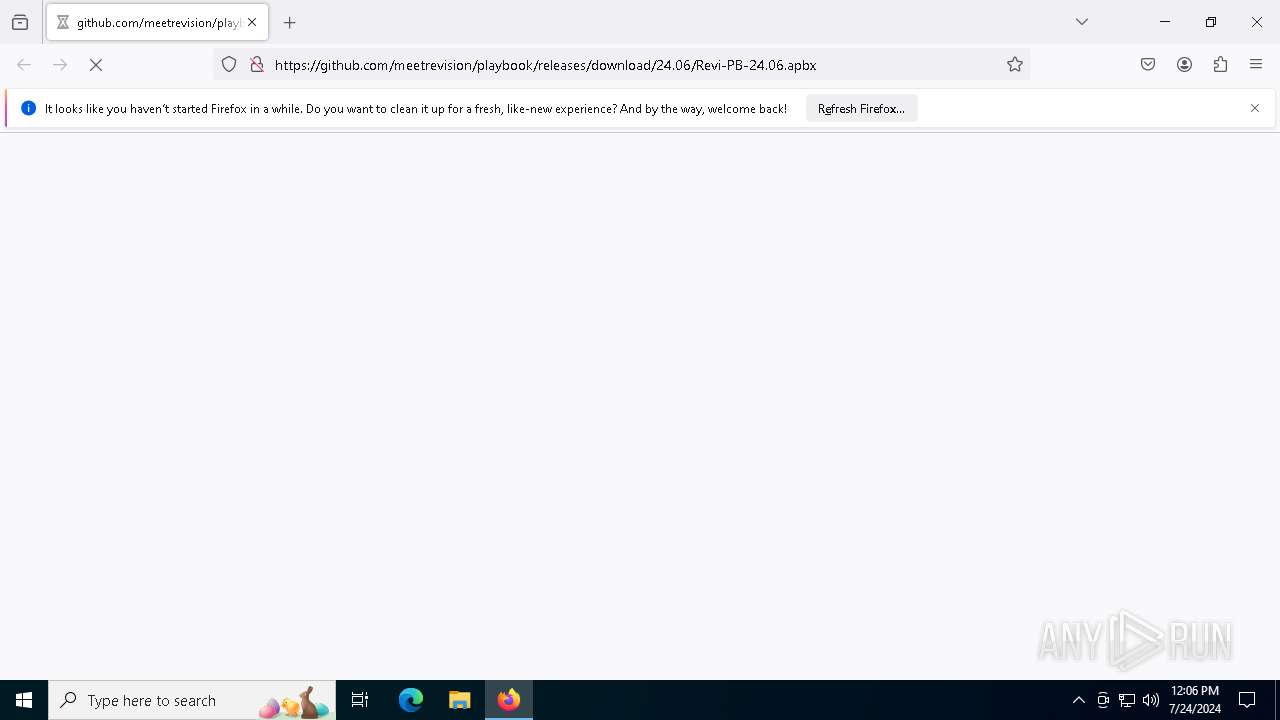
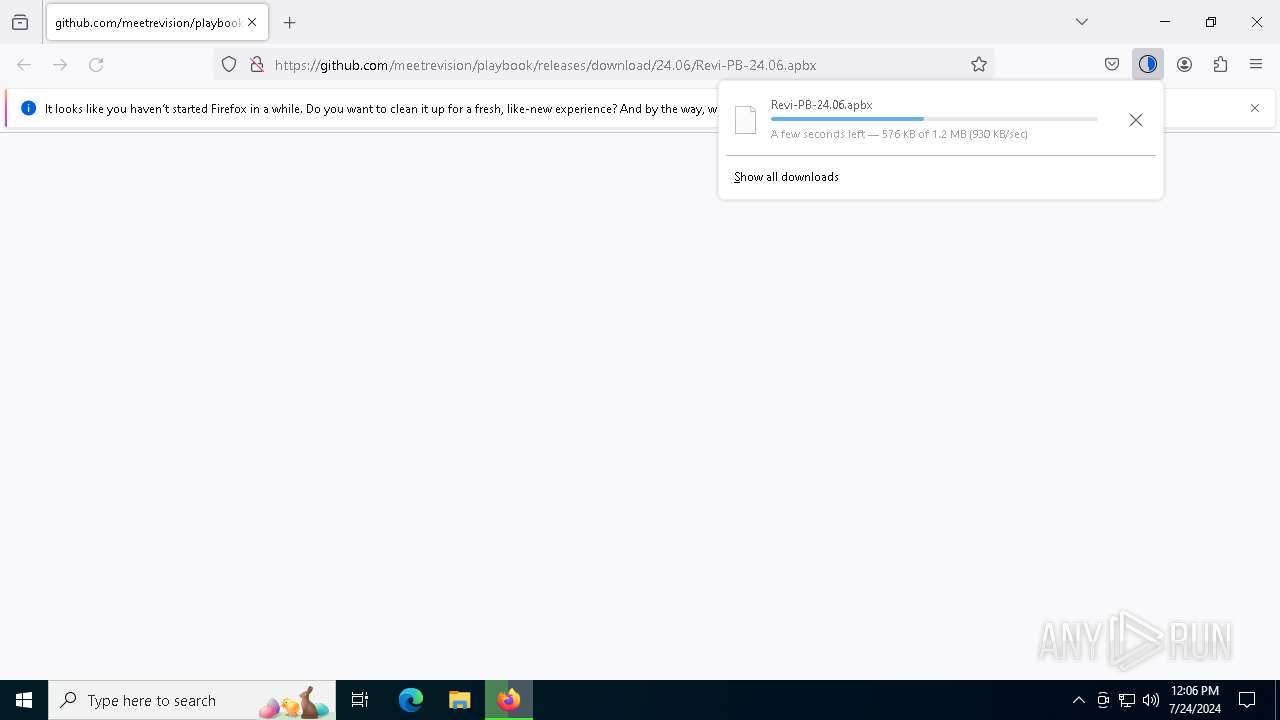
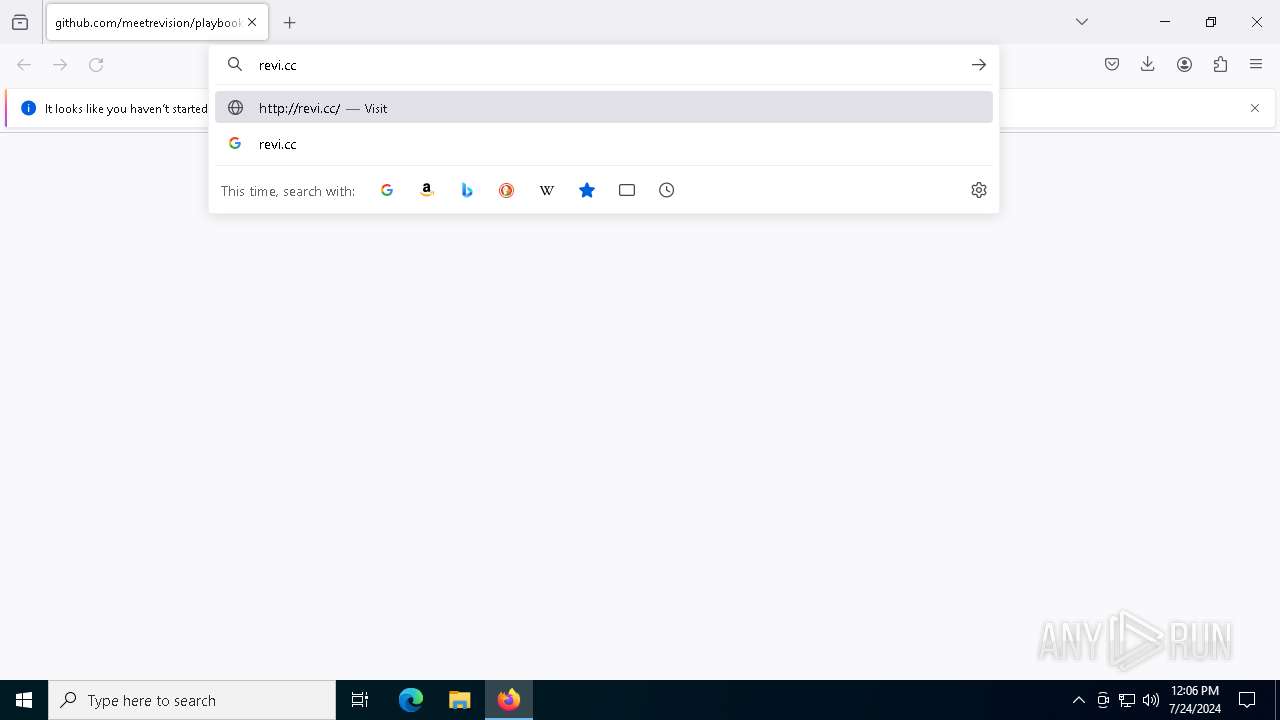
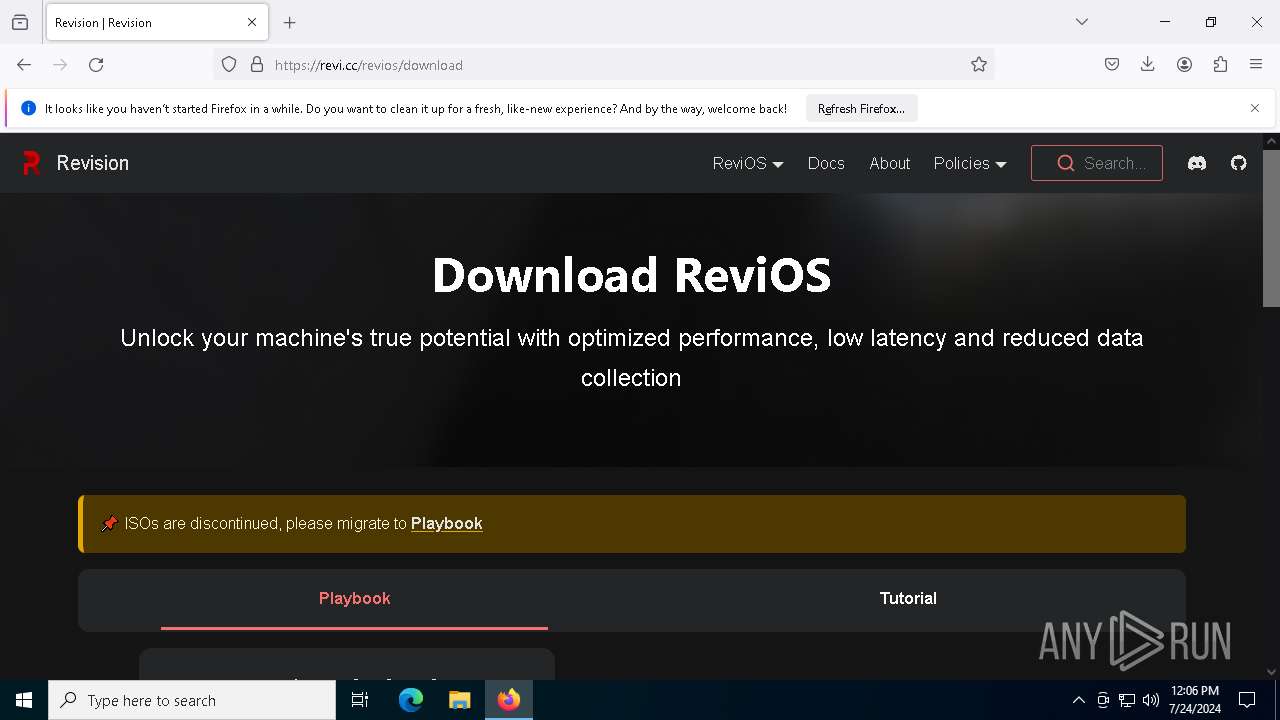
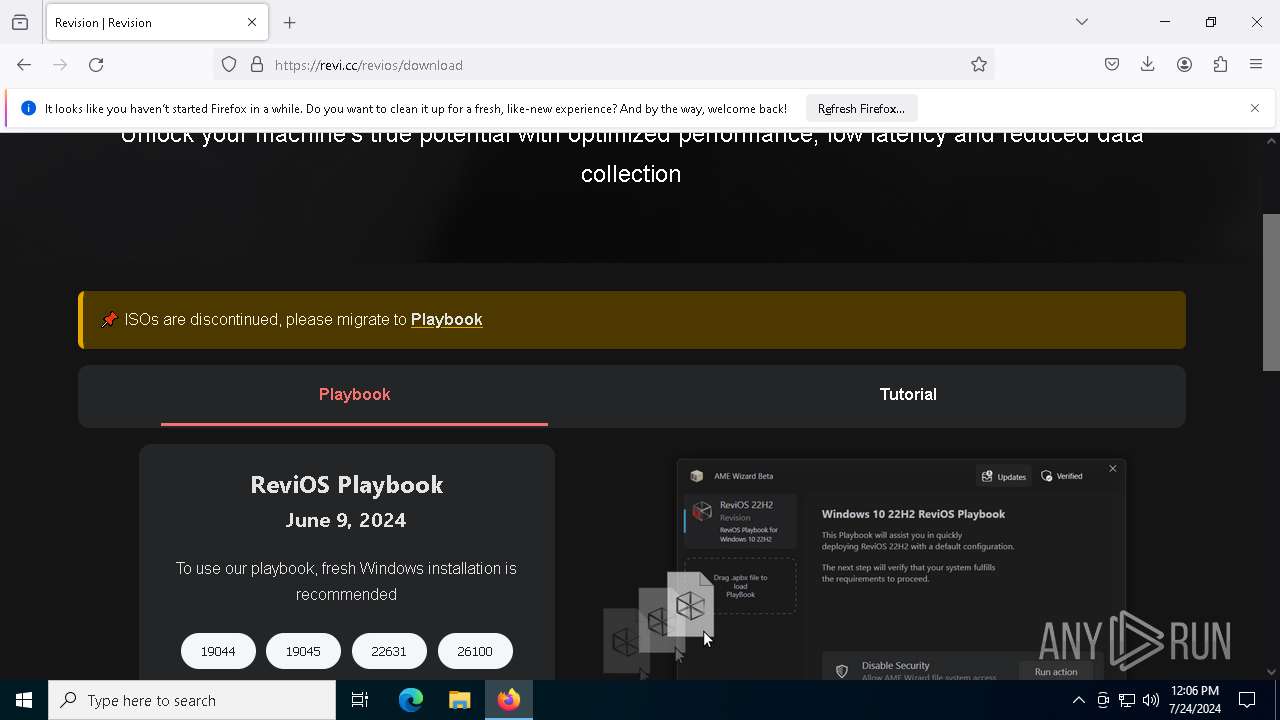
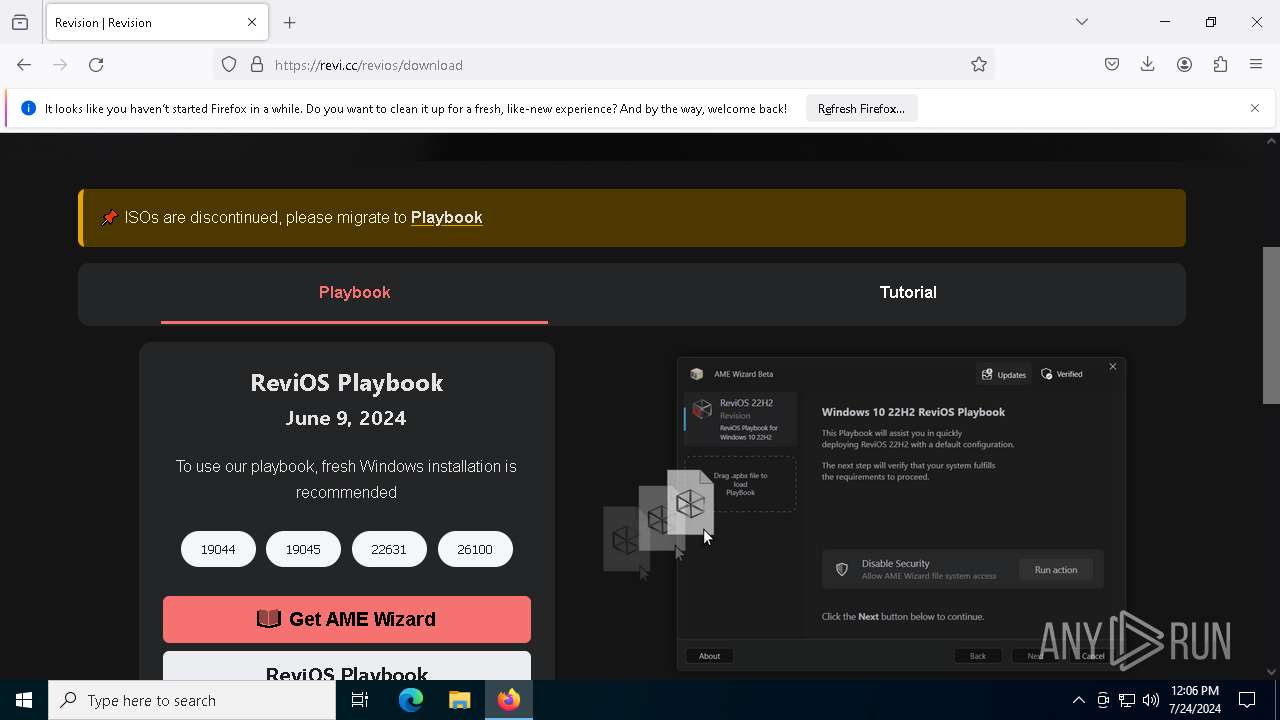
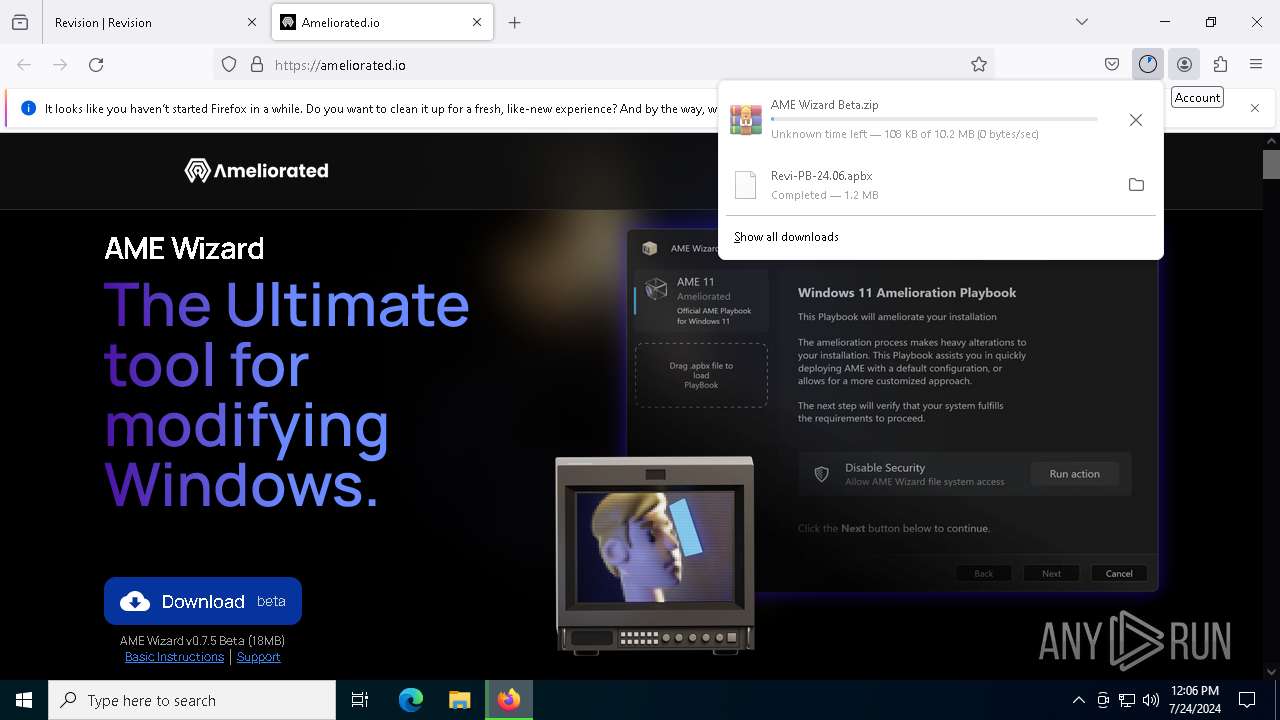
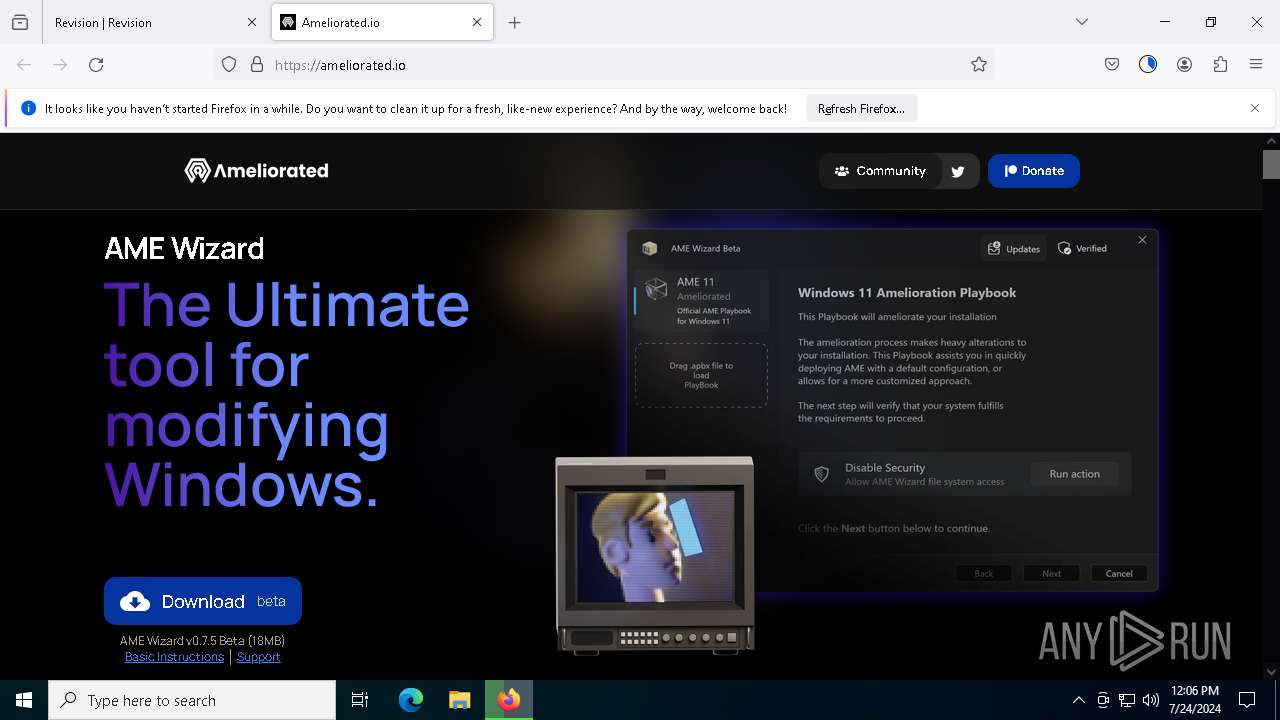
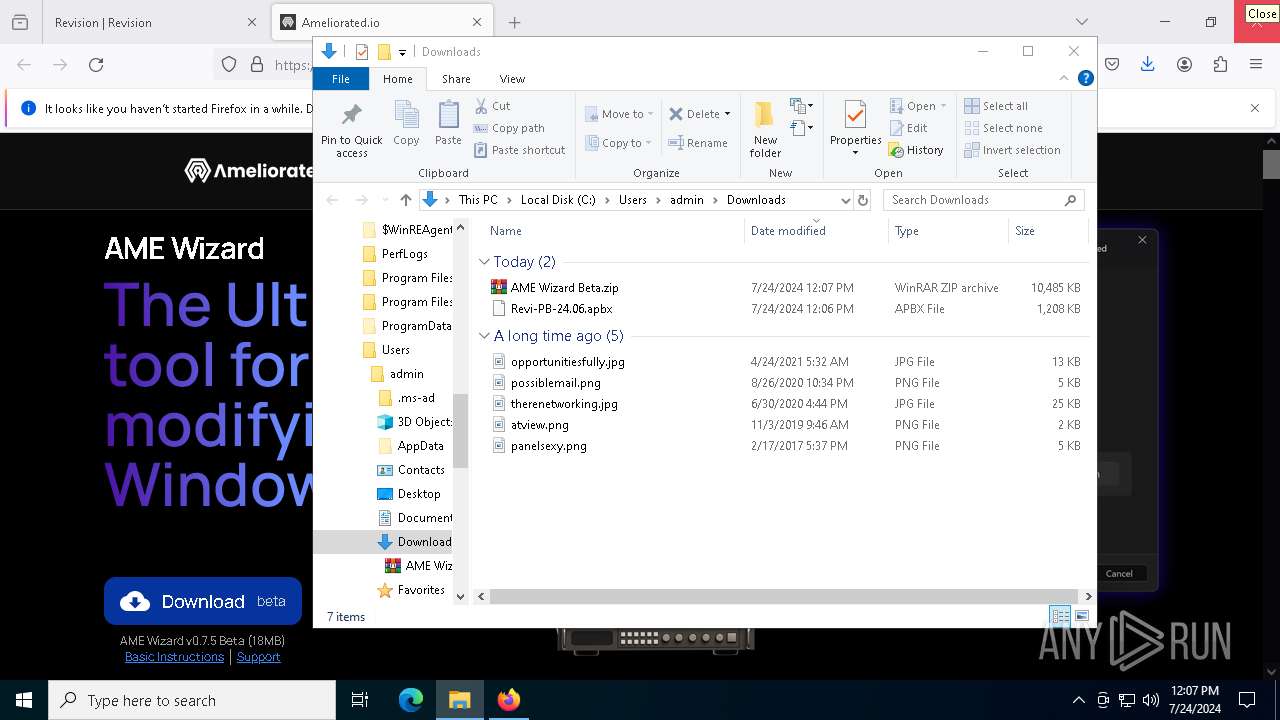
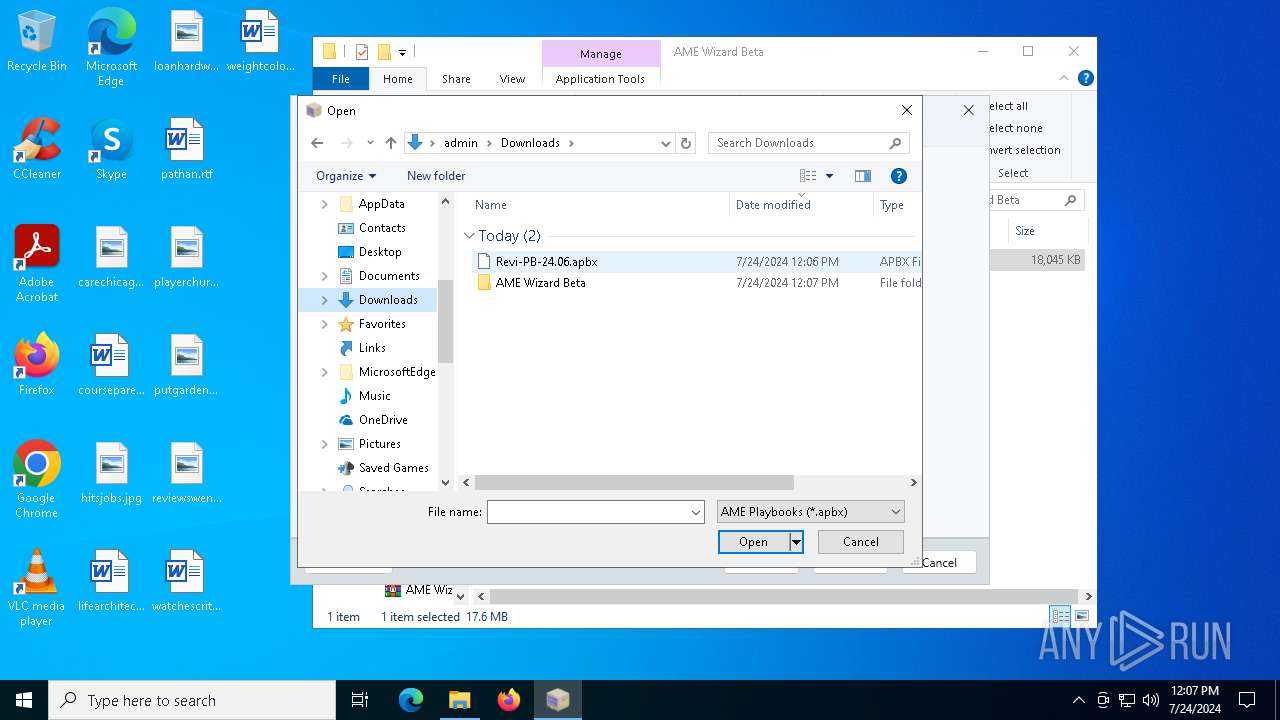
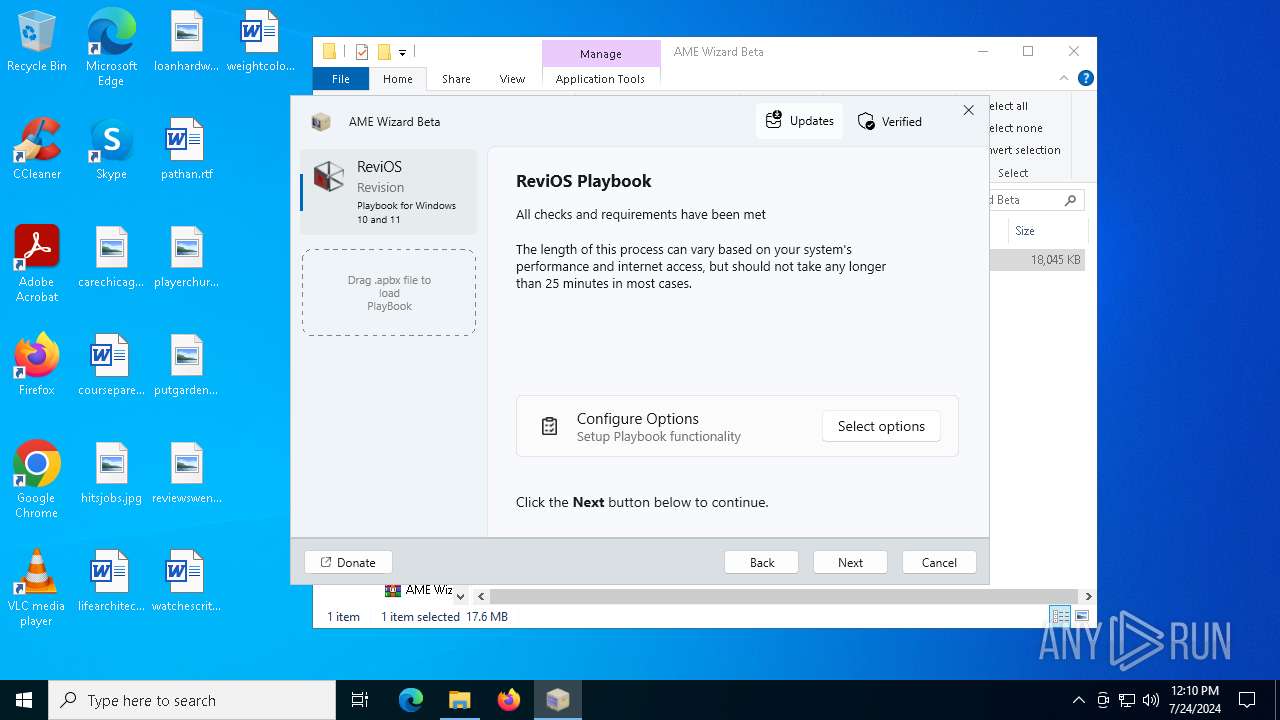
| URL: | https://github.com/meetrevision/playbook/releases/download/24.06/Revi-PB-24.06.apbx |
| Full analysis: | https://app.any.run/tasks/a69803b1-2b92-4db4-bde9-a77955c9dce5 |
| Verdict: | Malicious activity |
| Threats: | Stealers are a group of malicious software that are intended for gaining unauthorized access to users’ information and transferring it to the attacker. The stealer malware category includes various types of programs that focus on their particular kind of data, including files, passwords, and cryptocurrency. Stealers are capable of spying on their targets by recording their keystrokes and taking screenshots. This type of malware is primarily distributed as part of phishing campaigns. |
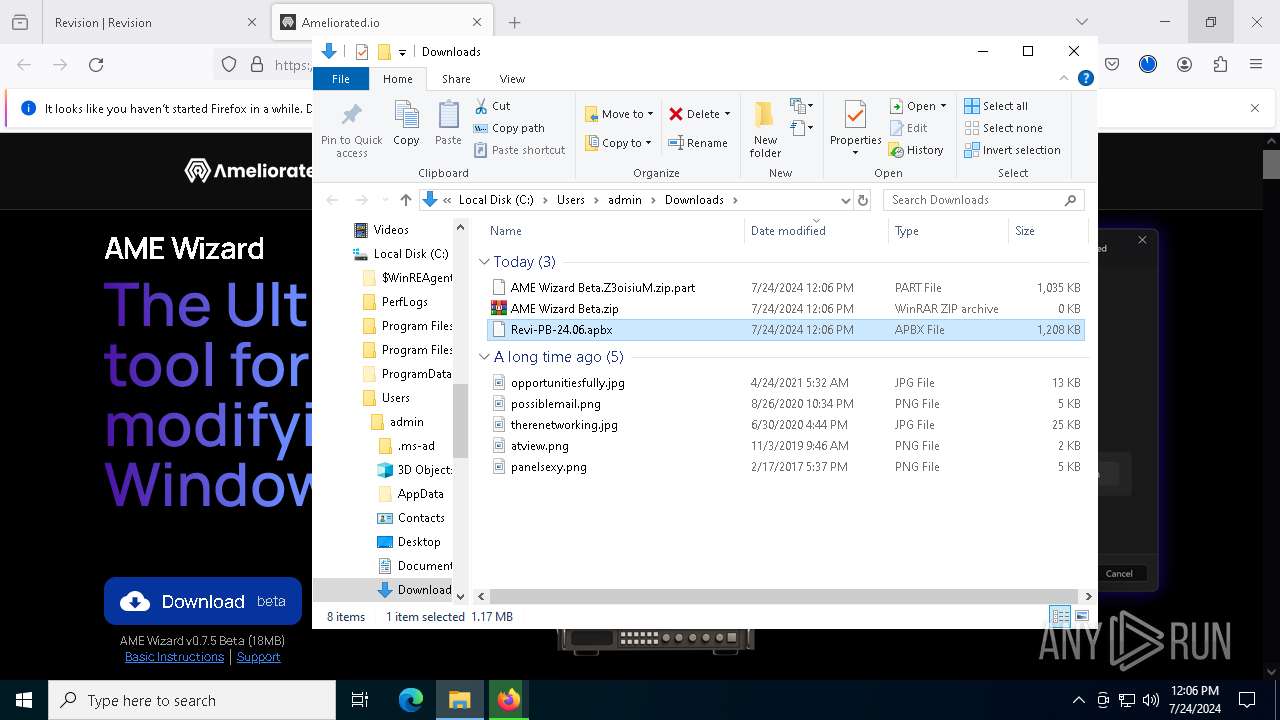
| Analysis date: | July 24, 2024, 12:06:23 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 89EF70E5CDF9E077C4EFC0537DA353DC |
| SHA1: | 4EADE608EF649E5B72DAB9C214F85FC2A700E5F8 |
| SHA256: | 6E6D61D98C38AF95FD4C167ED3C003D4FD24593C6EB987586B8EF3C73240862B |
| SSDEEP: | 3:N8tEd48q1sAE2kCXnTsc1gktd:2uu8q6MNsEFv |
MALICIOUS
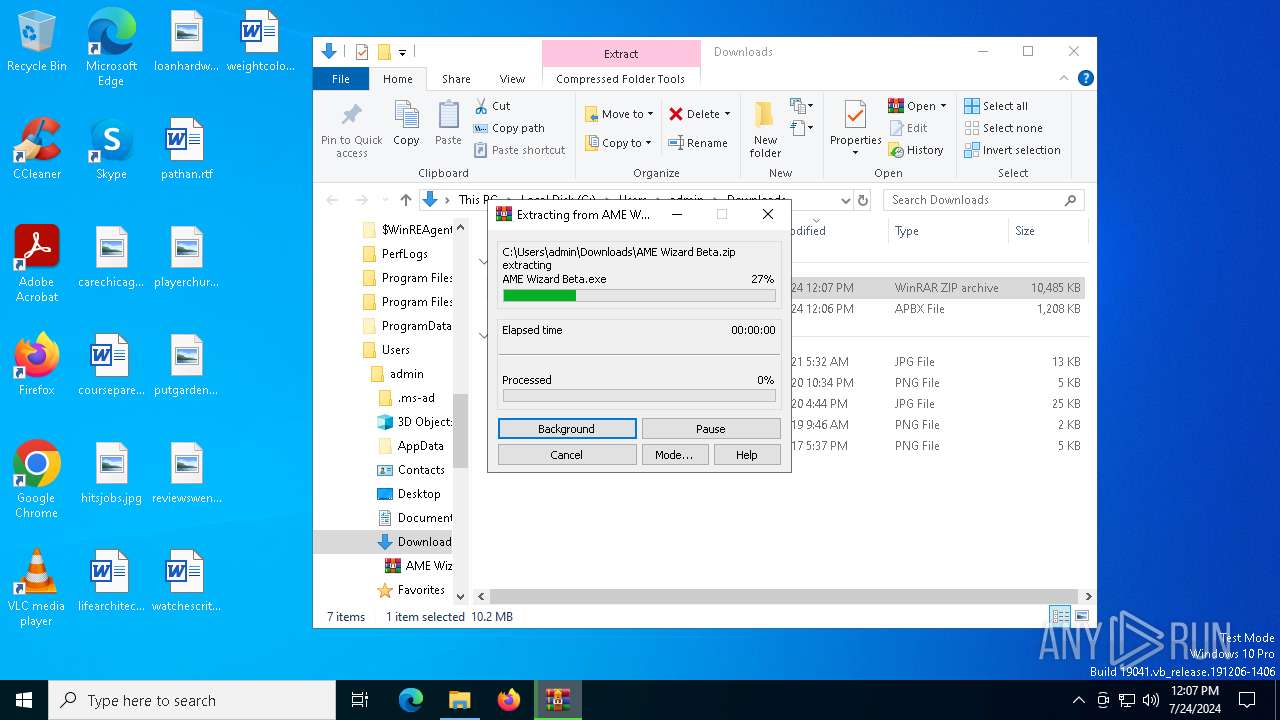
Drops the executable file immediately after the start
- AME Wizard Beta.exe (PID: 7424)
- powershell.exe (PID: 3848)
- RevisionTool-Setup.exe (PID: 2200)
- RevisionTool-Setup.tmp (PID: 1696)
- 7za.exe (PID: 7572)
MIMIKATZ has been detected (YARA)
- AME Wizard Beta.exe (PID: 7424)
- AME Wizard Beta.exe (PID: 3968)
- AME Wizard Beta.exe (PID: 5512)
- AME Wizard Beta.exe (PID: 7324)
Actions looks like stealing of personal data
- 7za.exe (PID: 7340)
Runs injected code in another process
- AME Wizard Beta.exe (PID: 5512)
Application was injected by another process
- AME Wizard Beta.exe (PID: 7324)
Bypass execution policy to execute commands
- powershell.exe (PID: 4548)
- powershell.exe (PID: 3848)
- powershell.exe (PID: 1112)
Modifies hosts file to block updates
- cmd.exe (PID: 7732)
Changes powershell execution policy (Bypass)
- AME Wizard Beta.exe (PID: 7324)
SUSPICIOUS
Drops 7-zip archiver for unpacking
- AME Wizard Beta.exe (PID: 7424)
Executable content was dropped or overwritten
- AME Wizard Beta.exe (PID: 7424)
- 7za.exe (PID: 7572)
- powershell.exe (PID: 3848)
- RevisionTool-Setup.exe (PID: 2200)
- RevisionTool-Setup.tmp (PID: 1696)
The process drops C-runtime libraries
- AME Wizard Beta.exe (PID: 7424)
- 7za.exe (PID: 7572)
- RevisionTool-Setup.tmp (PID: 1696)
The process creates files with name similar to system file names
- AME Wizard Beta.exe (PID: 7424)
Process drops legitimate windows executable
- AME Wizard Beta.exe (PID: 7424)
- 7za.exe (PID: 7572)
- RevisionTool-Setup.tmp (PID: 1696)
Reads the date of Windows installation
- AME Wizard Beta.exe (PID: 7424)
Reads security settings of Internet Explorer
- AME Wizard Beta.exe (PID: 5512)
- AME Wizard Beta.exe (PID: 7424)
- AME Wizard Beta.exe (PID: 3968)
- AME Wizard Beta.exe (PID: 7324)
Application launched itself
- AME Wizard Beta.exe (PID: 7424)
Connects to unusual port
- AME Wizard Beta.exe (PID: 7424)
Process drops SQLite DLL files
- 7za.exe (PID: 7572)
Starts CMD.EXE for commands execution
- AME Wizard Beta.exe (PID: 7324)
Process uses IPCONFIG to clear DNS cache
- cmd.exe (PID: 1124)
Uses powercfg.exe to modify the power settings
- AME Wizard Beta.exe (PID: 7324)
- powershell.exe (PID: 4548)
The process bypasses the loading of PowerShell profile settings
- AME Wizard Beta.exe (PID: 7324)
Starts POWERSHELL.EXE for commands execution
- AME Wizard Beta.exe (PID: 7324)
The process hide an interactive prompt from the user
- AME Wizard Beta.exe (PID: 7324)
Request a resource from the Internet using PowerShell's cmdlet
- AME Wizard Beta.exe (PID: 7324)
The executable file from the user directory is run by the CMD process
- RevisionTool-Setup.exe (PID: 2200)
Reads the Windows owner or organization settings
- RevisionTool-Setup.tmp (PID: 1696)
The process executes Powershell scripts
- AME Wizard Beta.exe (PID: 7324)
INFO
Application launched itself
- firefox.exe (PID: 132)
- firefox.exe (PID: 1772)
Checks proxy server information
- slui.exe (PID: 6592)
- AME Wizard Beta.exe (PID: 7424)
Reads Microsoft Office registry keys
- firefox.exe (PID: 132)
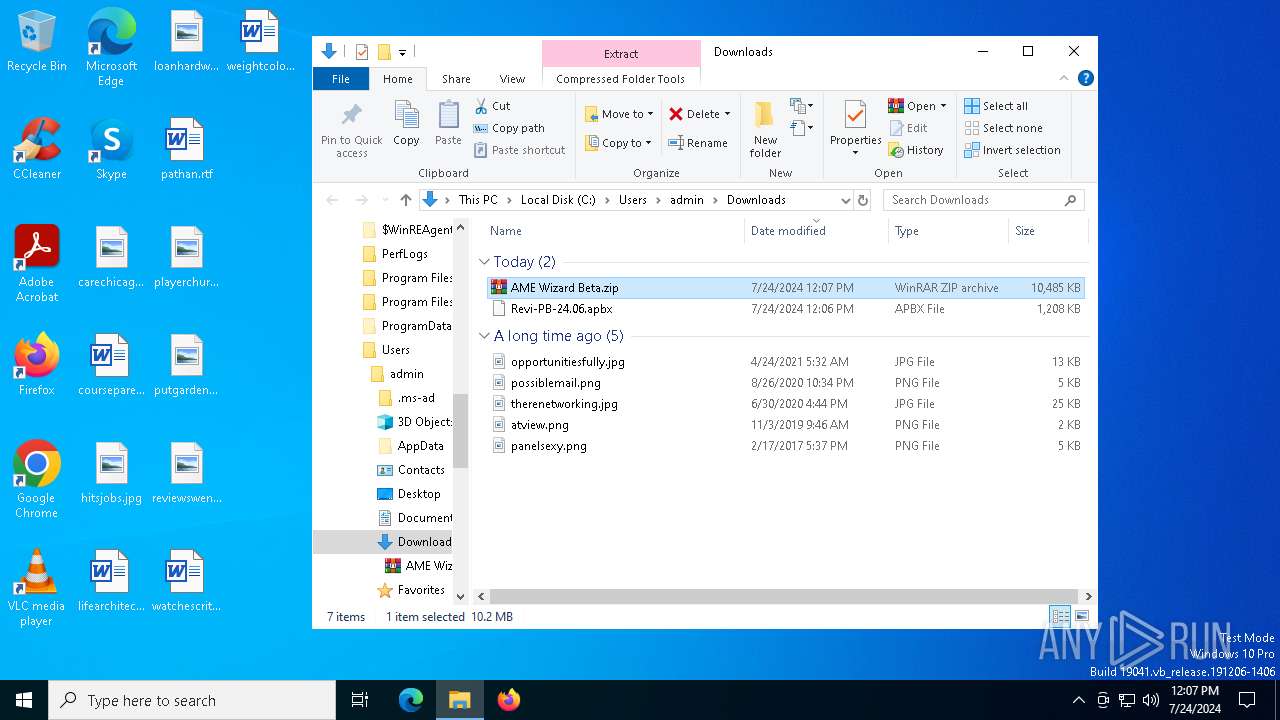
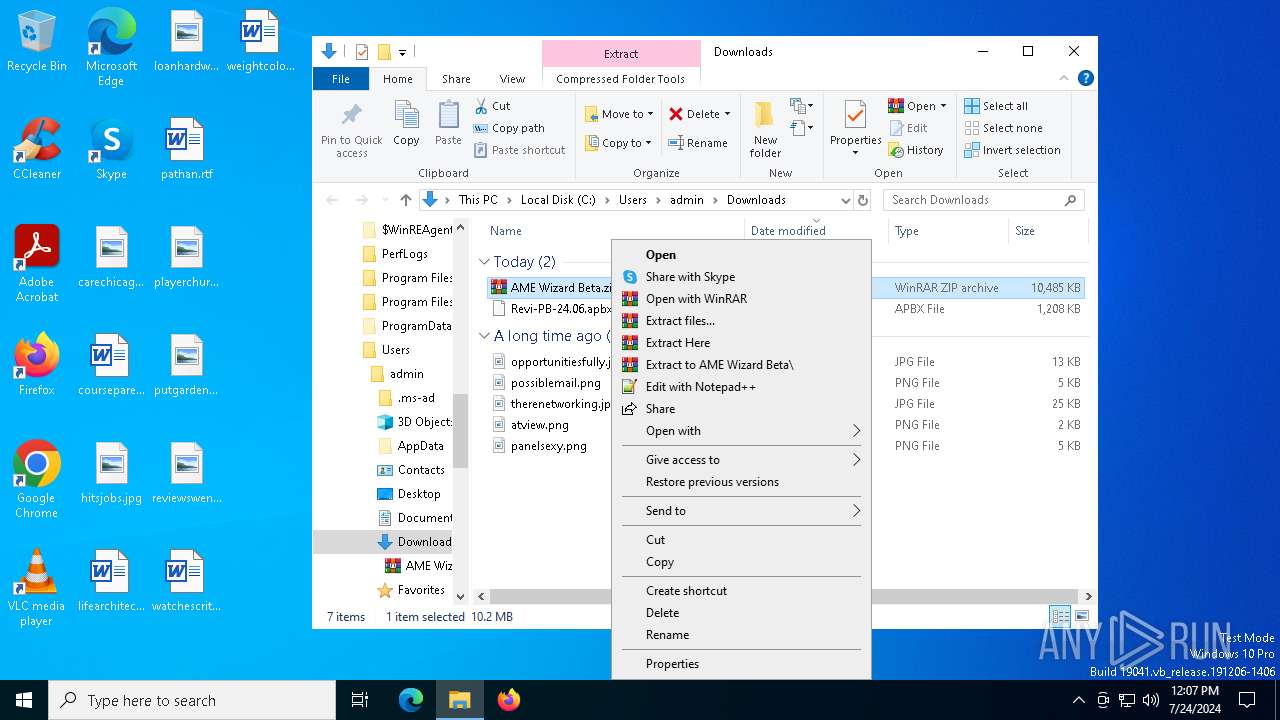
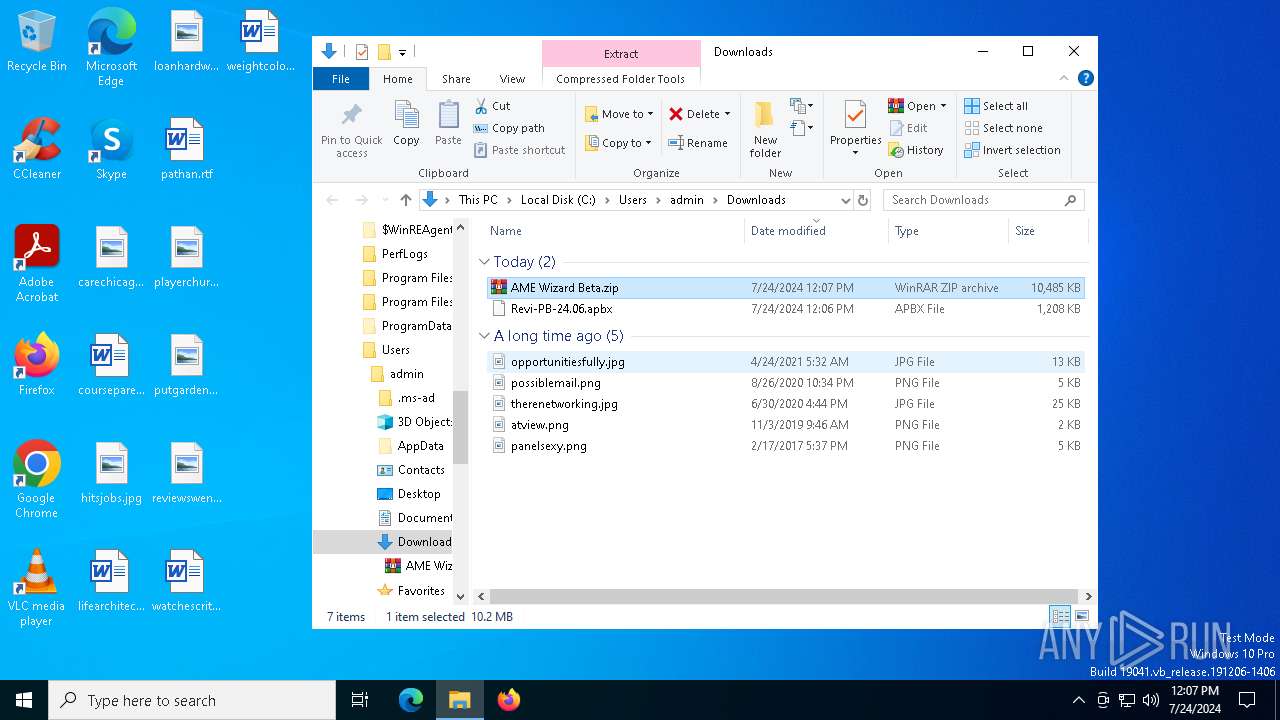
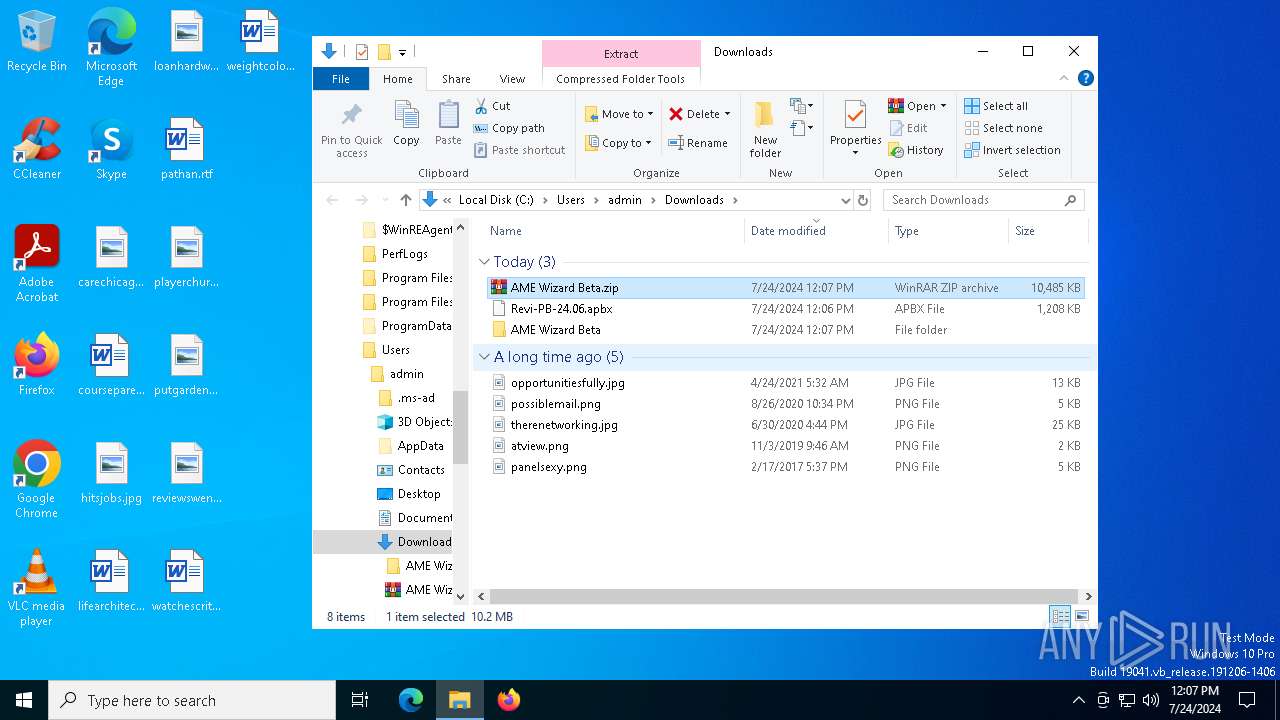
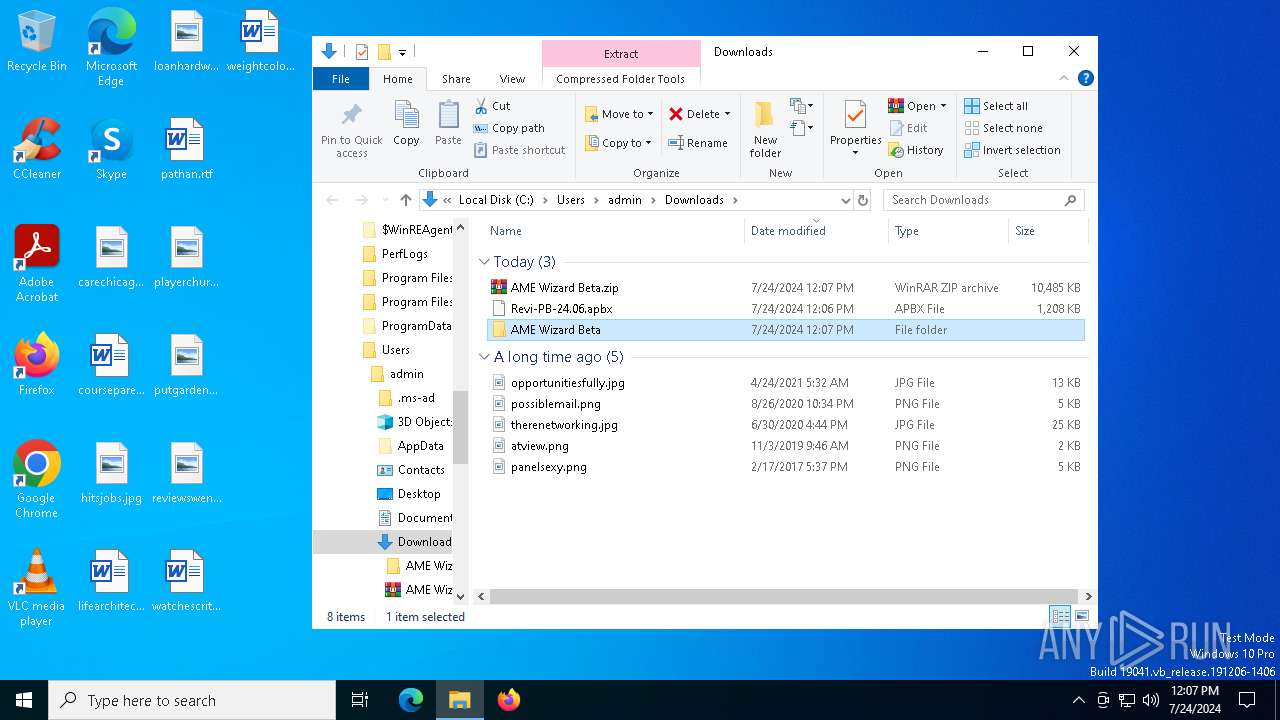
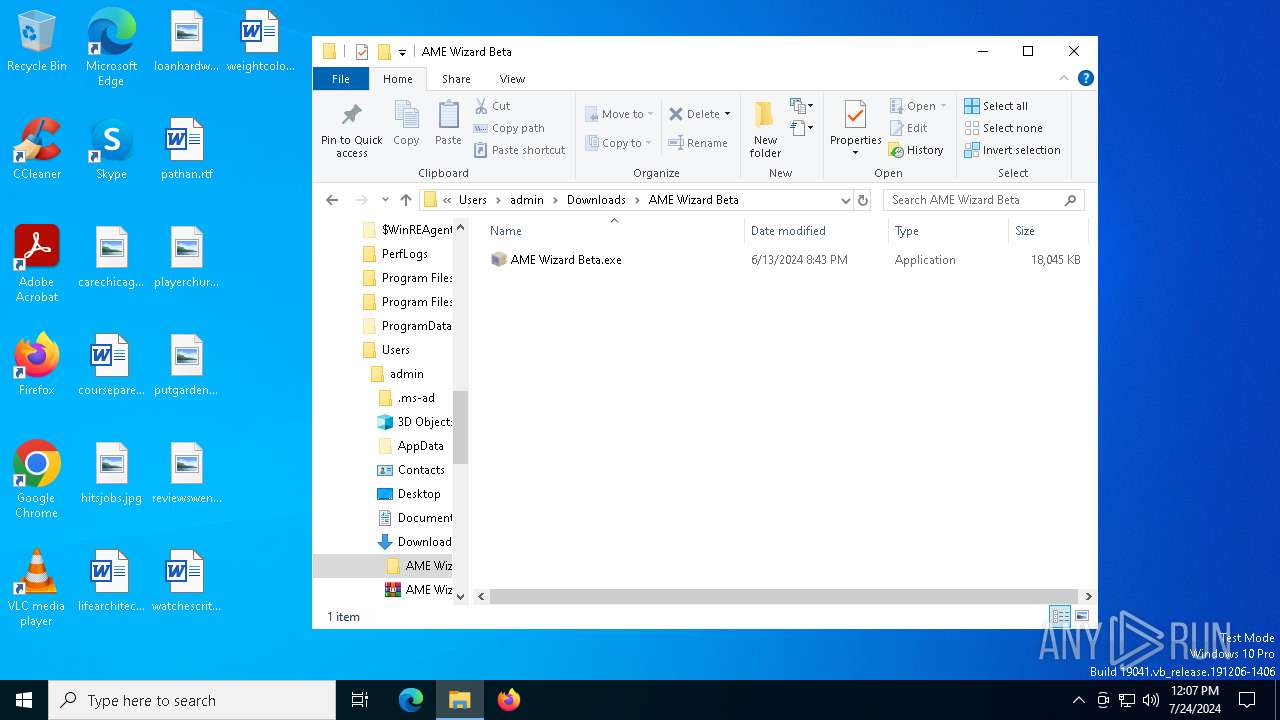
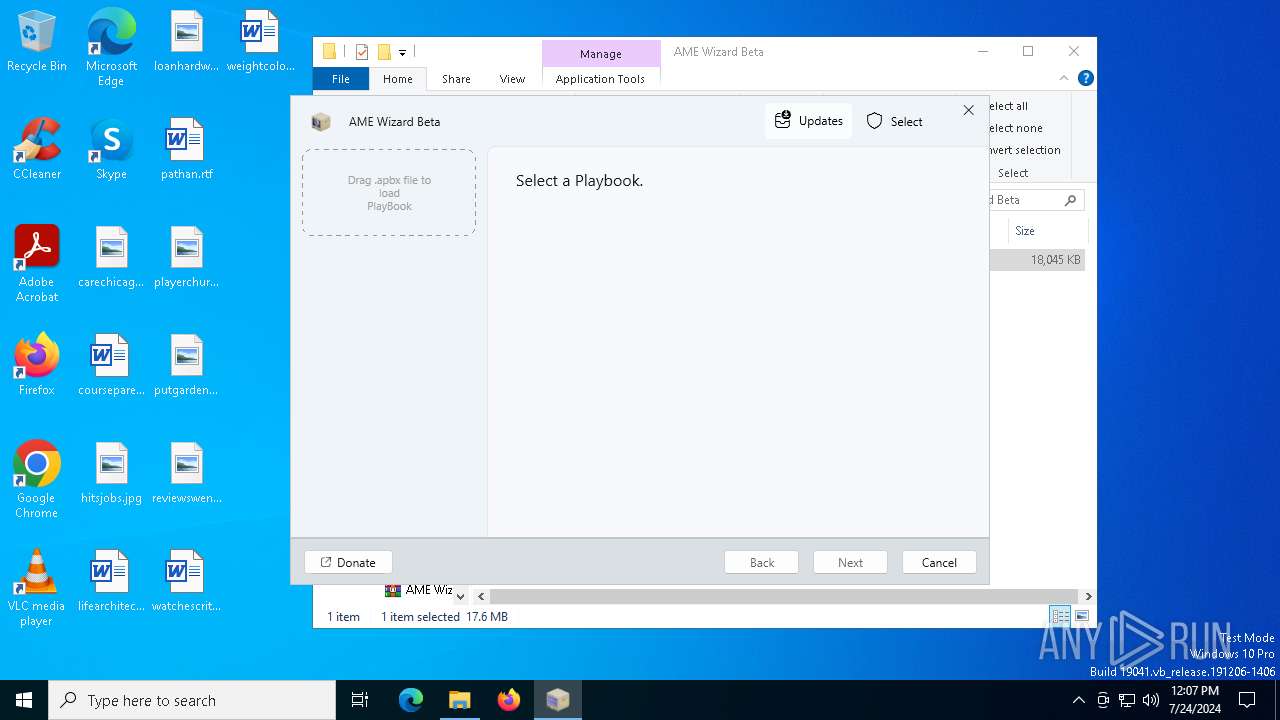
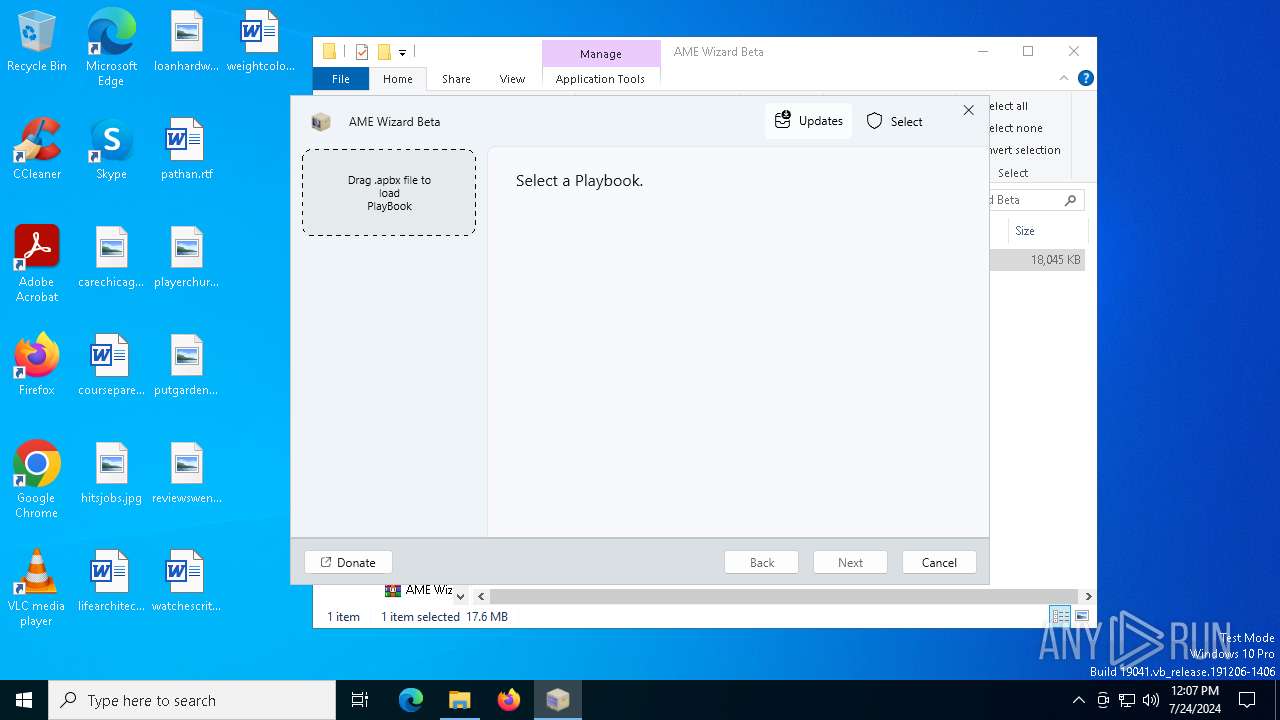
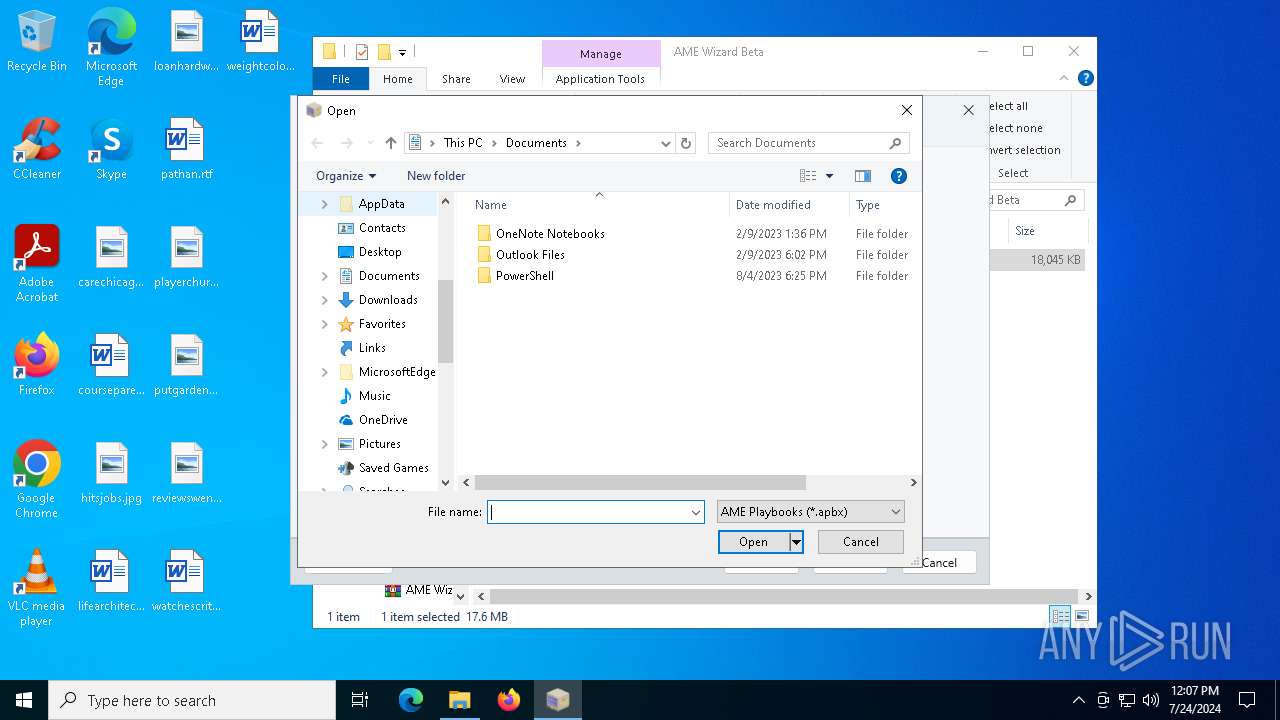
Manual execution by a user
- WinRAR.exe (PID: 4544)
- AME Wizard Beta.exe (PID: 7424)
Checks supported languages
- TextInputHost.exe (PID: 8080)
- AME Wizard Beta.exe (PID: 7424)
- AME Wizard Beta.exe (PID: 5512)
- 7za.exe (PID: 7228)
- AME Wizard Beta.exe (PID: 3968)
- 7za.exe (PID: 7340)
- 7za.exe (PID: 7572)
- AME Wizard Beta.exe (PID: 7324)
- RevisionTool-Setup.tmp (PID: 1696)
- RevisionTool-Setup.exe (PID: 2200)
The process uses the downloaded file
- firefox.exe (PID: 132)
- WinRAR.exe (PID: 4544)
- AME Wizard Beta.exe (PID: 5512)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 4544)
Drops the executable file immediately after the start
- WinRAR.exe (PID: 4544)
- firefox.exe (PID: 132)
Reads the software policy settings
- slui.exe (PID: 6592)
- AME Wizard Beta.exe (PID: 7424)
- powershell.exe (PID: 4548)
Reads the computer name
- TextInputHost.exe (PID: 8080)
- AME Wizard Beta.exe (PID: 7424)
- AME Wizard Beta.exe (PID: 5512)
- 7za.exe (PID: 7228)
- 7za.exe (PID: 7340)
- AME Wizard Beta.exe (PID: 3968)
- AME Wizard Beta.exe (PID: 7324)
- RevisionTool-Setup.tmp (PID: 1696)
- 7za.exe (PID: 7572)
Reads the machine GUID from the registry
- AME Wizard Beta.exe (PID: 7424)
- AME Wizard Beta.exe (PID: 5512)
- AME Wizard Beta.exe (PID: 3968)
- AME Wizard Beta.exe (PID: 7324)
Create files in a temporary directory
- AME Wizard Beta.exe (PID: 7424)
- 7za.exe (PID: 7228)
- 7za.exe (PID: 7340)
- 7za.exe (PID: 7572)
- powershell.exe (PID: 4548)
- RevisionTool-Setup.exe (PID: 2200)
- RevisionTool-Setup.tmp (PID: 1696)
Reads Environment values
- AME Wizard Beta.exe (PID: 7424)
- AME Wizard Beta.exe (PID: 5512)
- AME Wizard Beta.exe (PID: 7324)
Creates files in the program directory
- AME Wizard Beta.exe (PID: 7424)
- AME Wizard Beta.exe (PID: 5512)
- AME Wizard Beta.exe (PID: 7324)
- RevisionTool-Setup.tmp (PID: 1696)
Process checks computer location settings
- AME Wizard Beta.exe (PID: 7424)
Disables trace logs
- AME Wizard Beta.exe (PID: 7424)
- powershell.exe (PID: 3848)
Creates a software uninstall entry
- RevisionTool-Setup.tmp (PID: 1696)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
211
Monitored processes
69
Malicious processes
10
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 132 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://github.com/meetrevision/playbook/releases/download/24.06/Revi-PB-24.06.apbx | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 892 | ipconfig /flushdns | C:\Windows\System32\ipconfig.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: IP Configuration Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1084 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=2912 -childID 7 -isForBrowser -prefsHandle 7120 -prefMapHandle 2928 -prefsLen 31161 -prefMapSize 244343 -jsInitHandle 1172 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {c2a42e2e-3a94-4a18-a53f-c18004b91059} 132 "\\.\pipe\gecko-crash-server-pipe.132" 24913a65150 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1112 | "PowerShell" -NoP -ExecutionPolicy Bypass -File ngen.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | AME Wizard Beta.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 1124 | "cmd.exe" /C "ipconfig /flushdns" | C:\Windows\System32\cmd.exe | — | AME Wizard Beta.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1432 | "powercfg" -setacvalueindex scheme_current sub_processor PERFDECTHRESHOLD 8 | C:\Windows\System32\powercfg.exe | — | AME Wizard Beta.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Power Settings Command-Line Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1696 | "C:\Users\admin\AppData\Local\Temp\is-LE6DB.tmp\RevisionTool-Setup.tmp" /SL5="$40366,13799805,807936,C:\Users\admin\AppData\Local\Temp\RevisionTool-Setup.exe" /VERYSILENT /TASKS="desktopicon" | C:\Users\admin\AppData\Local\Temp\is-LE6DB.tmp\RevisionTool-Setup.tmp | RevisionTool-Setup.exe | ||||||||||||
User: SYSTEM Company: Revision Integrity Level: SYSTEM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 1720 | "cmd.exe" /C "robocopy "Licenses" "%SystemDrive%\Licenses" /E /PURGE /IM /IT /NP" | C:\Windows\System32\cmd.exe | — | AME Wizard Beta.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1772 | "C:\Program Files\Mozilla Firefox\firefox.exe" "https://github.com/meetrevision/playbook/releases/download/24.06/Revi-PB-24.06.apbx" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 1780 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powercfg.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
39 744
Read events
39 549
Write events
183
Delete events
12
Modification events
| (PID) Process: | (1772) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: C88FA6C400000000 | |||
| (PID) Process: | (132) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: C760A8C400000000 | |||
| (PID) Process: | (132) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 0 | |||
| (PID) Process: | (132) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Progress |
Value: 1 | |||
| (PID) Process: | (132) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Installer\308046B0AF4A39CB |
| Operation: | delete value | Name: | installer.taskbarpin.win10.enabled |
Value: | |||
| (PID) Process: | (132) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (132) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (132) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Theme |
Value: 1 | |||
| (PID) Process: | (132) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\PreXULSkeletonUISettings |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Enabled |
Value: 1 | |||
| (PID) Process: | (132) firefox.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
Executable files
114
Suspicious files
196
Text files
166
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 132 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 132 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 132 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 132 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 132 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs-1.js | text | |
MD5:7A97B8DBC4F98D175F958C00F463A52A | SHA256:92074D2ED1AA1FD621287E35DB9EF1AE3DC04777EFAE5F09E7A3B4534C201548 | |||
| 132 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\3561288849sdhlie.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 132 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cookies.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 132 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\storage\permanent\chrome\idb\1657114595AmcateirvtiSty.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 132 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\prefs.js | text | |
MD5:7A97B8DBC4F98D175F958C00F463A52A | SHA256:92074D2ED1AA1FD621287E35DB9EF1AE3DC04777EFAE5F09E7A3B4534C201548 | |||
| 132 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\cert9.db | sqlite | |
MD5:68CEA1D3B3C04A00D85782F62F0B7C4D | SHA256:7AE6CCC57EF1E9AF6885FA6757149DAEBA8462FE535BEDF185DA9EDE8175D947 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
122
DNS requests
151
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
132 | firefox.exe | POST | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/ | unknown | — | — | unknown |
132 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
132 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/canonical.html | unknown | — | — | whitelisted |
132 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | unknown | — | — | whitelisted |
132 | firefox.exe | POST | 200 | 184.24.77.55:80 | http://r3.o.lencr.org/ | unknown | — | — | unknown |
132 | firefox.exe | POST | 200 | 142.250.185.195:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
132 | firefox.exe | POST | — | 142.250.185.195:80 | http://o.pki.goog/wr2 | unknown | — | — | unknown |
132 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
132 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
132 | firefox.exe | POST | 200 | 184.24.77.62:80 | http://r10.o.lencr.org/ | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6012 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4016 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3500 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.23.209.185:443 | — | Akamai International B.V. | GB | whitelisted |
— | — | 4.208.221.206:443 | licensing.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
4204 | svchost.exe | 4.208.221.206:443 | licensing.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4048 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6592 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
licensing.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
detectportal.firefox.com |
| whitelisted |
github.com |
| shared |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
contile.services.mozilla.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2284 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2284 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2284 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2284 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2284 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2284 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |
2284 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .cc TLD |