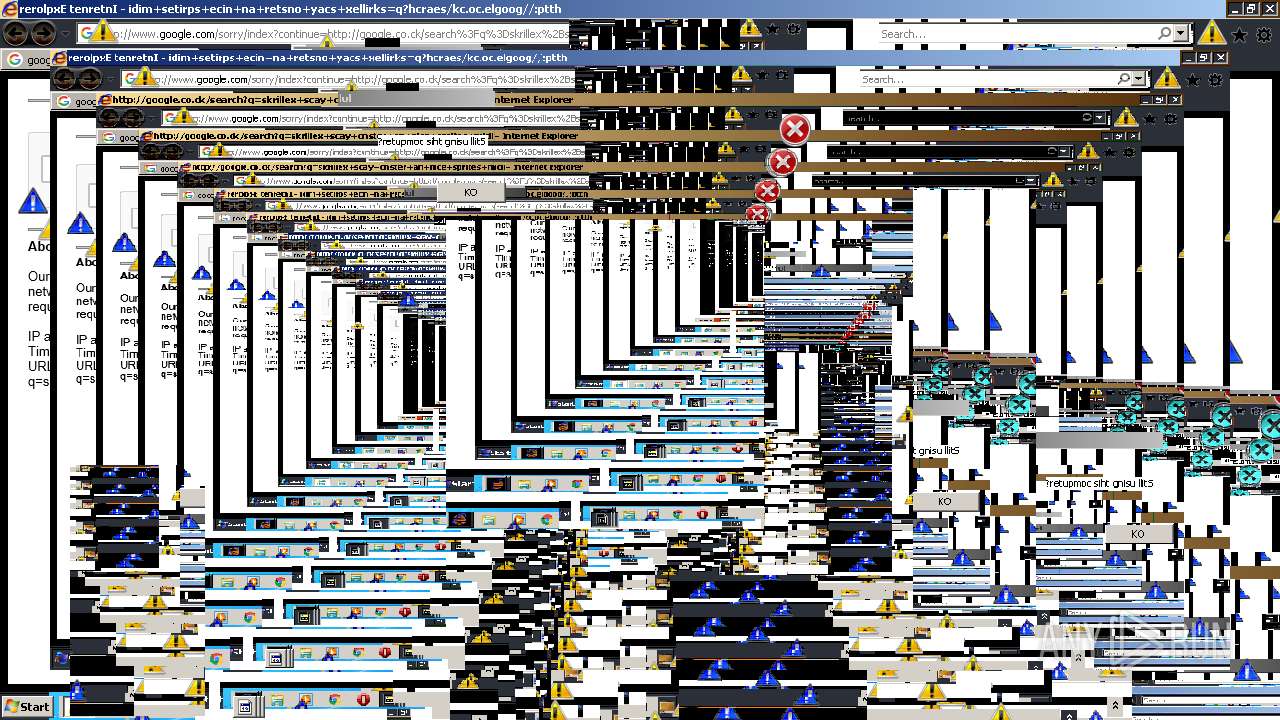
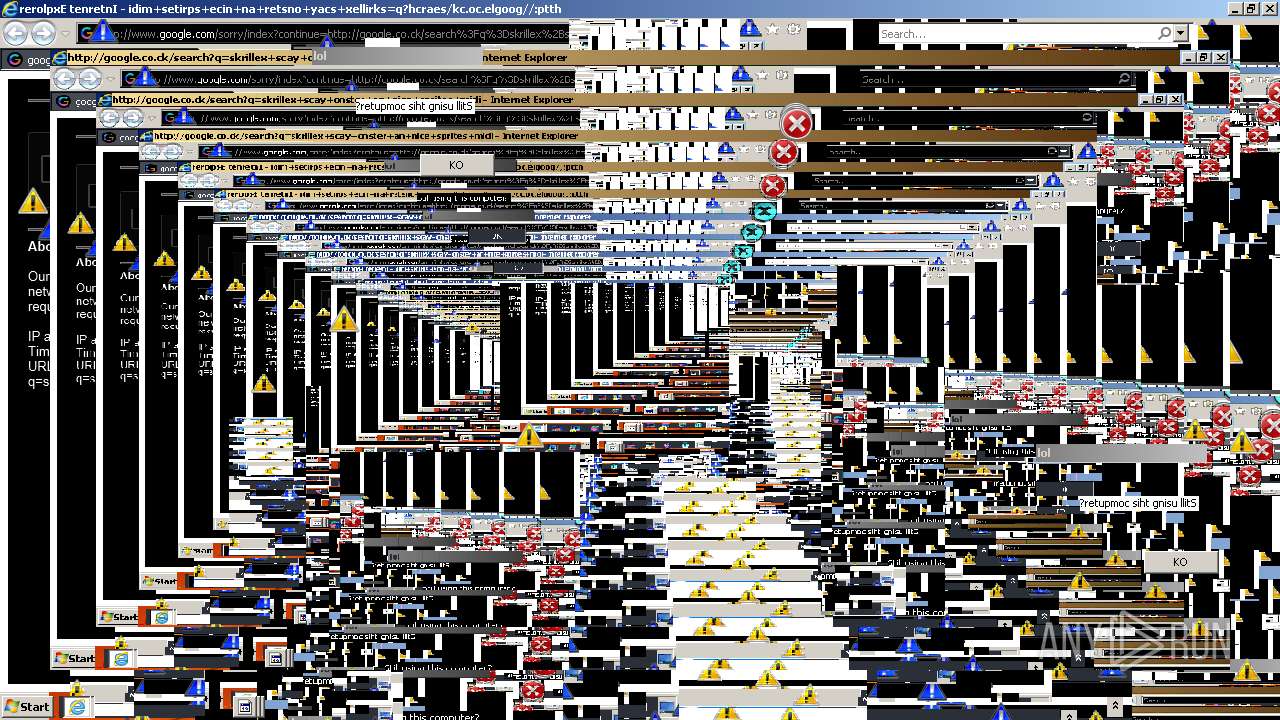
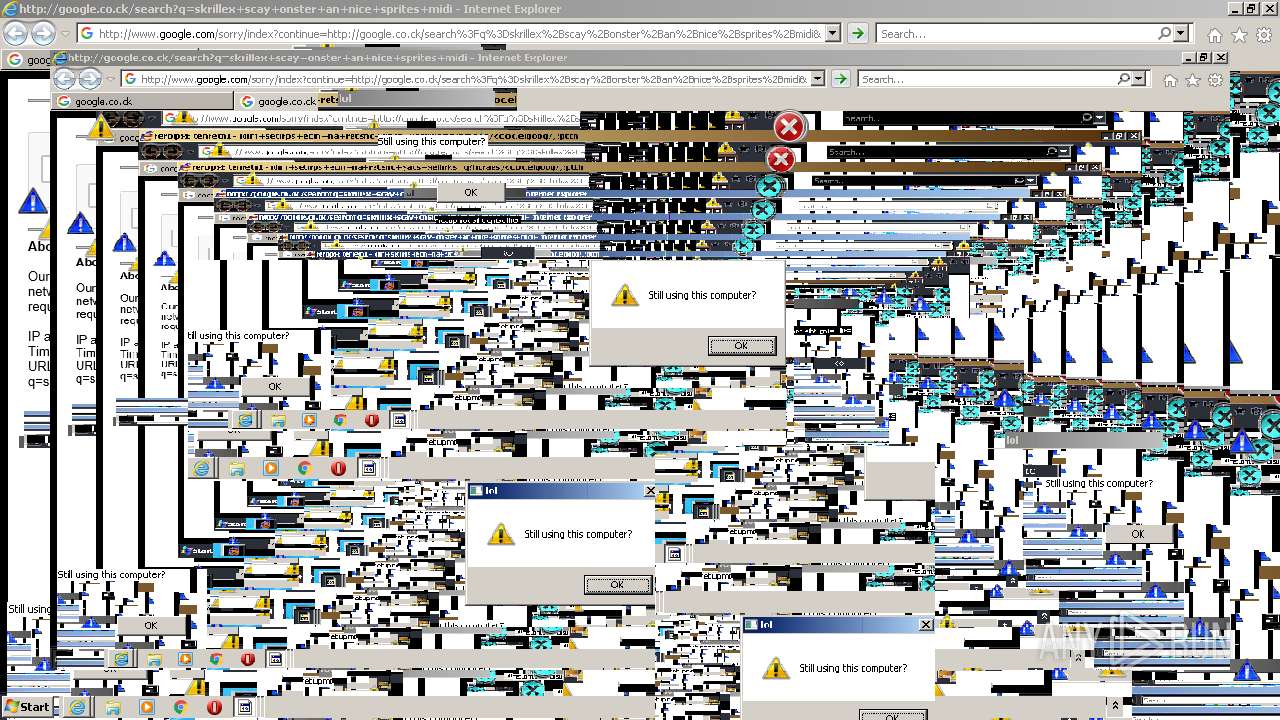
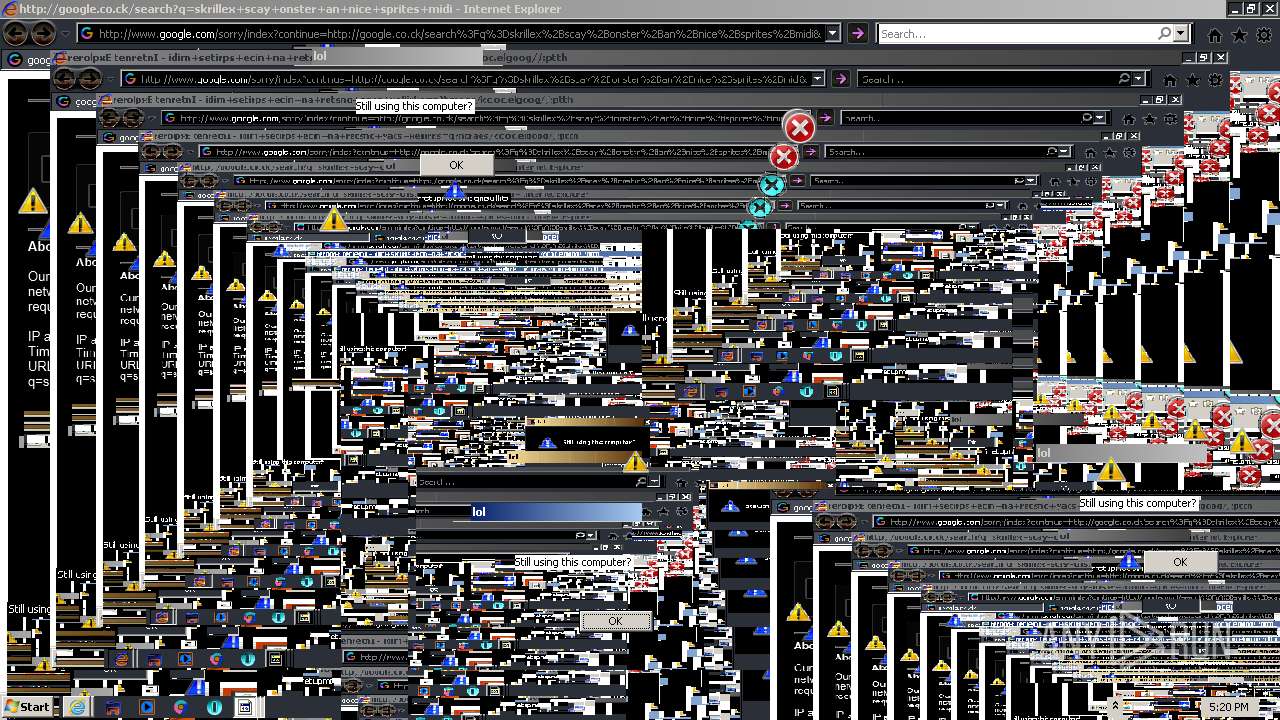
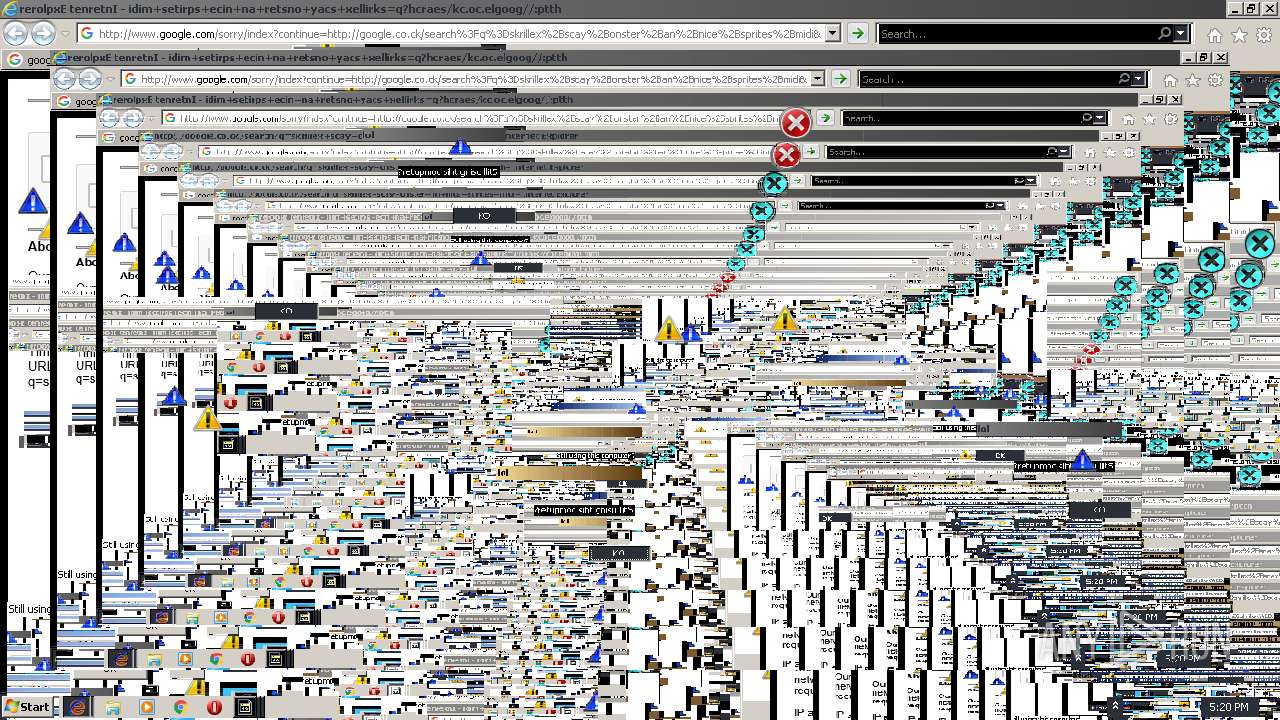
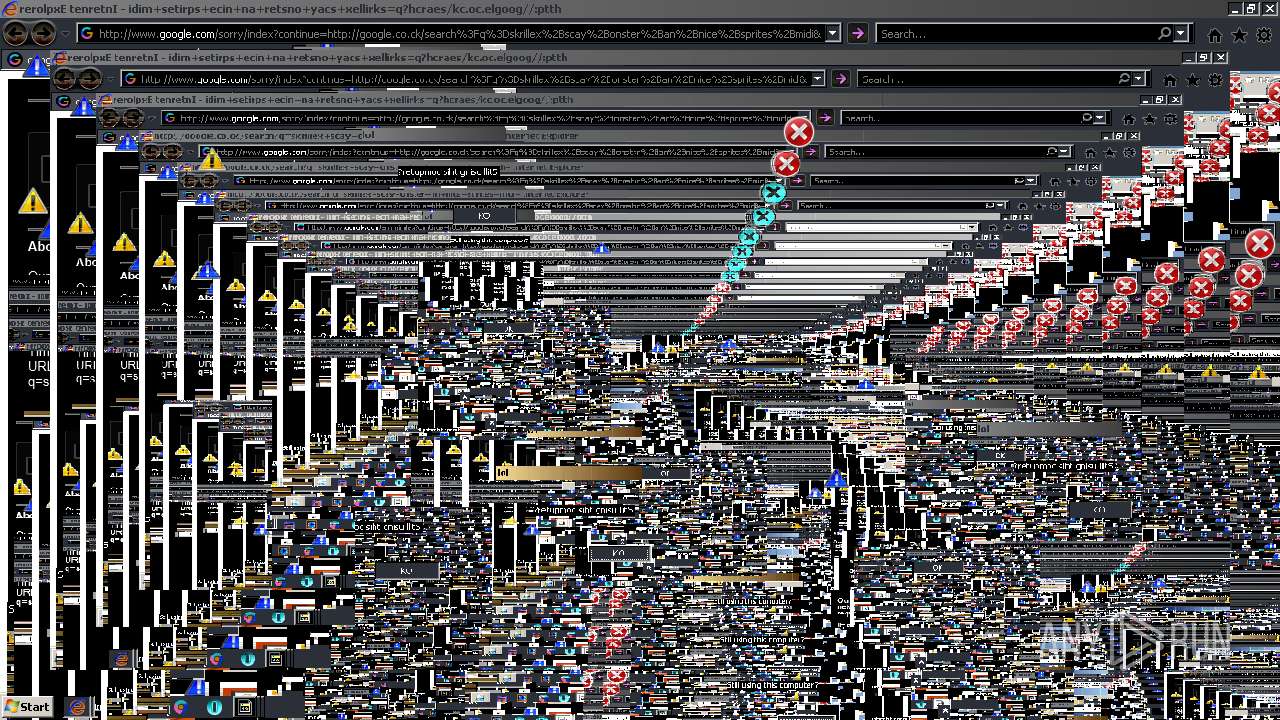
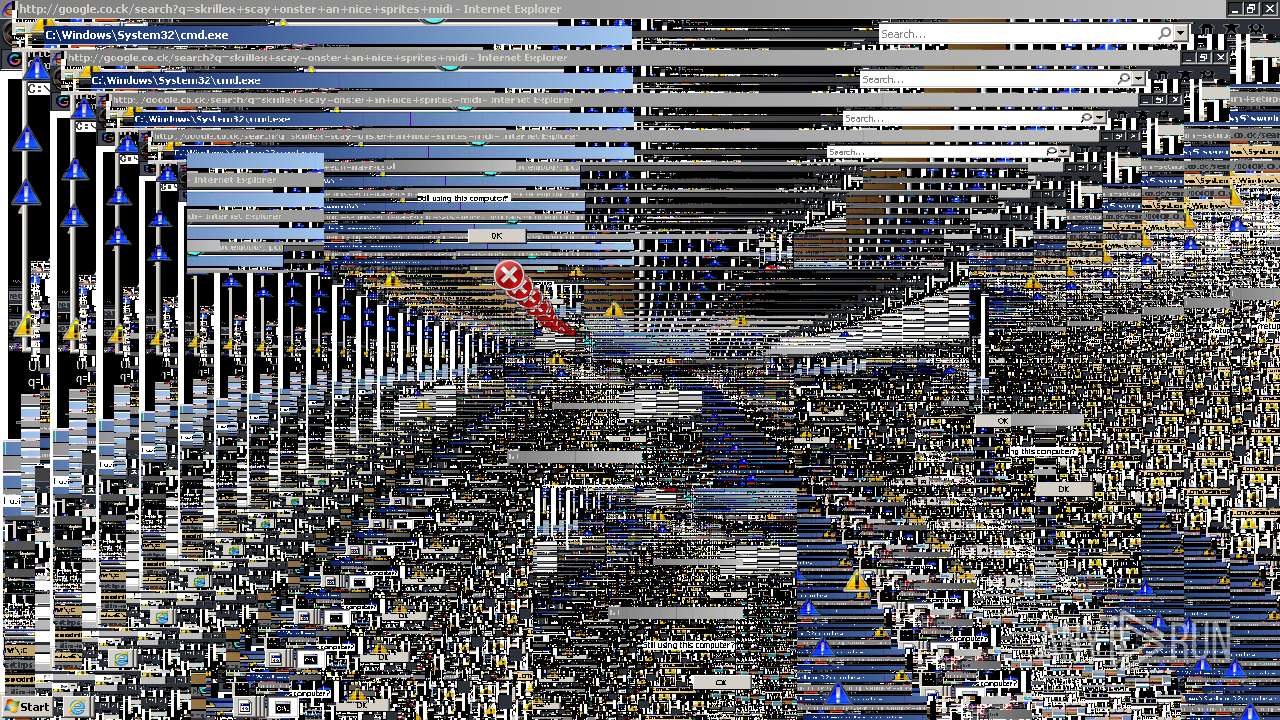
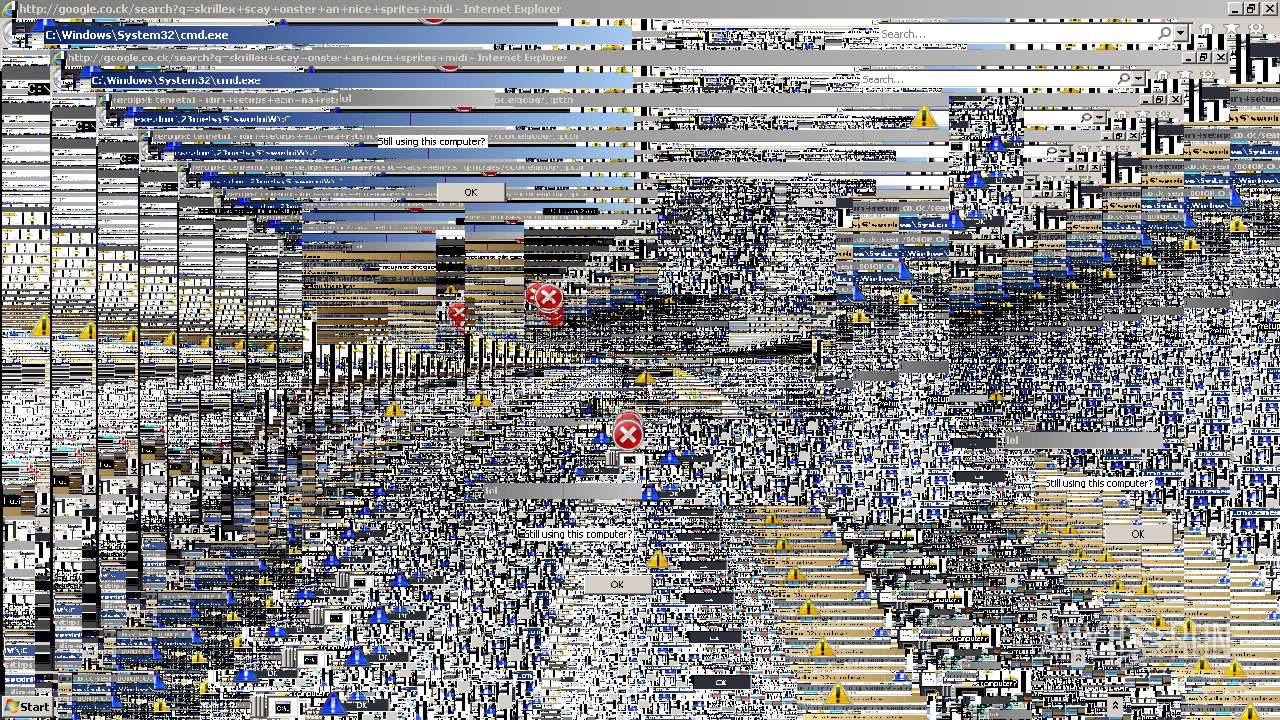
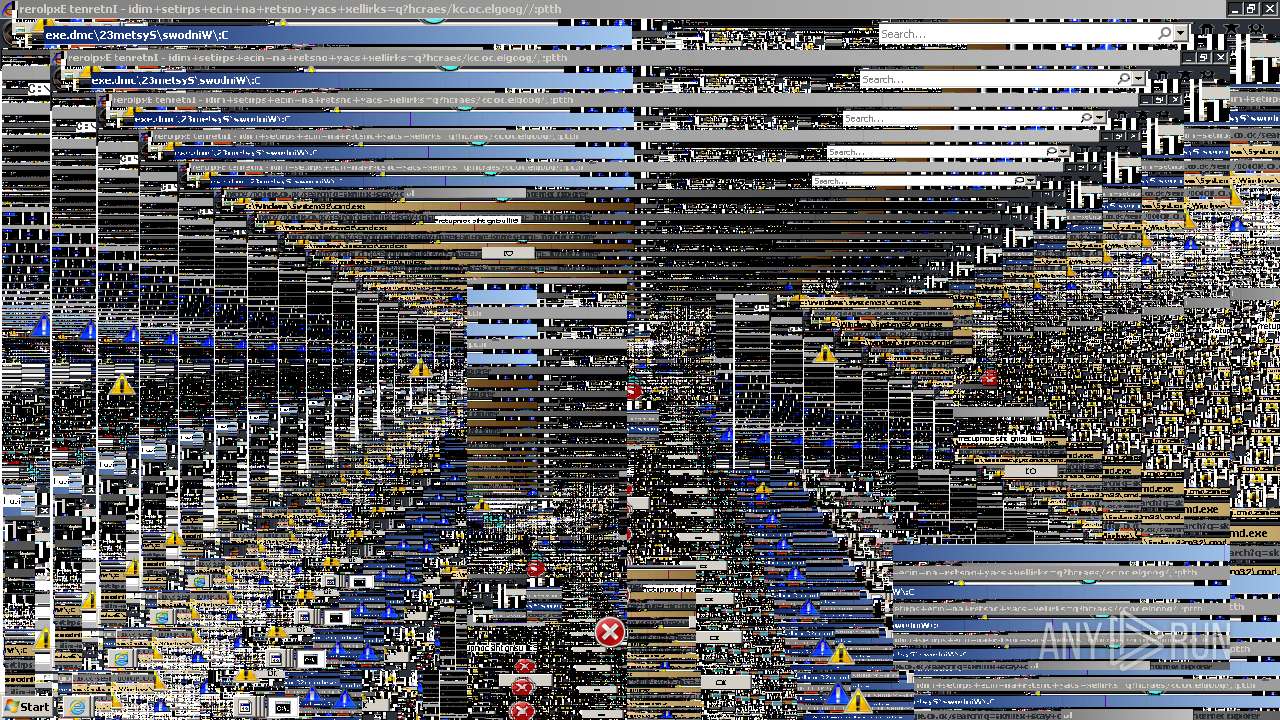
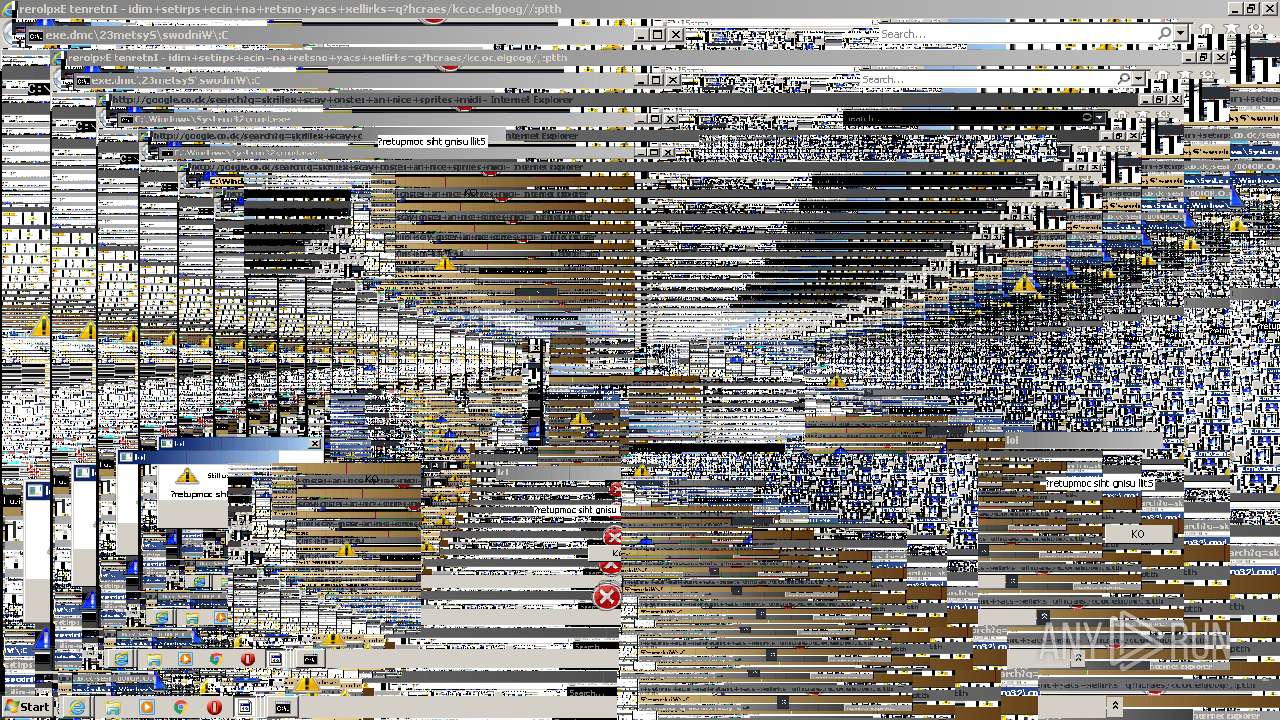
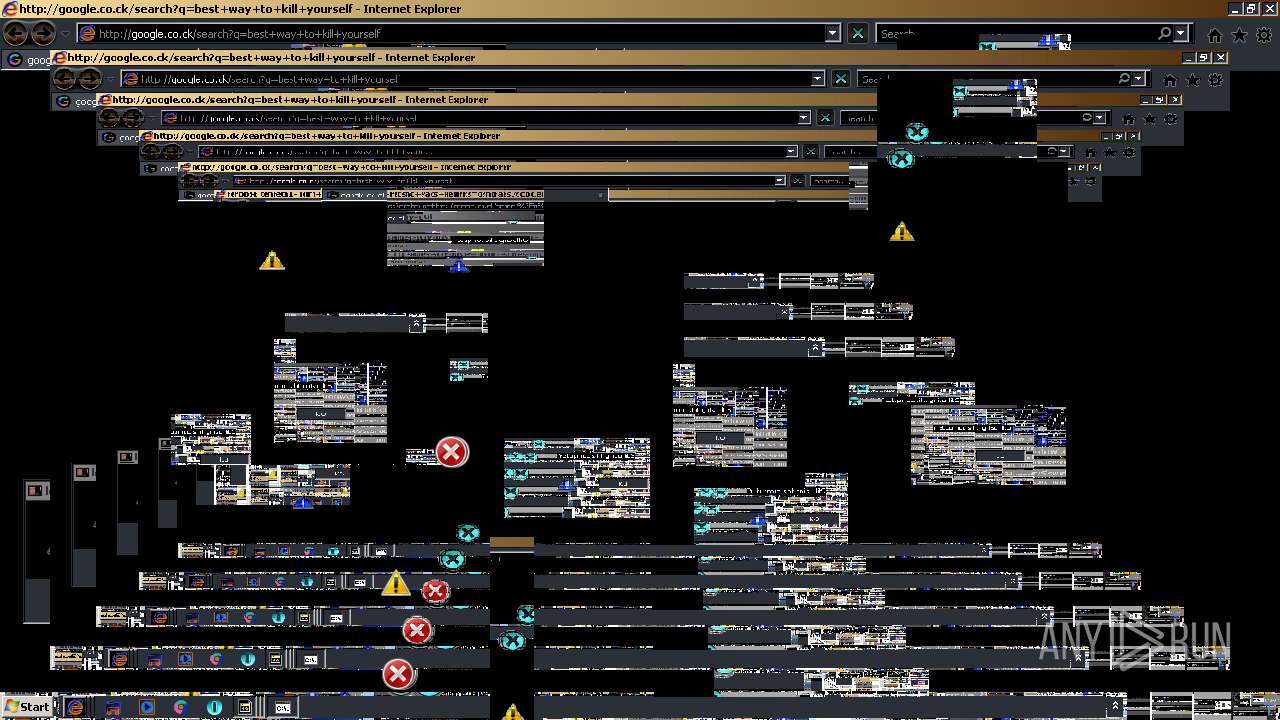
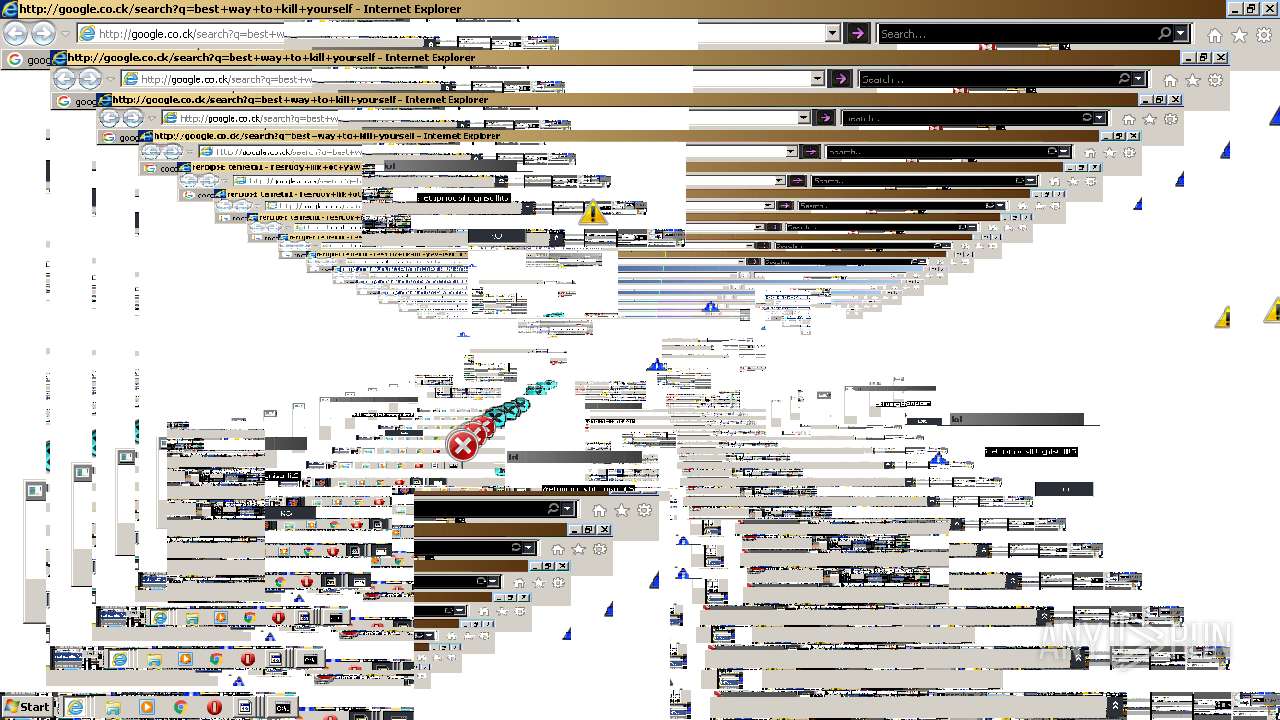
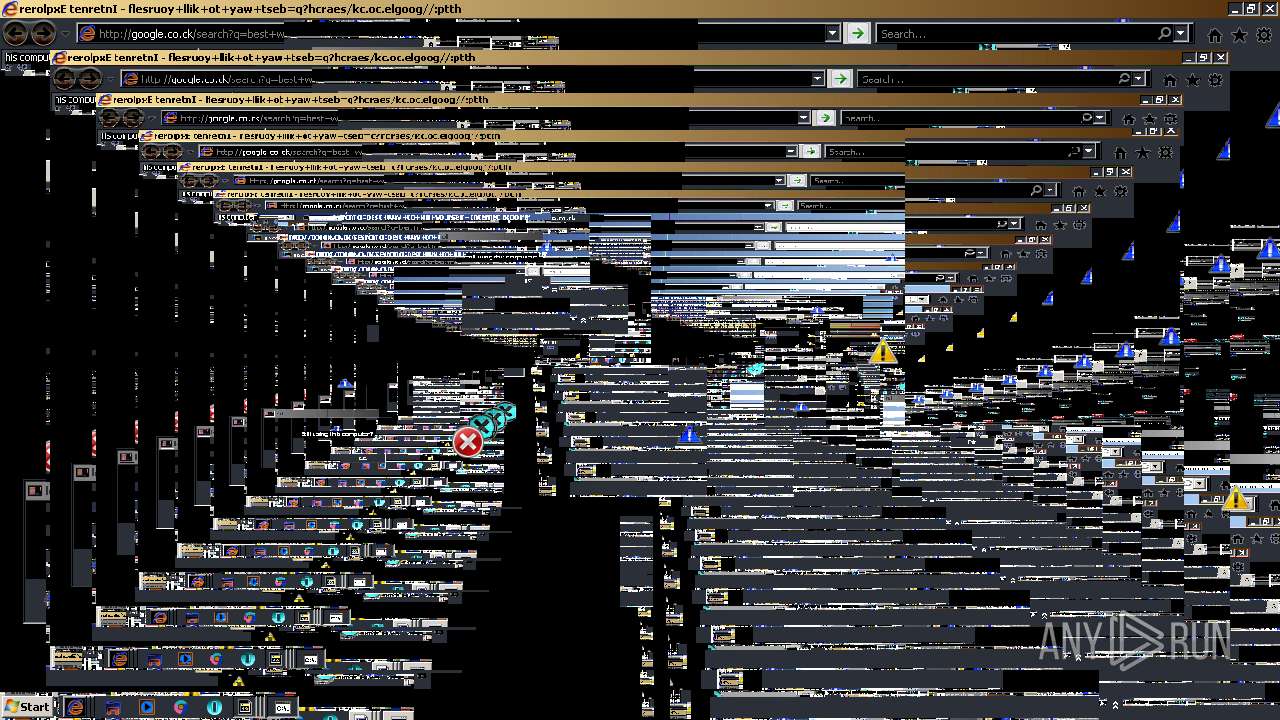
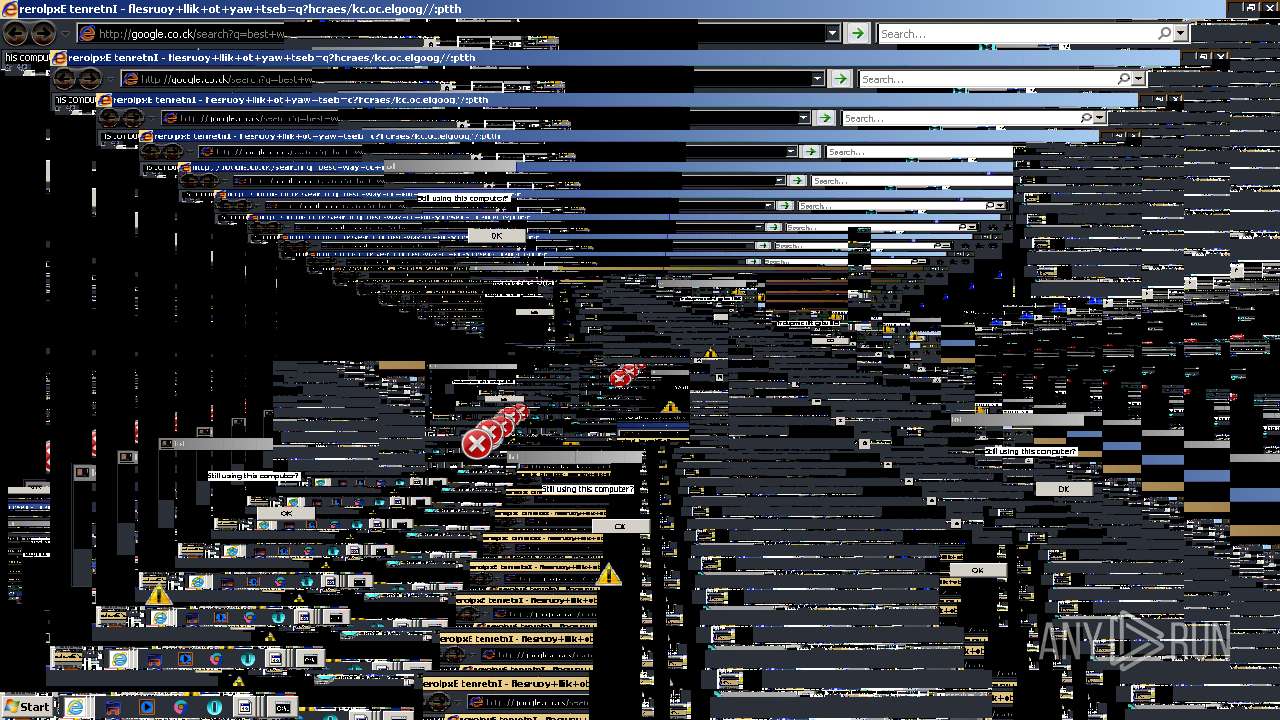
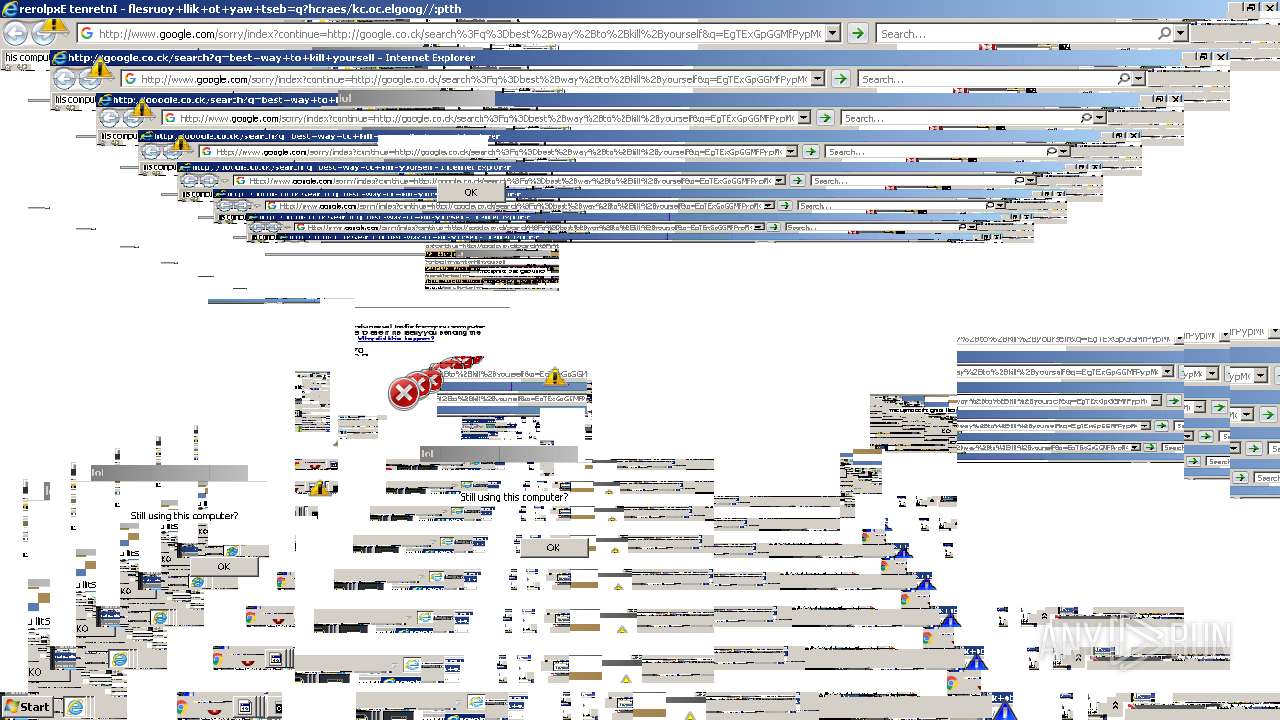
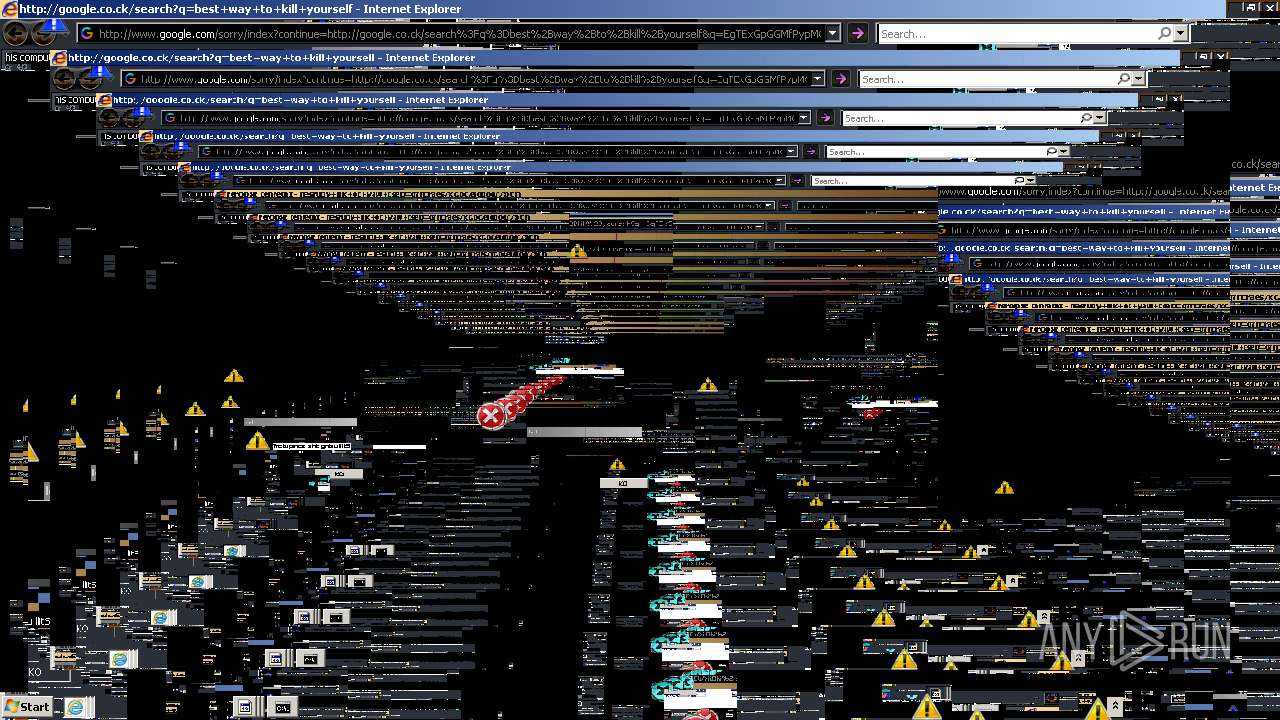
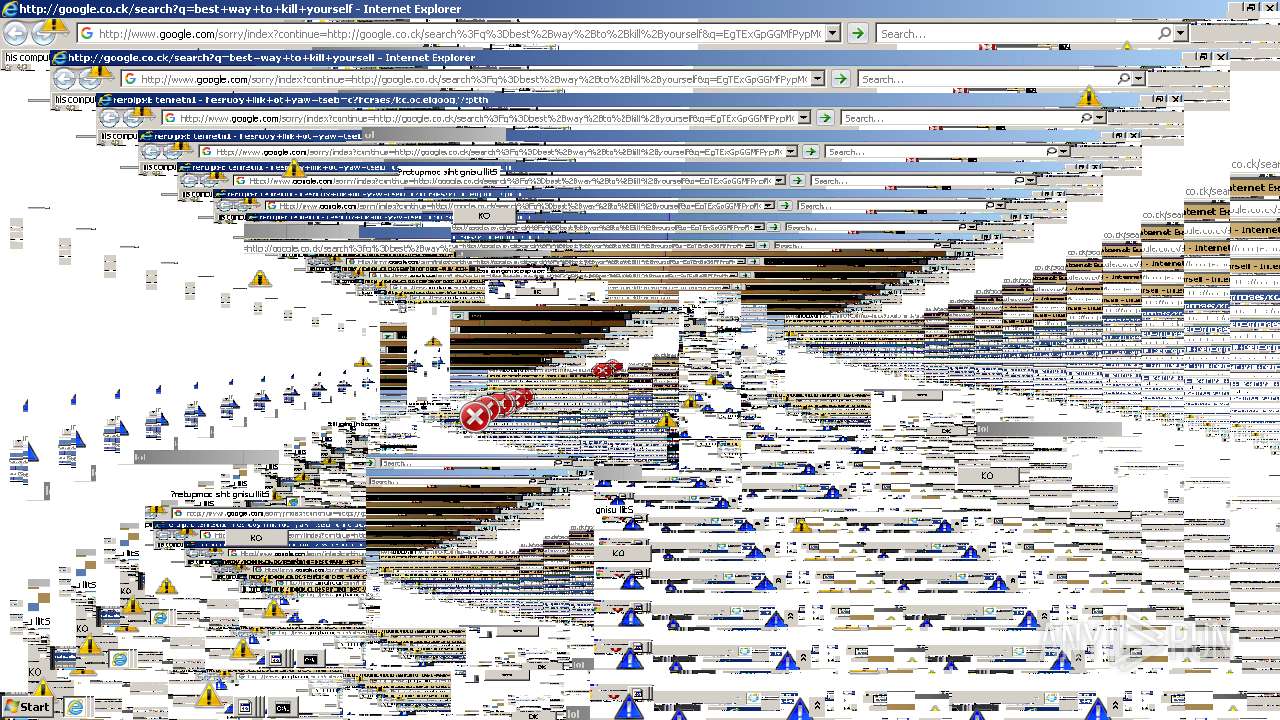
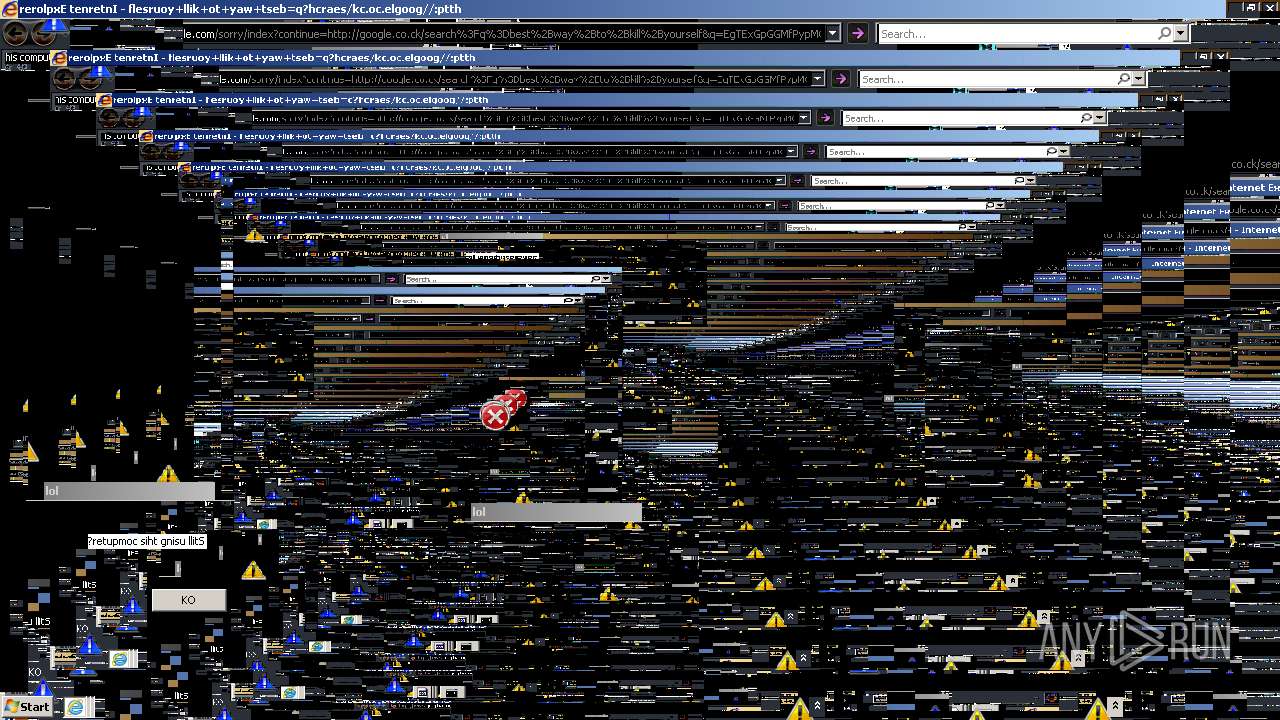
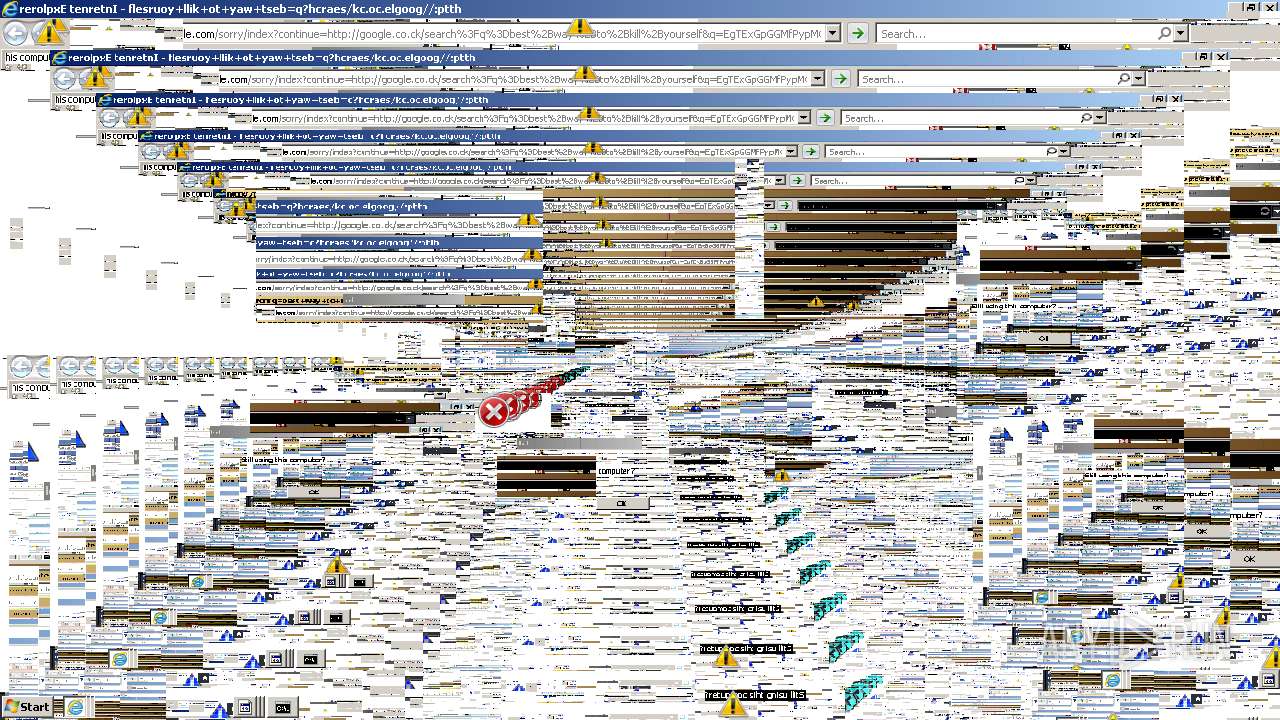
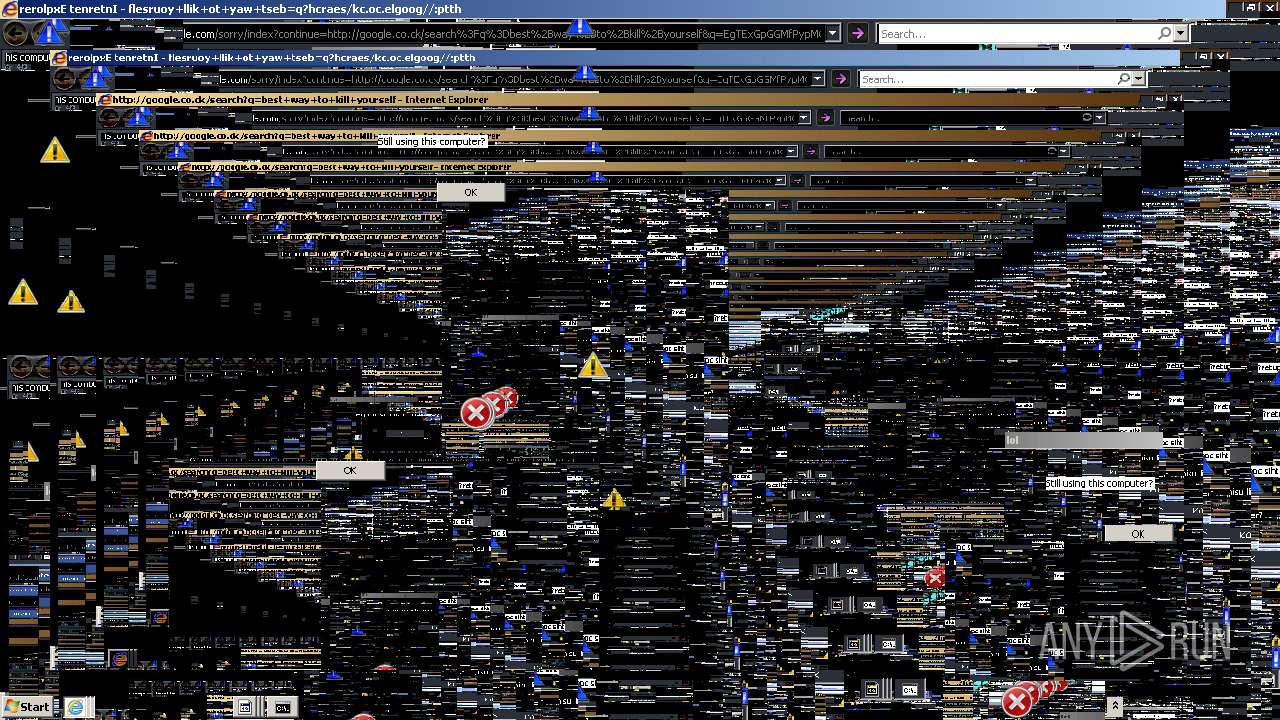
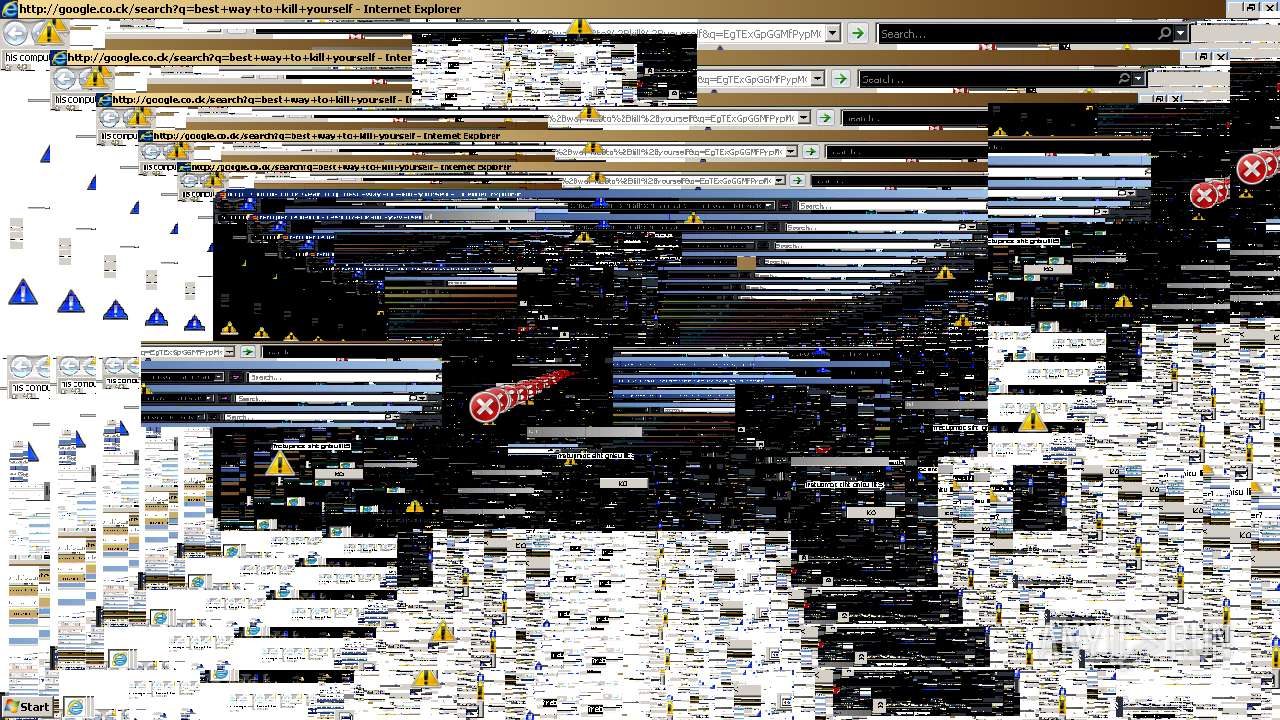
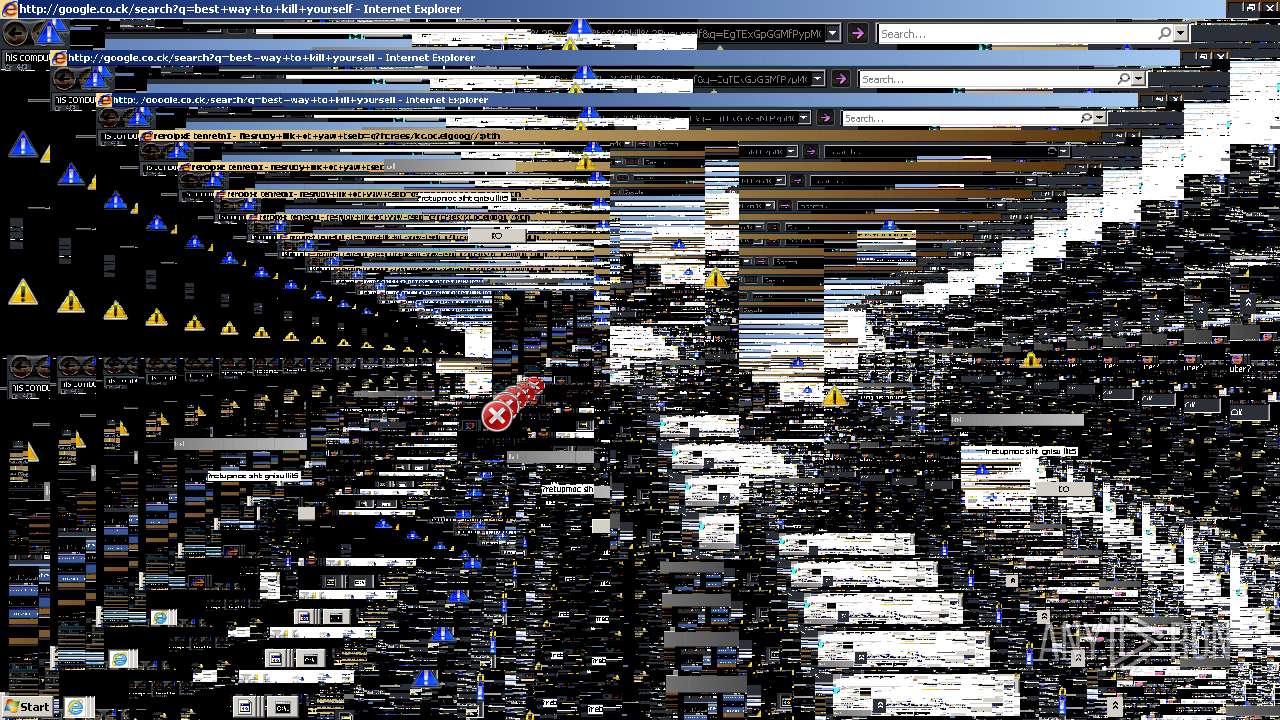
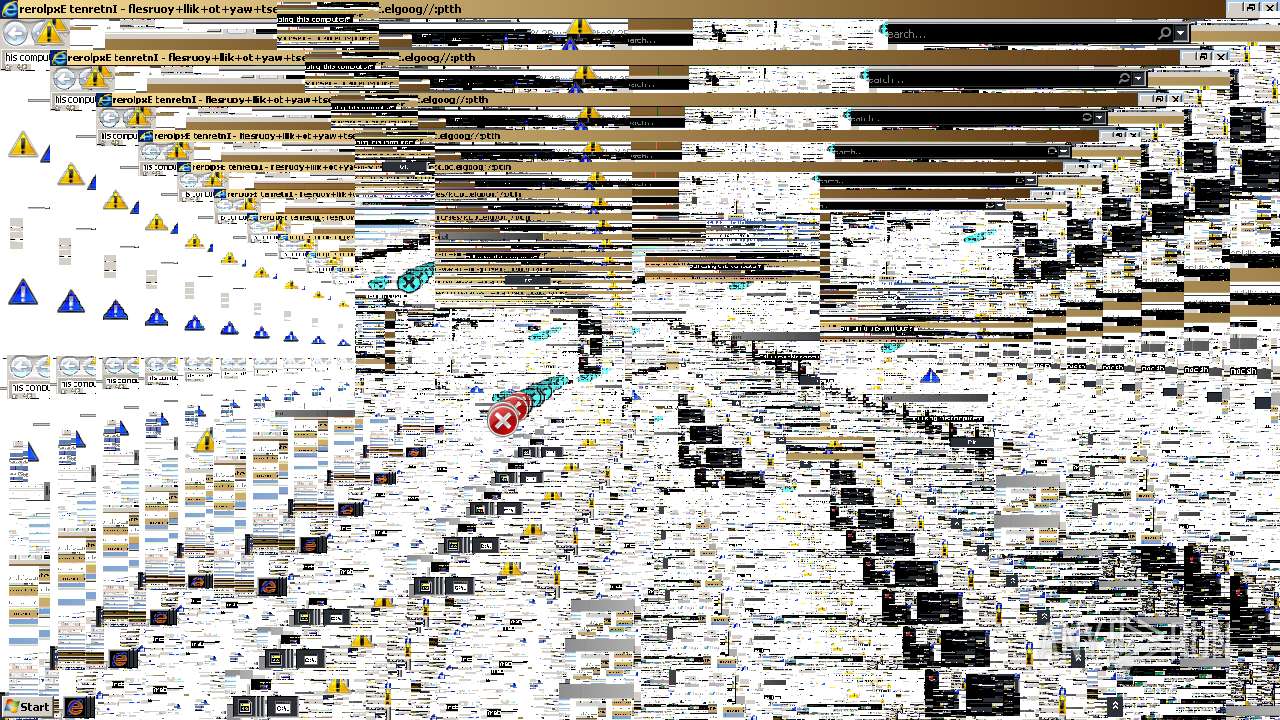
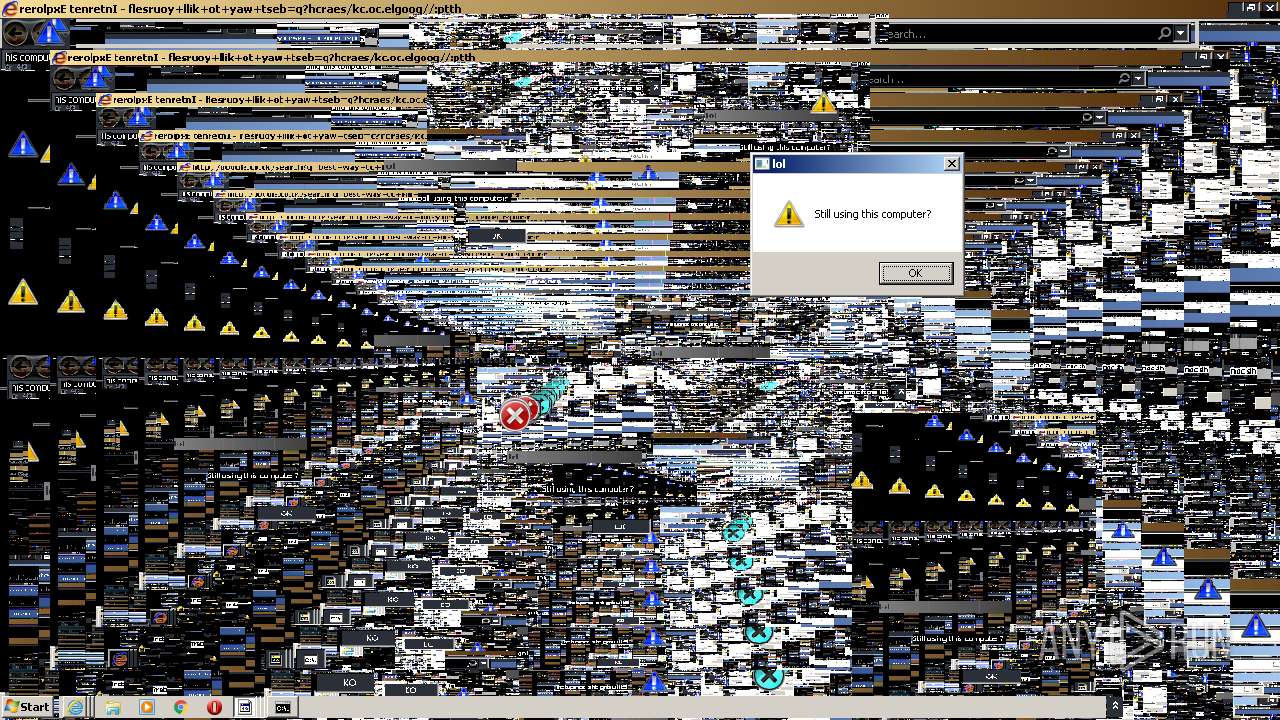
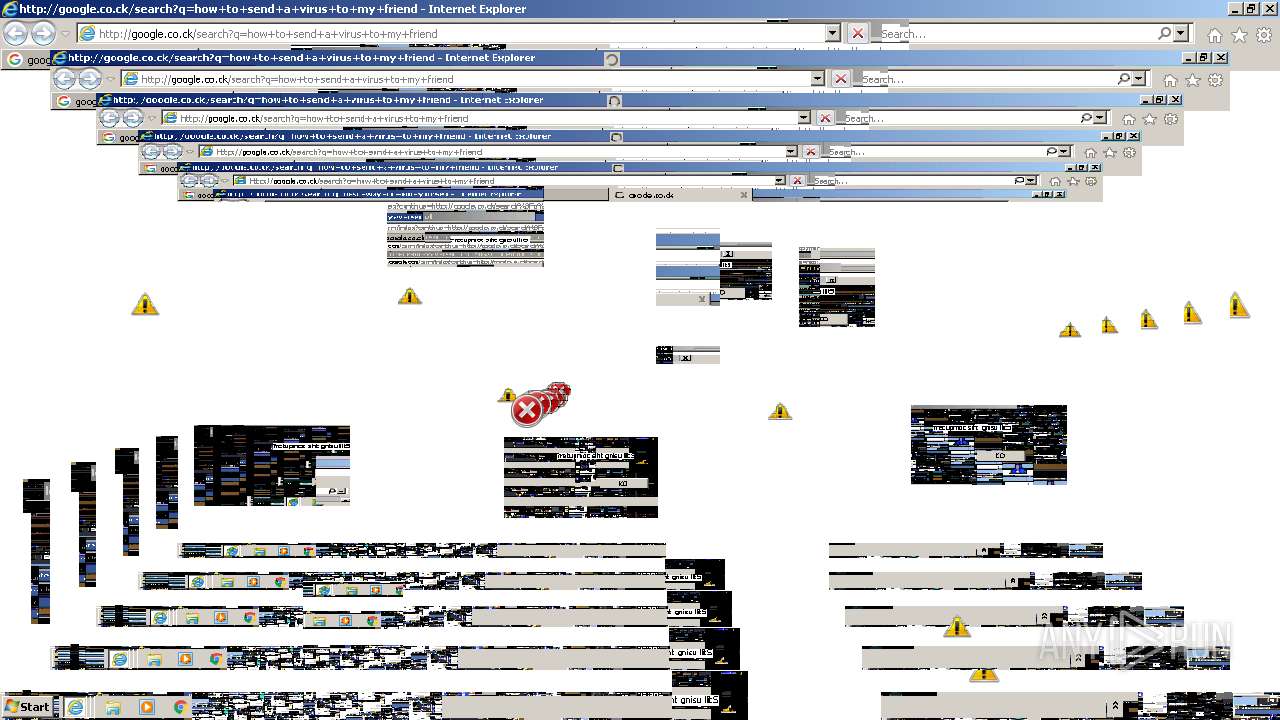
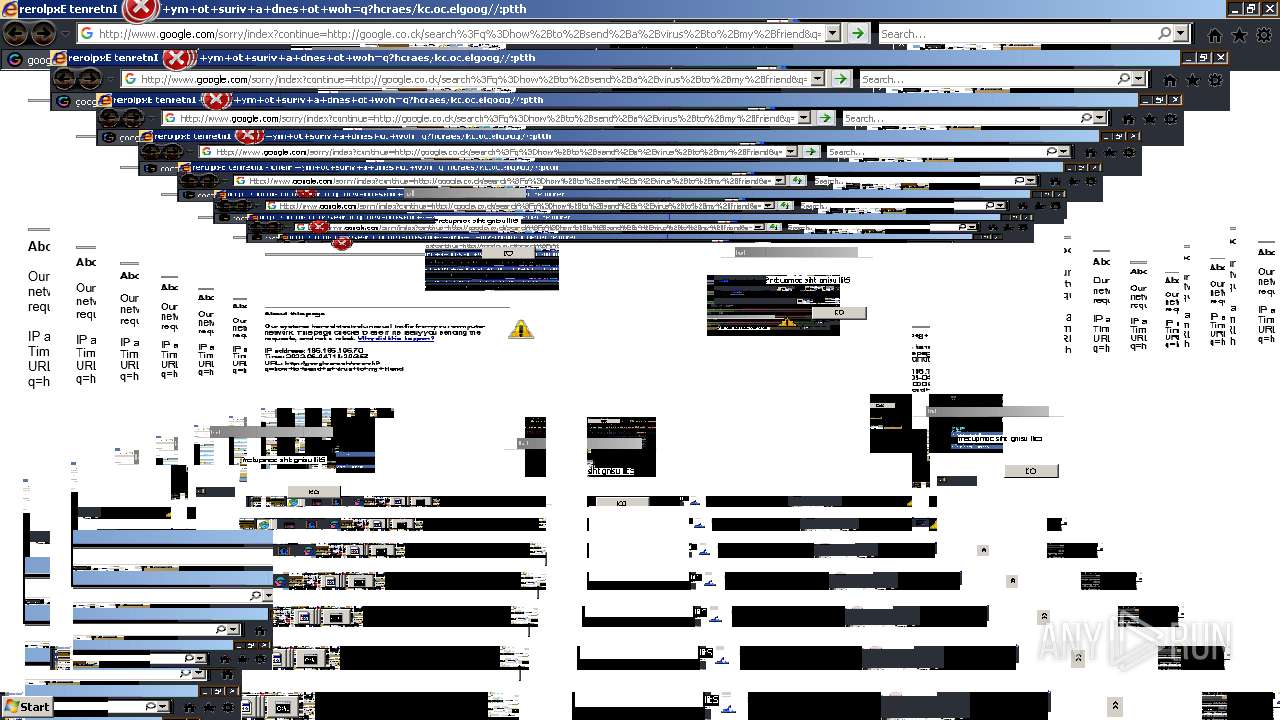
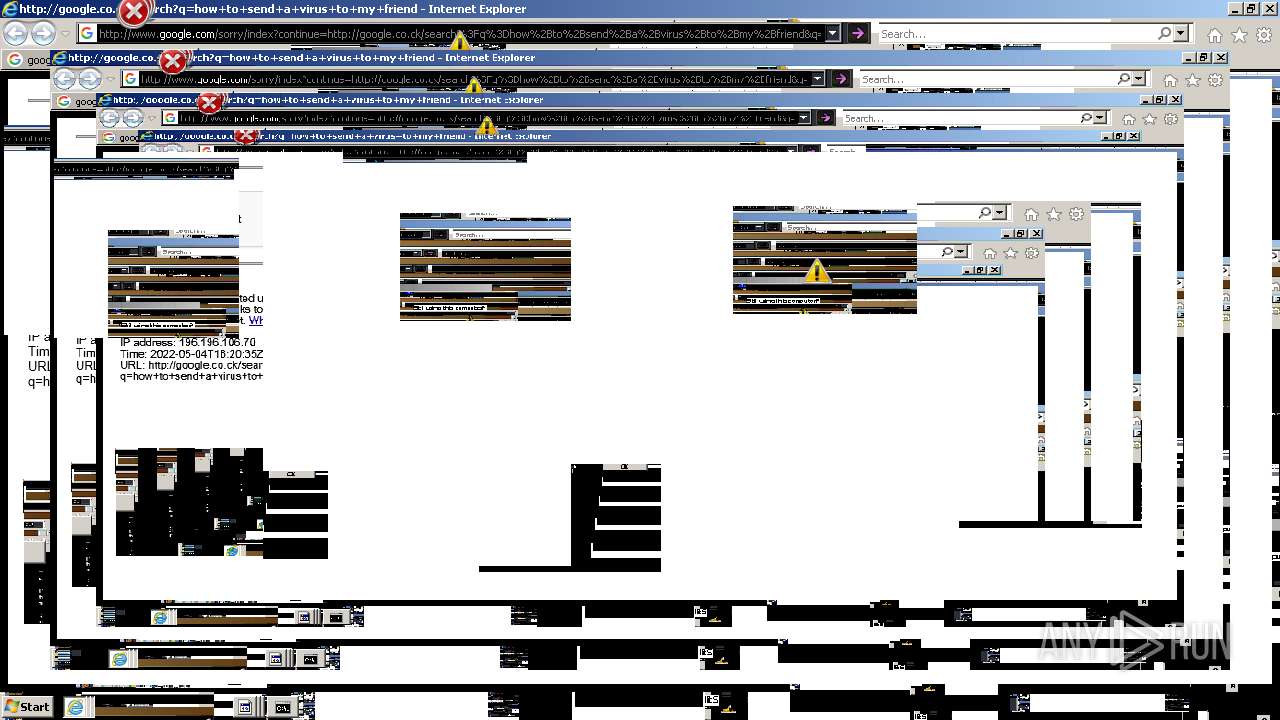
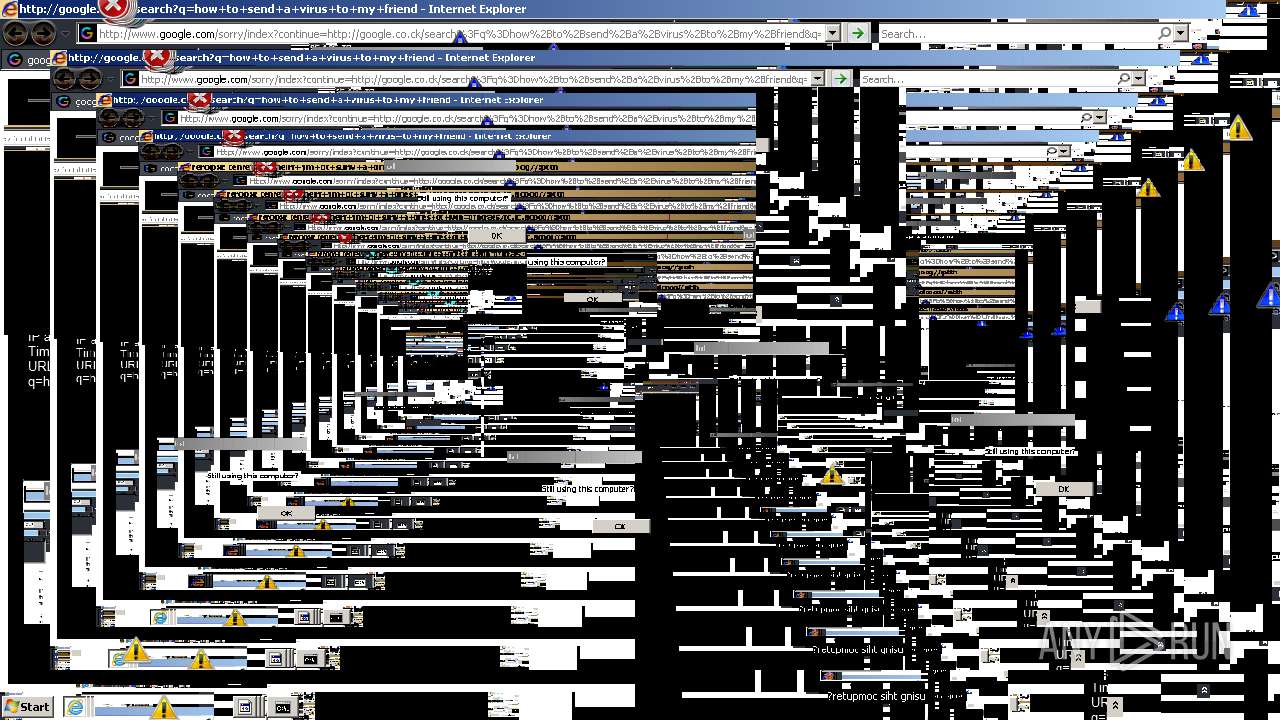
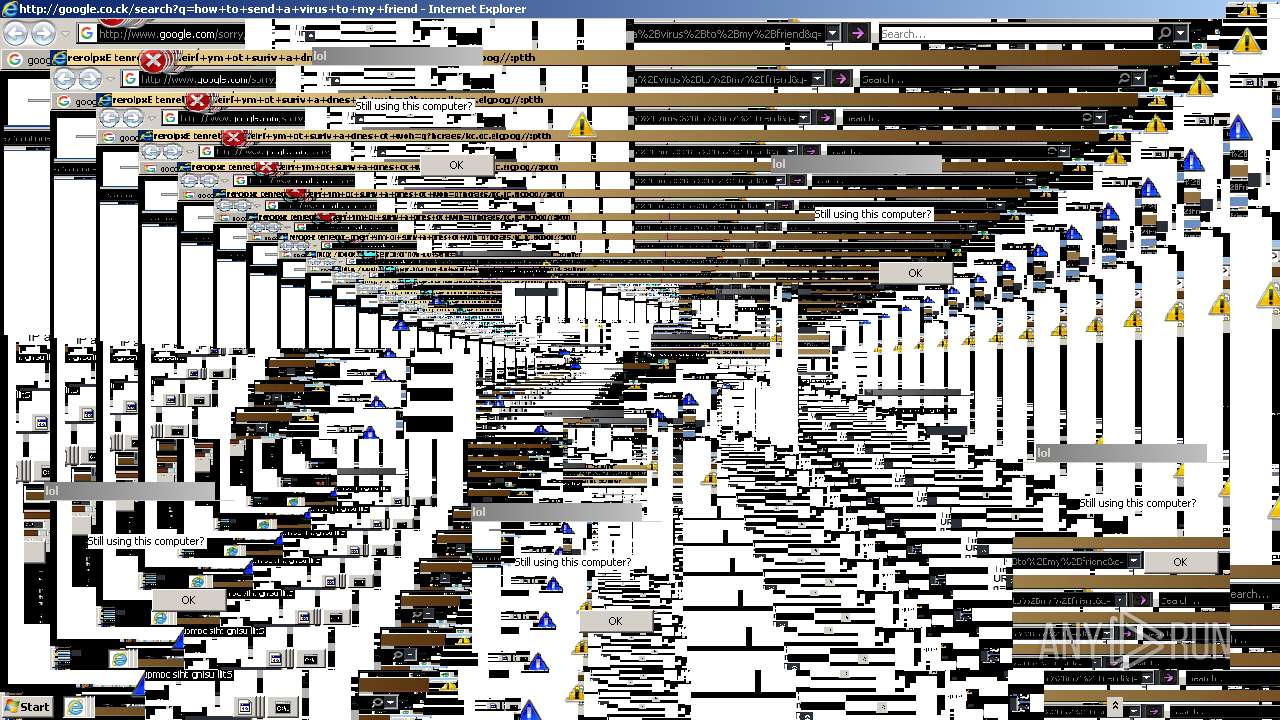
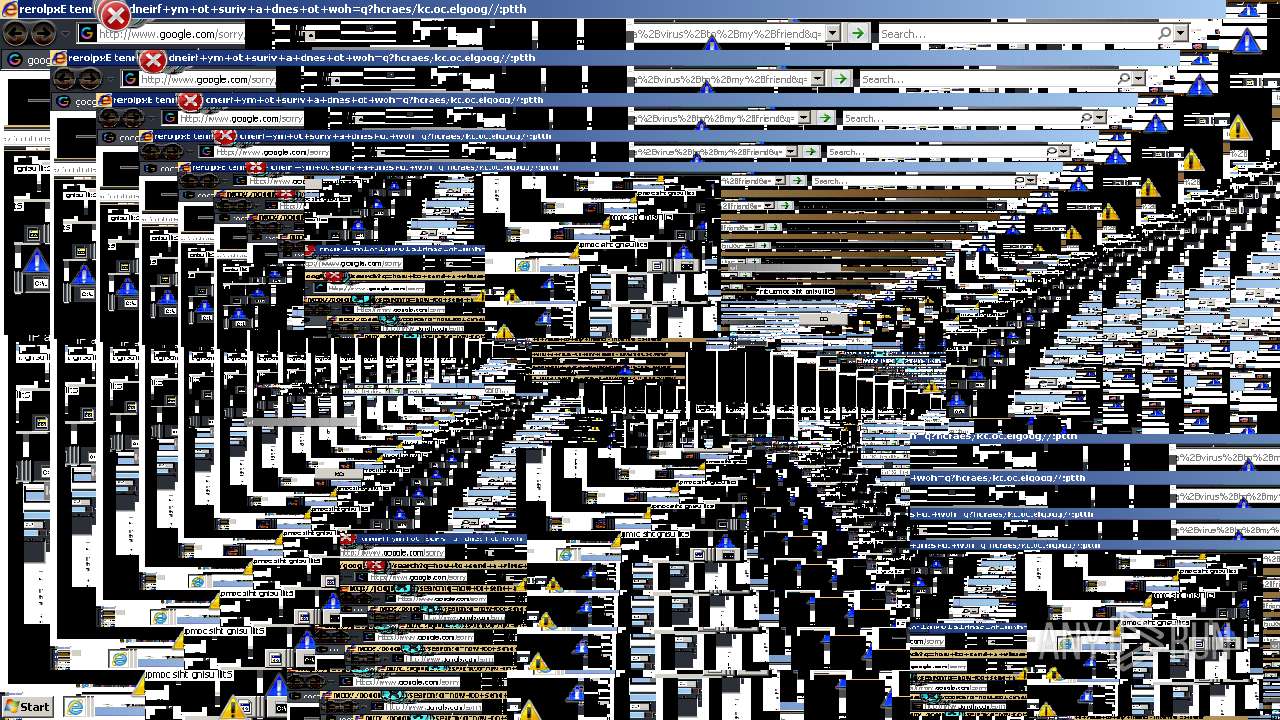
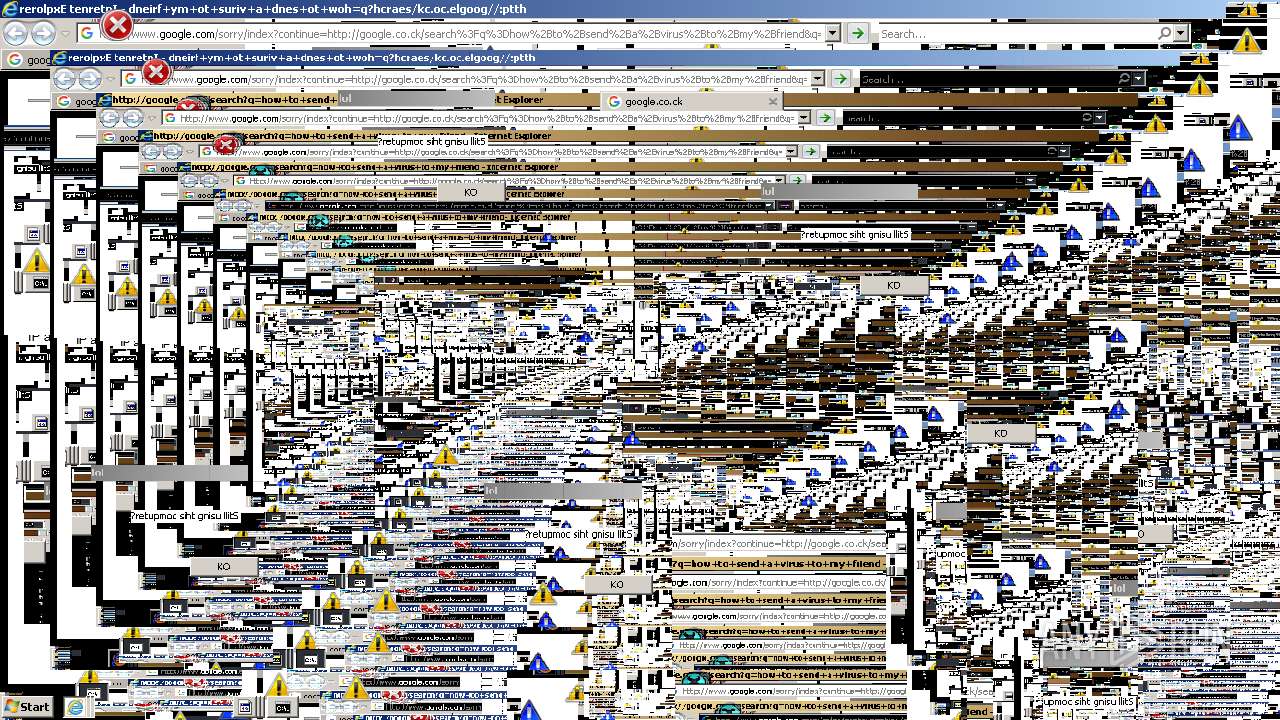
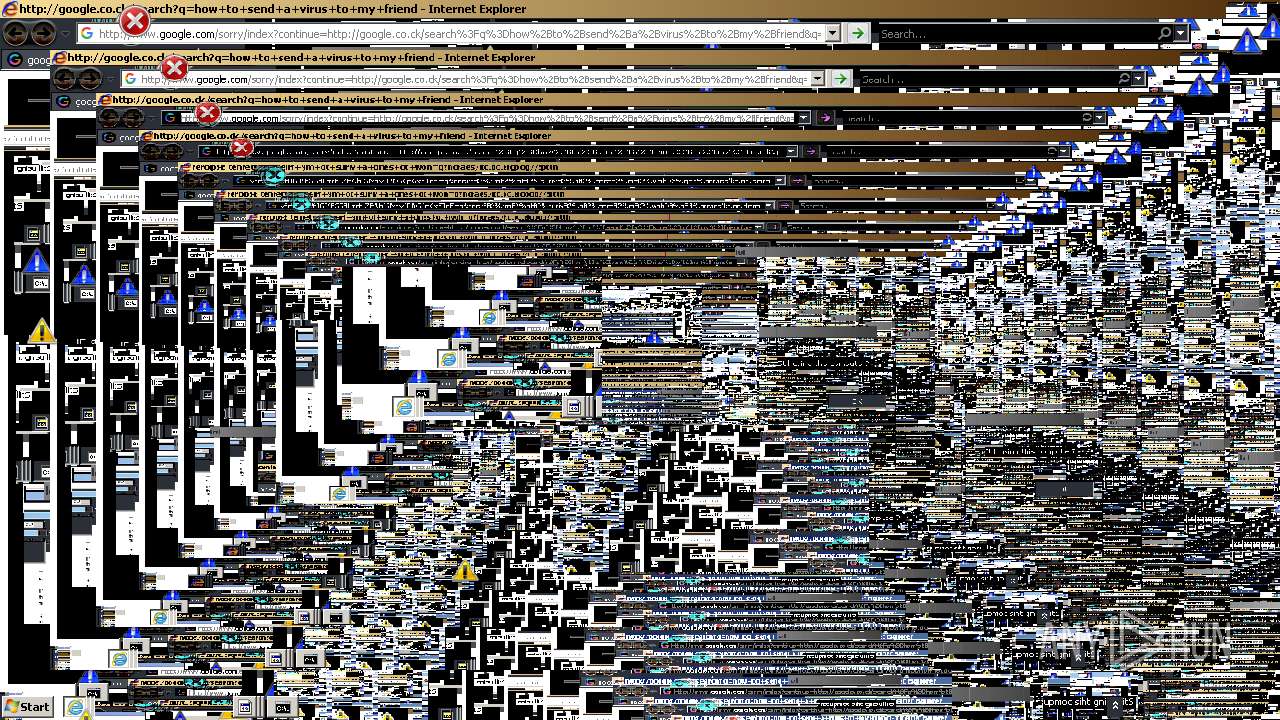
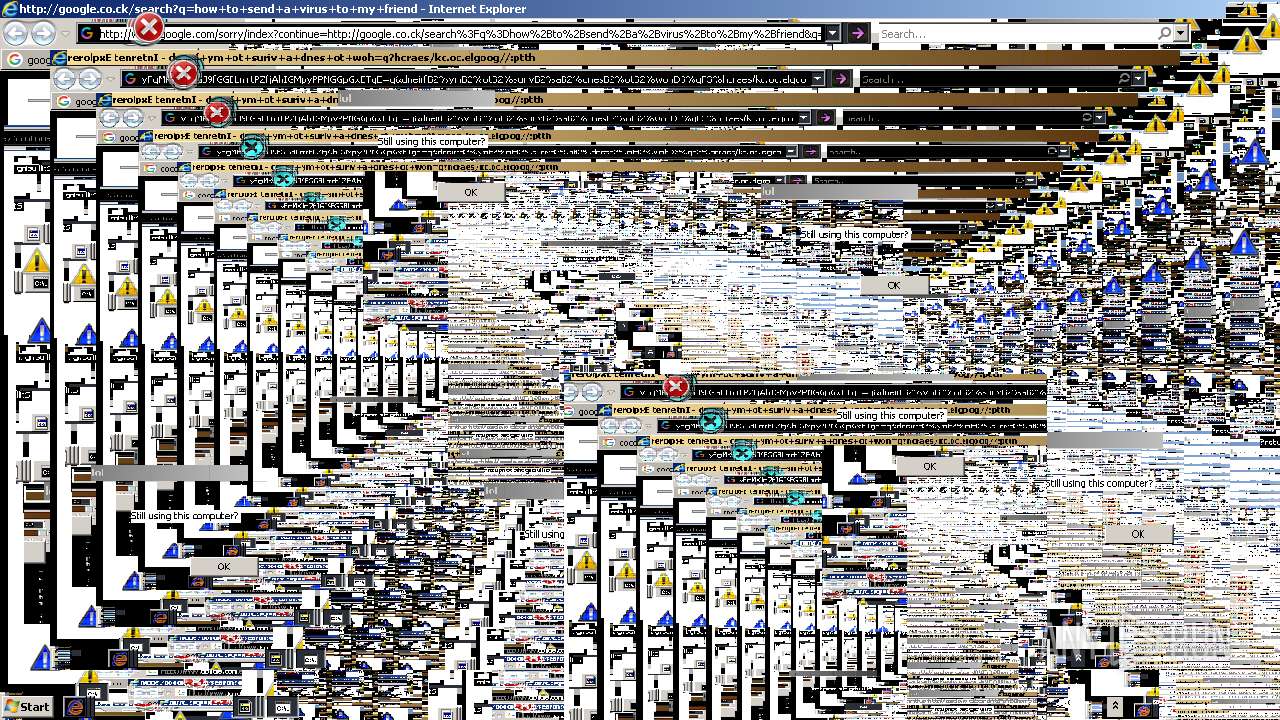
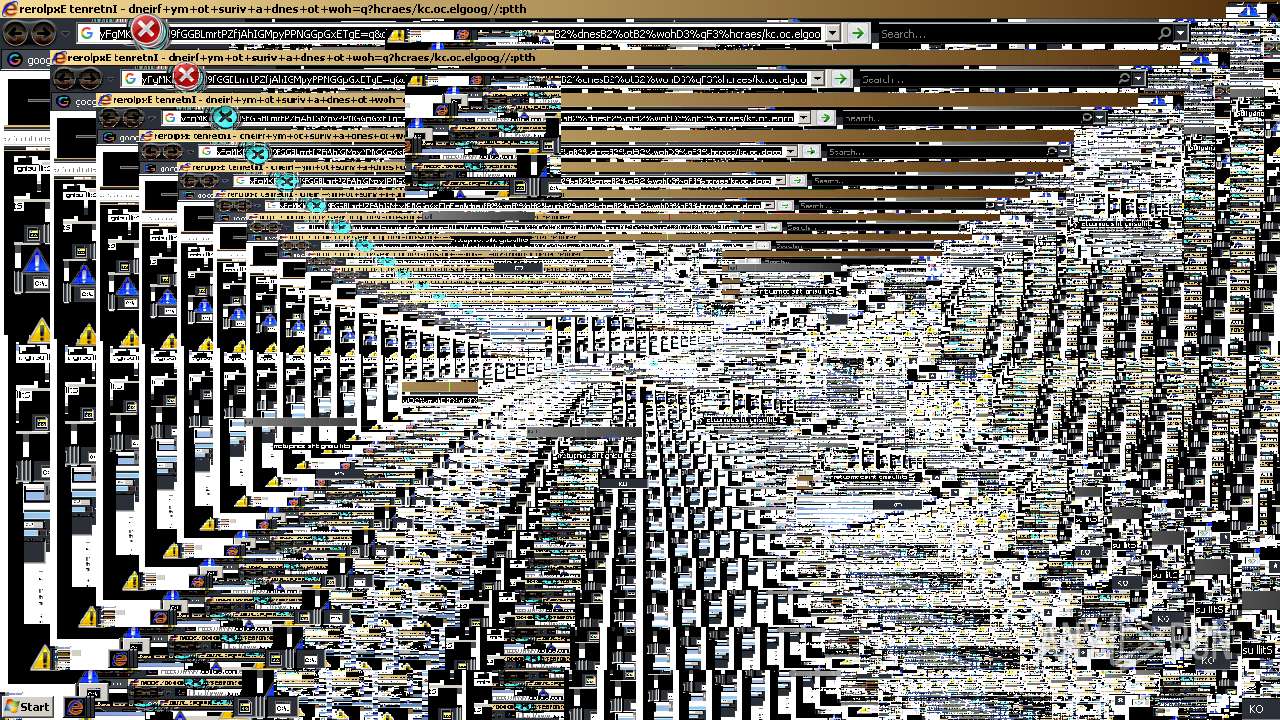
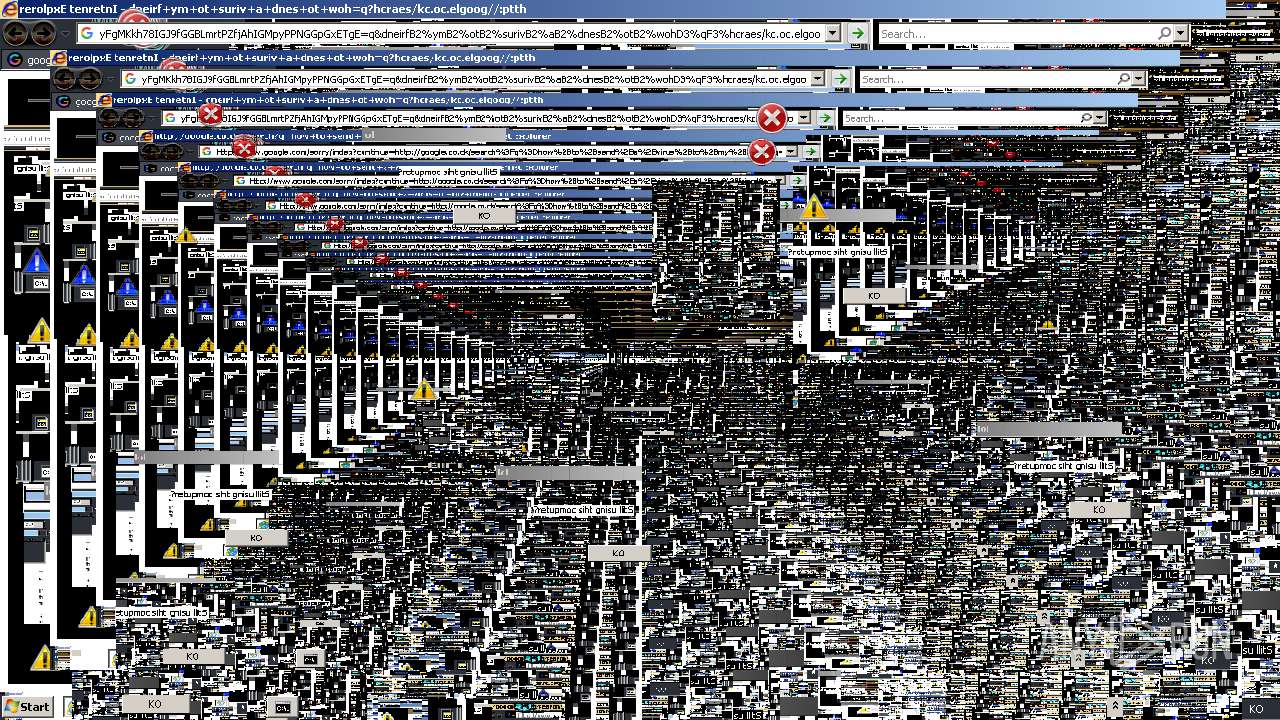
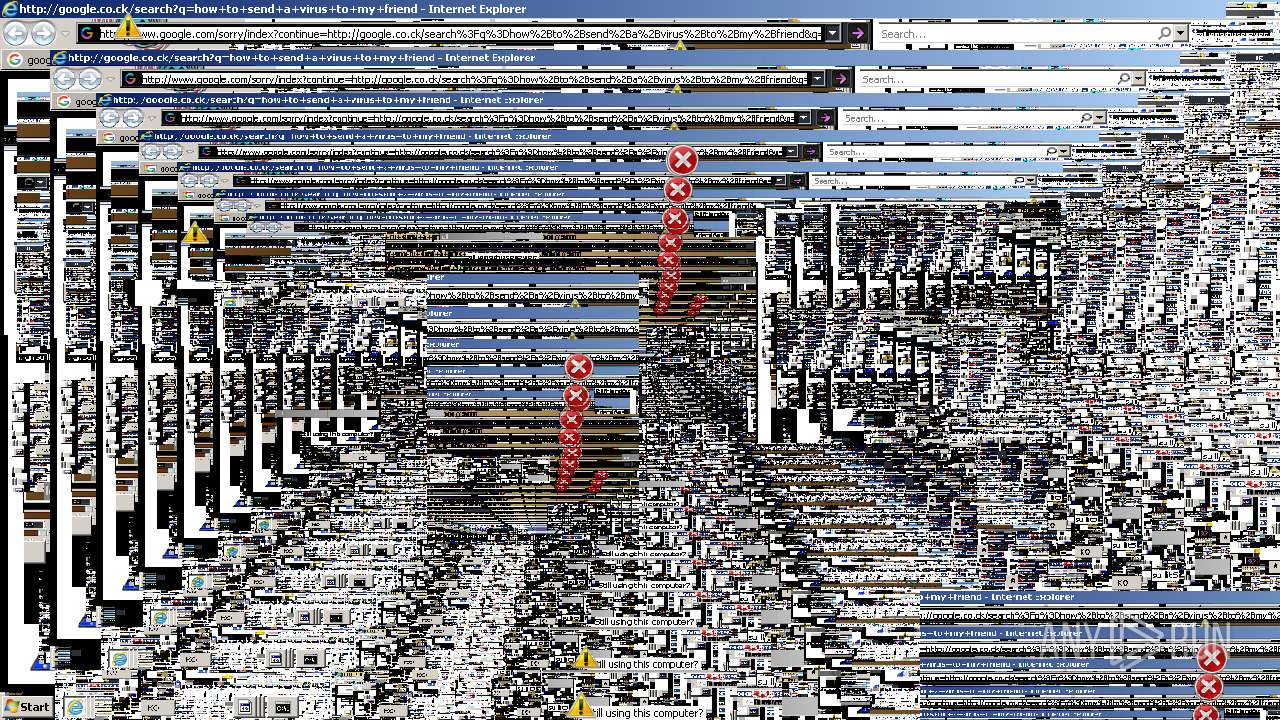
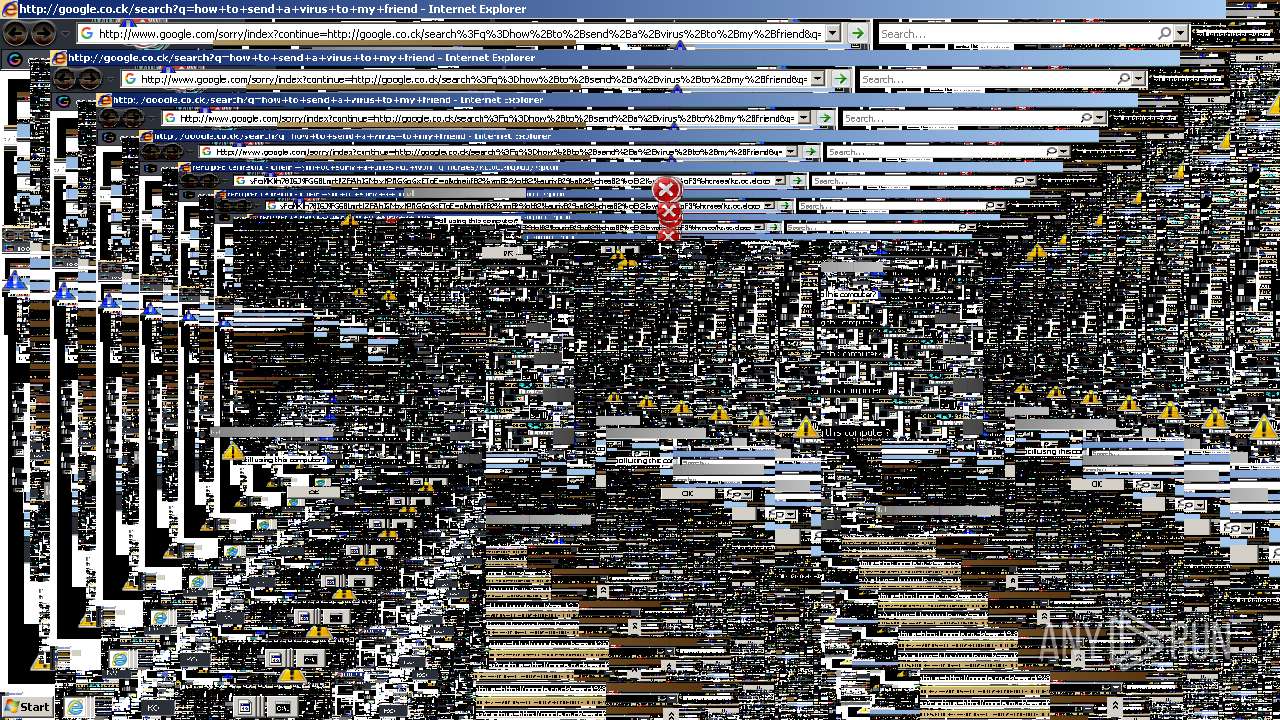
Starts Internet Explorer
- MEMZ-Clean.exe (PID: 3080)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 736)
- iexplore.exe (PID: 4012)
- iexplore.exe (PID: 1940)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 3148)
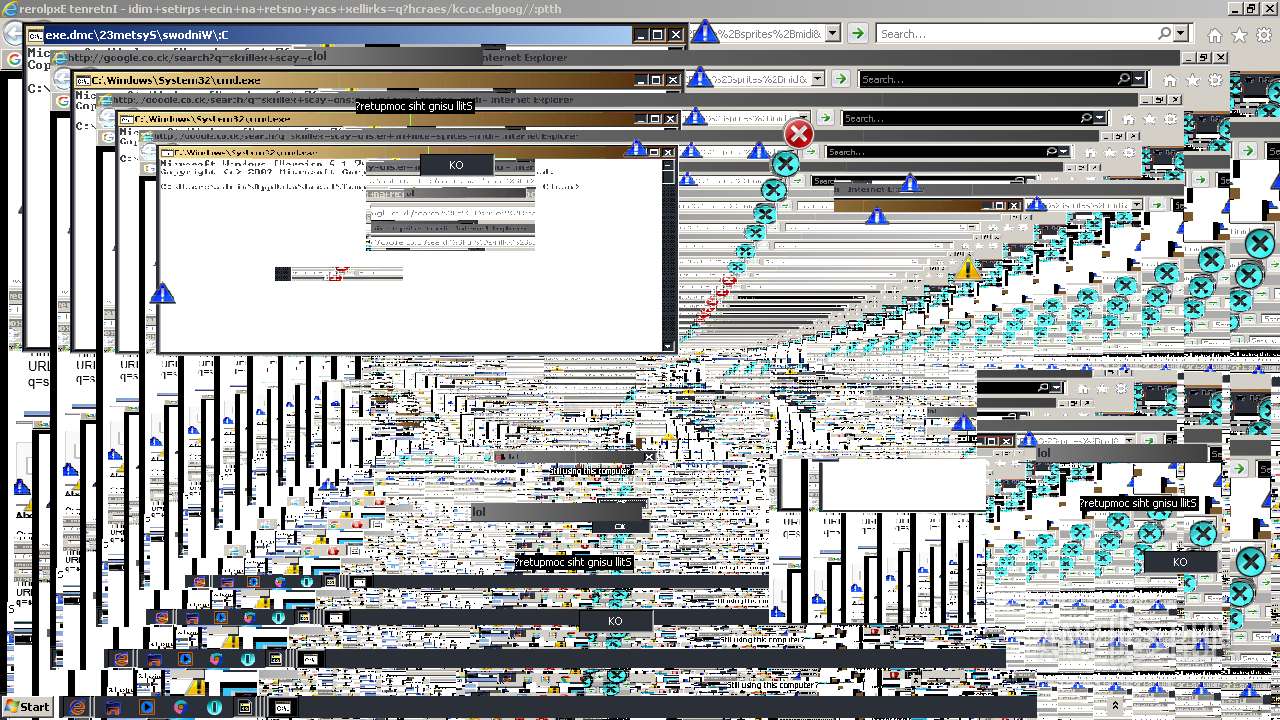
Starts CMD.EXE for commands execution
- MEMZ-Clean.exe (PID: 3080)
INFO
Reads CPU info
- firefox.exe (PID: 3172)
Reads the computer name
- firefox.exe (PID: 1068)
- firefox.exe (PID: 2416)
- firefox.exe (PID: 3276)
- firefox.exe (PID: 760)
- firefox.exe (PID: 3172)
- firefox.exe (PID: 2444)
- firefox.exe (PID: 3744)
- firefox.exe (PID: 2968)
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 736)
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 4012)
- iexplore.exe (PID: 1940)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 3148)
Application launched itself
- firefox.exe (PID: 2832)
- firefox.exe (PID: 3172)
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 3084)
Checks supported languages
- firefox.exe (PID: 3744)
- firefox.exe (PID: 3172)
- firefox.exe (PID: 2444)
- firefox.exe (PID: 1068)
- firefox.exe (PID: 2832)
- firefox.exe (PID: 2416)
- firefox.exe (PID: 3276)
- firefox.exe (PID: 760)
- firefox.exe (PID: 2968)
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 736)
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 4012)
- iexplore.exe (PID: 1940)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 3148)
Creates files in the program directory
- firefox.exe (PID: 3172)
Creates files in the user directory
- firefox.exe (PID: 3172)
- iexplore.exe (PID: 736)
- iexplore.exe (PID: 4012)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 1940)
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 3148)
Checks Windows Trust Settings
- firefox.exe (PID: 3172)
- iexplore.exe (PID: 736)
- iexplore.exe (PID: 4012)
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 1940)
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 2748)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 3172)
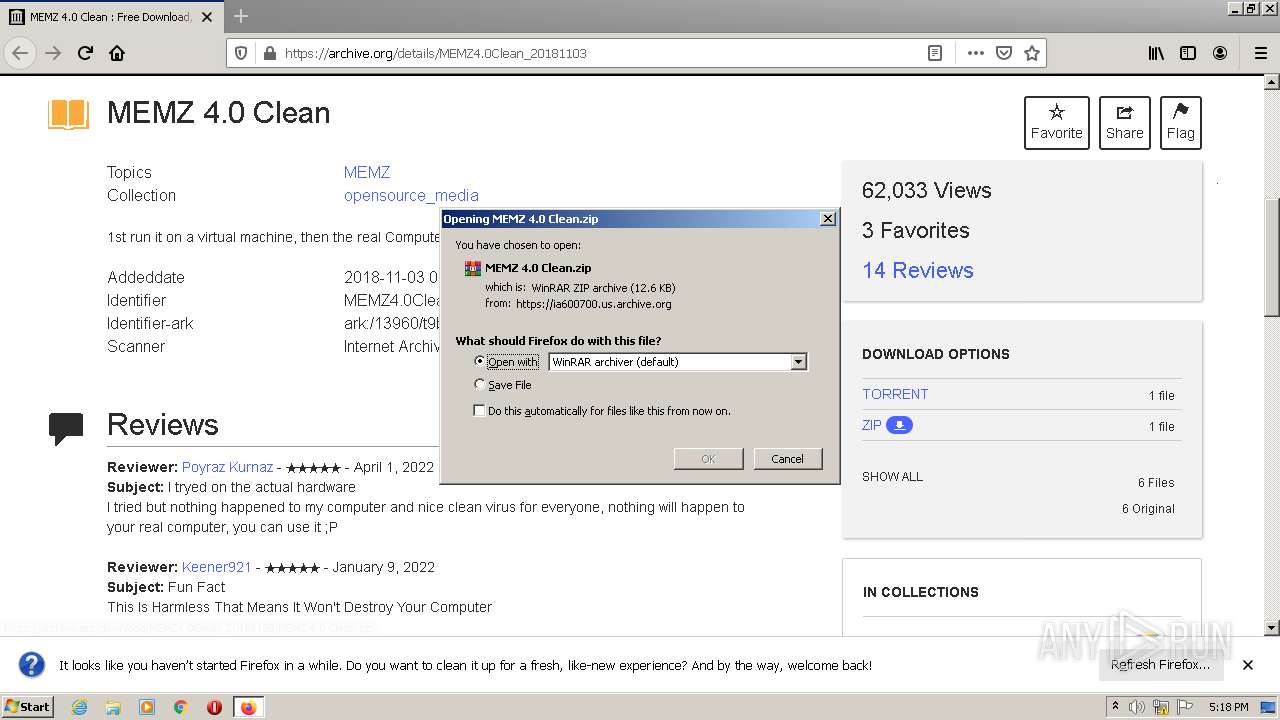
Manual execution by user
- WinRAR.exe (PID: 2488)
Reads the date of Windows installation
- firefox.exe (PID: 3172)
- iexplore.exe (PID: 3848)
Reads settings of System Certificates
- iexplore.exe (PID: 736)
- iexplore.exe (PID: 4012)
- iexplore.exe (PID: 3084)
- iexplore.exe (PID: 1940)
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 2748)
Changes internet zones settings
- iexplore.exe (PID: 3848)
- iexplore.exe (PID: 3084)
Reads internet explorer settings
- iexplore.exe (PID: 736)
- iexplore.exe (PID: 4012)
- iexplore.exe (PID: 1940)
- iexplore.exe (PID: 2748)
- iexplore.exe (PID: 3148)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3084)
Changes settings of System certificates
- iexplore.exe (PID: 3084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
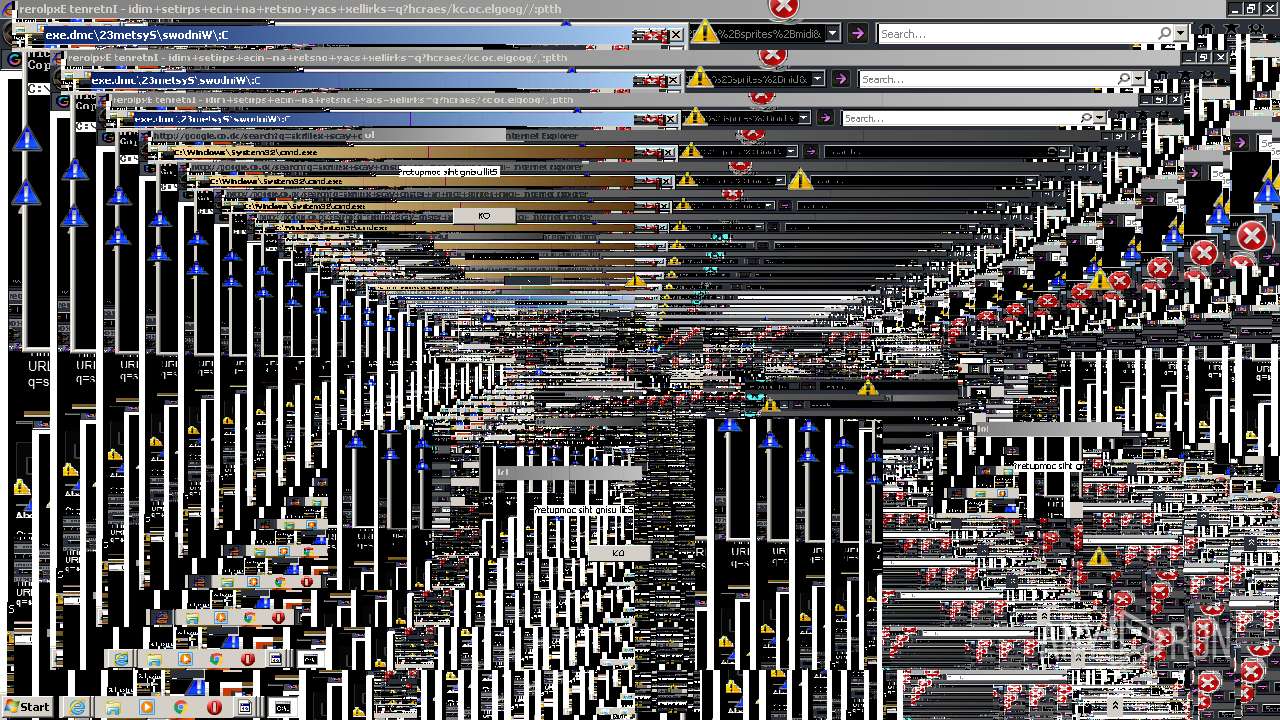
Total processes
59
Monitored processes
19
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3848 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 760 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3172.34.1963545407\1779411445" -childID 5 -isForBrowser -prefsHandle 3508 -prefMapHandle 3720 -prefsLen 7307 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3172 "\\.\pipe\gecko-crash-server-pipe.3172" 3752 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1068 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3172.6.1544345674\184131849" -childID 1 -isForBrowser -prefsHandle 2976 -prefMapHandle 2972 -prefsLen 245 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3172 "\\.\pipe\gecko-crash-server-pipe.3172" 2988 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 1940 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3084 CREDAT:1316105 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2244 | "C:\Windows\System32\cmd.exe" | C:\Windows\System32\cmd.exe | — | MEMZ-Clean.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2416 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3172.21.2129190286\1961509232" -childID 4 -isForBrowser -prefsHandle 3508 -prefMapHandle 3504 -prefsLen 7307 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3172 "\\.\pipe\gecko-crash-server-pipe.3172" 3544 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="3172.0.247093387\1667740240" -parentBuildID 20201112153044 -prefsHandle 1124 -prefMapHandle 1116 -prefsLen 1 -prefMapSize 238726 -appdir "C:\Program Files\Mozilla Firefox\browser" - 3172 "\\.\pipe\gecko-crash-server-pipe.3172" 1208 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 1 Version: 83.0 Modules
| |||||||||||||||
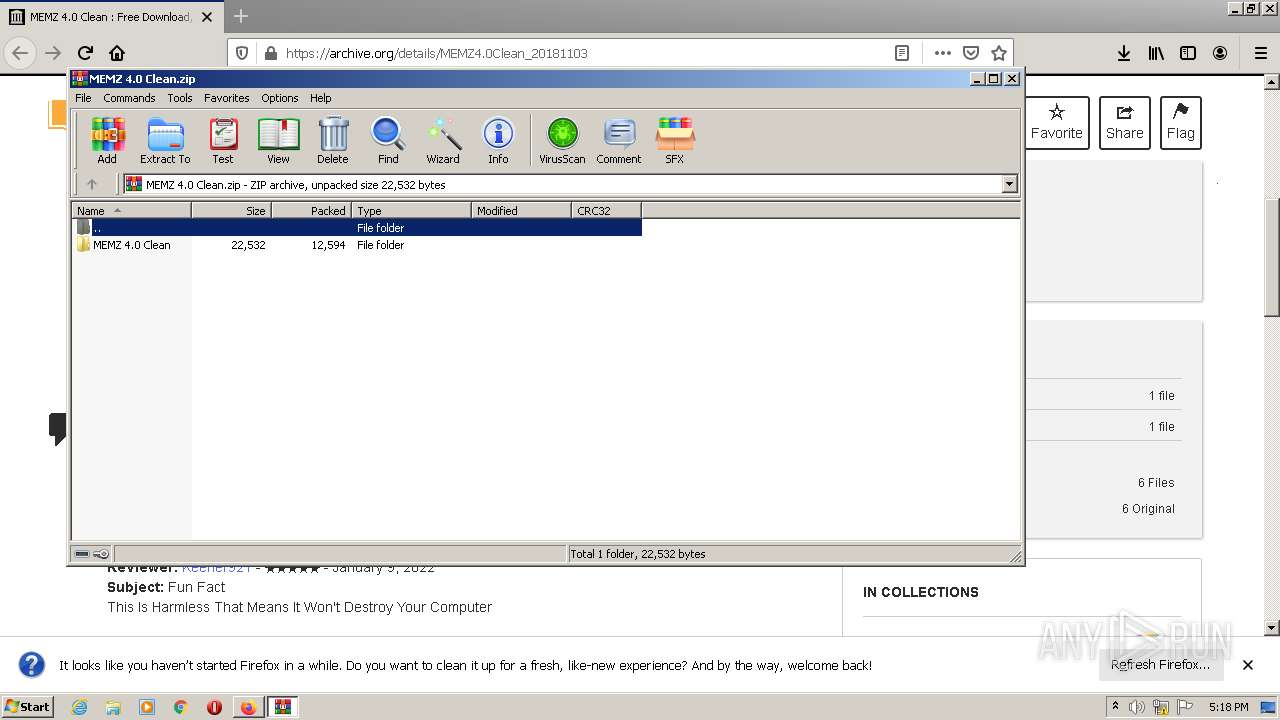
| 2488 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\MEMZ 4.0 Clean.zip" | C:\Program Files\WinRAR\WinRAR.exe | Explorer.EXE | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2748 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3084 CREDAT:1250572 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://www.google.com/url?sa=t&rct=j&q=&esrc=s&source=web&cd=&cad=rja&uact=8&ved=2ahUKEwiK7Y-sn8b3AhXCJkQIHV8ABuUQFnoECAMQAQ&url=https%3A%2F%2Farchive.org%2Fdetails%2FMEMZ4.0Clean_20181103&usg=AOvVaw3fZvyxiPtOvz66R0xNMJgN" | C:\Program Files\Mozilla Firefox\firefox.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
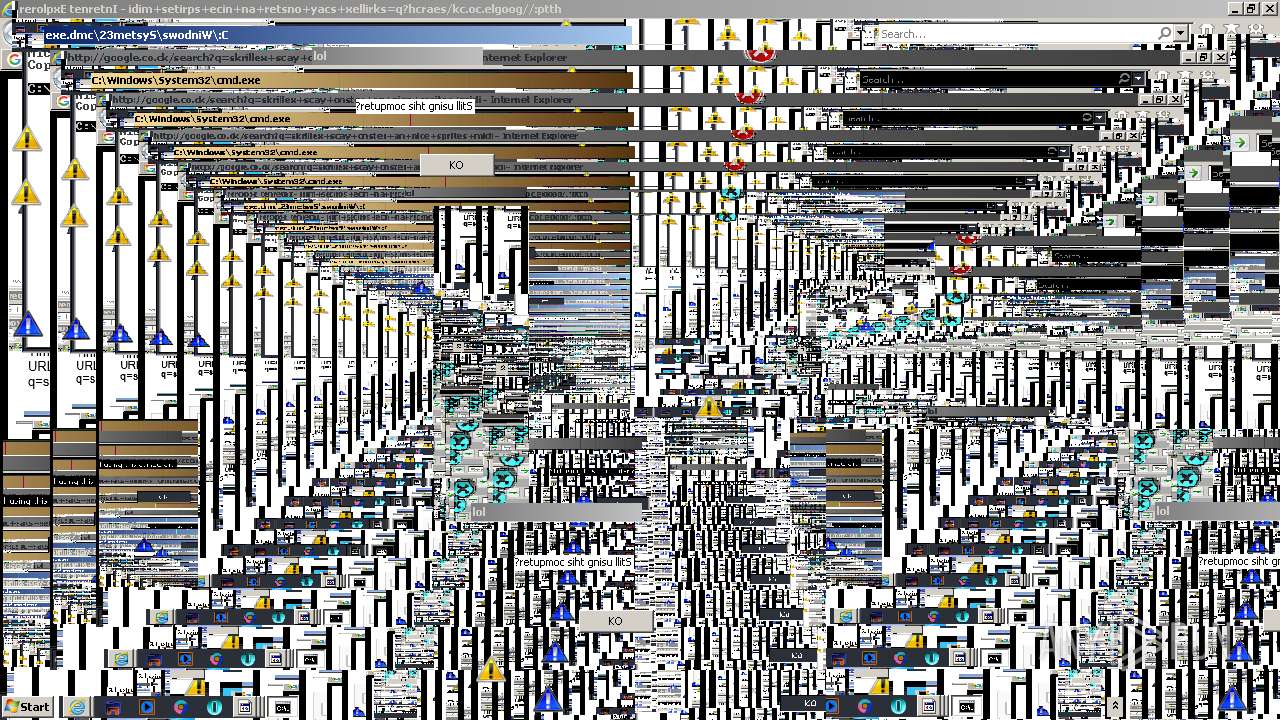
Total events
41 104
Read events
40 719
Write events
380
Delete events
5
Modification events
| (PID) Process: | (2832) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 51B4132E40000000 | |||
| (PID) Process: | (3172) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: DCBF132E40000000 | |||
| (PID) Process: | (3172) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (3172) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (3172) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (3172) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (3172) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (3172) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
| (PID) Process: | (3172) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3172) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
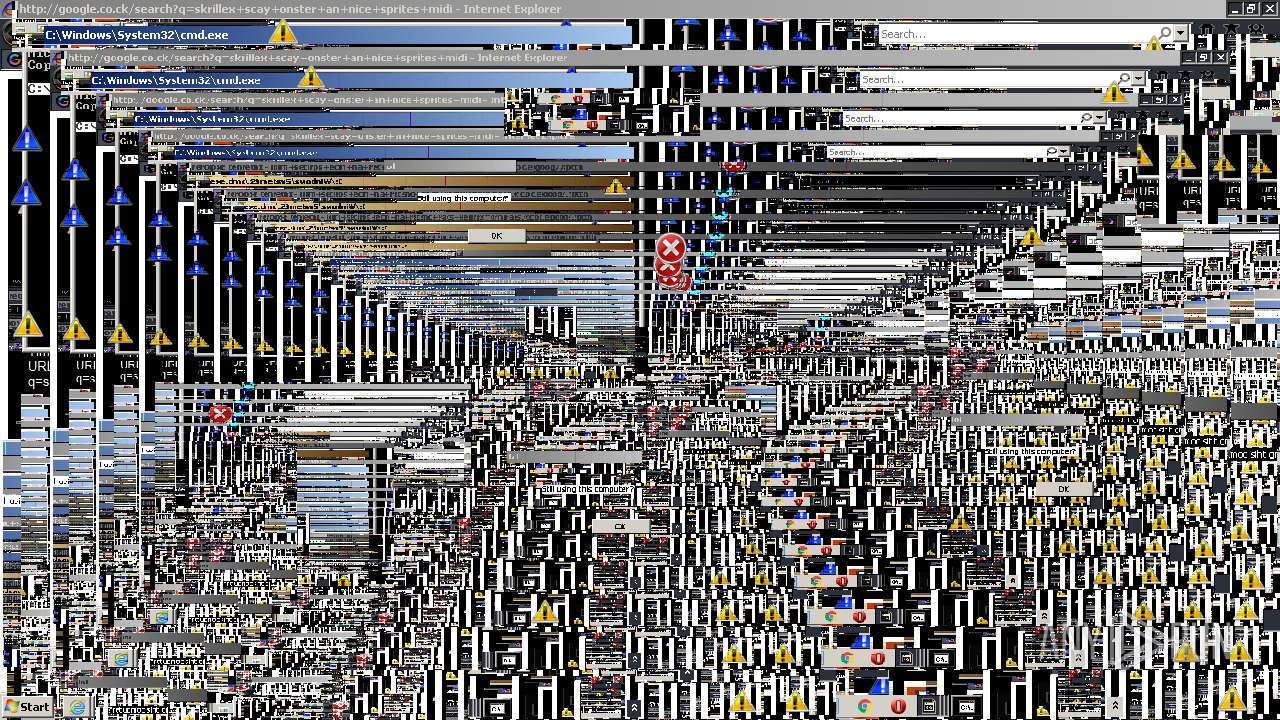
Executable files
1
Suspicious files
142
Text files
82
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3172 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 3172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 3172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:— | SHA256:— | |||
| 3172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\protections.sqlite-journal | binary | |
MD5:— | SHA256:— | |||
| 3172 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:994A33896BB41A278A315D0D796422B6 | SHA256:54EC50A20FFF8CC016710E49437CF6A11D3FE5EE7B28C185E4A9AAFEE2908B63 | |||
| 3172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\1451318868ntouromlalnodry--epcr.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 3172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 3172 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
115
DNS requests
94
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3172 | firefox.exe | POST | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
3172 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
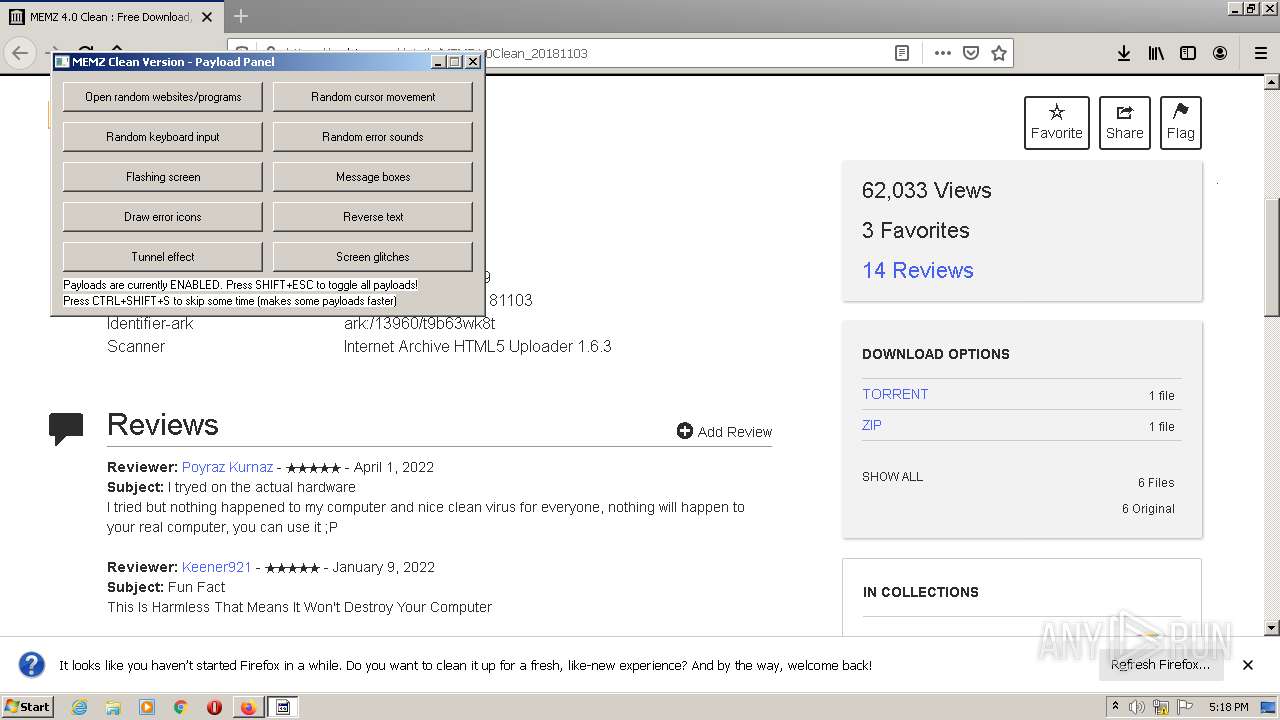
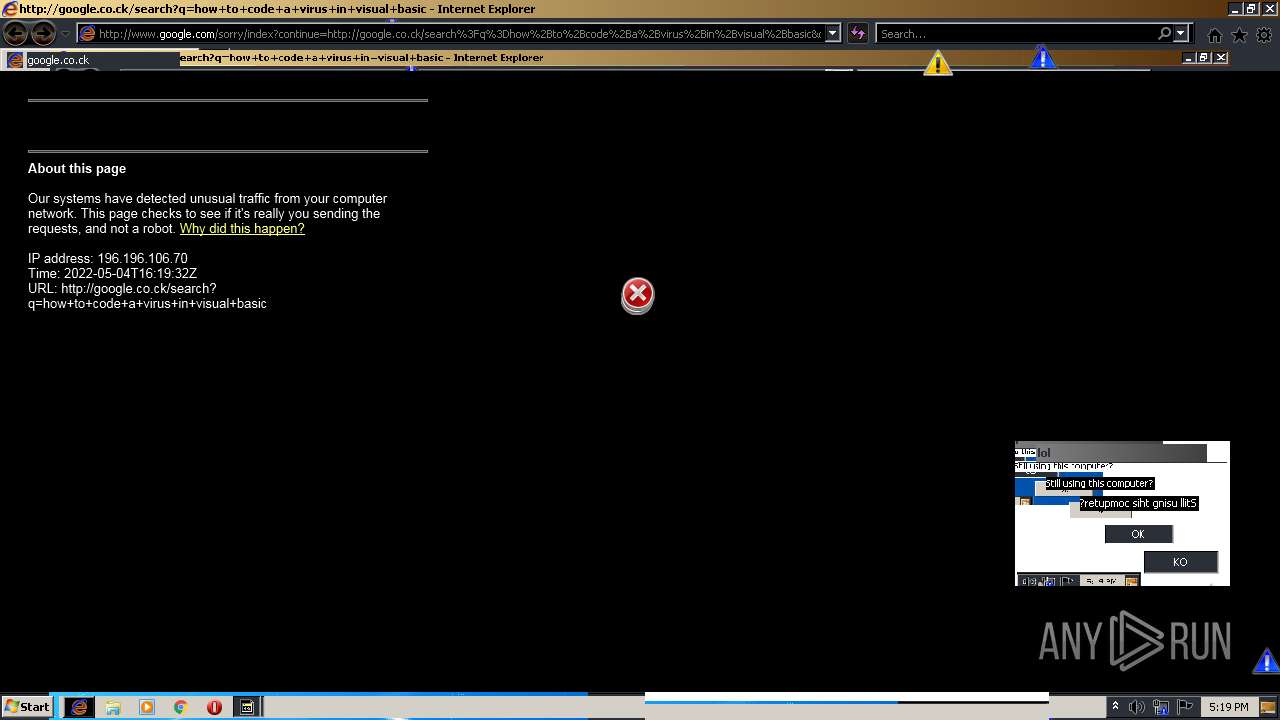
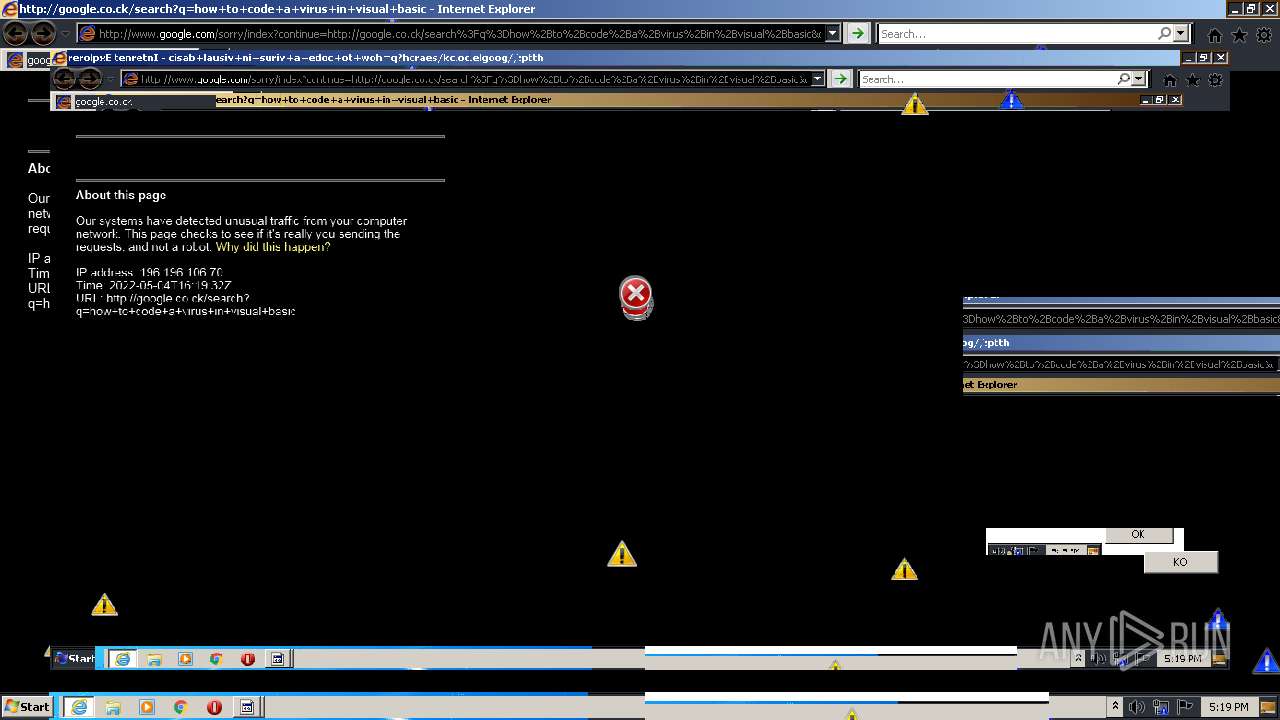
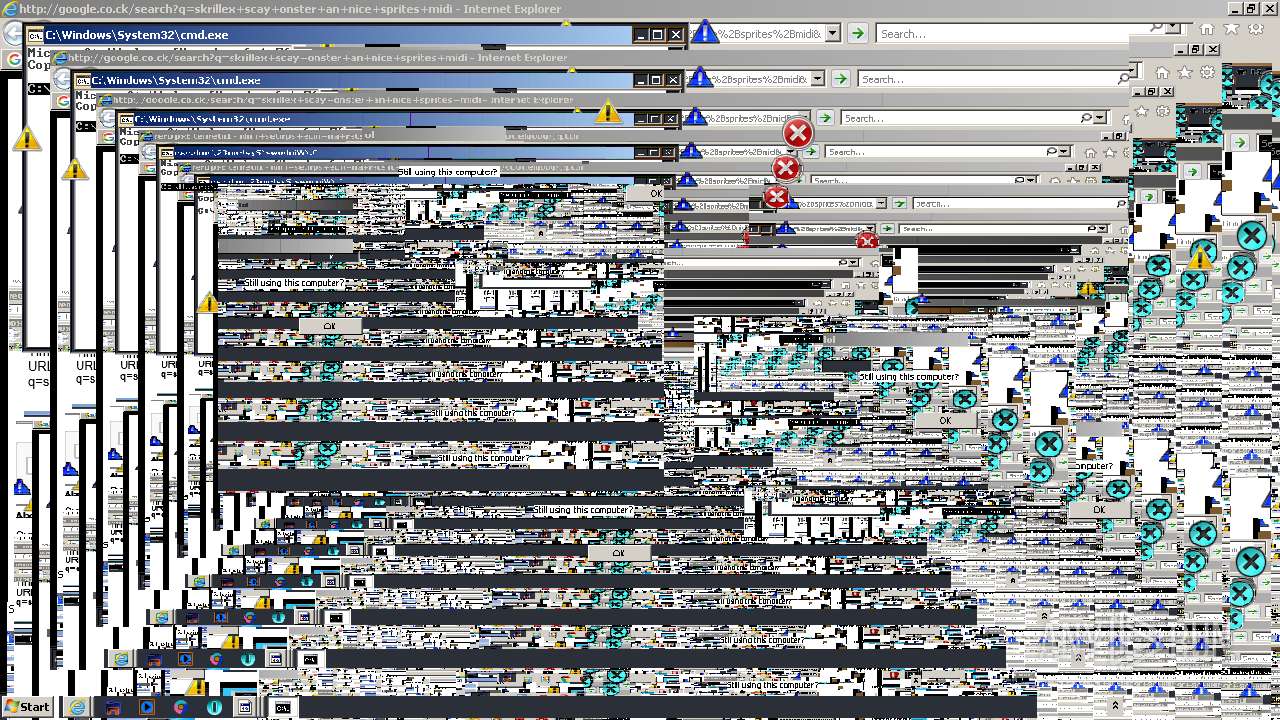
4012 | iexplore.exe | GET | 302 | 142.250.185.228:80 | http://google.co.ck/search?q=how+to+code+a+virus+in+visual+basic | US | html | 373 b | whitelisted |
3172 | firefox.exe | POST | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
3172 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3172 | firefox.exe | POST | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
4012 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDZVQ0c3n%2F16xKL4oJJTrDj | US | der | 472 b | whitelisted |
3172 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
4012 | iexplore.exe | GET | 200 | 172.217.23.99:80 | http://ocsp.pki.goog/gts1c3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEFBpiRkWWQcXClTQVPWVHTs%3D | US | der | 471 b | whitelisted |
3084 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3172 | firefox.exe | 142.250.186.36:443 | www.google.com | Google Inc. | US | whitelisted |
3172 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | — | US | whitelisted |
3172 | firefox.exe | 142.250.184.234:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
3172 | firefox.exe | 143.204.201.8:443 | firefox.settings.services.mozilla.com | — | US | malicious |
3172 | firefox.exe | 65.9.63.59:443 | firefox-settings-attachments.cdn.mozilla.net | AT&T Services, Inc. | US | unknown |
3172 | firefox.exe | 207.241.224.2:443 | archive.org | Internet Archive | US | malicious |
3172 | firefox.exe | 54.148.56.186:443 | push.services.mozilla.com | Amazon.com, Inc. | US | unknown |
3172 | firefox.exe | 207.241.239.242:443 | polyfill.archive.org | Internet Archive | US | suspicious |
3172 | firefox.exe | 99.86.4.128:443 | content-signature-2.cdn.mozilla.net | AT&T Services, Inc. | US | suspicious |
3172 | firefox.exe | 207.241.227.160:443 | ia600700.us.archive.org | Internet Archive | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
www.google.com |
| malicious |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
ocsp.pki.goog |
| whitelisted |
pki-goog.l.google.com |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3172 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |
3172 | firefox.exe | Potentially Bad Traffic | ET INFO Terse Request for .txt - Likely Hostile |