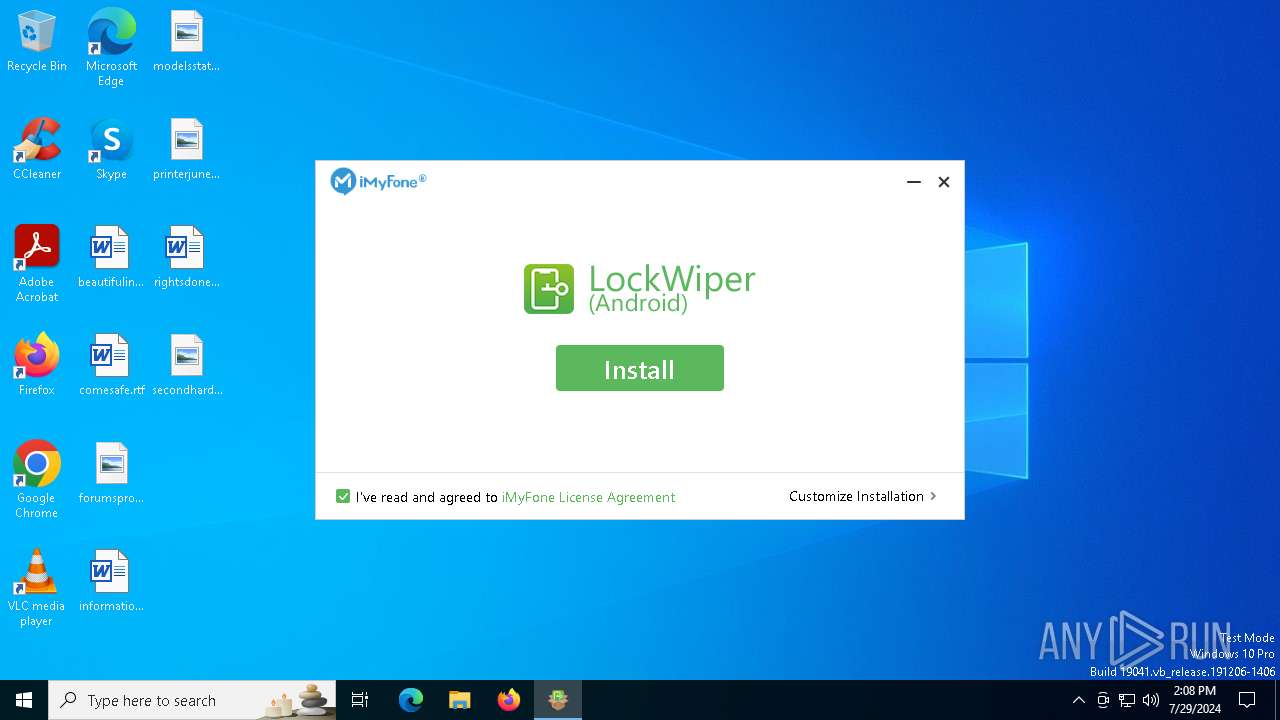
| File name: | imyfone-lockwiper-android_setup-com_tw.exe |
| Full analysis: | https://app.any.run/tasks/1fbf5a29-c6c0-48d2-b3f6-5020ab56a194 |
| Verdict: | Malicious activity |
| Analysis date: | July 29, 2024, 14:08:15 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BAB45D0F16D78724162136776E1ABCA1 |
| SHA1: | 8F79AF20CF1B07EA1158D5844B4A7D69636EB584 |
| SHA256: | 6E826D6F2B32DACA6B5AF4A8C7A29882B20844333CD69F9ED9271008481F8196 |
| SSDEEP: | 98304:rg5E057nmBV0wb/Zd0Xwi1ZZ6UWVWe0XEeqO3vbq+HqnwrFUtPx8VuZCcbP2Hyx/:9FBc1hA |
MALICIOUS
Drops the executable file immediately after the start
- imyfone-lockwiper-android_setup-com_tw.exe (PID: 7028)
- imyfone-download.exe (PID: 1180)
- imyfone-download.tmp (PID: 2112)
SUSPICIOUS
Reads security settings of Internet Explorer
- imyfone-lockwiper-android_setup-com_tw.exe (PID: 7028)
Executable content was dropped or overwritten
- imyfone-download.tmp (PID: 2112)
- imyfone-download.exe (PID: 1180)
Starts CMD.EXE for commands execution
- imyfone-download.tmp (PID: 2112)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 2668)
- cmd.exe (PID: 2480)
- cmd.exe (PID: 2192)
Reads the Windows owner or organization settings
- imyfone-download.tmp (PID: 2112)
Process drops legitimate windows executable
- imyfone-download.tmp (PID: 2112)
Process drops legitimate windows executable (CertUtil.exe)
- imyfone-download.tmp (PID: 2112)
Drops 7-zip archiver for unpacking
- imyfone-download.tmp (PID: 2112)
The process drops C-runtime libraries
- imyfone-download.tmp (PID: 2112)
Drops a system driver (possible attempt to evade defenses)
- imyfone-download.tmp (PID: 2112)
INFO
Reads the computer name
- imyfone-lockwiper-android_setup-com_tw.exe (PID: 7028)
- imyfone-download.tmp (PID: 2112)
Creates files in the program directory
- imyfone-lockwiper-android_setup-com_tw.exe (PID: 7028)
- imyfone-download.tmp (PID: 2112)
Reads product name
- imyfone-lockwiper-android_setup-com_tw.exe (PID: 7028)
Checks supported languages
- imyfone-lockwiper-android_setup-com_tw.exe (PID: 7028)
- imyfone-download.exe (PID: 1180)
- imyfone-download.tmp (PID: 2112)
Reads Environment values
- imyfone-lockwiper-android_setup-com_tw.exe (PID: 7028)
Create files in a temporary directory
- imyfone-download.exe (PID: 1180)
- imyfone-download.tmp (PID: 2112)
Reads the software policy settings
- slui.exe (PID: 6788)
- imyfone-lockwiper-android_setup-com_tw.exe (PID: 7028)
Checks proxy server information
- slui.exe (PID: 6788)
- imyfone-lockwiper-android_setup-com_tw.exe (PID: 7028)
Reads the machine GUID from the registry
- imyfone-lockwiper-android_setup-com_tw.exe (PID: 7028)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (3.6) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (1.6) |
| .exe | | | DOS Executable Generic (1.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:12:18 10:33:07+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 2118144 |
| InitializedDataSize: | 2534400 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1bb644 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.3.0.1 |
| ProductVersionNumber: | 4.3.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | imyfone-lockwiper-android_setup-com_tw.exe |
| FileVersion: | 4.3.0.1 |
| LegalCopyright: | Copyright (C) 2024 iMyFone. All rights reserved. |
| ProductName: | iMyFone LockWiper (Android) |
| ProductVersion: | 4.3.0.1 |
Total processes
158
Monitored processes
14
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1180 | /verysilent /imyfone_down /wait_run /path="C:\Program Files (x86)\" /progress="C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\temp.progress" | C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\imyfone-download.exe | imyfone-lockwiper-android_setup-com_tw.exe | ||||||||||||
User: admin Company: Shenzhen iMyFone Technology Co., Ltd. Integrity Level: HIGH Description: iMyFone LockWiper (Android) Version: 5.4.8.1 Modules
| |||||||||||||||
| 2112 | "C:\Users\admin\AppData\Local\Temp\is-K9PIF.tmp\imyfone-download.tmp" /SL5="$B03FC,195668533,214016,C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\imyfone-download.exe" /verysilent /imyfone_down /wait_run /path="C:\Program Files (x86)\" /progress="C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\temp.progress" | C:\Users\admin\AppData\Local\Temp\is-K9PIF.tmp\imyfone-download.tmp | imyfone-download.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2116 | taskkill /f /t /im Feedback.exe | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2124 | "C:\Users\admin\AppData\Local\Temp\imyfone-lockwiper-android_setup-com_tw.exe" | C:\Users\admin\AppData\Local\Temp\imyfone-lockwiper-android_setup-com_tw.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: imyfone-lockwiper-android_setup-com_tw.exe Exit code: 3221226540 Version: 4.3.0.1 Modules
| |||||||||||||||
| 2192 | "cmd.exe" /c taskkill /f /t /im appAutoUpdate.exe | C:\Windows\SysWOW64\cmd.exe | — | imyfone-download.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2480 | "cmd.exe" /c taskkill /f /t /im Feedback.exe | C:\Windows\SysWOW64\cmd.exe | — | imyfone-download.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2668 | "cmd.exe" /c taskkill /f /t /im adb.exe | C:\Windows\SysWOW64\cmd.exe | — | imyfone-download.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 128 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4548 | taskkill /f /t /im adb.exe | C:\Windows\SysWOW64\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4820 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6372 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
3 106
Read events
3 100
Write events
6
Delete events
0
Modification events
| (PID) Process: | (7028) imyfone-lockwiper-android_setup-com_tw.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\iMyfone\iMyfoneDown |
| Operation: | write | Name: | GUID |
Value: 683A12CE-F6D9-4a43-BF2A-F26DB1547F92 | |||
| (PID) Process: | (2112) imyfone-download.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 40080000B142E511C1E1DA01 | |||
| (PID) Process: | (2112) imyfone-download.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 51421DF0C70FC49EF4306F9607C8436B91B7BC3C22B157D54F8CADF57AAC99C3 | |||
| (PID) Process: | (2112) imyfone-download.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2112) imyfone-download.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files (x86)\iMyFone\iMyfone LockWiper (Android)\7z.dll | |||
| (PID) Process: | (2112) imyfone-download.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 820C3CD9BCDB48040FFDE3F9E8864A17F429127156F96C2861DA2677631AED76 | |||
Executable files
394
Suspicious files
179
Text files
1 545
Unknown types
123
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7028 | imyfone-lockwiper-android_setup-com_tw.exe | C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\language\Dutch\pr_1.png | image | |
MD5:9E5A3E164B6D86623EC84A19241F74E1 | SHA256:F3EECB73C259C024DE4F3A6C69011FFCBE4428090855B81C7A12874EC6C691F5 | |||
| 7028 | imyfone-lockwiper-android_setup-com_tw.exe | C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\language\Dutch\UrlInfo.ini | text | |
MD5:DA07B8686390EDB756D88AD774A622B6 | SHA256:5C9C4F7CC36131A29FD9F8DCD27485B340CE6F7B270278704133D71EB5329C8D | |||
| 7028 | imyfone-lockwiper-android_setup-com_tw.exe | C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\language\ChineseTW\text.ini | text | |
MD5:CA3A0F1453F6210B9D87E1B4C2FEBD86 | SHA256:51C9132DA03D5ACBD8CC641680ADF41E8E9E962766873B52E08A3238E683614B | |||
| 7028 | imyfone-lockwiper-android_setup-com_tw.exe | C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\language\Dutch\pr_2.png | image | |
MD5:D9BD60E7AEAA07F34C489E1F1F99E0B5 | SHA256:0CB2A92EB62F3CCDEA940DB52233043DAE214BF518B0A5B5F51035DD20EAAE0A | |||
| 7028 | imyfone-lockwiper-android_setup-com_tw.exe | C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\language\Chinese\pr_1.png | image | |
MD5:CE20D55C446BB069A51CD53BA2E8C815 | SHA256:DD4982542675238C74B94A24B4044D46D6A1DB8A52B15601841A87B3766755AA | |||
| 7028 | imyfone-lockwiper-android_setup-com_tw.exe | C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\language\Dutch\pr_3.png | image | |
MD5:45BAE5D0A90A80F08935B9631768E61C | SHA256:BB13C2E4BCD9E5BBB56A4CF88EF0661F12EC379E5FDB10B5010F71EA9C6075E8 | |||
| 7028 | imyfone-lockwiper-android_setup-com_tw.exe | C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\language\Chinese\UrlInfo.ini | text | |
MD5:D73850B48A31AAF94FFFDD2547E2789C | SHA256:444543DC030D831D03BA2B538F93AA0A375DC1A2F53ADF20C9CA02767E406230 | |||
| 7028 | imyfone-lockwiper-android_setup-com_tw.exe | C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\language\ChineseTW\pr_2.png | image | |
MD5:DC89FB9BEA54D06DEF5BD846CDA0BB34 | SHA256:8CFF16A1E81FD2224A17F87581ACC9516FAB2EEC44C7952CE4885C8B8099188D | |||
| 7028 | imyfone-lockwiper-android_setup-com_tw.exe | C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\language\ChineseTW\pr_1.png | image | |
MD5:9A0548388E035A60D788CAA093F6C143 | SHA256:DF478B04784DCE0BE5D4DB6450DF2EA96D1ECB9970C29CA948FB4AF0C83972AB | |||
| 7028 | imyfone-lockwiper-android_setup-com_tw.exe | C:\Program Files (x86)\imyfone_down\imyfone-lockwiper-android_setup-com_tw\language\Chinese\pr_2.png | image | |
MD5:FA971B8C6649D6810356F0010AA3428A | SHA256:77EB60EB2D69CC57EC8F89163C6FBB3A06F0C7264414FC859C83A14A7194E203 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
65
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEApDqVCbATUviZV57HIIulA%3D | US | binary | 471 b | whitelisted |
5368 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 313 b | whitelisted |
4424 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
4132 | OfficeClickToRun.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | US | binary | 471 b | whitelisted |
3676 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
5560 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
— | — | 92.123.104.51:443 | www.bing.com | Akamai International B.V. | DE | unknown |
5800 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6012 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6076 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1752 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
1328 | slui.exe | 20.83.72.98:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
a-ring-fallback.msedge.net |
| unknown |
www.bing.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
download.imyfone.com |
| whitelisted |
apipdm.imyfone.club |
| unknown |
www.google-analytics.com |
| whitelisted |
fp-afd-nocache-ccp.azureedge.net |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |