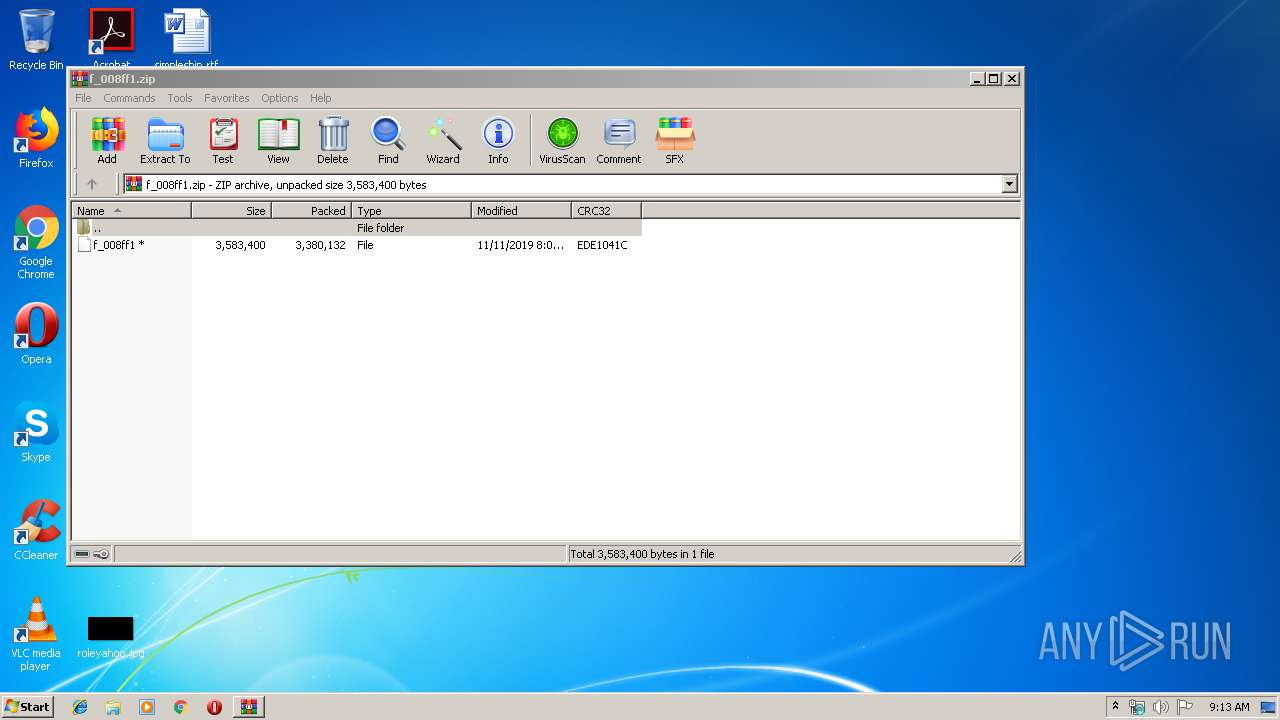
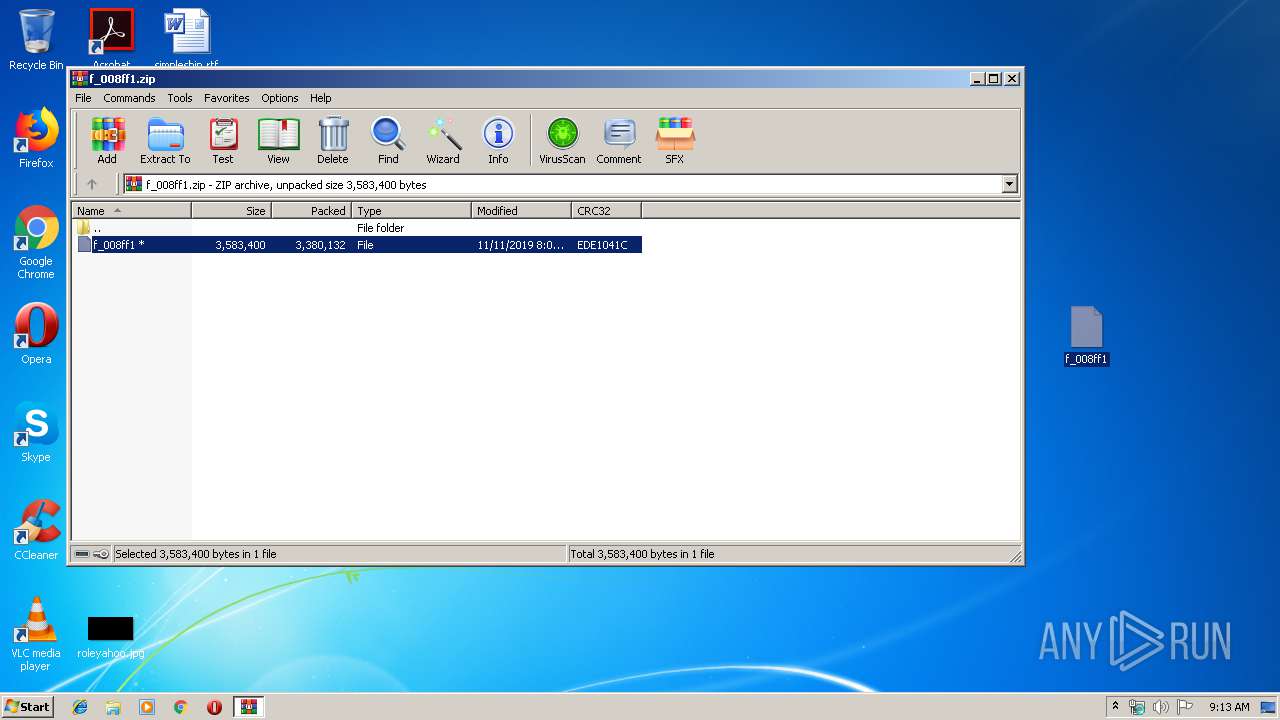
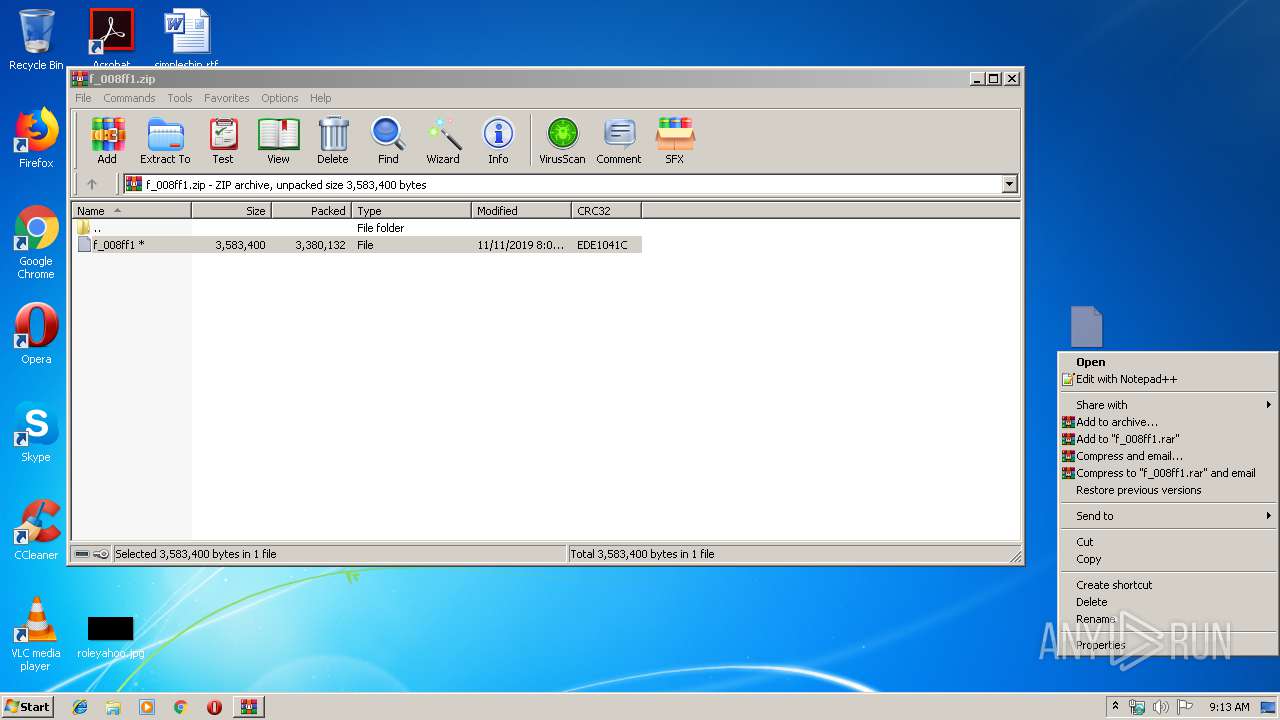
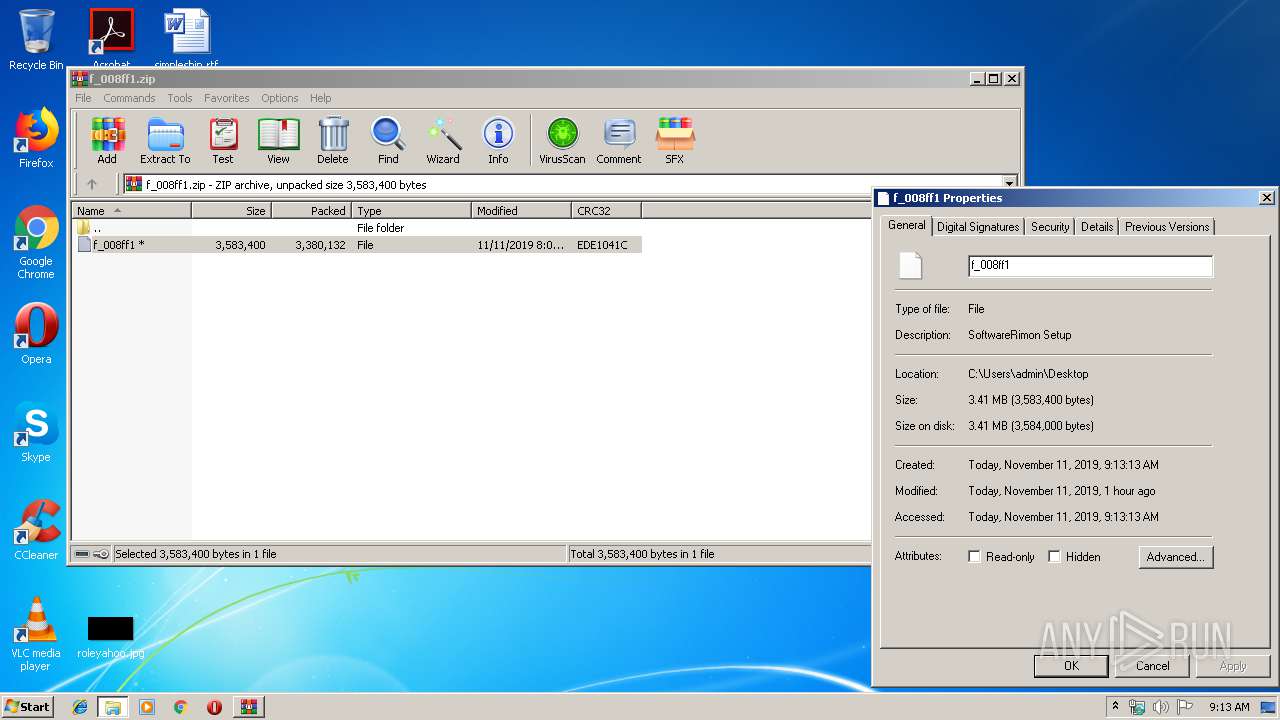
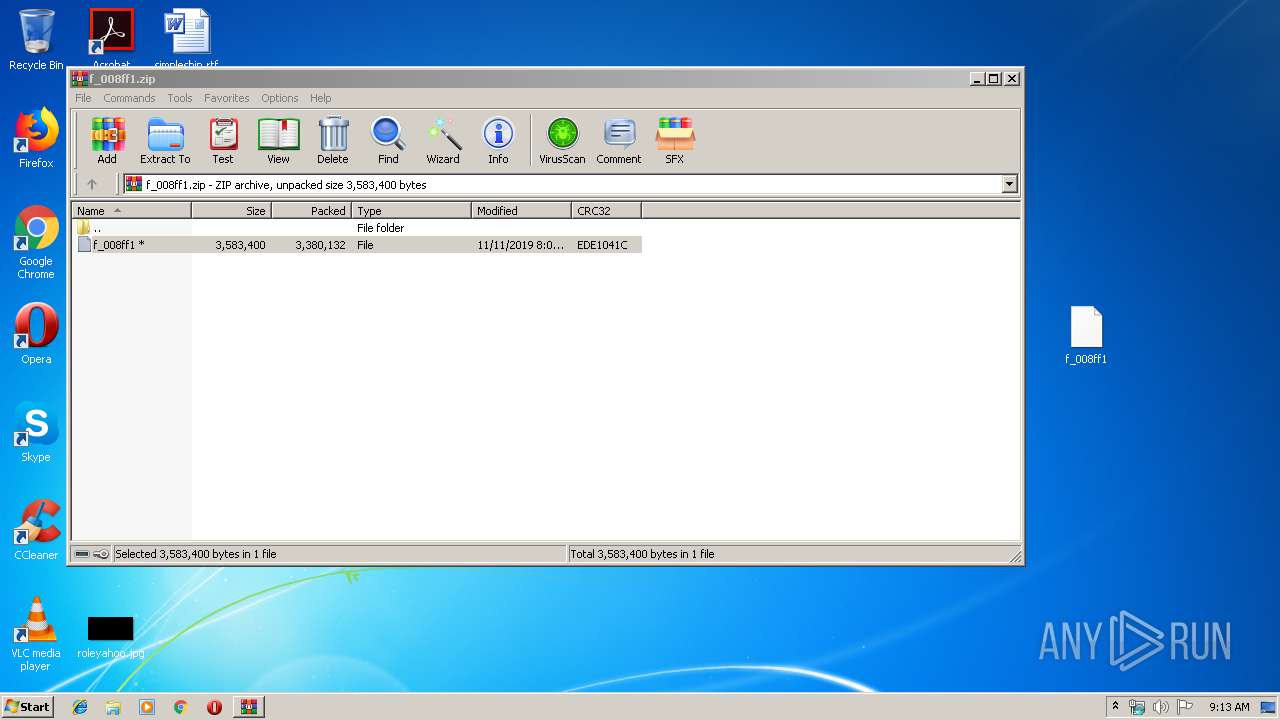
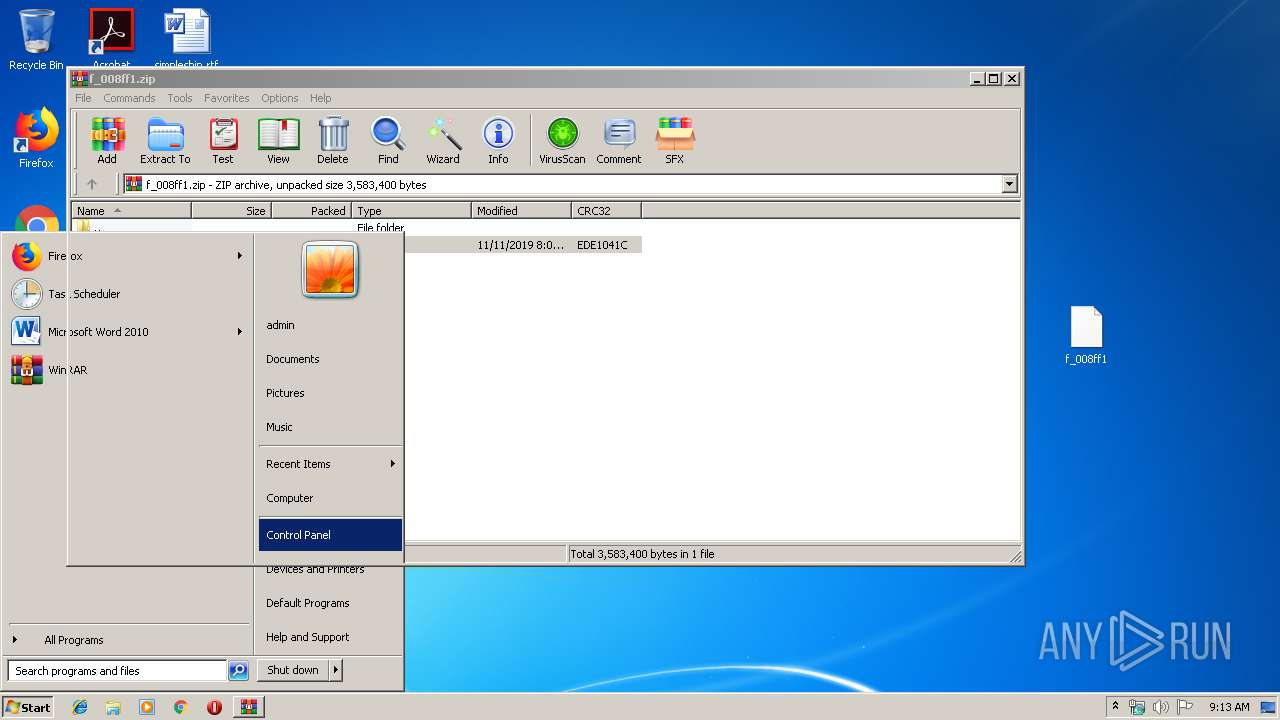
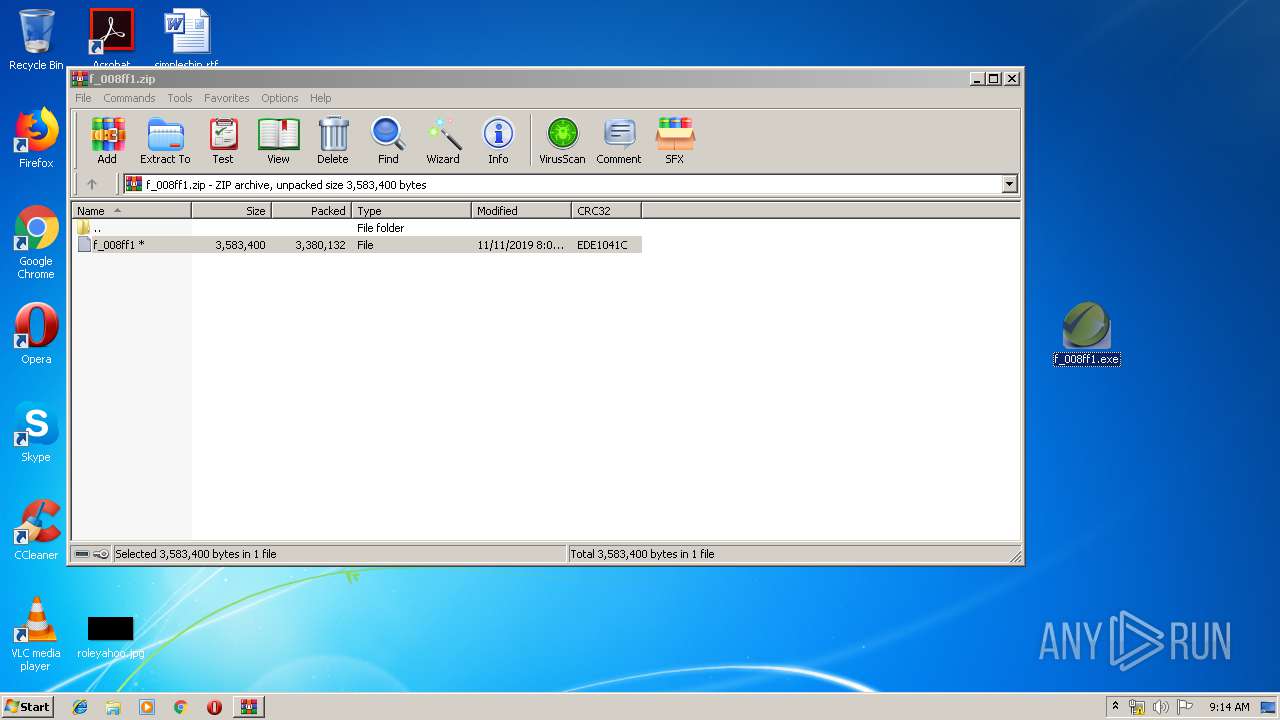
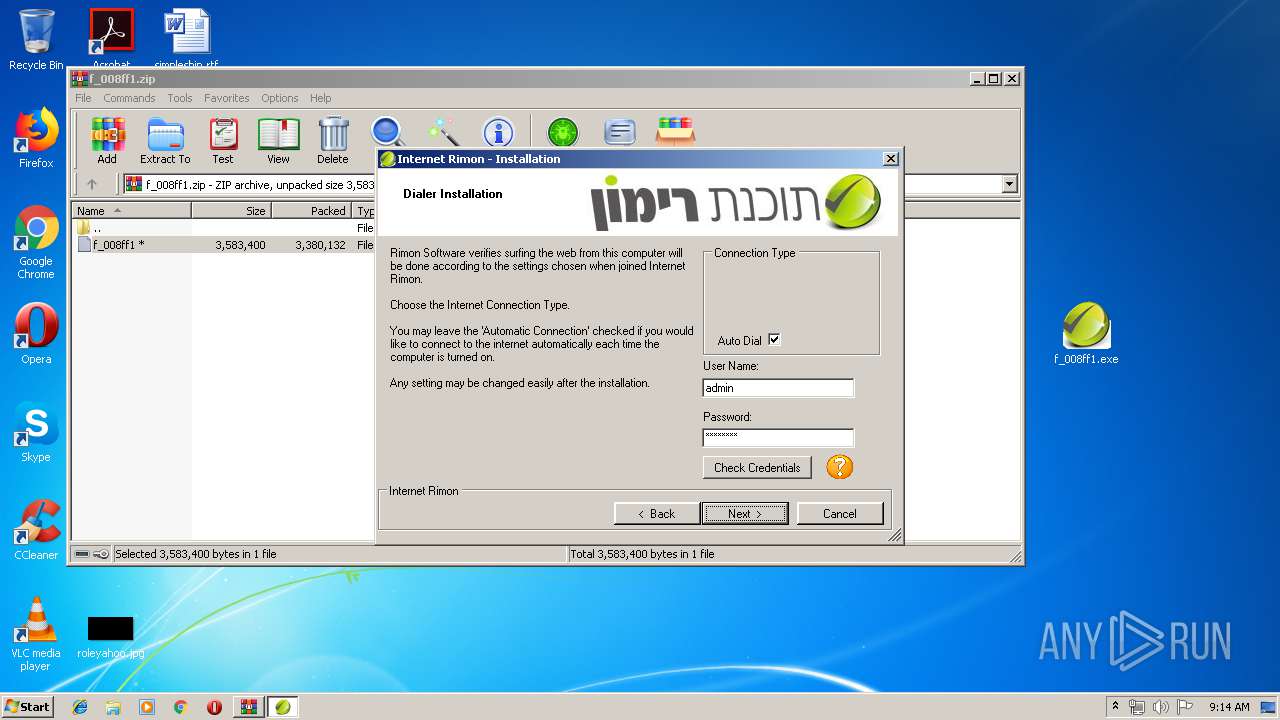
| File name: | f_008ff1.zip |
| Full analysis: | https://app.any.run/tasks/ebfc2039-f8a7-4e05-bce6-7368bdbbbdbc |
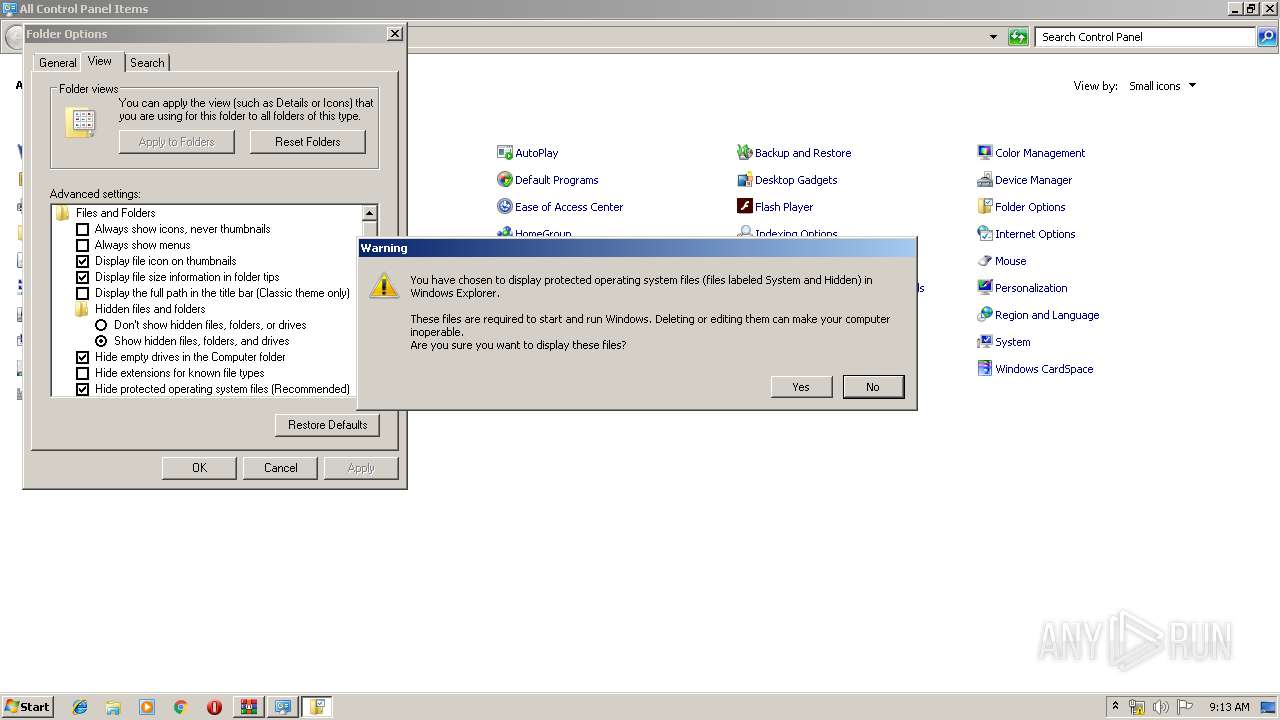
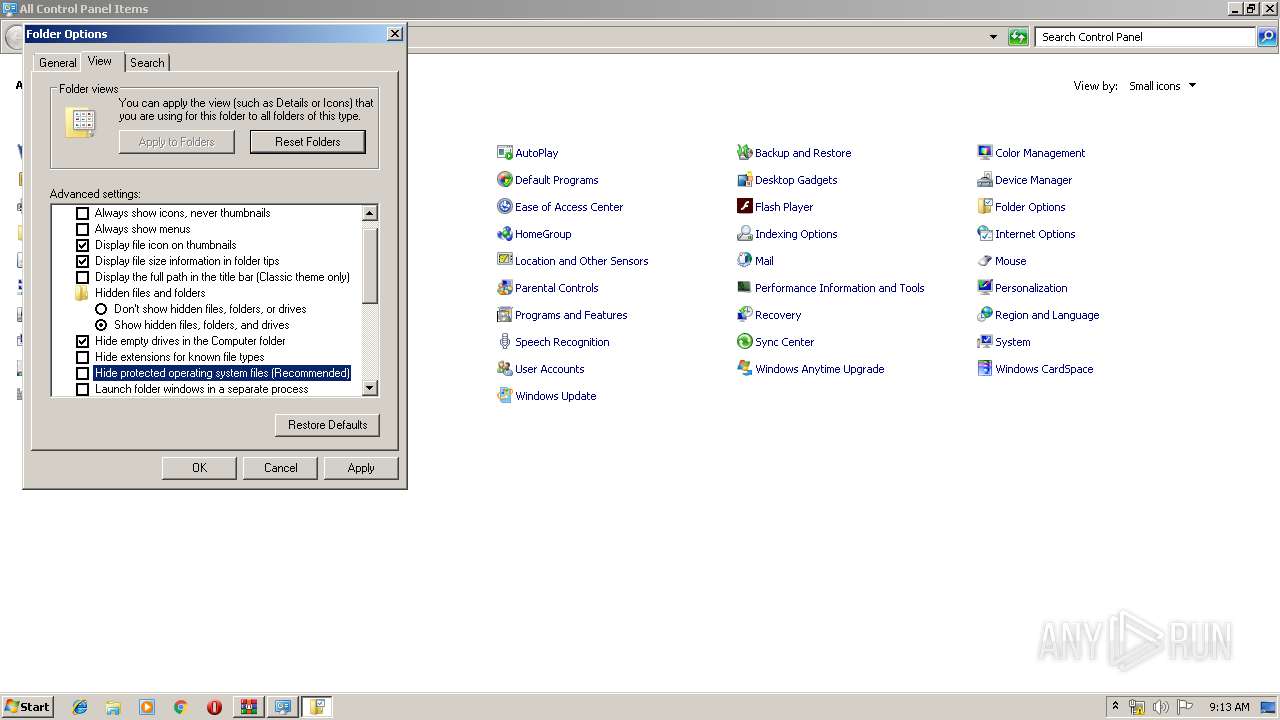
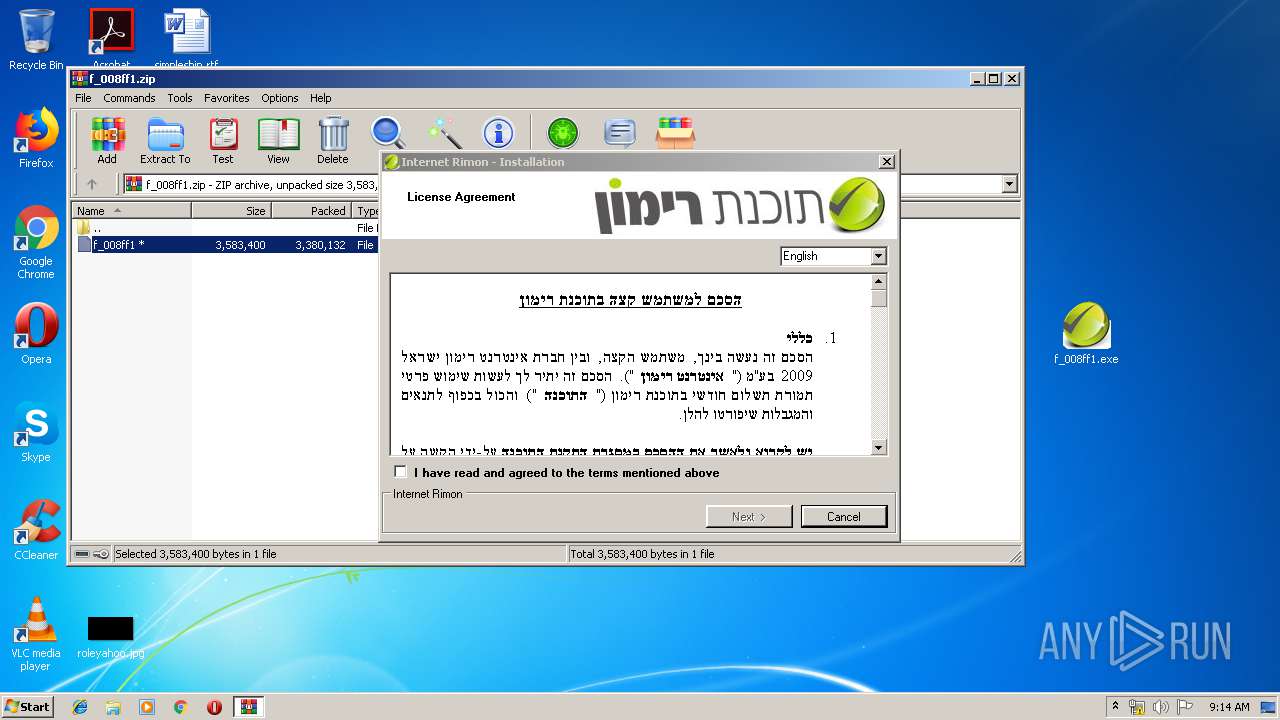
| Verdict: | Malicious activity |
| Analysis date: | November 11, 2019, 09:12:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 7D8D82760C007AC9BF27C5907F1514DB |
| SHA1: | ED8C00F65E82AC667653A6260CD6B53C7791FC2D |
| SHA256: | 6E585FCE11573CB467F876ED612C6B004012363969D128AACEAAEF6B242DCB76 |
| SSDEEP: | 98304:PMHznBSiWKWjZmp/I4TzZUUzrMI3dZn2tbYxEB8I:PsntCjZmCfjI3/IsxEB8I |
MALICIOUS
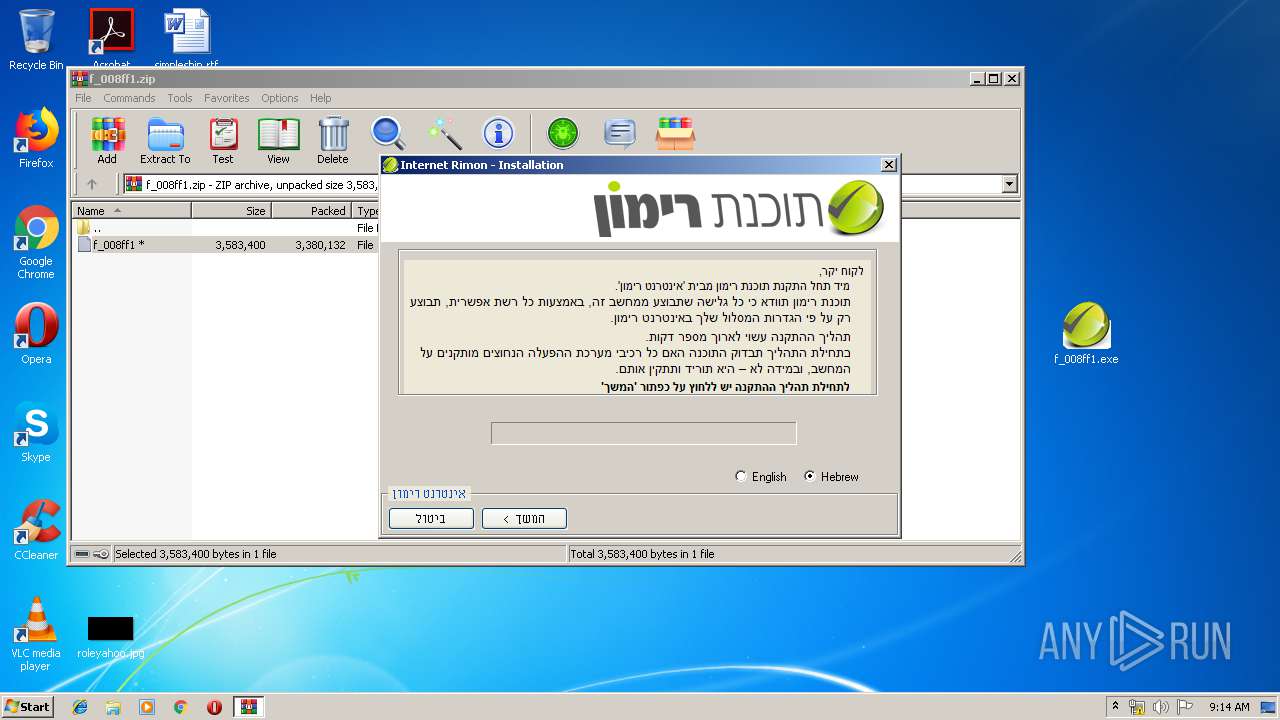
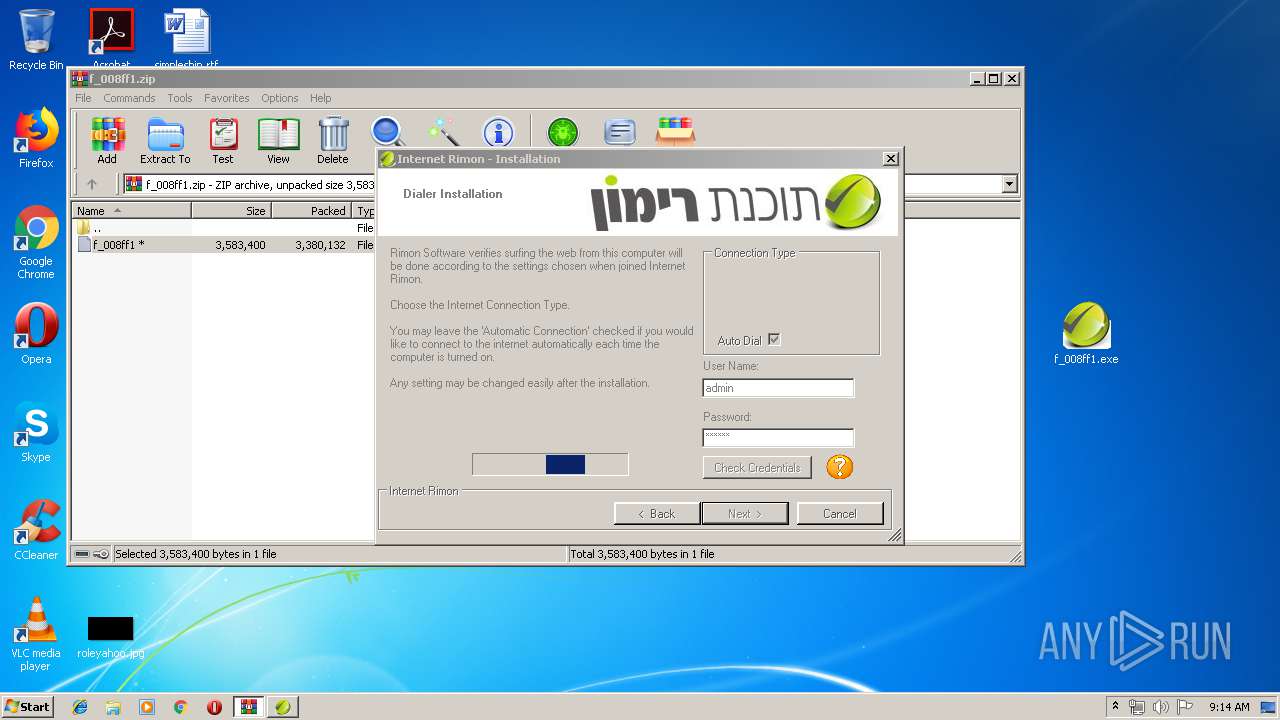
Application was dropped or rewritten from another process
- f_008ff1.exe (PID: 3796)
- f_008ff1.exe (PID: 3992)
- PreSetup.exe (PID: 3000)
- SoftwareRimonWin7.exe (PID: 492)
- RInstall.exe (PID: 3928)
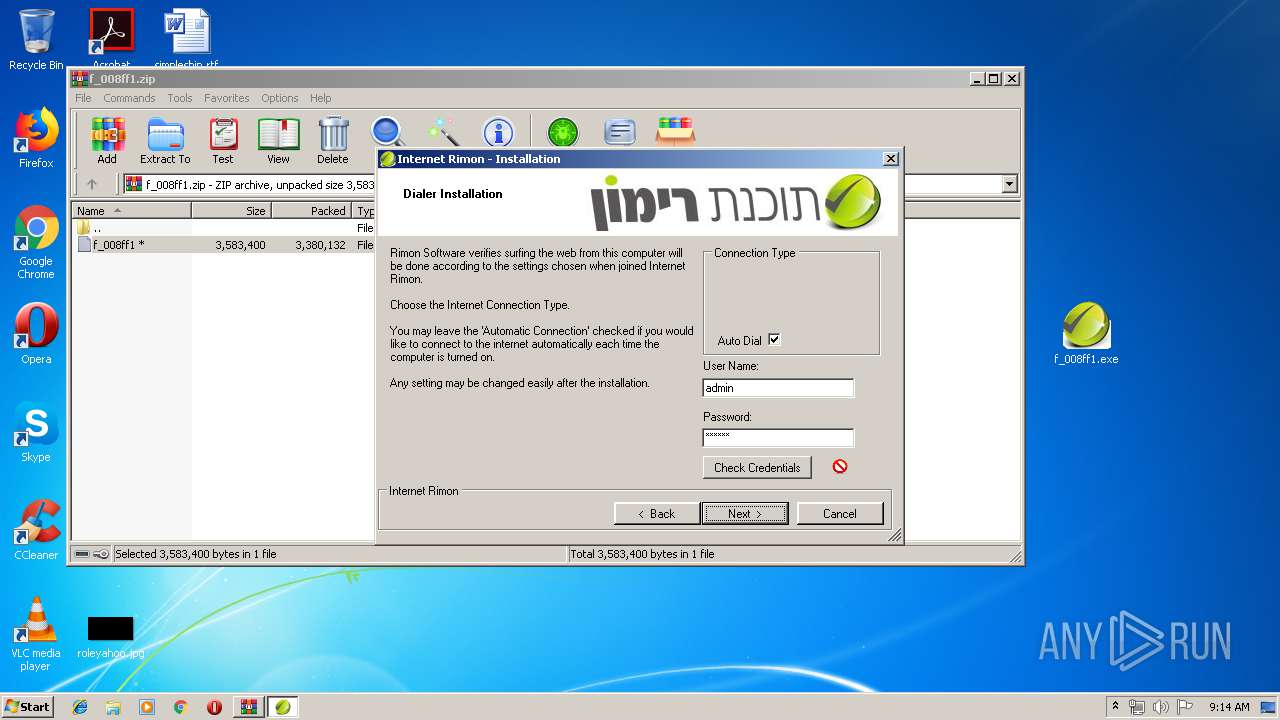
Changes settings of System certificates
- RInstall.exe (PID: 3928)
Loads dropped or rewritten executable
- RInstall.exe (PID: 3928)
SUSPICIOUS
Executable content was dropped or overwritten
- f_008ff1.exe (PID: 3796)
- f_008ff1.exe (PID: 3992)
- f_008ff1.tmp (PID: 3600)
- PreSetup.exe (PID: 3000)
- SoftwareRimonWin7.exe (PID: 492)
Reads the Windows organization settings
- f_008ff1.tmp (PID: 3600)
Reads Windows owner or organization settings
- f_008ff1.tmp (PID: 3600)
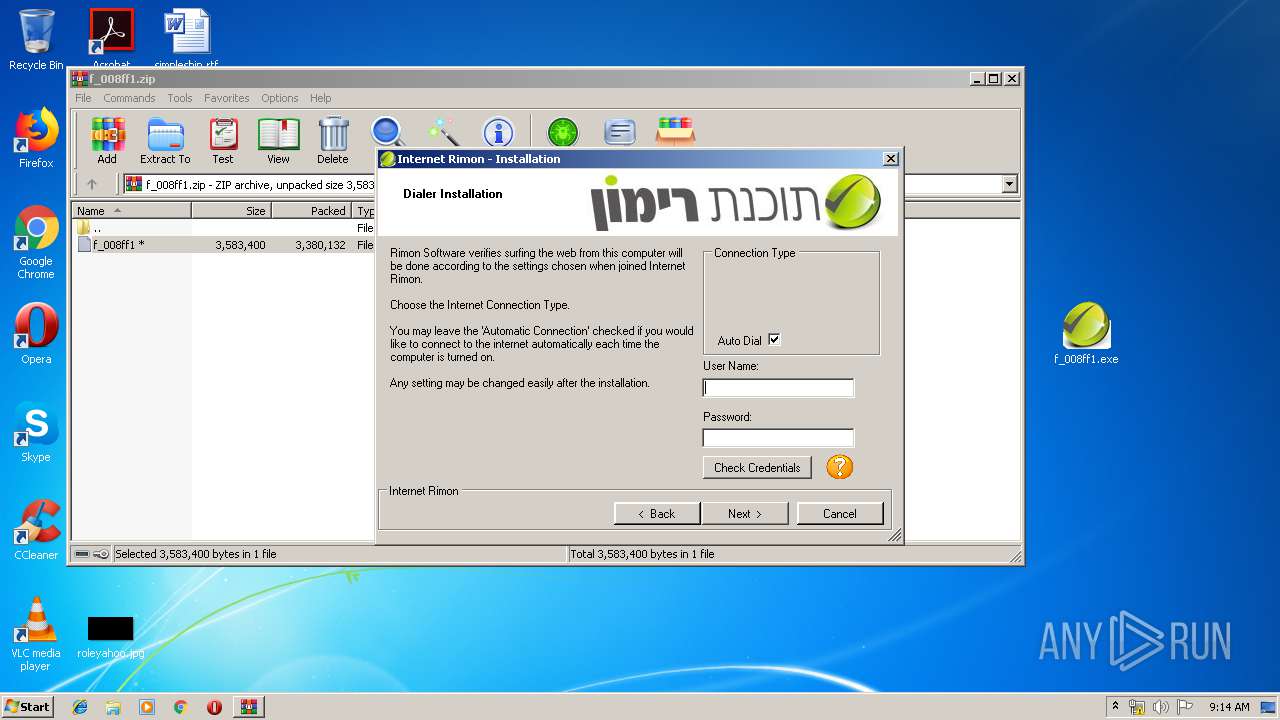
Reads internet explorer settings
- RInstall.exe (PID: 3928)
Adds / modifies Windows certificates
- RInstall.exe (PID: 3928)
Uses TASKKILL.EXE to kill process
- RInstall.exe (PID: 3928)
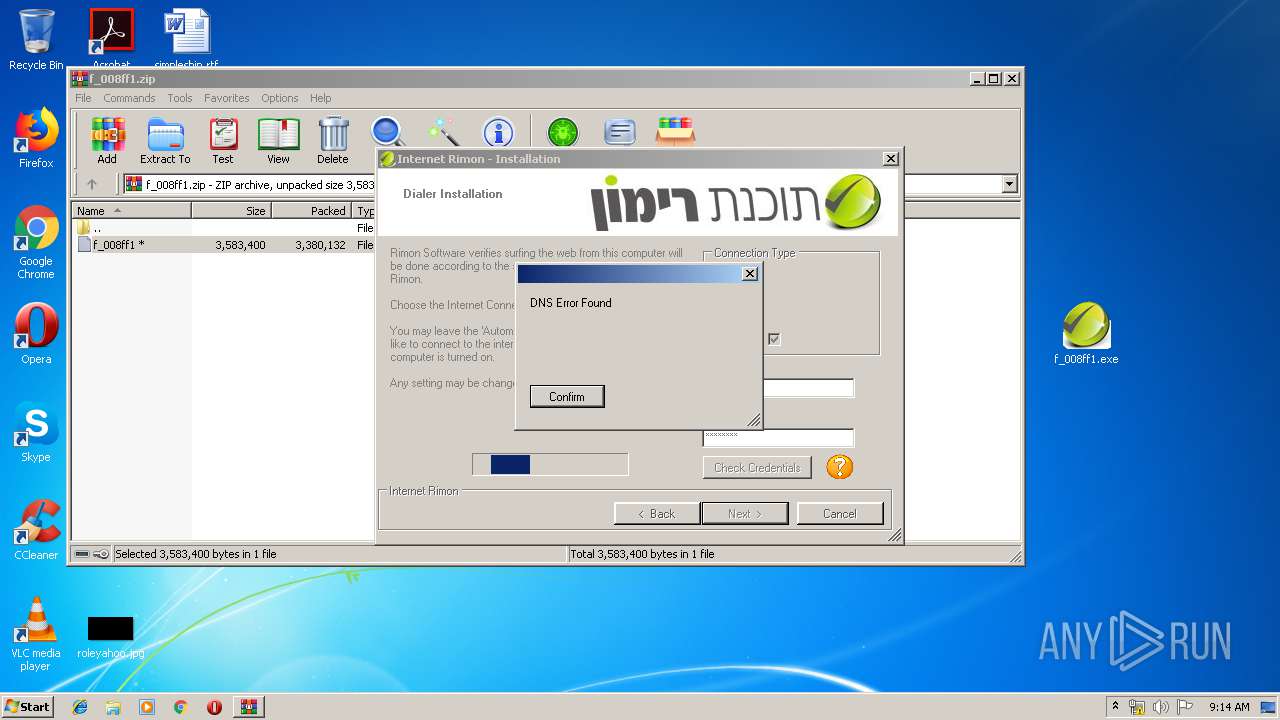
Connects to server without host name
- RInstall.exe (PID: 3928)
INFO
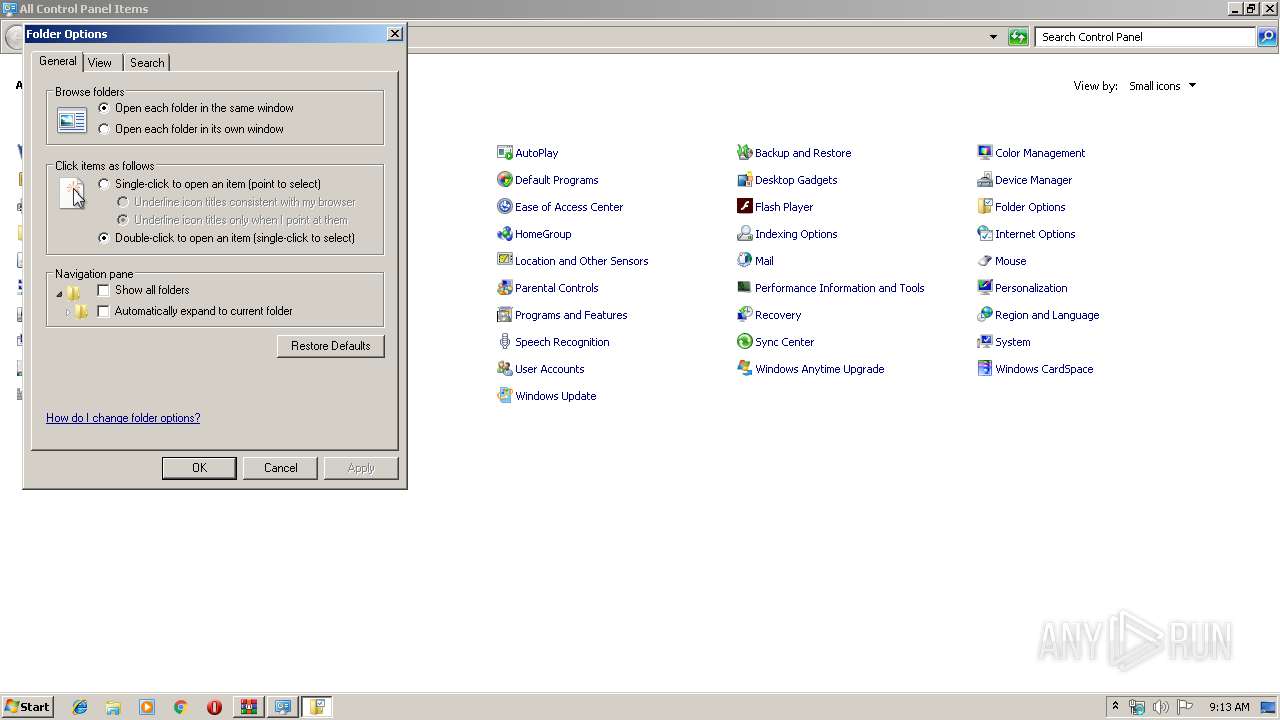
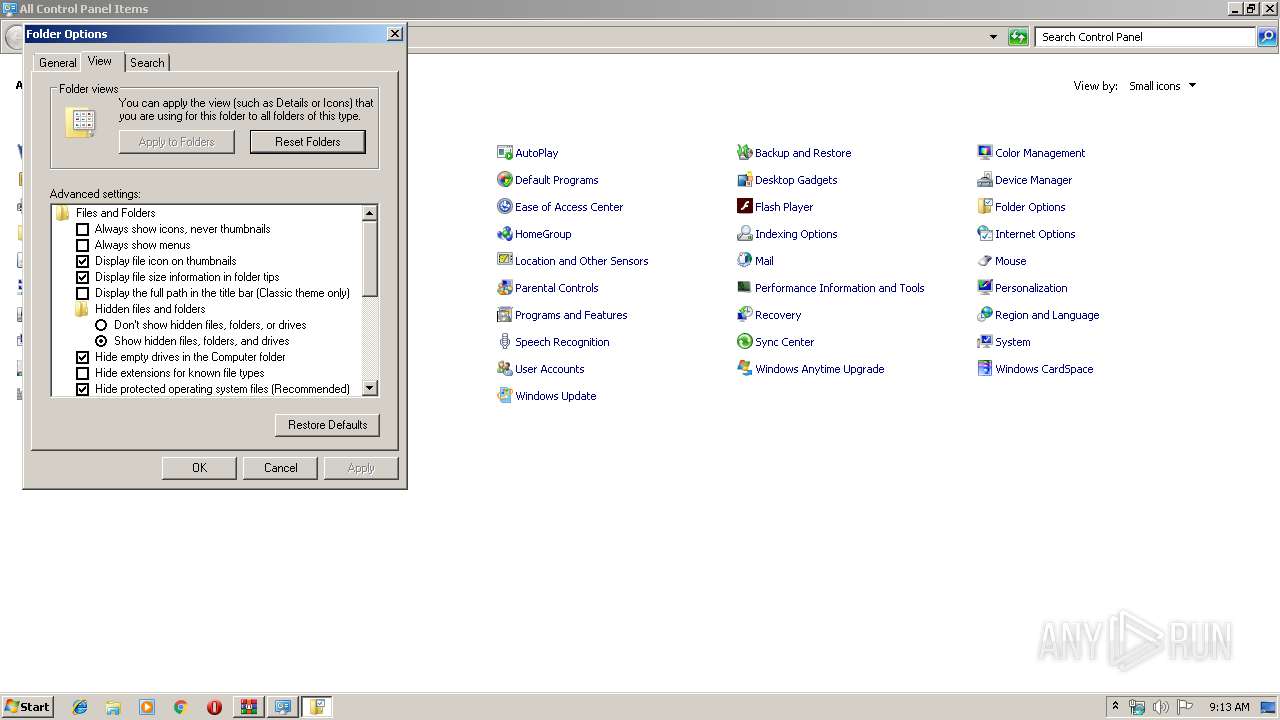
Manual execution by user
- rundll32.exe (PID: 2880)
- explorer.exe (PID: 1748)
- f_008ff1.exe (PID: 3796)
Application was dropped or rewritten from another process
- f_008ff1.tmp (PID: 3664)
- f_008ff1.tmp (PID: 3600)
Loads dropped or rewritten executable
- f_008ff1.tmp (PID: 3600)
Creates files in the program directory
- f_008ff1.tmp (PID: 3600)
Dropped object may contain Bitcoin addresses
- SoftwareRimonWin7.exe (PID: 492)
- PreSetup.exe (PID: 3000)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
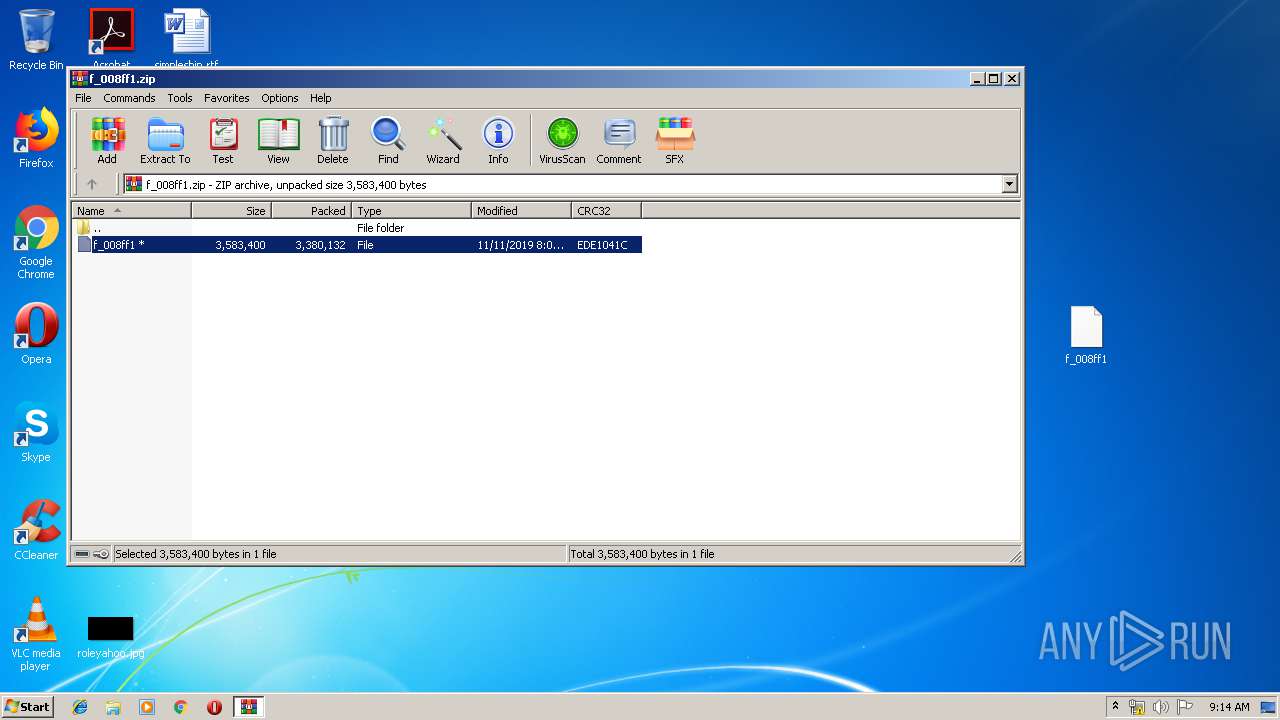
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:11:11 08:05:19 |
| ZipCRC: | 0xede1041c |
| ZipCompressedSize: | 3380132 |
| ZipUncompressedSize: | 3583400 |
| ZipFileName: | f_008ff1 |
Total processes
57
Monitored processes
13
Malicious processes
5
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 492 | "C:\Users\admin\AppData\Local\Temp\rimon\SoftwareRimonWin7.exe" | C:\Users\admin\AppData\Local\Temp\rimon\SoftwareRimonWin7.exe | f_008ff1.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1748 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2208 | "C:\Windows\System32\taskkill.exe" /F /IM nfserv.exe /IM nfwd.exe | C:\Windows\System32\taskkill.exe | — | RInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
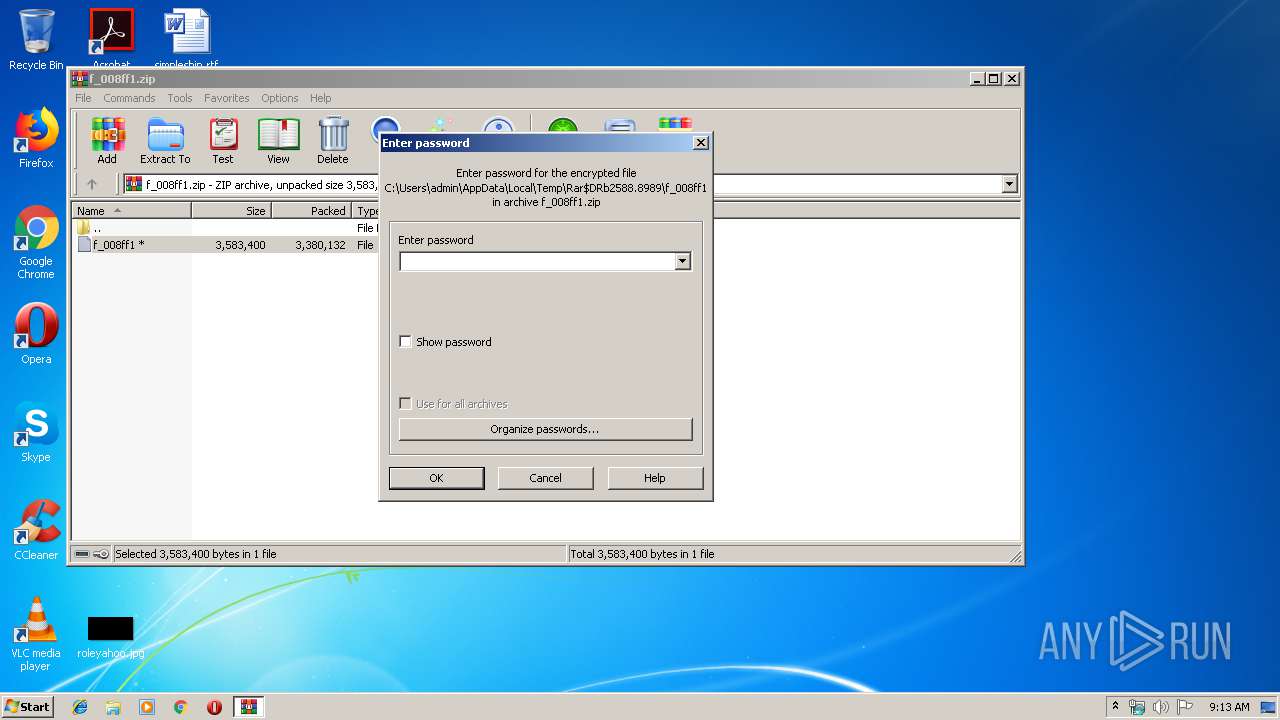
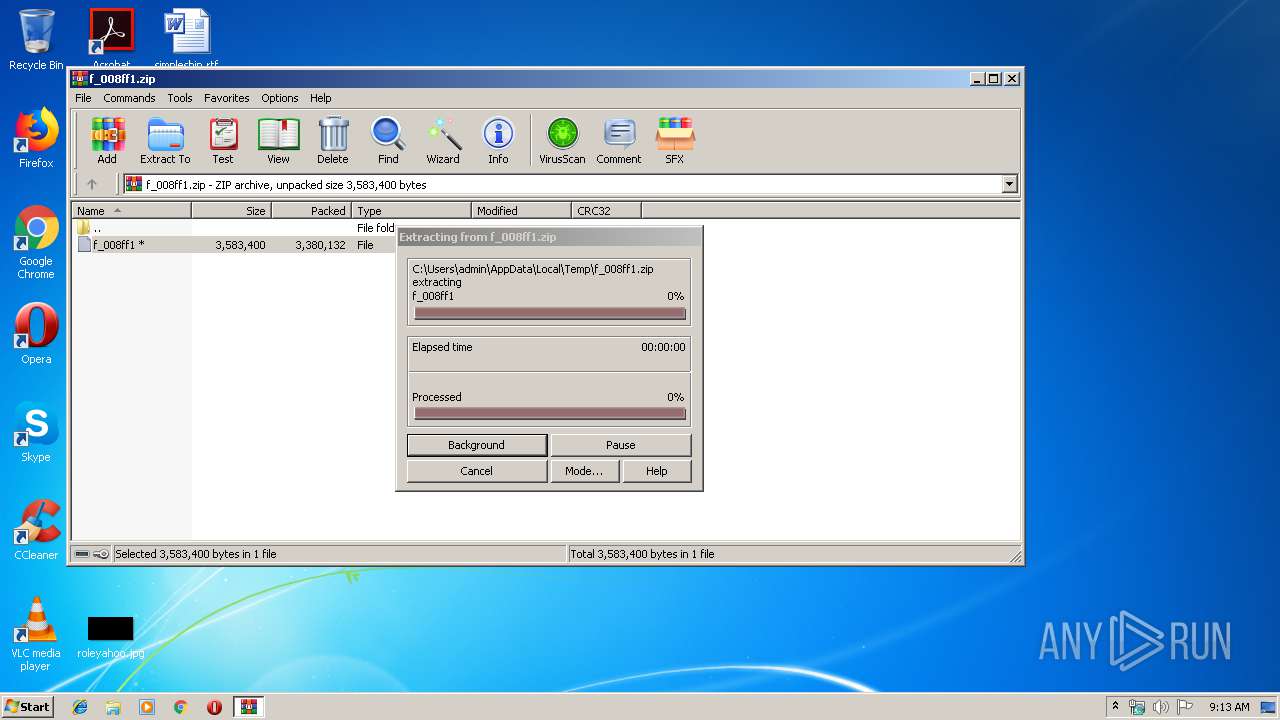
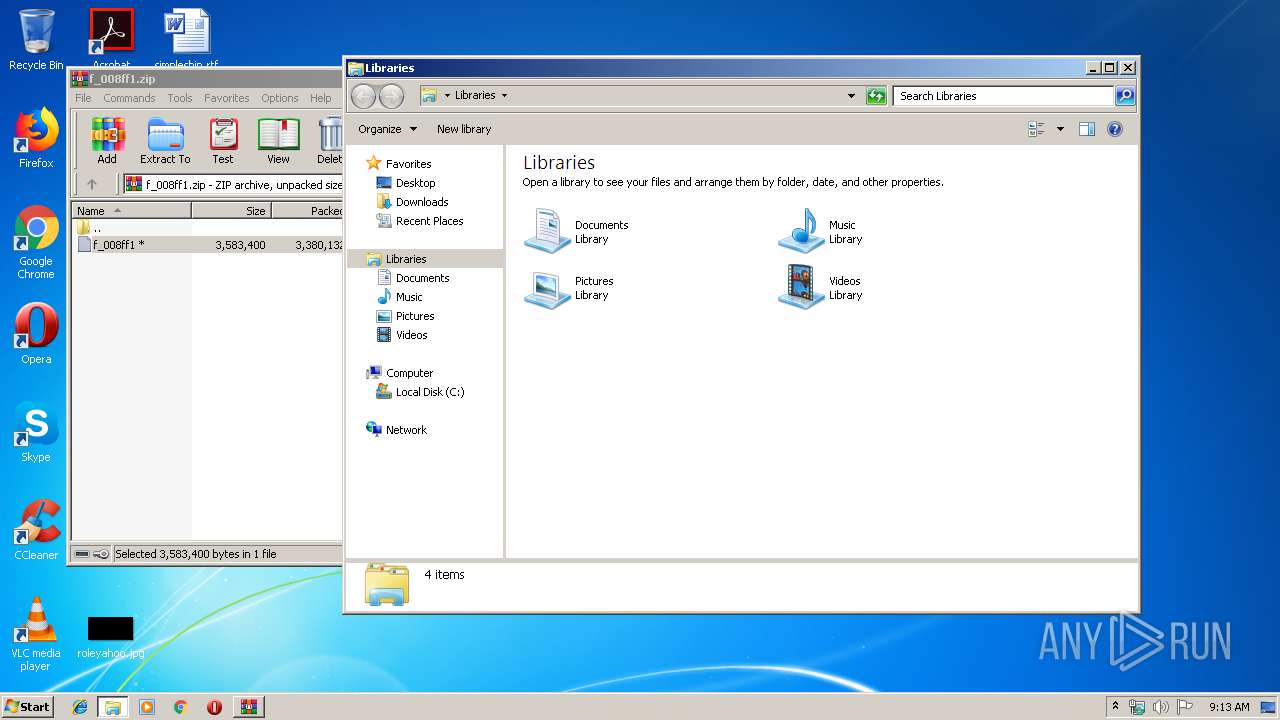
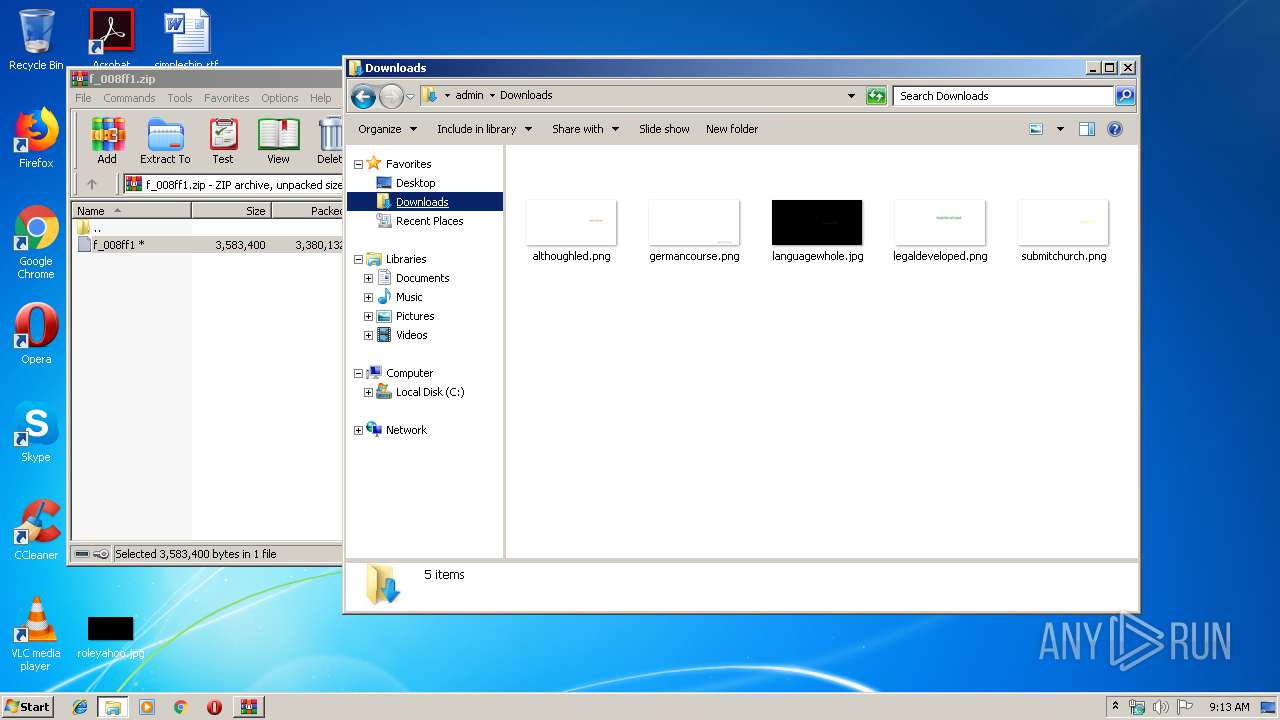
| 2588 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\f_008ff1.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2880 | "C:\Windows\System32\rundll32.exe" shell32.dll,Options_RunDLL 0 | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3000 | "C:\temprimon\PreSetup.exe" | C:\temprimon\PreSetup.exe | SoftwareRimonWin7.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Rimon Pre Installation File Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3600 | "C:\Users\admin\AppData\Local\Temp\is-J352J.tmp\f_008ff1.tmp" /SL5="$701B8,3147068,306176,C:\Users\admin\Desktop\f_008ff1.exe" /SPAWNWND=$601B4 /NOTIFYWND=$50170 | C:\Users\admin\AppData\Local\Temp\is-J352J.tmp\f_008ff1.tmp | f_008ff1.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3644 | "C:\Windows\System32\tskill.exe" nfserv | C:\Windows\System32\tskill.exe | — | RInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Remote Desktop Services End Process Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3664 | "C:\Users\admin\AppData\Local\Temp\is-G84N5.tmp\f_008ff1.tmp" /SL5="$50170,3147068,306176,C:\Users\admin\Desktop\f_008ff1.exe" | C:\Users\admin\AppData\Local\Temp\is-G84N5.tmp\f_008ff1.tmp | — | f_008ff1.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3788 | "C:\Windows\System32\tskill.exe" nfwd | C:\Windows\System32\tskill.exe | — | RInstall.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Remote Desktop Services End Process Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
938
Read events
866
Write events
65
Delete events
7
Modification events
| (PID) Process: | (2588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2588) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\f_008ff1.zip | |||
| (PID) Process: | (2588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2588) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3600) f_008ff1.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 100E000048F970637098D501 | |||
Executable files
32
Suspicious files
0
Text files
26
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2588 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2588.8989\f_008ff1 | — | |
MD5:— | SHA256:— | |||
| 3600 | f_008ff1.tmp | C:\Users\admin\AppData\Local\Temp\rimon\is-N87MS.tmp | — | |
MD5:— | SHA256:— | |||
| 3600 | f_008ff1.tmp | C:\Users\admin\AppData\Local\Temp\rimon\is-5FV3H.tmp | — | |
MD5:— | SHA256:— | |||
| 3600 | f_008ff1.tmp | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\SoftwareRimon\SoftwareRimon.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3992 | f_008ff1.exe | C:\Users\admin\AppData\Local\Temp\is-J352J.tmp\f_008ff1.tmp | executable | |
MD5:— | SHA256:— | |||
| 492 | SoftwareRimonWin7.exe | C:\temprimon\nfapi_64.dll | executable | |
MD5:— | SHA256:— | |||
| 492 | SoftwareRimonWin7.exe | C:\temprimon\nfapinet_64.dll | executable | |
MD5:— | SHA256:— | |||
| 492 | SoftwareRimonWin7.exe | C:\temprimon\LangSRV.xml | xml | |
MD5:— | SHA256:— | |||
| 3600 | f_008ff1.tmp | C:\Users\admin\AppData\Local\Temp\rimon\SoftwareRimonWin8.exe | executable | |
MD5:— | SHA256:— | |||
| 492 | SoftwareRimonWin7.exe | C:\temprimon\LicenseHE-IL.htm | html | |
MD5:6B7970A5517D1AF9FC73B3A121916AFC | SHA256:CB5417BB01FF491507EBD9429E48A2F01648A5B877642FE98FF514A8D756E44B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
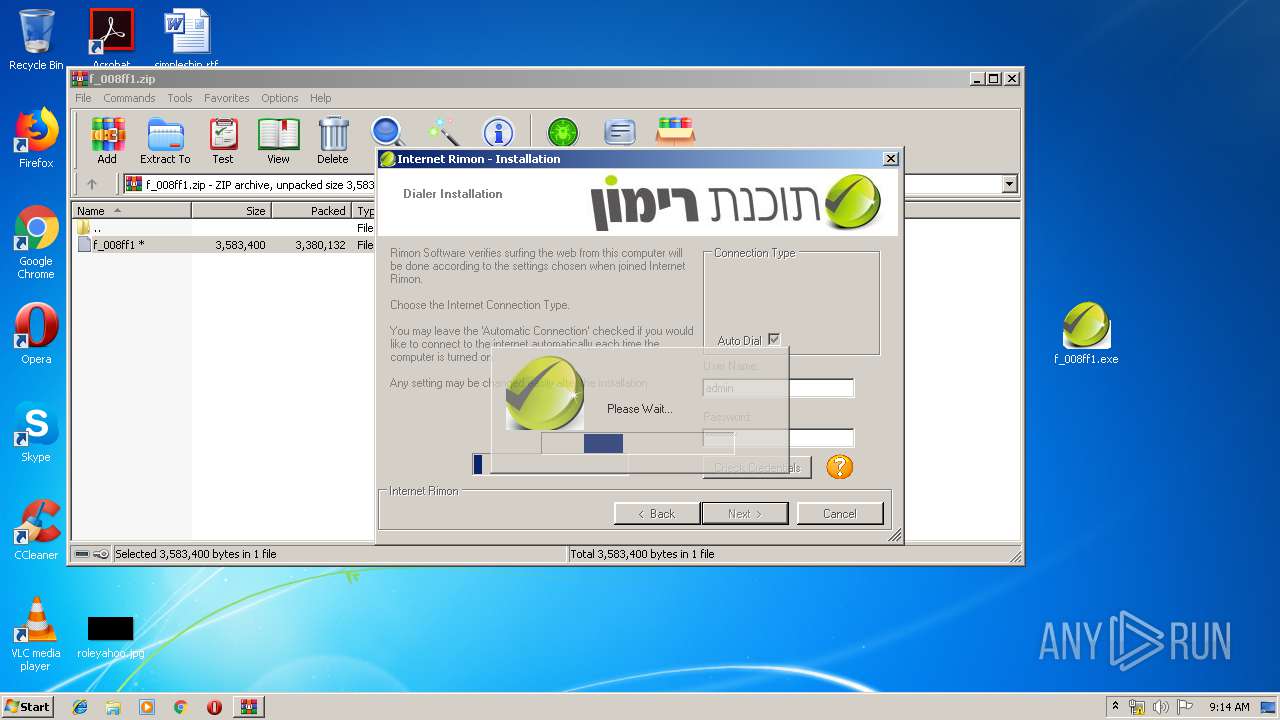
3928 | RInstall.exe | GET | 200 | 213.151.33.8:80 | http://service.neto.net.il/tochnanew/RimonConfig | IL | text | 6.45 Kb | unknown |
3928 | RInstall.exe | POST | 200 | 213.151.33.8:80 | http://213.151.33.8/tochnanew/bup?username=adminapi&password=admin | IL | text | 49 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3928 | RInstall.exe | 213.151.33.8:80 | service.neto.net.il | Internet Rimon LTD | IL | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
5.126.76.212.in-addr.arpa |
| unknown |
portal.tom.net.il |
| unknown |
service.neto.net.il |
| unknown |