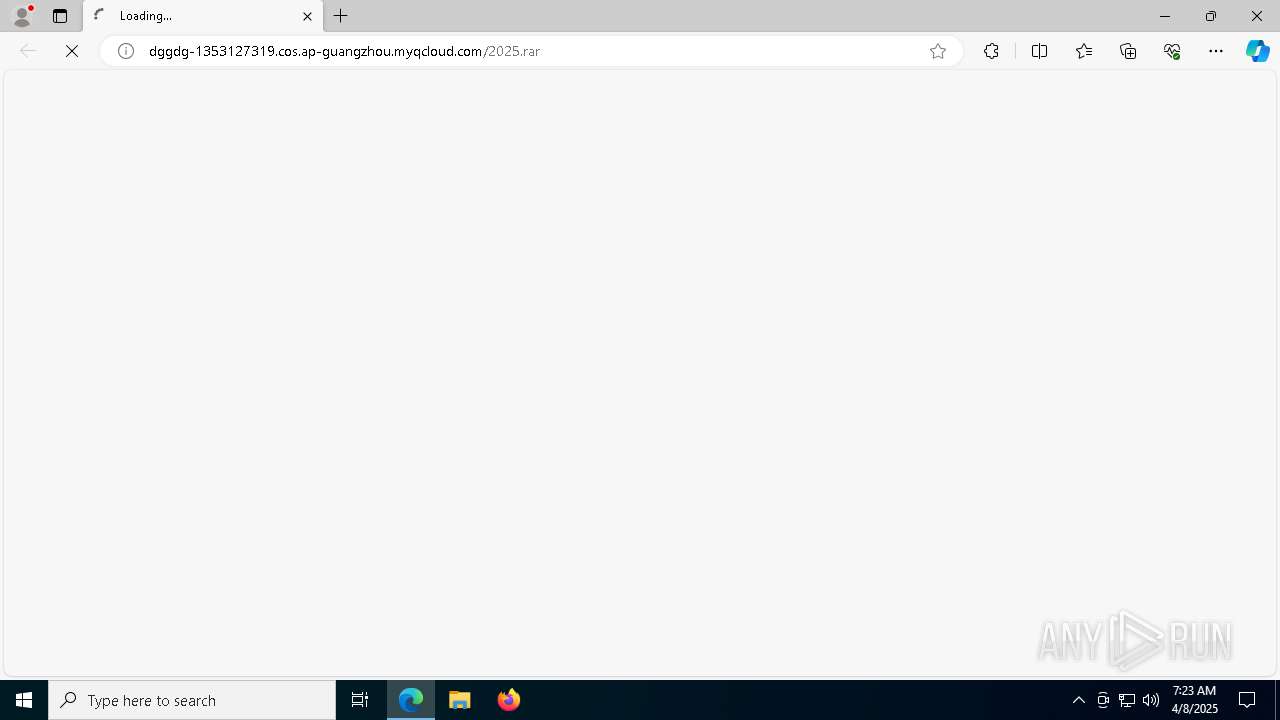
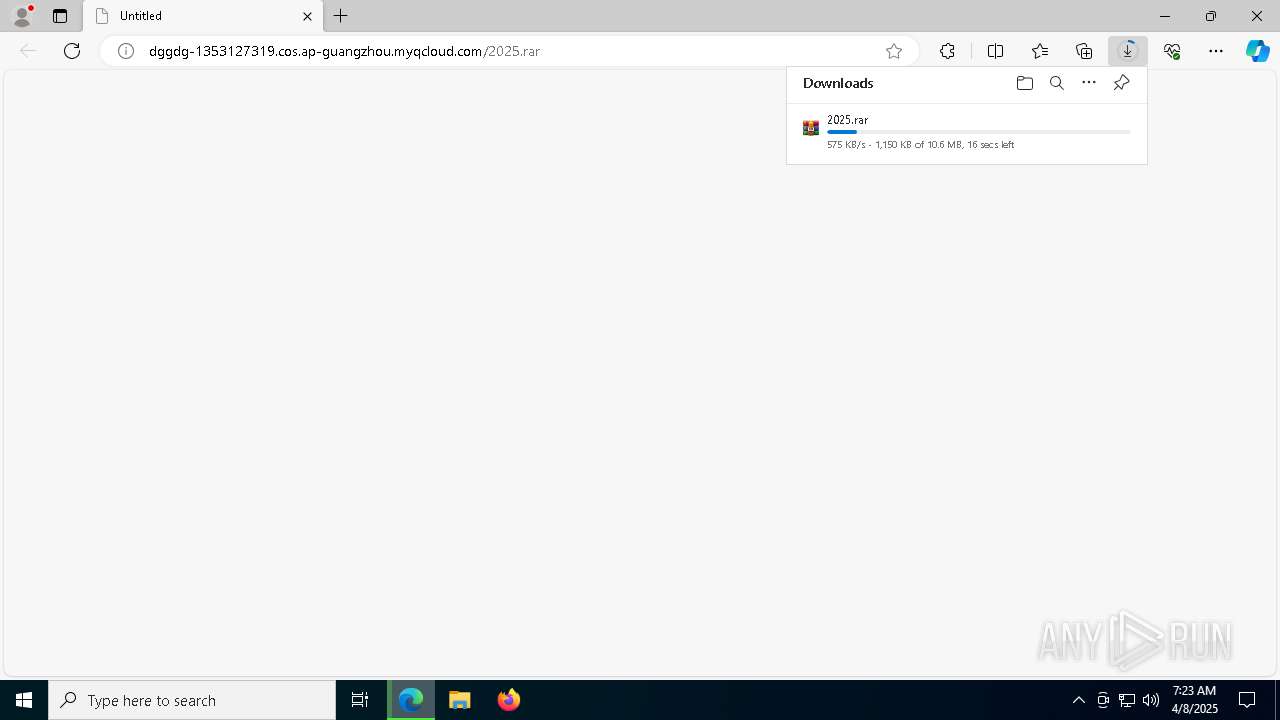
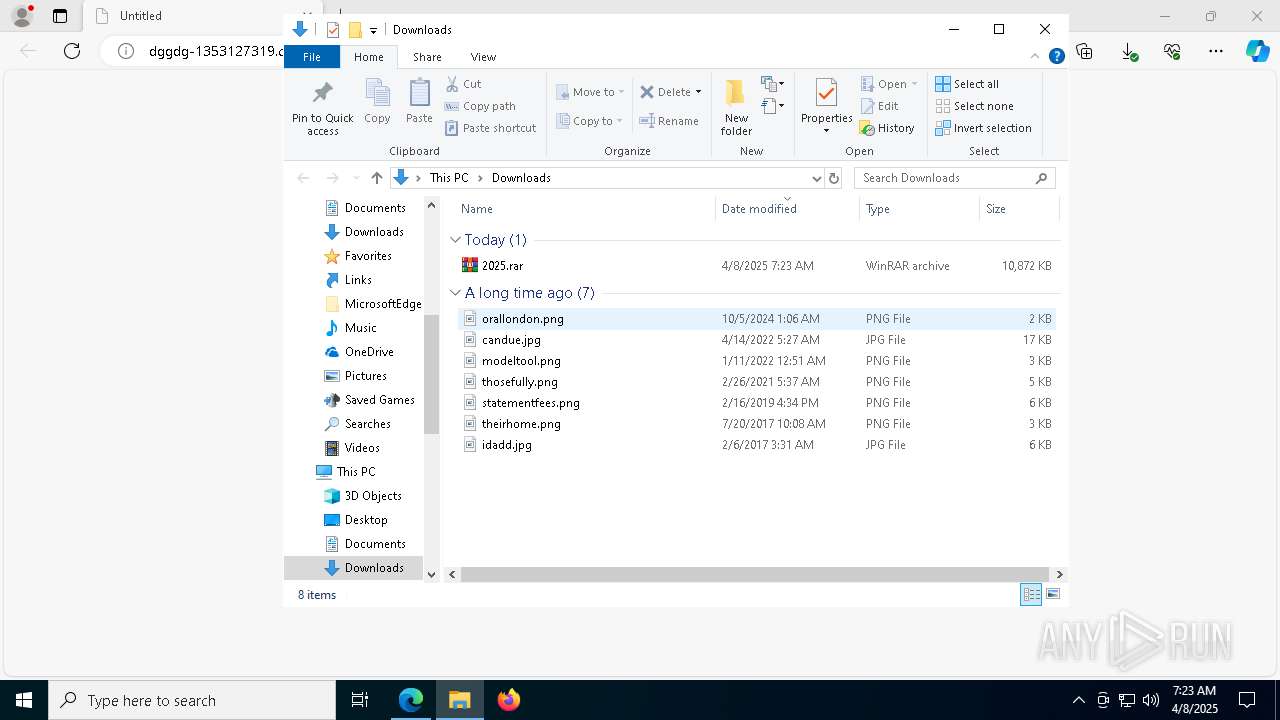
| URL: | dggdg-1353127319.cos.ap-guangzhou.myqcloud.com/2025.rar |
| Full analysis: | https://app.any.run/tasks/73c72fb4-50f3-4987-8837-15637ada3bb3 |
| Verdict: | Malicious activity |
| Analysis date: | April 08, 2025, 07:23:29 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 88543EE20BA994AED34F2FF51DD31EAA |
| SHA1: | 66CEDEE686EC921FD19E3577E6E761EC92701961 |
| SHA256: | 6E350C4B8AFDB7C07AE21F9B889AC96AAEDDA8D3DD9C835525F912E2E9EC0350 |
| SSDEEP: | 3:FLULO6UwV/QELCQeCeKAya:FLULObgYQVVAP |
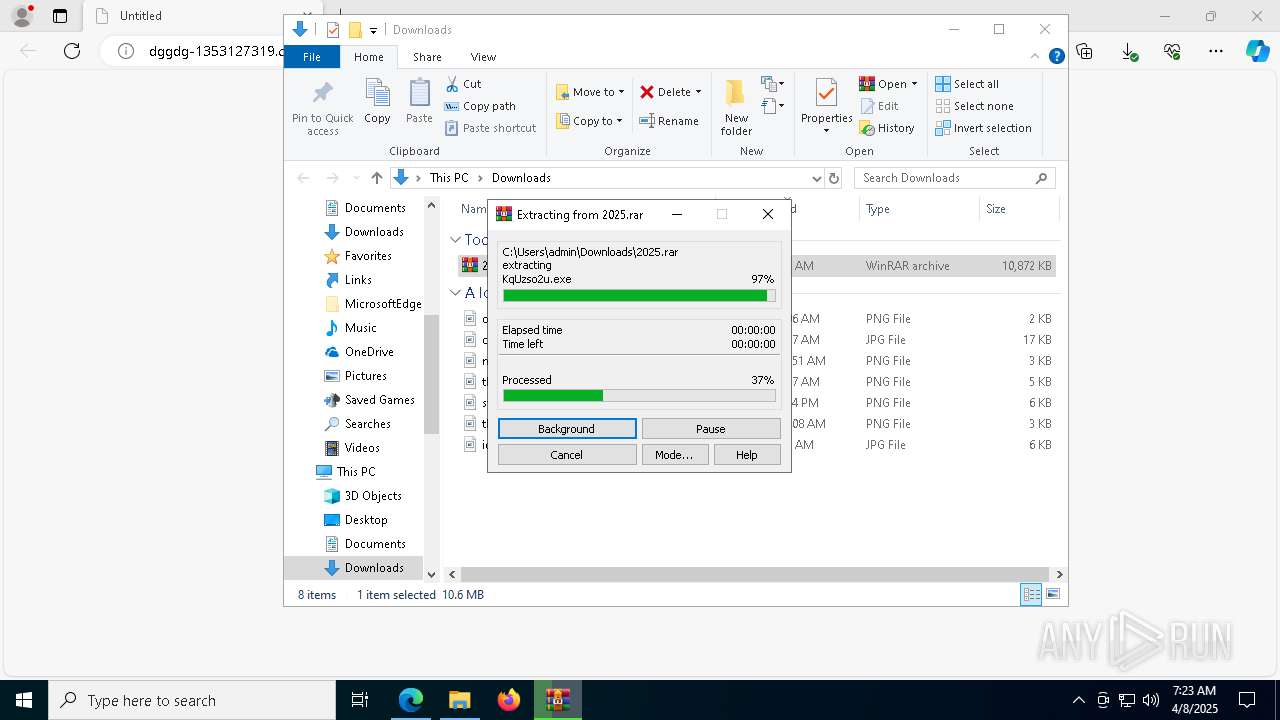
MALICIOUS
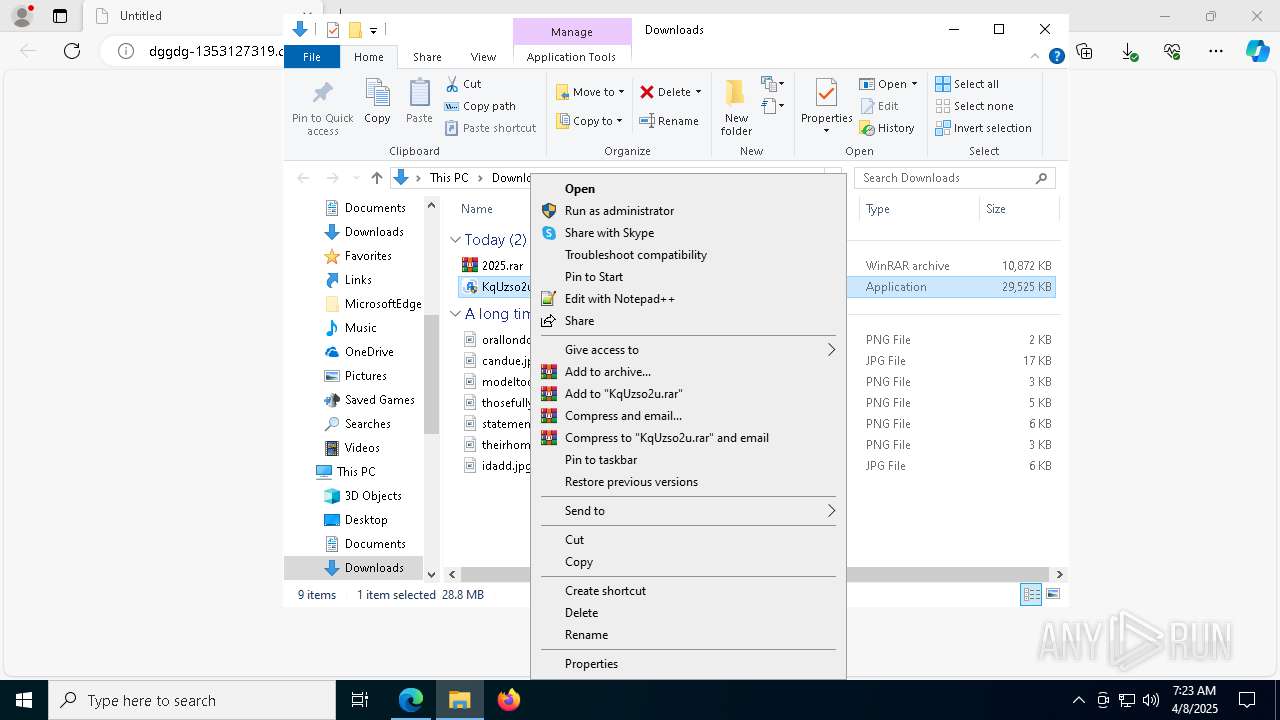
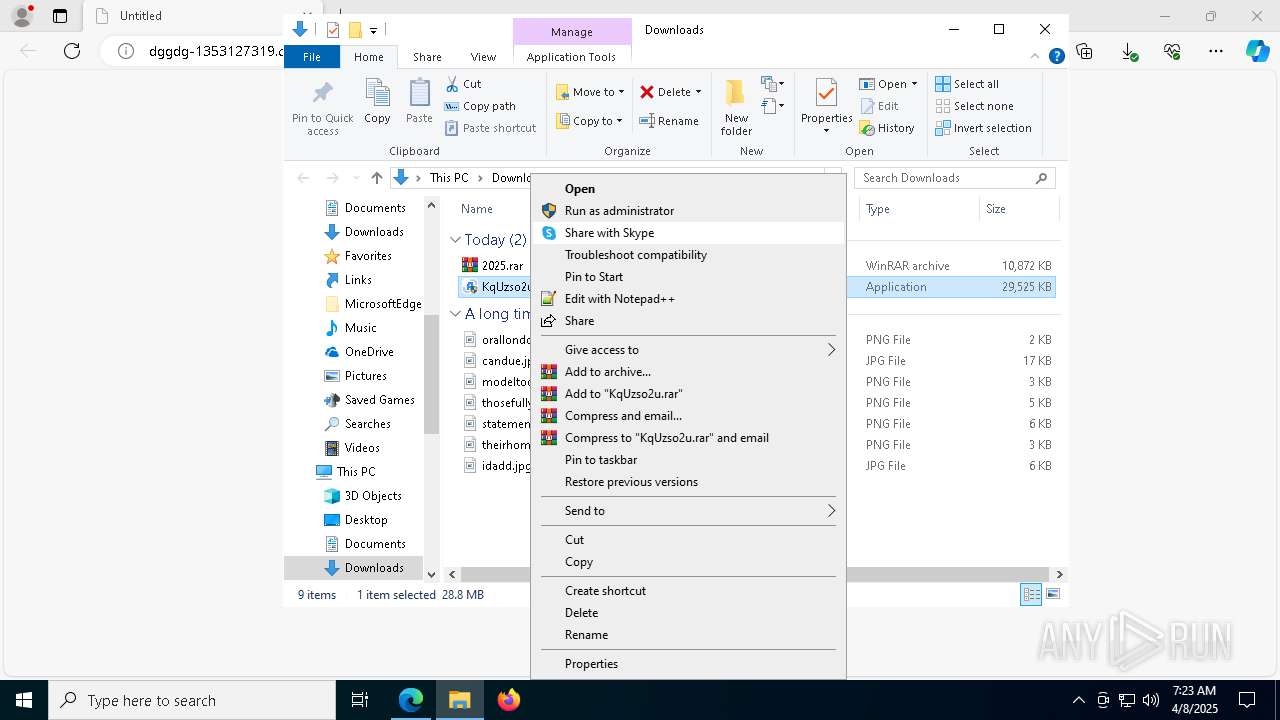
Executing a file with an untrusted certificate
- KqUzso2u.exe (PID: 8164)
- KqUzso2u.exe (PID: 2240)
Creates or modifies Windows services
- fZ7vbA.exe (PID: 8172)
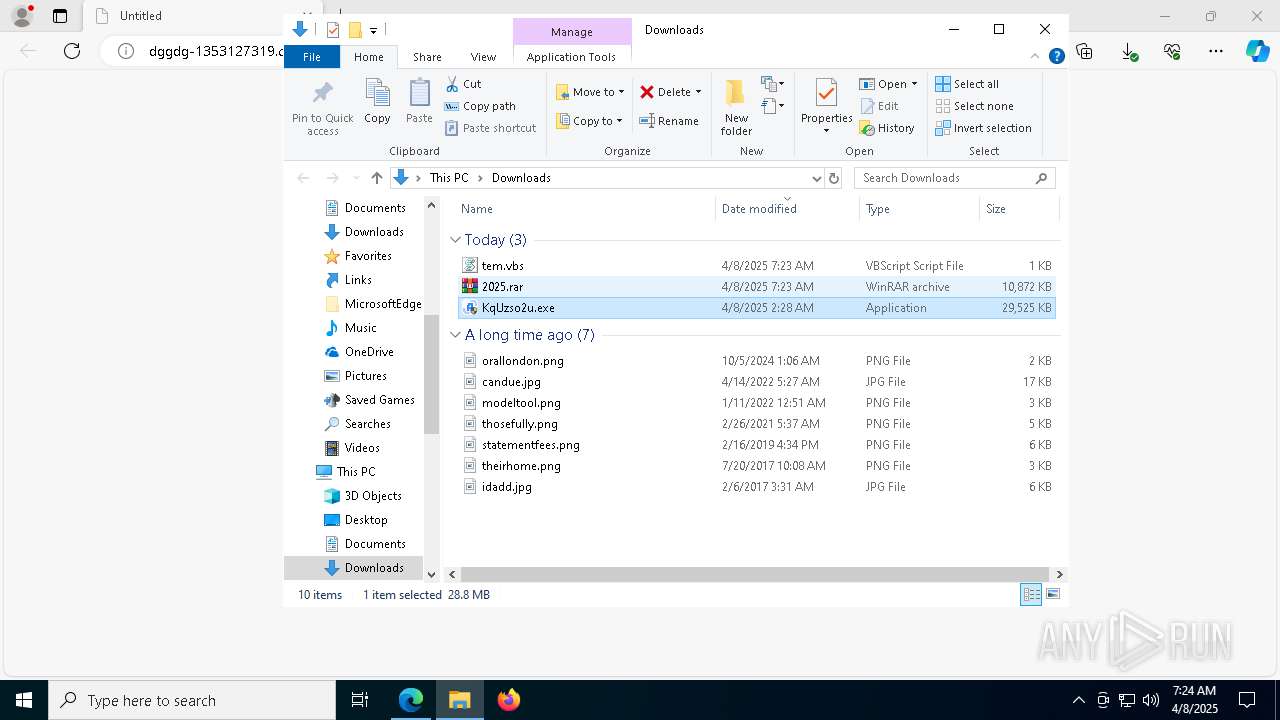
Deletes a file (SCRIPT)
- wscript.exe (PID: 4164)
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 4164)
SUSPICIOUS
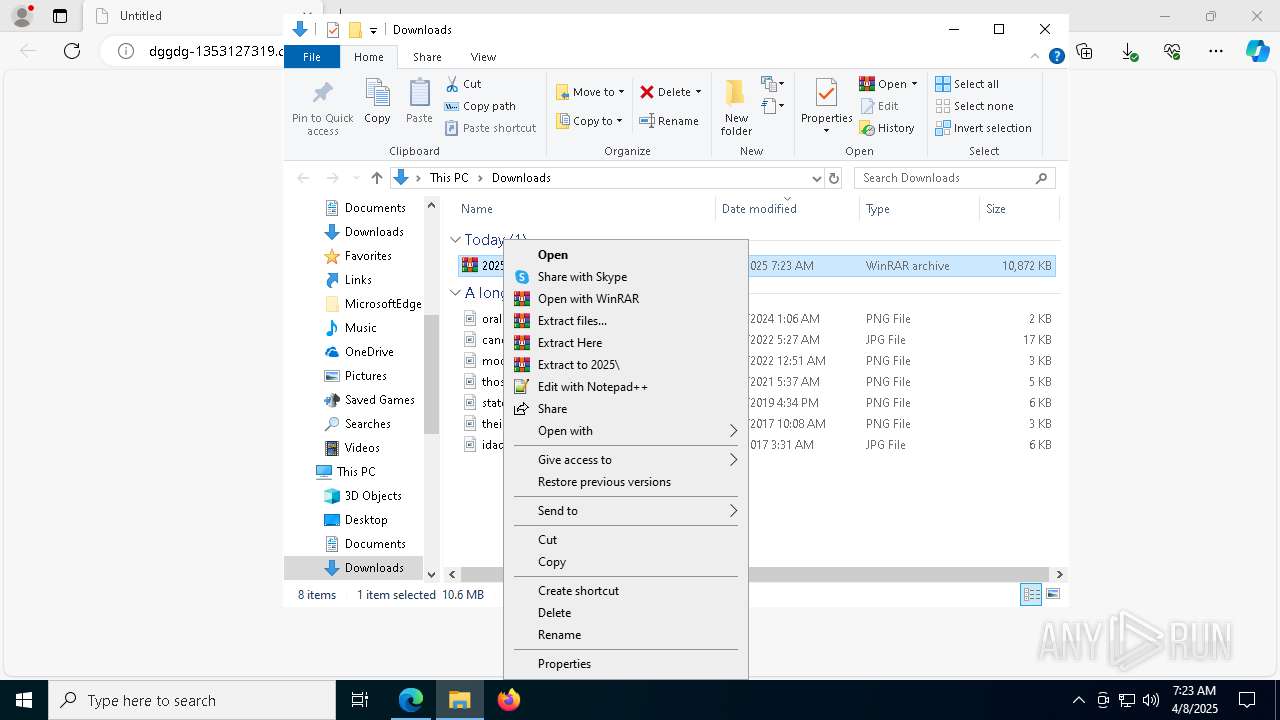
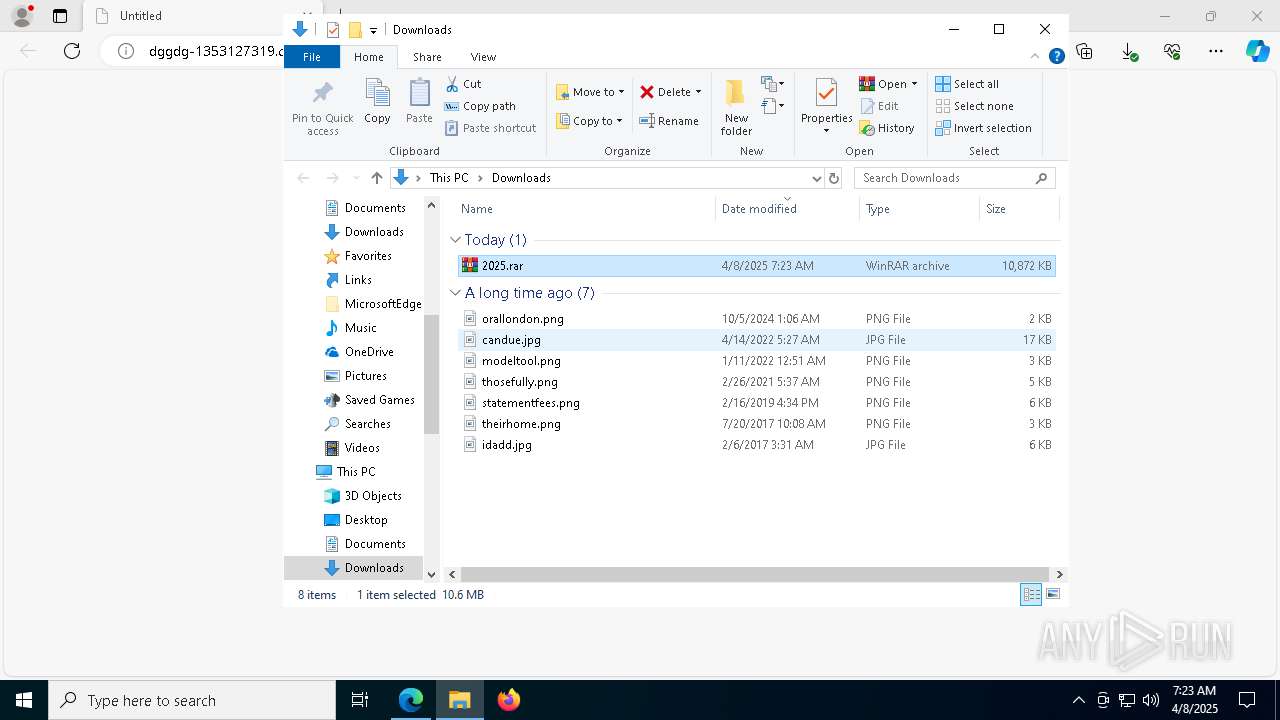
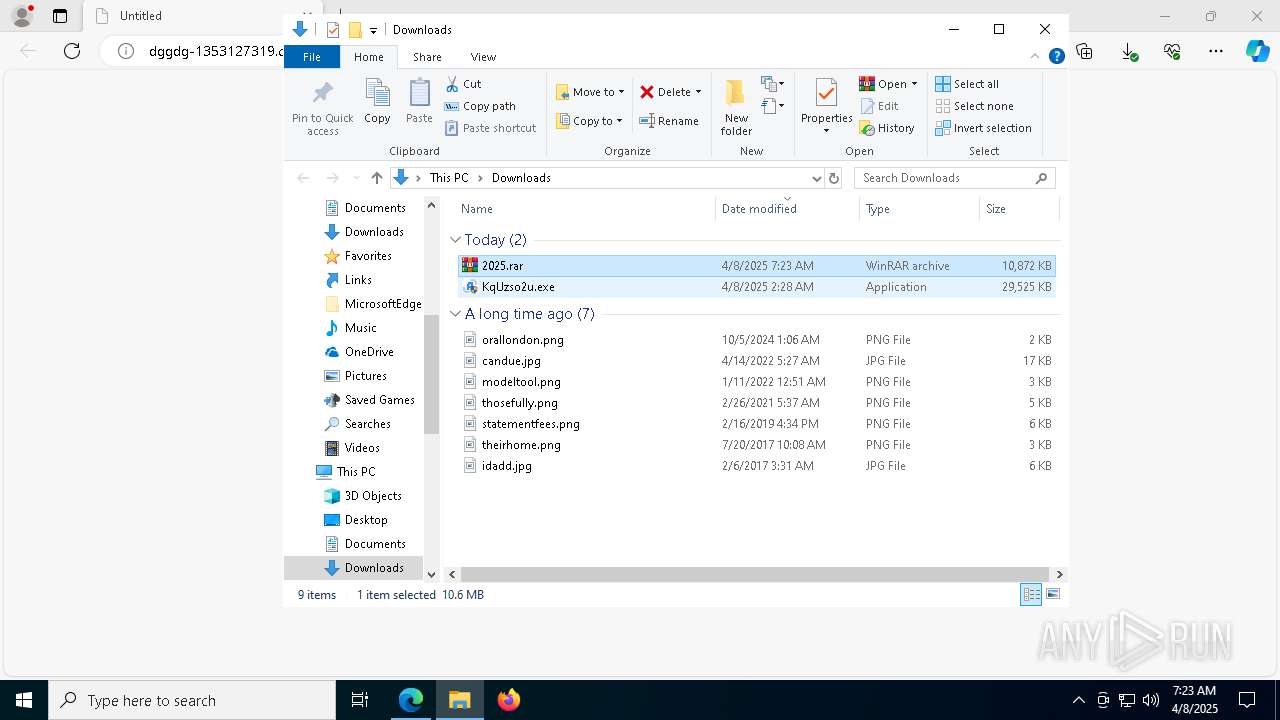
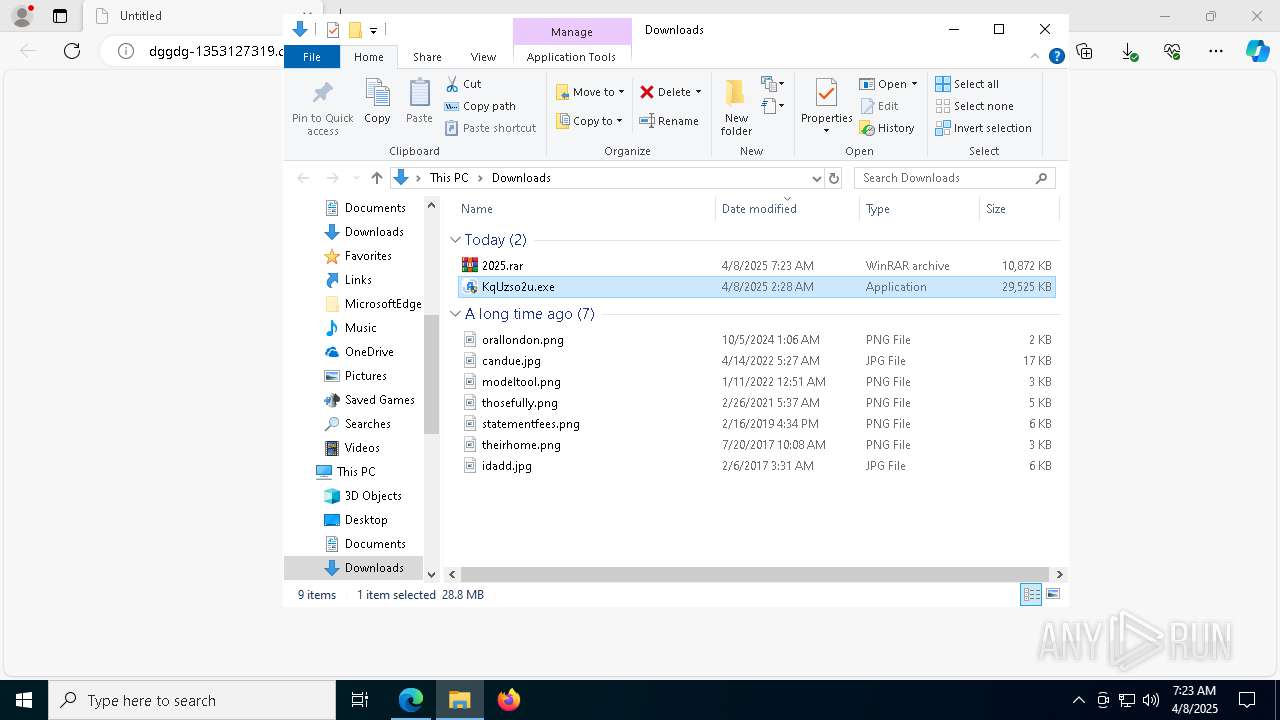
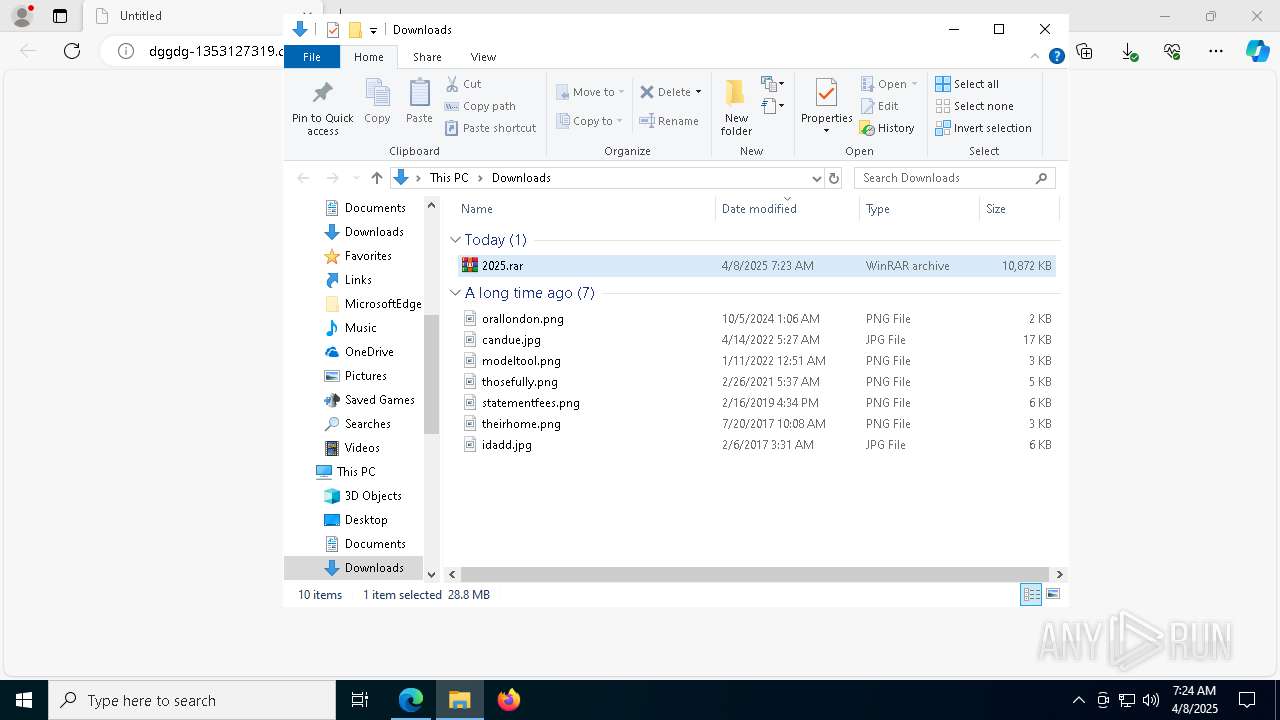
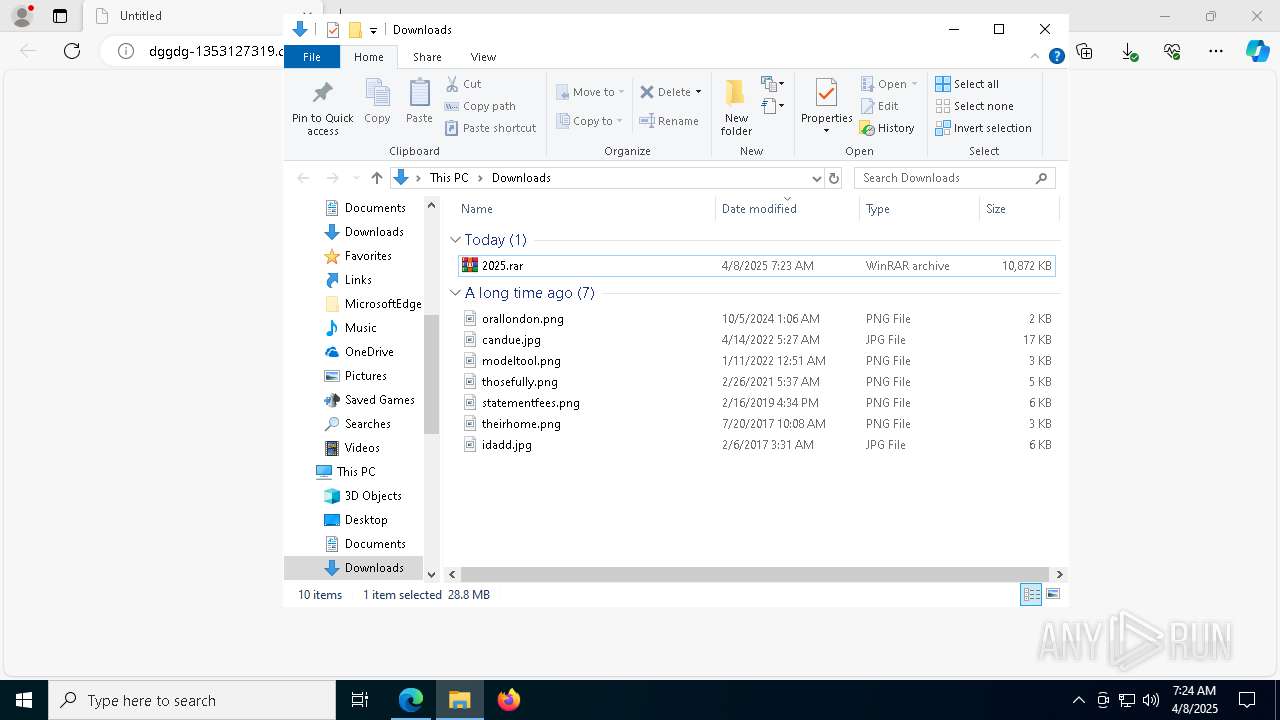
Process drops legitimate windows executable
- WinRAR.exe (PID: 5376)
Executable content was dropped or overwritten
- KqUzso2u.exe (PID: 2240)
- fZ7vbA.exe (PID: 8172)
Restarts service on failure
- sc.exe (PID: 2268)
Starts CMD.EXE for commands execution
- fZ7vbA.exe (PID: 8172)
- KqUzso2u.exe (PID: 2240)
Executing commands from a ".bat" file
- fZ7vbA.exe (PID: 8172)
Uses ROUTE.EXE to obtain the routing table information
- cmd.exe (PID: 5308)
Uses ROUTE.EXE to modify routing table
- cmd.exe (PID: 5048)
Creates file in the systems drive root
- all.exe (PID: 7736)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 4164)
Reads security settings of Internet Explorer
- KqUzso2u.exe (PID: 2240)
The process executes VB scripts
- KqUzso2u.exe (PID: 2240)
INFO
Checks supported languages
- identity_helper.exe (PID: 1628)
- KqUzso2u.exe (PID: 2240)
- fZ7vbA.exe (PID: 8172)
- all.exe (PID: 7736)
- all.exe (PID: 1328)
Reads Environment values
- identity_helper.exe (PID: 1628)
Application launched itself
- msedge.exe (PID: 4428)
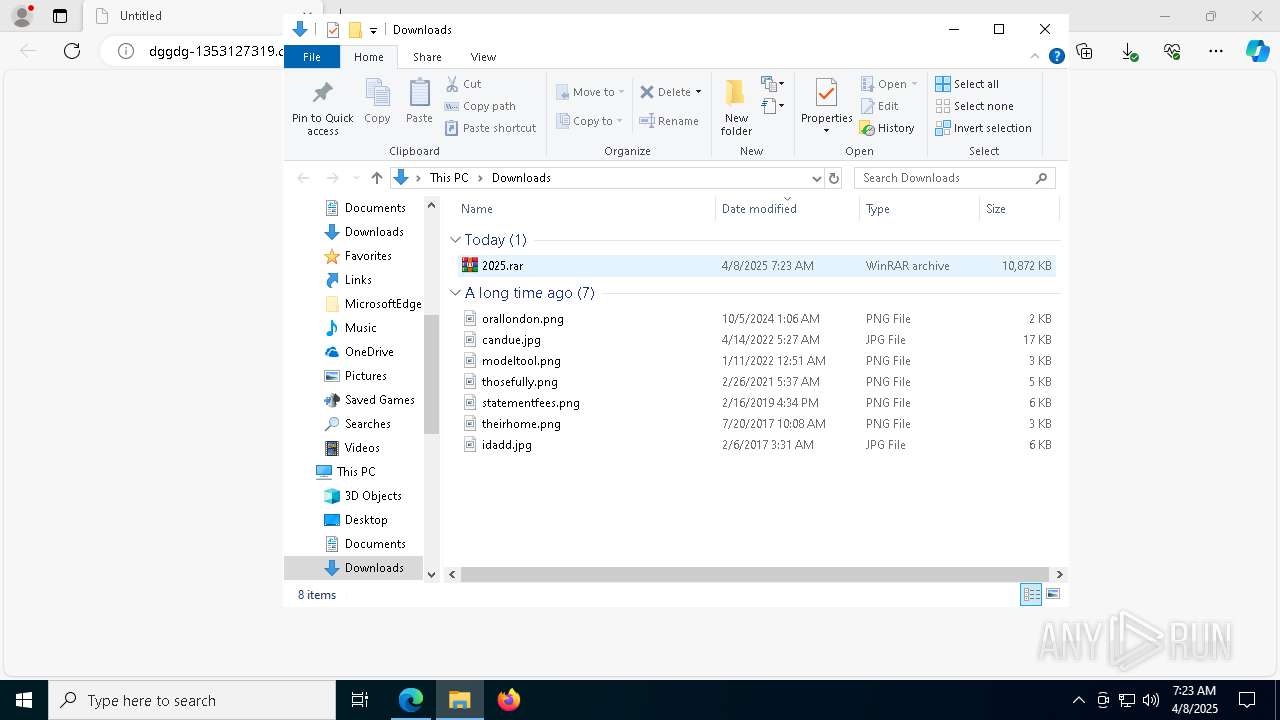
Manual execution by a user
- WinRAR.exe (PID: 5376)
- KqUzso2u.exe (PID: 8164)
- KqUzso2u.exe (PID: 2240)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 5376)
Autorun file from Downloads
- msedge.exe (PID: 8156)
The sample compiled with english language support
- WinRAR.exe (PID: 5376)
Reads the computer name
- identity_helper.exe (PID: 1628)
- fZ7vbA.exe (PID: 8172)
- KqUzso2u.exe (PID: 2240)
Disables trace logs
- KqUzso2u.exe (PID: 2240)
Adds a route via ROUTE.EXE
- ROUTE.EXE (PID: 1280)
The sample compiled with chinese language support
- fZ7vbA.exe (PID: 8172)
Creates files in the program directory
- fZ7vbA.exe (PID: 8172)
Reads the machine GUID from the registry
- KqUzso2u.exe (PID: 2240)
Deletes a route via ROUTE.EXE
- ROUTE.EXE (PID: 4448)
Process checks computer location settings
- KqUzso2u.exe (PID: 2240)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
200
Monitored processes
56
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=7048 --field-trial-handle=2348,i,644366733990944493,5074394628903757760,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1280 | route add 0.0.0.0 mask 0.0.0.0 192.168.100.2 metric 5 | C:\Windows\SysWOW64\ROUTE.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Route Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1328 | C:\all.exe C:\2.sys 2 | C:\all.exe | — | cmd.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 1628 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6512 --field-trial-handle=2348,i,644366733990944493,5074394628903757760,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1672 | "C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=6512 --field-trial-handle=2348,i,644366733990944493,5074394628903757760,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\122.0.2365.59\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1676 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1560 --field-trial-handle=2348,i,644366733990944493,5074394628903757760,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1804 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=1540 --field-trial-handle=2348,i,644366733990944493,5074394628903757760,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2240 | "C:\Users\admin\Downloads\KqUzso2u.exe" | C:\Users\admin\Downloads\KqUzso2u.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft (R) Contacts Import Tool Exit code: 0 Version: 5.6.8267.699 Modules
| |||||||||||||||
| 2268 | sc failure FastUserSwitchingCompatibility reset= 86400 actions= restart/1000 | C:\Windows\SysWOW64\sc.exe | — | fZ7vbA.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
8 408
Read events
8 371
Write events
37
Delete events
0
Modification events
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: A1838F83D5902F00 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 64748683D5902F00 | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {07E4FB36-9C78-45E5-AF85-3DCB50A26BB7} | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262786 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {E7C8264A-77E9-47DA-A67F-616C67BDAE4F} | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | MicrosoftEdgeAutoLaunch_29EBC4579851B72EE312C449CF839B1A |
Value: "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window --win-session-start | |||
| (PID) Process: | (4428) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\Clients\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\Commands\on-logon-autolaunch |
| Operation: | write | Name: | Enabled |
Value: 0 | |||
Executable files
10
Suspicious files
208
Text files
40
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10b98e.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10b99d.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10b99d.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10b99d.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10b9cc.TMP | — | |
MD5:— | SHA256:— | |||
| 4428 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
42
DNS requests
43
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
— | — | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
5972 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
5972 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
660 | svchost.exe | GET | 200 | 174.35.118.62:80 | http://2025.ip138.com/ | US | html | 917 b | unknown |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.178:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
660 | svchost.exe | GET | 301 | 138.113.149.153:80 | http://www.ip138.com/ | US | html | 162 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.53.40.178:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
7344 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7344 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7344 | msedge.exe | 13.107.253.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7344 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7344 | msedge.exe | 2.16.168.107:443 | bzib.nelreports.net | Akamai International B.V. | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
dggdg-1353127319.cos.ap-guangzhou.myqcloud.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7344 | msedge.exe | Misc activity | ET INFO Tencent Cloud Storage Domain in DNS Lookup (myqcloud .com) |
7344 | msedge.exe | Misc activity | ET INFO Tencent Cloud Storage Domain in DNS Lookup (myqcloud .com) |
7344 | msedge.exe | Misc activity | ET INFO Tencent Cloud Storage Domain in DNS Lookup (myqcloud .com) |
7344 | msedge.exe | Misc activity | ET INFO Tencent Cloud Storage Domain in DNS Lookup (myqcloud .com) |
7344 | msedge.exe | Misc activity | ET INFO Observed Tencent Cloud Storage Domain (myqcloud .com in TLS SNI) |
7344 | msedge.exe | Misc activity | ET INFO Observed Tencent Cloud Storage Domain (myqcloud .com in TLS SNI) |
660 | svchost.exe | Misc activity | ET INFO Possible Host Profile Exfiltration In Pipe Delimited Format |