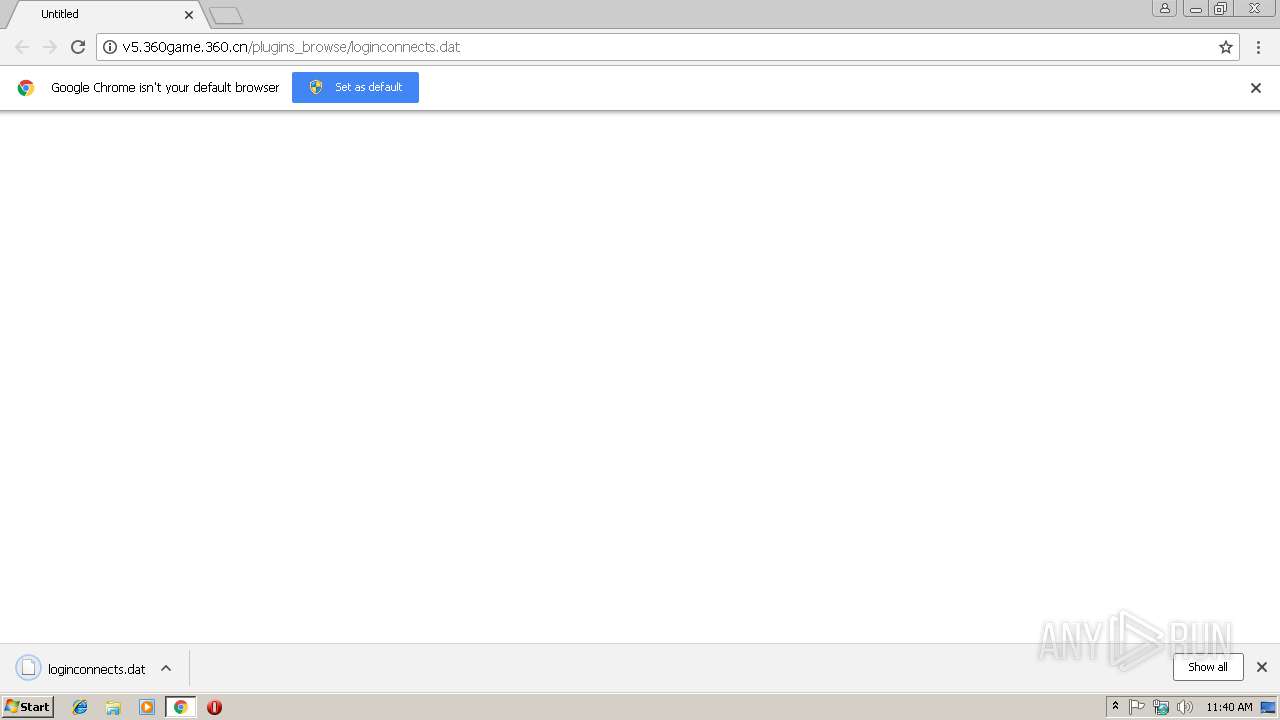
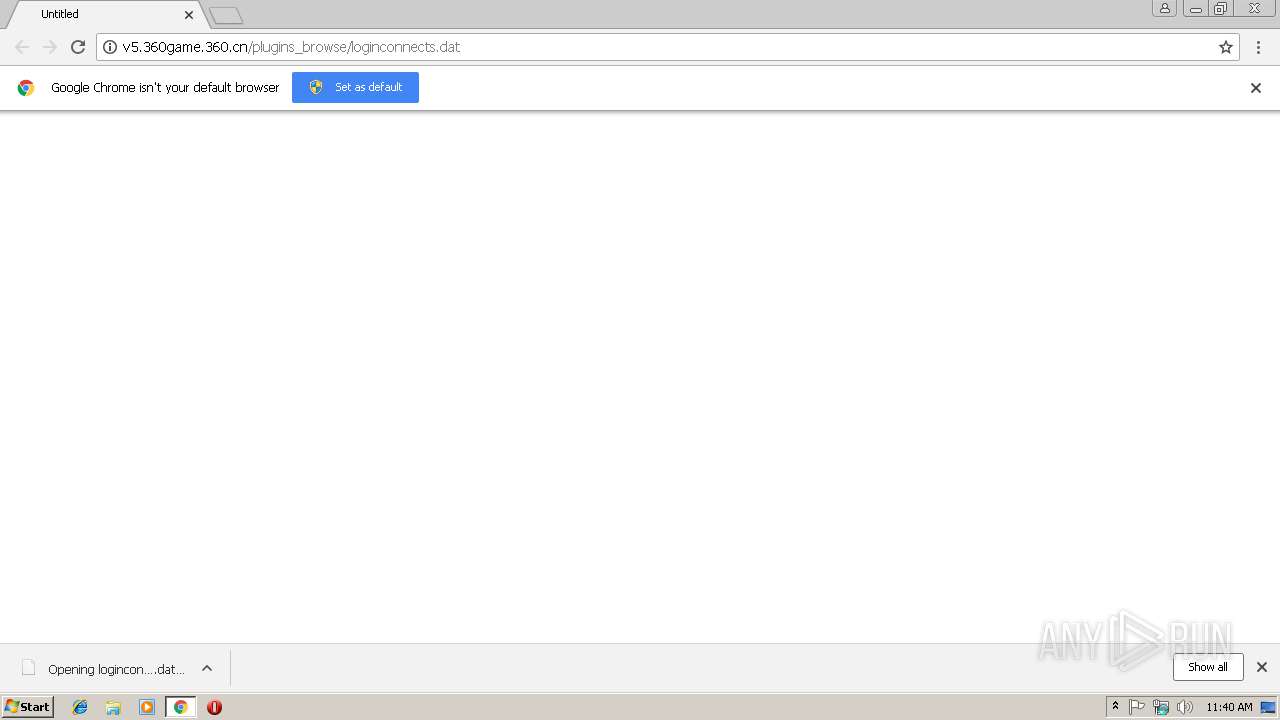
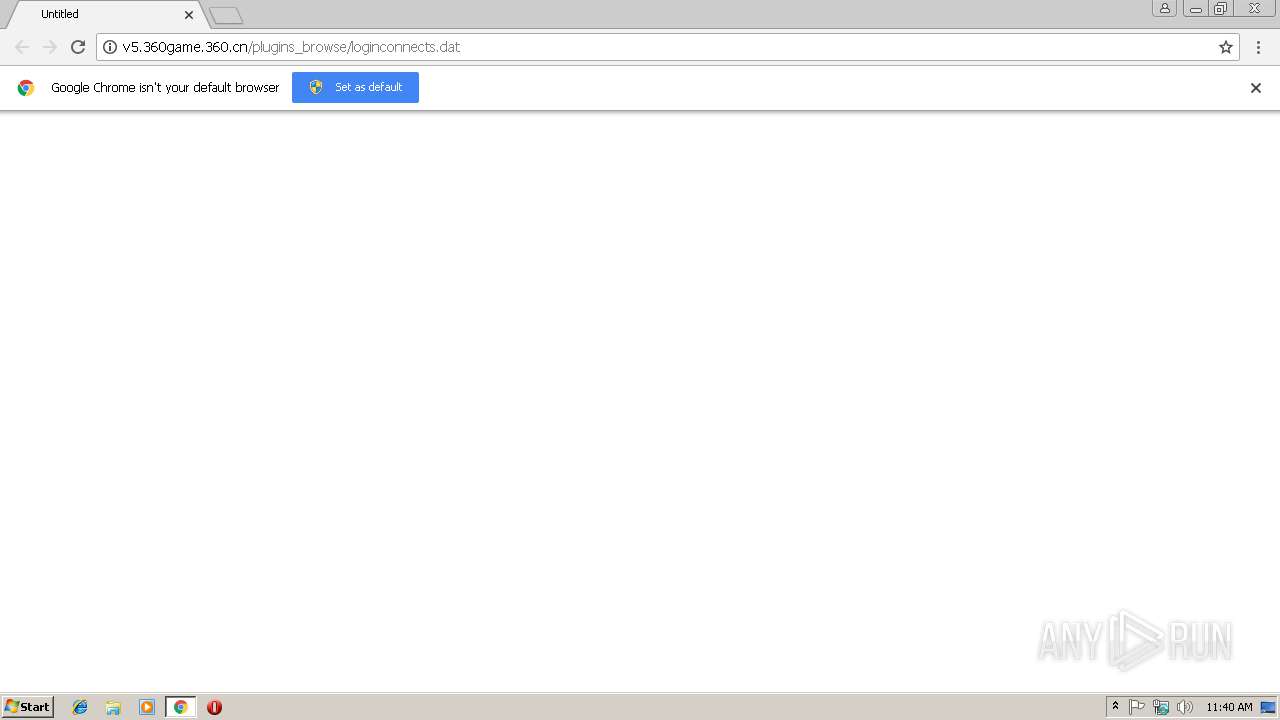
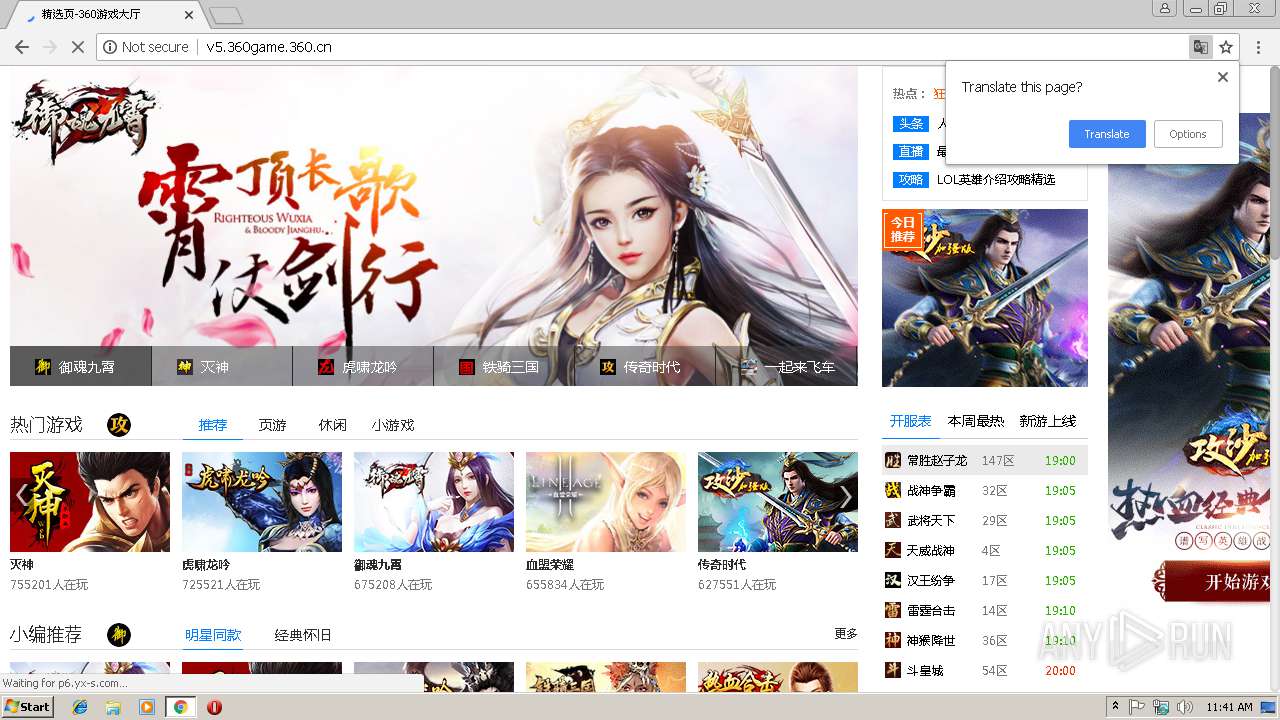
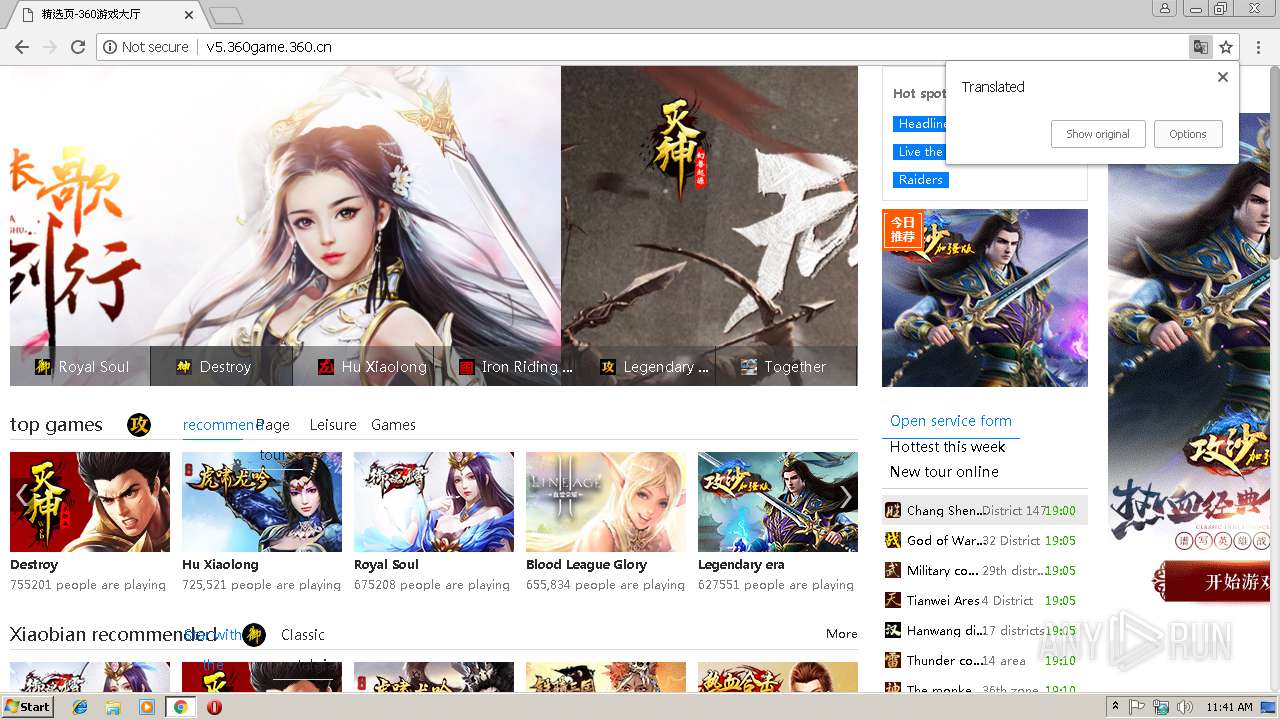
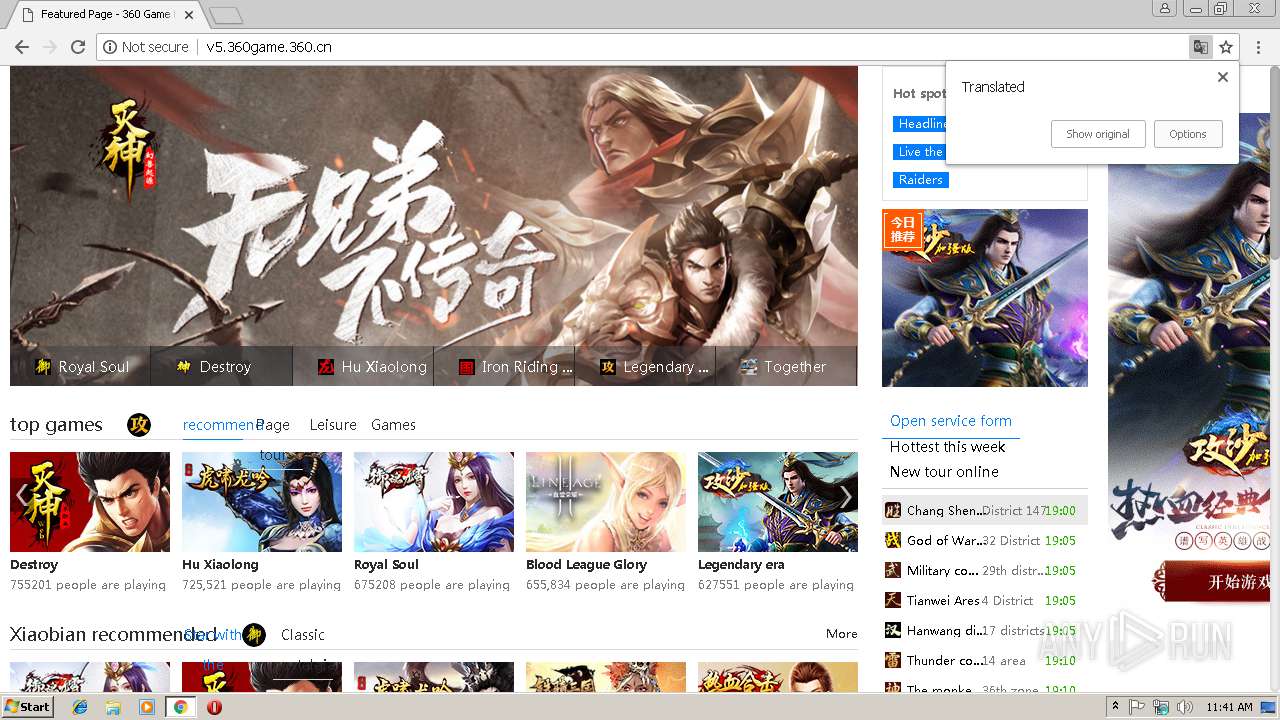
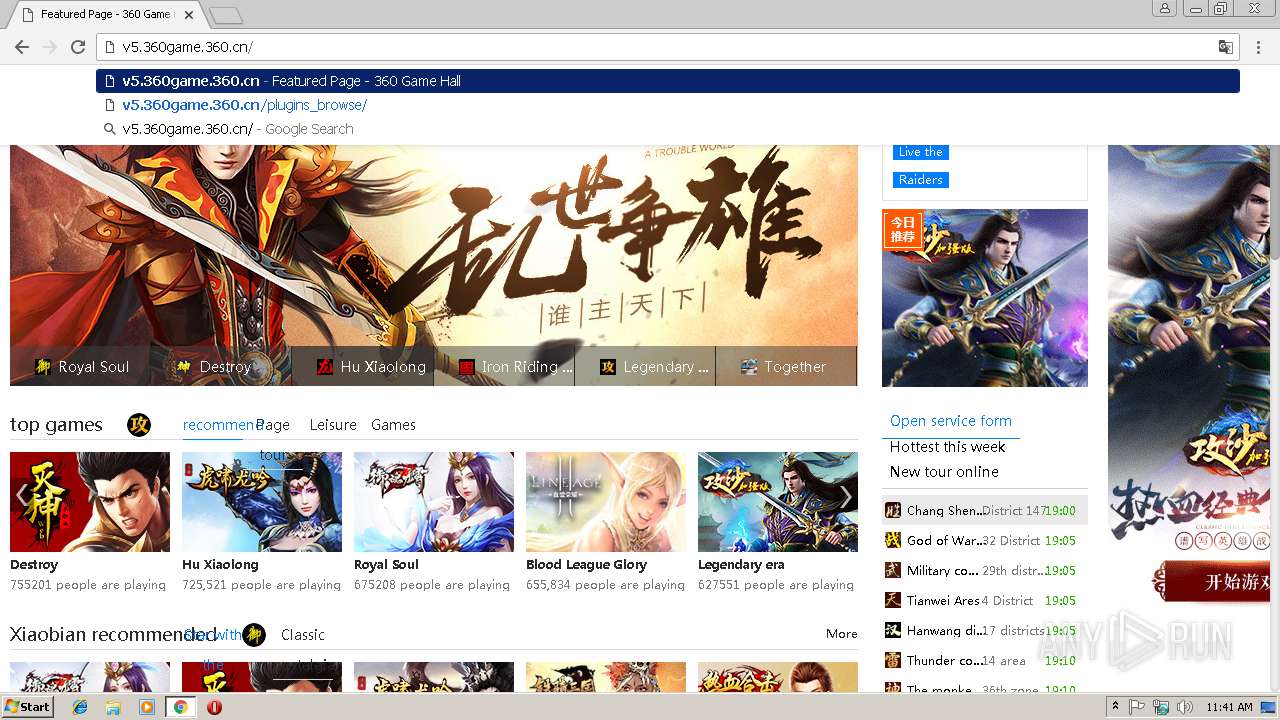
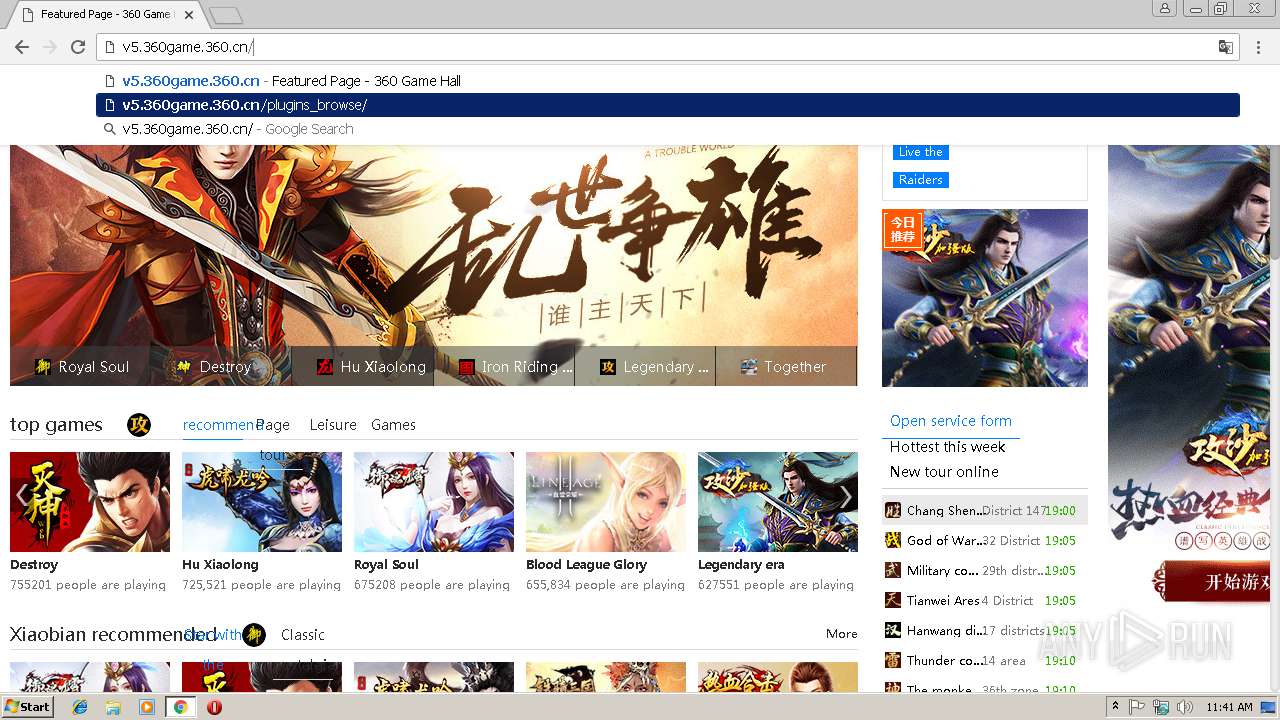
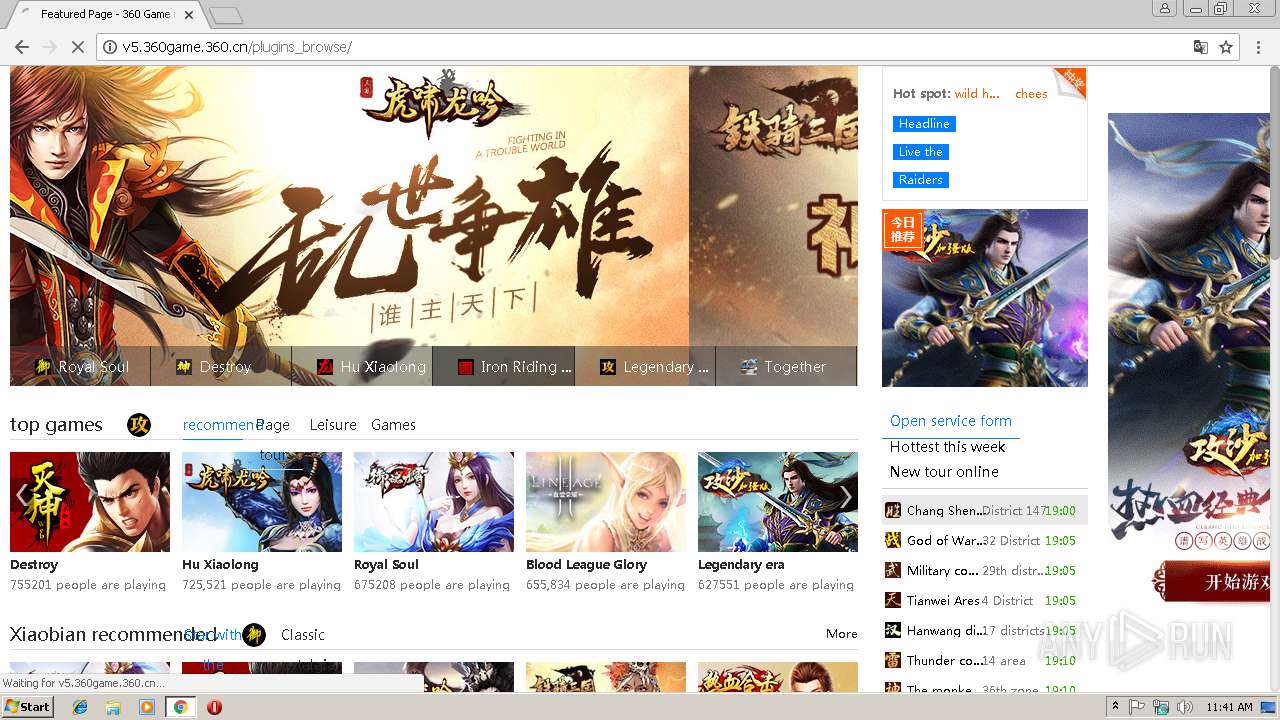
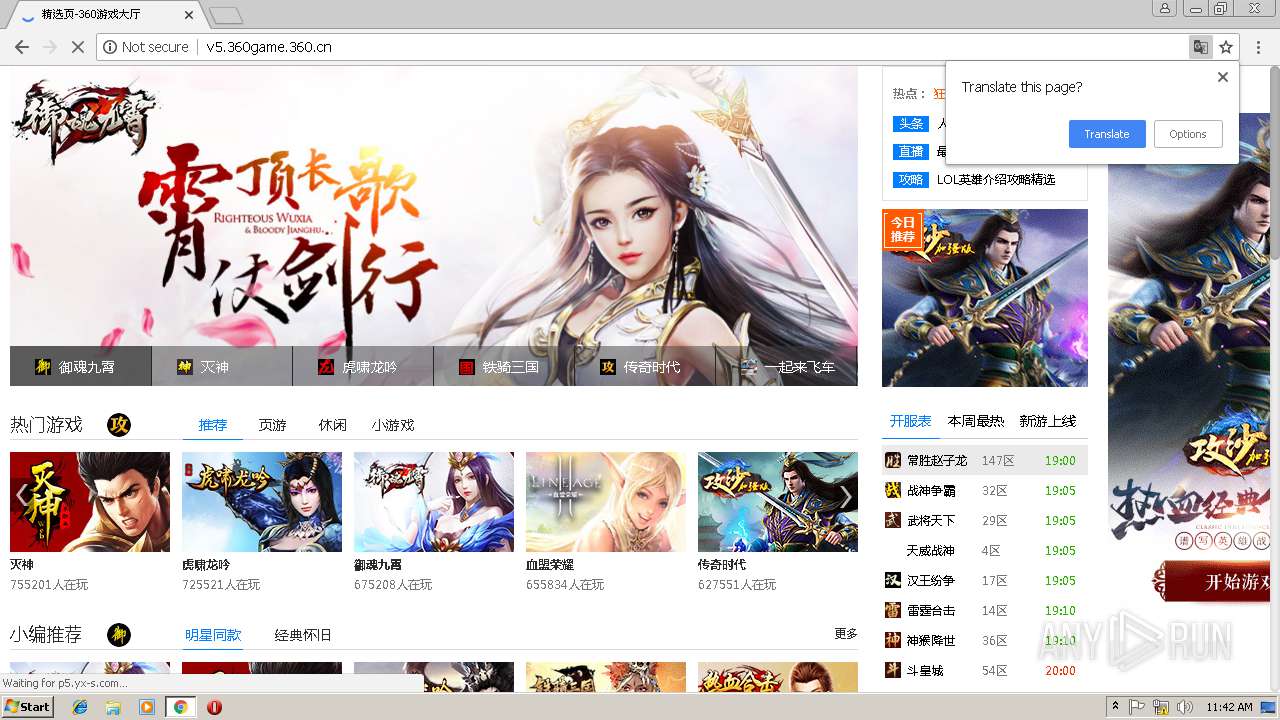
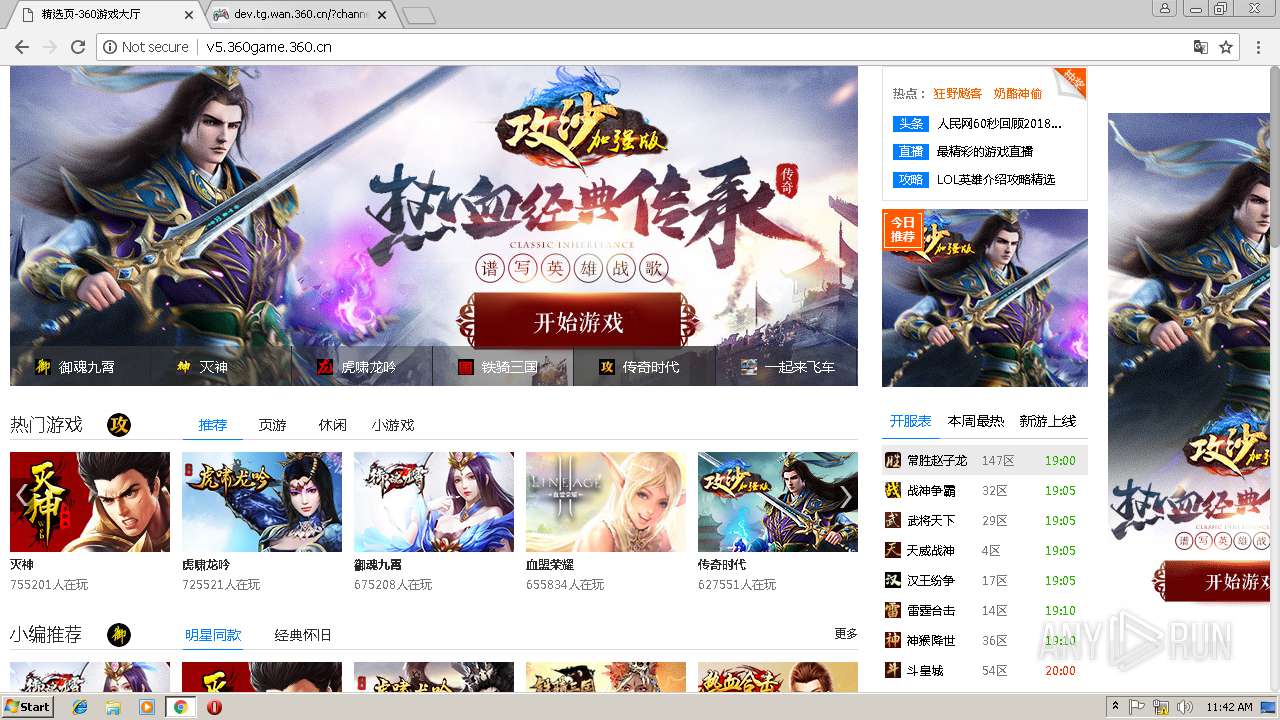
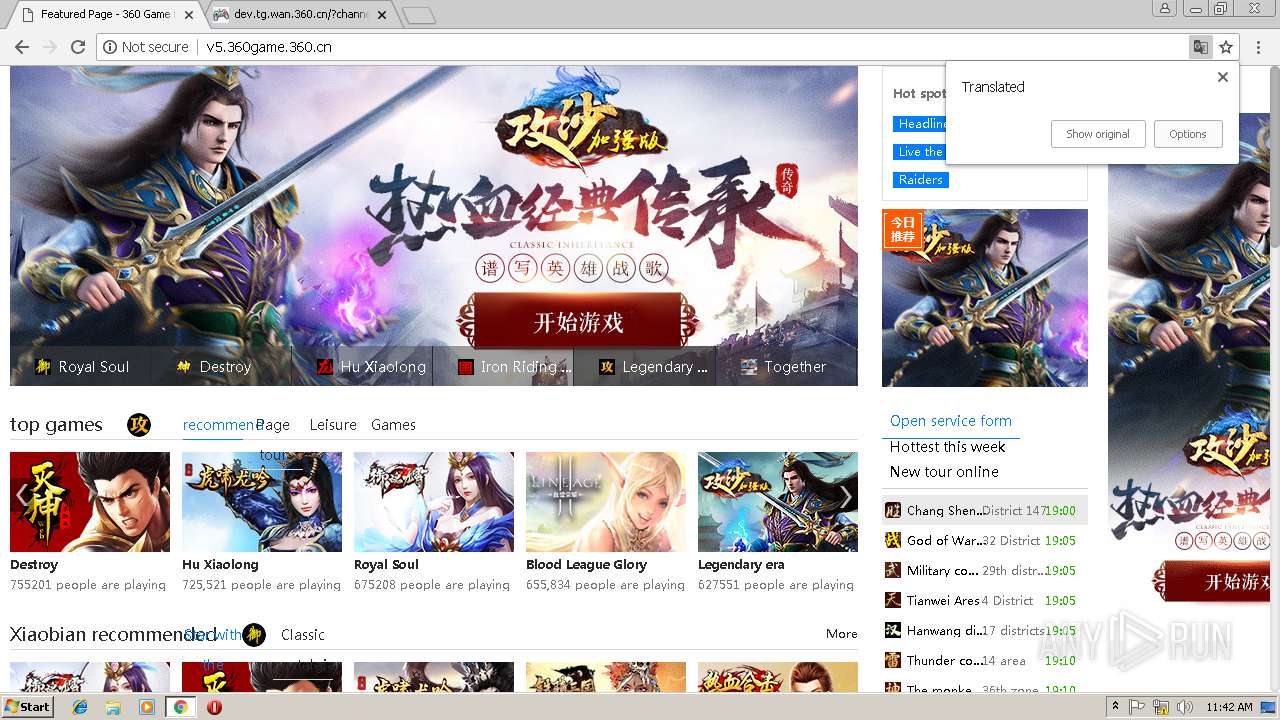
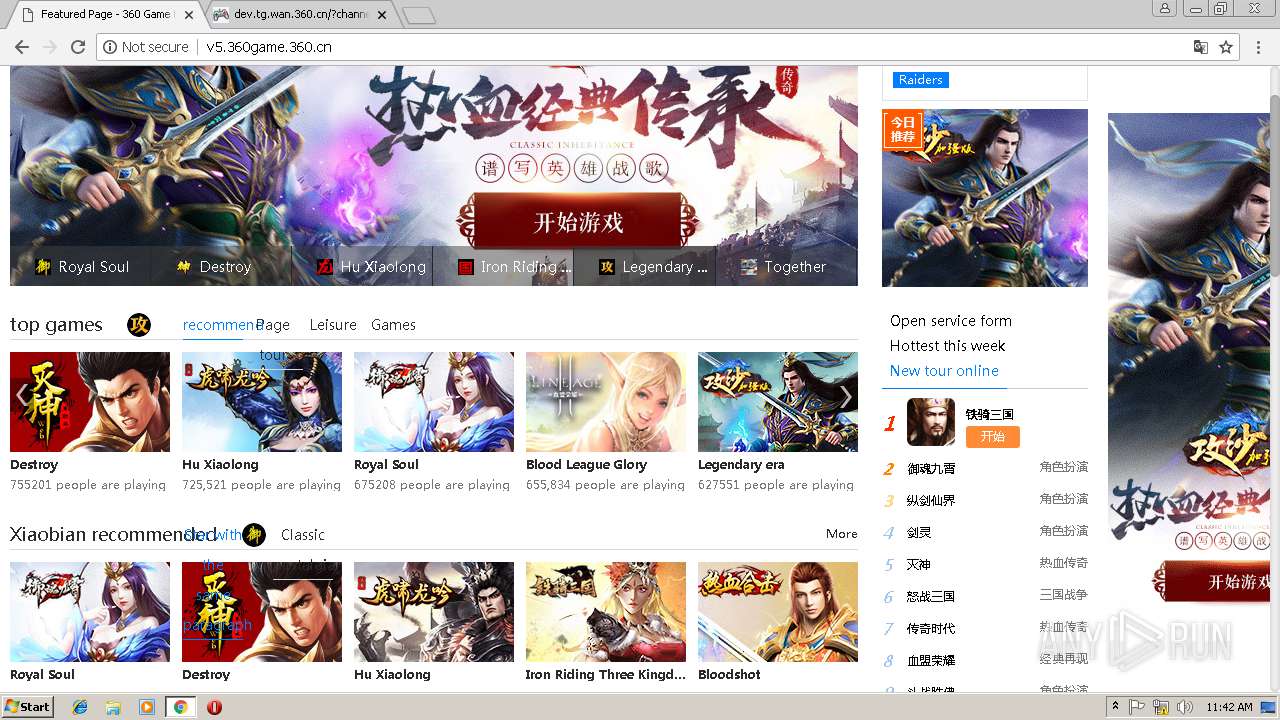
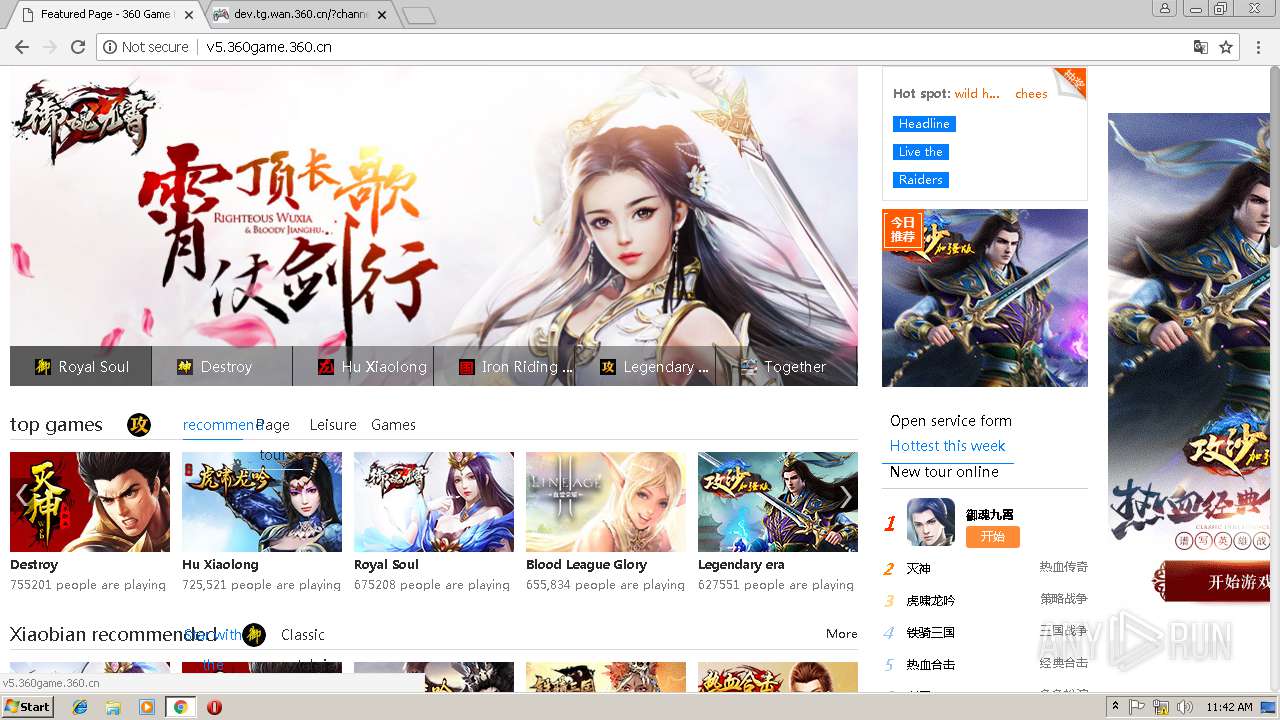
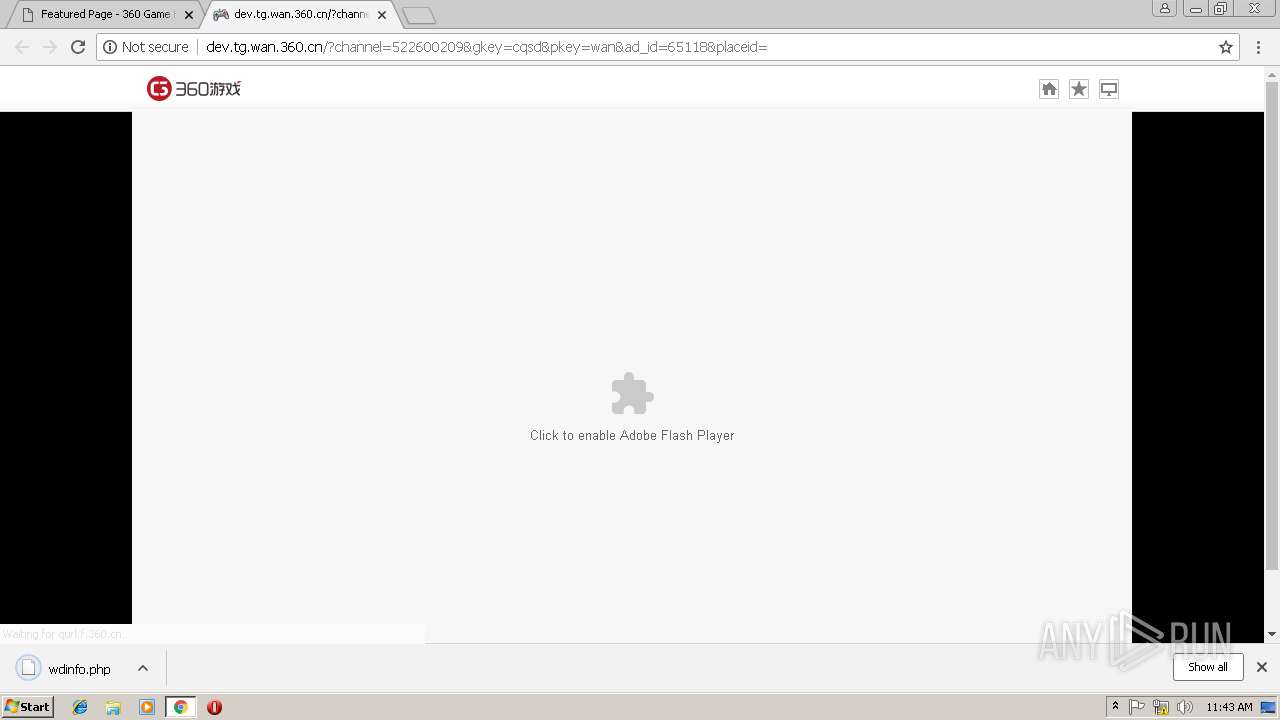
| URL: | http://v5.360game.360.cn/plugins_browse/loginconnects.dat |
| Full analysis: | https://app.any.run/tasks/c1404ce1-1d90-48fe-82d9-b847cd8ebdbc |
| Verdict: | Malicious activity |
| Analysis date: | January 07, 2019, 11:40:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 64476577AEB60E1B24396EC3F197C4BB |
| SHA1: | 095A479838E9A4C682BA6B12A4593B0FE6F979C0 |
| SHA256: | 6E5469198EA635E156ED0BCFE448F368D22285A58D297CD6F496DC6EDA0A3407 |
| SSDEEP: | 3:N1KIQLDMW1RdK9HZqM/jV:CISXkqsV |
MALICIOUS
No malicious indicators.SUSPICIOUS
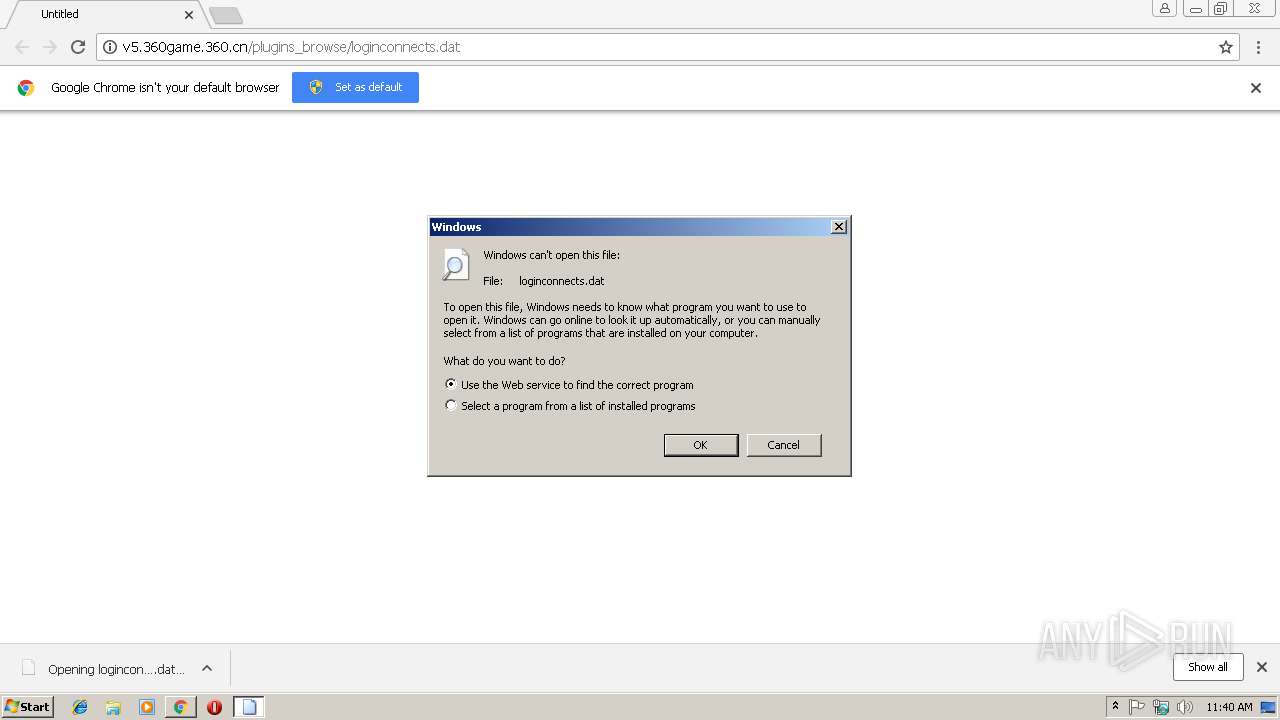
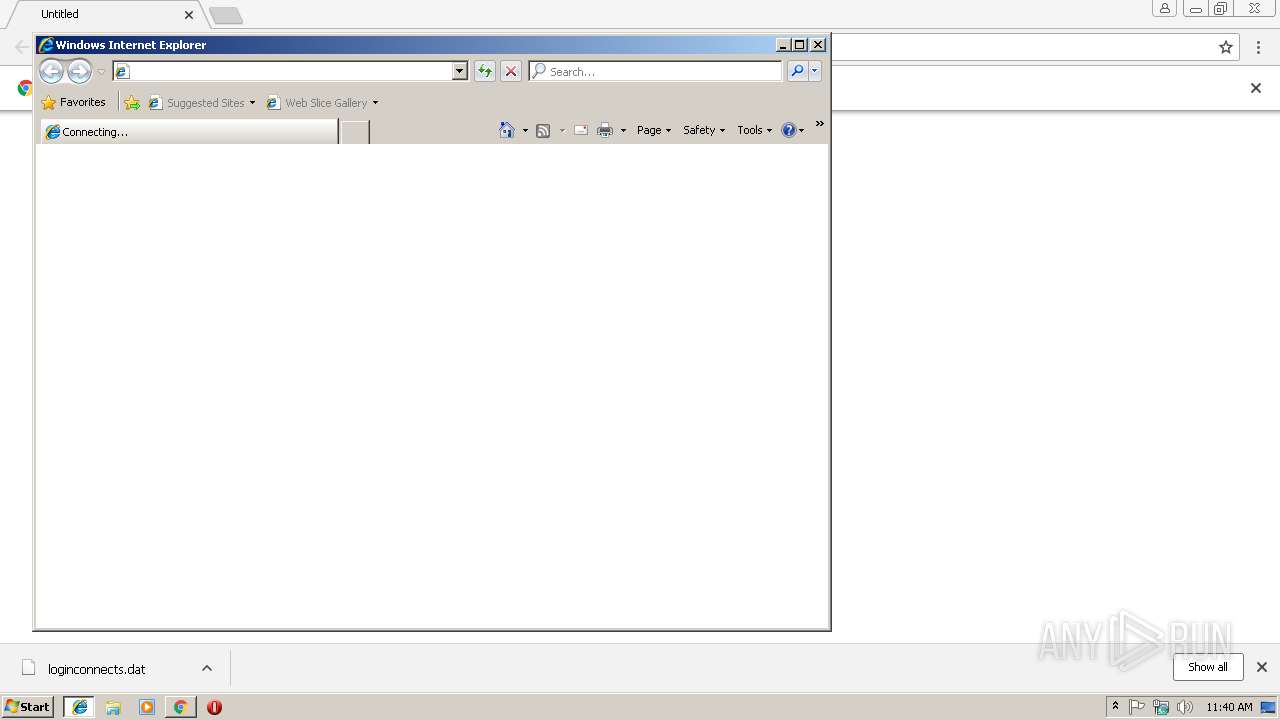
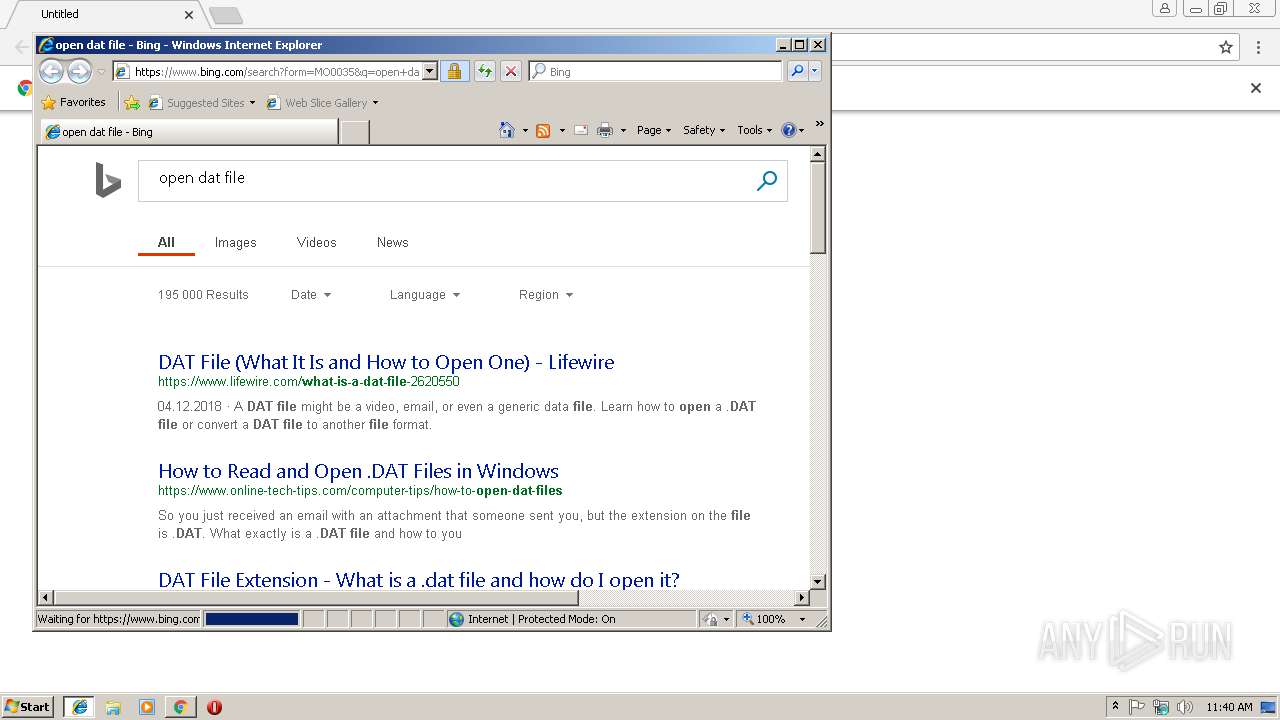
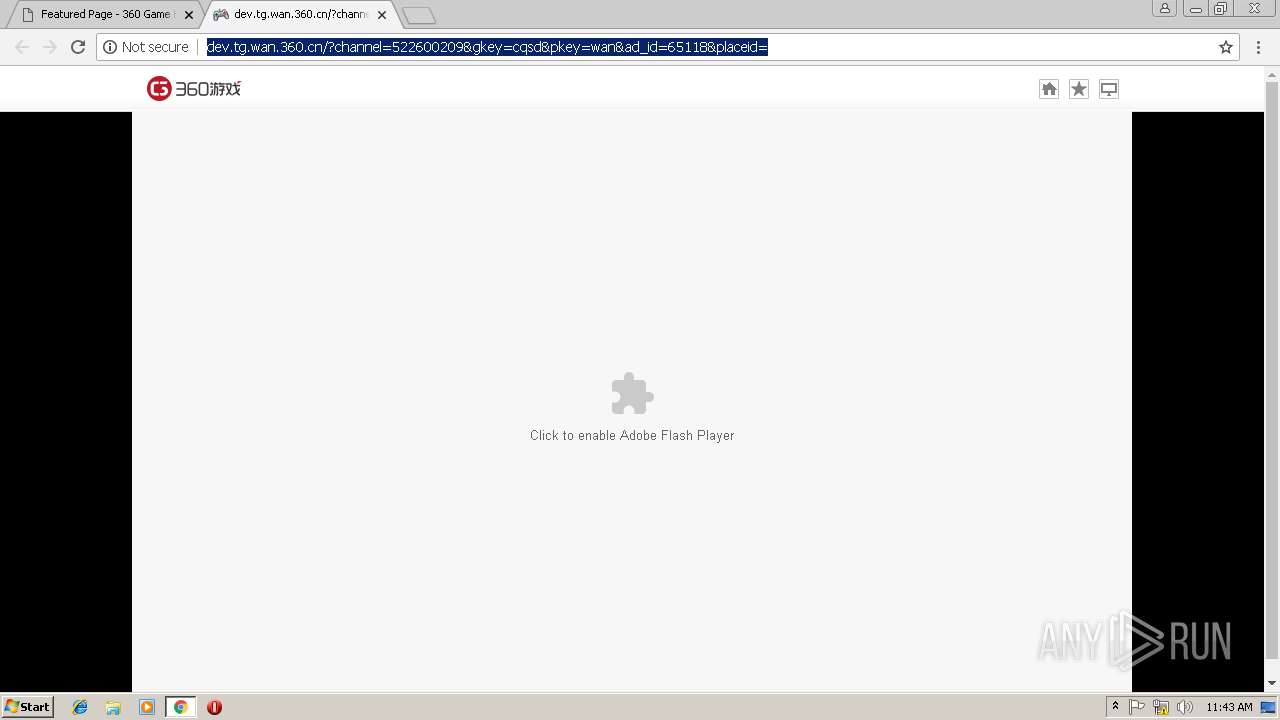
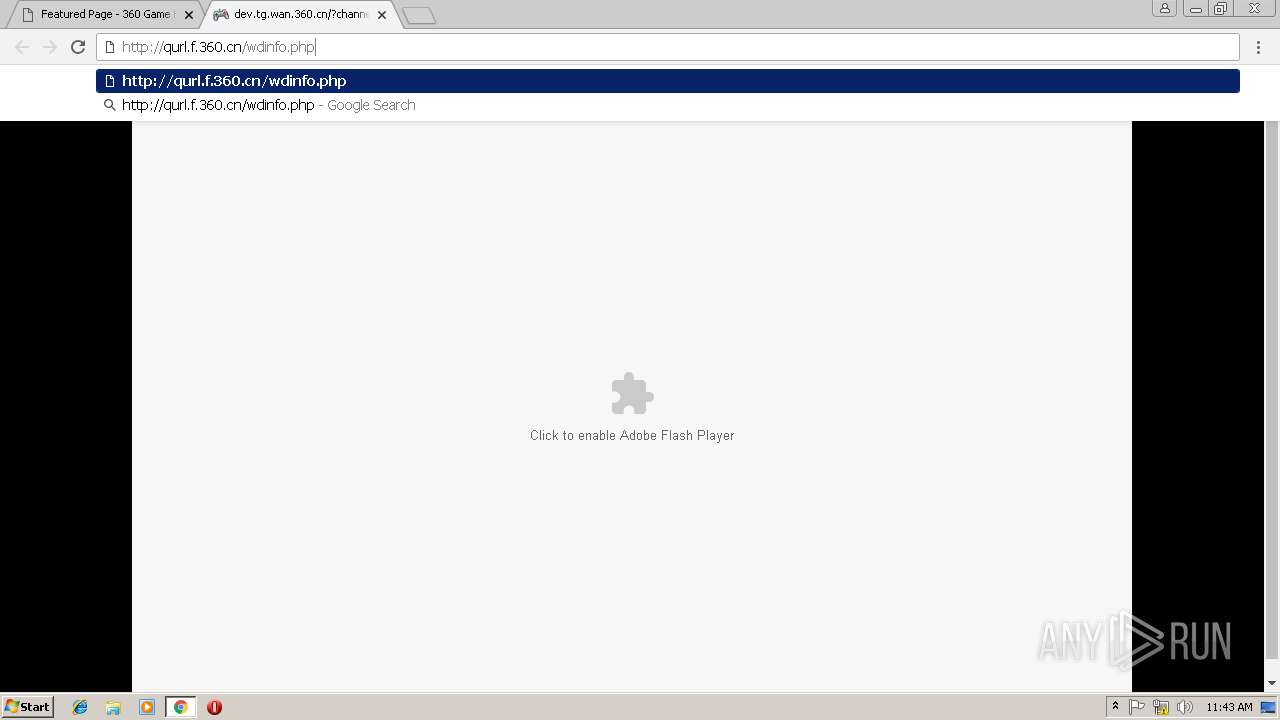
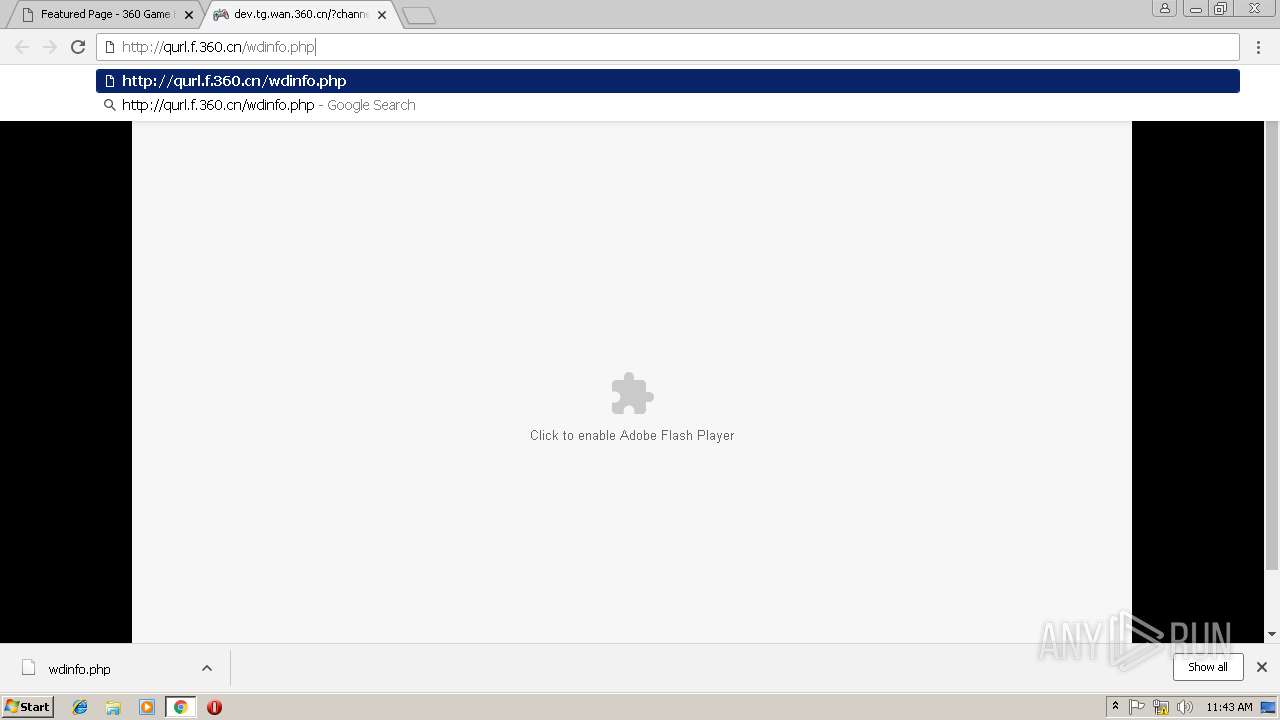
Starts Internet Explorer
- rundll32.exe (PID: 2332)
Uses RUNDLL32.EXE to load library
- chrome.exe (PID: 3040)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3040)
- iexplore.exe (PID: 3960)
Application launched itself
- chrome.exe (PID: 3040)
- iexplore.exe (PID: 3960)
Creates files in the user directory
- chrome.exe (PID: 3040)
- iexplore.exe (PID: 3048)
Reads Internet Cache Settings
- iexplore.exe (PID: 3048)
- chrome.exe (PID: 3040)
- iexplore.exe (PID: 3960)
Changes settings of System certificates
- iexplore.exe (PID: 3960)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3960)
Changes internet zones settings
- iexplore.exe (PID: 3960)
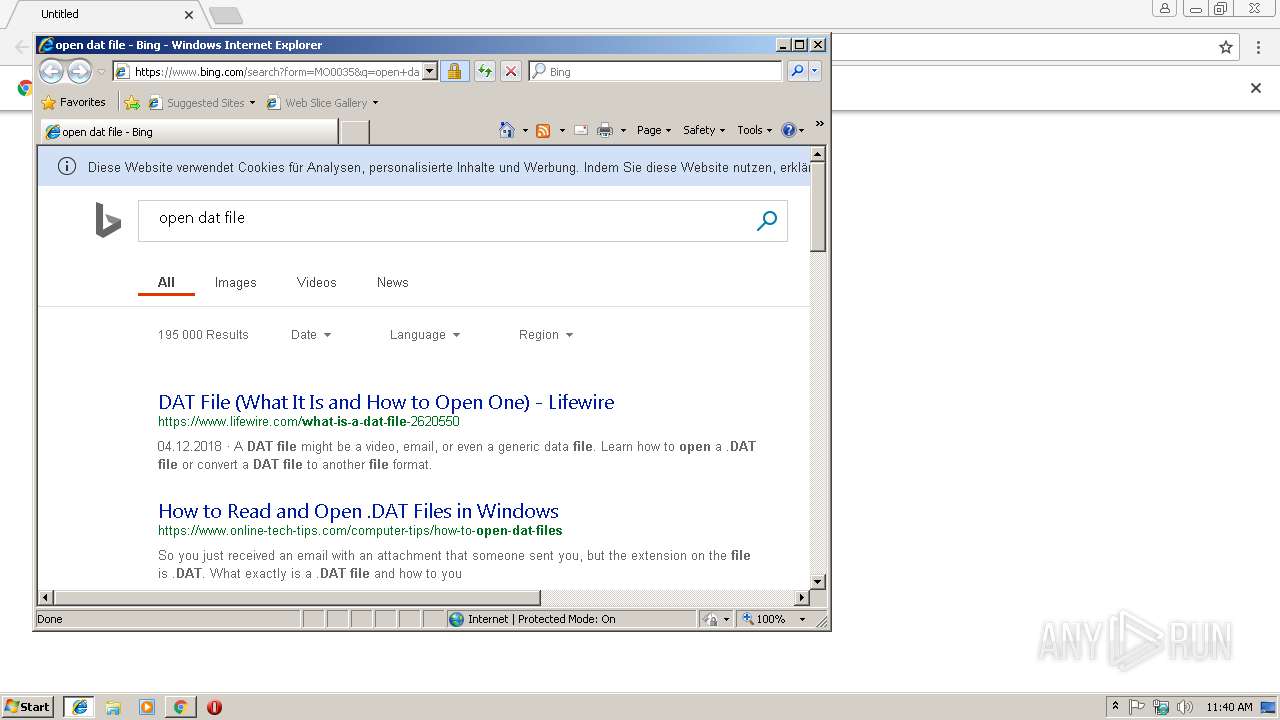
Reads internet explorer settings
- iexplore.exe (PID: 3048)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
45
Monitored processes
13
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=936,5487067942639420157,11828165495858623895,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=A9E38CEC3FD2AF82FA5EBE3E4975262F --mojo-platform-channel-handle=976 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,5487067942639420157,11828165495858623895,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=F225D58887B4574B2BABC308D10430B3 --mojo-platform-channel-handle=4244 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2332 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Downloads\loginconnects.dat | C:\Windows\system32\rundll32.exe | — | chrome.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2616 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,5487067942639420157,11828165495858623895,131072 --enable-features=PasswordImport --service-pipe-token=3B7461A966AFAF10C12EB132B02C3B3A --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3B7461A966AFAF10C12EB132B02C3B3A --renderer-client-id=4 --mojo-platform-channel-handle=1904 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,5487067942639420157,11828165495858623895,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=639204DFBEB0E377ED8B99AA3E3193D6 --mojo-platform-channel-handle=948 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3008 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3044 --on-initialized-event-handle=304 --parent-handle=308 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://v5.360game.360.cn/plugins_browse/loginconnects.dat | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3048 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3960 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=936,5487067942639420157,11828165495858623895,131072 --enable-features=PasswordImport --service-pipe-token=B4F513B91B1F342F1507E0ACAFD0C026 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B4F513B91B1F342F1507E0ACAFD0C026 --renderer-client-id=3 --mojo-platform-channel-handle=2144 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=936,5487067942639420157,11828165495858623895,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=029D547F997498B9758AA142039D7E3A --mojo-platform-channel-handle=1136 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 336
Read events
1 201
Write events
126
Delete events
9
Modification events
| (PID) Process: | (3008) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3040-13191334833500375 |
Value: 259 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3516-13180984670829101 |
Value: 0 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3040-13191334833500375 |
Value: 259 | |||
| (PID) Process: | (3040) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
0
Suspicious files
29
Text files
217
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\aab4a202-87b0-413f-a4e6-22869ff219f8.tmp | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\3a70d0e0-474b-4474-bb58-a8b0b1498f4d.tmp | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\Downloads\000a0204-6967-4007-9e60-f225ce66265a.tmp | — | |
MD5:— | SHA256:— | |||
| 3040 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\e96a2f83-6657-4daa-96bb-173313c723e3.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
280
TCP/UDP connections
124
DNS requests
106
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
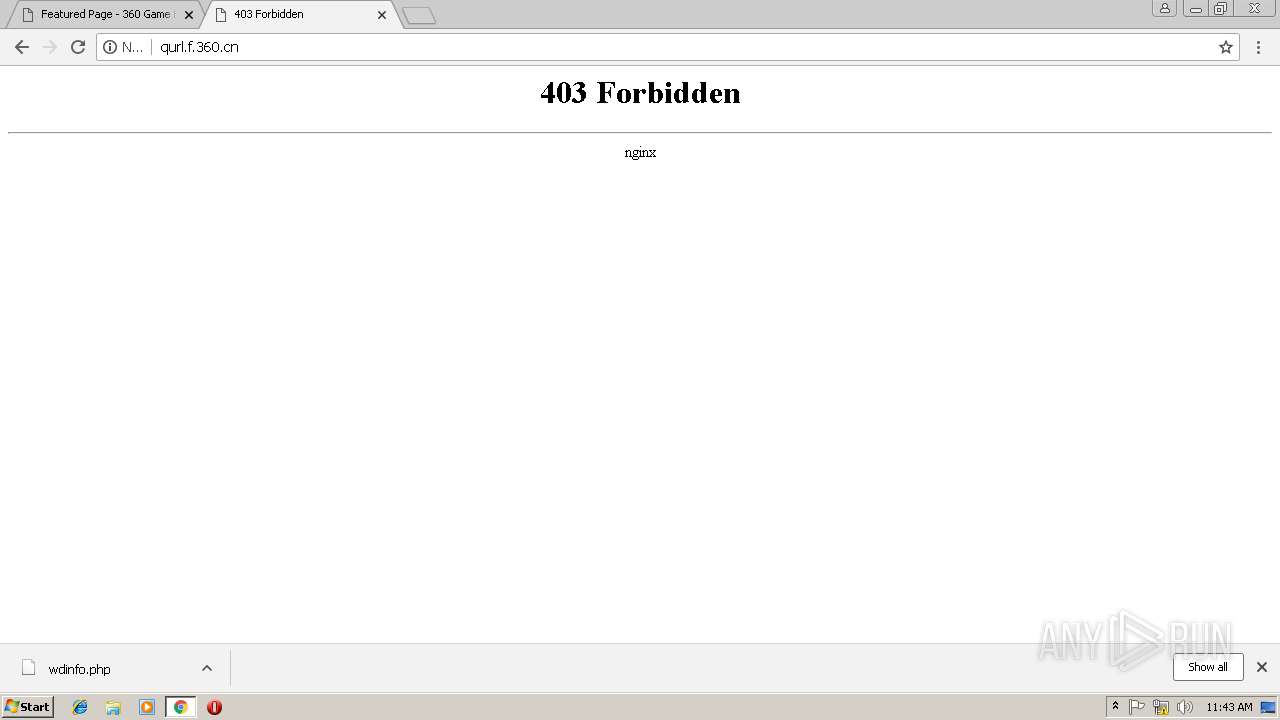
3048 | iexplore.exe | GET | 302 | 23.51.118.23:80 | http://go.microsoft.com/fwlink/?LinkId=57426&Ext=dat | NL | — | — | whitelisted |
3040 | chrome.exe | GET | — | 36.110.236.217:80 | http://v5.360game.360.cn/favicon.ico | CN | — | — | unknown |
3048 | iexplore.exe | GET | 301 | 2.16.186.16:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=dat | unknown | — | — | whitelisted |
3040 | chrome.exe | GET | 200 | 13.32.222.119:80 | http://p0.qhimg.com/t018e756e3a96335cef.jpg | US | image | 1.09 Kb | whitelisted |
3040 | chrome.exe | GET | 200 | 163.171.128.148:80 | http://p6.yx-s.com/t01a576717eefae0cf1.jpg | US | image | 169 Kb | malicious |
3040 | chrome.exe | GET | 200 | 13.32.222.119:80 | http://p0.qhimg.com/t01caf4fb2996c27091.jpg | US | image | 5.89 Kb | whitelisted |
3040 | chrome.exe | GET | 200 | 163.171.128.148:80 | http://p6.yx-s.com/t017010bdbdc774946a.jpg | US | image | 160 Kb | malicious |
3040 | chrome.exe | GET | 200 | 163.171.128.148:80 | http://p8.yx-s.com/t01768bc0dac4872dd5.jpg | US | image | 9.30 Kb | malicious |
3040 | chrome.exe | GET | 200 | 163.171.128.148:80 | http://p6.yx-s.com/t01e01d9fb679aa3fa1.jpg | US | image | 697 b | malicious |
3040 | chrome.exe | GET | 200 | 163.171.128.148:80 | http://p6.yx-s.com/t019f5a60171e2bfe6c.jpg | US | image | 779 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3960 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3048 | iexplore.exe | 23.51.118.23:80 | go.microsoft.com | Akamai Technologies, Inc. | NL | whitelisted |
3048 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3960 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3040 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3040 | chrome.exe | 216.58.207.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3040 | chrome.exe | 216.58.207.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3040 | chrome.exe | 172.217.22.35:443 | www.google.at | Google Inc. | US | whitelisted |
3040 | chrome.exe | 13.32.222.63:80 | s3.qhres.com | Amazon.com, Inc. | US | whitelisted |
3040 | chrome.exe | 163.171.128.148:80 | p8.yx-s.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
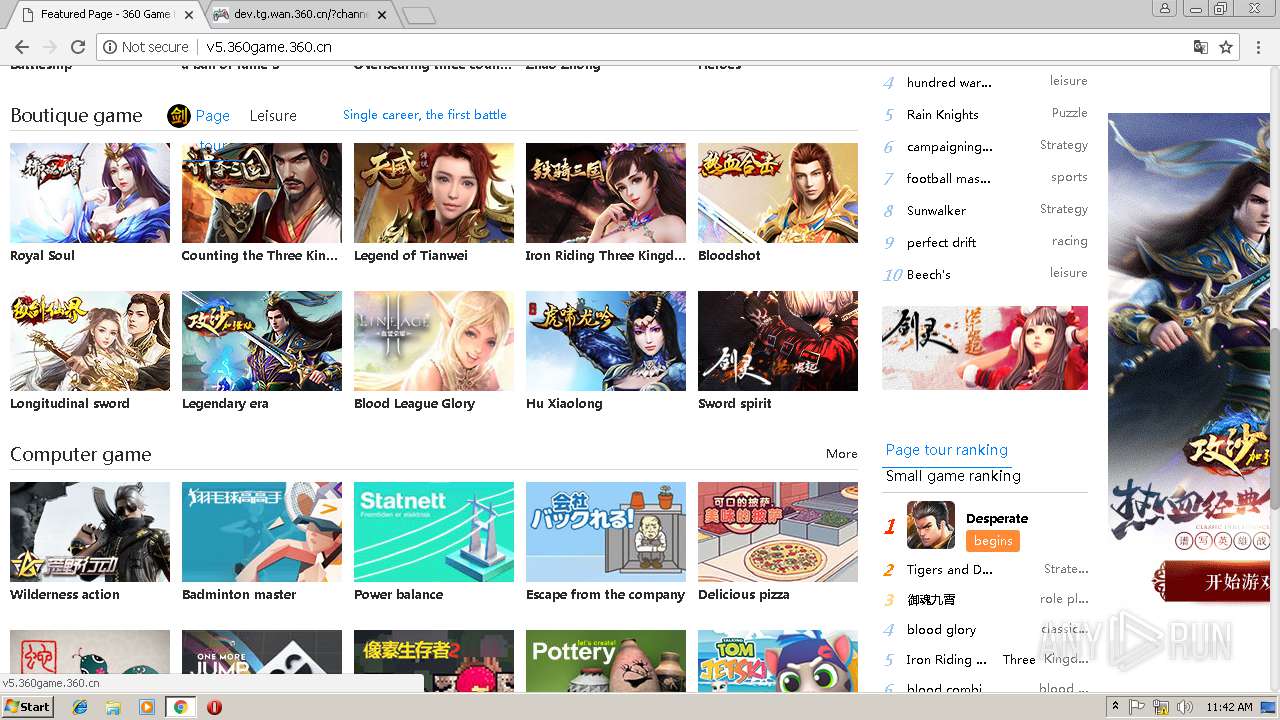
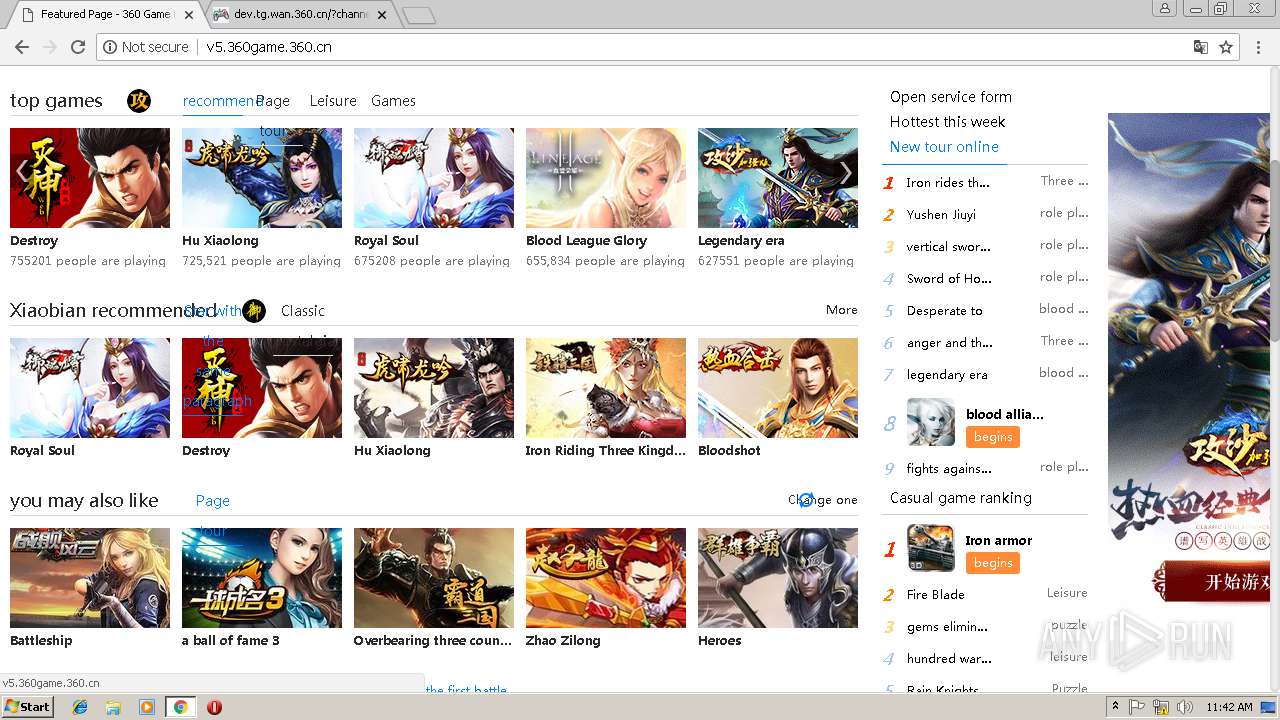
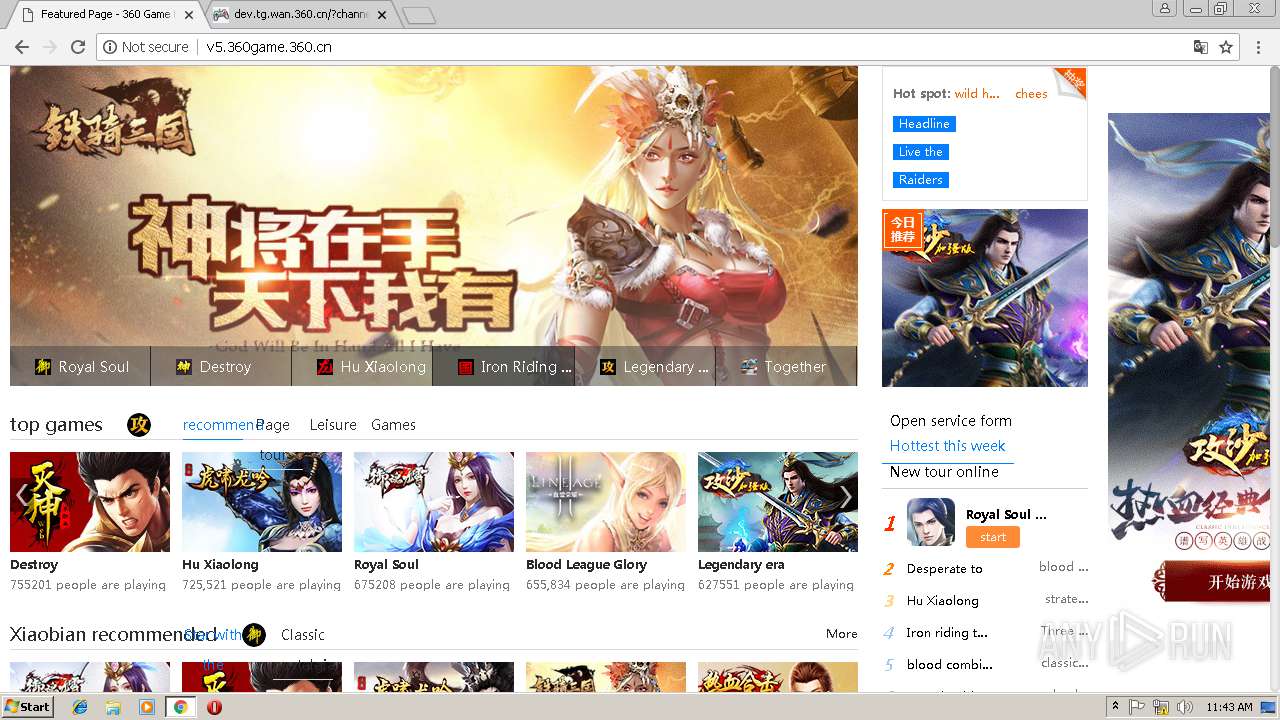
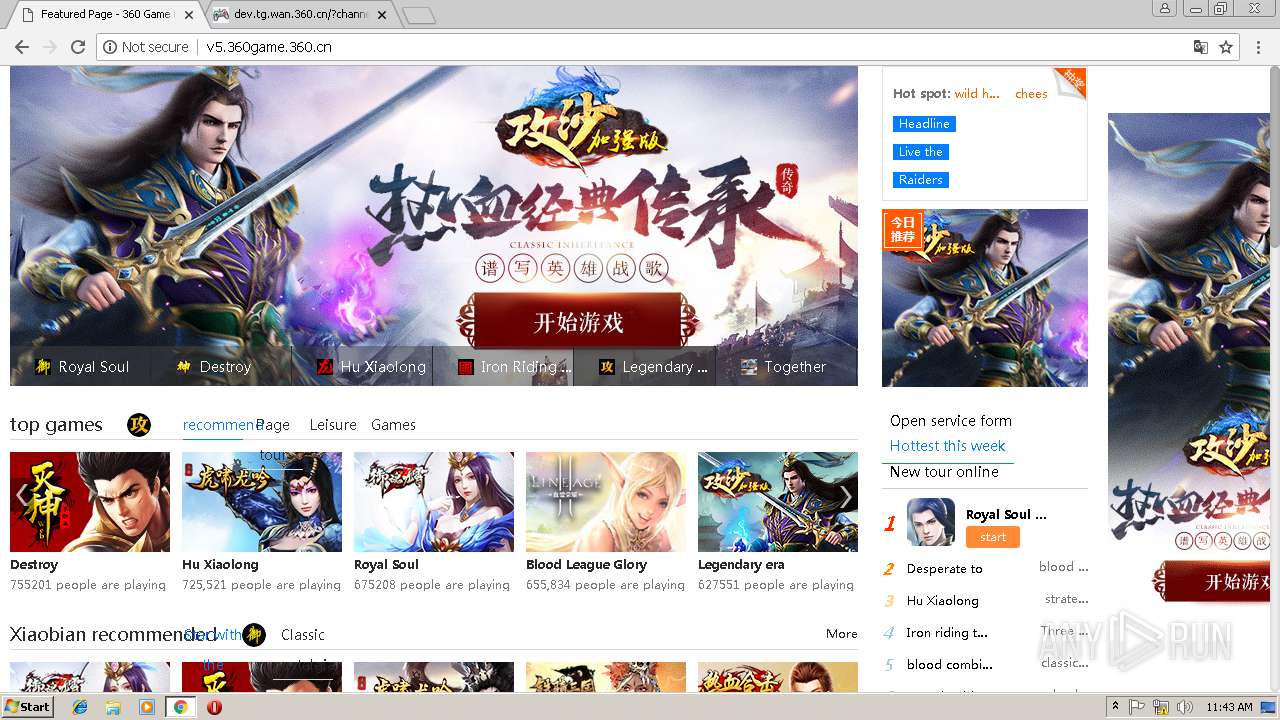
v5.360game.360.cn |
| unknown |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
shell.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3040 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |